| File name: | YoudaoDict-Setup-installe-LDZ.msc |
| Full analysis: | https://app.any.run/tasks/f3298a5b-fab3-4565-bd1e-1f4c045cb9d0 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 23:41:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with very long lines (61047), with CRLF line terminators |
| MD5: | 9B679C7F615EA748D0D511D6FC22316A |
| SHA1: | 86B80FDE33DF585E5D6B886127163C61E59232A6 |
| SHA256: | 8DECDFE5E000475D09F077A3D5B06843F1138E307141E0D0433526AE7037731D |
| SSDEEP: | 3072:3nIZcZhXen5+DO0GM8LpzdBA/TYUbEeTW7DX1Jc1zc:3nI2O+a00pnEY4Dq7DncZc |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- mmc.exe (PID: 4720)
Reads Internet Explorer settings
- mmc.exe (PID: 4720)
INFO
Creates files or folders in the user directory
- mmc.exe (PID: 4720)
Reads security settings of Internet Explorer
- mmc.exe (PID: 4720)
Checks proxy server information
- mmc.exe (PID: 4720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (ASCII) (62.5) |
|---|---|---|
| .html | | | HyperText Markup Language (37.5) |
EXIF
XMP
| MMC_ConsoleFileConsoleVersion: | 3 |
|---|---|
| MMC_ConsoleFileProgramMode: | UserSDI |
| MMC_ConsoleFileConsoleFileID: | a7bf8102-12e1-4226-aa6a-2ba71f6249d0 |
| MMC_ConsoleFileFrameStateShowStatusBar: | - |
| MMC_ConsoleFileFrameStateWindowPlacementShowCommand: | SW_HIDE |
| MMC_ConsoleFileFrameStateWindowPlacementPointName: | MinPosition |
| MMC_ConsoleFileFrameStateWindowPlacementPointX: | -1 |
| MMC_ConsoleFileFrameStateWindowPlacementPointY: | -1 |
| MMC_ConsoleFileFrameStateWindowPlacementRectangleName: | NormalPosition |
| MMC_ConsoleFileFrameStateWindowPlacementRectangleTop: | - |
| MMC_ConsoleFileFrameStateWindowPlacementRectangleBottom: | - |
| MMC_ConsoleFileFrameStateWindowPlacementRectangleLeft: | - |
| MMC_ConsoleFileFrameStateWindowPlacementRectangleRight: | - |
| MMC_ConsoleFileViewsViewId: | 1 |
| MMC_ConsoleFileViewsViewScopePaneWidth: | - |
| MMC_ConsoleFileViewsViewActionsPaneWidth: | -1 |
| MMC_ConsoleFileViewsViewBookMarkName: | RootNode |
| MMC_ConsoleFileViewsViewBookMarkNodeID: | 1 |
| MMC_ConsoleFileViewsViewWindowPlacementWpfRestoretomaximized: | |
| MMC_ConsoleFileViewsViewWindowPlacementShowCommand: | SW_HIDE |
| MMC_ConsoleFileViewsViewWindowPlacementPointName: | MinPosition |
| MMC_ConsoleFileViewsViewWindowPlacementPointX: | -1 |
| MMC_ConsoleFileViewsViewWindowPlacementPointY: | -1 |
| MMC_ConsoleFileViewsViewWindowPlacementRectangleName: | NormalPosition |
| MMC_ConsoleFileViewsViewWindowPlacementRectangleTop: | - |
| MMC_ConsoleFileViewsViewWindowPlacementRectangleBottom: | - |
| MMC_ConsoleFileViewsViewWindowPlacementRectangleLeft: | - |
| MMC_ConsoleFileViewsViewWindowPlacementRectangleRight: | - |
| MMC_ConsoleFileViewsViewViewOptionsViewMode: | Report |
| MMC_ConsoleFileViewsViewViewOptionsScopePaneVisible: | |
| MMC_ConsoleFileViewsViewViewOptionsActionsPaneVisible: | - |
| MMC_ConsoleFileViewsViewViewOptionsDescriptionBarVisible: | - |
| MMC_ConsoleFileViewsViewViewOptionsDefaultColumn0Width: | 200 |
| MMC_ConsoleFileViewsViewViewOptionsDefaultColumn1Width: | - |
| MMC_ConsoleFileVisualAttributesIconIndex: | 85 |
| MMC_ConsoleFileVisualAttributesIconFile: | %windir%\System32\imageres.dll |
| MMC_ConsoleFileVisualAttributesIconImageName: | Large |
| MMC_ConsoleFileVisualAttributesIconImageBinaryRefIndex: | 2 |
| MMC_ConsoleFileFavoritesFavoriteType: | Group |
| MMC_ConsoleFileFavoritesFavoriteStringName: | Name |
| MMC_ConsoleFileFavoritesFavoriteStringId: | 1 |
| MMC_ConsoleFileFavoritesFavoriteFavorites: | - |
| MMC_ConsoleFileScopeTreeSnapinCacheSnapinClsid: | {C96401CC-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeSnapinCacheSnapinAllExtensionsEnabled: | |
| MMC_ConsoleFileScopeTreeNodesNodeId: | 1 |
| MMC_ConsoleFileScopeTreeNodesNodeImageIdx: | - |
| MMC_ConsoleFileScopeTreeNodesNodeClsid: | {C96401CC-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeNodesNodePreload: | |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeId: | 13 |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeImageIdx: | - |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeClsid: | {C96401D1-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodePreload: | |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeNodes: | - |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeStringName: | Name |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeStringId: | 38 |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentDatasComponentDataGuidName: | Snapin |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentDatasComponentDataGuid: | {C96401D1-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentDatasComponentDataStreamBinaryRefIndex: | - |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponents: | - |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentsComponentViewID: | 1 |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentsComponentGuidName: | Snapin |
| MMC_ConsoleFileScopeTreeNodesNodeNodesNodeComponentsComponentGuid: | {C96401CF-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeNodesNodeStringName: | Name |
| MMC_ConsoleFileScopeTreeNodesNodeStringId: | 8 |
| MMC_ConsoleFileScopeTreeNodesNodeComponentDatasComponentDataGuidName: | Snapin |
| MMC_ConsoleFileScopeTreeNodesNodeComponentDatasComponentDataGuid: | {C96401CC-0E17-11D3-885B-00C04F72C717} |
| MMC_ConsoleFileScopeTreeNodesNodeComponents: | - |
| MMC_ConsoleFileConsoleTaskpads: | - |
| MMC_ConsoleFileViewSettingsCache: | - |
| MMC_ConsoleFileColumnSettingsCache: | - |
| MMC_ConsoleFileStringTablesIdentifierPoolAbsoluteMin: | 1 |
| MMC_ConsoleFileStringTablesIdentifierPoolAbsoluteMax: | 65535 |
| MMC_ConsoleFileStringTablesIdentifierPoolNextAvailable: | 40 |
| MMC_ConsoleFileStringTablesStringTableGuid: | {71E5B33E-1064-11D2-808F-0000F875A9CE} |
| MMC_ConsoleFileStringTablesStringTableStringsStringId: | 1 |
| MMC_ConsoleFileStringTablesStringTableStringsStringRefs: | 1 |
| MMC_ConsoleFileStringTablesStringTableStringsString: | (Binary data 9 bytes, use -b option to extract) |
| MMC_ConsoleFileBinaryStorageBinary: | AQAAABQAAAAAAAAAJgAAACcAAAA= |
| MMC_ConsoleFileBinaryStorageBinaryName: | CONSOLE_FILE_ICON_LARGE |
Total processes
134
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4720 | "C:\WINDOWS\system32\mmc.exe" C:\Users\admin\Desktop\YoudaoDict-Setup-installe-LDZ.msc | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6064 | "C:\WINDOWS\system32\mmc.exe" C:\Users\admin\Desktop\YoudaoDict-Setup-installe-LDZ.msc | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 780
Read events
1 767
Write events
13
Delete events
0
Modification events
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @mmcbase.dll,-214 |
Value: ActiveX Control | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @mmcbase.dll,-14010 |
Value: Link to Web Address | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4720) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
87
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
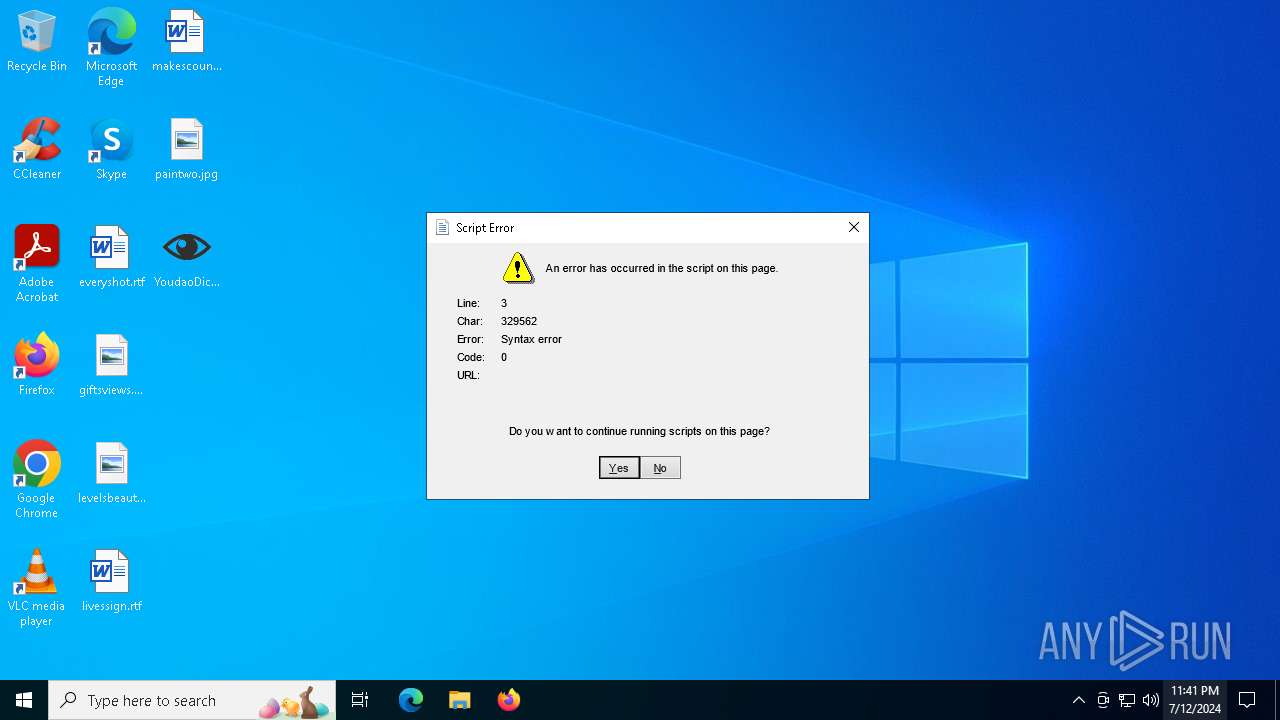
4720 | mmc.exe | GET | 404 | 154.82.92.201:80 | http://154.82.92.201/0day.js | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4448 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4720 | mmc.exe | 154.82.92.201:80 | — | TERAEXCH | HK | malicious |
4656 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | unknown |
1060 | svchost.exe | 2.19.105.250:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3680 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3040 | OfficeClickToRun.exe | 52.111.227.14:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |