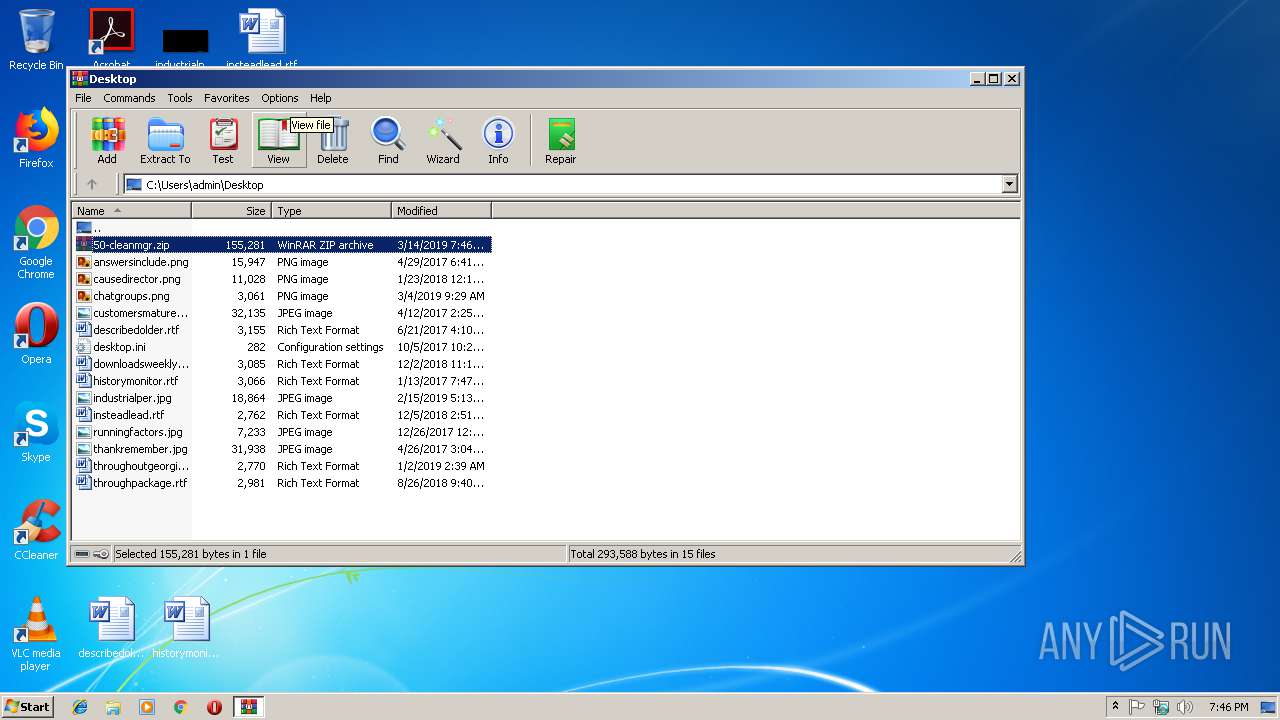
| download: | 50-cleanmgr |
| Full analysis: | https://app.any.run/tasks/4e070233-4915-4dfd-b062-e88908b88de8 |
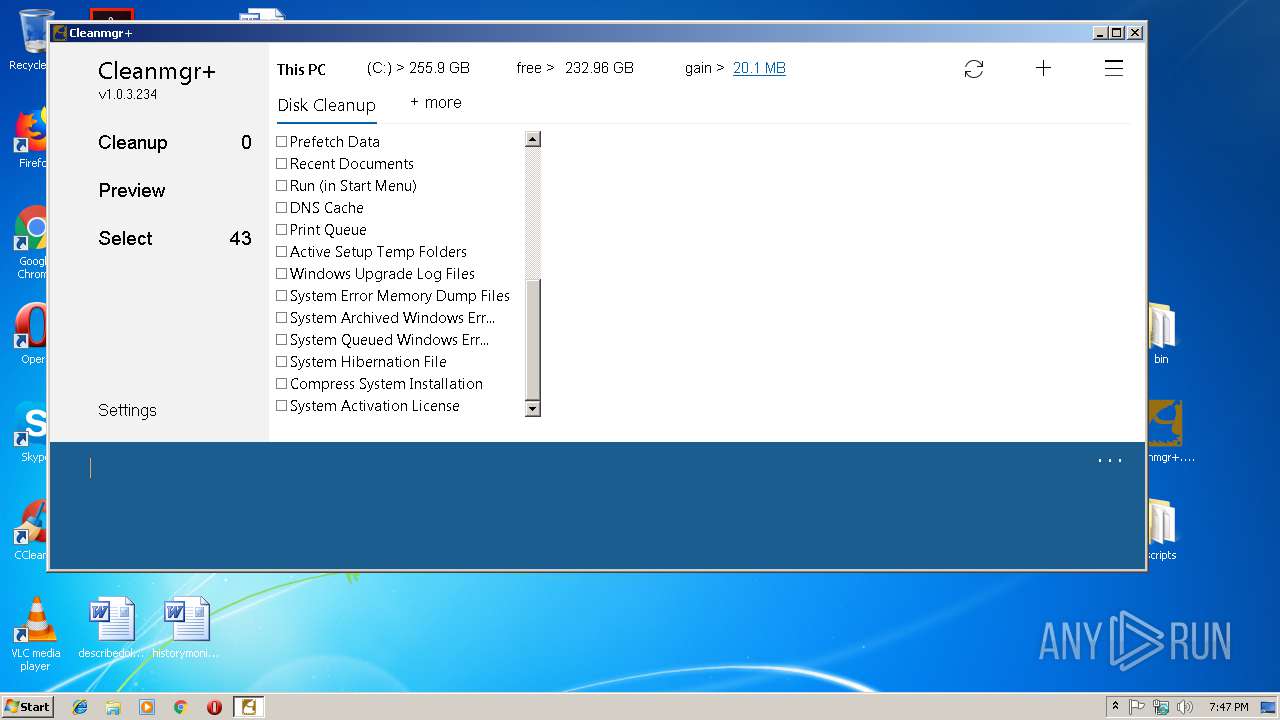
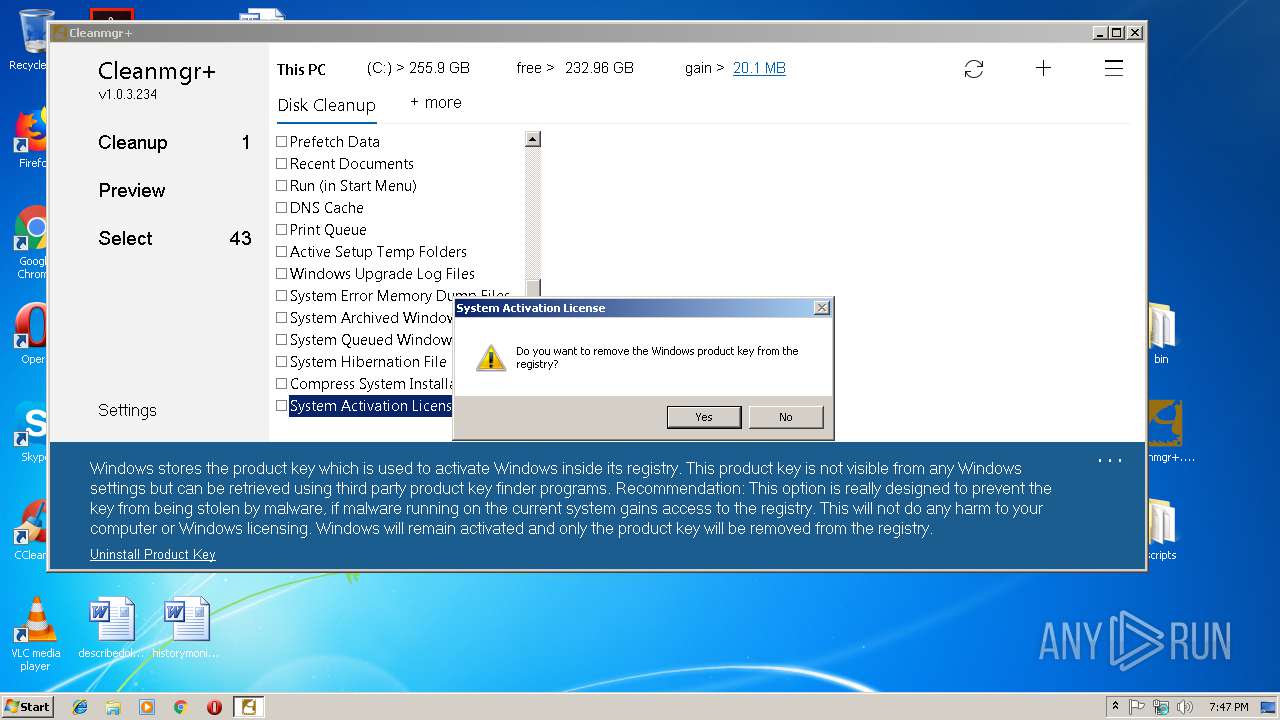
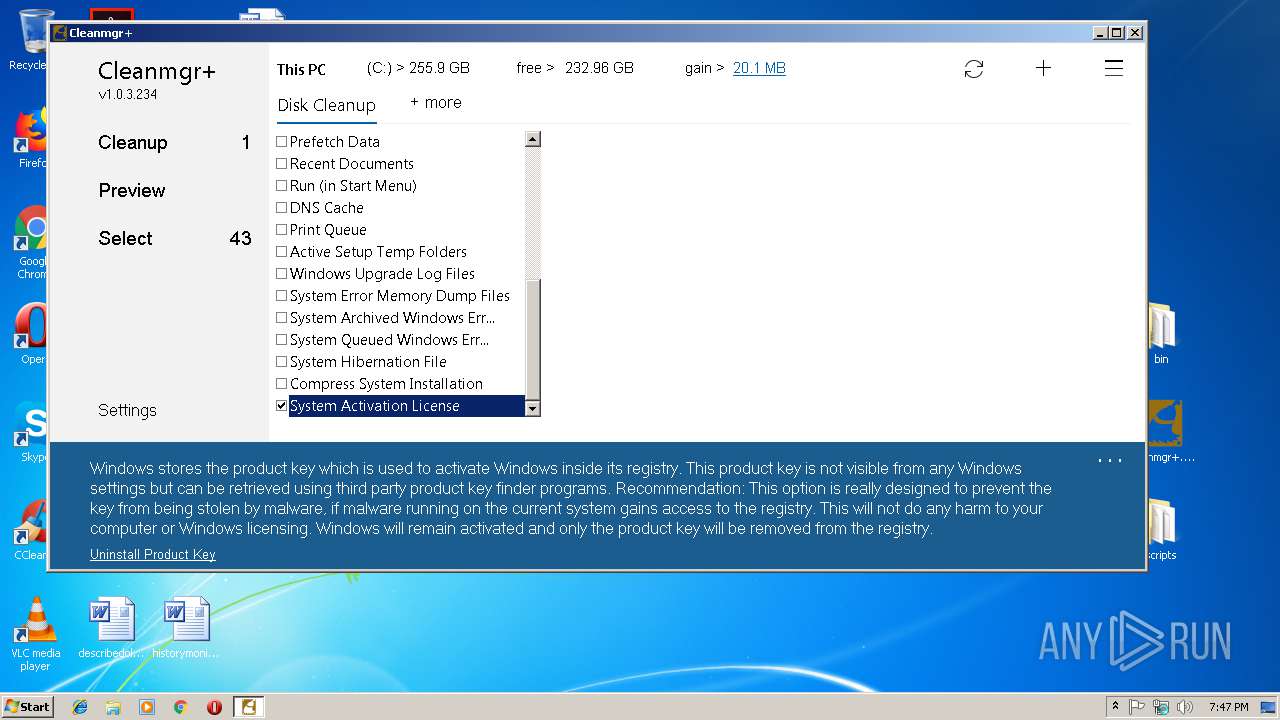
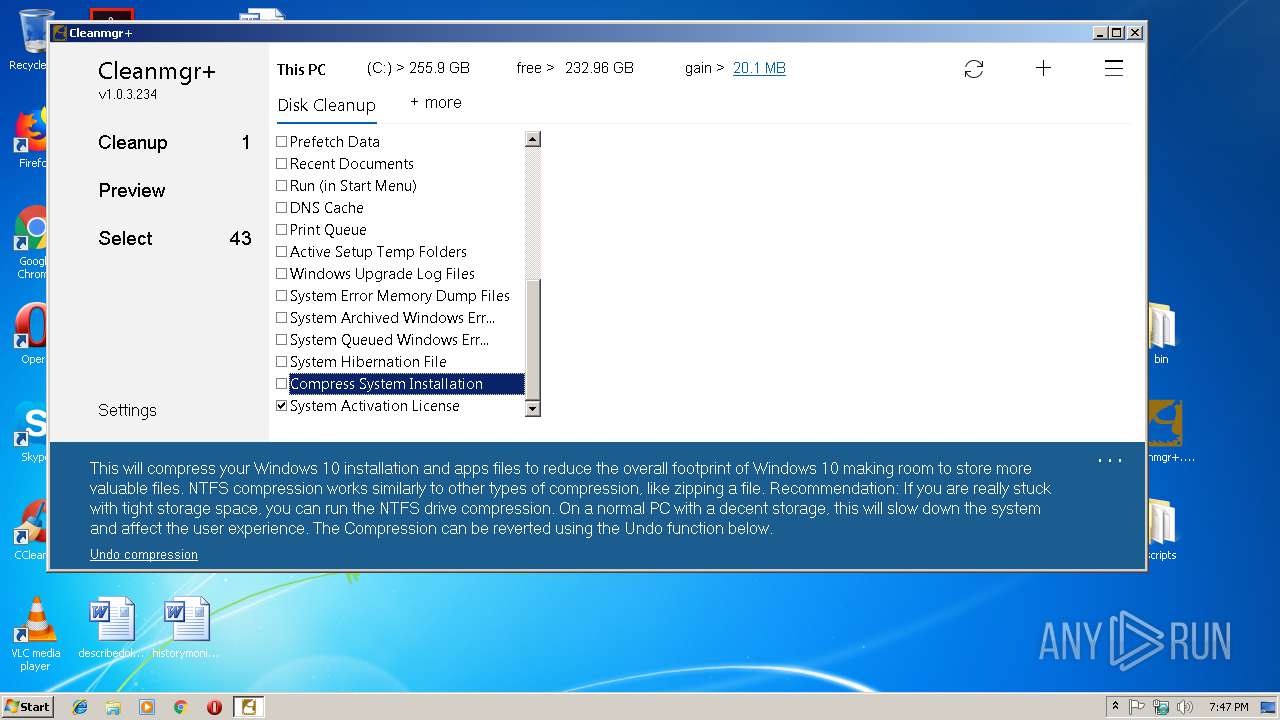
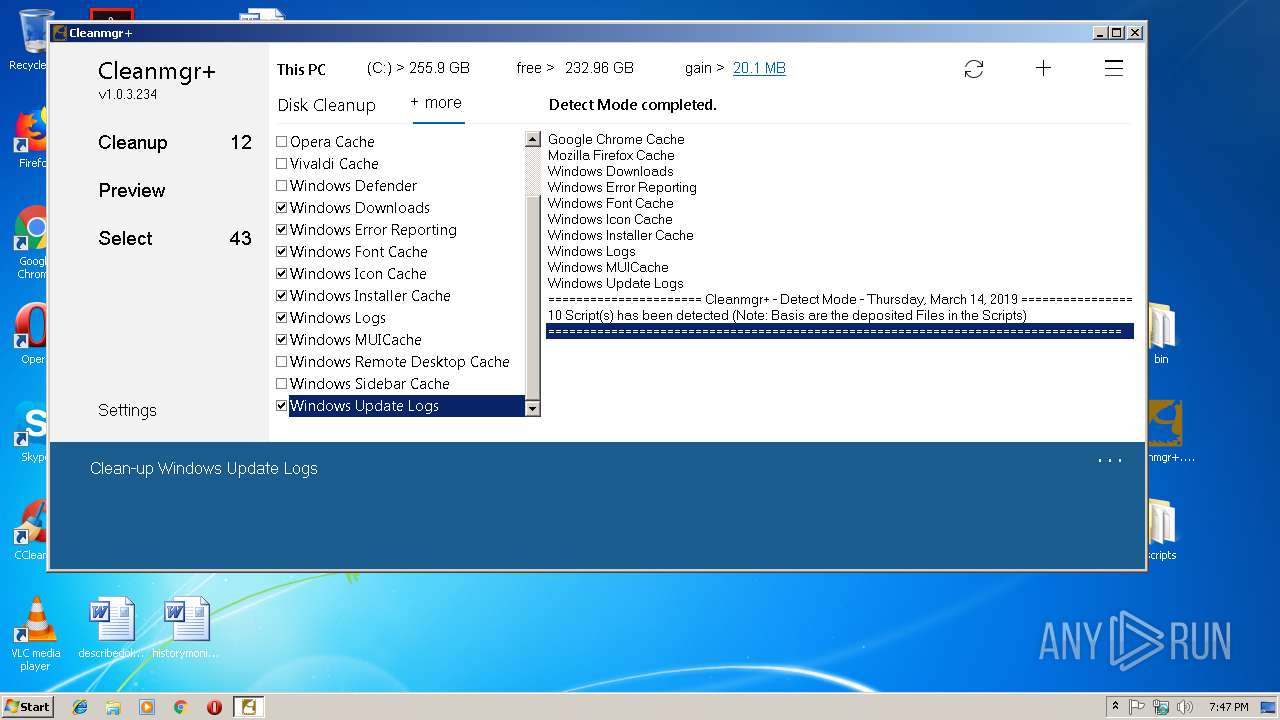
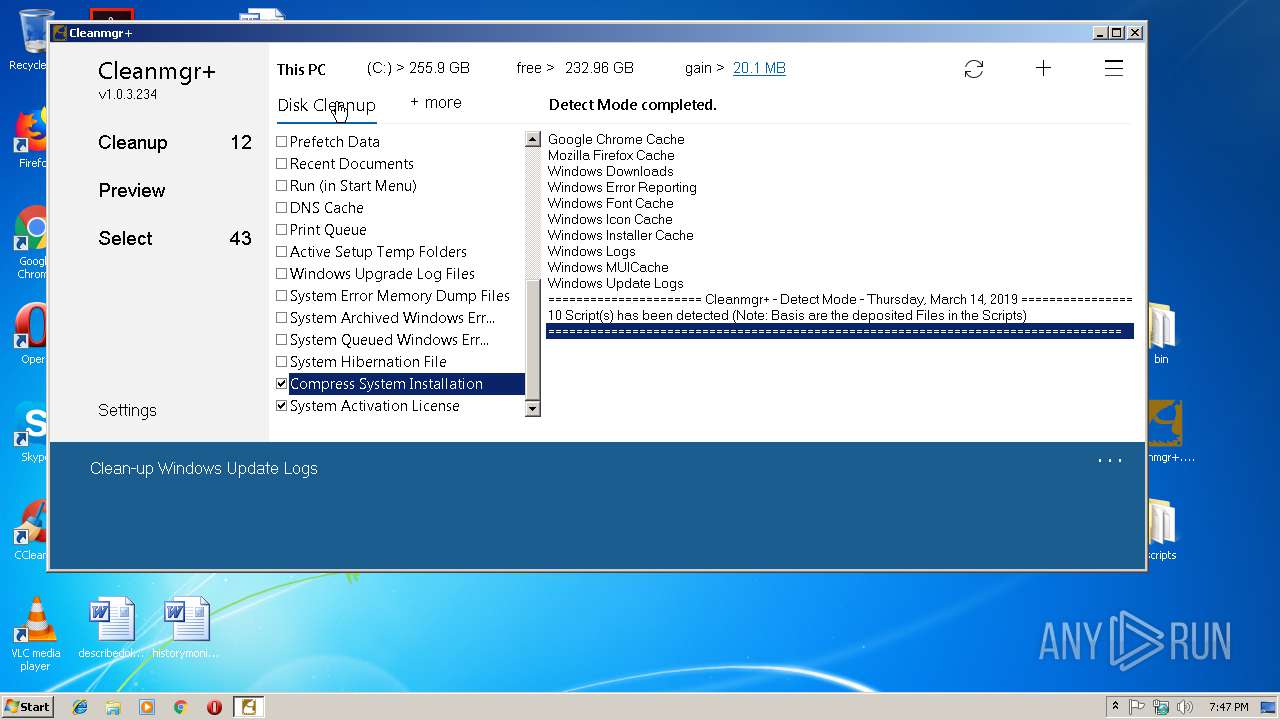
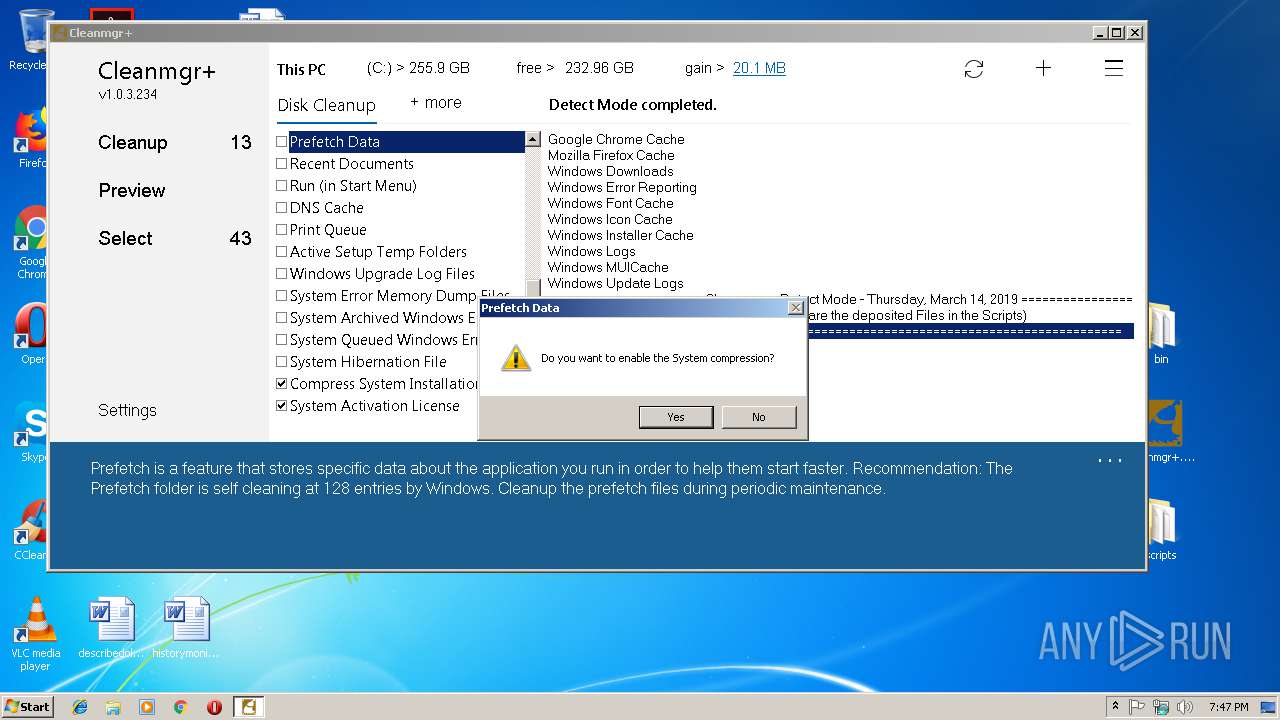
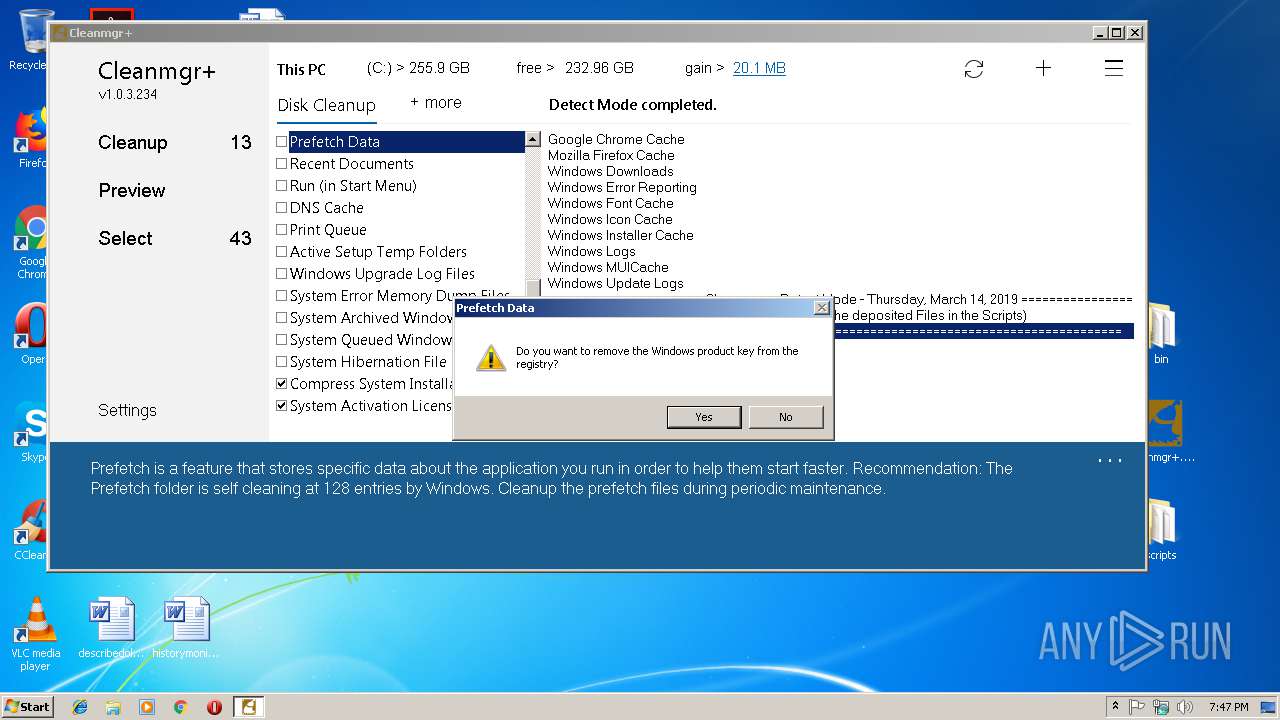
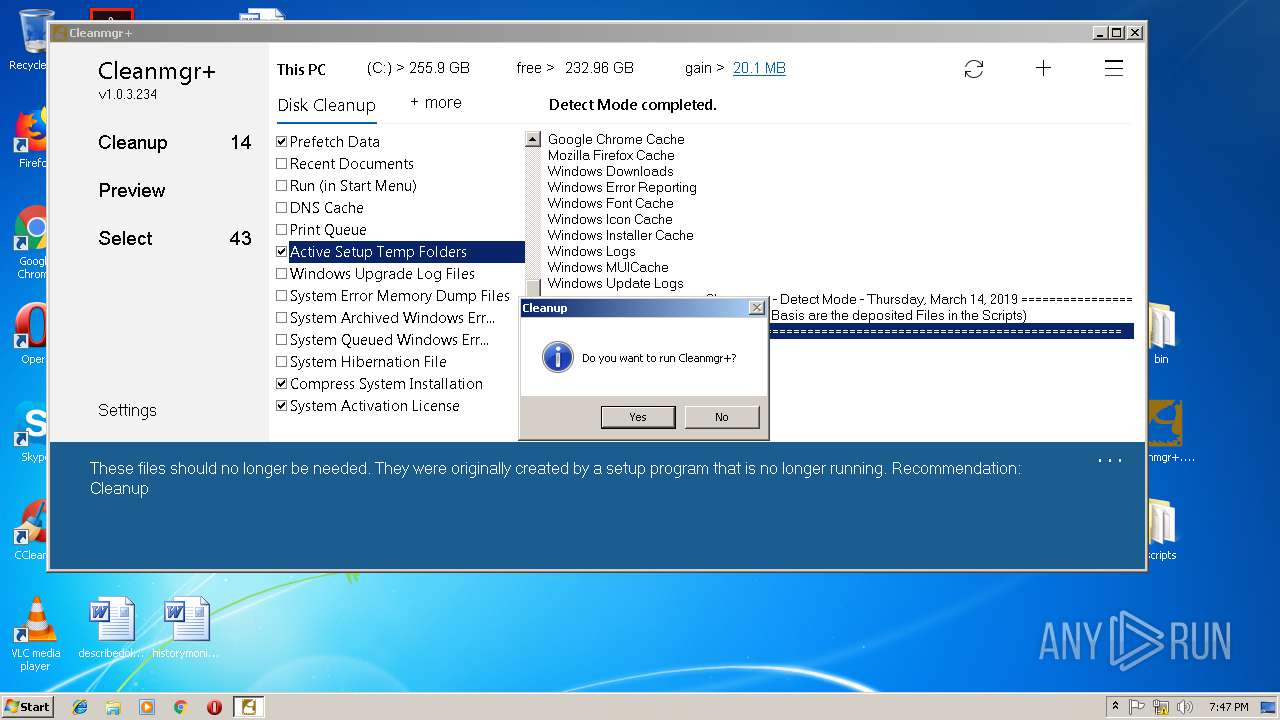
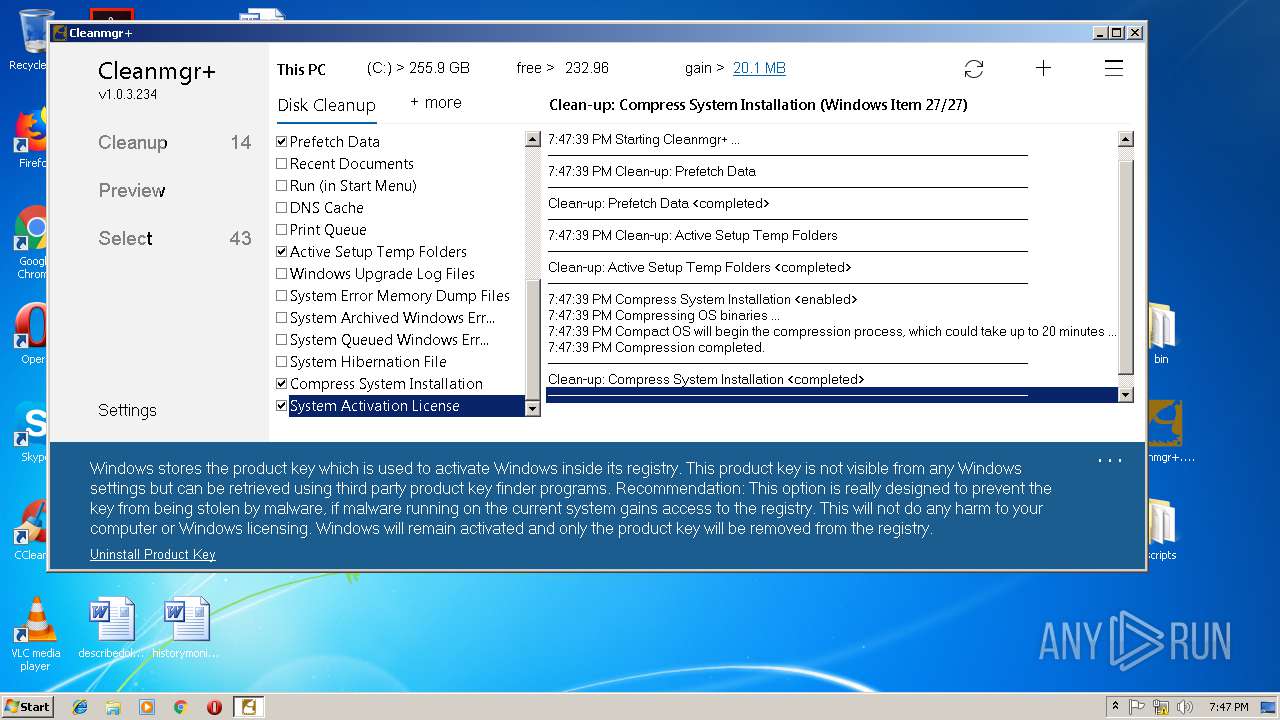
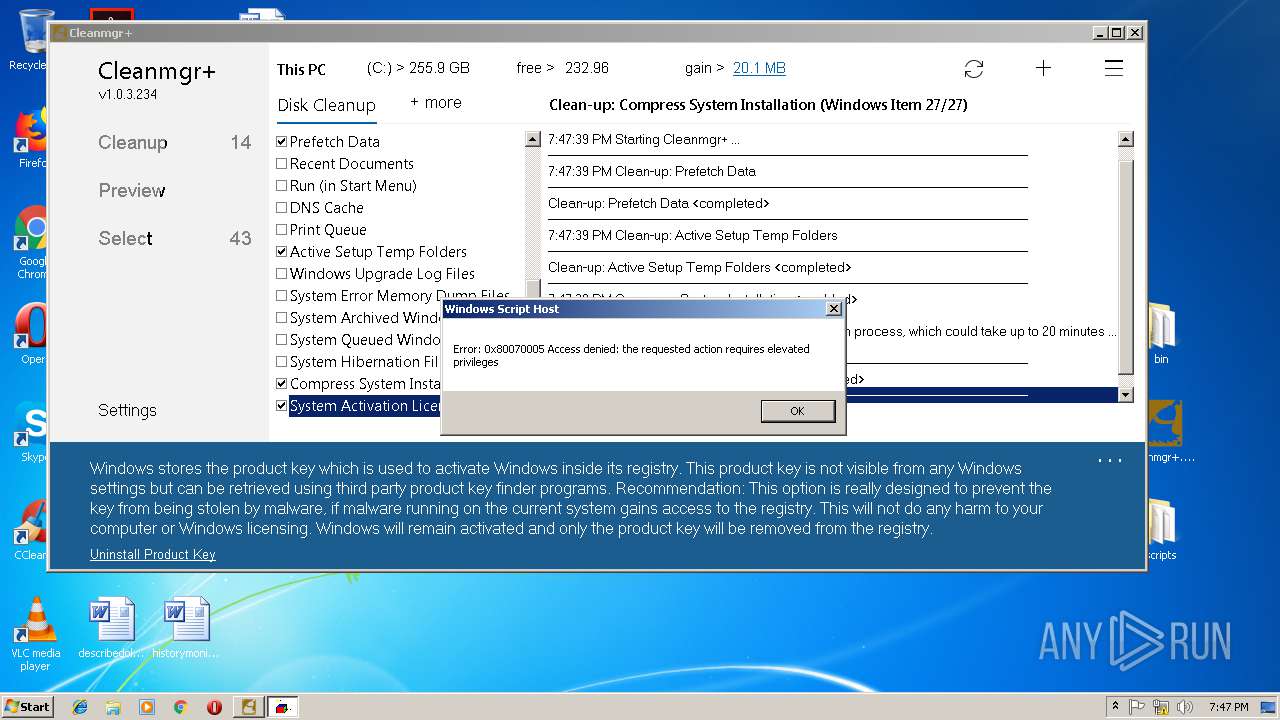
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 19:46:17 |
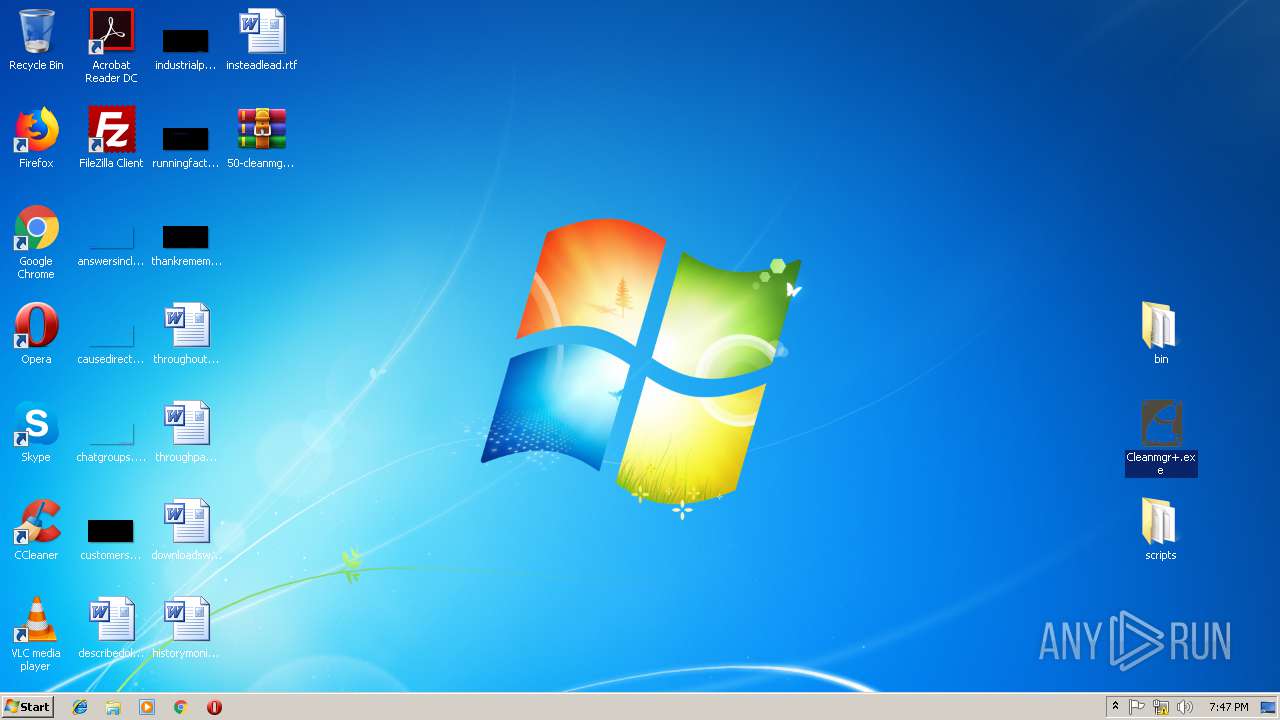
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BFF153DC4180EA9D22A835D5D395D2B1 |
| SHA1: | E4C39669CE27AB03DFC304AF31667F0689DC4819 |
| SHA256: | 8DE9A135D4BCD350DDE9C044F9E2DC7C5B8D9E5524F72569F54AB319F57E6704 |
| SSDEEP: | 3072:H4+GMxUJ6jGOg0xF7Xe7WH+C8tgJpRBxVnDyJXNkpuIjNWFxnYX8Qhxv1p8:HuMBgmF7XlH/JpxlDyJyBhWxInvs |
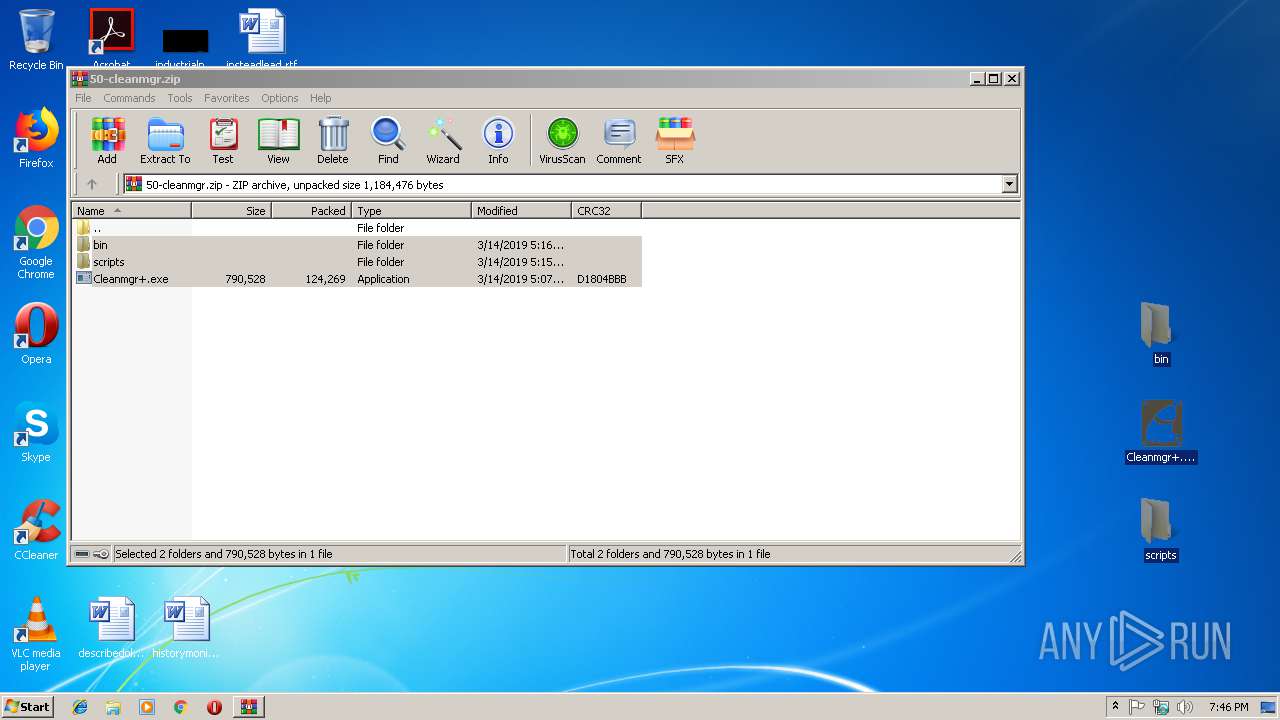
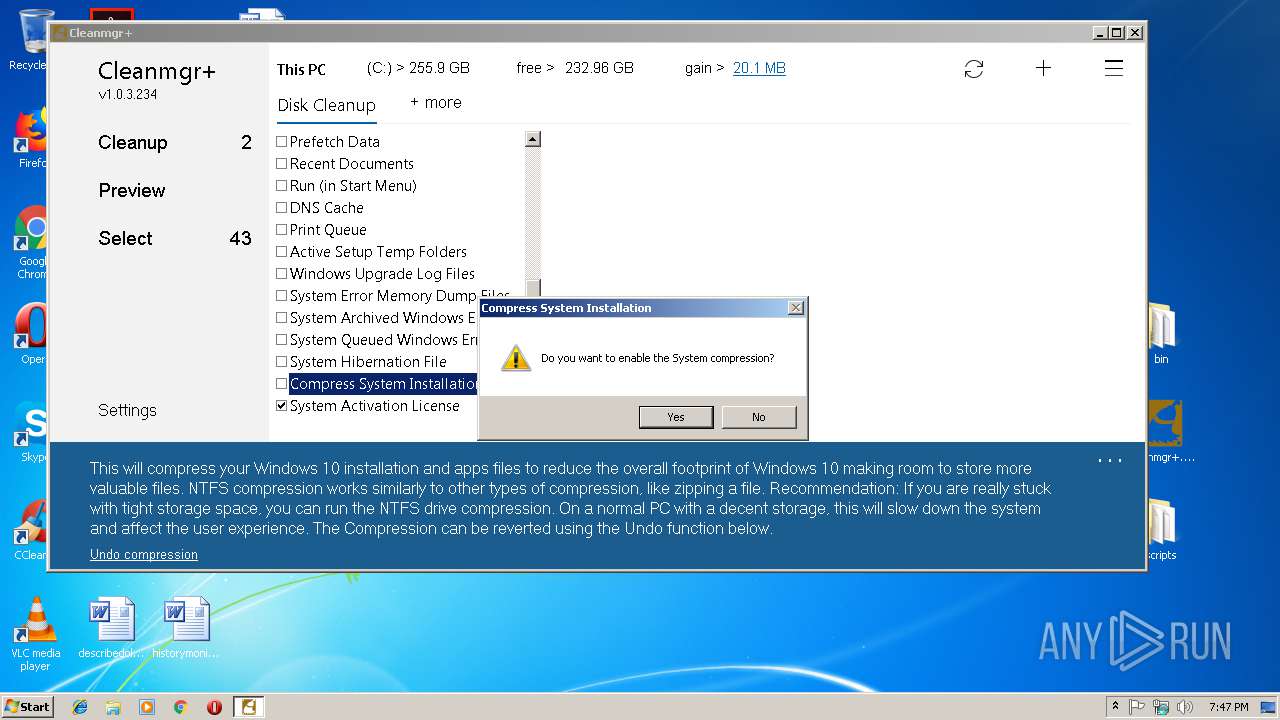
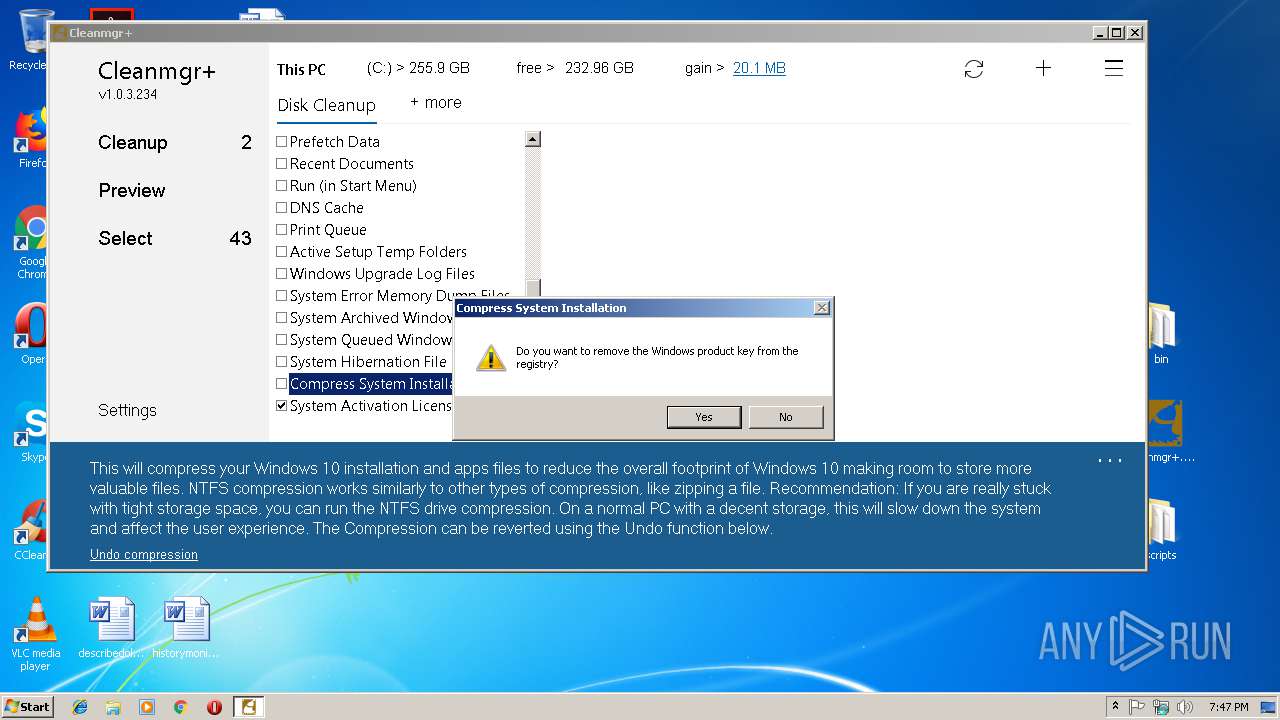
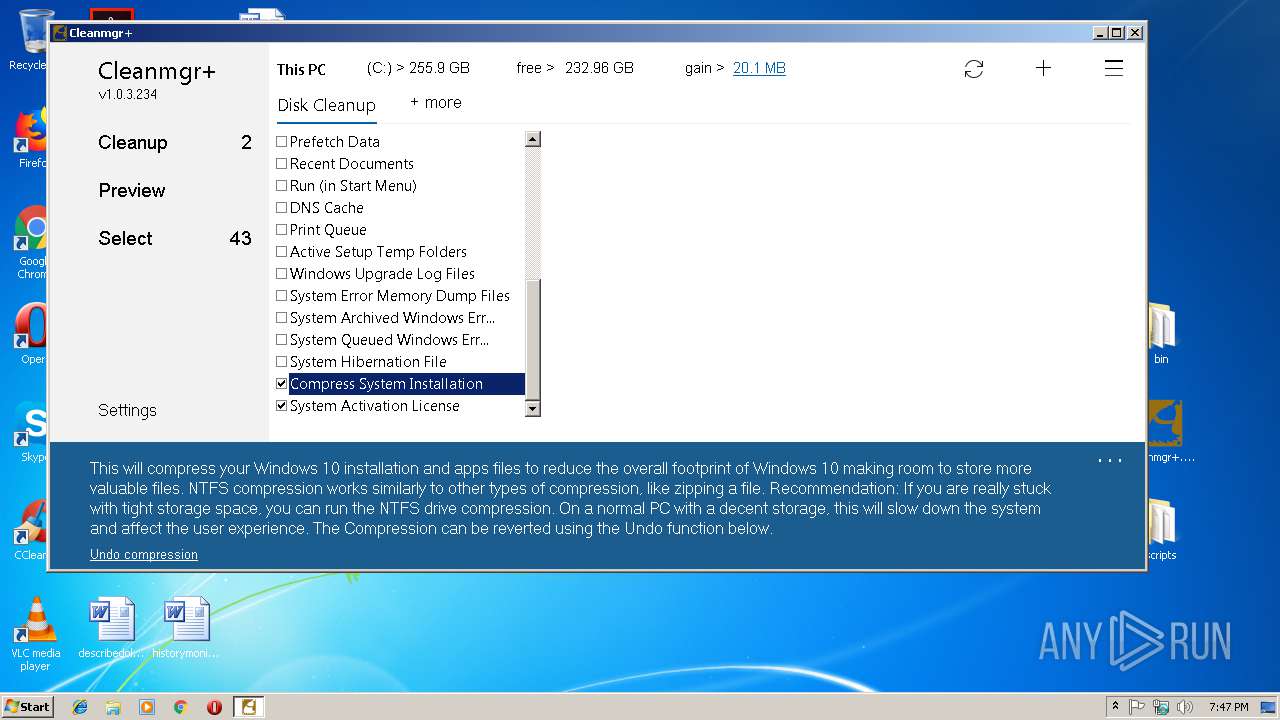
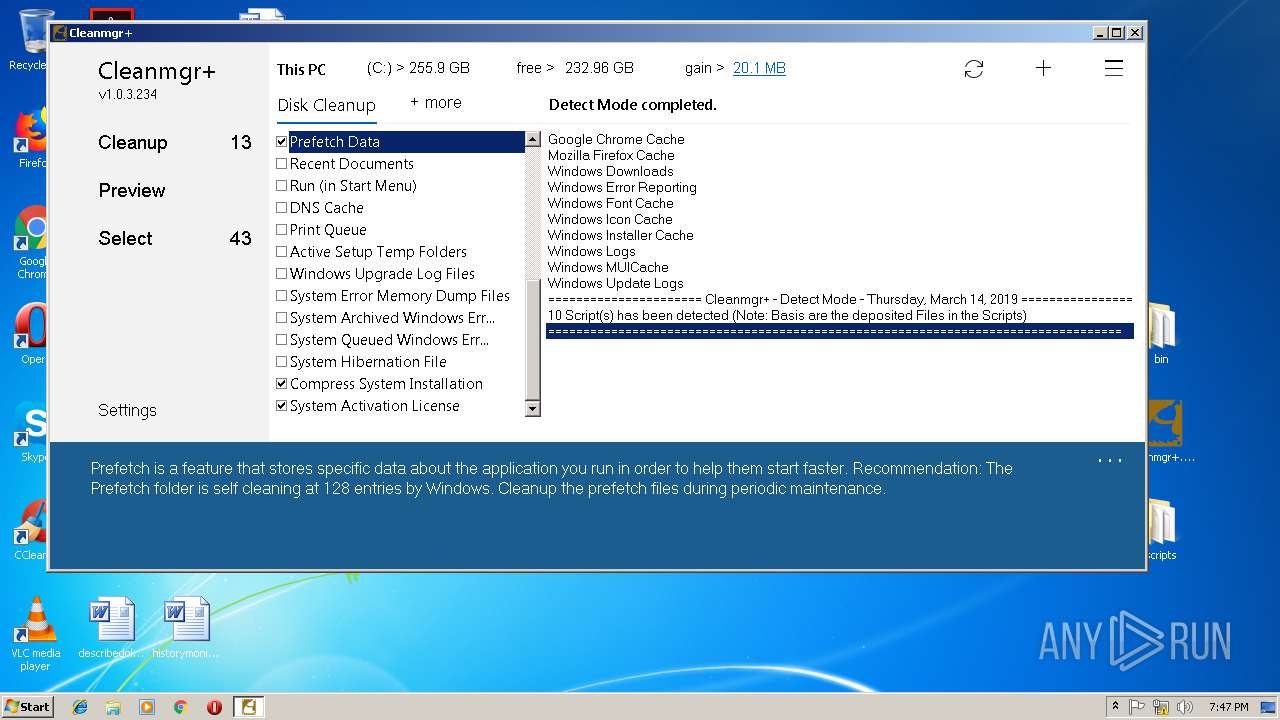
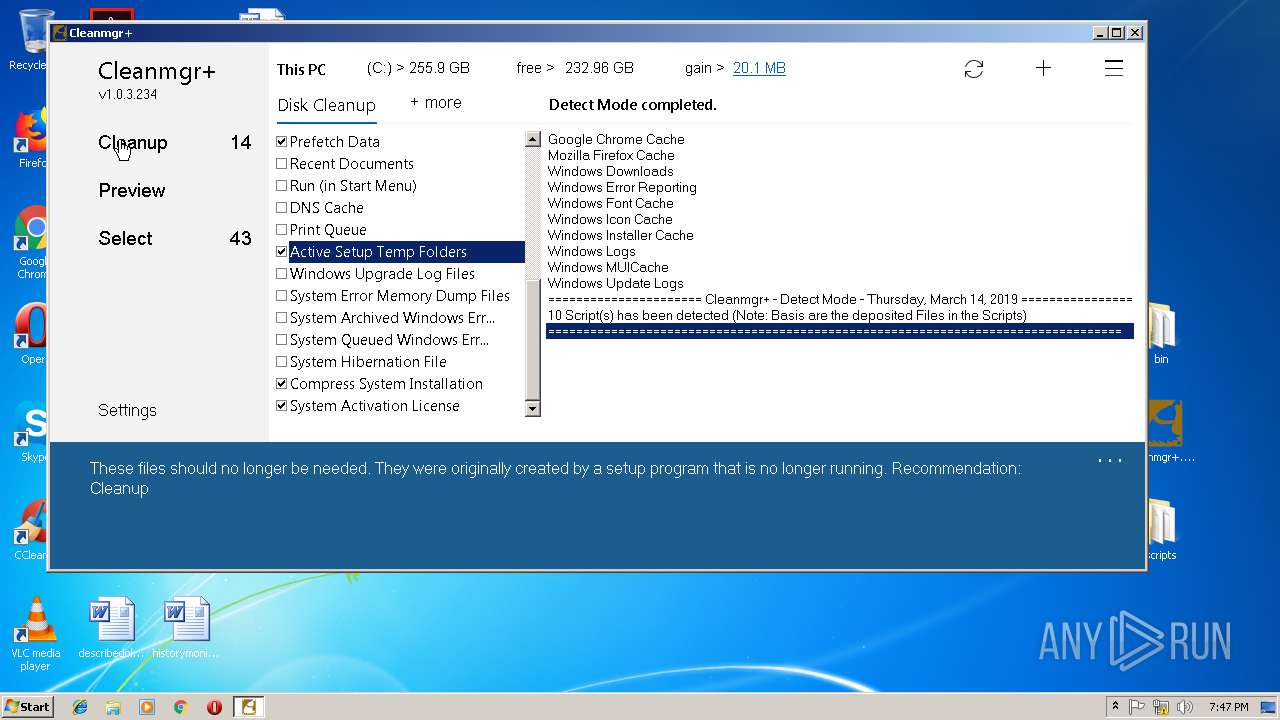
MALICIOUS
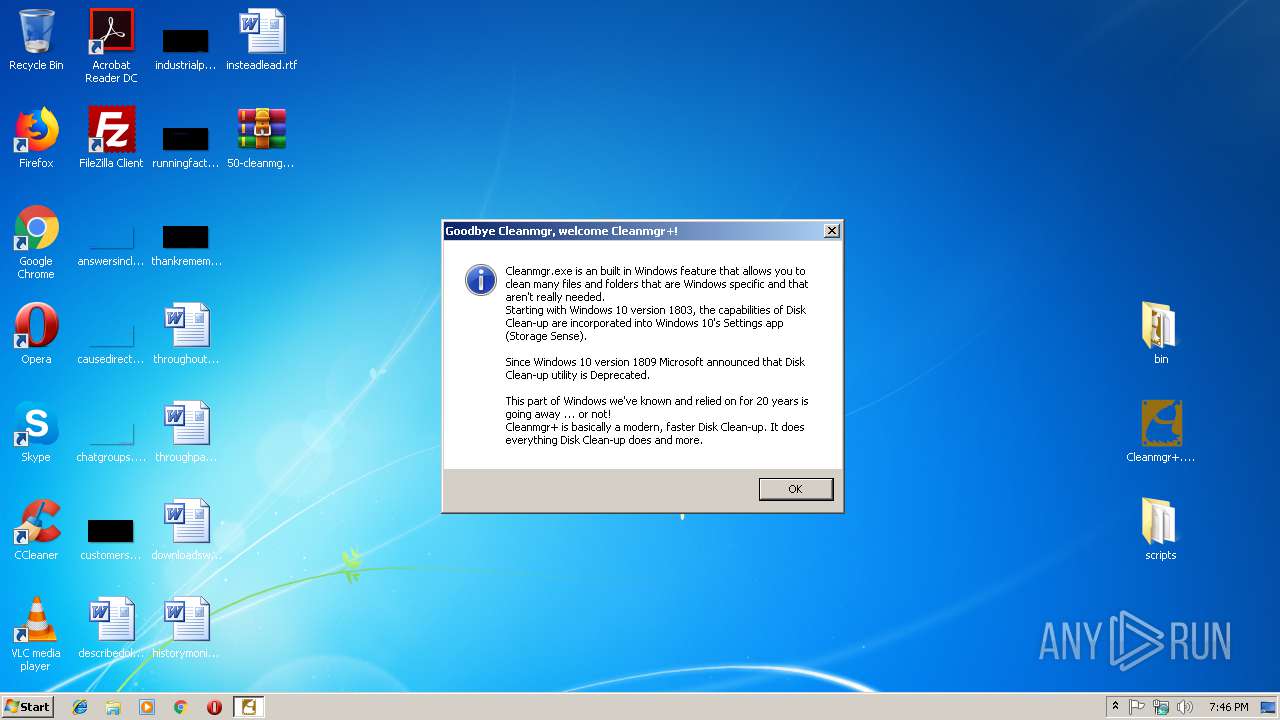
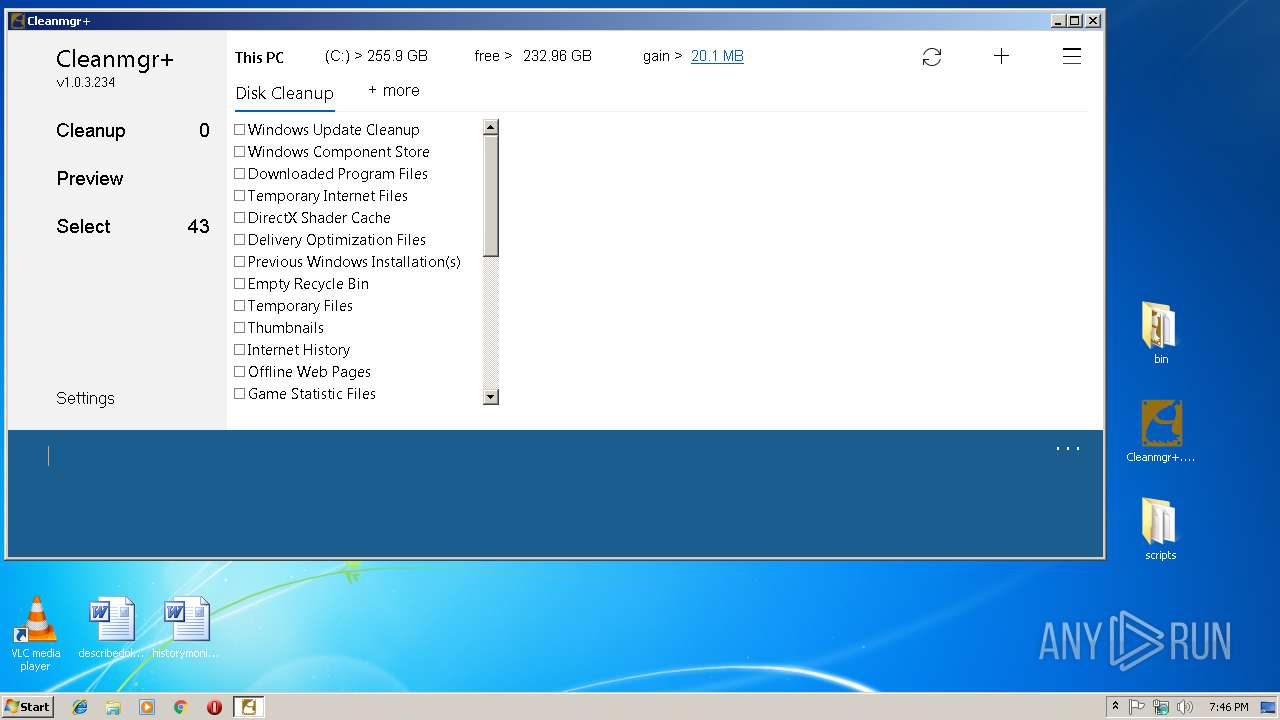
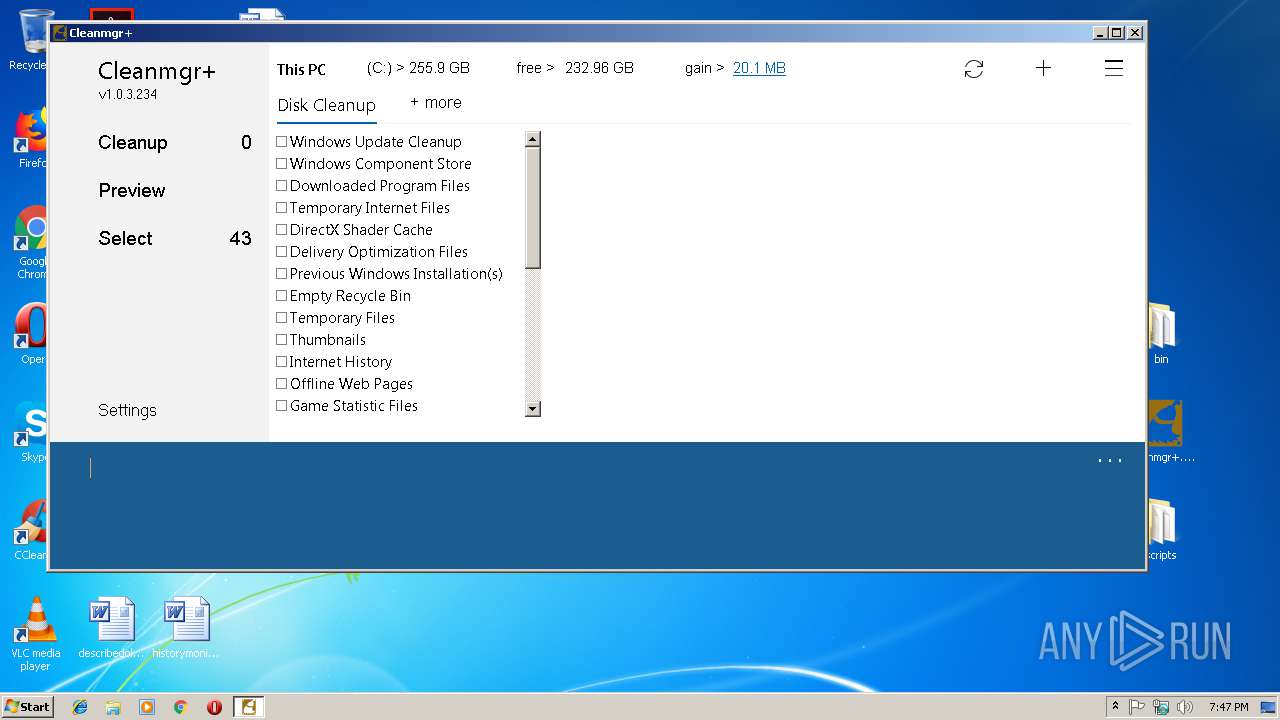
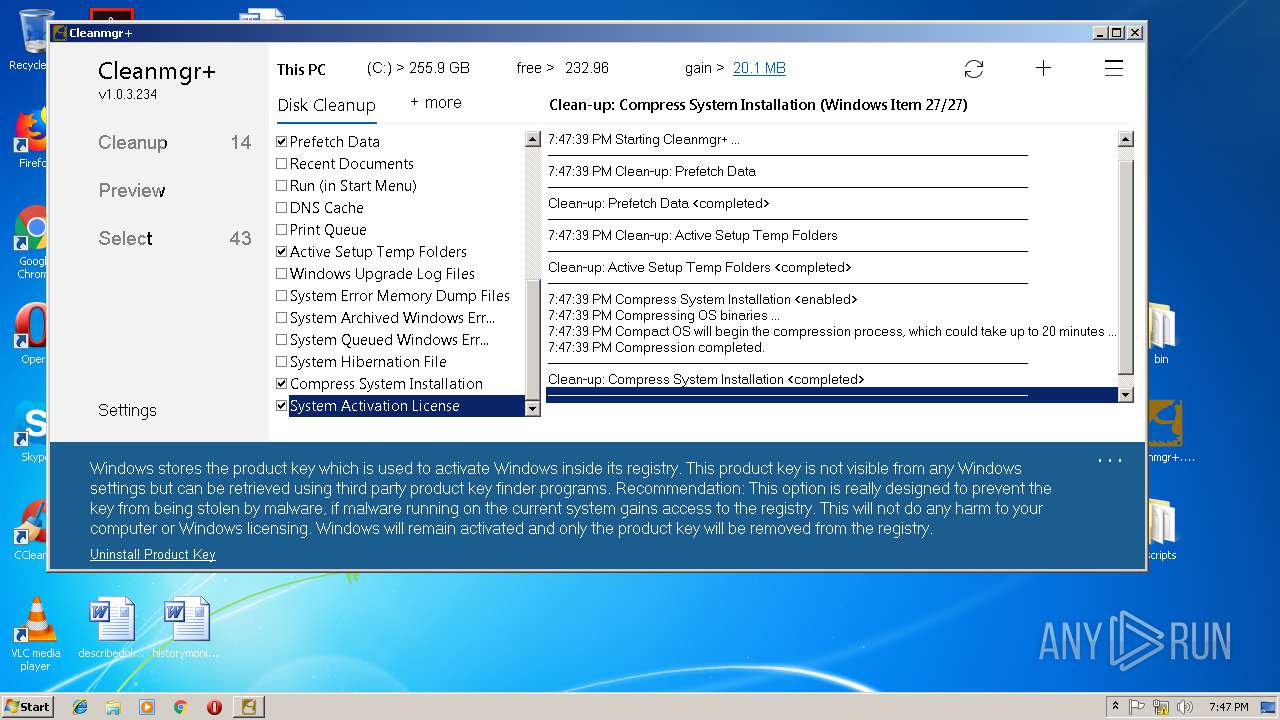
Application was dropped or rewritten from another process
- Cleanmgr+.exe (PID: 3112)
Starts NET.EXE for service management
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 2336)
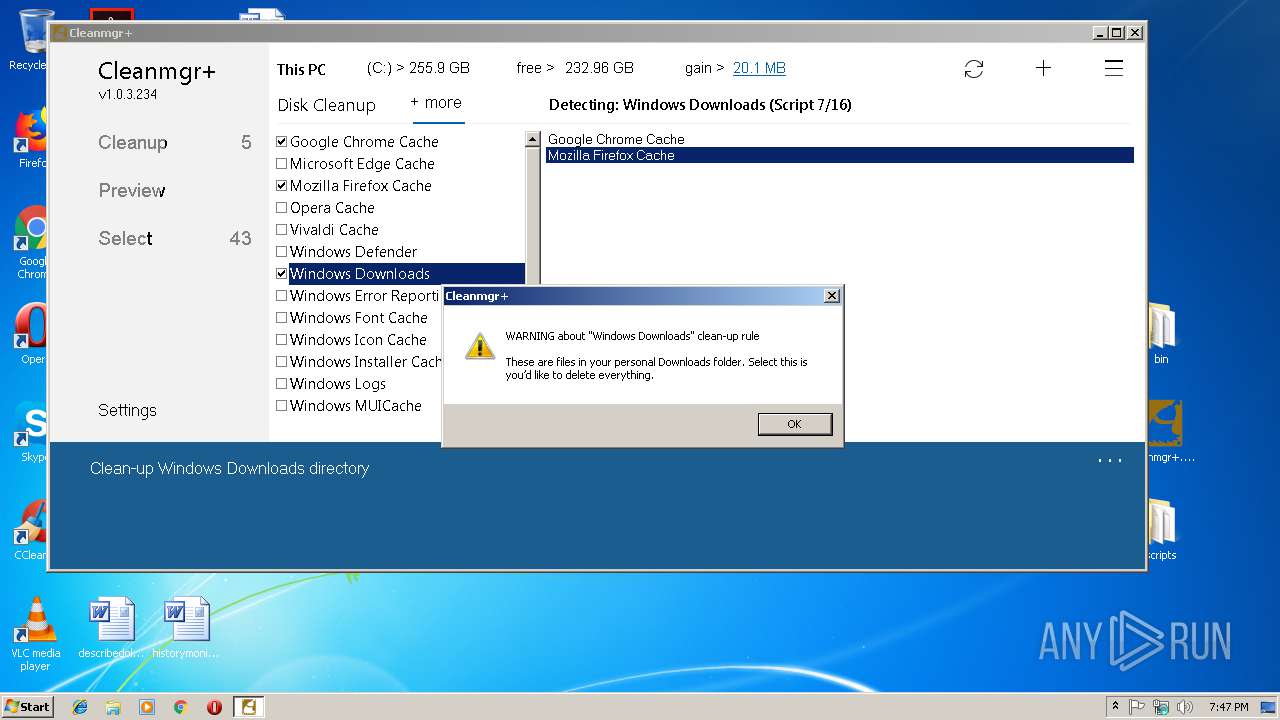
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 2316)
Starts CMD.EXE for commands execution
- Cleanmgr+.exe (PID: 3112)
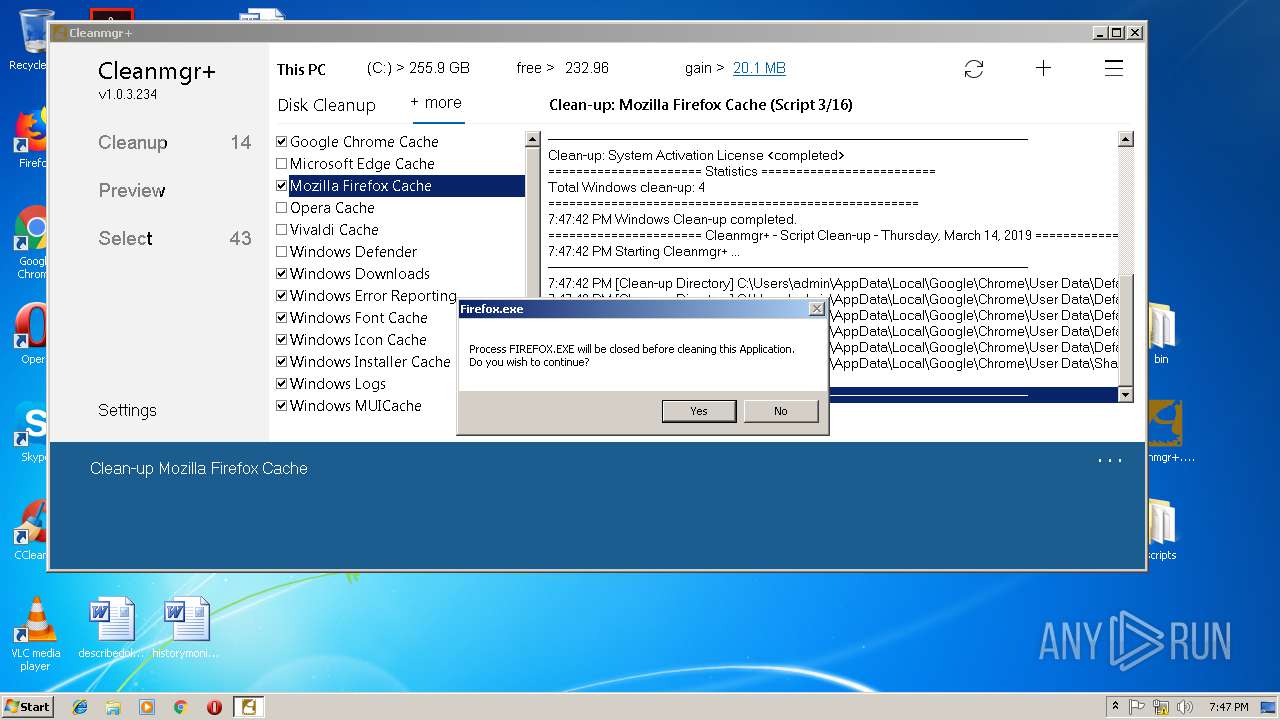
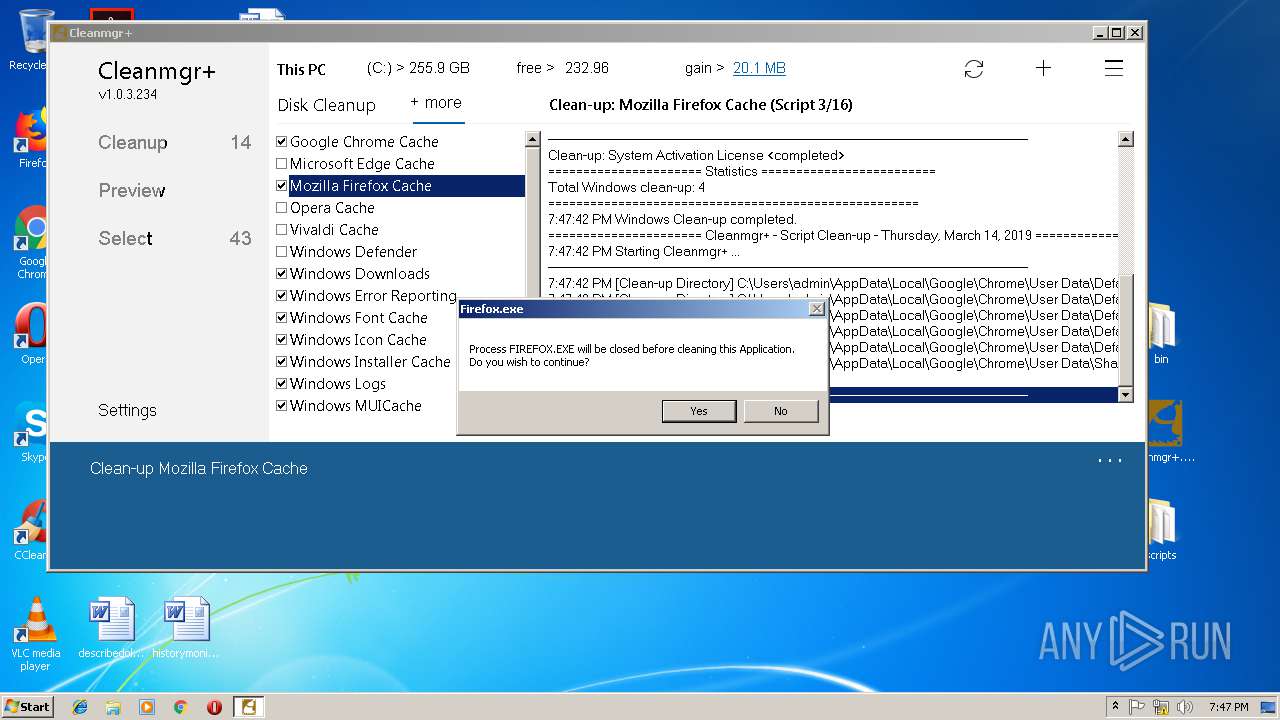
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3180)
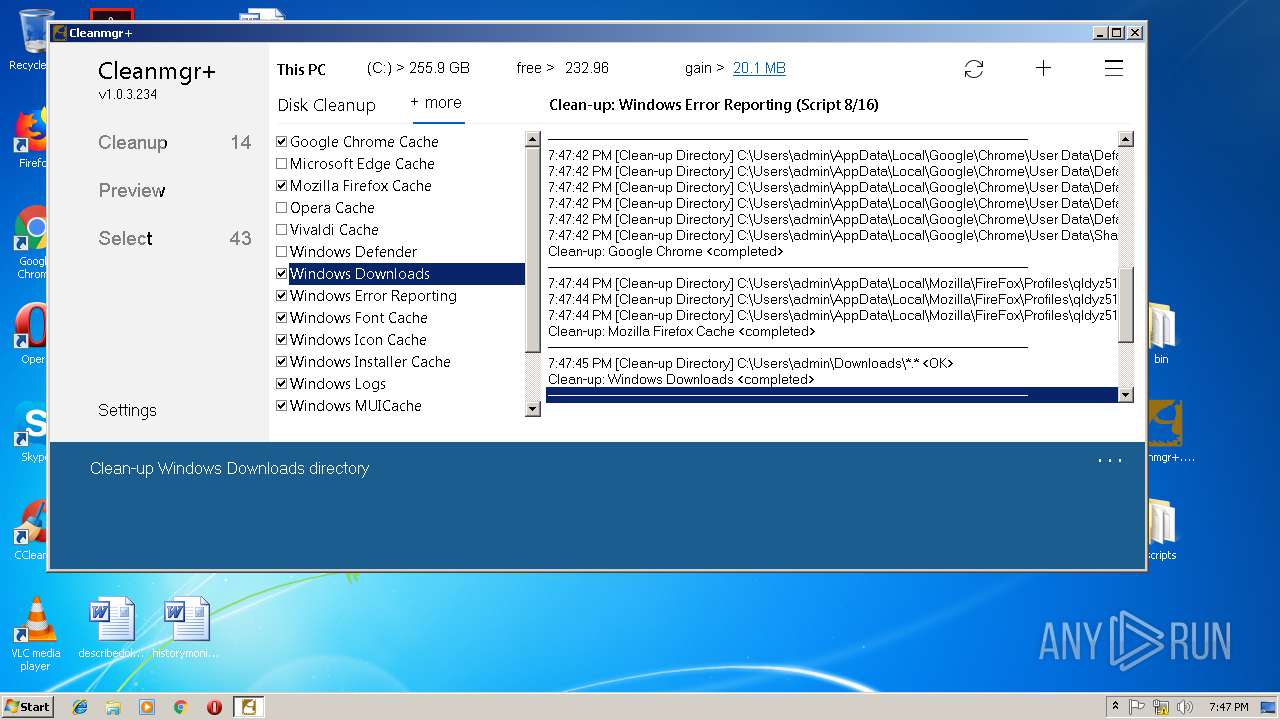
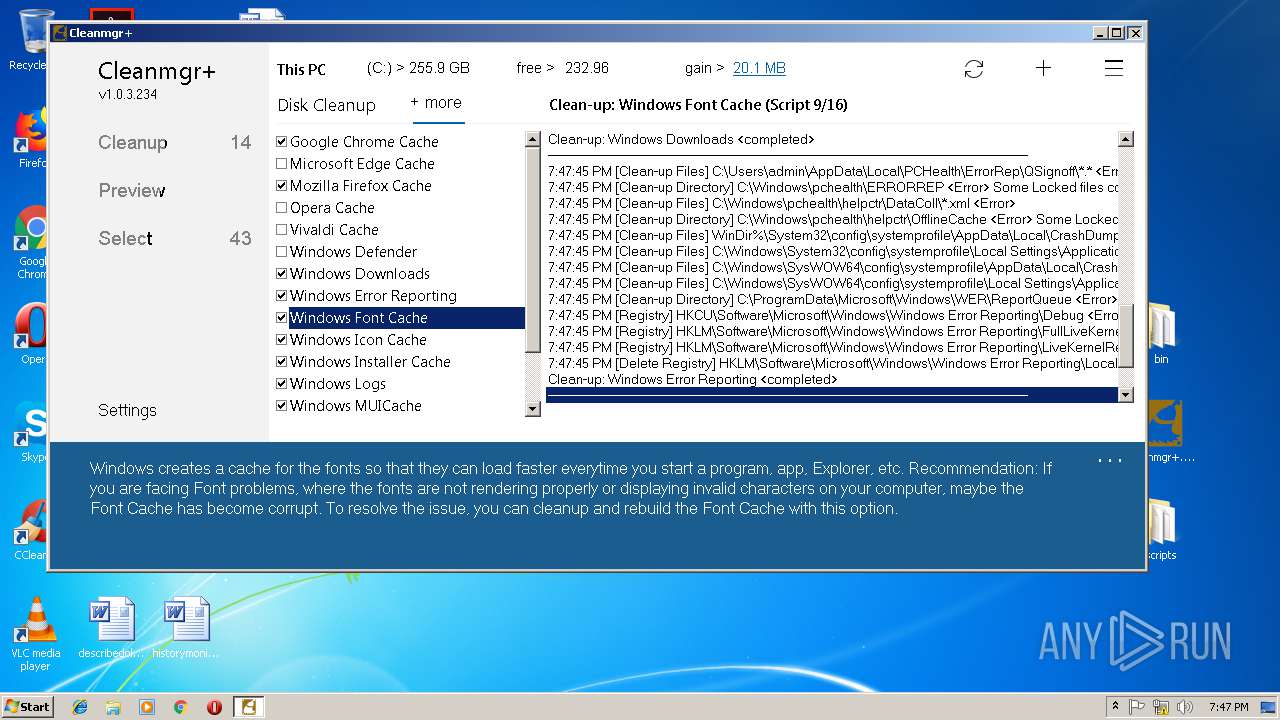
Uses REG.EXE to modify Windows registry
- Cleanmgr+.exe (PID: 3112)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:03:14 18:16:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | bin/ |
Total processes
70
Monitored processes
26
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
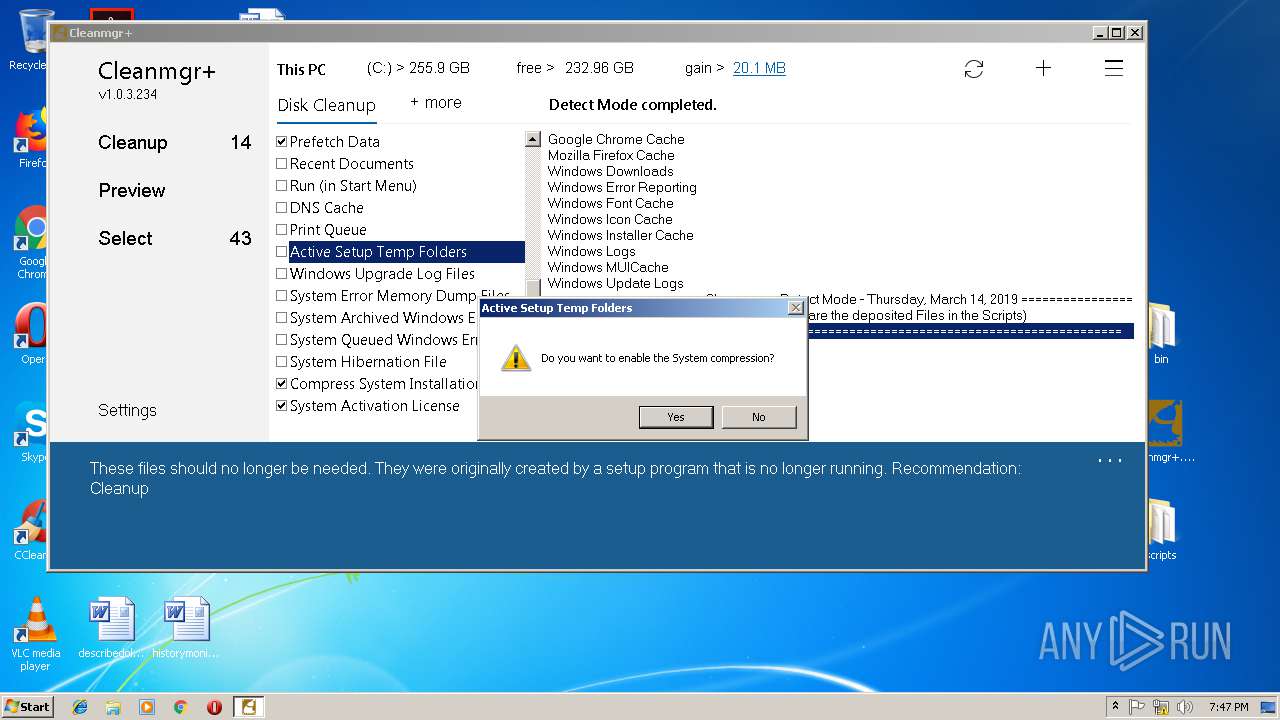
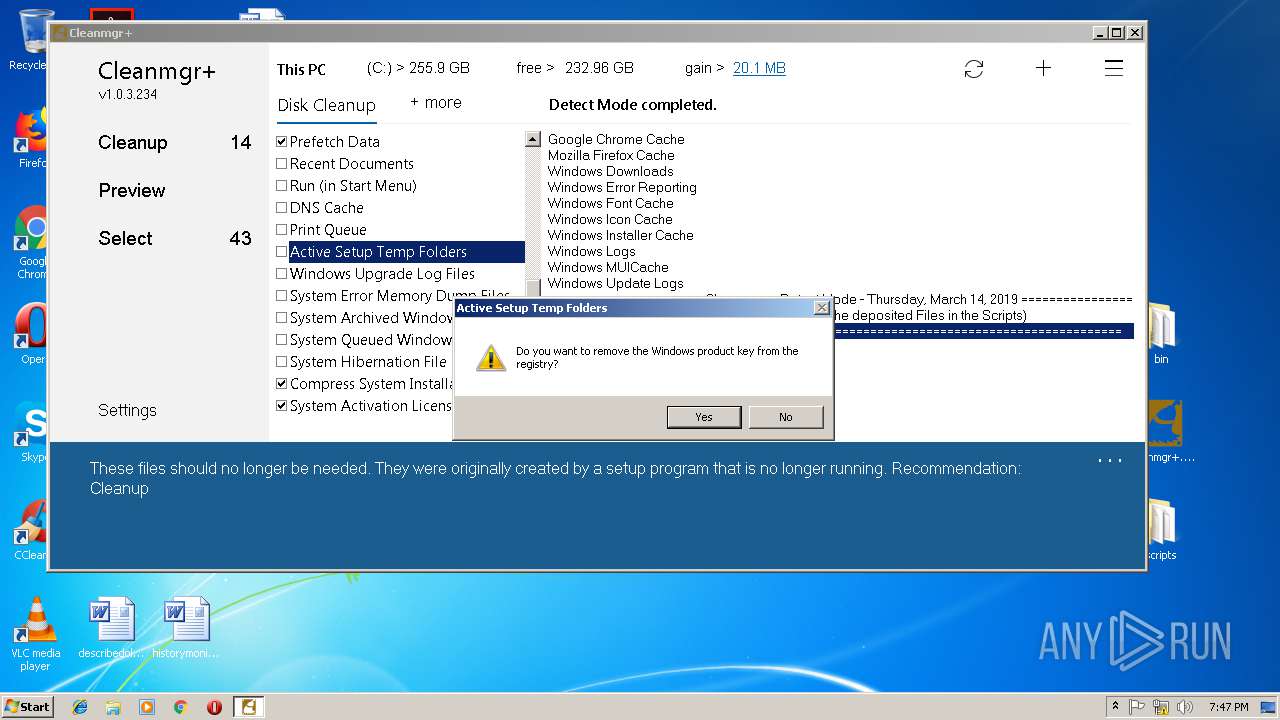
| 2316 | cmd.exe /Cslmgr /cpky | C:\Windows\system32\cmd.exe | — | Cleanmgr+.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2147942405 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
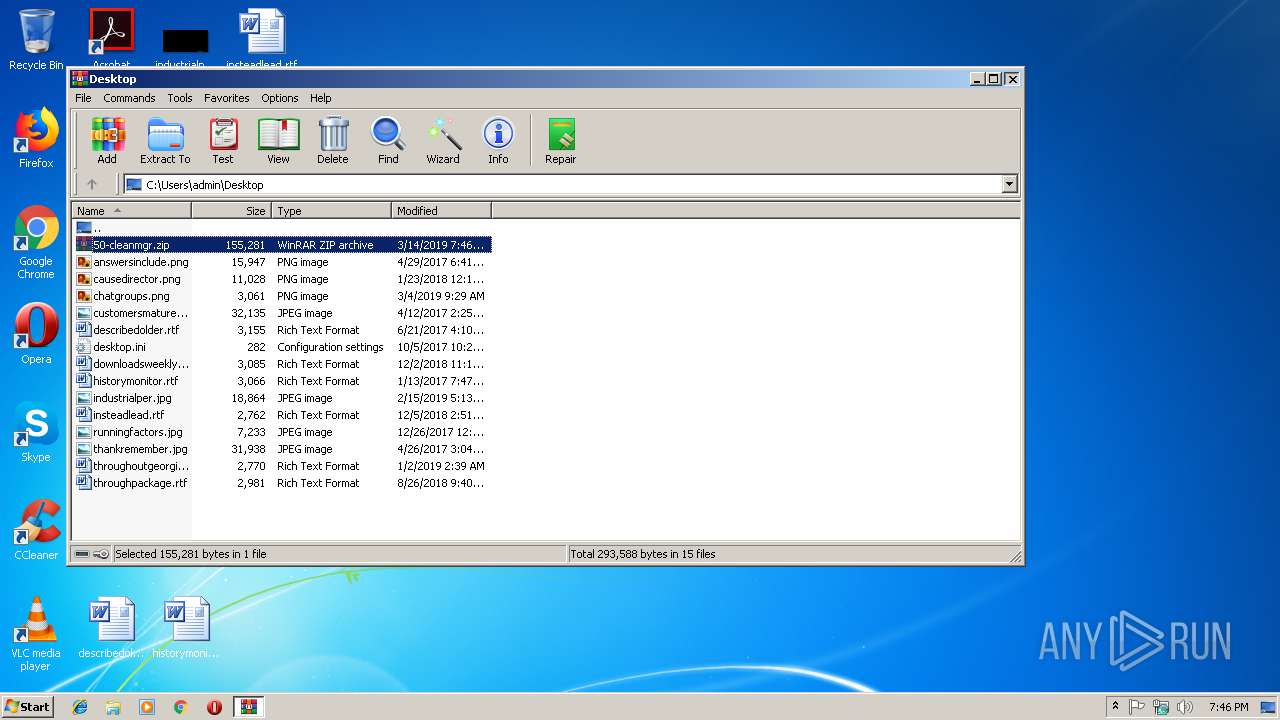
| 2332 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\50-cleanmgr.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2336 | cmd.exe /Cnet stop FontCache3.0.0.0 | C:\Windows\system32\cmd.exe | — | Cleanmgr+.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2348 | taskkill /f /im Firefox.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
| 2500 | C:\Windows\system32\net1 start FontCache | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2524 | net stop FontCache | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | net stop FontCache3.0.0.0 | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2704 | C:\Windows\system32\net1 stop FontCache3.0.0.0 | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\50-cleanmgr.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
873
Read events
823
Write events
50
Delete events
0
Modification events
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\50-cleanmgr.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
0
Text files
21
Unknown types
0
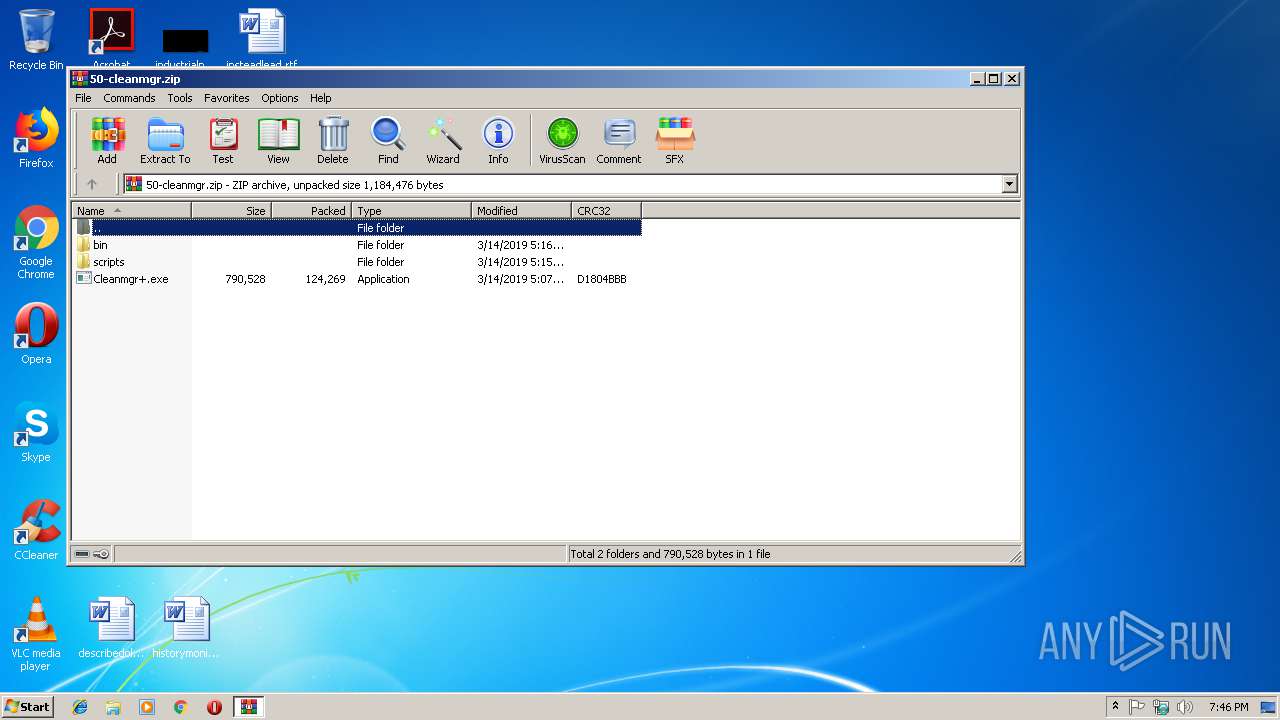
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\bin\cleanmgr+.ico | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\bin\windata.ini | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\Cleanmgr+.exe | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\#Rules.txt | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Google Chrome Cache.csc | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Microsoft Edge Cache.csc | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Mozilla Firefox Cache.csc | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Opera Cache.csc | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Vivaldi Cache.csc | — | |
MD5:— | SHA256:— | |||
| 2332 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2332.31477\scripts\Windows Defender.csc | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report