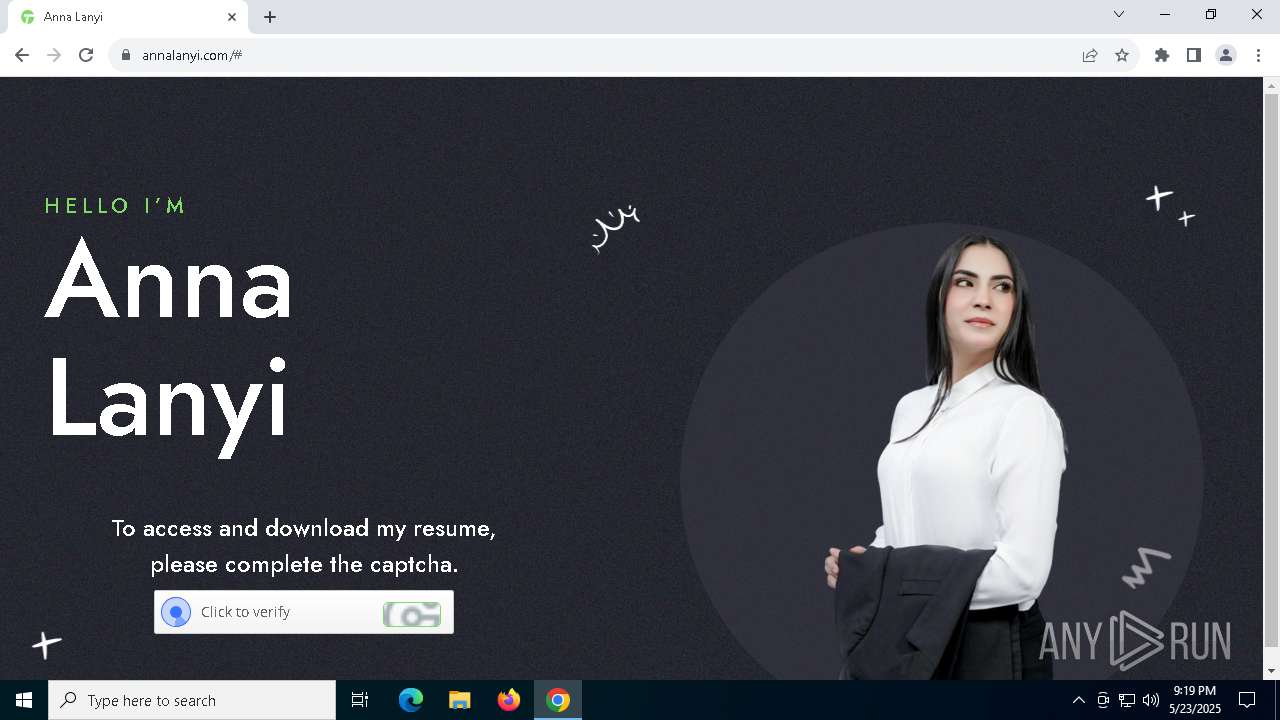
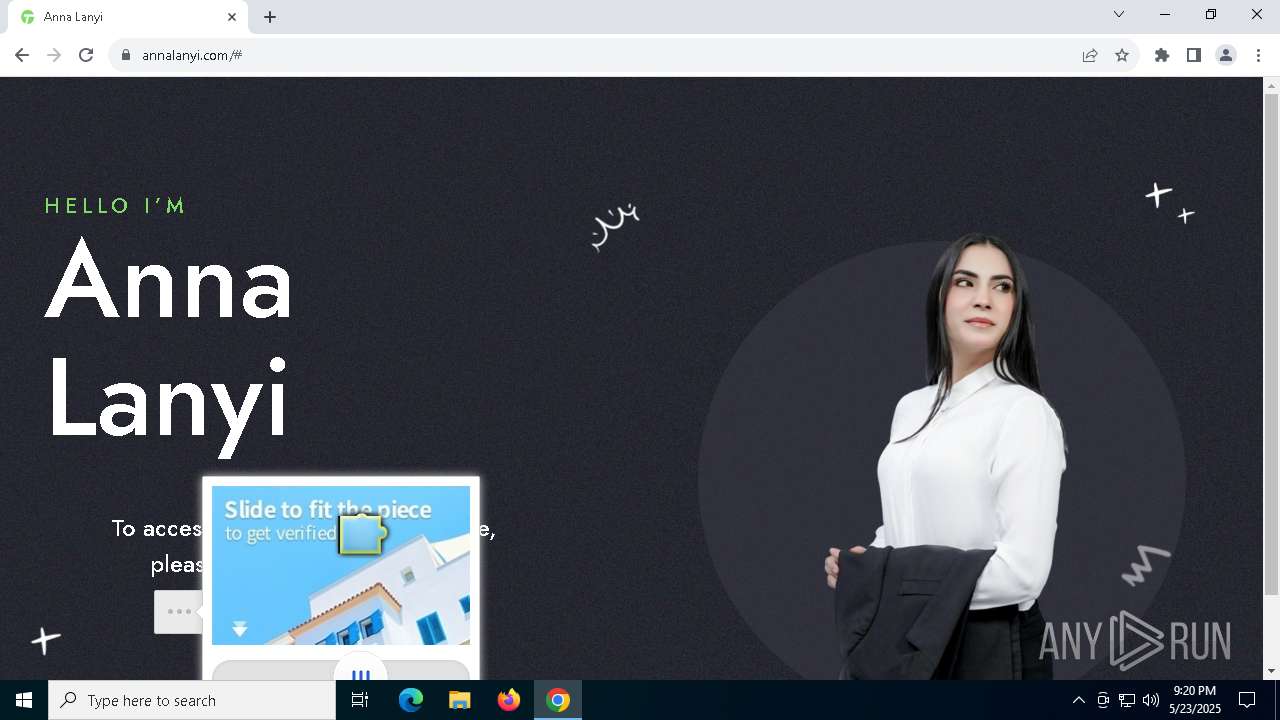
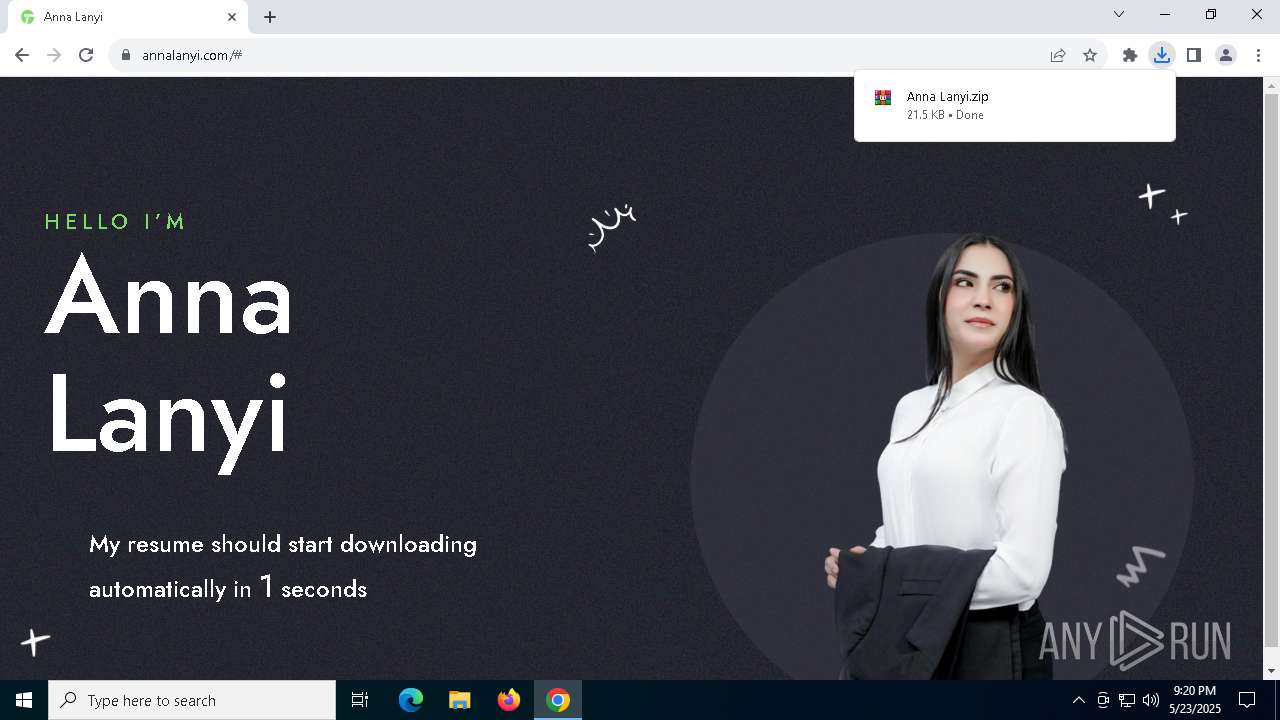
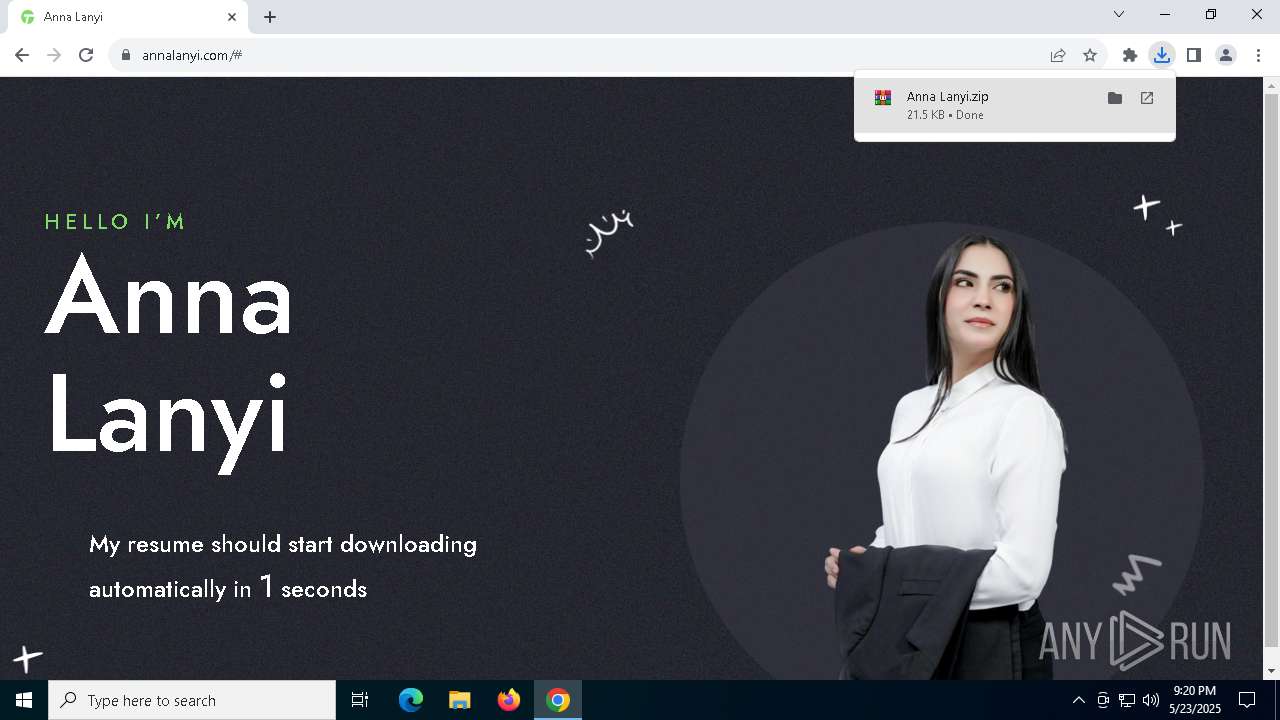
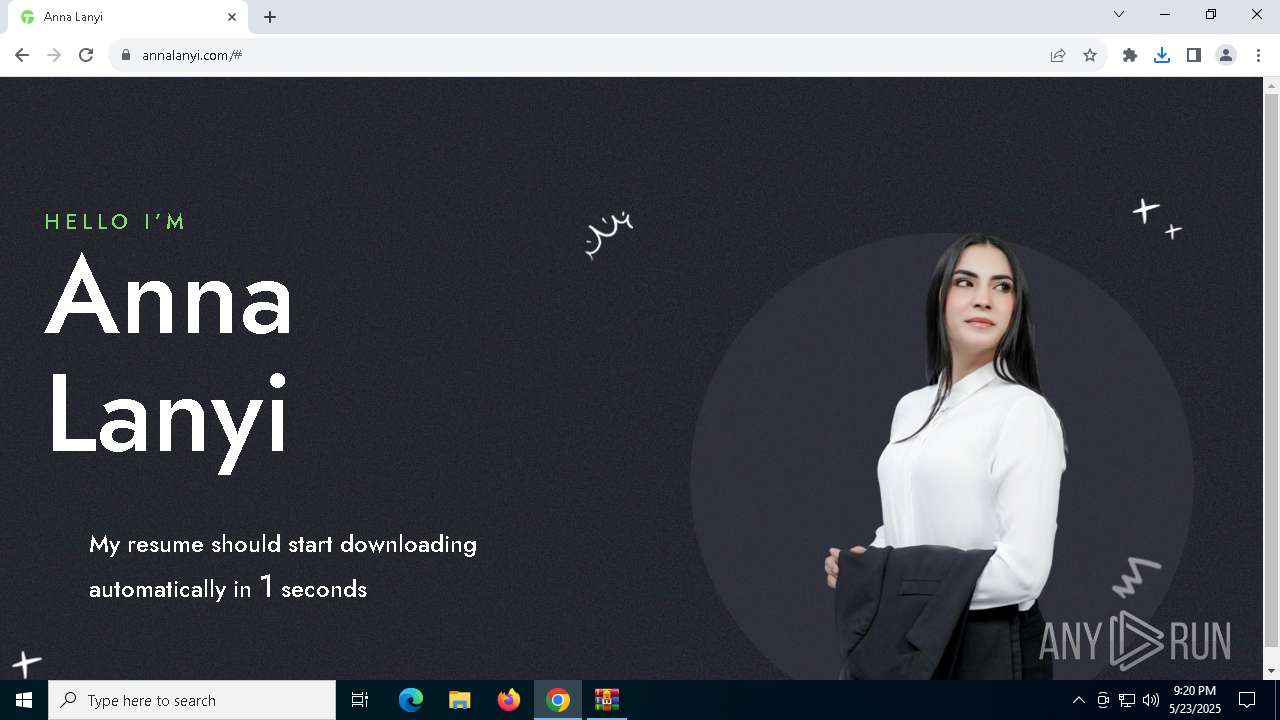
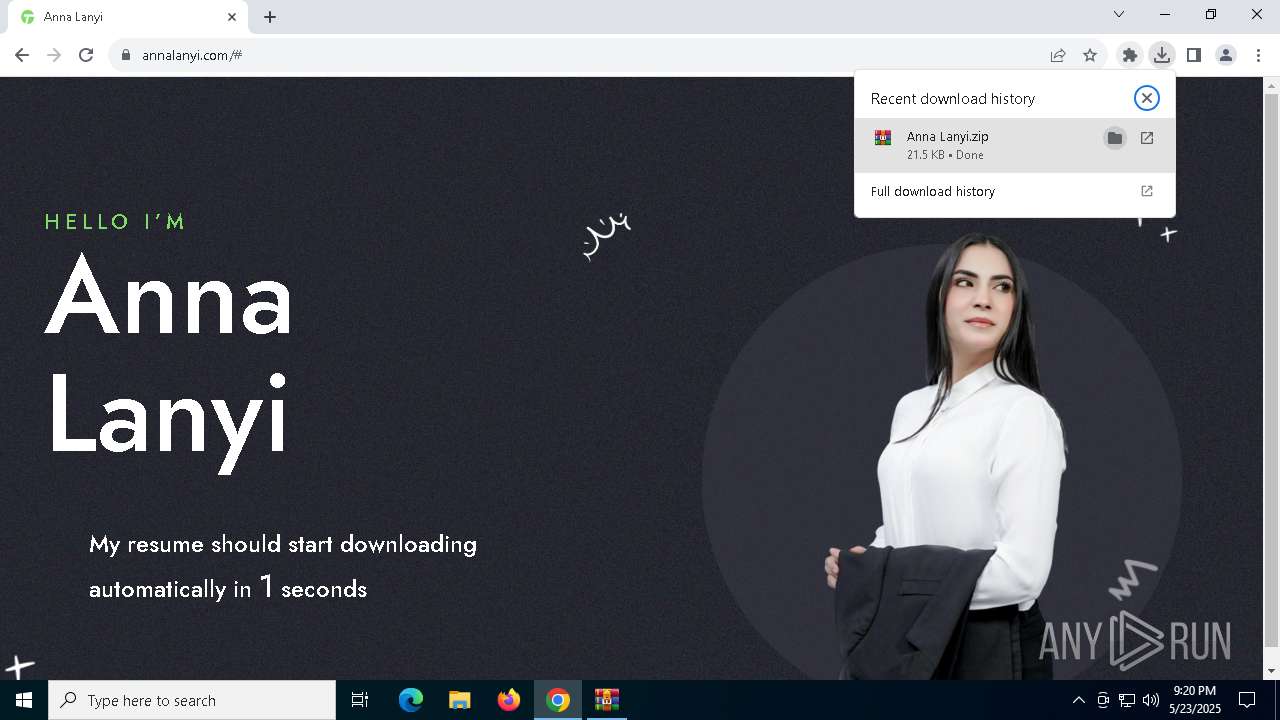
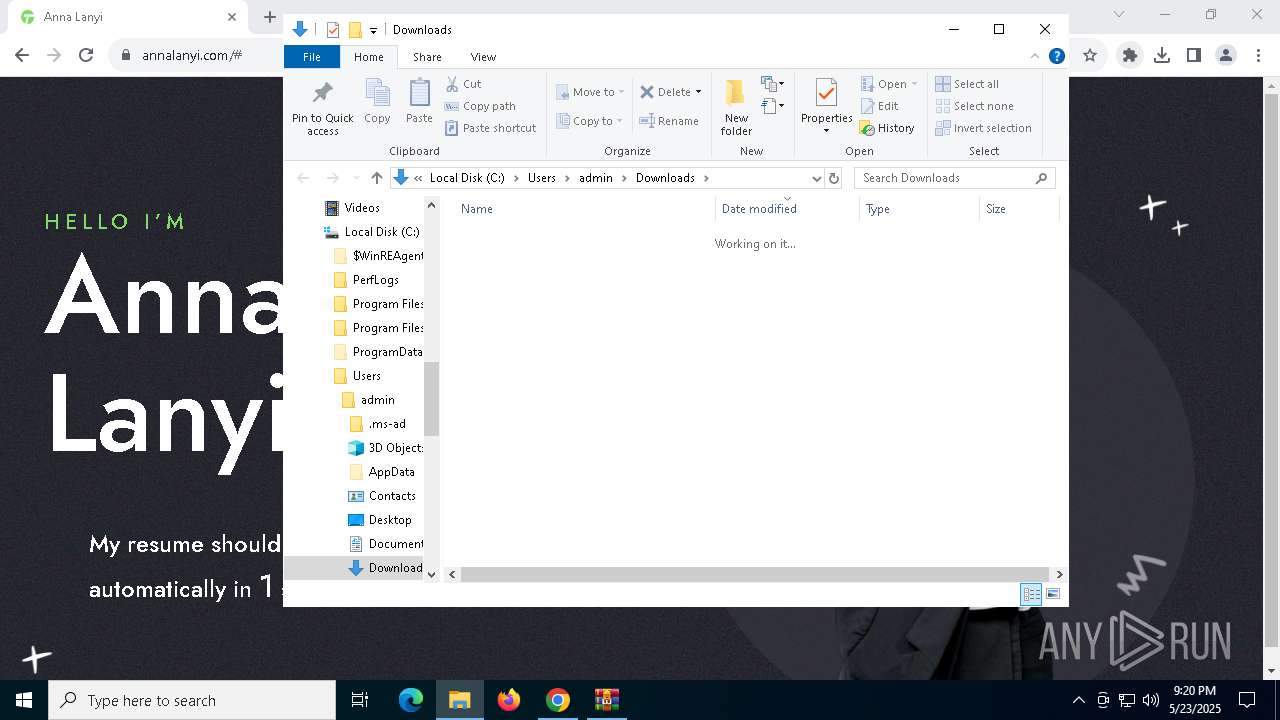
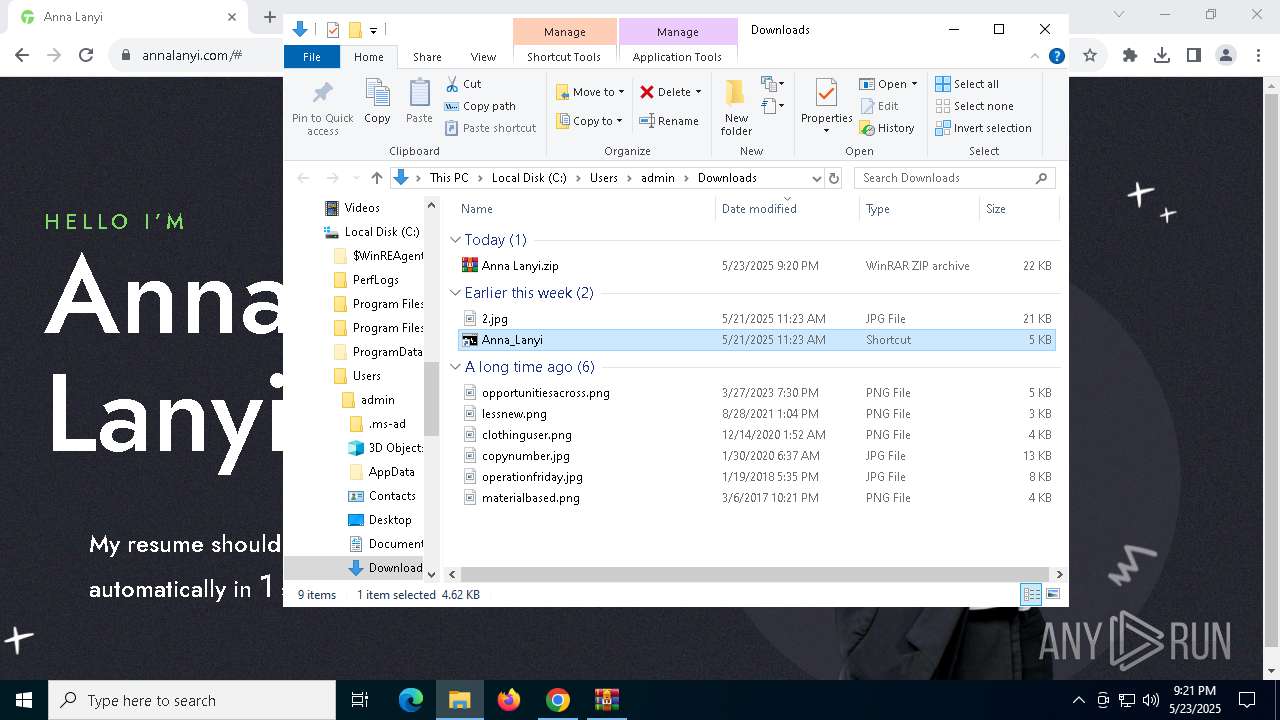
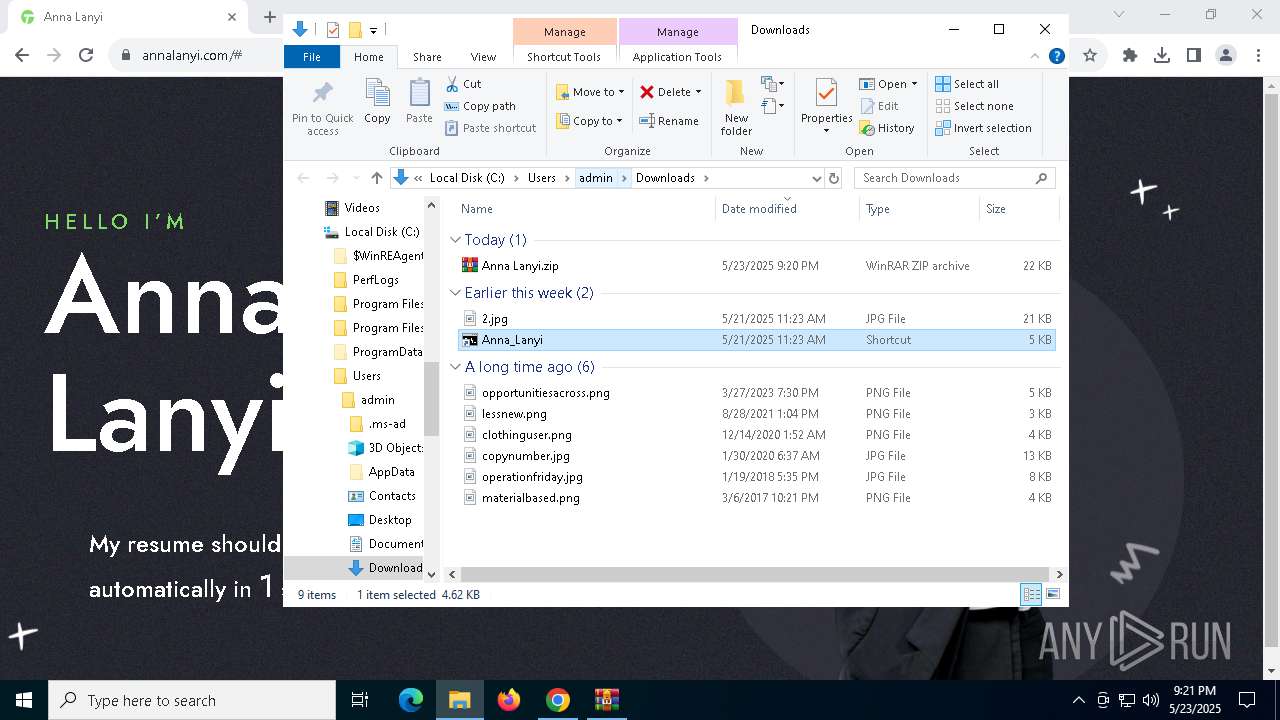
| URL: | https://annalanyi.com |
| Full analysis: | https://app.any.run/tasks/98b4d521-0649-4a17-a8fa-46e606c50a01 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 21:19:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DD018166992F1866CBA64CBA574E7DE5 |
| SHA1: | C6CE617BD43445A9C3DA6141DB48D0EE5761F19D |
| SHA256: | 8DE52992DC636535A278226C6F38D14EDB890F40705CF291EDE74D0EFA444F6C |
| SSDEEP: | 3:N8MpdI:2kdI |
MALICIOUS
Executing a file with an untrusted certificate
- msxsl.exe (PID: 7704)
- msxsl.exe (PID: 6480)
- msxsl.exe (PID: 5236)
- msxsl.exe (PID: 7968)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 2908)
- msxsl.exe (PID: 3868)
- msxsl.exe (PID: 4068)
- msxsl.exe (PID: 6028)
- msxsl.exe (PID: 6988)
- msxsl.exe (PID: 5228)
- msxsl.exe (PID: 8100)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 7608)
- msxsl.exe (PID: 6852)
- msxsl.exe (PID: 5640)
- msxsl.exe (PID: 4164)
- msxsl.exe (PID: 4244)
- msxsl.exe (PID: 7904)
- msxsl.exe (PID: 208)
- msxsl.exe (PID: 896)
- msxsl.exe (PID: 300)
- msxsl.exe (PID: 5304)
- msxsl.exe (PID: 3888)
- msxsl.exe (PID: 5344)
- msxsl.exe (PID: 3208)
- msxsl.exe (PID: 8180)
SUSPICIOUS
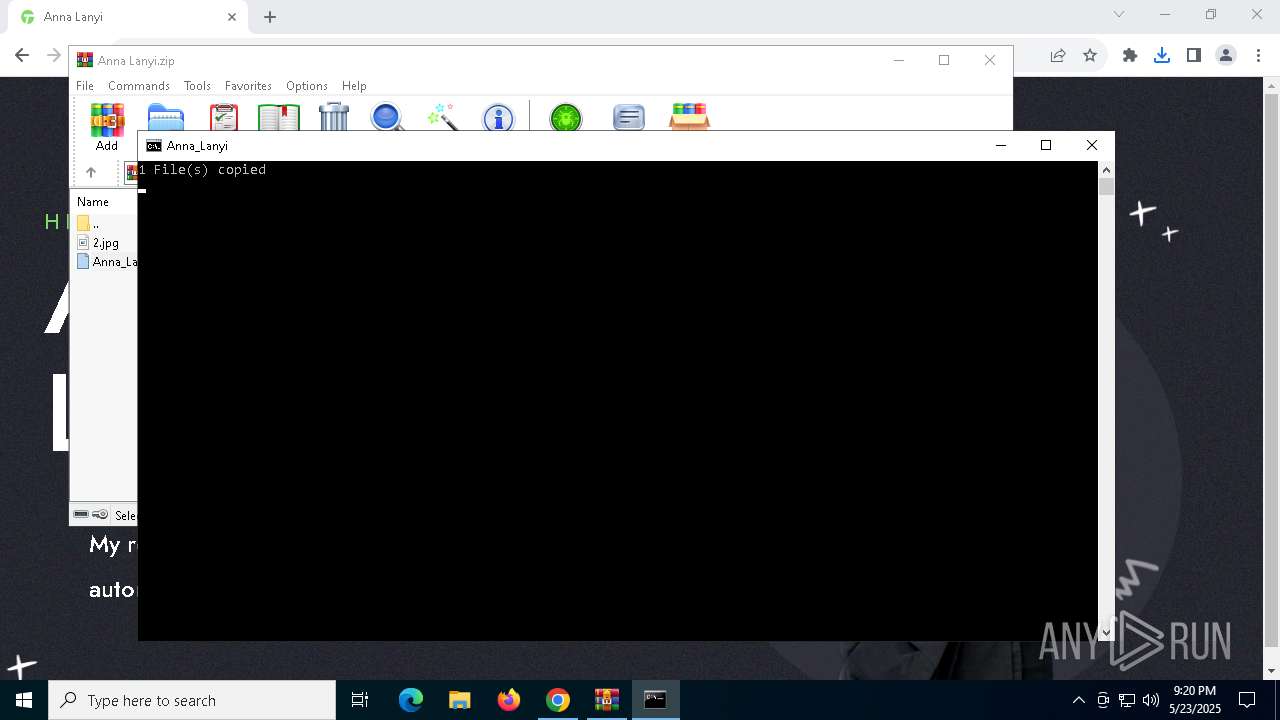
Executable content was dropped or overwritten
- xcopy.exe (PID: 8148)
- ie4uinit.exe (PID: 5236)
- ie4uinit.exe (PID: 5608)
- regsvr32.exe (PID: 4404)
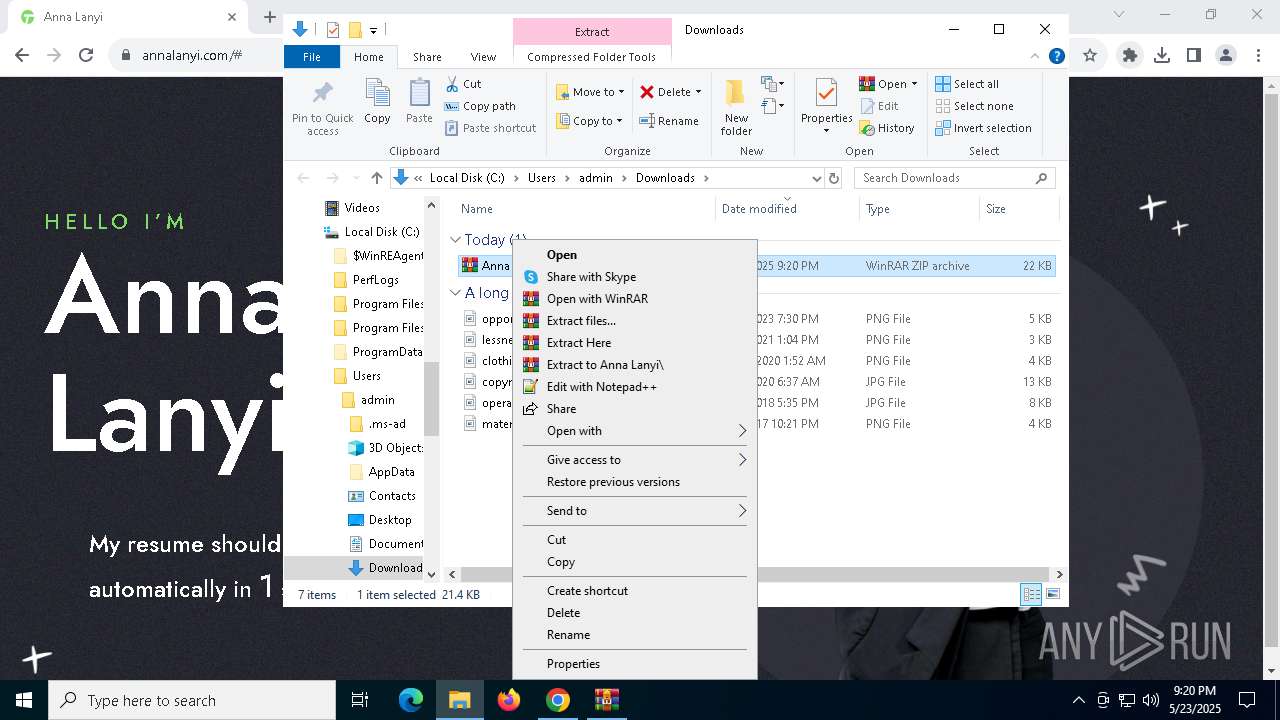
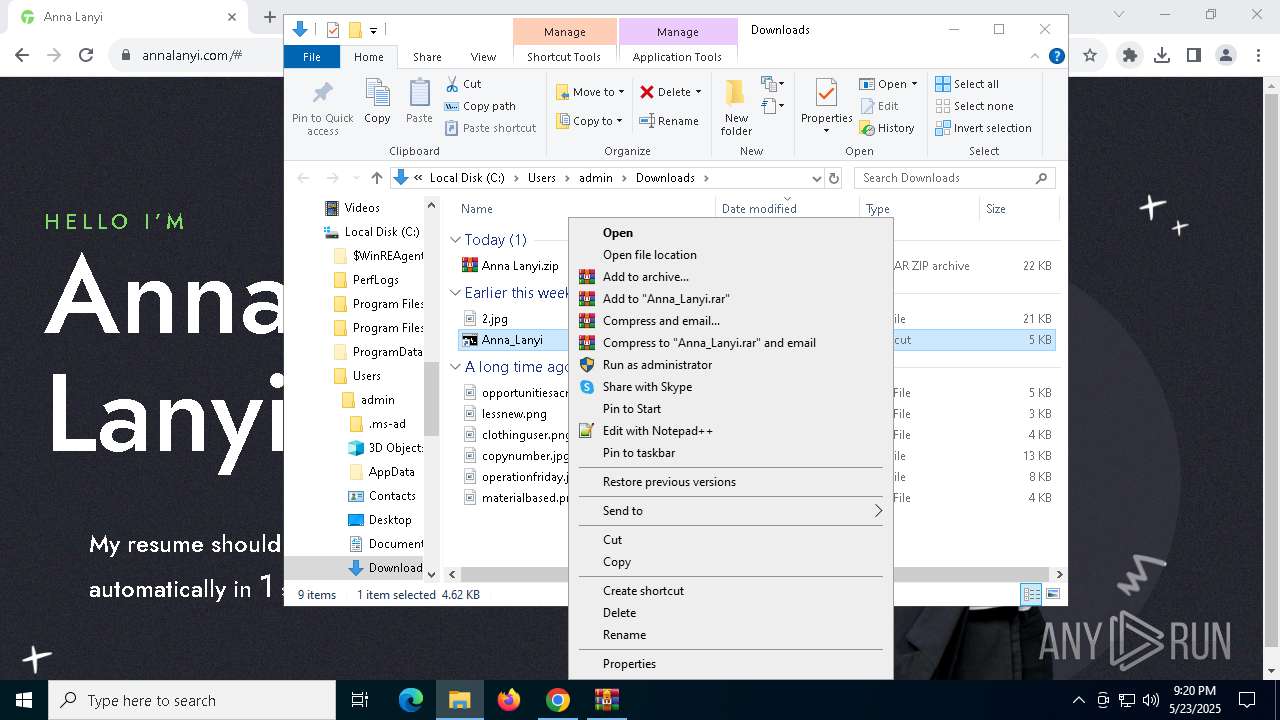
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 6300)
- regsvr32.exe (PID: 4016)
Process copies executable file
- cmd.exe (PID: 8132)
- cmd.exe (PID: 6940)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6300)
- ie4uinit.exe (PID: 5236)
- ie4uinit.exe (PID: 8176)
The executable file from the user directory is run by the CMD process
- ie4uinit.exe (PID: 5236)
Application launched itself
- ie4uinit.exe (PID: 5236)
- ie4uinit.exe (PID: 5608)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 8176)
- ie4uinit.exe (PID: 7888)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- ie4uinit.exe (PID: 5236)
Changes charset (SCRIPT)
- ie4uinit.exe (PID: 5236)
Saves data to a binary file (SCRIPT)
- ie4uinit.exe (PID: 5236)
Writes binary data to a Stream object (SCRIPT)
- ie4uinit.exe (PID: 5236)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- ie4uinit.exe (PID: 5236)
Executed via WMI
- regsvr32.exe (PID: 4192)
- regsvr32.exe (PID: 5508)
- msxsl.exe (PID: 7704)
- msxsl.exe (PID: 5236)
- msxsl.exe (PID: 7968)
- msxsl.exe (PID: 6480)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 2908)
- msxsl.exe (PID: 3868)
- msxsl.exe (PID: 6028)
- msxsl.exe (PID: 6988)
- msxsl.exe (PID: 5228)
- msxsl.exe (PID: 8100)
- msxsl.exe (PID: 4068)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 7608)
- msxsl.exe (PID: 4244)
- msxsl.exe (PID: 4164)
- msxsl.exe (PID: 6852)
- msxsl.exe (PID: 5640)
- msxsl.exe (PID: 7904)
- msxsl.exe (PID: 208)
- msxsl.exe (PID: 896)
- msxsl.exe (PID: 300)
- msxsl.exe (PID: 3888)
- msxsl.exe (PID: 3208)
- msxsl.exe (PID: 5304)
- msxsl.exe (PID: 5344)
- msxsl.exe (PID: 8180)
Creates an object to access WMI (SCRIPT)
- ie4uinit.exe (PID: 5236)
Executes application which crashes
- msxsl.exe (PID: 7704)
- msxsl.exe (PID: 5236)
- msxsl.exe (PID: 7968)
- msxsl.exe (PID: 6480)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 2908)
- msxsl.exe (PID: 4068)
- msxsl.exe (PID: 6028)
- msxsl.exe (PID: 6988)
- msxsl.exe (PID: 5228)
- msxsl.exe (PID: 3868)
- msxsl.exe (PID: 8100)
- msxsl.exe (PID: 5124)
- msxsl.exe (PID: 7608)
- msxsl.exe (PID: 5640)
- msxsl.exe (PID: 7904)
- msxsl.exe (PID: 208)
- msxsl.exe (PID: 896)
- msxsl.exe (PID: 5344)
- msxsl.exe (PID: 300)
- msxsl.exe (PID: 5304)
- msxsl.exe (PID: 3888)
- msxsl.exe (PID: 3208)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6300)
- chrome.exe (PID: 4756)
Application launched itself
- chrome.exe (PID: 4756)
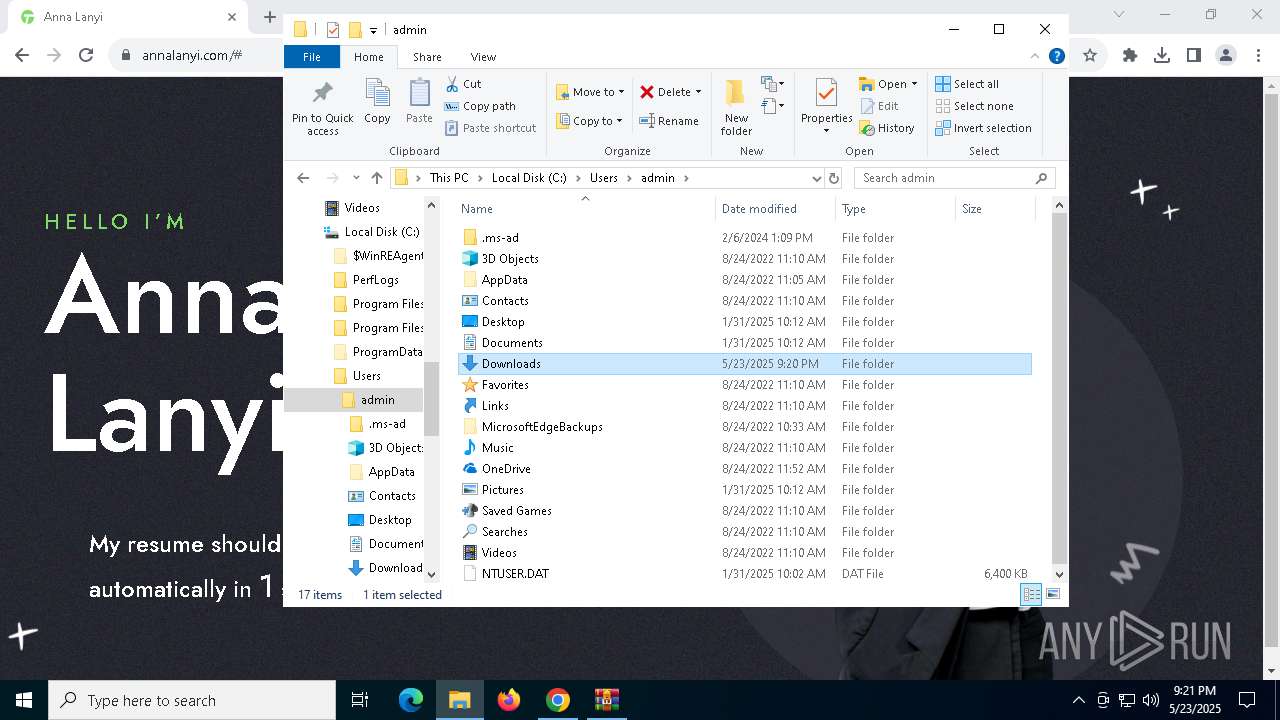
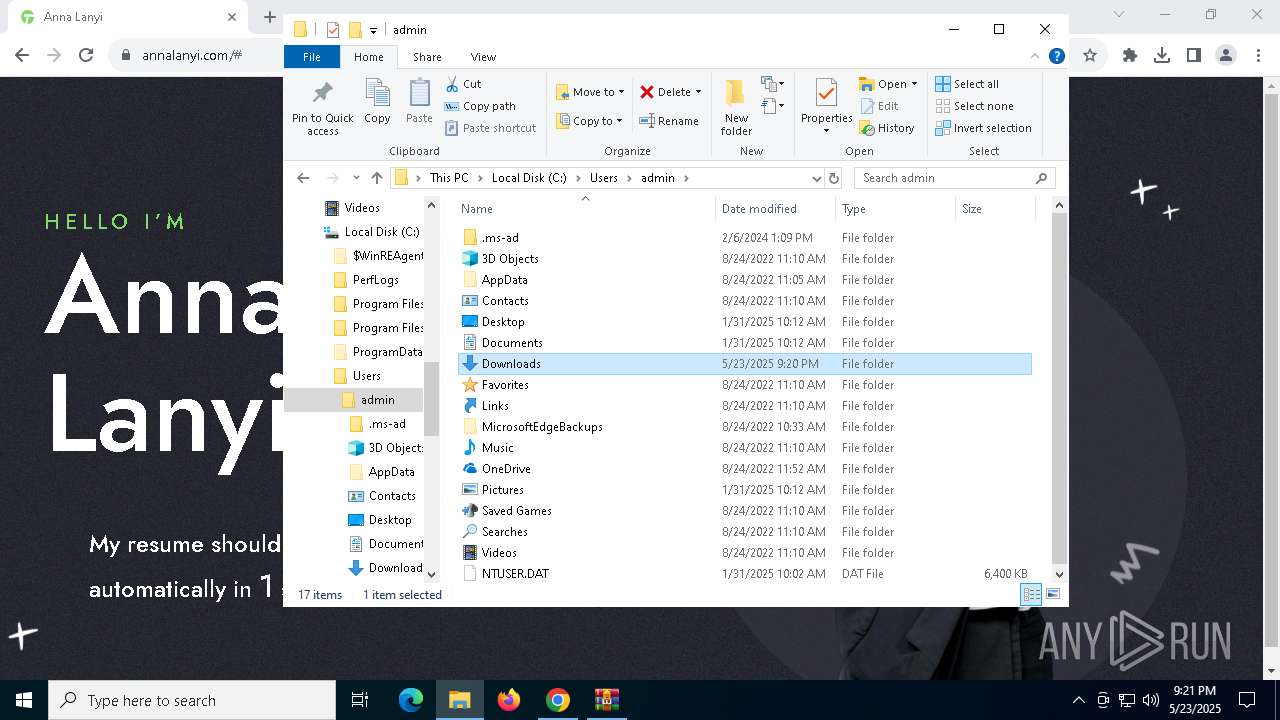
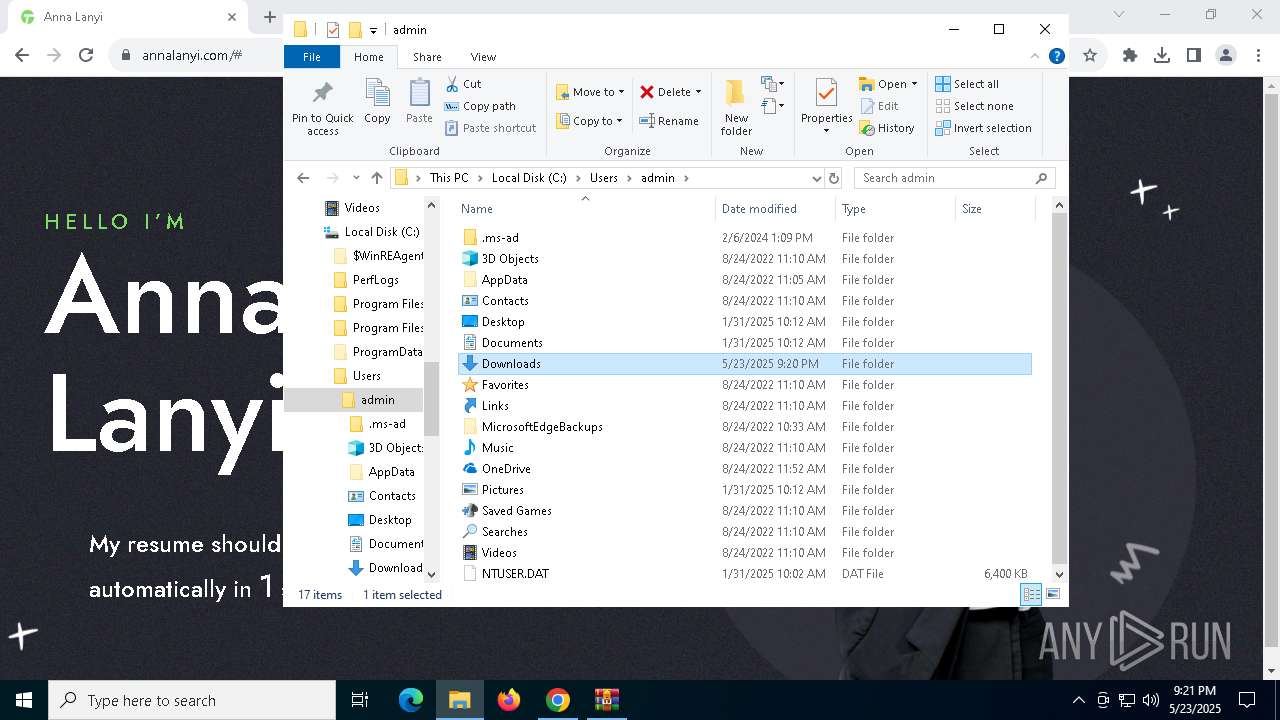
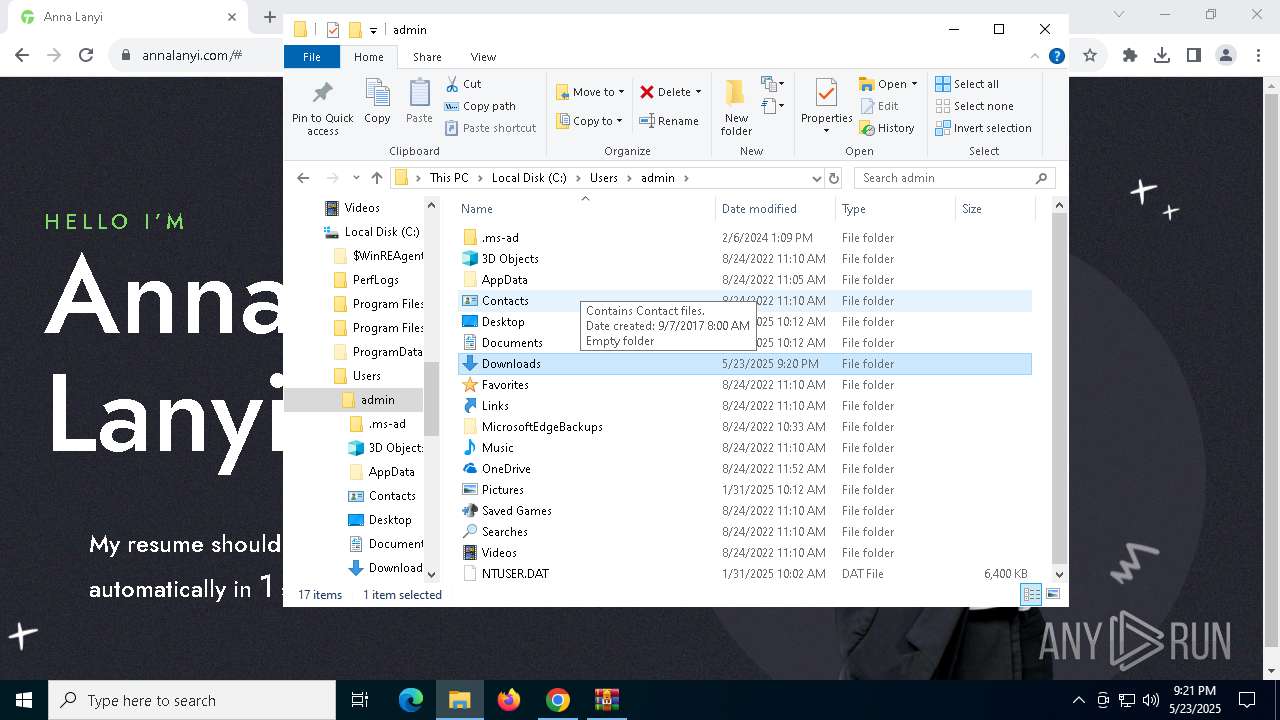
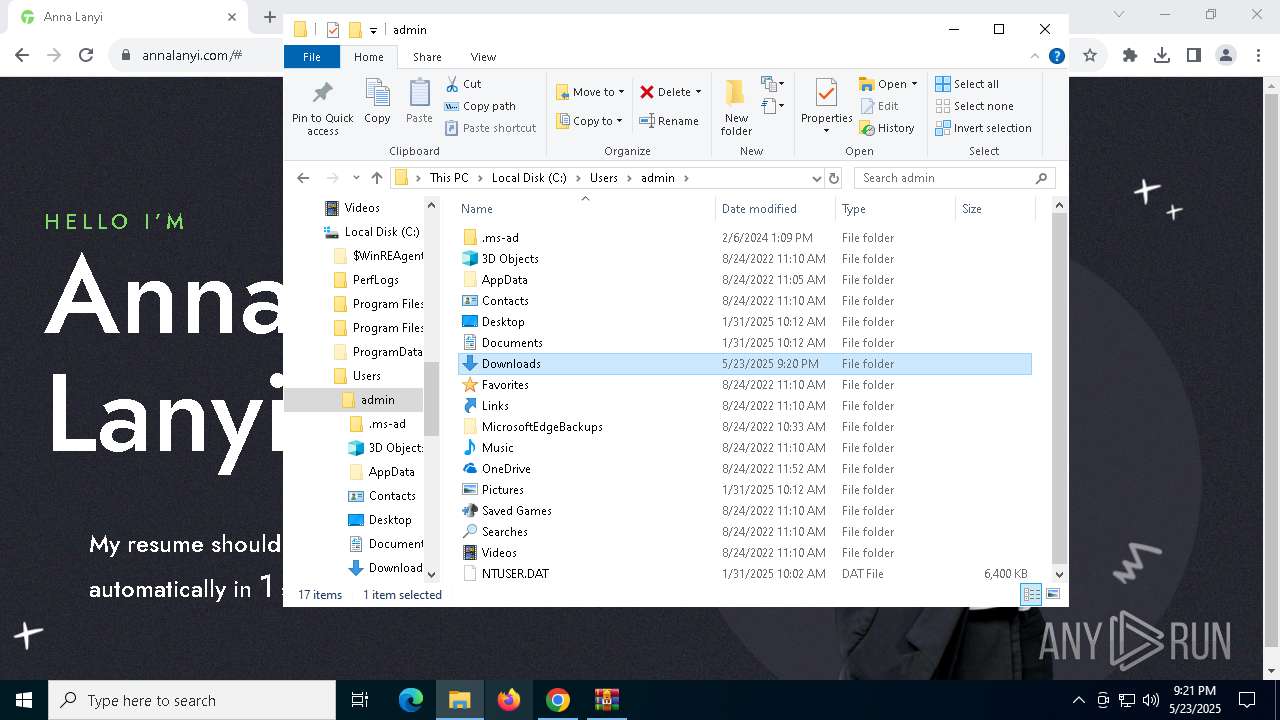
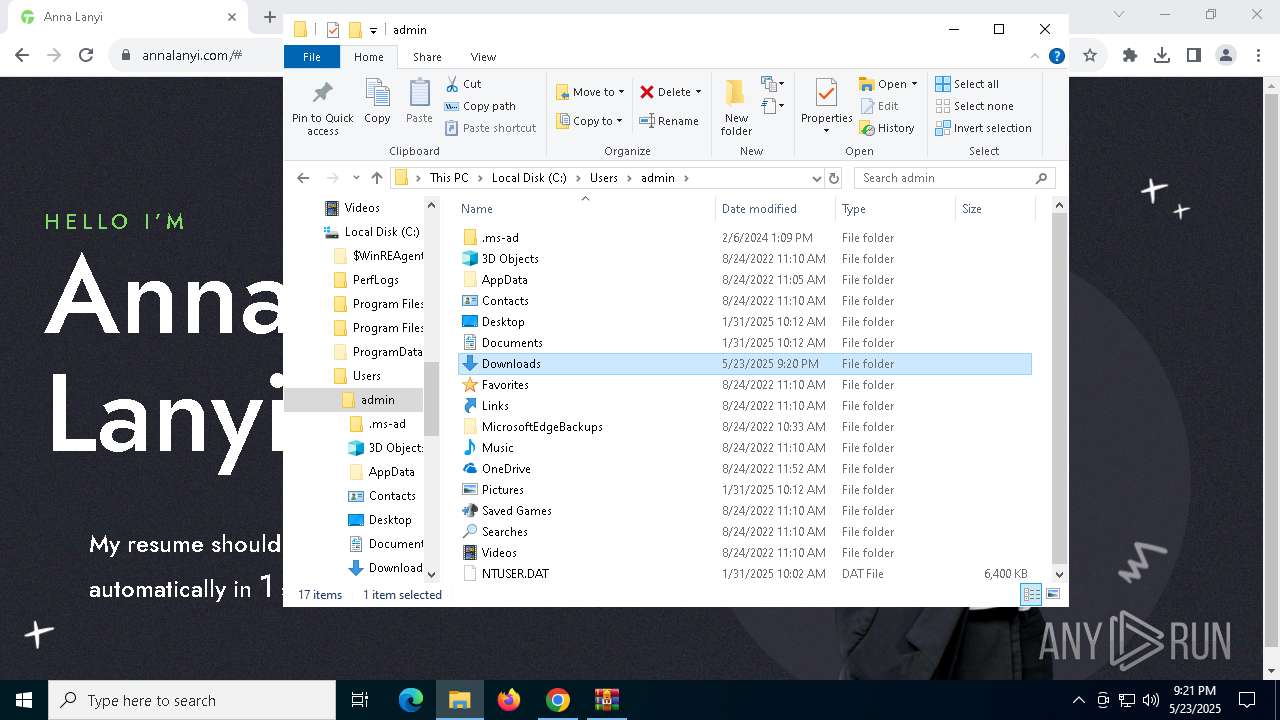
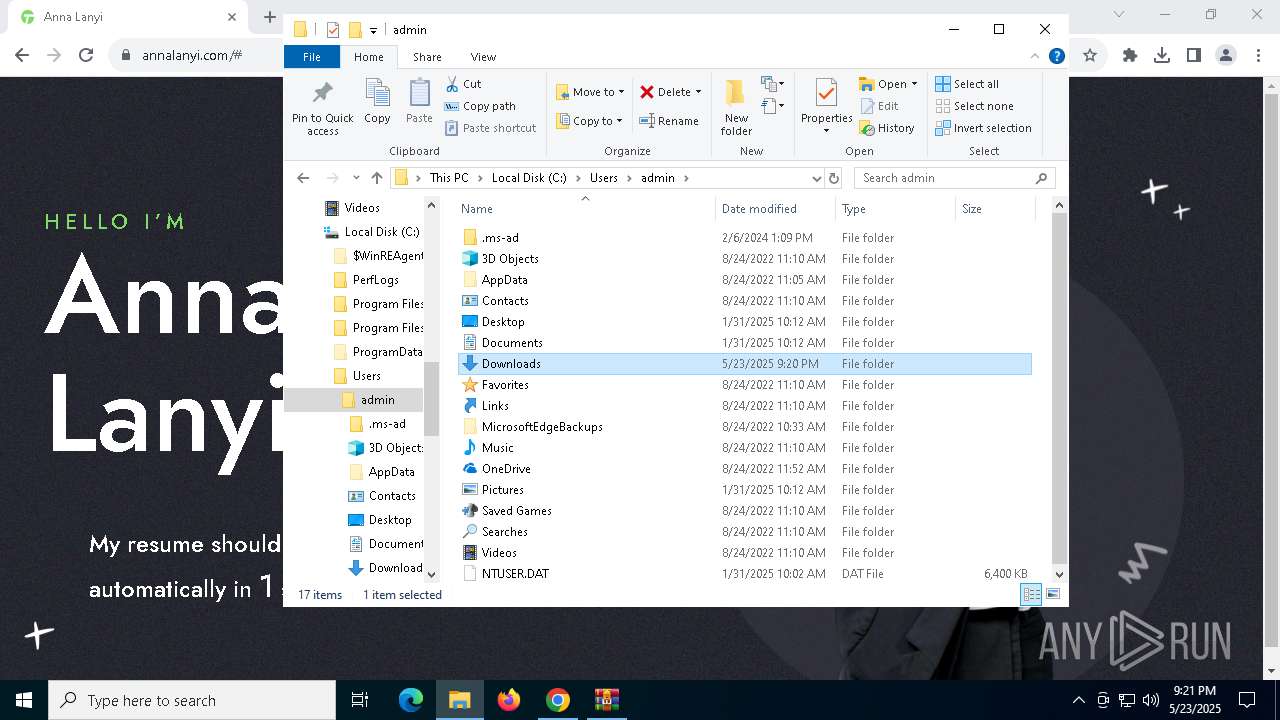
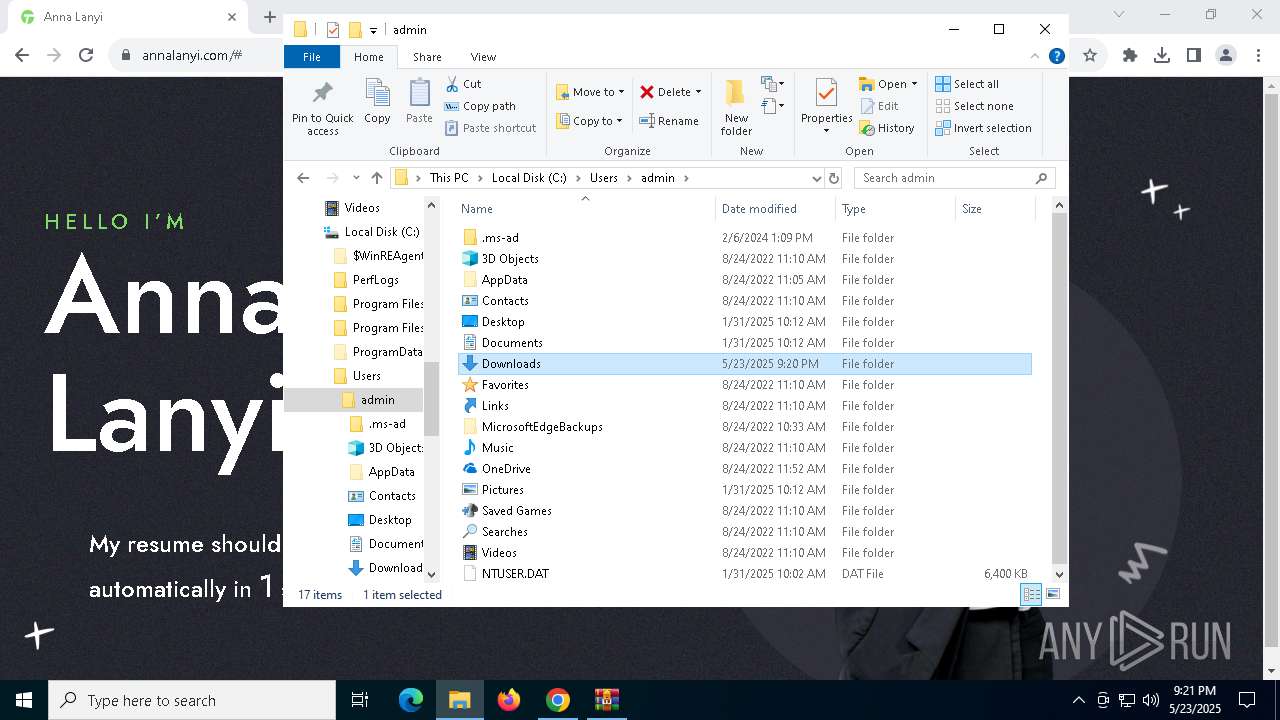
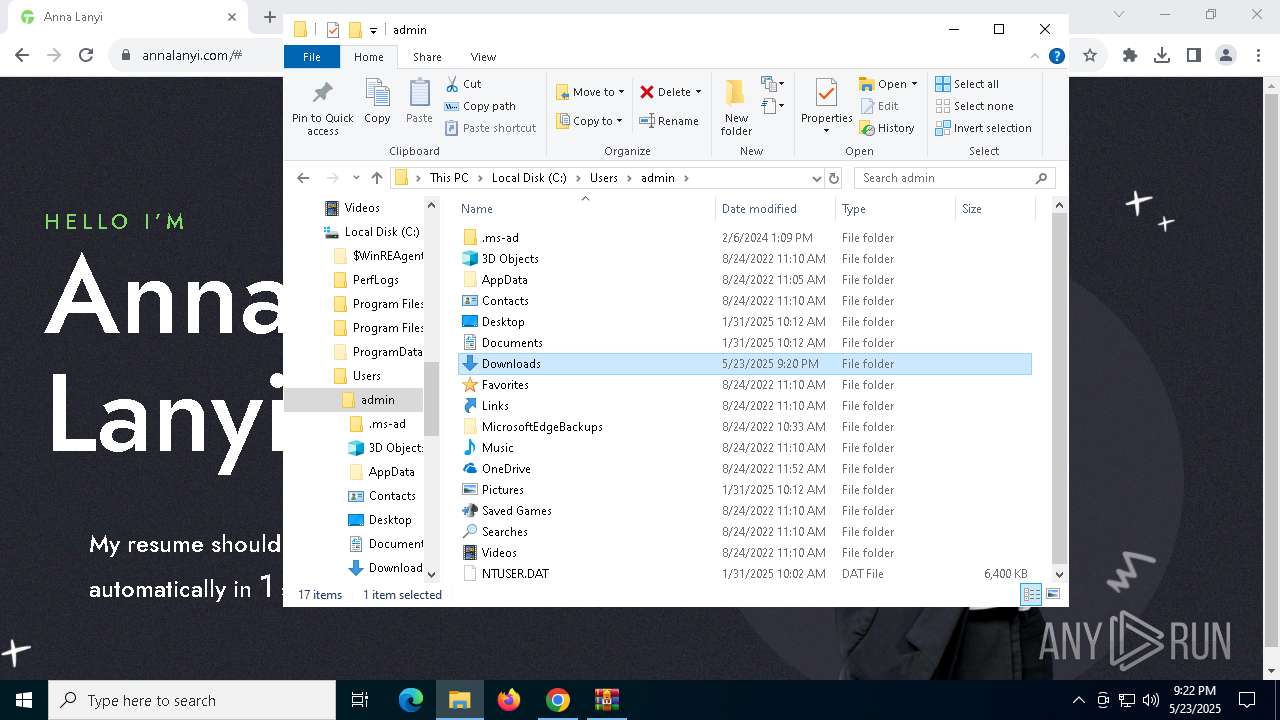
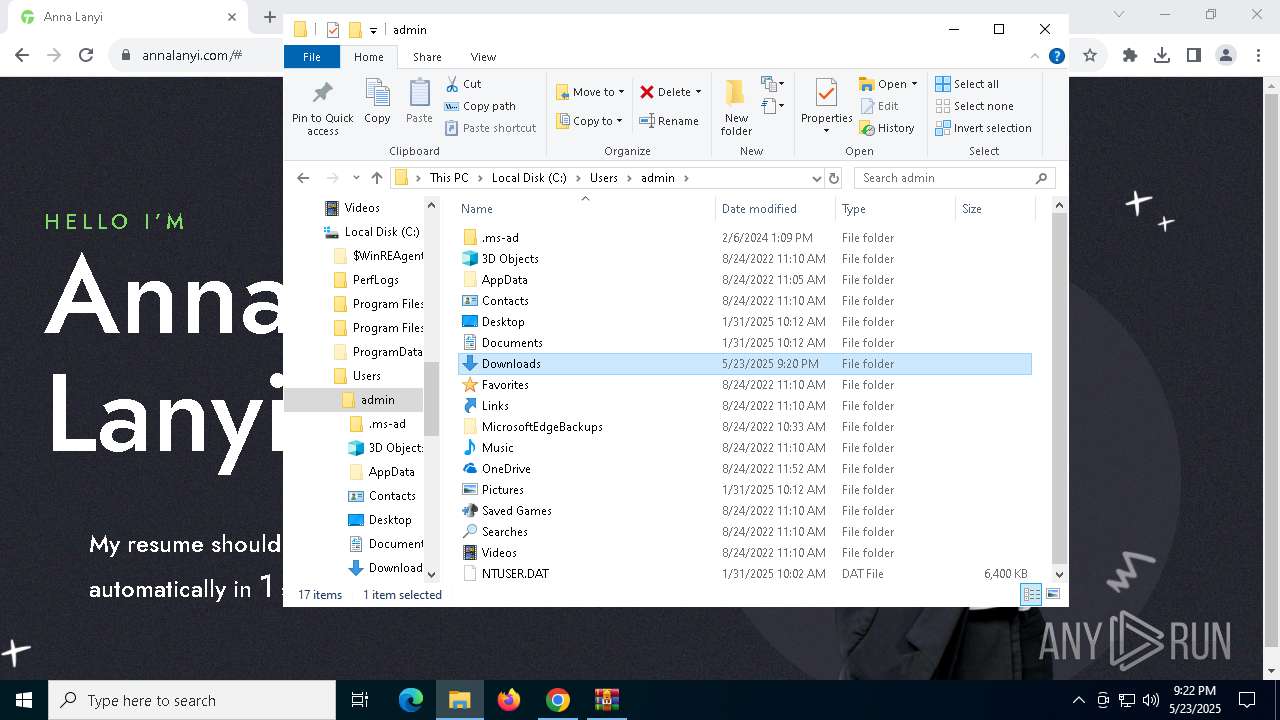
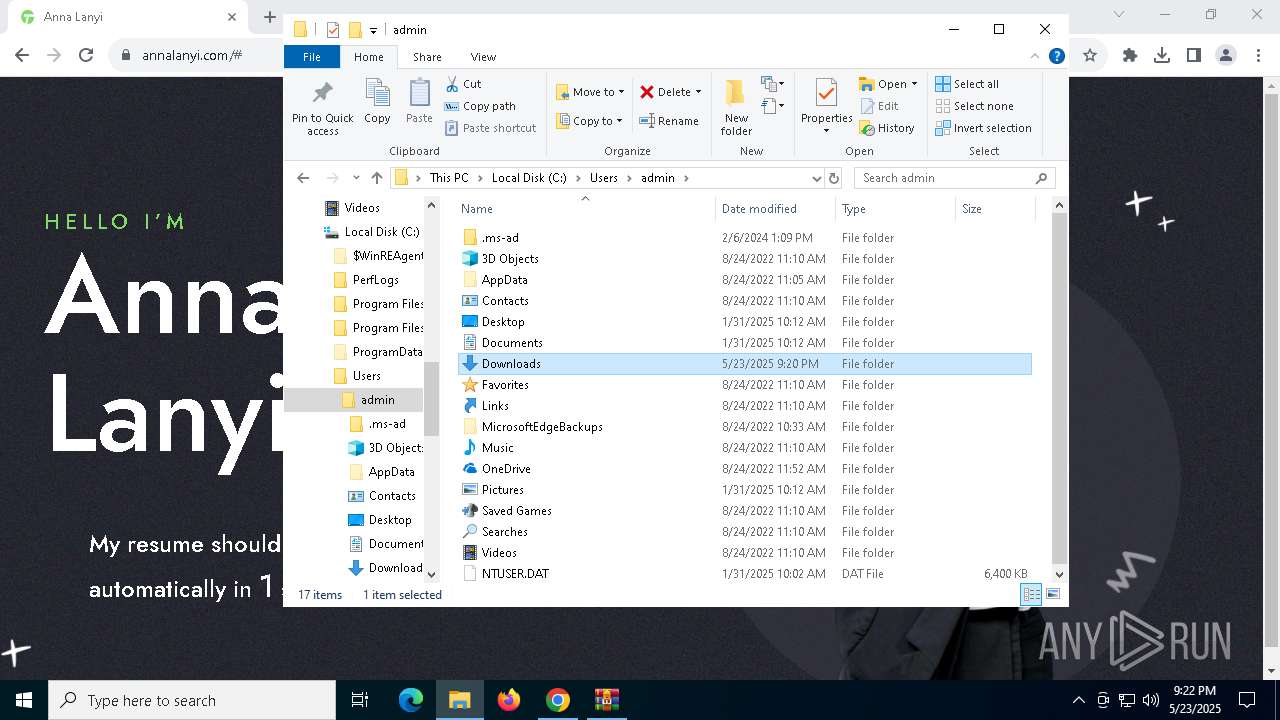
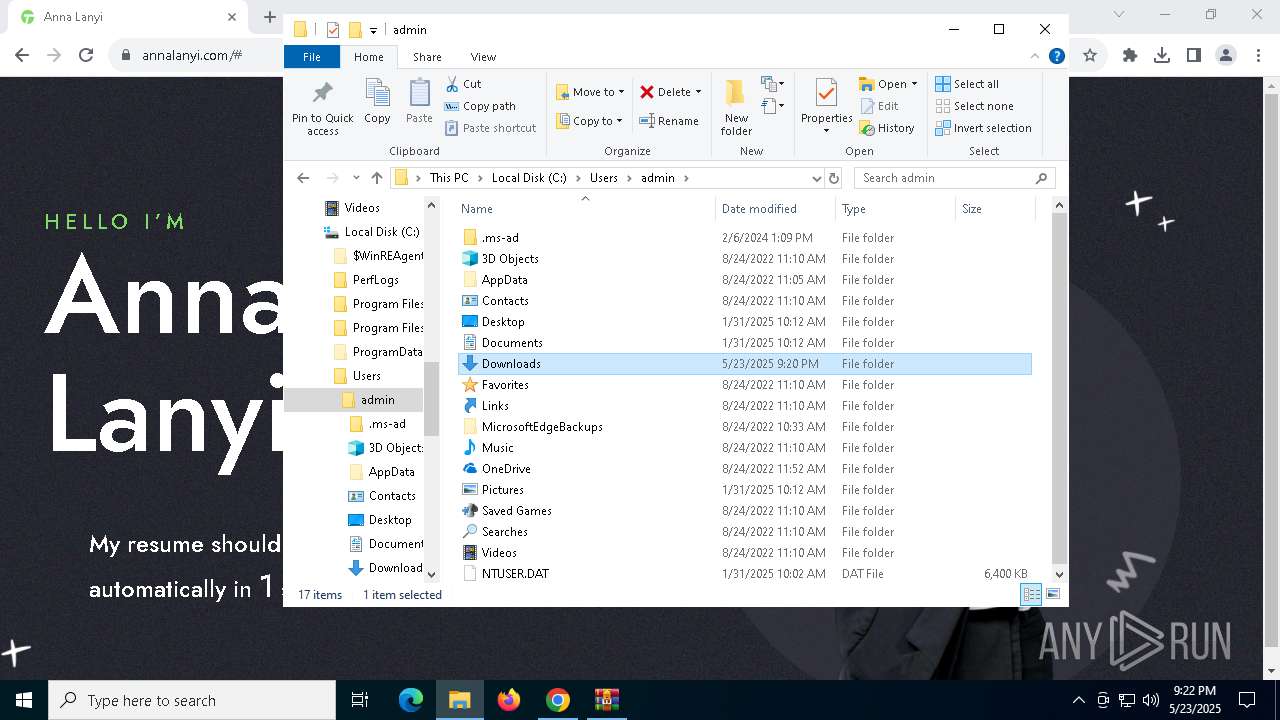
Creates files or folders in the user directory
- xcopy.exe (PID: 8148)
- ie4uinit.exe (PID: 5236)
The sample compiled with english language support
- xcopy.exe (PID: 8148)
- regsvr32.exe (PID: 4404)
- chrome.exe (PID: 7968)
Checks supported languages
- ie4uinit.exe (PID: 5236)
- ie4uinit.exe (PID: 8176)
Reads the computer name
- ie4uinit.exe (PID: 5236)
- ie4uinit.exe (PID: 8176)
Checks proxy server information
- ie4uinit.exe (PID: 5236)
Reads Environment values
- ie4uinit.exe (PID: 5236)
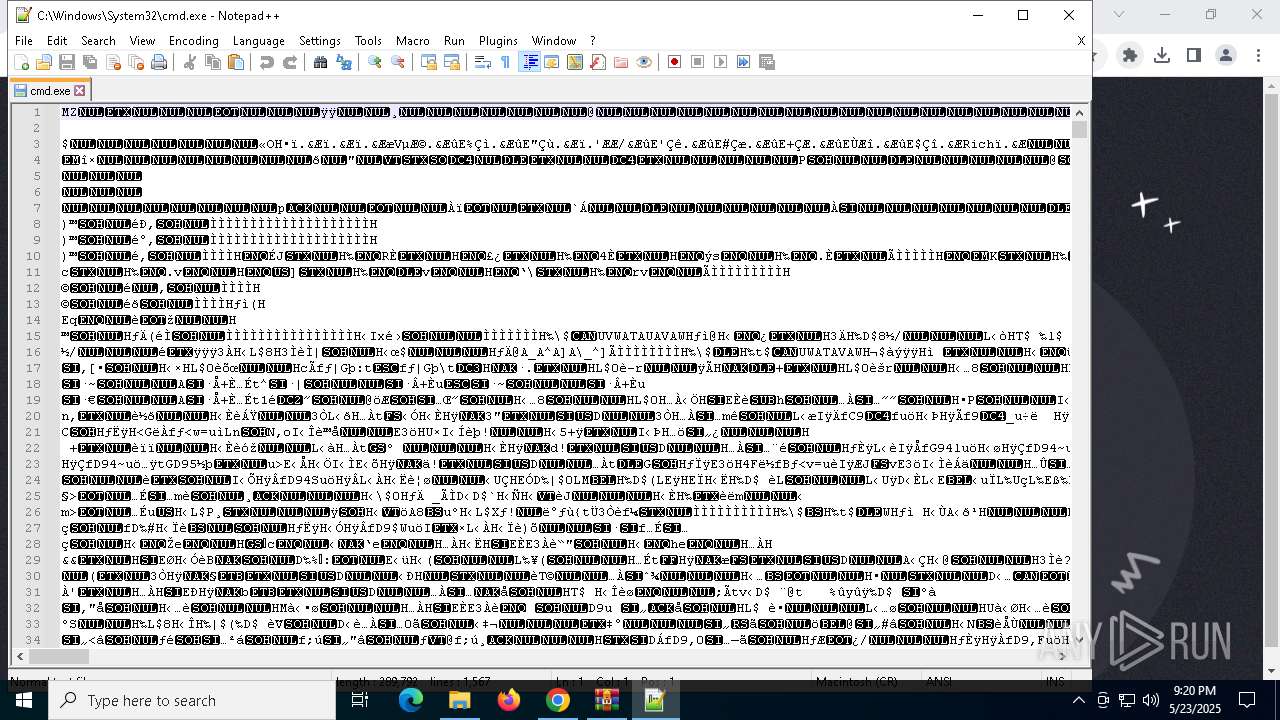
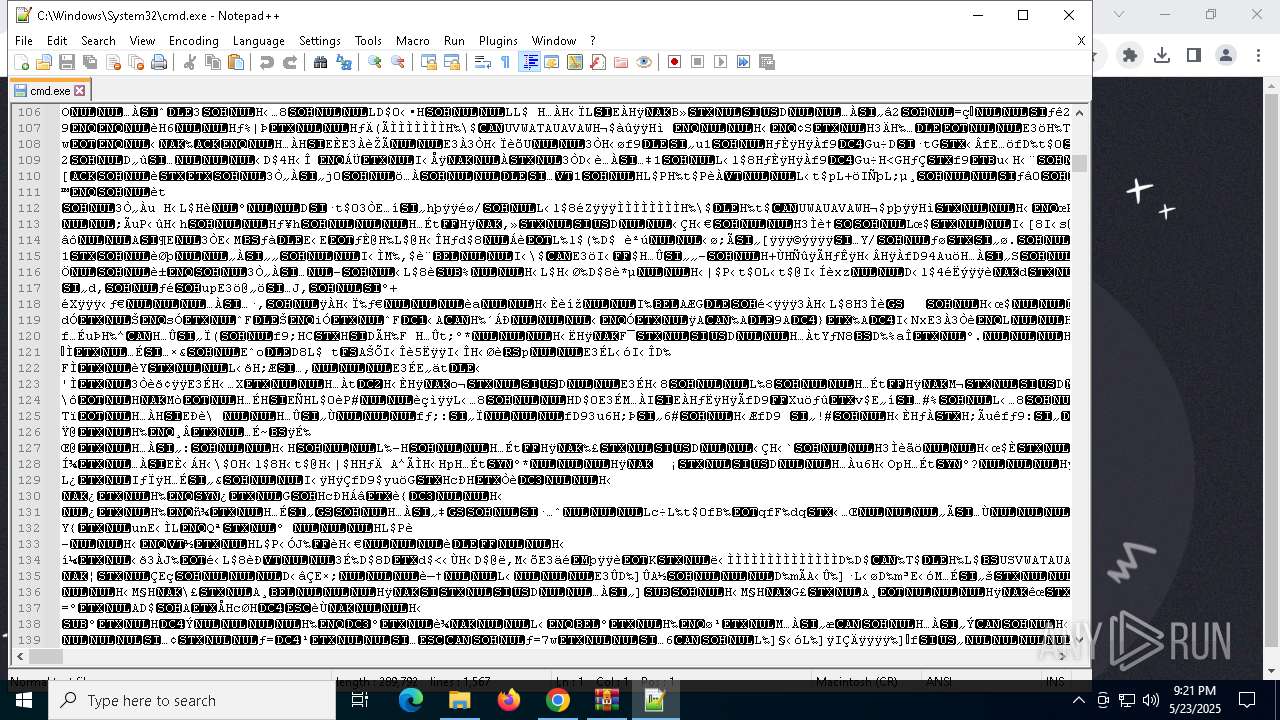
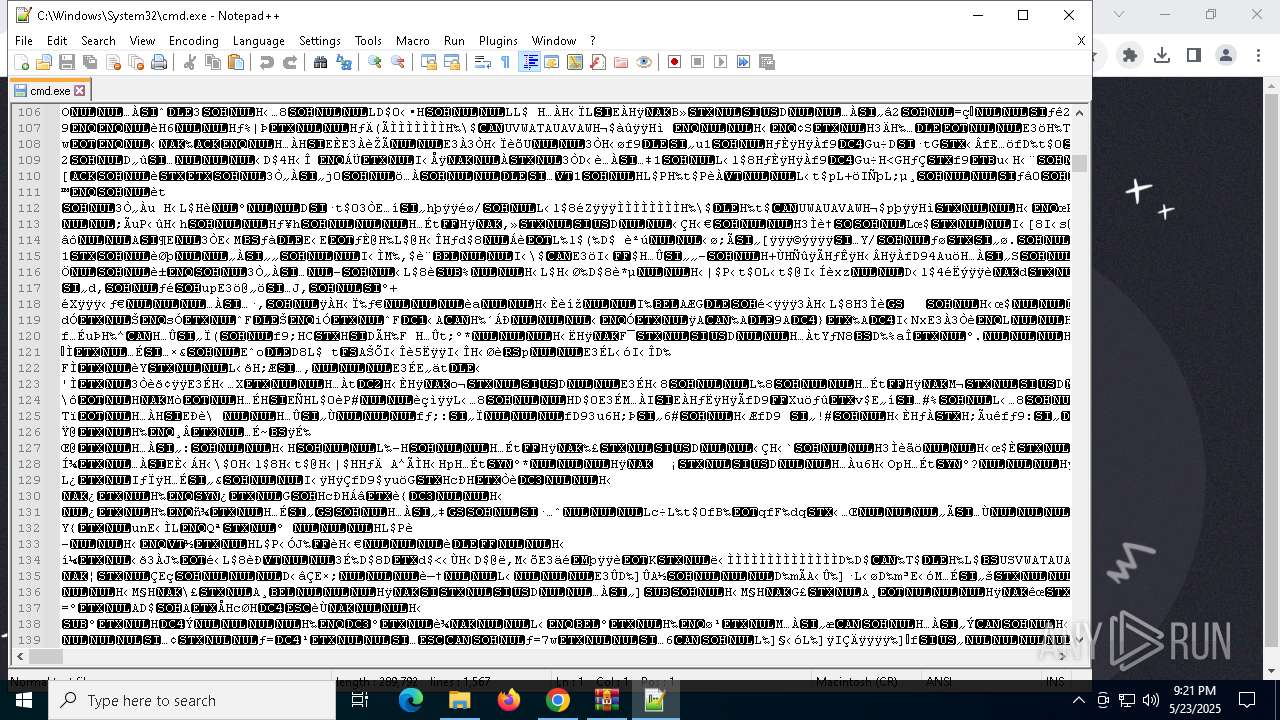
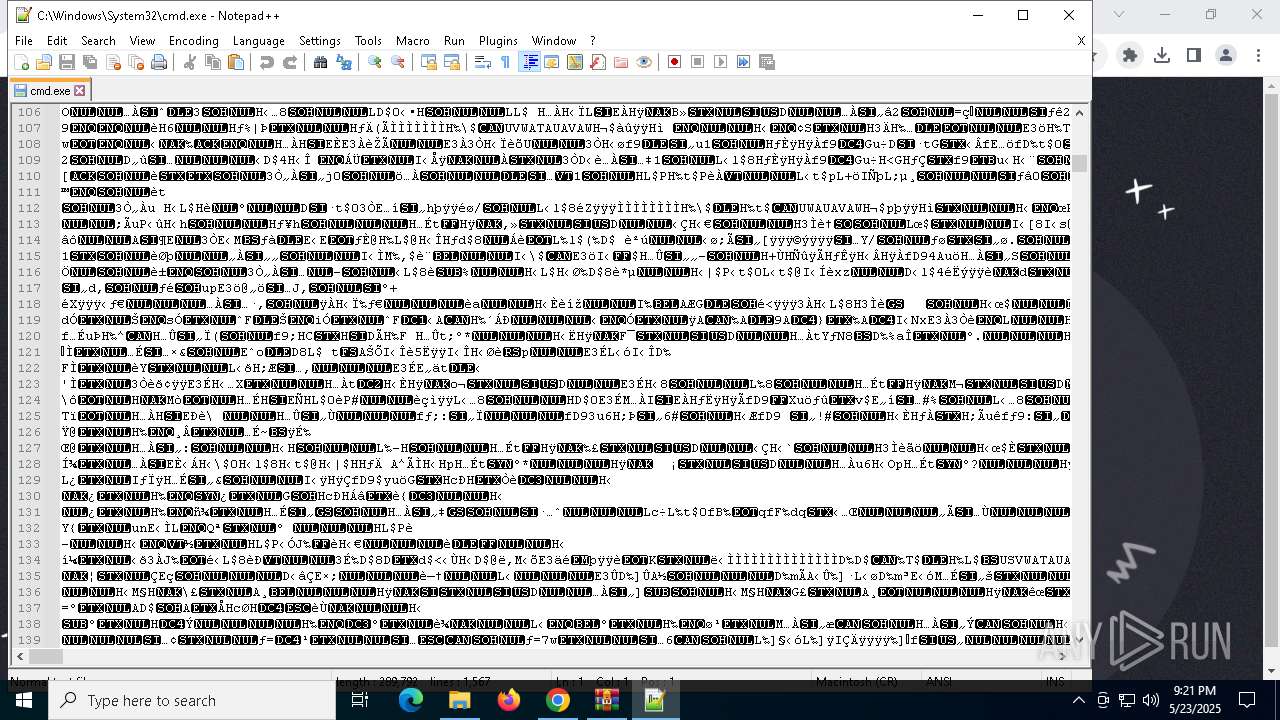
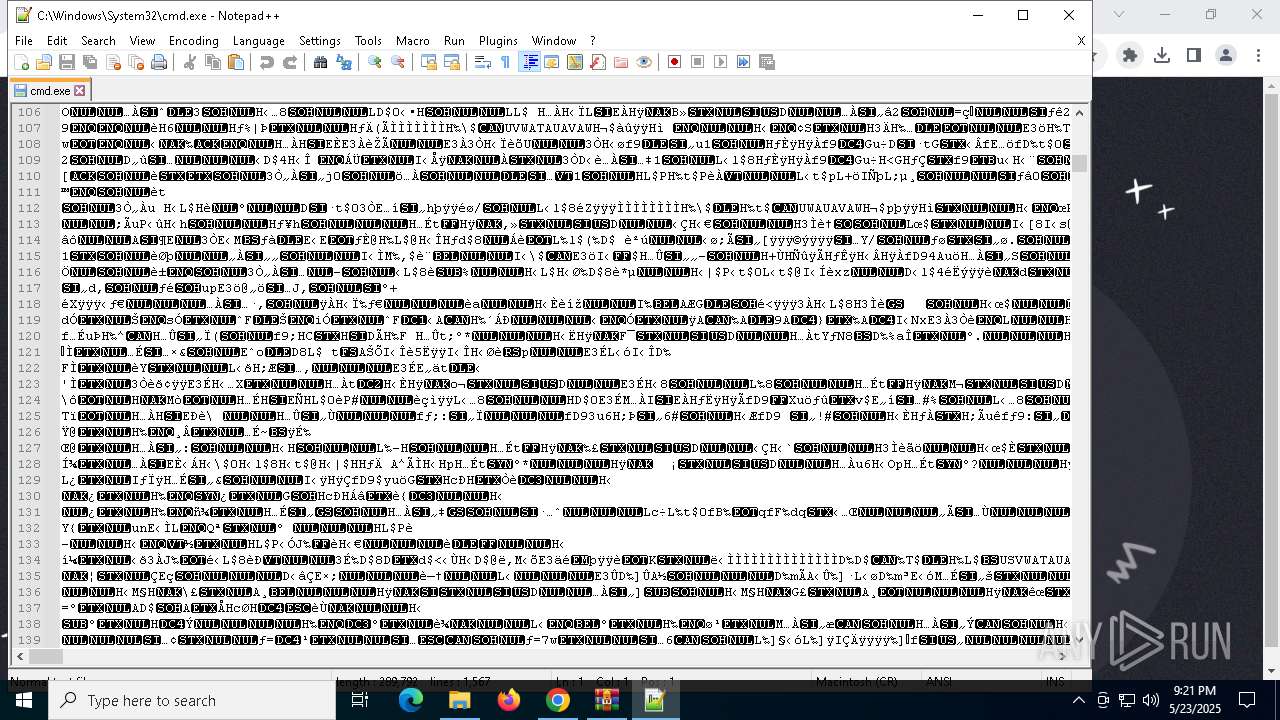
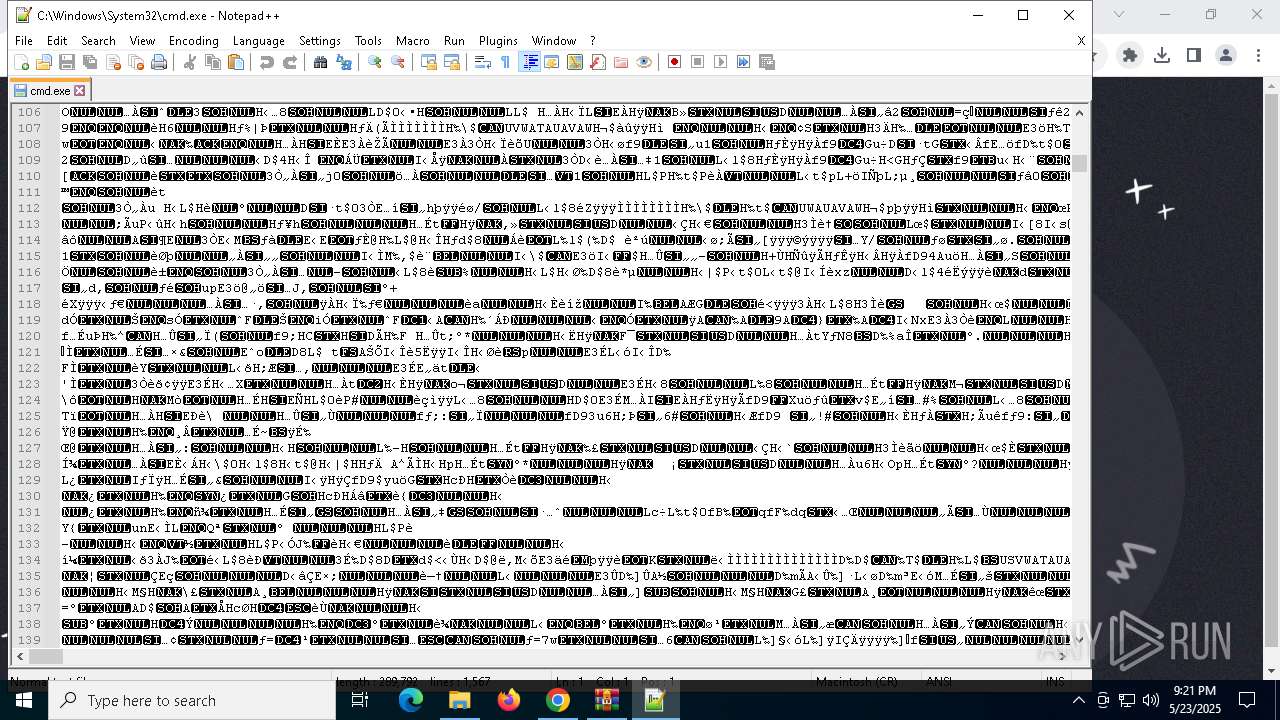
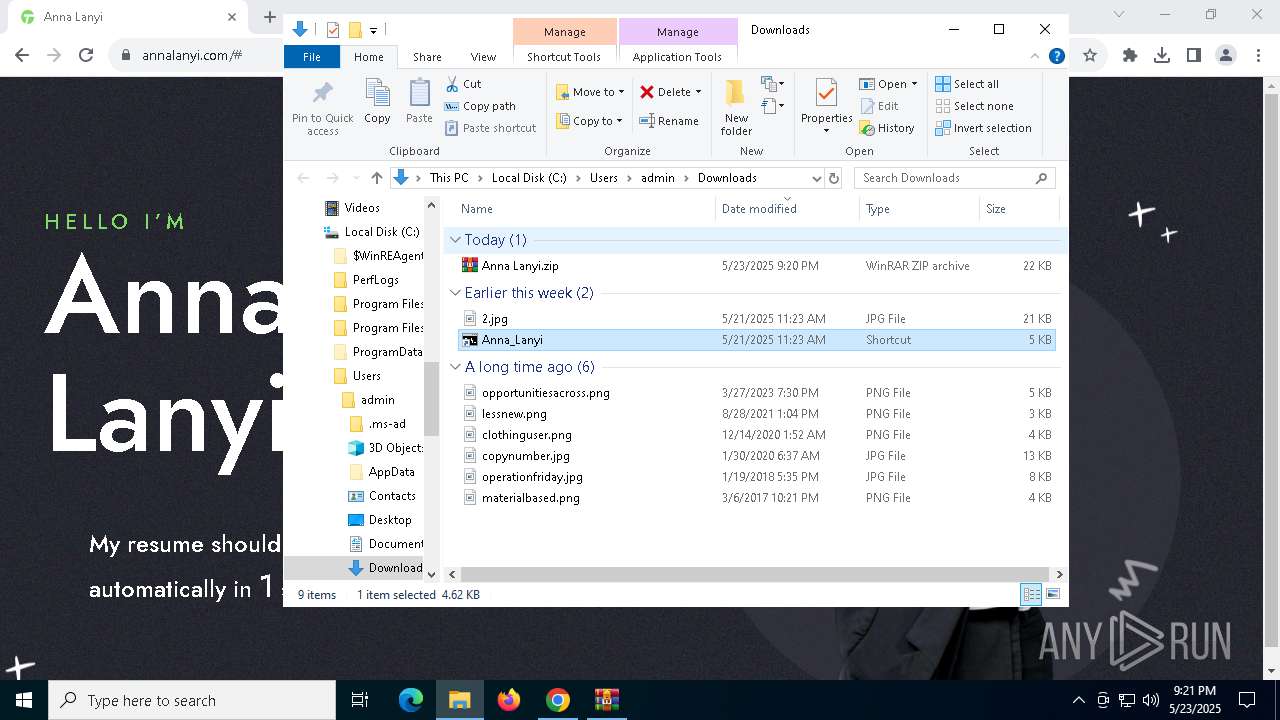
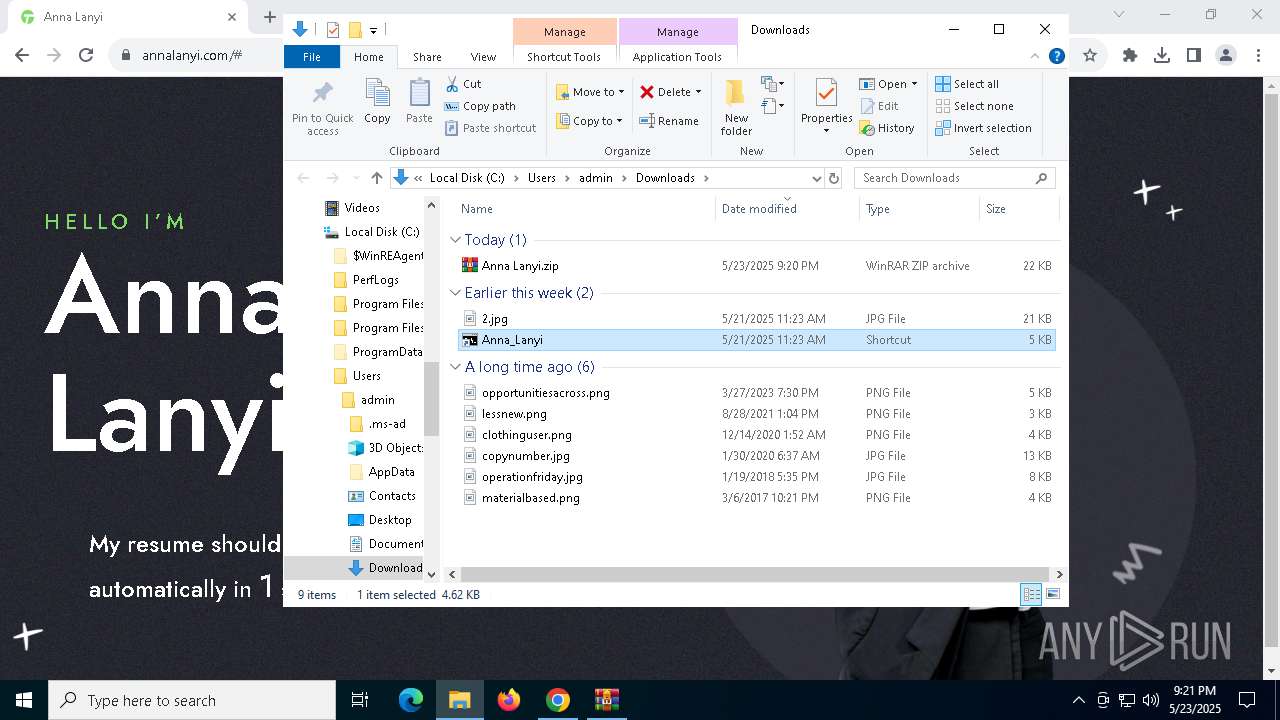
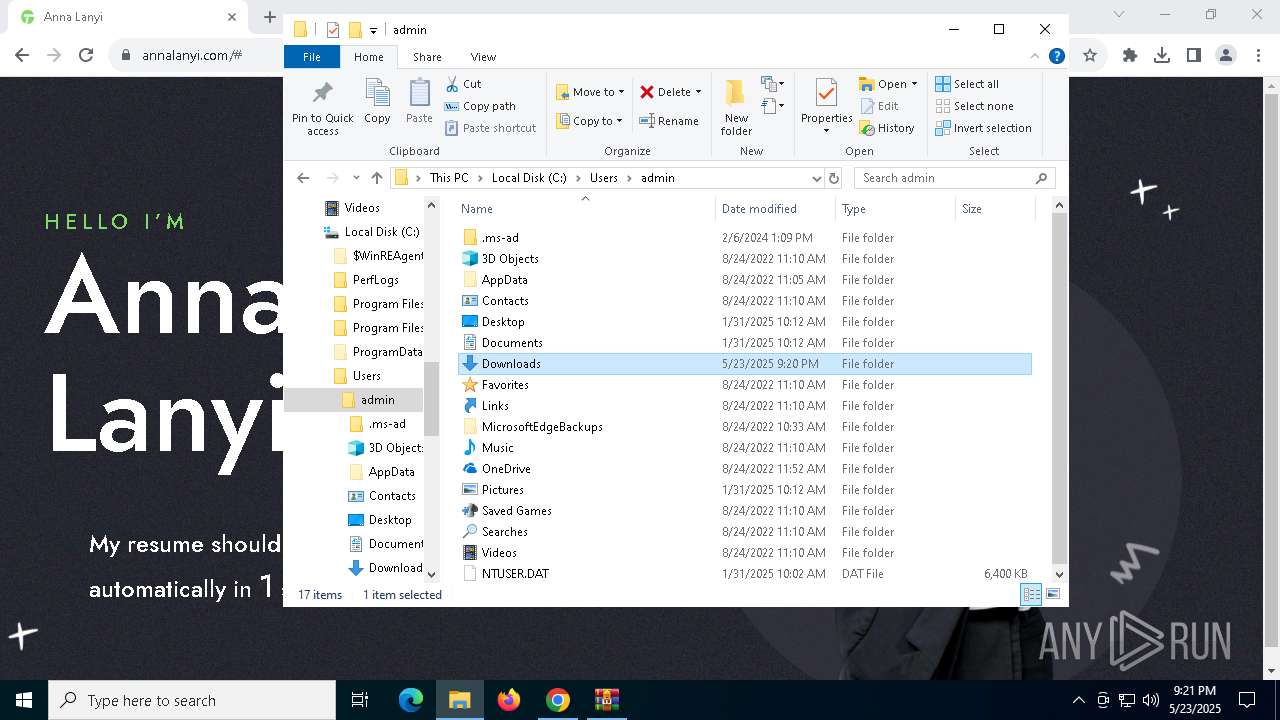
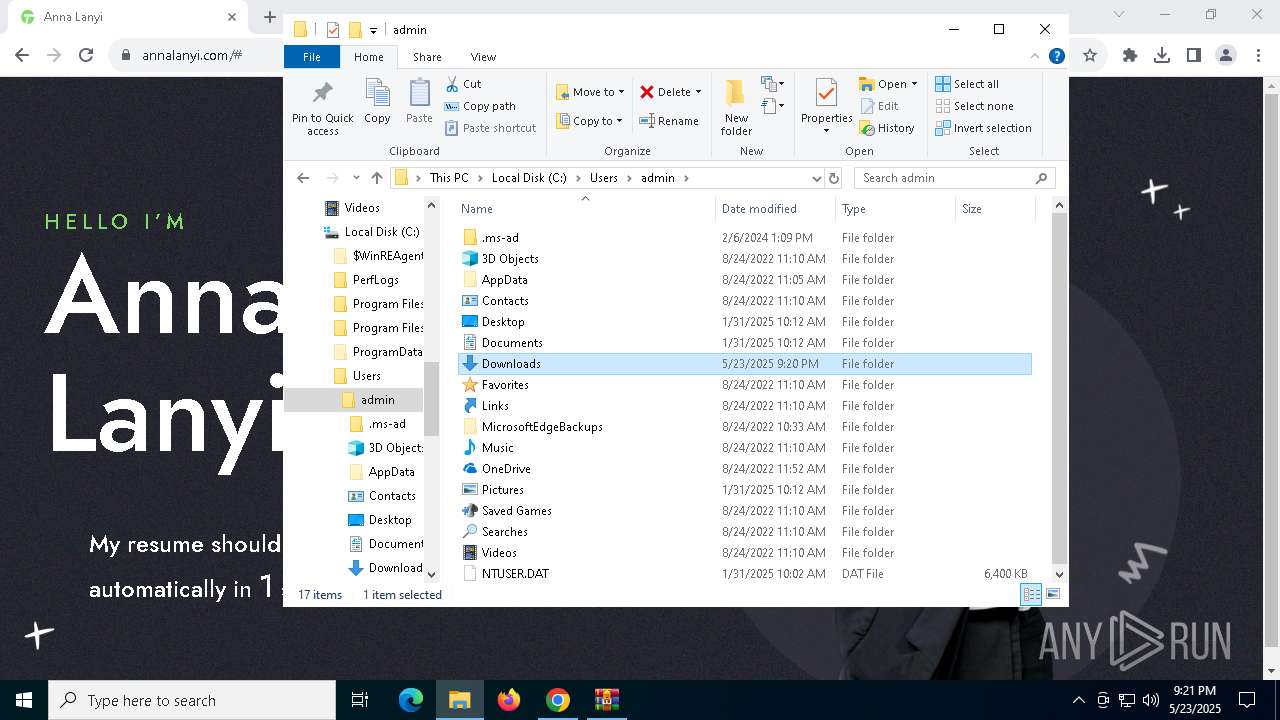
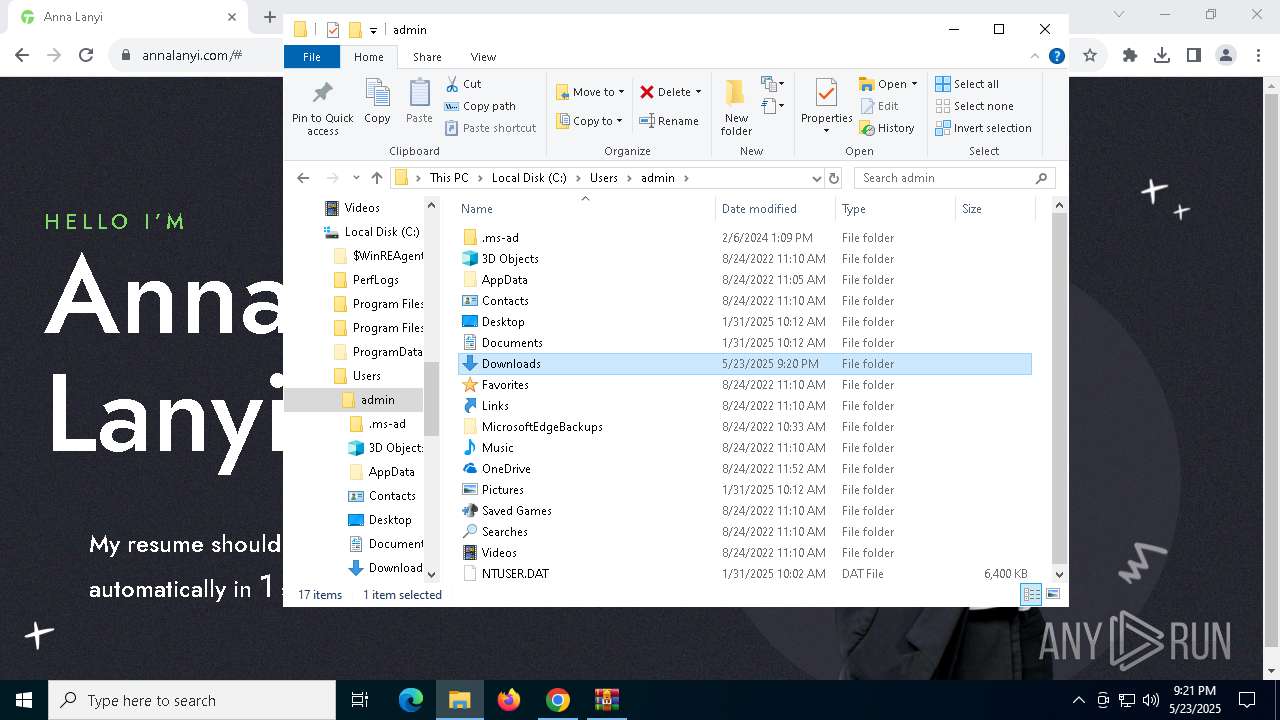
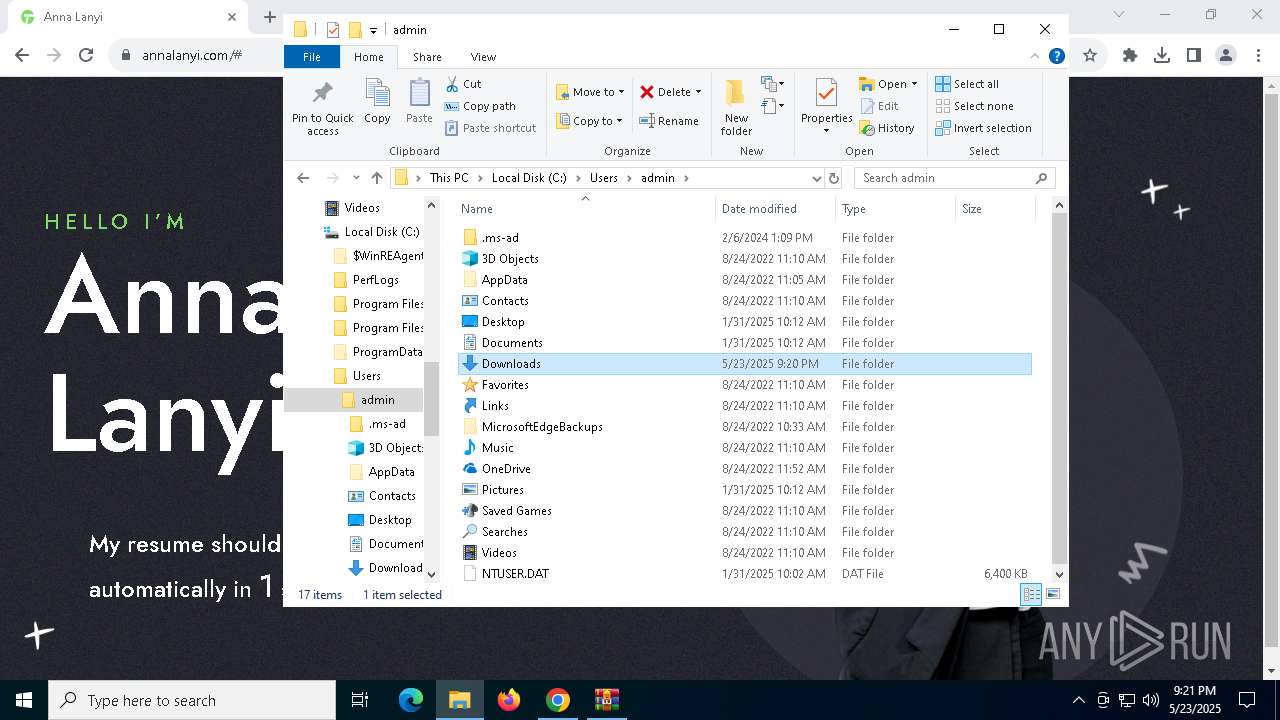
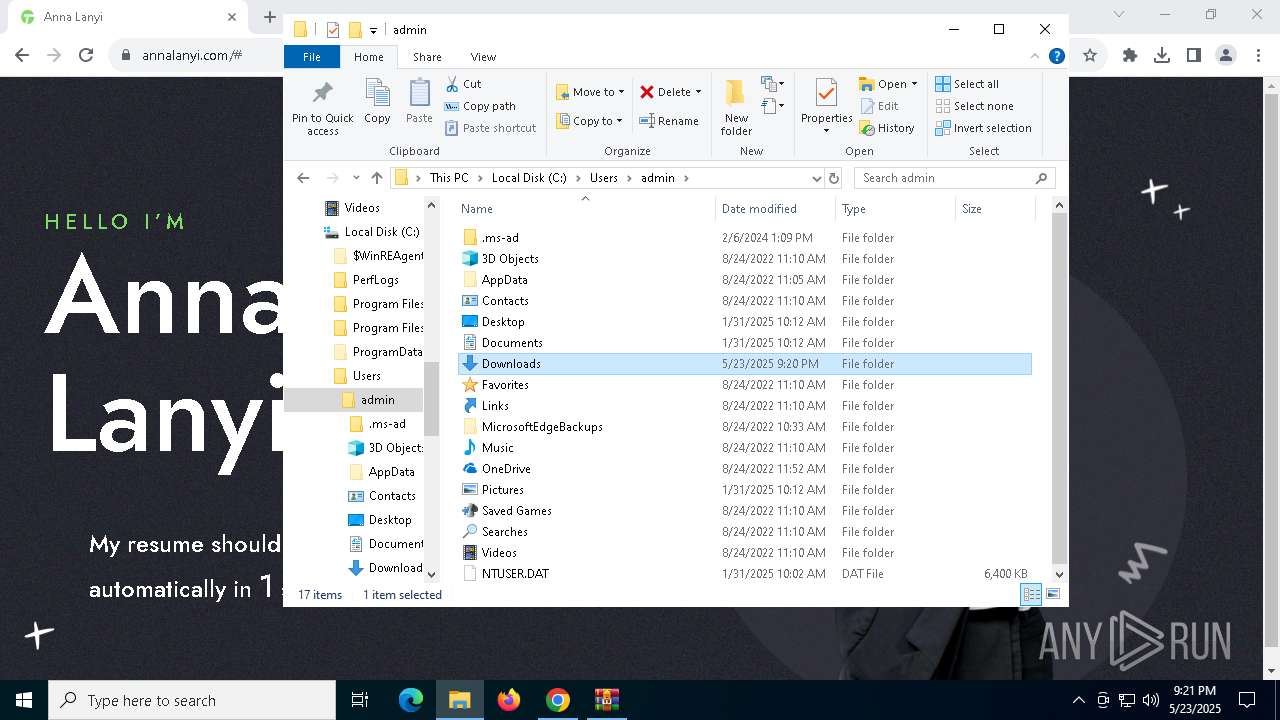
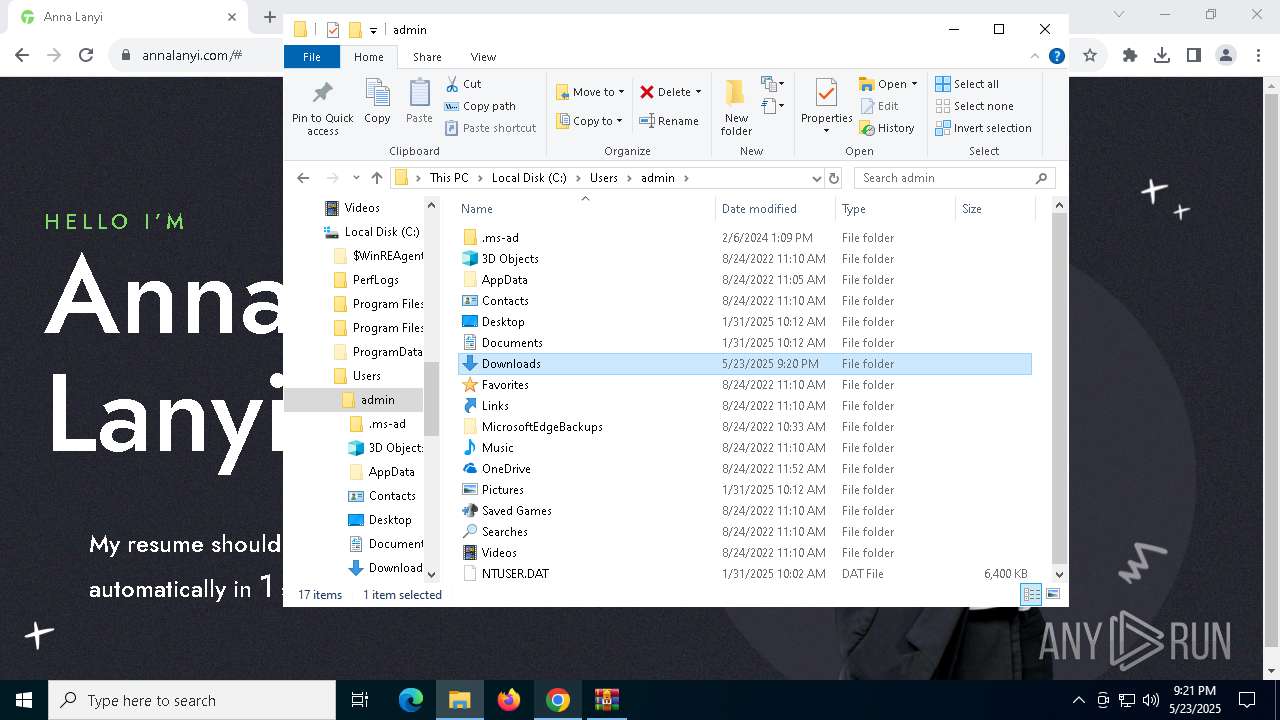
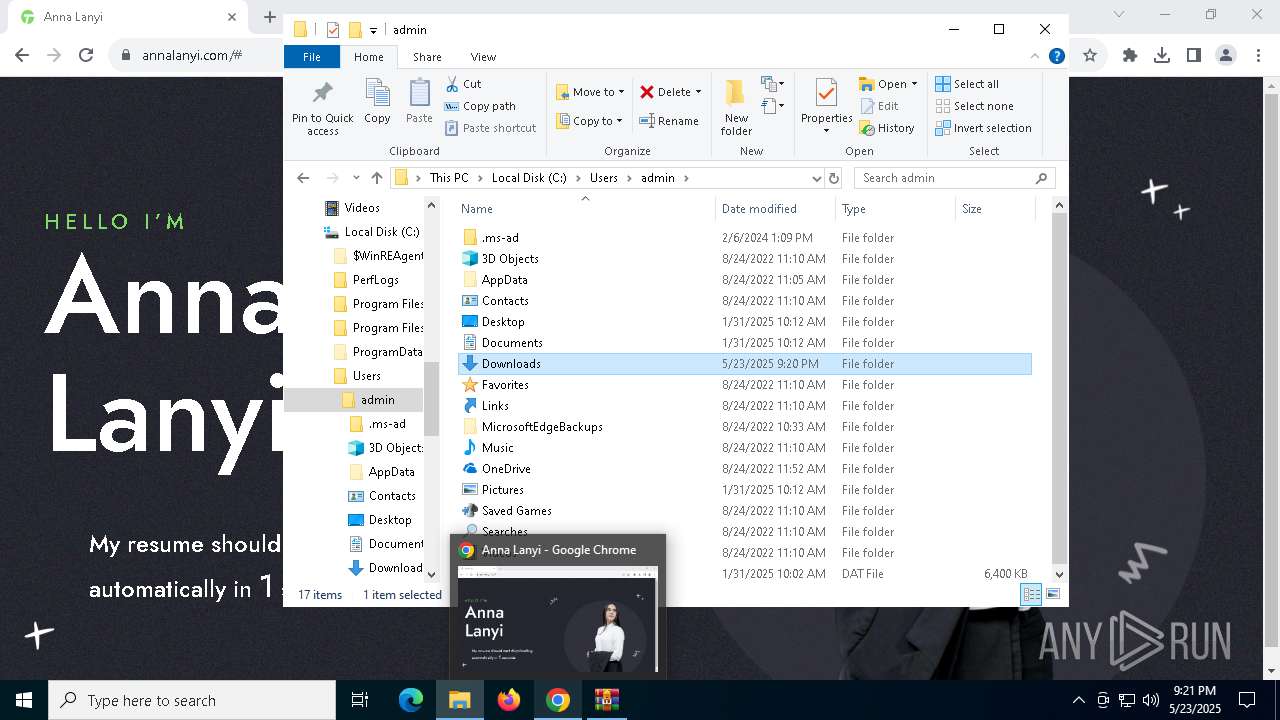
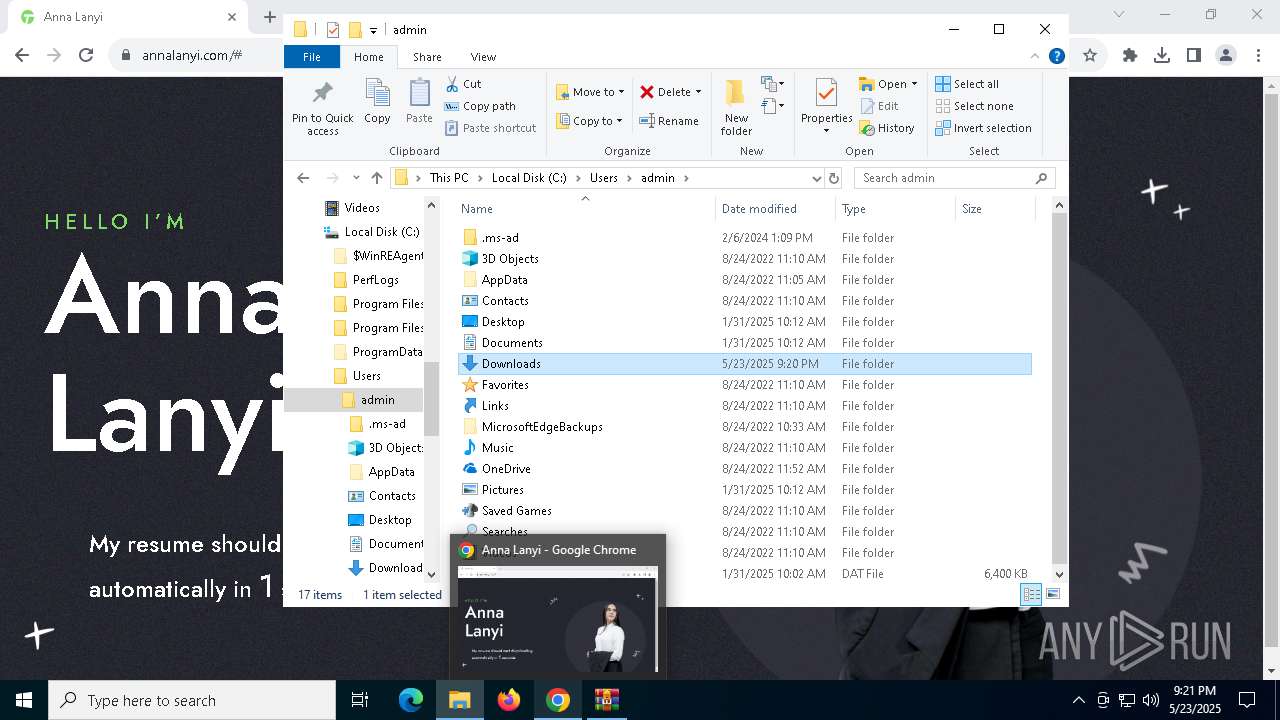
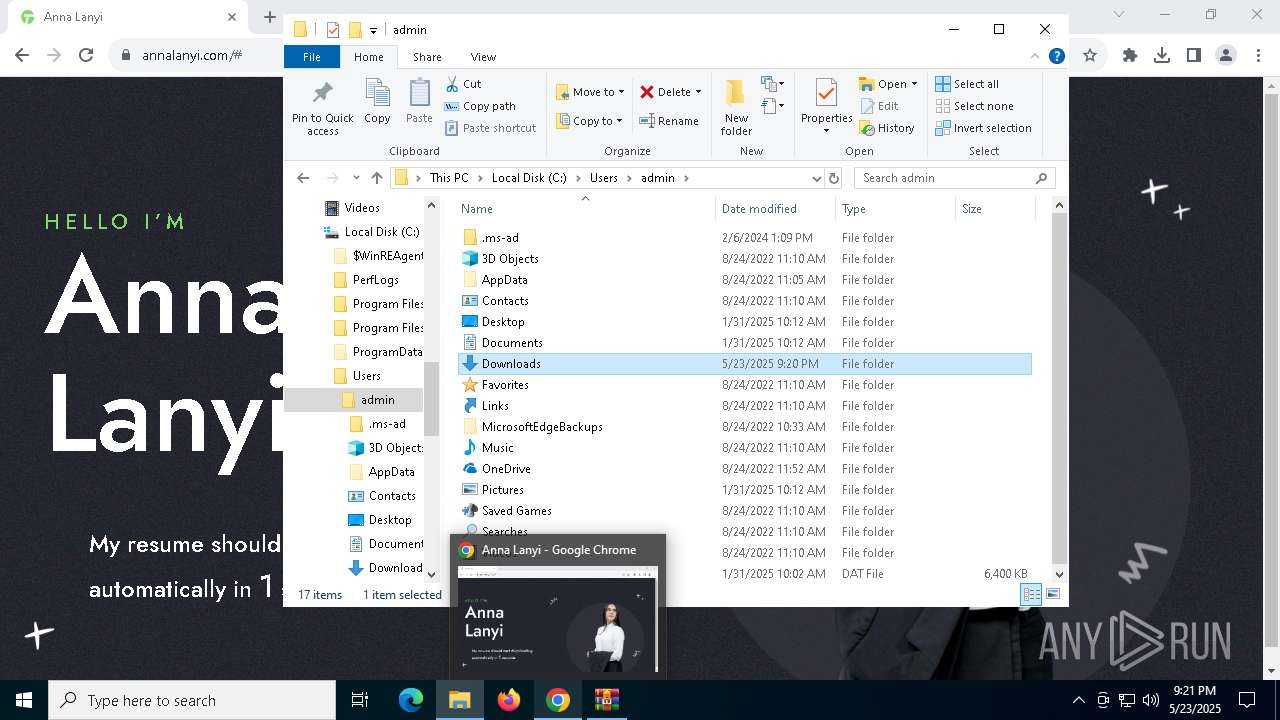
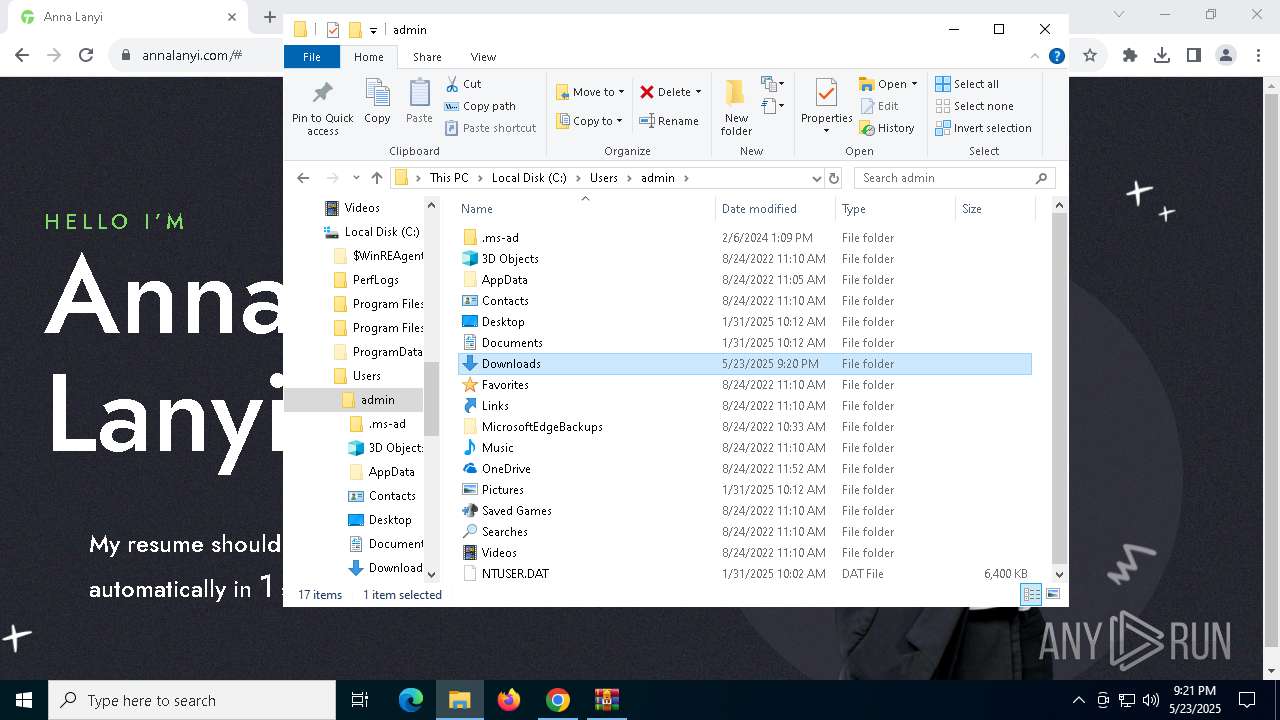
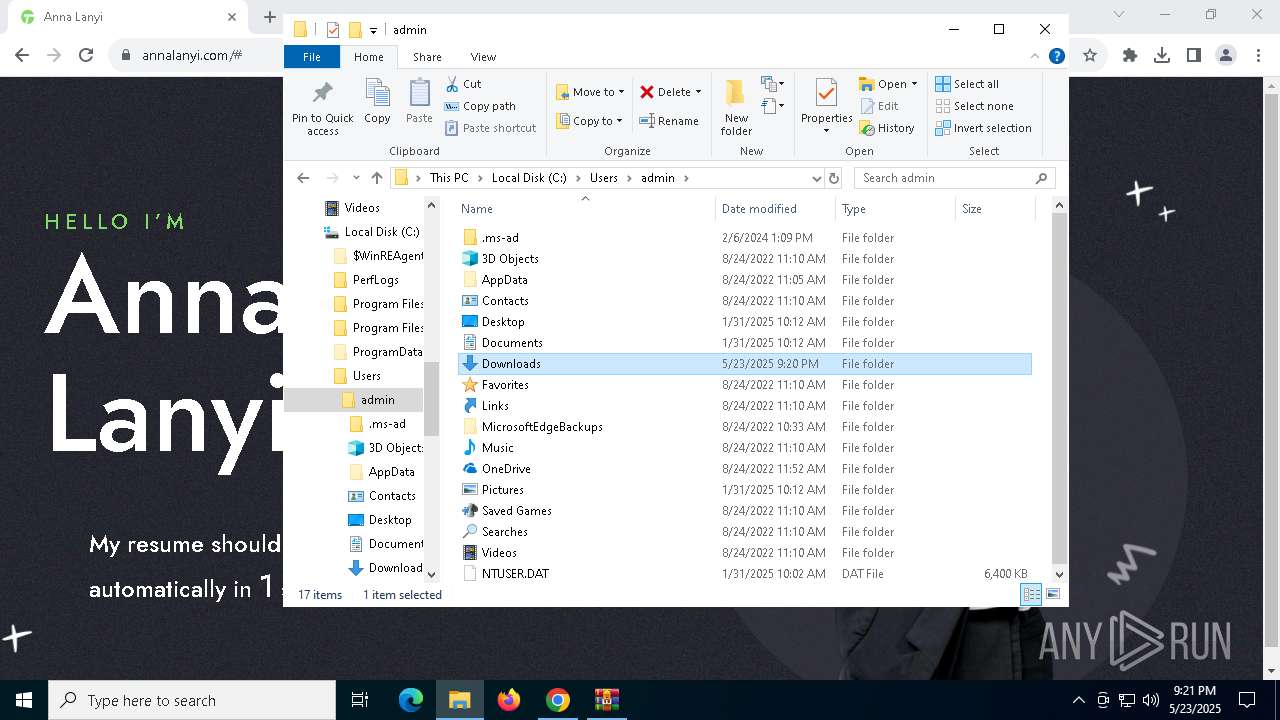
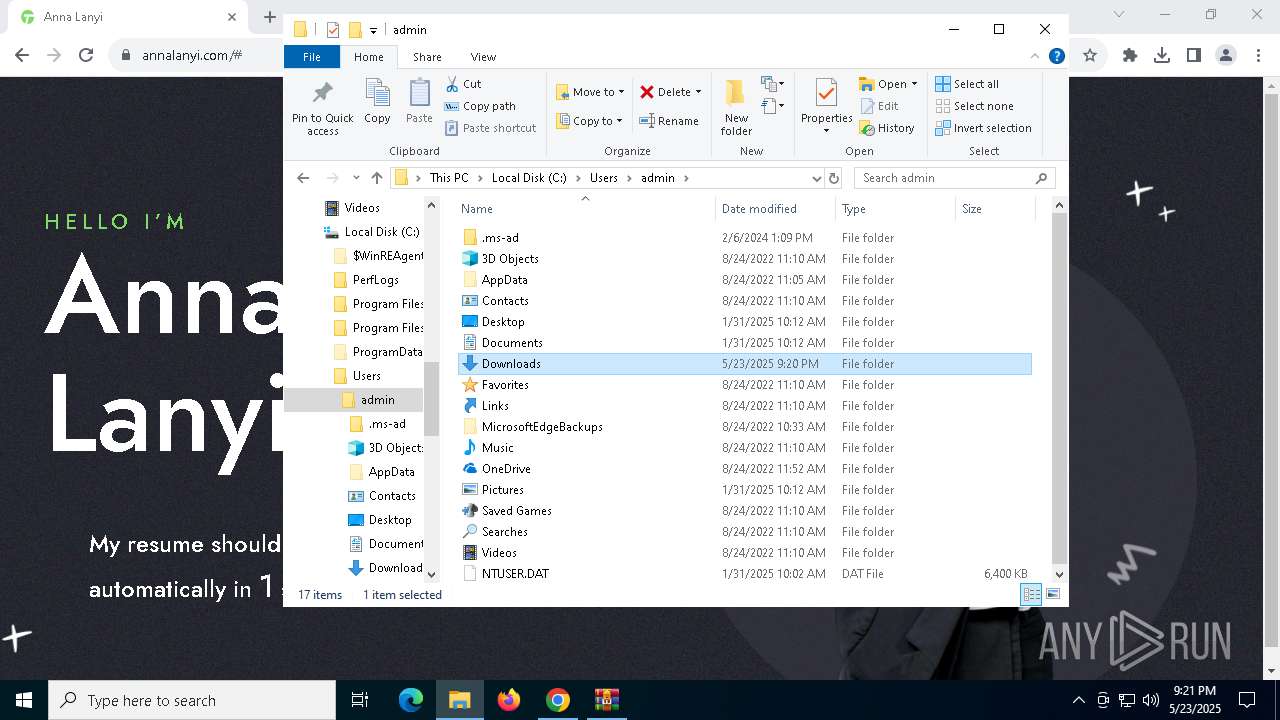
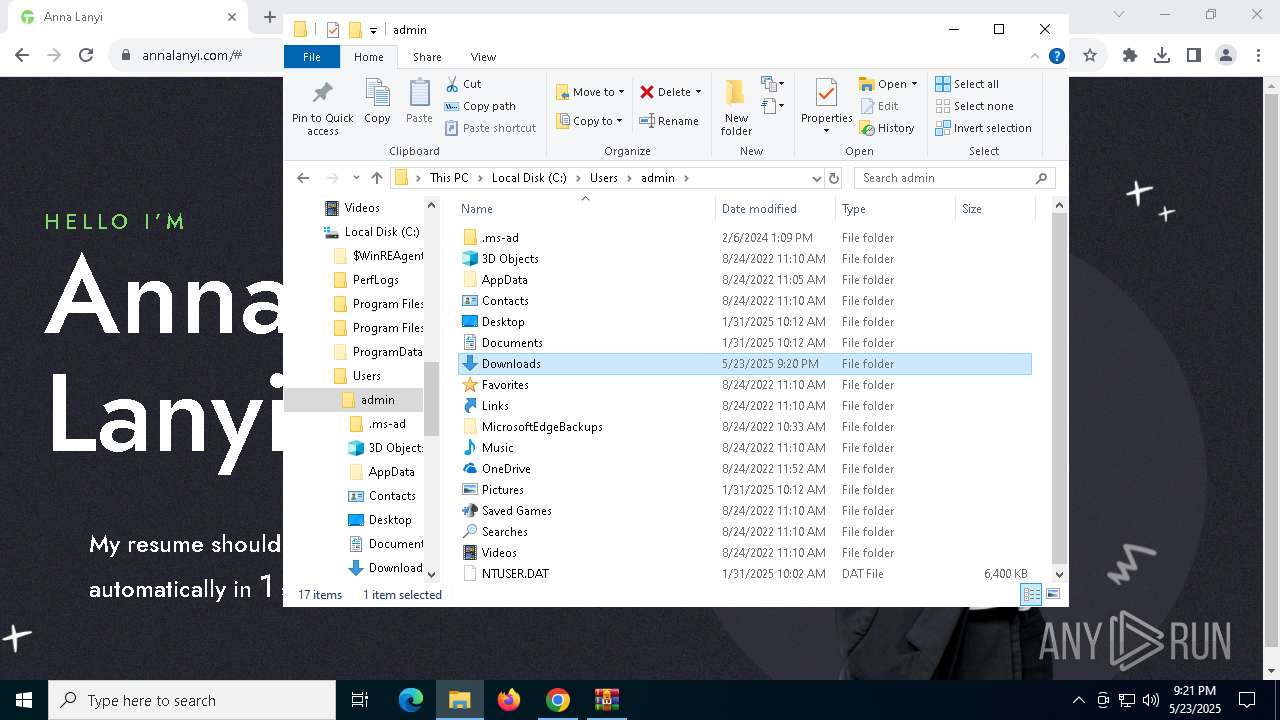
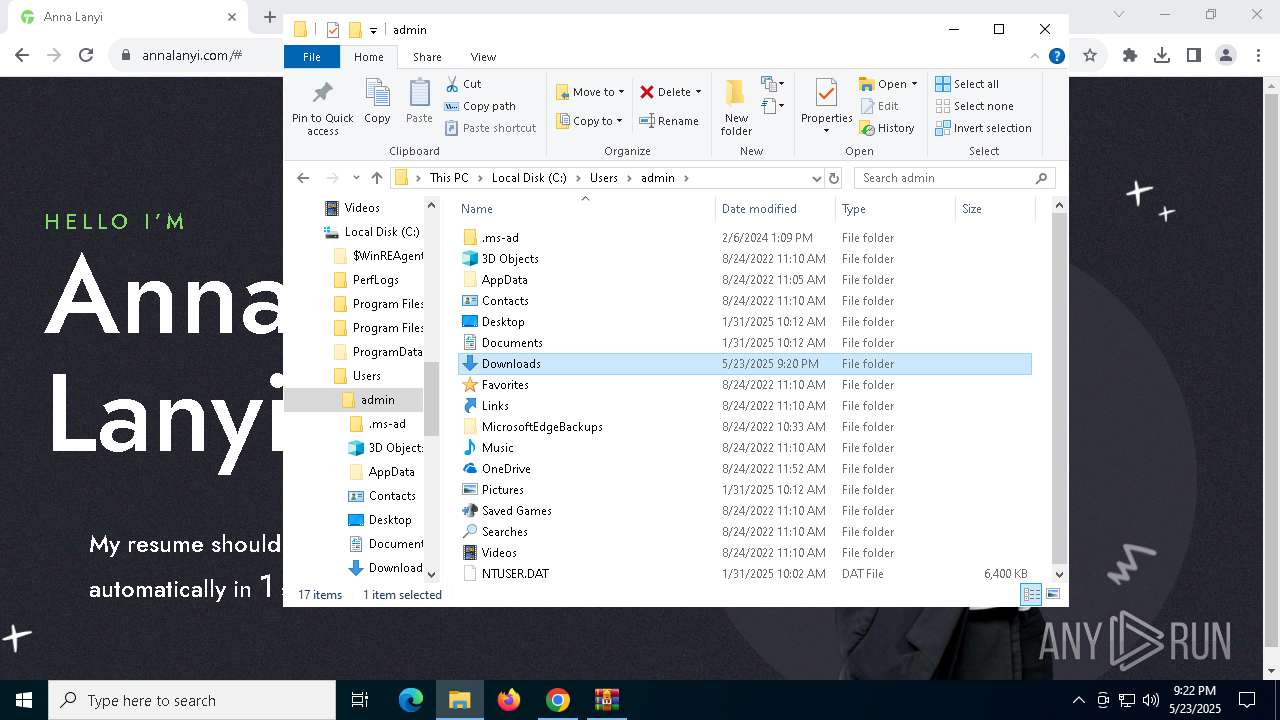
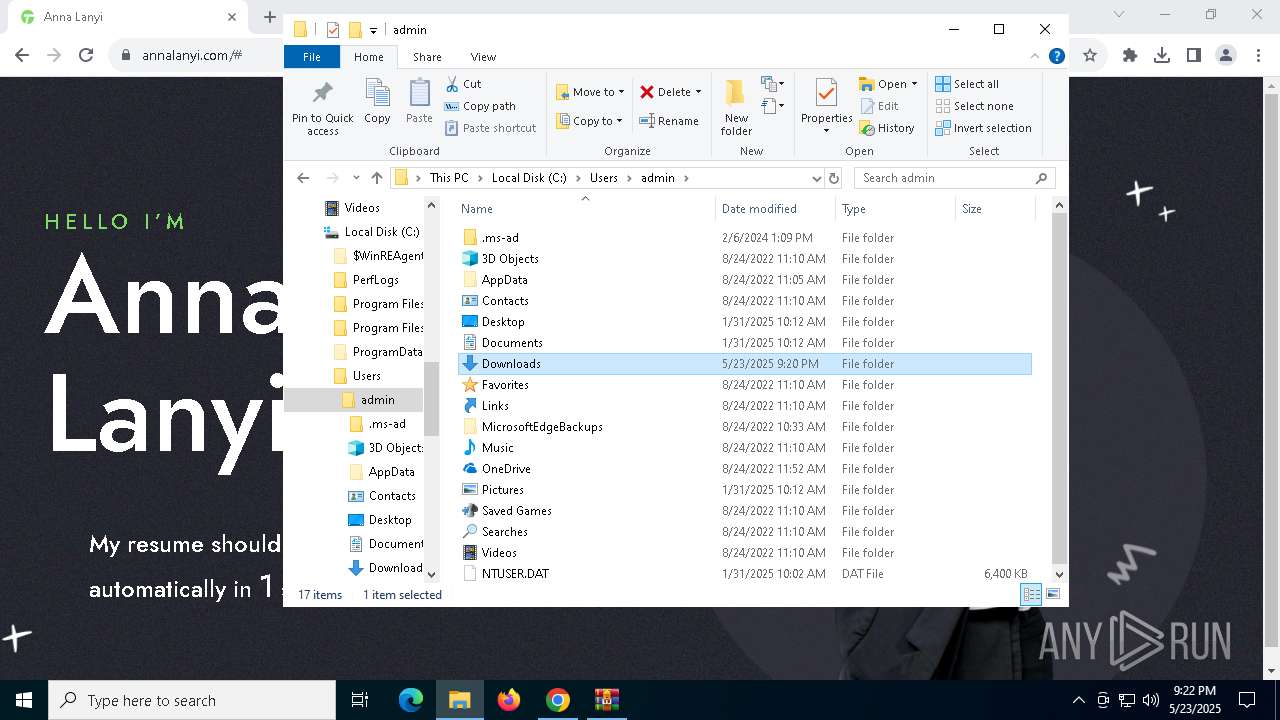
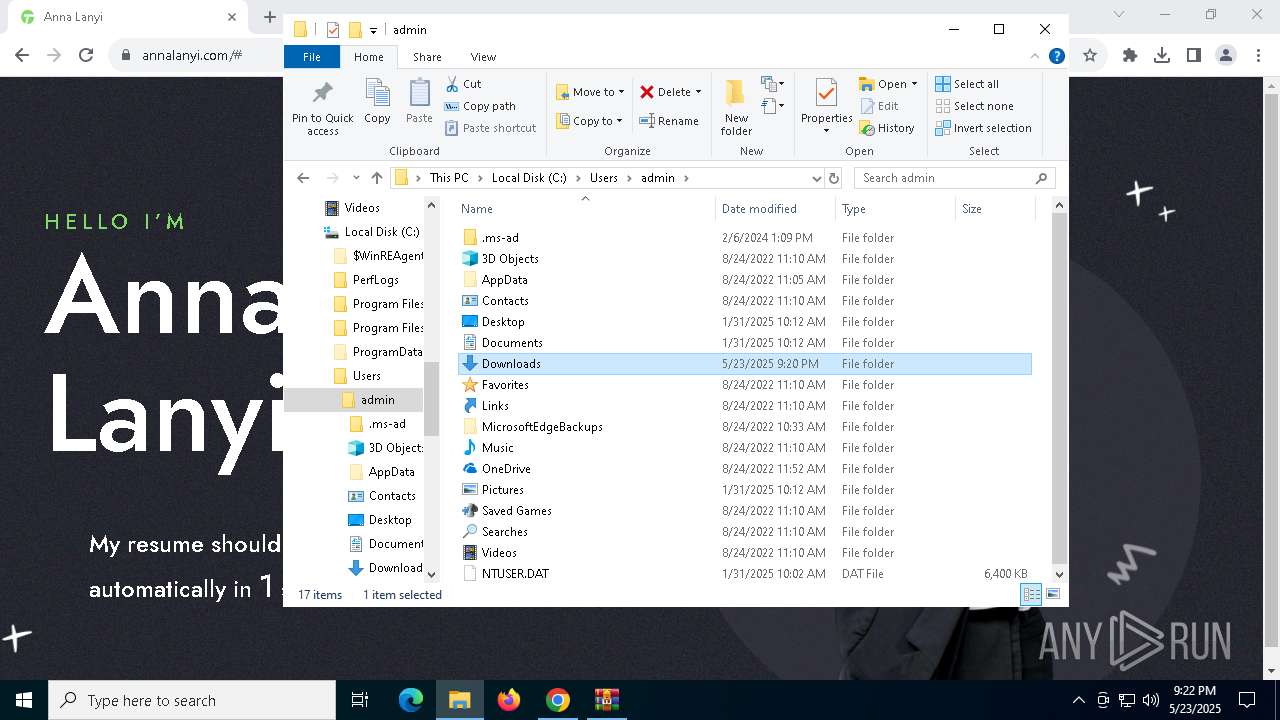
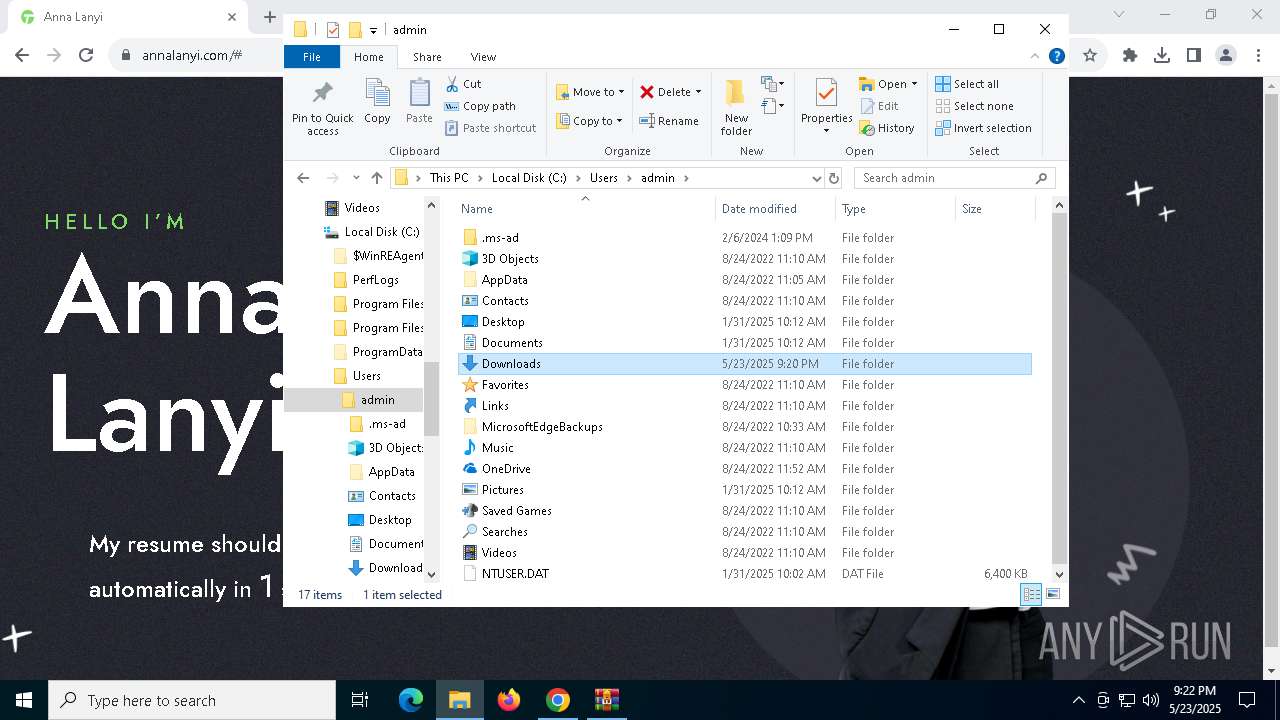
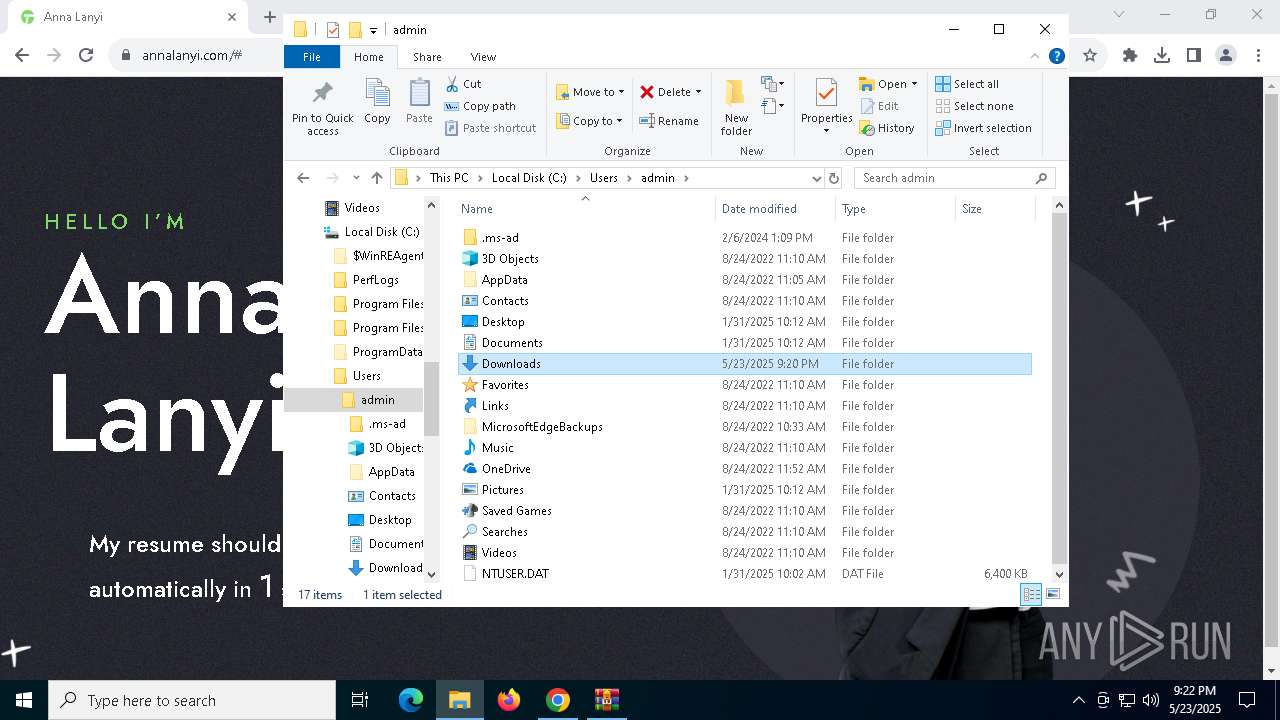
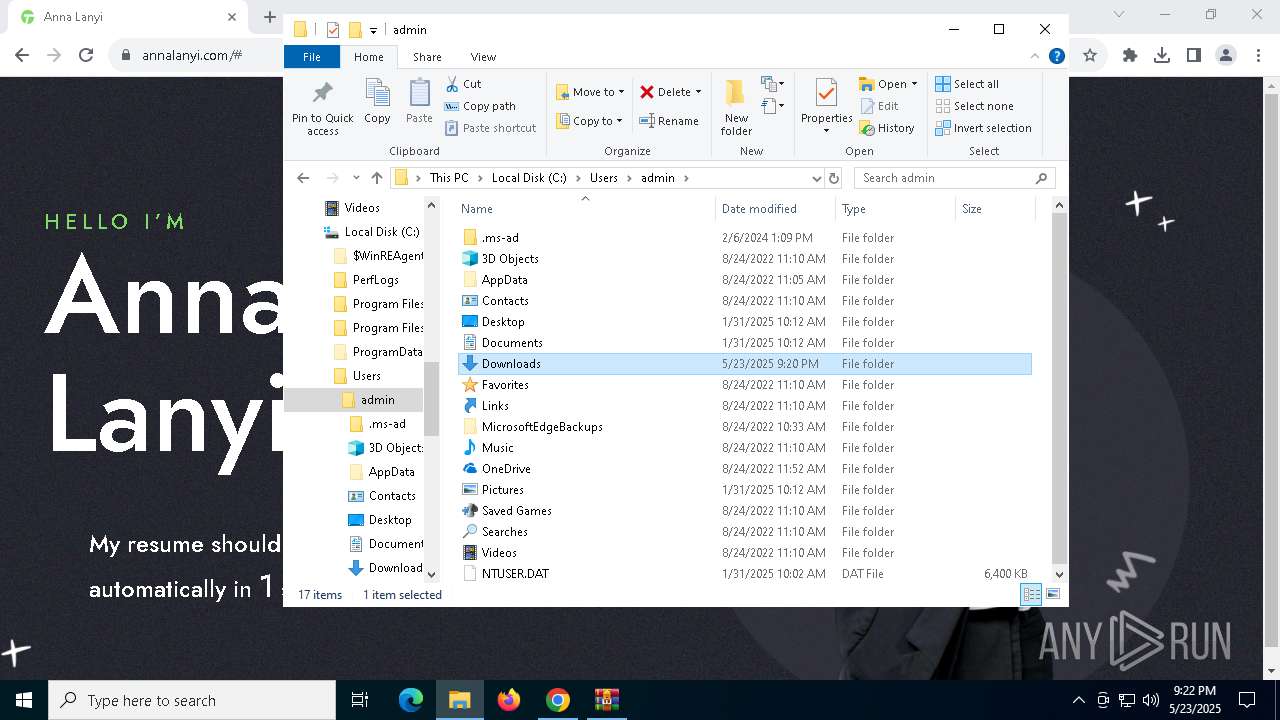
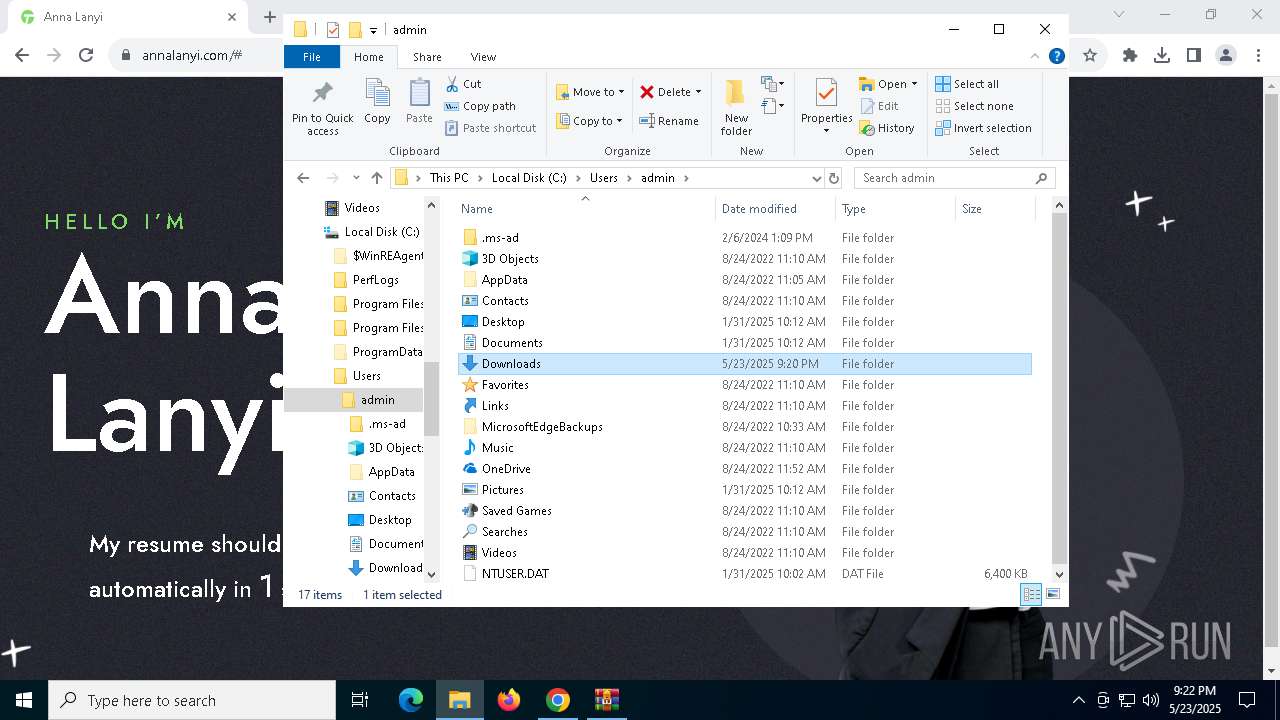
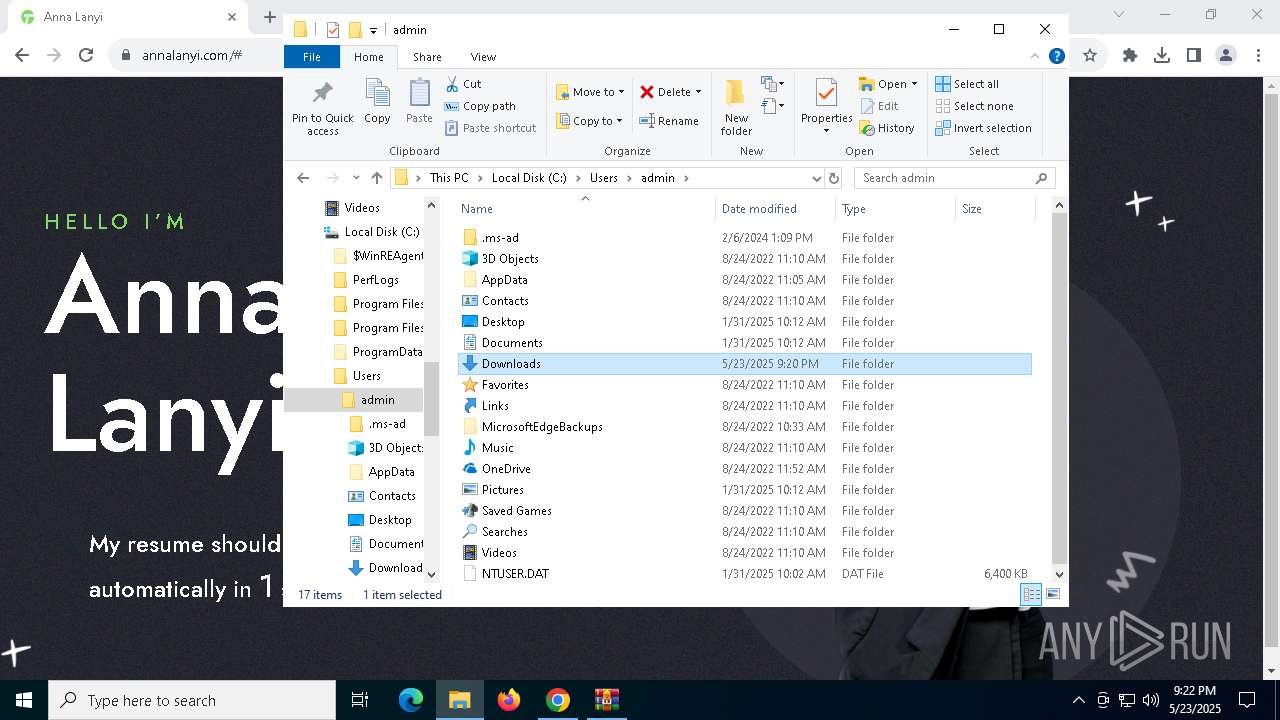
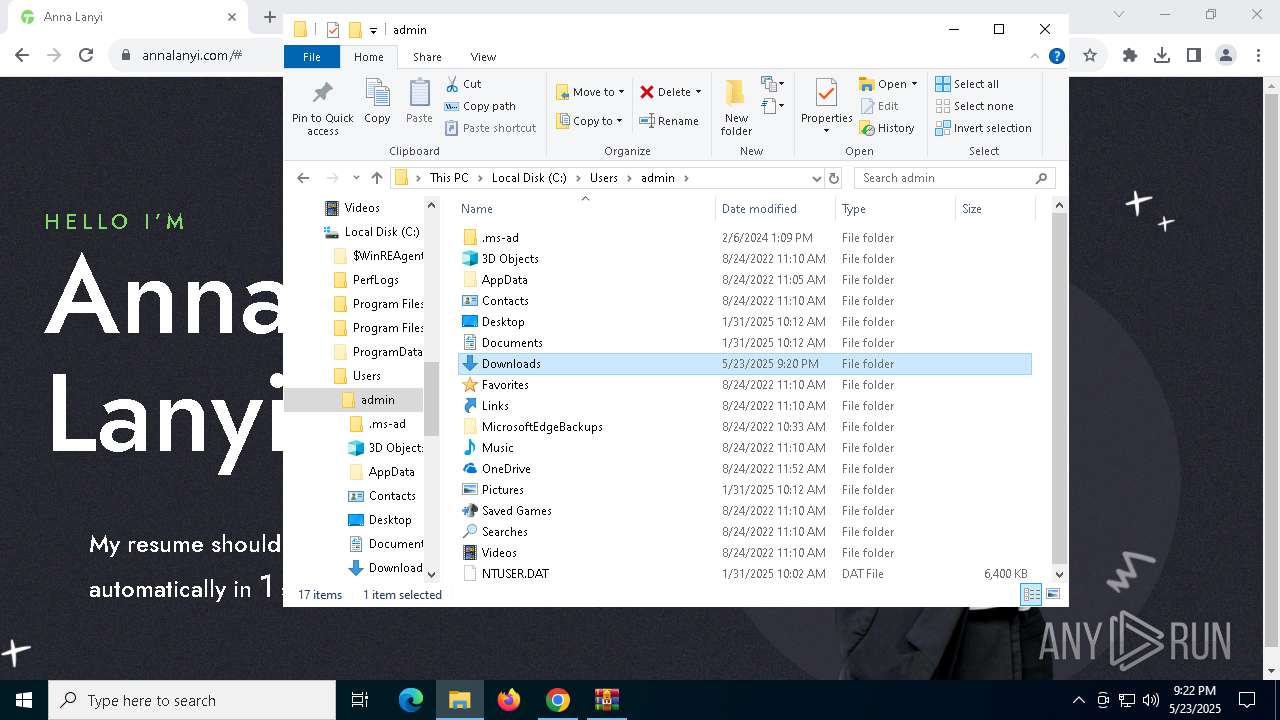
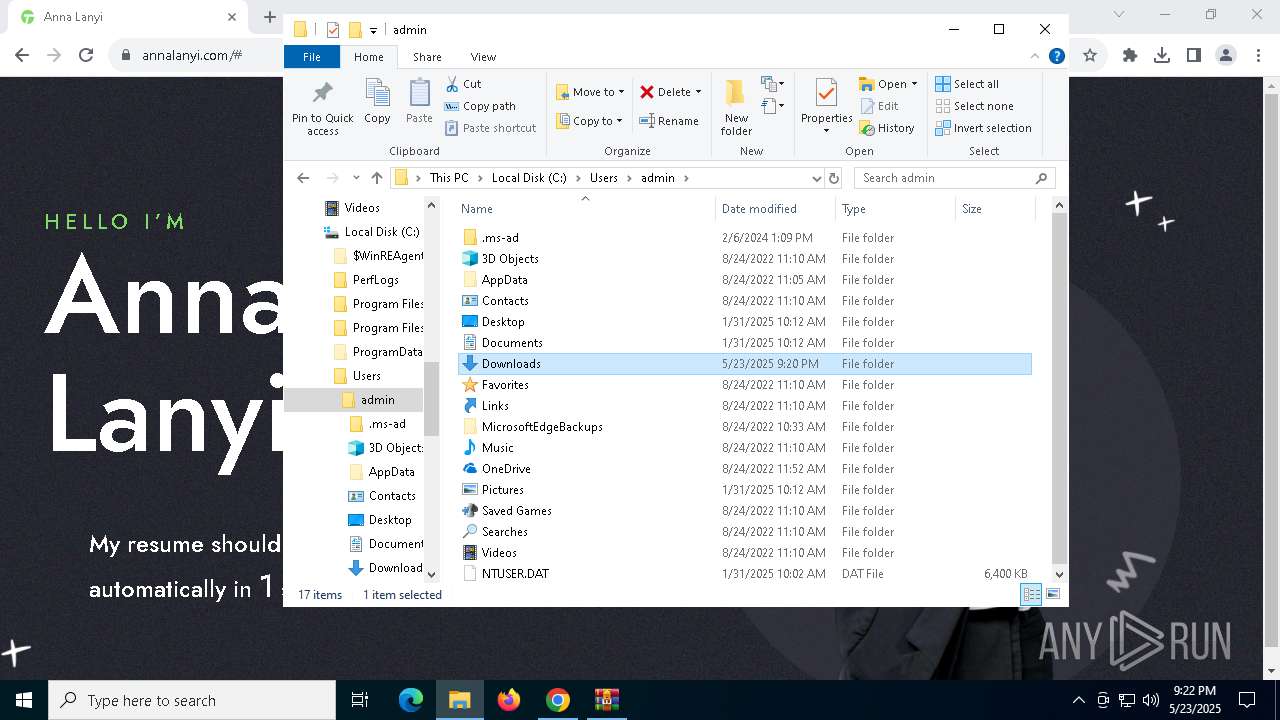
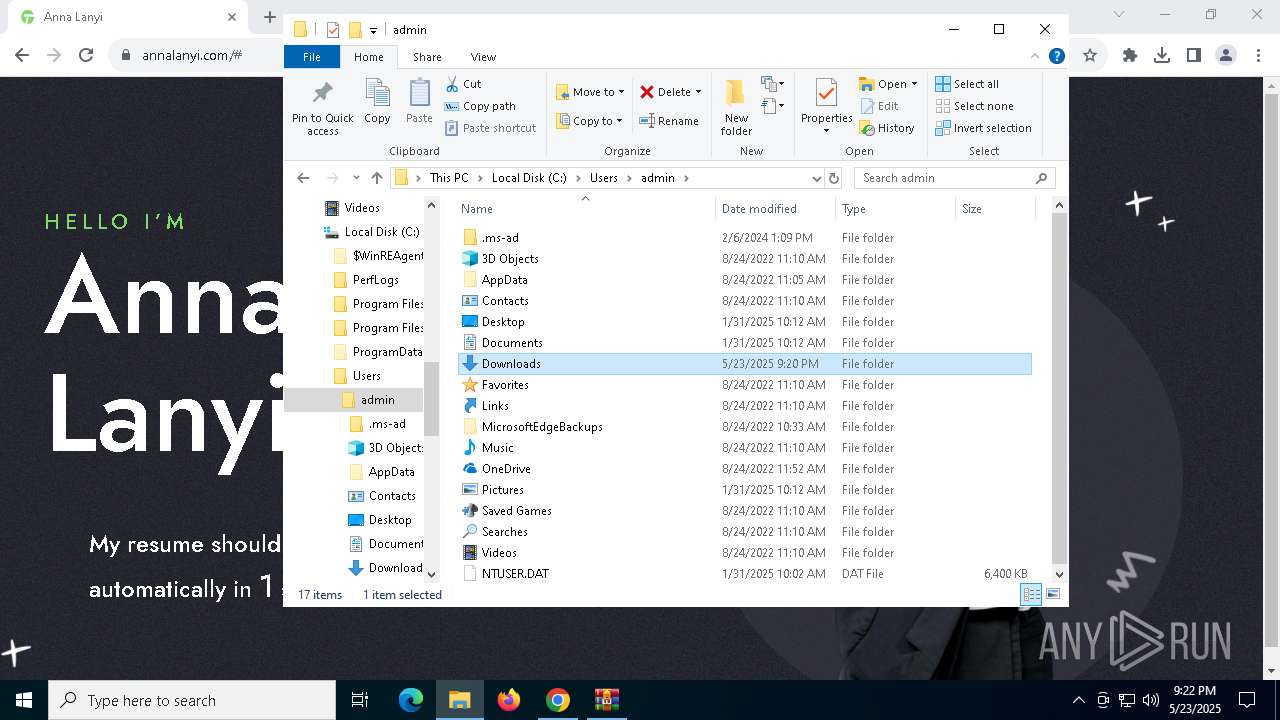
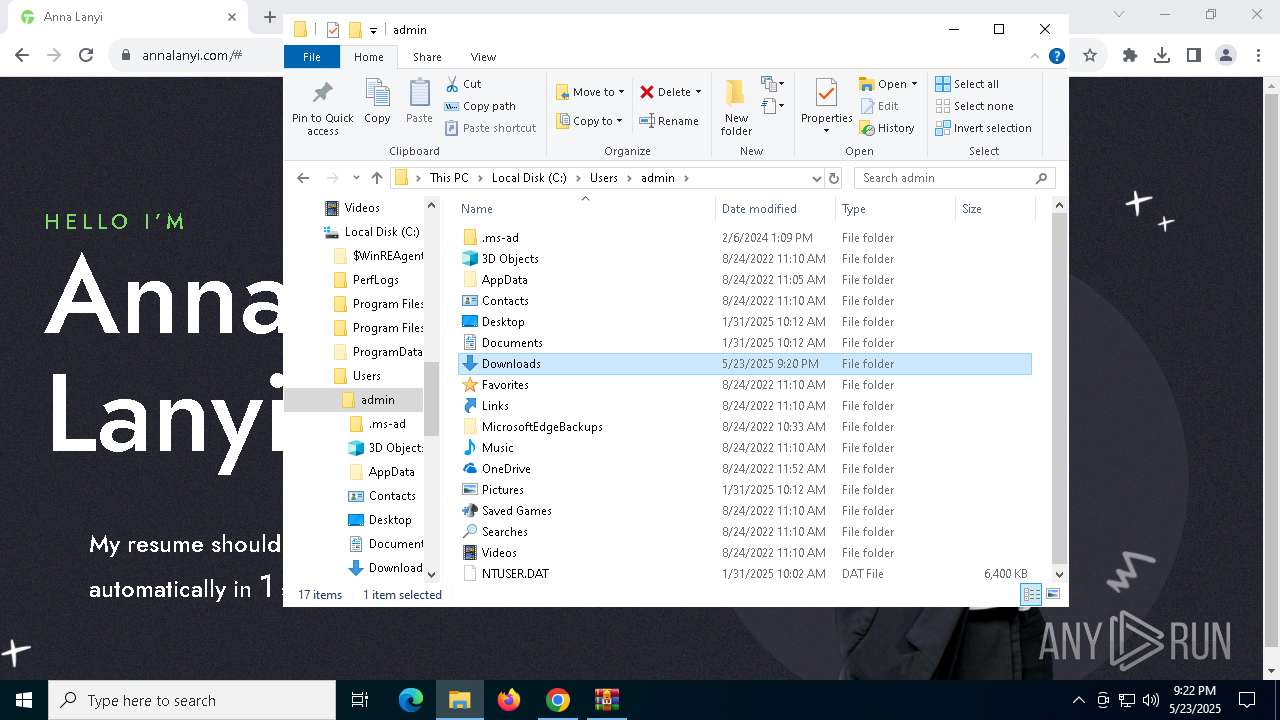
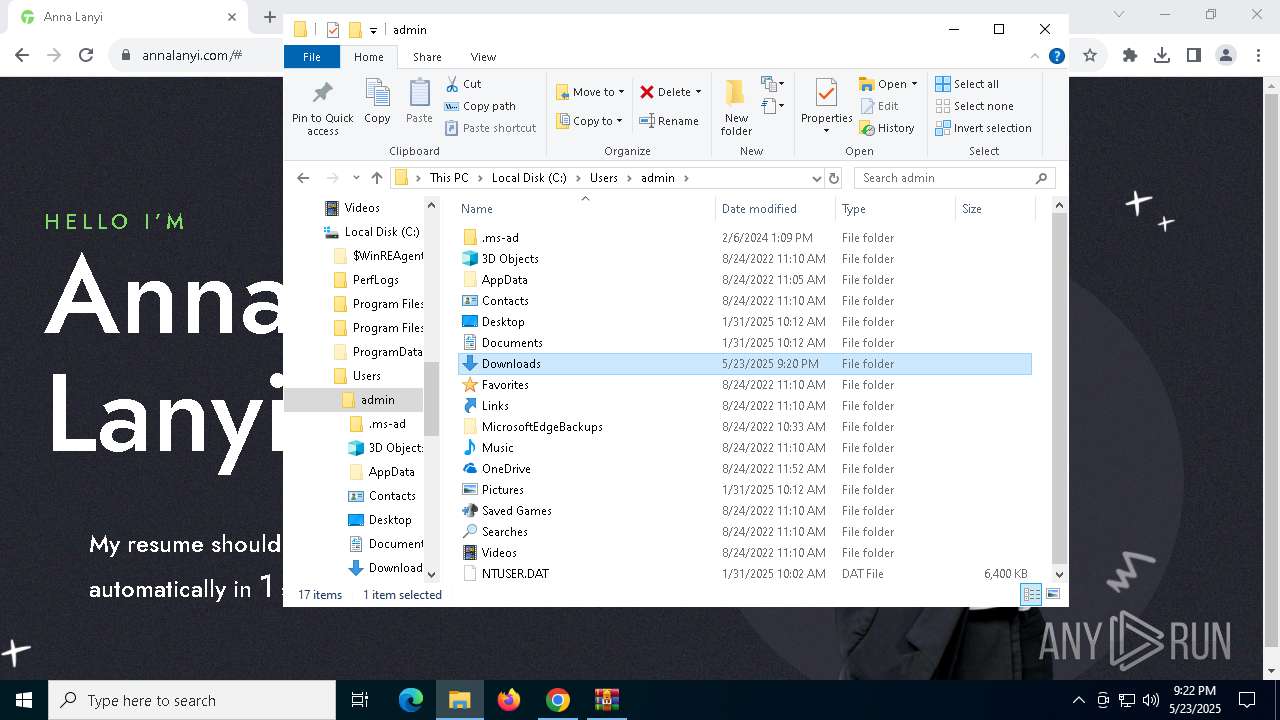
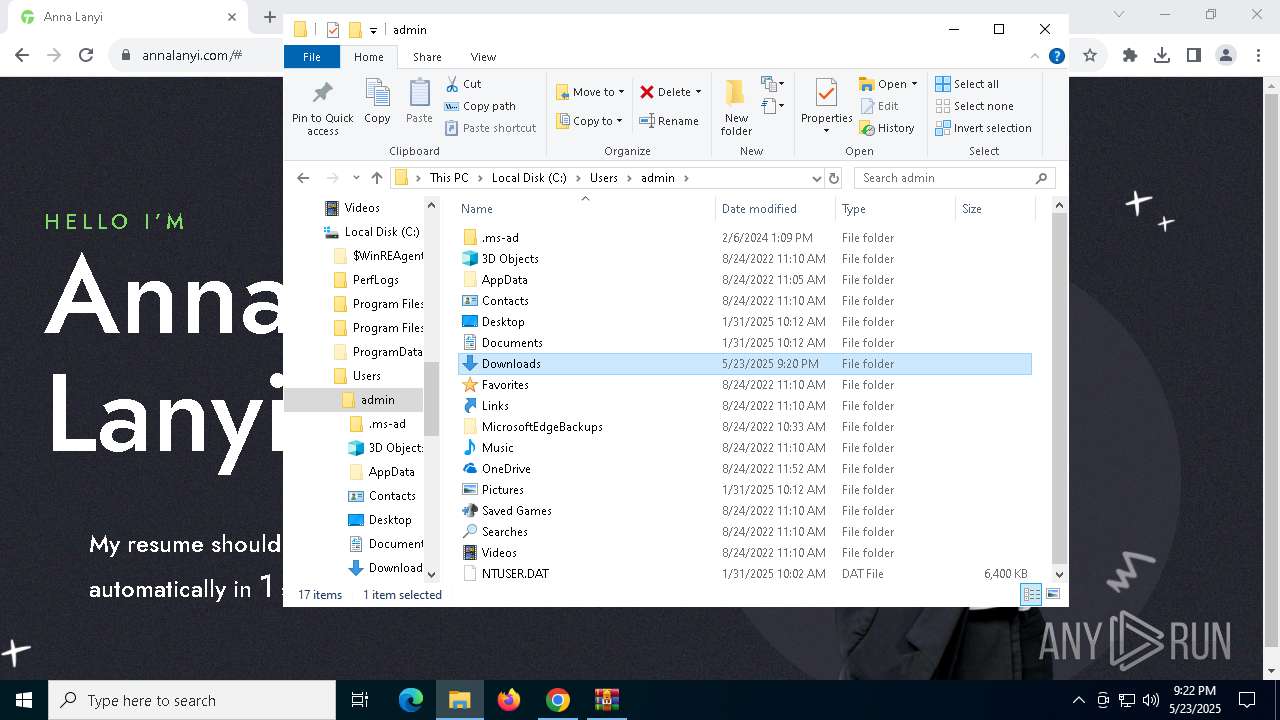
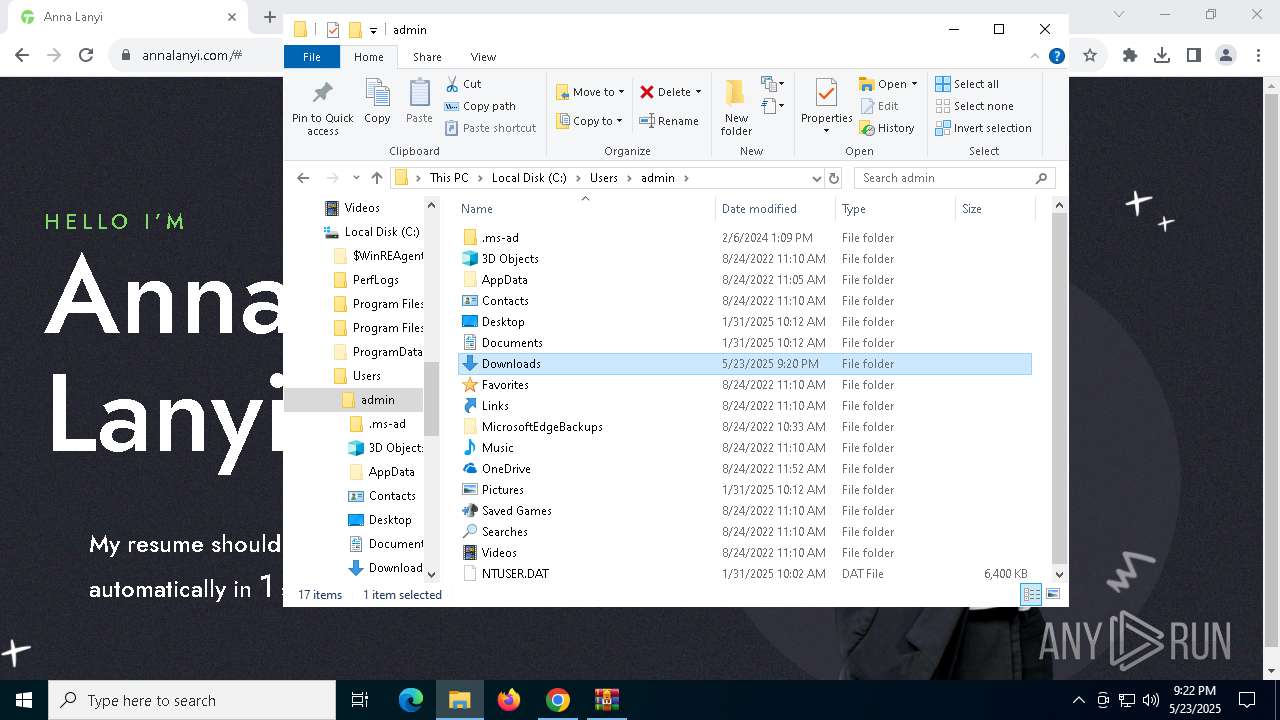
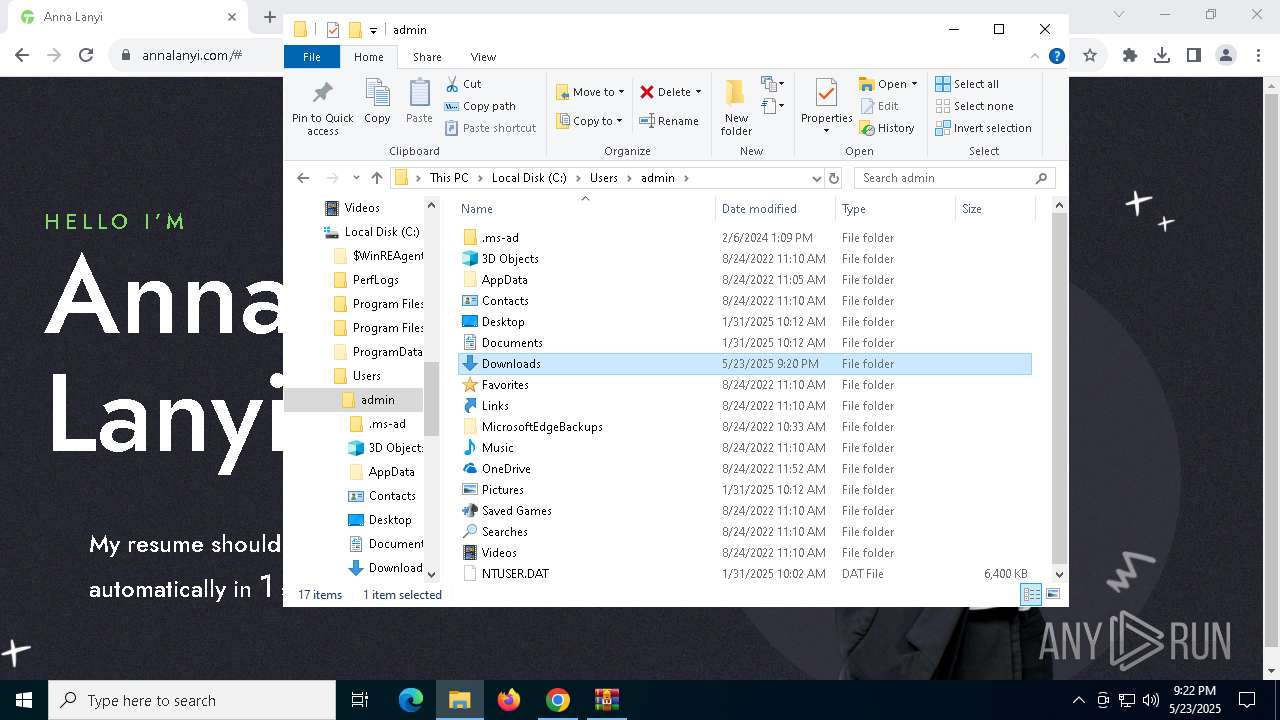
Manual execution by a user
- notepad++.exe (PID: 2088)
- WinRAR.exe (PID: 684)
- cmd.exe (PID: 6940)
Reads the software policy settings
- slui.exe (PID: 7792)
Reads the machine GUID from the registry
- ie4uinit.exe (PID: 5236)
Executable content was dropped or overwritten
- chrome.exe (PID: 7968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
282
Monitored processes
123
Malicious processes
29
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5228 -s 2440 | C:\Windows\SysWOW64\WerFault.exe | — | msxsl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe 550BA14D9.txt 550BA14D9.txt | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: msxsl Exit code: 3221225477 Version: 1.1.0.1 Modules
| |||||||||||||||
| 240 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 8100 -s 2444 | C:\Windows\SysWOW64\WerFault.exe | — | msxsl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe 550BA14D9.txt 550BA14D9.txt | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: msxsl Exit code: 3221225477 Version: 1.1.0.1 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | msxsl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5236 -s 2412 | C:\Windows\SysWOW64\WerFault.exe | — | msxsl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
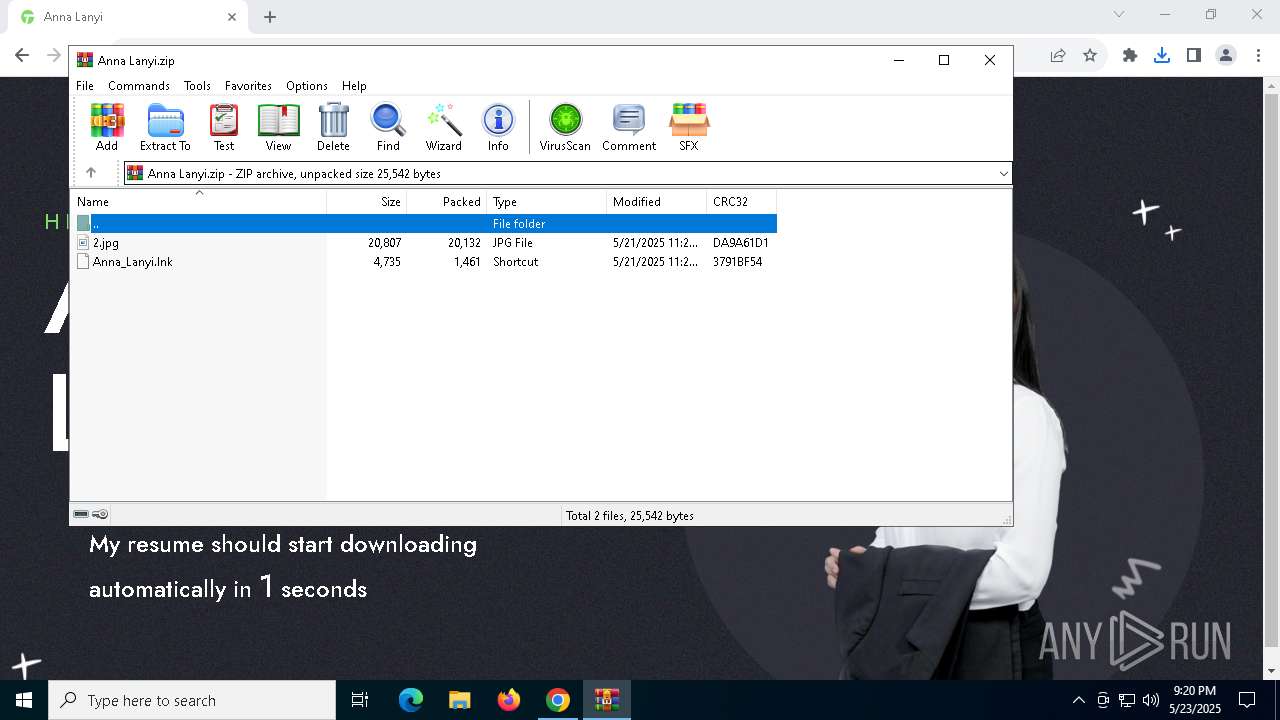
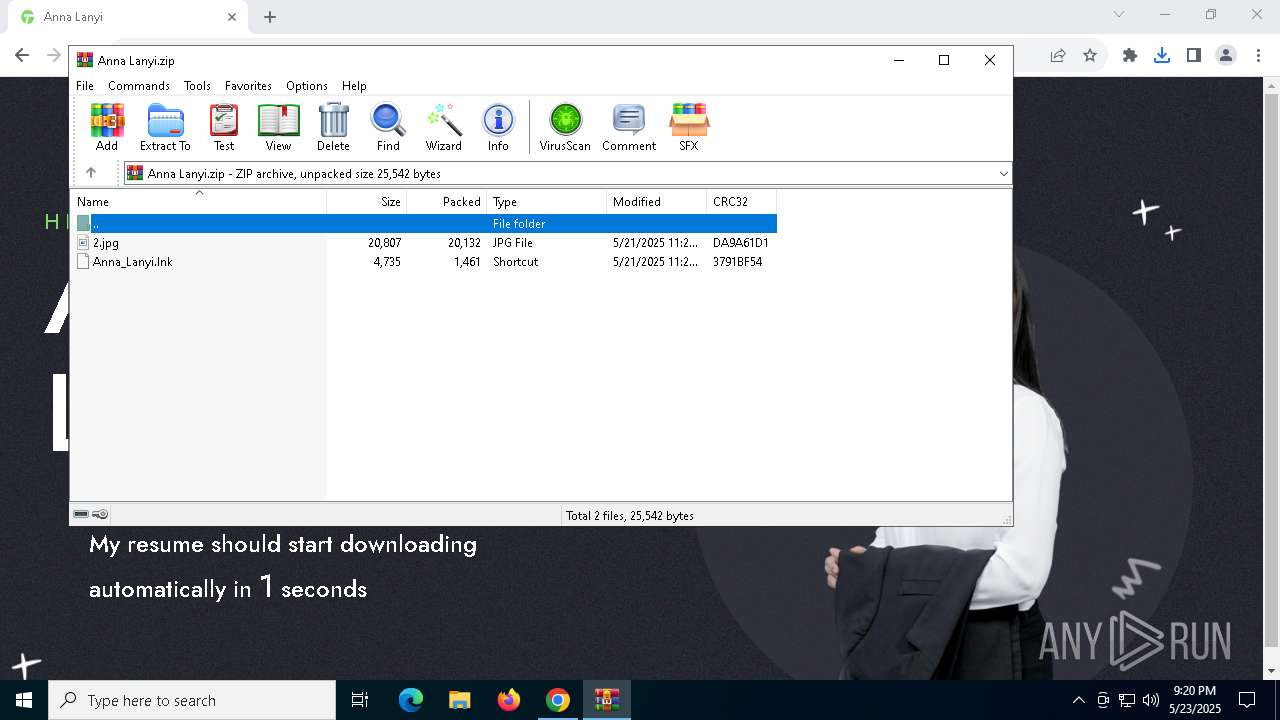
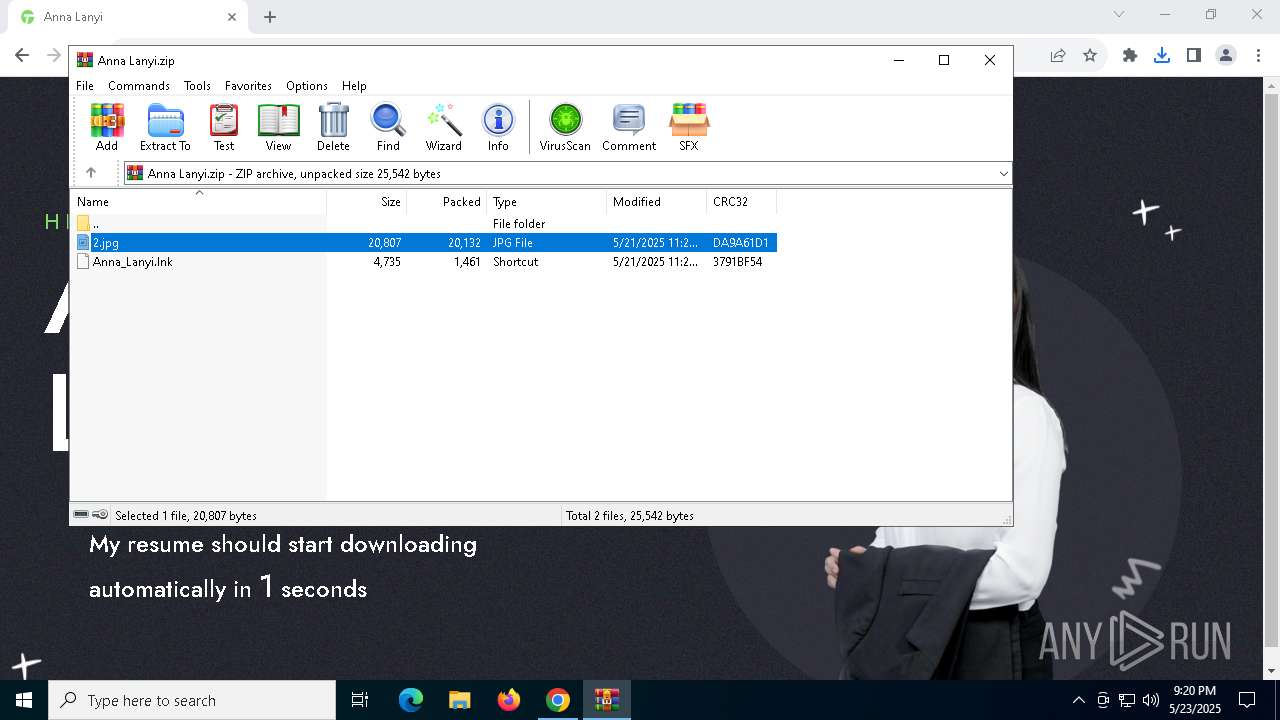
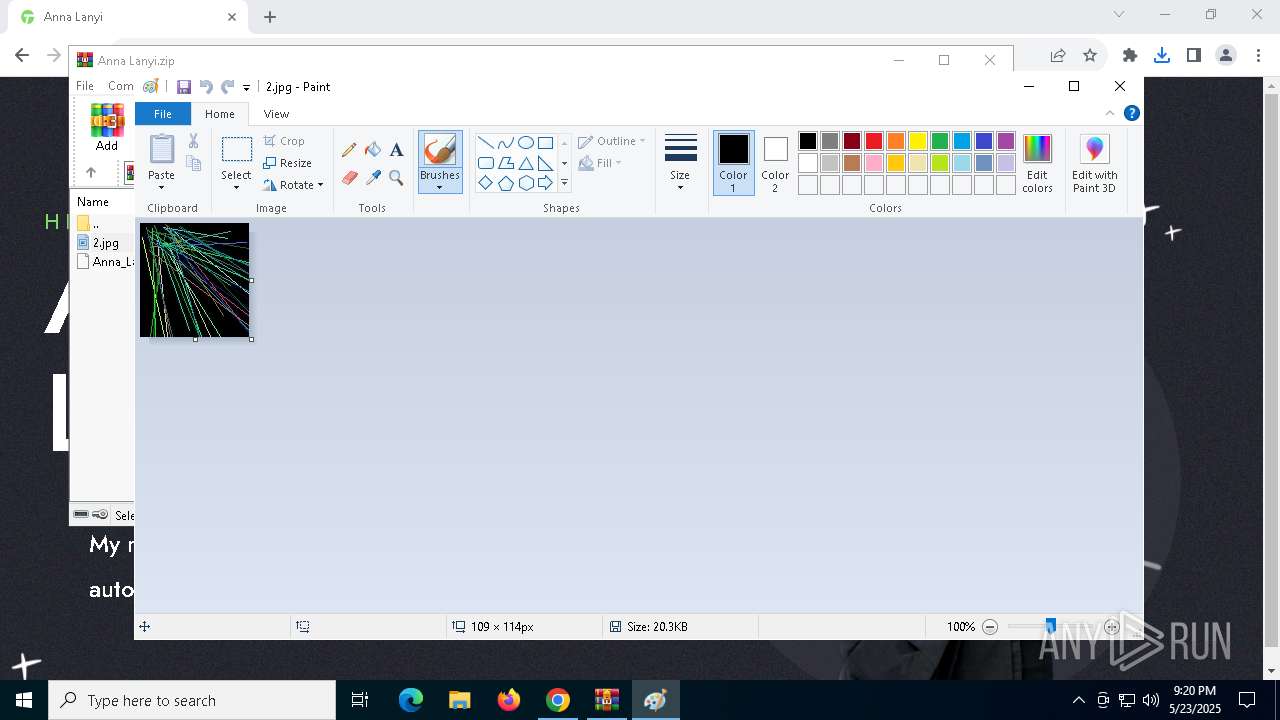
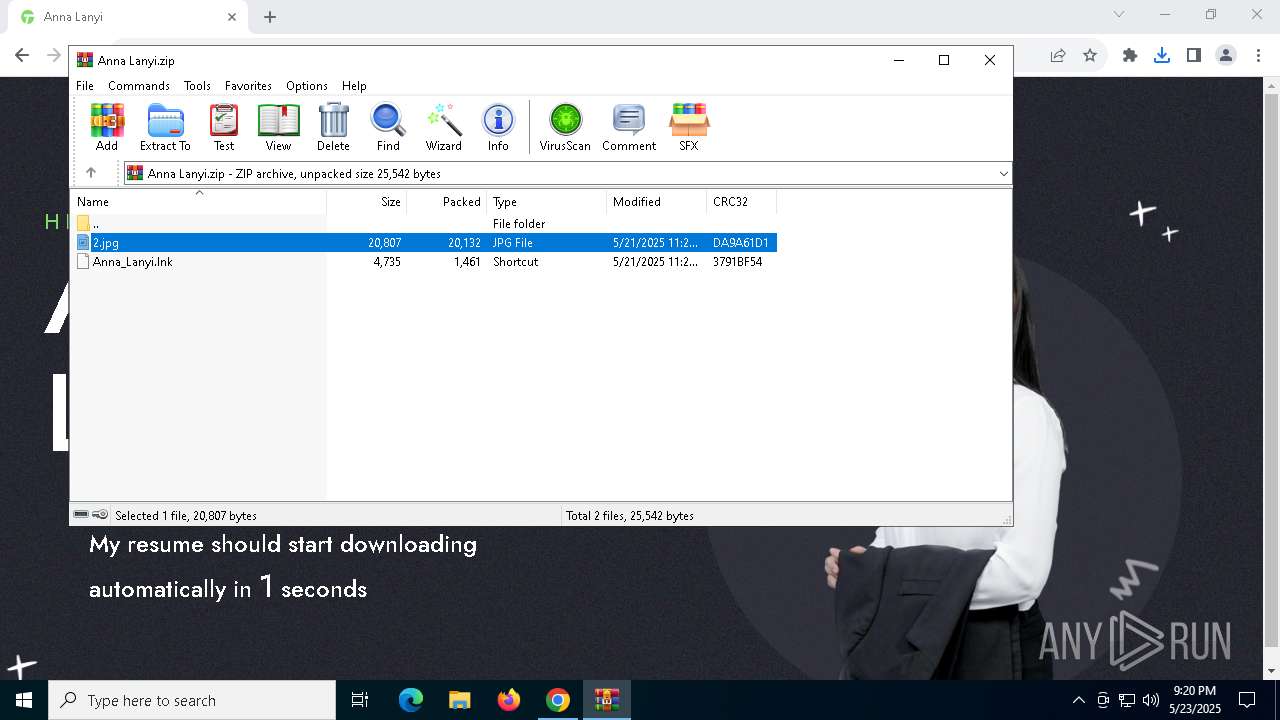
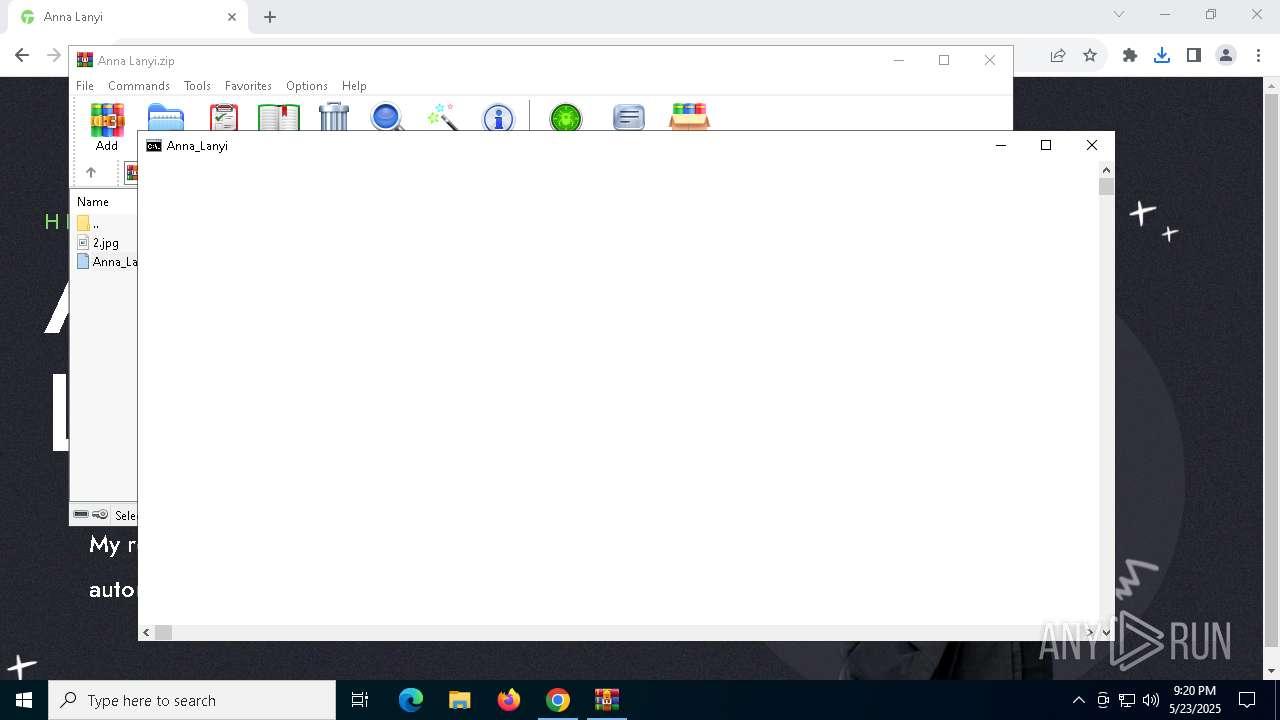
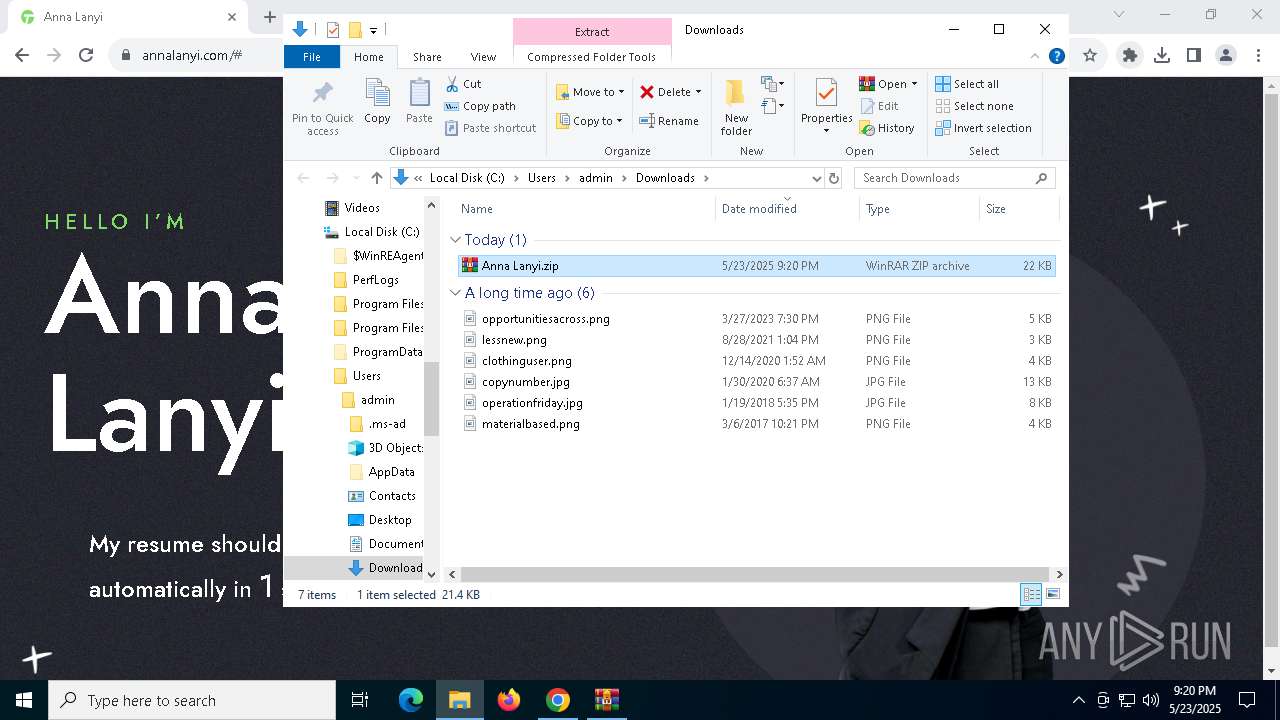
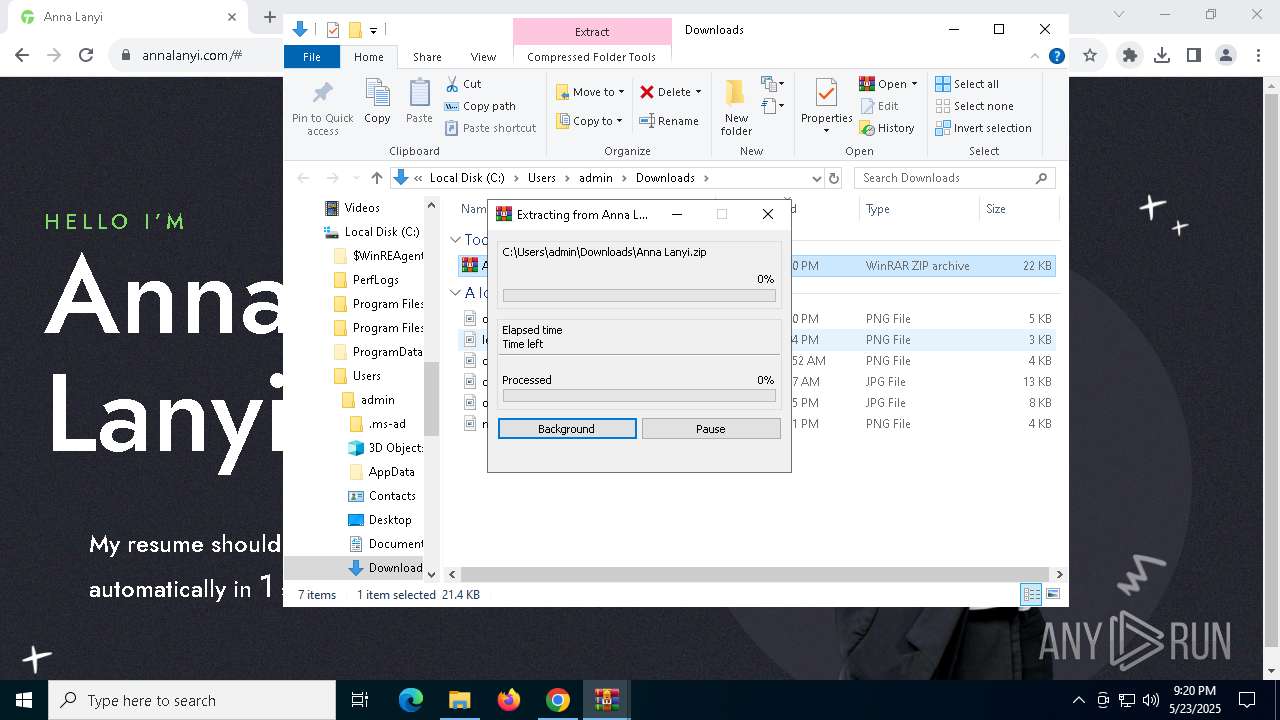
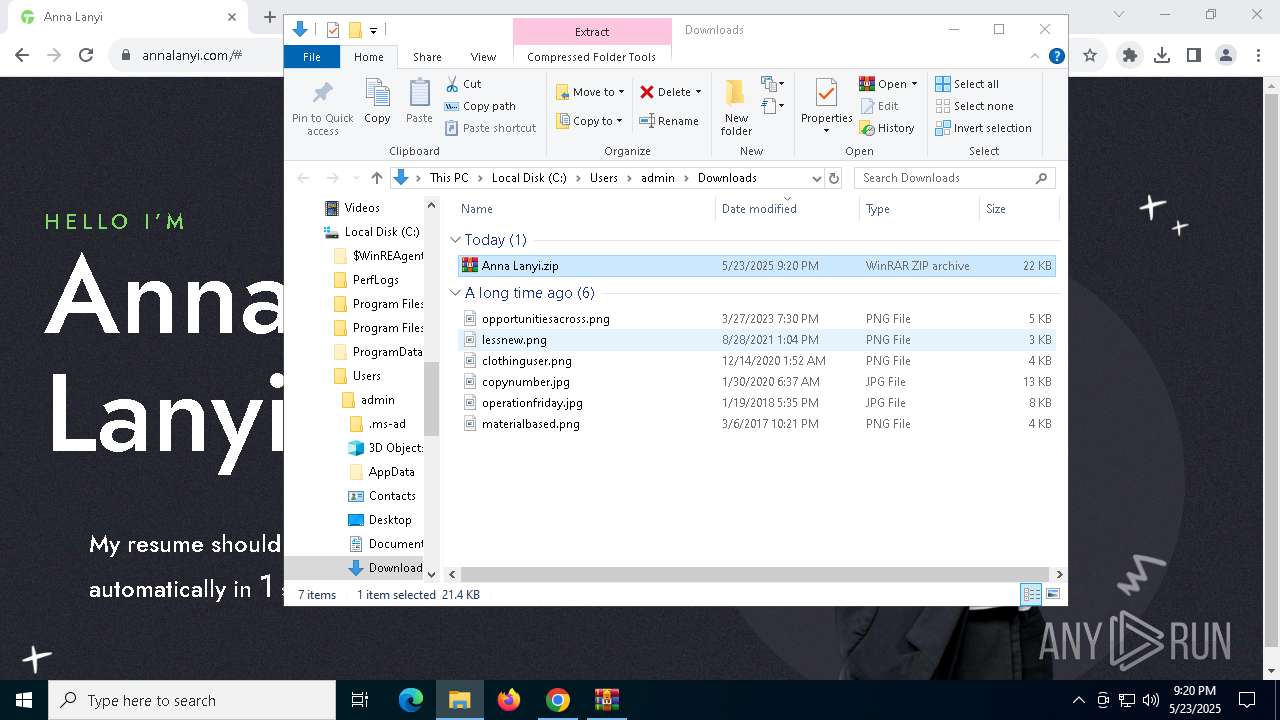
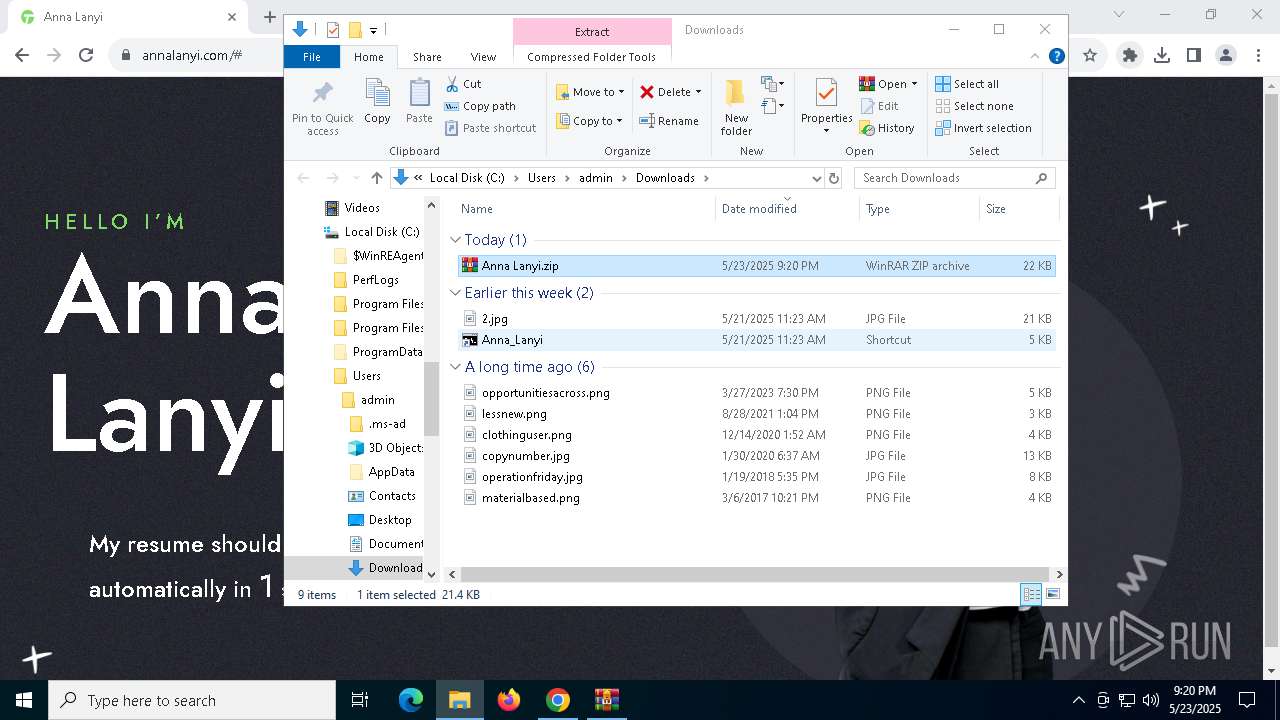
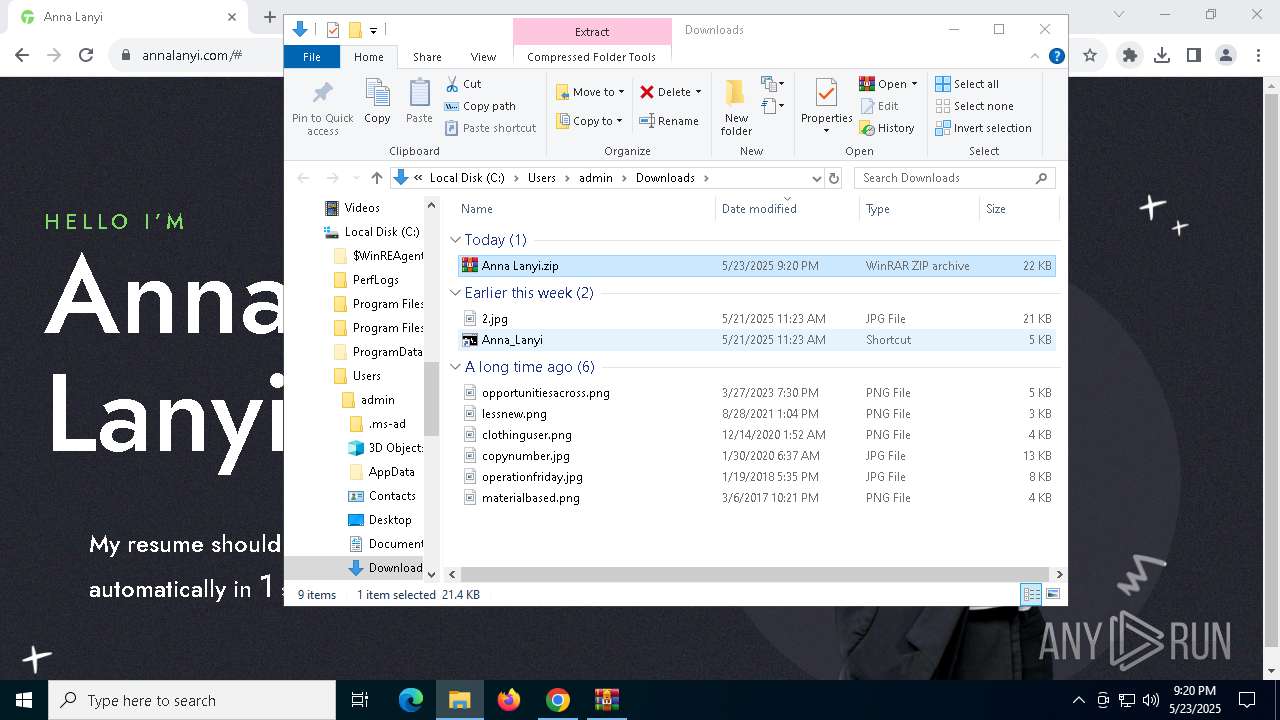
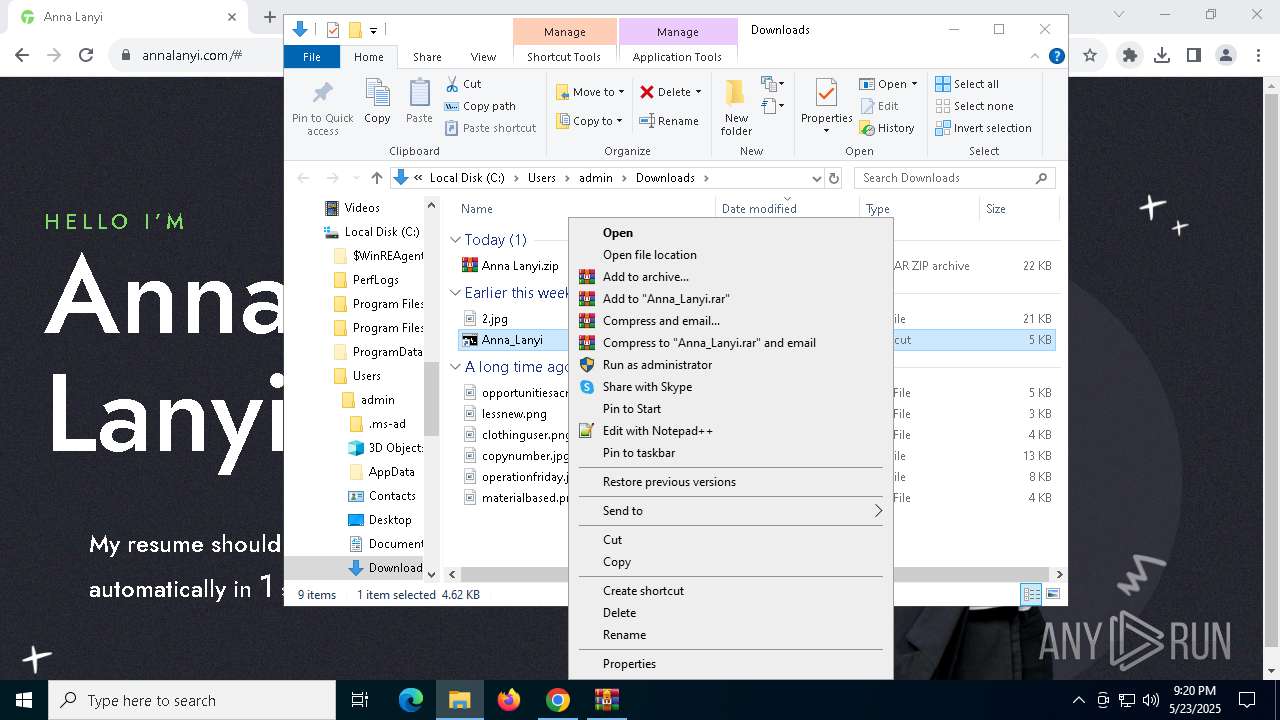
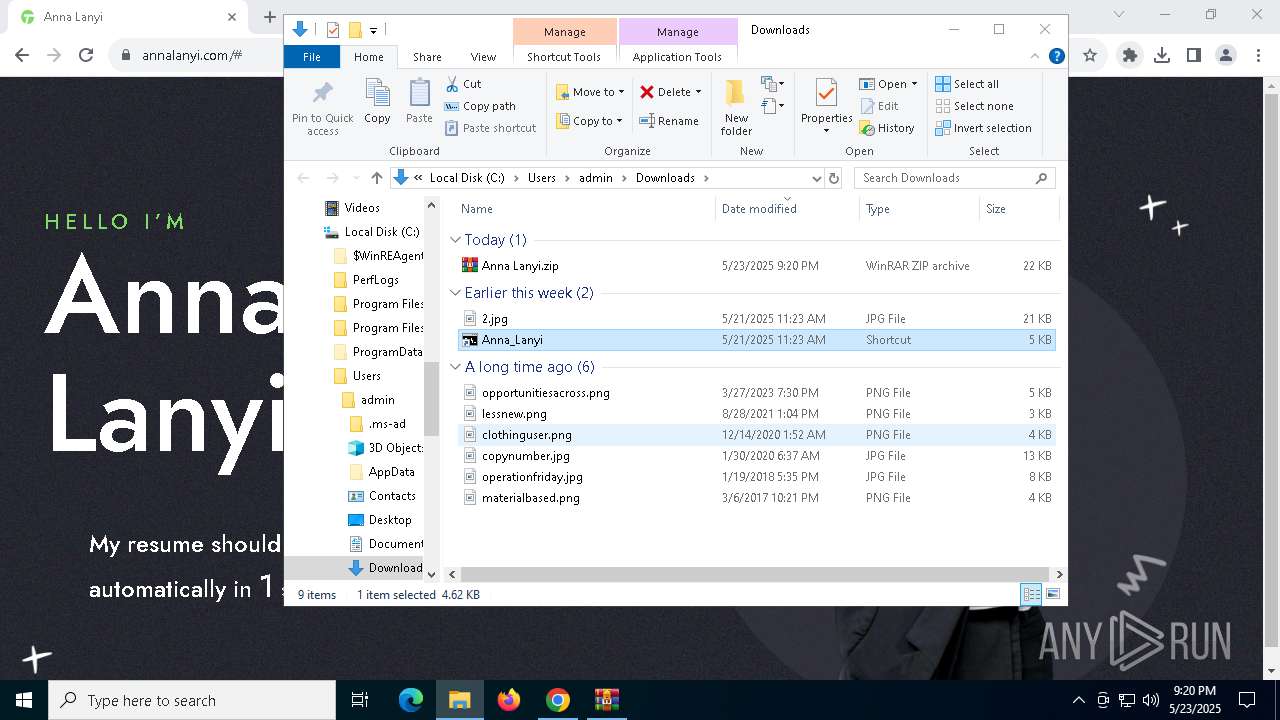
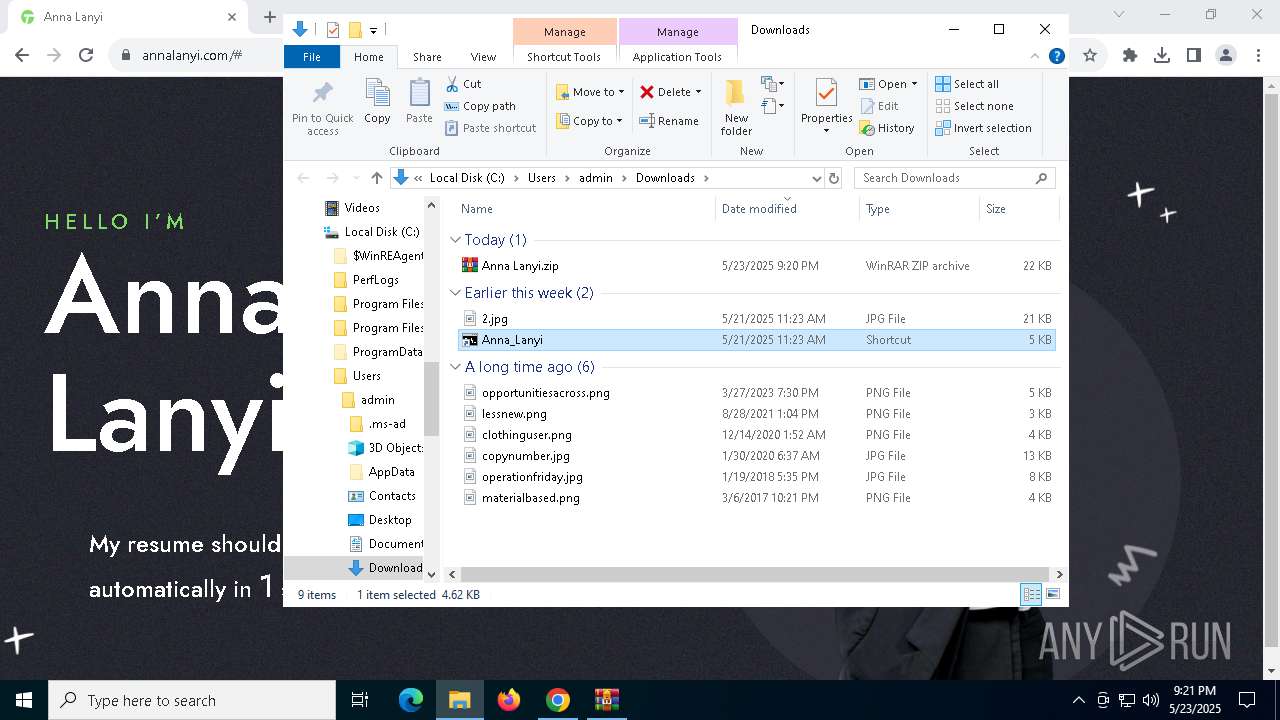
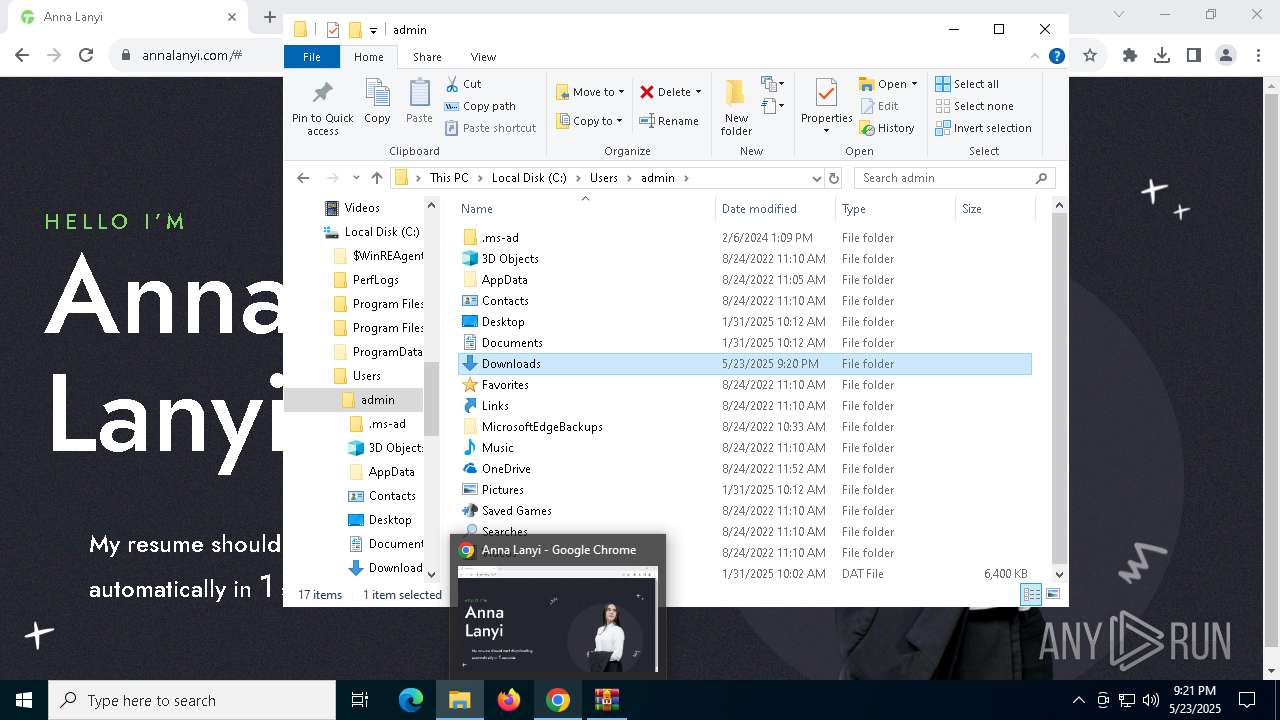
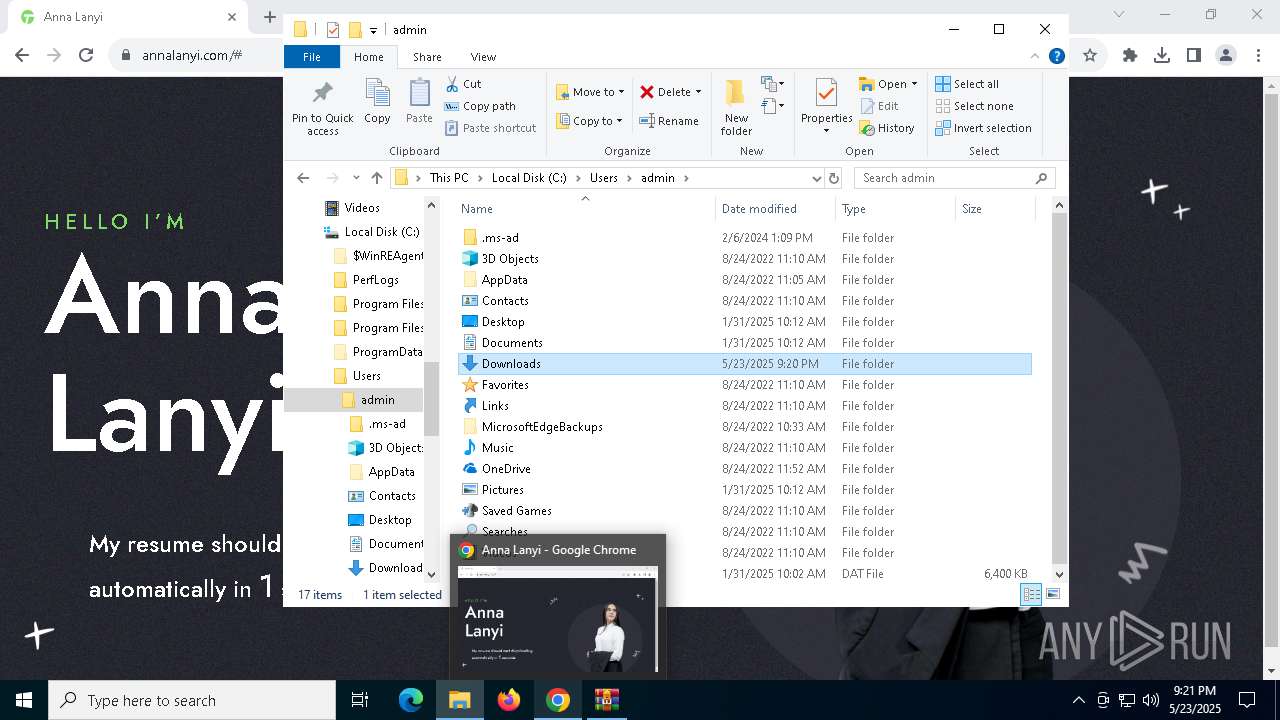
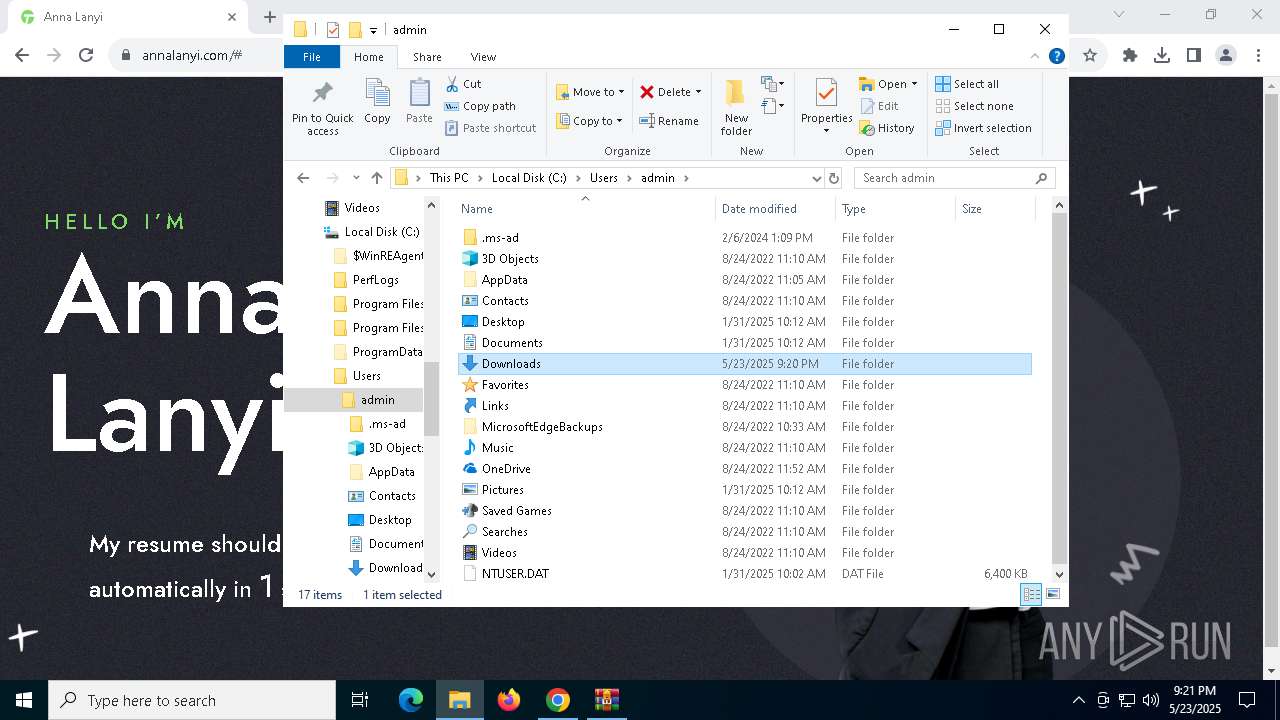
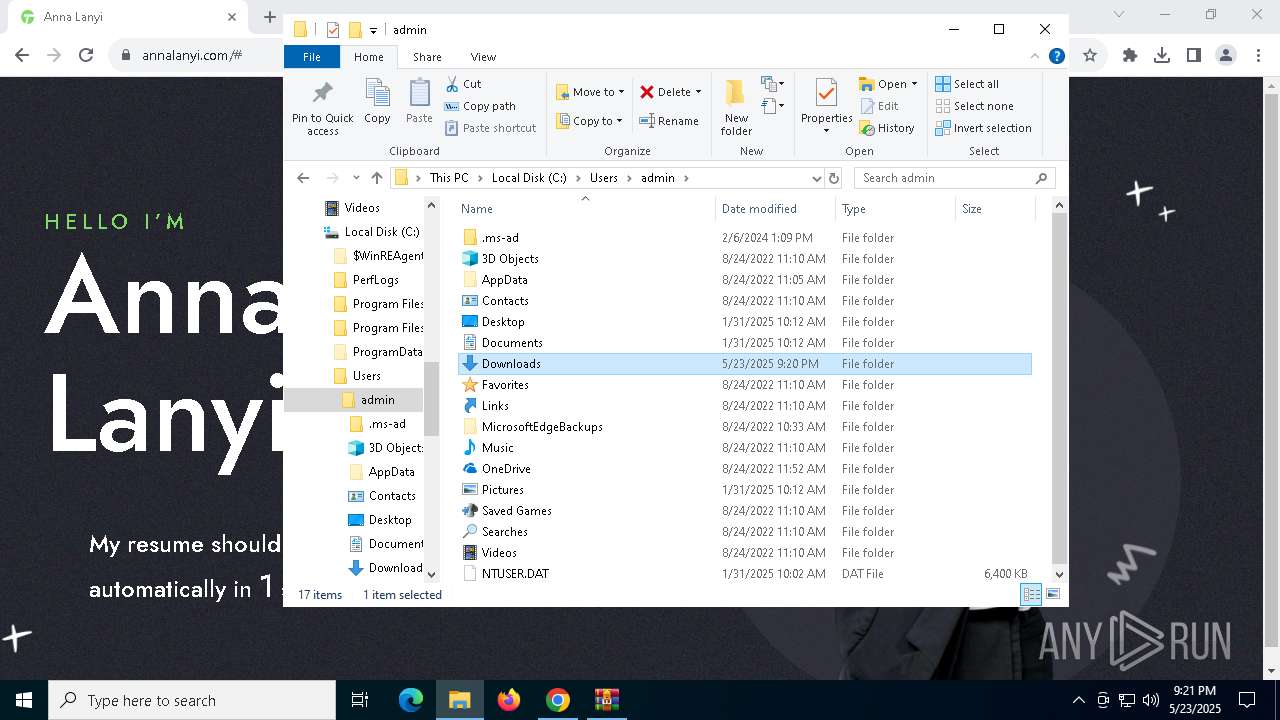
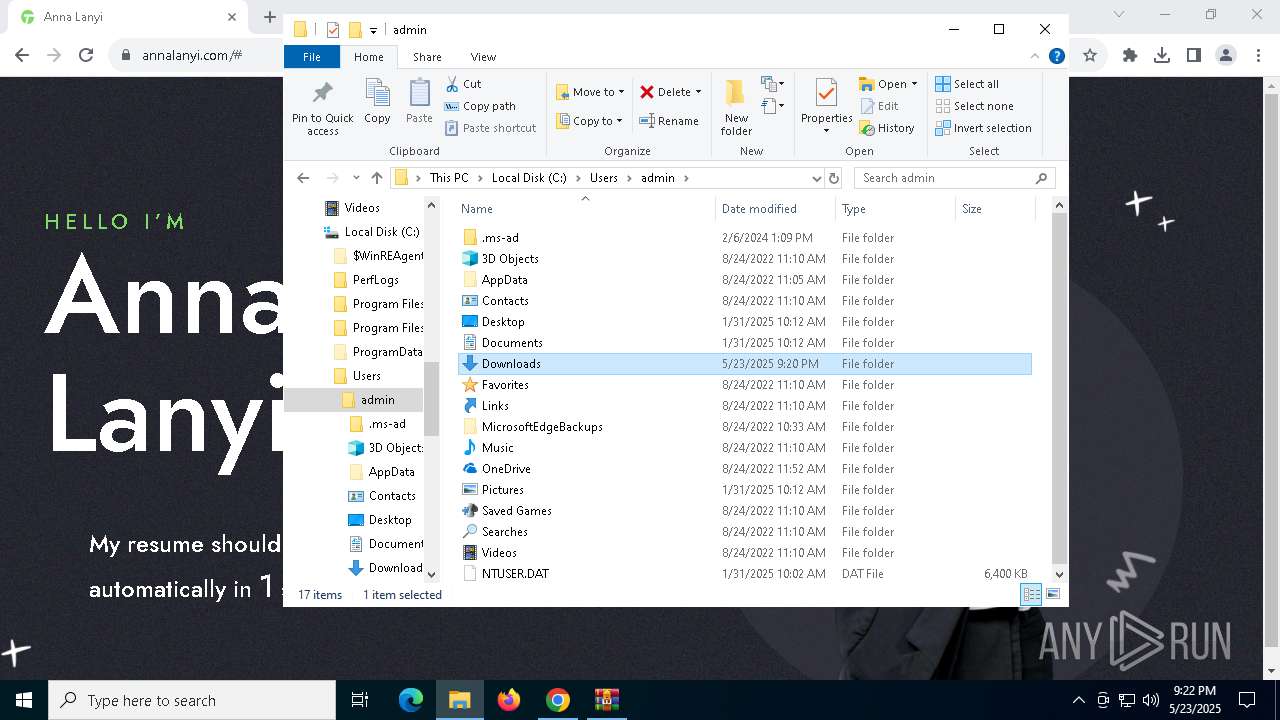
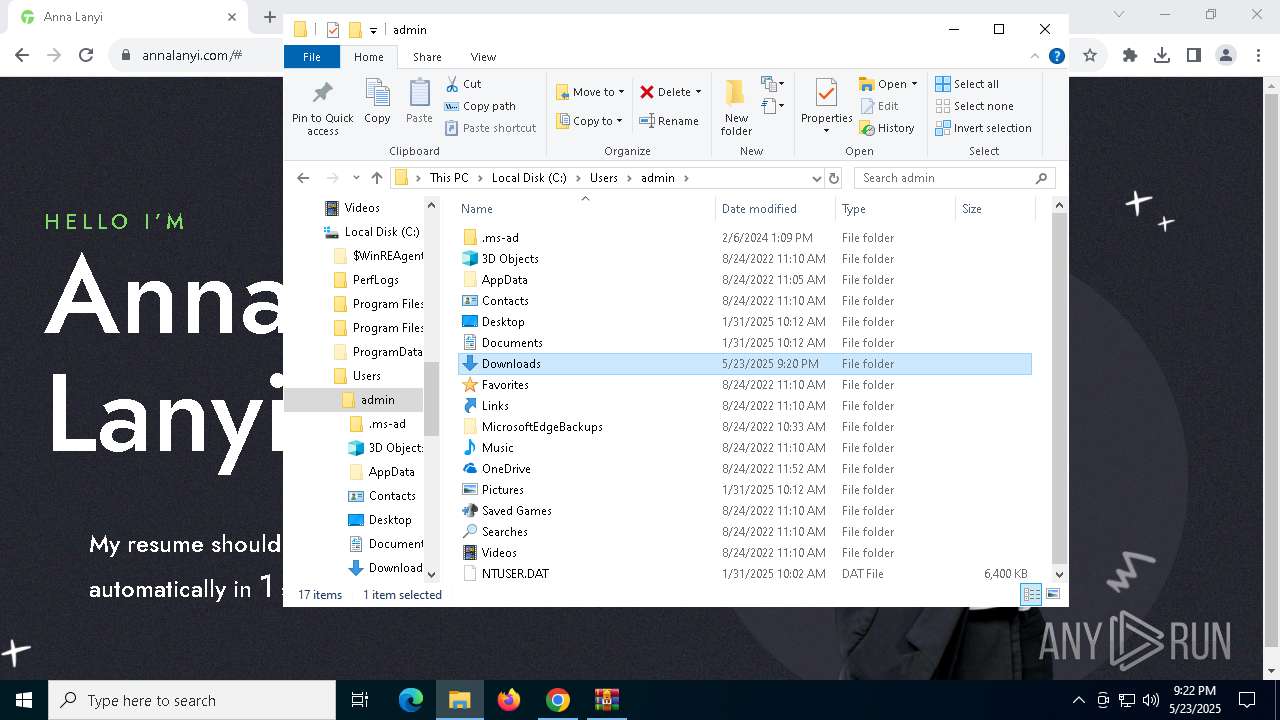
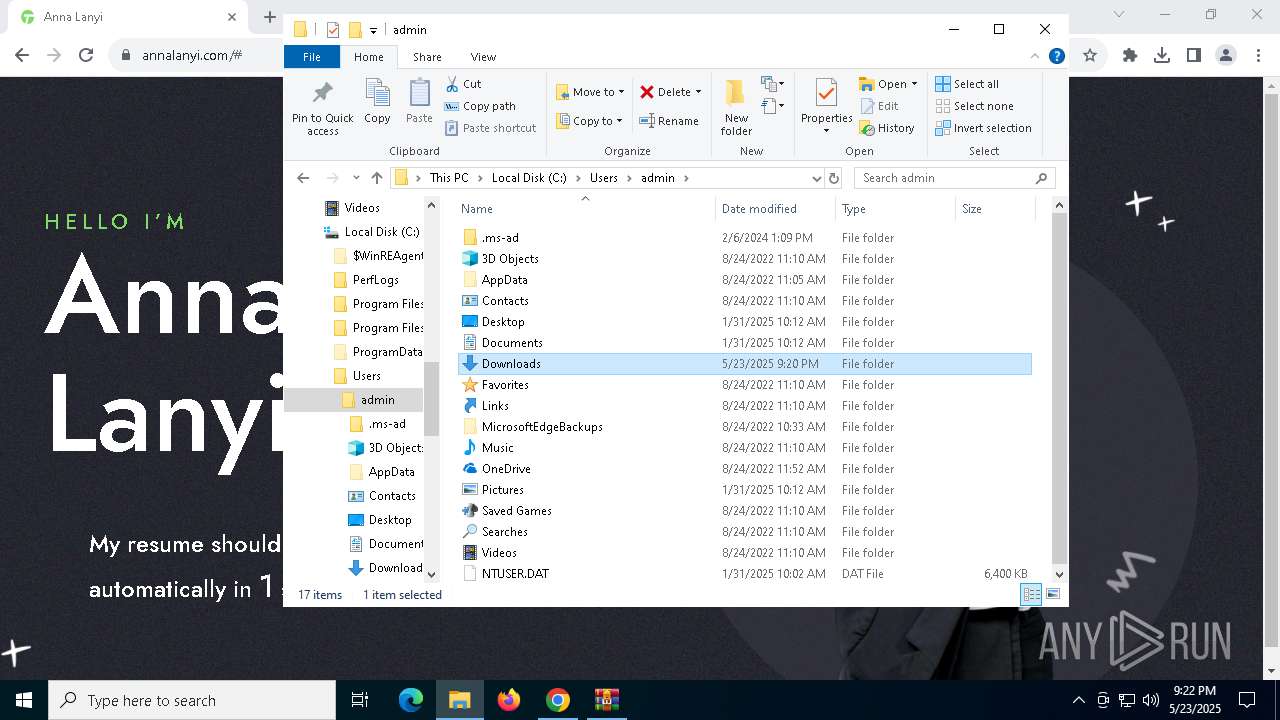
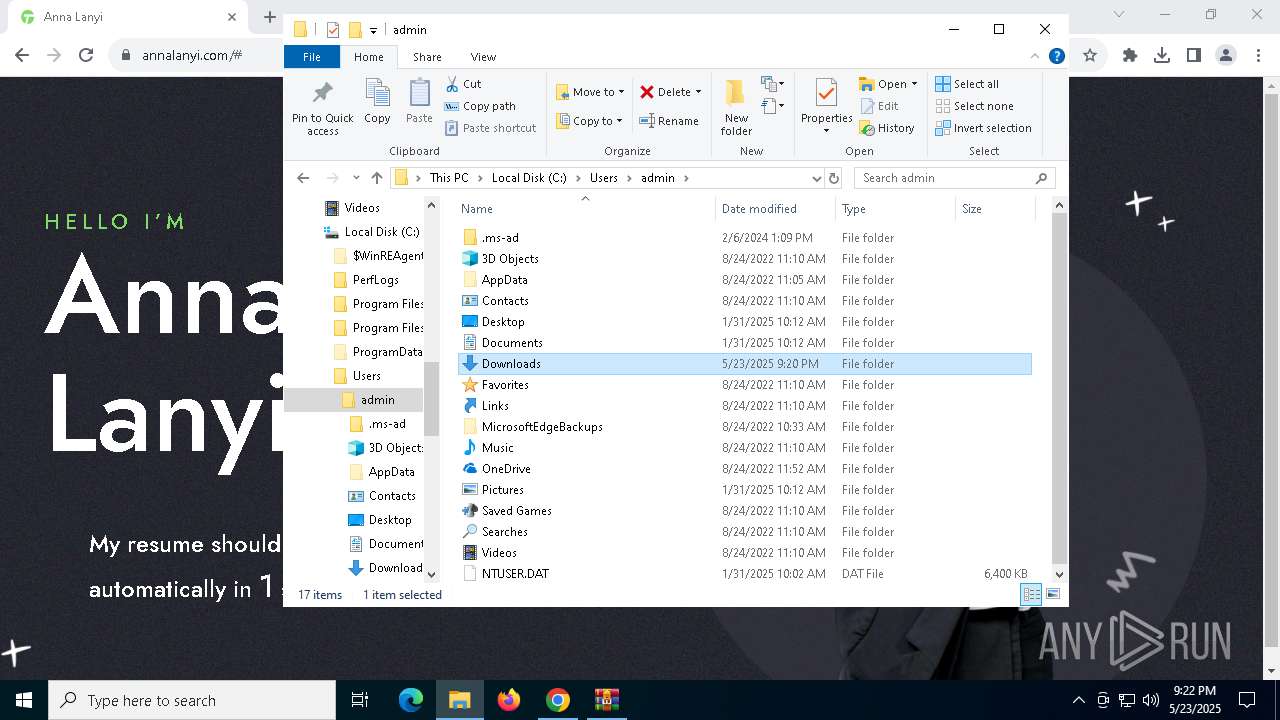
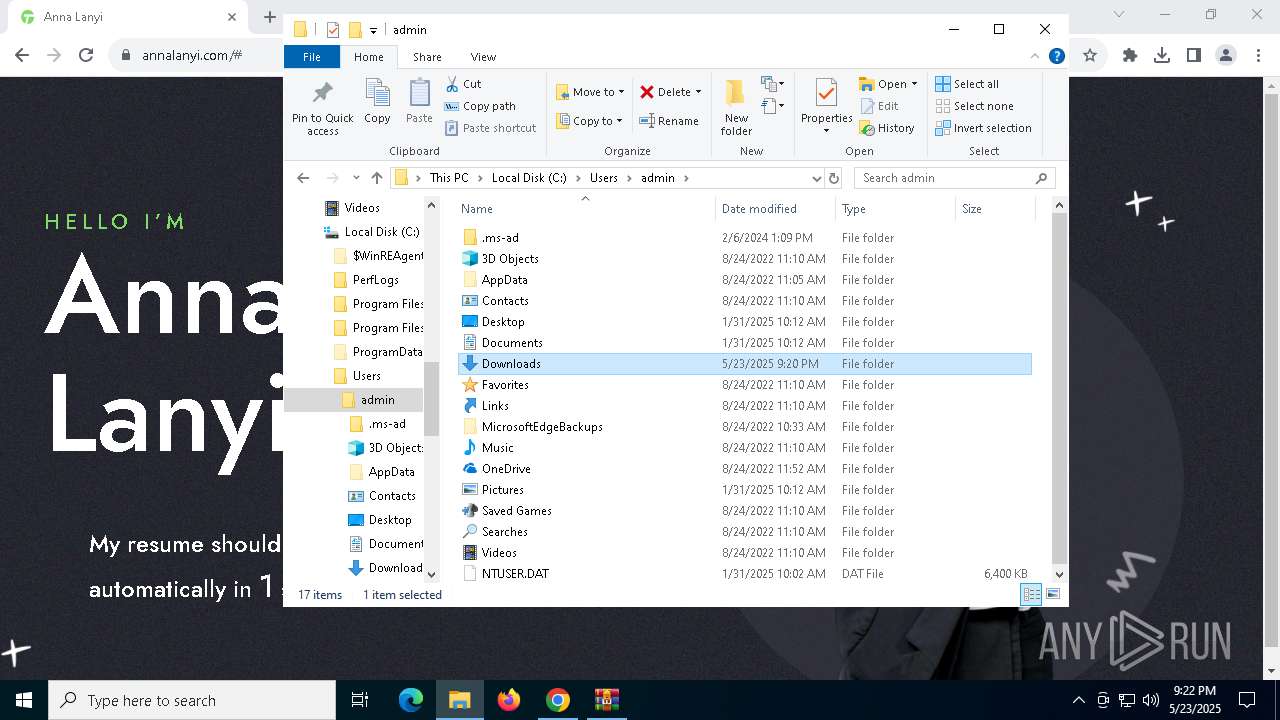
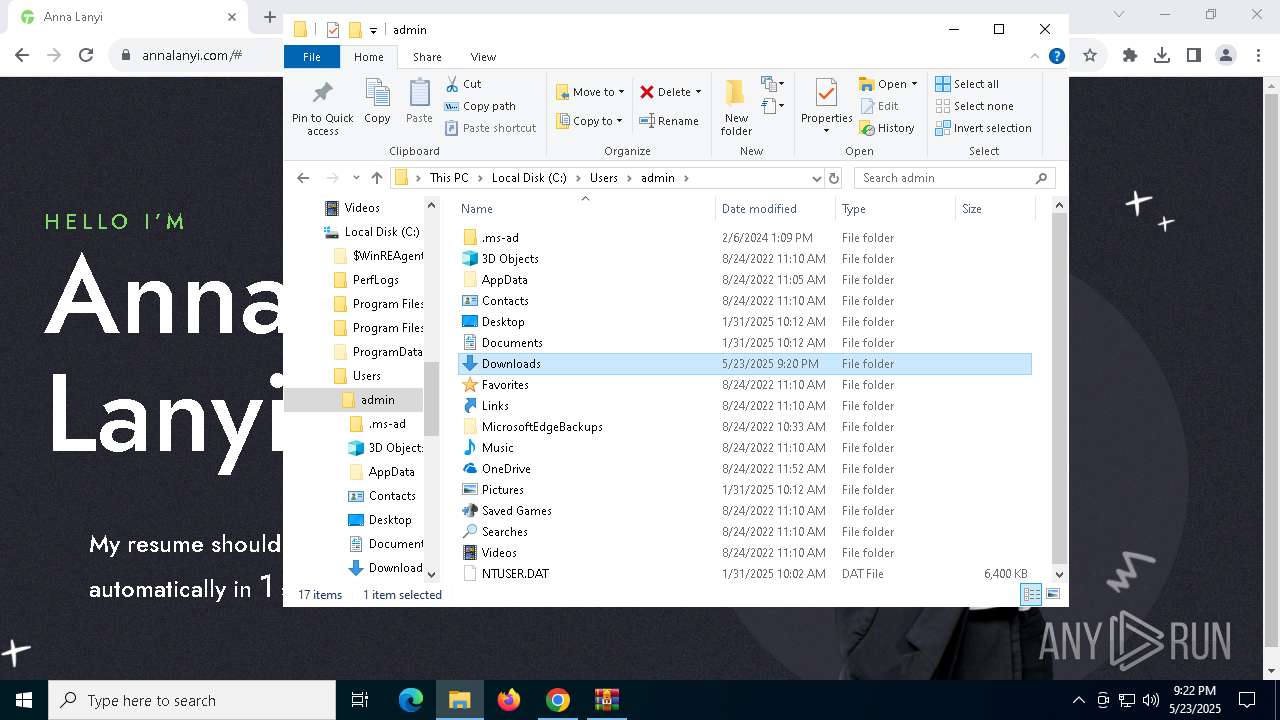
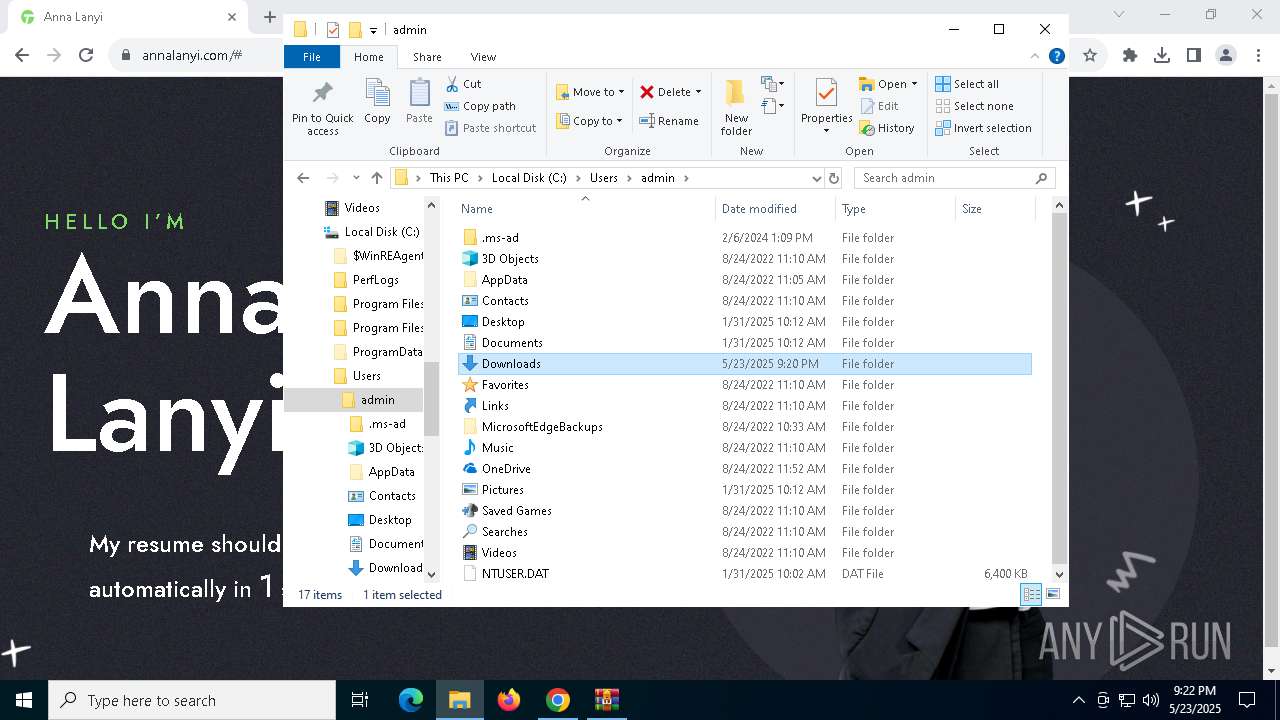
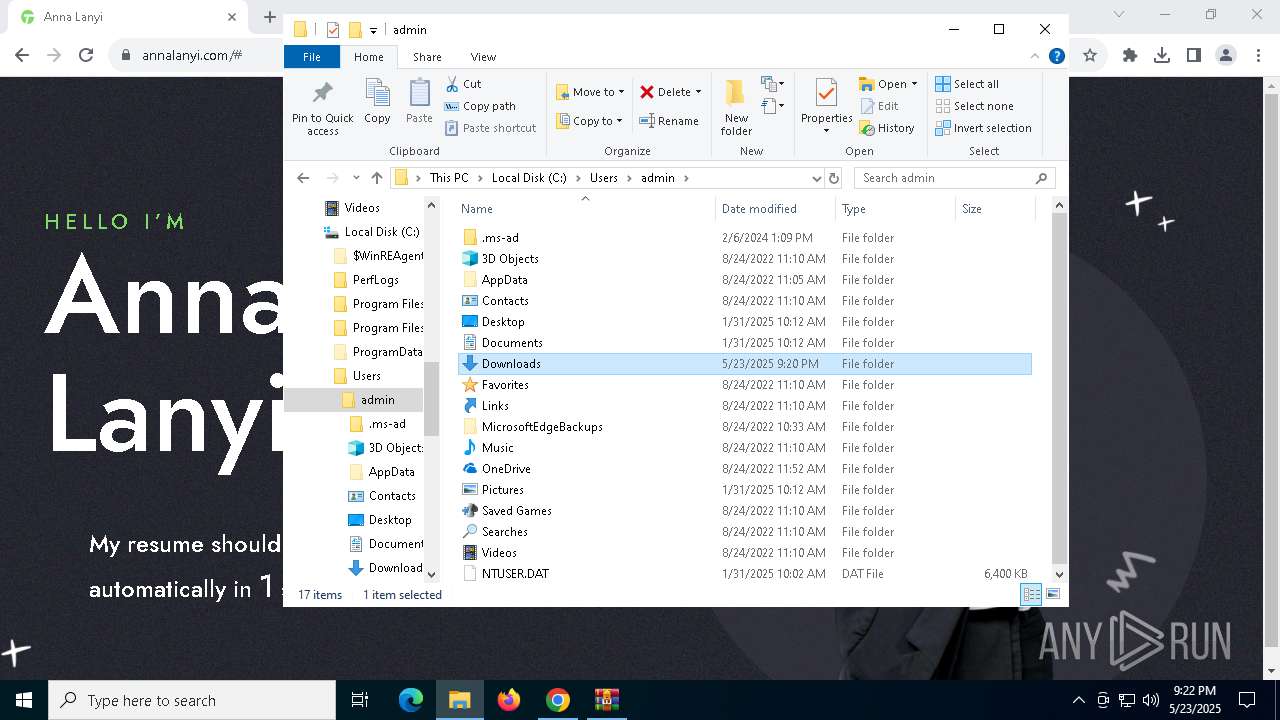
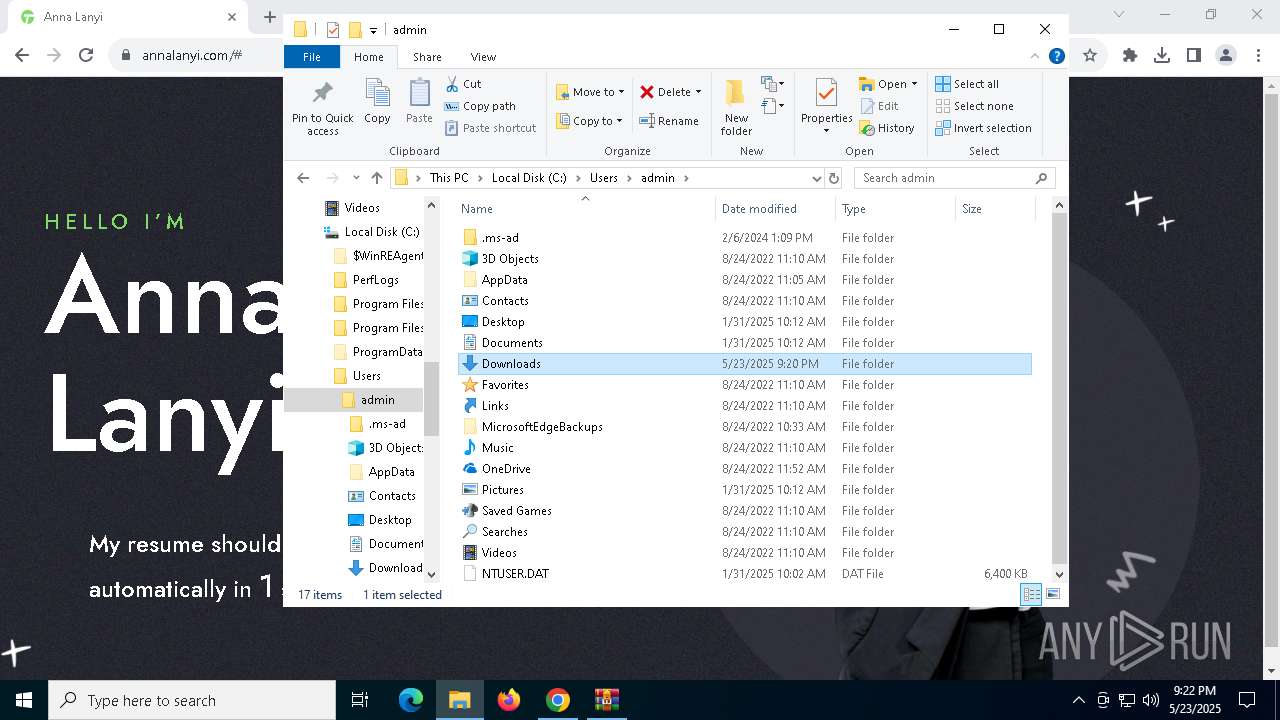
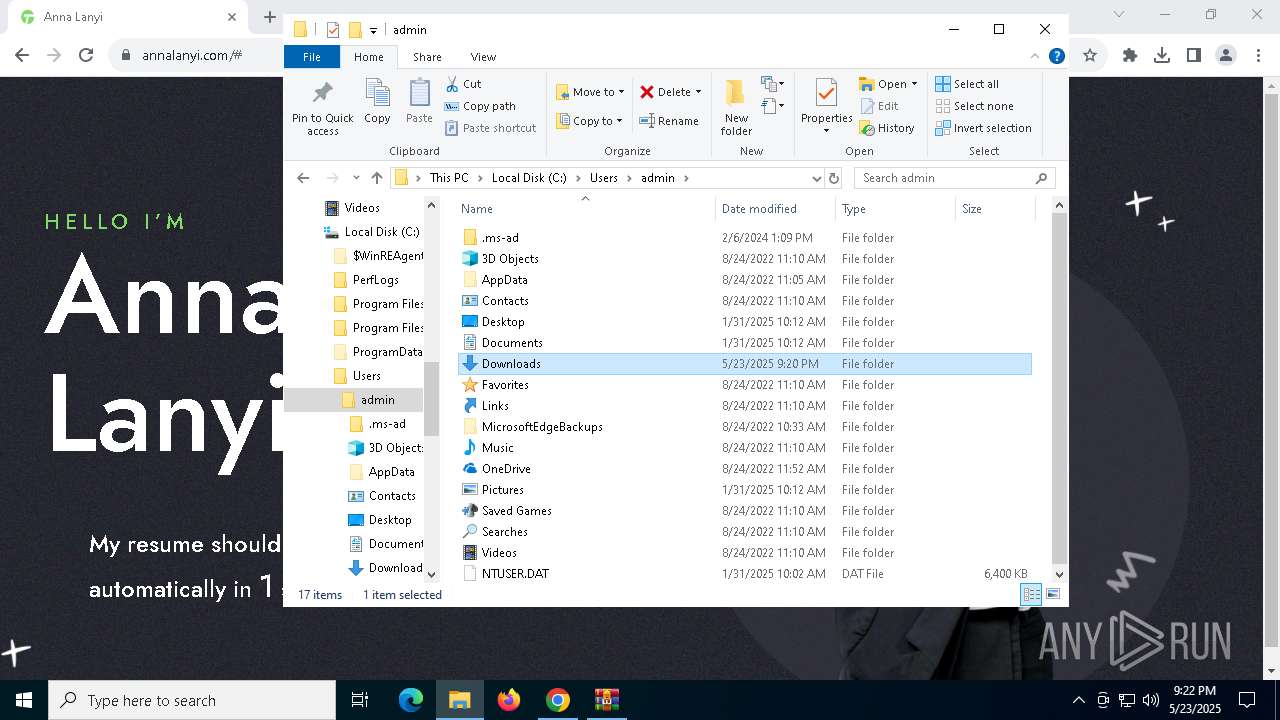
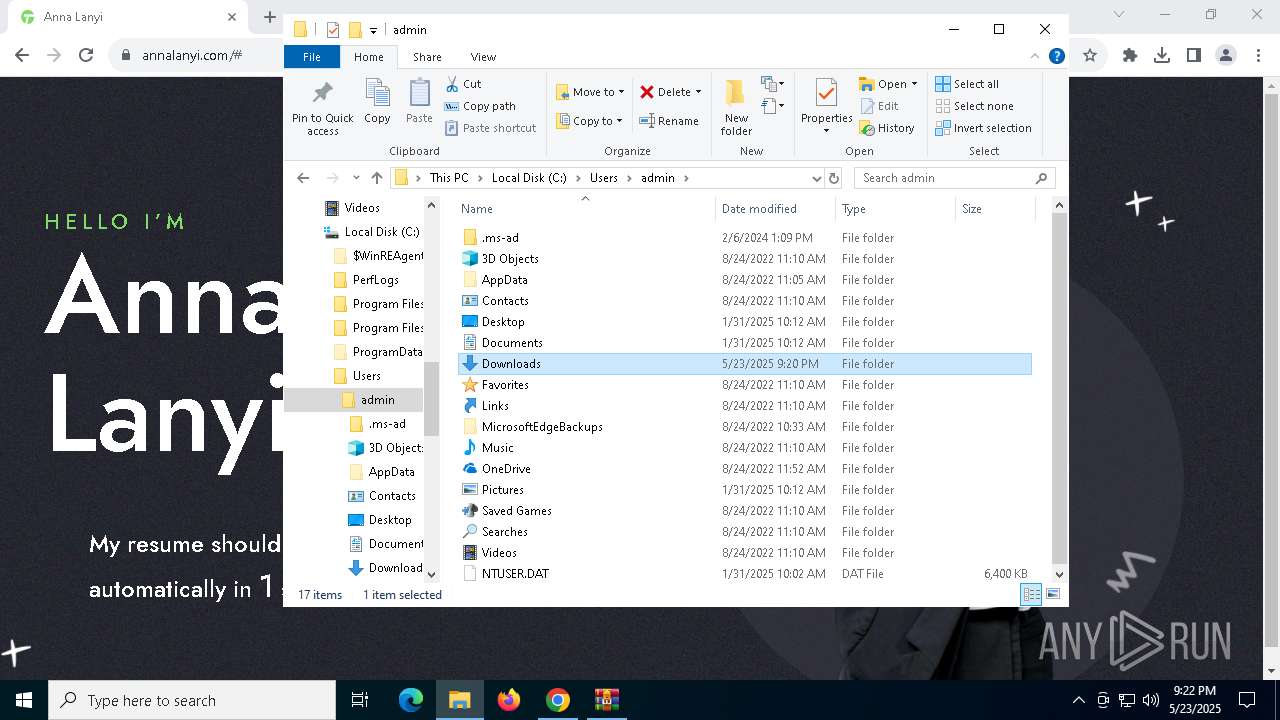
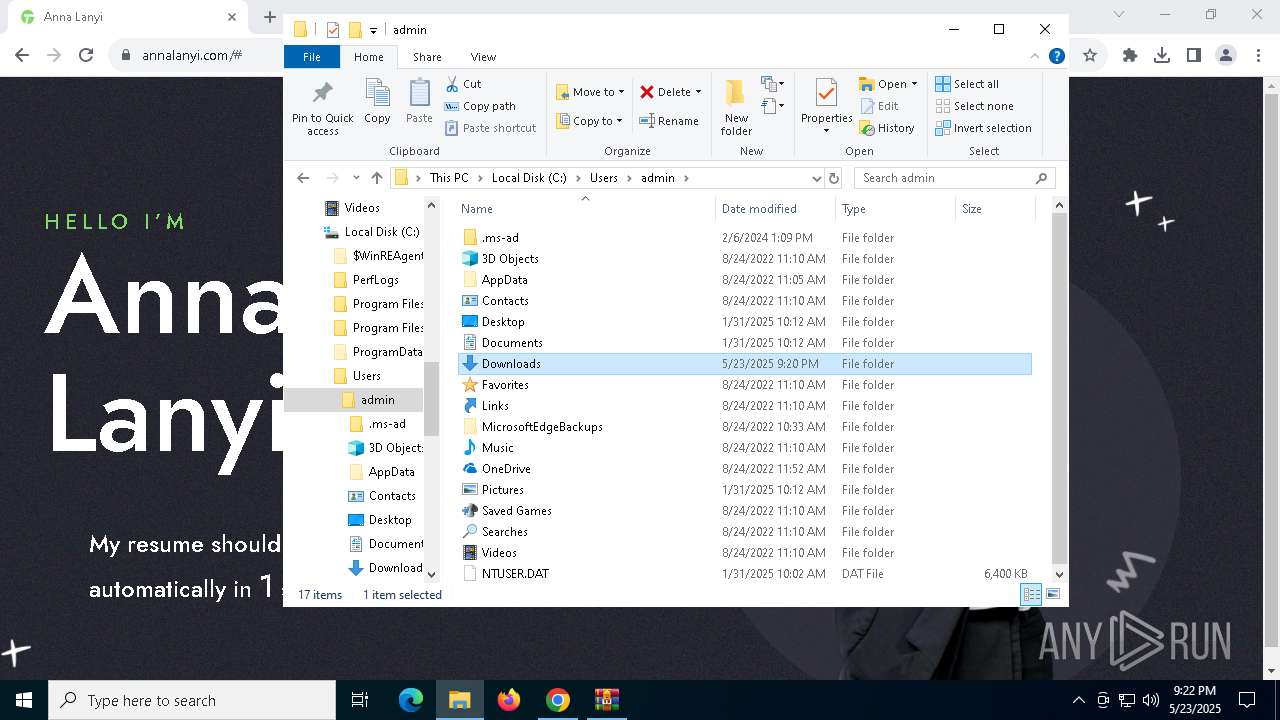
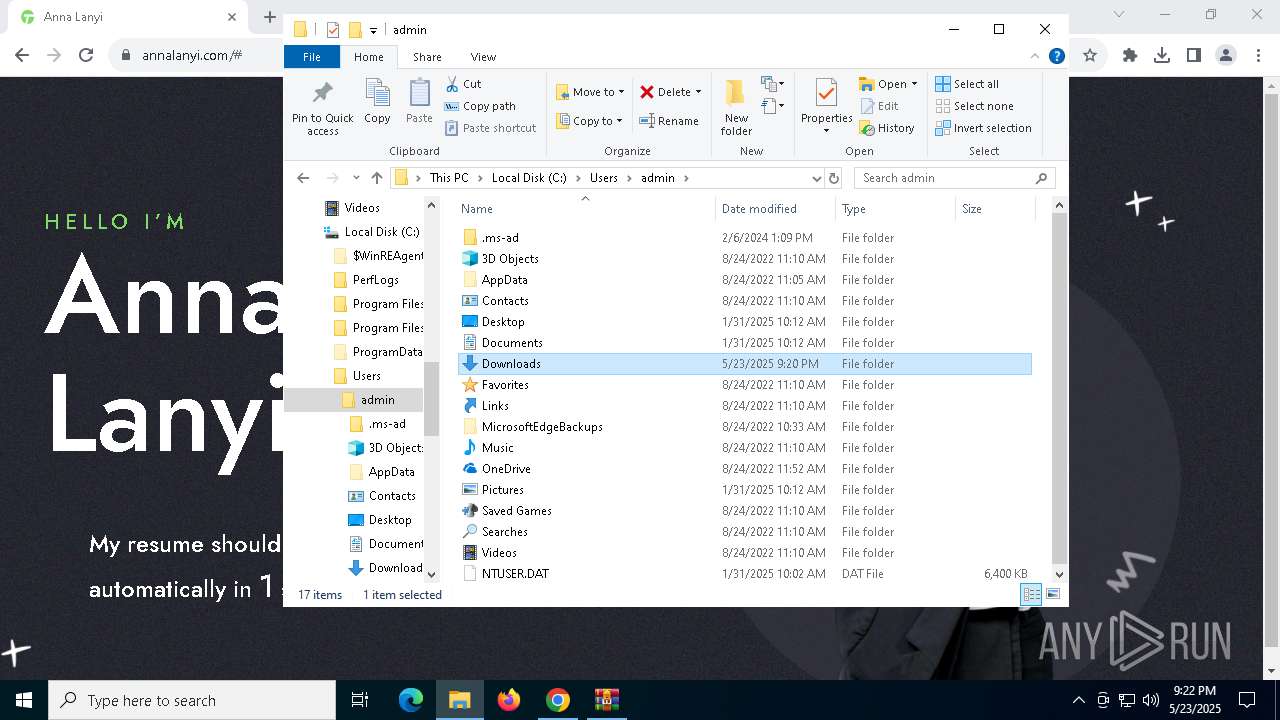
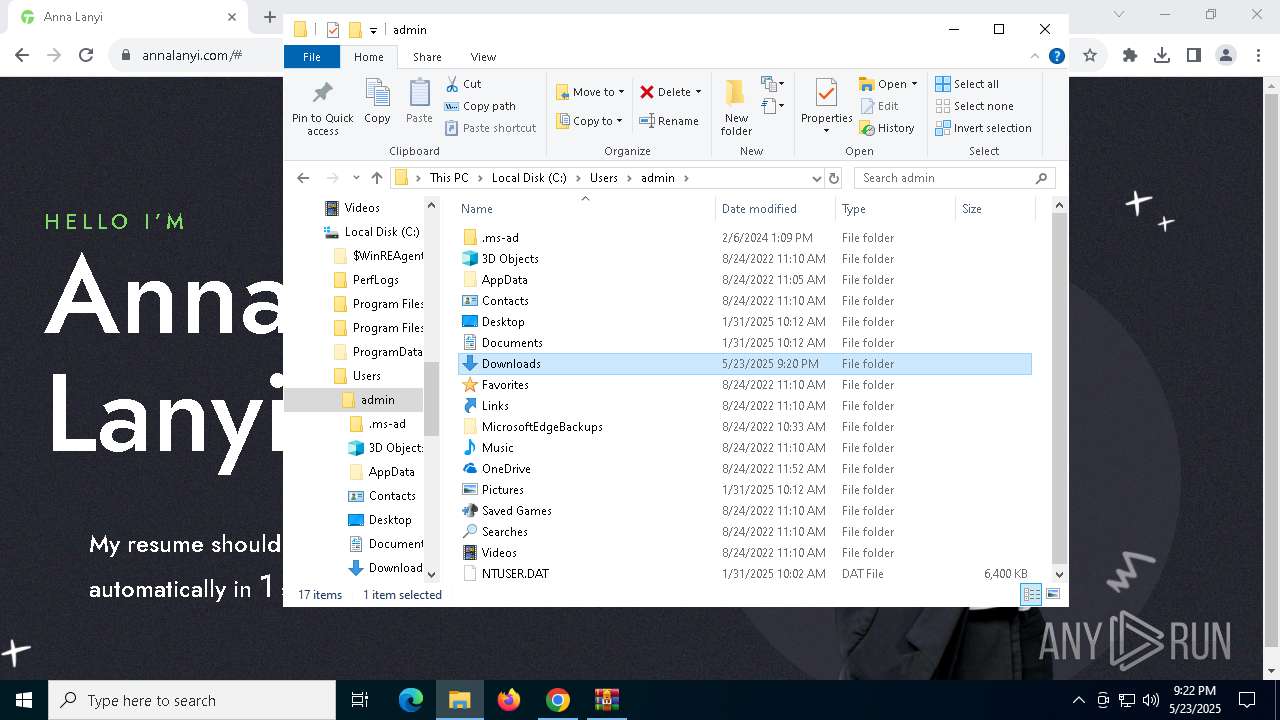
| 684 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Anna Lanyi.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | msxsl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4724 --field-trial-handle=1896,i,7739561192823118088,5757820847359145039,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 896 | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe 550BA14D9.txt 550BA14D9.txt | C:\Users\admin\AppData\Roaming\Adobe\msxsl.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: msxsl Exit code: 3221225477 Version: 1.1.0.1 Modules
| |||||||||||||||
Total events
137 392
Read events
137 152
Write events
233
Delete events
7
Modification events
| (PID) Process: | (4756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4756) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D140AB7828CCDB01 | |||
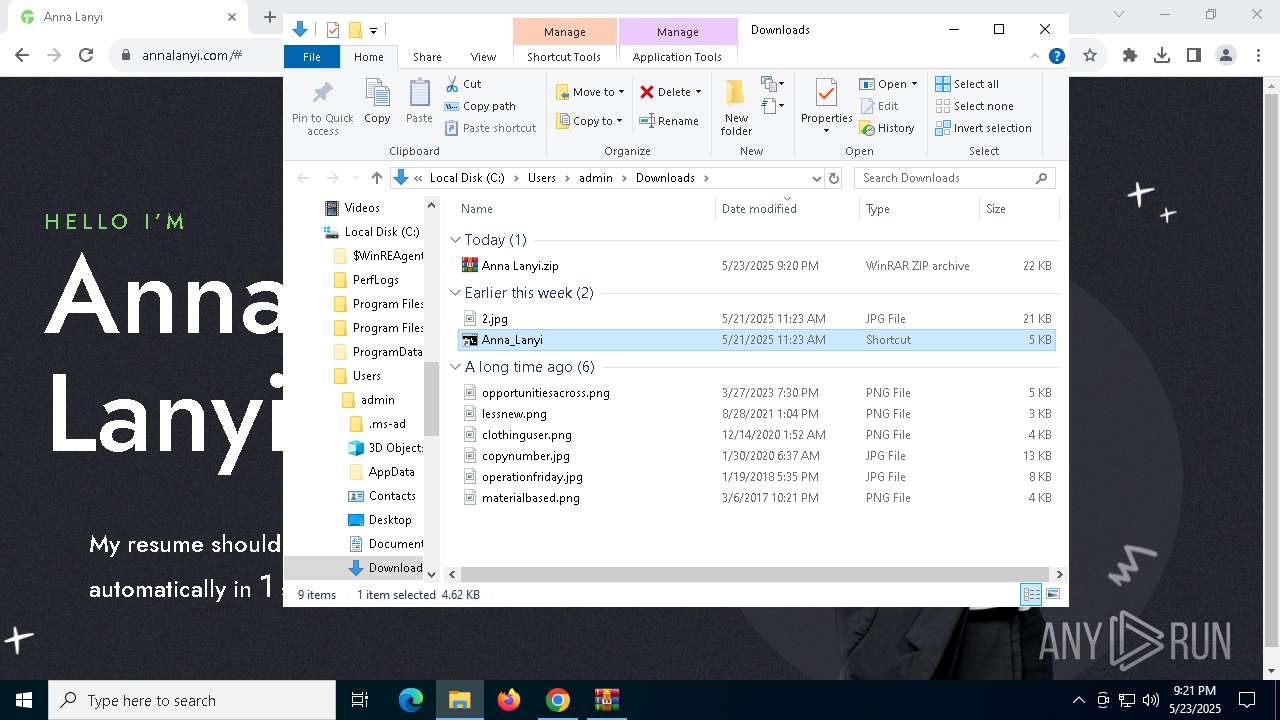
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6300) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Anna Lanyi.zip | |||
Executable files
16
Suspicious files
171
Text files
100
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10a877.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10a896.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10a896.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10a8a6.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10a867.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
135
DNS requests
57
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac2ulwywnwgn2xush6ktfxep2vqq_3070/jflookgnkcckhobaglndicnbbgbonegd_3070_all_p53ihrr5e6fkjxlsapvf6bvruy.crx3 | unknown | — | — | whitelisted |
7324 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1244 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4756 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
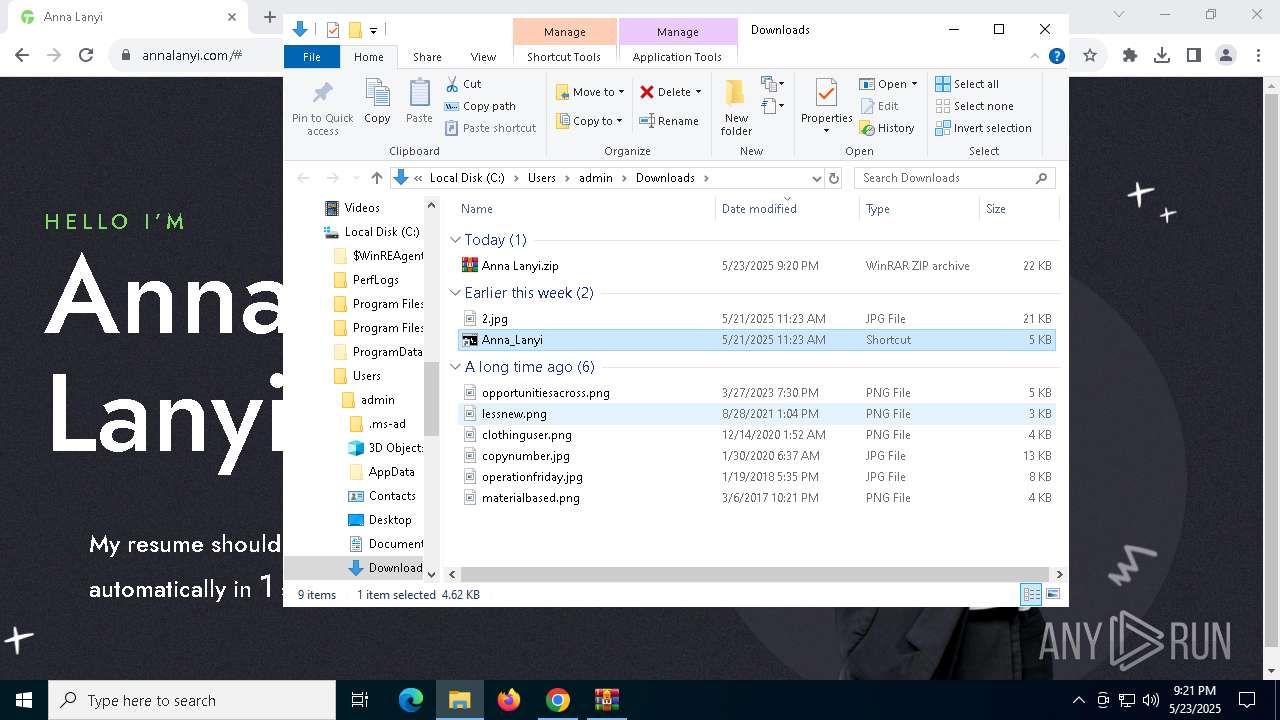
7236 | chrome.exe | 3.15.10.170:443 | annalanyi.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
annalanyi.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
static.geetest.com |
| shared |
cdn.jsdelivr.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7236 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | A Network Trojan was detected | ET MALWARE Observed DNS Query to Venom Spider/TA4557 Domain (tool .municipiodechepo .org) |
7704 | msxsl.exe | A Network Trojan was detected | ET MALWARE Observed Venom Spider/TA4557 Domain (tool .municipiodechepo .org in TLS SNI) |
5236 | msxsl.exe | A Network Trojan was detected | ET MALWARE Observed Venom Spider/TA4557 Domain (tool .municipiodechepo .org in TLS SNI) |
7968 | msxsl.exe | A Network Trojan was detected | ET MALWARE Observed Venom Spider/TA4557 Domain (tool .municipiodechepo .org in TLS SNI) |
6480 | msxsl.exe | A Network Trojan was detected | ET MALWARE Observed Venom Spider/TA4557 Domain (tool .municipiodechepo .org in TLS SNI) |
5124 | msxsl.exe | A Network Trojan was detected | ET MALWARE Observed Venom Spider/TA4557 Domain (tool .municipiodechepo .org in TLS SNI) |