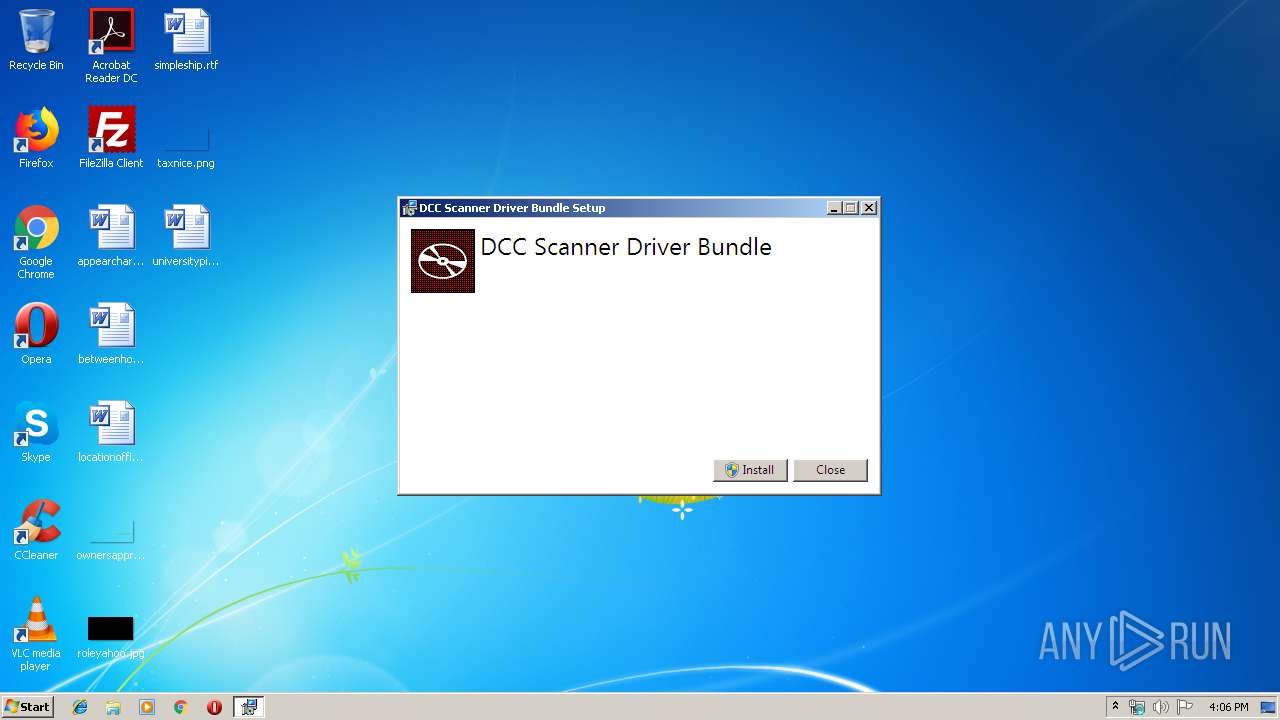
| File name: | DCC_Setup_Bundle.exe |
| Full analysis: | https://app.any.run/tasks/31b291b6-5780-4bf7-99f4-d7f53e2a0a6a |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2019, 16:06:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EA374D3E1F615005A3123662A8D8330B |
| SHA1: | 595F8EBB1A0EDB0CAFE8E9A1A97A6601A75154E9 |
| SHA256: | 8DE33209EA5B2D0E1CEB4177FB37172AC7CB07DE9A4DE5B8A9317117309D043F |
| SSDEEP: | 196608:1ciIKU+v3AQfcpenSqSqR4O41yJVW6bUJ1W0nBuzTKoeX7h9ilF/cEs:1/ZDvngenQ4IsJckmBSTKo4HilF0Es |
MALICIOUS
Loads dropped or rewritten executable
- DCC_Setup_Bundle.exe (PID: 2304)
- D247.ScannerService.WindowsService.exe (PID: 1012)
- D247.ScannerServiceRefresh.WindowsService.exe (PID: 1816)
Changes the autorun value in the registry
- DCC_Setup_Bundle.exe (PID: 2576)
Changes settings of System certificates
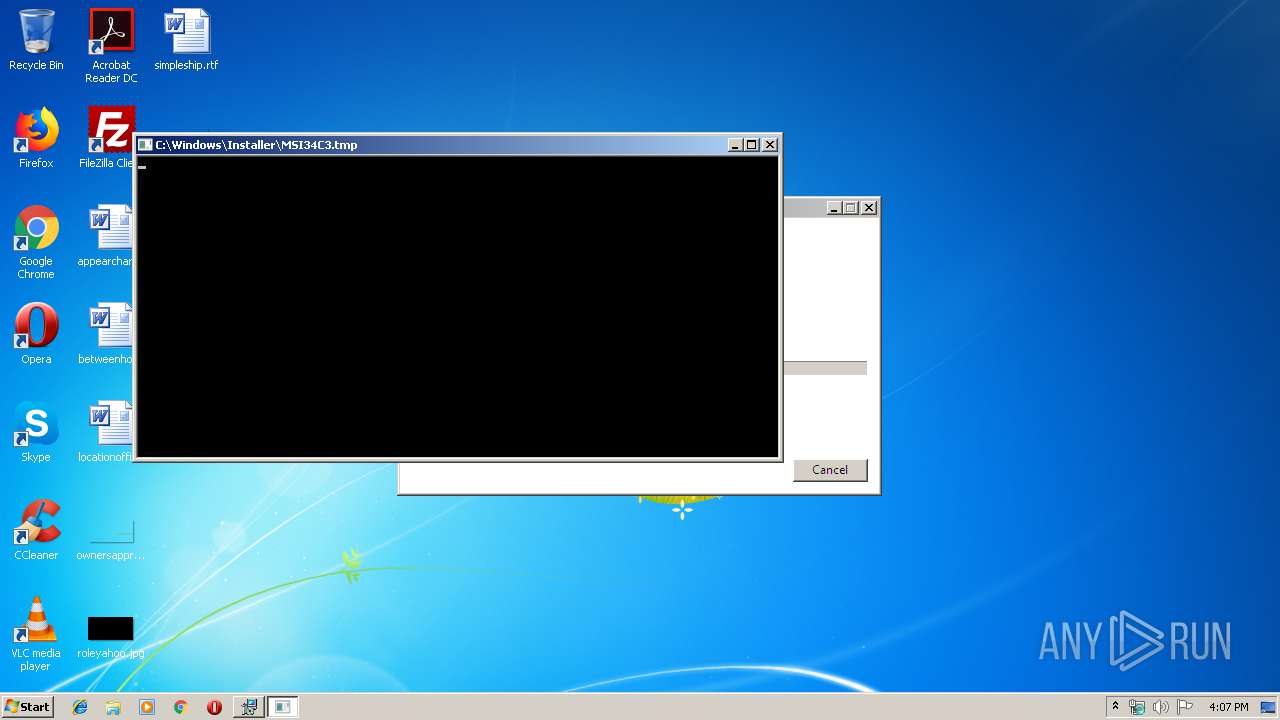
- MSI34C3.tmp (PID: 1316)
Application was dropped or rewritten from another process
- D247.ScannerService.WindowsService.exe (PID: 1012)
- D247.ScannerServiceRefresh.WindowsService.exe (PID: 1816)
- DCC TellerScan.exe (PID: 1752)
- SetScannerDriver.exe (PID: 184)
- DCC TellerScan.exe (PID: 2488)
- TellerScanDriver_17.02.exe (PID: 928)
- DPInst32.exe (PID: 1972)
- DevCon.exe (PID: 2192)
- DevCon.exe (PID: 3876)
- DevCon.exe (PID: 900)
- DPInst32.exe (PID: 324)
- DPInst32.exe (PID: 3432)
Writes to the hosts file
- MSI34C3.tmp (PID: 1316)
SUSPICIOUS
Starts itself from another location
- DCC_Setup_Bundle.exe (PID: 3960)
- DCC_Setup_Bundle.exe (PID: 2304)
- DCC TellerScan.exe (PID: 1752)
Executed as Windows Service
- vssvc.exe (PID: 3744)
- D247.ScannerService.WindowsService.exe (PID: 1012)
- D247.ScannerServiceRefresh.WindowsService.exe (PID: 1816)
Executable content was dropped or overwritten
- DCC_Setup_Bundle.exe (PID: 2576)
- DCC_Setup_Bundle.exe (PID: 3960)
- msiexec.exe (PID: 3972)
- DCC_Setup_Bundle.exe (PID: 2304)
- DCC TellerScan.exe (PID: 1752)
- DCC TellerScan.exe (PID: 2488)
- MSIEXEC.EXE (PID: 3148)
- MsiExec.exe (PID: 748)
- TellerScanDriver_17.02.exe (PID: 928)
- TellerScanDriver_17.02.tmp (PID: 3544)
- DPInst32.exe (PID: 3432)
Searches for installed software
- DCC_Setup_Bundle.exe (PID: 2576)
Creates files in the program directory
- DCC_Setup_Bundle.exe (PID: 2576)
- MSI34C3.tmp (PID: 1316)
- D247.ScannerServiceRefresh.WindowsService.exe (PID: 1816)
- D247.ScannerService.WindowsService.exe (PID: 1012)
Uses NETSH.EXE for network configuration
- MSI34C3.tmp (PID: 1316)
Creates a software uninstall entry
- DCC_Setup_Bundle.exe (PID: 2576)
Starts Microsoft Installer
- DCC TellerScan.exe (PID: 2488)
Reads Environment values
- D247.ScannerService.WindowsService.exe (PID: 1012)
Creates files in the user directory
- msiexec.exe (PID: 3972)
Removes files from Windows directory
- MsiExec.exe (PID: 748)
- TellerScanDriver_17.02.tmp (PID: 3544)
- DrvInst.exe (PID: 3816)
- DrvInst.exe (PID: 3388)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 748)
- MsiExec.exe (PID: 3980)
Creates files in the driver directory
- MsiExec.exe (PID: 748)
- DrvInst.exe (PID: 3816)
- DrvInst.exe (PID: 3388)
- TellerScanDriver_17.02.tmp (PID: 3544)
Creates files in the Windows directory
- MsiExec.exe (PID: 748)
- TellerScanDriver_17.02.tmp (PID: 3544)
- DrvInst.exe (PID: 3816)
- DPInst32.exe (PID: 1972)
- DrvInst.exe (PID: 3388)
Executed via COM
- DrvInst.exe (PID: 3816)
- DrvInst.exe (PID: 3388)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3260)
INFO
Starts application with an unusual extension
- msiexec.exe (PID: 3972)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3972)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3744)
Reads the hosts file
- MSI34C3.tmp (PID: 1316)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3260)
Creates a software uninstall entry
- msiexec.exe (PID: 3972)
- TellerScanDriver_17.02.tmp (PID: 3544)
Application was dropped or rewritten from another process
- MSI34C3.tmp (PID: 1316)
- TellerScanDriver_17.02.tmp (PID: 3544)
Application launched itself
- msiexec.exe (PID: 3972)
- chrome.exe (PID: 3260)
Creates files in the program directory
- msiexec.exe (PID: 3972)
- TellerScanDriver_17.02.tmp (PID: 3544)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3980)
- MsiExec.exe (PID: 748)
- TellerScanDriver_17.02.tmp (PID: 3544)
Searches for installed software
- msiexec.exe (PID: 3972)
Manual execution by user
- chrome.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:16 22:18:53+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 300032 |
| InitializedDataSize: | 160768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2c86e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Wausau Financial |
| FileDescription: | DCC Scanner Driver Bundle |
| FileVersion: | 1.0.0.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Wausau Financial. All rights reserved. |
| OriginalFileName: | DCC_Setup_Bundle.exe |
| ProductName: | DCC Scanner Driver Bundle |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2016 21:18:53 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Wausau Financial |
| FileDescription: | DCC Scanner Driver Bundle |
| FileVersion: | 1.0.0.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Wausau Financial. All rights reserved. |
| OriginalFilename: | DCC_Setup_Bundle.exe |
| ProductName: | DCC Scanner Driver Bundle |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 16-Jan-2016 21:18:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000493E7 | 0x00049400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56579 |
.rdata | 0x0004B000 | 0x0001E994 | 0x0001EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12486 |
.data | 0x0006A000 | 0x00001768 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.79138 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.581309 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006E000 | 0x00003A54 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.53853 |
.reloc | 0x00072000 | 0x00003D30 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.75498 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
138
Monitored processes
76
Malicious processes
16
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\ProgramData\Package Cache\7A2122E40E13B64095EE353823BECBE075A4D712\SetScannerDriver.exe" DCCTS | C:\ProgramData\Package Cache\7A2122E40E13B64095EE353823BECBE075A4D712\SetScannerDriver.exe | — | DCC_Setup_Bundle.exe | |||||||||||
User: admin Integrity Level: HIGH Description: SetScannerDriver Exit code: 0 Version: 1709.27.3.0 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,2383210518634298645,14076602017372909072,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1039363165964842563 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,2383210518634298645,14076602017372909072,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13433266366889668461 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 324 | "C:\Program Files\TellerScan\Drivers\32-bit\DPInst32.exe" /u dccst3.inf /d /q | C:\Program Files\TellerScan\Drivers\32-bit\DPInst32.exe | — | TellerScanDriver_17.02.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
| 328 | "netsh.exe" http show sslcert ipport=0.0.0.0:4443 | C:\Windows\system32\netsh.exe | MSI34C3.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,2383210518634298645,14076602017372909072,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2172974018892828495 --mojo-platform-channel-handle=3200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "netsh.exe" http add urlacl url=https://deposit247scanner:4443/ user=Everyone | C:\Windows\system32\netsh.exe | MSI34C3.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,2383210518634298645,14076602017372909072,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1997445757461185567 --mojo-platform-channel-handle=4084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | C:\Windows\system32\MsiExec.exe -Embedding 93D022C0FC3C56ADF342F289248CDC2D | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Program Files\TellerScan\Drivers\DevCon.exe" disable *VID_08B1* | C:\Program Files\TellerScan\Drivers\DevCon.exe | — | TellerScanDriver_17.02.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
Total events
3 182
Read events
2 109
Write events
1 020
Delete events
53
Modification events
| (PID) Process: | (2304) DCC_Setup_Bundle.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2304) DCC_Setup_Bundle.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2576) DCC_Setup_Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000E82C9B61AAA3D501100A0000F8010000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) DCC_Setup_Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000E82C9B61AAA3D501100A0000F8010000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) DCC_Setup_Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (2576) DCC_Setup_Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000369FEE61AAA3D501100A0000F8010000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2576) DCC_Setup_Bundle.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009001F161AAA3D501100A0000E4090000E8030000010000000000000000000000F2A3F0E59684DD46914CC8F7362F2F350000000000000000 | |||
| (PID) Process: | (3744) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F88AFA61AAA3D501A00E0000E0090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3744) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F88AFA61AAA3D501A00E0000080B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3744) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F88AFA61AAA3D501A00E0000EC0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
92
Suspicious files
54
Text files
271
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2576 | DCC_Setup_Bundle.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2304 | DCC_Setup_Bundle.exe | C:\Users\admin\AppData\Local\Temp\{3757C115-3F3E-4E01-AA3D-1B8D26E0F5E2}\TellerScan | — | |
MD5:— | SHA256:— | |||
| 2304 | DCC_Setup_Bundle.exe | C:\Users\admin\AppData\Local\Temp\{3757C115-3F3E-4E01-AA3D-1B8D26E0F5E2}\SetScannerDriveUtility | — | |
MD5:— | SHA256:— | |||
| 2576 | DCC_Setup_Bundle.exe | C:\ProgramData\Package Cache\.unverified\ScannerService | — | |
MD5:— | SHA256:— | |||
| 2576 | DCC_Setup_Bundle.exe | C:\ProgramData\Package Cache\.unverified\ScannerServiceRefresh | — | |
MD5:— | SHA256:— | |||
| 2576 | DCC_Setup_Bundle.exe | C:\ProgramData\Package Cache\.unverified\TellerScan | — | |
MD5:— | SHA256:— | |||
| 2576 | DCC_Setup_Bundle.exe | C:\ProgramData\Package Cache\.unverified\SetScannerDriveUtility | — | |
MD5:— | SHA256:— | |||
| 3744 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3972 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFEC7DB2D47C194120.TMP | — | |
MD5:— | SHA256:— | |||
| 2576 | DCC_Setup_Bundle.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
26
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3324 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3324 | chrome.exe | GET | 200 | 185.38.0.205:80 | http://r2---sn-4ox-uh2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=196.244.192.14&mm=28&mn=sn-4ox-uh2e&ms=nvh&mt=1574698044&mv=m&mvi=1&pl=24&shardbypass=yes | FI | crx | 862 Kb | whitelisted |
3324 | chrome.exe | GET | 200 | 185.38.0.205:80 | http://r2---sn-4ox-uh2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=196.244.192.14&mm=28&mn=sn-4ox-uh2e&ms=nvh&mt=1574698044&mv=m&mvi=1&pl=24&shardbypass=yes | FI | crx | 293 Kb | whitelisted |
3324 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3324 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.22.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 216.58.208.35:443 | www.google.se | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.21.238:443 | play.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.se |
| whitelisted |
Threats
Process | Message |
|---|---|
D247.ScannerService.WindowsService.exe | 1:Src=USER-PC:D247.ScannerService.WindowsService 2019-11-25 16:07:28.2437500 Level=NA~
ScannerService Log will watch for changes to File C:\Program Files\Wausau Financial\D247.ScannerService \ WfsLogSettings.config
|
D247.ScannerServiceRefresh.WindowsService.exe | 1:Src=USER-PC:D247.ScannerServiceRefresh.WindowsService 2019-11-25 16:07:31.1031250 Level=NA~
ScannerServiceRefresh Log will watch for changes to File C:\Program Files\Wausau Financial\D247.ScannerServiceRefresh \ WfsLogSettings.config
|