| File name: | Server.vmp.exe |
| Full analysis: | https://app.any.run/tasks/b1d359bf-2875-4425-bcf0-e1f3a896c171 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2022, 12:42:29 |
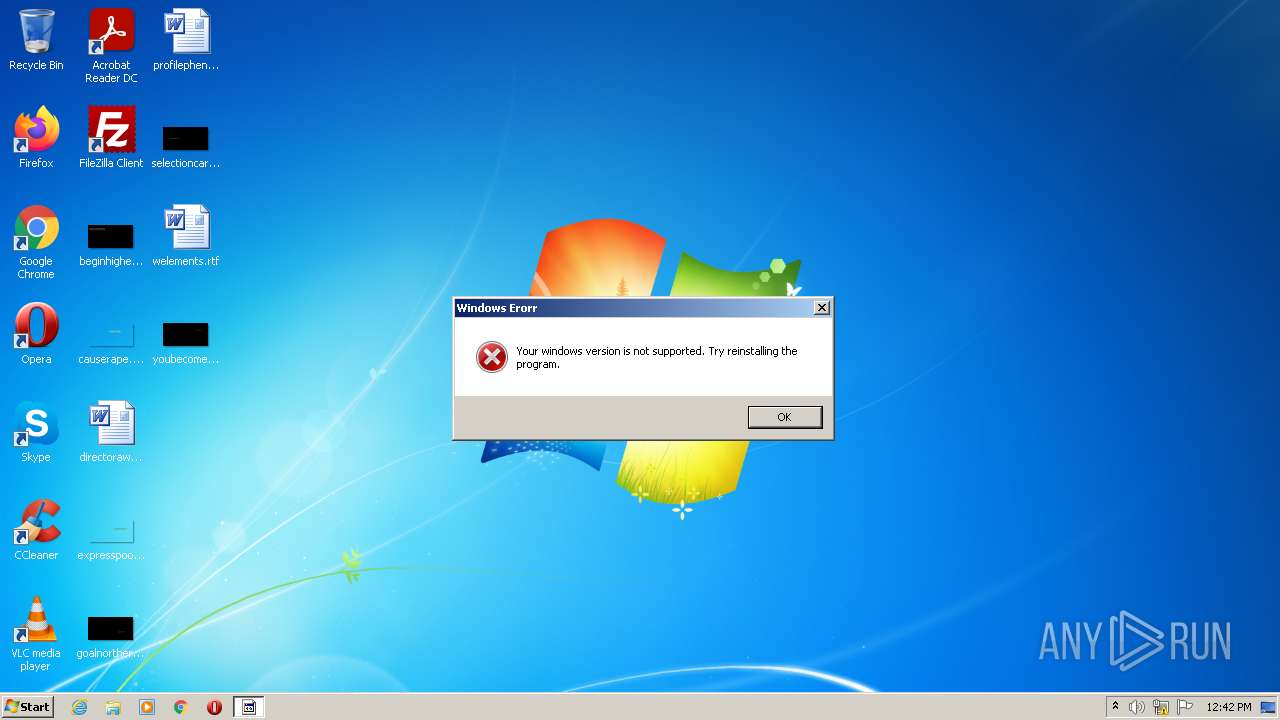
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 396C1C140DF103E306F499818F6B108B |
| SHA1: | 7BF36C5C74F96B805F6843296F70291508F76982 |
| SHA256: | 8DDCB19FCA82B7B588C7EEB61AEA330098F3058921A409199676032DCC61AA01 |
| SSDEEP: | 3072:G2xP91CtHX/0AGDzi0WajRvpfKYxyYE/fuobECWQ6neHDVrUpDhajpL450:G2194X/rGDZW+CYxtE/fuoRpnopDh0p |
MALICIOUS
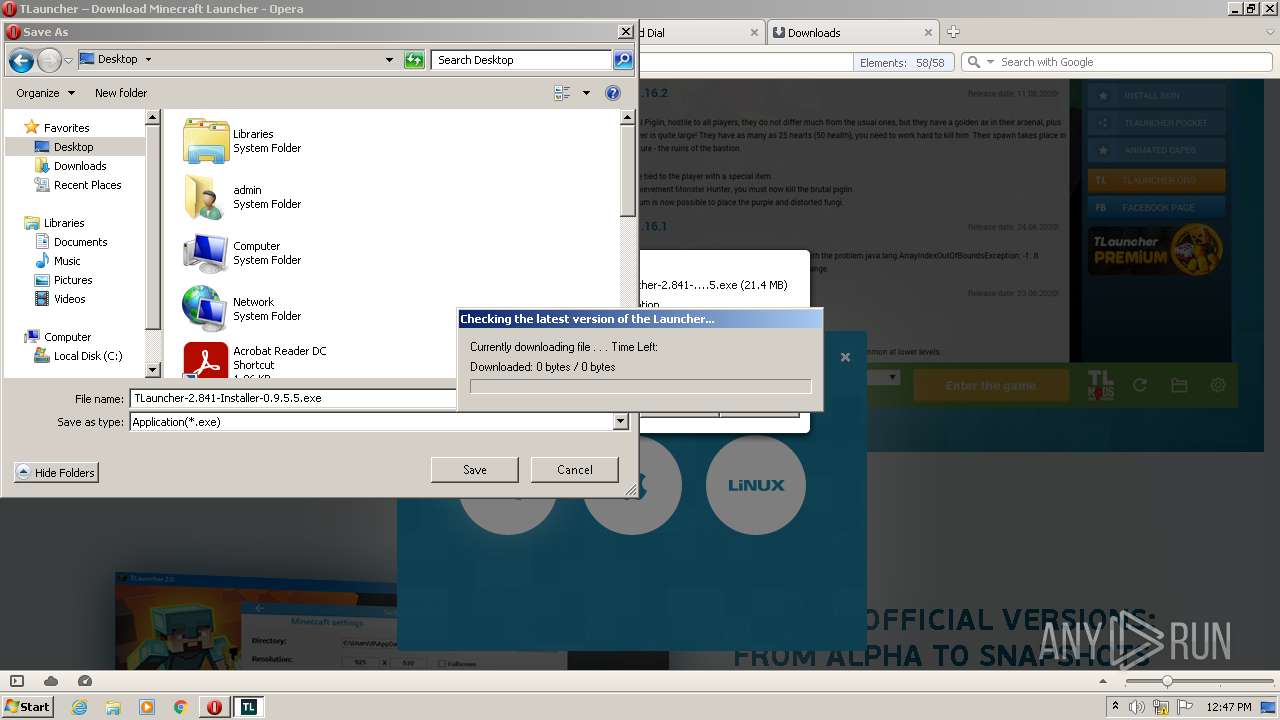
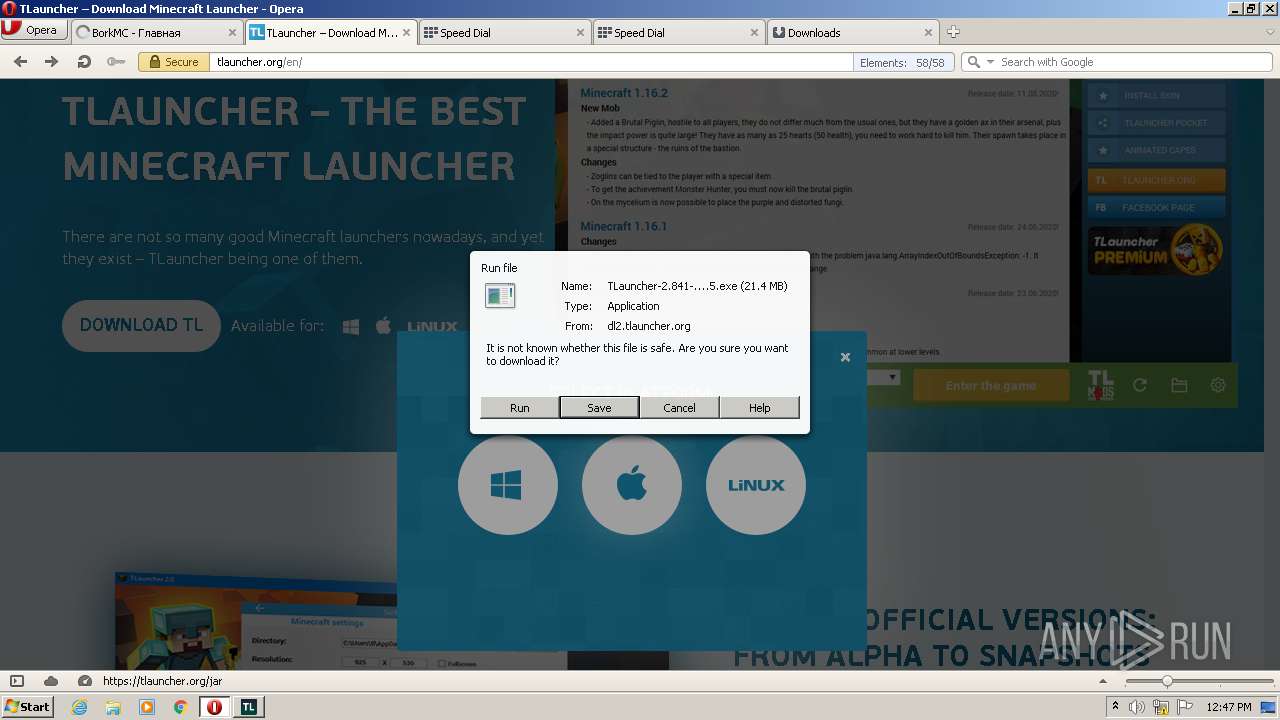
Application was dropped or rewritten from another process
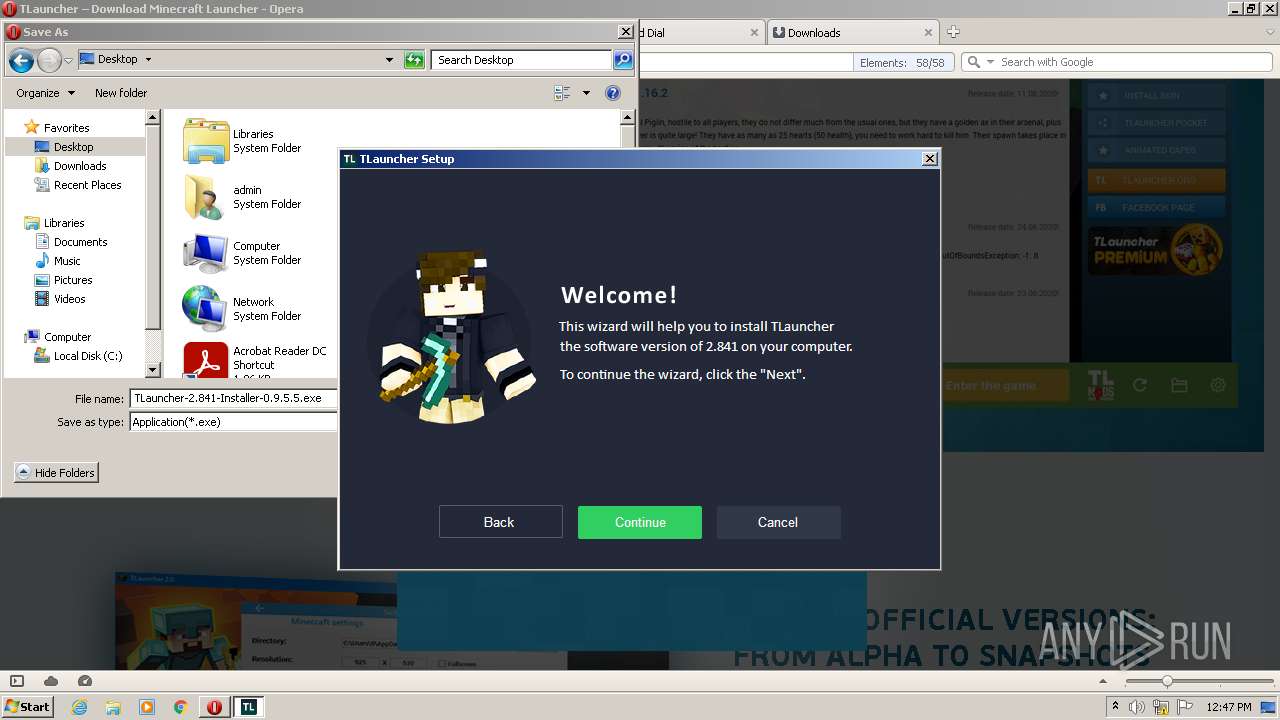
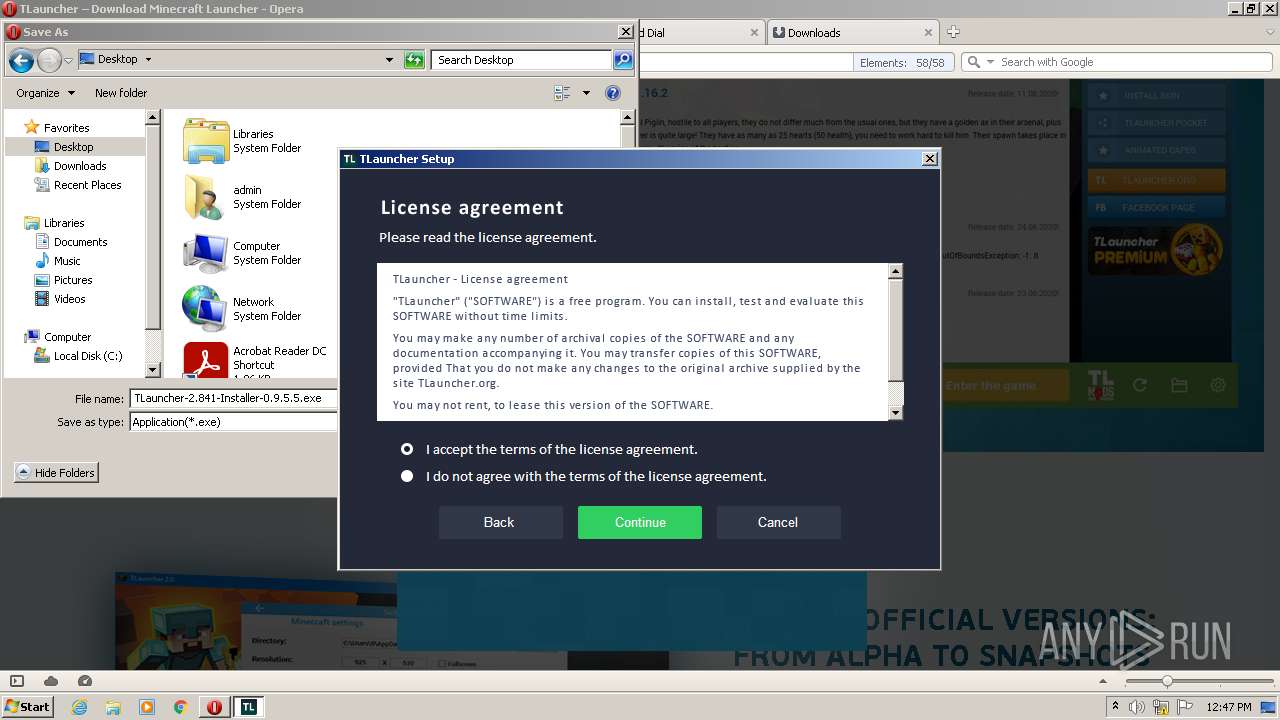
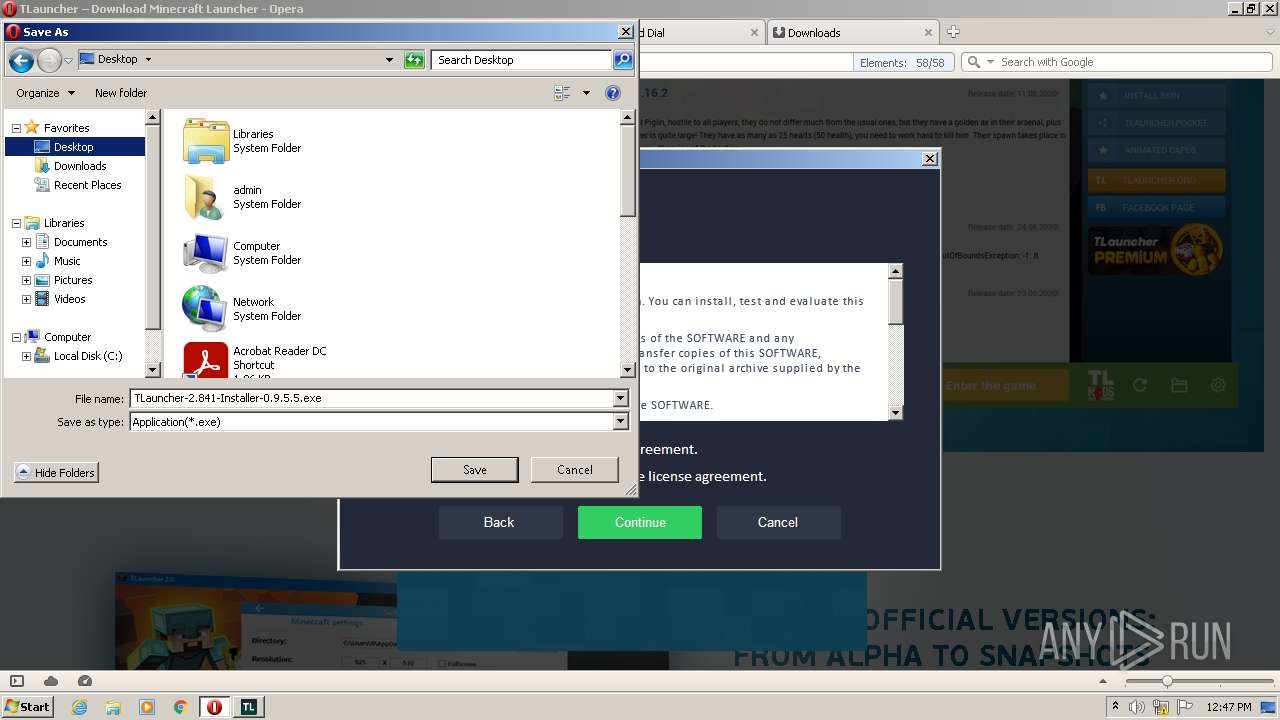
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 704)
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 2632)
- AdditionalExecuteTL.exe (PID: 412)
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
Drops executable file immediately after starts
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 2632)
- AdditionalExecuteTL.exe (PID: 412)
Changes settings of System certificates
- irsetup.exe (PID: 3808)
Actions looks like stealing of personal data
- irsetup.exe (PID: 3808)
Loads dropped or rewritten executable
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
SUSPICIOUS
Reads the computer name
- Server.vmp.exe (PID: 2300)
- irsetup.exe (PID: 3808)
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 2632)
- AdditionalExecuteTL.exe (PID: 412)
- irsetup.exe (PID: 2576)
Checks supported languages
- Server.vmp.exe (PID: 2300)
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 2632)
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
- AdditionalExecuteTL.exe (PID: 412)
Reads Environment values
- netsh.exe (PID: 3628)
- netsh.exe (PID: 2892)
- netsh.exe (PID: 2348)
- Server.vmp.exe (PID: 2300)
Creates files in the user directory
- Server.vmp.exe (PID: 2300)
Uses NETSH.EXE for network configuration
- Server.vmp.exe (PID: 2300)
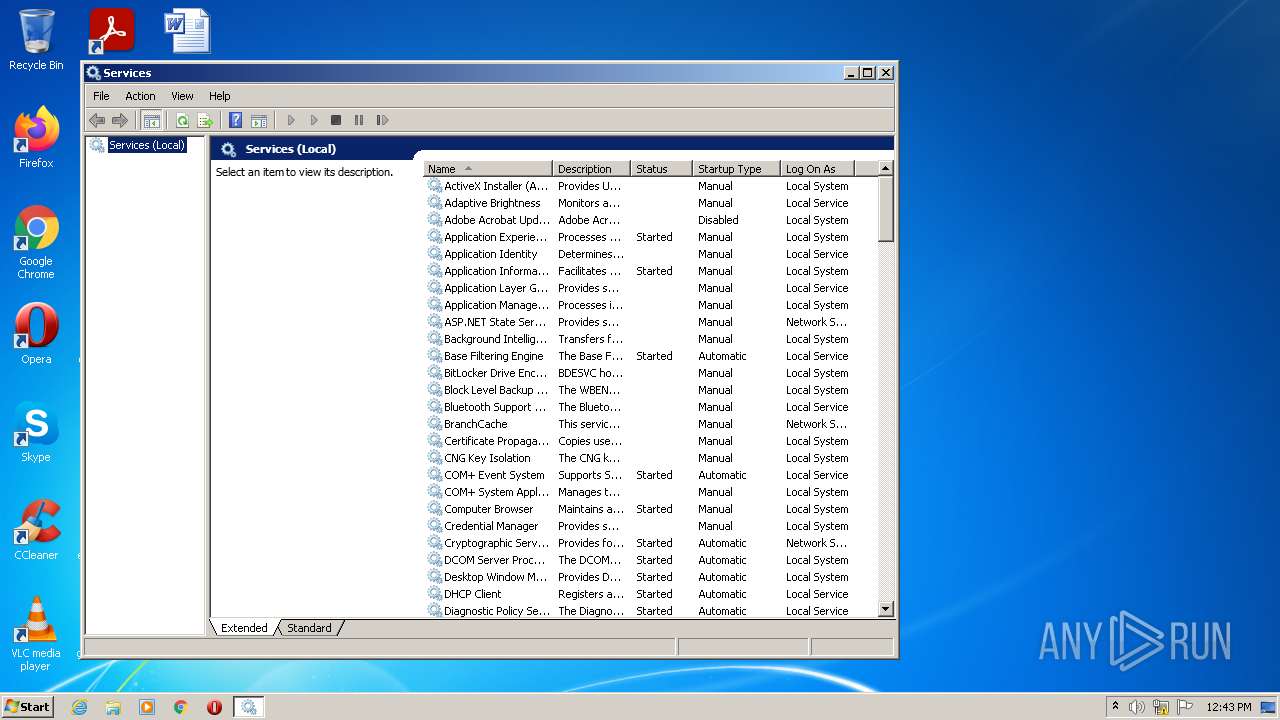
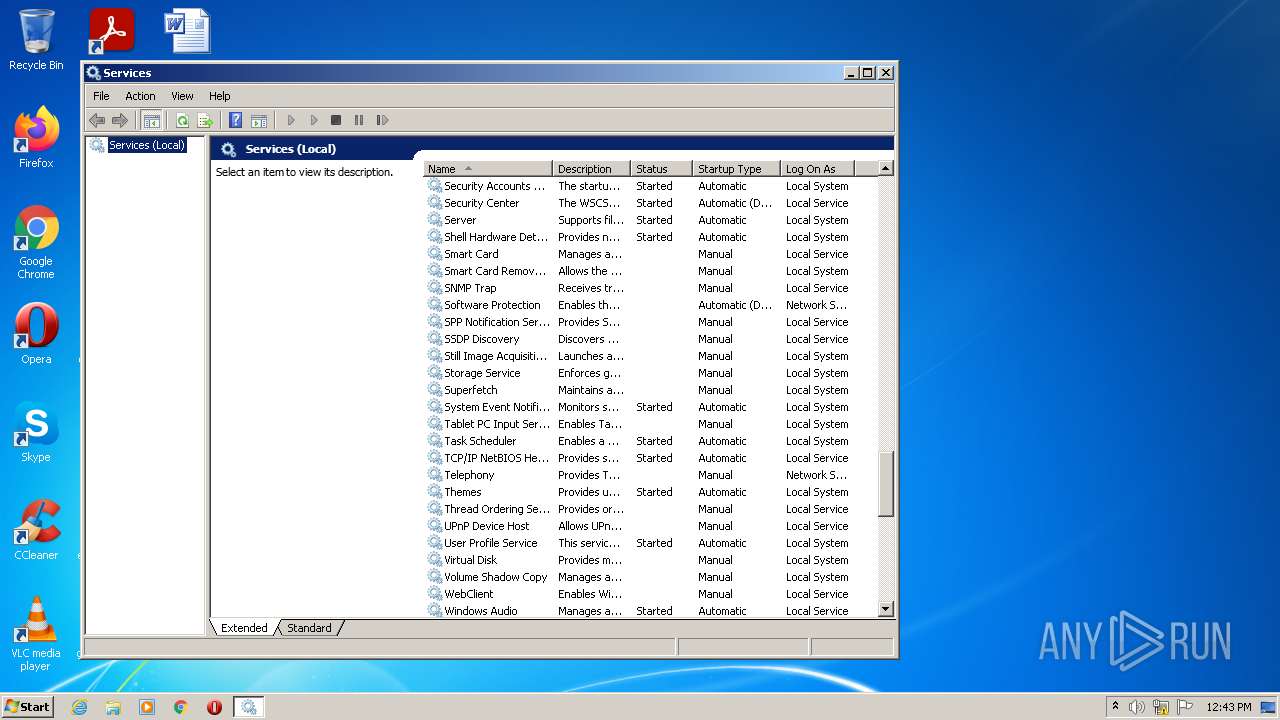
Reads Microsoft Outlook installation path
- mmc.exe (PID: 2600)
- irsetup.exe (PID: 3808)
Reads internet explorer settings
- mmc.exe (PID: 2600)
- irsetup.exe (PID: 3808)
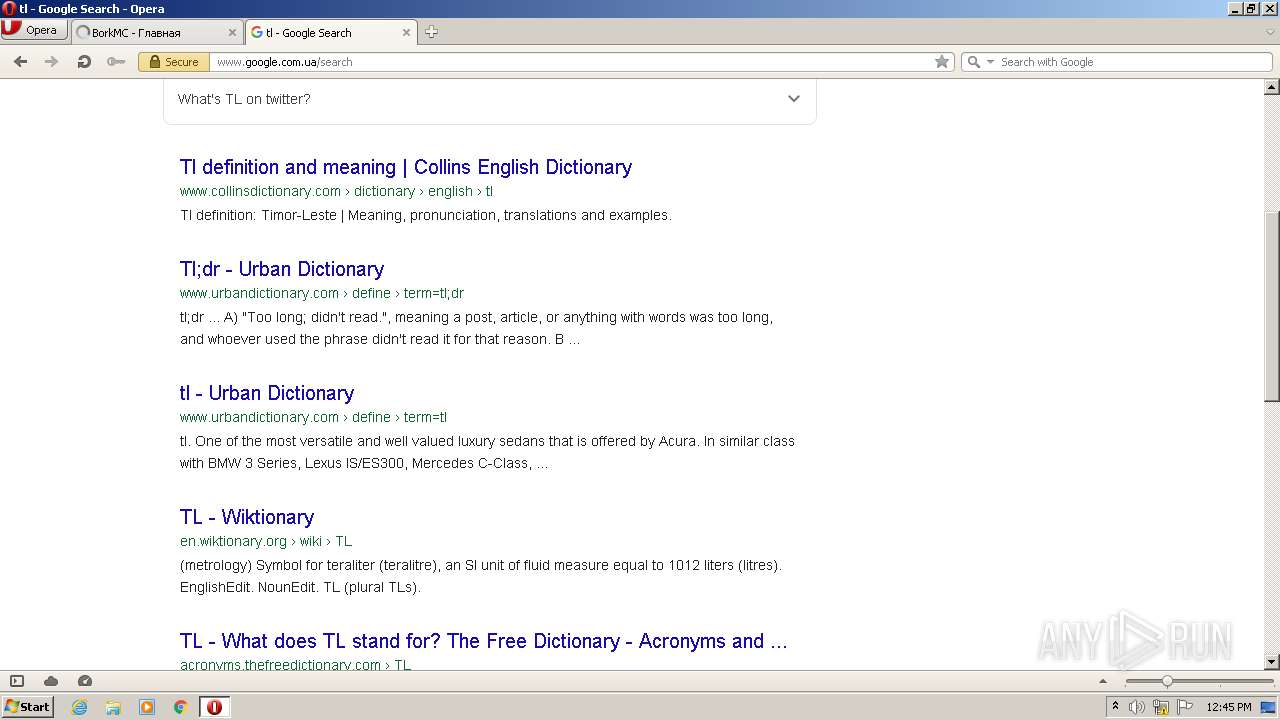
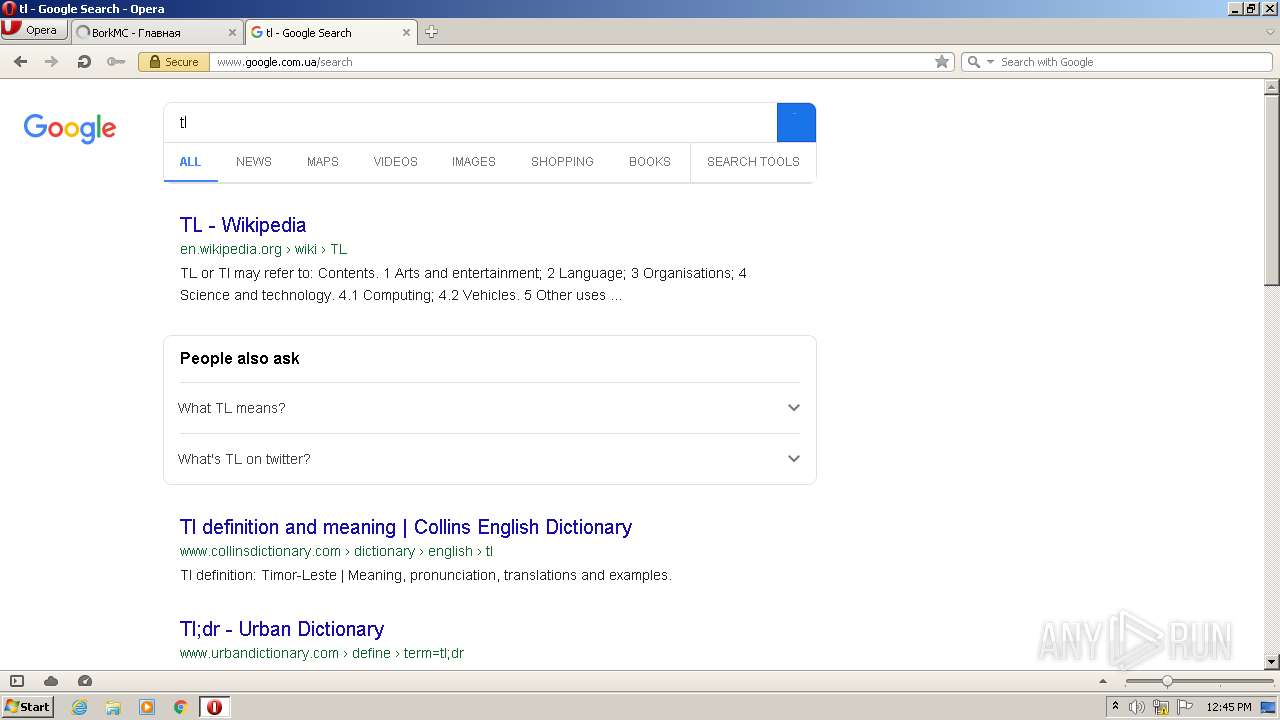
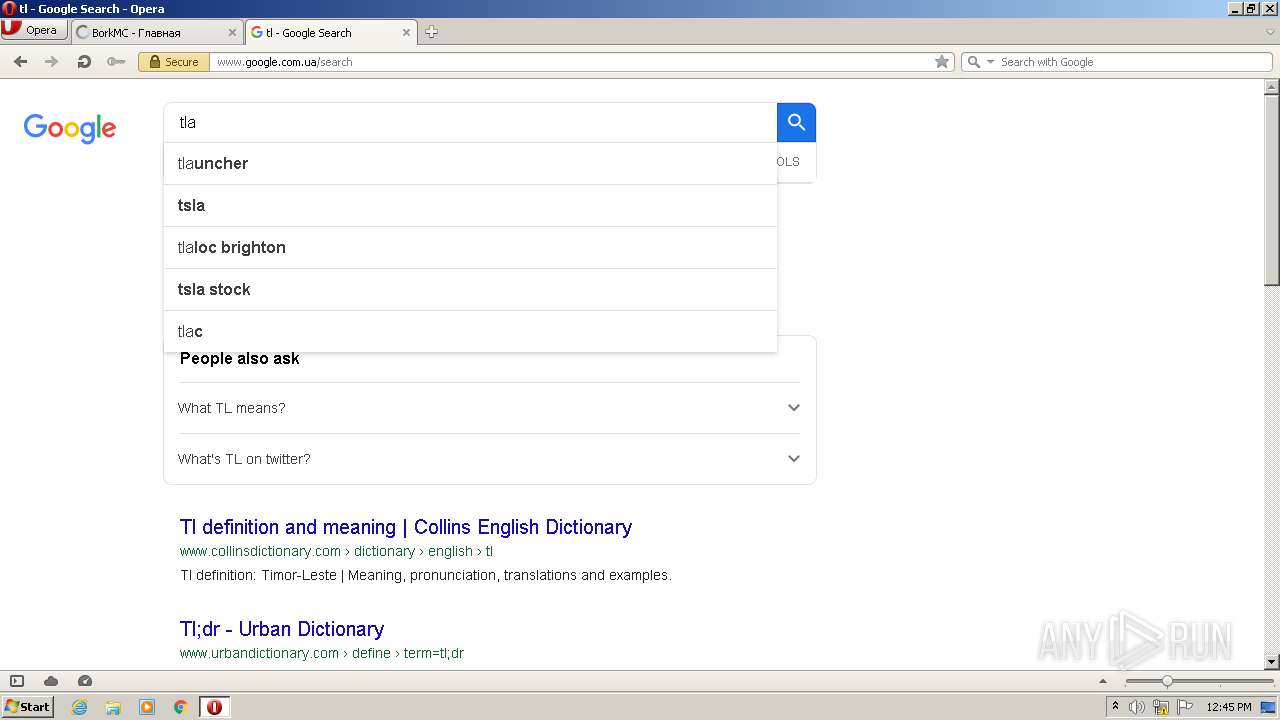
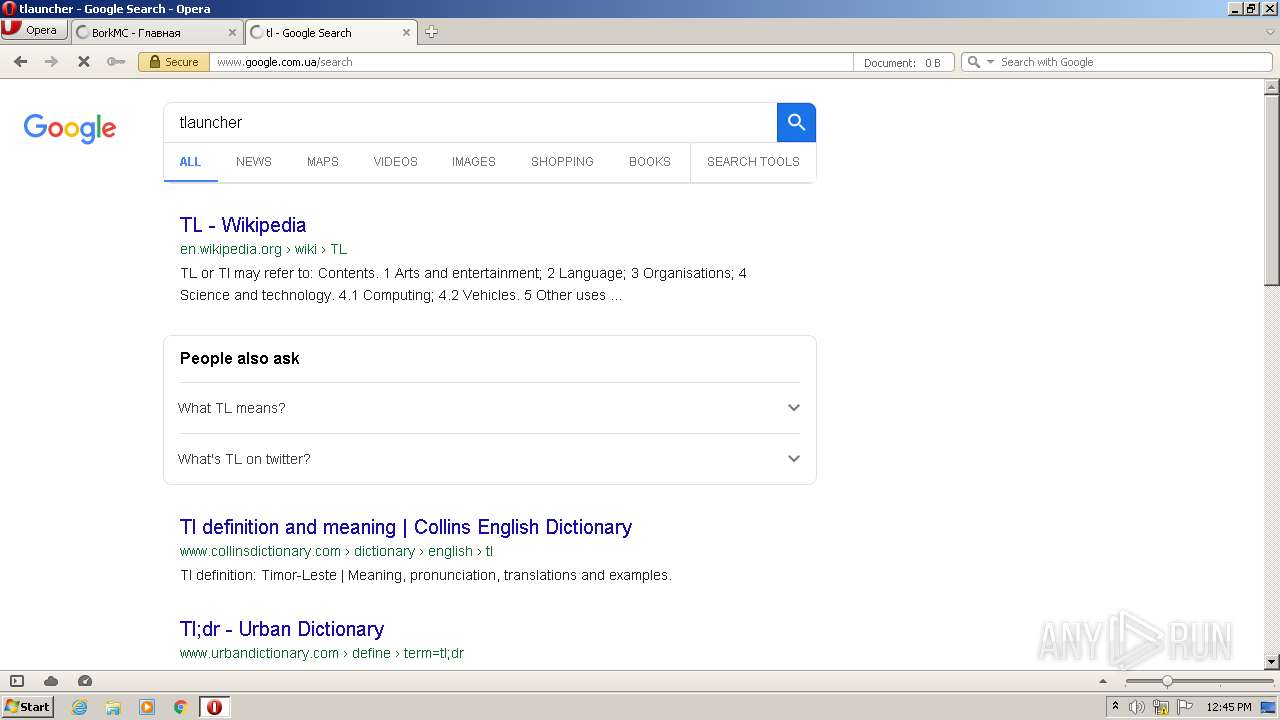
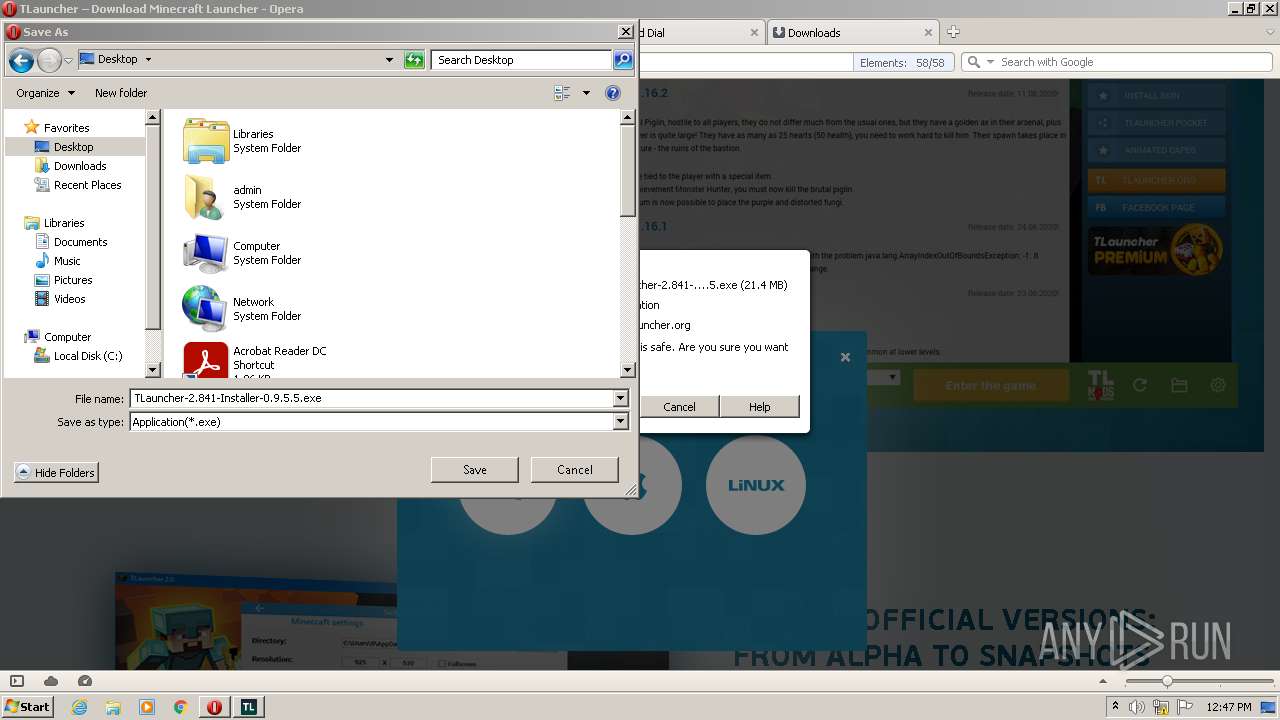
Executable content was dropped or overwritten
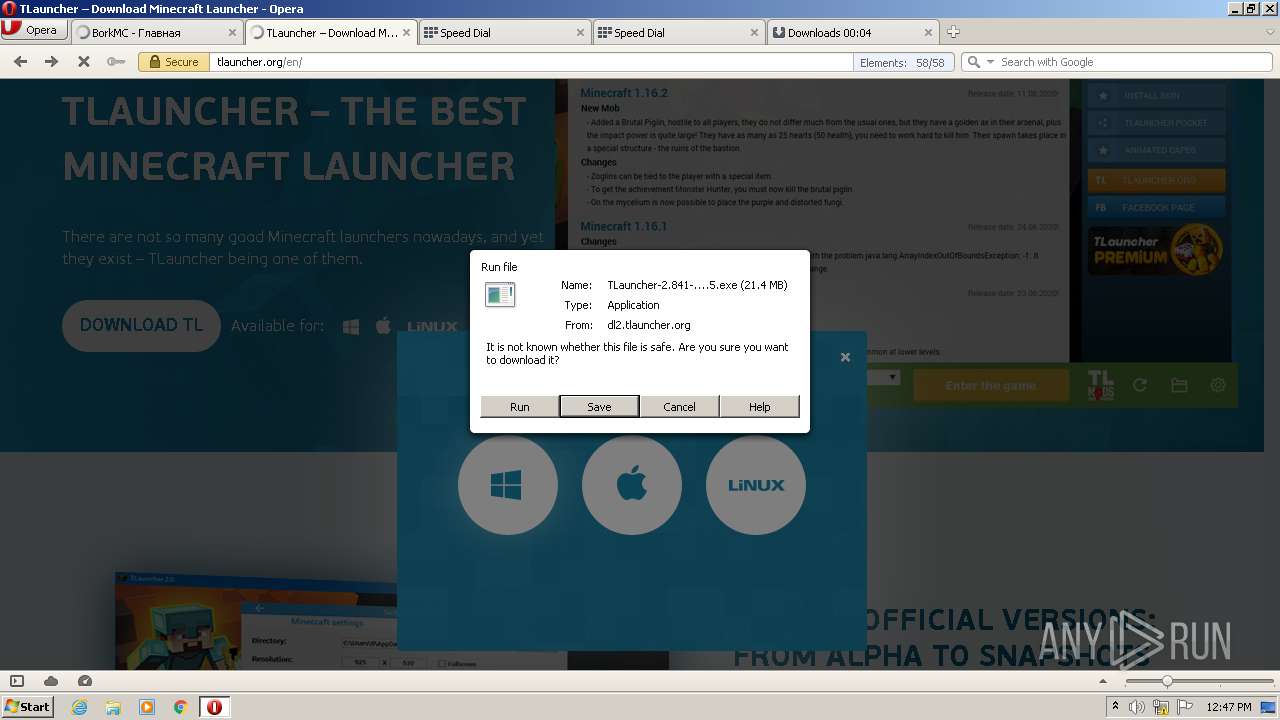
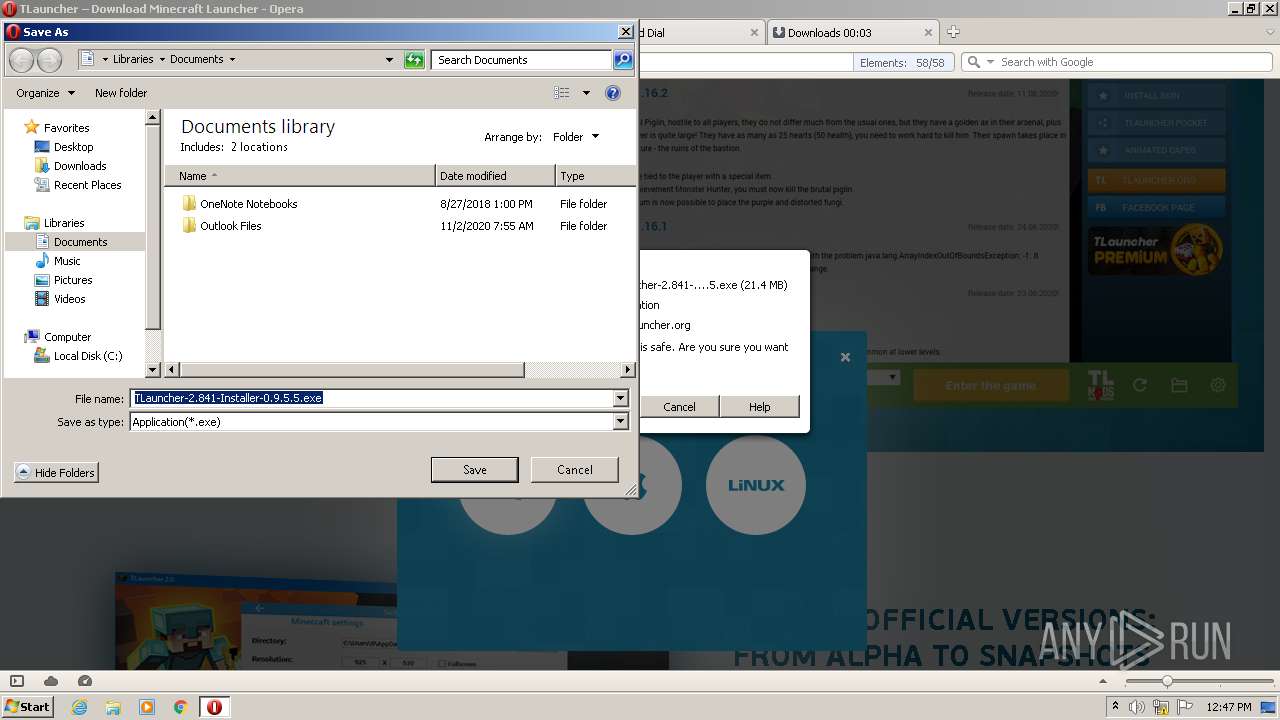
- opera.exe (PID: 2520)
- TLauncher-2.841-Installer-0.9.5.5.exe (PID: 2632)
- irsetup.exe (PID: 3808)
- AdditionalExecuteTL.exe (PID: 412)
Reads the Windows organization settings
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
Reads Windows owner or organization settings
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
Check for Java to be installed
- irsetup.exe (PID: 3808)
Adds / modifies Windows certificates
- irsetup.exe (PID: 3808)
INFO
Checks supported languages
- netsh.exe (PID: 3628)
- netsh.exe (PID: 2348)
- netsh.exe (PID: 2892)
- mmc.exe (PID: 2600)
- opera.exe (PID: 2520)
Reads the computer name
- netsh.exe (PID: 3628)
- netsh.exe (PID: 2892)
- netsh.exe (PID: 2348)
- mmc.exe (PID: 2600)
- opera.exe (PID: 2520)
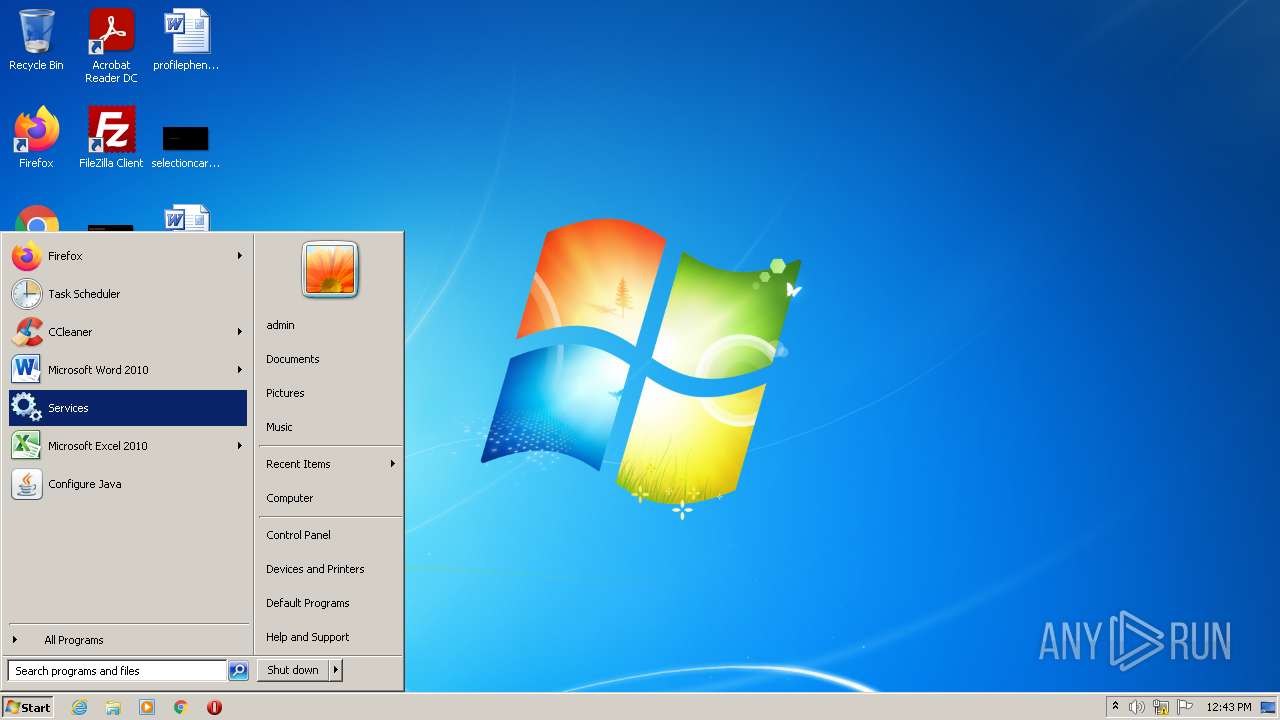
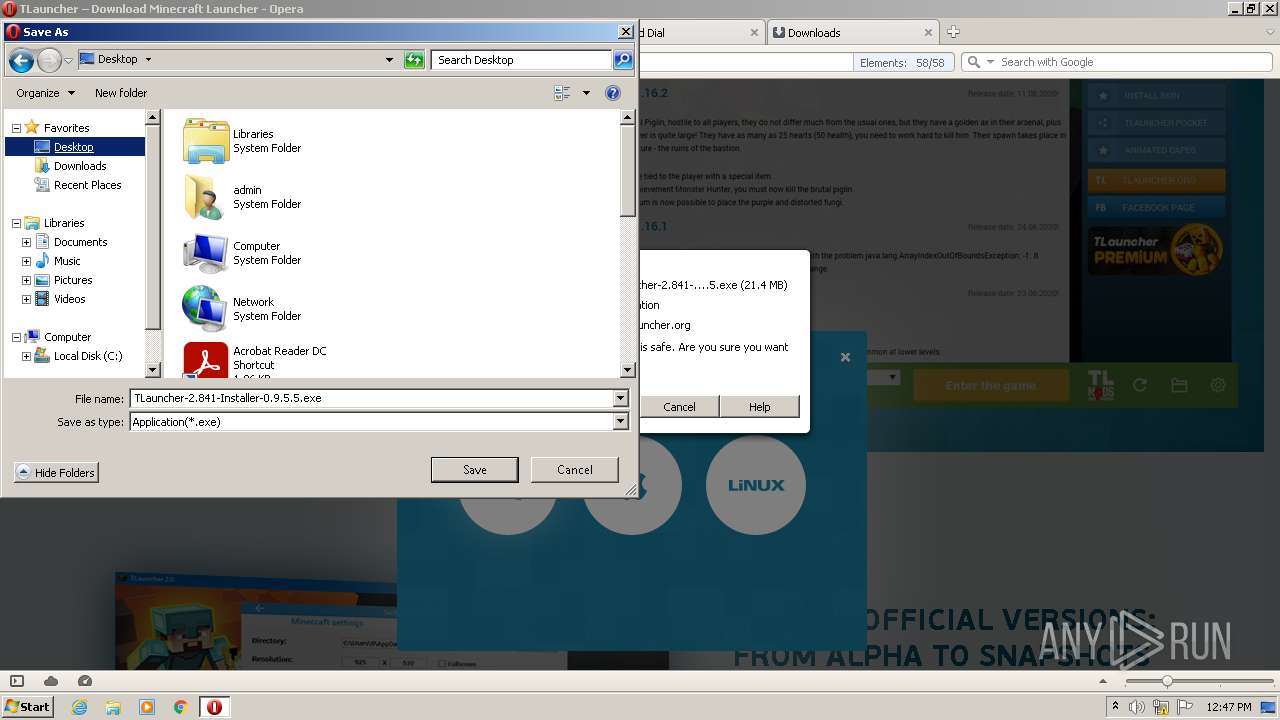
Manual execution by user
- mmc.exe (PID: 2076)
- mmc.exe (PID: 2600)
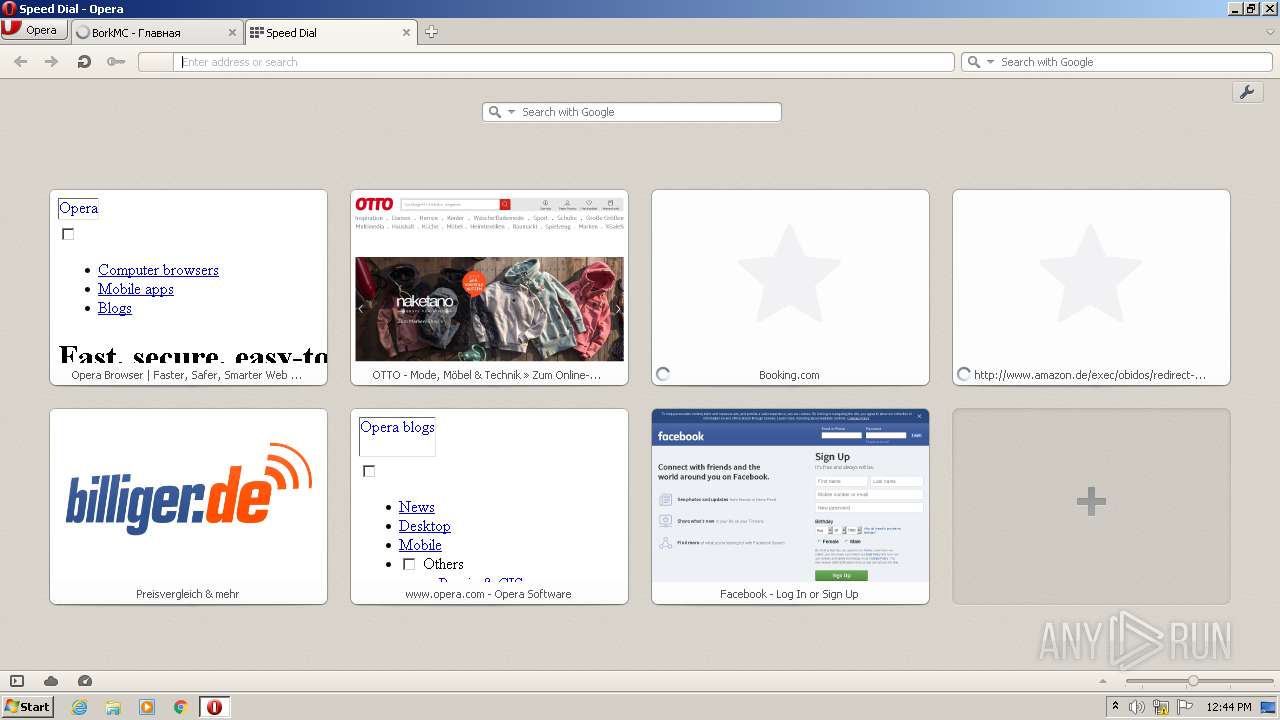
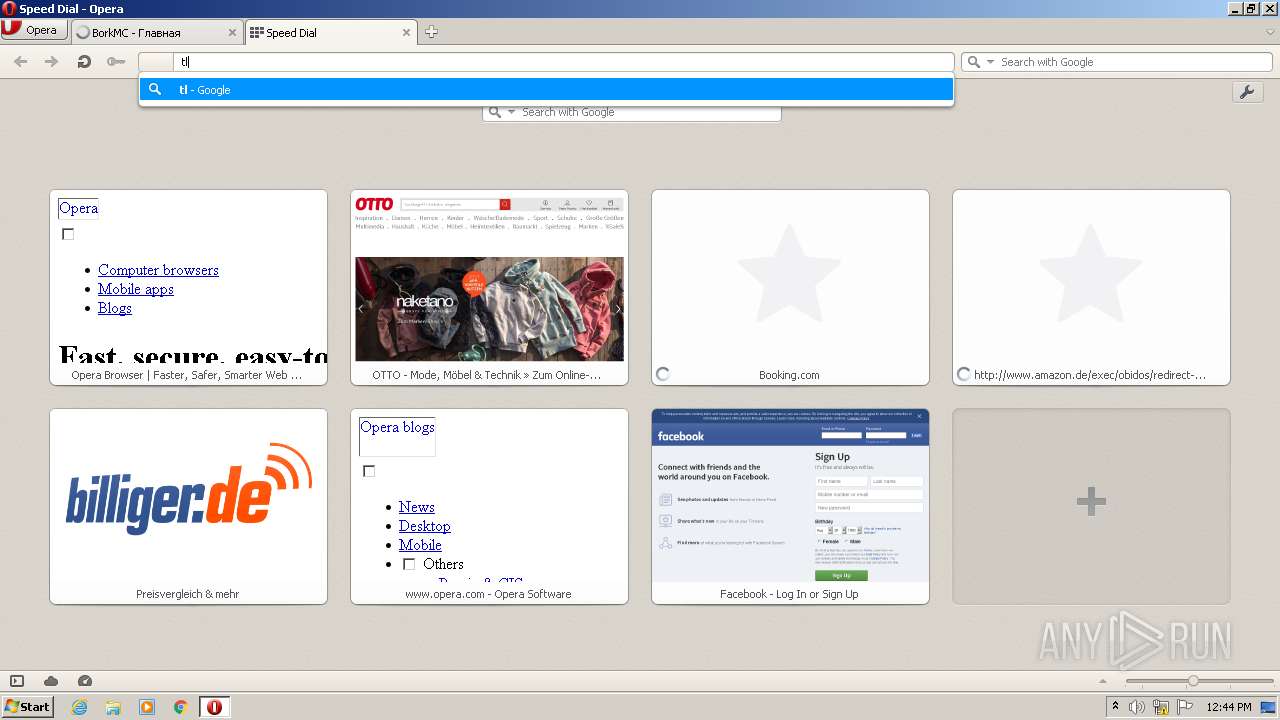
- opera.exe (PID: 2520)
Check for Java to be installed
- opera.exe (PID: 2520)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2520)
Reads the date of Windows installation
- opera.exe (PID: 2520)
Creates files in the user directory
- opera.exe (PID: 2520)
Checks Windows Trust Settings
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
Reads settings of System Certificates
- irsetup.exe (PID: 3808)
- irsetup.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31) |
| .scr | | | Windows screen saver (14.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1ca1e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 512 |
| CodeSize: | 94208 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2022:02:04 13:41:58+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Feb-2022 12:41:58 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 04-Feb-2022 12:41:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00016F64 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp0 | 0x0001A000 | 0x00000574 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp1 | 0x0001C000 | 0x0003341C | 0x00033600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59893 |
.reloc | 0x00050000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.122276 |
Imports
mscoree.dll |
Total processes
57
Monitored processes
12
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\AdditionalExecuteTL.exe" /S:C:\Users\admin\AppData\Local\Temp\setuparguments.ini | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\AdditionalExecuteTL.exe | irsetup.exe | ||||||||||||
User: admin Company: AdditionalExecuteTL Integrity Level: HIGH Description: AdditionalExecuteTL Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
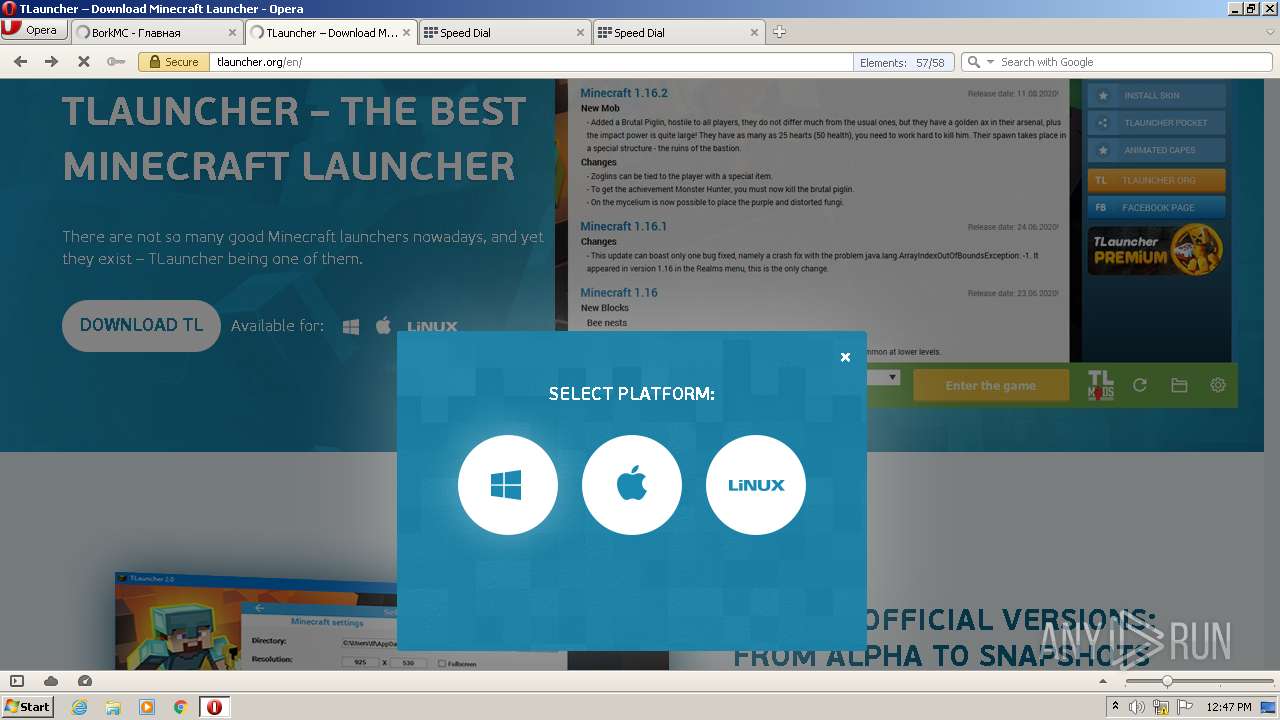
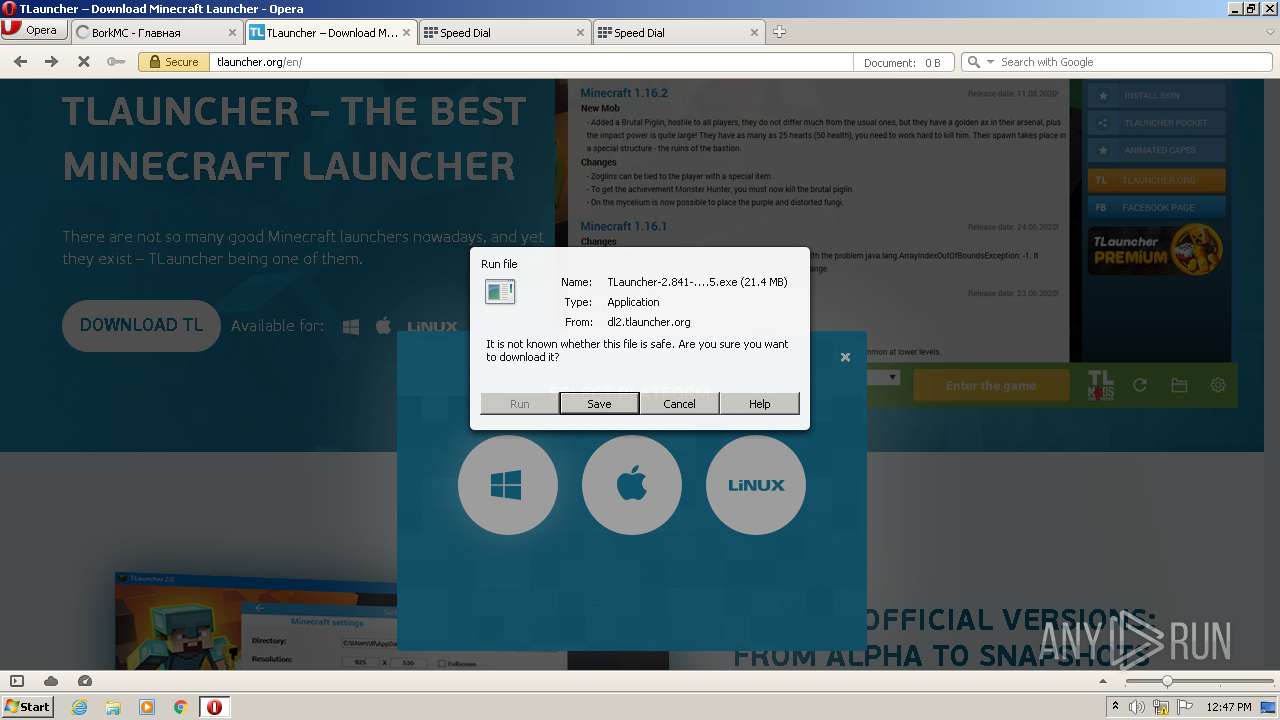
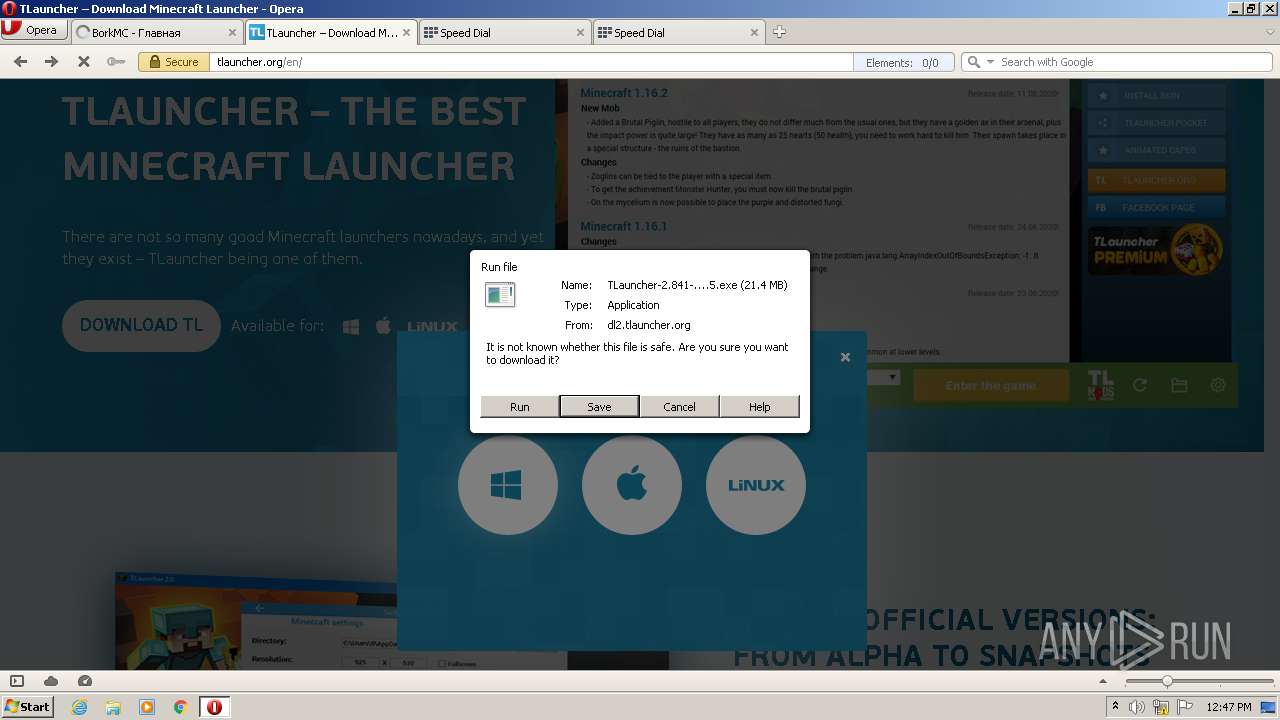
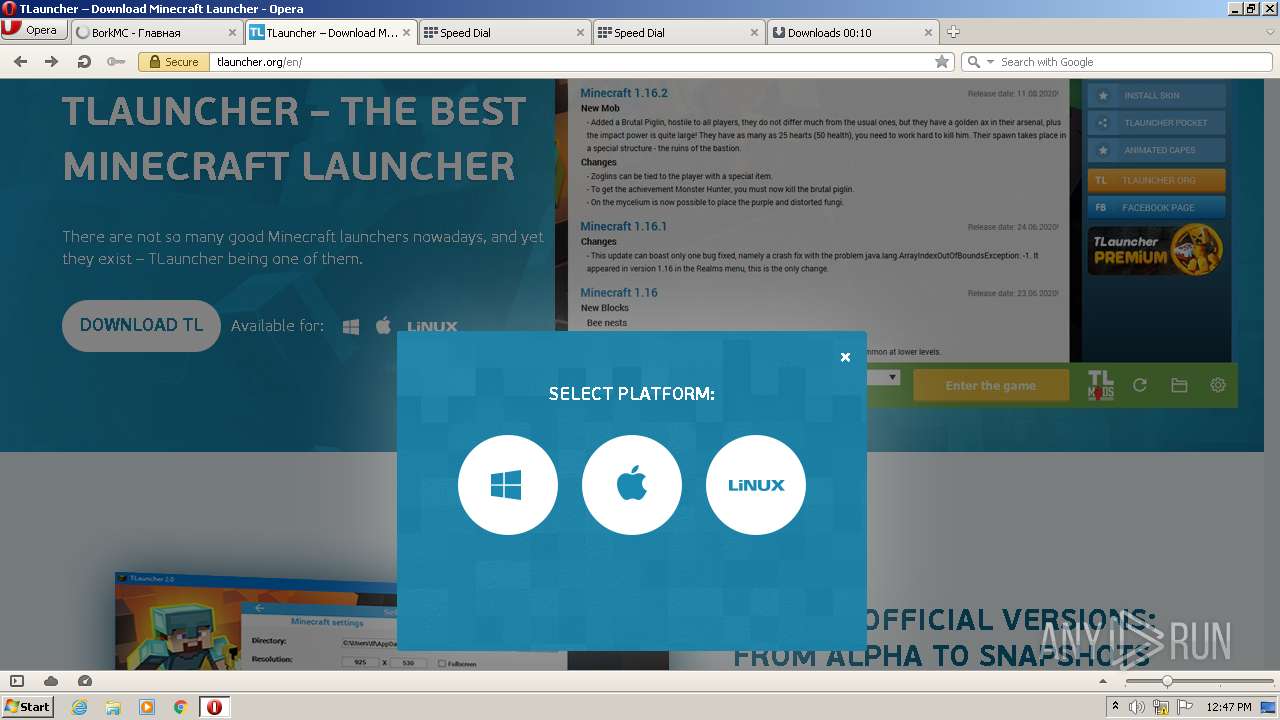
| 704 | "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\TLauncher-2.841-Installer-0.9.5.5.exe" | C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\TLauncher-2.841-Installer-0.9.5.5.exe | — | opera.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 3221226540 Version: 0.9.5.5 Modules
| |||||||||||||||
| 2076 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\AppData\Local\Temp\Server.vmp.exe" | C:\Users\admin\AppData\Local\Temp\Server.vmp.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2348 | netsh firewall delete allowedprogram "C:\Users\admin\AppData\Local\Temp\Server.vmp.exe" | C:\Windows\system32\netsh.exe | — | Server.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe" /S:C:\Users\admin\AppData\Local\Temp\setuparguments.ini __IRAOFF:1814730 "__IRAFN:C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\AdditionalExecuteTL.exe" "__IRCT:3" "__IRTSS:1839134" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe | AdditionalExecuteTL.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
| 2600 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\TLauncher-2.841-Installer-0.9.5.5.exe" | C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\TLauncher-2.841-Installer-0.9.5.5.exe | opera.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: HIGH Description: TLauncher Setup Exit code: 0 Version: 0.9.5.5 Modules
| |||||||||||||||
| 2892 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Local\Temp\Server.vmp.exe" "Server.vmp.exe" ENABLE | C:\Windows\system32\netsh.exe | — | Server.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 003
Read events
14 610
Write events
389
Delete events
4
Modification events
| (PID) Process: | (2300) Server.vmp.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | SEE_MASK_NOZONECHECKS |
Value: 1 | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (3628) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
Executable files
9
Suspicious files
69
Text files
504
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF548.tmp | text | |
MD5:6082DC09DCFA394D035CC5C53EF8ED97 | SHA256:9E00C3347A4FDD976C7BE933129B45F9F8697822341BE424AED7577A6F2F5090 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\g_0000\opr00004.tmp | text | |
MD5:5E9493D170163496A2FD843359D7E4C9 | SHA256:8F0B55231F12F1363DC0C4A33355999FB4482B5B1AF583D55220E54A4BA34D40 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:6082DC09DCFA394D035CC5C53EF8ED97 | SHA256:9E00C3347A4FDD976C7BE933129B45F9F8697822341BE424AED7577A6F2F5090 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:4C9A95FE61281C7BC0B2E0E7C0829C70 | SHA256:0327F69CC3EB9B0C7FA04613C2E1C5AD10B7BC4590315EC9E4EB8104F865BB99 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00003.tmp | xml | |
MD5:7966F3F842F1E41B71A94EE31B6DED29 | SHA256:1298A8BC01D74ACDDF2825B82EB242D005C0A816617A7E187FCC0B7BA8E23272 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DI8KFS5DE2DUT2DLE3RQ.temp | binary | |
MD5:3F7590FD56AC999E0289444034C9CC80 | SHA256:632F80B7AD1F589FE608EF8546E3E7D1B0501A9EC3E38C0140EA1C10ED3E602B | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:3F7590FD56AC999E0289444034C9CC80 | SHA256:632F80B7AD1F589FE608EF8546E3E7D1B0501A9EC3E38C0140EA1C10ED3E602B | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr2BDB.tmp | text | |
MD5:51205D01D5B84046D31609C0AF2FFAC9 | SHA256:3AC968E330302220E1DFF71304C2A6A4ECA9904F54341896CCA5BD0AB1BC8496 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\g_0000\opr00005.tmp | compressed | |
MD5:0A3345AE0BCD514214E468B97CBCE860 | SHA256:BCDB32A735D4564E8B5941716BA36300A5AC896E51F22AFE041C692384713FB3 | |||
| 2520 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprF598.tmp | xml | |
MD5:C69FEF6DFE05C19C922D39FBD5502F48 | SHA256:76CDD0BA1038F108E408861334DFFFC6D3D951E0DEC0A026CA3C8859C2671A1B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
153
TCP/UDP connections
163
DNS requests
45
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
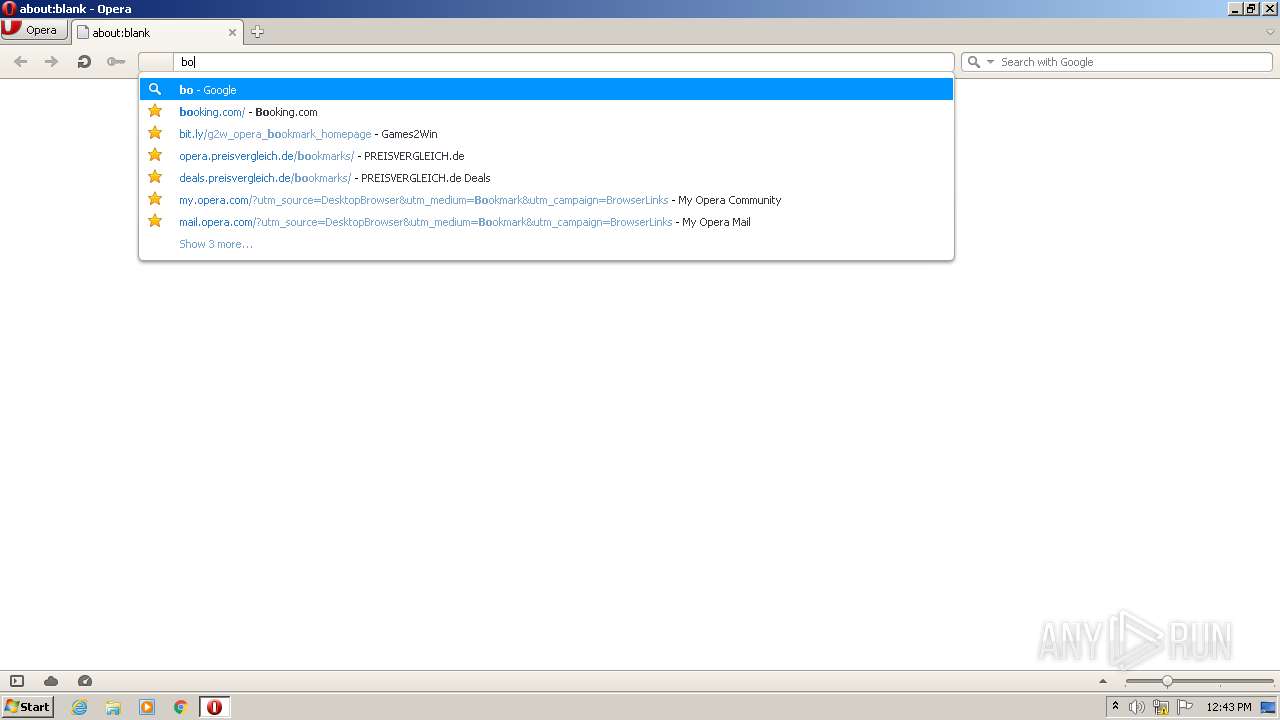
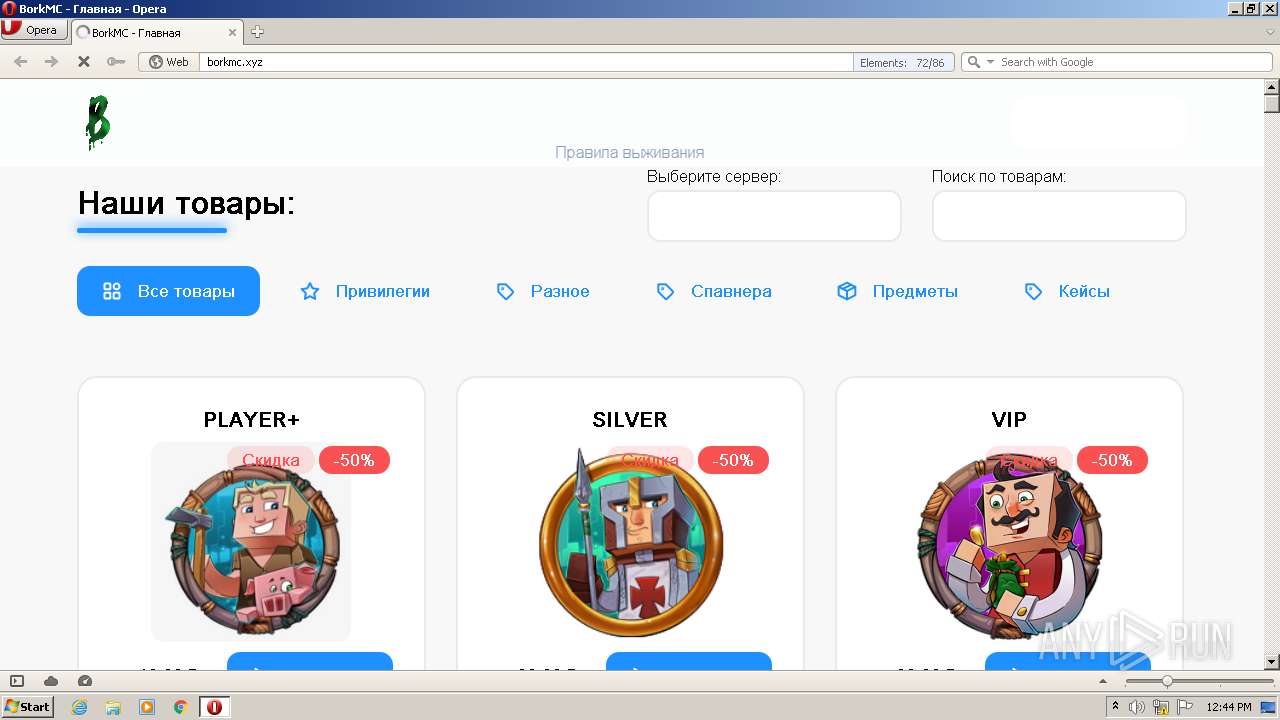
2520 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=bork&client=opera-suggest-omnibox&hl=de | US | text | 152 b | whitelisted |
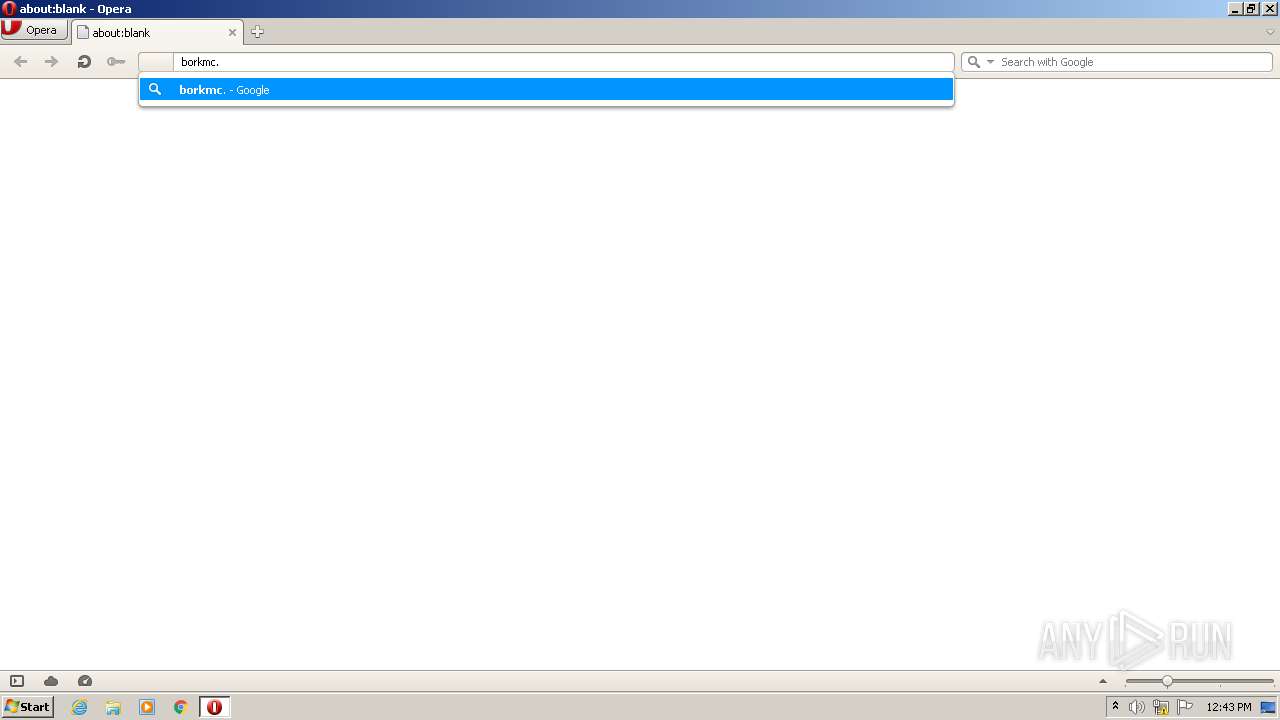
2520 | opera.exe | GET | 200 | 142.250.186.174:80 | http://clients1.google.com/complete/search?q=borkmc&client=opera-suggest-omnibox&hl=de | US | text | 84 b | whitelisted |
2520 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
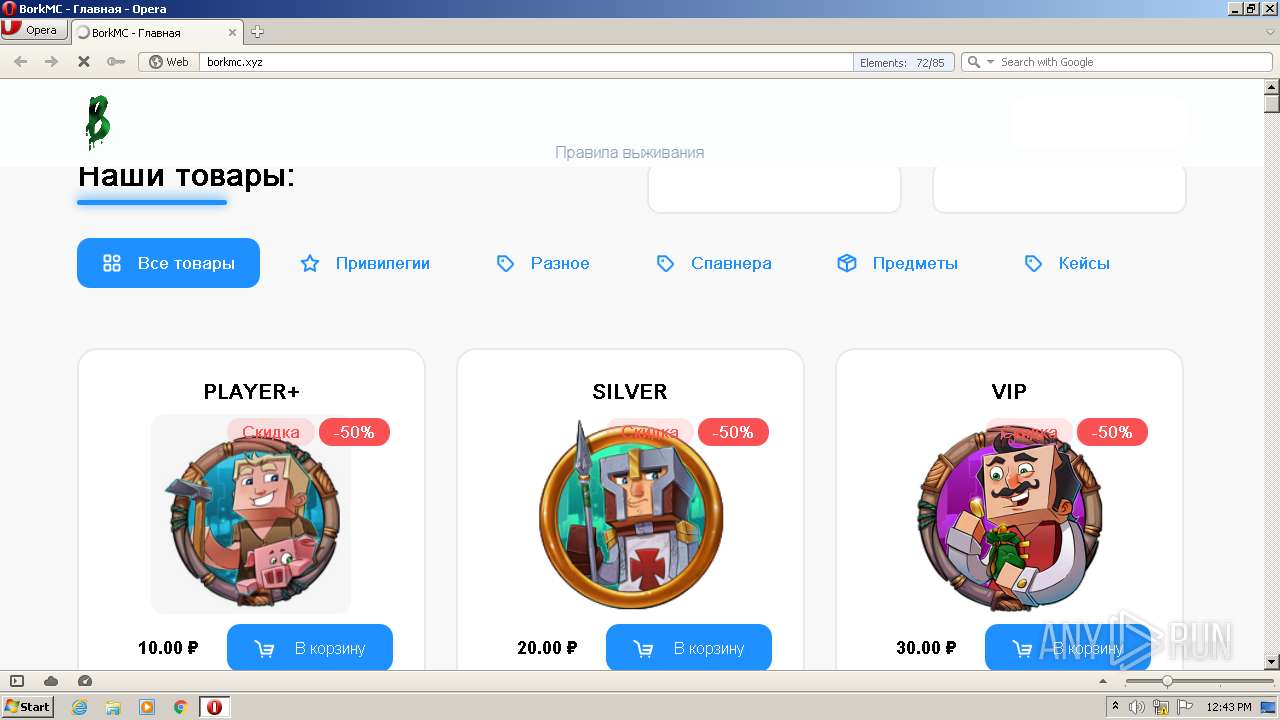
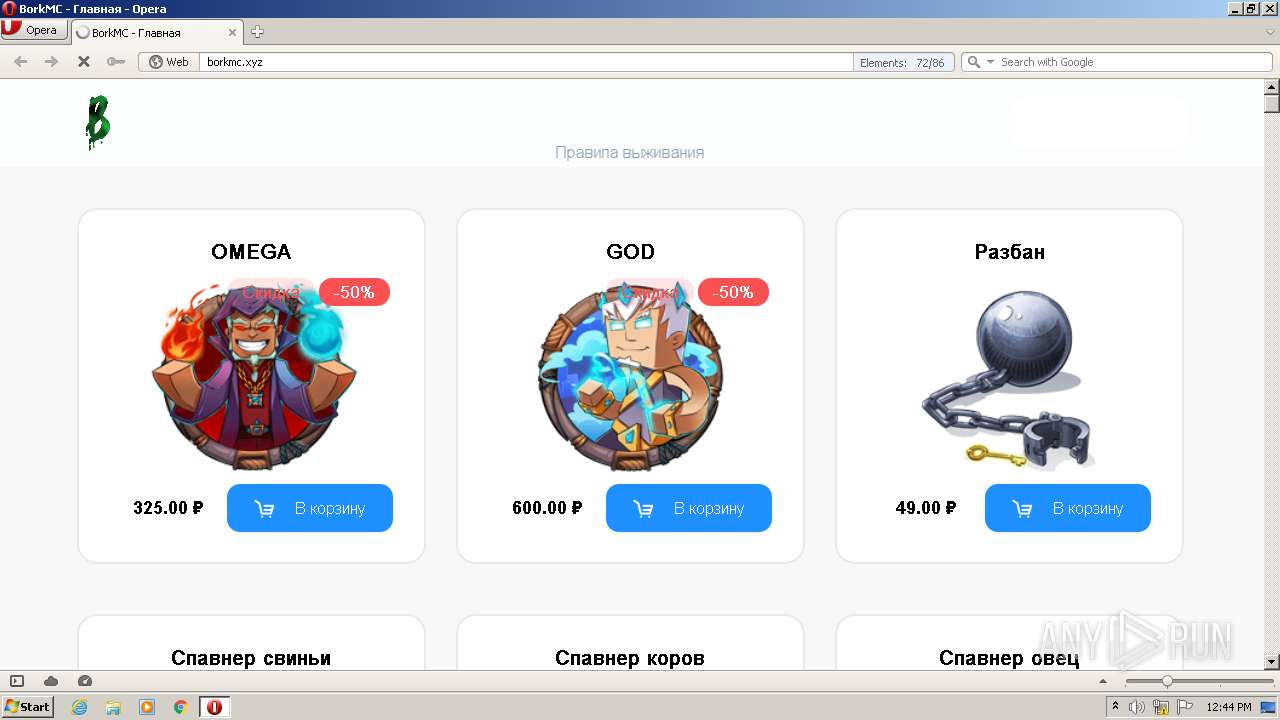
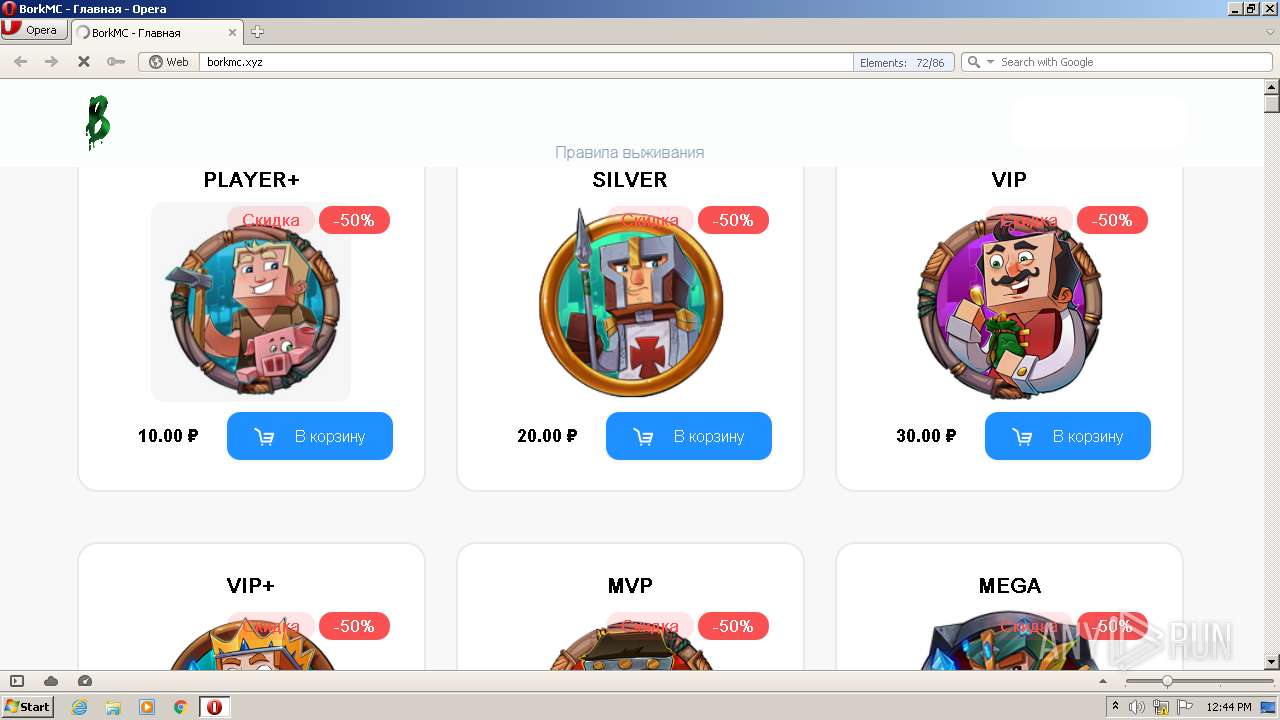
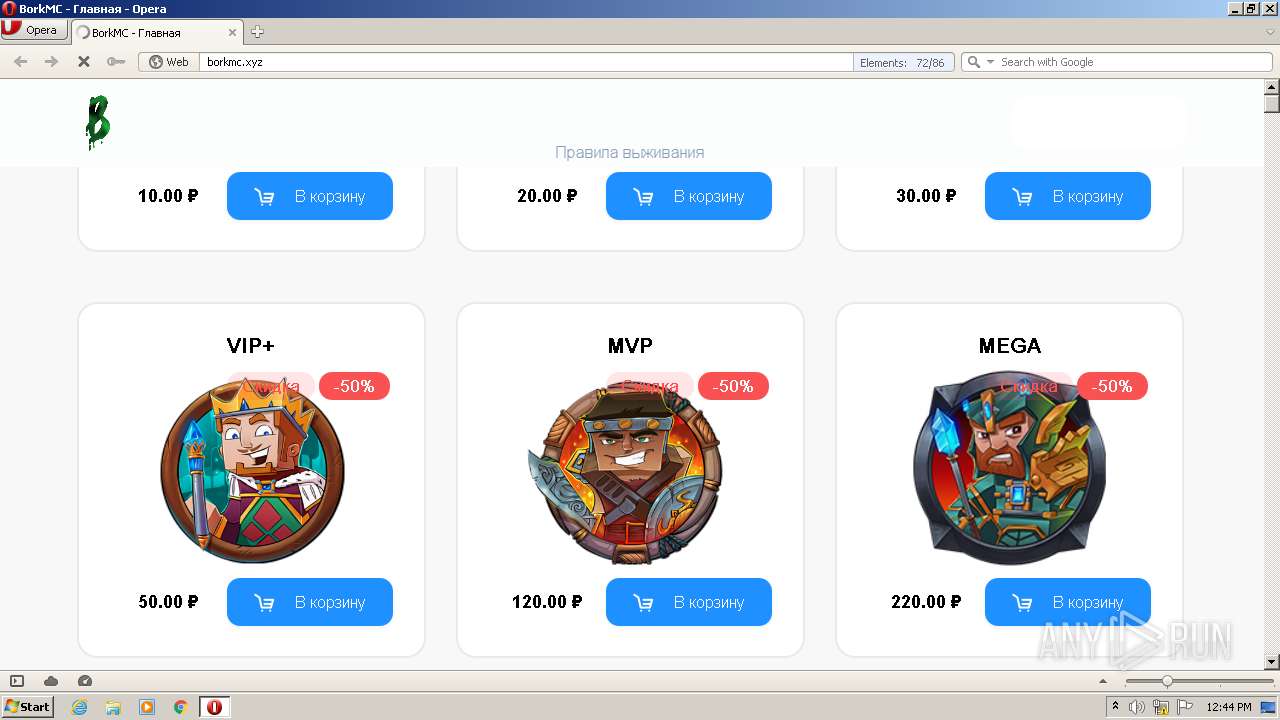
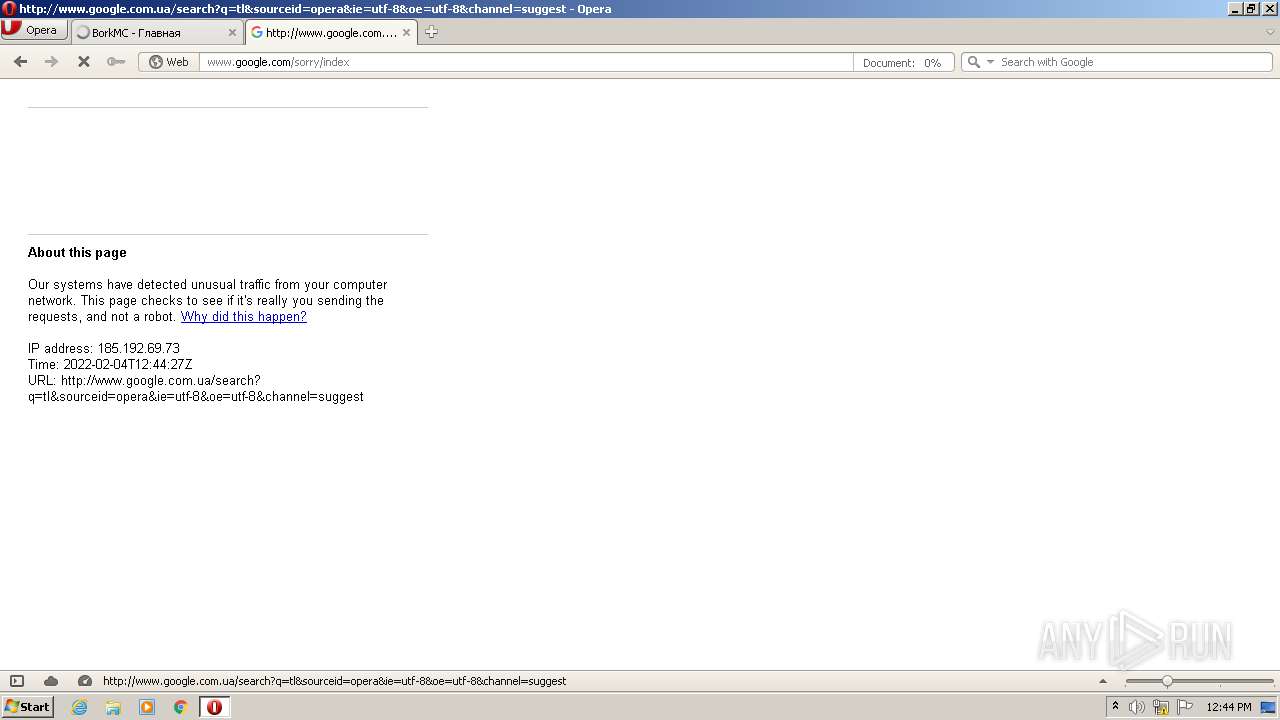
2520 | opera.exe | GET | — | 195.18.27.10:80 | http://borkmc.xyz/ | RU | — | — | suspicious |
2520 | opera.exe | GET | — | 195.18.27.10:80 | http://borkmc.xyz/themes/limbo/assets/js/jquery.min.js | RU | — | — | suspicious |
2520 | opera.exe | GET | — | 195.18.27.10:80 | http://borkmc.xyz/themes/limbo/assets/images/payment-types/applepay.svg | RU | — | — | suspicious |
2520 | opera.exe | GET | 200 | 195.18.27.10:80 | http://borkmc.xyz/themes/limbo/assets/images/icons/arrow-right.svg | RU | html | 13.9 Kb | suspicious |
2520 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=borkmc.xyz&hdn=j3GHryjMOK9RfEwjHIRq2Q== | unknown | html | 150 b | whitelisted |
2520 | opera.exe | GET | — | 195.18.27.10:80 | http://borkmc.xyz/plugins/dontfollow/easydonate/assets/js/payment.js?v=6 | RU | — | — | suspicious |
2520 | opera.exe | GET | — | 195.18.27.10:80 | http://borkmc.xyz/modules/system/assets/js/framework.js | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2520 | opera.exe | 2.16.186.10:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
2520 | opera.exe | 23.45.105.185:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
2520 | opera.exe | 2.16.186.35:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
— | — | 195.18.27.10:80 | borkmc.xyz | SvyazEnergoStroy Ltd | RU | suspicious |
2520 | opera.exe | 185.26.182.109:80 | redir.opera.com | Opera Software AS | — | unknown |
2520 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2520 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2520 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2520 | opera.exe | 142.250.186.174:80 | clients1.google.com | Google Inc. | US | whitelisted |
2520 | opera.exe | 195.18.27.10:80 | borkmc.xyz | SvyazEnergoStroy Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
borkmc.xyz |
| suspicious |
sitecheck2.opera.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cp.easydonate.ru |
| unknown |
vk.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
crl.globalsign.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2520 | opera.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |