| File name: | 连接驱动.exe |
| Full analysis: | https://app.any.run/tasks/9ba762ff-8a0d-49dc-bd69-fcb7b0b0555d |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2025, 08:59:14 |
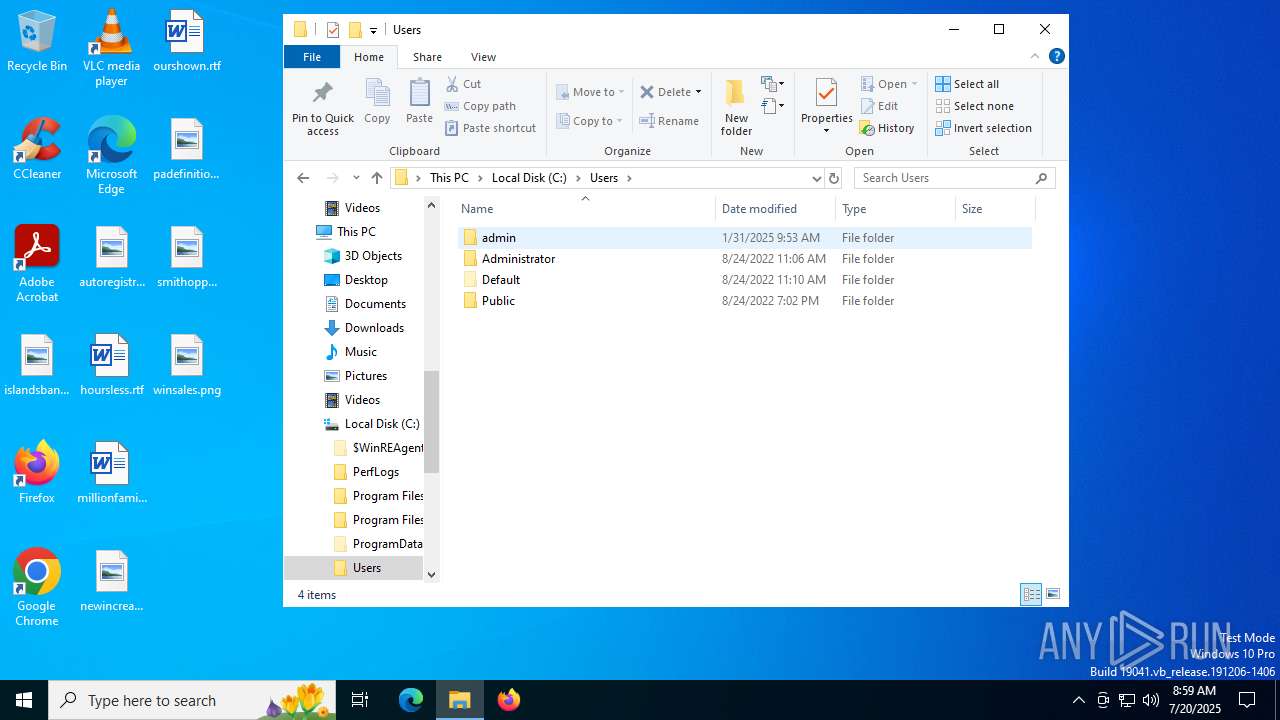
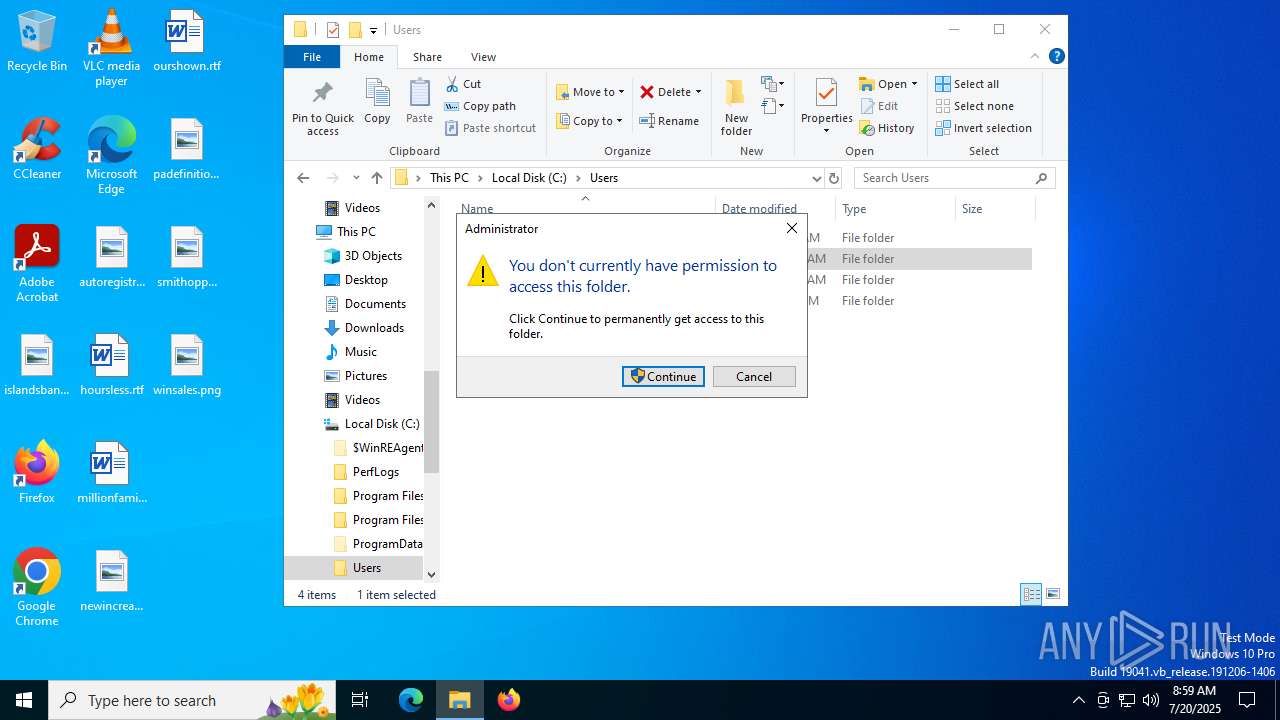
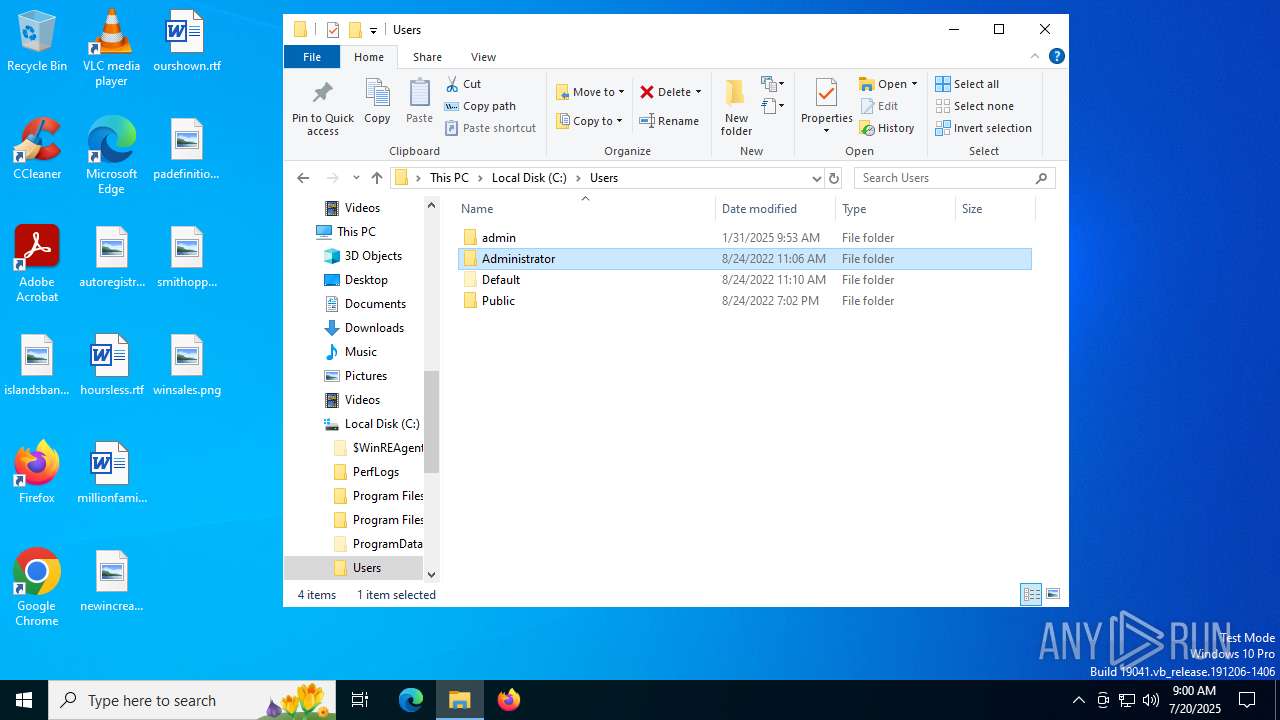
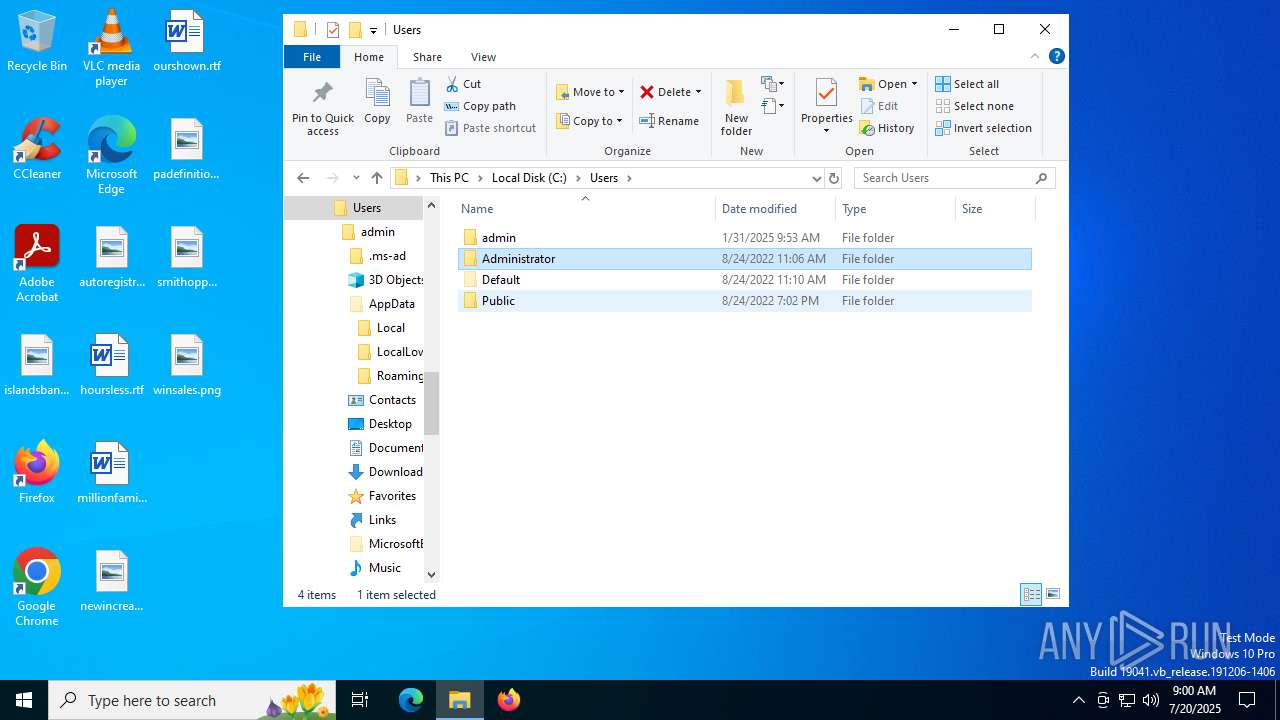
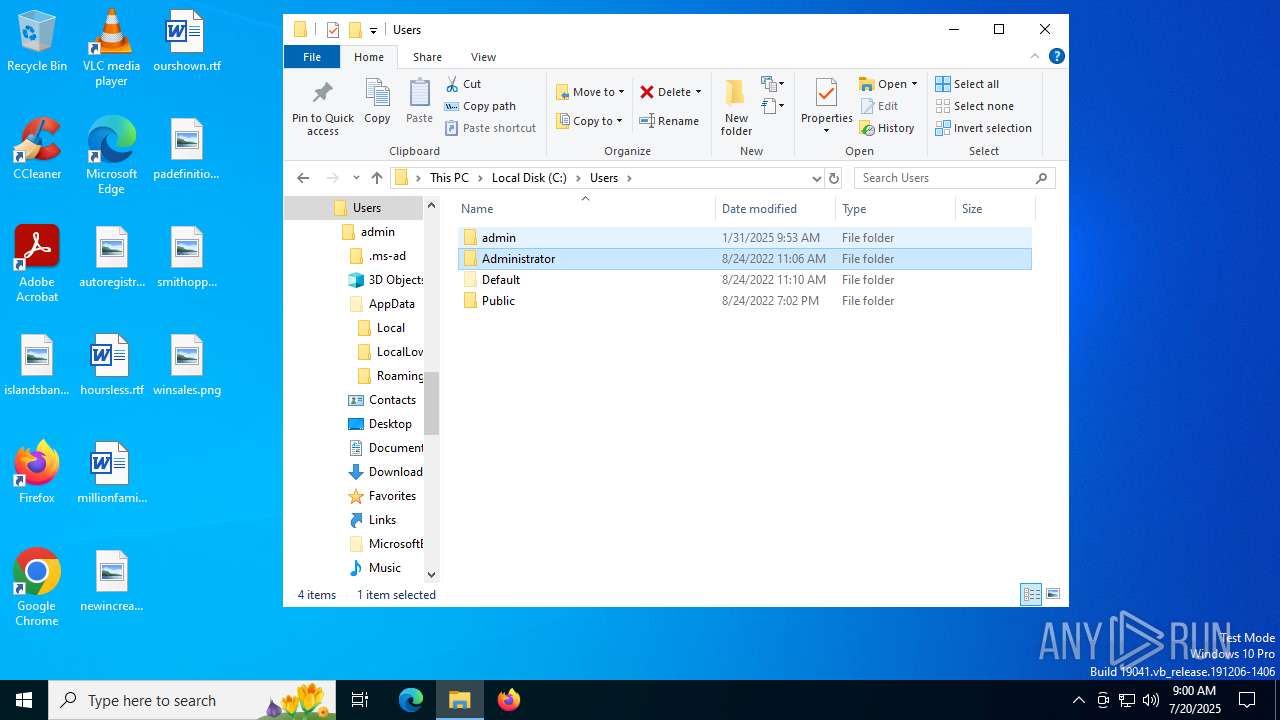
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 24375E87EF4115E3C390AD70417A450E |
| SHA1: | E7B66B9C25D4D343389F186D061E45D2C055DDB9 |
| SHA256: | 8DD0CADA7DA0C8A62A0A28FF38C9ECF82DC507259B2F53B709152DA2FB18B818 |
| SSDEEP: | 49152:pHmu9sF1YCpW1wmnBDpfiX4OmwPGiUtqQVvS:wuuFfpW1w8Bh5whUtS |
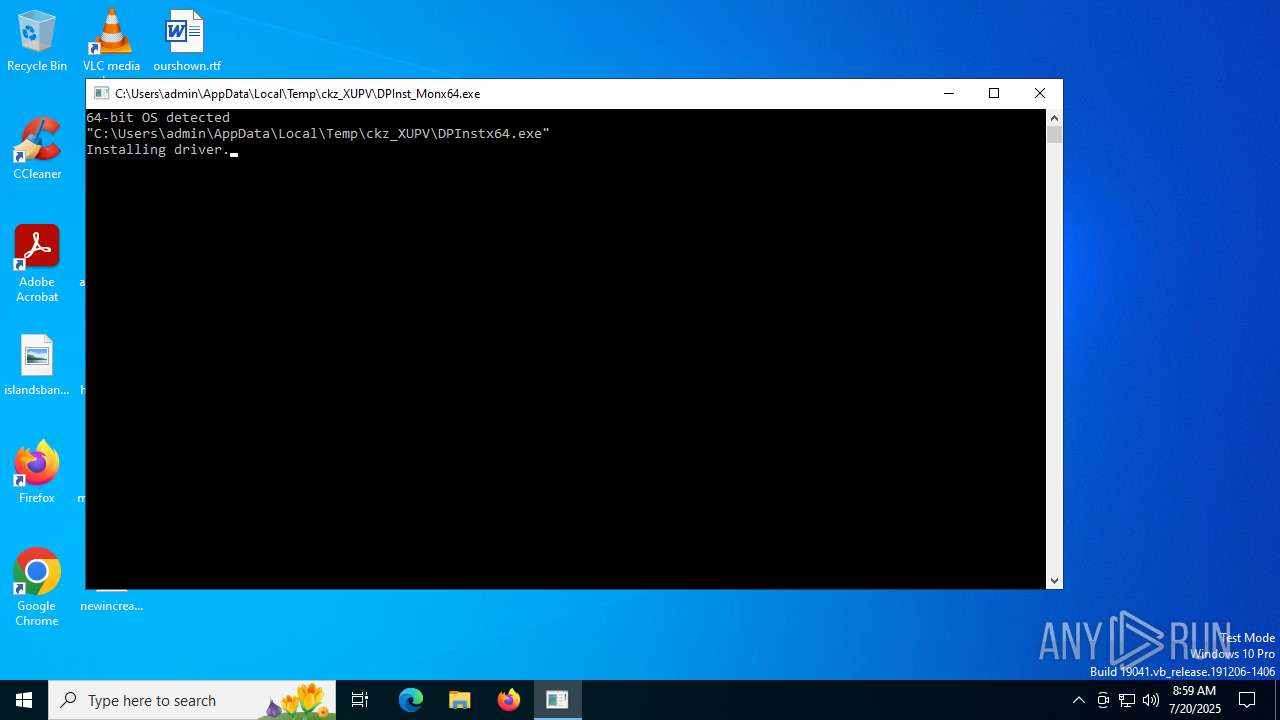
MALICIOUS
Executing a file with an untrusted certificate
- 连接驱动.exe (PID: 5716)
- DPInst_Monx64.exe (PID: 6292)
- OS_Detect.exe (PID: 3656)
- OS_Detect.exe (PID: 2964)
- DPInstx64.exe (PID: 72)
SUSPICIOUS
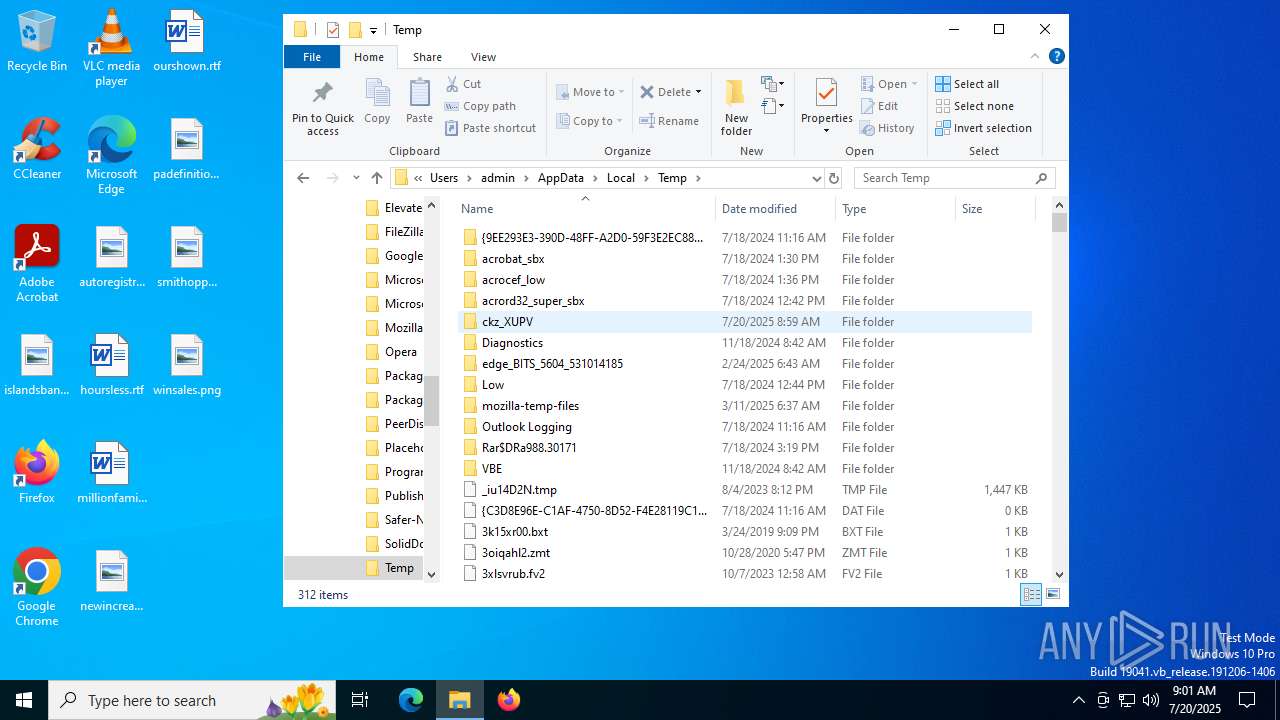
Drops a system driver (possible attempt to evade defenses)
- 连接驱动.exe (PID: 5716)
- DPInstx64.exe (PID: 72)
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
Executable content was dropped or overwritten
- 连接驱动.exe (PID: 5716)
- DPInstx64.exe (PID: 72)
- drvinst.exe (PID: 4100)
- drvinst.exe (PID: 6160)
Process drops legitimate windows executable
- 连接驱动.exe (PID: 5716)
Reads security settings of Internet Explorer
- 连接驱动.exe (PID: 5716)
- DPInst_Monx64.exe (PID: 6292)
- OS_Detect.exe (PID: 3656)
Reads the date of Windows installation
- DPInst_Monx64.exe (PID: 6292)
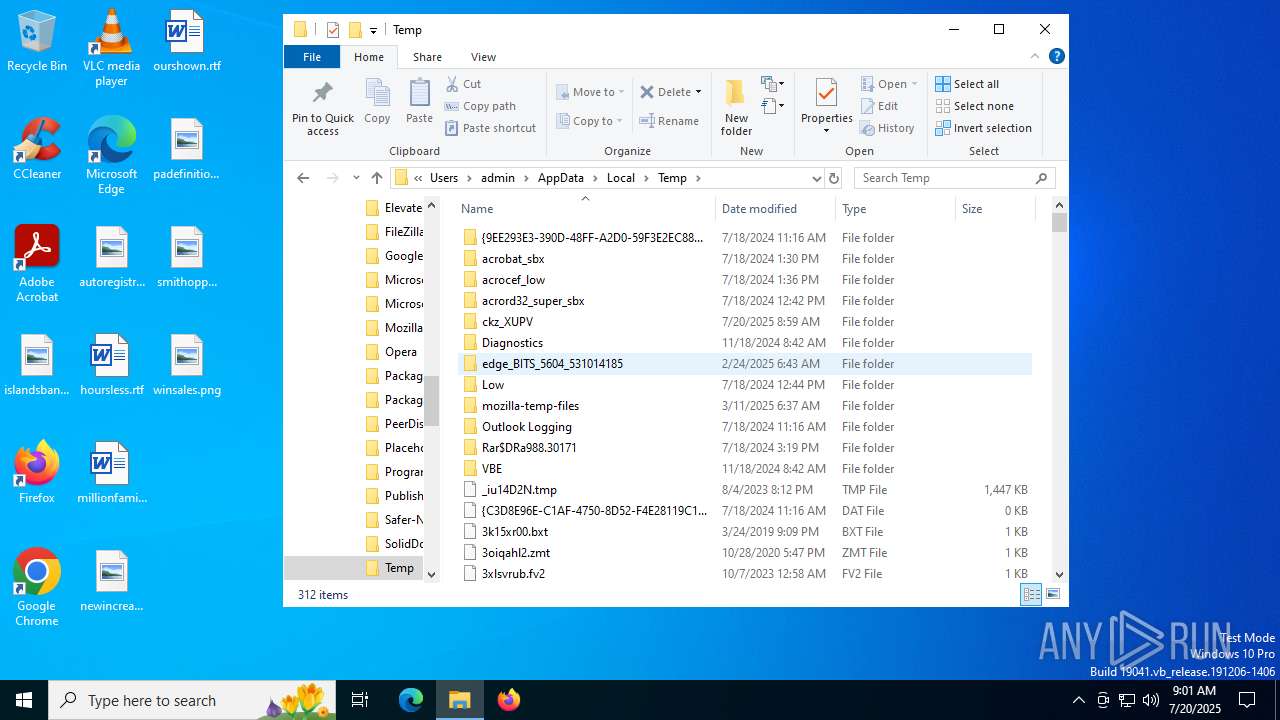
Starts a Microsoft application from unusual location
- DPInstx64.exe (PID: 72)
Creates files in the driver directory
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
INFO
The sample compiled with english language support
- 连接驱动.exe (PID: 5716)
- DPInstx64.exe (PID: 72)
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
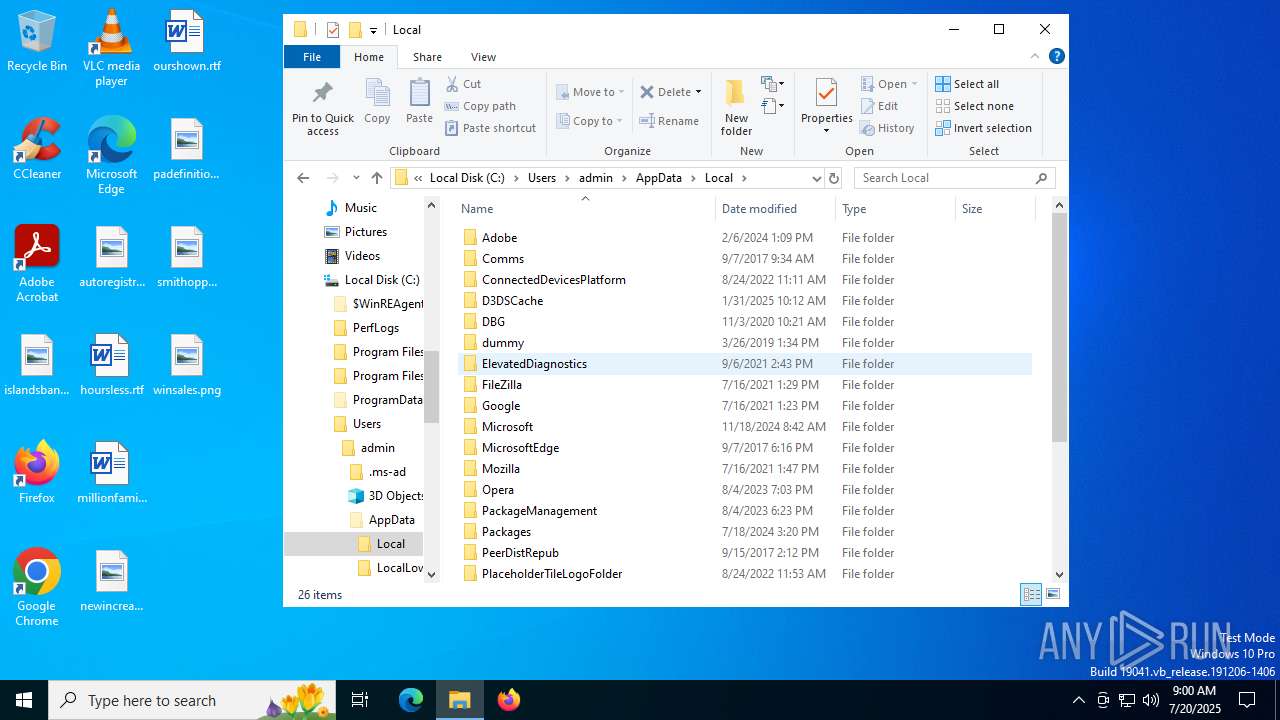
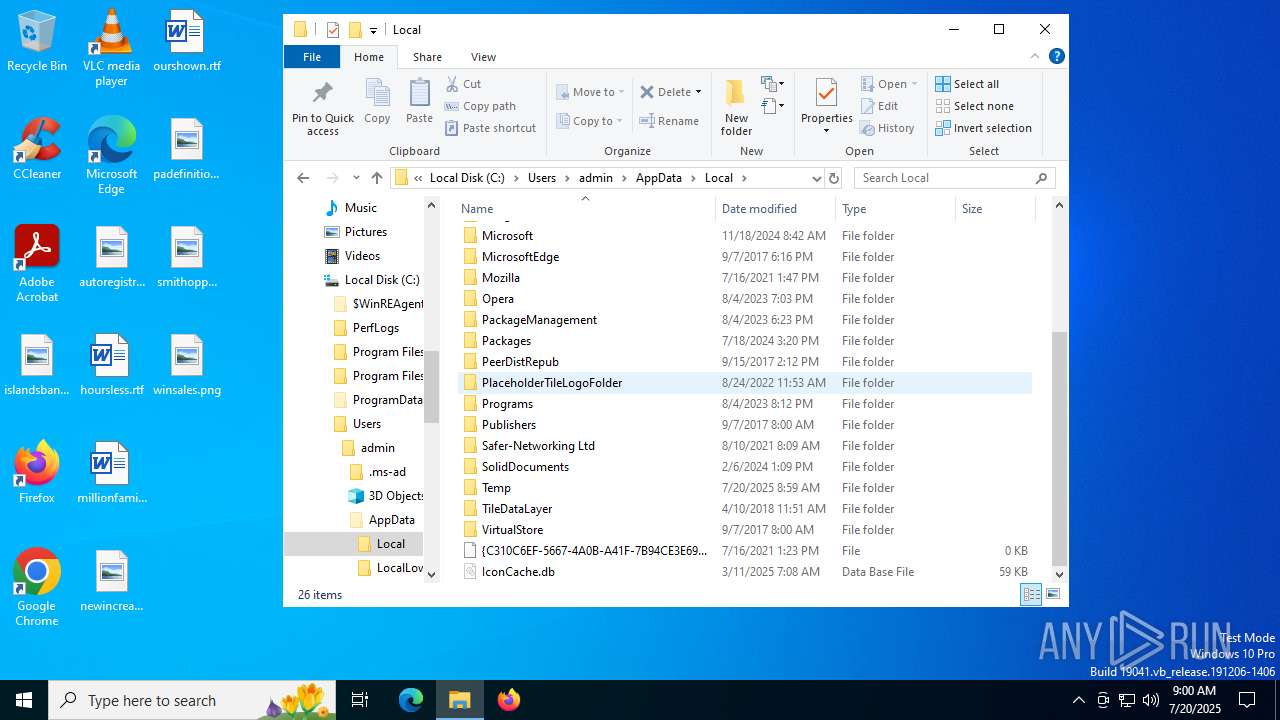
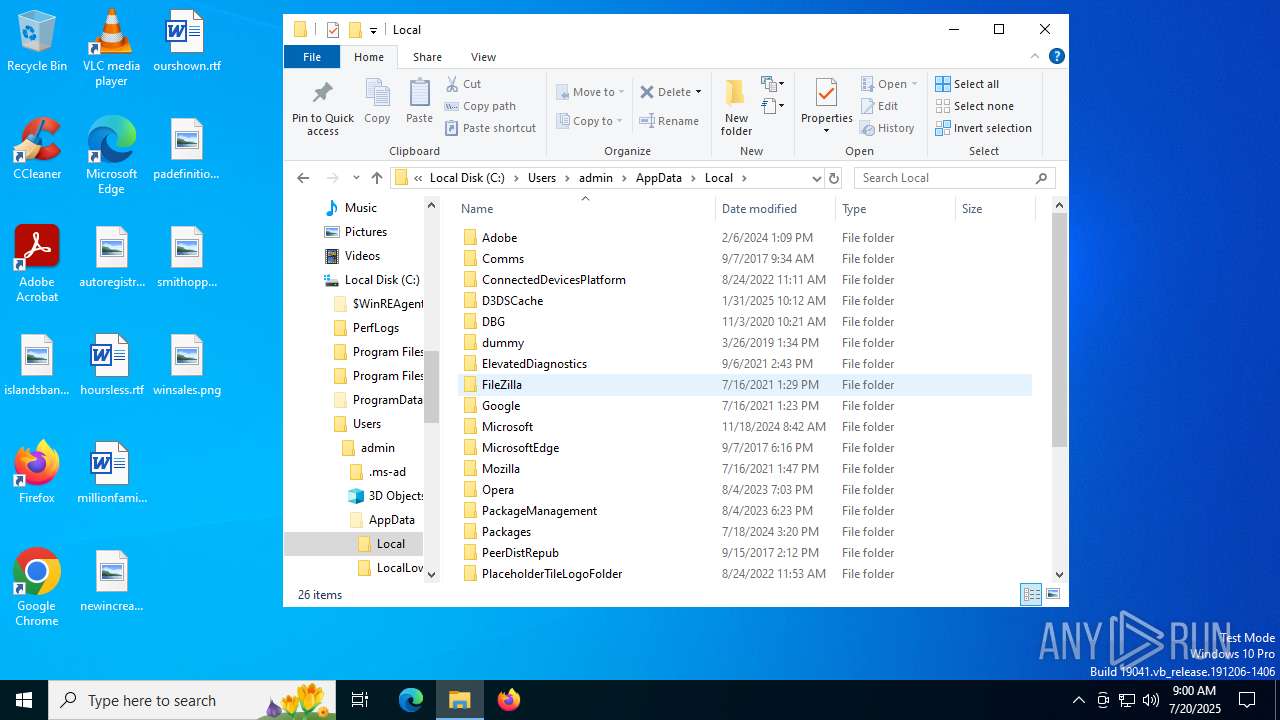
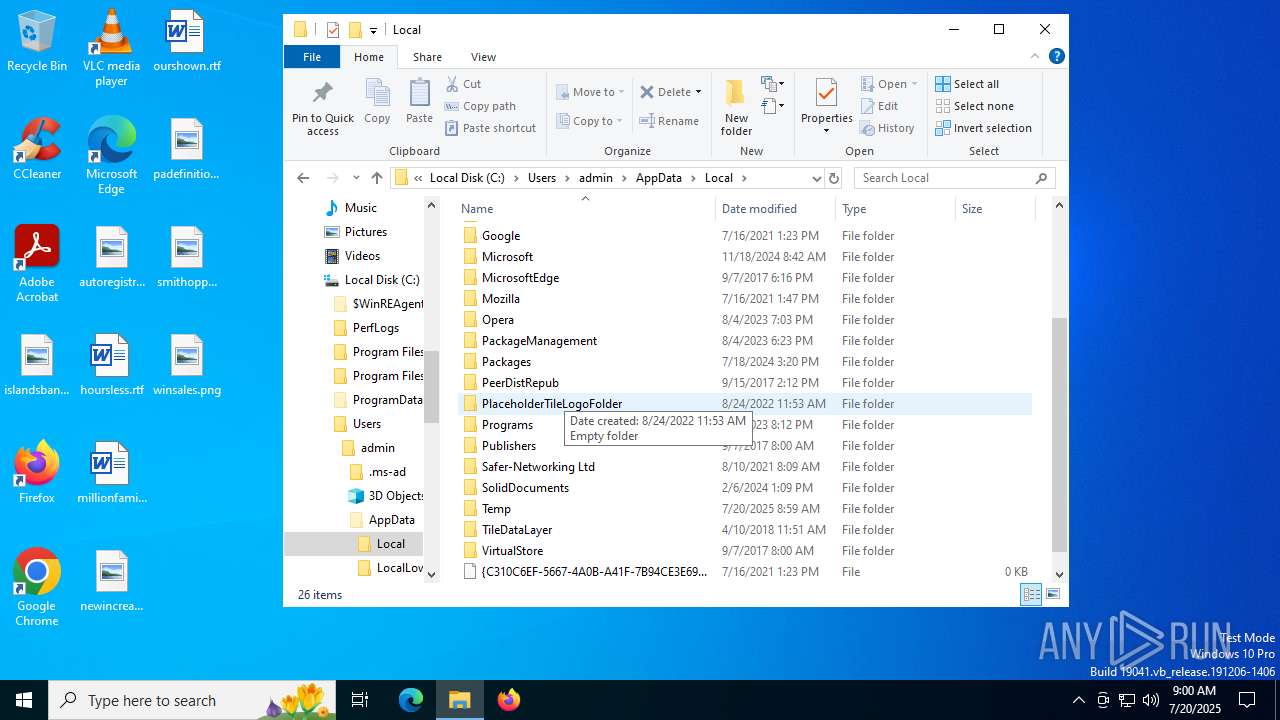
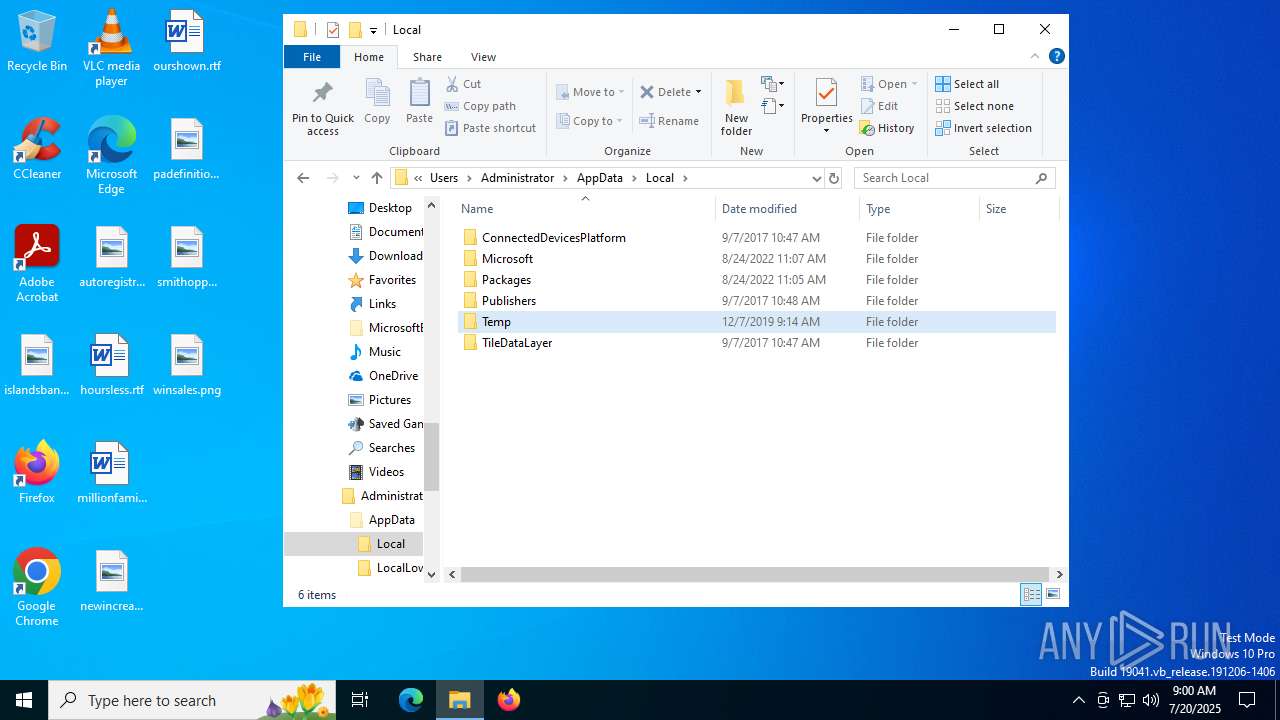
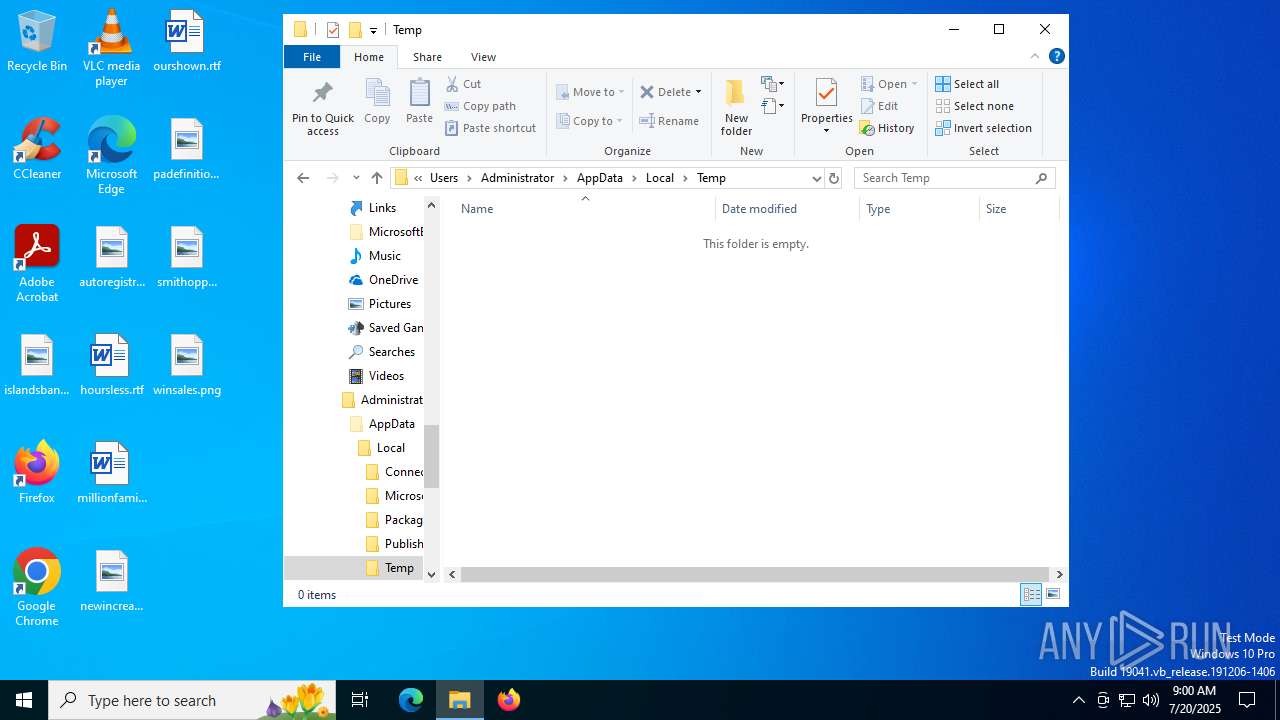
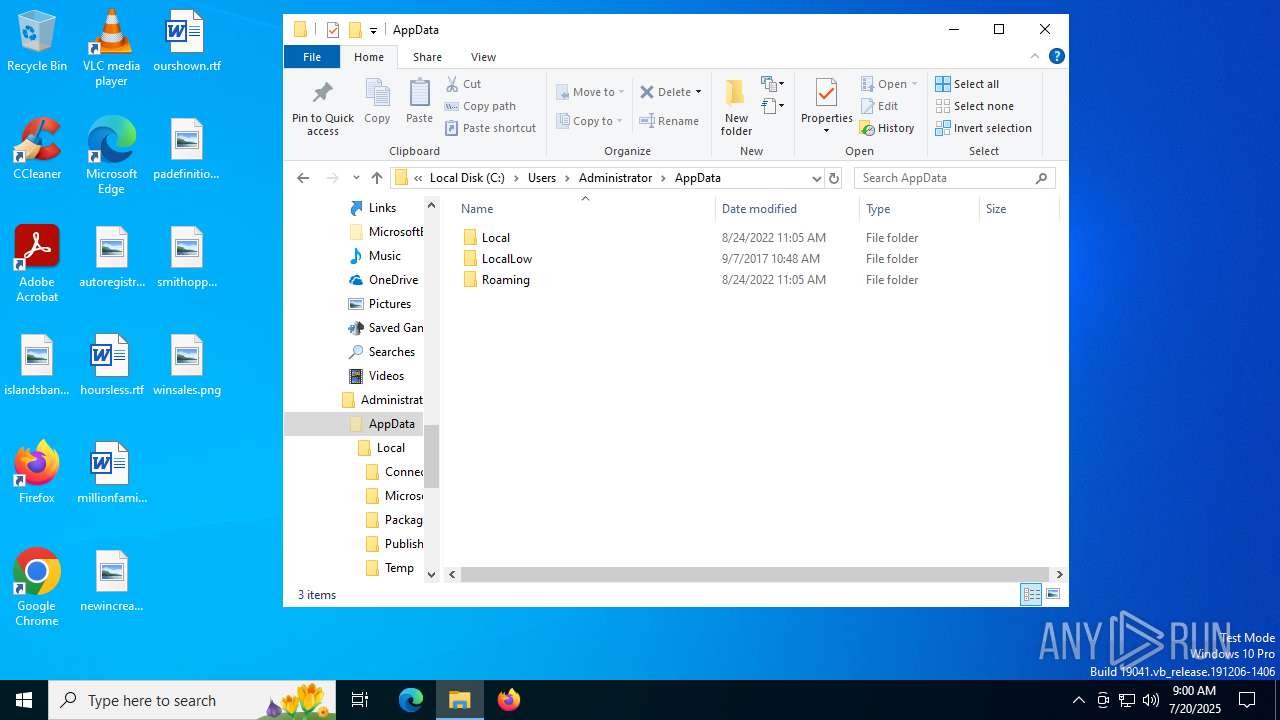
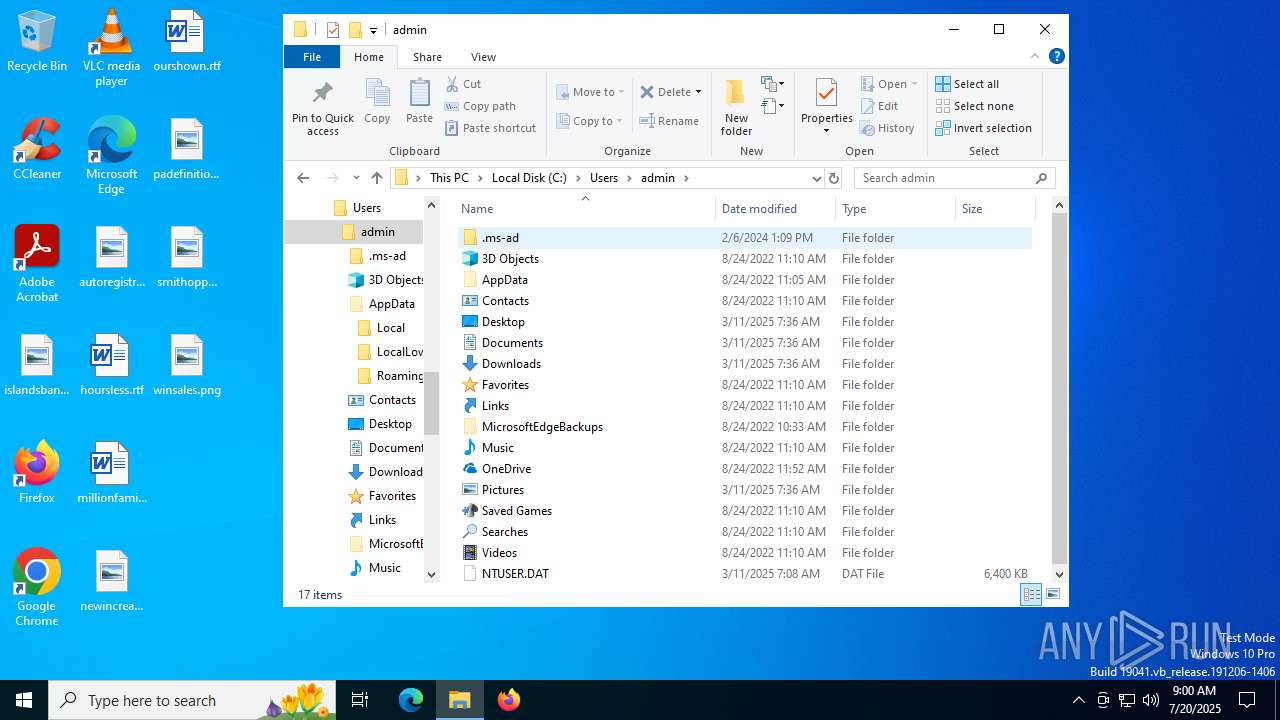
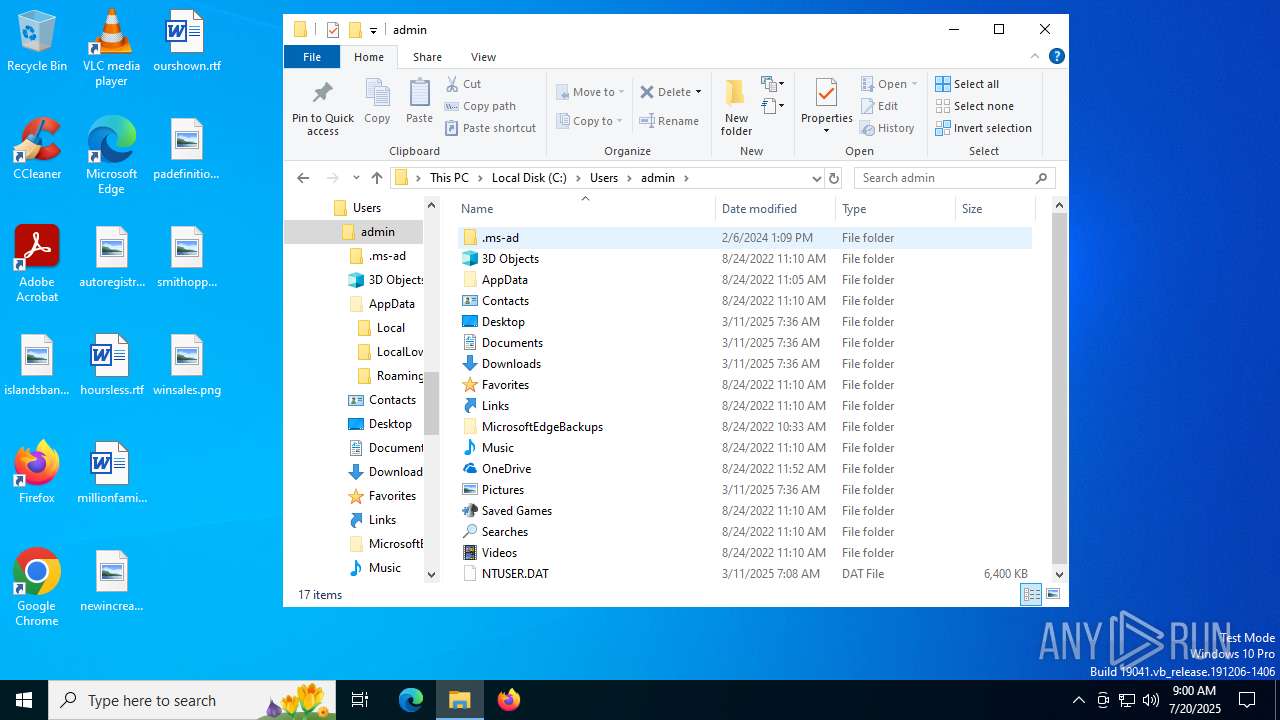
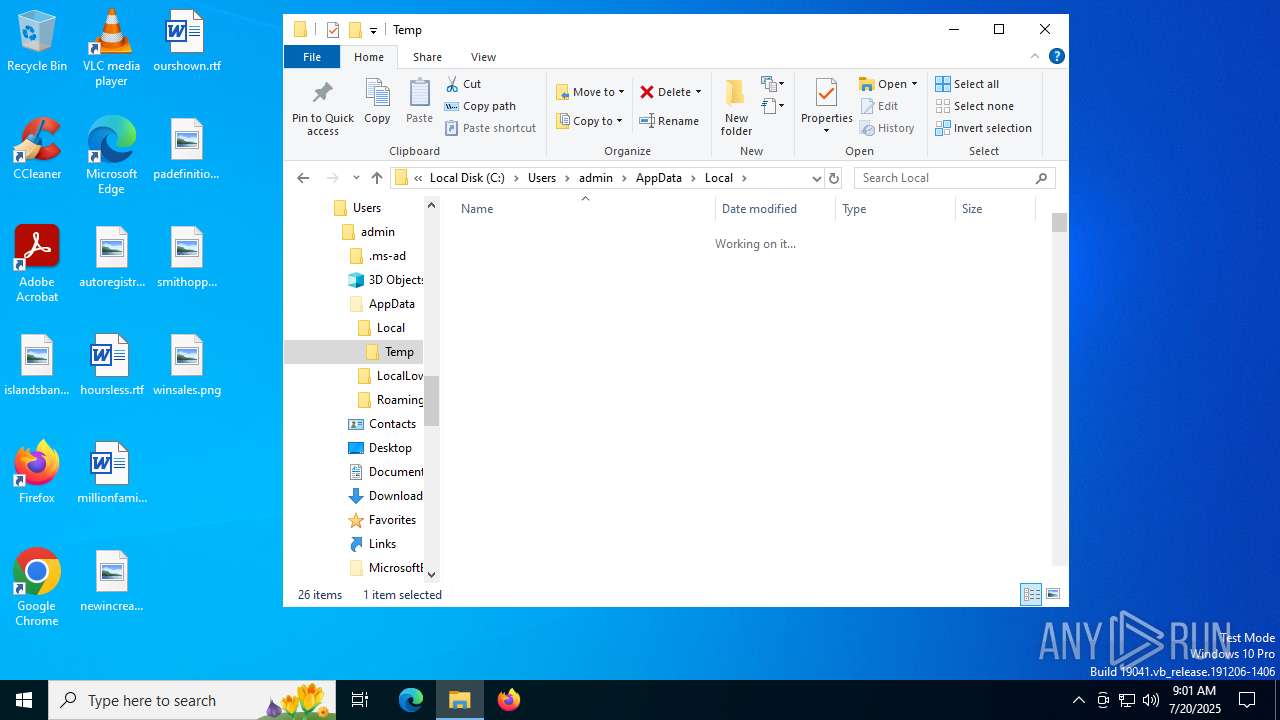
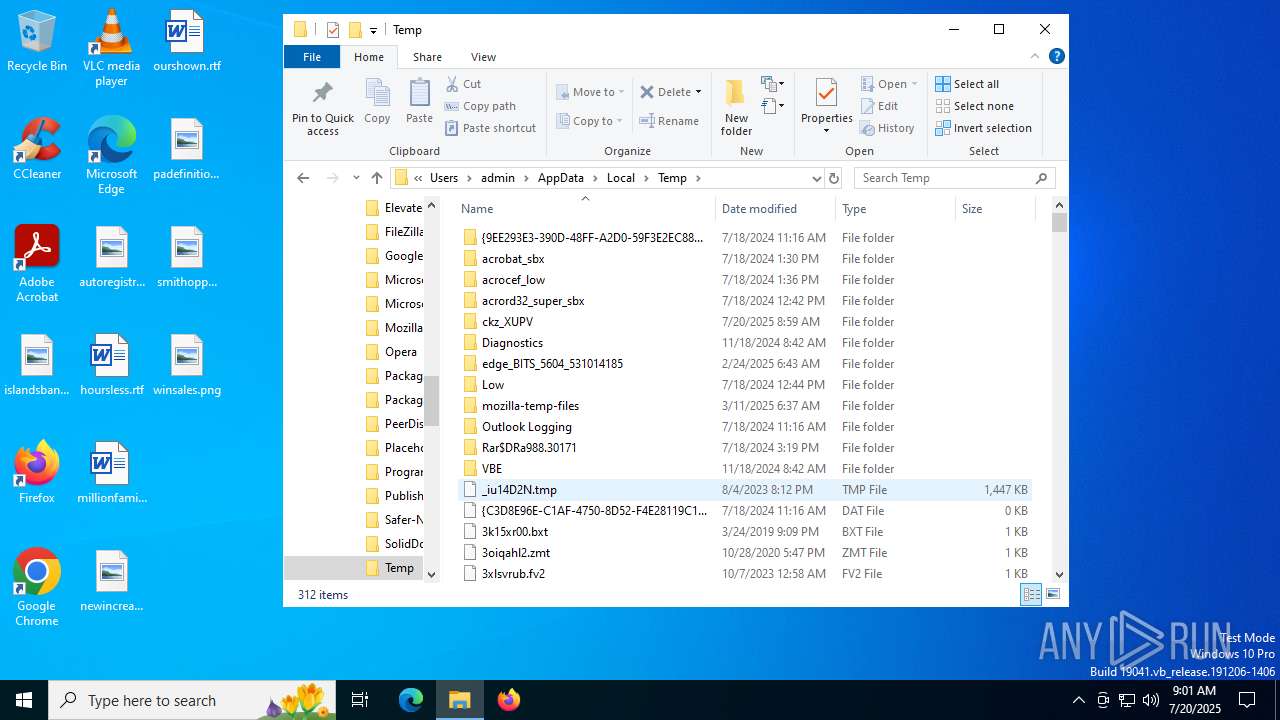
Create files in a temporary directory
- 连接驱动.exe (PID: 5716)
- DPInstx64.exe (PID: 72)
Process checks computer location settings
- 连接驱动.exe (PID: 5716)
- DPInst_Monx64.exe (PID: 6292)
- OS_Detect.exe (PID: 3656)
Reads the computer name
- 连接驱动.exe (PID: 5716)
- DPInst_Monx64.exe (PID: 6292)
- DPInstx64.exe (PID: 72)
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
- OS_Detect.exe (PID: 3656)
Checks supported languages
- 连接驱动.exe (PID: 5716)
- DPInst_Monx64.exe (PID: 6292)
- DPInstx64.exe (PID: 72)
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
- OS_Detect.exe (PID: 3656)
Reads the machine GUID from the registry
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
Reads the software policy settings
- drvinst.exe (PID: 6160)
- drvinst.exe (PID: 4100)
- slui.exe (PID: 2384)
Checks proxy server information
- slui.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:06:19 14:53:02+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 249856 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1add4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
152
Monitored processes
12
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
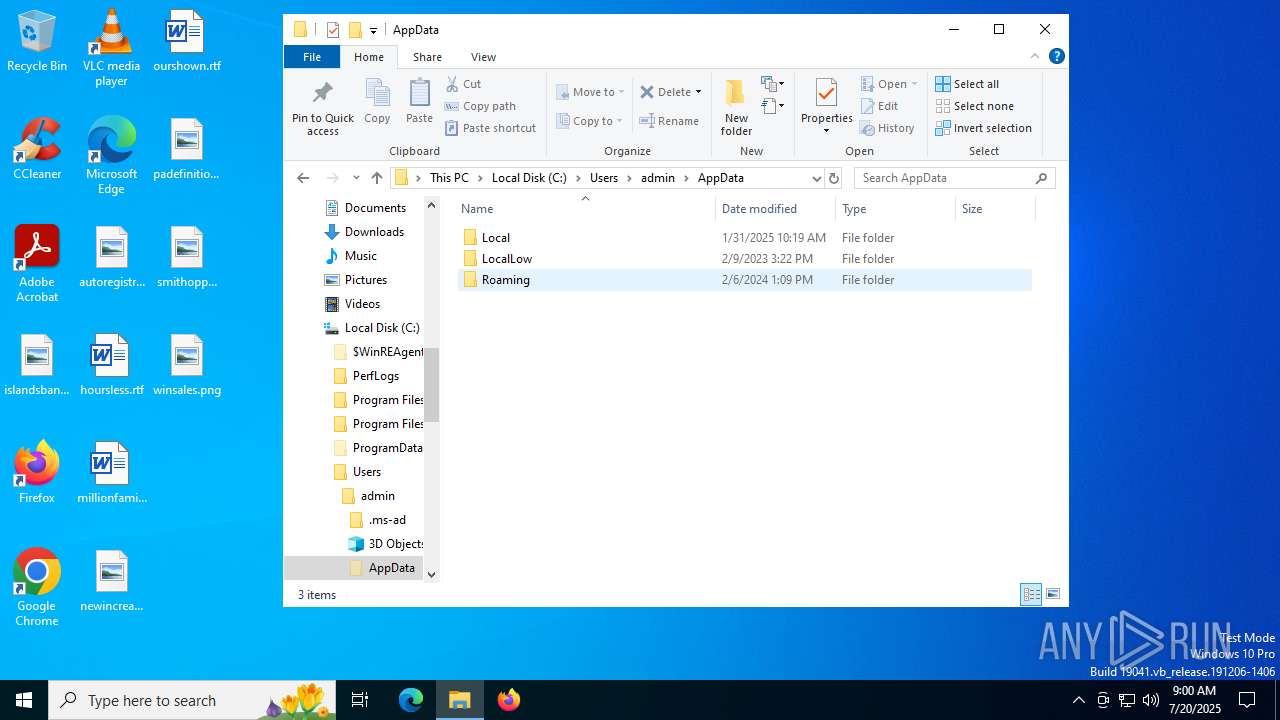
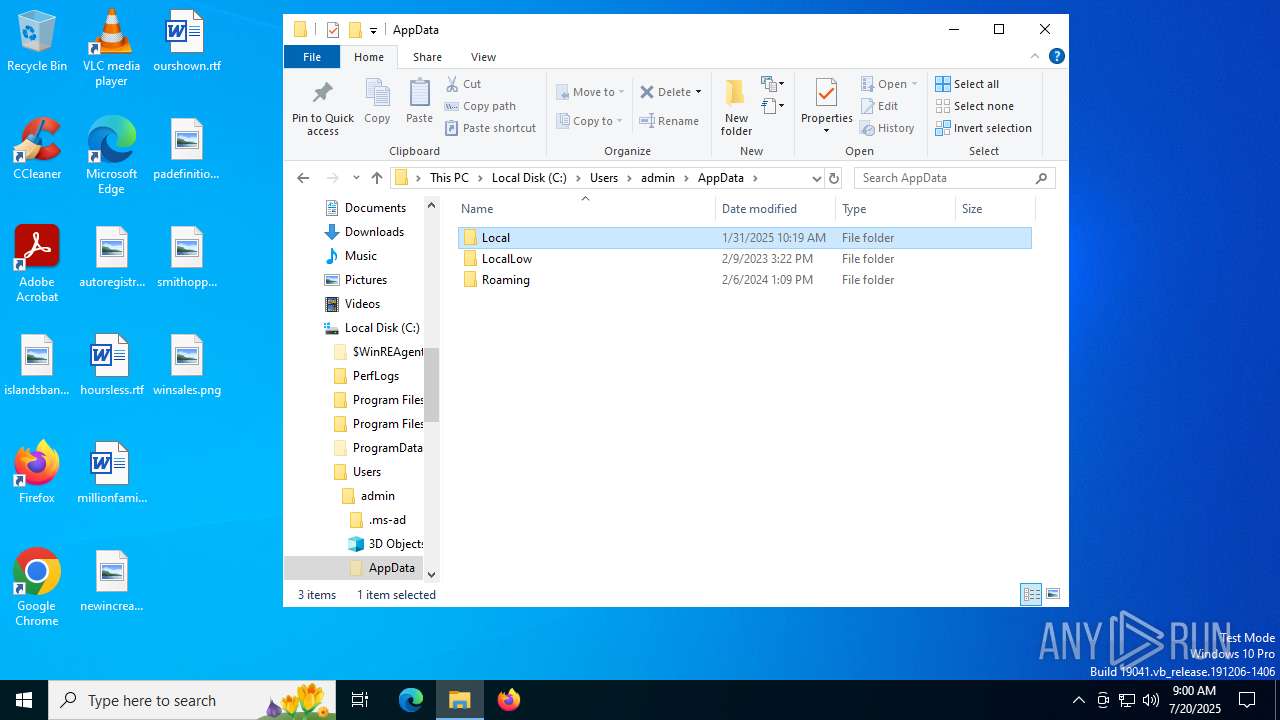
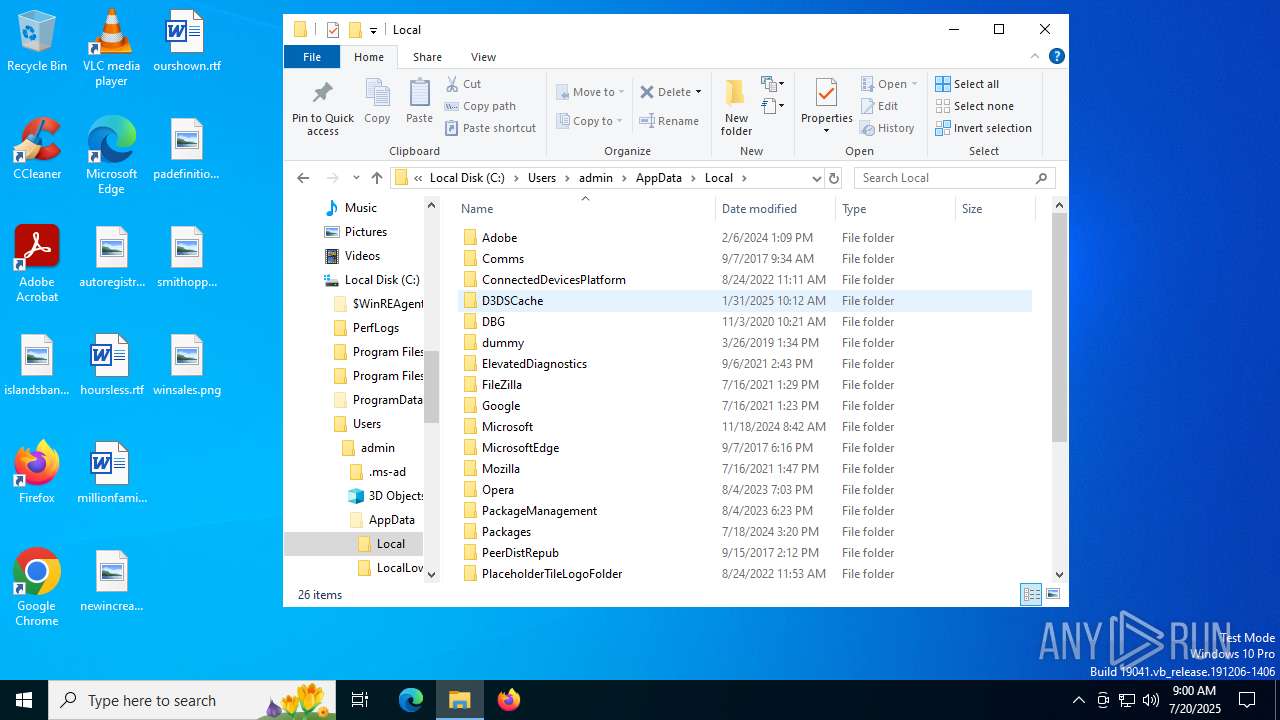
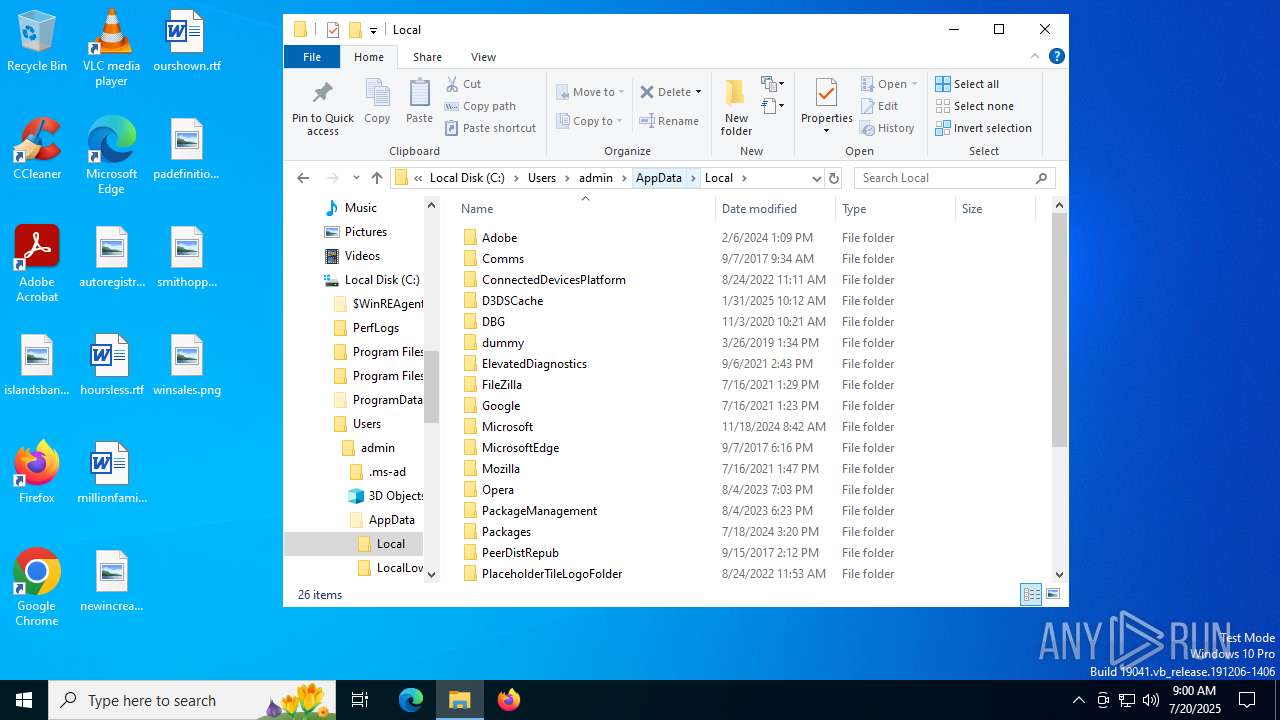
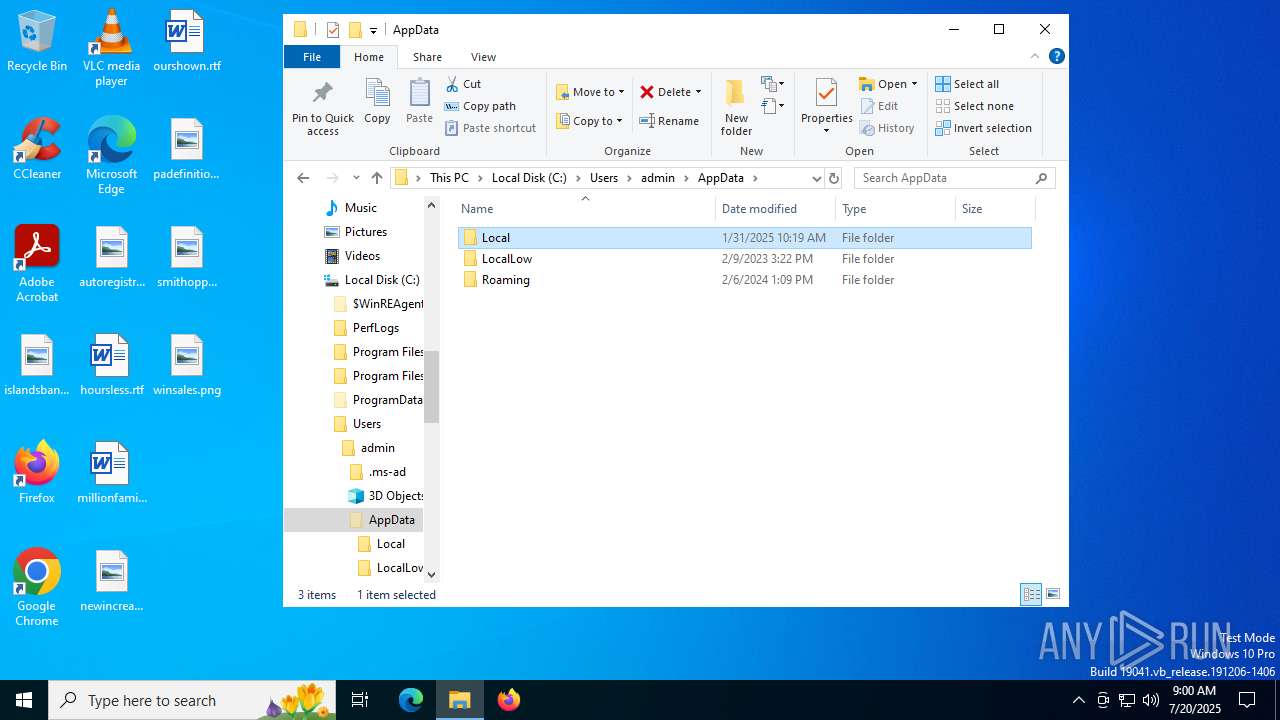
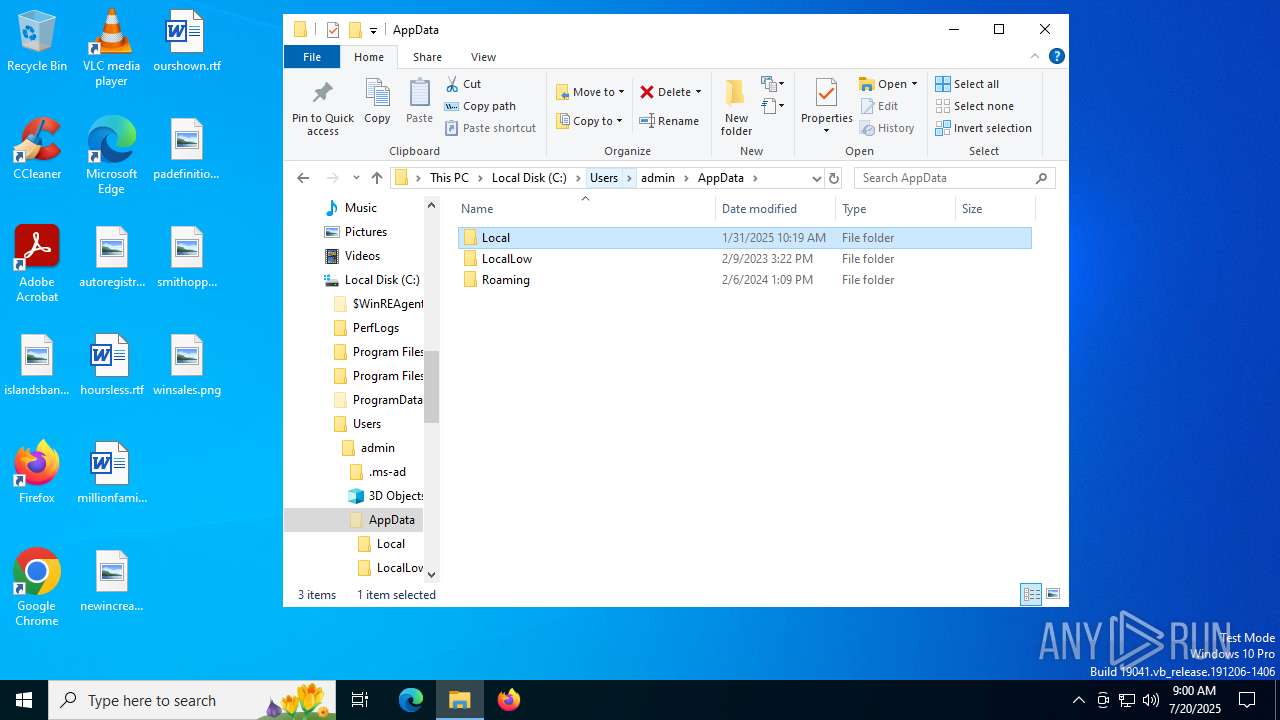
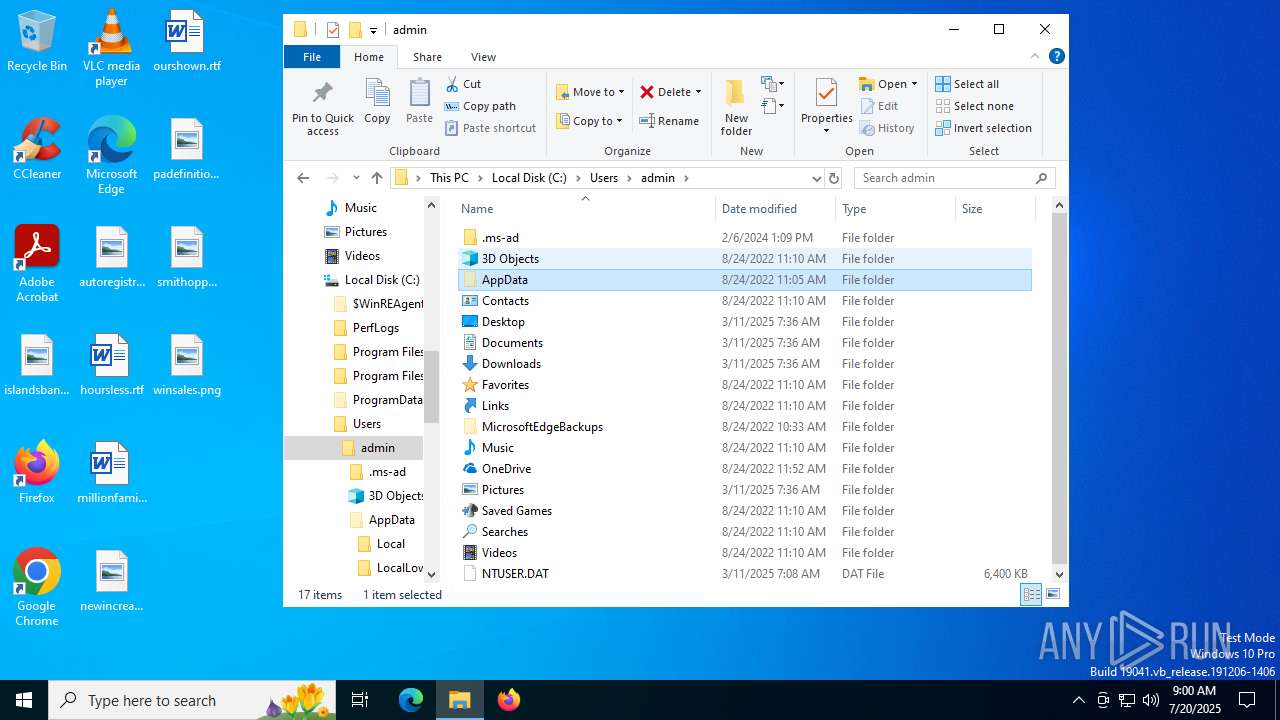
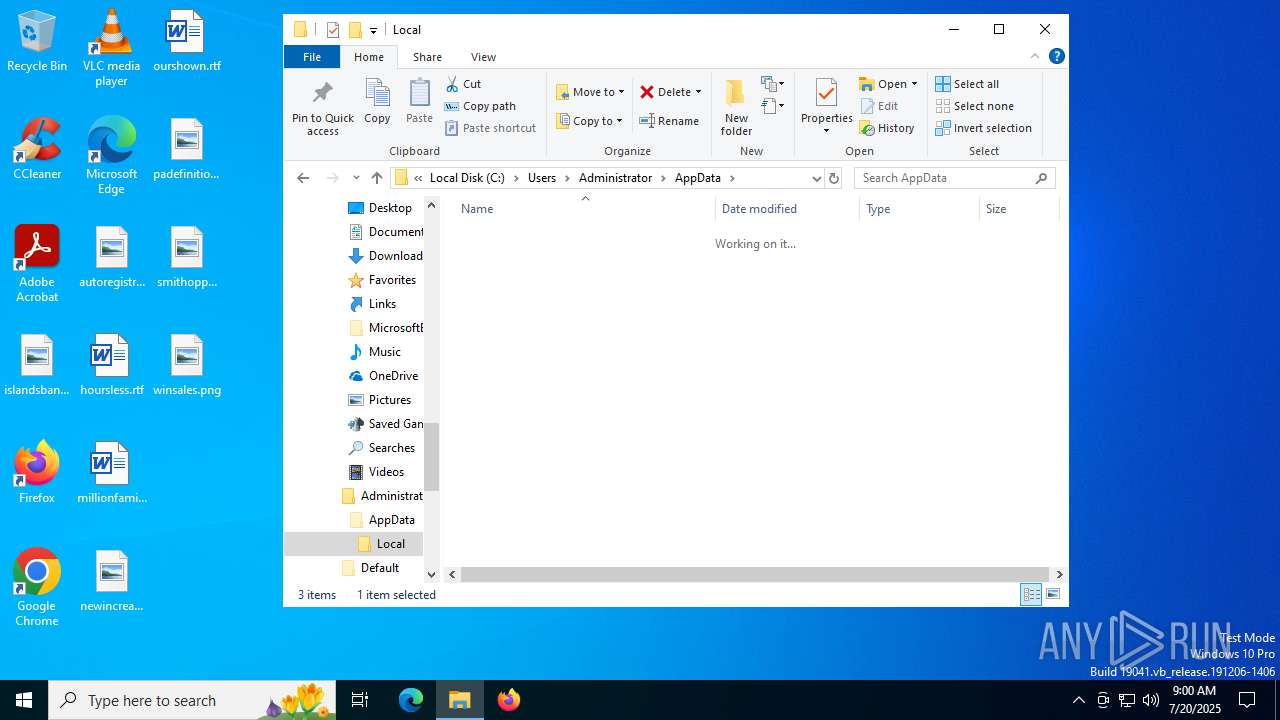
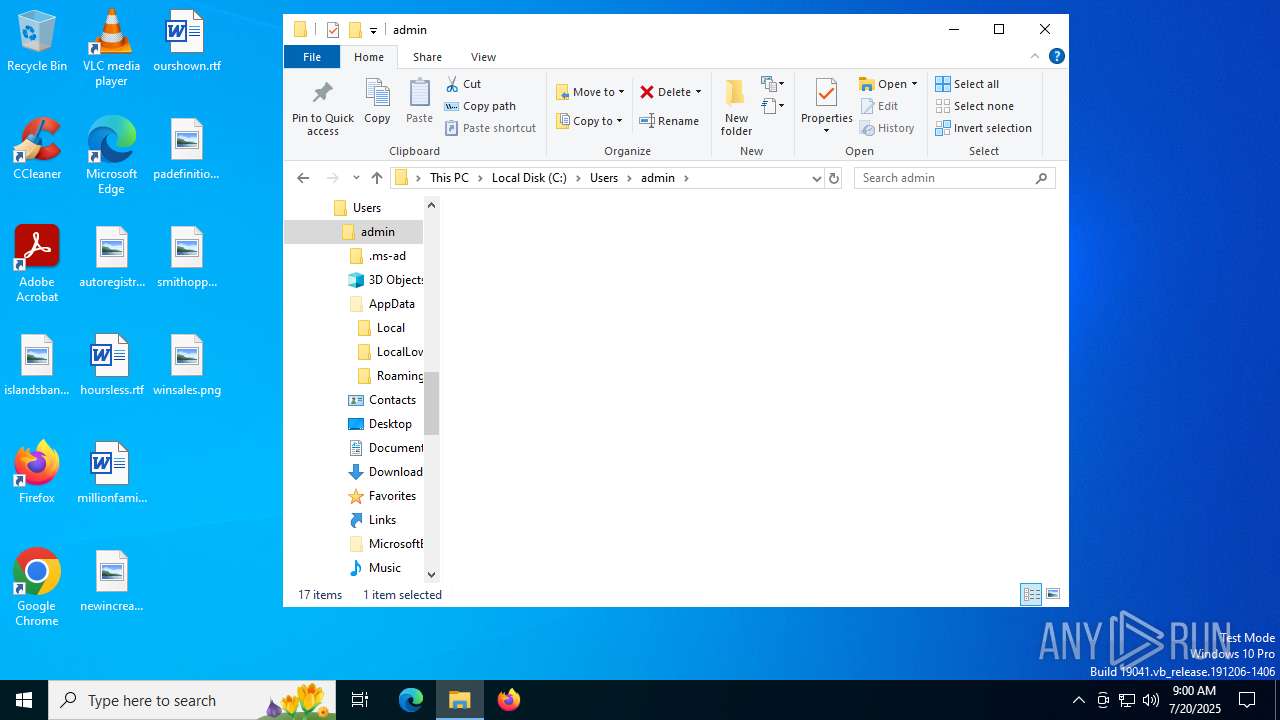
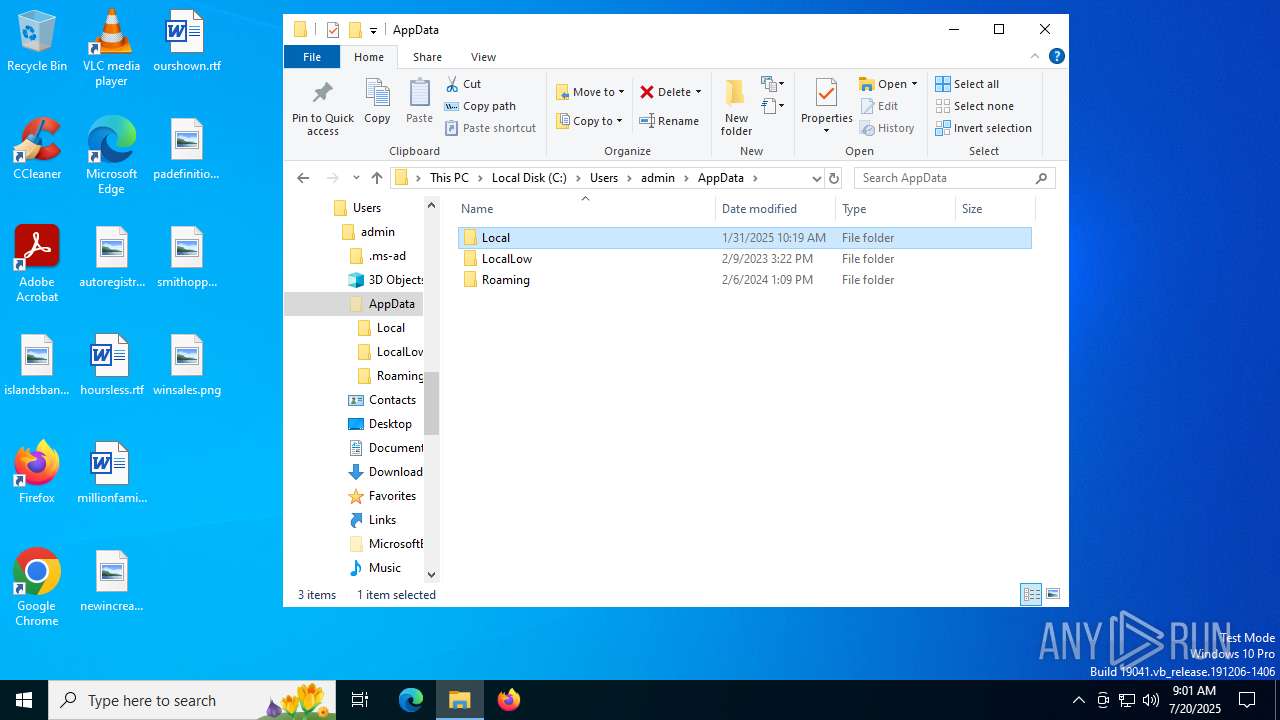
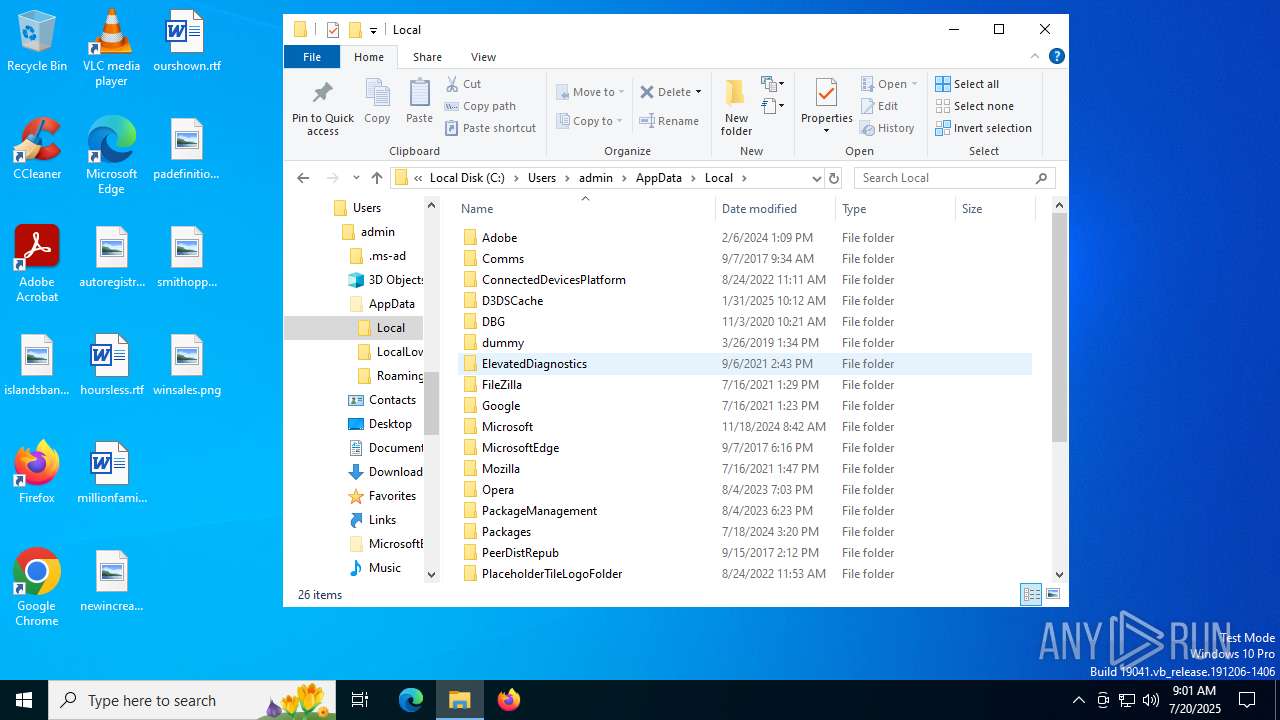
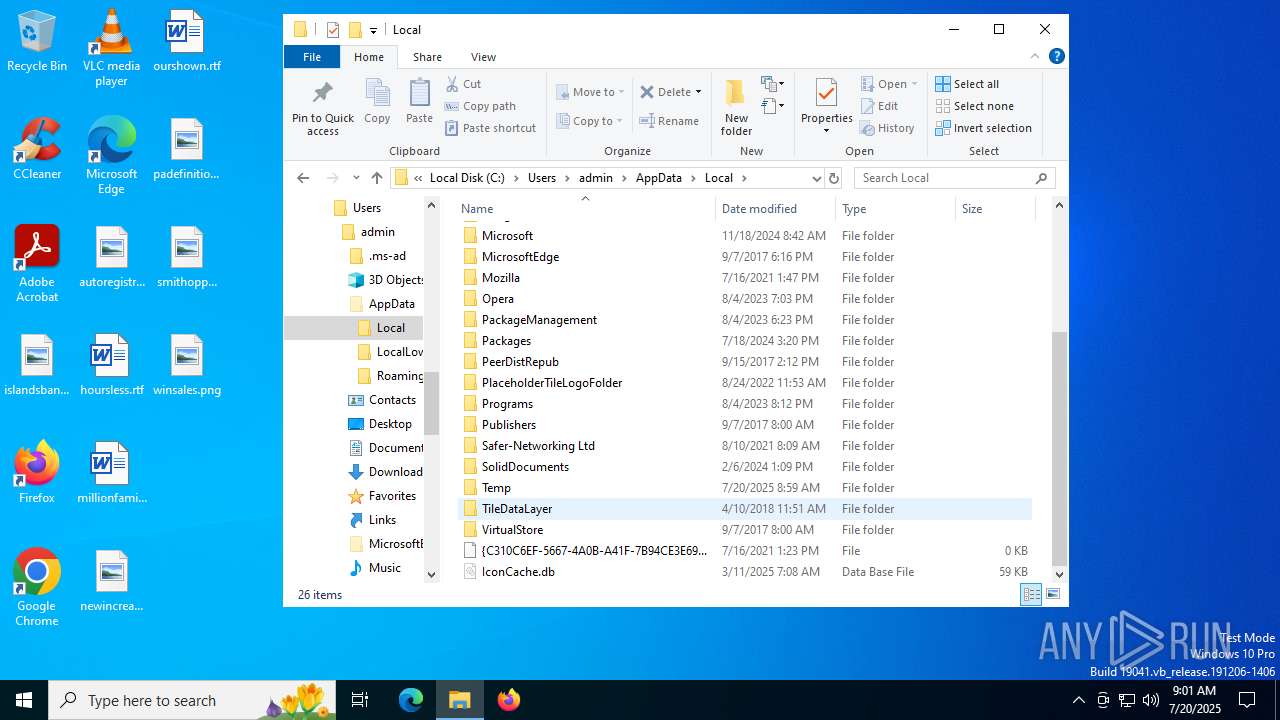
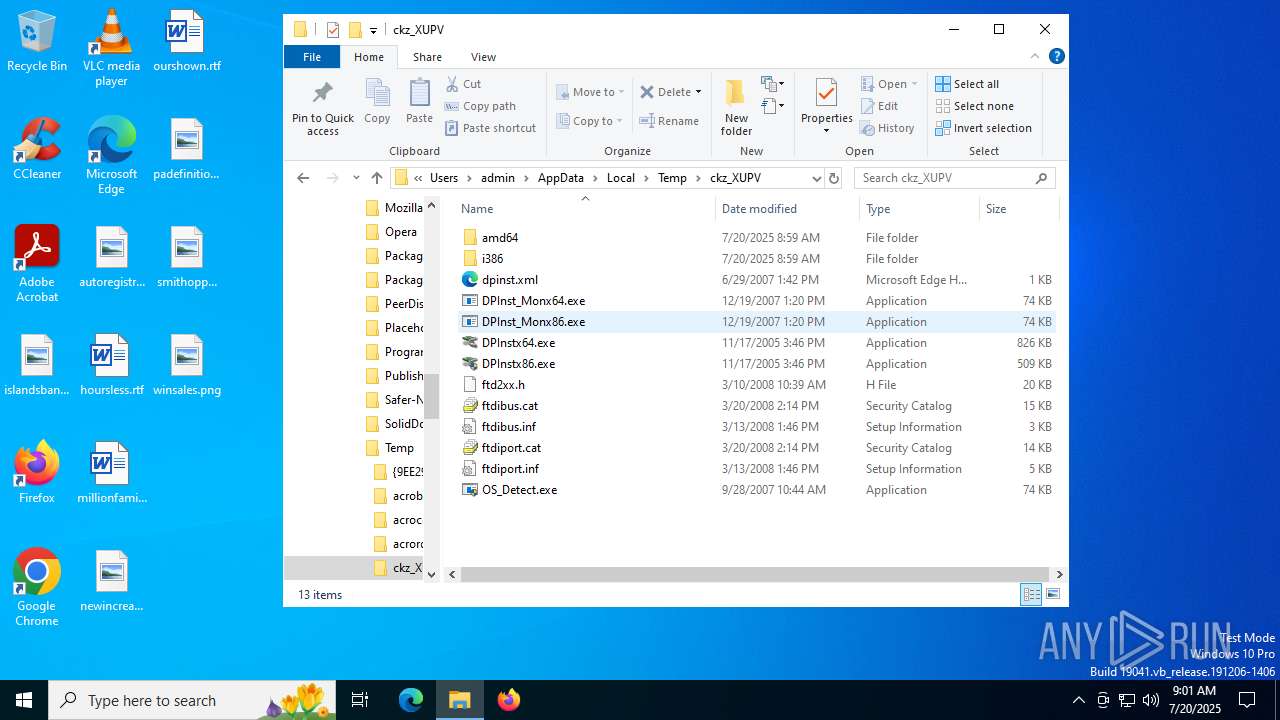
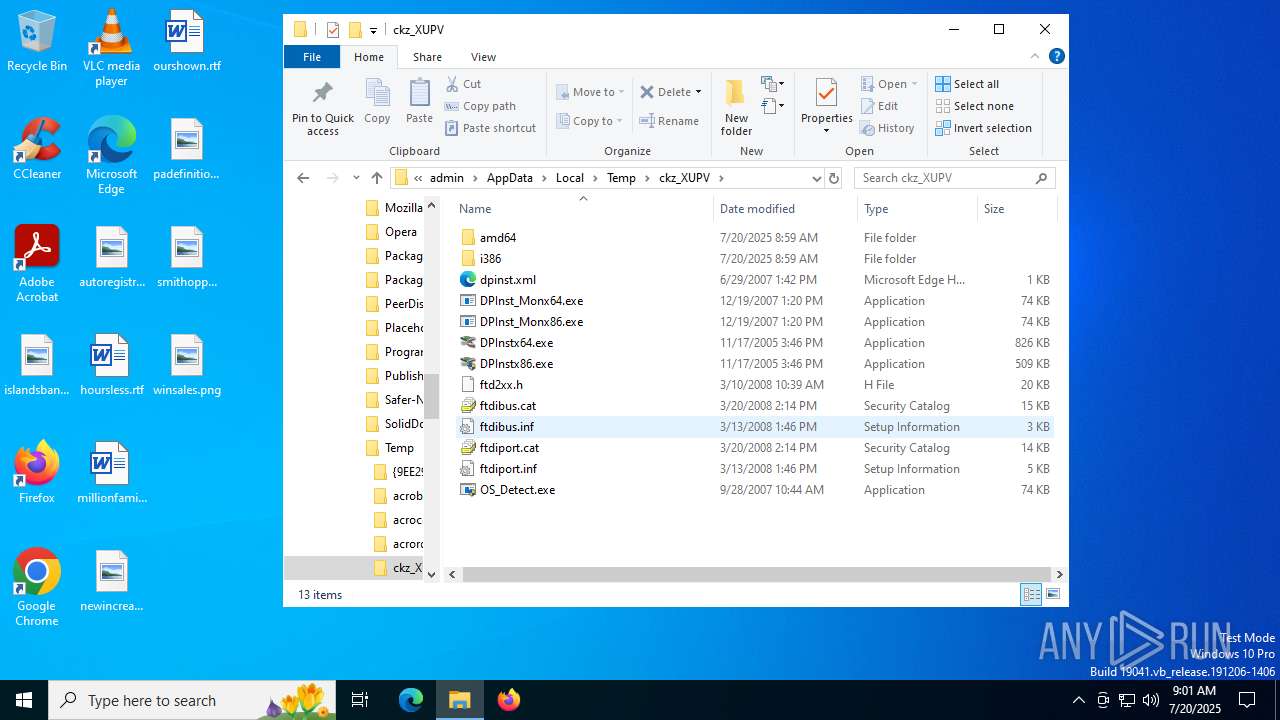
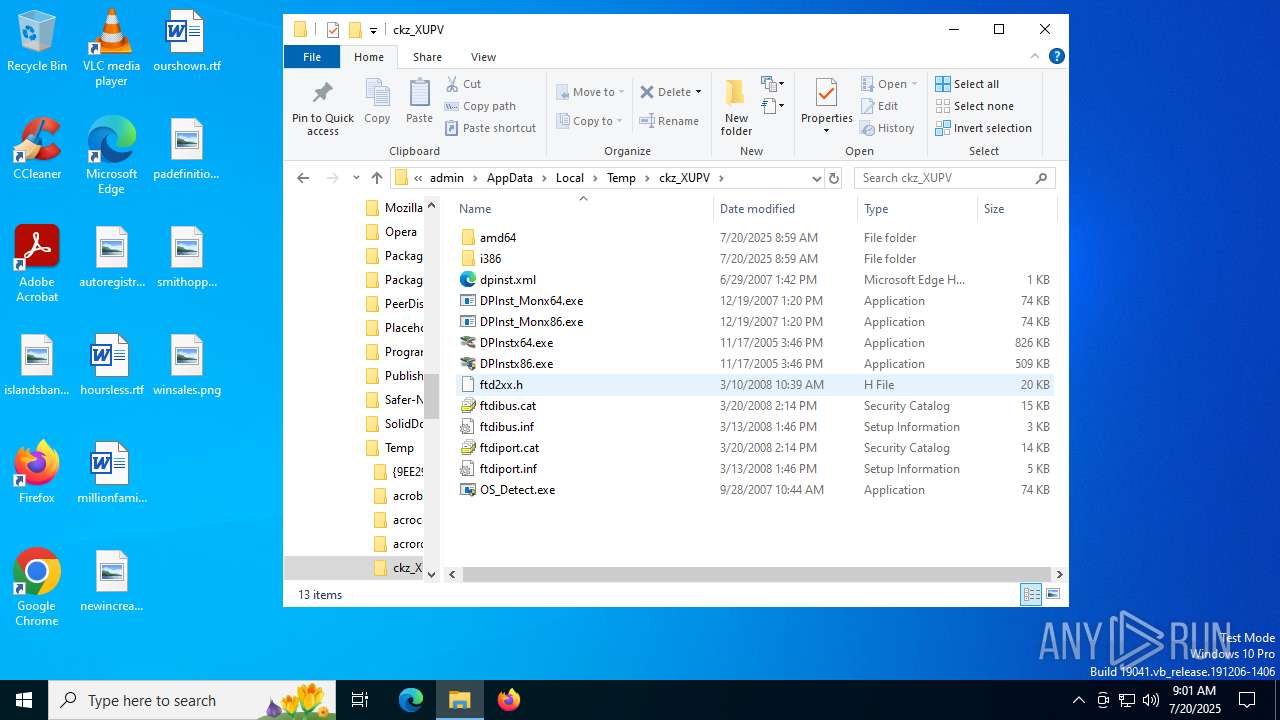
| 72 | "C:\Users\admin\AppData\Local\Temp\ckz_XUPV\DPInstx64.exe" | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\DPInstx64.exe | DPInst_Monx64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 512 Version: 2.01 Modules
| |||||||||||||||
| 1668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OS_Detect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2964 | "C:\Users\admin\AppData\Local\Temp\ckz_XUPV\OS_Detect.exe" | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\OS_Detect.exe | — | 连接驱动.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Local\Temp\ckz_XUPV\OS_Detect.exe" | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\OS_Detect.exe | 连接驱动.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4100 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{d0239a65-d7a4-b14e-93bb-4bdf4b97fcb0}\ftdiport.inf" "9" "433b40d03" "0000000000000204" "WinSta0\Default" "0000000000000208" "208" "c:\users\admin\appdata\local\temp\ckz_xupv" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | DPInst_Monx64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
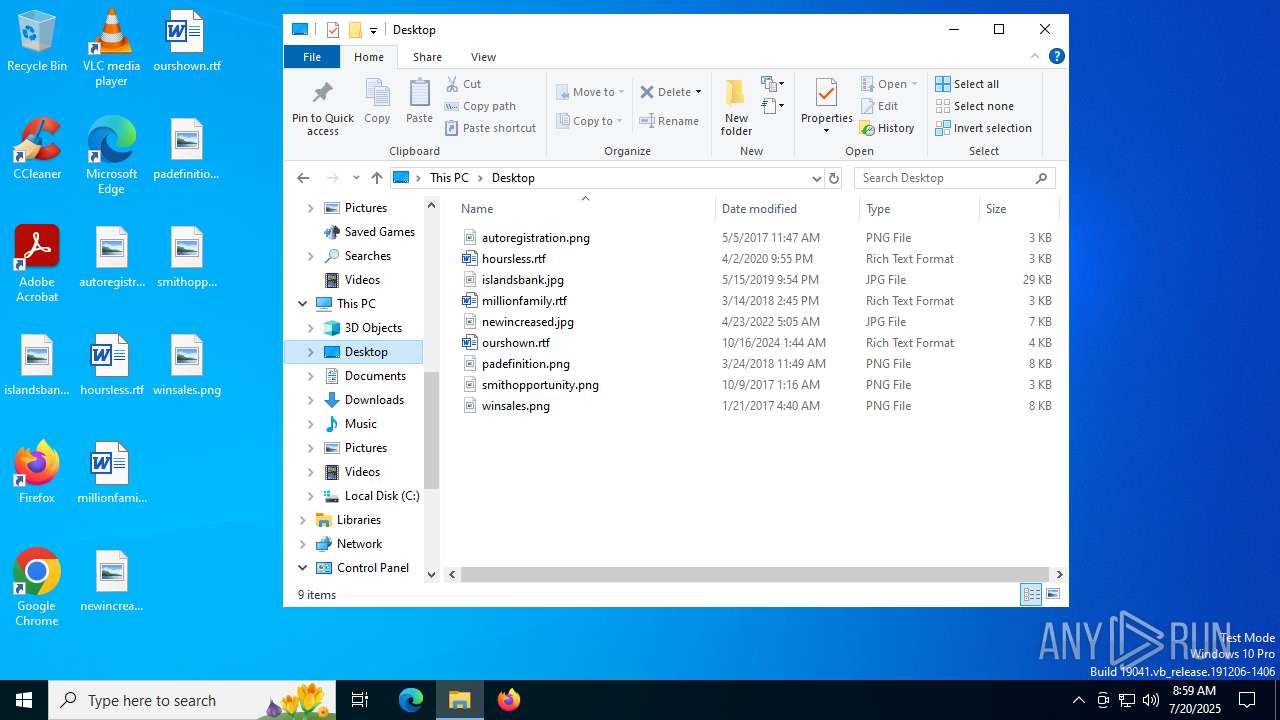
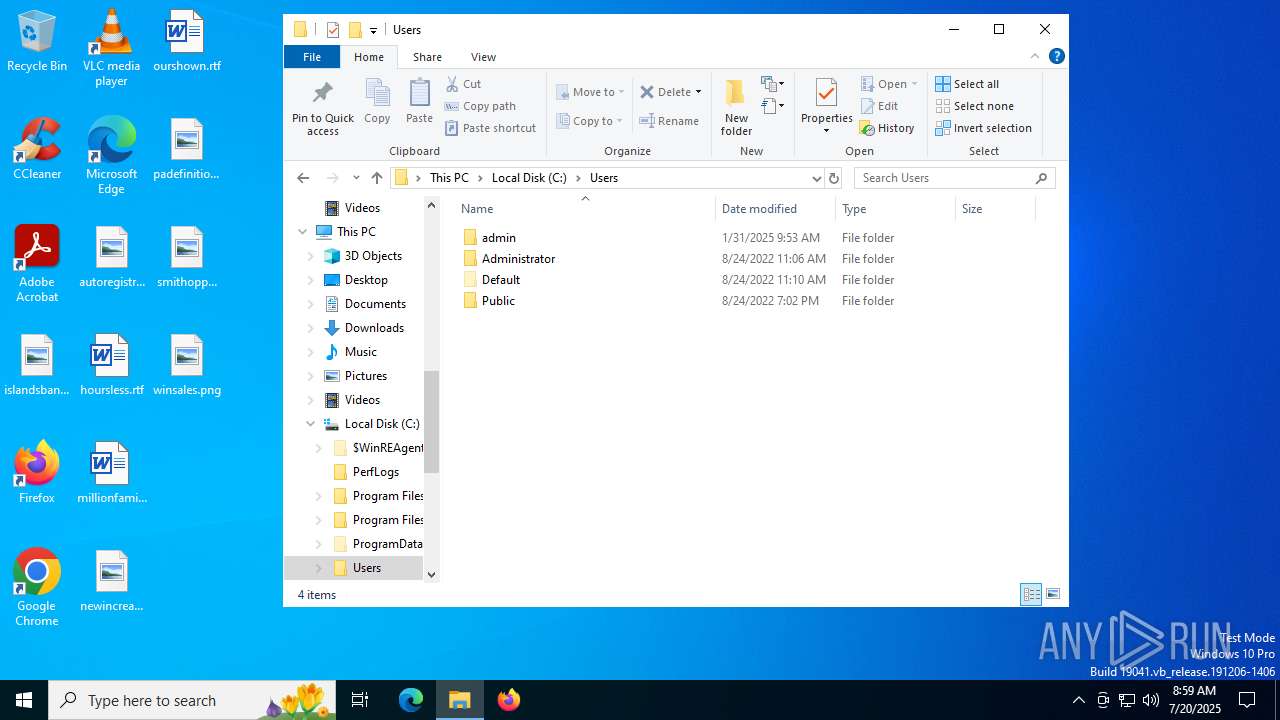
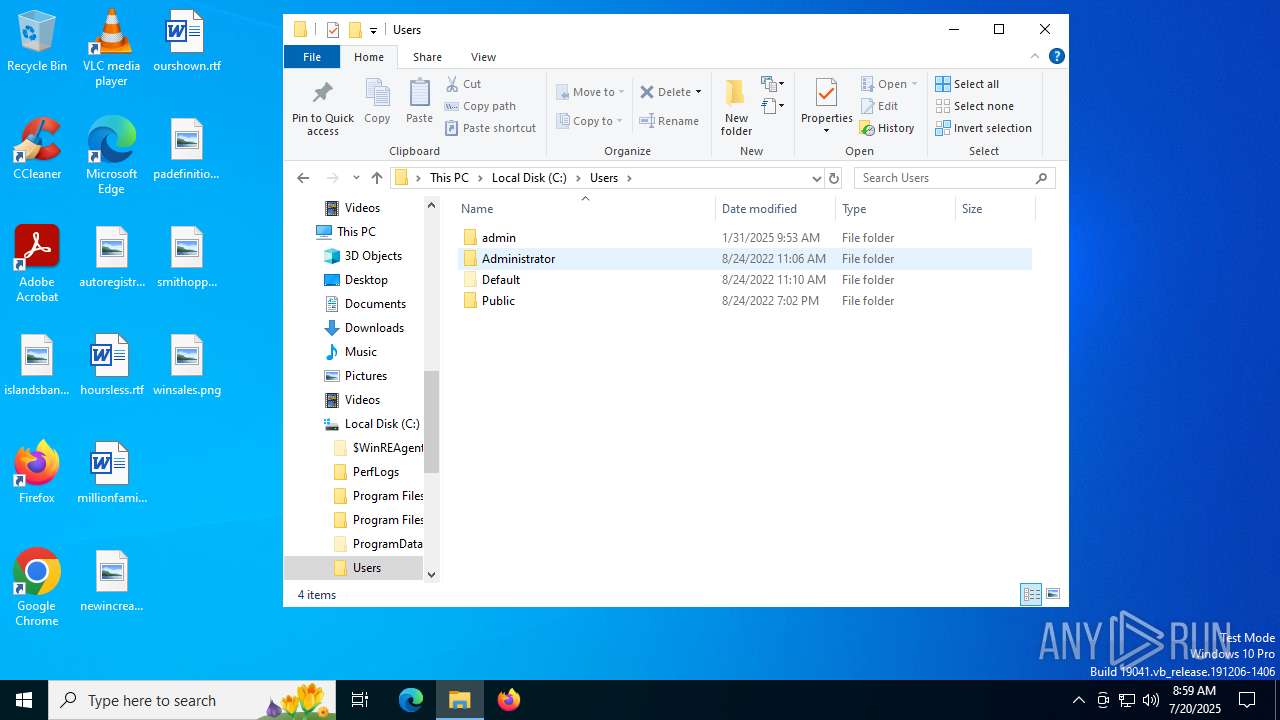
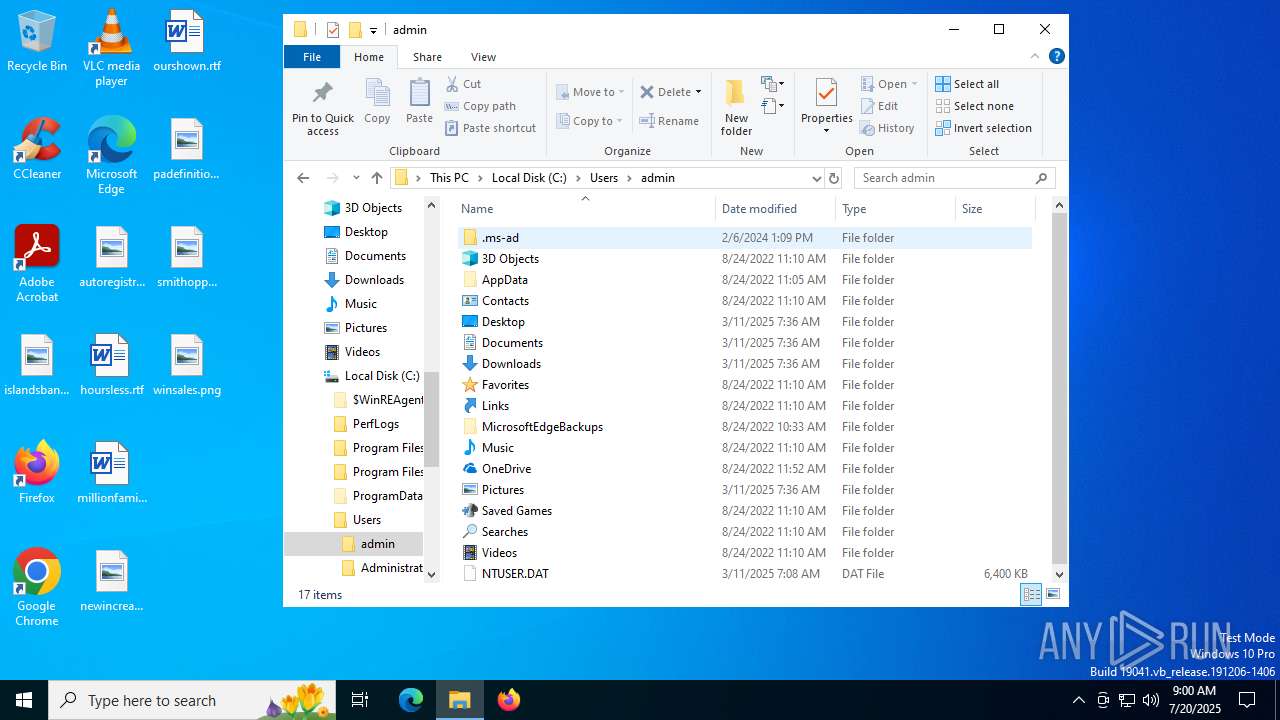
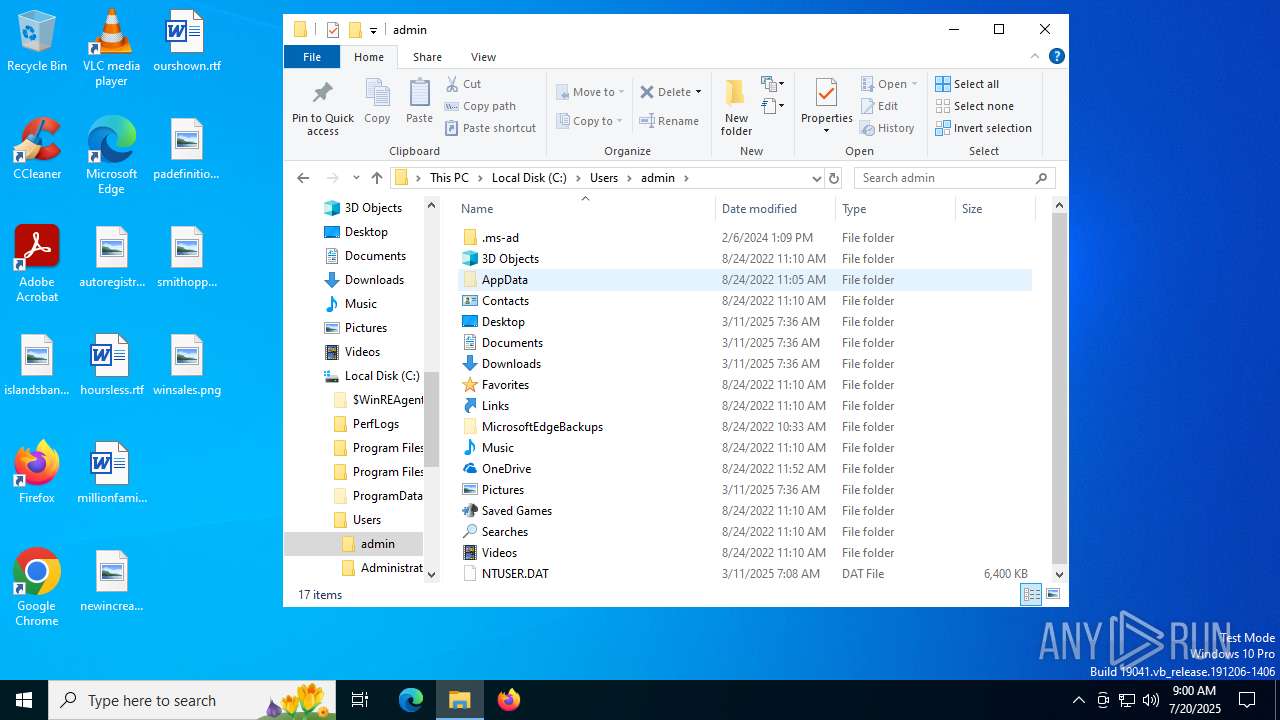
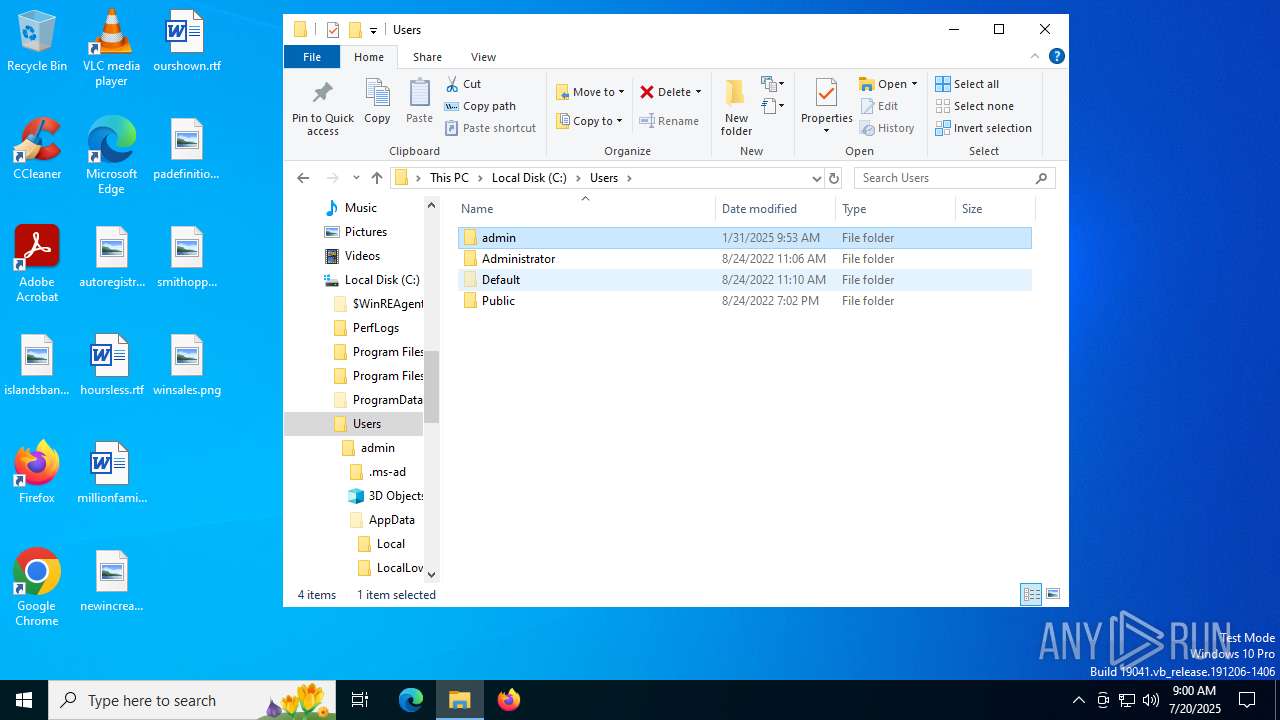
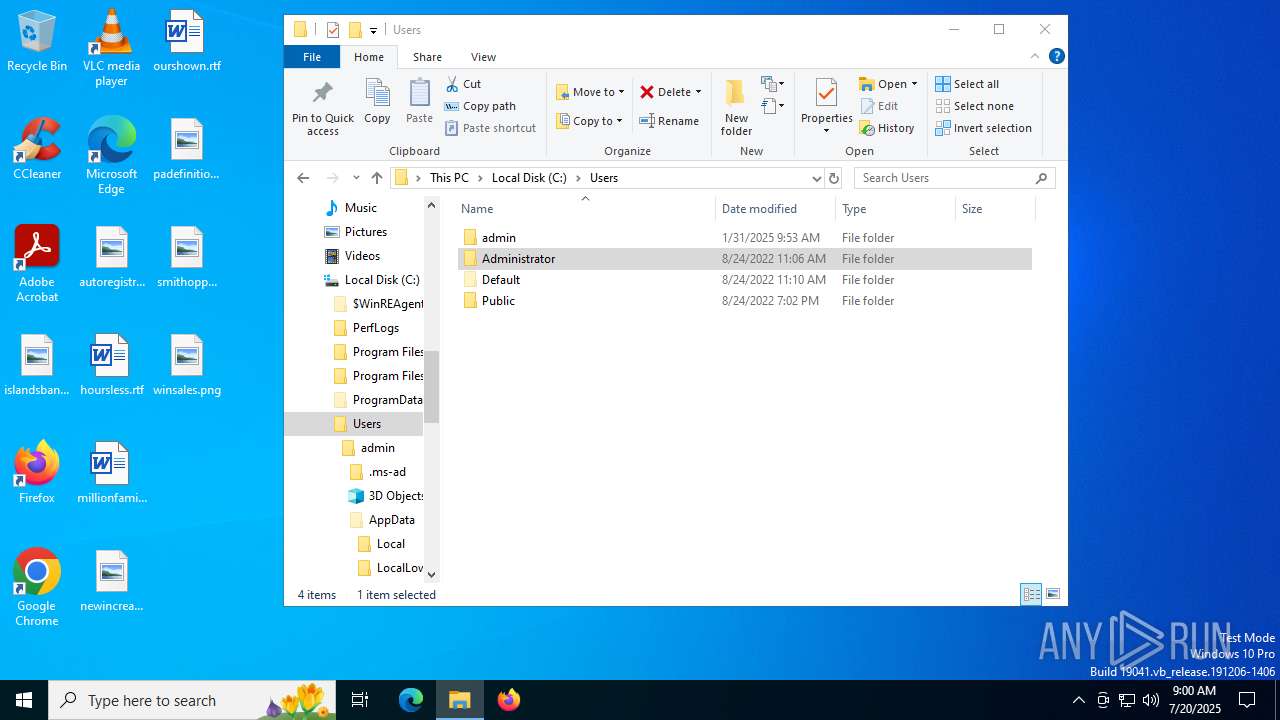
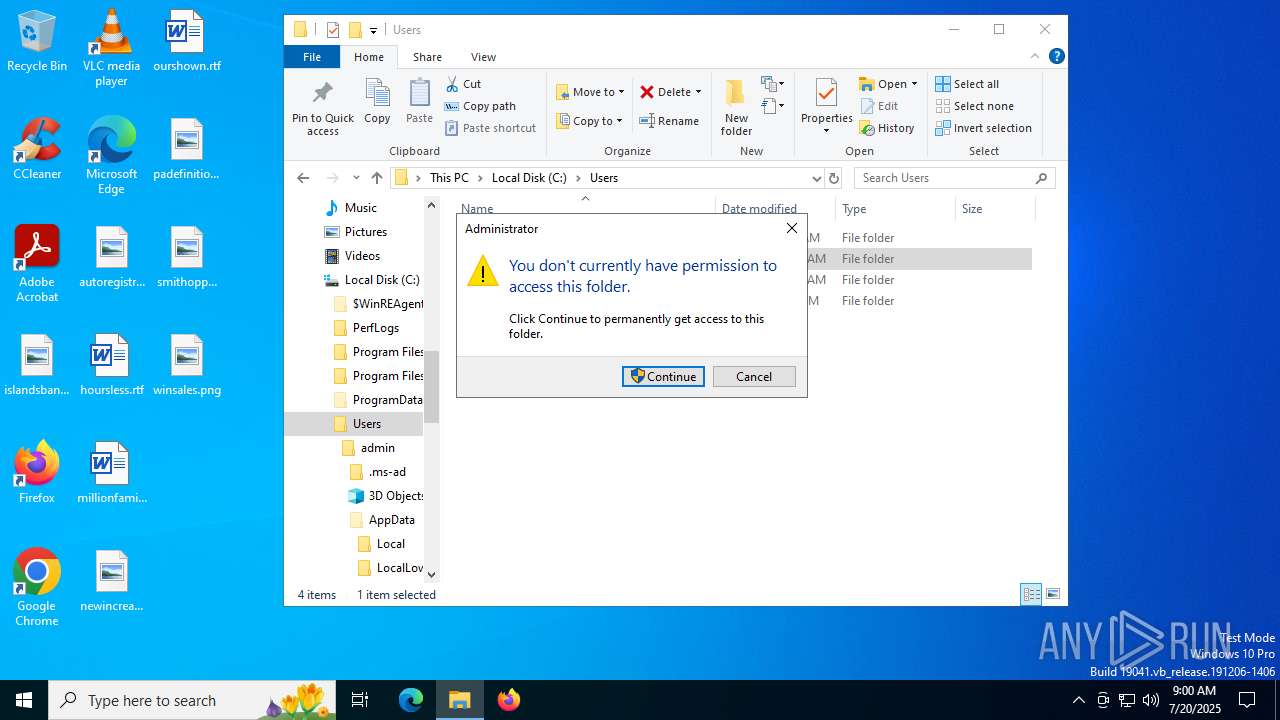
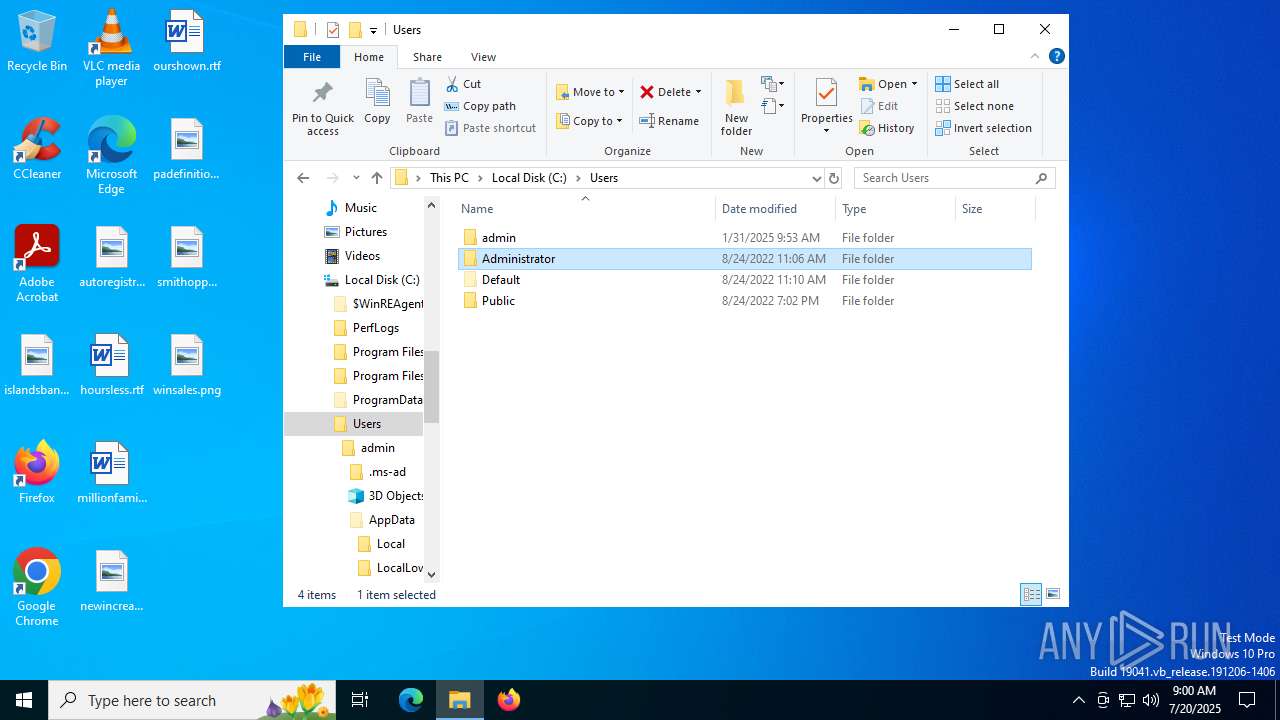
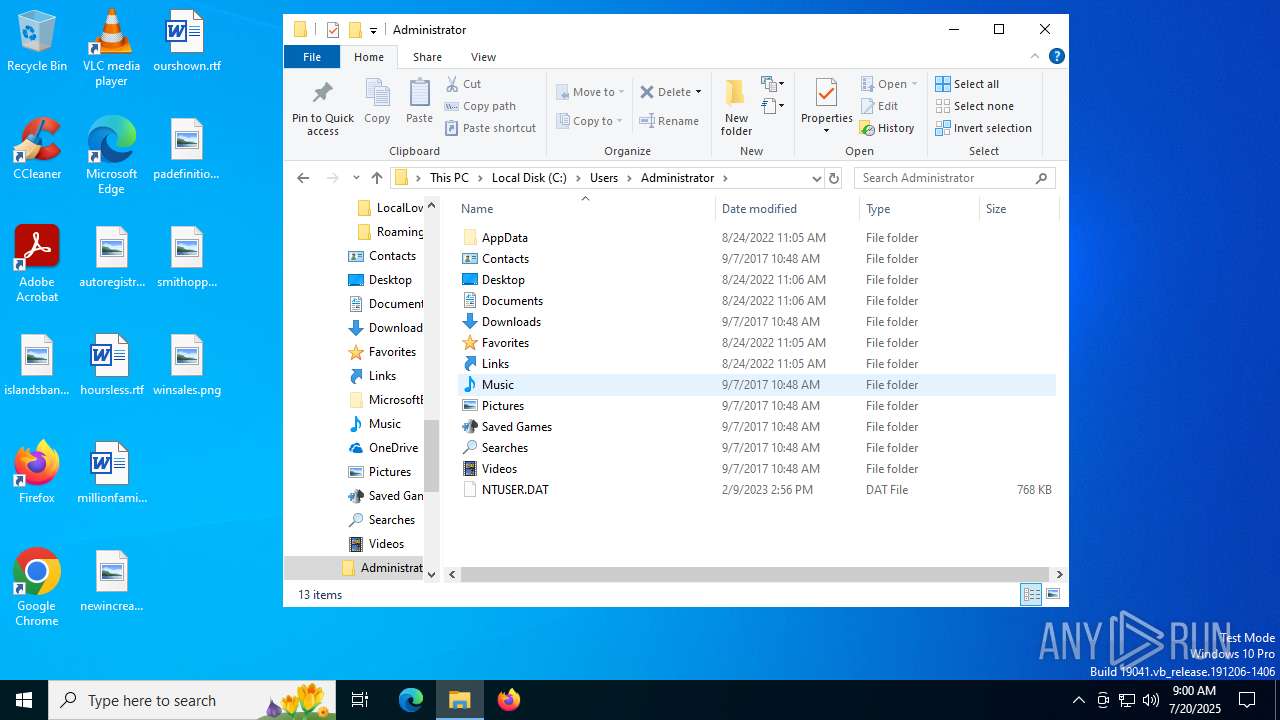
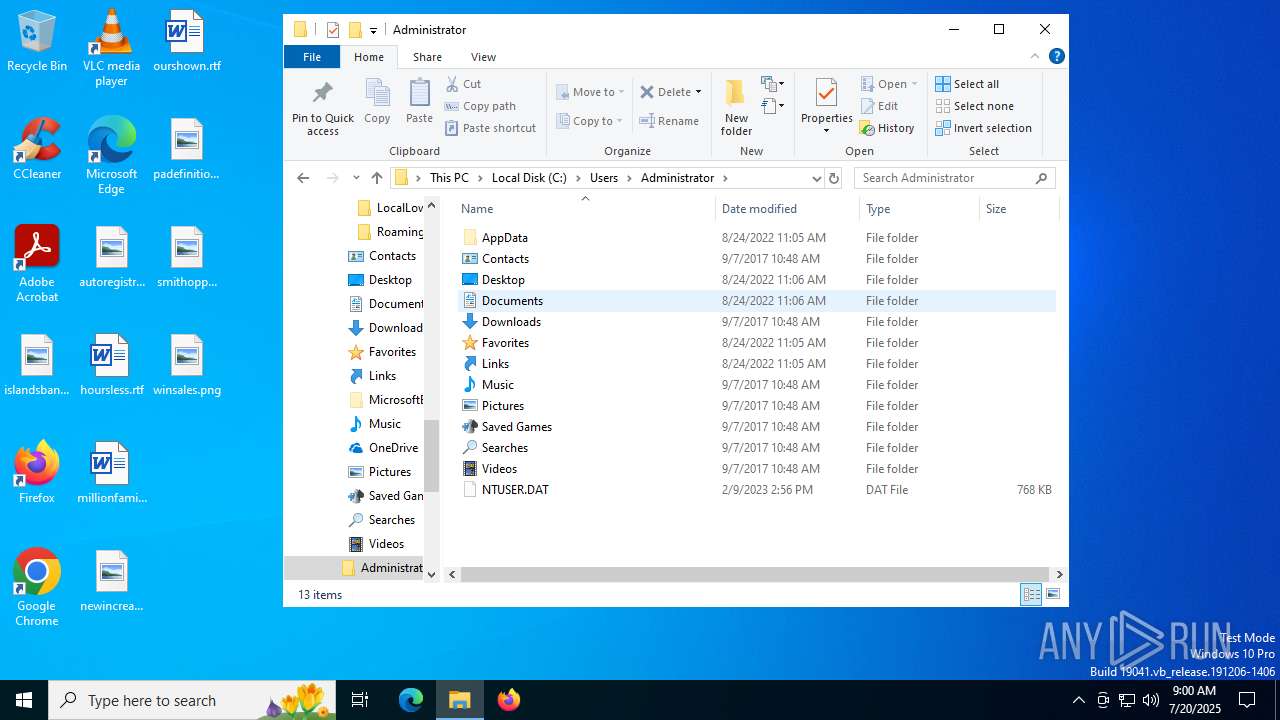
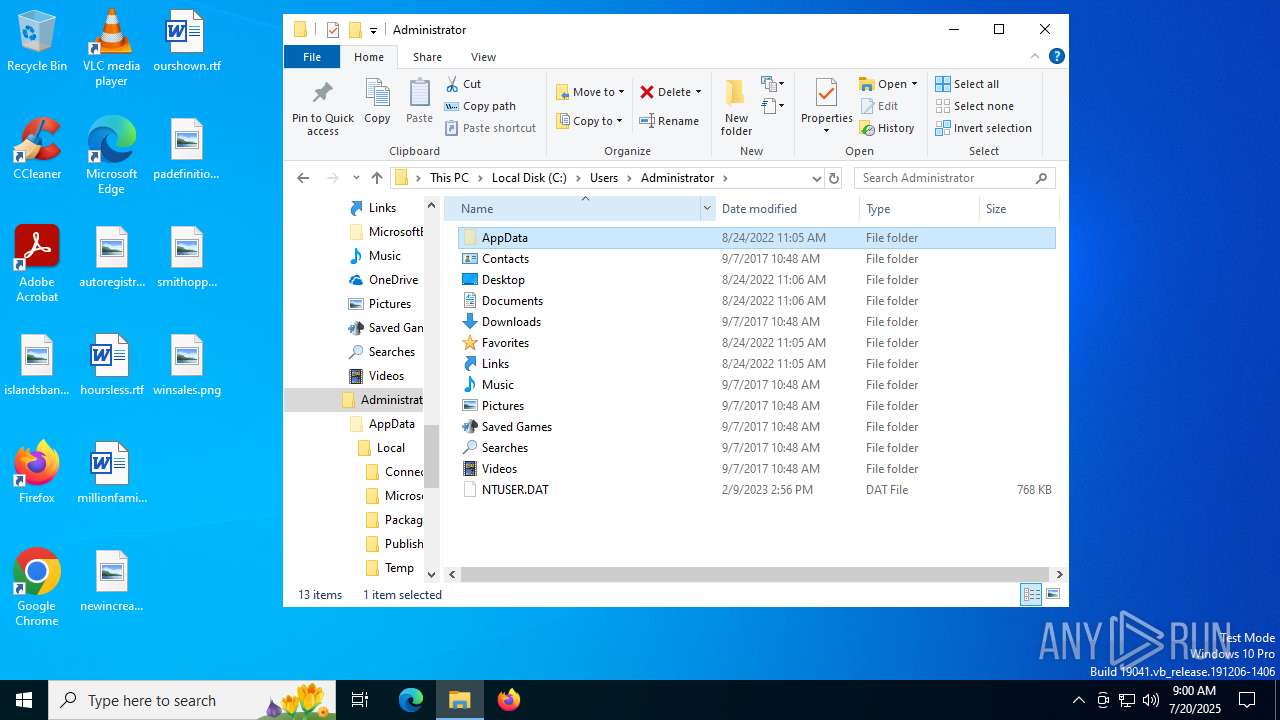
| 5716 | "C:\Users\admin\AppData\Local\Temp\连接驱动.exe" | C:\Users\admin\AppData\Local\Temp\连接驱动.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6160 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{f2321b7b-0d04-cc4a-82ec-a3979755d3cb}\ftdibus.inf" "9" "44aa7f39b" "00000000000001D4" "WinSta0\Default" "00000000000001EC" "208" "c:\users\admin\appdata\local\temp\ckz_xupv" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 978
Read events
7 977
Write events
1
Delete events
0
Modification events
| (PID) Process: | (72) DPInstx64.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
Executable files
52
Suspicious files
24
Text files
4
Unknown types
0
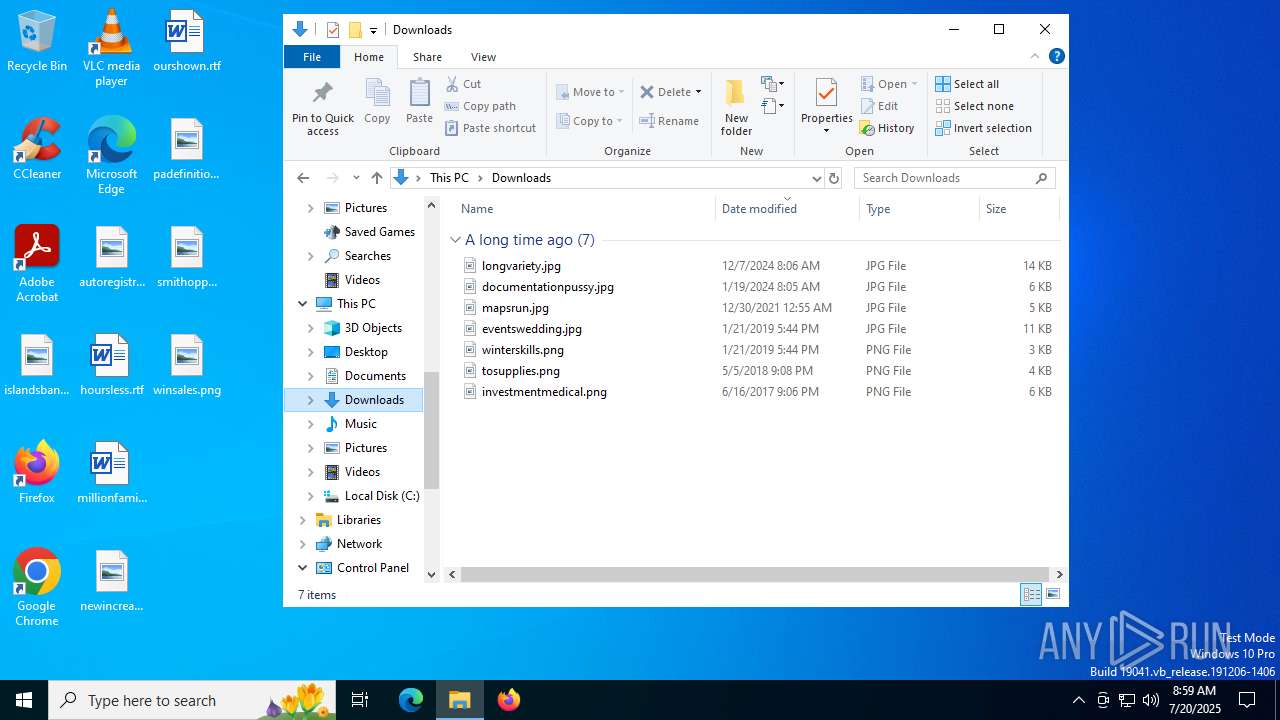
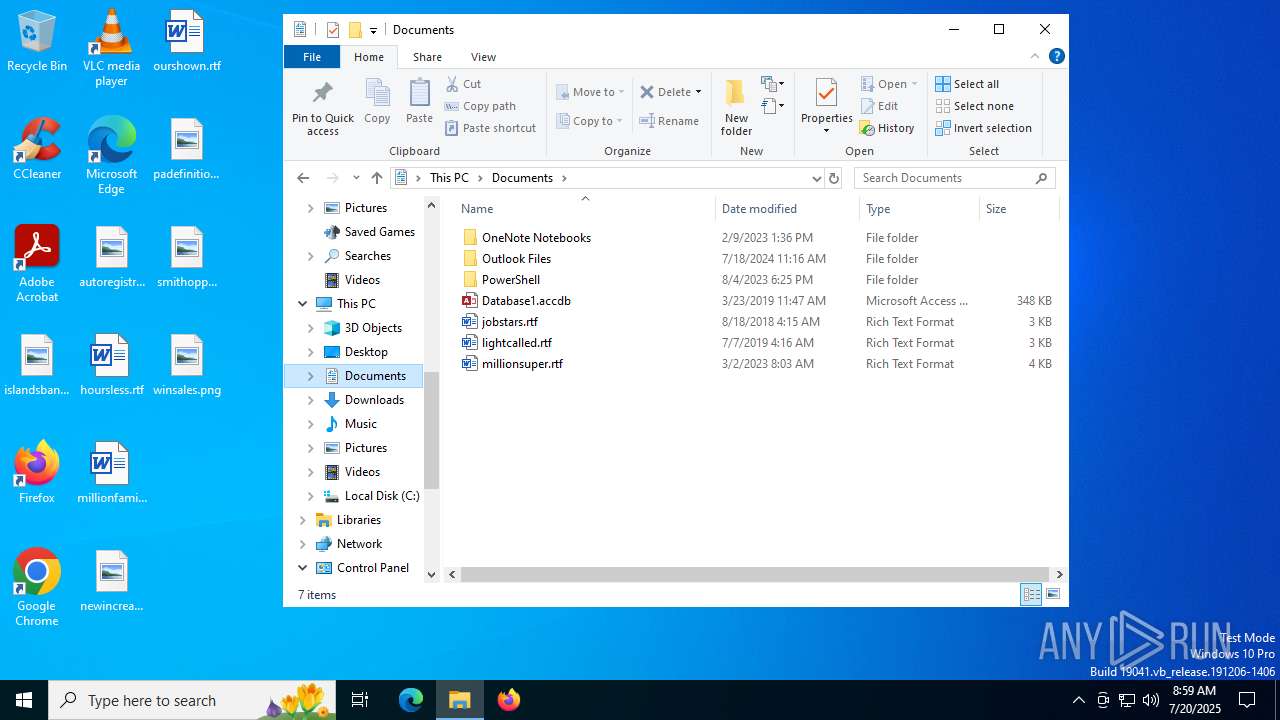
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
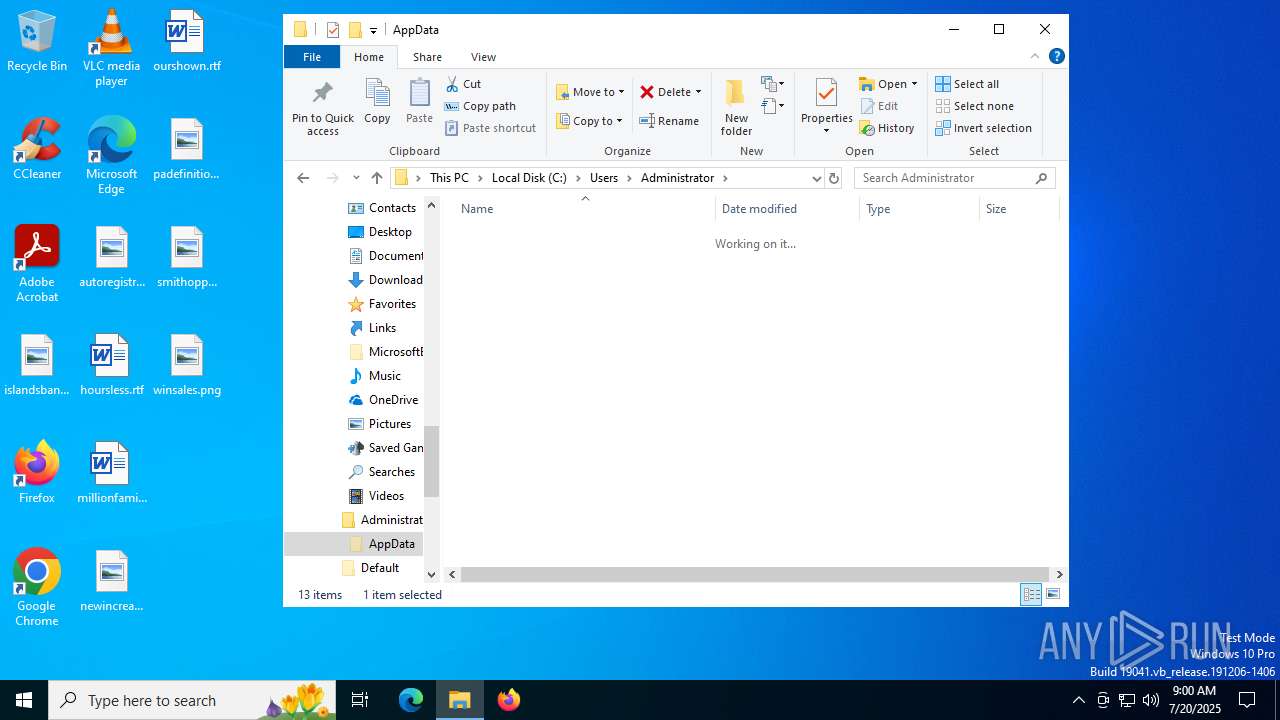
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\ftdiport.cat | binary | |
MD5:DB0F17A5F8F14D1D27D5A3BEF2E1D446 | SHA256:604B4CE2152CEC7E0B4A03EBF57D6C776F86628FEA573B06A8813ED3B1E99F91 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\amd64\ftd2xx.lib | binary | |
MD5:275115E5AFDAD0306EA4F565123DD07D | SHA256:2E37339CE126F2F3EDAD69863F4899BFED381F38B0A237129195D0D7768798F9 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\ftdiport.inf | binary | |
MD5:3F04F78F64151D11FE3BC91481AC3858 | SHA256:F50A99F3F48ED8790759CC2BB1AFC4B33323D30DE7E9A9DB8F9968BB6F64F42C | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\ftdibus.inf | binary | |
MD5:2D8CE77EA966581FC1C12150561B4320 | SHA256:3C16A535CCF2B4C31A115611AC231187A9F9E7DDE934A29E31941D6E57F49786 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\amd64\ftserui2.dll | executable | |
MD5:B0459A9D1D6037E8E40F5D268820BA67 | SHA256:E76748174AE74C59F22C668EBD034CF07A72A27BF46E8D19EED141D5E73DA579 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\amd64\ftlang.dll | executable | |
MD5:63C18CC6FF6130215D14C8212B1BD450 | SHA256:A68ED4225CDE423E8D2F2774FF26986B1B2E8B2C5B05412F95F5319CB5BF78E2 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\amd64\ftdibus.sys | executable | |
MD5:0F210048C6BFBFBC0F50816BCE40B575 | SHA256:73C015B6EE647A875BD124254542FF8759264D51F331FF95D14675C1599FAD94 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\amd64\ftcserco.dll | executable | |
MD5:3348E94EC66EB0435A4DD69961E3A11F | SHA256:8E3167B3E21D44B85BC69CDDBB893A90C13CB9501F98DCE8341F995F525D351B | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\OS_Detect.exe | executable | |
MD5:E80E0006EF399A18E44F28A918CAB6FB | SHA256:F434F110E0E99D3D829A0824CF5276DE60D5B927E7E7C1CDF5FB5A0EFF079224 | |||
| 5716 | 连接驱动.exe | C:\Users\admin\AppData\Local\Temp\ckz_XUPV\i386\ftd2xx.dll | executable | |
MD5:9ADBED60E17690BD72E3AB134CC97BBD | SHA256:B052D6DCF61B864E948743CD02C29F0BF80F94E6C705BC4DBE858B55EEABBBB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3944 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2940 | svchost.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | — | 825 b | whitelisted |
188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1156 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3944 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3944 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.241.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |