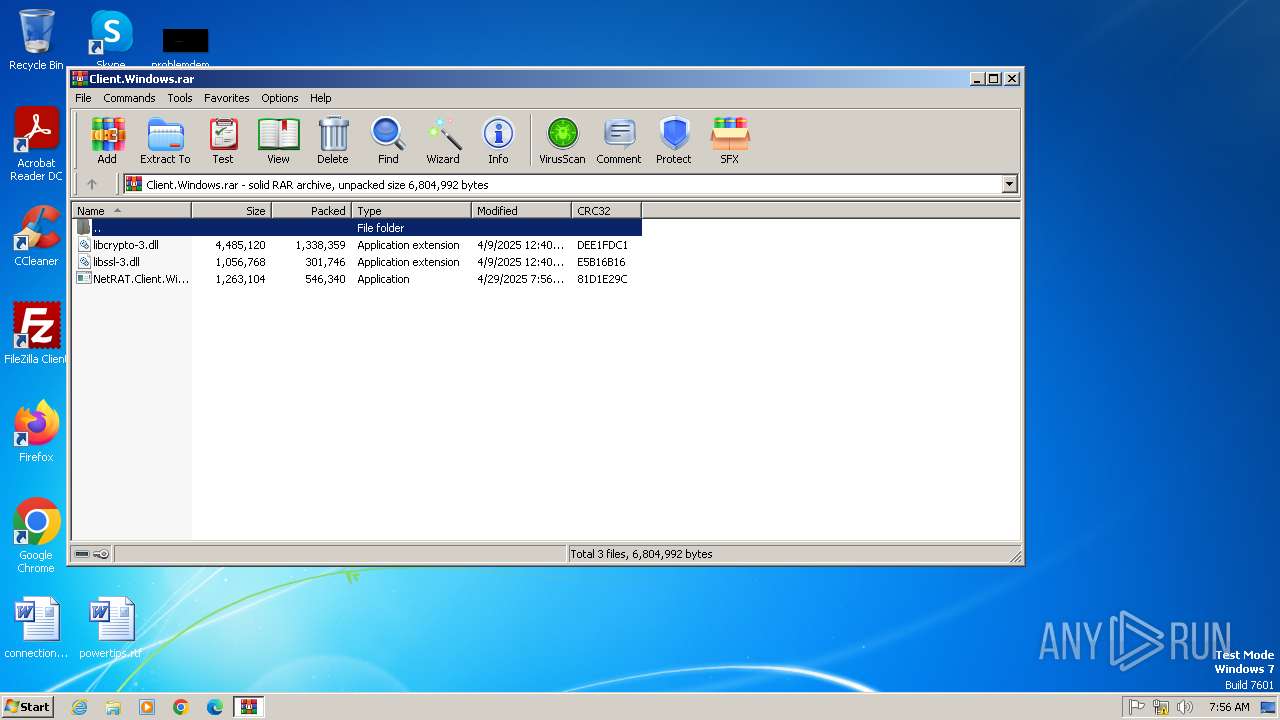
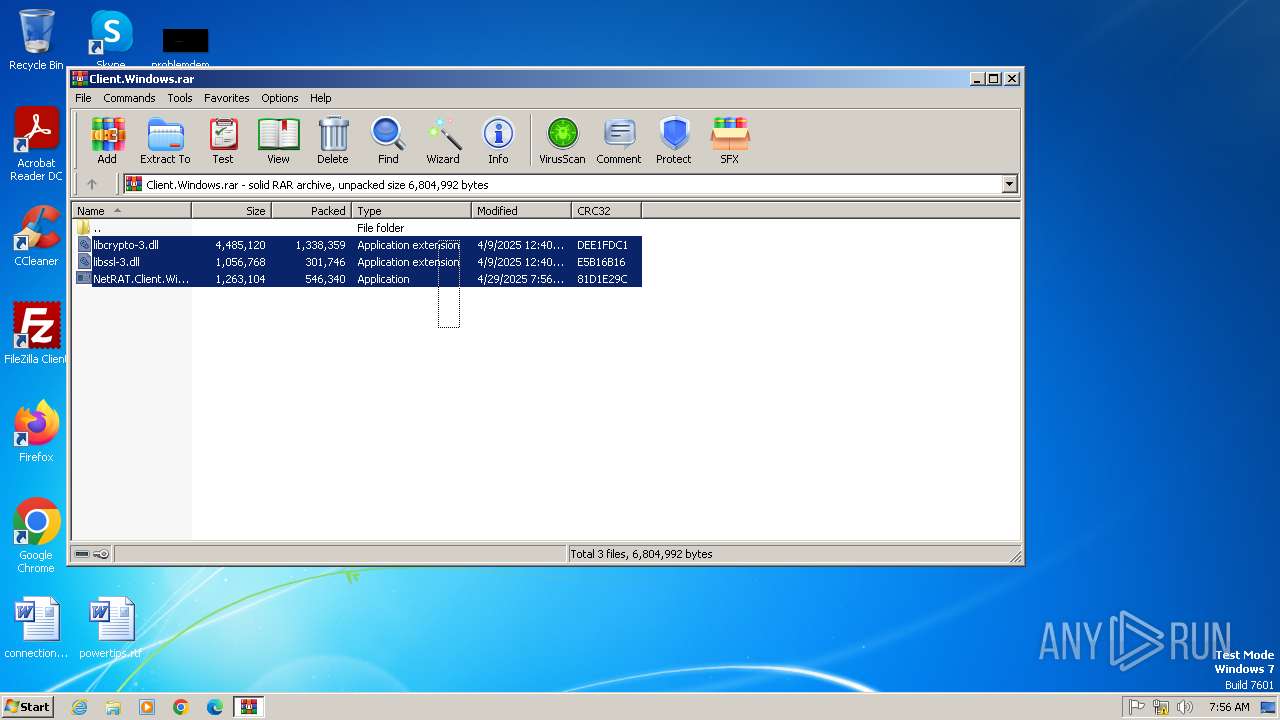
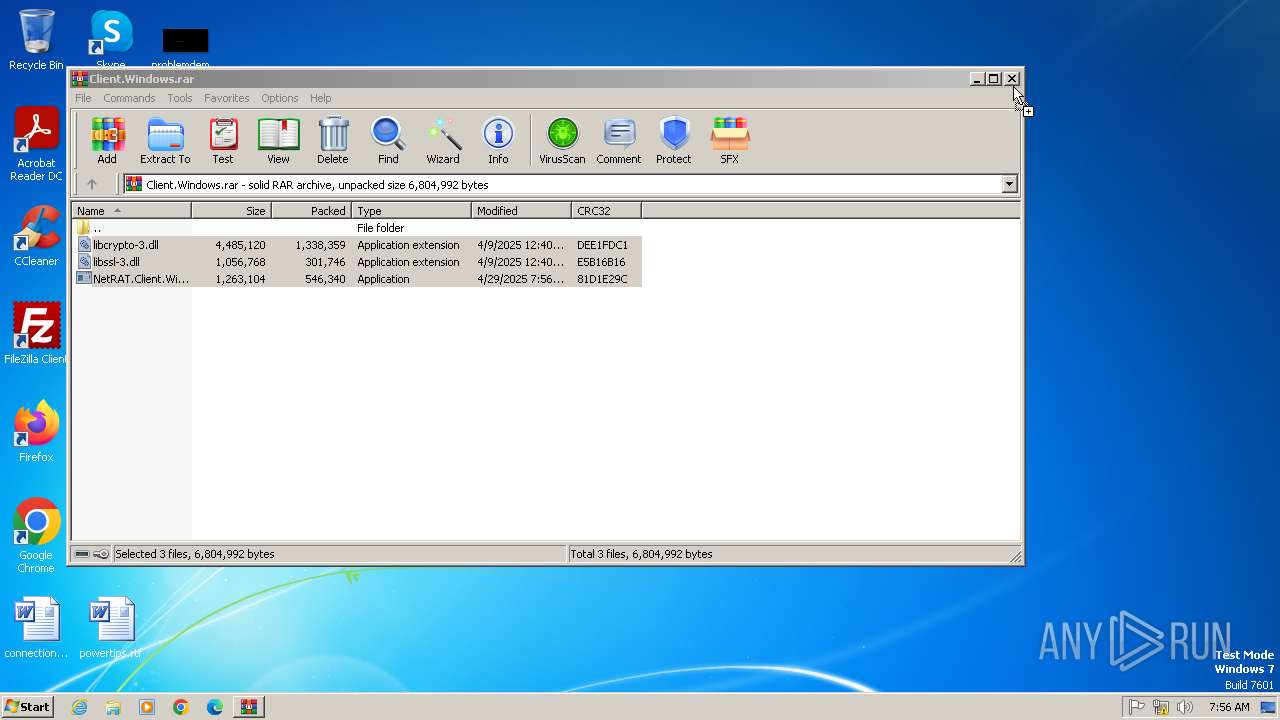
| File name: | Client.Windows.rar |
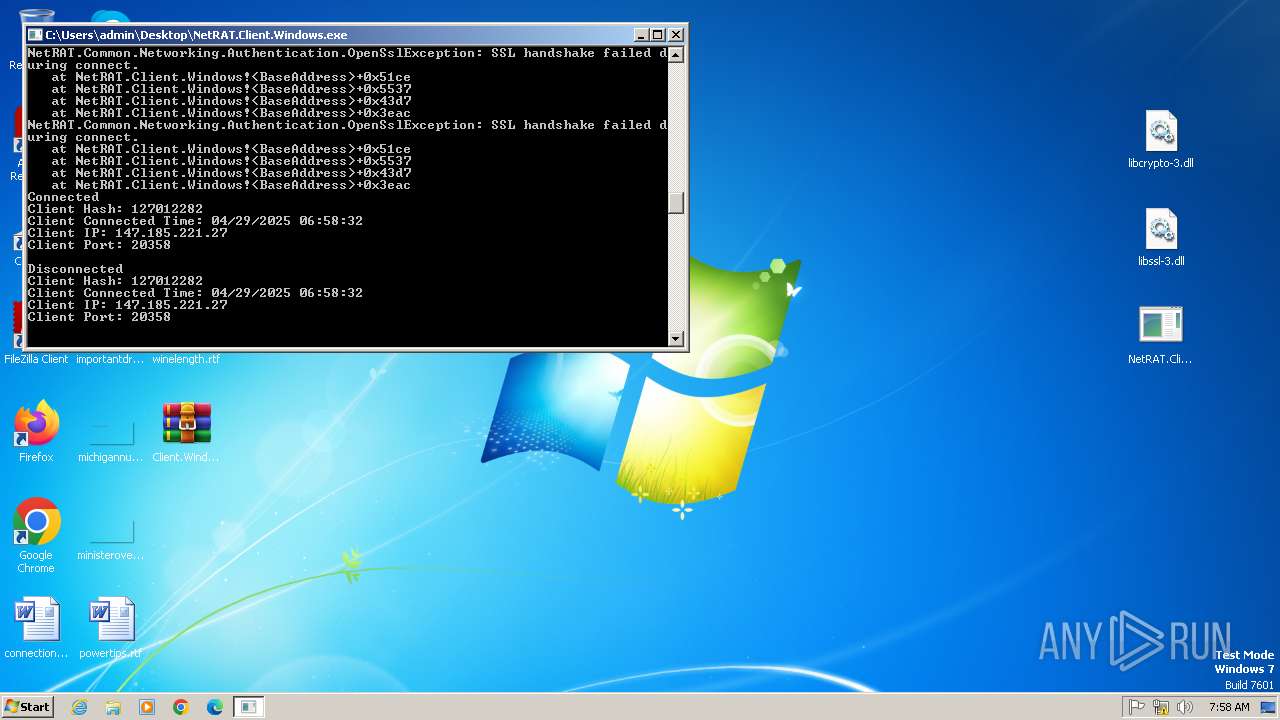
| Full analysis: | https://app.any.run/tasks/cebb6b63-a50e-48d5-a46f-0028f7dc97fe |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 06:56:24 |
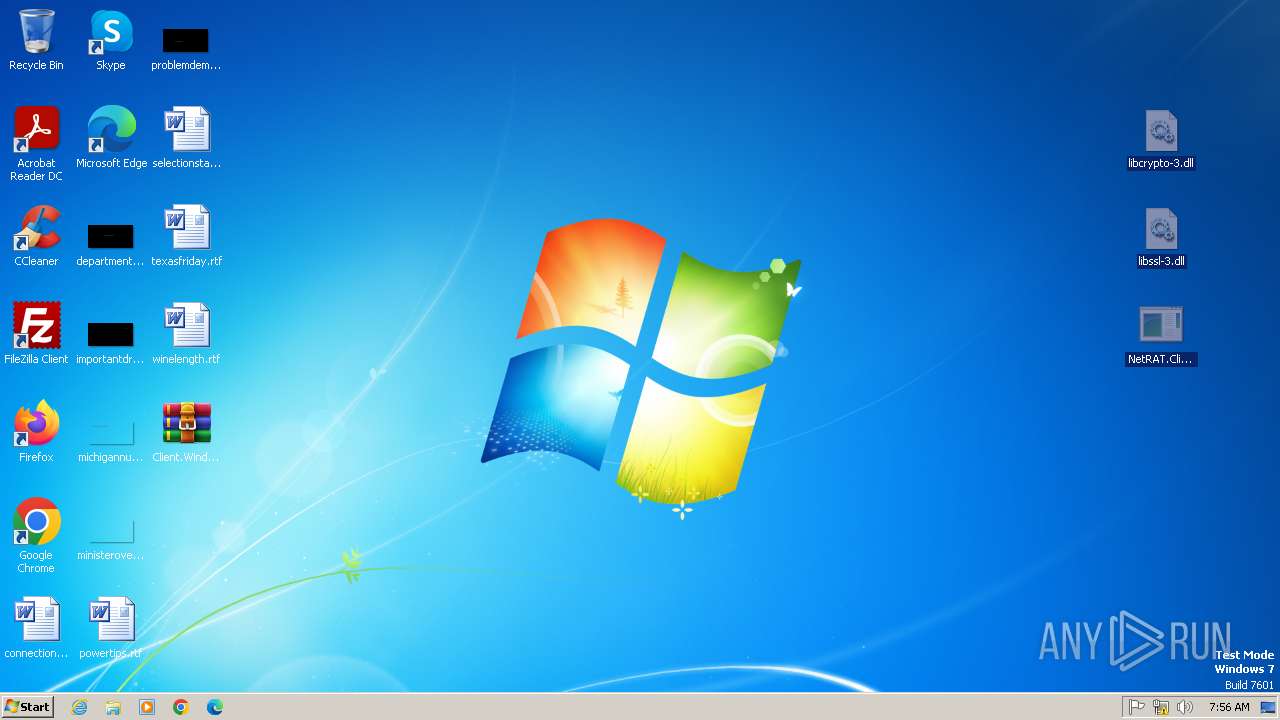
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 10AA4AA5ACB60D4C1E80259C6411A574 |
| SHA1: | 7C443851C2F178E91361080448AF0DCCEA70340D |
| SHA256: | 8DC7971573F48C18B3146ADB440A44D84CCF66A7083173C89D7F751EC6097BDF |
| SSDEEP: | 98304:aUiyRMBibWRxw08E7u4q+W1D2Wx/BK+jZfehId9gIREPb7fRzFQn7ttm6hjdx12o:VSEM88Fy |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2840)
SUSPICIOUS
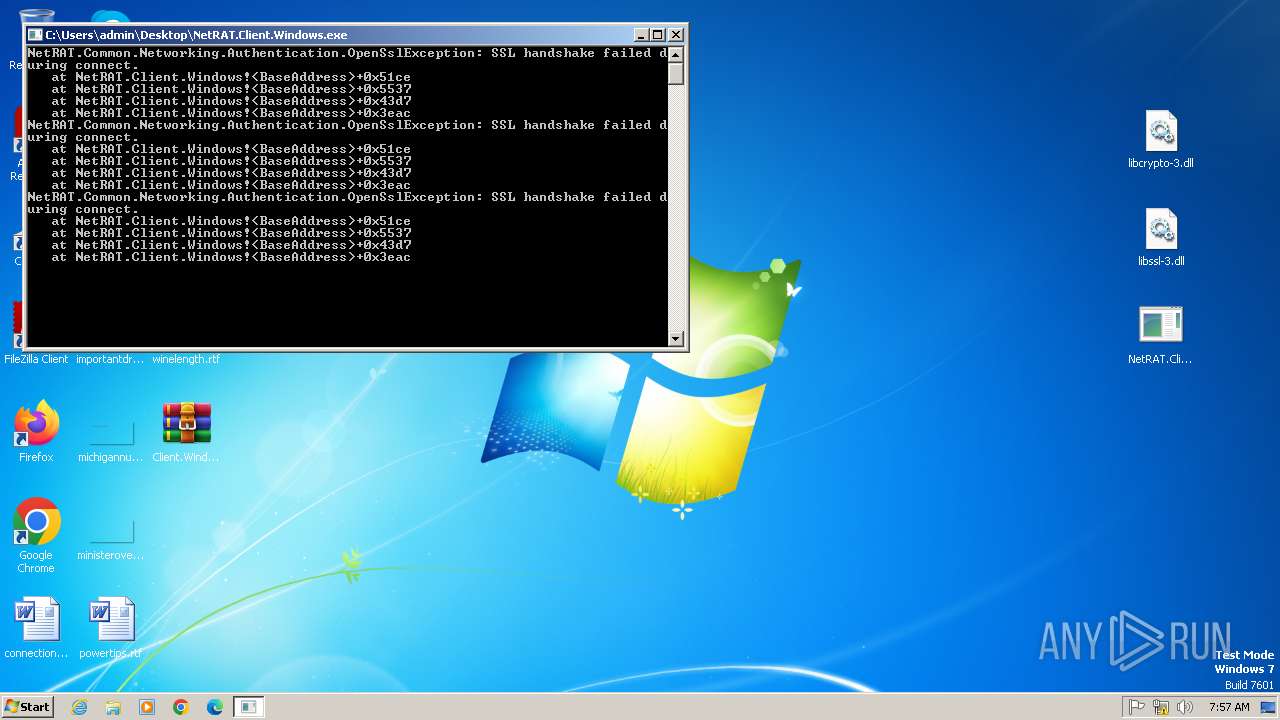
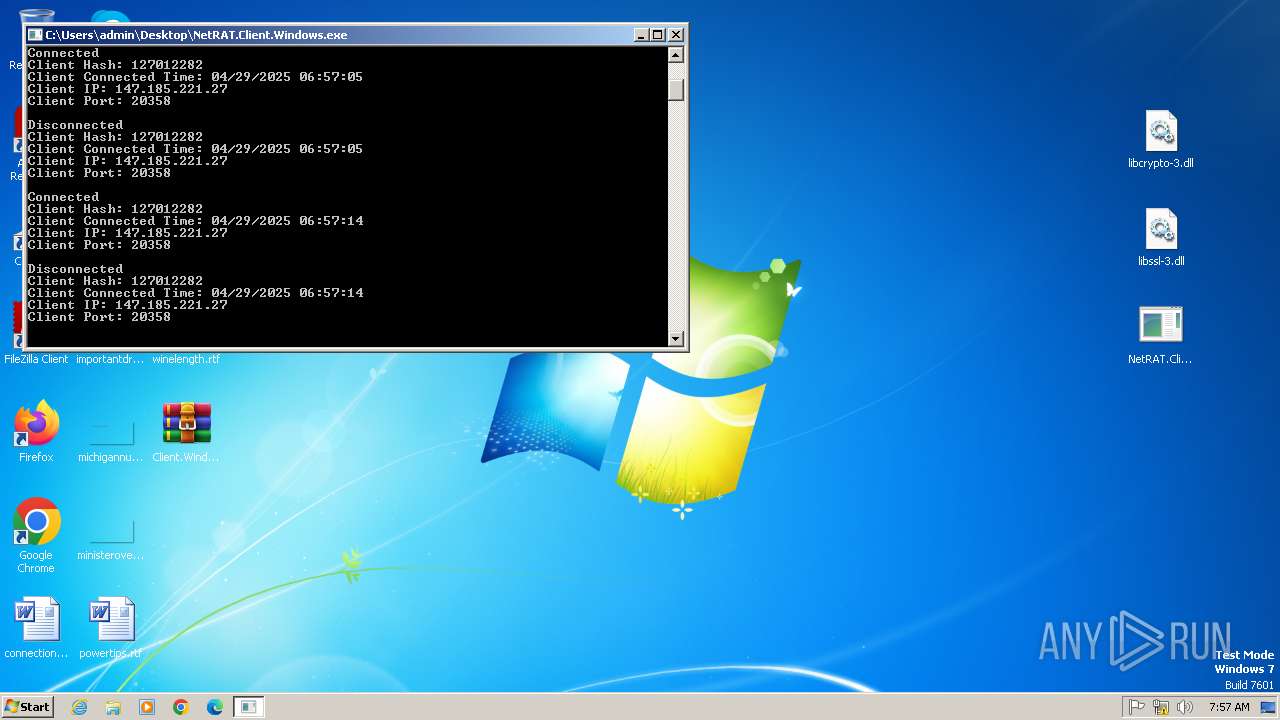
Connects to unusual port
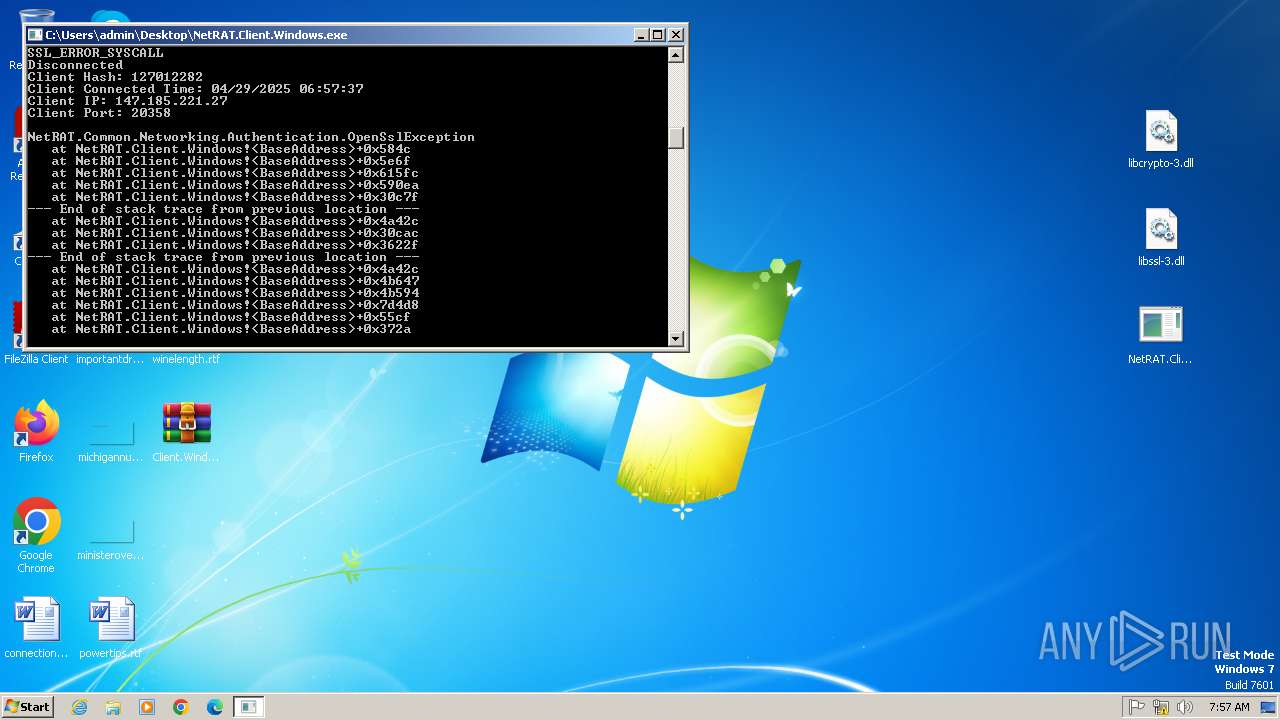
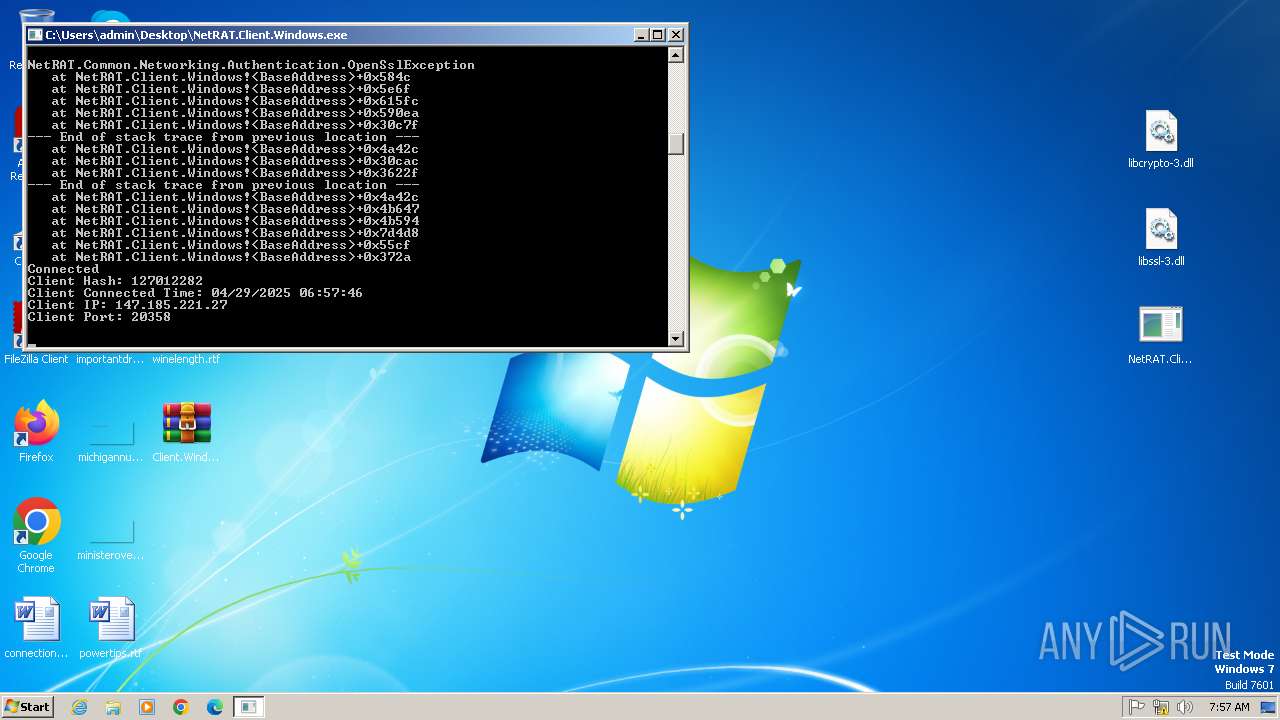
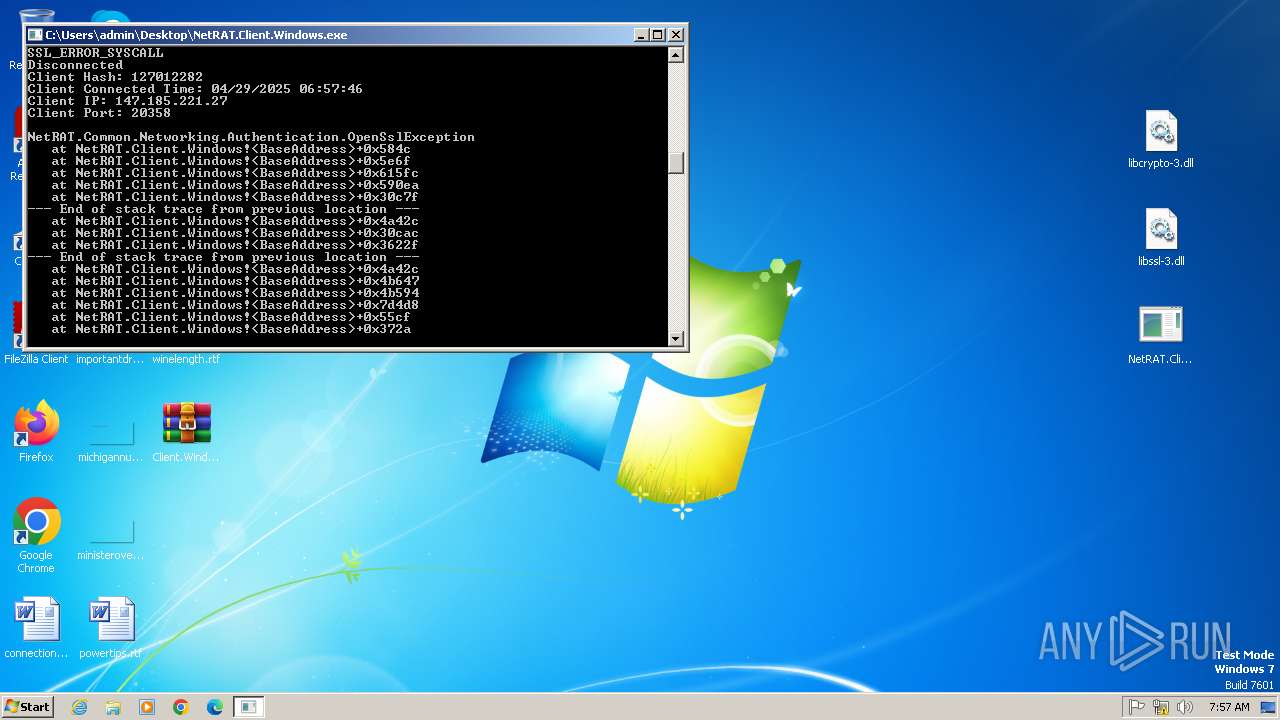
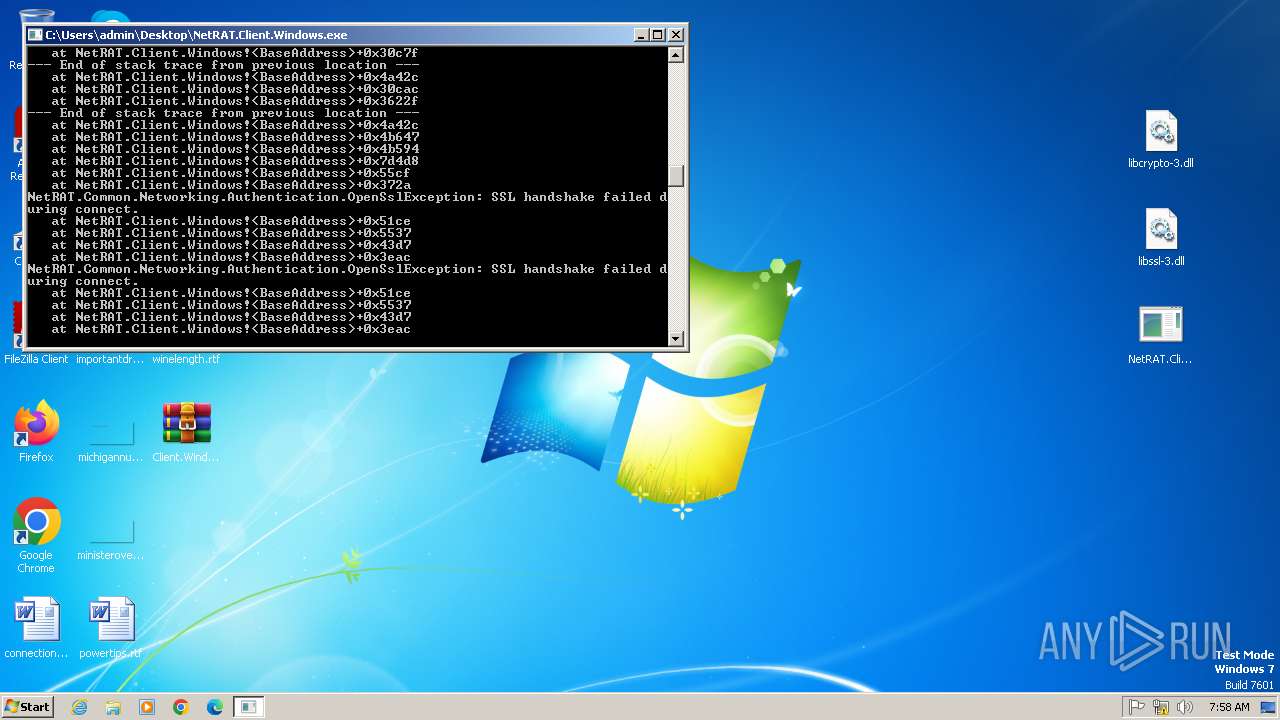
- NetRAT.Client.Windows.exe (PID: 2588)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2840)
Reads the machine GUID from the registry
- NetRAT.Client.Windows.exe (PID: 2588)
Checks supported languages
- NetRAT.Client.Windows.exe (PID: 2588)
Manual execution by a user
- NetRAT.Client.Windows.exe (PID: 2588)
Reads the computer name
- NetRAT.Client.Windows.exe (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 546340 |
| UncompressedSize: | 1263104 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | NetRAT.Client.Windows.exe |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\Desktop\NetRAT.Client.Windows.exe" | C:\Users\admin\Desktop\NetRAT.Client.Windows.exe | explorer.exe | ||||||||||||
User: admin Company: UnknownComp Integrity Level: MEDIUM Description: NetRAT Client Version: 2025.4.29.10024 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Client.Windows.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 913
Read events
2 891
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Client.Windows.rar | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.10590\libssl-3.dll | executable | |
MD5:44219E1430D570B42219623DAFE6F721 | SHA256:2459B52803E8D6A2A6D93A775A8618966C63265BF88AD8C0F761063783D96551 | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.10590\libcrypto-3.dll | executable | |
MD5:B80B7DE70E5250315EC6947472754EAF | SHA256:503AB52E2E455BB31E6B5D9983BDCEE758DDF3B5F393962F78ACD8420EFED69B | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.10590\NetRAT.Client.Windows.exe | executable | |
MD5:D2D3A849A6E739BD75A66743707074ED | SHA256:ECE9348FD02C9A6EBF1E991343865709D06BF488C31BE11113CE6B9DFFACF500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
21
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2588 | NetRAT.Client.Windows.exe | 147.185.221.27:20358 | european-liability.gl.at.ply.gg | PLAYIT-GG | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
european-liability.gl.at.ply.gg |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
1080 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |