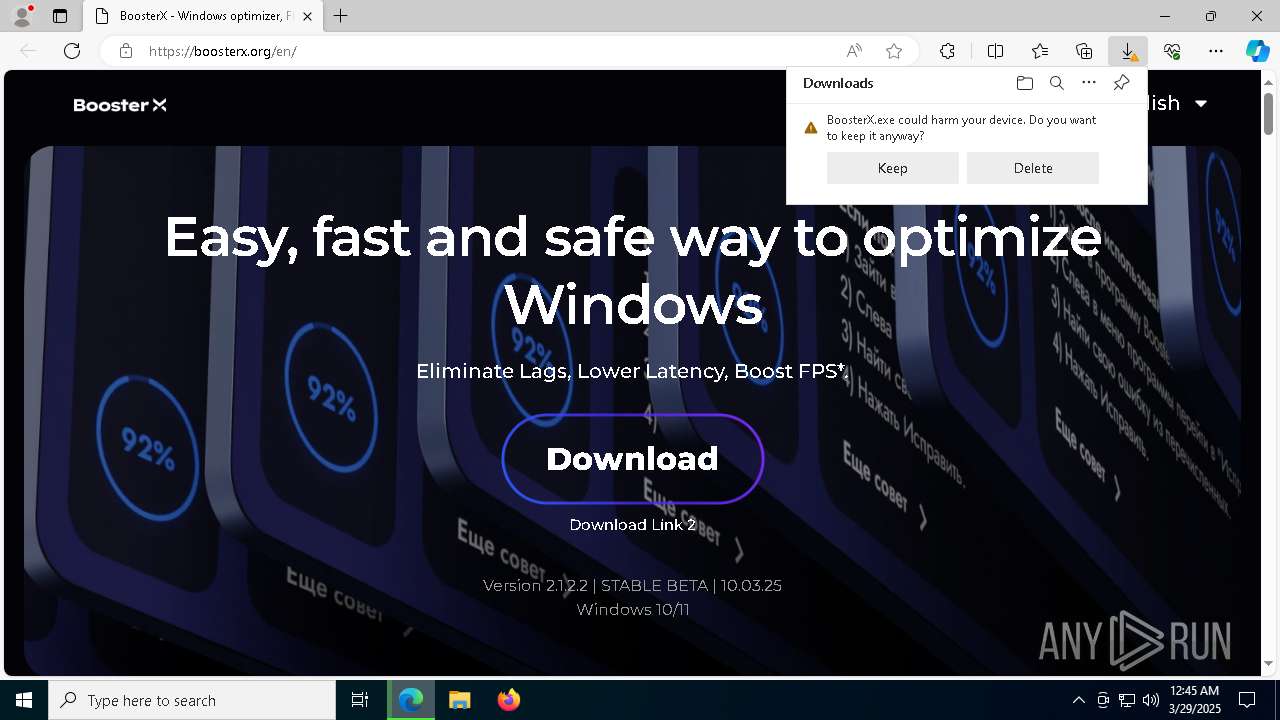
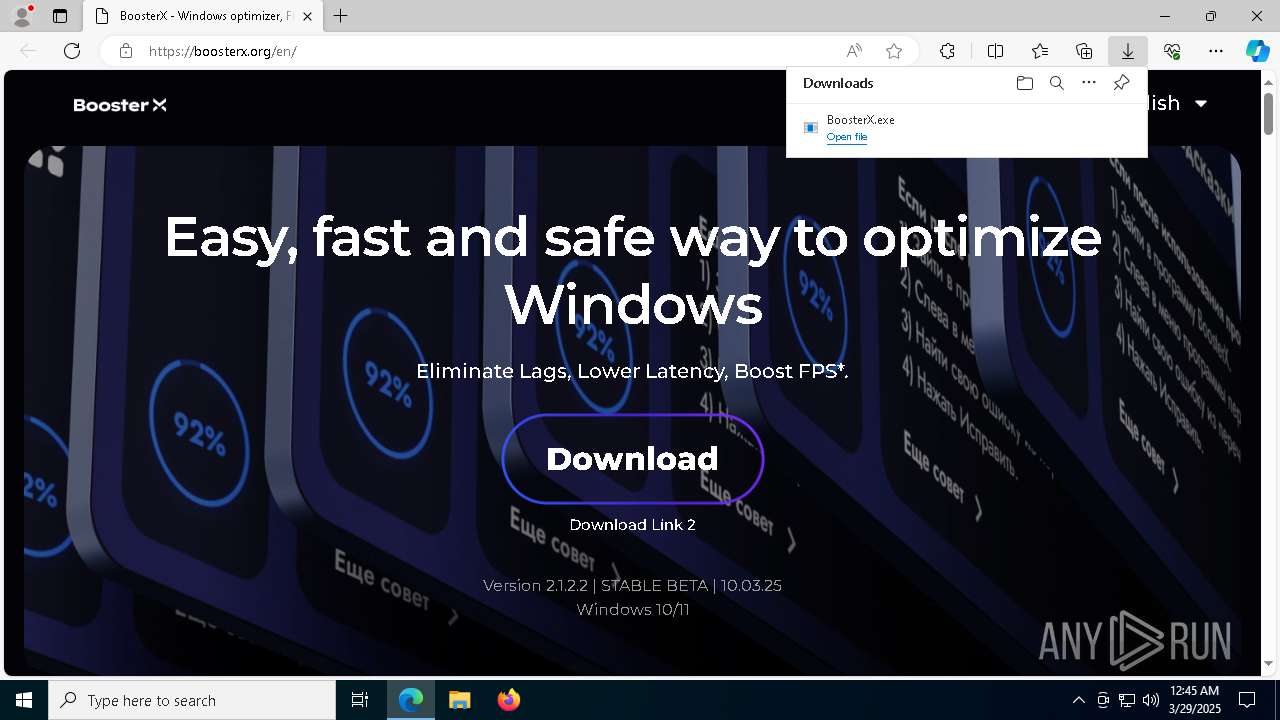
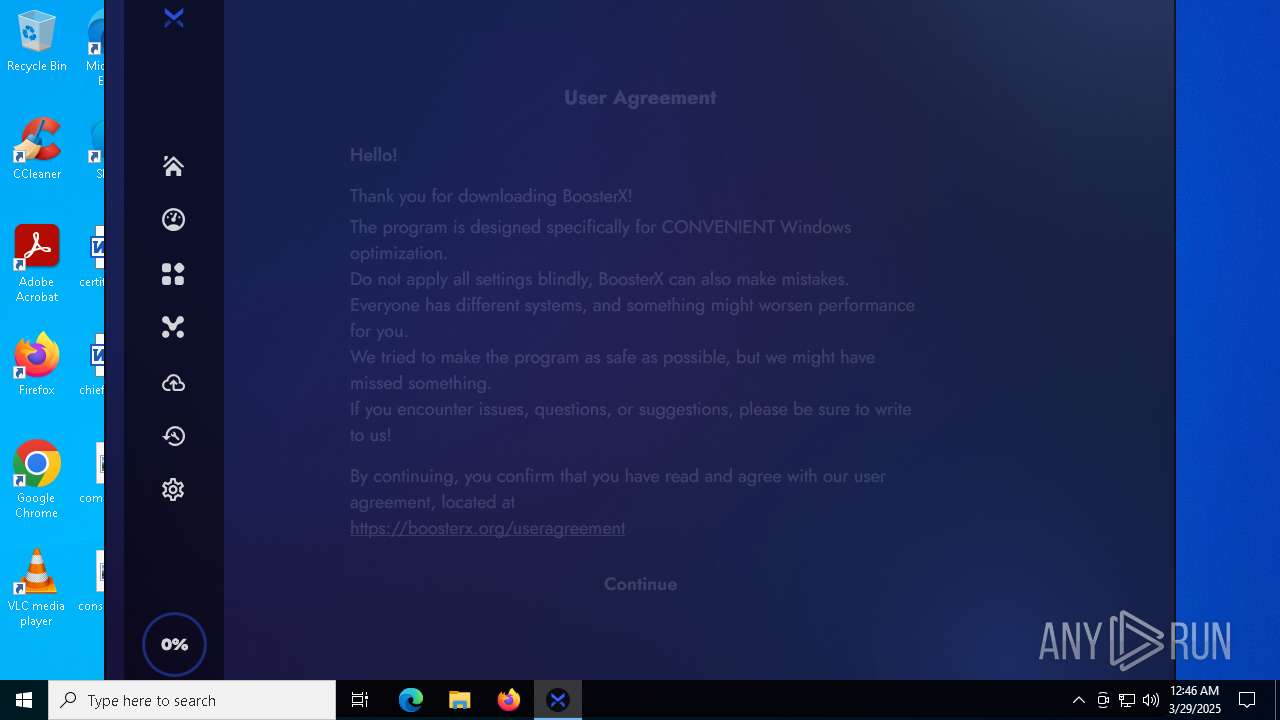
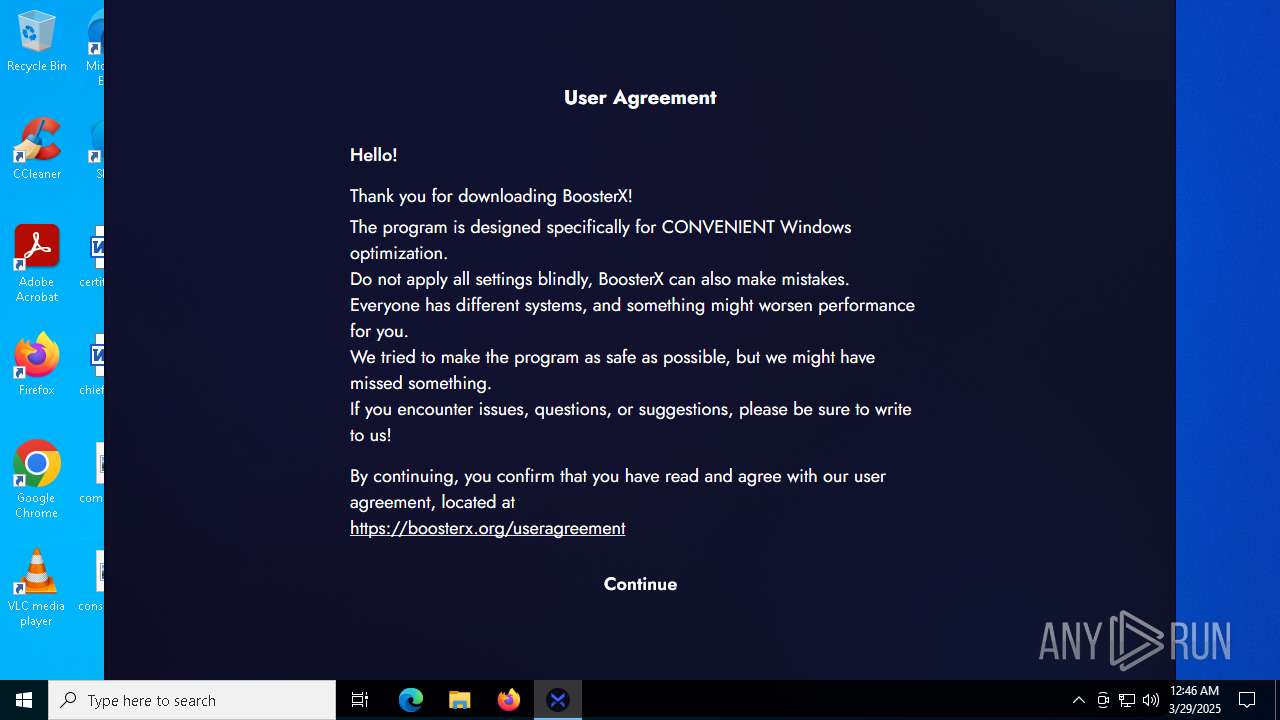
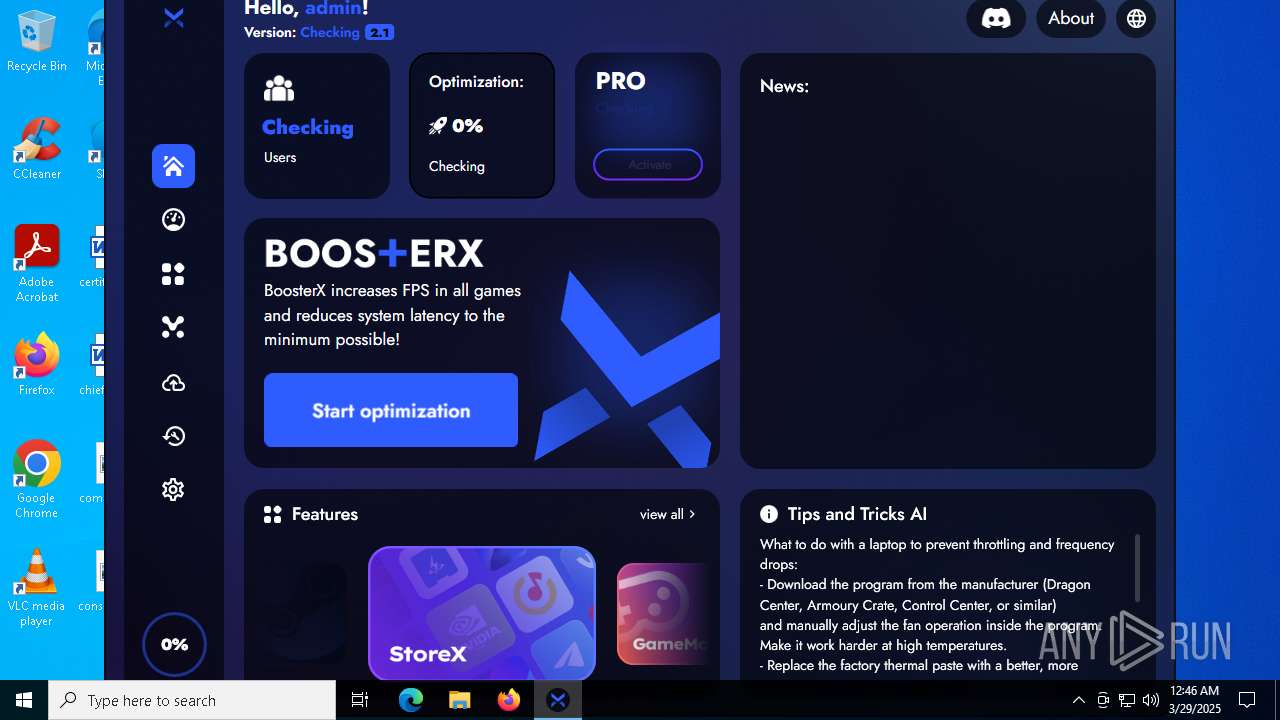
| URL: | https://boosterx.org/en/ |
| Full analysis: | https://app.any.run/tasks/3b24a4e9-de01-49ae-b9cf-3d9b7de6295b |
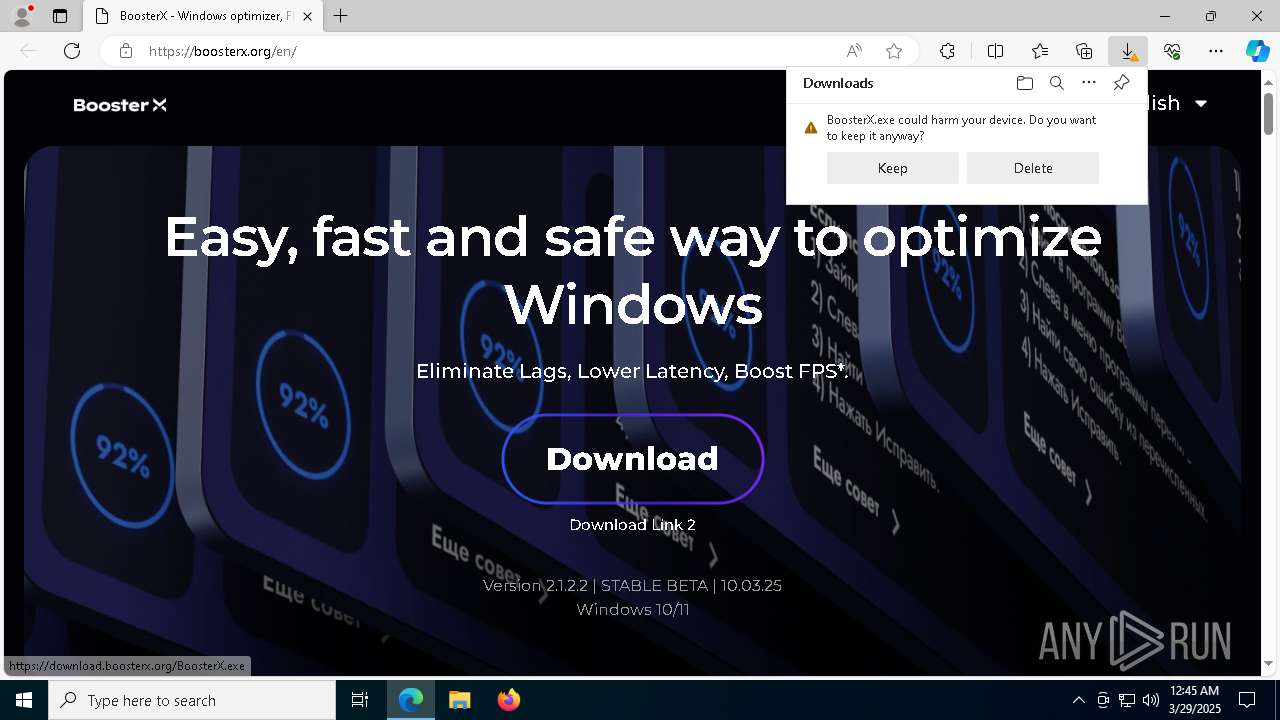
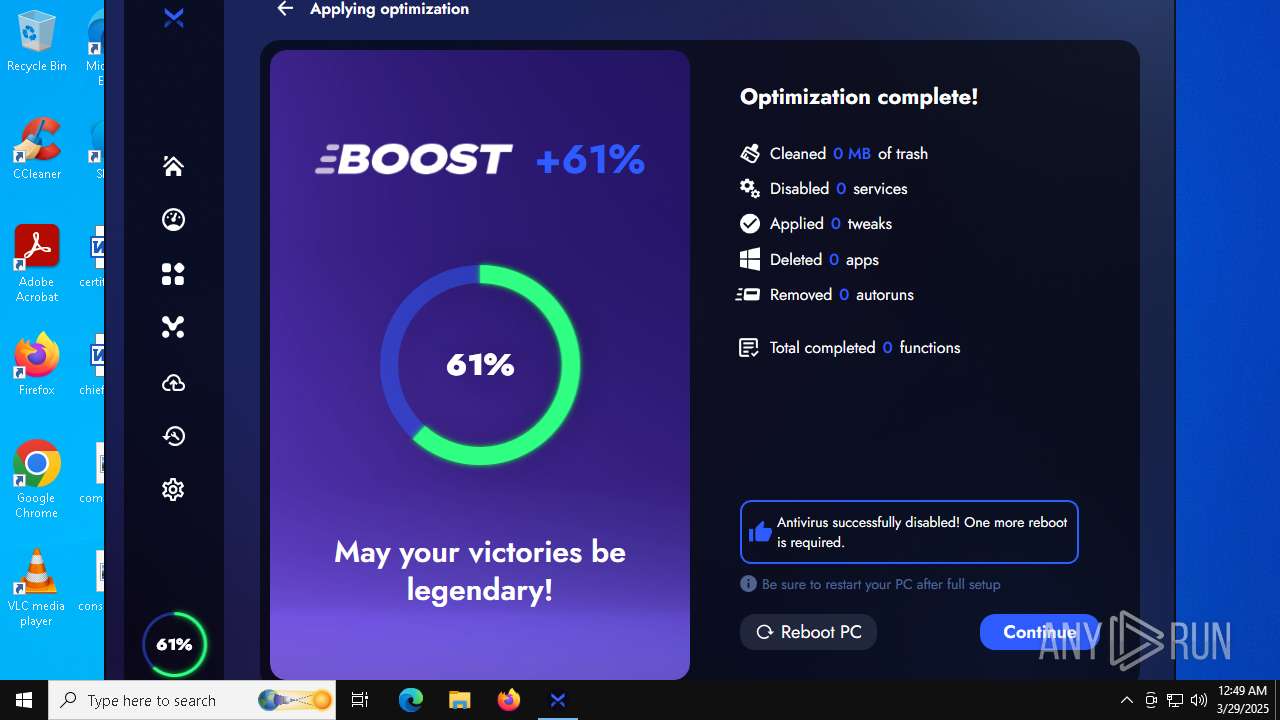
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2025, 00:45:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DB8D1DCC756227449D23021431778E4D |
| SHA1: | F99D7D191C6BE568E38DEFDDF213F80DC78A5F49 |
| SHA256: | 8DC26F2D579785B9274D568ACA7A78148C8DA2F77AFD768A54F454F118EFF200 |
| SSDEEP: | 3:N8KY6:2KY6 |
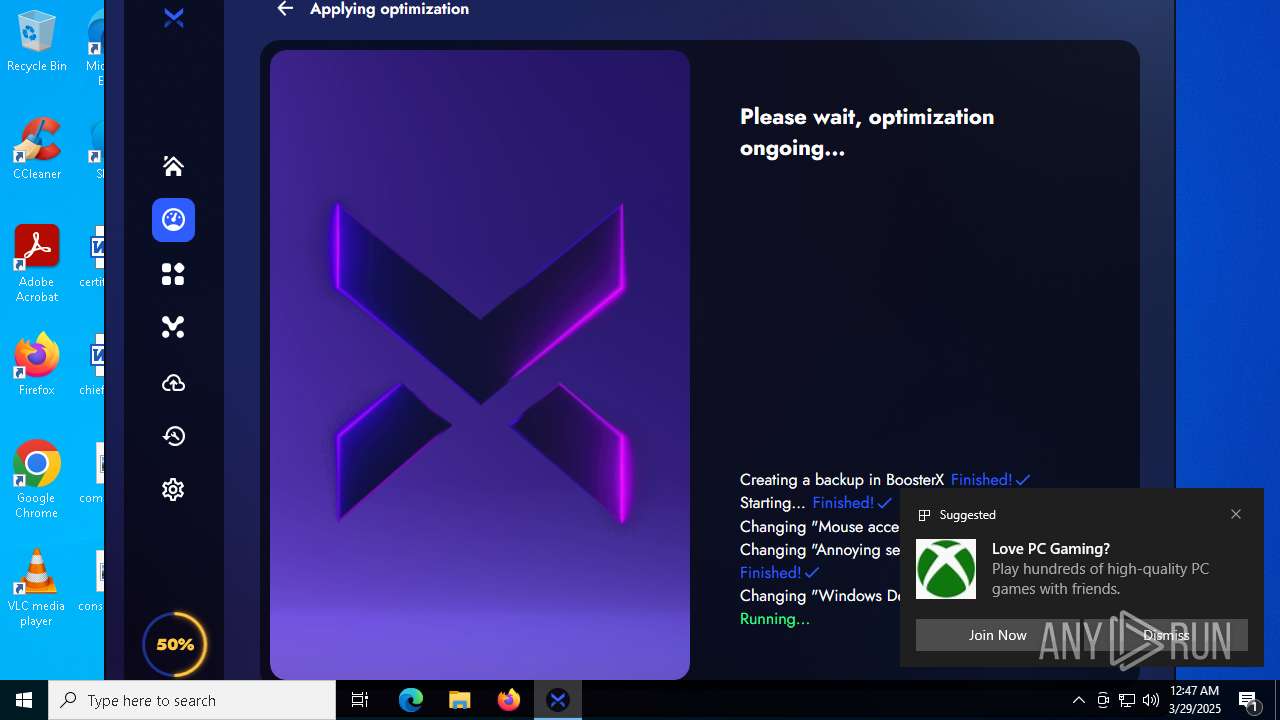
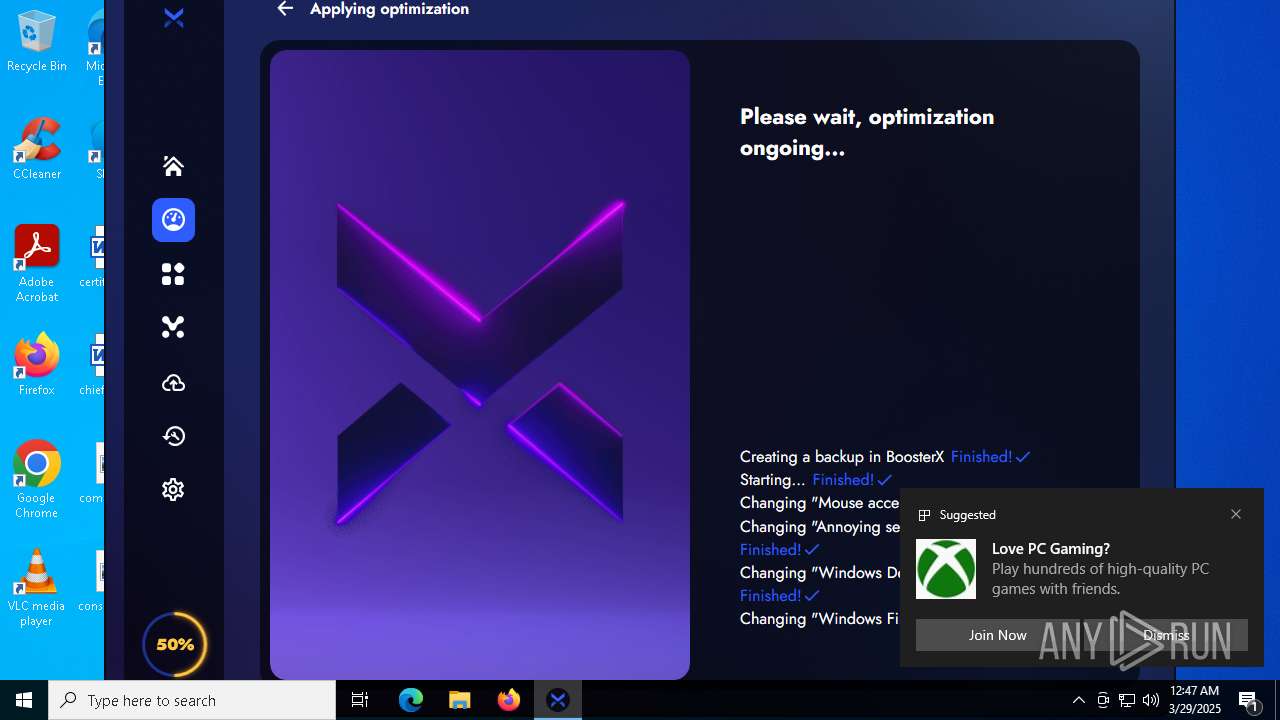
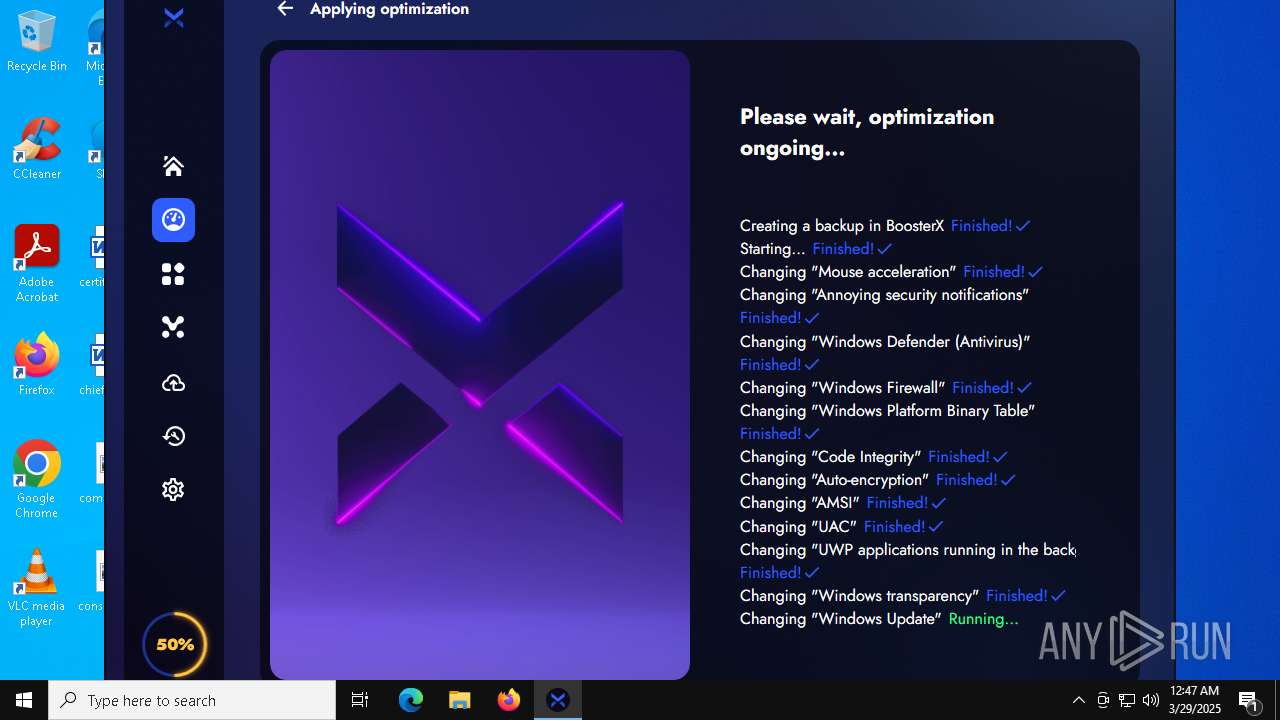
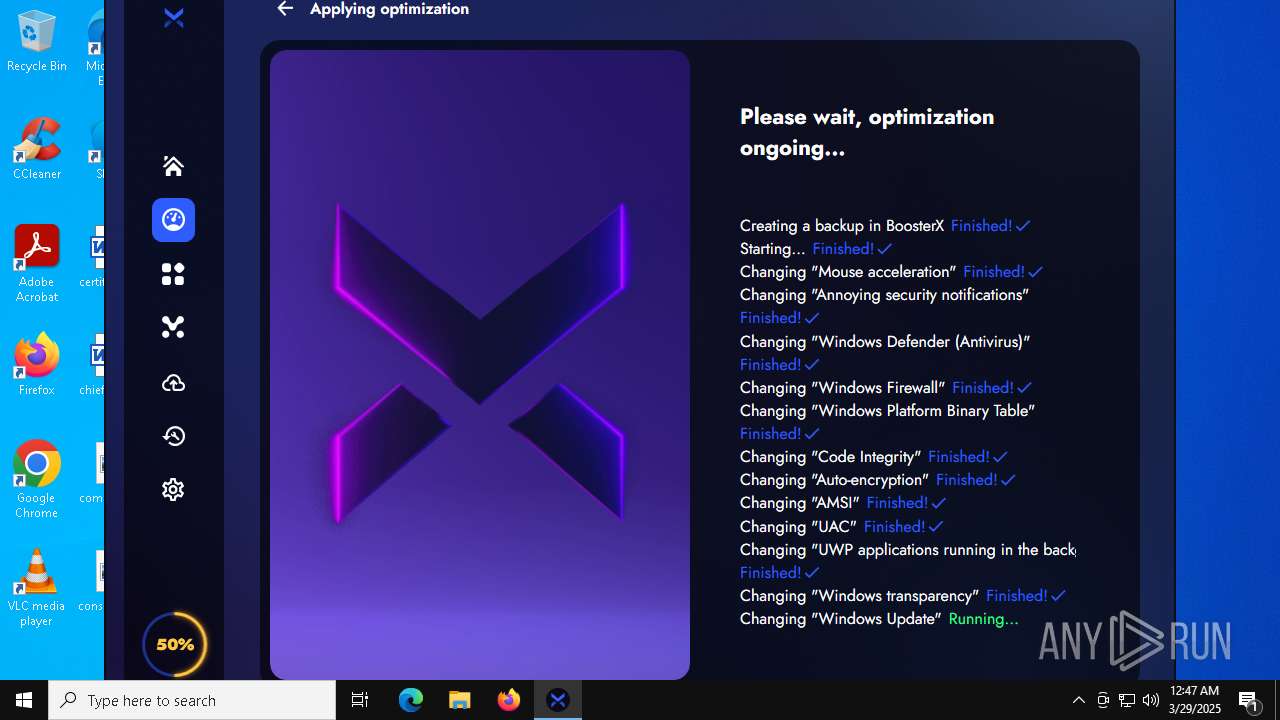
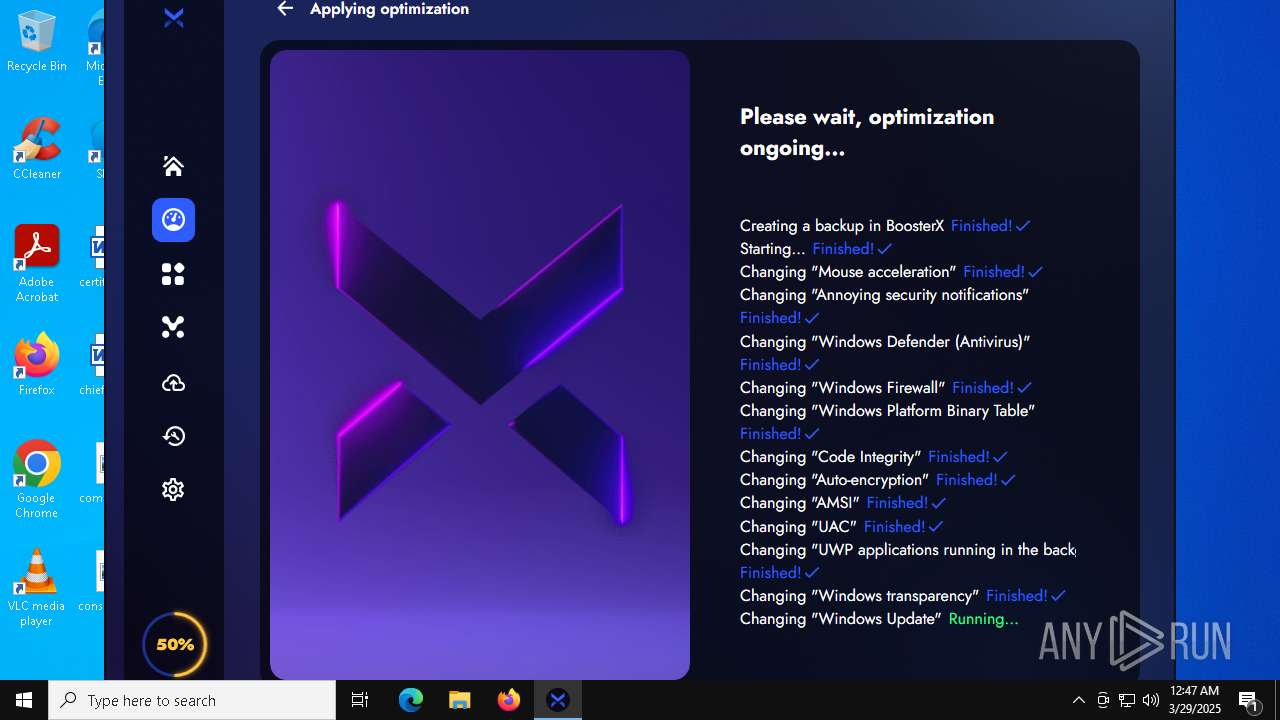
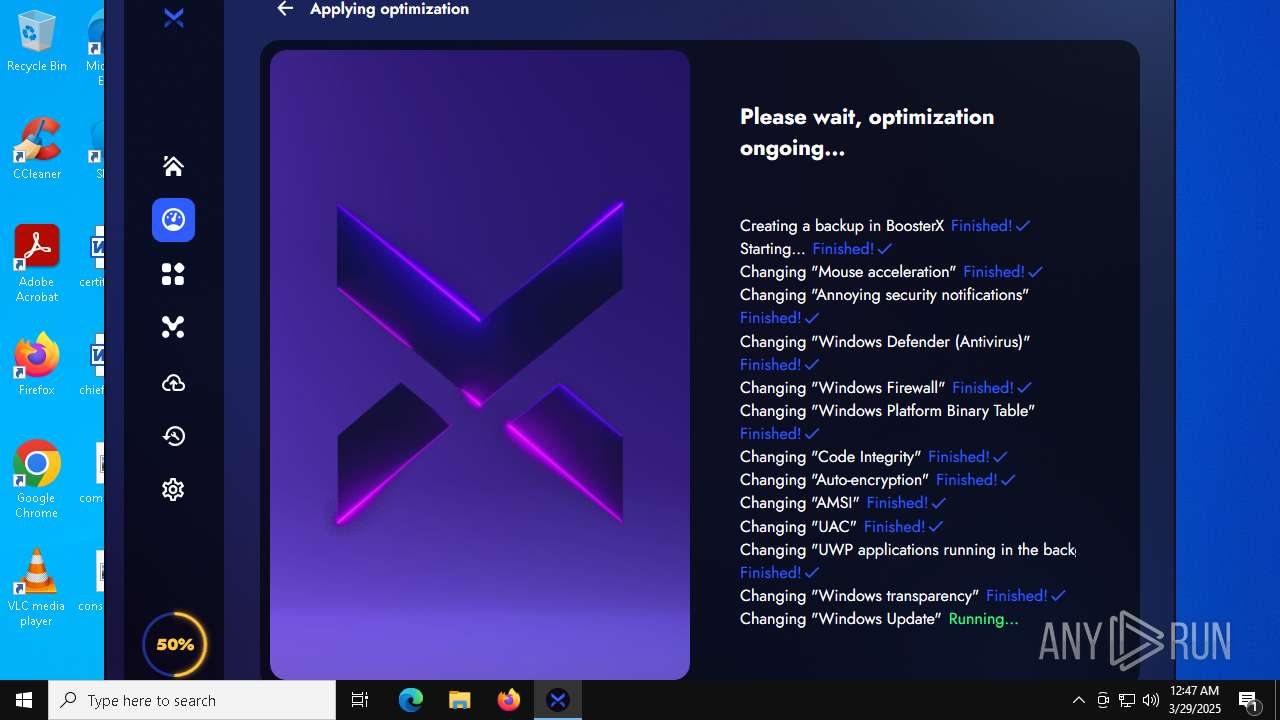
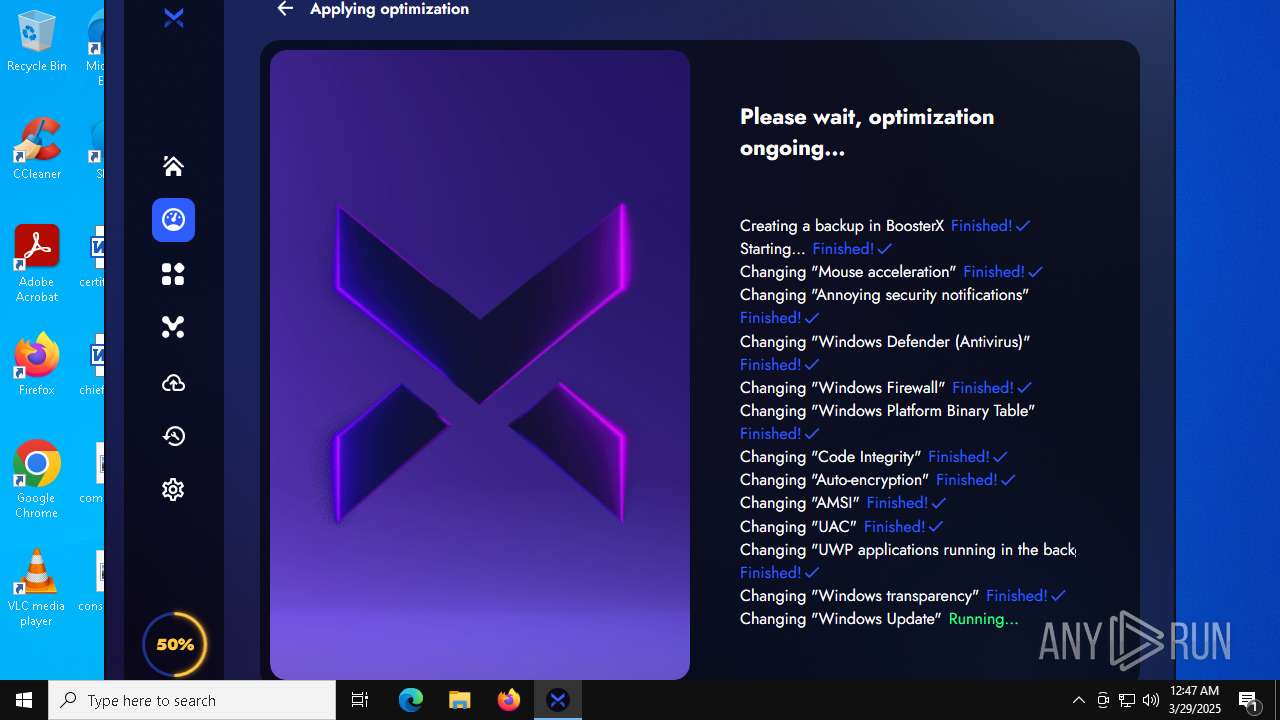
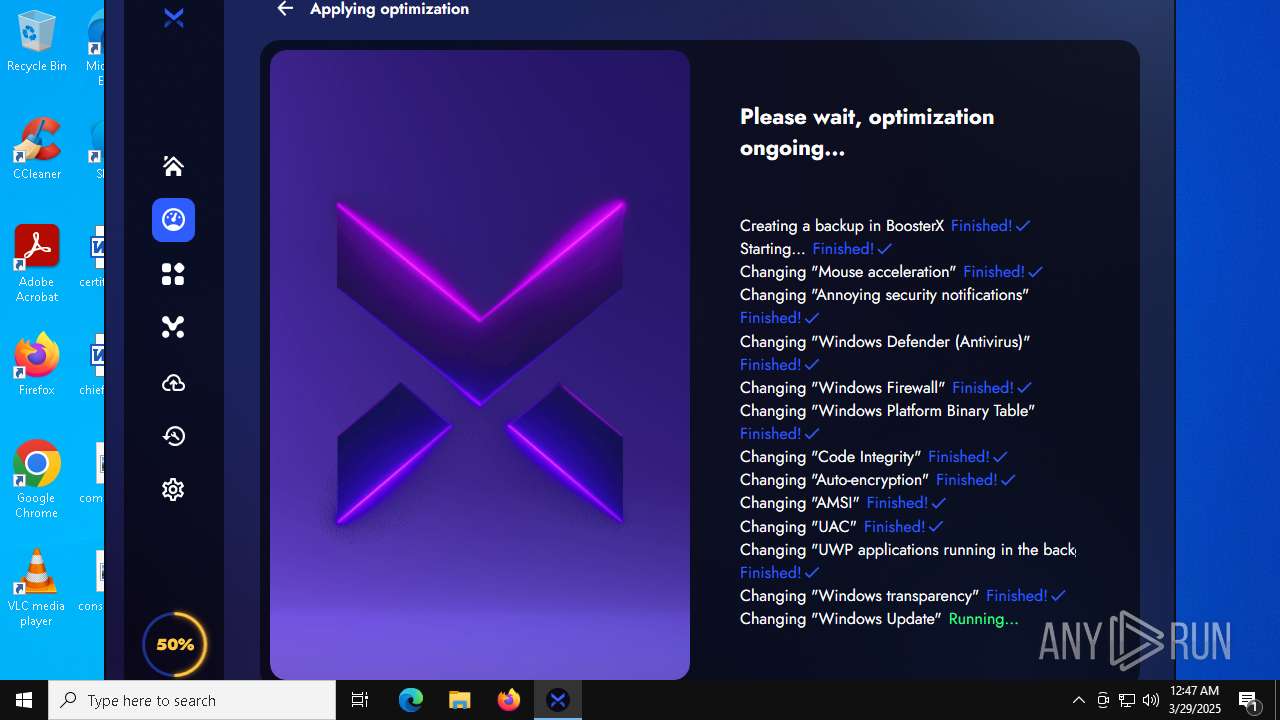
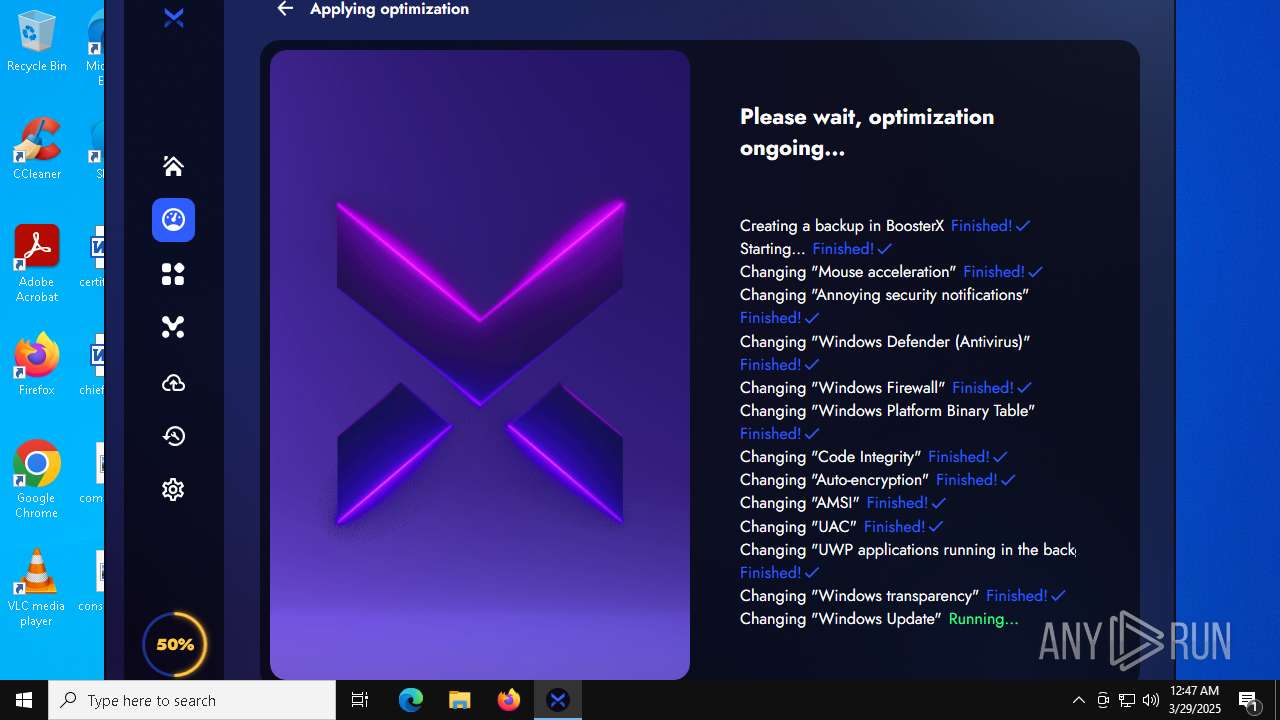
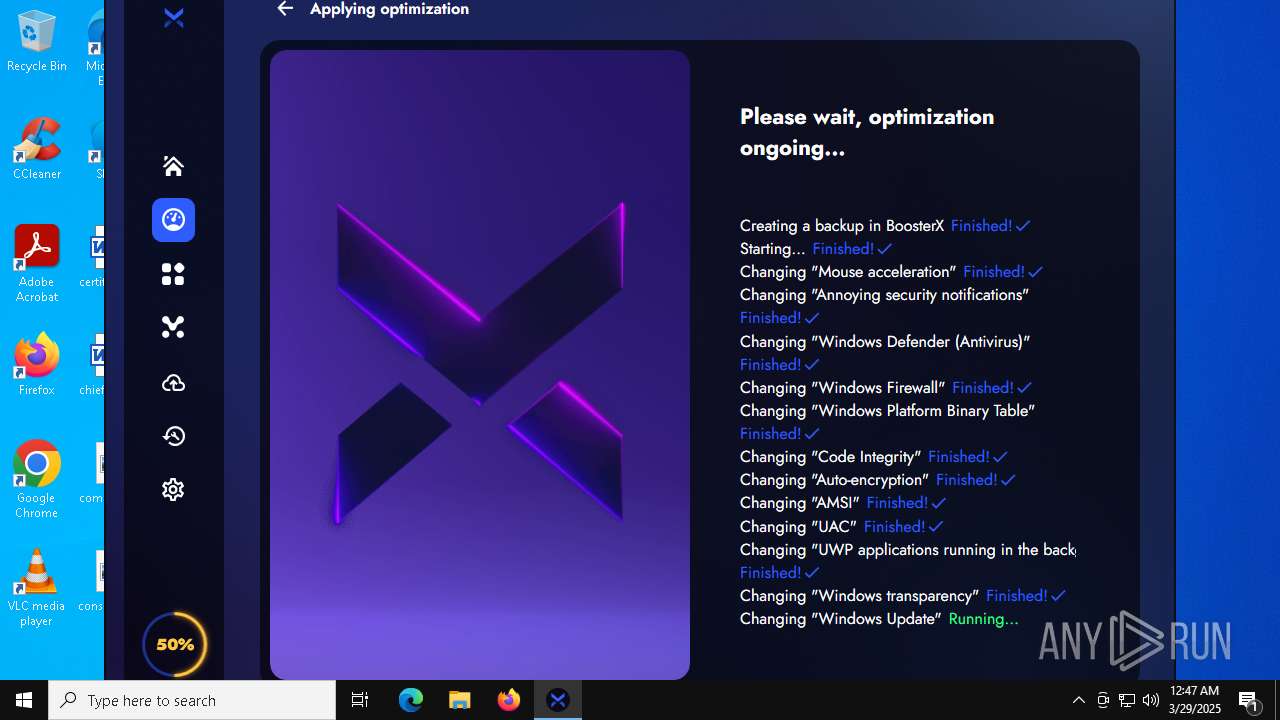
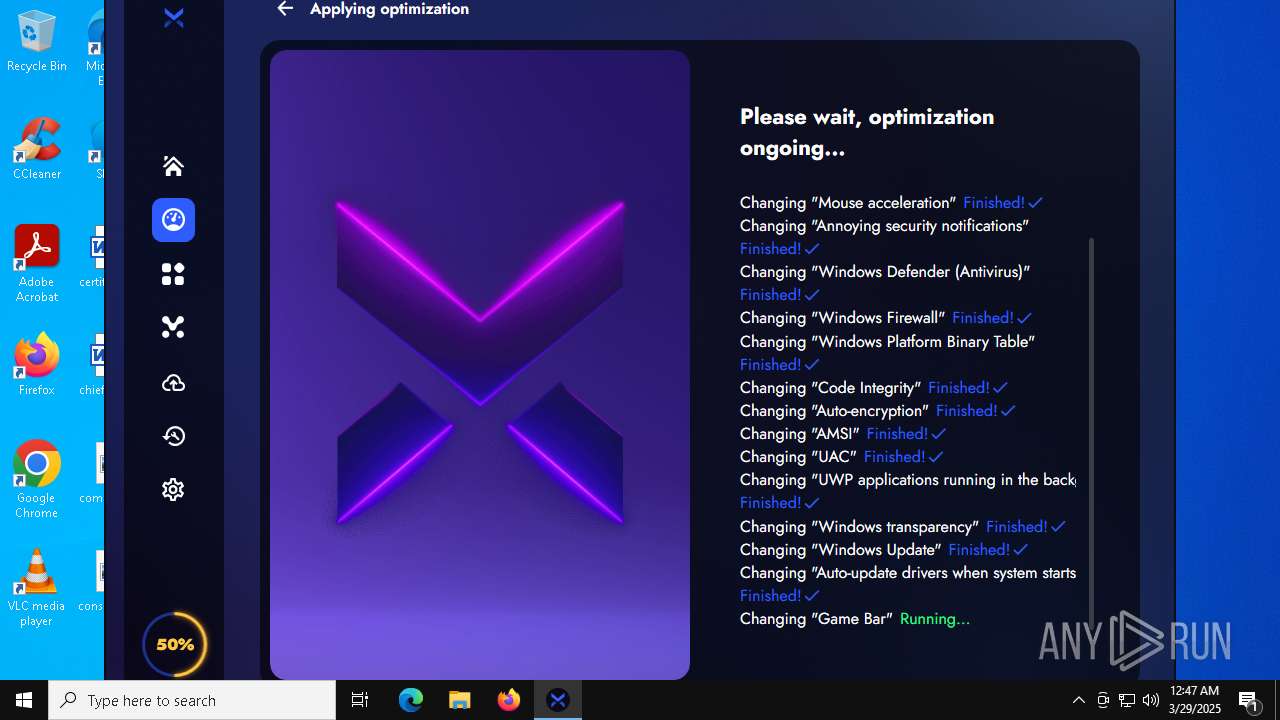
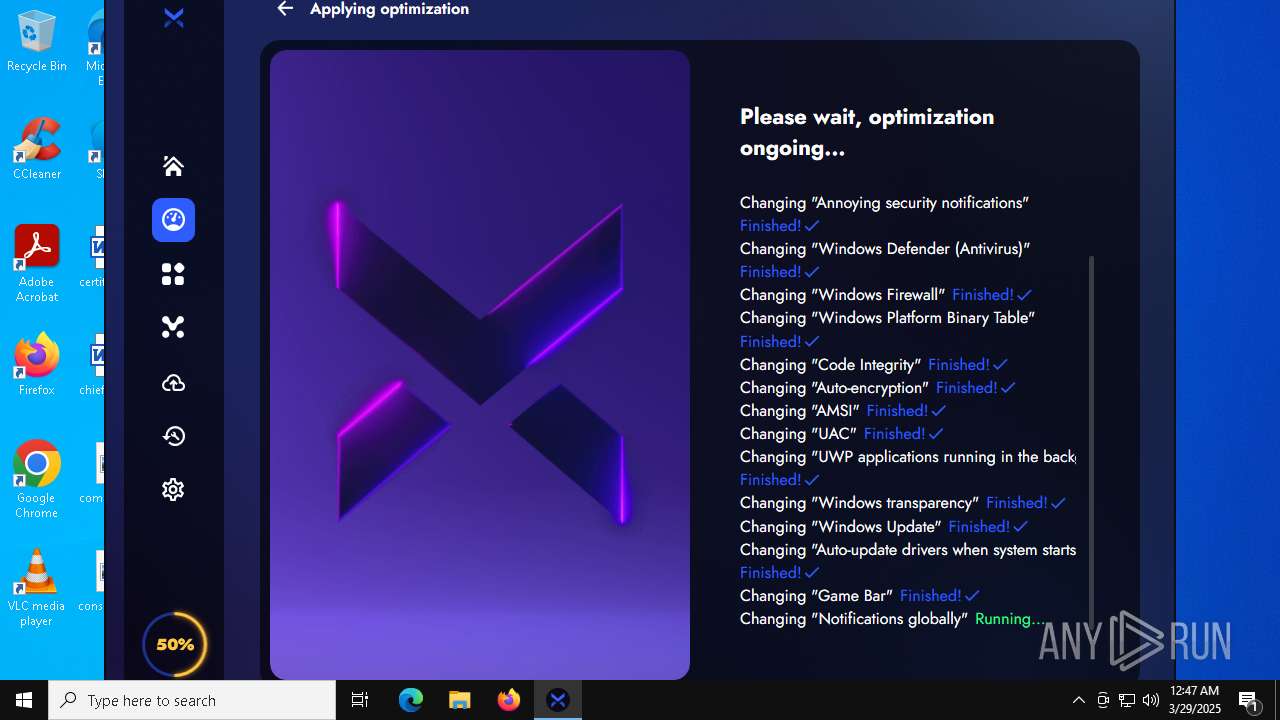
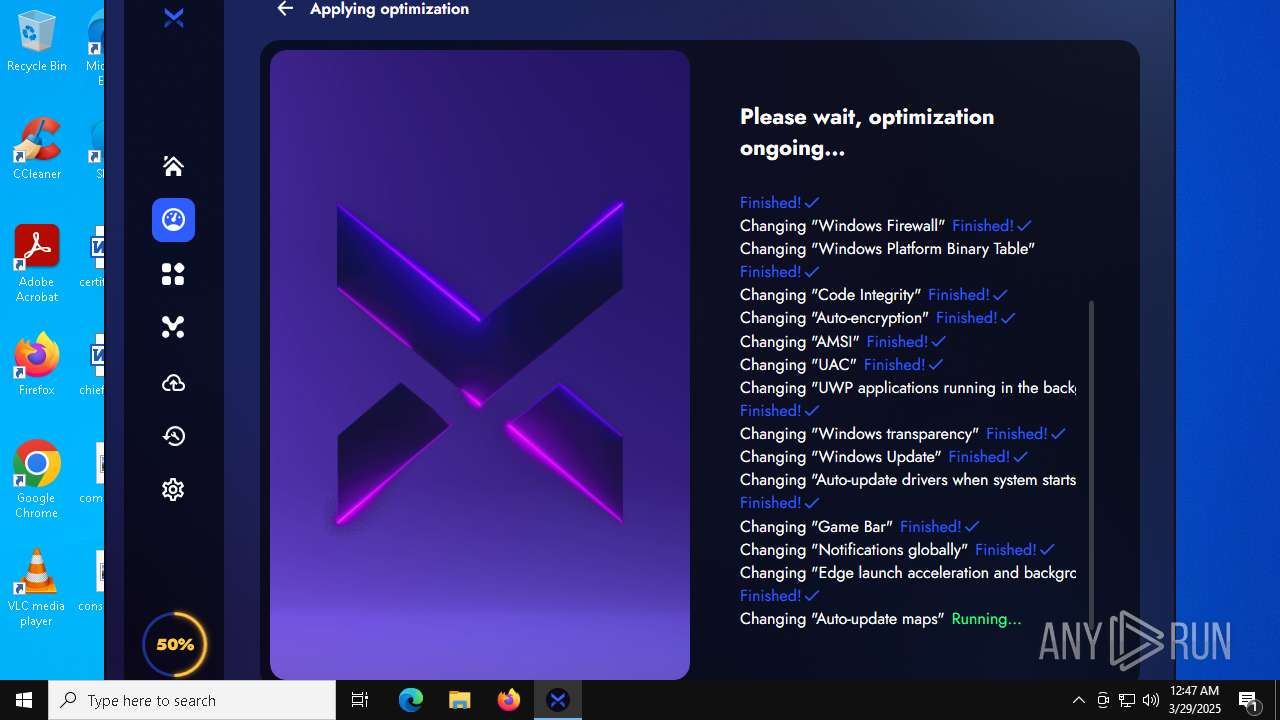
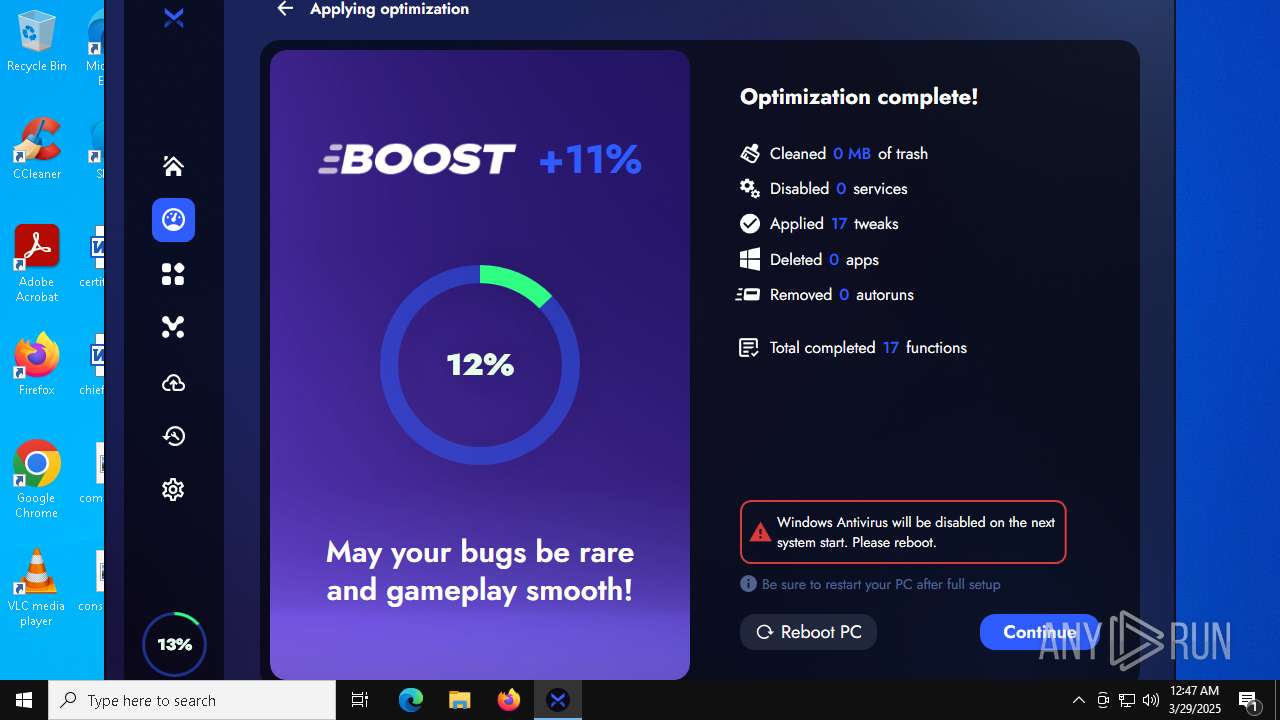
MALICIOUS
MENORAH has been detected (YARA)
- BoosterX.exe (PID: 7916)
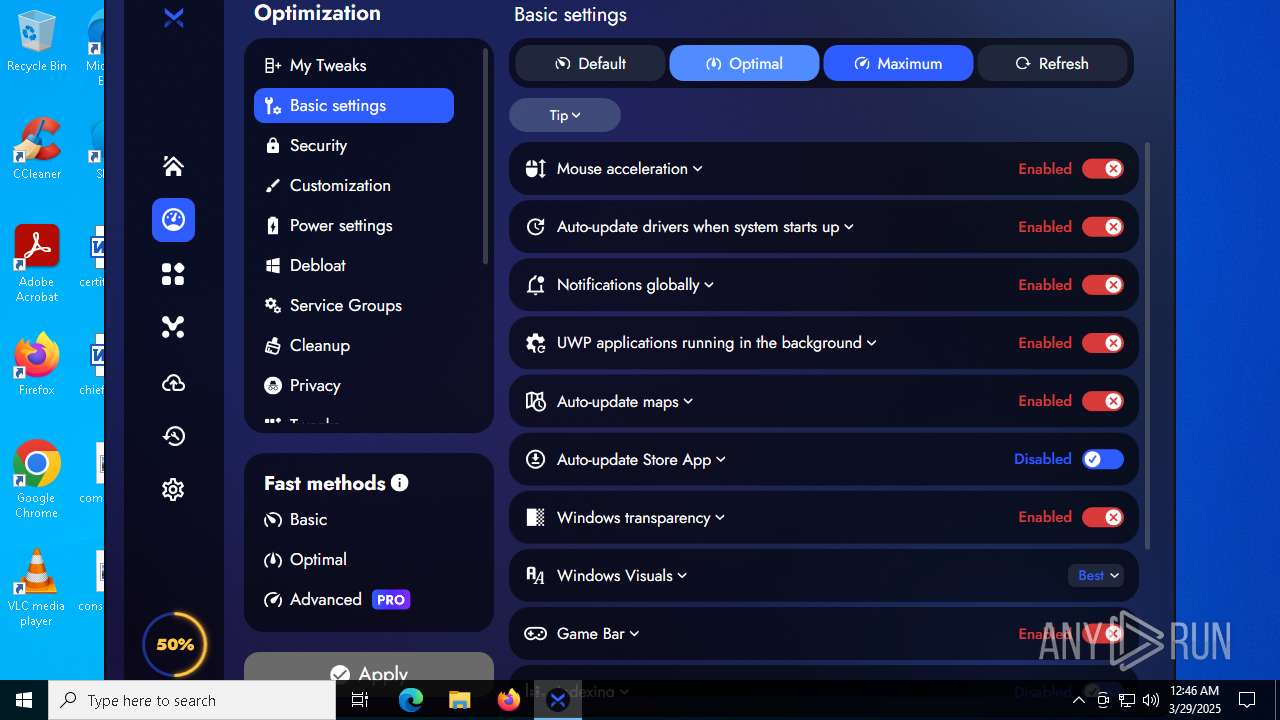
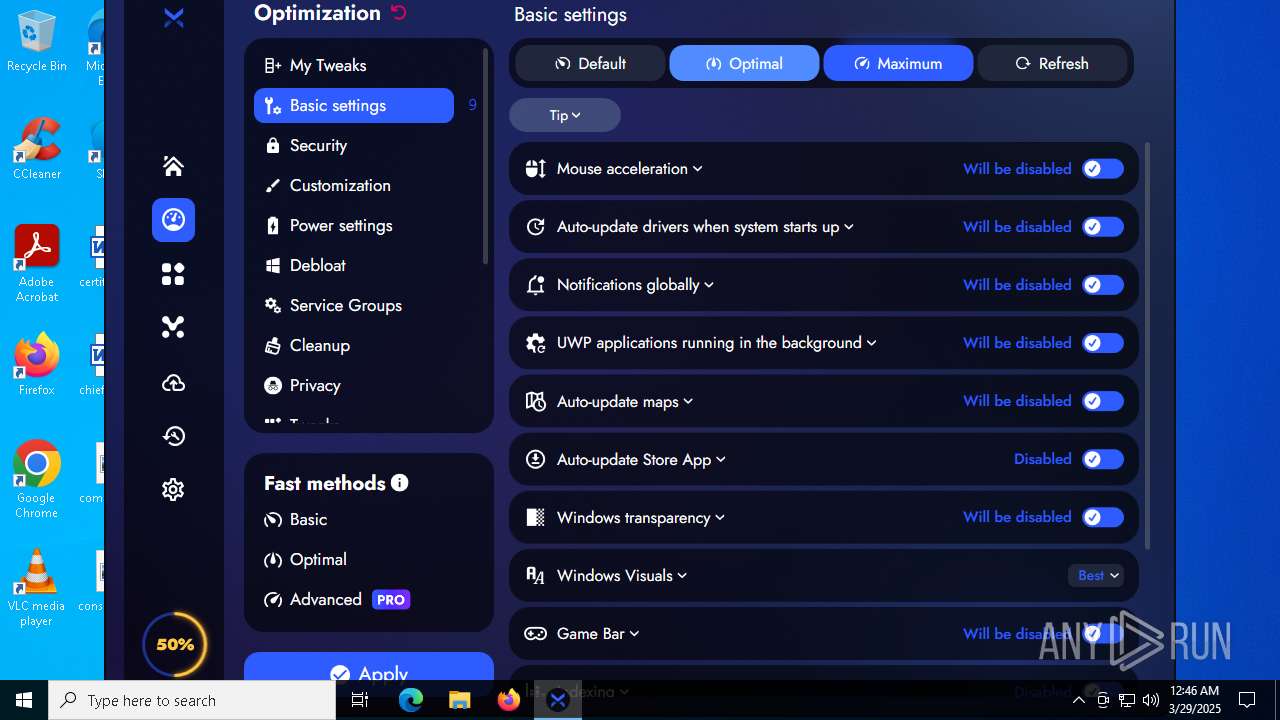
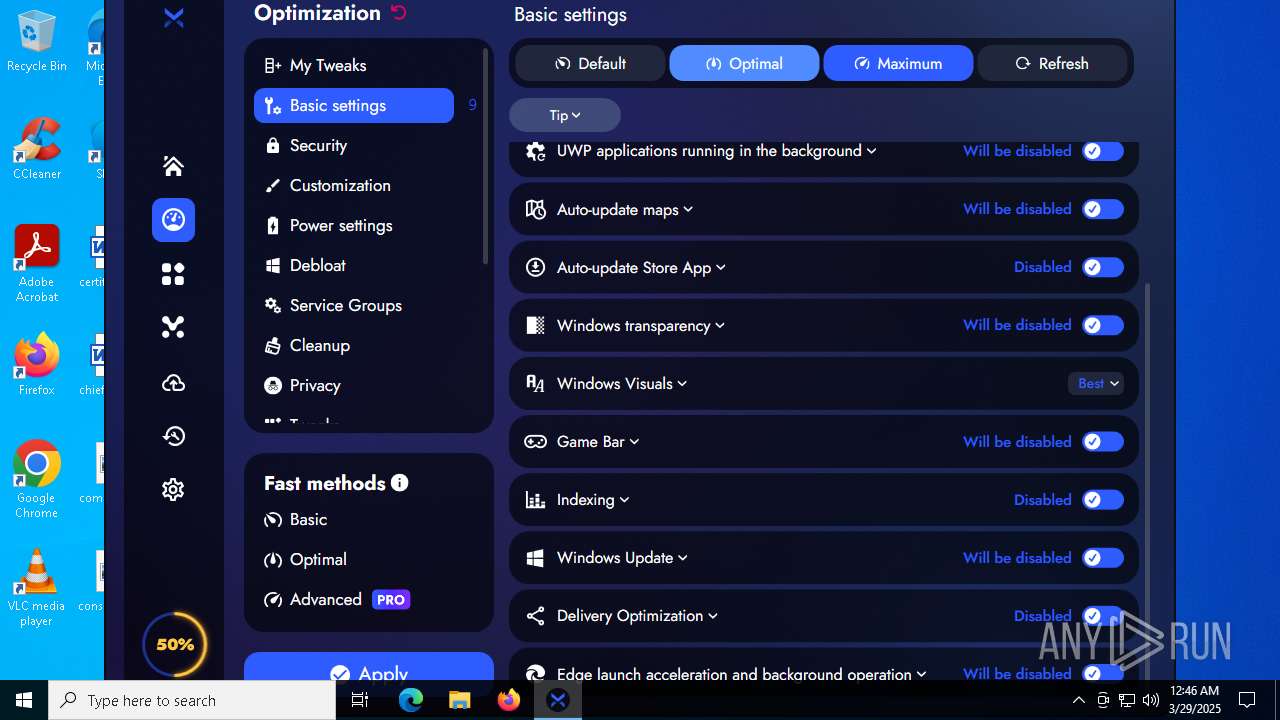
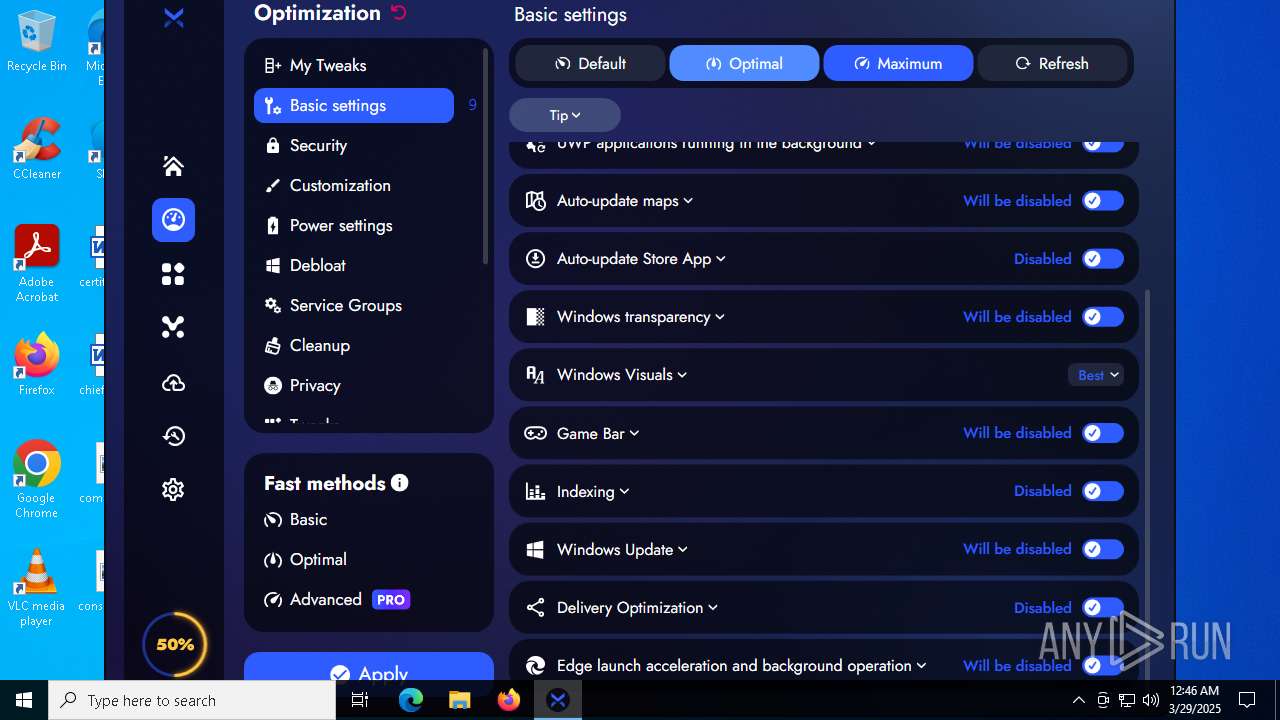
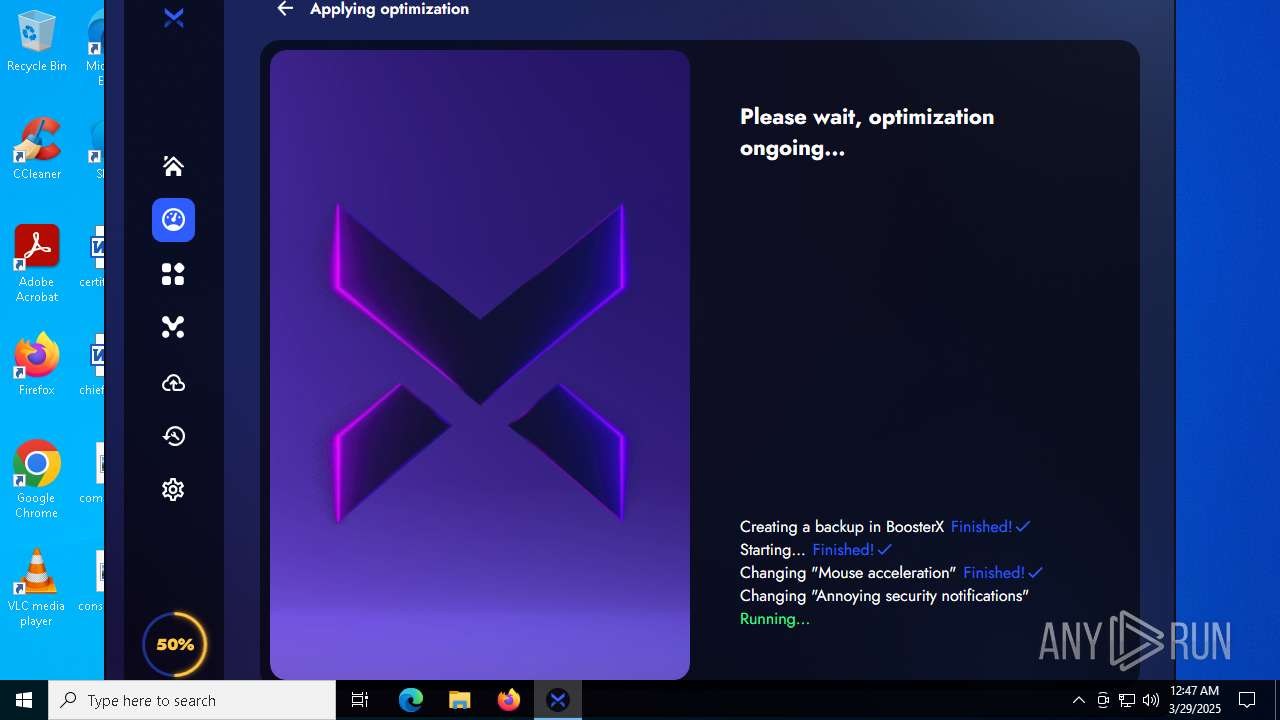
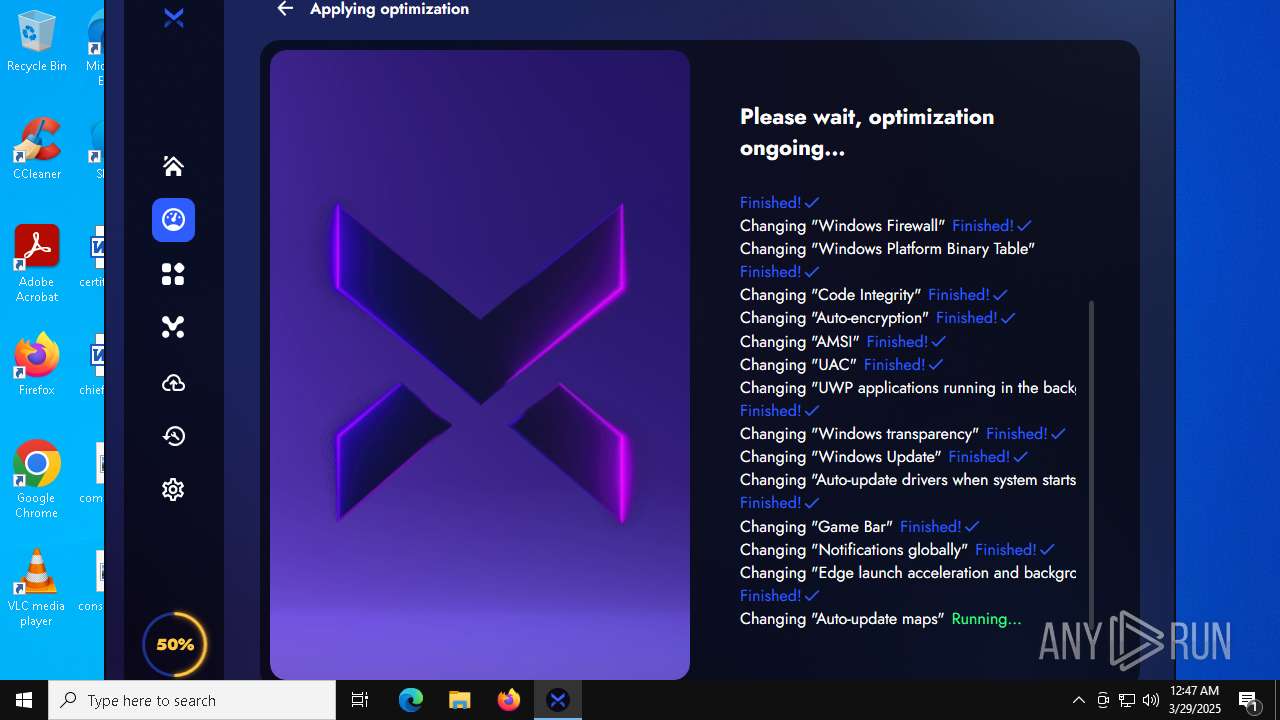
Changes the Windows auto-update feature
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Runs injected code in another process
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
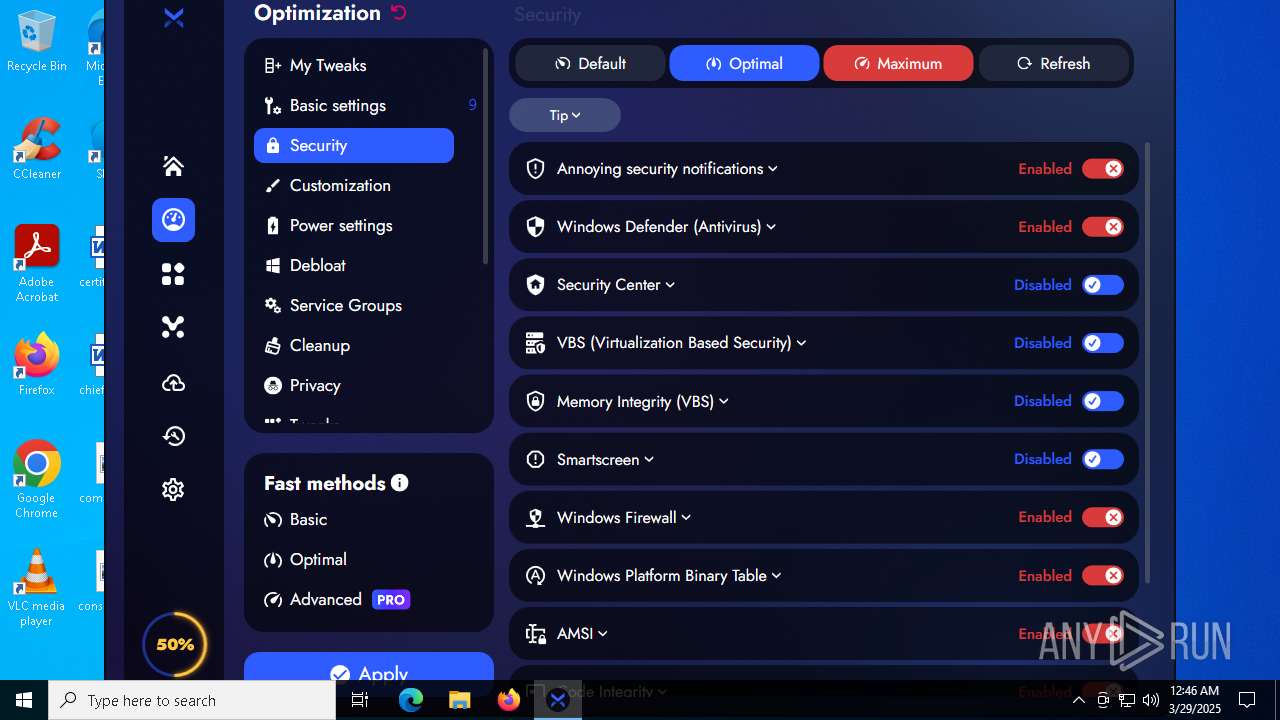
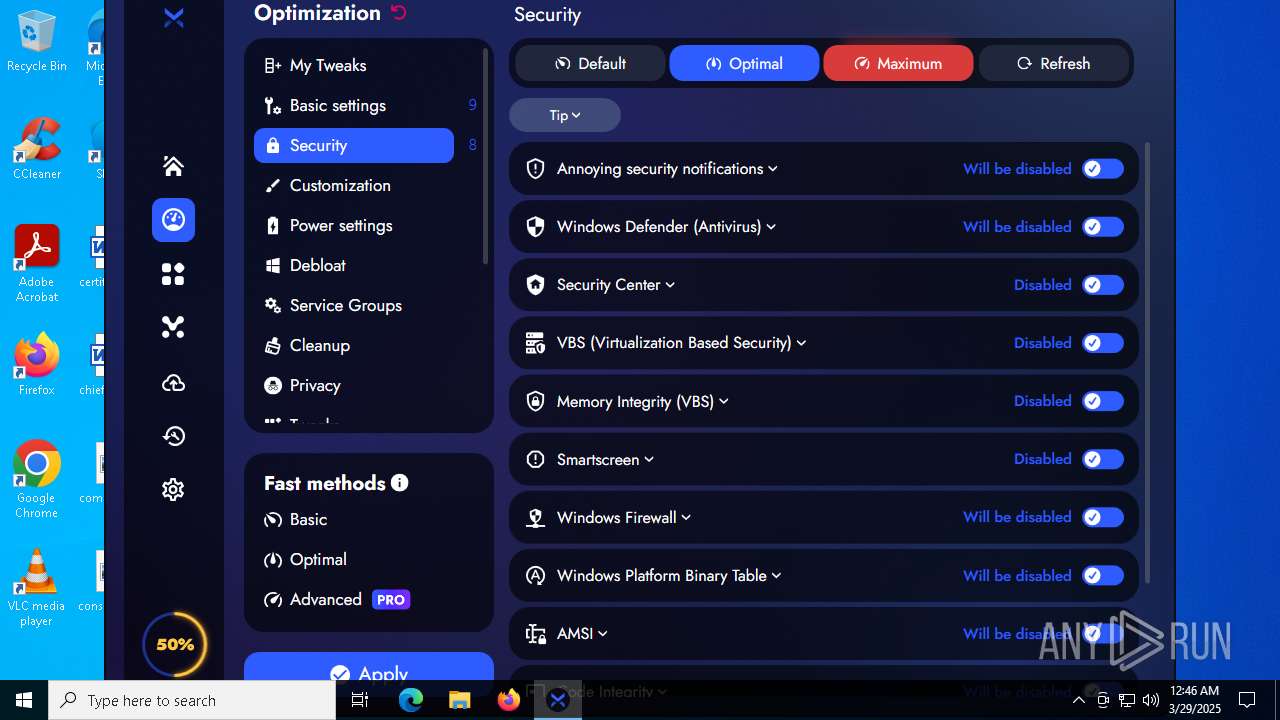
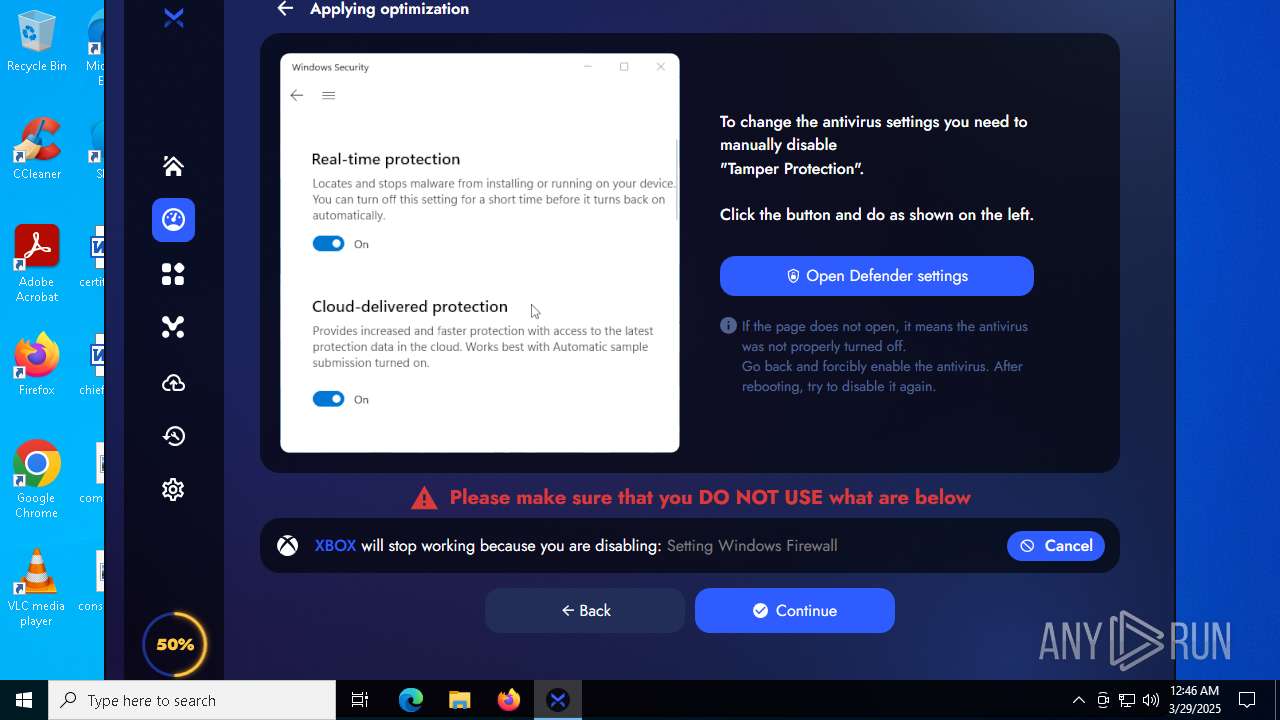
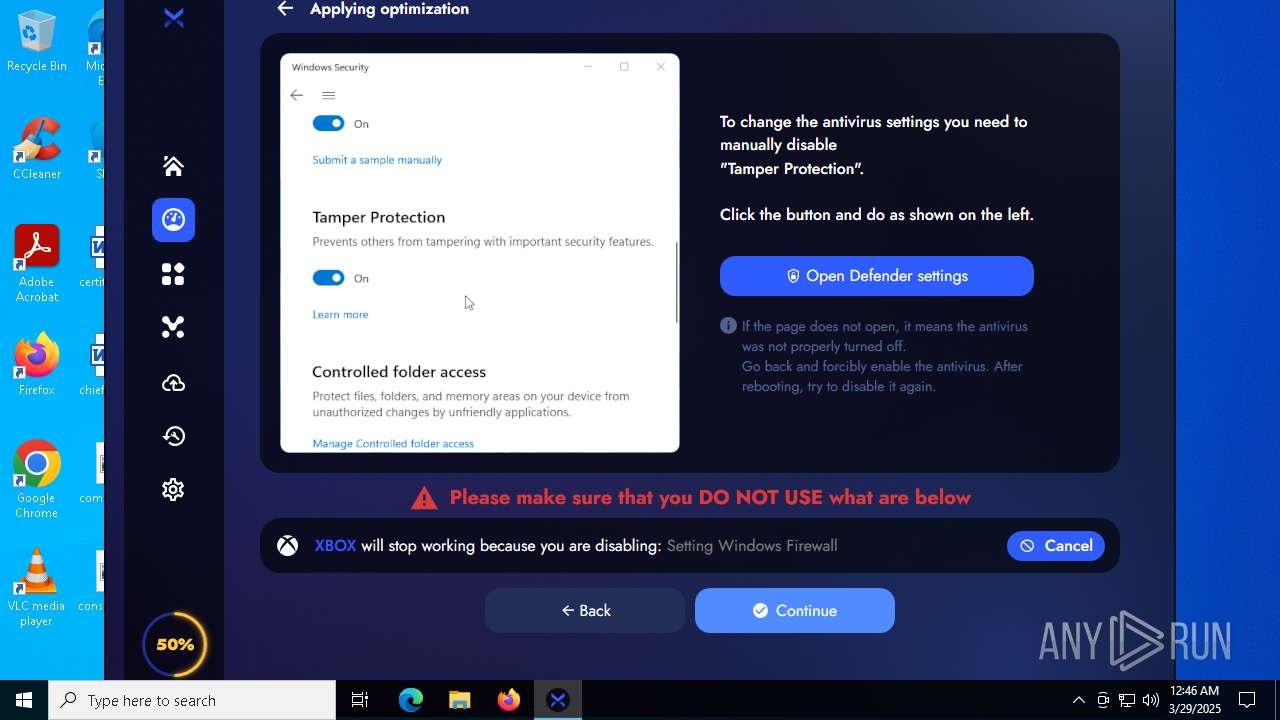
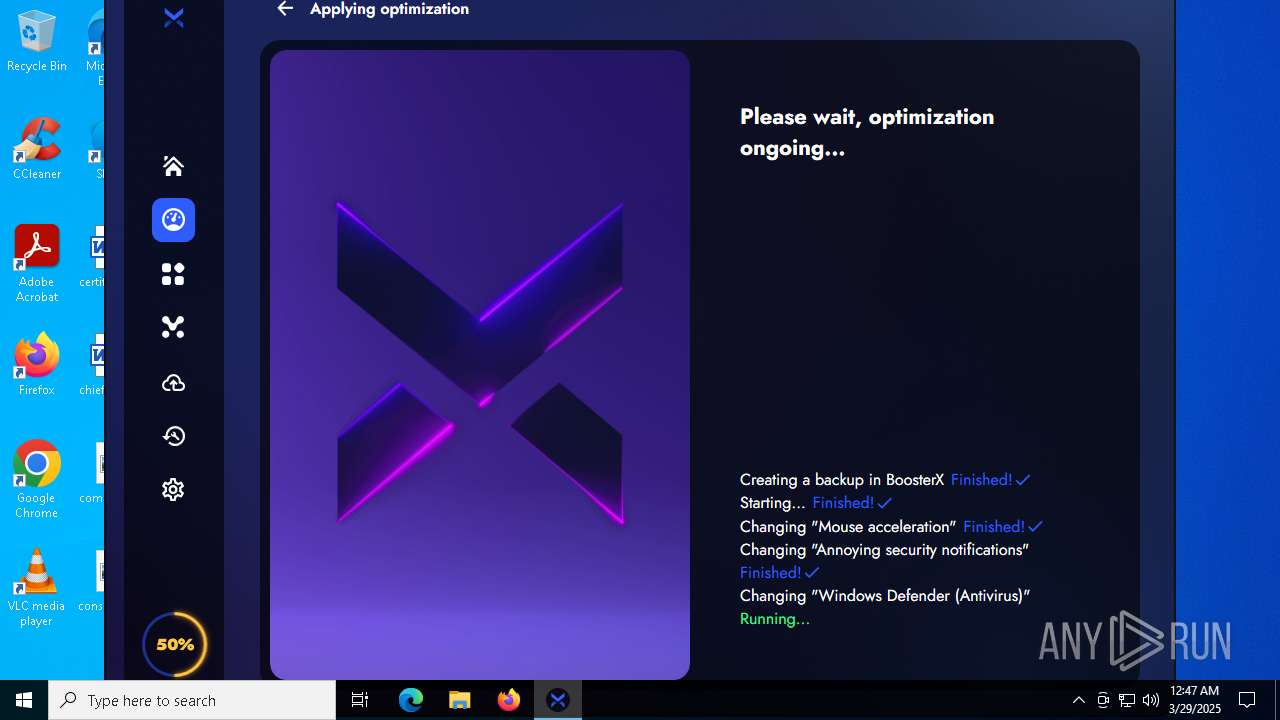
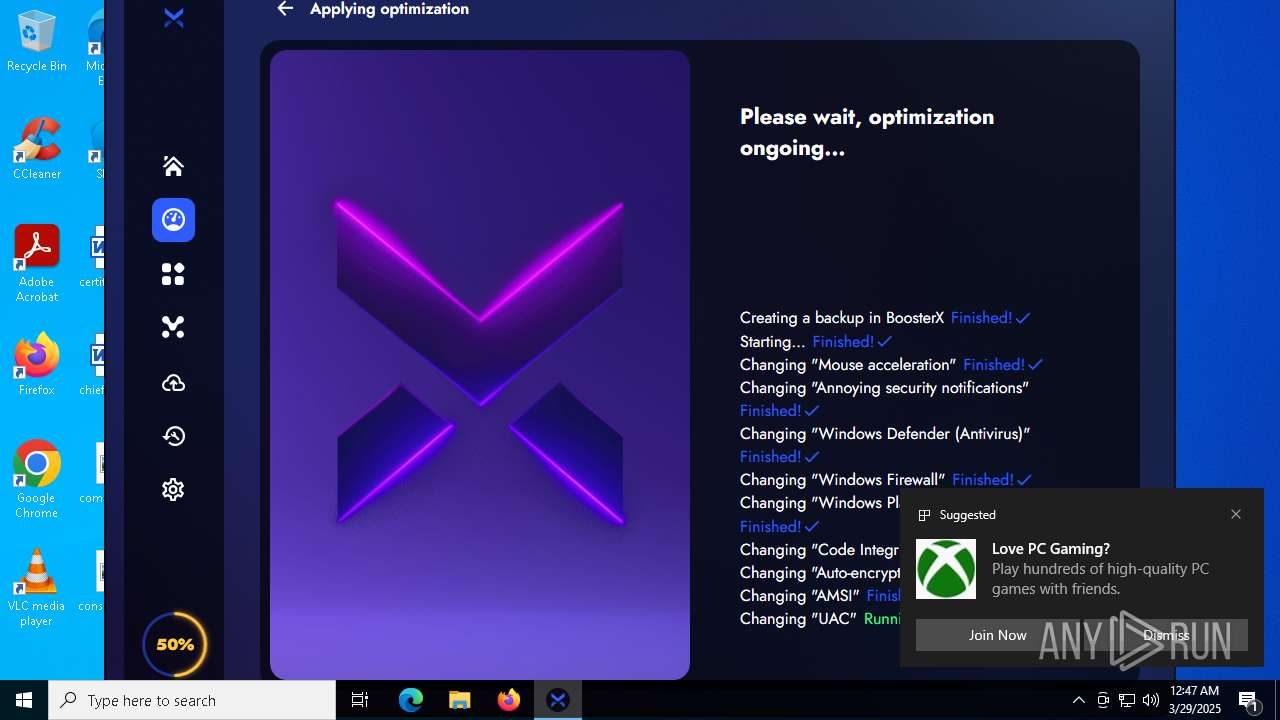
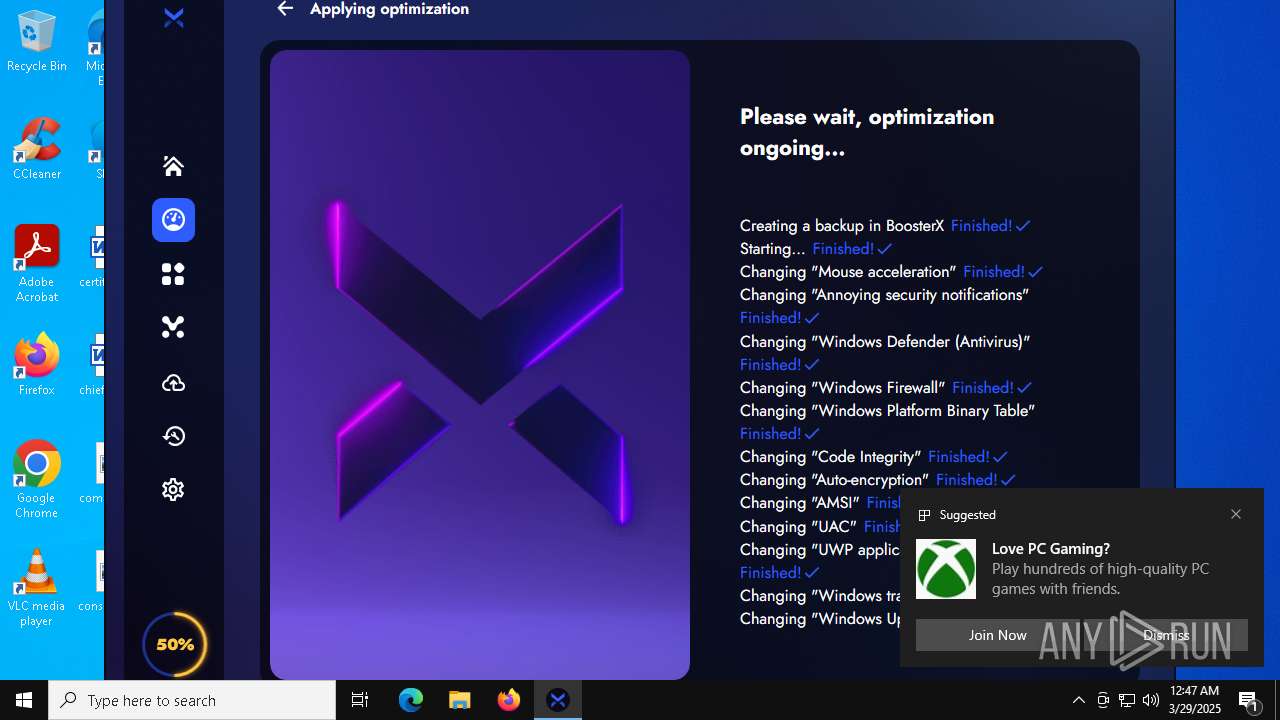
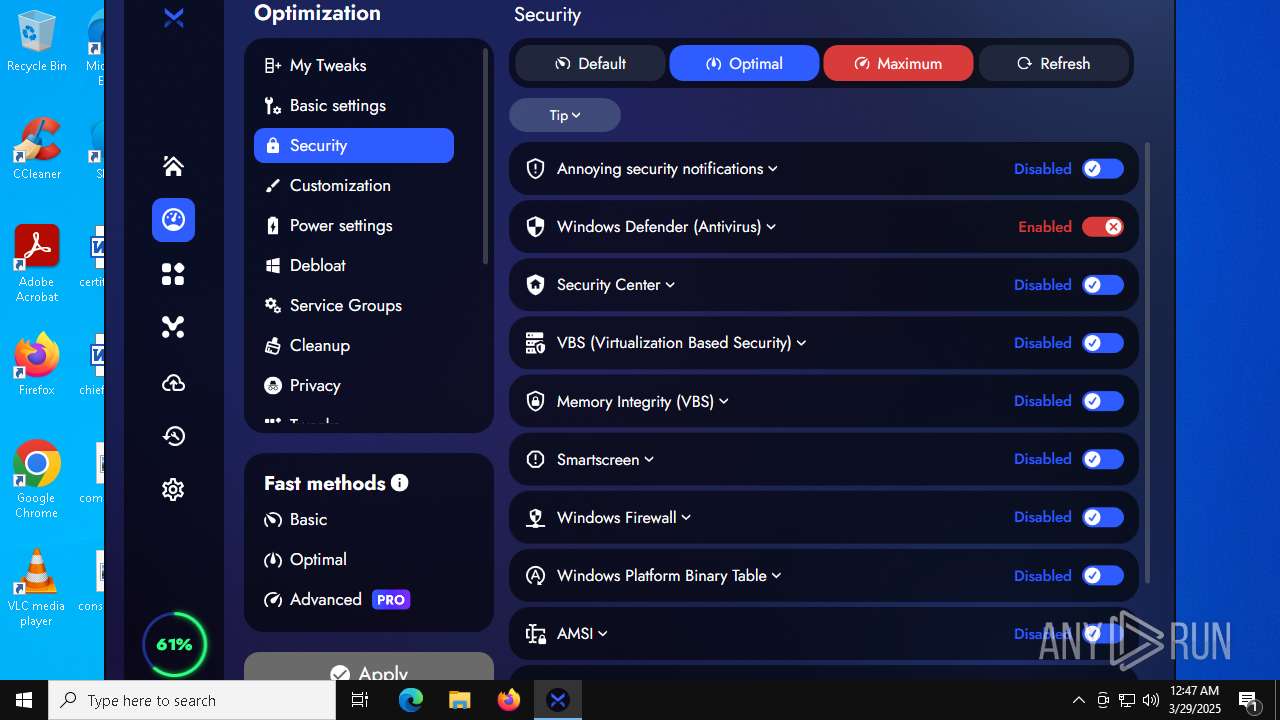
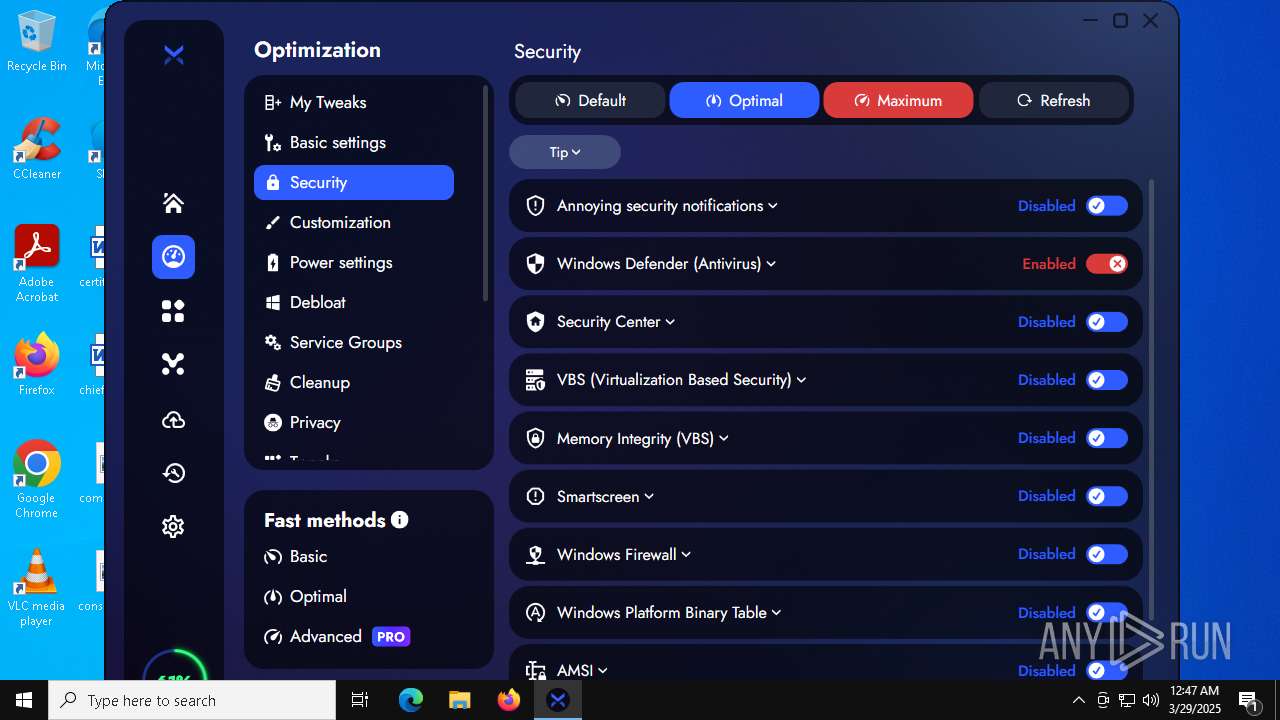
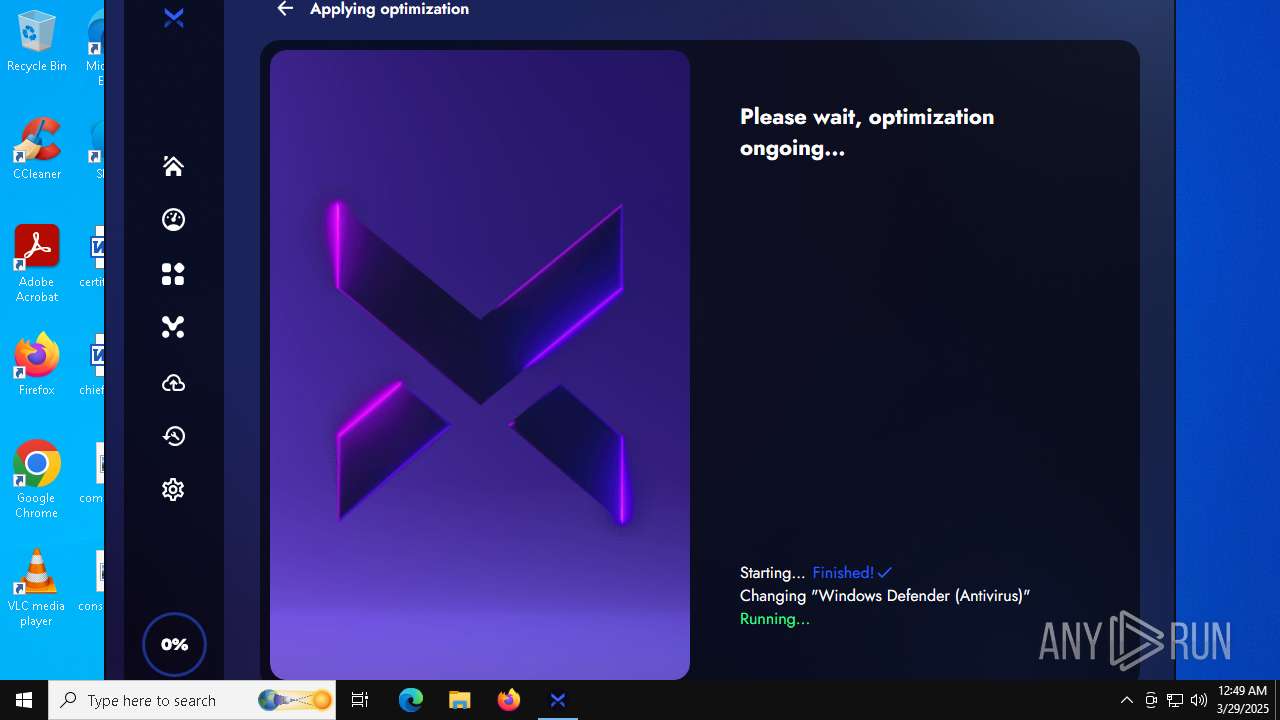
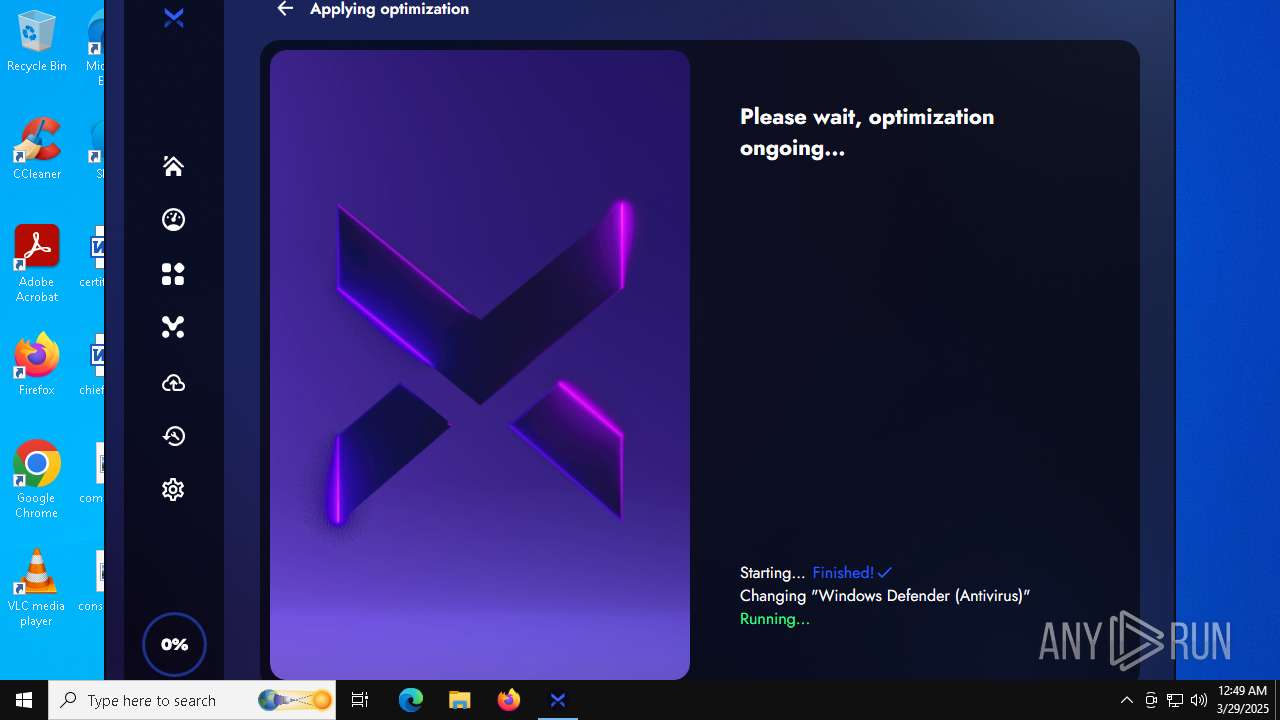
Changes Windows Defender settings
- cmd.exe (PID: 5416)
- cmd.exe (PID: 6136)
Application was injected by another process
- cmd.exe (PID: 5416)
- reg.exe (PID: 6112)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 6136)
Disables Windows firewall
- reg.exe (PID: 516)
- reg.exe (PID: 3976)
- reg.exe (PID: 7972)
Changes firewall settings
- reg.exe (PID: 516)
- reg.exe (PID: 7972)
- reg.exe (PID: 3976)
UAC/LUA settings modification
- reg.exe (PID: 7300)
Starts NET.EXE for service management
- cmd.exe (PID: 7180)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 7180)
SUSPICIOUS
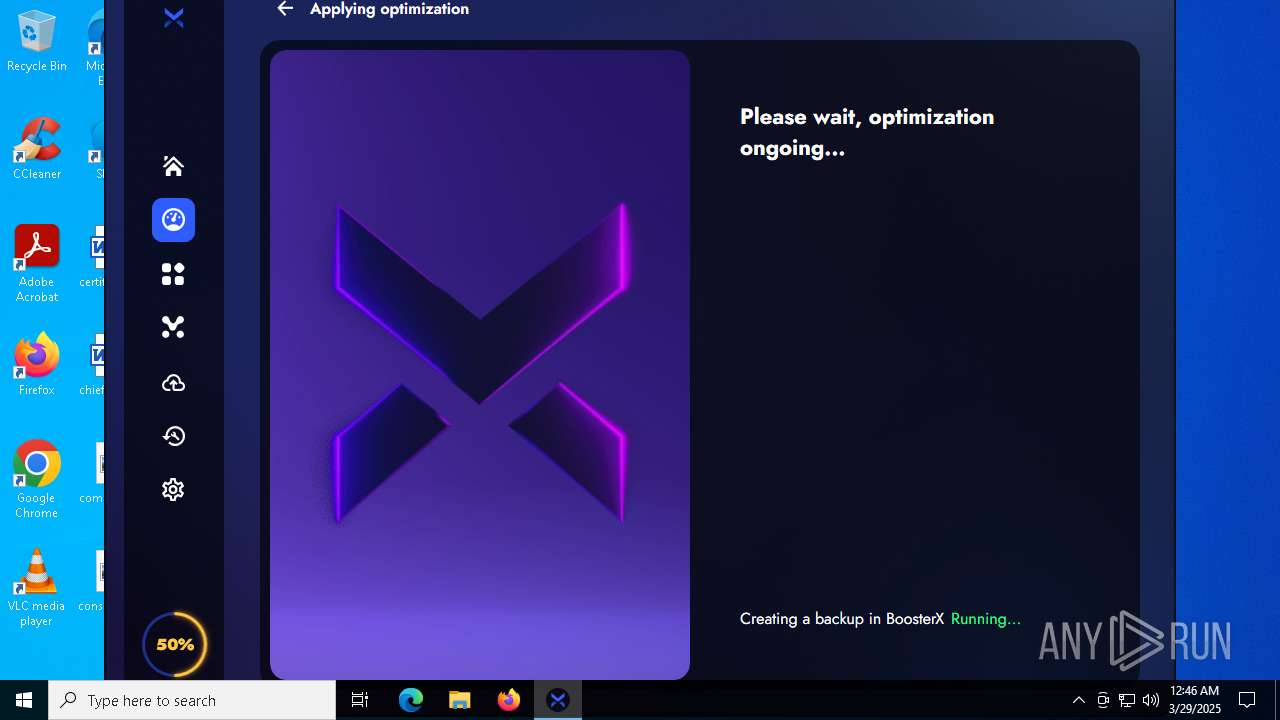
Executable content was dropped or overwritten
- BoosterX.exe (PID: 7916)
- cmd.exe (PID: 7180)
Adds/modifies Windows certificates
- BoosterX.exe (PID: 7916)
Reads security settings of Internet Explorer
- BoosterX.exe (PID: 7916)
- ShellExperienceHost.exe (PID: 7584)
- BoosterX.exe (PID: 2644)
Uses WEVTUTIL.EXE to get log configuration information
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Starts CMD.EXE for commands execution
- BoosterX.exe (PID: 7916)
- cmd.exe (PID: 5416)
- BoosterX.exe (PID: 2644)
- cmd.exe (PID: 6136)
Starts application with an unusual extension
- cmd.exe (PID: 7644)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 5624)
- cmd.exe (PID: 4508)
Checks for external IP
- BoosterX.exe (PID: 7916)
There is functionality for taking screenshot (YARA)
- BoosterX.exe (PID: 7916)
Connects to the server without a host name
- BoosterX.exe (PID: 7916)
Uses WEVTUTIL.EXE to change log configuration
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Reads the date of Windows installation
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2332)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 8532)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 5416)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 1276)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 8984)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 744)
- cmd.exe (PID: 8464)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 8584)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 648)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 6208)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 300)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 240)
- cmd.exe (PID: 8556)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 6740)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 4196)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 6136)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7784)
- cmd.exe (PID: 5944)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 7704)
Found strings related to reading or modifying Windows Defender settings
- BoosterX.exe (PID: 7916)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 5416)
- cmd.exe (PID: 6136)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5416)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 6136)
Creates or modifies Windows services
- reg.exe (PID: 4164)
- reg.exe (PID: 4932)
- reg.exe (PID: 7208)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 7180)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7180)
Starts SC.EXE for service management
- cmd.exe (PID: 7180)
- cmd.exe (PID: 904)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 8940)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 5072)
Process drops legitimate windows executable
- cmd.exe (PID: 7180)
Stops a currently running service
- sc.exe (PID: 8484)
- sc.exe (PID: 7680)
- sc.exe (PID: 5384)
Windows service management via SC.EXE
- sc.exe (PID: 8976)
- sc.exe (PID: 7988)
The process executes via Task Scheduler
- BoosterX.exe (PID: 2644)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5180)
INFO
Application launched itself
- msedge.exe (PID: 7508)
- msedge.exe (PID: 6512)
Checks supported languages
- identity_helper.exe (PID: 8792)
- BoosterX.exe (PID: 7916)
- chcp.com (PID: 7672)
- identity_helper.exe (PID: 9000)
- ShellExperienceHost.exe (PID: 7584)
- chcp.com (PID: 2416)
- chcp.com (PID: 8960)
- BoosterX.exe (PID: 2644)
- chcp.com (PID: 1044)
- chcp.com (PID: 4404)
Reads Environment values
- identity_helper.exe (PID: 8792)
- identity_helper.exe (PID: 9000)
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Reads the computer name
- identity_helper.exe (PID: 8792)
- BoosterX.exe (PID: 7916)
- ShellExperienceHost.exe (PID: 7584)
- identity_helper.exe (PID: 9000)
- BoosterX.exe (PID: 2644)
Executable content was dropped or overwritten
- msedge.exe (PID: 7508)
- msedge.exe (PID: 7768)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8300)
- BackgroundTransferHost.exe (PID: 7552)
- BackgroundTransferHost.exe (PID: 9036)
- BackgroundTransferHost.exe (PID: 6344)
- BackgroundTransferHost.exe (PID: 8372)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8372)
- BoosterX.exe (PID: 7916)
- slui.exe (PID: 7836)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8372)
- BoosterX.exe (PID: 7916)
- powercfg.exe (PID: 8172)
- BoosterX.exe (PID: 2644)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8372)
- BoosterX.exe (PID: 7916)
- slui.exe (PID: 8648)
- slui.exe (PID: 7836)
- BoosterX.exe (PID: 2644)
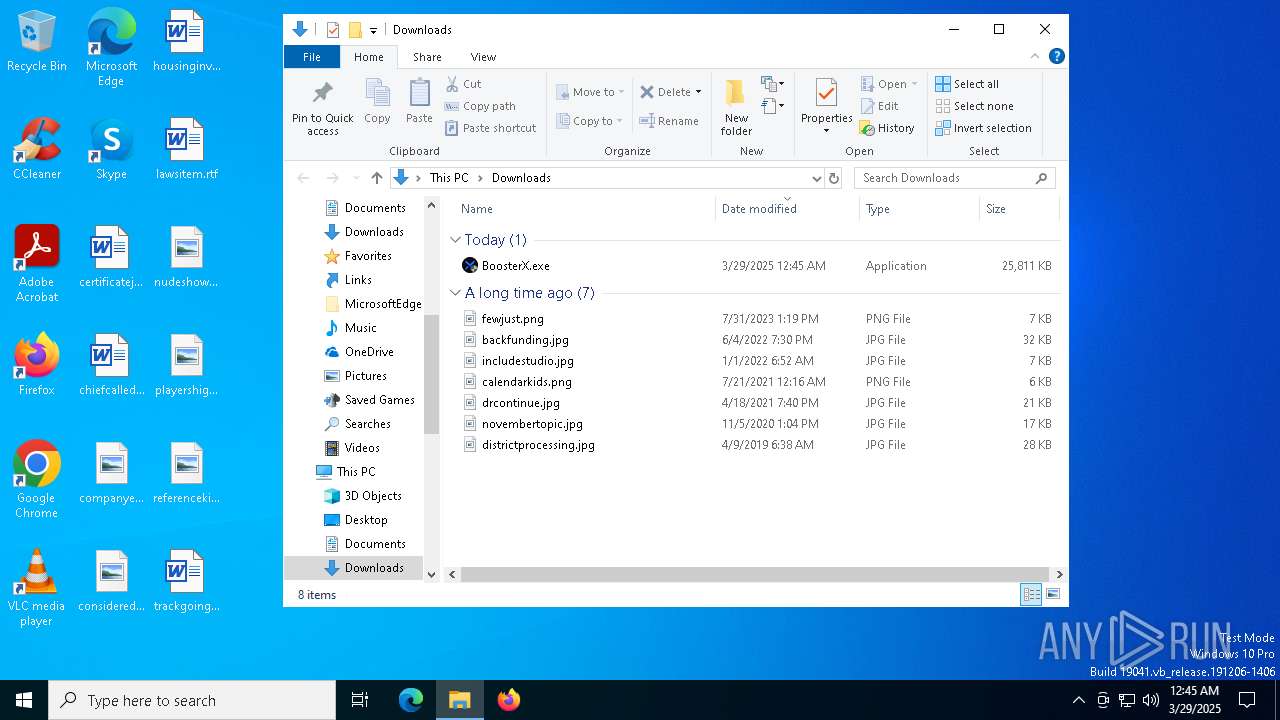
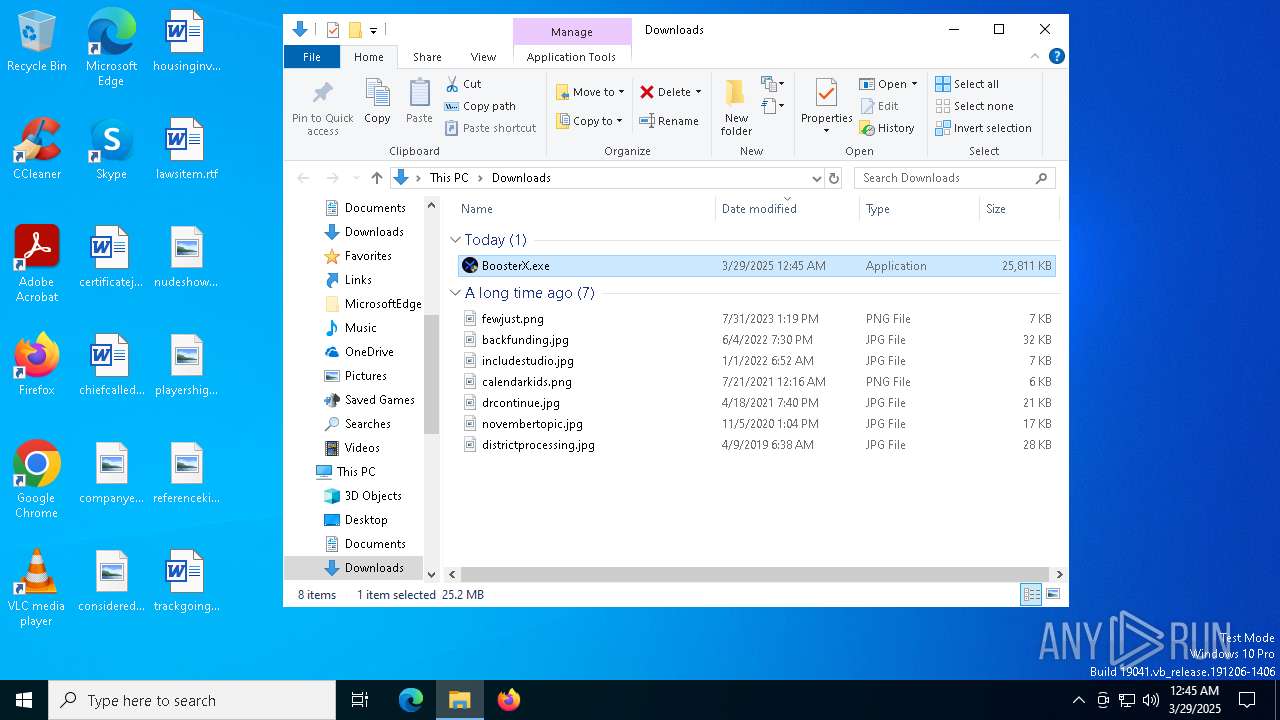
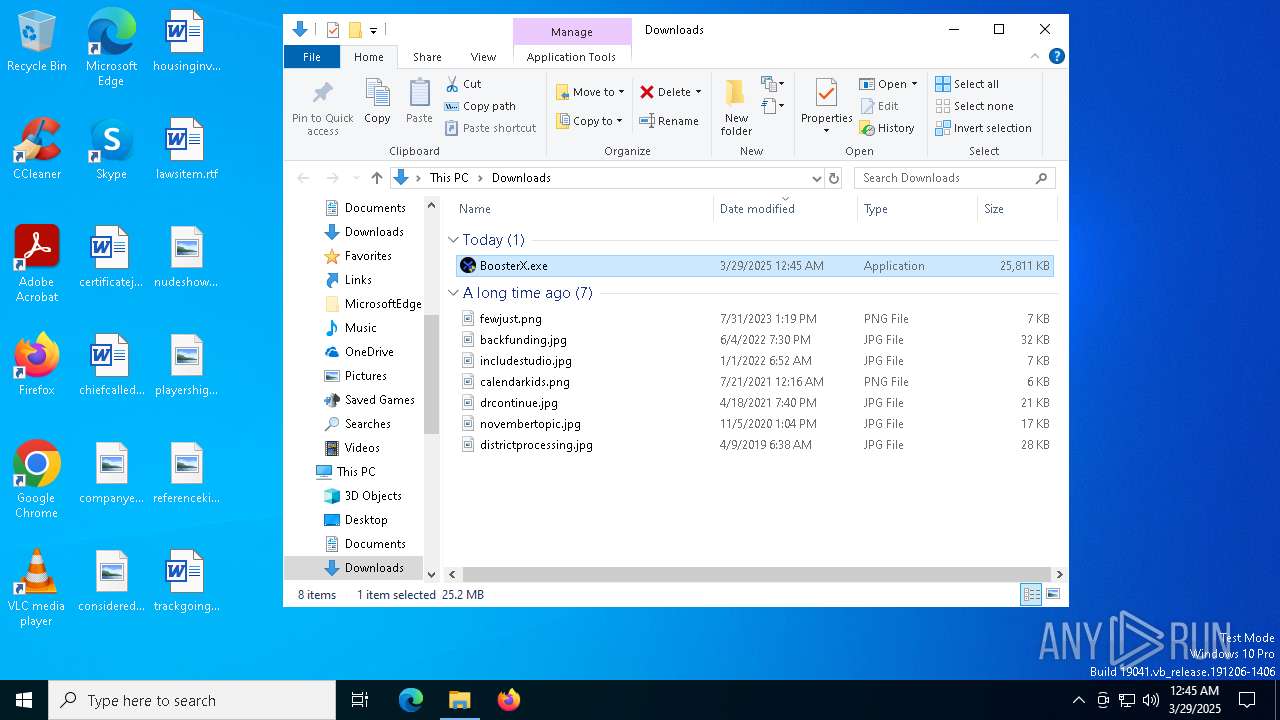
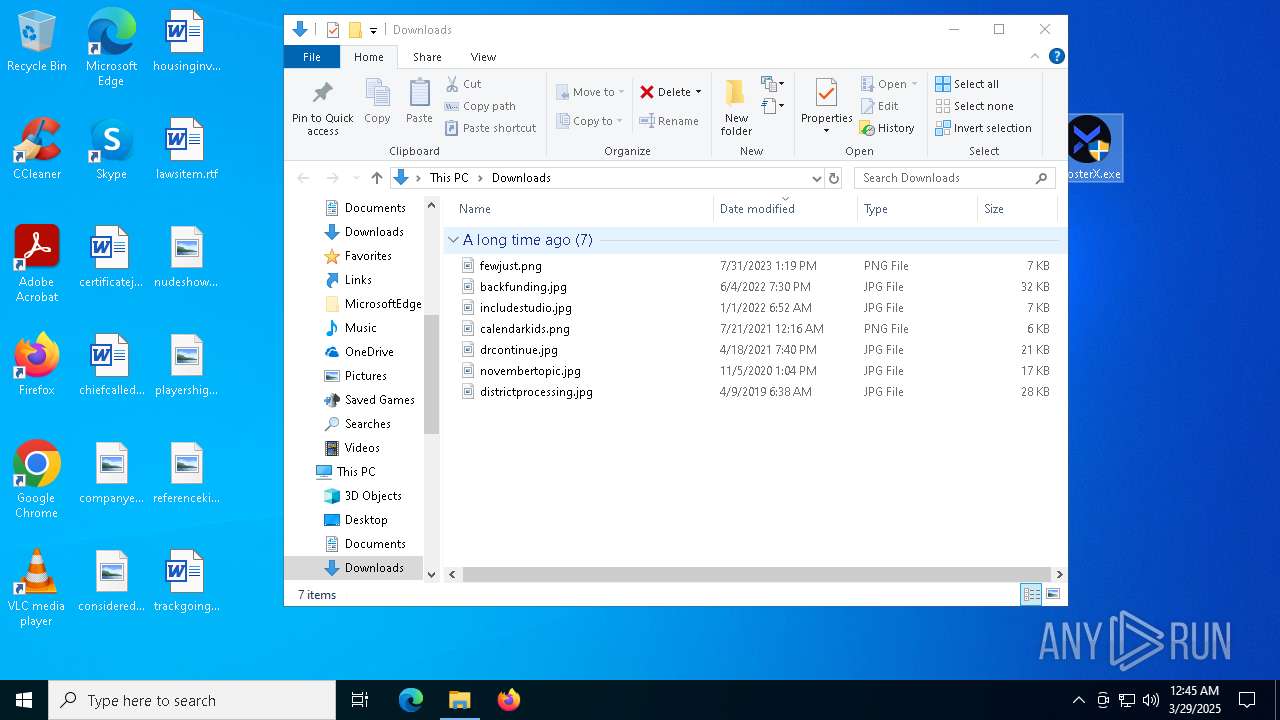
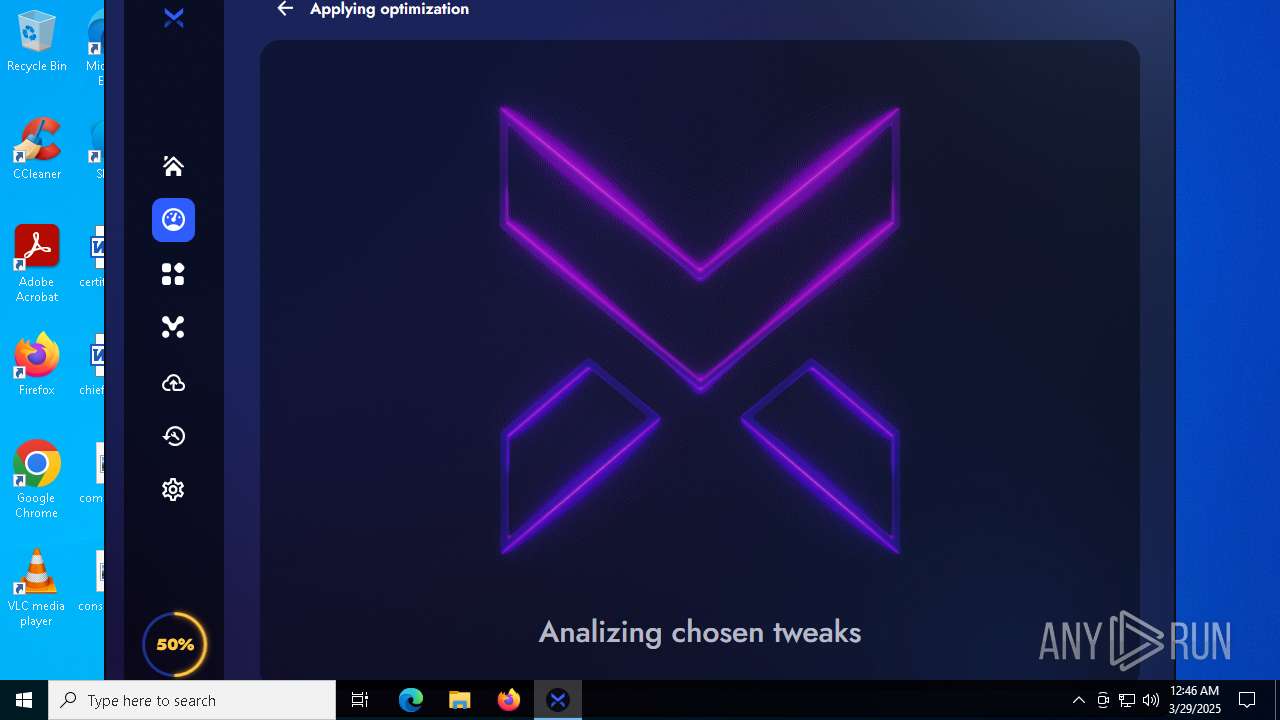
Manual execution by a user
- BoosterX.exe (PID: 8960)
- BoosterX.exe (PID: 7916)
Create files in a temporary directory
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Reads the machine GUID from the registry
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Creates files in the program directory
- BoosterX.exe (PID: 7916)
Reads CPU info
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Reads mouse settings
- BoosterX.exe (PID: 7916)
- reg.exe (PID: 5780)
- reg.exe (PID: 8556)
- reg.exe (PID: 8252)
- BoosterX.exe (PID: 2644)
Changes the display of characters in the console
- cmd.exe (PID: 7644)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 5624)
- cmd.exe (PID: 4508)
Process checks whether UAC notifications are on
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
UPX packer has been detected
- BoosterX.exe (PID: 7916)
Disables trace logs
- BoosterX.exe (PID: 7916)
Process checks computer location settings
- BoosterX.exe (PID: 7916)
- BoosterX.exe (PID: 2644)
Autorun file from Downloads
- msedge.exe (PID: 9048)
- msedge.exe (PID: 7508)
The sample compiled with english language support
- cmd.exe (PID: 7180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
759
Monitored processes
284
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | "C:\Windows\System32\cmd.exe" /c reg add "HKEY_LOCAL_MACHINE\SYSTEM\Maps" /v "AutoUpdateEnabled" /t reg_dword /d "0" /f | C:\Windows\System32\cmd.exe | — | BoosterX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Windows\System32\cmd.exe" /c reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\DriverSearching" /v "SearchOrderConfig" /t reg_dword /d "3" /f | C:\Windows\System32\cmd.exe | — | BoosterX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | reg add "HKLM\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile" /v "EnableFirewall" /t reg_dword /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | "C:\Windows\System32\cmd.exe" /c reg add "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\GameDVR" /v "AppCaptureEnabled" /t reg_dword /d "0" /f | C:\Windows\System32\cmd.exe | — | BoosterX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Windows\System32\cmd.exe" /c reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Search" /v "BackgroundAppGlobalToggle" /t reg_dword /d "0" /f | C:\Windows\System32\cmd.exe | — | BoosterX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | reg add "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "PromptOnSecureDesktop" /t reg_dword /d "0" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
56 541
Read events
55 479
Write events
674
Delete events
388
Modification events
| (PID) Process: | (7508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (7376) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7508) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
20
Suspicious files
389
Text files
108
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb14.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb24.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb24.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb24.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb34.TMP | — | |
MD5:— | SHA256:— | |||
| 7508 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
152
DNS requests
89
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7680 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7916 | BoosterX.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
7916 | BoosterX.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | — | — | whitelisted |
7916 | BoosterX.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDCA%2Bm9pn2L4BUkZvtw%3D%3D | unknown | — | — | whitelisted |
8372 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7916 | BoosterX.exe | GET | 200 | 139.162.165.156:80 | http://reserve.boosterx.org/_health | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
7508 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7768 | msedge.exe | 172.67.146.209:443 | boosterx.org | — | — | unknown |
7768 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7768 | msedge.exe | 142.250.185.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
7768 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7768 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
boosterx.org |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7916 | BoosterX.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
7916 | BoosterX.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7916 | BoosterX.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |