| File name: | Patch-Proteus-8.16-SP3-36097.0.exe |
| Full analysis: | https://app.any.run/tasks/cb66db7b-36a9-4093-b014-a0ca4f7bf463 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2024, 14:31:46 |
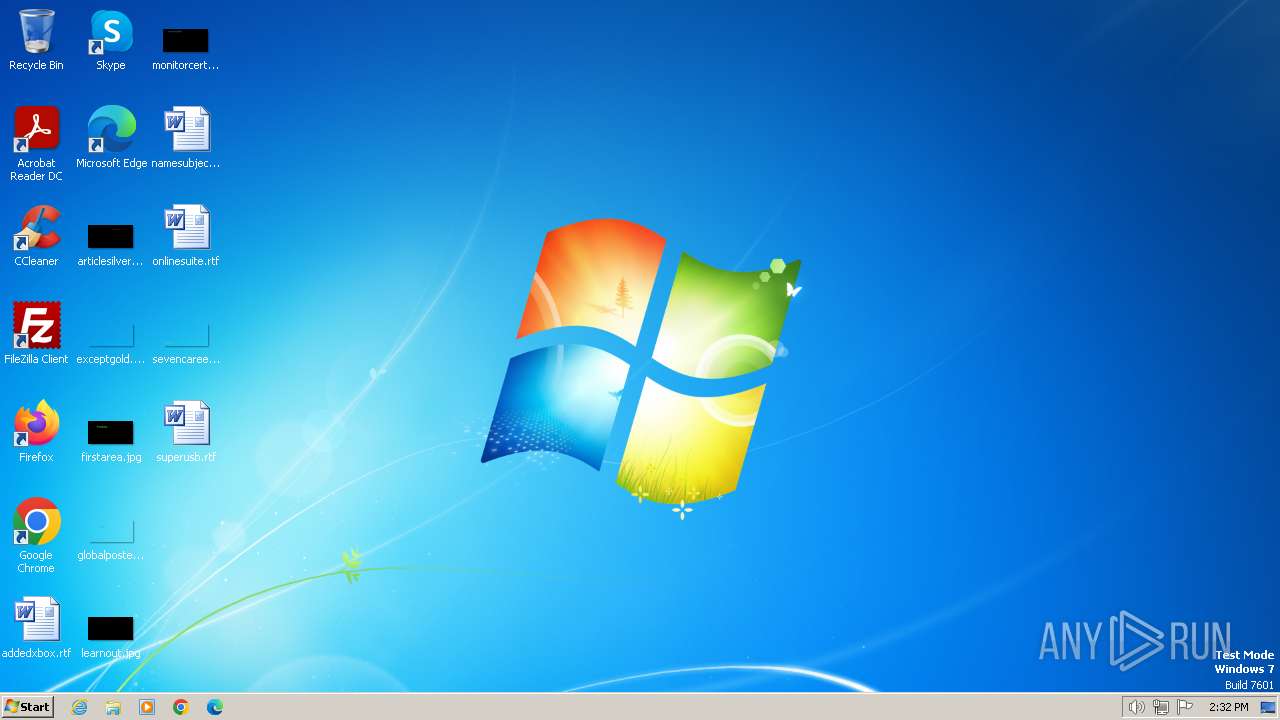
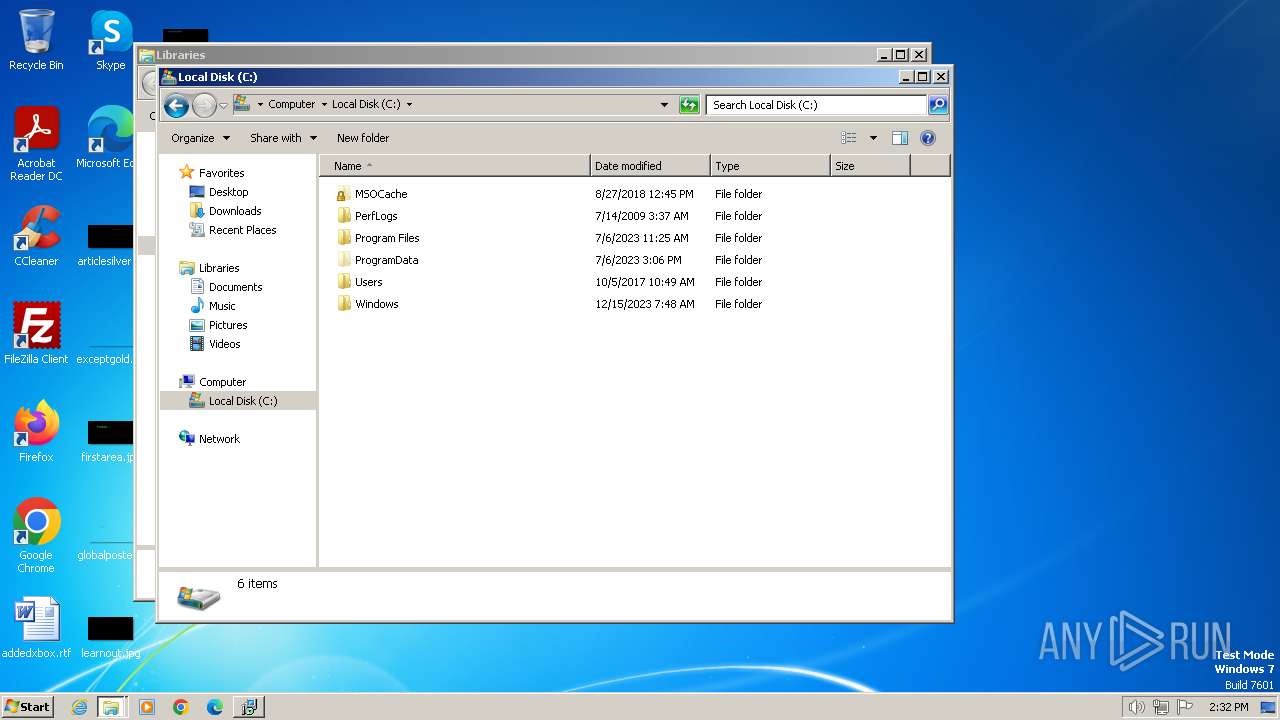
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CC4D5485B540C520B1B08766B8A9D7F8 |
| SHA1: | 01502DC675737E40E528EC4B4D46A10442FC8EEA |
| SHA256: | 8DA492EC20E29D7C7153EC476A44298938849C675D400E447BF1992BE90C361A |
| SSDEEP: | 49152:6wE0tiseX1R/ZgNIhy334y/YxAfctNHf+oEtq1osvNEjIADRJtJRPYF606Y0efCC:o0ti3xgNIhu34y6OOHf+y1SjTD4FZ92C |
MALICIOUS
Drops the executable file immediately after the start
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3656)
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3944)
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 3228)
SUSPICIOUS
Reads the Windows owner or organization settings
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 3228)
Executable content was dropped or overwritten
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3656)
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 3228)
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3944)
INFO
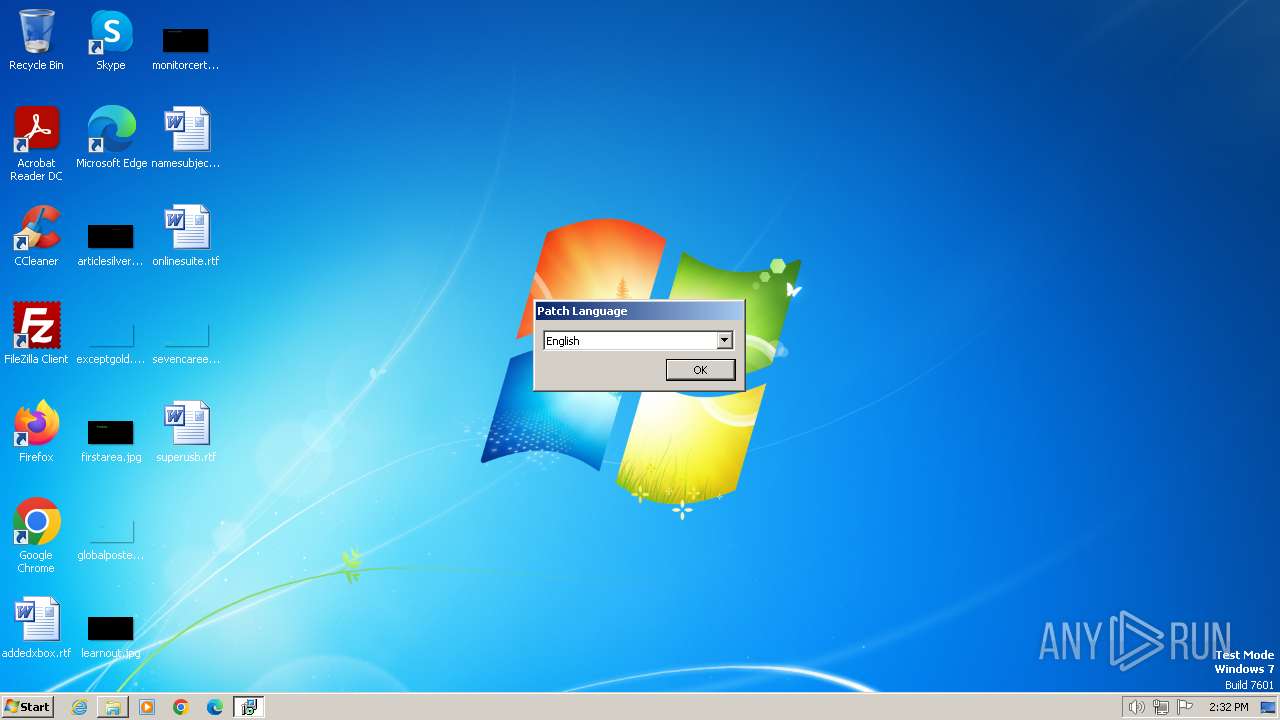
Checks supported languages
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 3228)
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 1432)
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3656)
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3944)
- wmpnscfg.exe (PID: 1928)
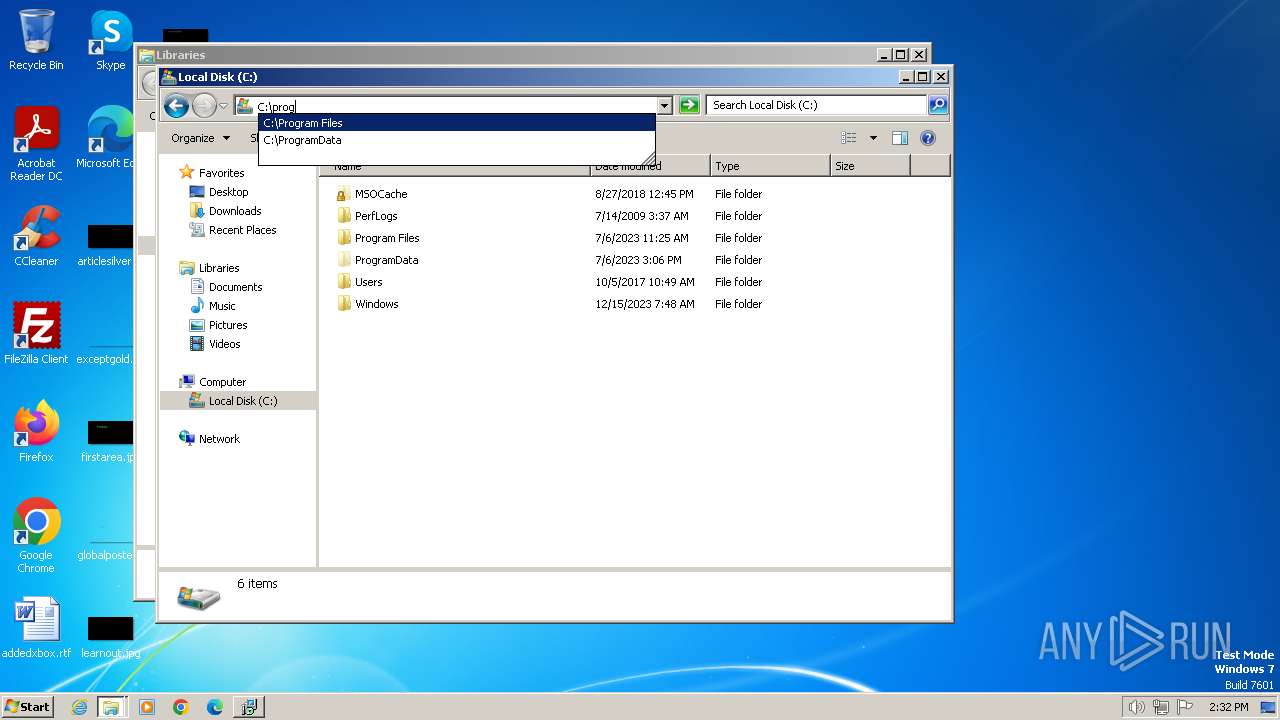
Create files in a temporary directory
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3656)
- Patch-Proteus-8.16-SP3-36097.0.exe (PID: 3944)
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 3228)
Reads the computer name
- Patch-Proteus-8.16-SP3-36097.0.tmp (PID: 1432)
- wmpnscfg.exe (PID: 1928)
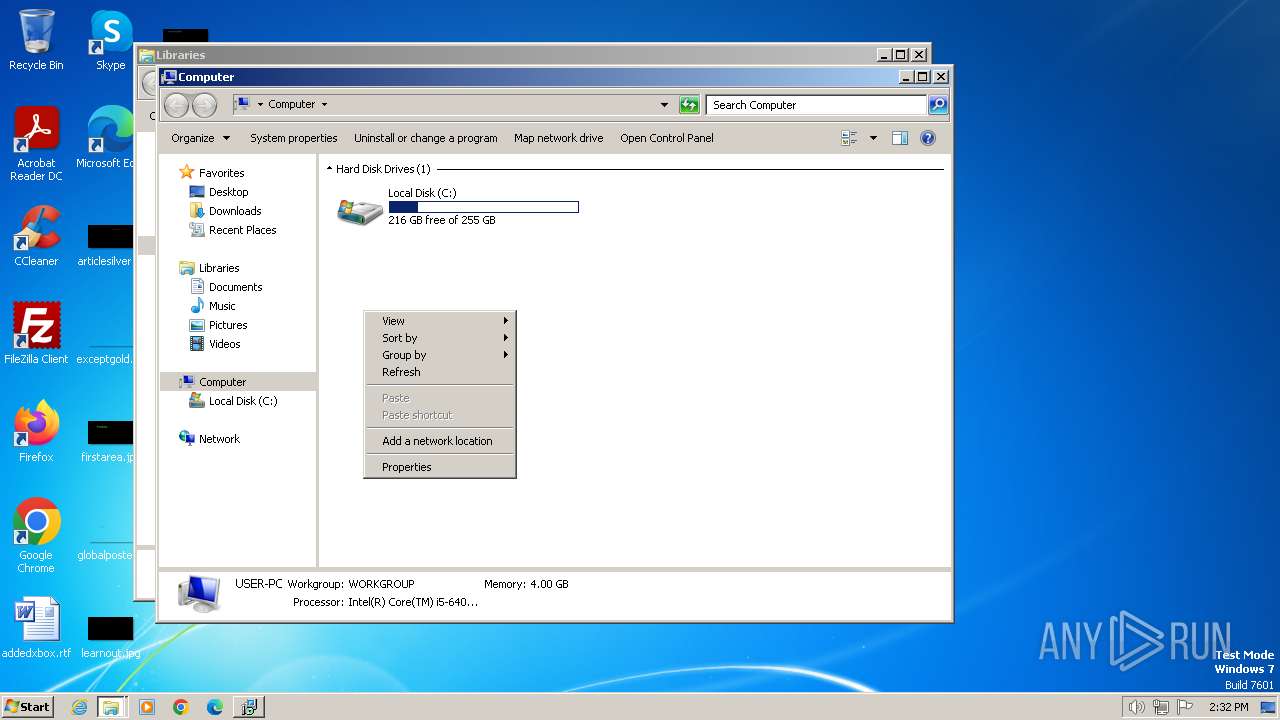
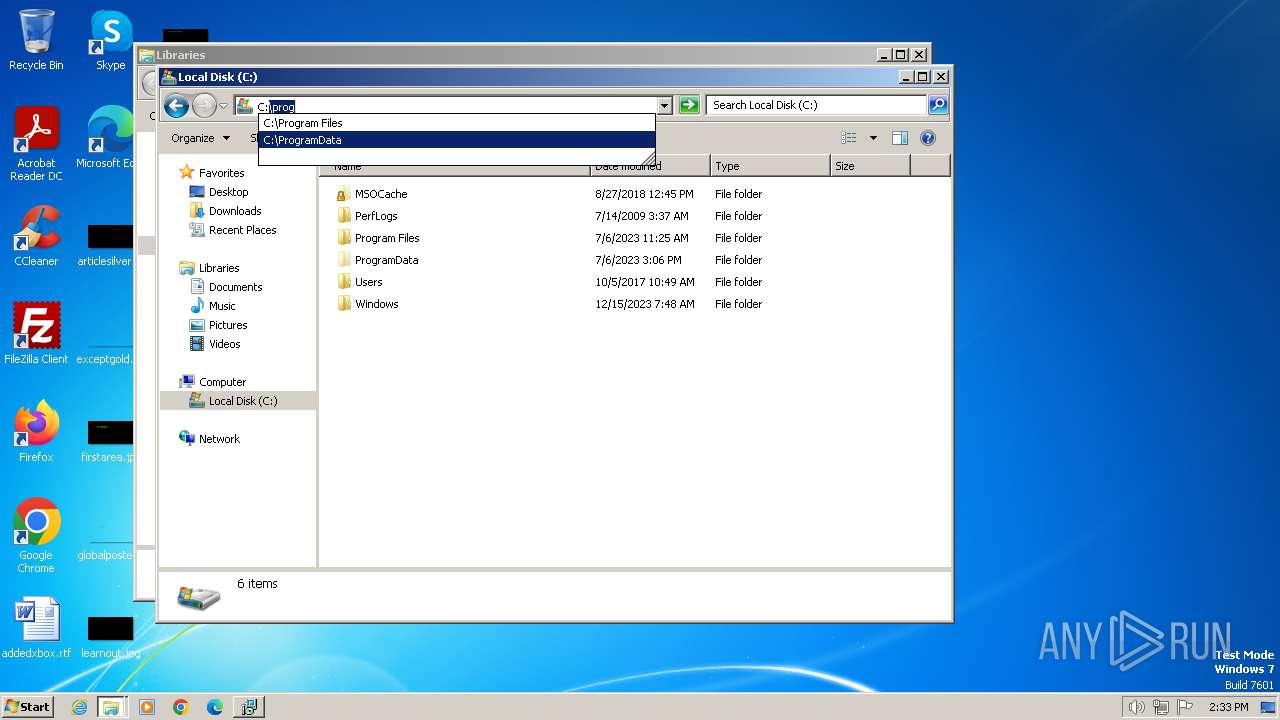
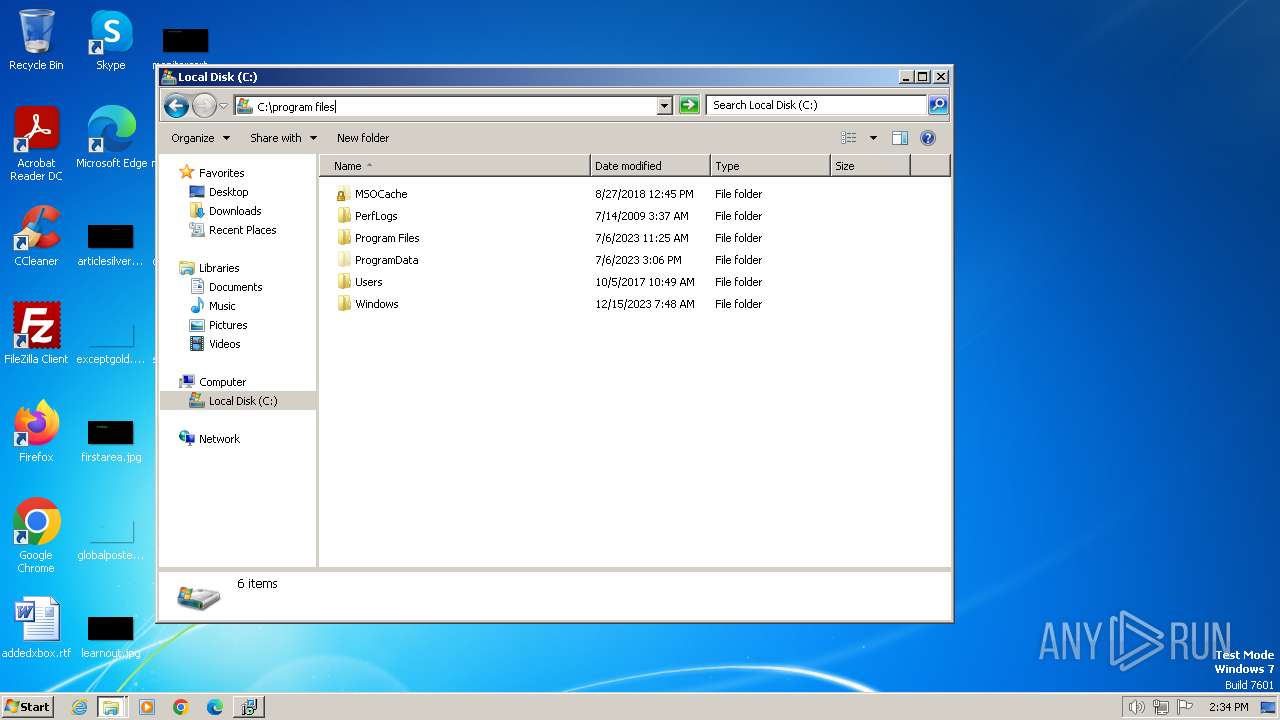
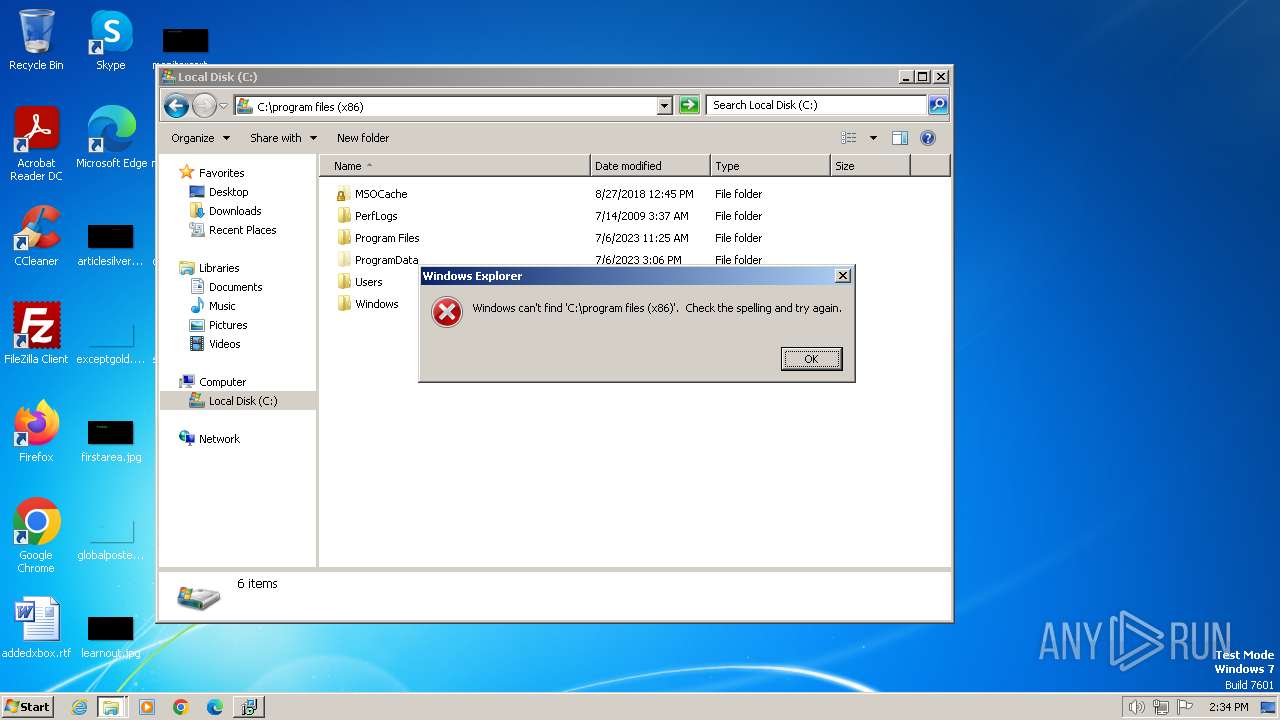
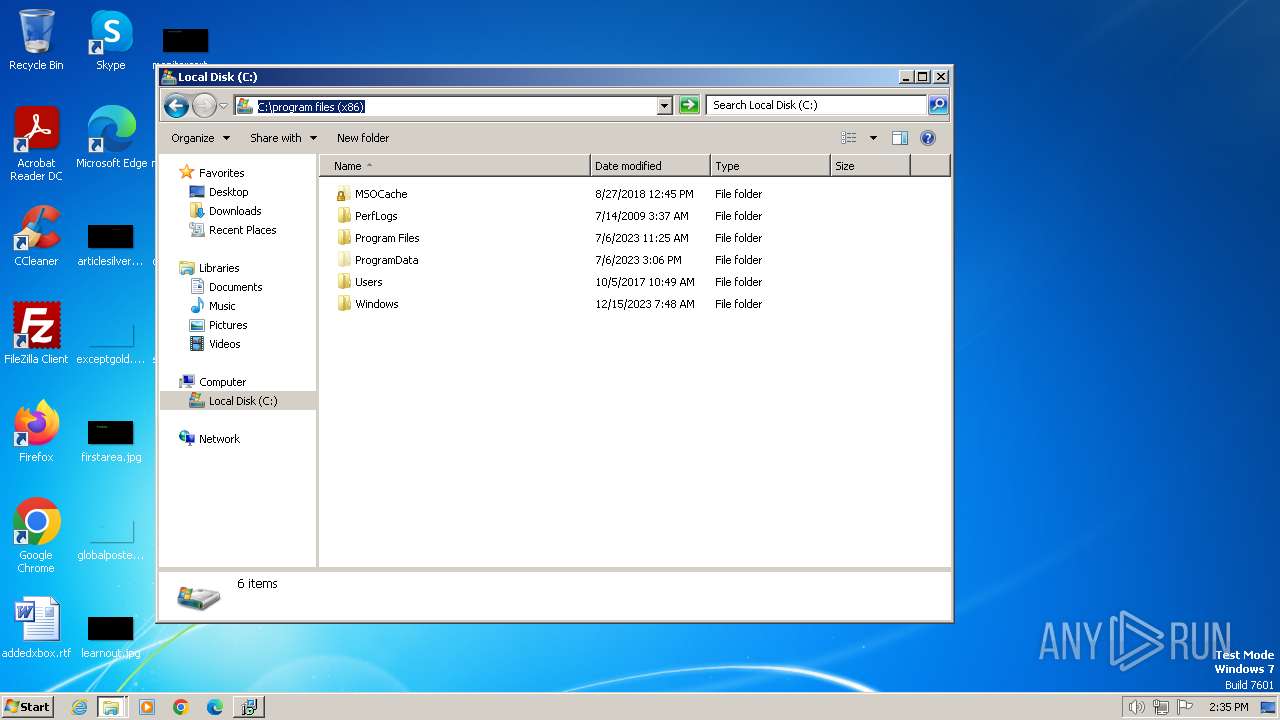
Manual execution by a user
- explorer.exe (PID: 3304)
- wmpnscfg.exe (PID: 1928)
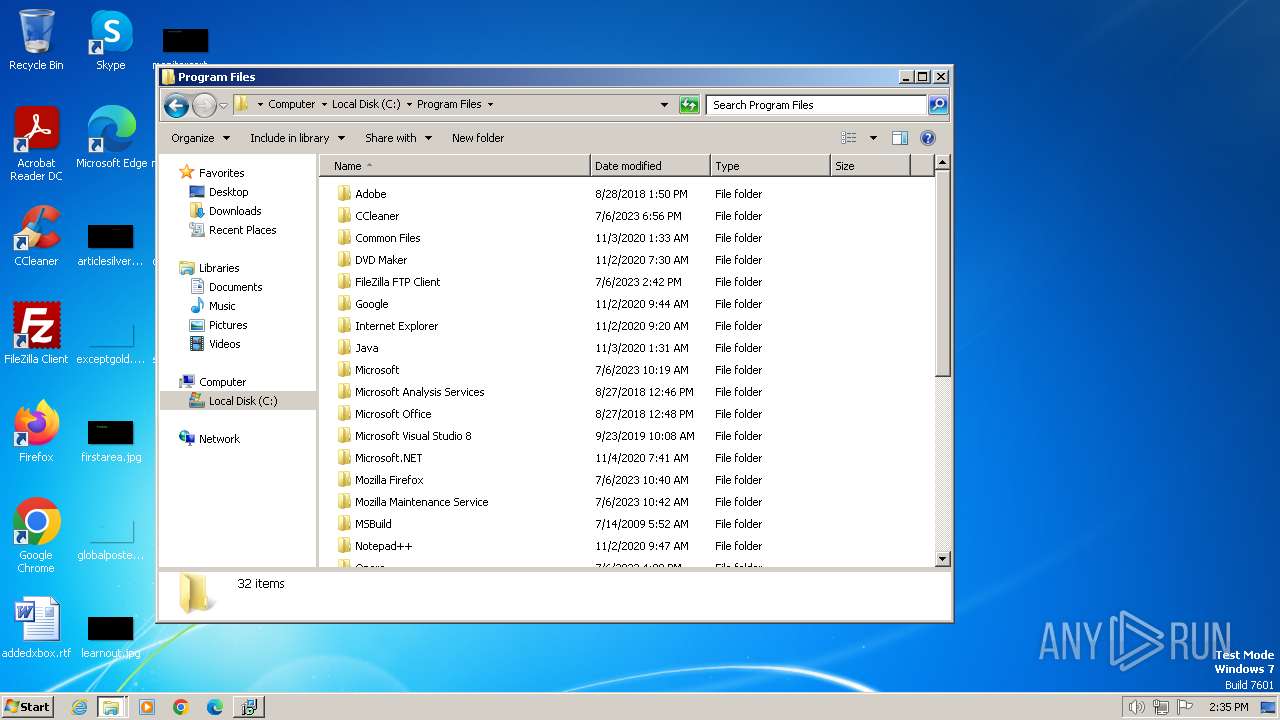
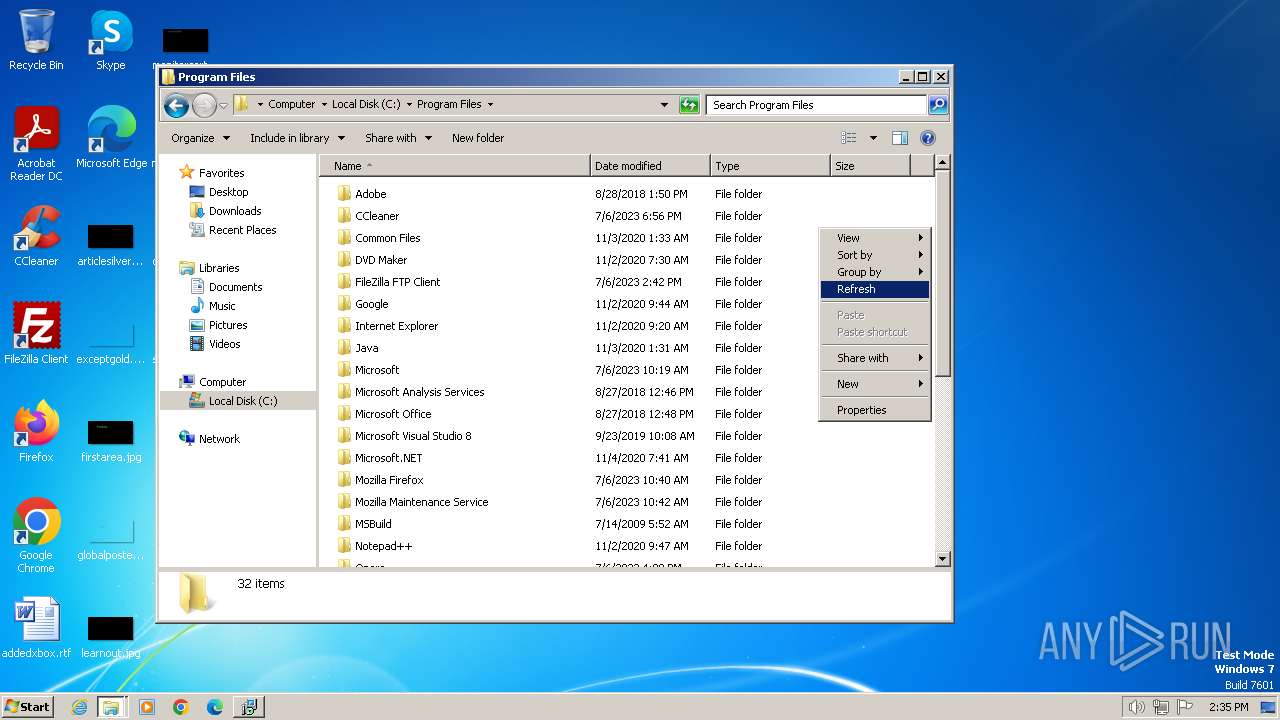
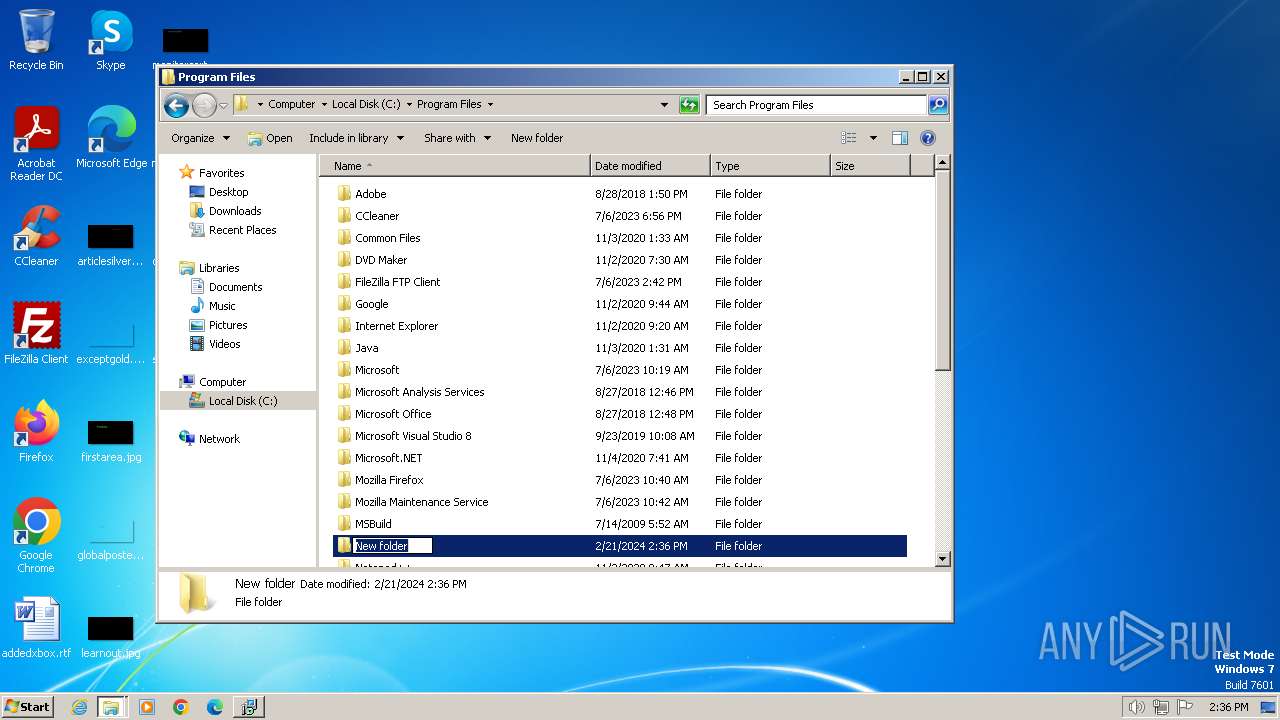
Creates files in the program directory
- dllhost.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 13:27:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | My Company |
| FileDescription: | Patch for Proteus |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Anonymous |
| ProductName: | Proteus |
| ProductVersion: | 1.0.0.0 |
Total processes
49
Monitored processes
7
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1432 | "C:\Users\admin\AppData\Local\Temp\is-4KDNU.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp" /SL5="$E0170,1298840,121344,C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe" | C:\Users\admin\AppData\Local\Temp\is-4KDNU.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp | — | Patch-Proteus-8.16-SP3-36097.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\AppData\Local\Temp\is-JA07A.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp" /SL5="$100130,1298840,121344,C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe" /SPAWNWND=$18013E /NOTIFYWND=$E0170 | C:\Users\admin\AppData\Local\Temp\is-JA07A.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp | Patch-Proteus-8.16-SP3-36097.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3304 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe" | C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe | explorer.exe | ||||||||||||
User: admin Company: My Company Integrity Level: MEDIUM Description: Patch for Proteus Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe" /SPAWNWND=$18013E /NOTIFYWND=$E0170 | C:\Users\admin\AppData\Local\Temp\Patch-Proteus-8.16-SP3-36097.0.exe | Patch-Proteus-8.16-SP3-36097.0.tmp | ||||||||||||
User: admin Company: My Company Integrity Level: HIGH Description: Patch for Proteus Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 863
Read events
2 860
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3228) Patch-Proteus-8.16-SP3-36097.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 9C0C00008CBC65BBD264DA01 | |||
| (PID) Process: | (3228) Patch-Proteus-8.16-SP3-36097.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 9601978C45F80A0EFF41054EFD5E61175DF51C8EE0B428AD12AAD148E93A69A4 | |||
| (PID) Process: | (3228) Patch-Proteus-8.16-SP3-36097.0.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
6
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\English.ini | text | |
MD5:4FB66AF3052A25731D1F9C96BD17A654 | SHA256:C15E8CE6FE9CBF5FF30D3002619A55774F8C6198678CF6DA26C6768F2A56B6FA | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\Dutch.ini | text | |
MD5:19EFA220A5C5FF287A83075BF69C8D92 | SHA256:377ED1A0F6D26AC799BDDC35F7677BAFF122E03CCE70DF1A80C7358B658372D6 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\Italian.ini | text | |
MD5:92CCEED7990382F4F34A7A15E66B96E3 | SHA256:60C0823A9D451868DD60A472849DFE9C2A557B4CC62FE40BACF4074C89514970 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\wintb.dll | executable | |
MD5:9436DF49E08C83BAD8DDC906478C2041 | SHA256:1910537AA95684142250CA0C7426A0B5F082E39F6FBDBDBA649AECB179541435 | |||
| 3656 | Patch-Proteus-8.16-SP3-36097.0.exe | C:\Users\admin\AppData\Local\Temp\is-4KDNU.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp | executable | |
MD5:34ACC2BDB45A9C436181426828C4CB49 | SHA256:9C81817ACD4982632D8C7F1DF3898FCA1477577738184265D735F49FC5480F07 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\German.ini | text | |
MD5:B35BC657CCBFF642E13DDE3A7664C758 | SHA256:95C7895FE10FA03D4A0A47D9F37BE6020E72582819B22AAE60B07D524E33DBB7 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\isproc.dll | executable | |
MD5:4BAFB0739C5FCD96BE991F2A3CC9AC2F | SHA256:7F74F1C445BF5E9456AAE6FAE695A8CA60E1D0EB5A2F44AC2CF0239A71F1A8A1 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\Polish.ini | text | |
MD5:7D036F232CE9C88FFF6123C953B85635 | SHA256:9F5D6C5C56939DEC8B578A5CE4EA4D5B656442BA4BBDE429EA983F48F9F23687 | |||
| 3228 | Patch-Proteus-8.16-SP3-36097.0.tmp | C:\Users\admin\AppData\Local\Temp\is-D8DDM.tmp\lang\Portuguese.ini | text | |
MD5:97F4CE0805B41B213B57760BFE19D8AD | SHA256:5EE928ABDD572EFE72E4AC05FBCD9596DF2954883A898A4014151E8D994FA572 | |||
| 3944 | Patch-Proteus-8.16-SP3-36097.0.exe | C:\Users\admin\AppData\Local\Temp\is-JA07A.tmp\Patch-Proteus-8.16-SP3-36097.0.tmp | executable | |
MD5:34ACC2BDB45A9C436181426828C4CB49 | SHA256:9C81817ACD4982632D8C7F1DF3898FCA1477577738184265D735F49FC5480F07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |