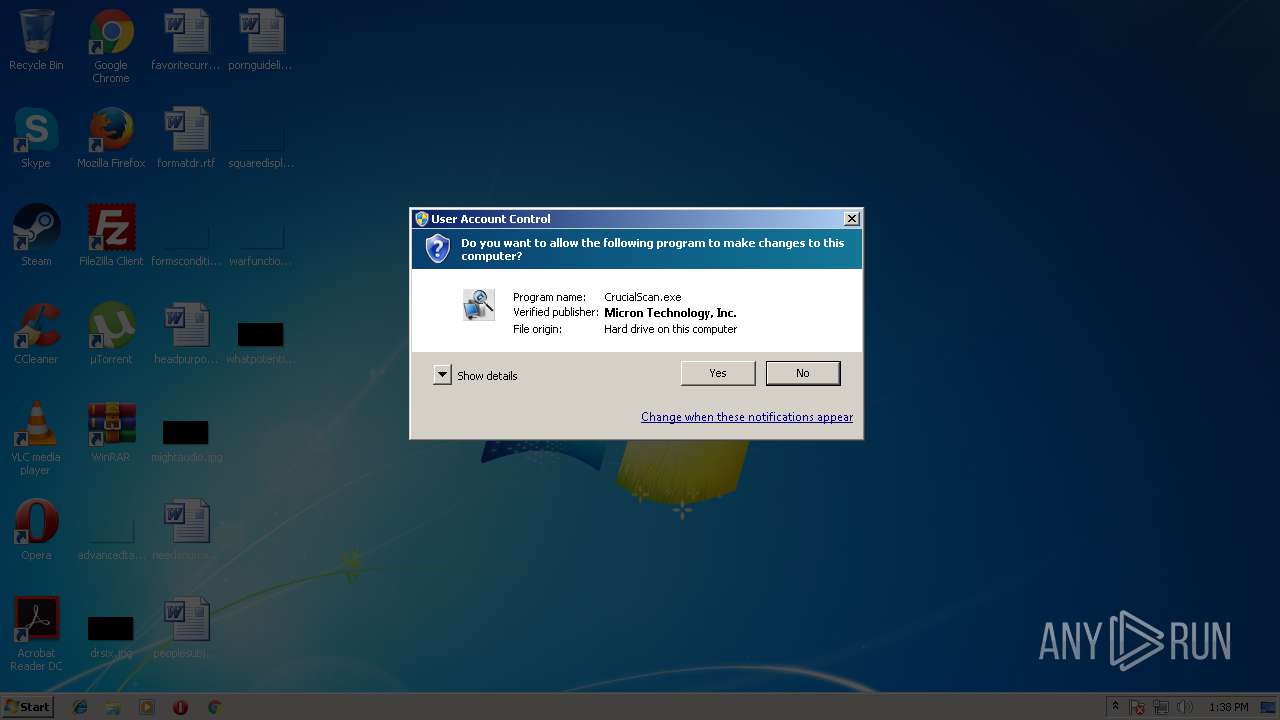
| download: | CrucialScan.exe |
| Full analysis: | https://app.any.run/tasks/6c120373-9f27-4071-aa6f-7fbda9d84461 |
| Verdict: | No threats detected |
| Analysis date: | August 31, 2018, 12:37:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | C8D3353A59AF1D76A5D78F09F6238CE1 |
| SHA1: | F37C9A8AA3CA3EEB83E1CE5CCEC4916476666D4C |
| SHA256: | 8D9CF4309A7CA3B2F13F01D7700145EFA597BC6BB30D4080305BD69912E8CA40 |
| SSDEEP: | 3072:lO3WoLgcAfkEld57woDFUdza9TSQGEWUVs3kt982S6ZfaSEHKSff1SStN:eXAcidnFUdGtSOc3082VCZHKa9Vf |
MALICIOUS
No malicious indicators.SUSPICIOUS
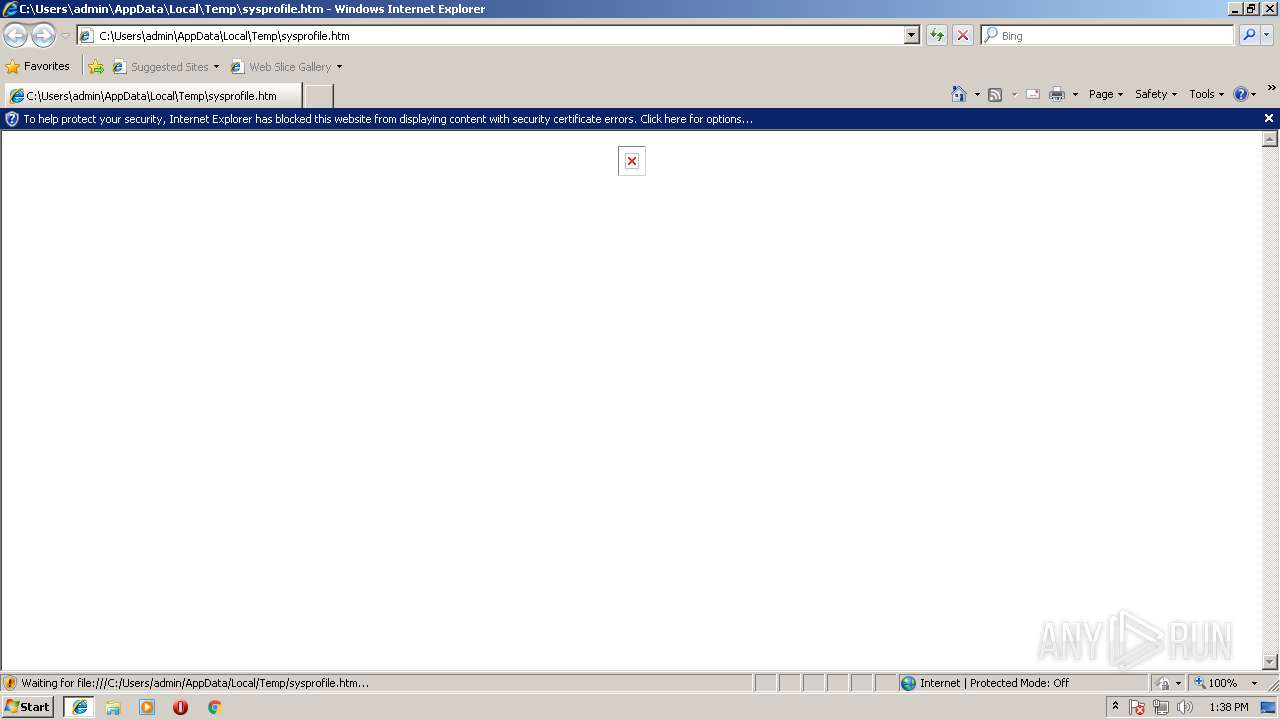
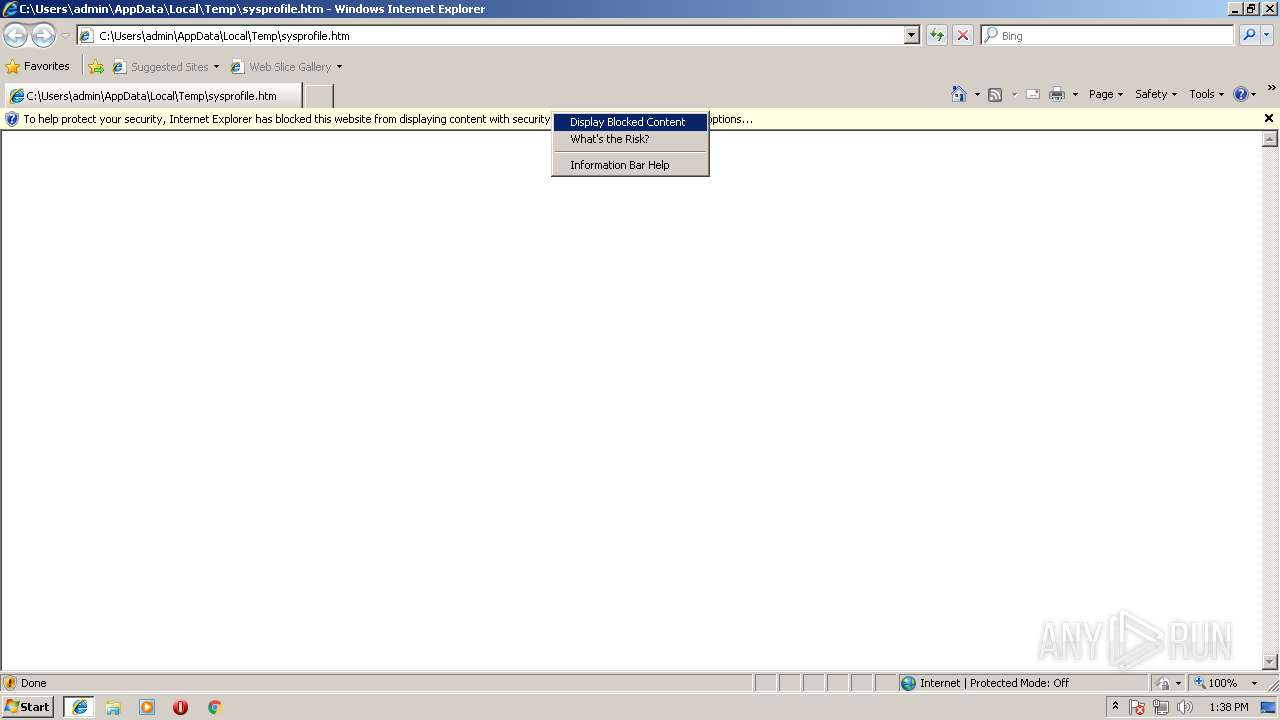
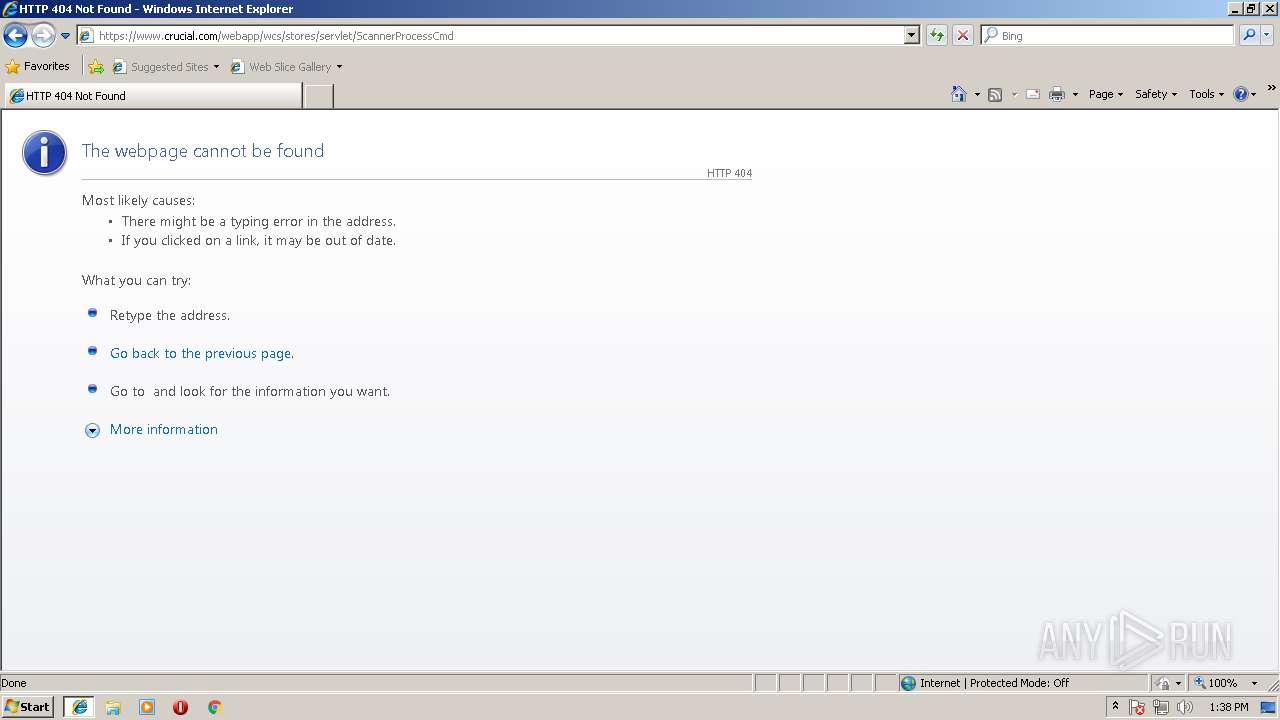
Starts Internet Explorer
- CrucialScan.exe (PID: 2136)
Executable content was dropped or overwritten
- CrucialScan.exe (PID: 2136)
INFO
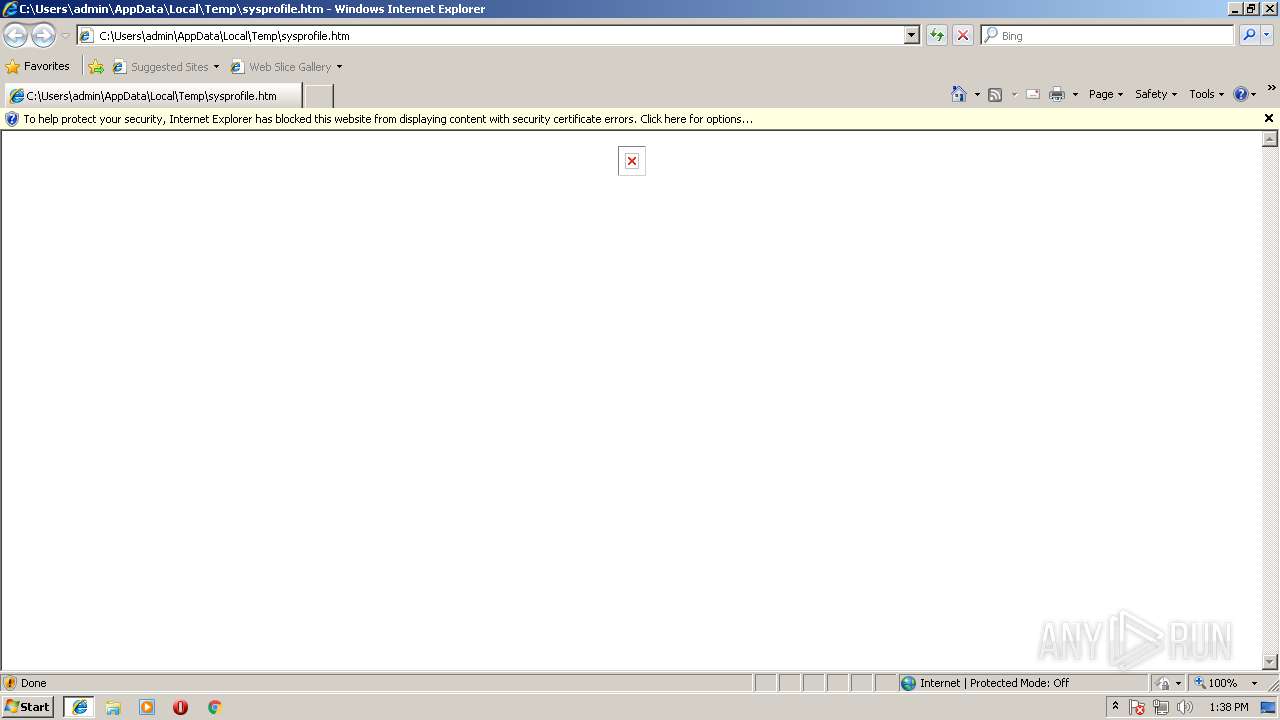
Changes internet zones settings
- iexplore.exe (PID: 2580)
Dropped object may contain URL's
- CrucialScan.exe (PID: 2136)
- iexplore.exe (PID: 2096)
- iexplore.exe (PID: 2580)
Reads internet explorer settings
- iexplore.exe (PID: 2096)
Application launched itself
- iexplore.exe (PID: 2580)
Reads Internet Cache Settings
- iexplore.exe (PID: 2580)
- iexplore.exe (PID: 2096)
Creates files in the user directory
- iexplore.exe (PID: 2096)
- iexplore.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:10 16:51:30+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 122880 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf644 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 10-Aug-2018 14:51:30 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Aug-2018 14:51:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001D798 | 0x0001E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47067 |
.rdata | 0x0001F000 | 0x00006B14 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39331 |
.data | 0x00026000 | 0x00003280 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59317 |
.rsrc | 0x0002A000 | 0x0000E750 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.47382 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91785 | 501 | Latin 1 / Western European | English - United States | RT_MANIFEST |
116 | 6.57738 | 18608 | Latin 1 / Western European | English - United States | EXTFILE |
117 | 6.49265 | 16264 | Latin 1 / Western European | English - United States | EXTFILE |
121 | 6.09738 | 9344 | Latin 1 / Western European | English - United States | EXTFILE |
122 | 5.83948 | 11776 | Latin 1 / Western European | English - United States | EXTFILE |
IDI_ICON1 | 1.81924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1600 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2580 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\CrucialScan.exe" | C:\Users\admin\AppData\Local\Temp\CrucialScan.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2284 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | CrucialScan.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3340 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
869
Read events
780
Write events
87
Delete events
2
Modification events
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\AdminActive |
| Operation: | write | Name: | {B844A146-AD1A-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207080005001F000C0026000B00CB03 | |||
Executable files
1
Suspicious files
5
Text files
21
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | CrucialScan.exe | C:\Users\admin\AppData\Local\Temp\sysprofile.htm | html | |
MD5:— | SHA256:— | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018083120180901\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB70EE7149711D860.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | CrucialScan.exe | C:\Users\admin\AppData\Local\Temp\CrucialSMBusScan_V32.sys | executable | |
MD5:66F76DF3DB2020477A970F7F6EAB1BCA | SHA256:5729F1121FF4C2CBC029EE1CB86E5580B783336337E25DE795DD861F05B8BC33 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2CCB5172A3FF3204.TMP | — | |
MD5:— | SHA256:— | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\NBLQPZGH\green_shield[1] | image | |
MD5:254D388CE19D84A54FD44571E049E6A6 | SHA256:C686BABC034F53A24A1206019E958BA8FC879216FD7B6A4B972F188535341227 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDD3D75DE401EAD06.TMP | — | |
MD5:— | SHA256:— | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\invalidcert[1] | html | |
MD5:E2817FEBFEDE77B8CC498C4833098742 | SHA256:AAB4F5B4BDD02B66B46643B0BBD40761C694B14857E6943F3AC03B692FD08047 | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GUFVP8I9\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\red_shield_48[1] | image | |
MD5:F413DD8A75B81A154A1FD5E4C4A0A782 | SHA256:F2AFC04A24C9D89D3C2F0D73F8CD6FB6B65ADBE333196C3F99CC7D6868847CEB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | iexplore.exe | GET | 404 | 131.253.33.200:80 | http://www.bing.com/favicon.ico | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
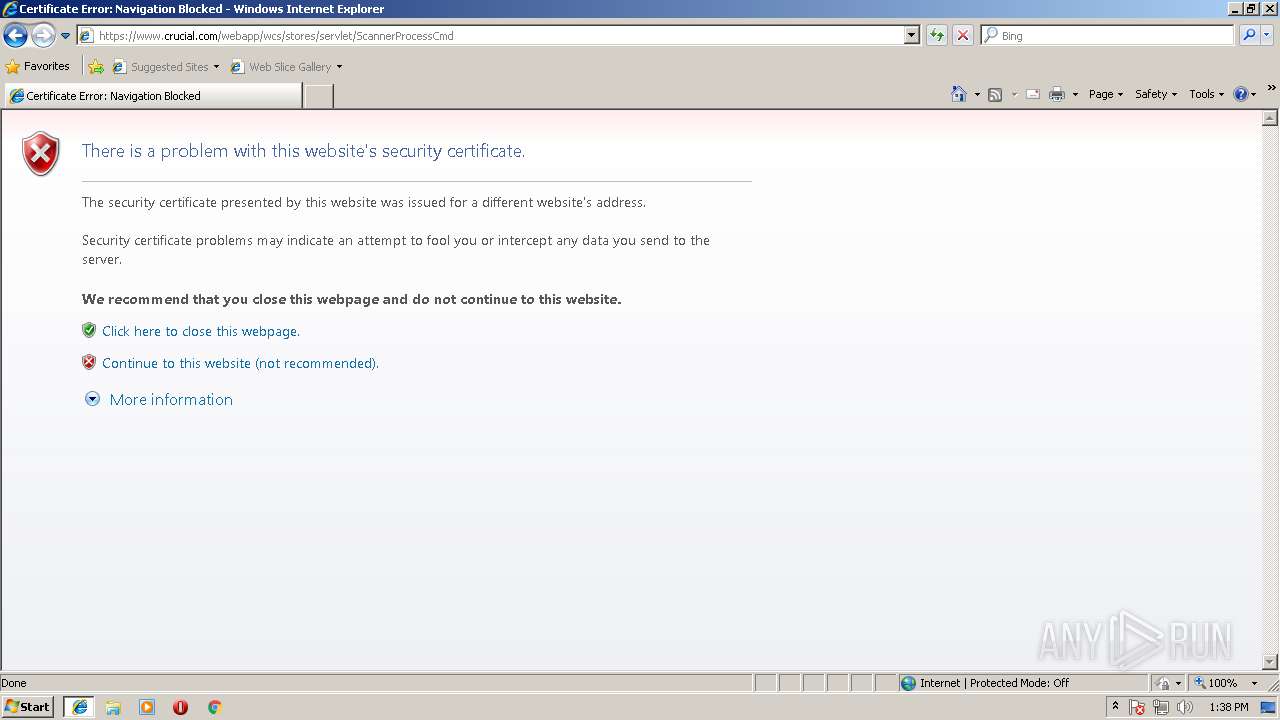
2096 | iexplore.exe | 68.232.35.24:443 | pics.crucial.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2096 | iexplore.exe | 192.229.182.59:443 | www.crucial.com | MCI Communications Services, Inc. d/b/a Verizon Business | GB | whitelisted |
2580 | iexplore.exe | 131.253.33.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
pics.crucial.com |
| unknown |
www.crucial.com |
| whitelisted |