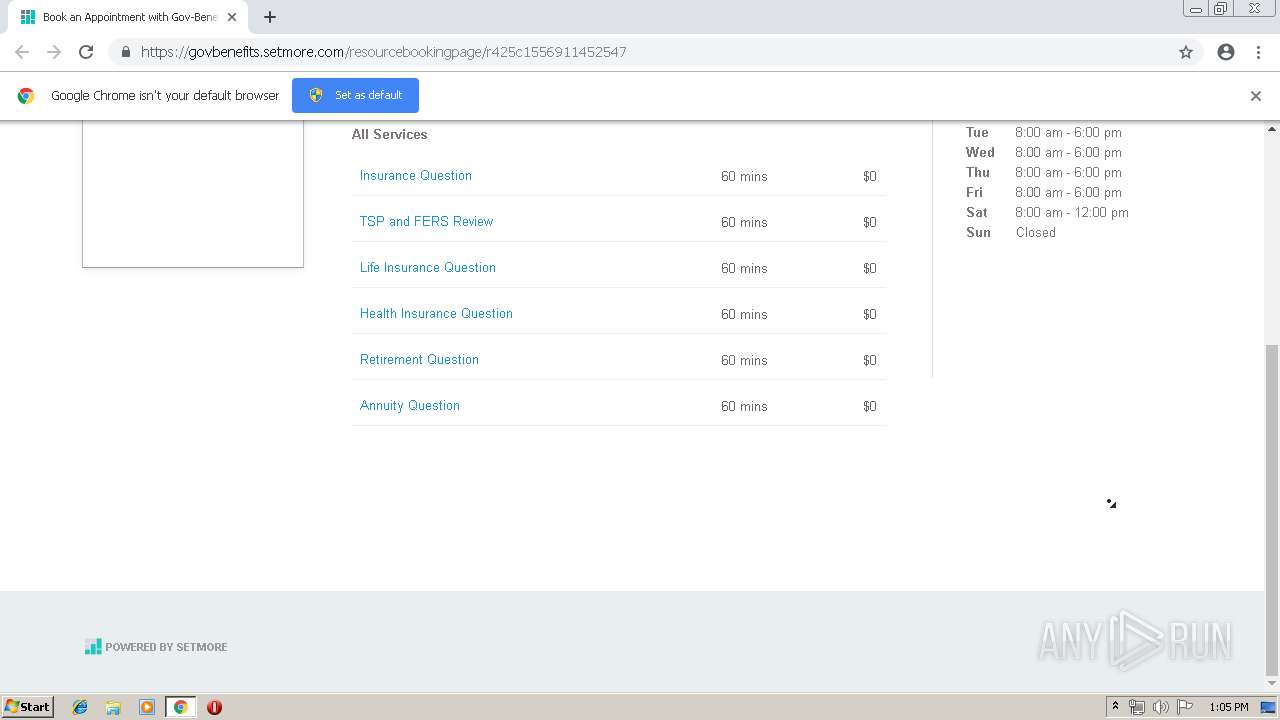
| URL: | http://r20.rs6.net/tn.jsp?f=001D4vAhpPoa-0ScKwSCzlU6bUDqfCts9djcoeJn0AzFdOQ3-6beAikM5p5p86lhXTfD-lSijCP00eZMHsFy0gmnELp57uL58KO628T_Ah_q2irB4fLHEr8FsqNuWuIIAEzR8kskh3aUErZDd2kNmRGbzuQLQrt5HPiYsv2gqv-Qw57QzmMKIf0Tm0MPw4YJ6Q57-6wiRdf6MWBwN_oo53uNRJIHpX-Cwa_LsLIJjI_p1IhPHc2QESFr40Q7LCd6DD7eZZ1NS3mu2Q=&c=ZZr1du4uu66zSAE5cR35V0ExbA0JRjpluKyRS5q5EjG_-pbFzicyjQ==&ch=OqYxE8L2i4H5LLtx_xz7GNVzqMibYjO3Pkb2lWmk-7j7rnGP6KzoCA== |
| Full analysis: | https://app.any.run/tasks/048cc0d0-09db-48a6-bc9b-d118e954c265 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 12:05:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 04E01D4FD3756FA8C306FF48A7FBD902 |
| SHA1: | 5EDF5AA99C95F0B073ED58B69EE62F8BC6660D59 |
| SHA256: | 8D9A63A3F2EF4A73995CDFF8850117981711728ACC1CEAC7D82A87B339549834 |
| SSDEEP: | 6:CMXVBTmkFlARWp9MK2JXgn27wekSxjnNxIzt/HwJlIeCPg+qwKYn9jTw3WIc3qsm:ZFBqkFLbp2kek6LAmJlIrg+qcRw3HG2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2836)
INFO
Application launched itself
- chrome.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13946079966633798136 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=278846143728141815 --mojo-platform-channel-handle=4348 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8253651769183678253 --mojo-platform-channel-handle=2824 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4624929951197163966 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8815811560281343055 --mojo-platform-channel-handle=4364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --service-pipe-token=14317209009794077821 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14317209009794077821 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --service-pipe-token=14499659466139193942 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14499659466139193942 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --service-pipe-token=7009548990111187456 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7009548990111187456 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9205985463139968871 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2215474050279412294 --mojo-platform-channel-handle=4240 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
556
Read events
466
Write events
85
Delete events
5
Modification events
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2836-13202395538952625 |
Value: 259 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2836) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
76
Text files
187
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\18d5d222-7a1d-4cdd-84f2-c4c2b6e7baab.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
34
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2836 | chrome.exe | GET | 302 | 208.75.122.11:80 | http://r20.rs6.net/tn.jsp?f=001D4vAhpPoa-0ScKwSCzlU6bUDqfCts9djcoeJn0AzFdOQ3-6beAikM5p5p86lhXTfD-lSijCP00eZMHsFy0gmnELp57uL58KO628T_Ah_q2irB4fLHEr8FsqNuWuIIAEzR8kskh3aUErZDd2kNmRGbzuQLQrt5HPiYsv2gqv-Qw57QzmMKIf0Tm0MPw4YJ6Q57-6wiRdf6MWBwN_oo53uNRJIHpX-Cwa_LsLIJjI_p1IhPHc2QESFr40Q7LCd6DD7eZZ1NS3mu2Q=&c=ZZr1du4uu66zSAE5cR35V0ExbA0JRjpluKyRS5q5EjG_-pbFzicyjQ==&ch=OqYxE8L2i4H5LLtx_xz7GNVzqMibYjO3Pkb2lWmk-7j7rnGP6KzoCA== | US | — | — | whitelisted |
2836 | chrome.exe | GET | 302 | 64.233.184.198:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2836 | chrome.exe | GET | 200 | 217.146.165.206:80 | http://r3---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.108&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1557920949&mv=u&pl=27&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2836 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
2836 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
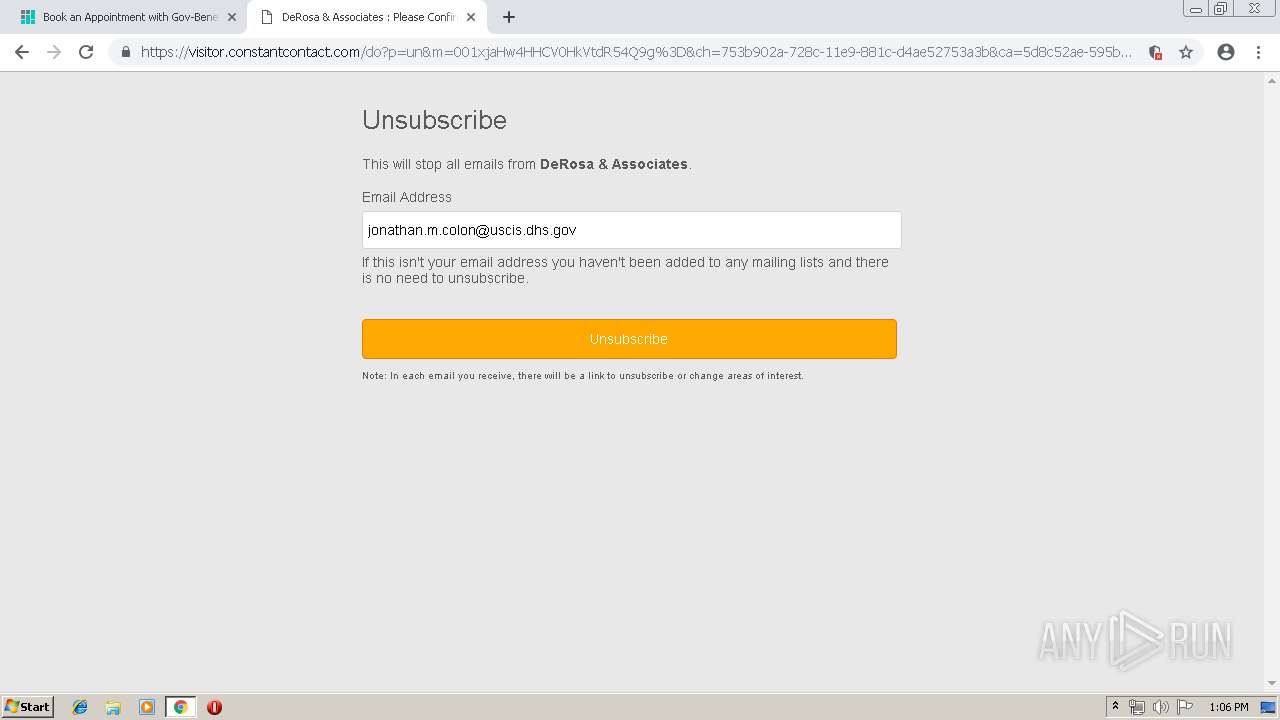
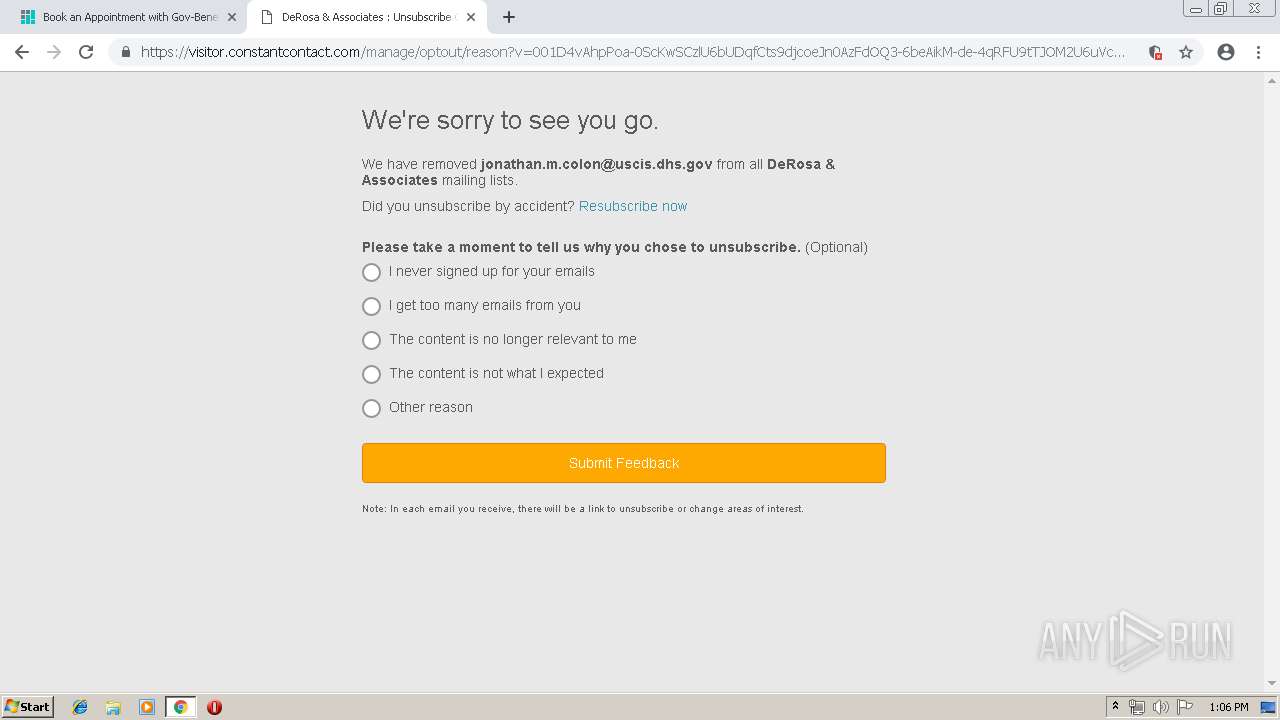
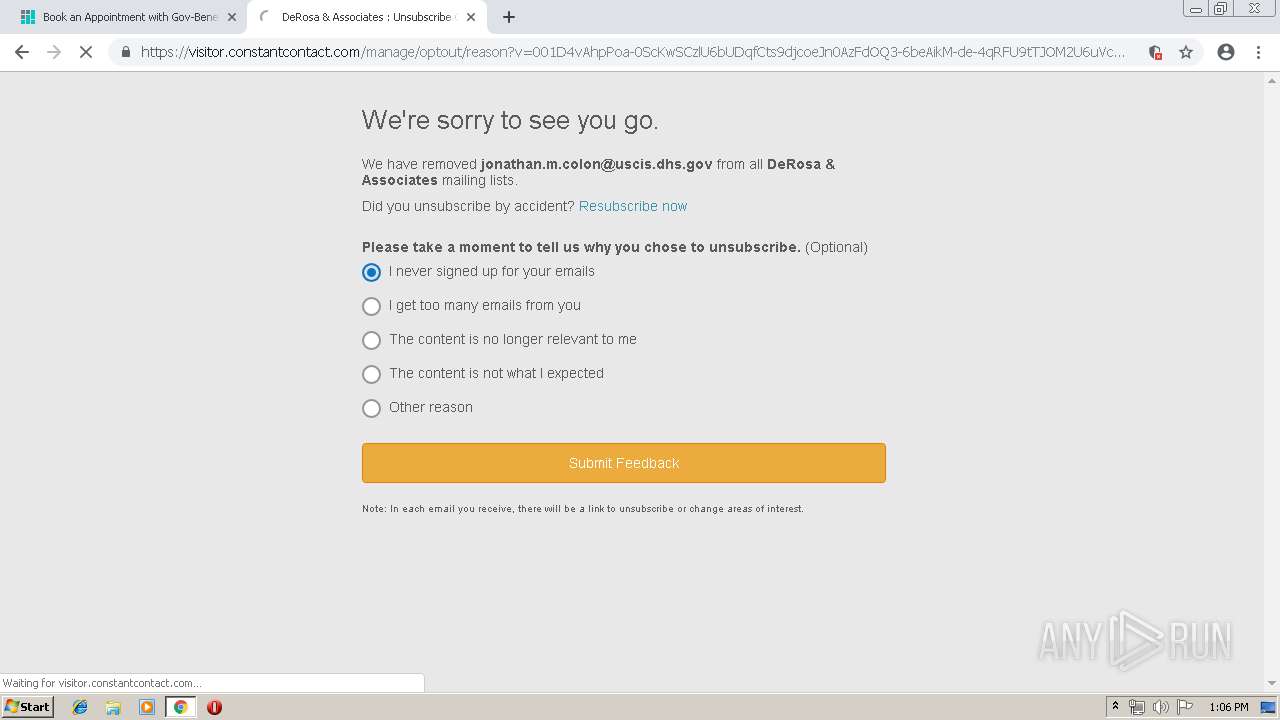
2836 | chrome.exe | 208.75.122.11:80 | r20.rs6.net | Constant Contact, Inc | US | suspicious |
2836 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
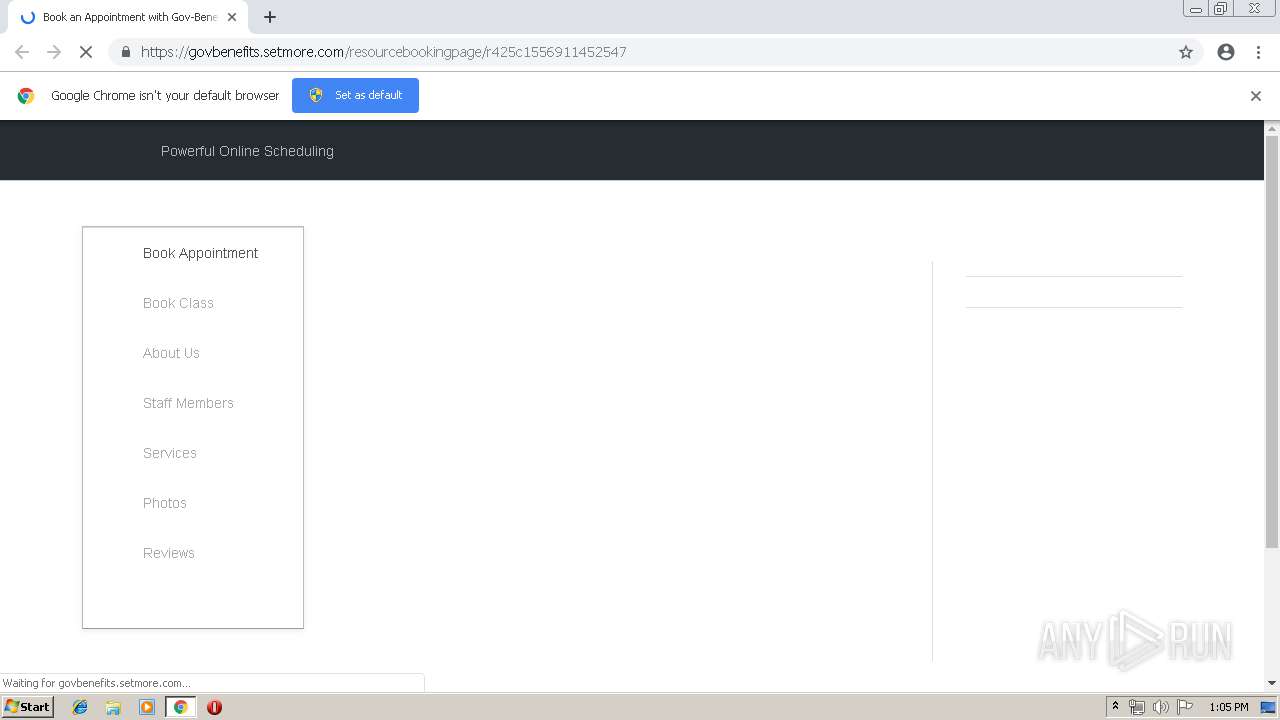
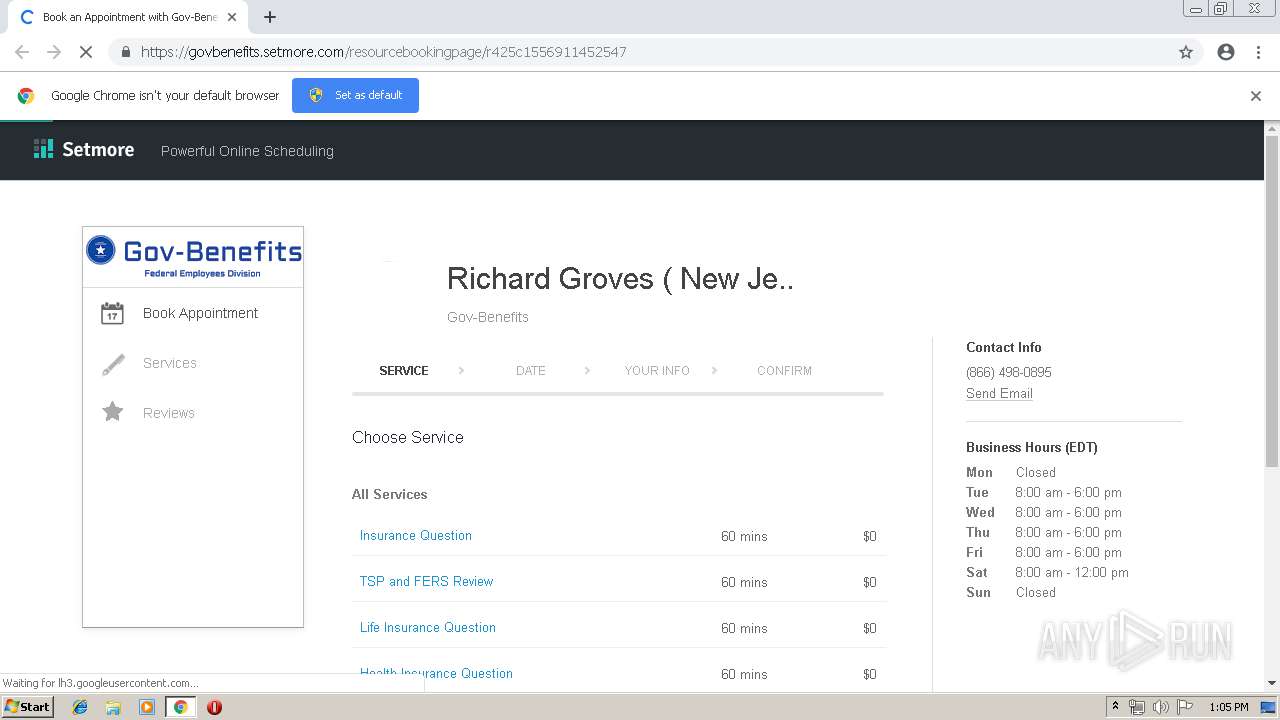
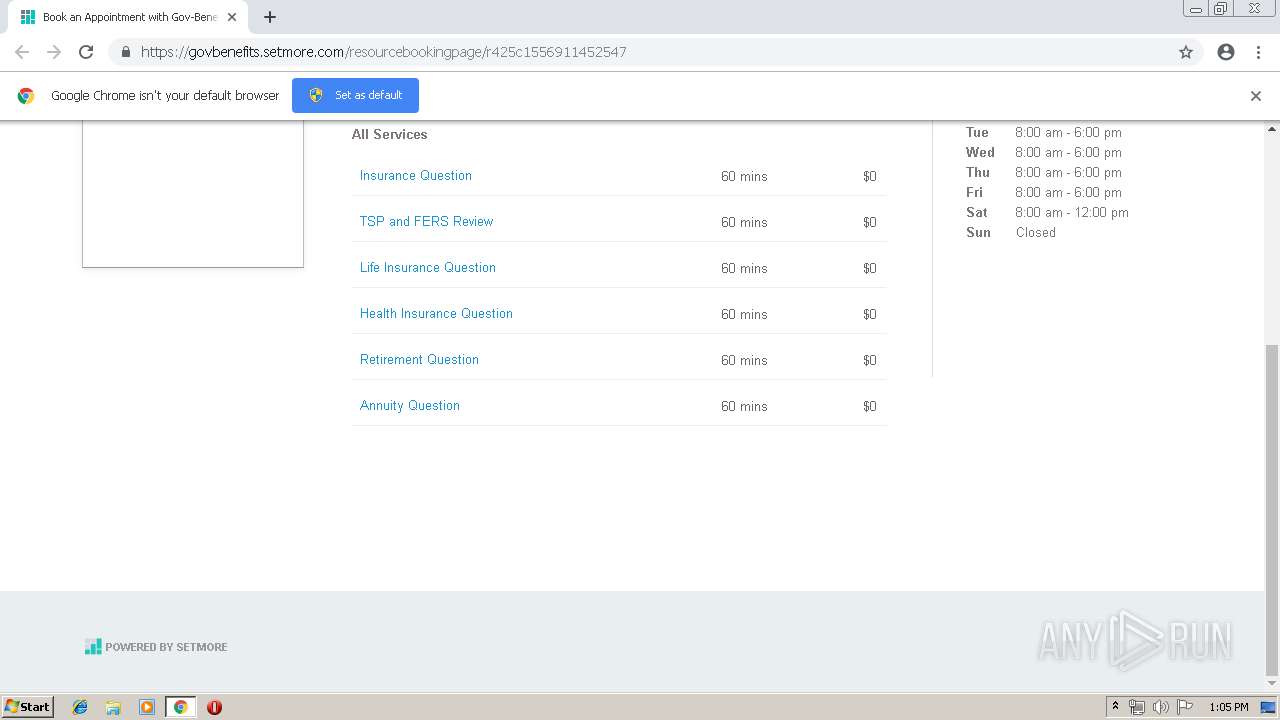
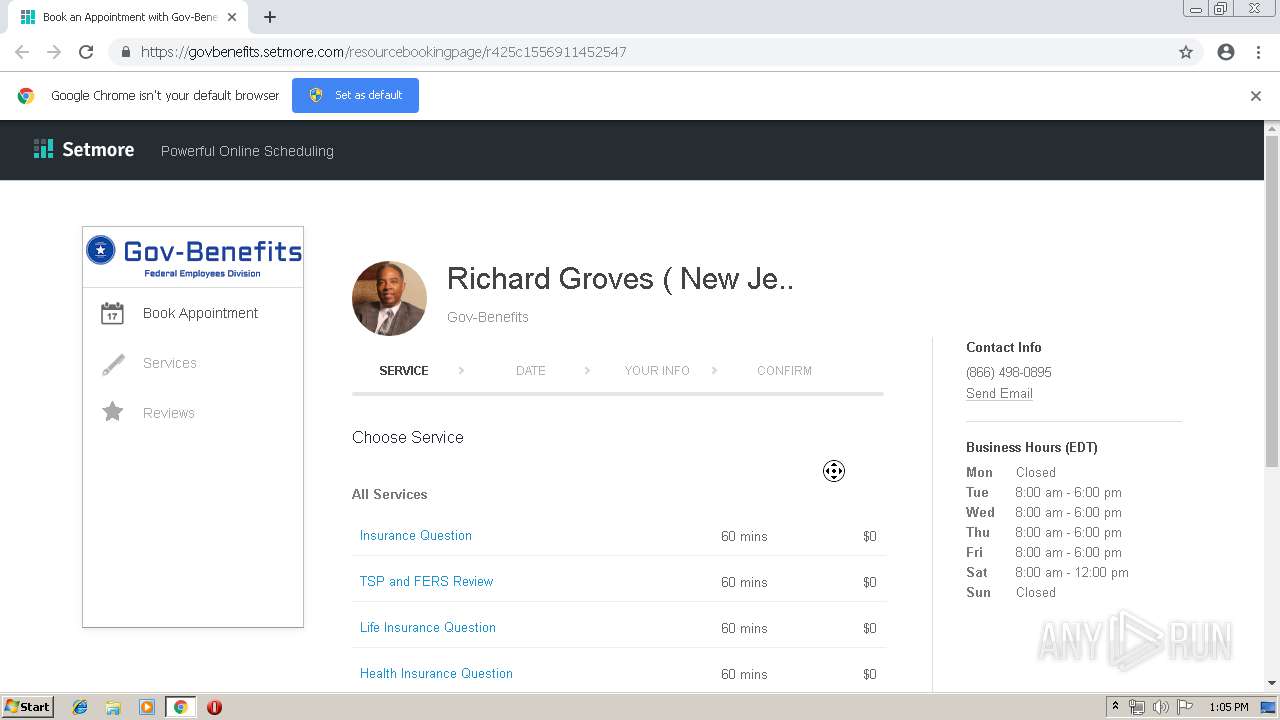
2836 | chrome.exe | 216.58.207.51:443 | govbenefits.setmore.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 157.240.1.23:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
— | — | 172.217.21.193:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
2836 | chrome.exe | 104.19.198.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2836 | chrome.exe | 74.122.190.85:443 | js.squareup.com | Square, Inc. | US | malicious |
2836 | chrome.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2836 | chrome.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
r20.rs6.net |
| whitelisted |
accounts.google.com |
| shared |
govbenefits.setmore.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
js.squareup.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
unpkg.com |
| whitelisted |
my.setmore.com |
| malicious |