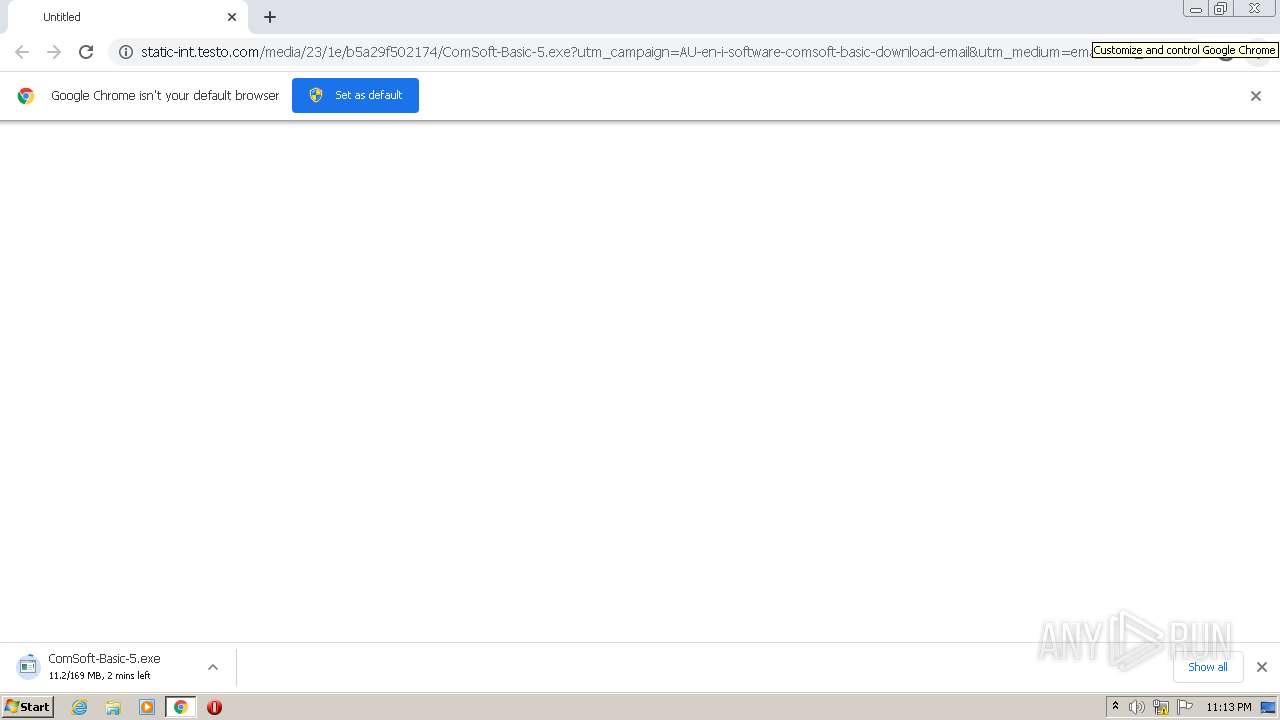
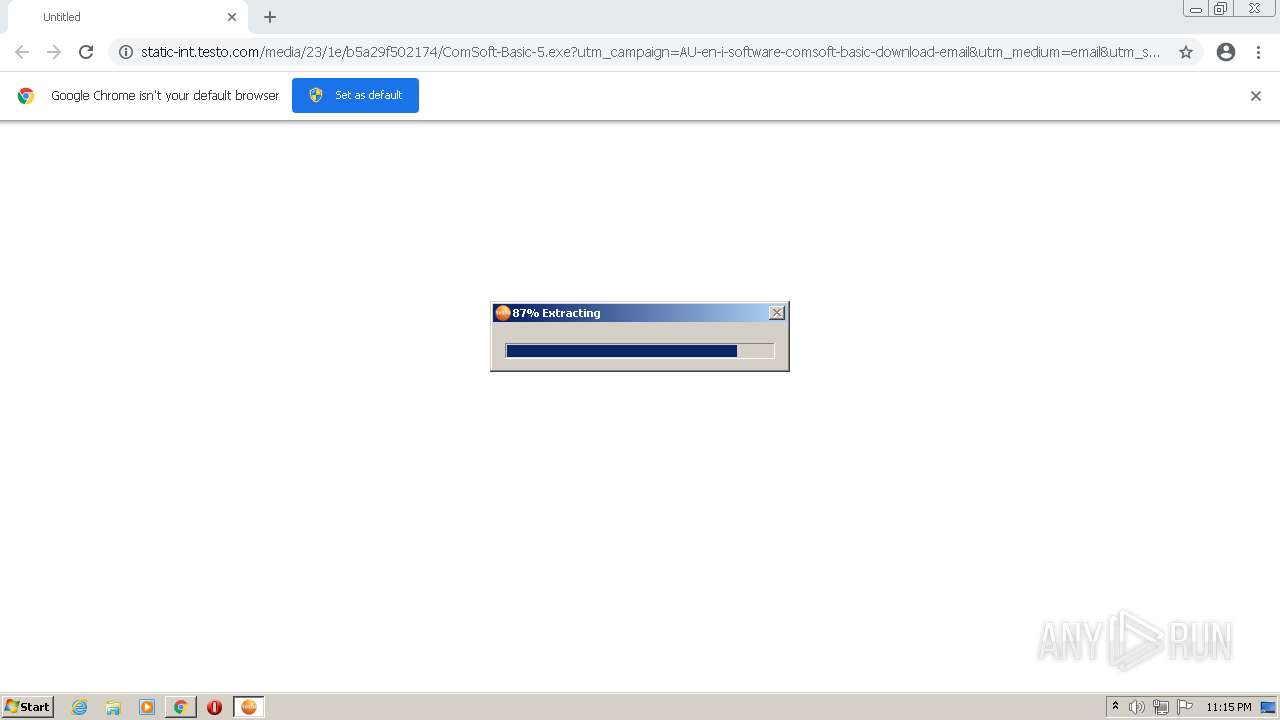
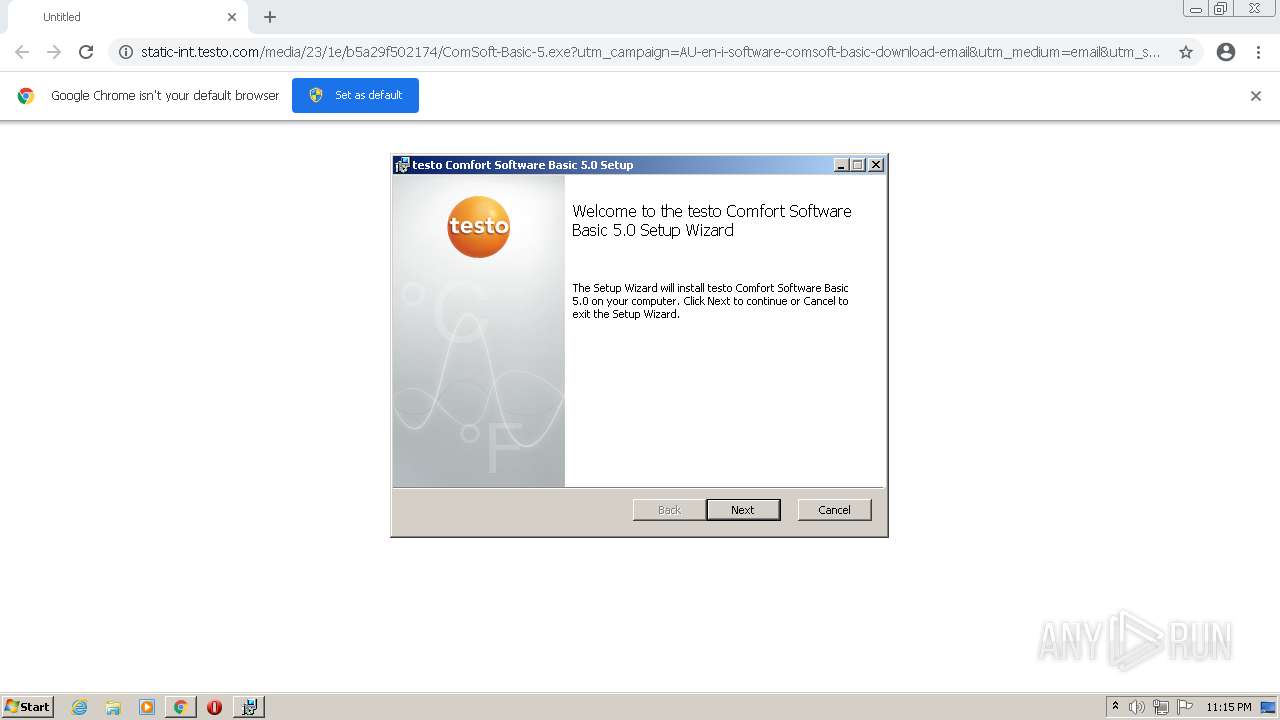
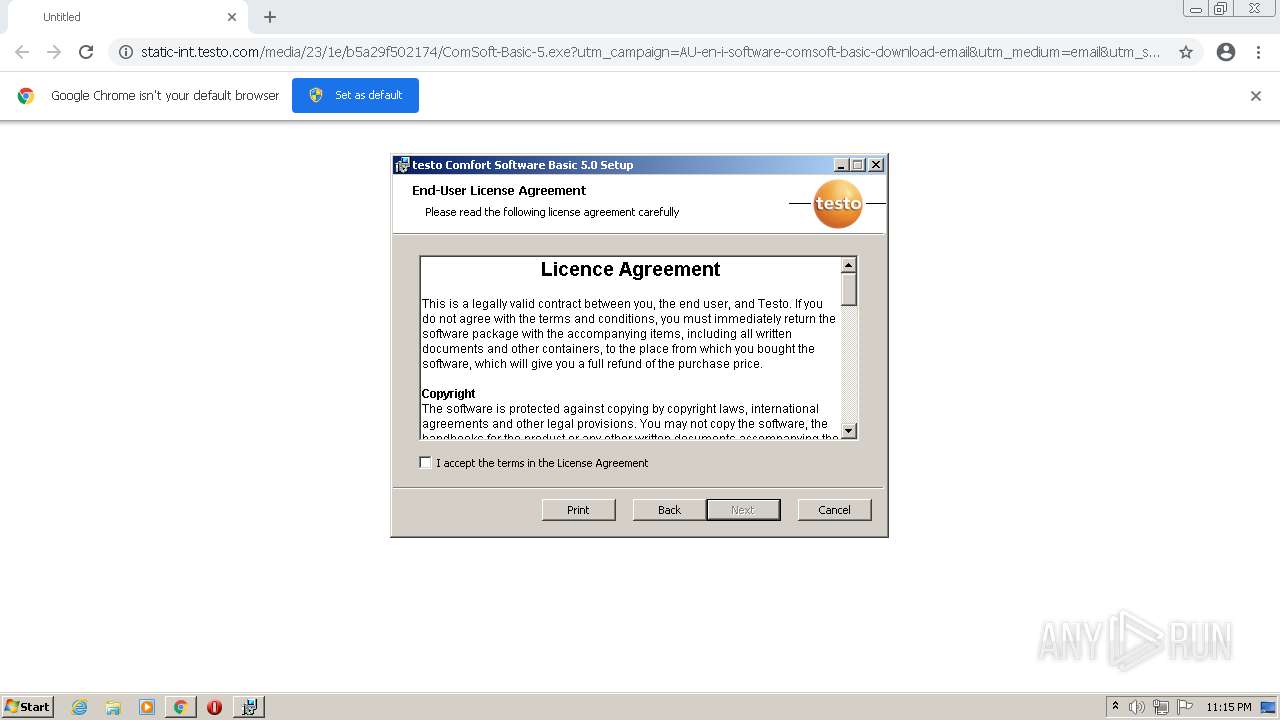
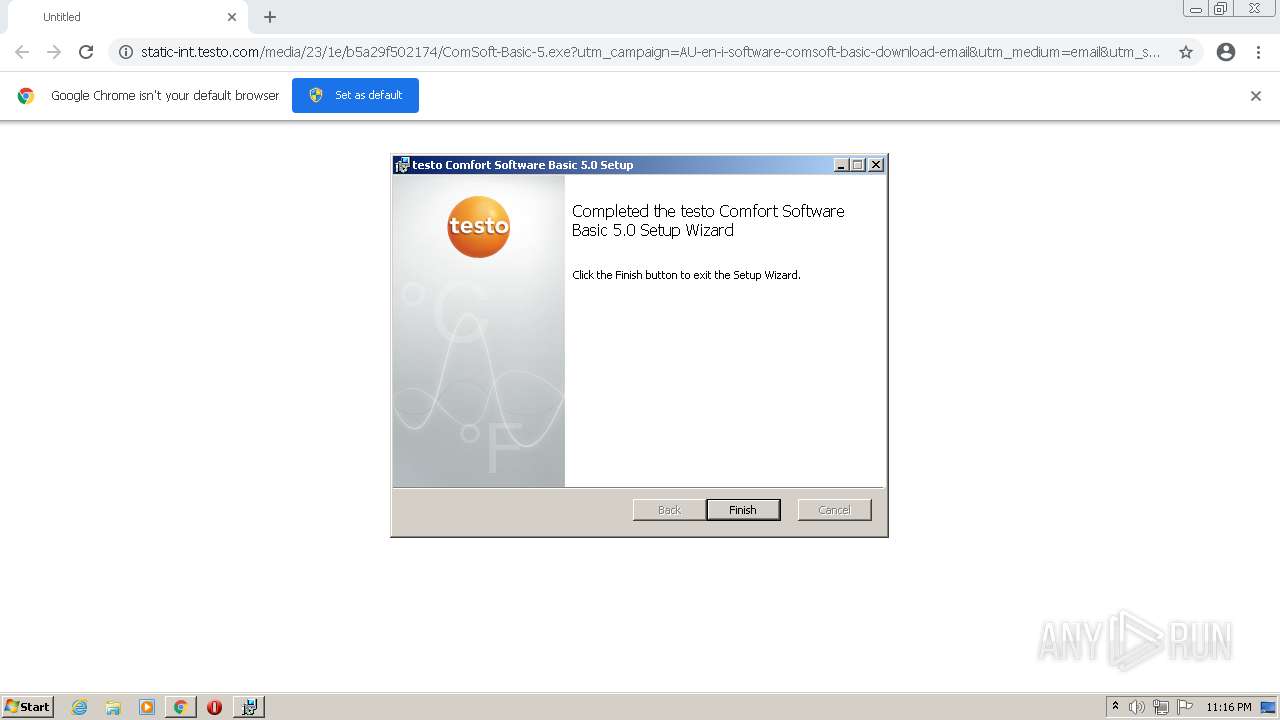
| URL: | https://static-int.testo.com/media/23/1e/b5a29f502174/ComSoft-Basic-5.exe?utm_campaign=AU-en-i-software-comsoft-basic-download-email&utm_medium=email&utm_source=Eloqua&elqTrackId=a9aa1a6e292b40959f0cec81e1b13b59&elq=86f6b23605d440a9ad6d2dc8fd13c62d&elqaid=22443&elqat=1&elqCampaignId=&elqcst=272&elqcsid=1034 |
| Full analysis: | https://app.any.run/tasks/05f809f3-a39b-42d1-a1a4-8bfb58165295 |
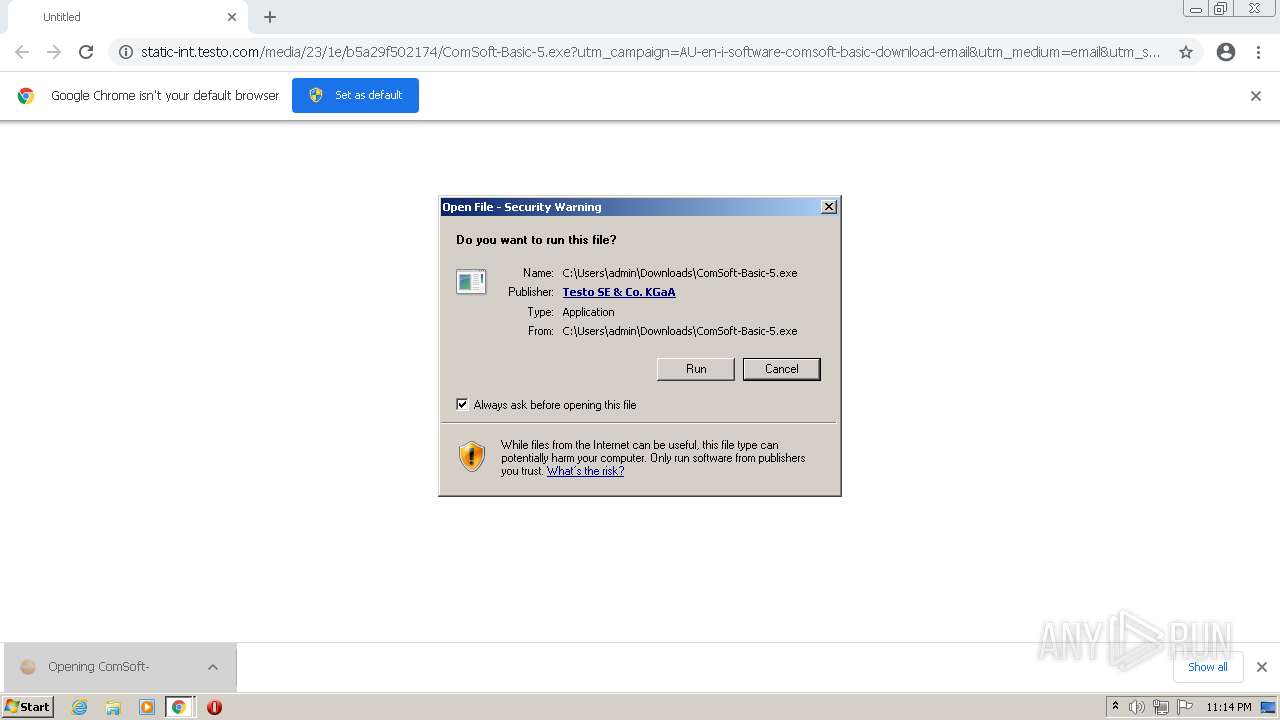
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2022, 23:13:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 10B3BB052CA21170A1E72CFA2486956B |
| SHA1: | CD415C59BA6C8777D7ADCC97B05C588EF78D0817 |
| SHA256: | 8D895426ABB4320F2B0987B21EF383782C43800A54BBBC0DDEBAEE879A0FE27E |
| SSDEEP: | 6:2cQj1AuGdLm+9YAjsw52QfWRJBStJYTRPq++KdXHXEVLWDLgPJHQXR:2cxdLmwYAjfUQmJBSLY19pX3kLWXuHqR |
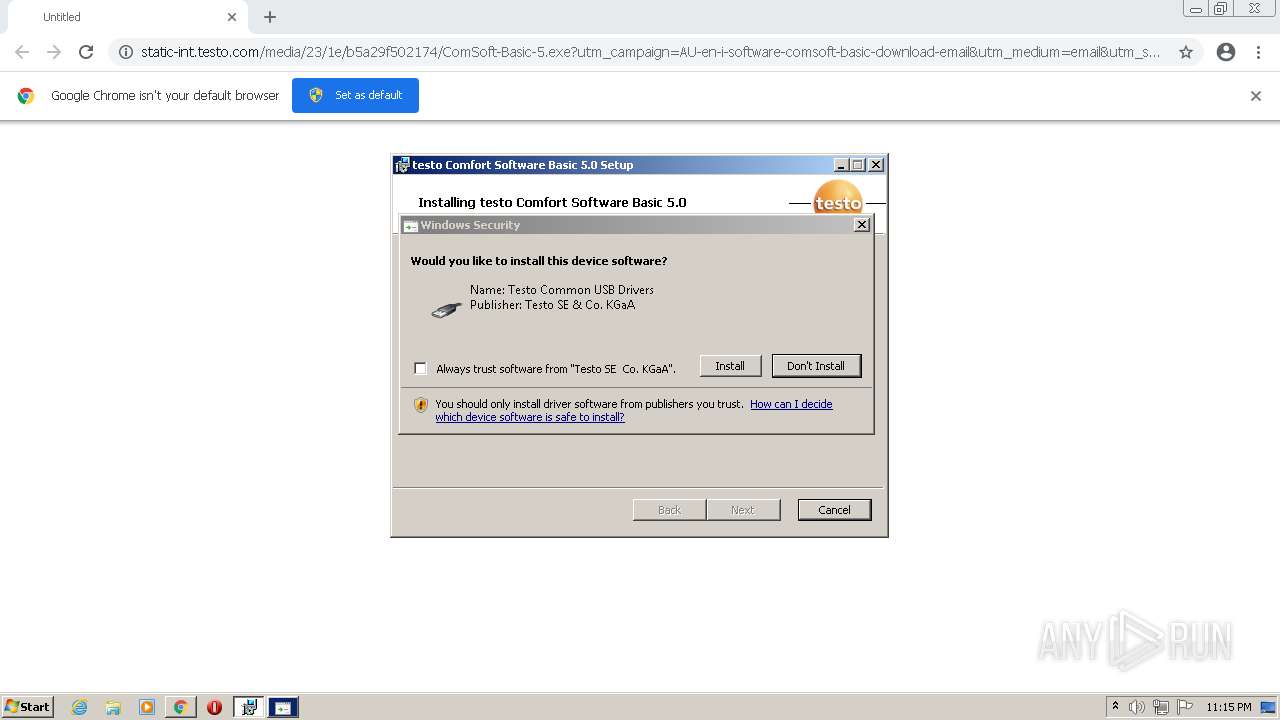
MALICIOUS
Application was dropped or rewritten from another process
- ComSoft-Basic-5.exe (PID: 2340)
- TestoSetup.exe (PID: 3328)
- setup.exe (PID: 576)
- ComSoft.exe (PID: 3404)
- setup.exe (PID: 3276)
Actions looks like stealing of personal data
- TestoSetup.exe (PID: 3328)
- msiexec.exe (PID: 1376)
Drops executable file immediately after starts
- setup.exe (PID: 3276)
- MsiExec.exe (PID: 3944)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
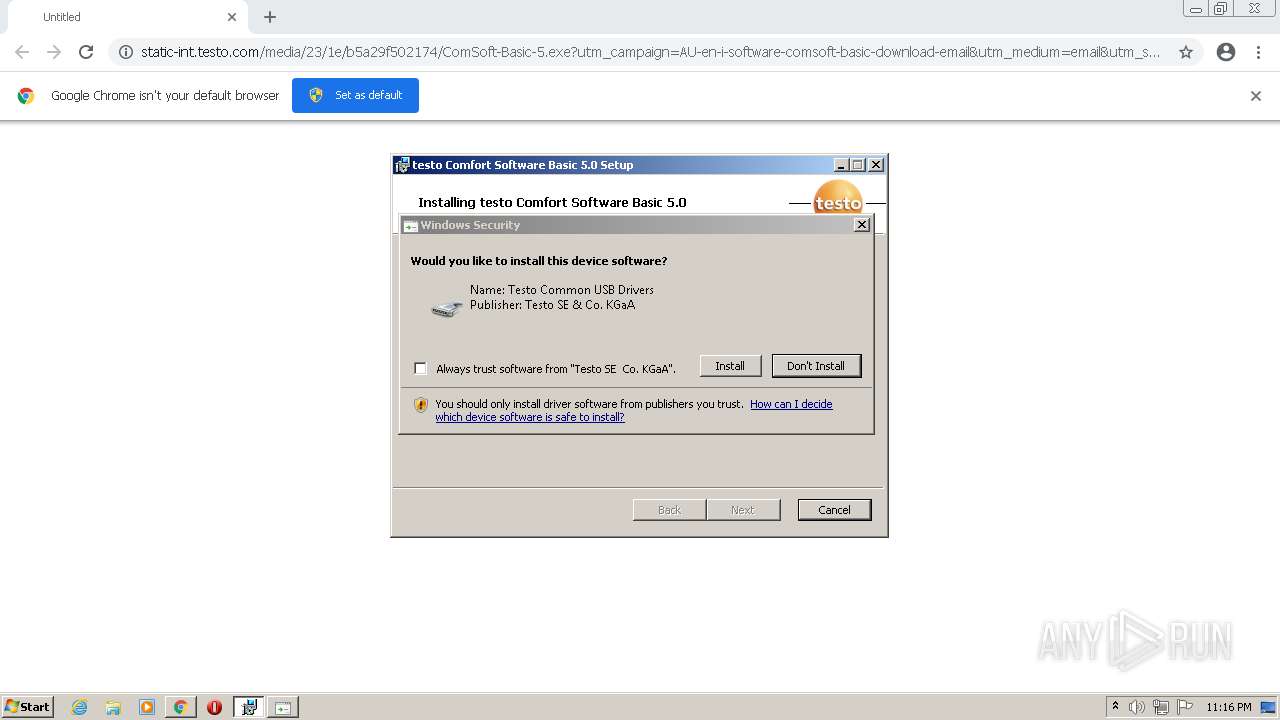
Changes settings of System certificates
- setup.exe (PID: 3276)
- rundll32.exe (PID: 3316)
Loads dropped or rewritten executable
- setup.exe (PID: 3276)
- ComSoft.exe (PID: 3404)
SUSPICIOUS
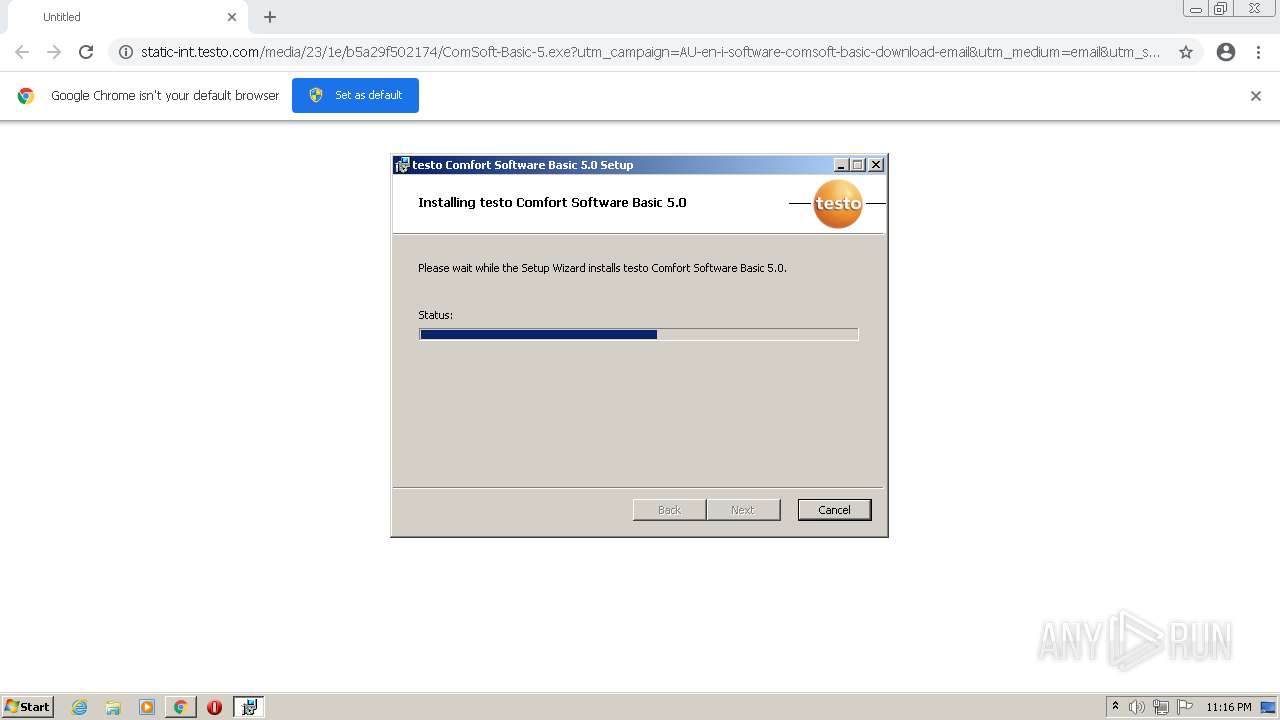
Executable content was dropped or overwritten
- chrome.exe (PID: 3652)
- ComSoft-Basic-5.exe (PID: 2340)
- msiexec.exe (PID: 1032)
- setup.exe (PID: 3276)
- msiexec.exe (PID: 1376)
- MsiExec.exe (PID: 3944)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Checks supported languages
- ComSoft-Basic-5.exe (PID: 2340)
- setup.exe (PID: 576)
- TestoSetup.exe (PID: 3328)
- setup.exe (PID: 3276)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
- ComSoft.exe (PID: 3404)
Drops a file with too old compile date
- ComSoft-Basic-5.exe (PID: 2340)
- setup.exe (PID: 3276)
- msiexec.exe (PID: 1376)
Drops a file that was compiled in debug mode
- ComSoft-Basic-5.exe (PID: 2340)
- msiexec.exe (PID: 1032)
- setup.exe (PID: 3276)
- msiexec.exe (PID: 1376)
- MsiExec.exe (PID: 3944)
- DrvInst.exe (PID: 2524)
- DrvInst.exe (PID: 3544)
Reads the computer name
- setup.exe (PID: 576)
- ComSoft-Basic-5.exe (PID: 2340)
- TestoSetup.exe (PID: 3328)
- setup.exe (PID: 3276)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
- ComSoft.exe (PID: 3404)
Executed as Windows Service
- msiexec.exe (PID: 1376)
- vssvc.exe (PID: 2332)
Reads Windows owner or organization settings
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
Reads the Windows organization settings
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
Application launched itself
- msiexec.exe (PID: 1376)
Searches for installed software
- msiexec.exe (PID: 1376)
Reads Environment values
- vssvc.exe (PID: 2332)
- setup.exe (PID: 3276)
Creates a directory in Program Files
- msiexec.exe (PID: 1376)
- setup.exe (PID: 3276)
Drops a file with a compile date too recent
- msiexec.exe (PID: 1376)
Creates files in the Windows directory
- setup.exe (PID: 3276)
- msiexec.exe (PID: 1376)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 2524)
- DrvInst.exe (PID: 3544)
Creates files in the program directory
- msiexec.exe (PID: 1376)
- setup.exe (PID: 3276)
Creates a software uninstall entry
- setup.exe (PID: 3276)
- msiexec.exe (PID: 1376)
Creates files in the driver directory
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Executed via COM
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Removes files from Windows directory
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Adds / modifies Windows certificates
- rundll32.exe (PID: 3316)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 1376)
Creates files in the user directory
- ComSoft.exe (PID: 3404)
INFO
Checks supported languages
- chrome.exe (PID: 3972)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 372)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 468)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 1156)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 884)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 416)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 3296)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
- vssvc.exe (PID: 2332)
- MsiExec.exe (PID: 2720)
- MsiExec.exe (PID: 2380)
- MsiExec.exe (PID: 3944)
- rundll32.exe (PID: 2188)
- rundll32.exe (PID: 3316)
- WISPTIS.EXE (PID: 2704)
Reads the hosts file
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3928)
Reads the computer name
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 468)
- chrome.exe (PID: 1156)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 884)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3296)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
- MsiExec.exe (PID: 2380)
- vssvc.exe (PID: 2332)
- MsiExec.exe (PID: 2720)
- MsiExec.exe (PID: 3944)
- rundll32.exe (PID: 2188)
- rundll32.exe (PID: 3316)
- WISPTIS.EXE (PID: 2704)
Application launched itself
- chrome.exe (PID: 3652)
Reads settings of System Certificates
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3652)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
- DrvInst.exe (PID: 3716)
- setup.exe (PID: 3276)
- DrvInst.exe (PID: 3544)
- rundll32.exe (PID: 2188)
- DrvInst.exe (PID: 2524)
- rundll32.exe (PID: 3316)
Reads the date of Windows installation
- chrome.exe (PID: 2920)
Checks Windows Trust Settings
- chrome.exe (PID: 3652)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 1376)
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- rundll32.exe (PID: 3316)
- DrvInst.exe (PID: 2524)
- rundll32.exe (PID: 2188)
Changes settings of System certificates
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
- DrvInst.exe (PID: 2524)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3716)
- DrvInst.exe (PID: 3544)
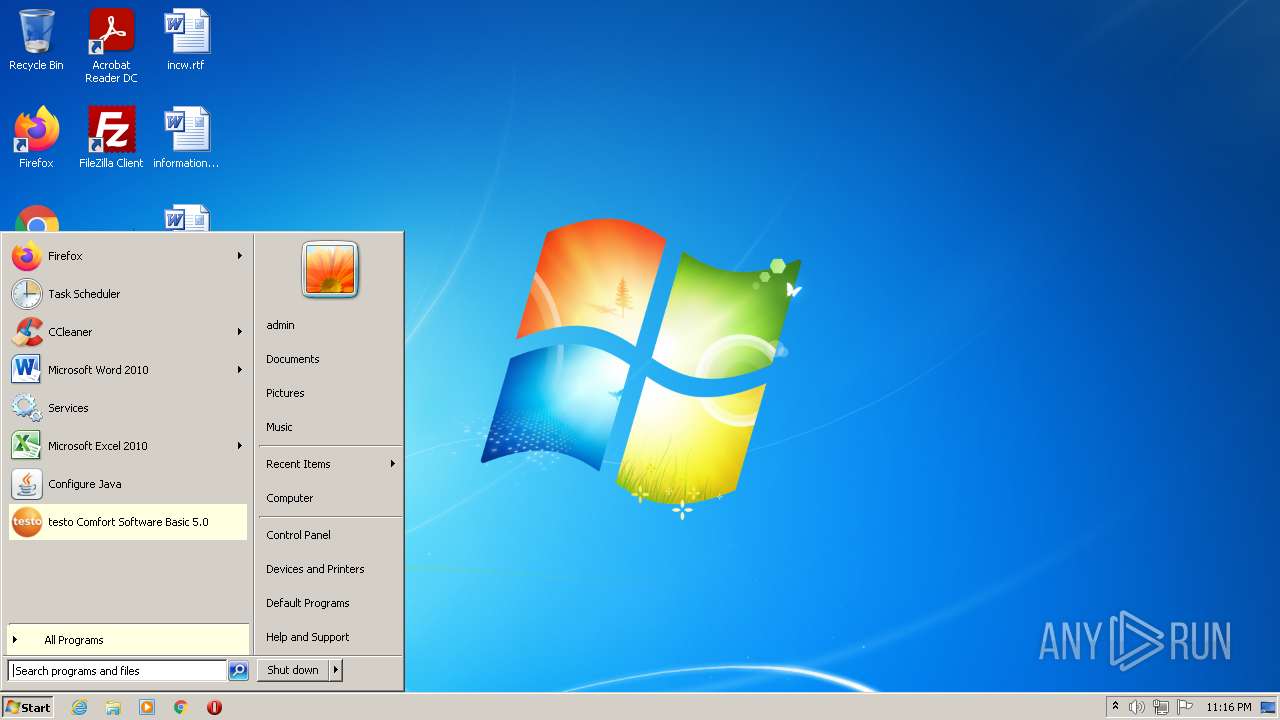
Manual execution by user
- ComSoft.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
38
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3220 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2680 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\Temp\testo\ComsoftBasic\csbasic32\setup.exe" | C:\Users\admin\AppData\Local\Temp\testo\ComsoftBasic\csbasic32\setup.exe | — | TestoSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2060 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Windows\system32\msiexec.exe" -I "C:\Users\admin\AppData\Local\Temp\testo\ComsoftBasic\csbasic32\csbasic32.msi" | C:\Windows\system32\msiexec.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3292 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1376 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1028,11087181637561965786,803424556770054839,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2188 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{6cf04ec6-9c14-5f50-0e57-3a62a310bf19} Global\{0ba065aa-c3a3-36c2-e9db-7912294c2b4a} C:\Windows\System32\DriverStore\Temp\{6023b7a7-f6da-5ea1-f815-7d3d855d023b}\ftdibus.inf C:\Windows\System32\DriverStore\Temp\{6023b7a7-f6da-5ea1-f815-7d3d855d023b}\ftdibus.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
54 445
Read events
52 516
Write events
1 903
Delete events
26
Modification events
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
230
Suspicious files
84
Text files
142
Unknown types
551
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62044A81-E44.pma | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12c934.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c7d4ec6f-09ef-458f-b606-5c41bfc06a8f.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF12c953.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF12ca2e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
11
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
872 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acswg5tbkr2ithrql6kjeh6vvwrq_2022.1.24.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.1.24.1201_all_oa3ppuxckzsaqpp445iqxhz4e4.crx3 | US | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.69 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 43.4 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 88.4 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 178 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 358 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
872 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
3928 | chrome.exe | 142.250.185.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1032 | msiexec.exe | 8.248.149.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3928 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
3928 | chrome.exe | 13.225.80.117:443 | static-int.testo.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
static-int.testo.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
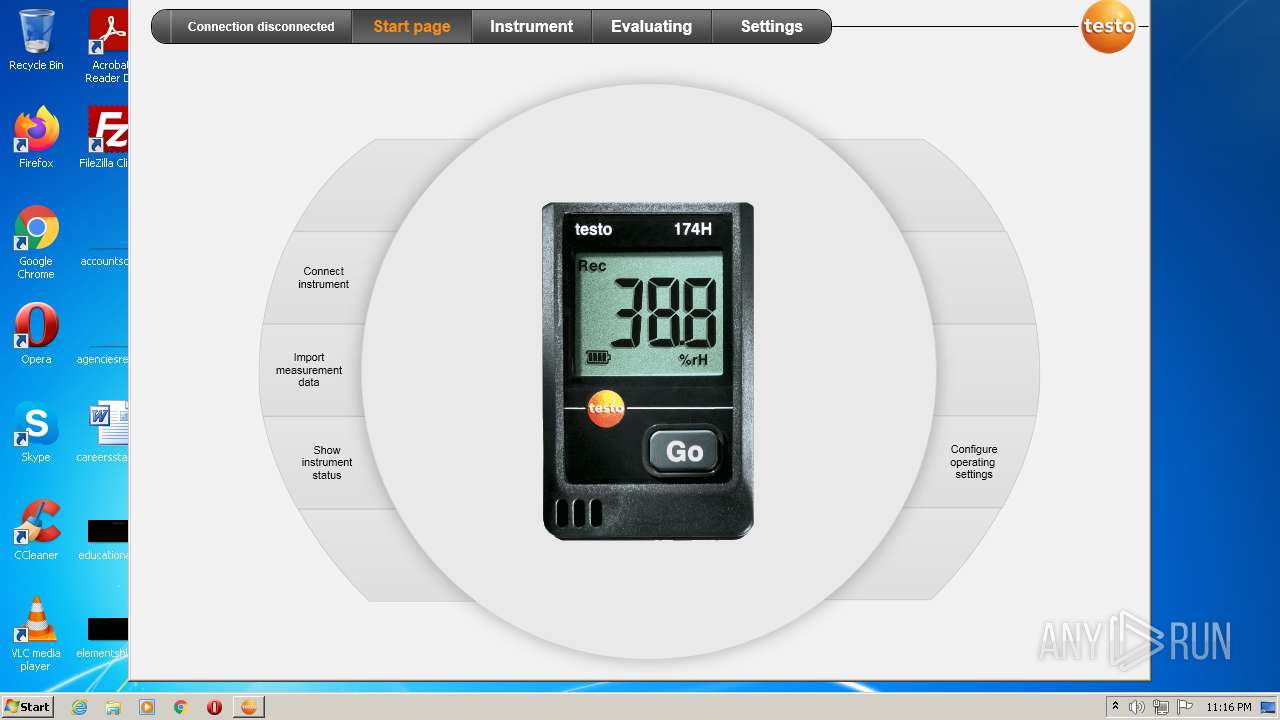
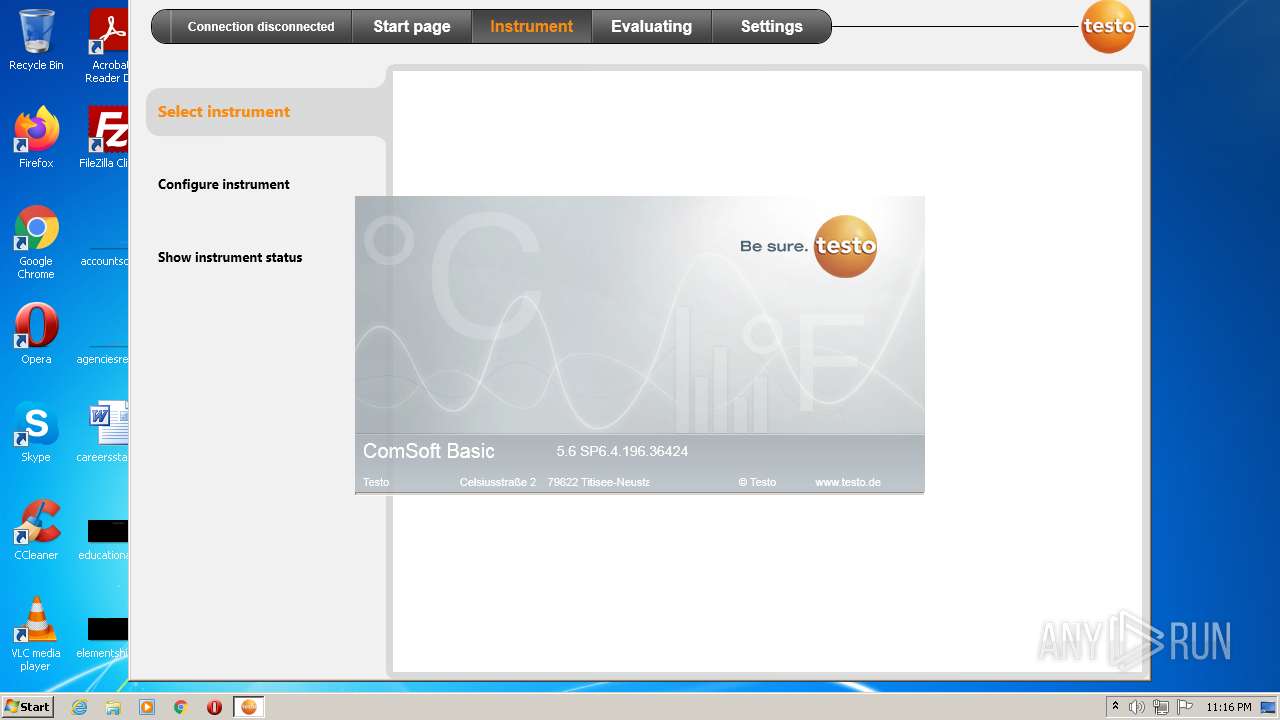
ComSoft.exe | log4net: Configuration update mode [Merge].
|
ComSoft.exe | log4net: Logger [root] Level string is [ALL].
|
ComSoft.exe | log4net: Logger [root] level set to [name="ALL",value=-2147483648].
|
ComSoft.exe | log4net: Loading Appender [rollingFile] type: [log4net.Appender.RollingFileAppender,log4net]
|
ComSoft.exe | log4net: Setting Property [File] to String value [C:\Users\admin\AppData\Roaming\Testo\ComSoftBasic\log.txt]
|
ComSoft.exe | log4net: Setting Property [AppendToFile] to Boolean value [False]
|
ComSoft.exe | log4net: Setting Property [RollingStyle] to RollingMode value [Size]
|
ComSoft.exe | log4net: Setting Property [MaximumFileSize] to String value [5mb]
|
ComSoft.exe | log4net: Setting Property [MaxSizeRollBackups] to Int32 value [5]
|
ComSoft.exe | log4net: Setting Property [StaticLogFileName] to Boolean value [True]
|