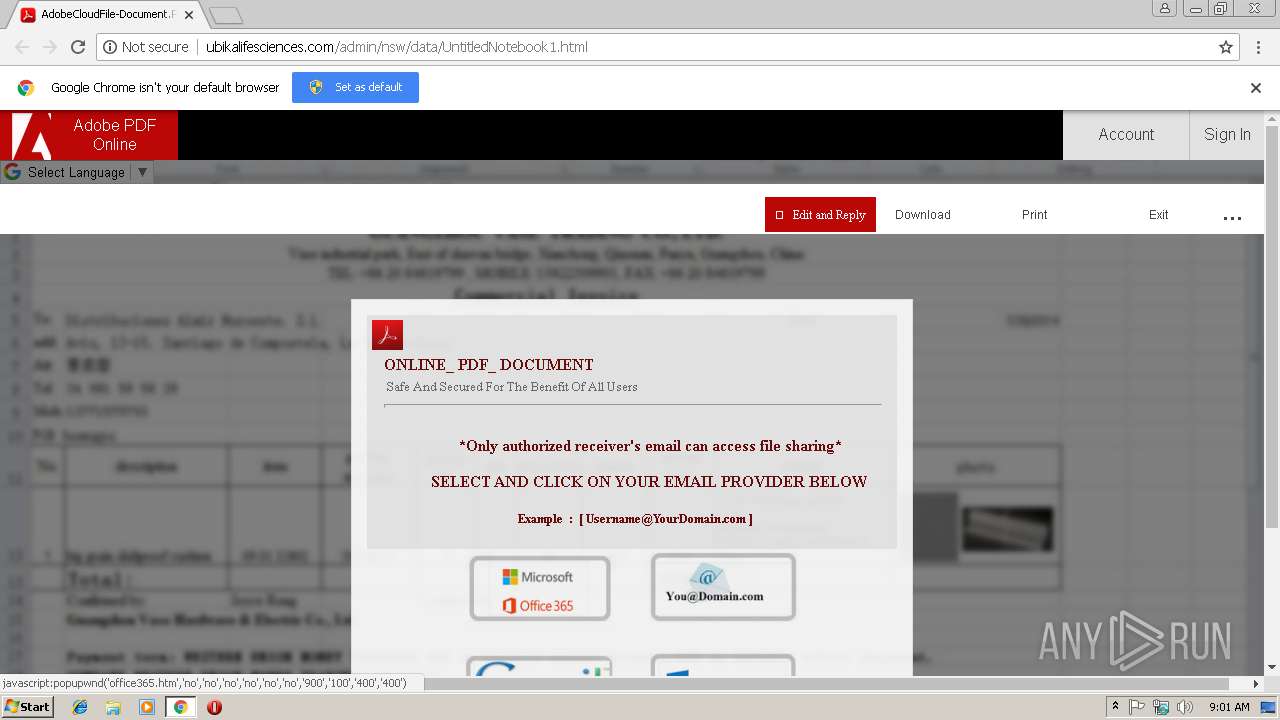
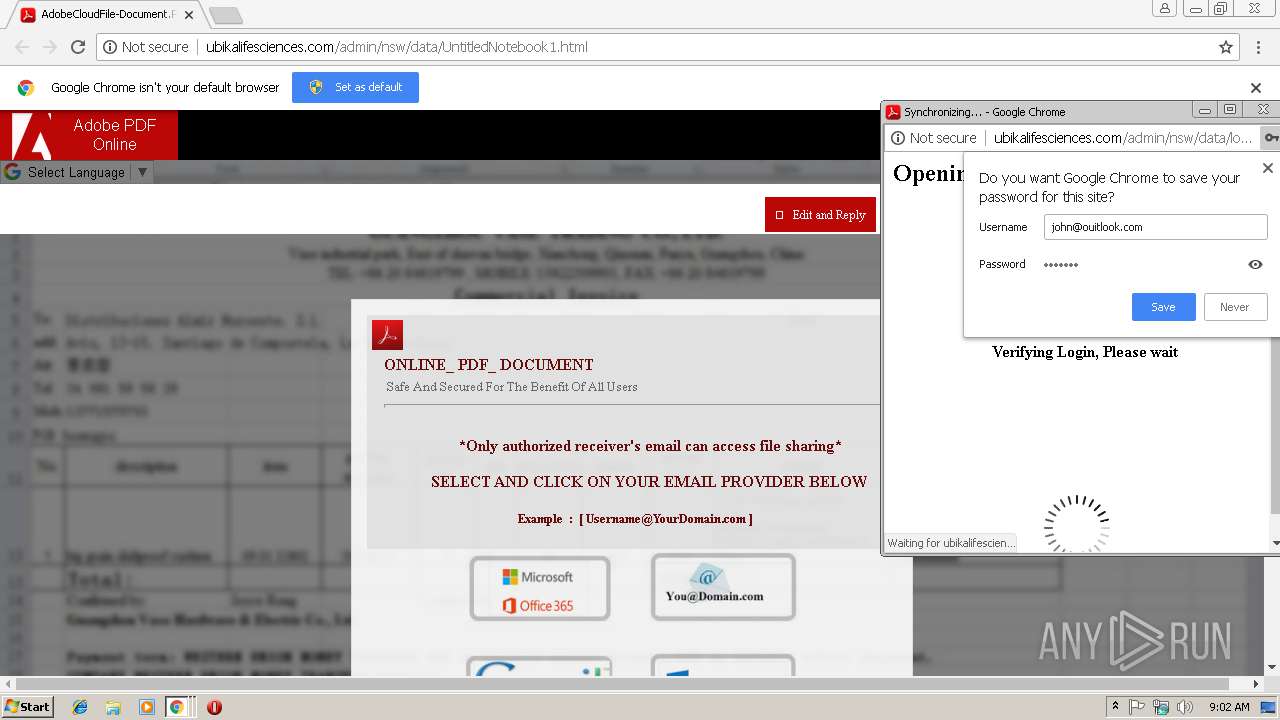
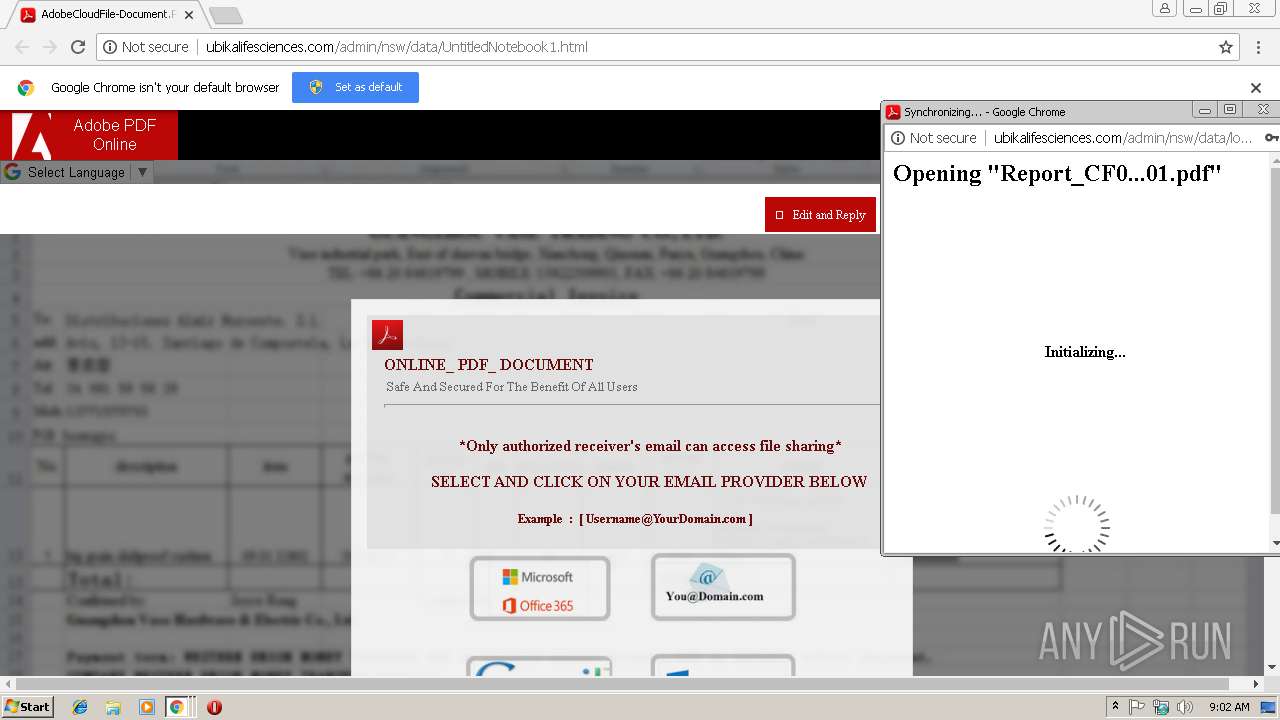
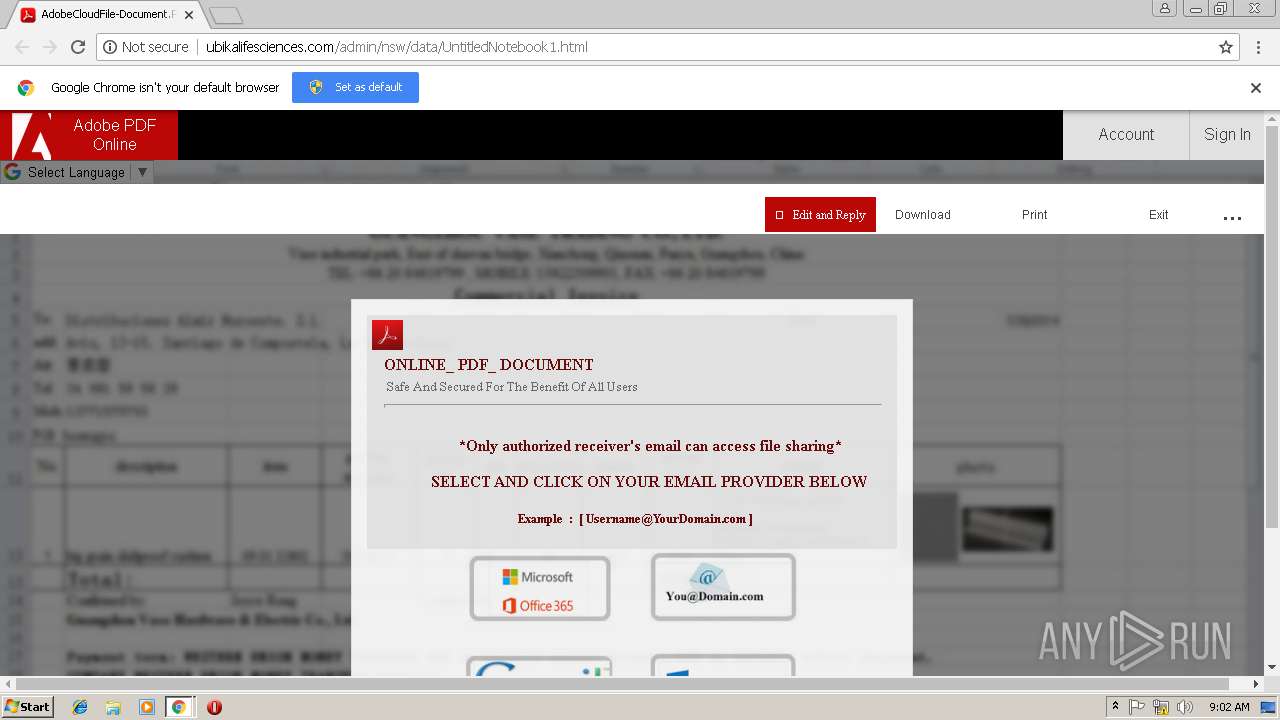
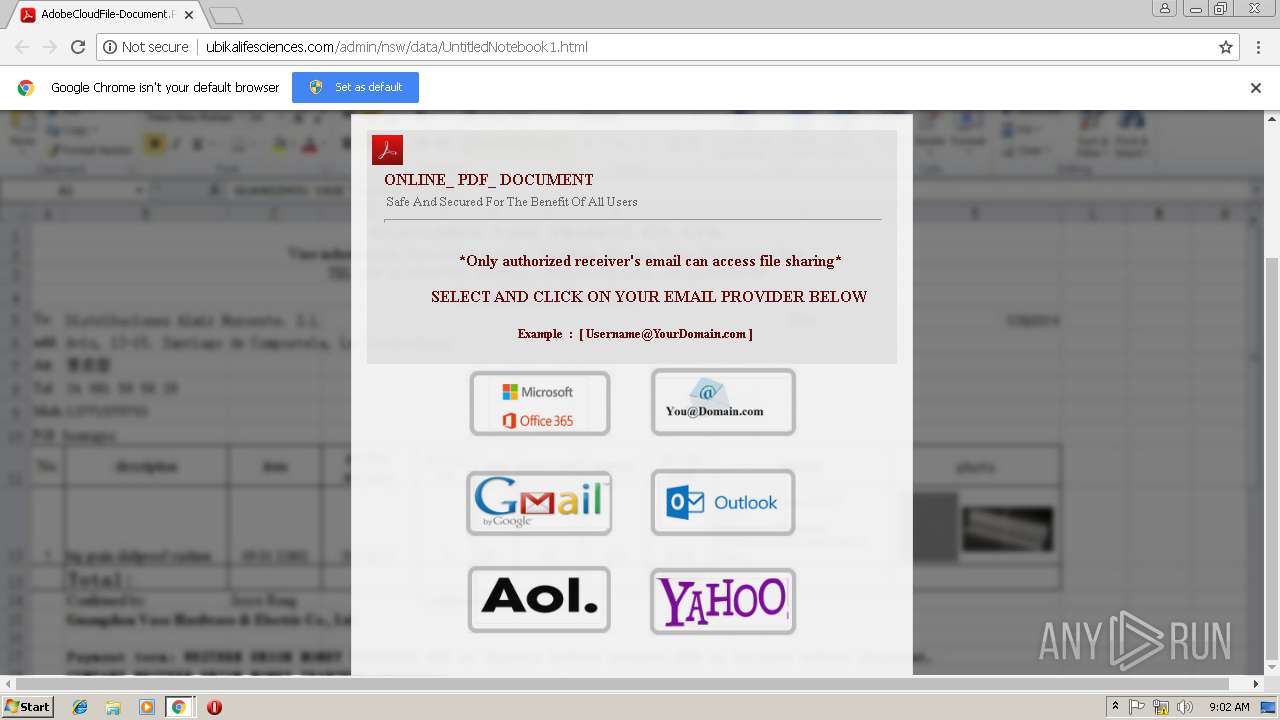
| URL: | http://ubikalifesciences.com/admin/nsw/data/UntitledNotebook1.html |
| Full analysis: | https://app.any.run/tasks/065c66f6-16a6-45d1-aca3-f4acb47a1a18 |
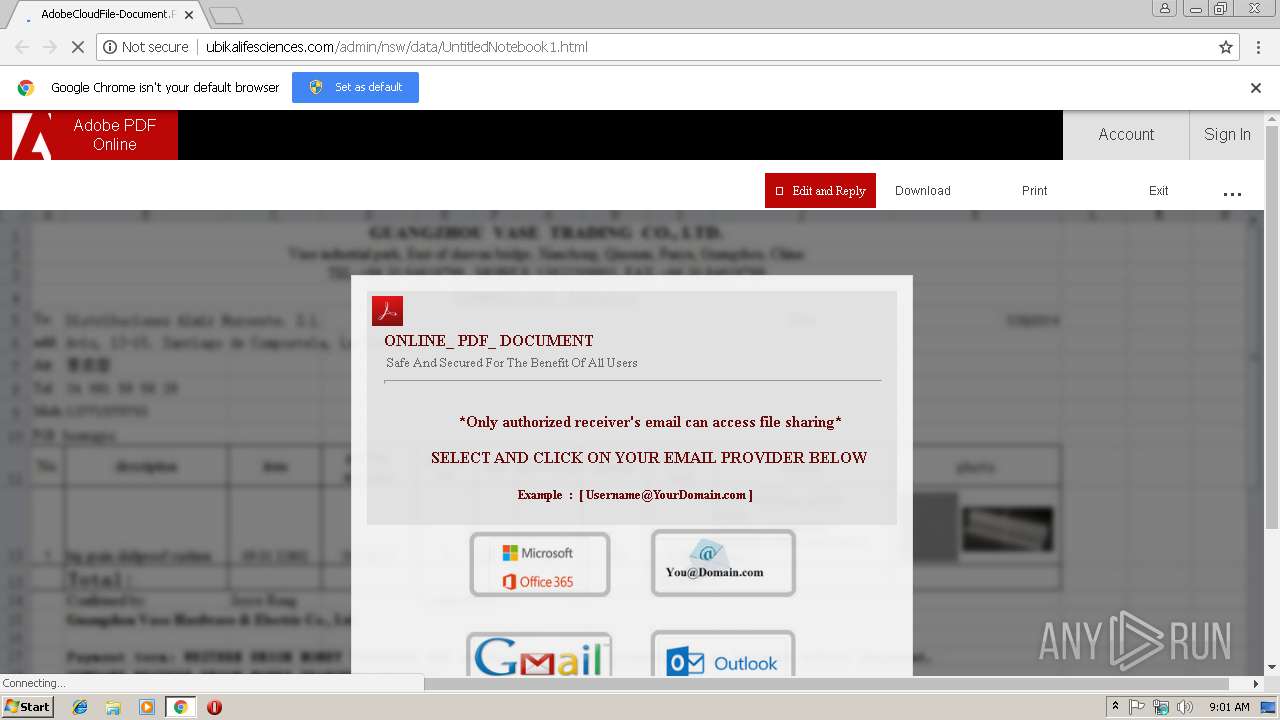
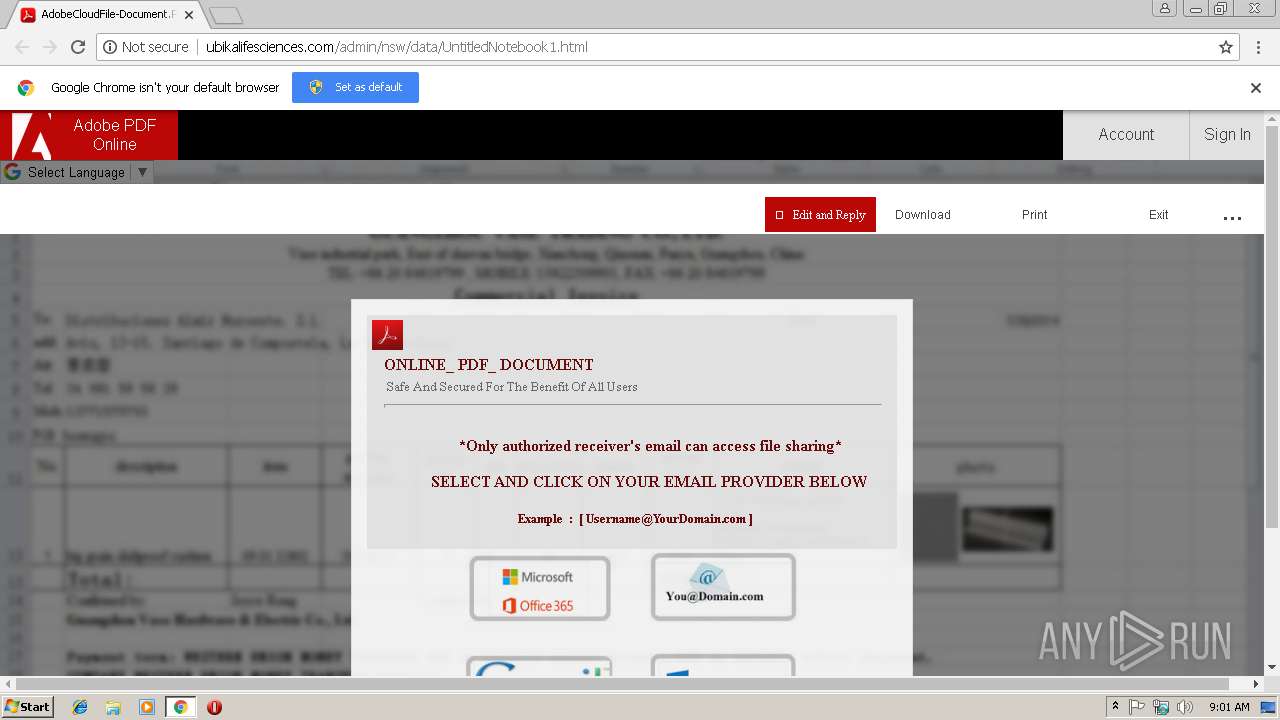
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 09:01:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6A74493D04CBF8350173DA46752CA5A5 |
| SHA1: | 9D047F18E4D7EE2528A6EE96B0C4A3E79211CD9B |
| SHA256: | 8D7E90615187D9E4C35B875237A5AD93E8C315BAABC89FDD16D0DFD0D416F769 |
| SSDEEP: | 3:N1KLclWkyAzfz+AERMlxBfh0:CwhyKfKA4KHu |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3004)
Reads settings of System Certificates
- chrome.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=08F278718AA80D4D9F8649370B092521 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --service-pipe-token=BA9BD930A5890A3E39150447521DBC3E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BA9BD930A5890A3E39150447521DBC3E --renderer-client-id=4 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=F676B002A21A18CB2978BFB7E0AF5BD5 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3008 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://ubikalifesciences.com/admin/nsw/data/UntitledNotebook1.html | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=25030AB64B8DFE5F22A80D2CBD628CF4 --mojo-platform-channel-handle=3660 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --service-pipe-token=7E360A6DF4E09C821D35A4A55A420B7B --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7E360A6DF4E09C821D35A4A55A420B7B --renderer-client-id=3 --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=916,1118884064671851102,3336870485949245273,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3D492186DAECEC8C26707F6713D5BC68 --mojo-platform-channel-handle=2368 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
593
Read events
543
Write events
47
Delete events
3
Modification events
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3004-13192275700788625 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3004-13192275700788625 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
8
Text files
63
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cd1f1ed2-5ebe-481d-9595-8de9f9c3fba1.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\981a97f0-d6eb-4170-900a-58225caee35a.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF199919.TMP | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF199939.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
31
DNS requests
13
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
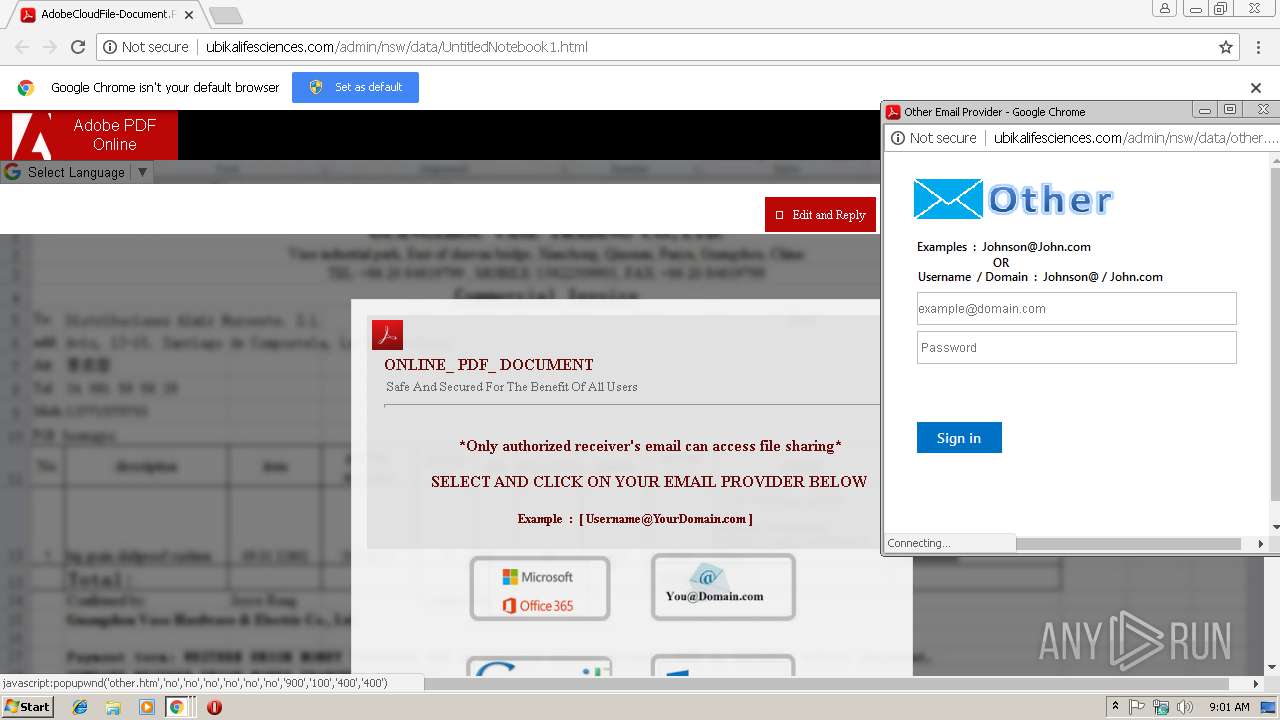
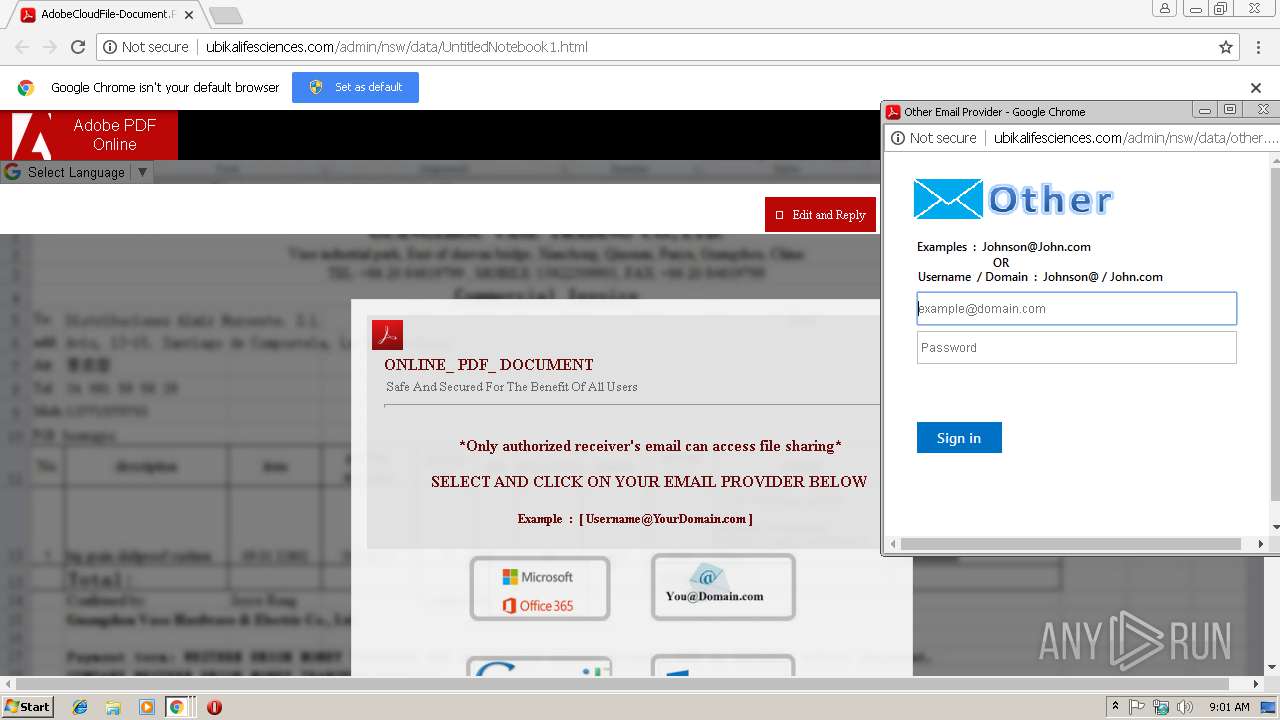
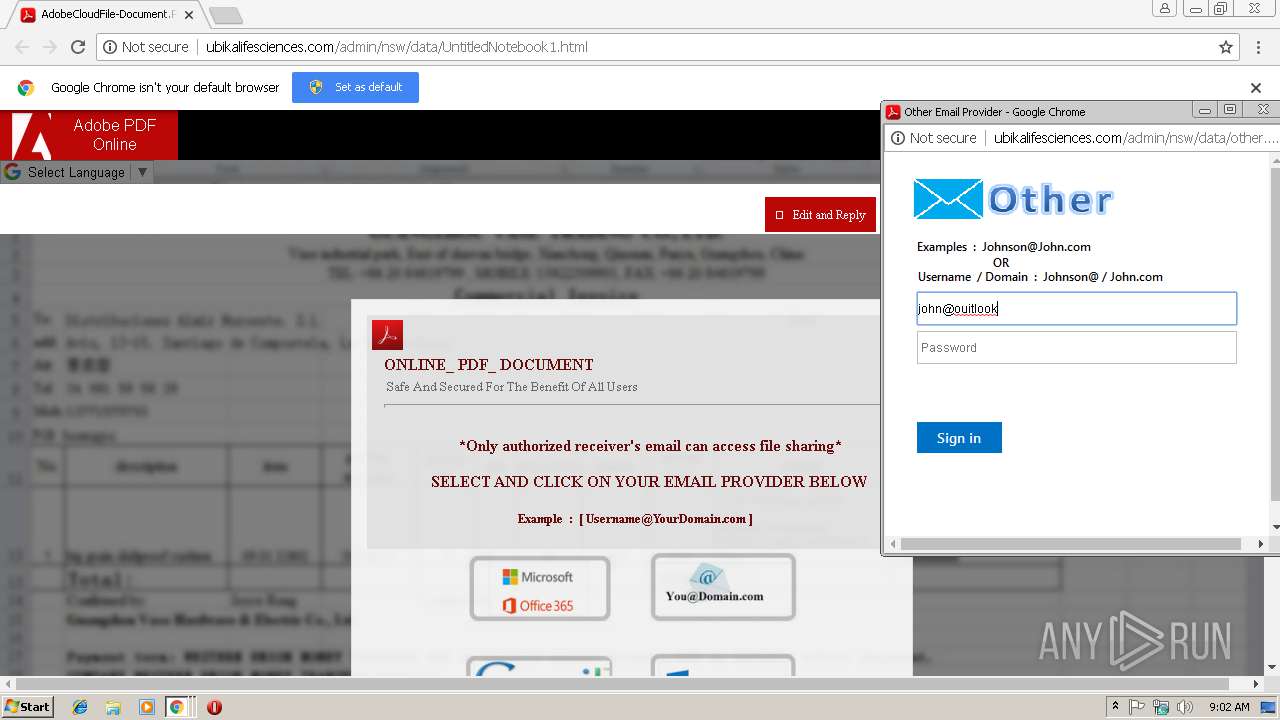
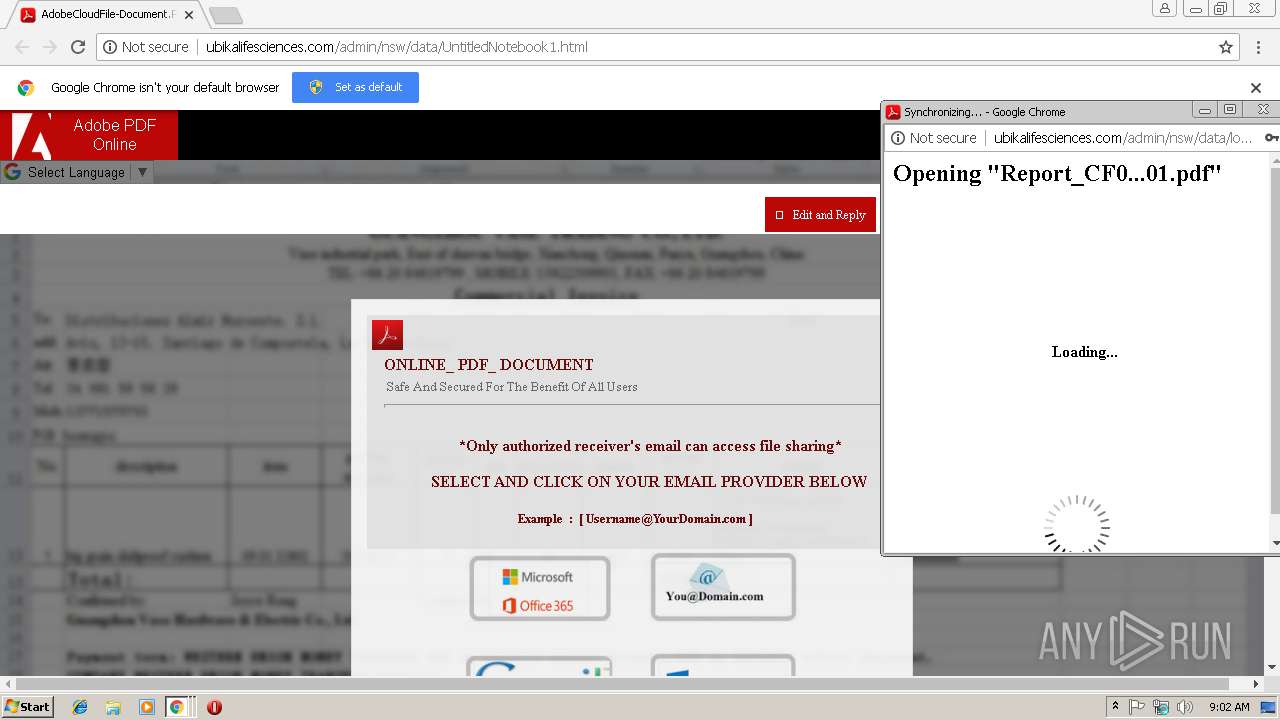
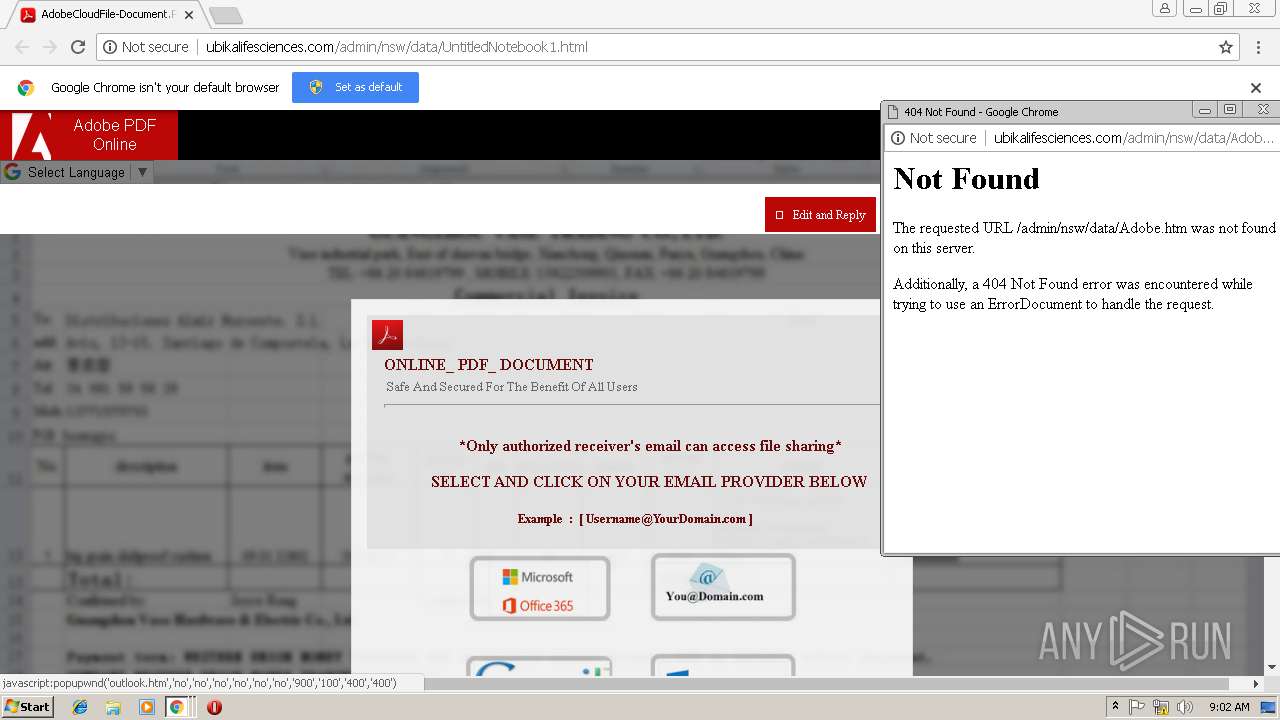
3004 | chrome.exe | GET | 200 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/other.htm | US | html | 1.92 Kb | suspicious |
3004 | chrome.exe | GET | 200 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/office365.htm | US | html | 2.14 Kb | suspicious |
3004 | chrome.exe | GET | 200 | 104.25.156.13:80 | http://icons.iconarchive.com/icons/alecive/flatwoken/128/Apps-Pdf-icon.png | US | image | 7.71 Kb | whitelisted |
3004 | chrome.exe | GET | 200 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/images/Snapshot_2014-07-15_001646.png | US | image | 11.9 Kb | suspicious |
3004 | chrome.exe | GET | 200 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/images/Snapshot_2014-07-15_001647.png | US | image | 10.9 Kb | suspicious |
3004 | chrome.exe | GET | 404 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/fonts/et-line.ttf | US | html | 349 b | suspicious |
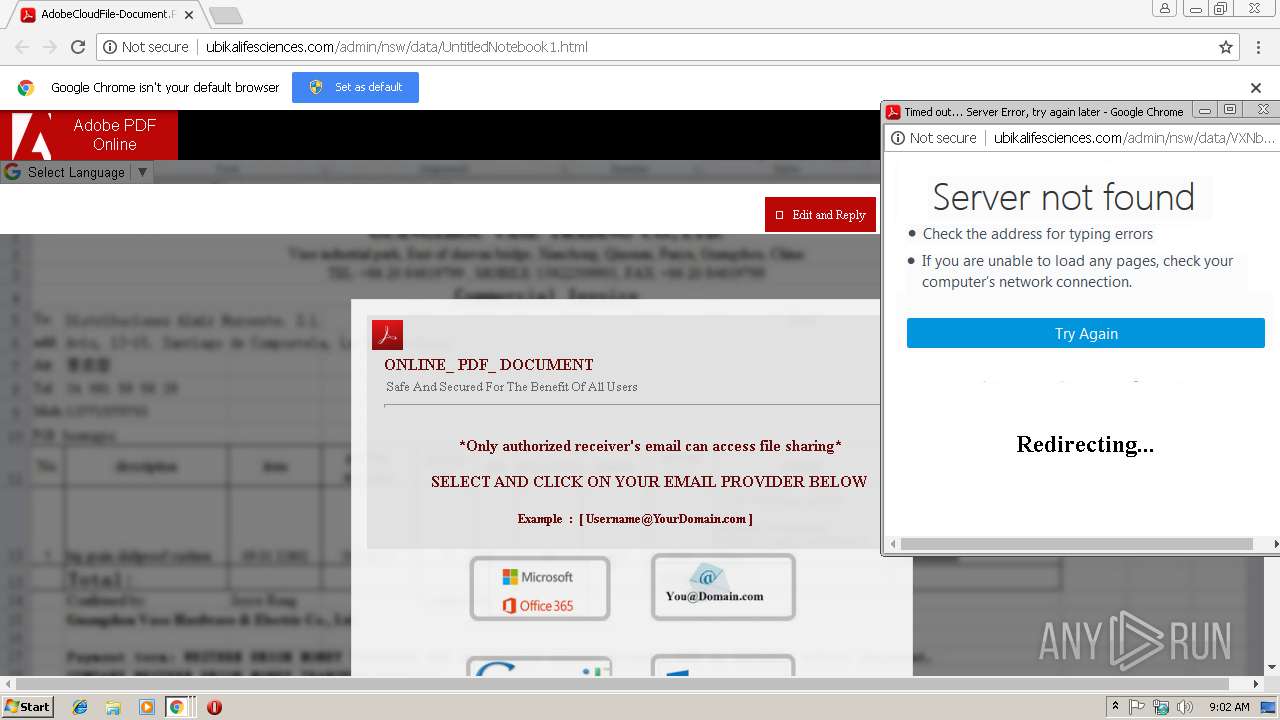
3004 | chrome.exe | POST | 302 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/post.php | US | — | — | suspicious |
3004 | chrome.exe | GET | 200 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/loading.htm | US | html | 3.78 Kb | suspicious |
3004 | chrome.exe | GET | 404 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/:abstract.simplenet.com/point.gif | US | html | 365 b | suspicious |
3004 | chrome.exe | GET | 404 | 96.127.176.189:80 | http://ubikalifesciences.com/admin/nsw/data/abstract.simplenet.com/point2.html | US | html | 366 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | chrome.exe | 96.127.176.189:80 | ubikalifesciences.com | SingleHop, Inc. | US | suspicious |
3004 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.18.174:80 | translate.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.18.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 104.25.156.13:80 | icons.iconarchive.com | Cloudflare Inc | US | shared |
3004 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 184.31.91.81:443 | auth.gfx.ms | Akamai International B.V. | NL | whitelisted |
3004 | chrome.exe | 104.25.157.13:80 | icons.iconarchive.com | Cloudflare Inc | US | shared |
3004 | chrome.exe | 216.58.208.46:443 | clients4.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ubikalifesciences.com |
| suspicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
translate.google.com |
| whitelisted |
static.adobelogin.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
icons.iconarchive.com |
| whitelisted |
auth.gfx.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Phish - Other Credentials Nov 21 2012 |
3 ETPRO signatures available at the full report