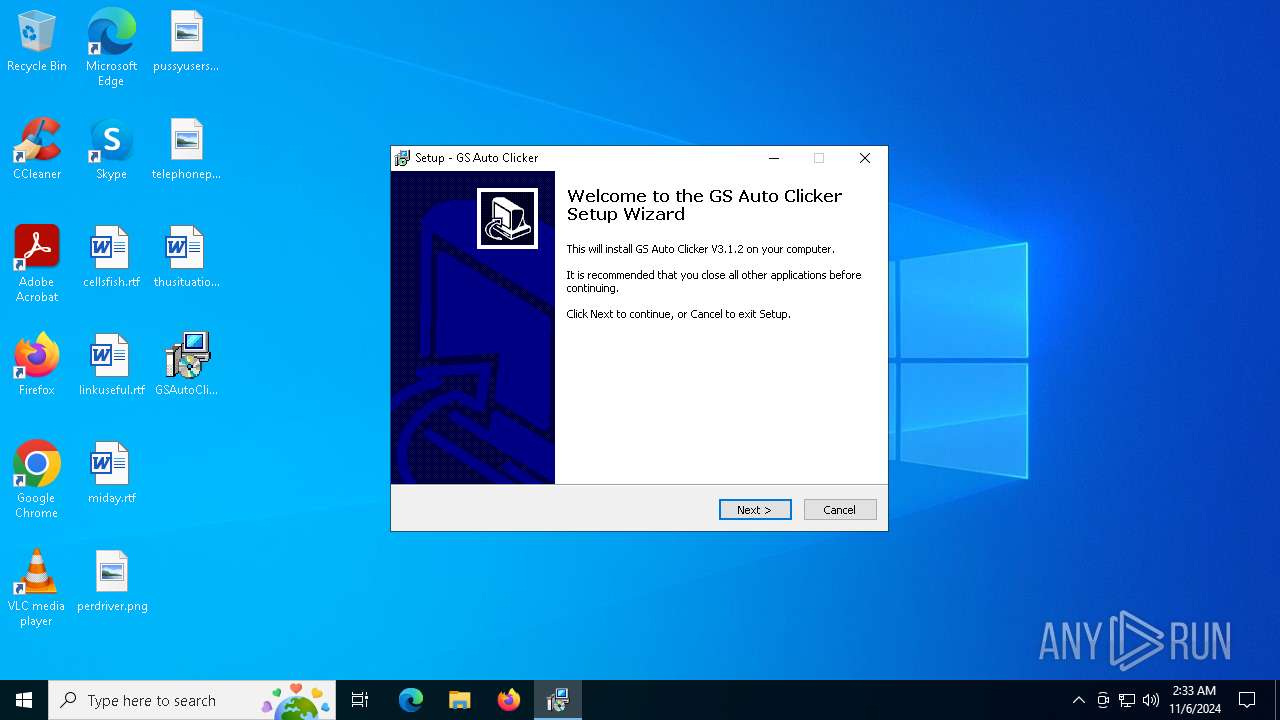
| File name: | GSAutoClicker-Setup.exe |
| Full analysis: | https://app.any.run/tasks/1424406b-d076-40e6-ace6-a0d7d1900597 |
| Verdict: | Malicious activity |
| Analysis date: | November 06, 2024, 02:33:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | CC4A03C642AAC8EF110A97EAE7F7FFDF |
| SHA1: | 36773E076EB396E2A59D26452CD4D2BEE46F4912 |
| SHA256: | 8D6F2B28503680D8705818E417293D9E0027DA62AA9492389217BA84CB8B6497 |
| SSDEEP: | 49152:lStcODmV5pY+DtXfhFVrmSImYUSu45XyXZtB3TocuFGWbkNjL5NW01o5w3vHzz/H:AGH7Y+DtXJTmYYFXykcuFLE/5NW01qwv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- GSAutoClicker-Setup.tmp (PID: 6568)
Executable content was dropped or overwritten
- GSAutoClicker-Setup.exe (PID: 6256)
- GSAutoClicker-Setup.exe (PID: 5100)
- GSAutoClicker-Setup.tmp (PID: 2648)
Reads the Windows owner or organization settings
- GSAutoClicker-Setup.tmp (PID: 2648)
Process drops legitimate windows executable
- GSAutoClicker-Setup.tmp (PID: 2648)
INFO
Checks supported languages
- GSAutoClicker-Setup.exe (PID: 6256)
- GSAutoClicker-Setup.tmp (PID: 6568)
- GSAutoClicker-Setup.exe (PID: 5100)
- GSAutoClicker-Setup.tmp (PID: 2648)
Create files in a temporary directory
- GSAutoClicker-Setup.exe (PID: 6256)
- GSAutoClicker-Setup.tmp (PID: 2648)
- GSAutoClicker-Setup.exe (PID: 5100)
Reads the computer name
- GSAutoClicker-Setup.tmp (PID: 6568)
- GSAutoClicker-Setup.tmp (PID: 2648)
Process checks computer location settings
- GSAutoClicker-Setup.tmp (PID: 6568)
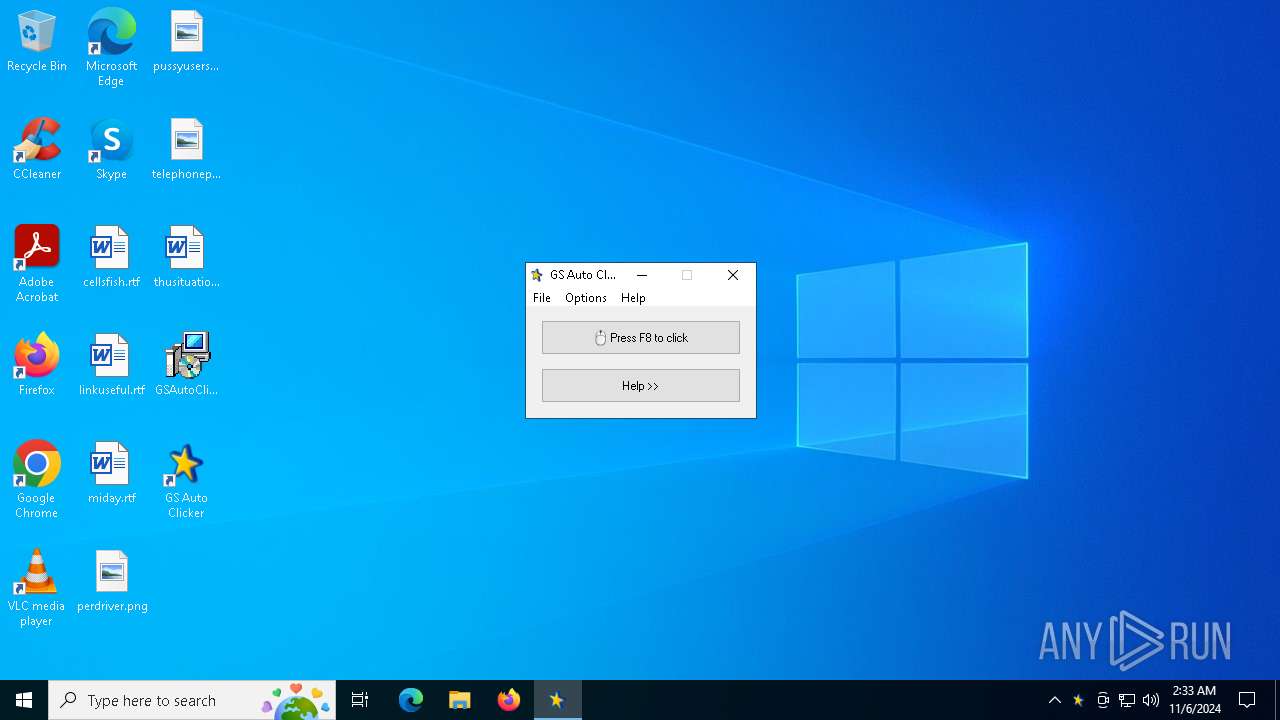
The process uses AutoIt
- GSAutoClicker.exe (PID: 6128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.2.0 |
| ProductVersionNumber: | 3.1.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | goldensoft.org |
| FileDescription: | GS Auto Clicker |
| FileVersion: | GS Auto Clicker V3.1 |
| LegalCopyright: | www.goldensoft.org |
| ProductName: | GS Auto Clicker |
| ProductVersion: | V3.1.2 |
Total processes
130
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2648 | "C:\Users\admin\AppData\Local\Temp\is-OVGNN.tmp\GSAutoClicker-Setup.tmp" /SL5="$50274,638401,54272,C:\Users\admin\Desktop\GSAutoClicker-Setup.exe" /SPAWNWND=$40280 /NOTIFYWND=$8028E | C:\Users\admin\AppData\Local\Temp\is-OVGNN.tmp\GSAutoClicker-Setup.tmp | GSAutoClicker-Setup.exe | ||||||||||||
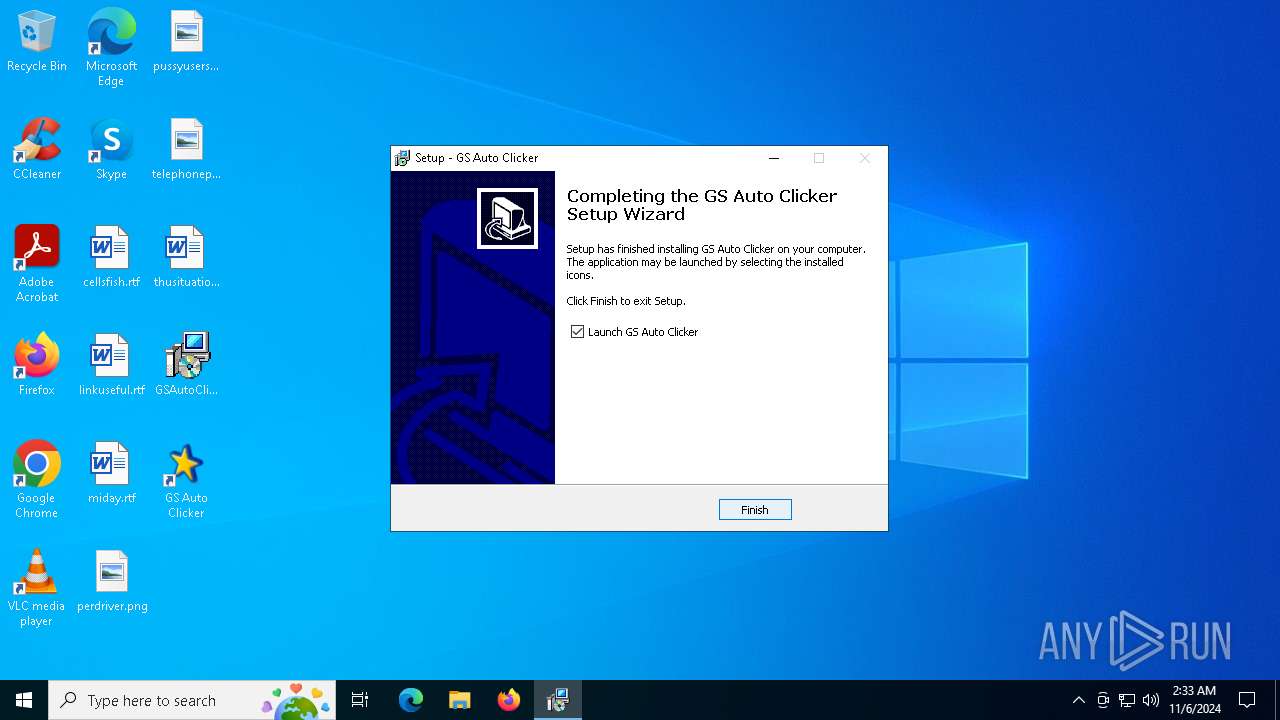
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 5100 | "C:\Users\admin\Desktop\GSAutoClicker-Setup.exe" /SPAWNWND=$40280 /NOTIFYWND=$8028E | C:\Users\admin\Desktop\GSAutoClicker-Setup.exe | GSAutoClicker-Setup.tmp | ||||||||||||
User: admin Company: goldensoft.org Integrity Level: HIGH Description: GS Auto Clicker Exit code: 0 Version: GS Auto Clicker V3.1 Modules
| |||||||||||||||
| 6128 | "C:\Program Files (x86)\GSAutoClicker3\GSAutoClicker.exe" | C:\Program Files (x86)\GSAutoClicker3\GSAutoClicker.exe | GSAutoClicker-Setup.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: GS Auto Clicker Version: 3.1.2 Modules
| |||||||||||||||
| 6256 | "C:\Users\admin\Desktop\GSAutoClicker-Setup.exe" | C:\Users\admin\Desktop\GSAutoClicker-Setup.exe | explorer.exe | ||||||||||||
User: admin Company: goldensoft.org Integrity Level: MEDIUM Description: GS Auto Clicker Exit code: 0 Version: GS Auto Clicker V3.1 Modules
| |||||||||||||||
| 6568 | "C:\Users\admin\AppData\Local\Temp\is-7RNB9.tmp\GSAutoClicker-Setup.tmp" /SL5="$8028E,638401,54272,C:\Users\admin\Desktop\GSAutoClicker-Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-7RNB9.tmp\GSAutoClicker-Setup.tmp | — | GSAutoClicker-Setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
507
Read events
488
Write events
19
Delete events
0
Modification events
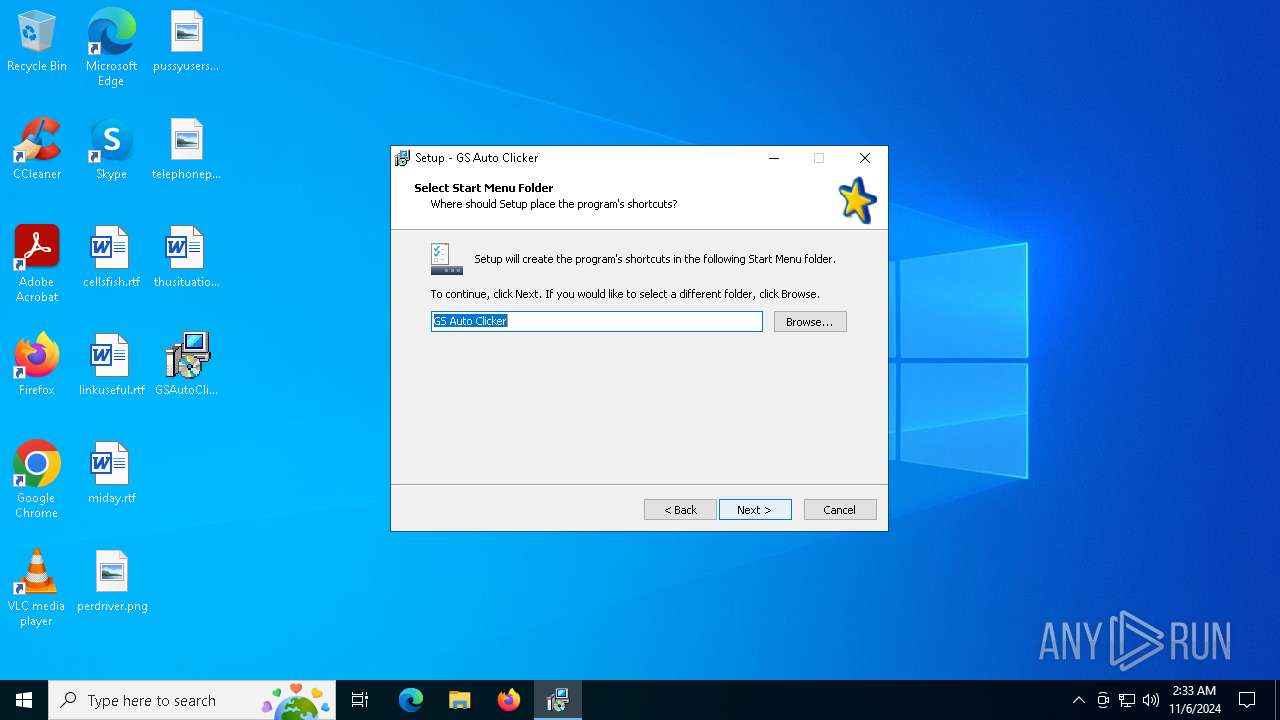
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.4.2 (a) | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\GSAutoClicker3 | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\GSAutoClicker3\ | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: GS Auto Clicker | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | DisplayName |
Value: GS Auto Clicker | |||
| (PID) Process: | (2648) GSAutoClicker-Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\GS Auto Clicker_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\GSAutoClicker3\conf\ext\app_ico.ico | |||
Executable files
13
Suspicious files
4
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6256 | GSAutoClicker-Setup.exe | C:\Users\admin\AppData\Local\Temp\is-7RNB9.tmp\GSAutoClicker-Setup.tmp | executable | |
MD5:C765336F0DCF4EFDCC2101EED67CD30C | SHA256:C5177FDC6031728E10141745CD69EDBC91C92D14411A2DEC6E8E8CAA4F74AB28 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-LG0MS.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-LG0MS.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-LG0MS.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 5100 | GSAutoClicker-Setup.exe | C:\Users\admin\AppData\Local\Temp\is-OVGNN.tmp\GSAutoClicker-Setup.tmp | executable | |
MD5:C765336F0DCF4EFDCC2101EED67CD30C | SHA256:C5177FDC6031728E10141745CD69EDBC91C92D14411A2DEC6E8E8CAA4F74AB28 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Program Files (x86)\GSAutoClicker3\is-UJQ5O.tmp | executable | |
MD5:227D1EF4D93903971AA391DBDBA5BFEA | SHA256:B0B0BBAA5C26C2F3FAEA0355FB85691FA61BA76B7EE5073E35F9026AA086581D | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Program Files (x86)\GSAutoClicker3\unins000.exe | executable | |
MD5:227D1EF4D93903971AA391DBDBA5BFEA | SHA256:B0B0BBAA5C26C2F3FAEA0355FB85691FA61BA76B7EE5073E35F9026AA086581D | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Program Files (x86)\GSAutoClicker3\is-RP86E.tmp | executable | |
MD5:F3F2B98844F393BB0E69A1AAF39B044E | SHA256:707D1BDDA3ECB63A5B595744EBA6D1924D91EB34548689C90F53B11F56614D19 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Users\admin\Documents\AutomaticSolution Software\GSAutoClicker\conf\is-4EVP5.tmp | text | |
MD5:1DF4327BF232884E73BFE564435F810B | SHA256:7FE4E20CC78801D93427EC6927F553CA88453E79D42E10933309428B52AB4910 | |||
| 2648 | GSAutoClicker-Setup.tmp | C:\Program Files (x86)\GSAutoClicker3\GSAutoClicker.exe | executable | |
MD5:F3F2B98844F393BB0E69A1AAF39B044E | SHA256:707D1BDDA3ECB63A5B595744EBA6D1924D91EB34548689C90F53B11F56614D19 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3396 | RUXIMICS.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3396 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 204 | 104.126.37.128:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
— | — | POST | 204 | 104.126.37.128:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3396 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3396 | RUXIMICS.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3396 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |