| URL: | https://inimpese1977.blogspot.co.il/ |
| Full analysis: | https://app.any.run/tasks/3e94ef29-515a-4e59-99aa-f872d21381ed |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 19:45:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7F708A9FE3D62439145EB10D7B31D58E |
| SHA1: | 6714FB25C36A46C909D747268A453E16306BC742 |
| SHA256: | 8D5E3B310A089CAD69C0FECE282A12571AAF91581529B5F53801FD20D0E66994 |
| SSDEEP: | 3:N8RUAFdHrzKK:2iAFdLzR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18131491035734983955 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10344273750713815787 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12270464680219093956 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2615770736535421682 --mojo-platform-channel-handle=2768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6181070585771429362 --mojo-platform-channel-handle=3808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11639123826855875842 --mojo-platform-channel-handle=2708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6919916013890209377 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16609720009588817369 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,17962473826454419857,8045169081680778509,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4941601037005708467 --mojo-platform-channel-handle=2736 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3124 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
167
Read events
132
Write events
32
Delete events
3
Modification events
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13207347926717000 |
Value: 259 | |||
Executable files
0
Suspicious files
20
Text files
158
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c0f0d6d5-eb1b-4ab8-97c4-00b3619edc54.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF100b7b.TMP | text | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF100b9a.TMP | text | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF100bd9.TMP | text | |
MD5:— | SHA256:— | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF100bc9.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
32
DNS requests
20
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
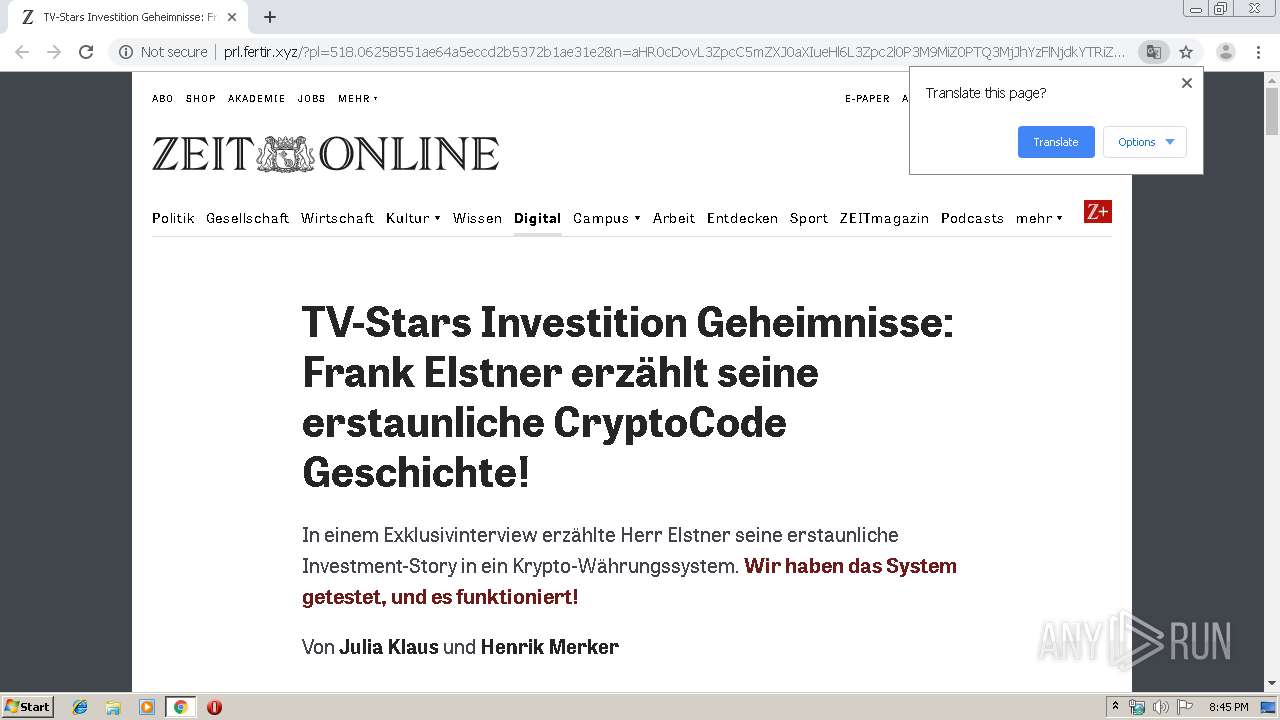
2564 | chrome.exe | GET | 302 | 104.18.32.168:80 | http://vip.fertir.xyz/tracker?offer_id=2560&aff_id=225&u=1187:100&pl=518:100 | US | — | — | suspicious |
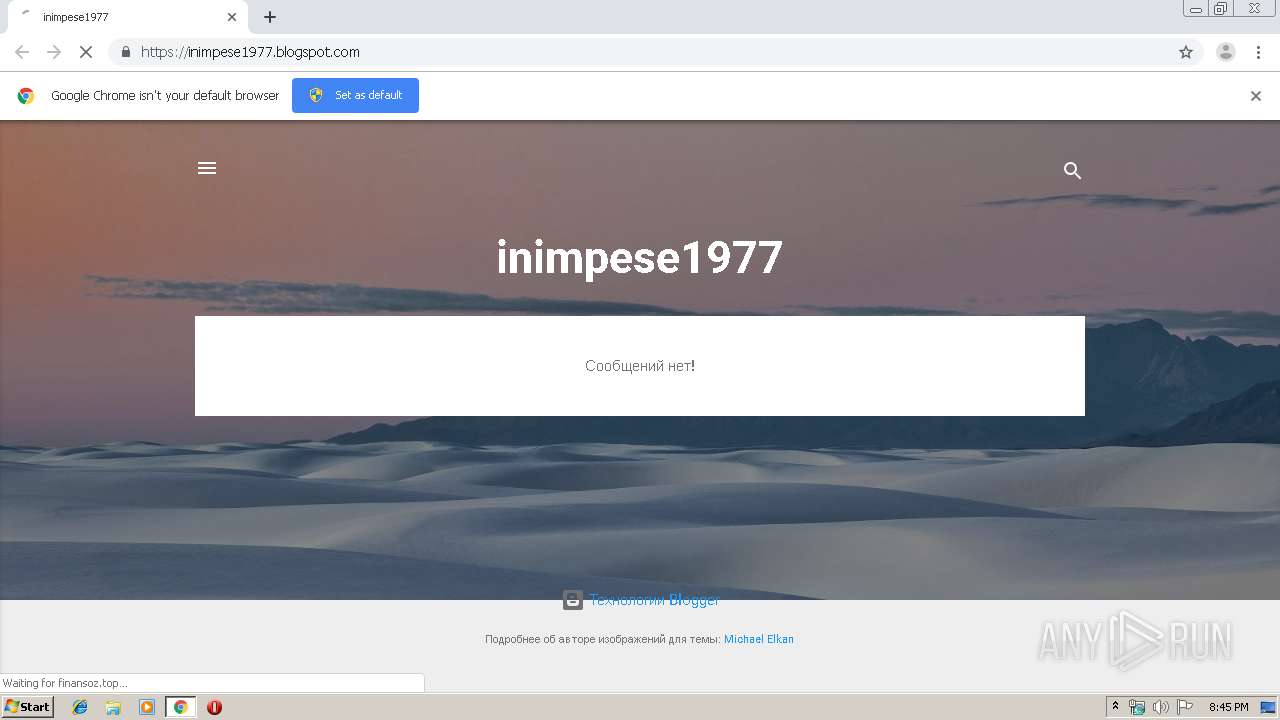
2564 | chrome.exe | GET | — | 130.193.35.172:80 | http://finansoz.top/favicon.ico | RU | — | — | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/?pl=518.06258551ae64a5eccd2b5372b1ae31e2&n=aHR0cDovL3ZpcC5mZXJ0aXIueHl6L3Zpc2l0P3M9MiZ0PTQ3MjJhYzFlNjdkYTRiZTU4NDUwZDUzNWUzNGIzMDg1Jm49YUhSMGNEb3ZMMmRvTG1OeWVYQjBieTFqYjJSbFlYQndMblpwY0M1bVpYSjBhWEl1ZUhsNkx6OXpaWE56YVc5dVBUUTNNakpoWXpGbE5qZGtZVFJpWlRVNE5EVXdaRFV6TldVek5HSXpNRGcxSm1GbVpsOXBaRDB5TWpVbVpuQndQVEU9 | US | html | 42.8 Kb | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/normalize.css | US | text | 859 b | suspicious |
2564 | chrome.exe | GET | 200 | 130.193.35.172:80 | http://finansoz.top/de.html | RU | html | 147 b | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/comments.css | US | text | 3.43 Kb | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/article.css | US | text | 2.38 Kb | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/content.css | US | text | 10.4 Kb | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/base.css | US | text | 8.09 Kb | suspicious |
2564 | chrome.exe | GET | 200 | 104.18.32.168:80 | http://prl.fertir.xyz/prelands/518/css/gallery.css | US | text | 1.36 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | chrome.exe | 172.217.22.33:443 | inimpese1977.blogspot.co.il | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.16.129:443 | inimpese1977.blogspot.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 216.58.207.73:443 | www.blogger.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.18.105:443 | resources.blogblog.com | Google Inc. | US | suspicious |
2564 | chrome.exe | 172.217.22.97:443 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 130.193.35.172:80 | finansoz.top | — | RU | suspicious |
2564 | chrome.exe | 172.217.18.97:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 130.193.35.172:80 | finansoz.top | — | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
inimpese1977.blogspot.co.il |
| whitelisted |
accounts.google.com |
| shared |
inimpese1977.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
www.blogger.com |
| shared |
themes.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2564 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2564 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |