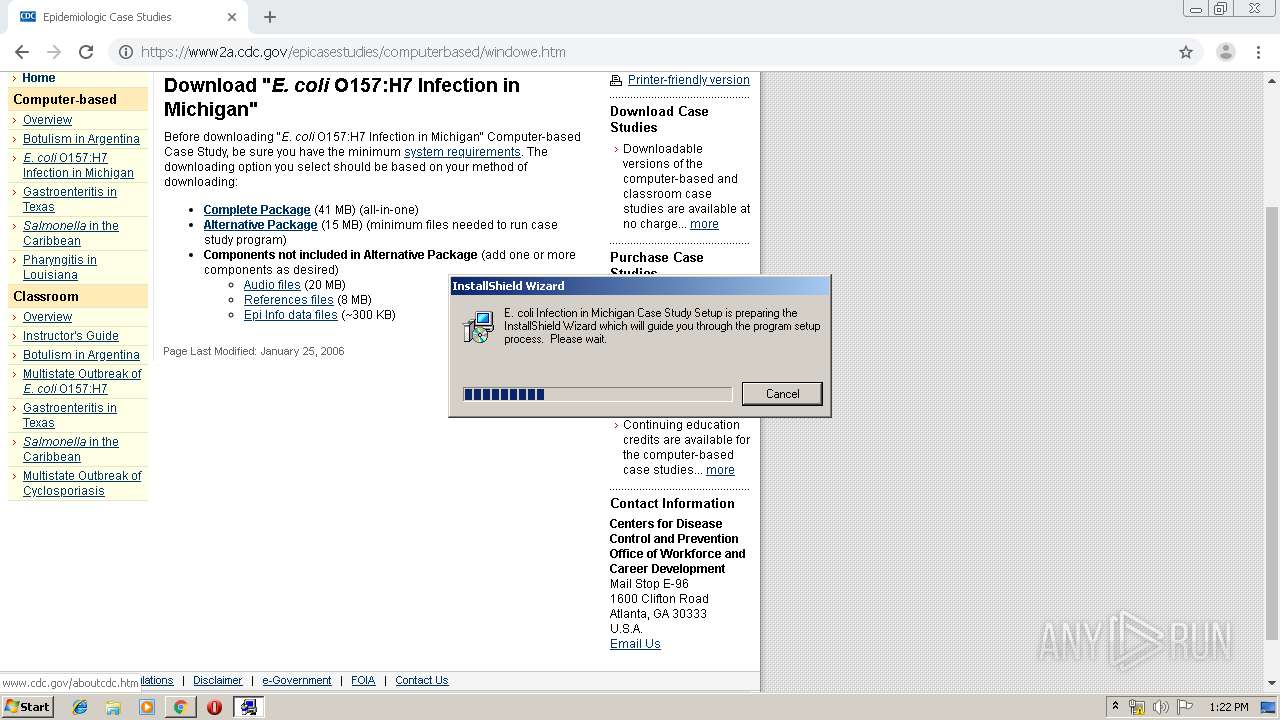
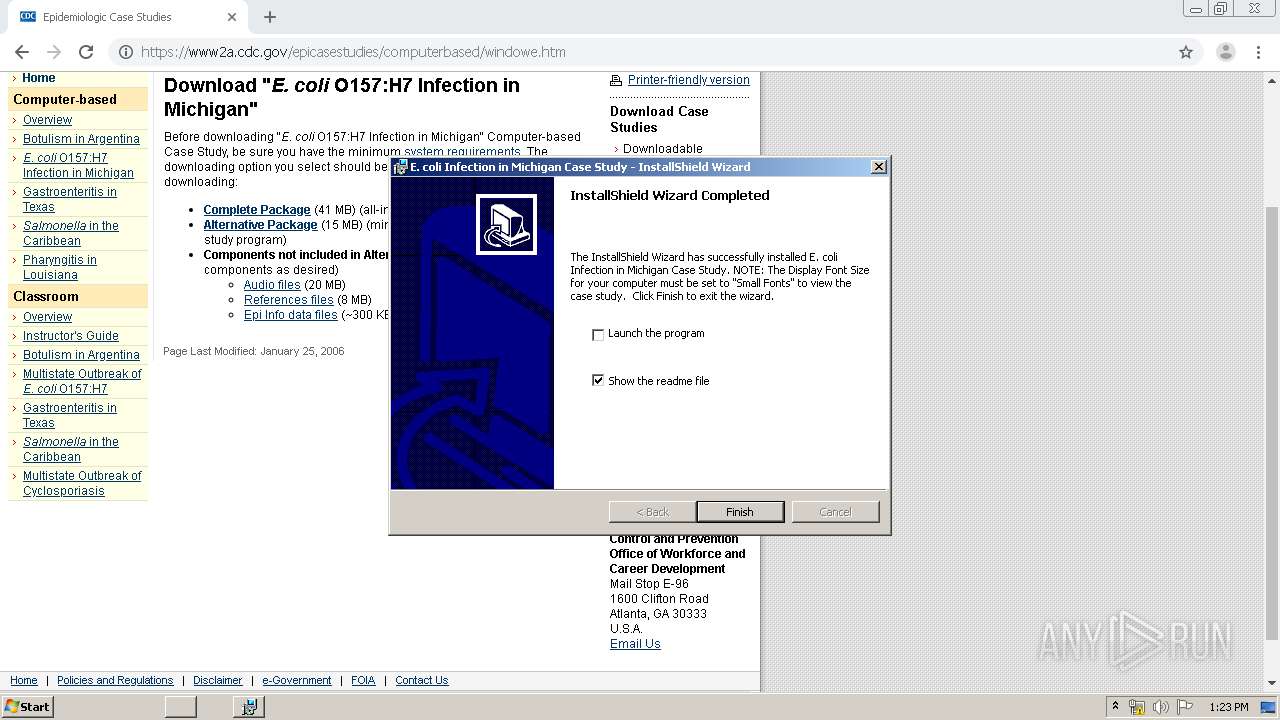
| URL: | https://www2a.cdc.gov/epicasestudies/computerbased/ecoli.htm |
| Full analysis: | https://app.any.run/tasks/44421ab5-f79f-4ec3-b20a-7e92c2631ca9 |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2019, 12:19:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5E5F1EE980140413DF4EFEDAB306389D |
| SHA1: | 426761626FB19CC7708065A089E61B47BA2EAE65 |
| SHA256: | 8D5D333BC6989C5CC32D12E8D66AB0C40FDBA032C15BCE2F3CEFB5C89BBA7584 |
| SSDEEP: | 3:N8DSXFXrWdKc4K5RIn:2OXFXIgK5un |
MALICIOUS
Application was dropped or rewritten from another process
- EcoliComp.exe (PID: 3768)
- EcoliComp.exe (PID: 796)
- Ecoli_Login.exe (PID: 3784)
Loads dropped or rewritten executable
- Ecoli_Login.exe (PID: 3784)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3836)
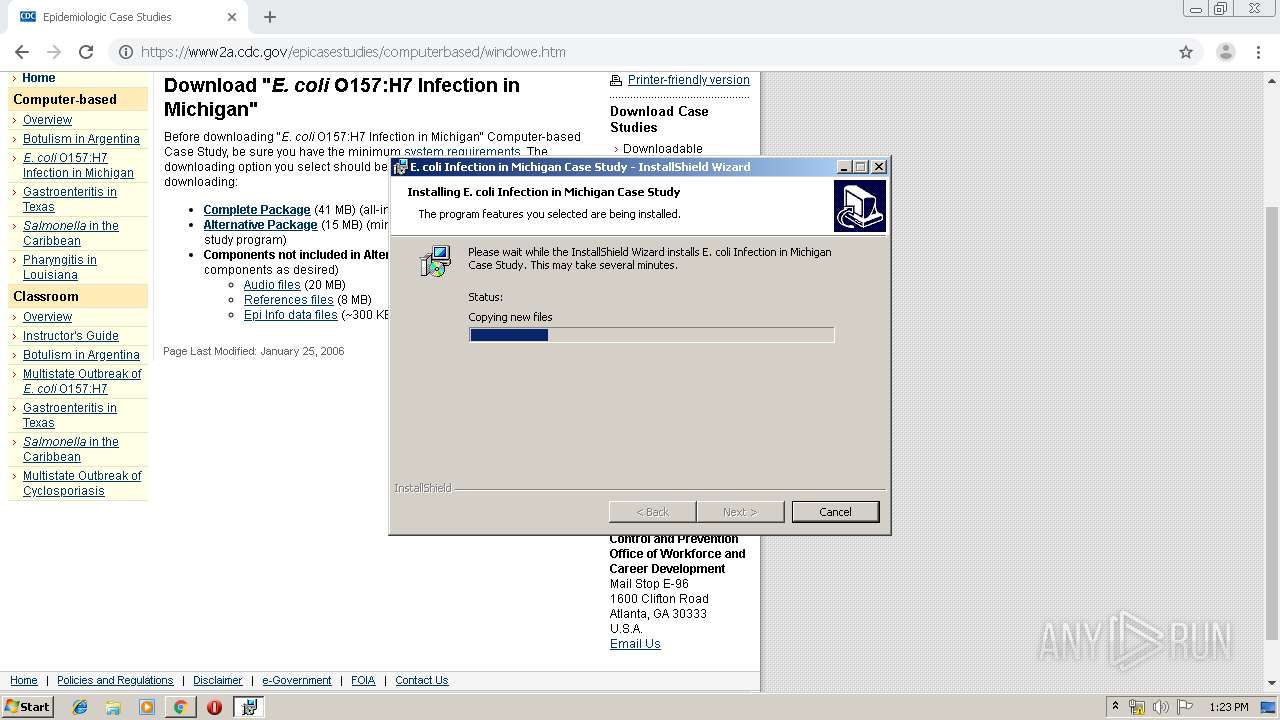
Executable content was dropped or overwritten
- chrome.exe (PID: 3836)
- msiexec.exe (PID: 1772)
- MSIEXEC.EXE (PID: 3228)
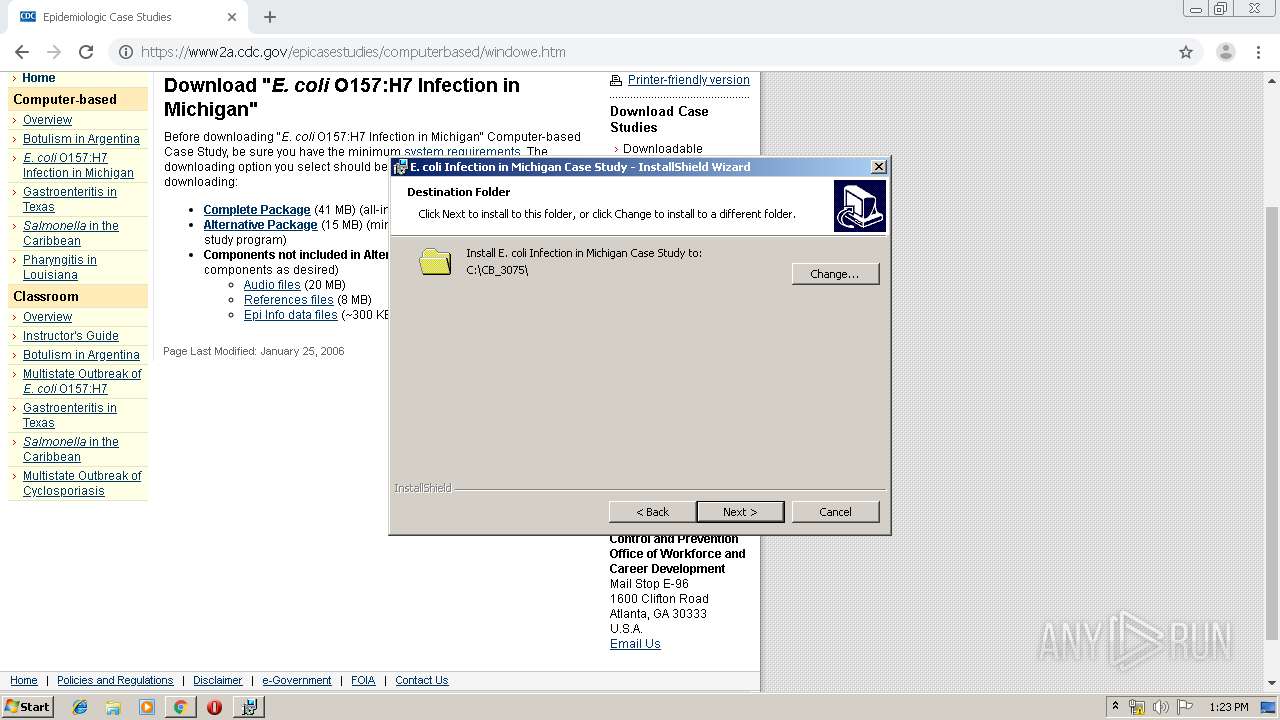
Starts Microsoft Installer
- EcoliComp.exe (PID: 796)
Executed as Windows Service
- vssvc.exe (PID: 2516)
Executed via COM
- DrvInst.exe (PID: 3968)
Creates files in the user directory
- Ecoli_Login.exe (PID: 3784)
- msiexec.exe (PID: 1772)
INFO
Application launched itself
- chrome.exe (PID: 3836)
- msiexec.exe (PID: 1772)
Reads Internet Cache Settings
- chrome.exe (PID: 3836)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2516)
Changes settings of System certificates
- DrvInst.exe (PID: 3968)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3968)
Creates a software uninstall entry
- msiexec.exe (PID: 1772)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 1772)
Searches for installed software
- msiexec.exe (PID: 1772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
30
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Users\admin\Downloads\EcoliComp.exe" | C:\Users\admin\Downloads\EcoliComp.exe | chrome.exe | ||||||||||||
User: admin Company: Installshield Software Corporation Integrity Level: HIGH Description: Setup Launcher Exit code: 0 Version: 3.03.099 Modules
| |||||||||||||||
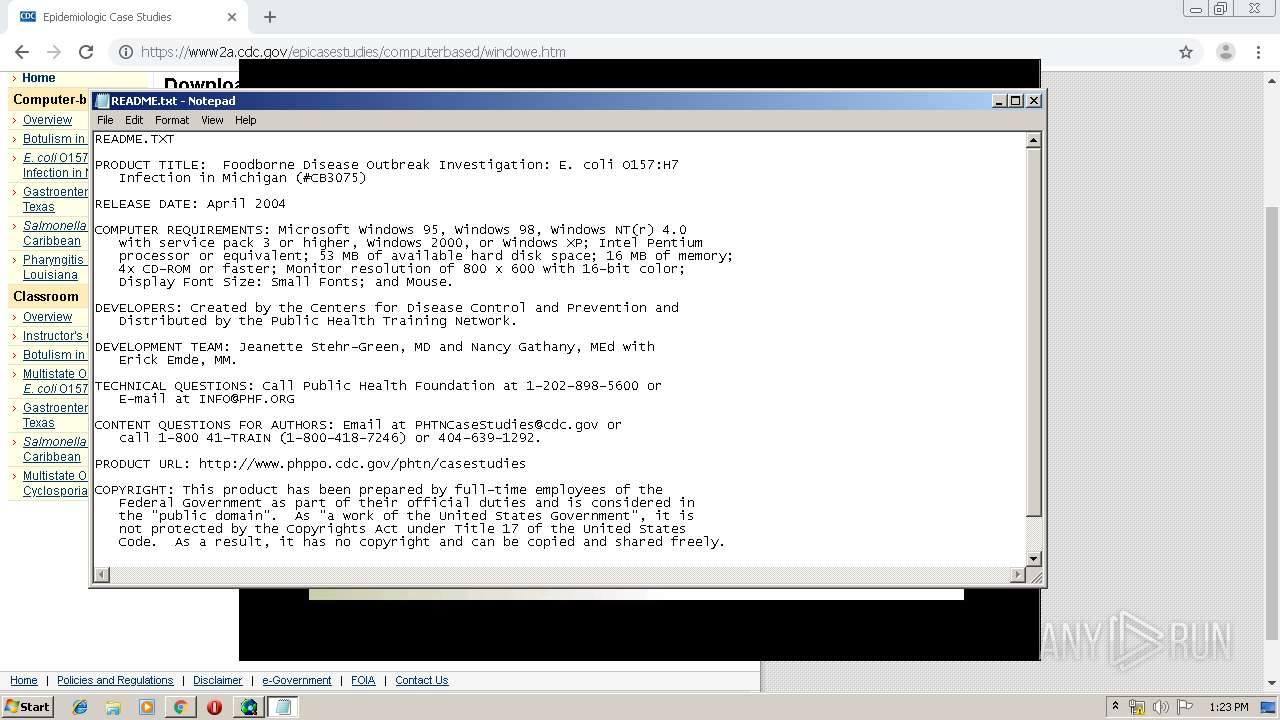
| 1344 | "C:\Windows\system32\NOTEPAD.EXE" C:\CB_3075\README.txt | C:\Windows\system32\NOTEPAD.EXE | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14269351852883129997 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10316832251529786705 --mojo-platform-channel-handle=3668 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2516 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13490406237921846380 --mojo-platform-channel-handle=3580 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2812 | C:\Windows\system32\MsiExec.exe -Embedding 0E9127FCC22420B2BA173C1C03D096D0 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,2808521579063662300,2381437257828957443,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9576330214078448891 --mojo-platform-channel-handle=3832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 790
Read events
1 324
Write events
449
Delete events
17
Modification events
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3836-13211641203951500 |
Value: 259 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3836) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
43
Suspicious files
82
Text files
395
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eb382ad9-16ee-4b51-8606-abf8144da374.tmp | — | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169b89.TMP | text | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169b89.TMP | text | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169bb8.TMP | text | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3308 | chrome.exe | C:\Users\admin\AppData\Local\Temp\CabA08A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
3308 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3308 | chrome.exe | GET | 200 | 173.194.19.153:80 | http://r3---sn-5go7yn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.103.130.130&mm=28&mn=sn-5go7yn7l&ms=nvh&mt=1567167520&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | chrome.exe | 104.109.79.19:80 | www.cdc.gov | Akamai International B.V. | NL | whitelisted |
3308 | chrome.exe | 198.246.102.32:443 | www2a.cdc.gov | U.S. Center For Disease Control and Prevention | US | unknown |
3308 | chrome.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3308 | chrome.exe | 104.109.79.19:443 | www.cdc.gov | Akamai International B.V. | NL | whitelisted |
3308 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 66.117.29.228:443 | cdc.112.2o7.net | Adobe Systems Inc. | US | unknown |
3308 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 173.194.19.153:80 | r3---sn-5go7yn7l.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www2a.cdc.gov |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
www.cdc.gov |
| whitelisted |
cdc.112.2o7.net |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |