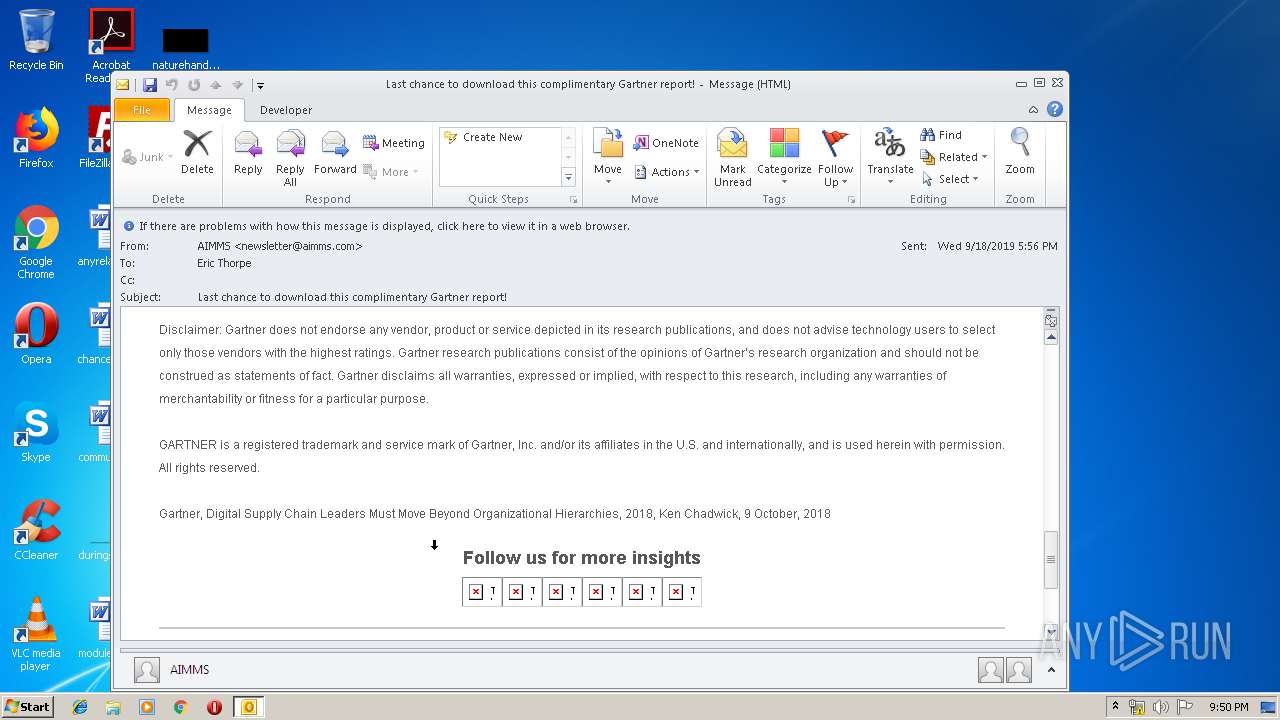
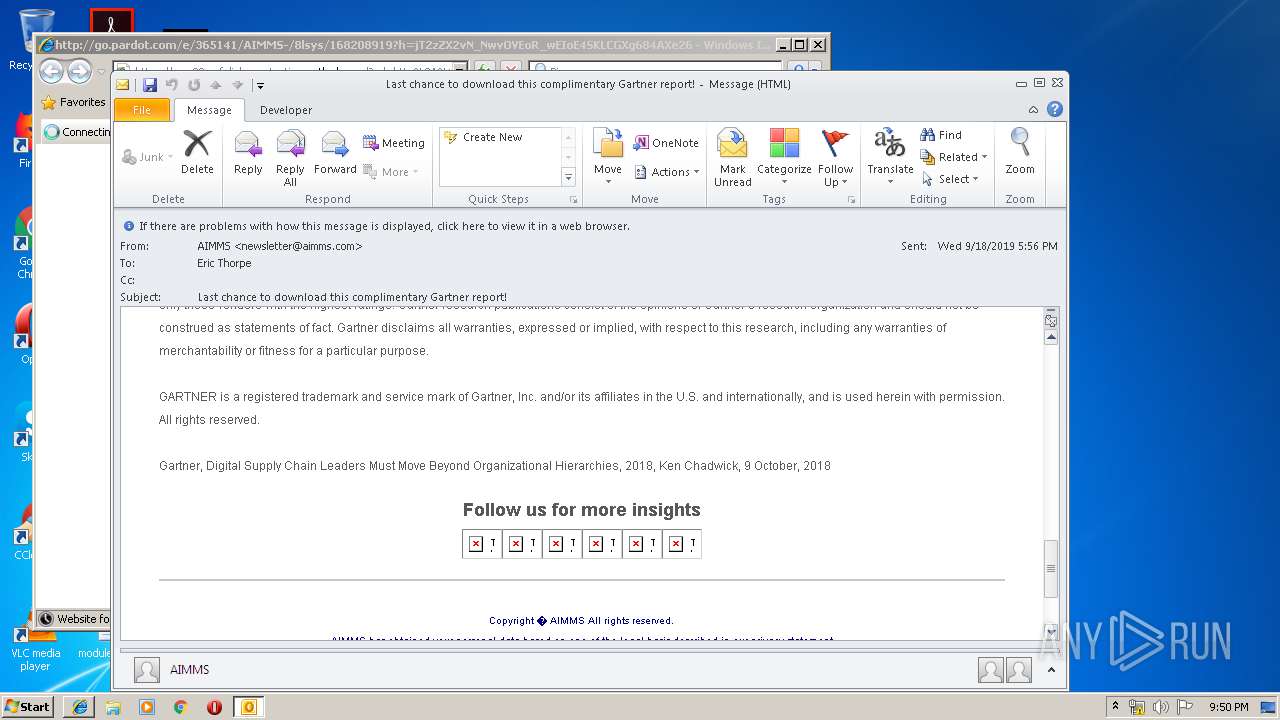
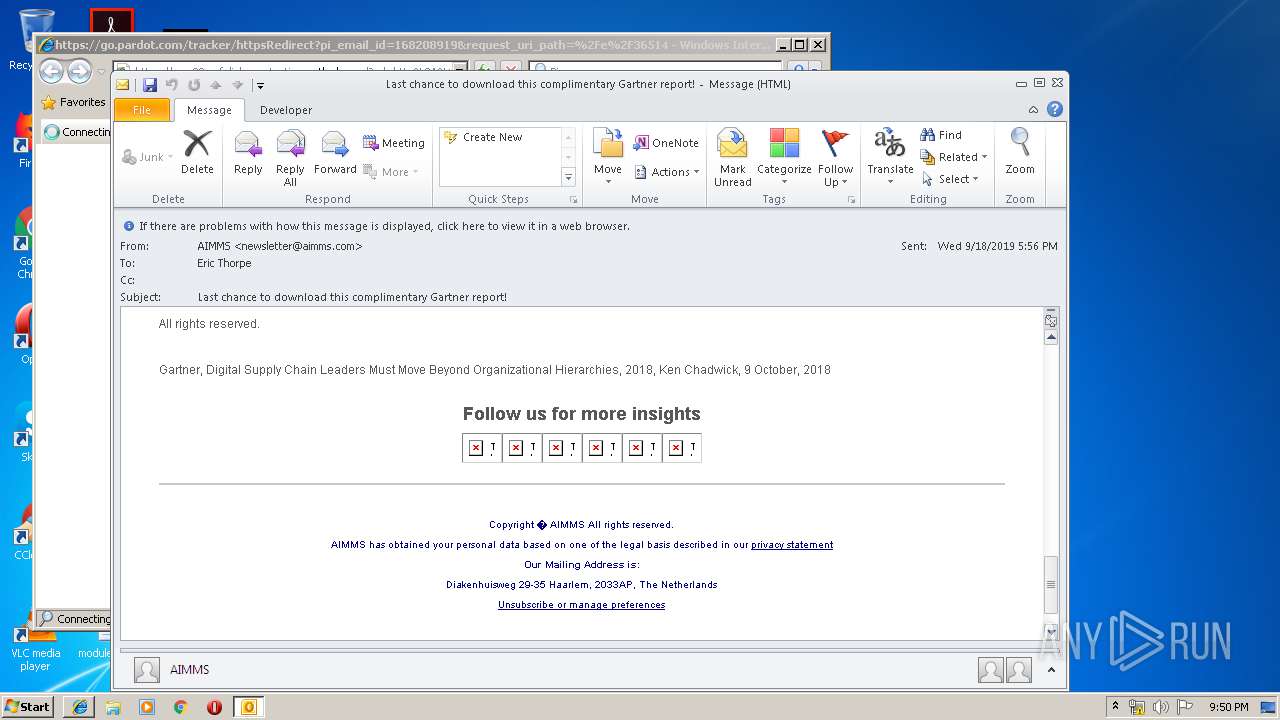
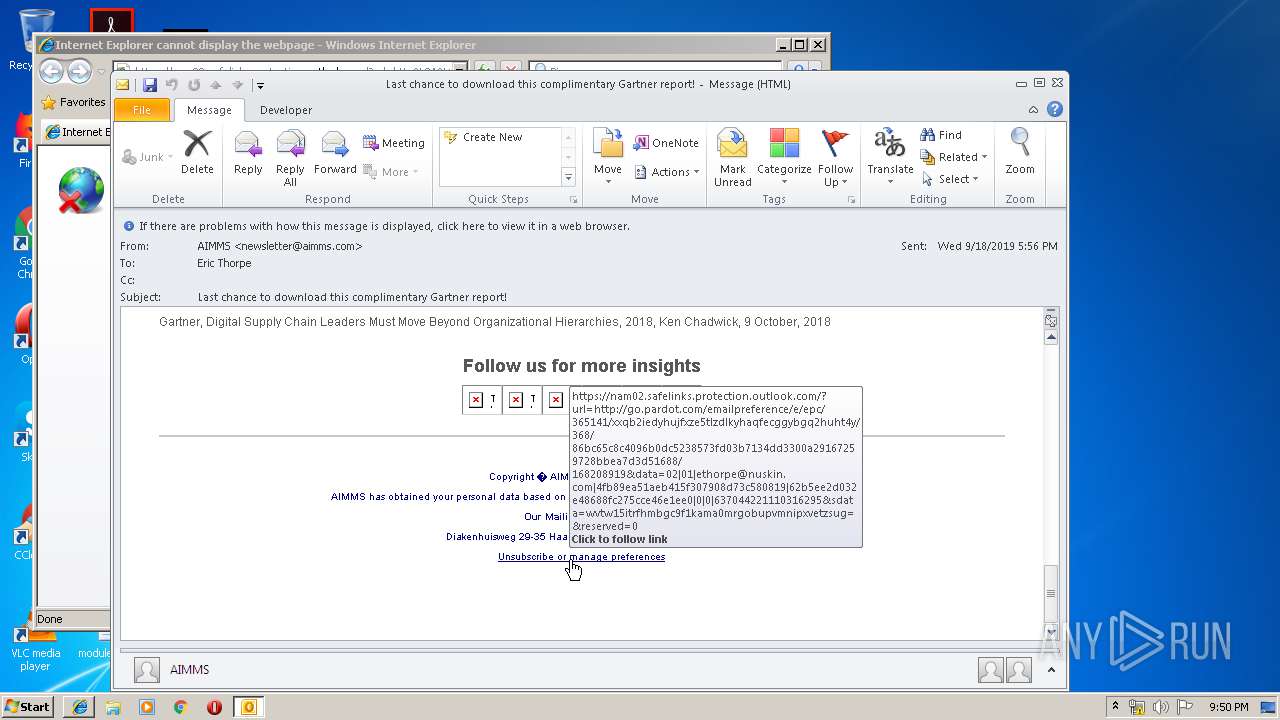
| File name: | Last chance to download this complimentary Gartner report!.eml |
| Full analysis: | https://app.any.run/tasks/faa64903-1928-4230-bec9-647b344bd8c0 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 20:48:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | A9A37C968136565D317B6F0ABC3B314D |
| SHA1: | 60B003113E407A597174FA996B31853FA5AD7866 |
| SHA256: | 8D4FB2D0923D712FB79F1D713A67AB78D0072DA26D3DF8804132BD2727C8D5B3 |
| SSDEEP: | 768:u4btVDOiL2VRYZDZSSSIKZi/HFuhPLKB2PW8xqzneJE2ls:37DfUYZDQSiWEFRs |
MALICIOUS
No malicious indicators.SUSPICIOUS
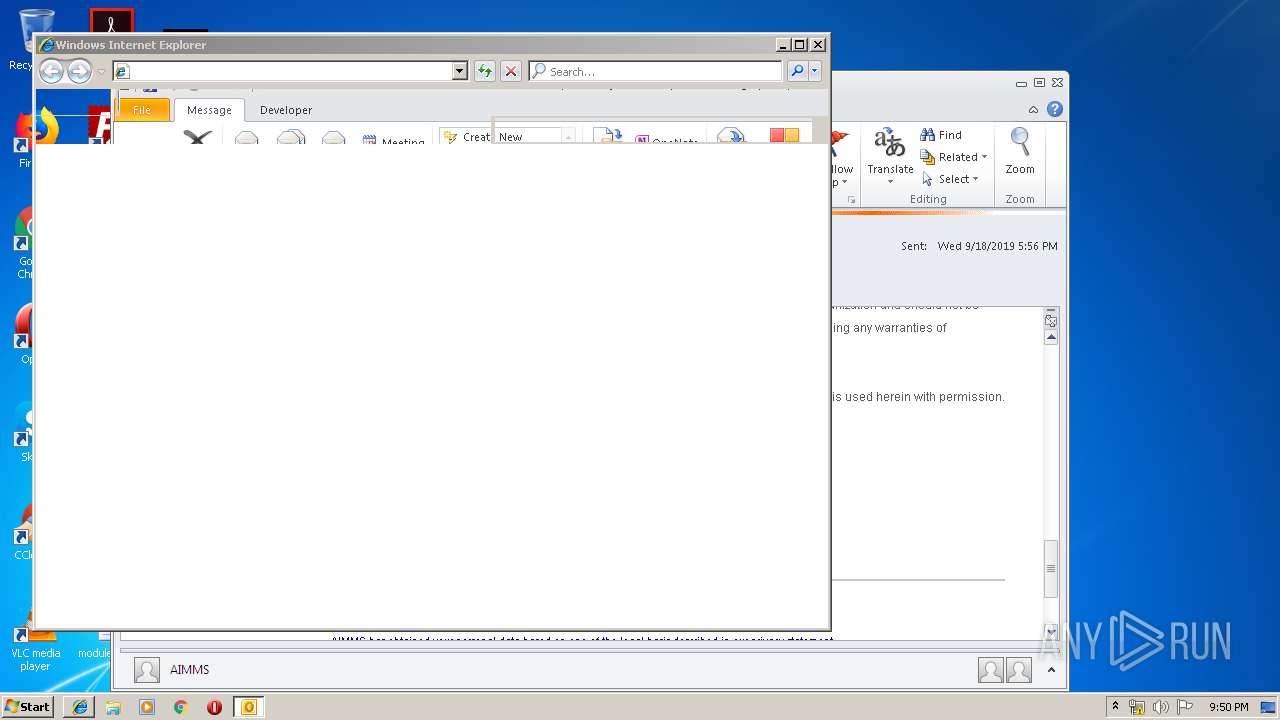
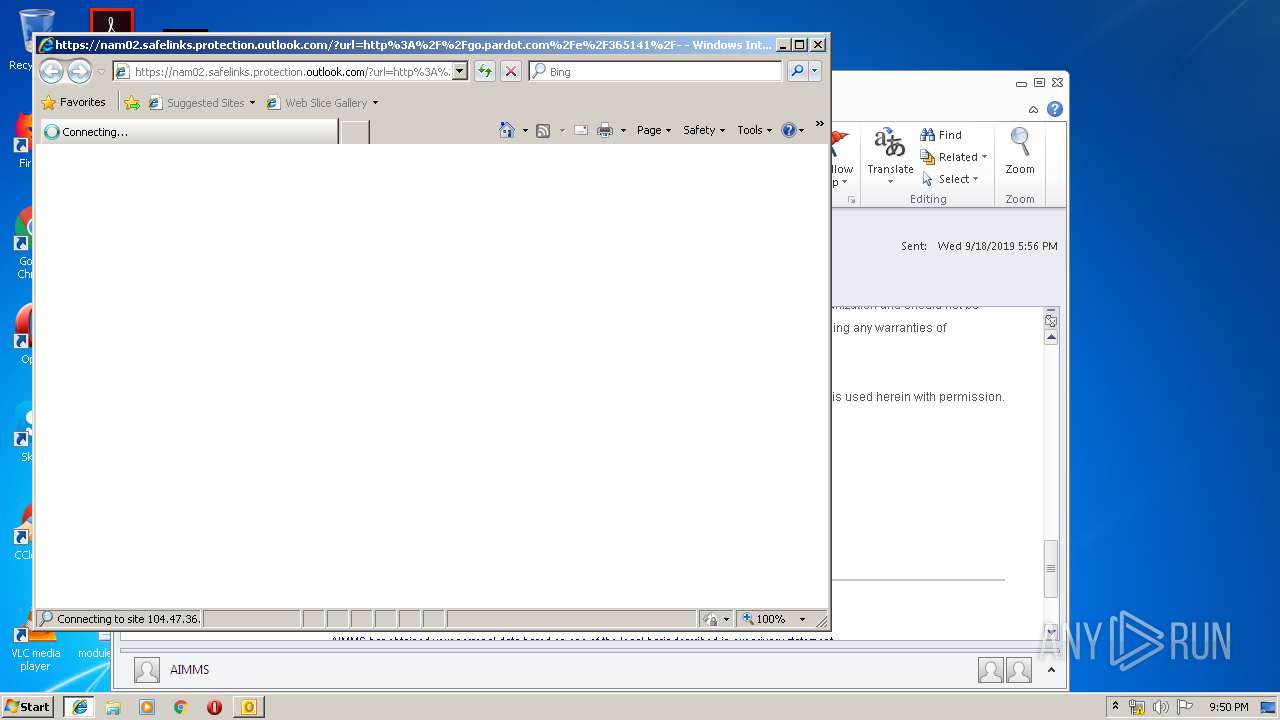
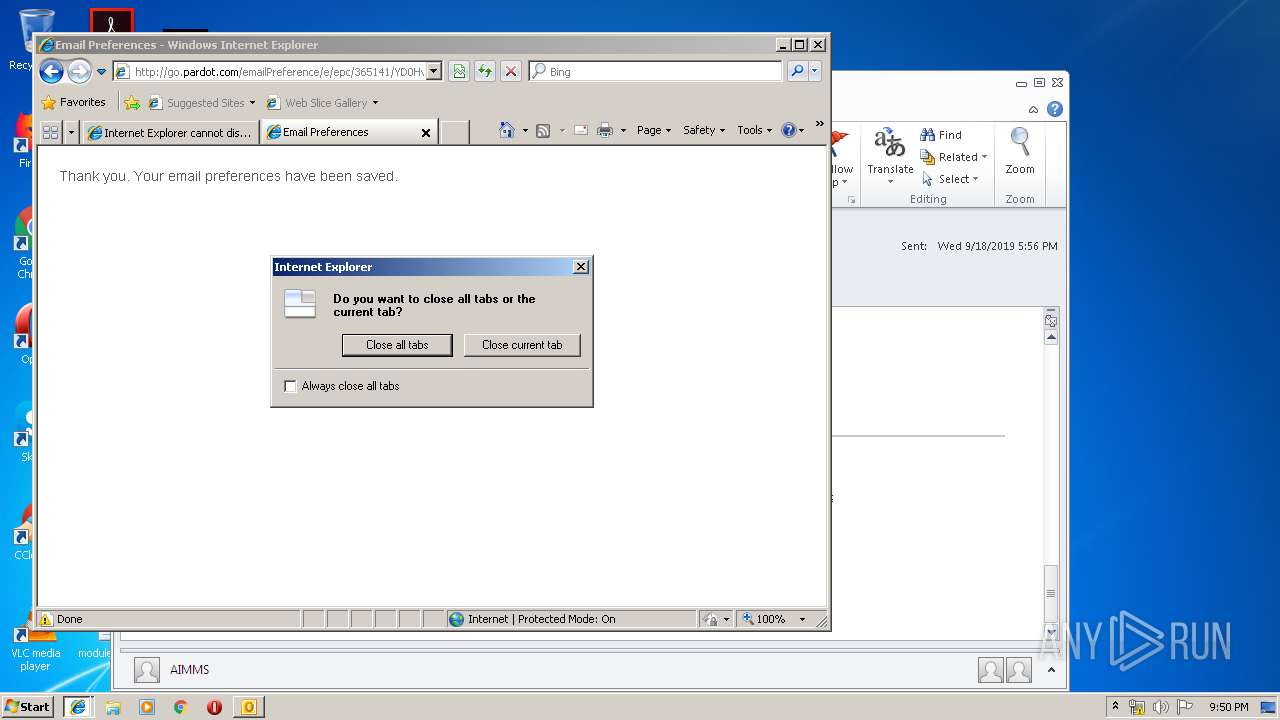
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3548)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3548)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3548)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2812)
Creates files in the user directory
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2092)
Reads internet explorer settings
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2092)
Reads Internet Cache Settings
- iexplore.exe (PID: 1092)
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 2092)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3548)
Application launched itself
- iexplore.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 3) (100) |
|---|
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2812 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2812 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
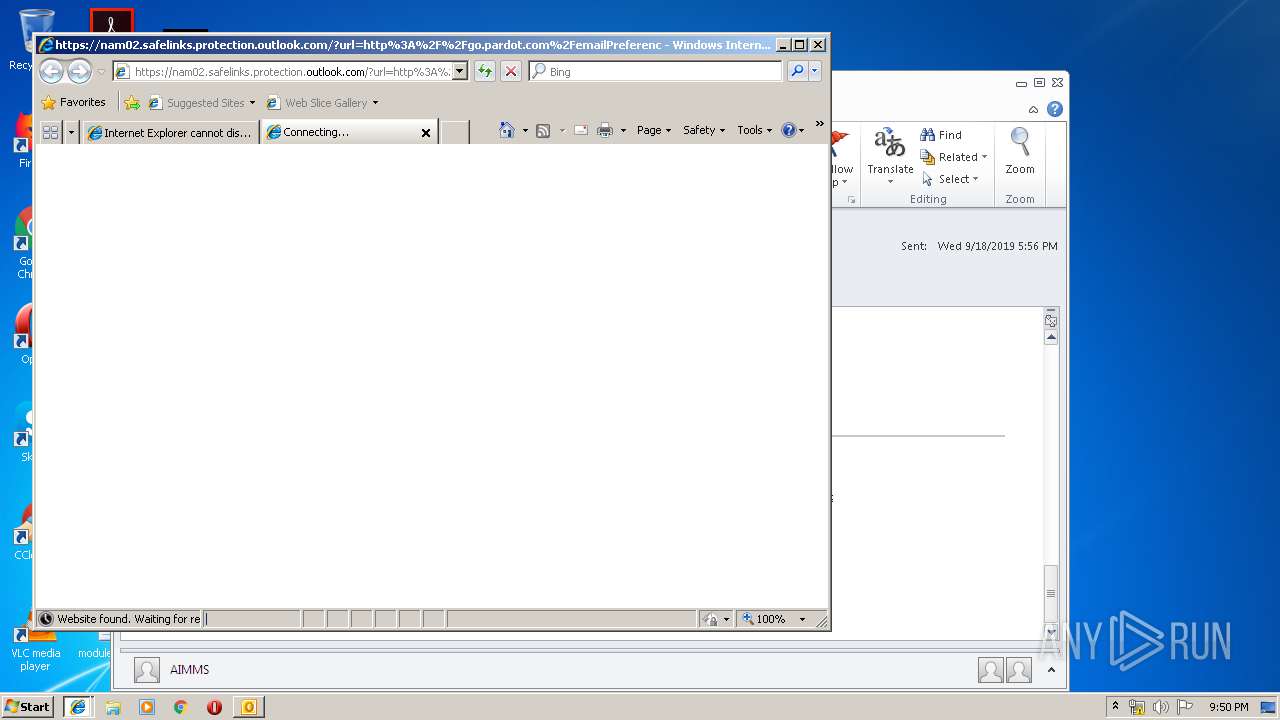
| 2812 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam02.safelinks.protection.outlook.com/?url=http%3A%2F%2Fgo.pardot.com%2Fe%2F365141%2F-trk-nmp-rec-act-company-photo%2F8lsyv%2F168208919%3Fh%3DjT2zZX2vN_NwvOVEoR_wEIoE4SKLCGXg684AXe26pi0&data=02%7C01%7Cethorpe%40nuskin.com%7C4fb89ea51aeb415f307908d73c580819%7C62b5ee2d032e48688fc275cce46e1ee0%7C0%7C0%7C637044221110286308&sdata=4aZKcgRDK%2Fvno4NRxUFJvmRlk9PkhYk0V%2F%2FrRTpadqY%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Last chance to download this complimentary Gartner report!.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 915
Read events
1 414
Write events
480
Delete events
21
Modification events
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | .z$ |
Value: 2E7A2400DC0D0000010000000000000000000000 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: DC0D0000082C2581626ED50100000000 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220220640 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3548) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328676885 | |||
Executable files
0
Suspicious files
0
Text files
55
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9AAE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso9F82.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2812 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
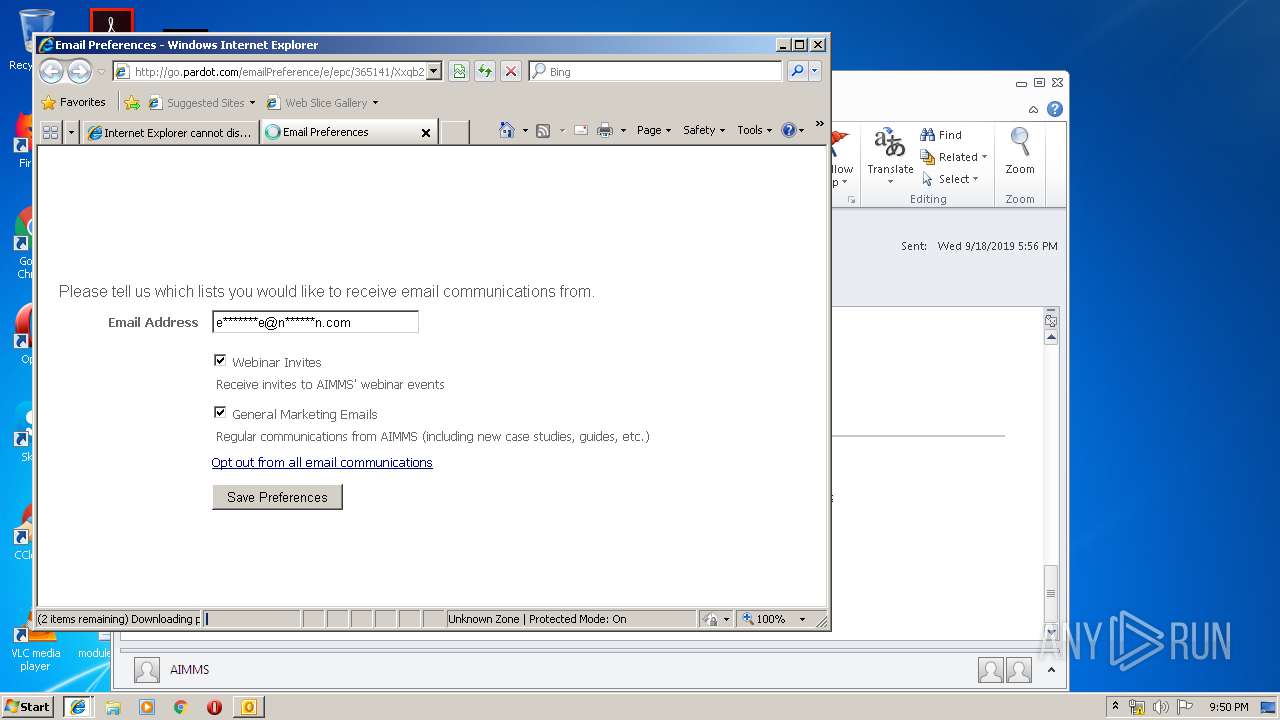
| 1092 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@pardot[1].txt | — | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@geikev2y.emltrk[1].txt | text | |
MD5:— | SHA256:— | |||
| 1092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3548 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@35.175.225[1].txt | text | |
MD5:— | SHA256:— | |||
| 1092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
66
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3548 | OUTLOOK.EXE | GET | — | 35.174.151.106:80 | http://go.pardot.com/l/365141/2019-03-08/4wxh5/365141/64256/Turtle_iStock_176016673.jpg | US | — | — | whitelisted |
3548 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3548 | OUTLOOK.EXE | GET | — | 35.174.151.106:80 | http://go.pardot.com/l/365141/2019-03-26/4zct5/365141/66916/190307_Gartner_Email_Header_02.jpg | US | — | — | whitelisted |
3548 | OUTLOOK.EXE | GET | 200 | 35.175.225.72:80 | http://35.175.225.72//geikev2y?d=%5bUNIQUE%5d&r=0 | US | — | — | unknown |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2019-03-08/4wxh5/365141/64256/Turtle_iStock_176016673.jpg | US | html | 137 b | whitelisted |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2017-05-22/9qg/365141/1297/forwardicon.png | US | html | 124 b | whitelisted |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2019-03-26/4zct5/365141/66916/190307_Gartner_Email_Header_02.jpg | US | html | 142 b | whitelisted |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2017-05-22/9q8/365141/1291/twitter_icon.png | US | html | 126 b | whitelisted |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2017-05-22/9ql/365141/1301/linkedinicon.png | US | html | 125 b | whitelisted |
3548 | OUTLOOK.EXE | GET | 301 | 35.174.151.106:80 | http://go.pardot.com/l/365141/2017-05-22/9qb/365141/1293/contacticon.png | US | html | 124 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2092 | iexplore.exe | 104.47.36.28:443 | nam02.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
2092 | iexplore.exe | 35.174.151.106:80 | go.pardot.com | Amazon.com, Inc. | US | malicious |
2092 | iexplore.exe | 143.204.247.9:443 | storage.pardot.com | — | US | unknown |
3548 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3548 | OUTLOOK.EXE | 35.174.151.106:80 | go.pardot.com | Amazon.com, Inc. | US | malicious |
3548 | OUTLOOK.EXE | 52.44.160.4:443 | geikev2y.emltrk.com | Amazon.com, Inc. | US | unknown |
— | — | 143.204.247.118:80 | storage.pardot.com | — | US | unknown |
— | — | 143.204.247.118:443 | storage.pardot.com | — | US | unknown |
3548 | OUTLOOK.EXE | 35.175.225.72:80 | — | Amazon.com, Inc. | US | unknown |
3548 | OUTLOOK.EXE | 143.204.247.118:80 | storage.pardot.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
go.pardot.com |
| whitelisted |
geikev2y.emltrk.com |
| unknown |
storage.pardot.com |
| whitelisted |
nam02.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.pardot.com |
| malicious |
pi.pardot.com |
| whitelisted |