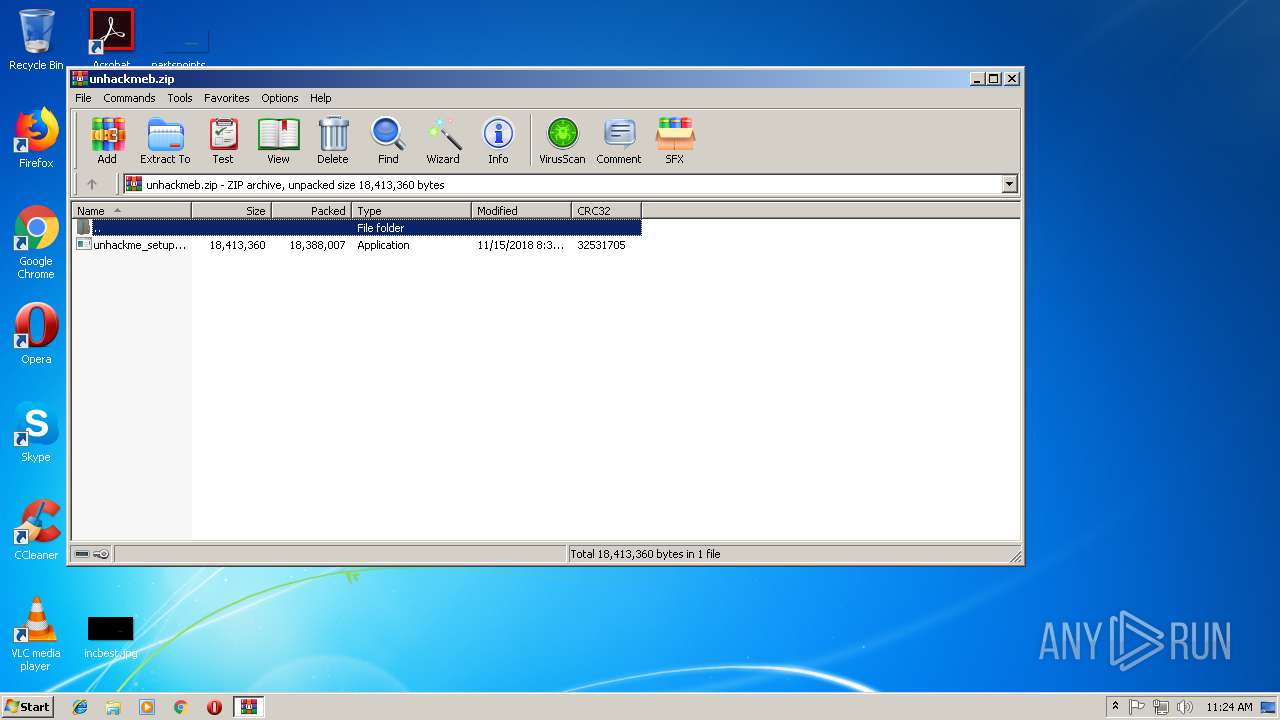
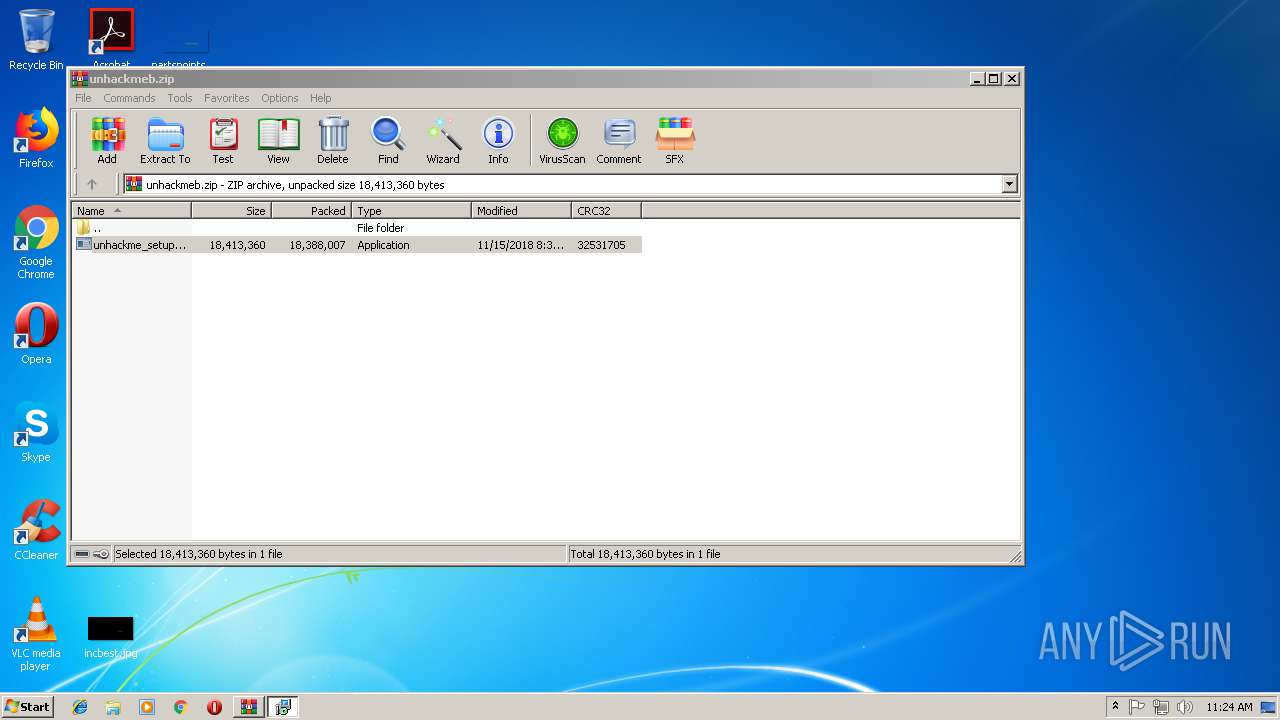
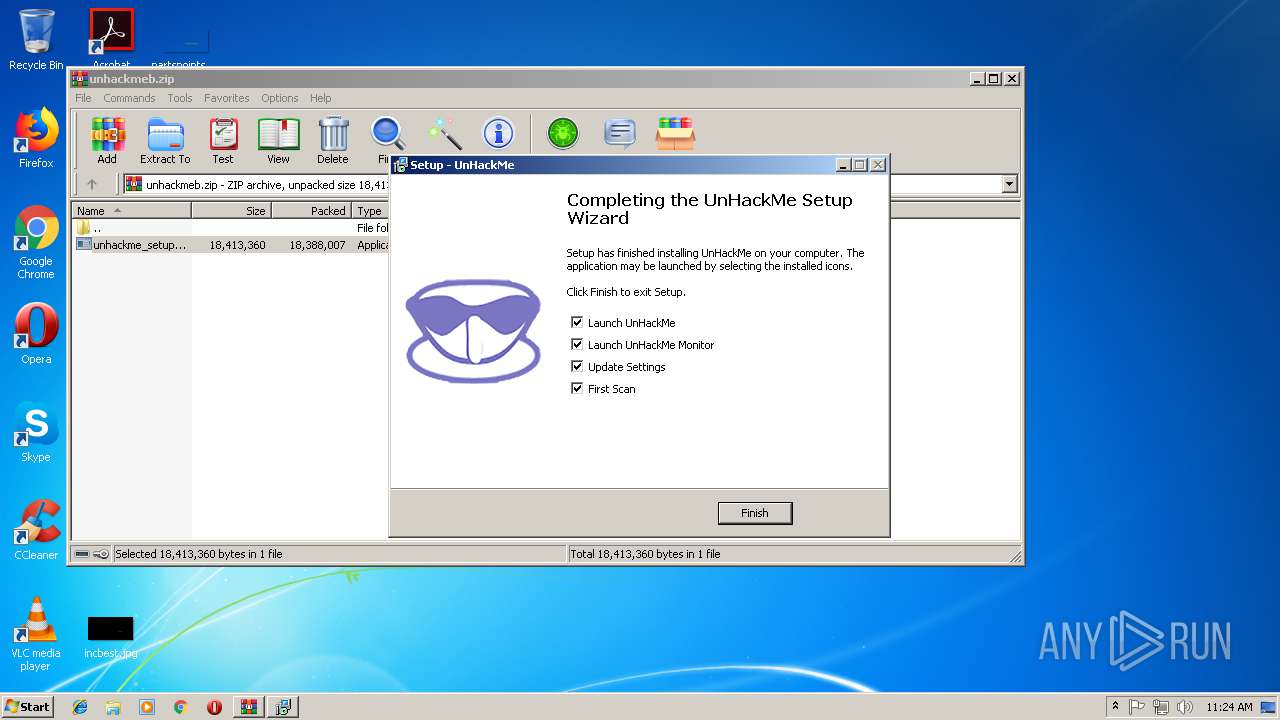
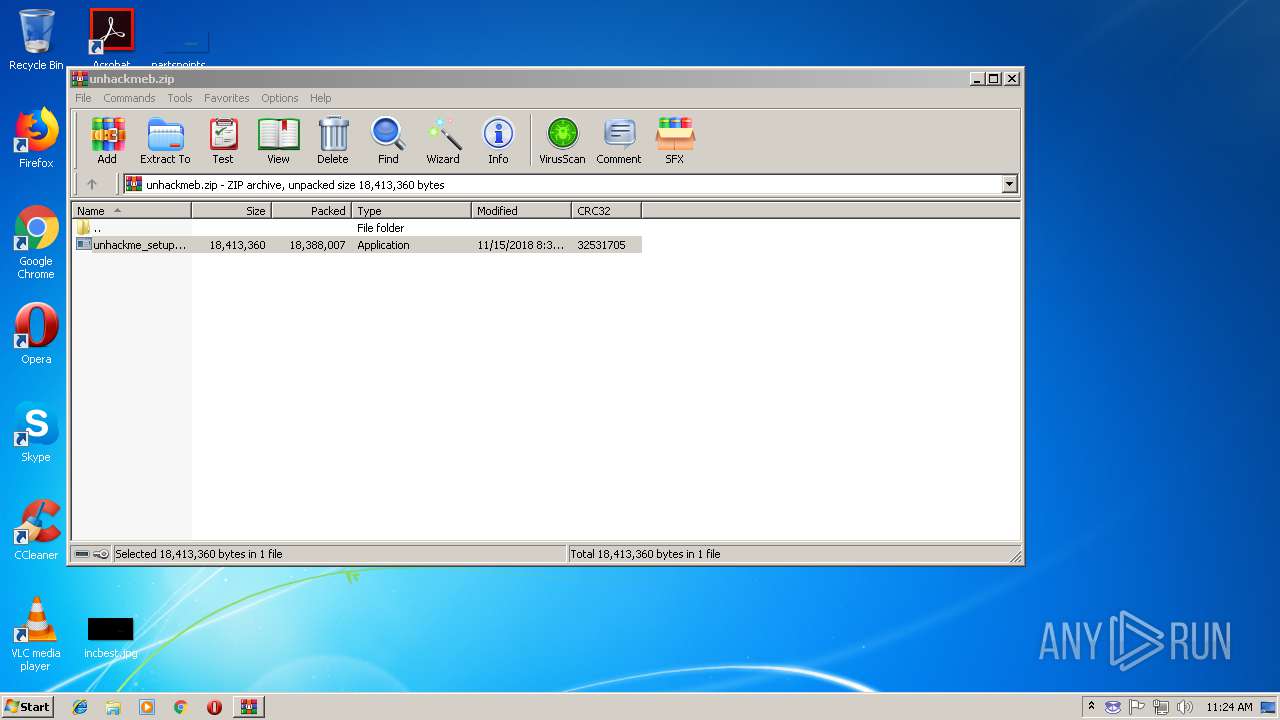
| download: | unhackmeb.zip |
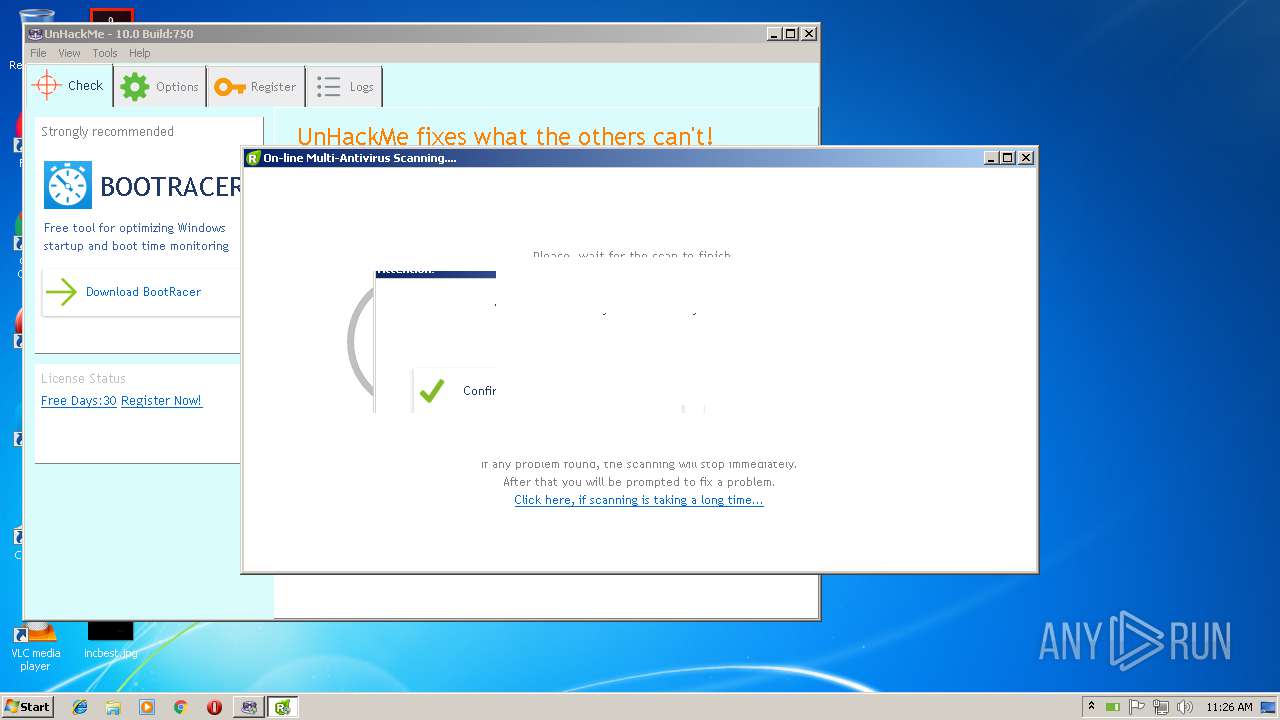
| Full analysis: | https://app.any.run/tasks/1dc400fb-541b-4c9c-890e-82e887ff4149 |
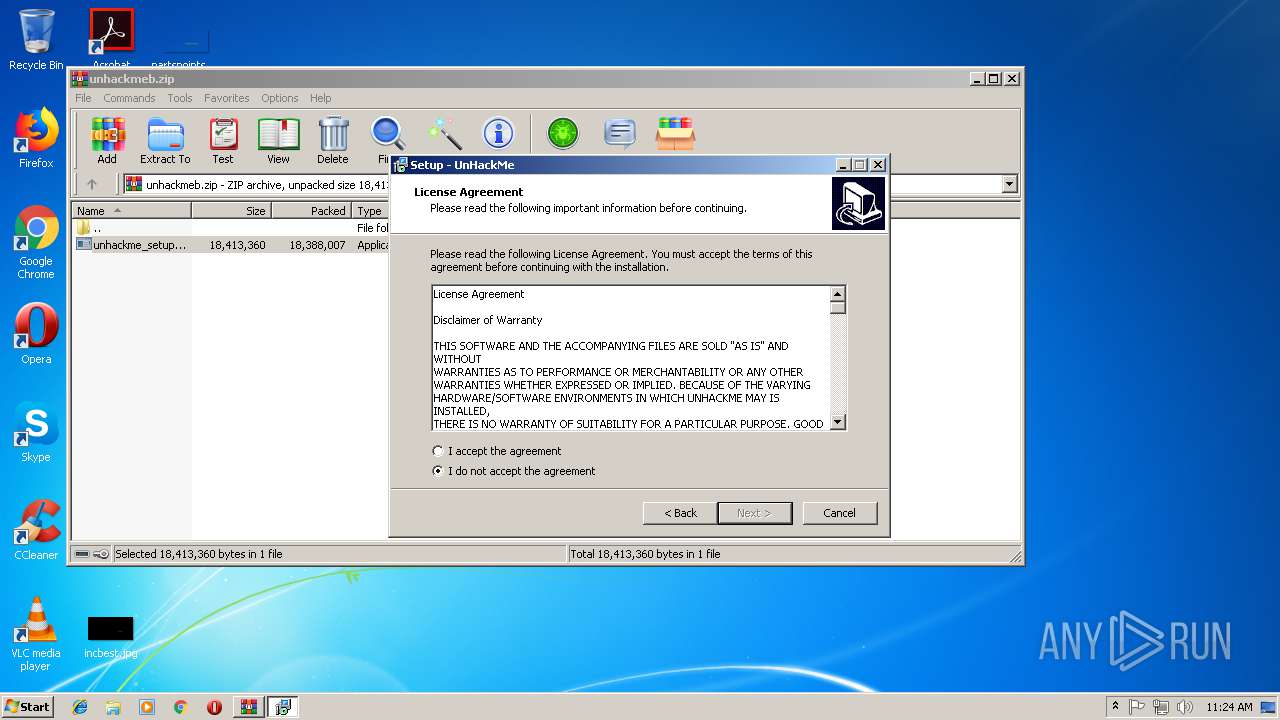
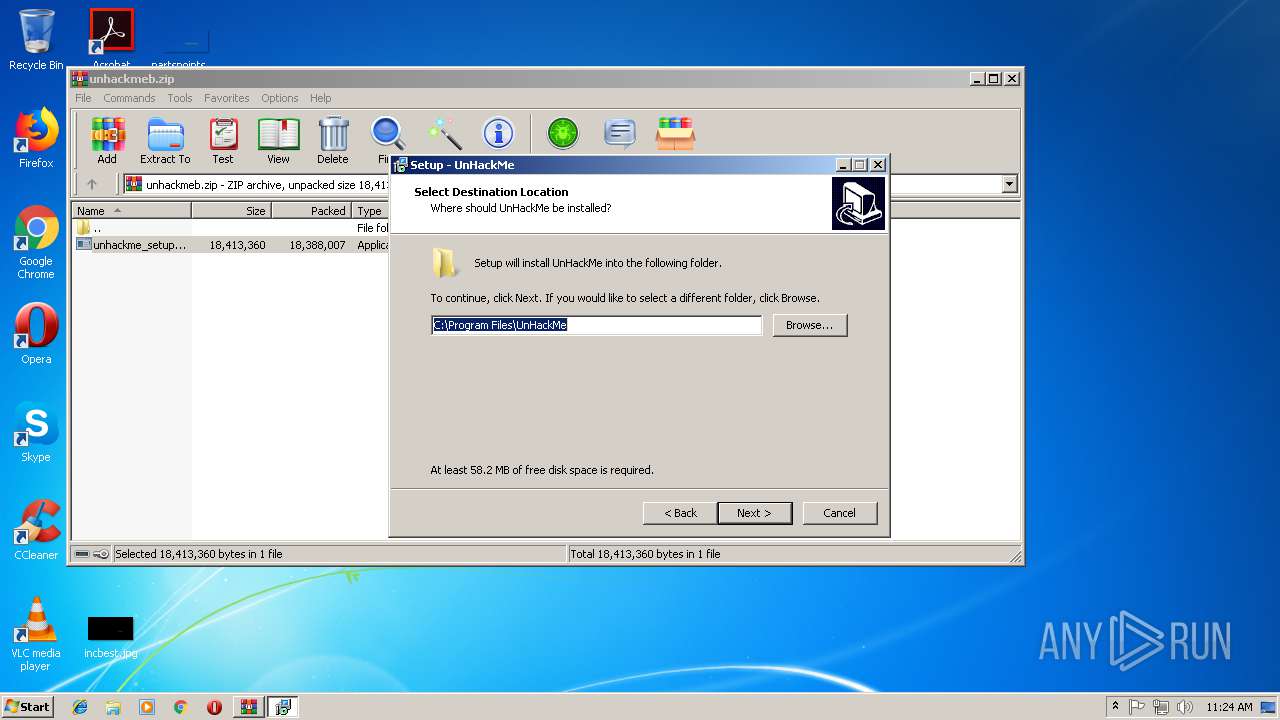
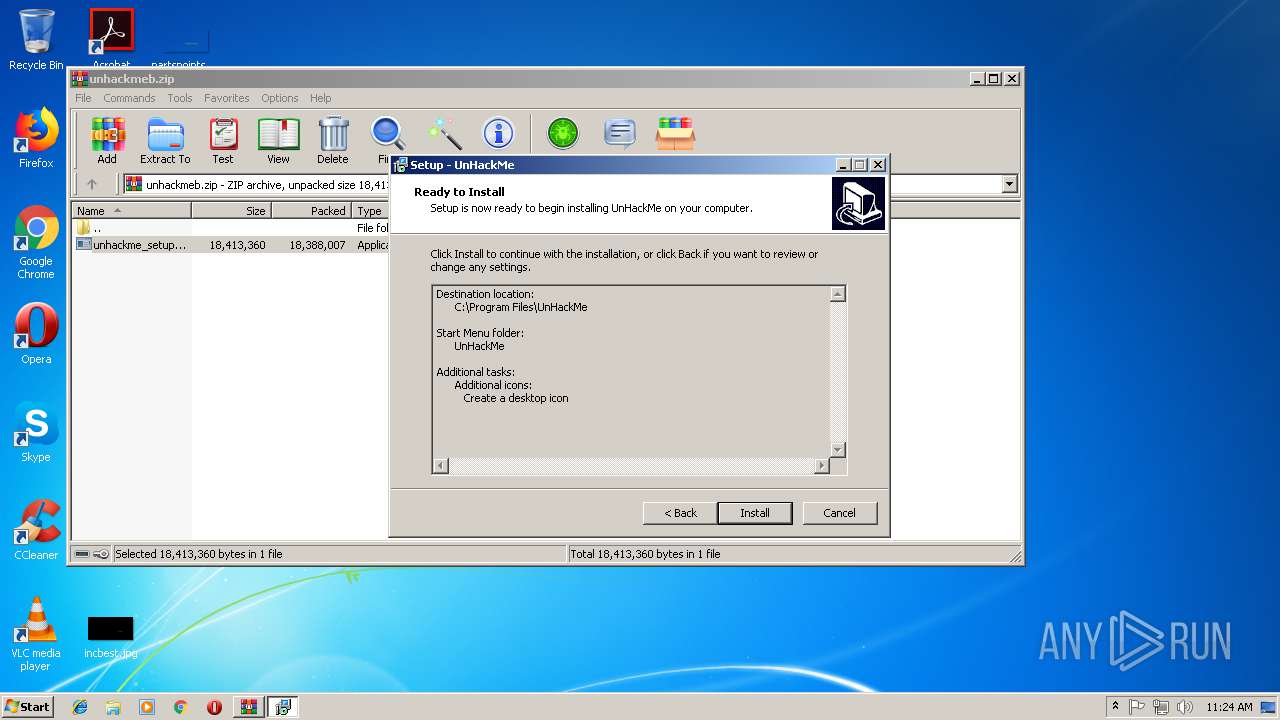
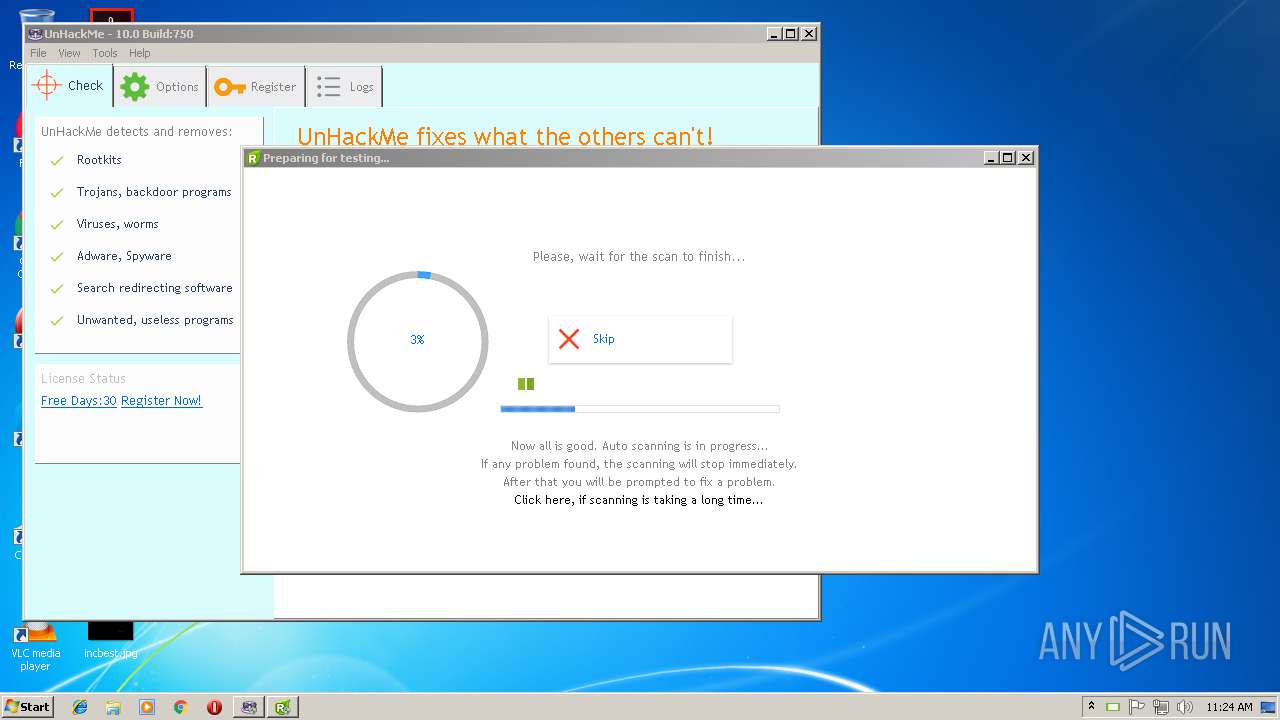
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
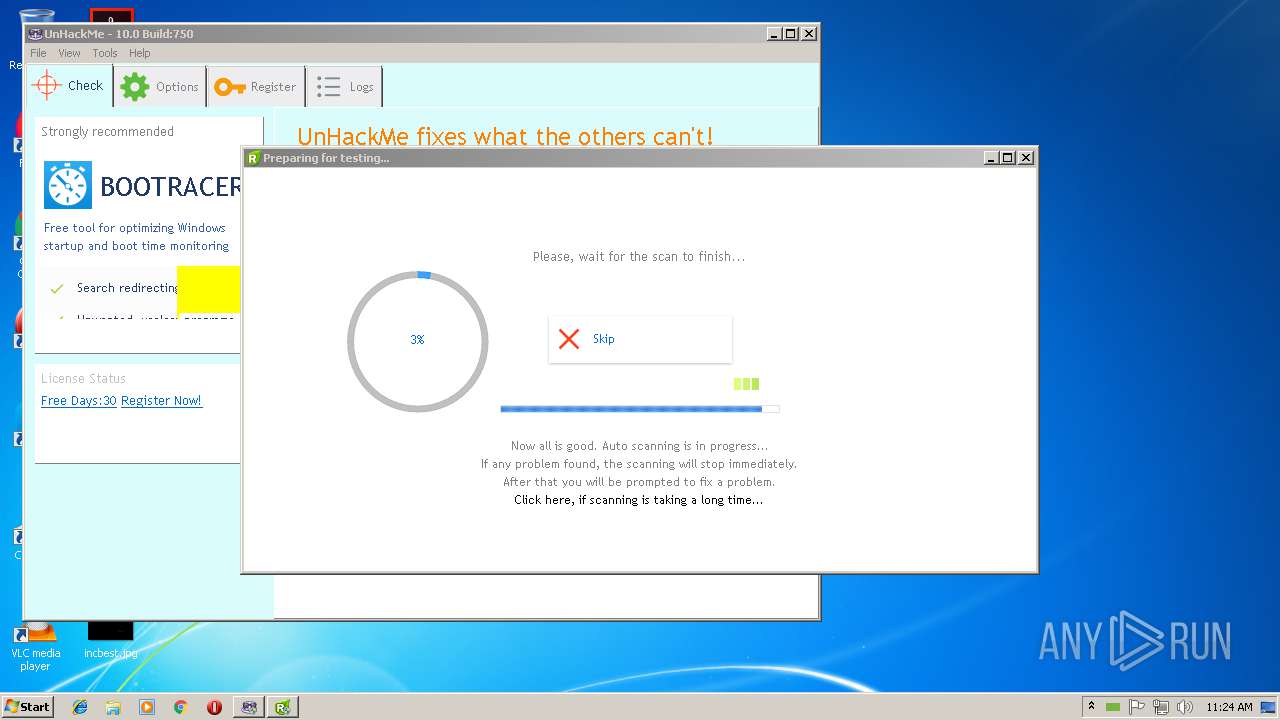
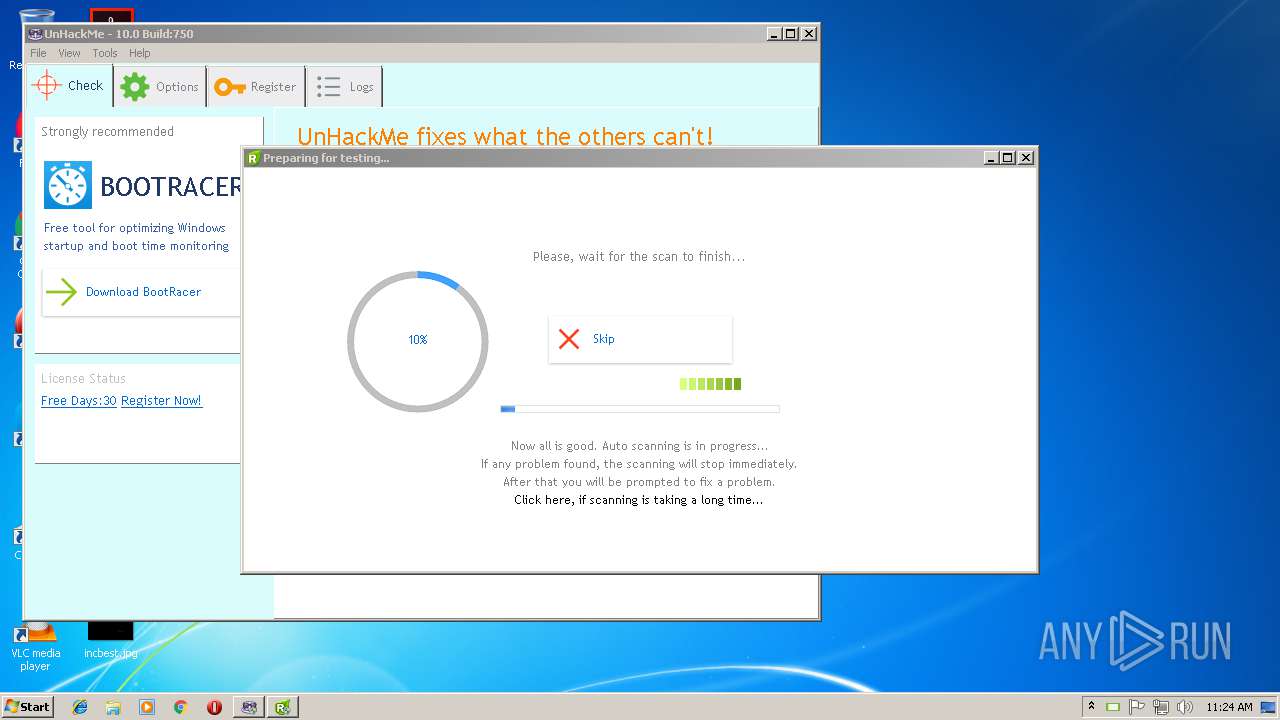
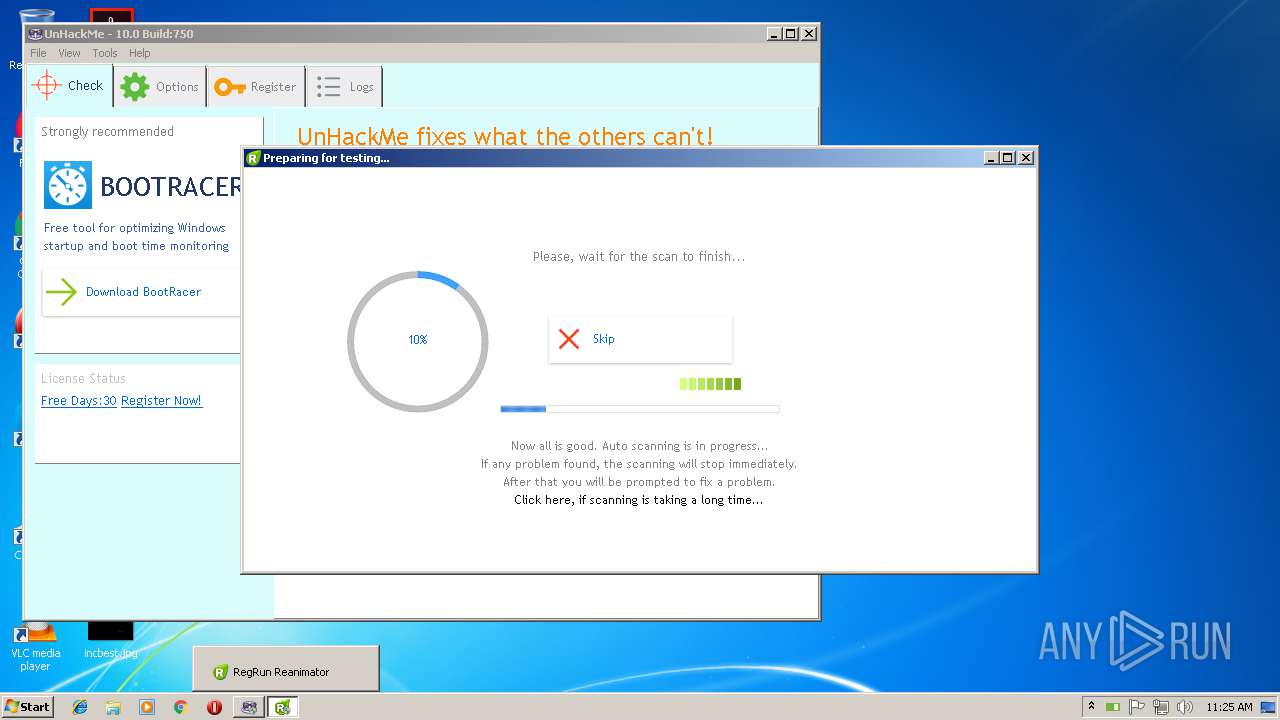
| Analysis date: | November 15, 2018, 11:23:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1B943C8DD6C470440F38FF2521596C8E |
| SHA1: | DCB6E51EEB014E42B60103636701998F73D3E543 |
| SHA256: | 8D3ABCF61676F676D9EF869FAD41B8243AAAEEA8D45122978F8764709A717AAB |
| SSDEEP: | 393216:S1XqrzEiFPPVEH3UscxXOtmX+GVjE1kqoKveVJ6Lv+0:kXqvEiRNEH3UFXWQTFlqeHyvt |
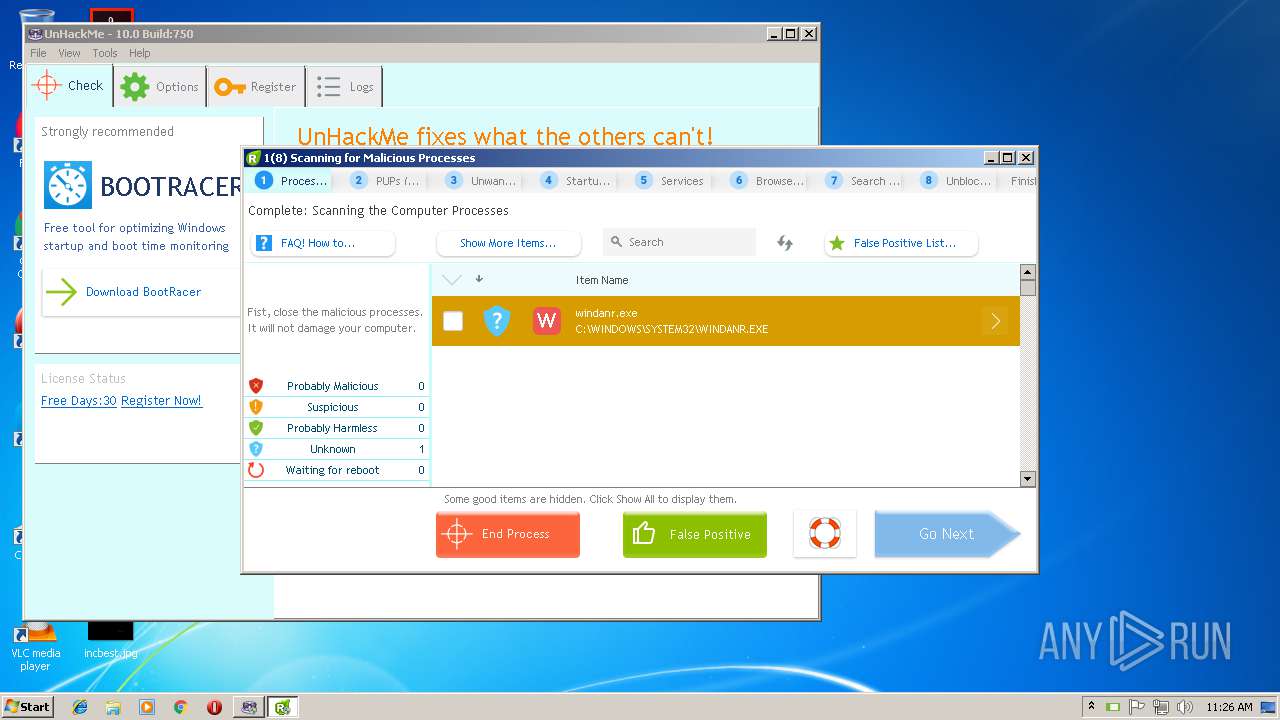
MALICIOUS
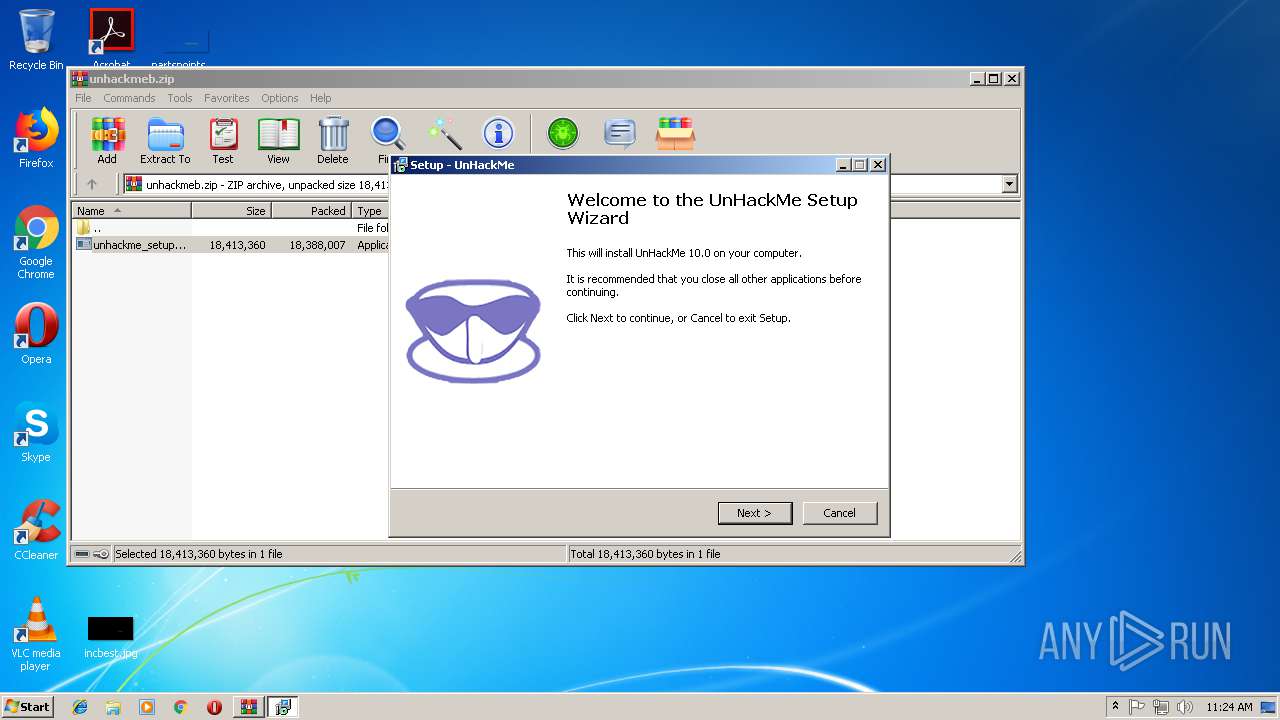
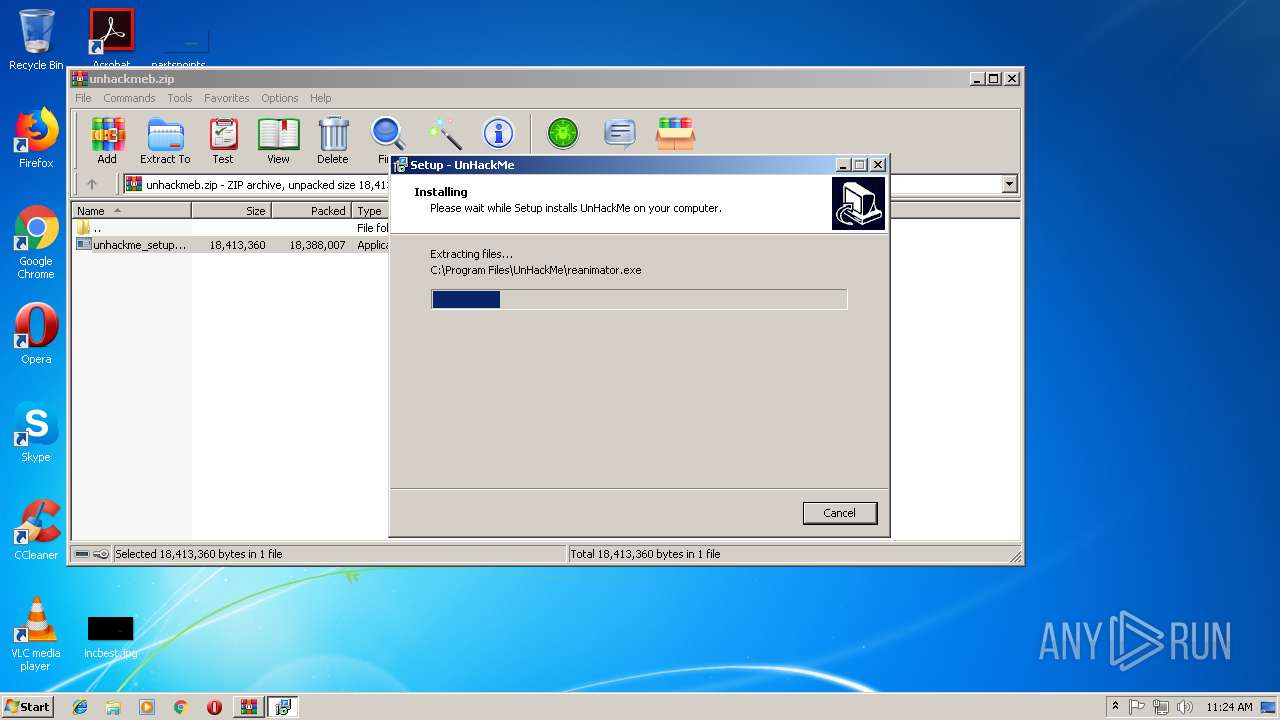
Application was dropped or rewritten from another process
- unhackme_setup.exe (PID: 1968)
- unhackme_setup.exe (PID: 2316)
- reanimator.exe (PID: 1180)
- Unhackme.exe (PID: 456)
- hackmon.exe (PID: 2284)
- reanimator.exe (PID: 236)
- regruninfo.exe (PID: 1960)
- unhackmeschedule.exe (PID: 256)
- ShowTrayIcon.exe (PID: 1684)
- mozlz4d.exe (PID: 4068)
- wu.exe (PID: 1320)
- wu.exe (PID: 2192)
- regruninfo.exe (PID: 1216)
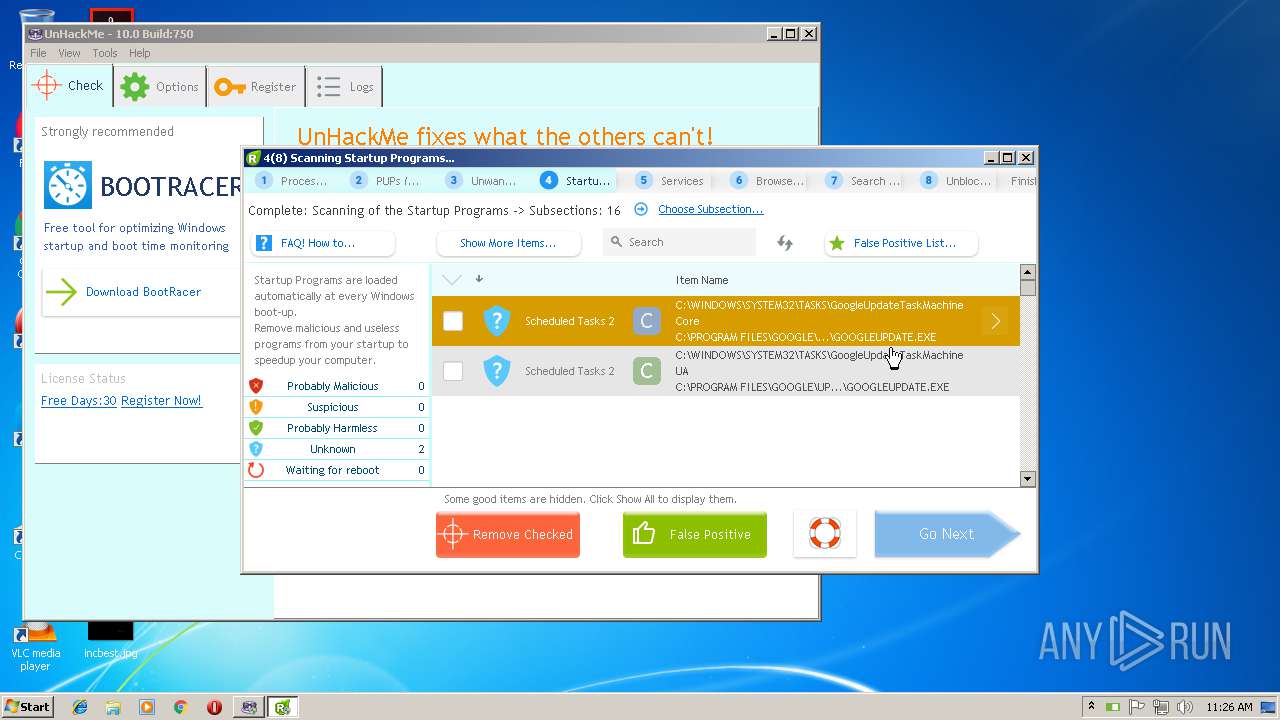
Loads the Task Scheduler COM API
- unhackmeschedule.exe (PID: 256)
Loads dropped or rewritten executable
- reanimator.exe (PID: 1180)
- reanimator.exe (PID: 236)
Changes settings of System certificates
- regruninfo.exe (PID: 1960)
- reanimator.exe (PID: 236)
Loads the Task Scheduler DLL interface
- reanimator.exe (PID: 236)
Actions looks like stealing of personal data
- reanimator.exe (PID: 236)
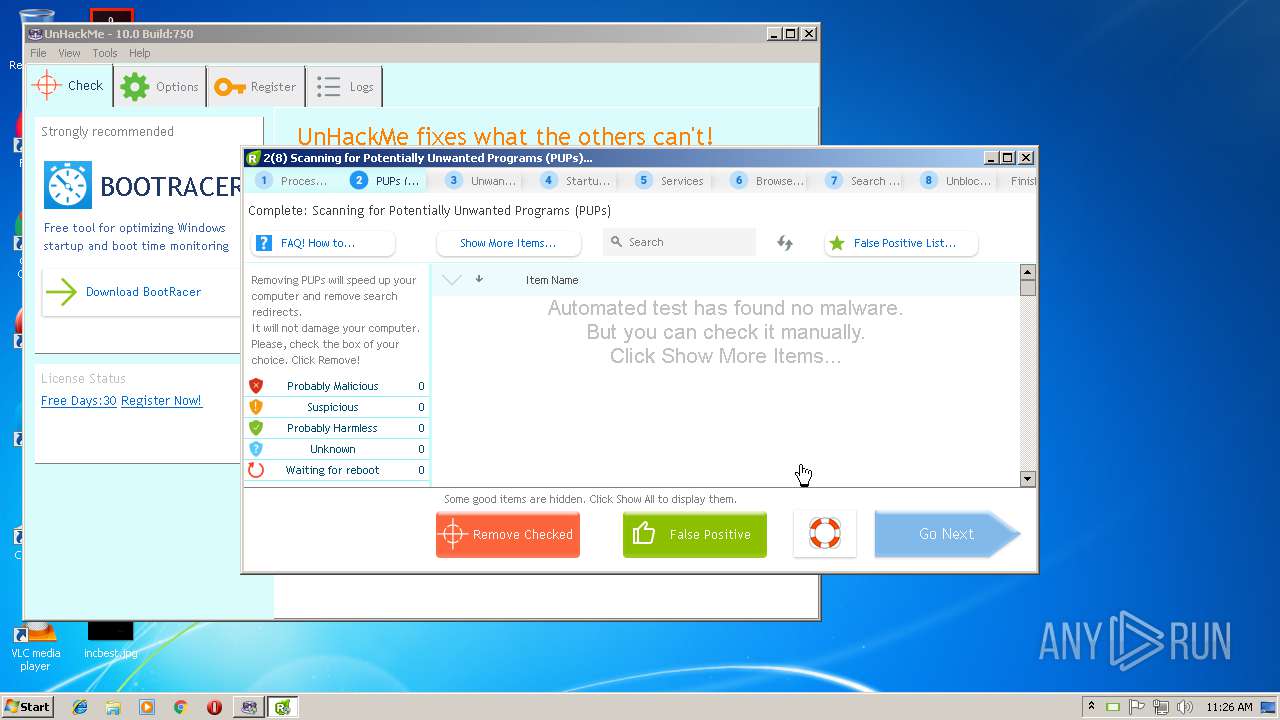
SUSPICIOUS
Executable content was dropped or overwritten
- unhackme_setup.exe (PID: 1968)
- WinRAR.exe (PID: 2416)
- unhackme_setup.exe (PID: 2316)
- unhackme_setup.tmp (PID: 2952)
Dropped object may contain URLs of mainers pools
- unhackme_setup.tmp (PID: 2952)
Creates files in the Windows directory
- unhackme_setup.tmp (PID: 2952)
- Unhackme.exe (PID: 456)
Creates files in the driver directory
- unhackme_setup.tmp (PID: 2952)
- Unhackme.exe (PID: 456)
Modifies the open verb of a shell class
- unhackme_setup.tmp (PID: 2952)
Uses NETSH.EXE for network configuration
- unhackme_setup.tmp (PID: 2952)
Adds / modifies Windows certificates
- regruninfo.exe (PID: 1960)
- reanimator.exe (PID: 236)
Creates files in the program directory
- wu.exe (PID: 1320)
- reanimator.exe (PID: 1180)
- reanimator.exe (PID: 236)
- wu.exe (PID: 2192)
Creates COM task schedule object
- Unhackme.exe (PID: 456)
Low-level read access rights to disk partition
- reanimator.exe (PID: 236)
Creates files in the user directory
- regruninfo.exe (PID: 1216)
Searches for installed software
- reanimator.exe (PID: 236)
INFO
Loads dropped or rewritten executable
- unhackme_setup.tmp (PID: 2952)
Application was dropped or rewritten from another process
- unhackme_setup.tmp (PID: 1460)
- unhackme_setup.tmp (PID: 2952)
Creates files in the program directory
- unhackme_setup.tmp (PID: 2952)
Dropped object may contain Bitcoin addresses
- unhackme_setup.tmp (PID: 2952)
- reanimator.exe (PID: 236)
- regruninfo.exe (PID: 1216)
Dropped object may contain TOR URL's
- unhackme_setup.tmp (PID: 2952)
- Unhackme.exe (PID: 456)
- reanimator.exe (PID: 236)
Creates a software uninstall entry
- unhackme_setup.tmp (PID: 2952)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2660)
Reads settings of System Certificates
- reanimator.exe (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:15 11:38:21 |
| ZipCRC: | 0x32531705 |
| ZipCompressedSize: | 18388007 |
| ZipUncompressedSize: | 18413360 |
| ZipFileName: | unhackme_setup.exe |
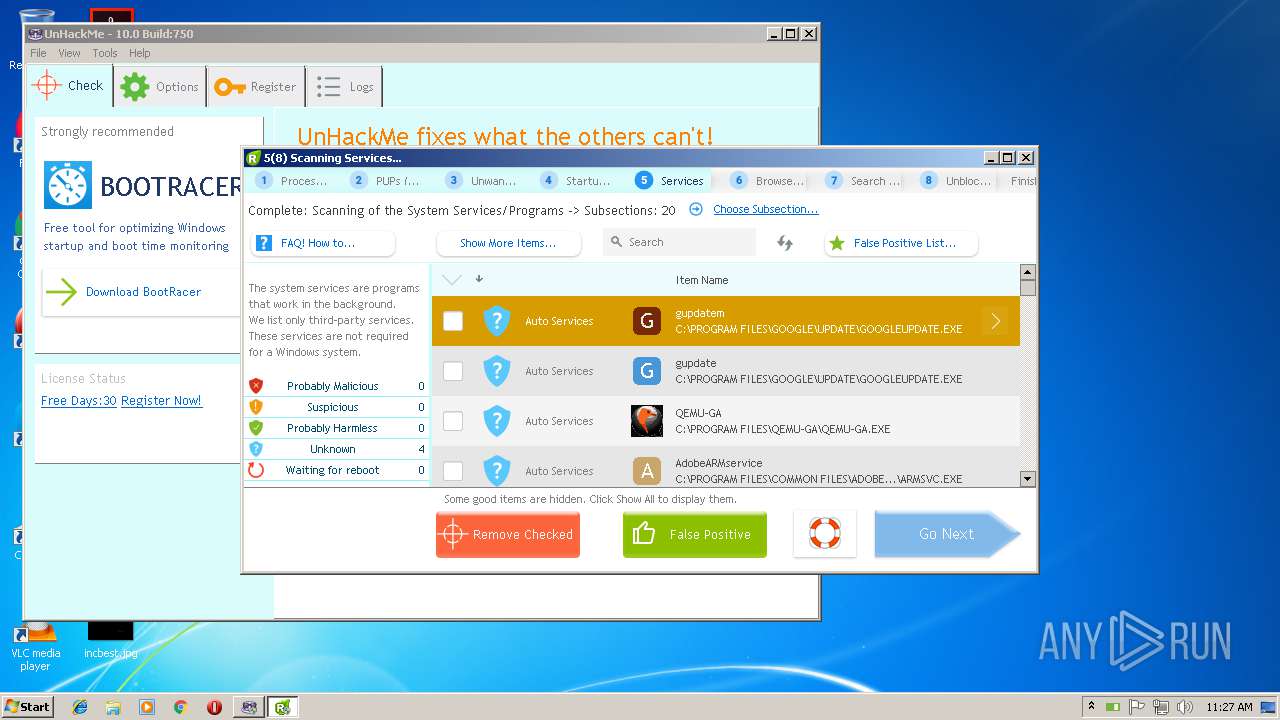
Total processes
64
Monitored processes
21
Malicious processes
6
Suspicious processes
3
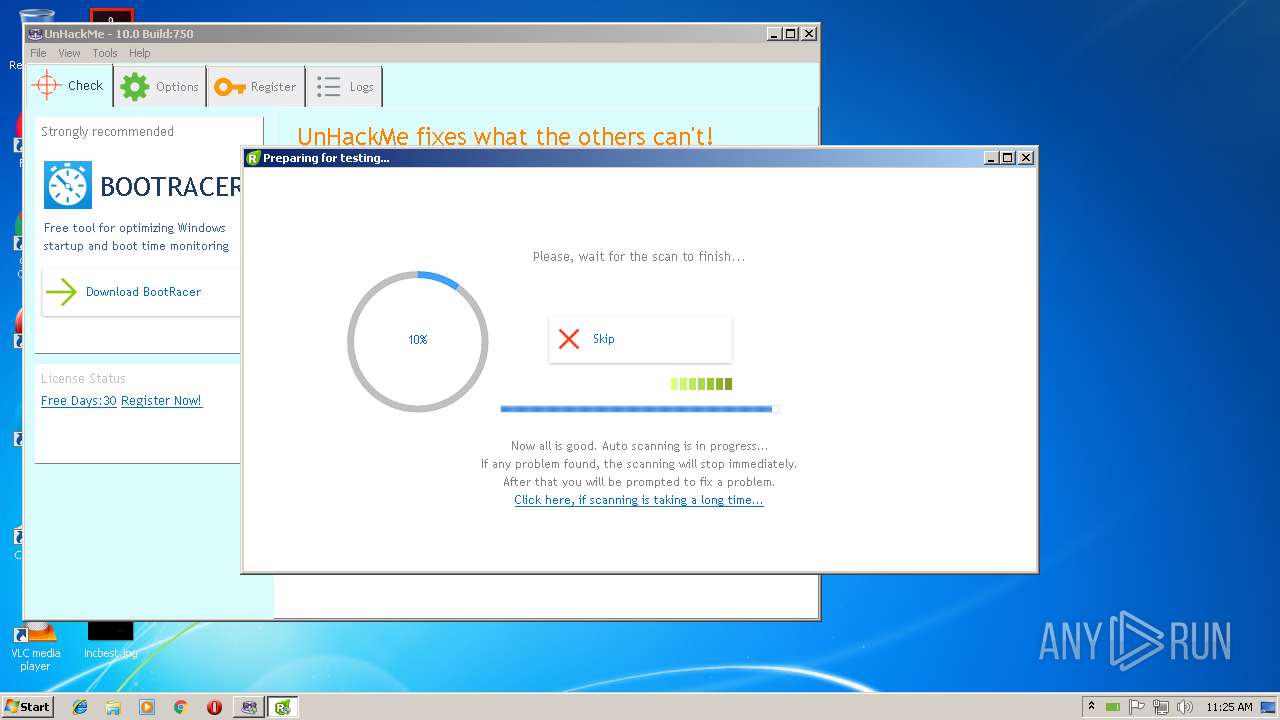
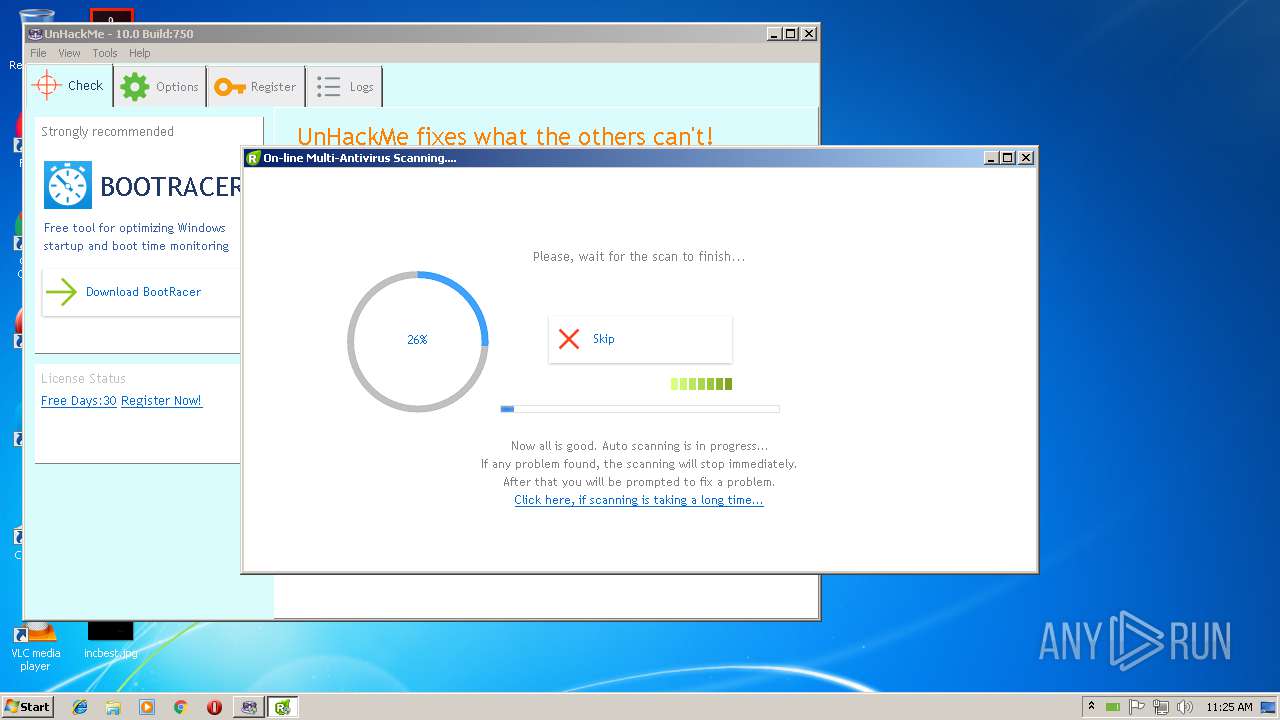
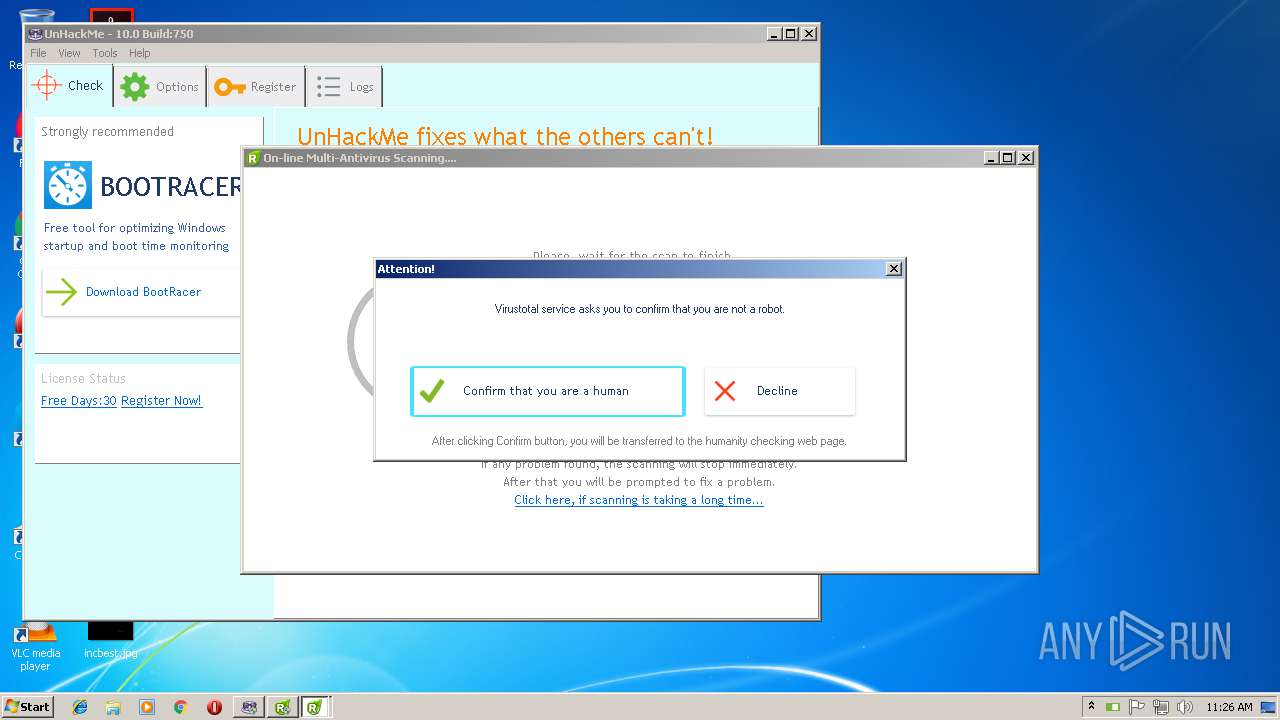
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\UnHackMe\reanimator.exe" /wiz /full /malw | C:\Program Files\UnHackMe\reanimator.exe | unhackme_setup.tmp | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: RegRun Start Control Exit code: 0 Version: 10.0.0.750 Modules
| |||||||||||||||
| 256 | "C:\Program Files\UnHackMe\unhackmeschedule.exe" | C:\Program Files\UnHackMe\unhackmeschedule.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: UnHackMe Schedule Creator Exit code: 0 Version: 5, 0, 9, 9 Modules
| |||||||||||||||
| 456 | "C:\Program Files\UnHackMe\Unhackme.exe" | C:\Program Files\UnHackMe\Unhackme.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Detects and removes rootkits Exit code: 0 Version: 10.0.0.750 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\UnHackMe\reanimator.exe" /c | C:\Program Files\UnHackMe\reanimator.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: RegRun Start Control Exit code: 0 Version: 10.0.0.750 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\UnHackMe\regruninfo.exe" C:\Users\admin\DOCUME~1\RegRun2\regrunlog.txt /hid: "2018-11-15-11:24:26 On-line Multi-Antivirus Scanning...." /mal: C:\Users\admin\DOCUME~1\RegRun2\ | C:\Program Files\UnHackMe\regruninfo.exe | reanimator.exe | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Module for retrieving file info from Internet Exit code: 0 Version: 10.0.0.750 Modules
| |||||||||||||||
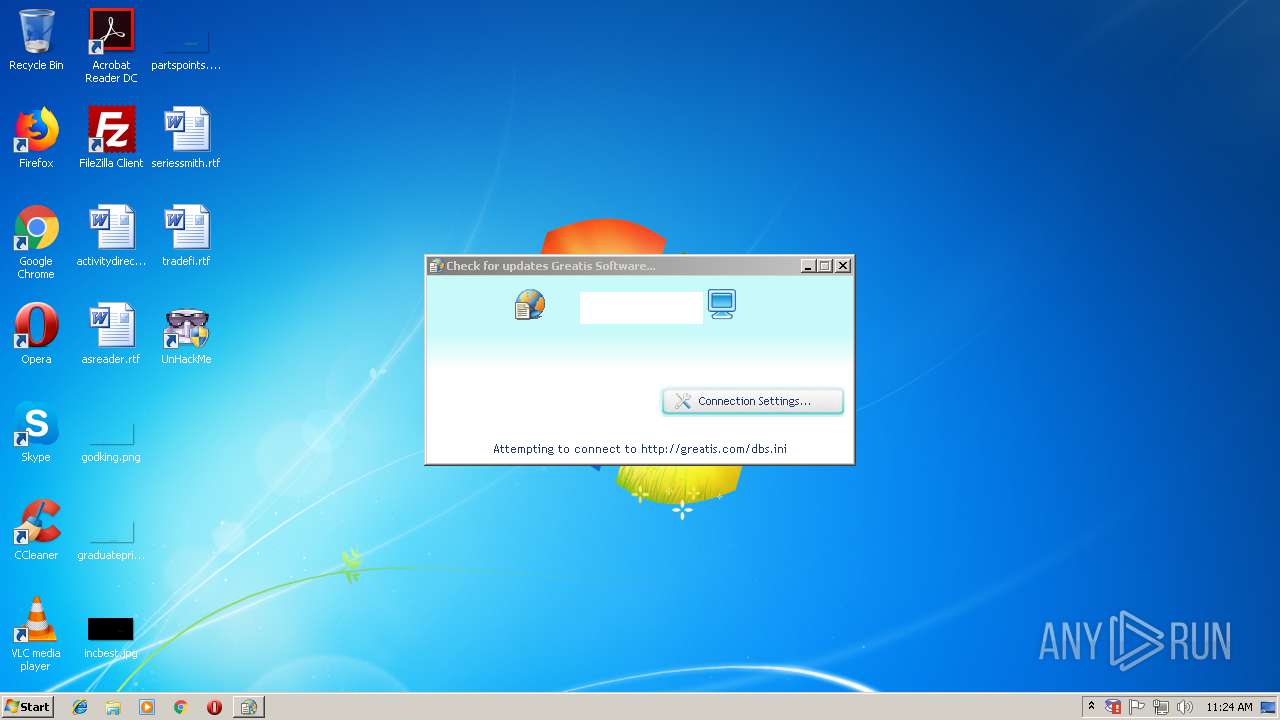
| 1320 | "C:\Program Files\UnHackMe\wu.exe" http://greatis.com/dbs.ini /r /i | C:\Program Files\UnHackMe\wu.exe | reanimator.exe | ||||||||||||
User: admin Company: Greais Software Integrity Level: HIGH Description: Web Update component Exit code: 0 Version: 9.40.0.2018 Modules
| |||||||||||||||
| 1460 | "C:\Users\admin\AppData\Local\Temp\is-3775G.tmp\unhackme_setup.tmp" /SL5="$1F0382,18149027,56832,C:\Users\admin\AppData\Local\Temp\Rar$EXa2416.4466\unhackme_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-3775G.tmp\unhackme_setup.tmp | — | unhackme_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1580 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000003BC" "000005BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1684 | "C:\Program Files\UnHackMe\ShowTrayIcon.exe" | C:\Program Files\UnHackMe\ShowTrayIcon.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: MEDIUM Description: Always display UnHackMe tray icon Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\UnHackMe\regruninfo.exe" /postins | C:\Program Files\UnHackMe\regruninfo.exe | unhackme_setup.tmp | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Module for retrieving file info from Internet Exit code: 0 Version: 10.0.0.750 Modules
| |||||||||||||||
Total events
5 022
Read events
2 851
Write events
2 089
Delete events
82
Modification events
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\unhackmeb.zip | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
22
Suspicious files
142
Text files
542
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-I1MEQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-IDRJH.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-2PMPD.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-GMDU1.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-CSLPD.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-7P9NE.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-9OKNR.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-IOOD6.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-F5HO4.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-LARG1.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1960 | regruninfo.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 54.4 Kb | whitelisted |
1320 | wu.exe | GET | 200 | 208.76.245.34:80 | http://greatis.com/dbs.ini | US | text | 386 b | whitelisted |
1960 | regruninfo.exe | GET | 200 | 54.192.94.69:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2192 | wu.exe | GET | 200 | 208.76.245.34:80 | http://greatis.com/unhackme.ini | US | text | 394 b | whitelisted |
2192 | wu.exe | GET | 200 | 208.76.245.34:80 | http://greatis.com/dbs.ini | US | text | 386 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1960 | regruninfo.exe | 52.54.253.2:443 | api.gameanalytics.com | Amazon.com, Inc. | US | unknown |
1960 | regruninfo.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1320 | wu.exe | 208.76.245.34:80 | greatis.com | Crucial Paradigm | US | malicious |
2192 | wu.exe | 208.76.245.34:80 | greatis.com | Crucial Paradigm | US | malicious |
1960 | regruninfo.exe | 54.192.94.69:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
1216 | regruninfo.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.gameanalytics.com |
| suspicious |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
greatis.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1320 | wu.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |
2192 | wu.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |
2192 | wu.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |