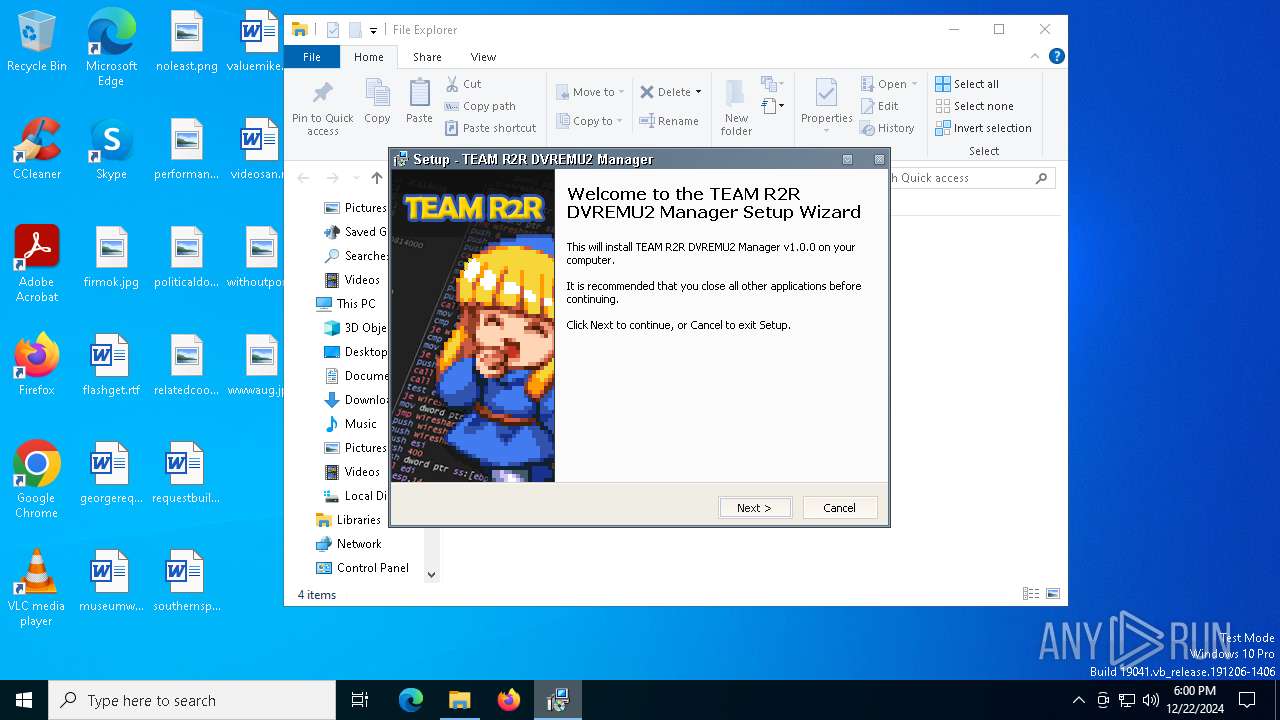
| File name: | Setup DVREMU2 Manager v1.0.0.exe |
| Full analysis: | https://app.any.run/tasks/f6e593d0-9697-440f-afb1-7610fab529a3 |
| Verdict: | Malicious activity |
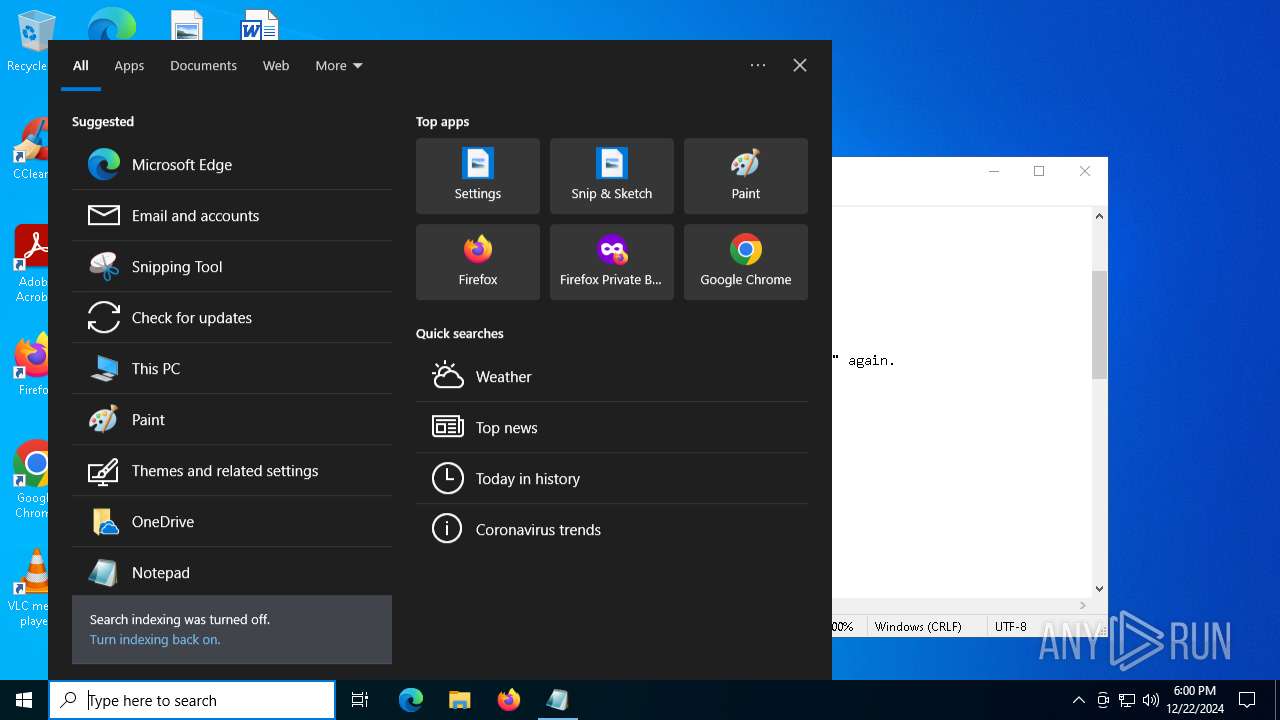
| Analysis date: | December 22, 2024, 18:00:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 712694288F0A36EFEAD1B9BA8B4C0AB0 |
| SHA1: | 543A71E15C14CB6A080F16AEA554EC2F5257D6C7 |
| SHA256: | 8D31D34083335DC0CC3C76BD5F418846E8F4DAAD5A437CEFD8E47DF332401B08 |
| SSDEEP: | 98304:o0sukgDZXTKbXS4LGwFe71oJA7qGRplv9iU+j9AjHOulFxvugZhwrJwquuT+uruU:Hbq1CPwDvt3uFGCC0f4 |
MALICIOUS
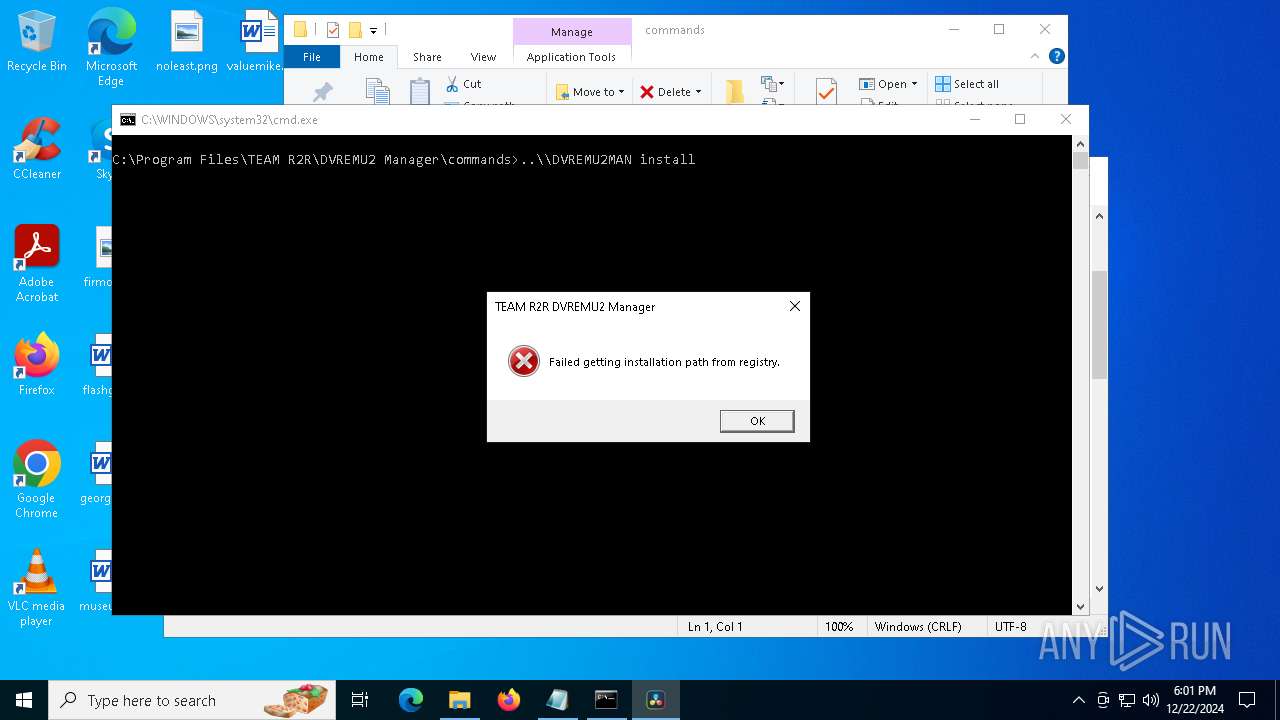
Executing a file with an untrusted certificate
- DVREMU2MAN.exe (PID: 6404)
- DVREMU2MAN.exe (PID: 1328)
- DVREMU2MAN.exe (PID: 6864)
- DVREMU2MAN.exe (PID: 6704)
- DVREMU2MAN.exe (PID: 6848)
- DVREMU2MAN.exe (PID: 4520)
- DVREMU2MAN.exe (PID: 7128)
- DVREMU2MAN.exe (PID: 4228)
- DVREMU2MAN.exe (PID: 6464)
- DVREMU2MAN.exe (PID: 6832)
- DVREMU2MAN.exe (PID: 6816)
- DVREMU2MAN.exe (PID: 6880)
- DVREMU2MAN.exe (PID: 4328)
- DVREMU2MAN.exe (PID: 6280)
SUSPICIOUS
Reads security settings of Internet Explorer
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6696)
- DVREMU2MAN.exe (PID: 6404)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
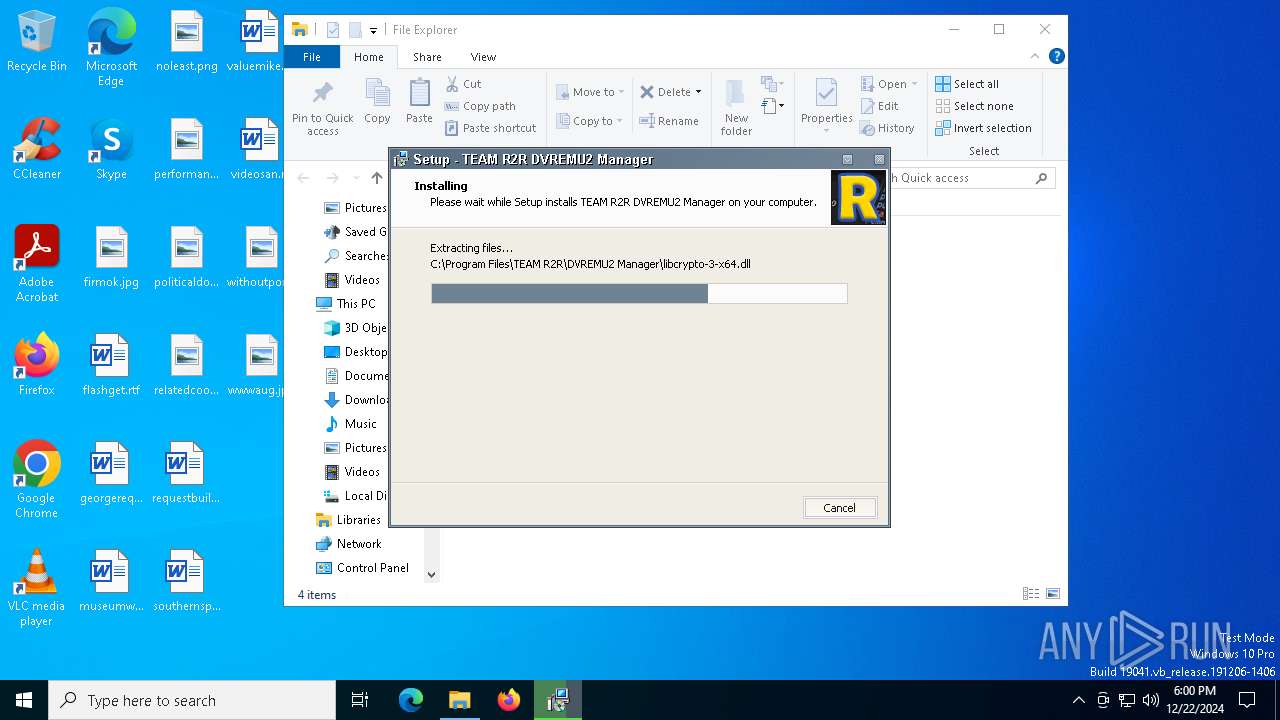
Executable content was dropped or overwritten
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6660)
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6836)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Reads the Windows owner or organization settings
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
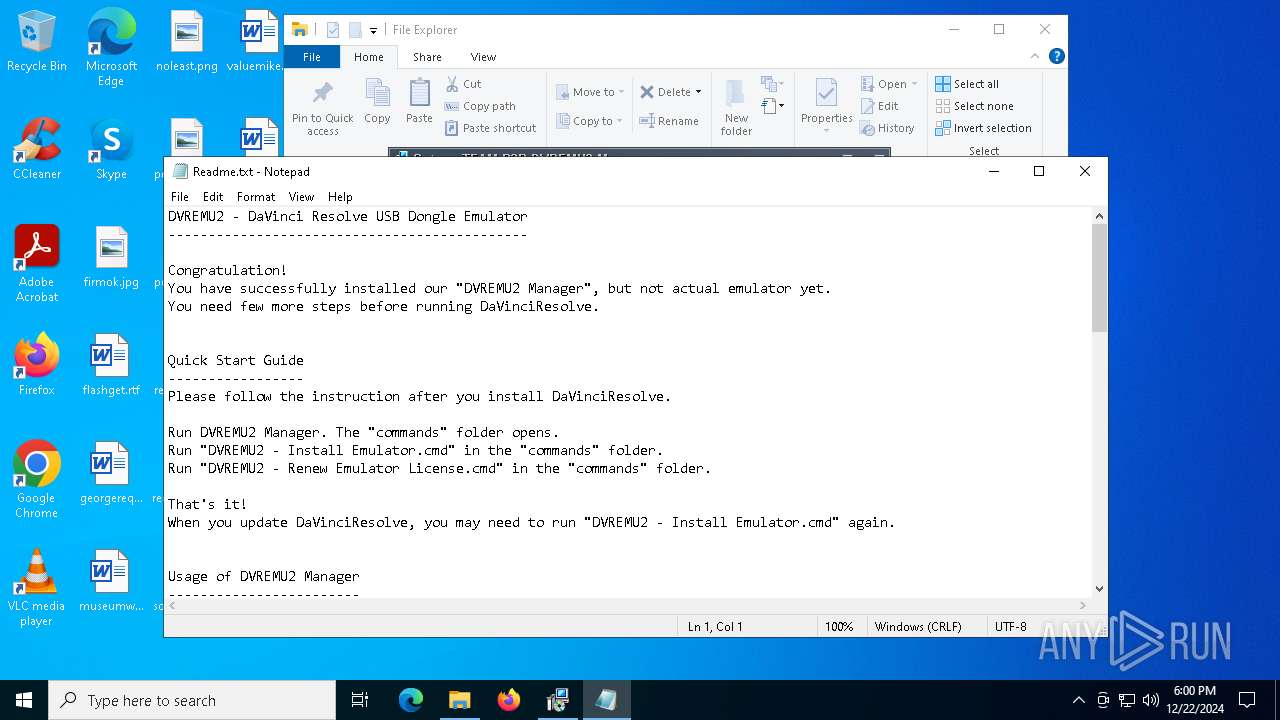
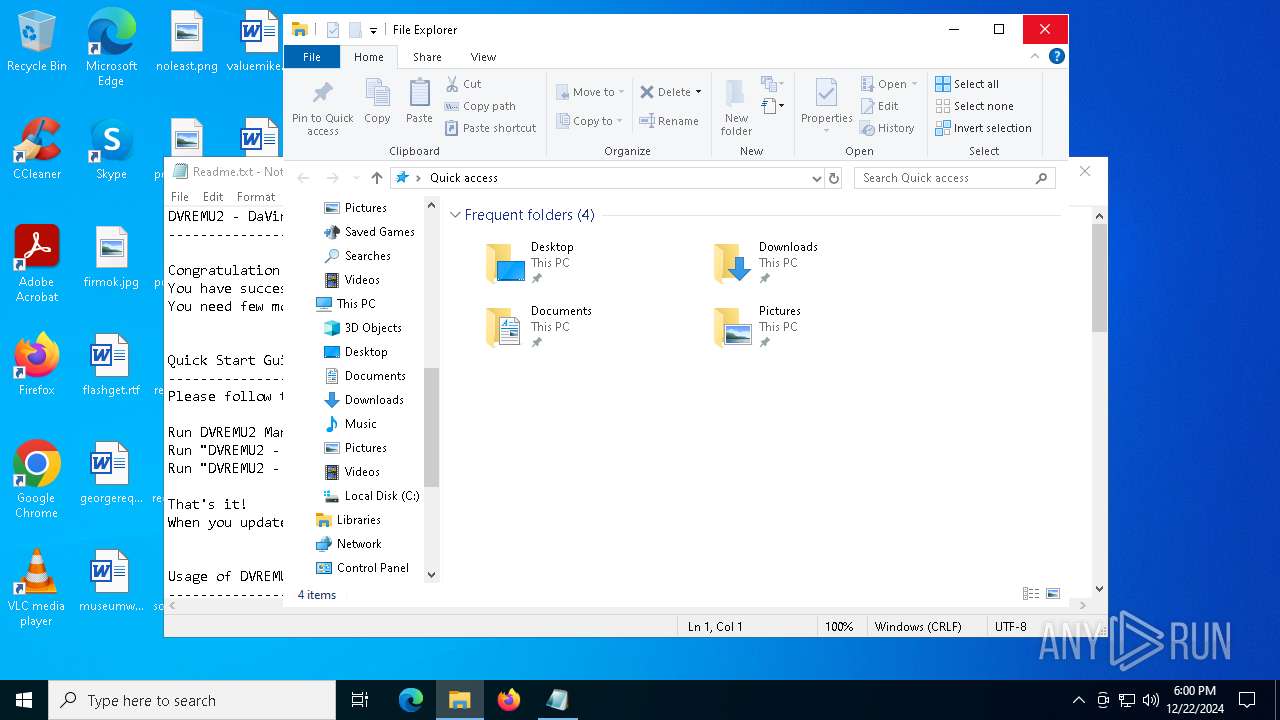
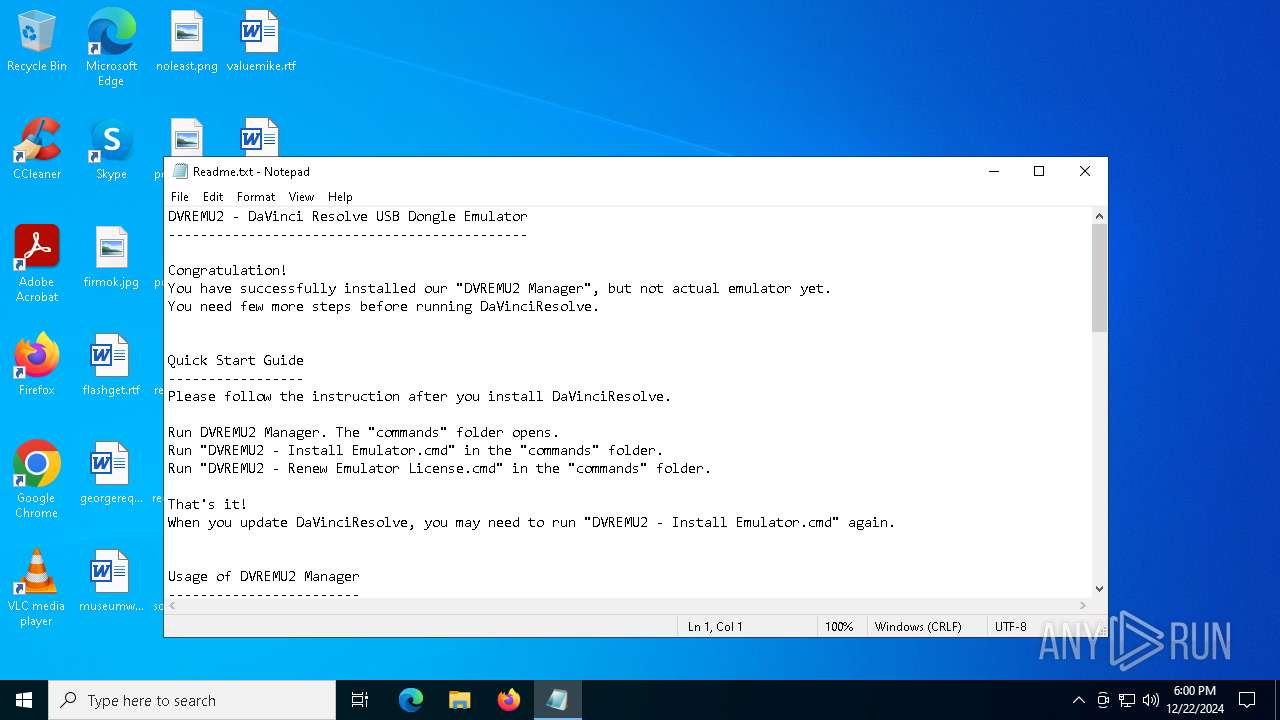
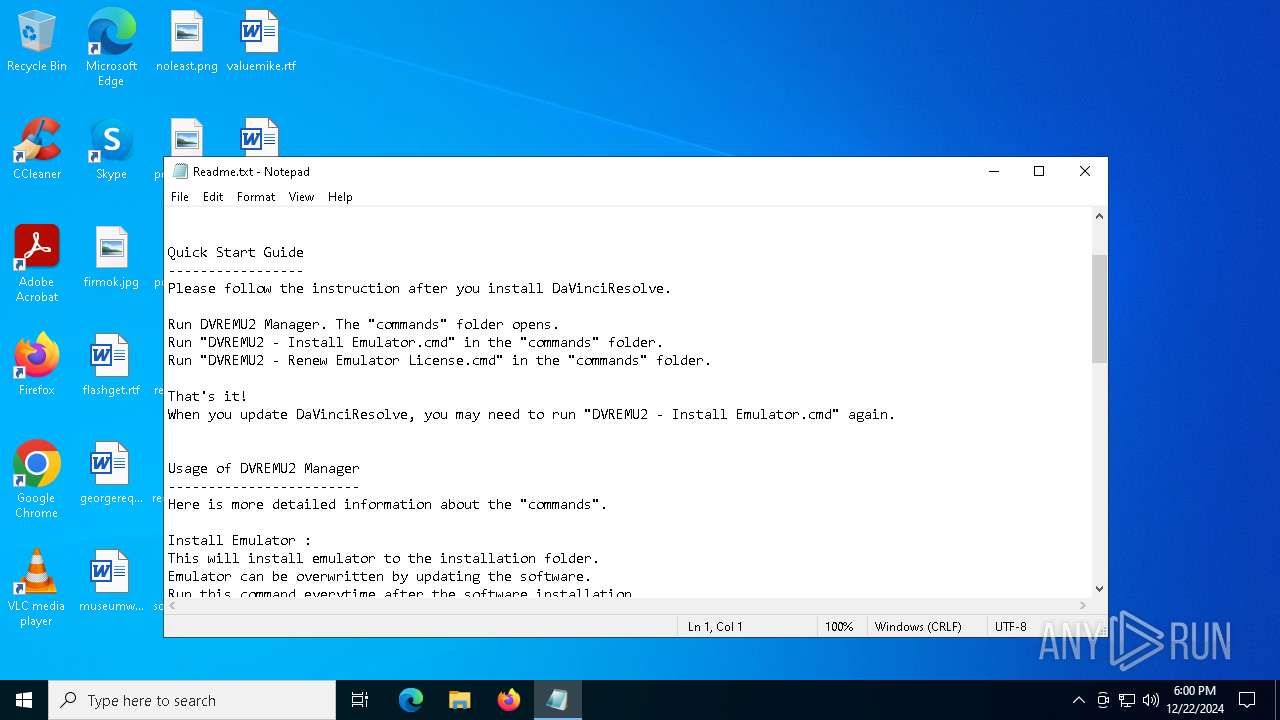
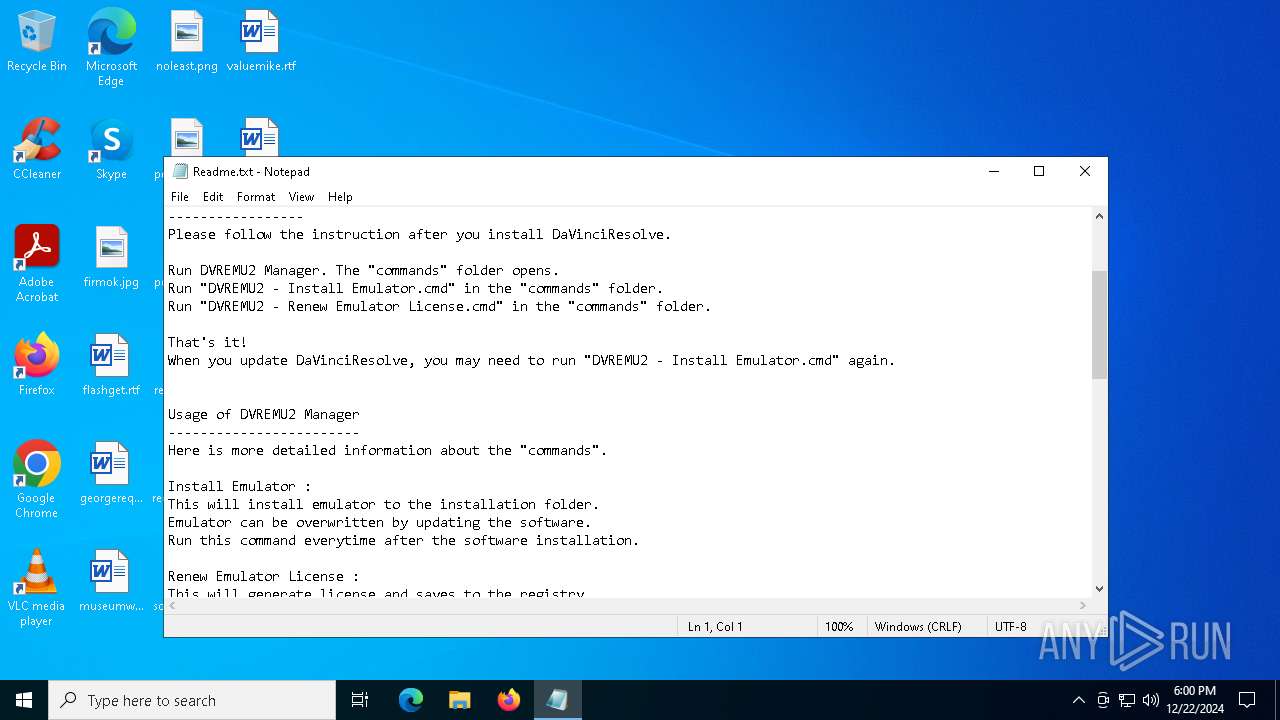
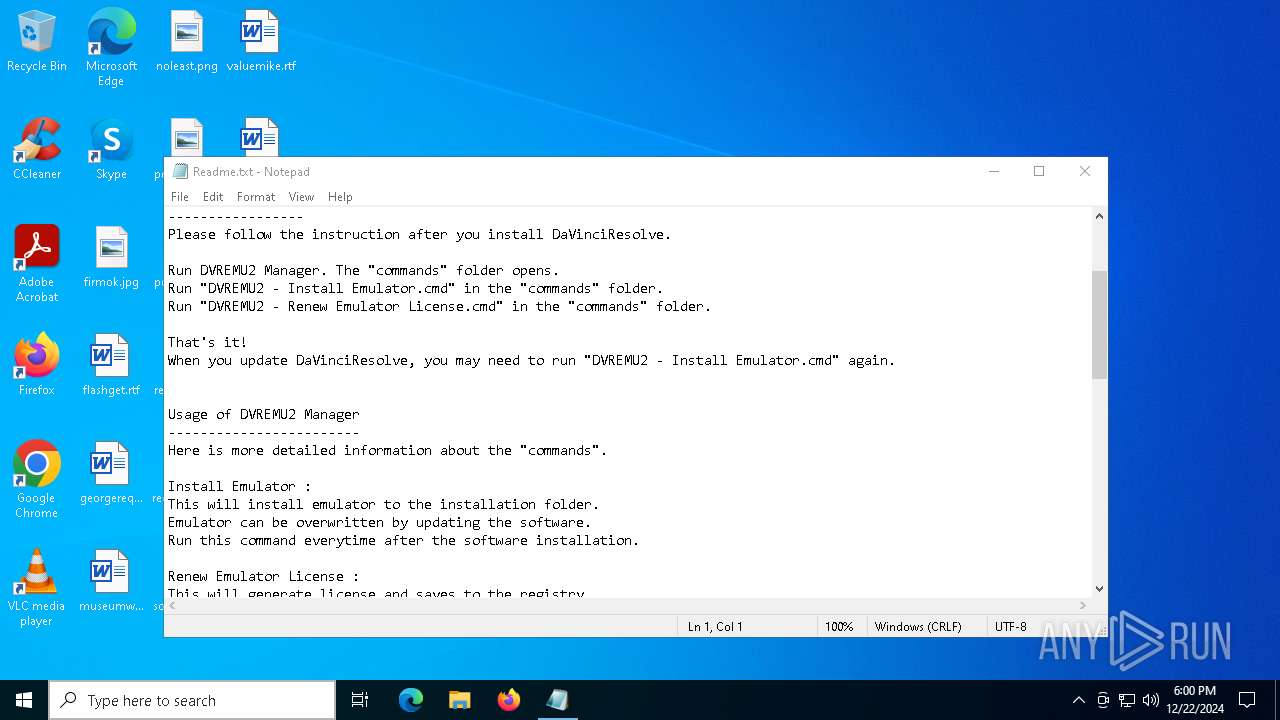
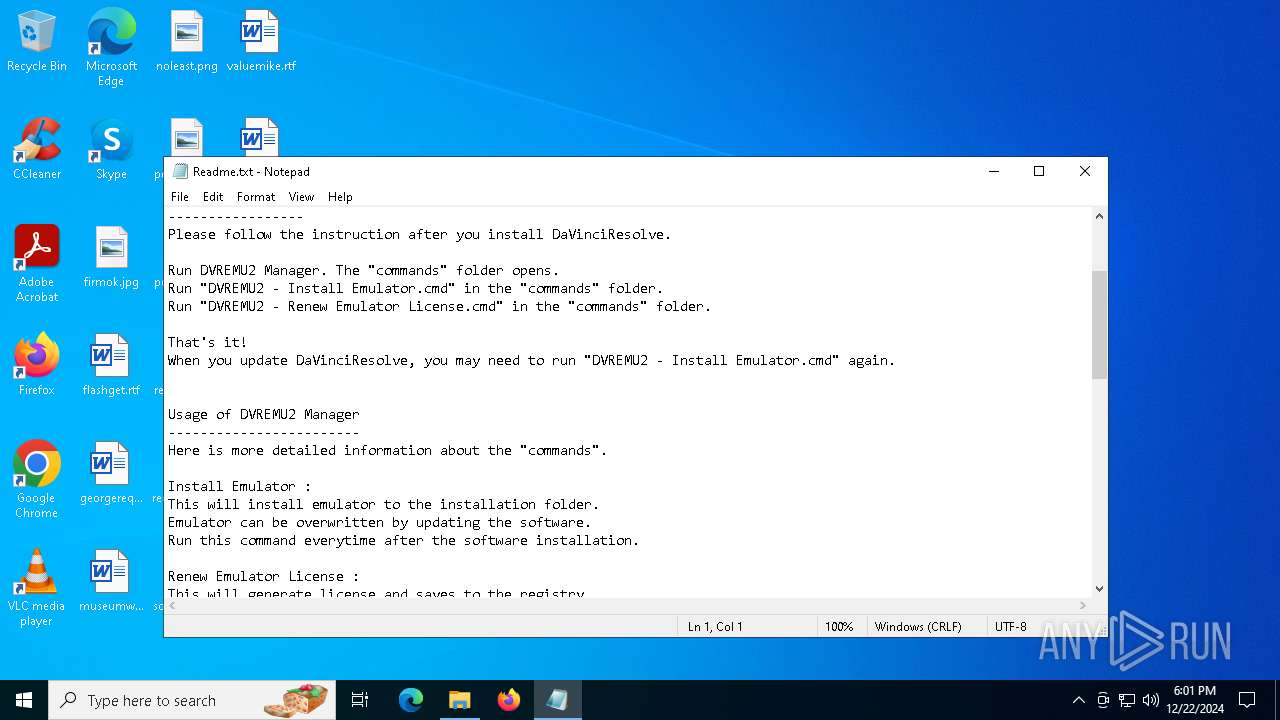
Start notepad (likely ransomware note)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Creates file in the systems drive root
- explorer.exe (PID: 7000)
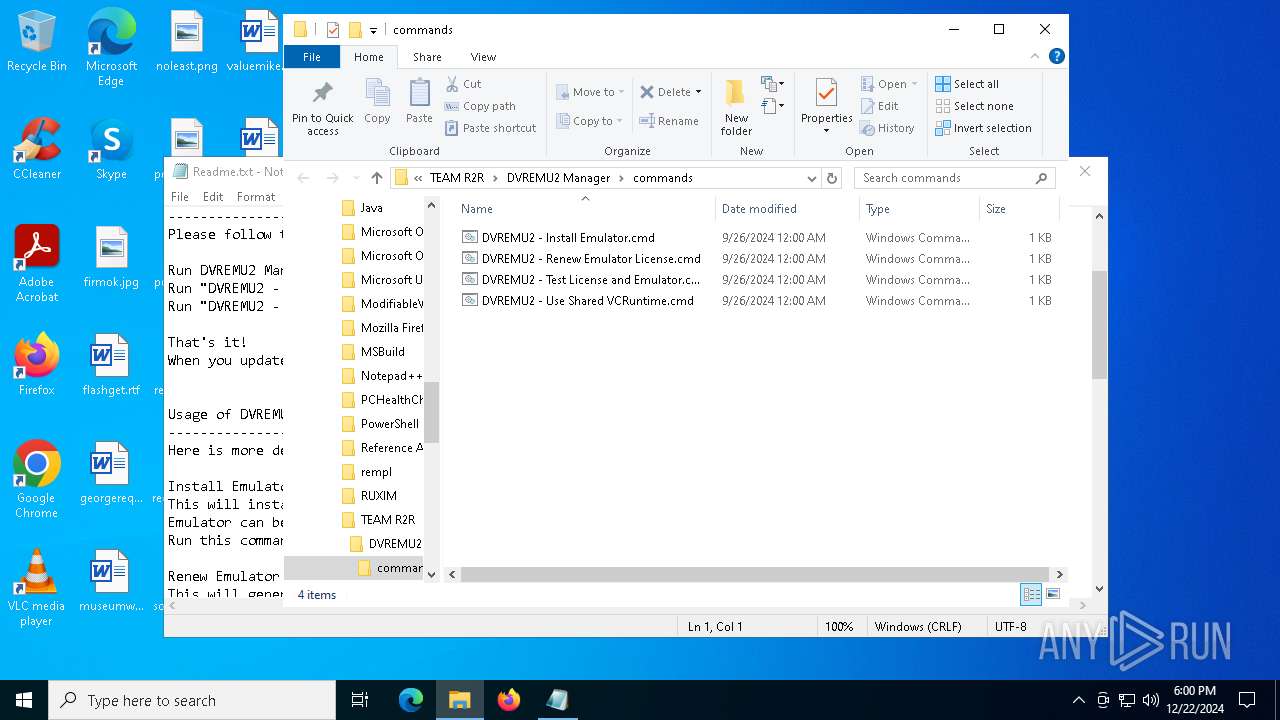
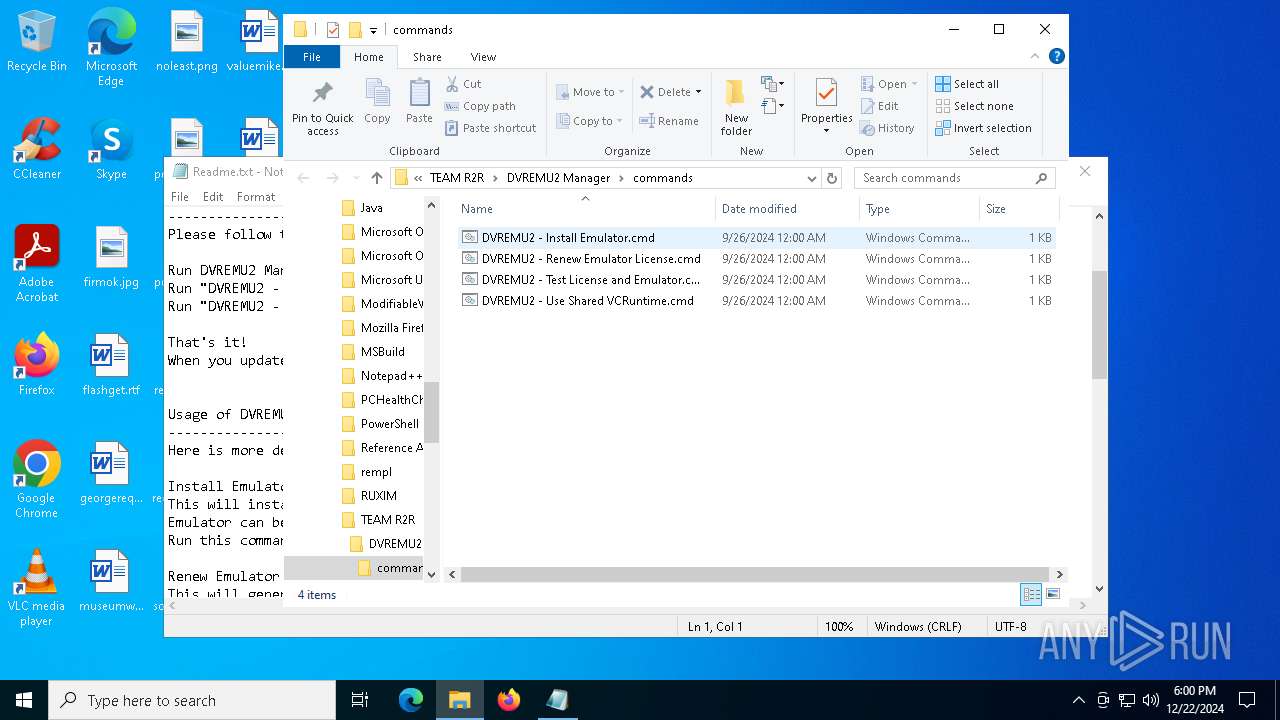
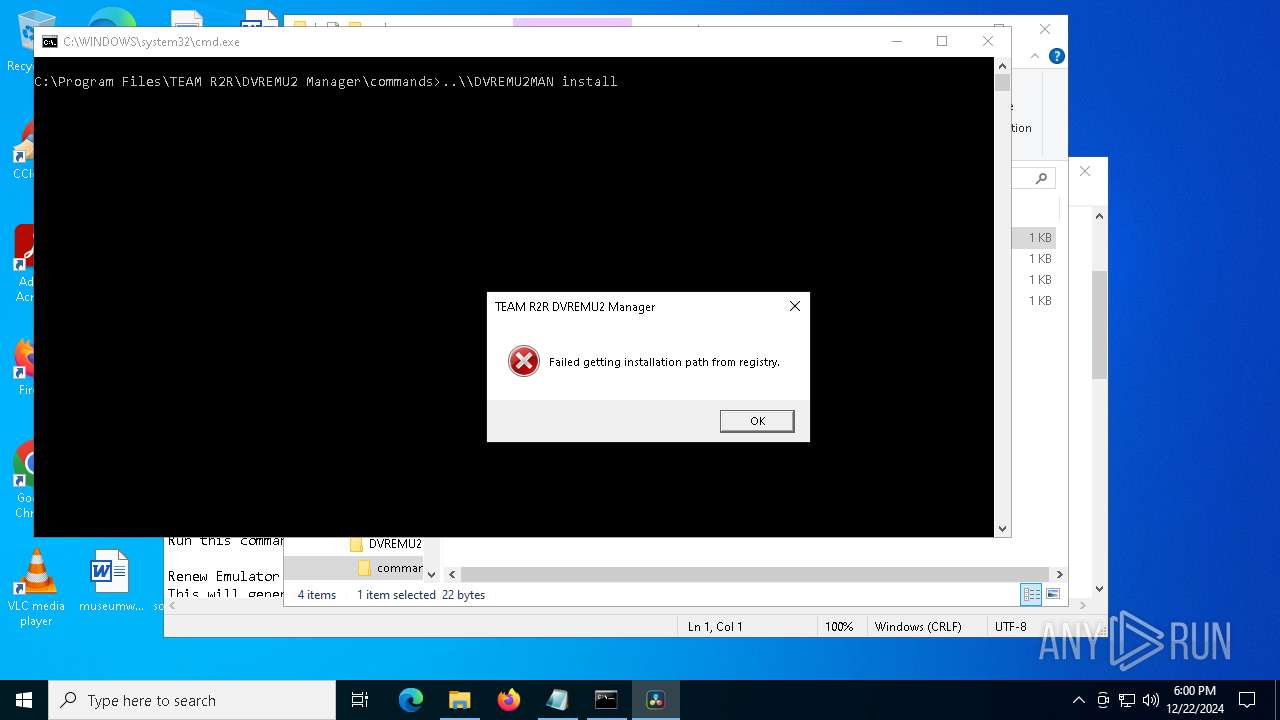
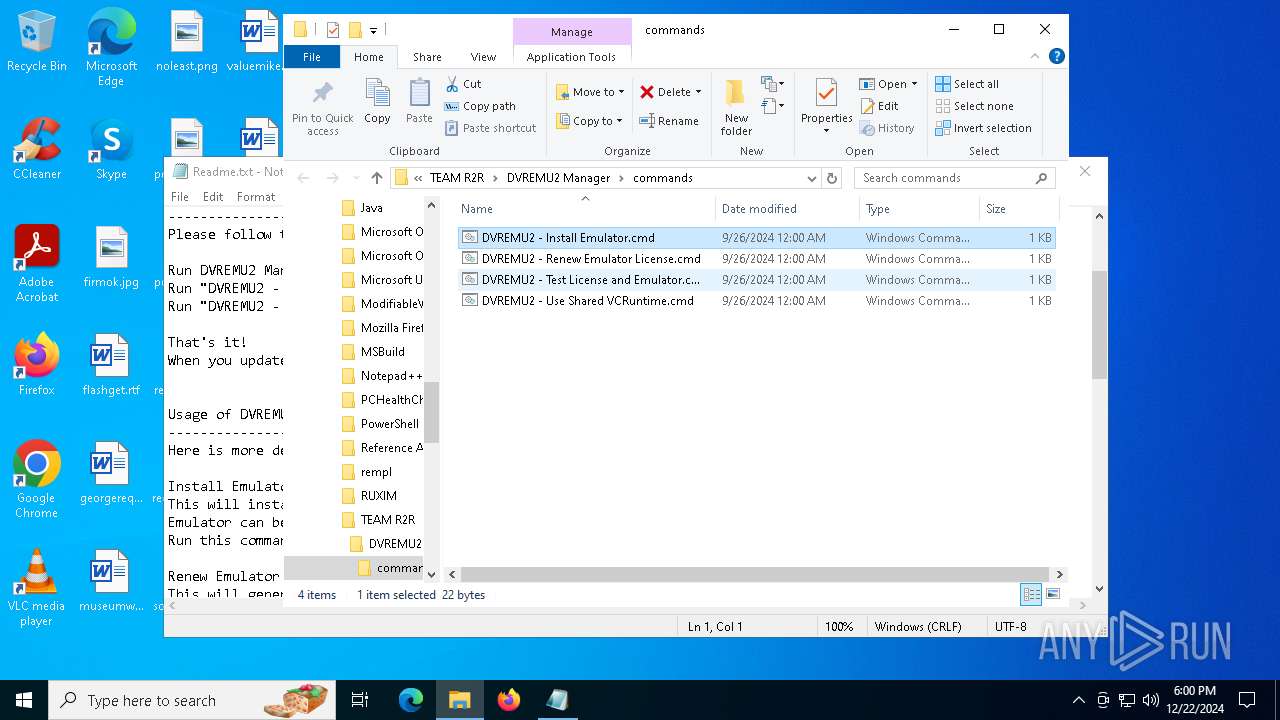
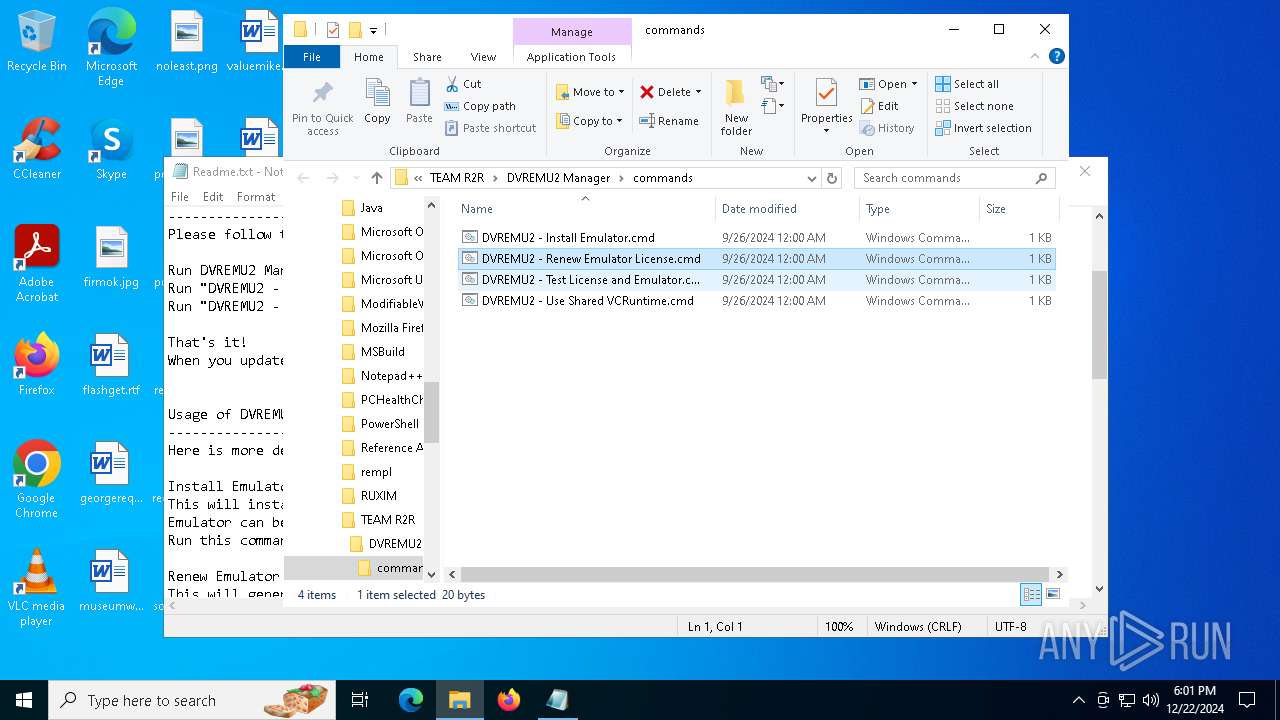
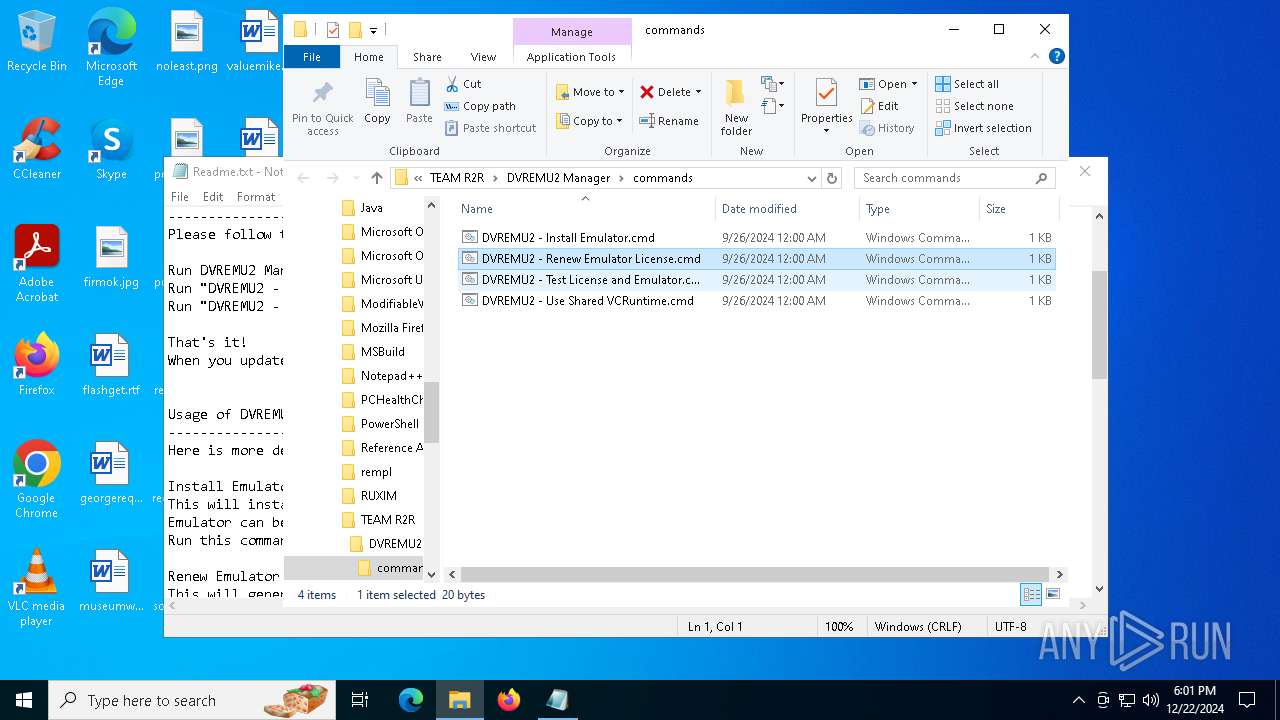
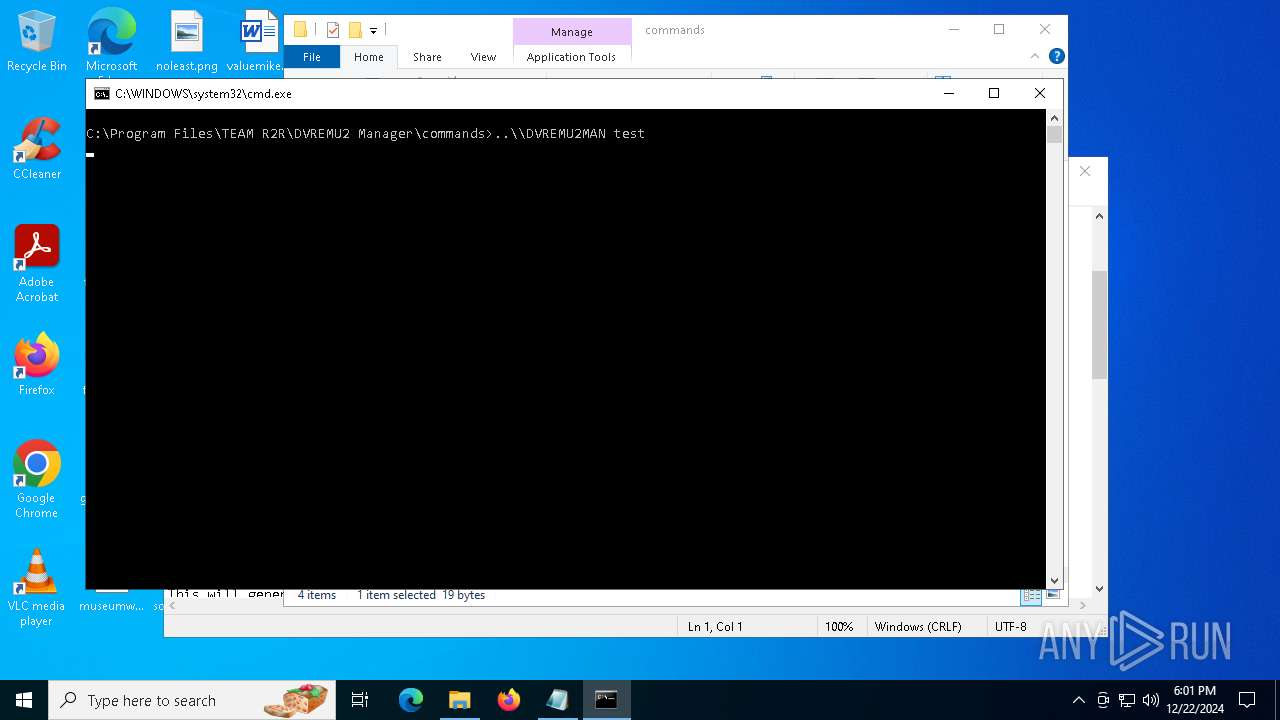
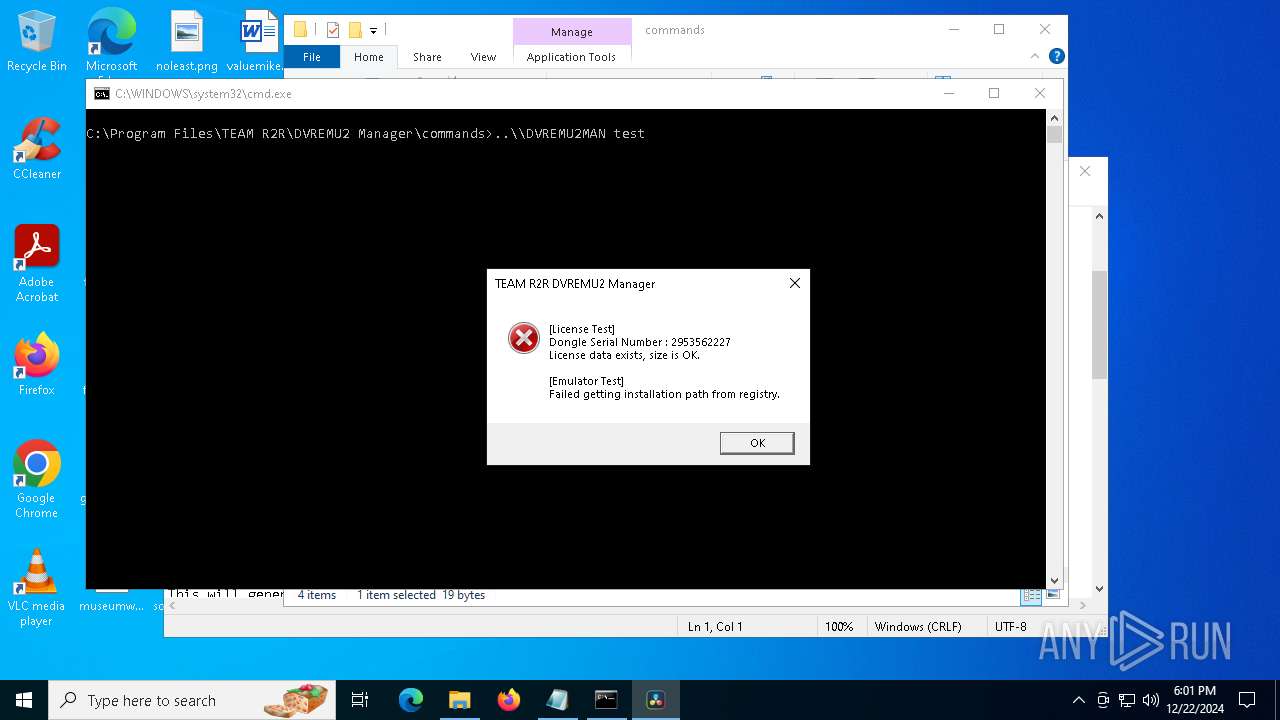
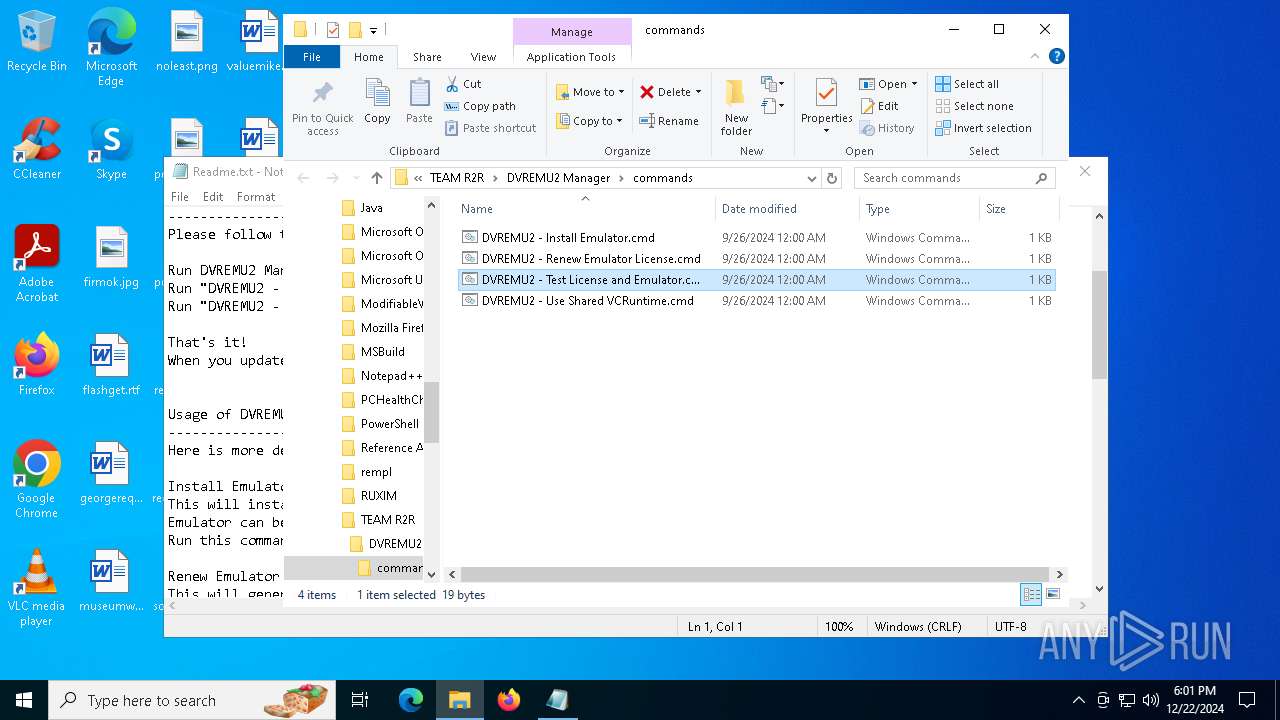
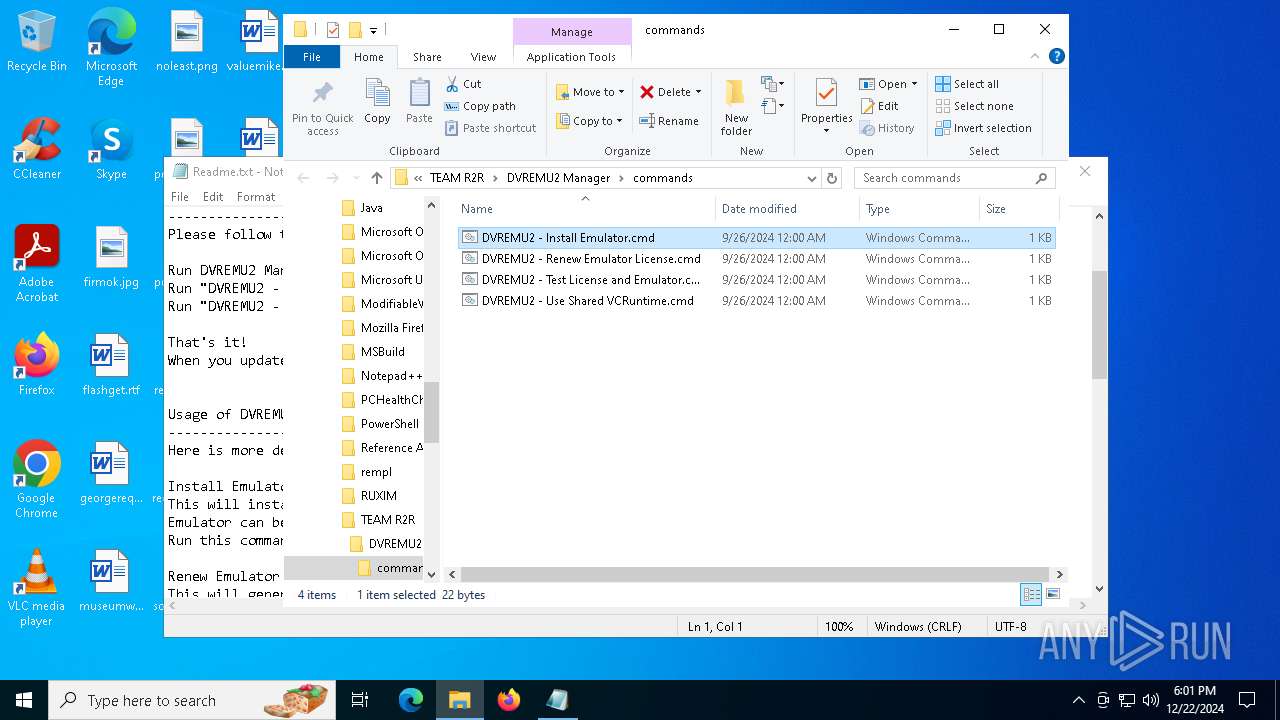
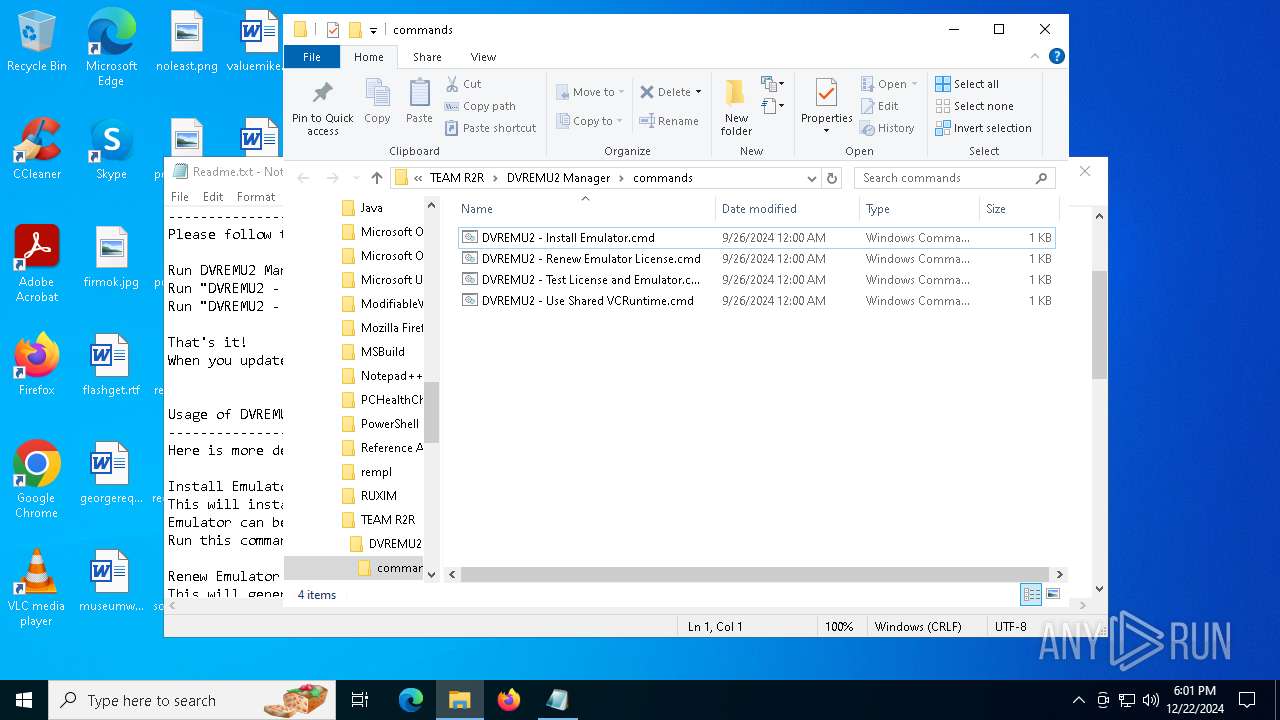
Executing commands from ".cmd" file
- explorer.exe (PID: 7000)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 7000)
Reads the date of Windows installation
- DVREMU2MAN.exe (PID: 6404)
INFO
Checks supported languages
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6660)
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6836)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6696)
- SearchApp.exe (PID: 5064)
- DVREMU2MAN.exe (PID: 6404)
- DVREMU2MAN.exe (PID: 6848)
- DVREMU2MAN.exe (PID: 6464)
- DVREMU2MAN.exe (PID: 7128)
- DVREMU2MAN.exe (PID: 6280)
Create files in a temporary directory
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6836)
- Setup DVREMU2 Manager v1.0.0.exe (PID: 6660)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Reads the computer name
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6696)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
- DVREMU2MAN.exe (PID: 6404)
- DVREMU2MAN.exe (PID: 6848)
- DVREMU2MAN.exe (PID: 6464)
- DVREMU2MAN.exe (PID: 7128)
- DVREMU2MAN.exe (PID: 6280)
Process checks computer location settings
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6696)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
- SearchApp.exe (PID: 5064)
- DVREMU2MAN.exe (PID: 6404)
The sample compiled with english language support
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6228)
- explorer.exe (PID: 7000)
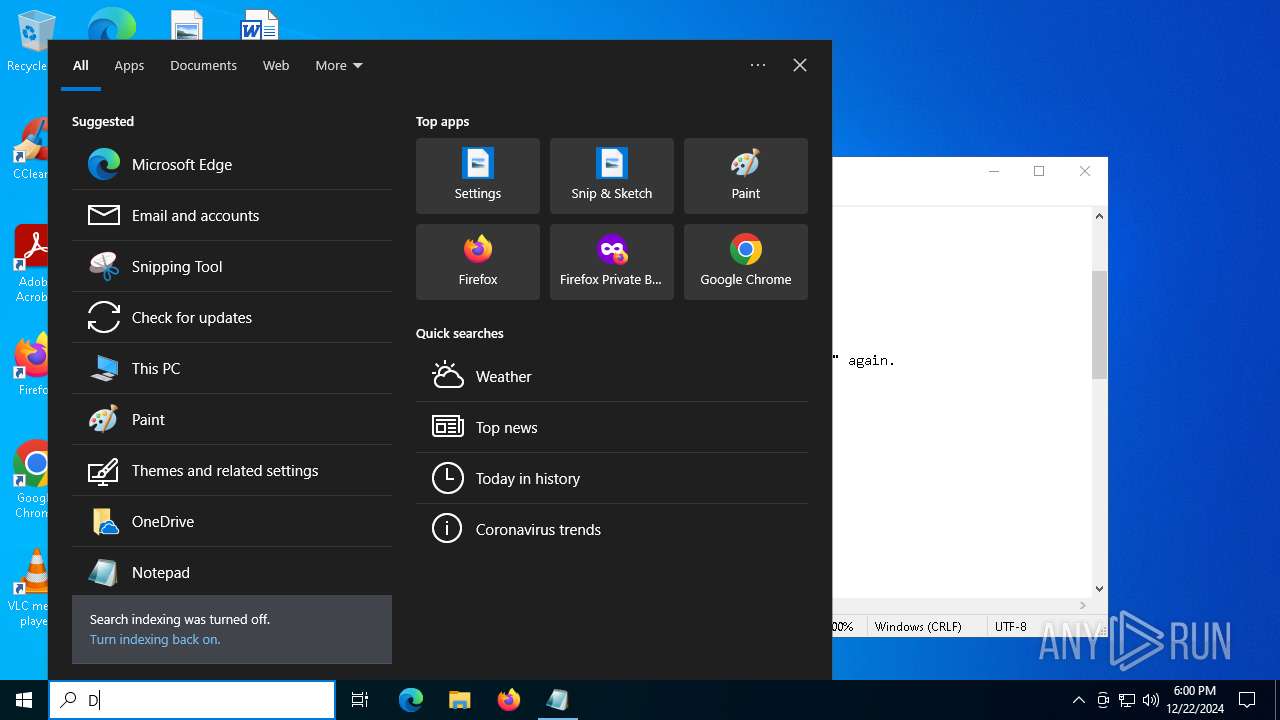
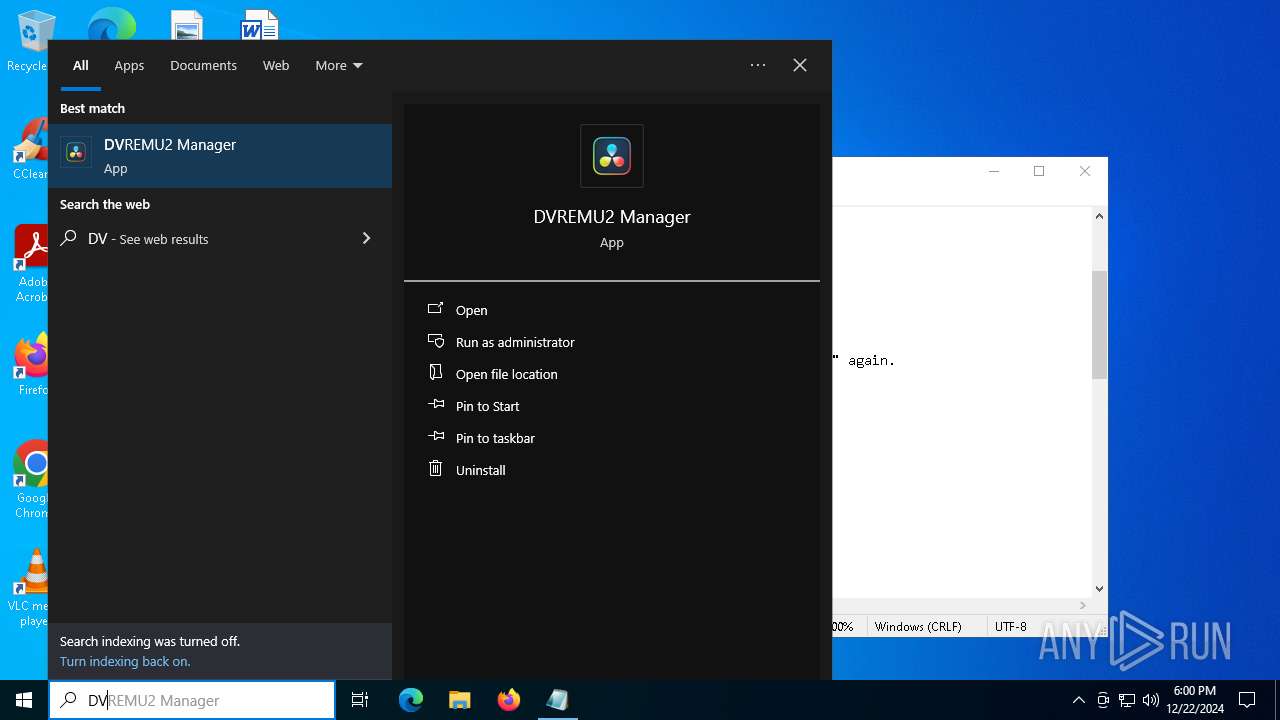
Manual execution by a user
- DVREMU2MAN.exe (PID: 6404)
- DVREMU2MAN.exe (PID: 1328)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
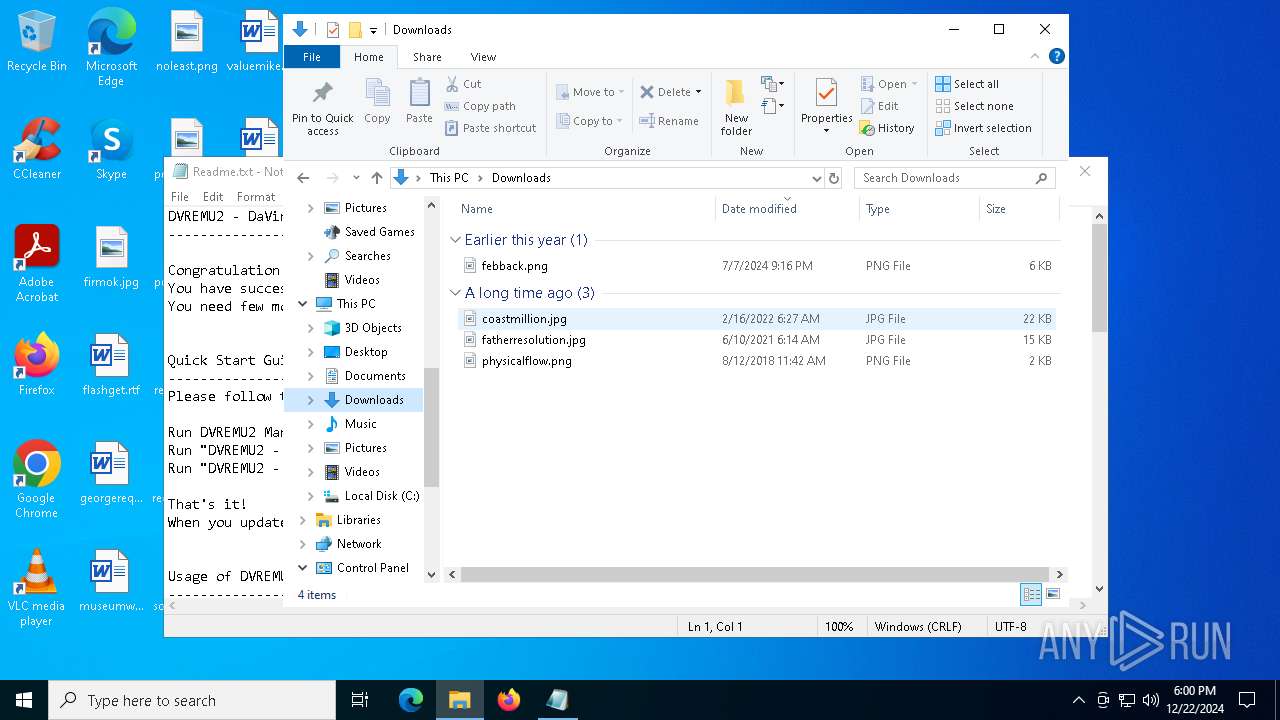
The process uses the downloaded file
- DVREMU2MAN.exe (PID: 6404)
- cmd.exe (PID: 736)
- explorer.exe (PID: 7000)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 644)
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- DVREMU2MAN.exe (PID: 6464)
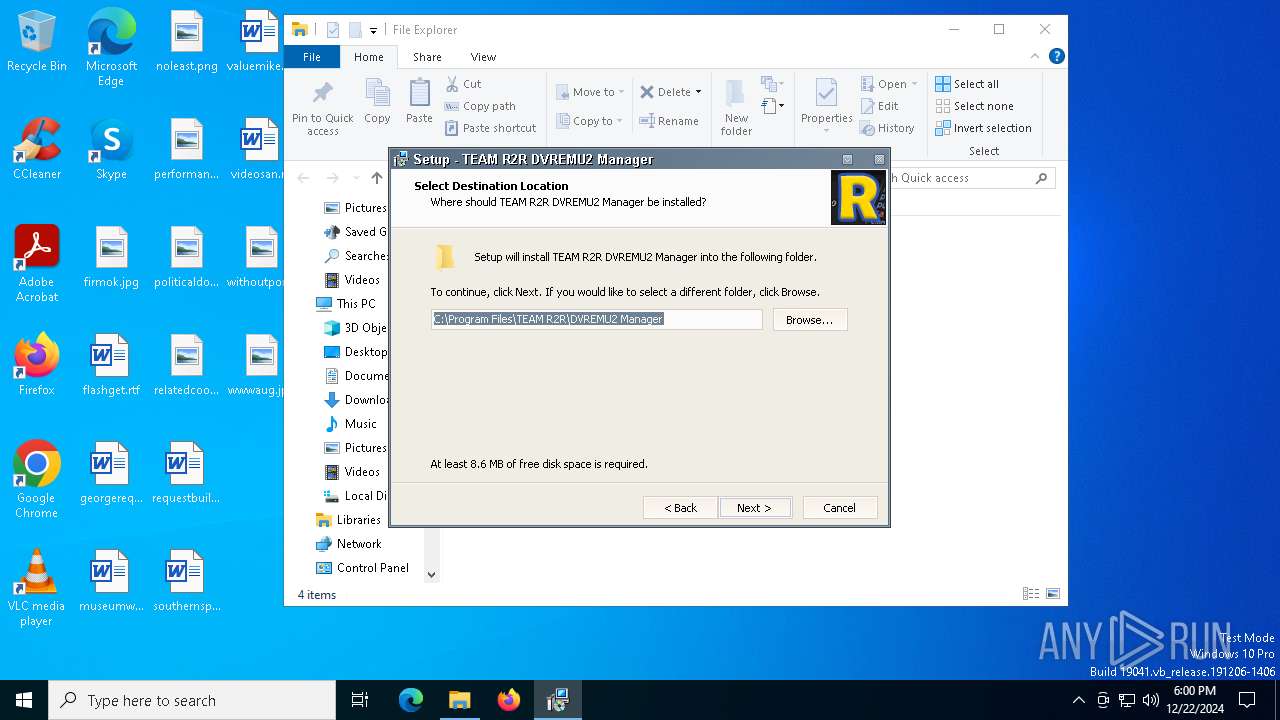
Creates files in the program directory
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Creates a software uninstall entry
- Setup DVREMU2 Manager v1.0.0.tmp (PID: 6872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (19) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 13:27:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
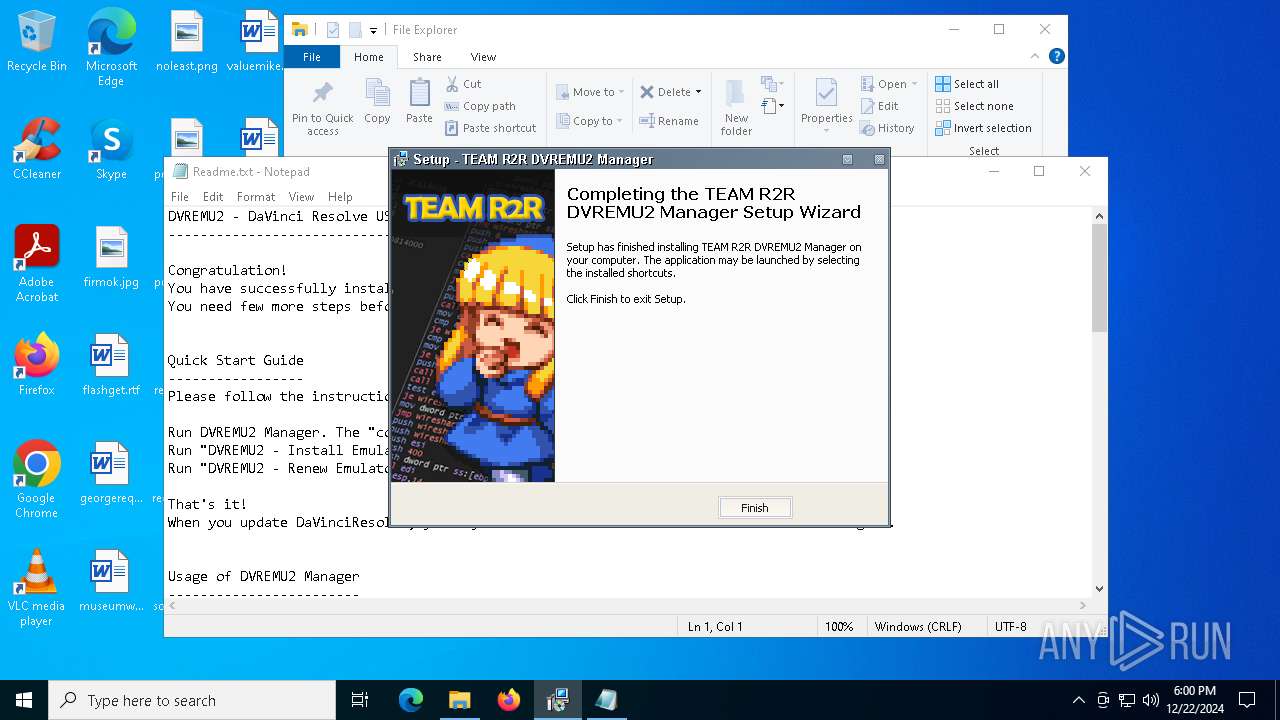
| CompanyName: | TEAM R2R |
| FileDescription: | TEAM R2R DVREMU2 Manager Setup |
| FileVersion: | 1.0.0 |
| LegalCopyright: | TEAM R2R |
| ProductName: | DVREMU2 Manager |
| ProductVersion: | 1.0.0 |
Total processes
167
Monitored processes
31
Malicious processes
5
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\TEAM R2R\DVREMU2 Manager\commands\DVREMU2 - Install Emulator.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\TEAM R2R\DVREMU2 Manager\commands\DVREMU2 - Install Emulator.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe" | C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe | — | explorer.exe | |||||||||||
User: admin Company: TEAM R2R Integrity Level: MEDIUM Description: DVREMU2 Manager Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2496 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\TEAM R2R\DVREMU2 Manager\commands\DVREMU2 - Renew Emulator License.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
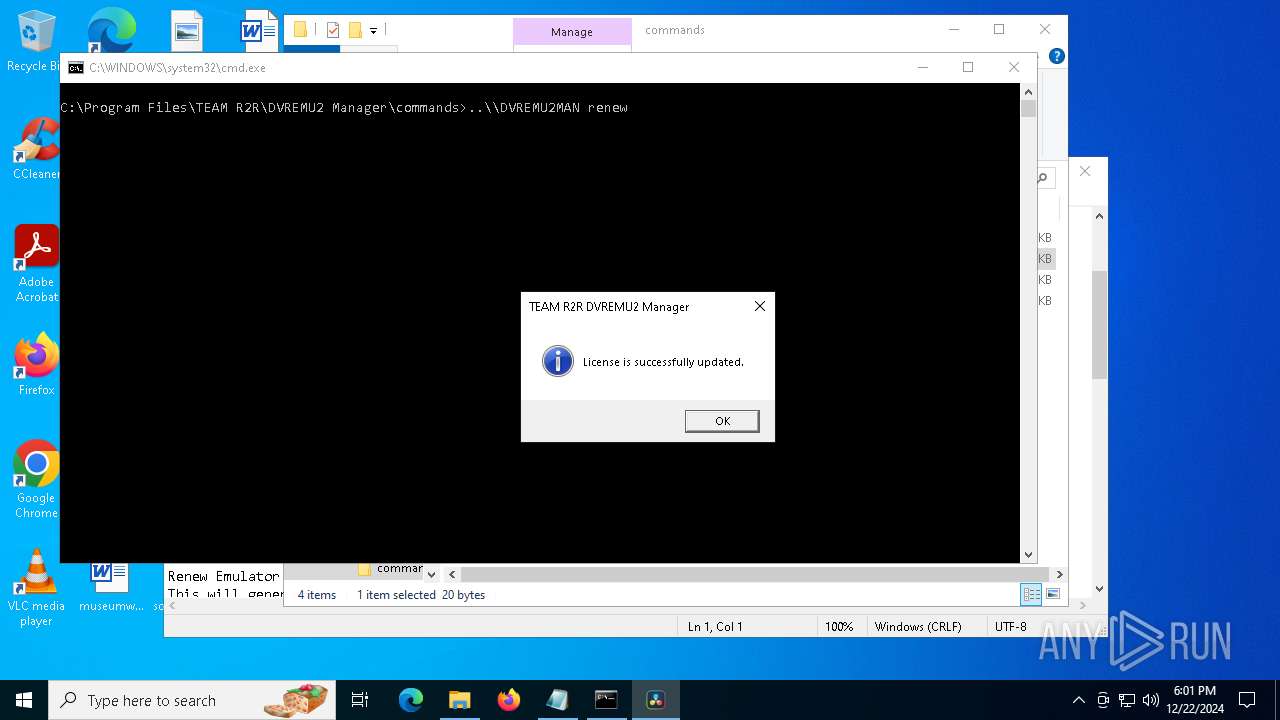
| 4228 | "C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe" renew | C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe | — | cmd.exe | |||||||||||
User: admin Company: TEAM R2R Integrity Level: MEDIUM Description: DVREMU2 Manager Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 4328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4328 | "C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe" install | C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe | — | cmd.exe | |||||||||||
User: admin Company: TEAM R2R Integrity Level: MEDIUM Description: DVREMU2 Manager Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
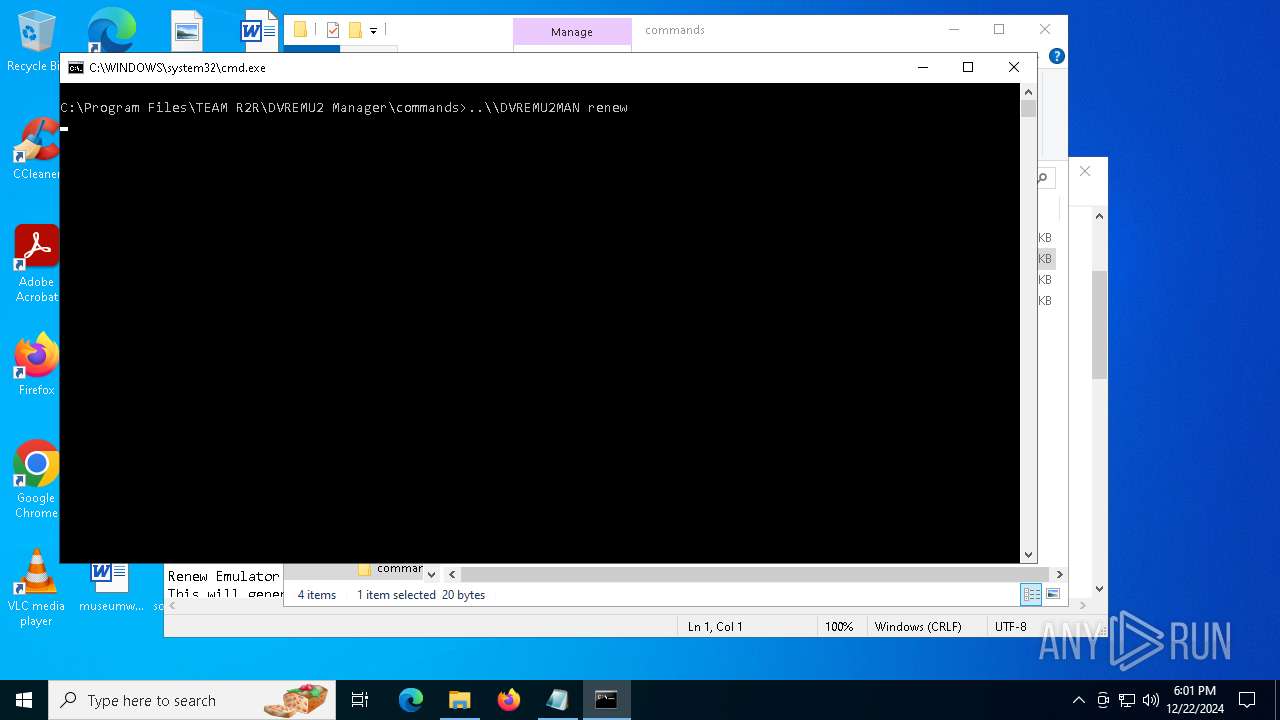
| 4520 | ..\\DVREMU2MAN renew | C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe | — | cmd.exe | |||||||||||
User: admin Company: TEAM R2R Integrity Level: MEDIUM Description: DVREMU2 Manager Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
21 576
Read events
21 437
Write events
134
Delete events
5
Modification events
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\TEAM R2R\DVREMU2 Manager | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\TEAM R2R\DVREMU2 Manager\ | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: TEAM R2R\DVREMU2 Manager | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: data | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: shortcutapp | |||
| (PID) Process: | (6872) Setup DVREMU2 Manager v1.0.0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TEAM R2R DVREMU2 Manager_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
Executable files
16
Suspicious files
55
Text files
103
Unknown types
2
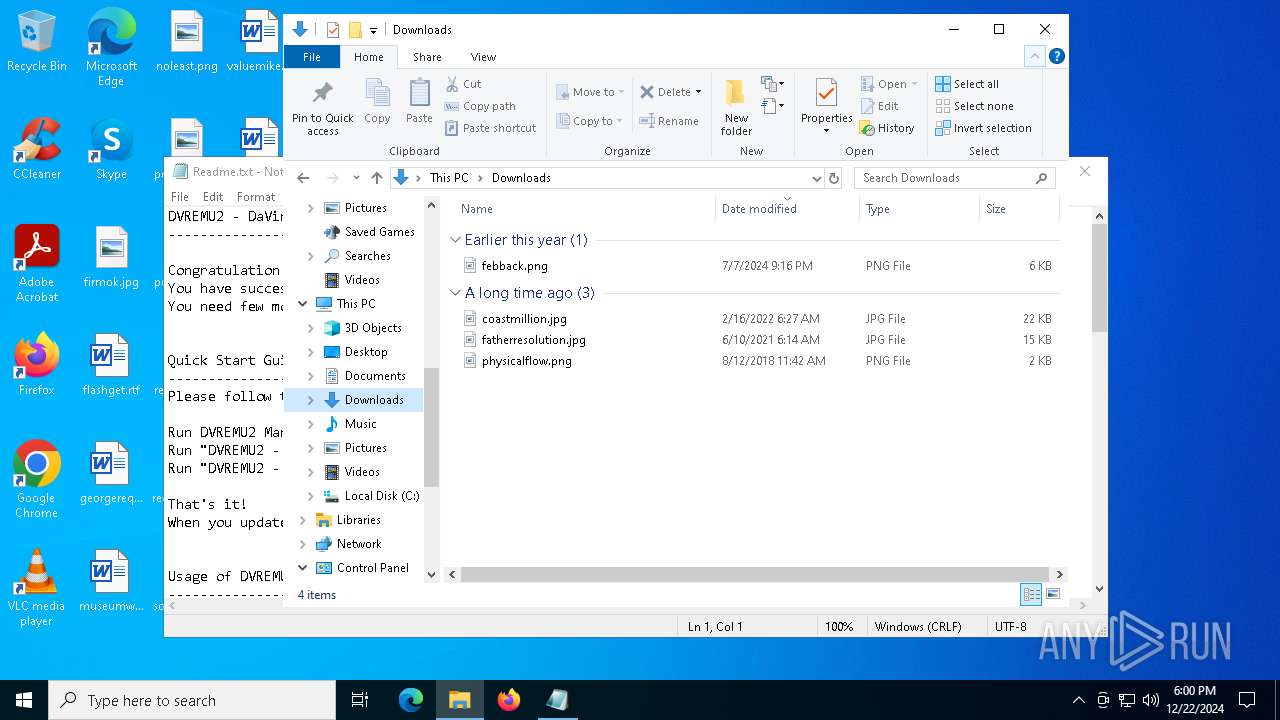
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6660 | Setup DVREMU2 Manager v1.0.0.exe | C:\Users\admin\AppData\Local\Temp\is-Q2ASH.tmp\Setup DVREMU2 Manager v1.0.0.tmp | executable | |
MD5:34ACC2BDB45A9C436181426828C4CB49 | SHA256:9C81817ACD4982632D8C7F1DF3898FCA1477577738184265D735F49FC5480F07 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\is-M1P2C.tmp | executable | |
MD5:2A052D9B7BDD115E24B7BC4B8475EDCE | SHA256:2083BEB78B4CEBA4A8FE819ED2307B4C0A22622F32CAEA60FCEA7DE0BCBD76B8 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Users\admin\AppData\Local\Temp\is-B2GND.tmp\R2RINNO.dll | executable | |
MD5:5DF8ADA84A16F5DFC24096EF90A5CE3A | SHA256:48A9C8C332FDE541B571D9D522D0E37834B452F55AF8CBDC341B12222E78FB5B | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Users\admin\AppData\Local\Temp\is-B2GND.tmp\ISSKINU.DLL | executable | |
MD5:F30AFCCD6FAFC1CAD4567ADA824C9358 | SHA256:E28D16FAD16BCA8198C47D7DD44ACFD362DD6BA1654F700ADD8AAF2C0732622D | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\is-IB3N5.tmp | text | |
MD5:0DE76EA95B6ECF3866D834FA1B078018 | SHA256:632E2772F9536A30DDA7E1F61F267CCEC1AAC7DD5F568260377C0573570A32A8 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\is-Q35RH.tmp | executable | |
MD5:E7463D58D7AFF43C7D71A3847BA8201E | SHA256:2249476A14DEA73AE271D661483BDC6C15E45B931F8DBFD0BD1B84193CF420EA | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\is-G073H.tmp | executable | |
MD5:908F64B344BCE85C344E88DB0C4C334F | SHA256:6BDC1C8F0A1BD5951E94F575E6B693D0150D25F3B62BC7314567B2C4C3A8F009 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\libbz2.dll | executable | |
MD5:B6C39AB833A3BC29183D0633BB9421AB | SHA256:57D9CB6E10BA90A3B8E9C2B2EAB2B80937B088123ADB482EAB71EF550CCE7794 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\DVREMU2MAN.exe | executable | |
MD5:2A052D9B7BDD115E24B7BC4B8475EDCE | SHA256:2083BEB78B4CEBA4A8FE819ED2307B4C0A22622F32CAEA60FCEA7DE0BCBD76B8 | |||
| 6872 | Setup DVREMU2 Manager v1.0.0.tmp | C:\Program Files\TEAM R2R\DVREMU2 Manager\unins000.exe | executable | |
MD5:908F64B344BCE85C344E88DB0C4C334F | SHA256:6BDC1C8F0A1BD5951E94F575E6B693D0150D25F3B62BC7314567B2C4C3A8F009 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
46
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
1684 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
1684 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
6428 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2396 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.209.141:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |