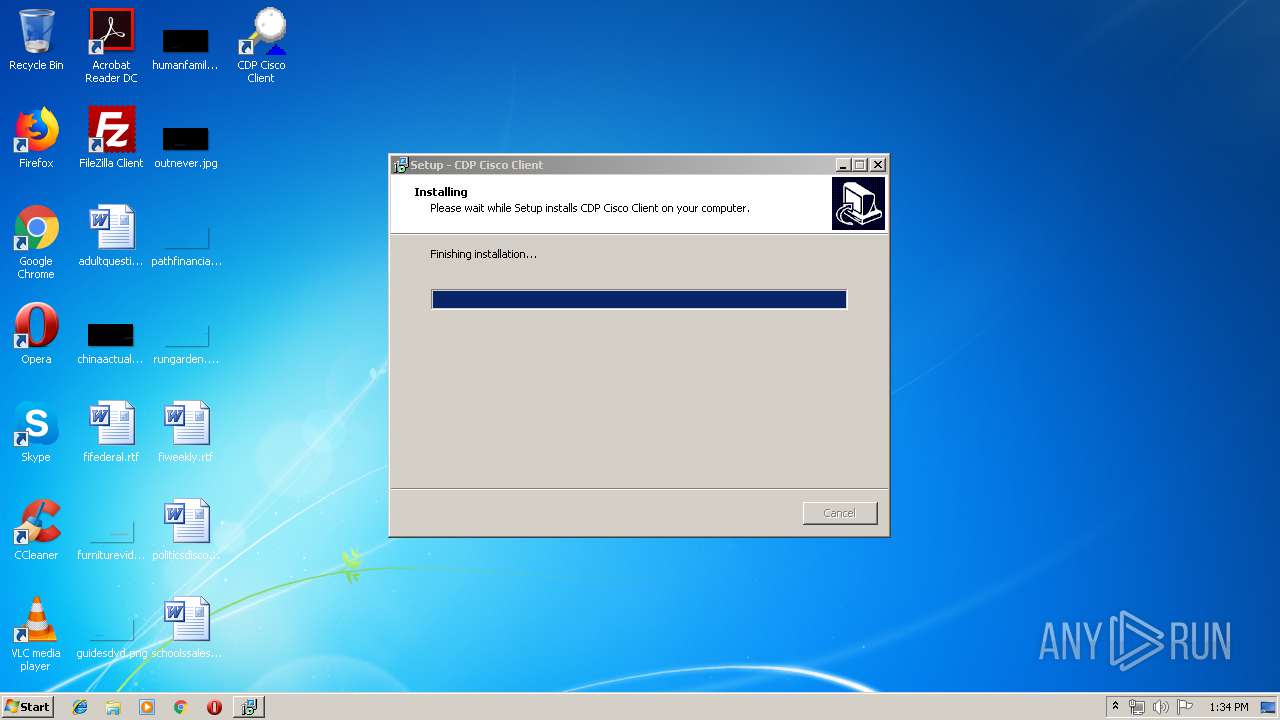
| File name: | cdpclient_setup.exe |
| Full analysis: | https://app.any.run/tasks/ae9cd02d-7edb-45cc-ac7f-9d16fab4ca4f |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 12:33:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0D770B5F1D8C593D5F1EE4EA9A096C30 |
| SHA1: | 13A658804235D5F360928B0D03C7BB31F9878B55 |
| SHA256: | 8D25412DE577569C9C56B5BF3598C4EEE43D770FEB22BFD52E90F3117A8302B1 |
| SSDEEP: | 24576:CQi1RYLm3//fcg1niFhMha2YcufzfZYHce00Od1Y6Ozbsl2Ad4gqQkIAVlONTGMs:C9wLY/8QgGhTYlfZice07cVboCGpf8 |
MALICIOUS
Loads dropped or rewritten executable
- winpcap.exe (PID: 2760)
- CDPService.exe (PID: 3308)
- CDPclient.exe (PID: 3312)
Application was dropped or rewritten from another process
- winpcap.exe (PID: 2760)
- CDPService.exe (PID: 3796)
- CDPService.exe (PID: 3308)
- CDPclient.exe (PID: 3312)
Starts NET.EXE for service management
- winpcap.exe (PID: 2760)
SUSPICIOUS
Executable content was dropped or overwritten
- cdpclient_setup.exe (PID: 296)
- cdpclient_setup.exe (PID: 1076)
- winpcap.exe (PID: 2760)
- cdpclient_setup.tmp (PID: 3504)
Creates files in the Windows directory
- winpcap.exe (PID: 2760)
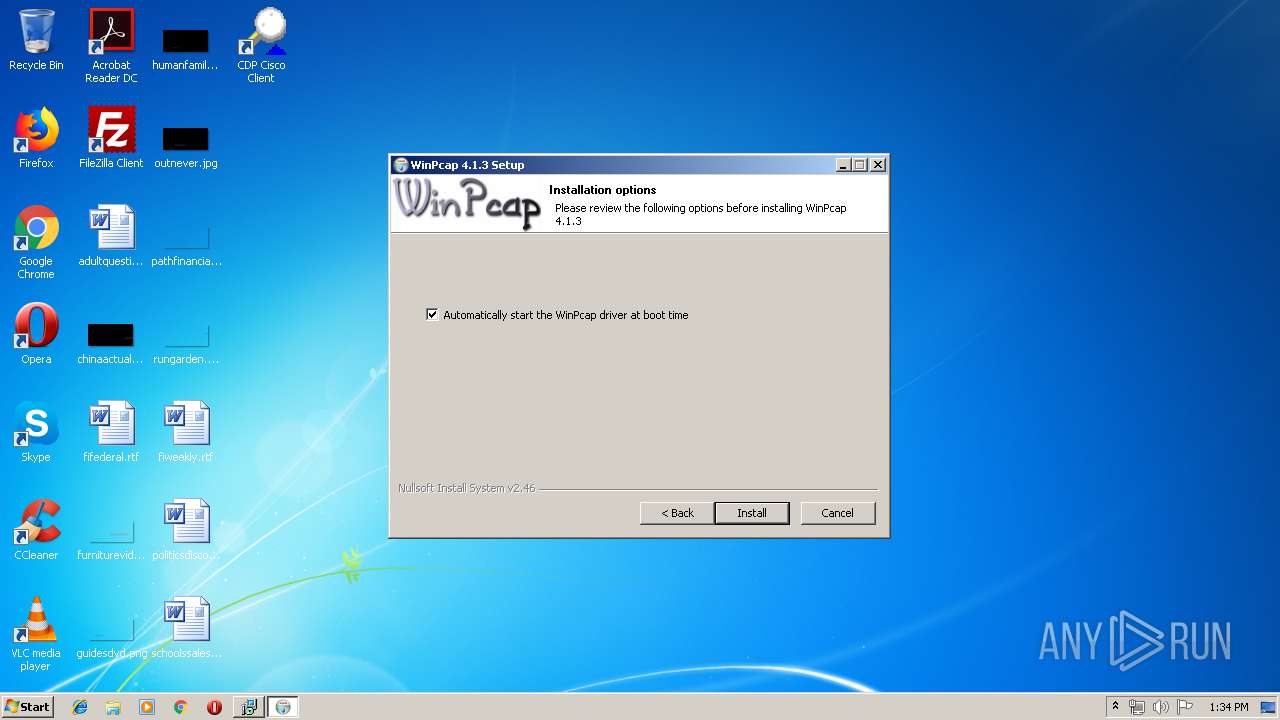
Creates or modifies windows services
- winpcap.exe (PID: 2760)
Creates files in the driver directory
- winpcap.exe (PID: 2760)
Creates files in the program directory
- winpcap.exe (PID: 2760)
Creates a software uninstall entry
- winpcap.exe (PID: 2760)
Reads Internet Cache Settings
- CDPclient.exe (PID: 3312)
INFO
Application was dropped or rewritten from another process
- cdpclient_setup.tmp (PID: 2128)
- cdpclient_setup.tmp (PID: 3504)
Loads dropped or rewritten executable
- cdpclient_setup.tmp (PID: 3504)
Creates a software uninstall entry
- cdpclient_setup.tmp (PID: 3504)
Creates files in the program directory
- cdpclient_setup.tmp (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
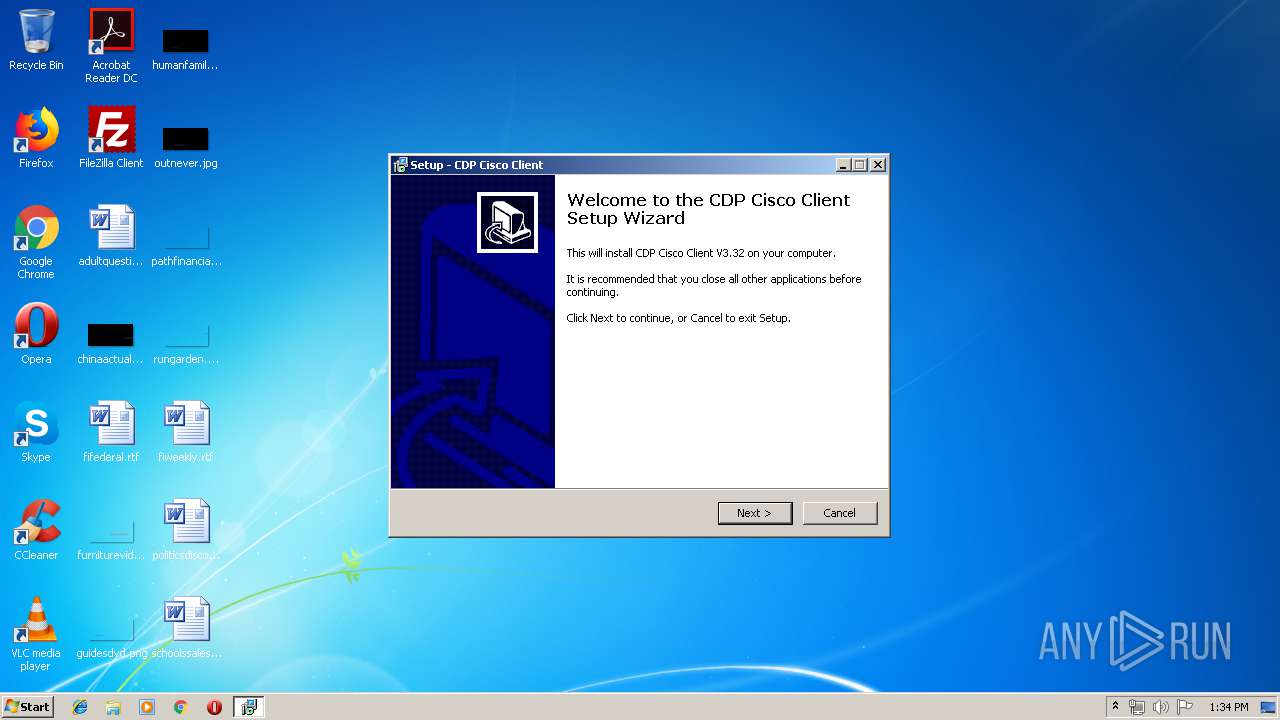
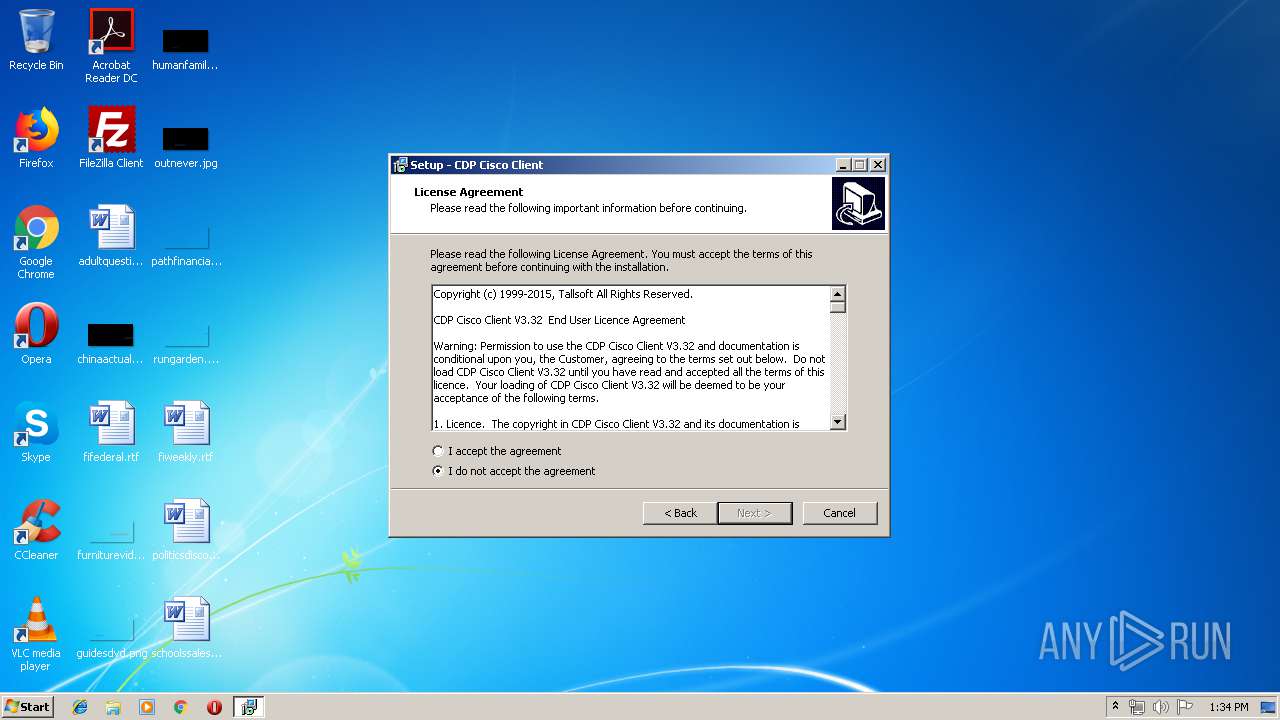
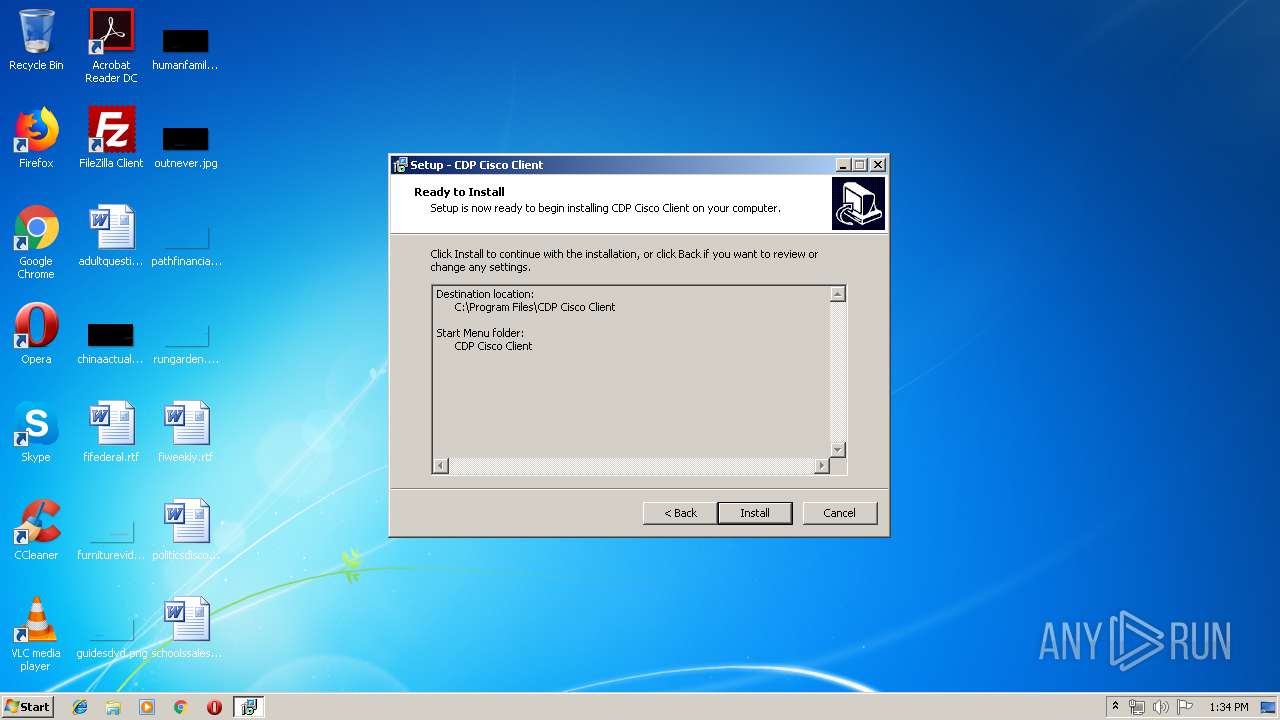
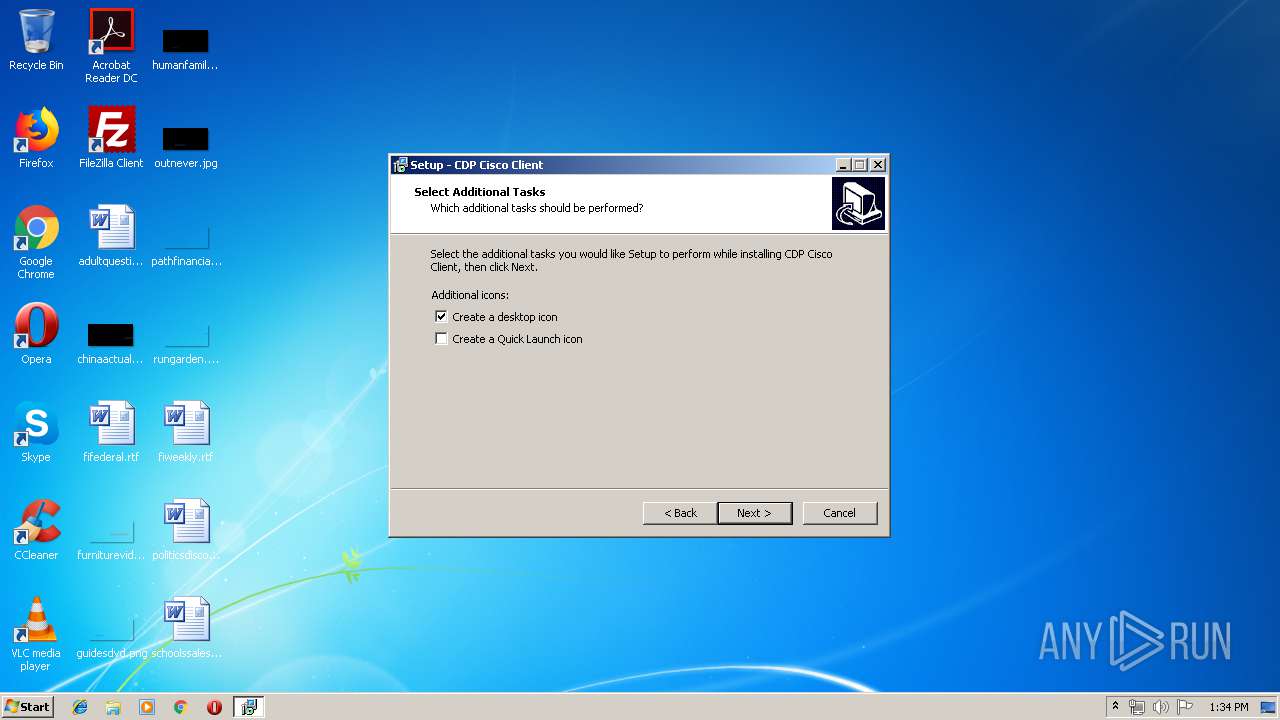
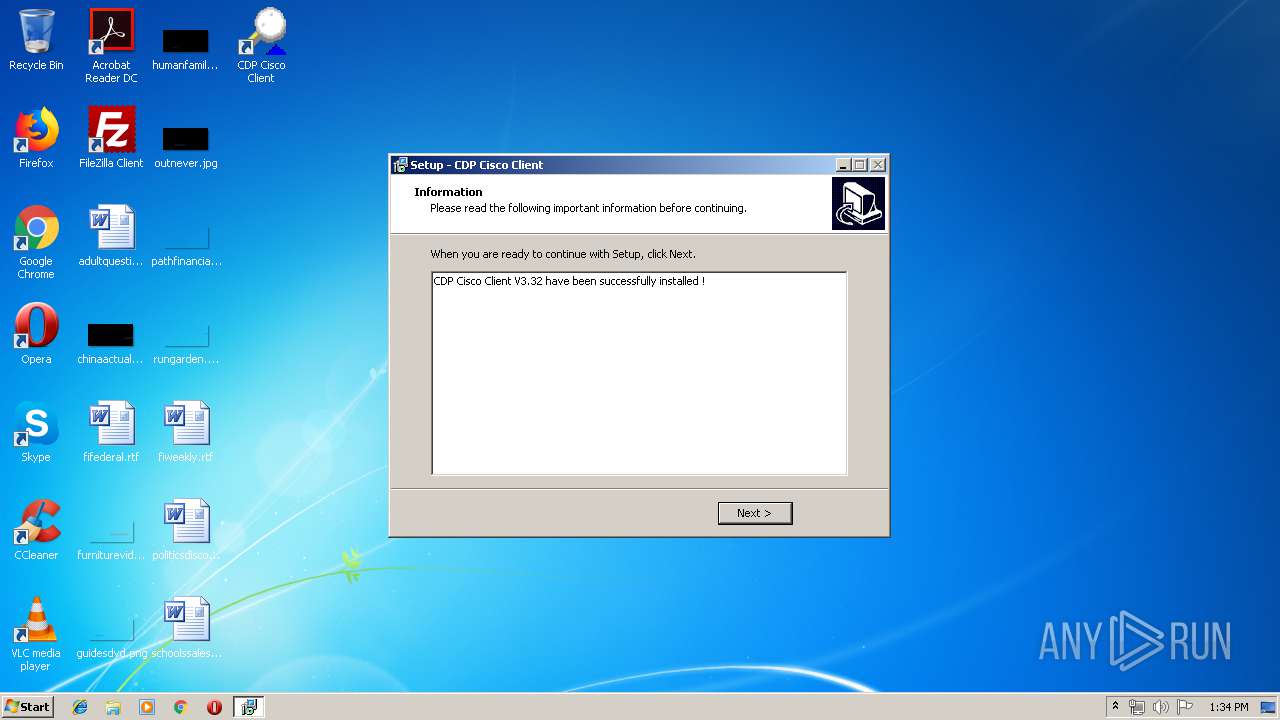
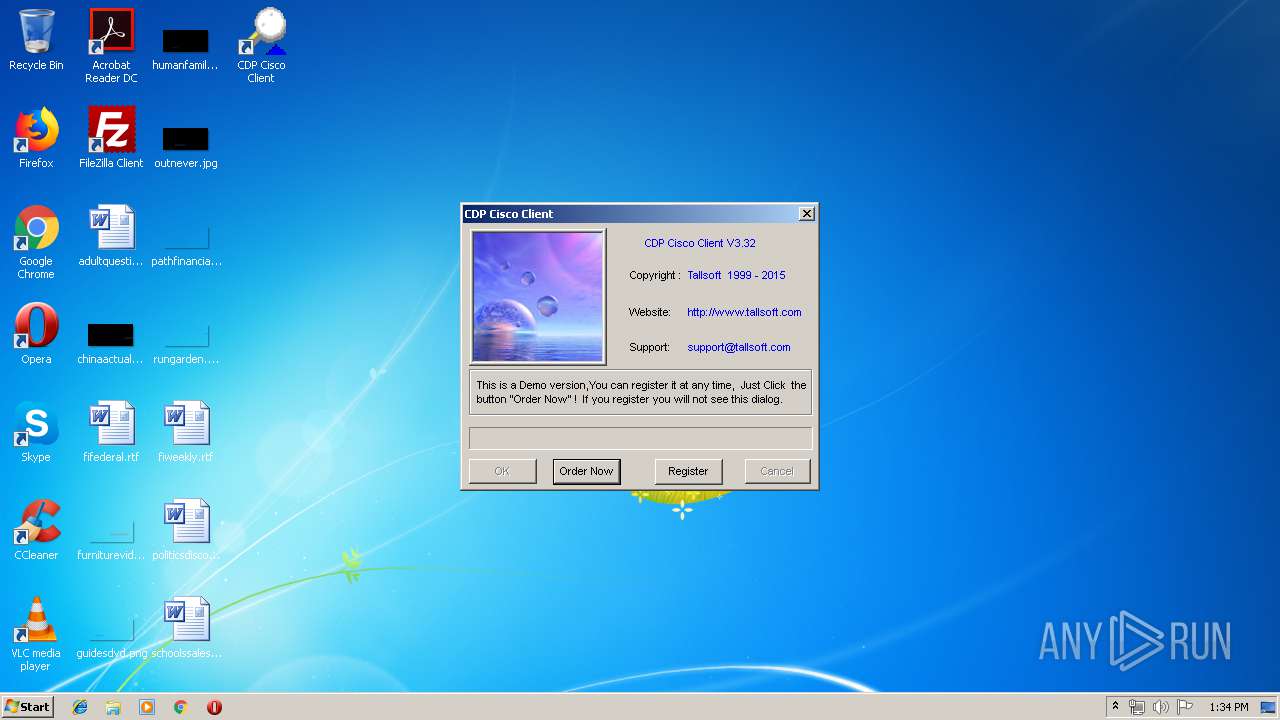
| CompanyName: | Tallsoft, Inc. |
| FileDescription: | CDP Cisco Client Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | CDP Cisco Client |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Tallsoft, Inc. |
| FileDescription: | CDP Cisco Client Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | CDP Cisco Client |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63177 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.54155 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
46
Monitored processes
10
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
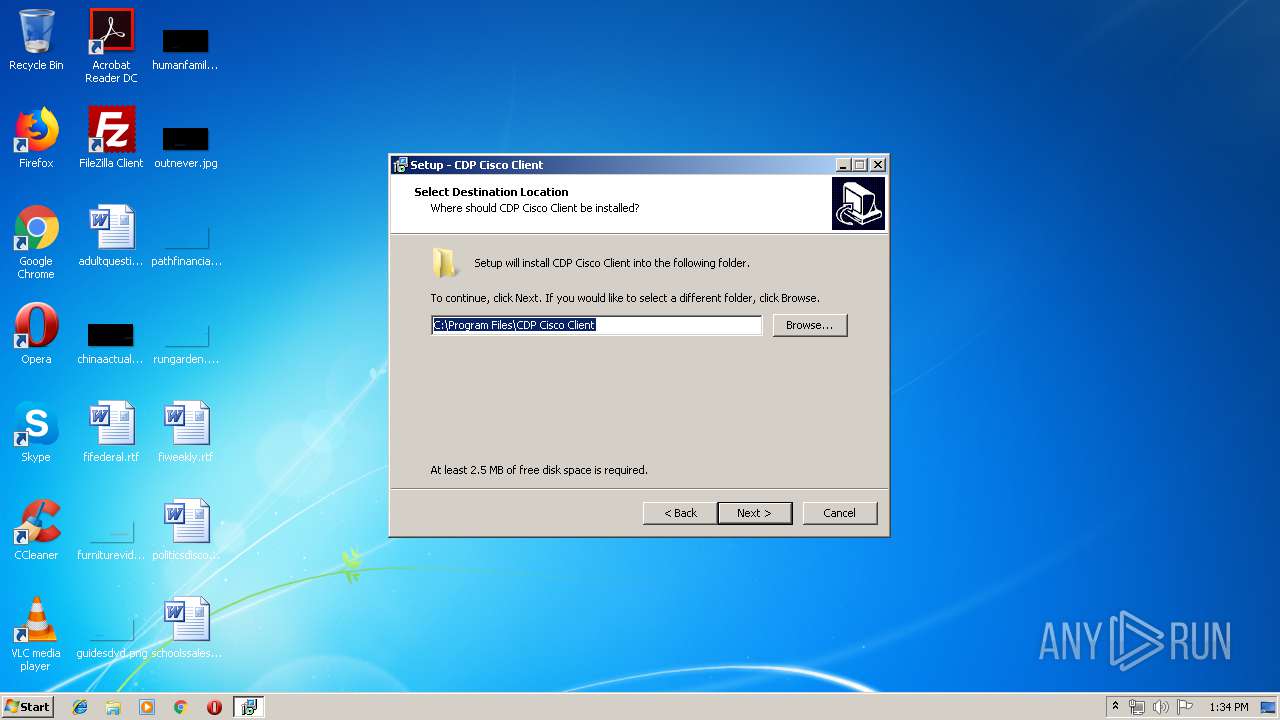
| 296 | "C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe" | C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Tallsoft, Inc. Integrity Level: MEDIUM Description: CDP Cisco Client Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe" /SPAWNWND=$70280 /NOTIFYWND=$60158 | C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe | cdpclient_setup.tmp | ||||||||||||
User: admin Company: Tallsoft, Inc. Integrity Level: HIGH Description: CDP Cisco Client Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\is-0V1TQ.tmp\cdpclient_setup.tmp" /SL5="$60158,1200634,56832,C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-0V1TQ.tmp\cdpclient_setup.tmp | — | cdpclient_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
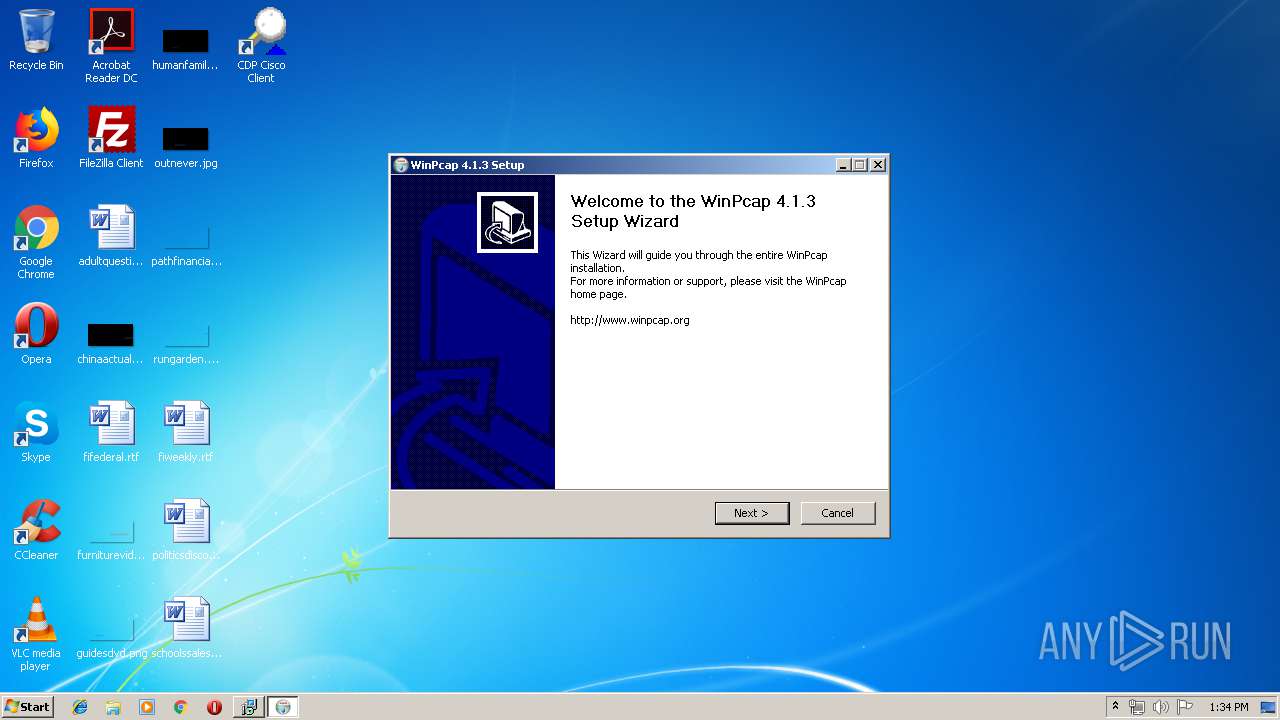
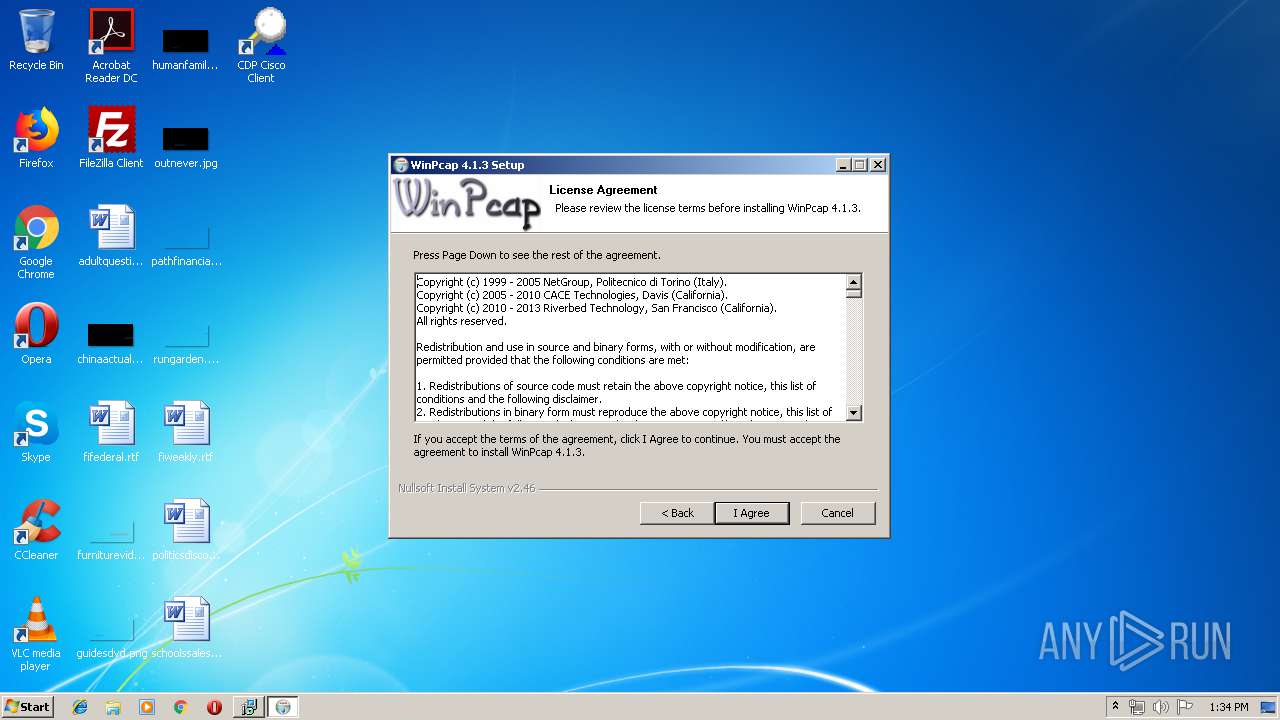
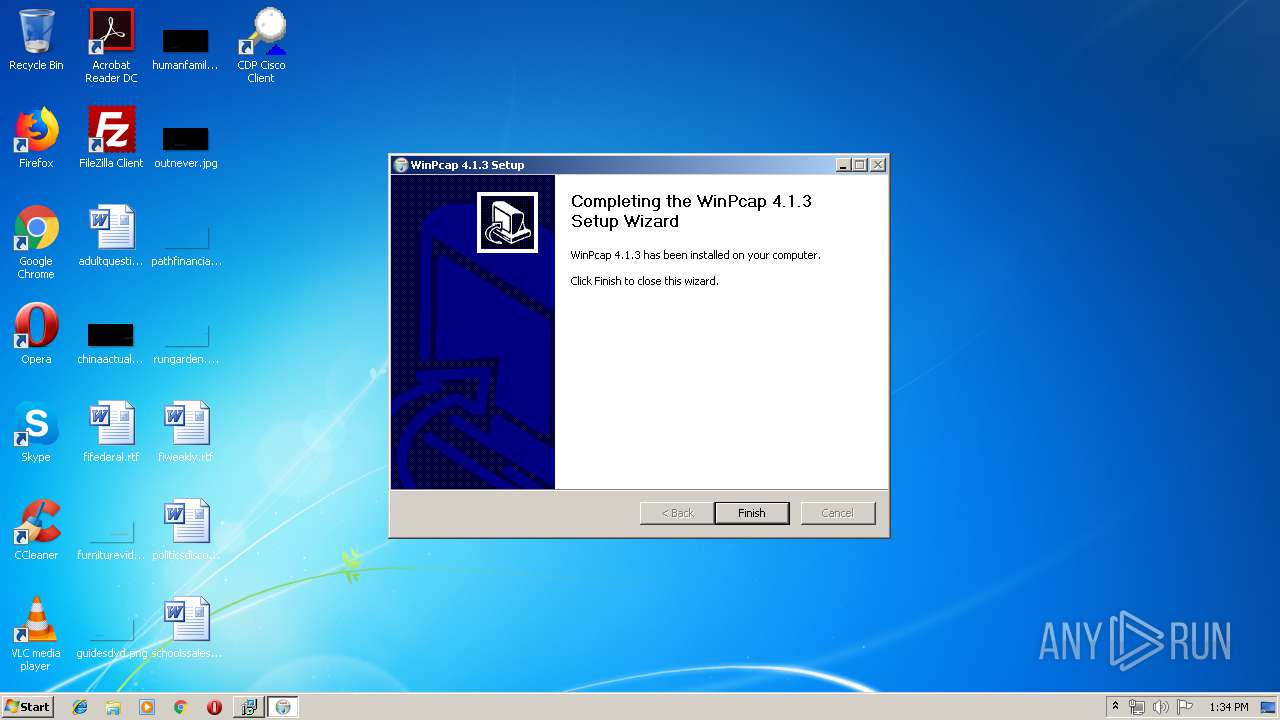
| 2760 | "C:\Program Files\CDP Cisco Client\winpcap.exe" | C:\Program Files\CDP Cisco Client\winpcap.exe | cdpclient_setup.tmp | ||||||||||||
User: admin Company: Riverbed Technology, Inc. Integrity Level: HIGH Description: WinPcap 4.1.3 installer Exit code: 0 Version: 4.1.0.2980 Modules
| |||||||||||||||
| 3284 | C:\Windows\system32\net1 start npf | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3308 | "C:\Program Files\CDP Cisco Client\CDPService.exe" | C:\Program Files\CDP Cisco Client\CDPService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
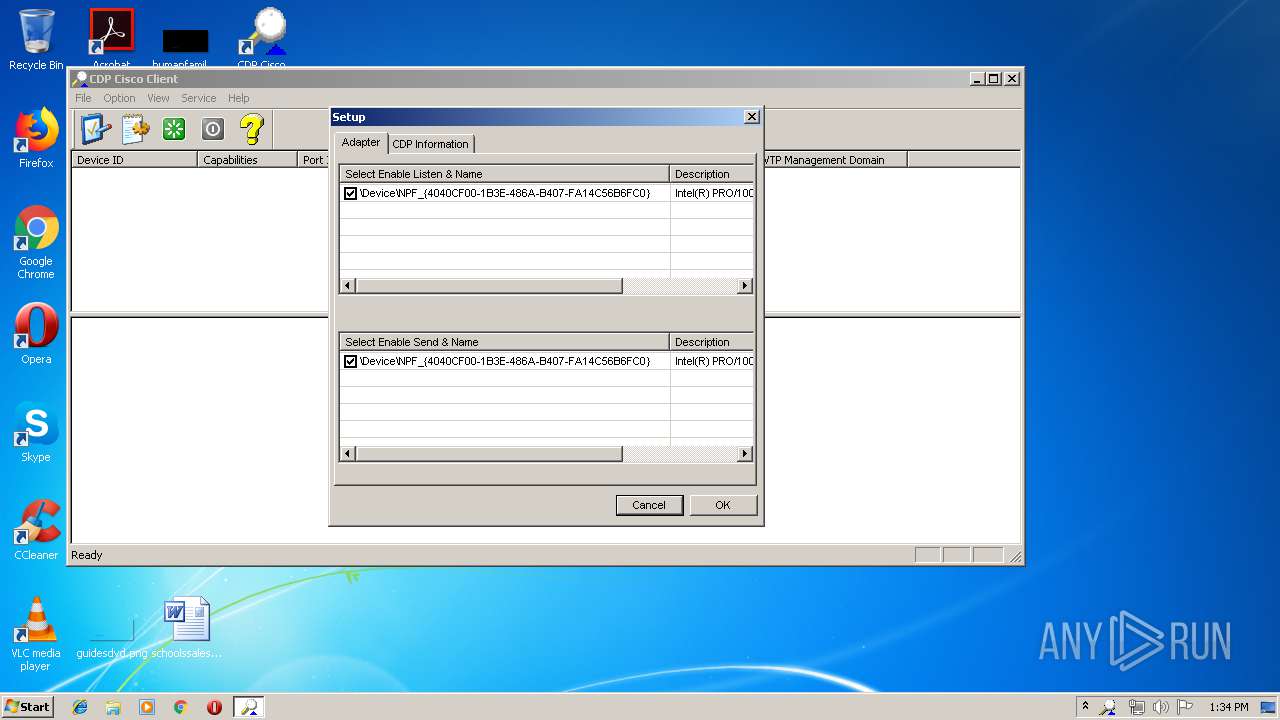
| 3312 | "C:\Program Files\CDP Cisco Client\CDPclient.exe" | C:\Program Files\CDP Cisco Client\CDPclient.exe | — | cdpclient_setup.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Description: CDP Monitor MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\is-I2RA8.tmp\cdpclient_setup.tmp" /SL5="$701F8,1200634,56832,C:\Users\admin\AppData\Local\Temp\cdpclient_setup.exe" /SPAWNWND=$70280 /NOTIFYWND=$60158 | C:\Users\admin\AppData\Local\Temp\is-I2RA8.tmp\cdpclient_setup.tmp | cdpclient_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3620 | net start npf | C:\Windows\system32\net.exe | — | winpcap.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3796 | "C:\Program Files\CDP Cisco Client\CDPService.exe" /install | C:\Program Files\CDP Cisco Client\CDPService.exe | — | cdpclient_setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 371
Read events
1 282
Write events
81
Delete events
8
Modification events
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B00D00003E71247B1A0BD501 | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: FD28D7581804605BAB02C2D1597DDC808E49B971C3F579B85970962F932A047C | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\CDP Cisco Client\CDPService.exe | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 00005A840061B81318AE18C4D5DF5081BD80E1942C70F92440B10E755AA9E0A0 | |||
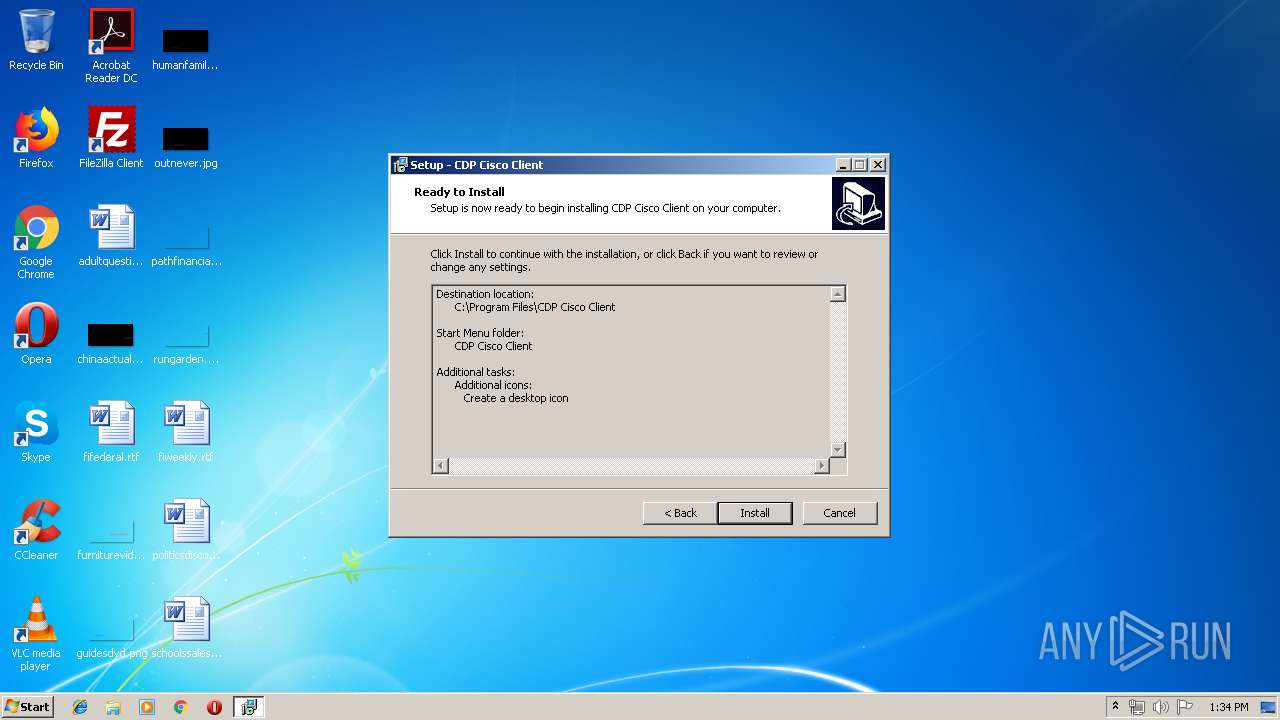
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CDP Cisco Client_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.5 (a) | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CDP Cisco Client_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\CDP Cisco Client | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CDP Cisco Client_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\CDP Cisco Client\ | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CDP Cisco Client_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: CDP Cisco Client | |||
| (PID) Process: | (3504) cdpclient_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CDP Cisco Client_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
18
Suspicious files
0
Text files
37
Unknown types
6
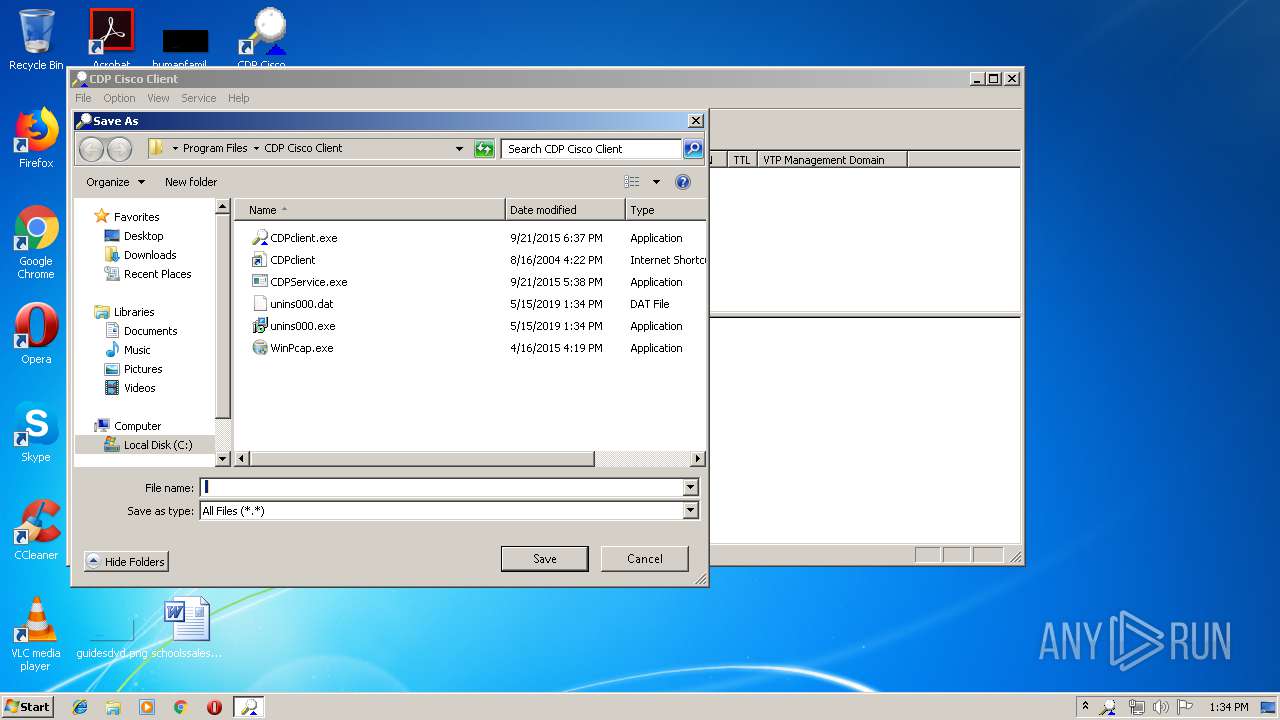
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
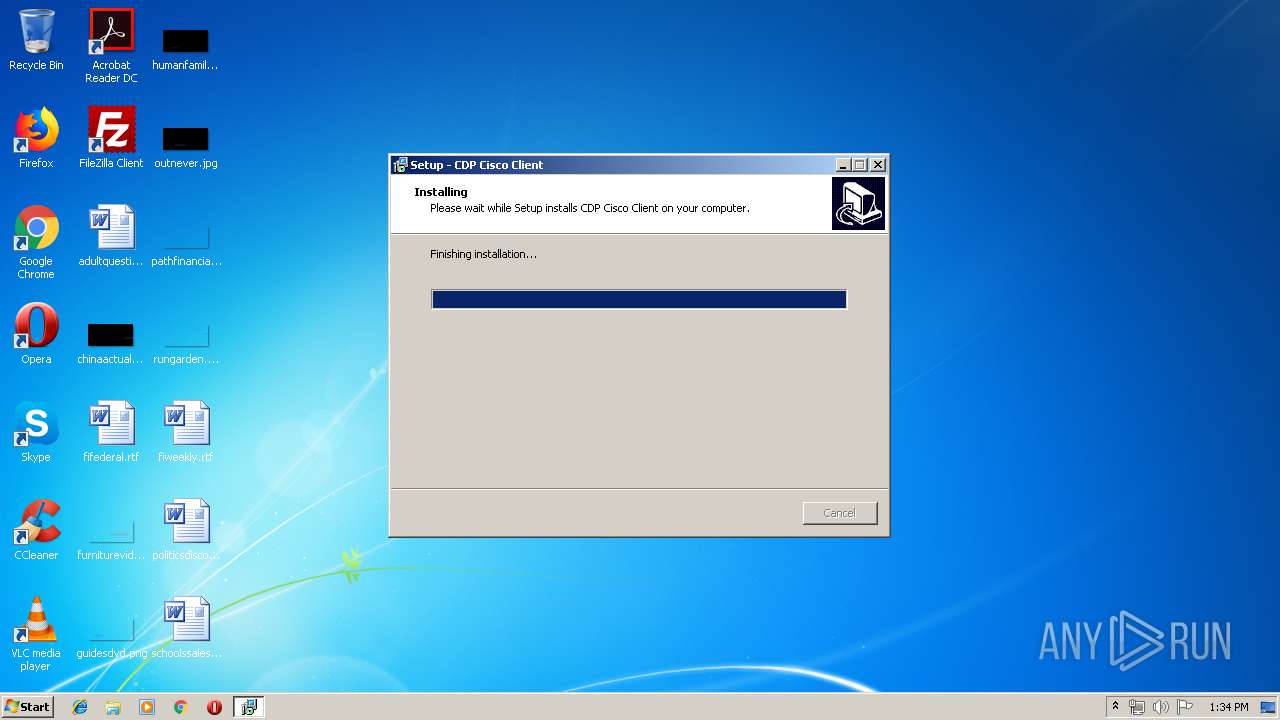
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\is-Q9A4D.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\is-EACRG.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\is-MKND5.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\is-K74SP.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\is-FSBV2.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\CDPService.exe | executable | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\Program Files\CDP Cisco Client\CDPclient.exe | executable | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CDP Cisco Client\Uninstall CDP Cisco Client.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3504 | cdpclient_setup.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CDP Cisco Client\CDP Cisco Client.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report