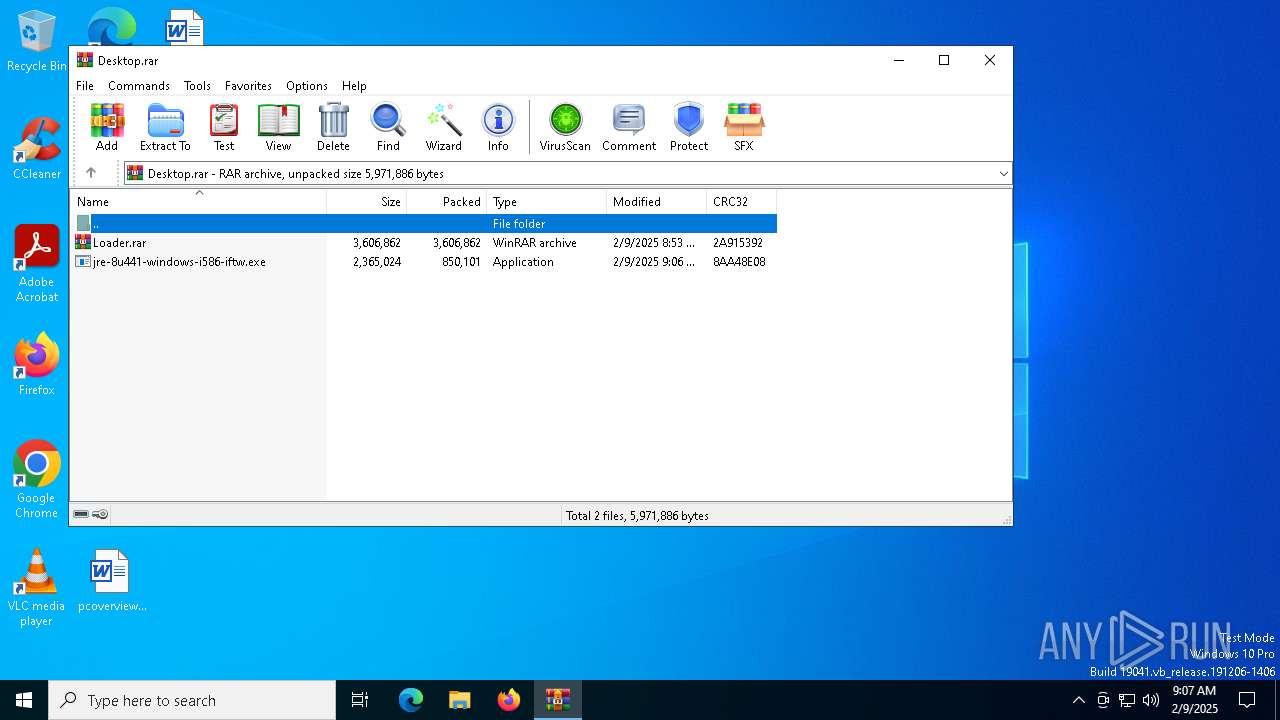
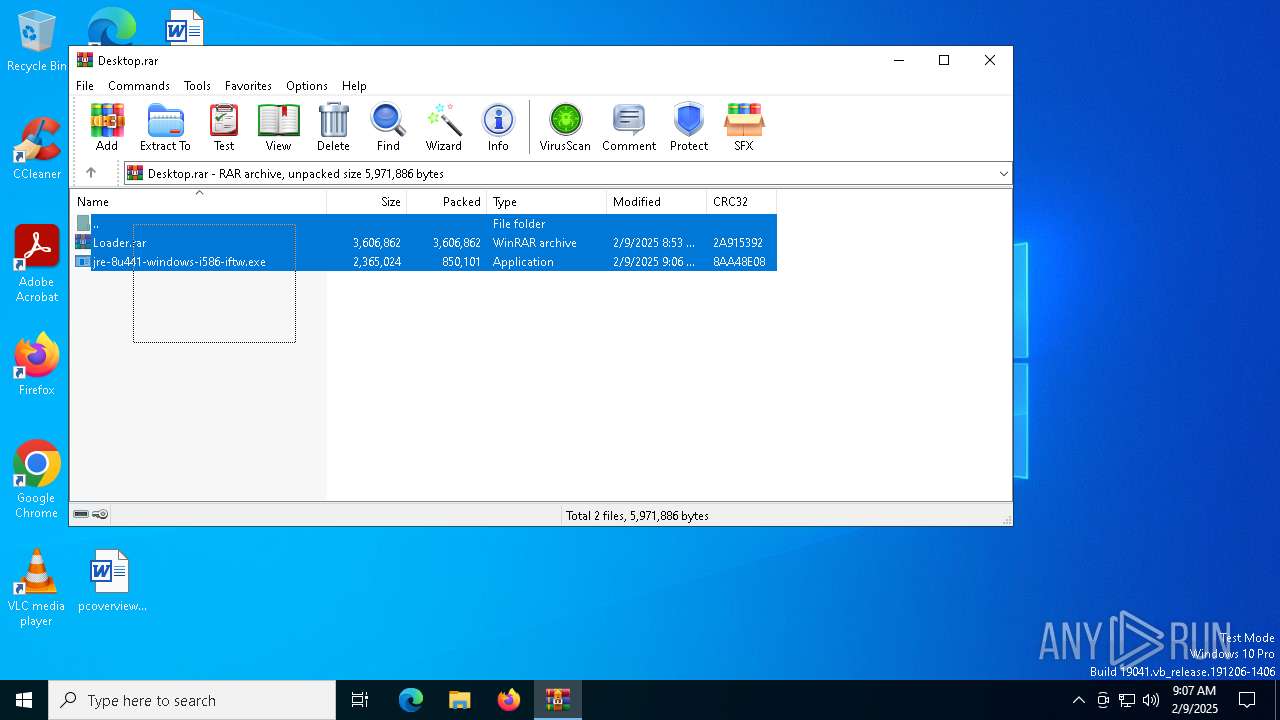
| File name: | Desktop.rar |
| Full analysis: | https://app.any.run/tasks/acdb499e-6adb-443f-9d26-5a66073d0231 |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2025, 09:07:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
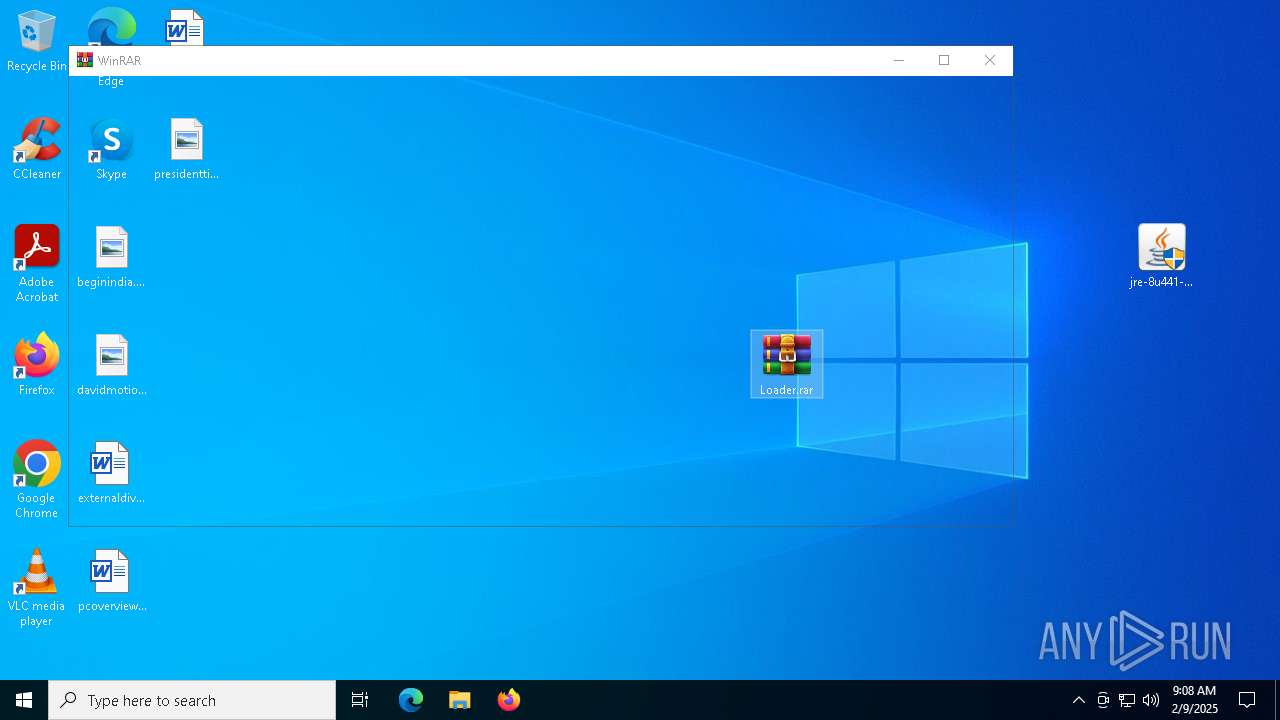
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 4D115DF5CA2776DE8918F81DA5523088 |
| SHA1: | A8ADDFA2BB6329C325A2E3F9B74E893900E40A79 |
| SHA256: | 8D13392542030833570BDBA6F1248715743A99774975A4D5676C63683B35351F |
| SSDEEP: | 98304:MaHwPbnSUzgEqkmpFNInUDdSyDBSOBZk2LZROGS+fW0+grhHarogf/ImnKNWqYLf:lLZHrK |
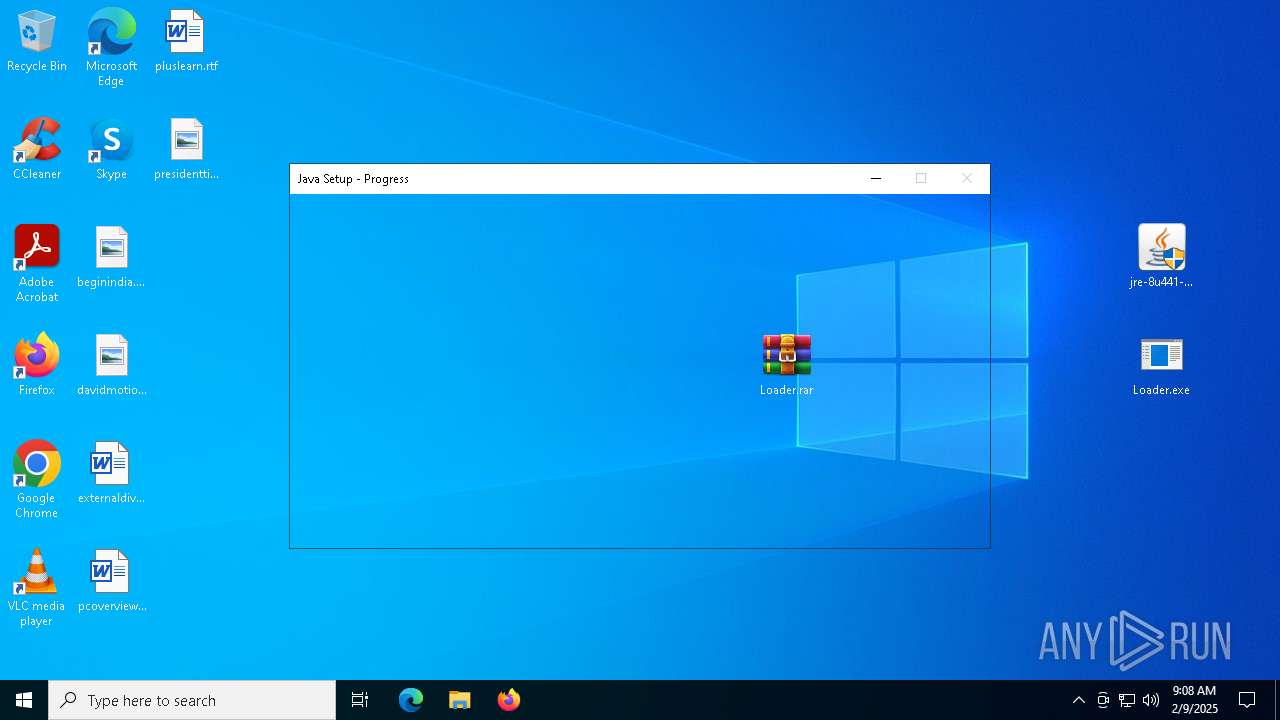
MALICIOUS
No malicious indicators.SUSPICIOUS
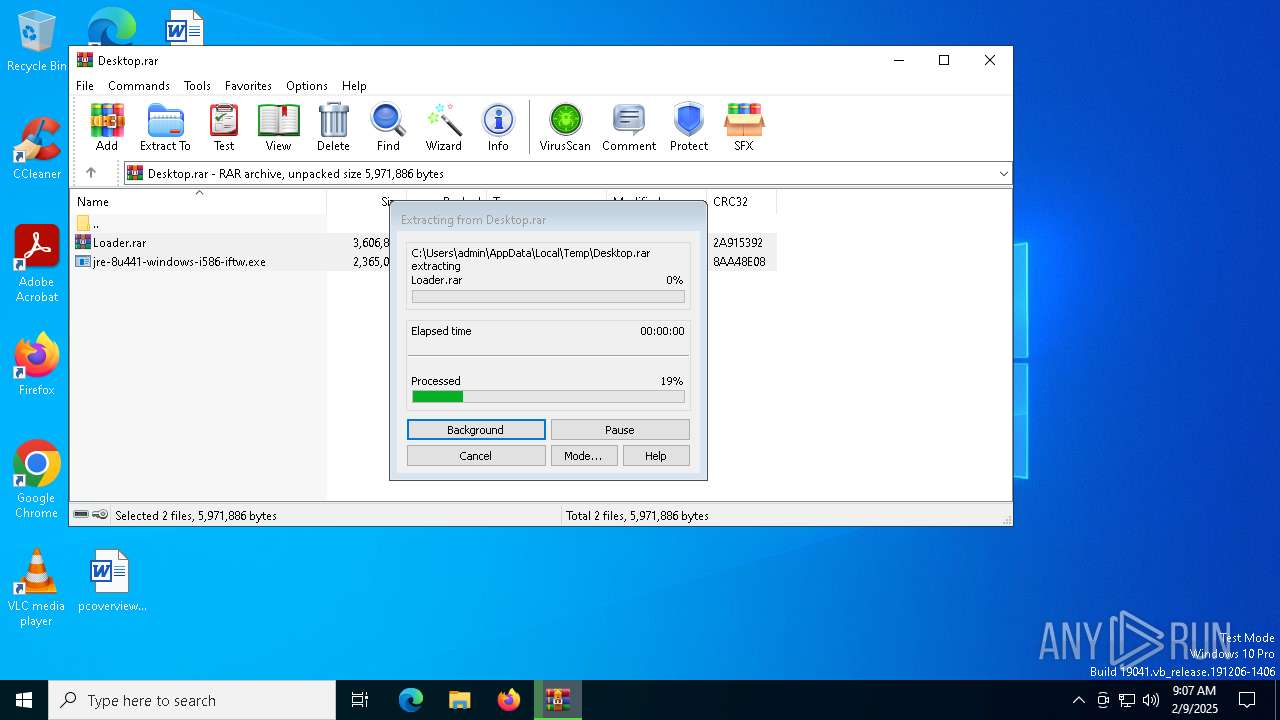
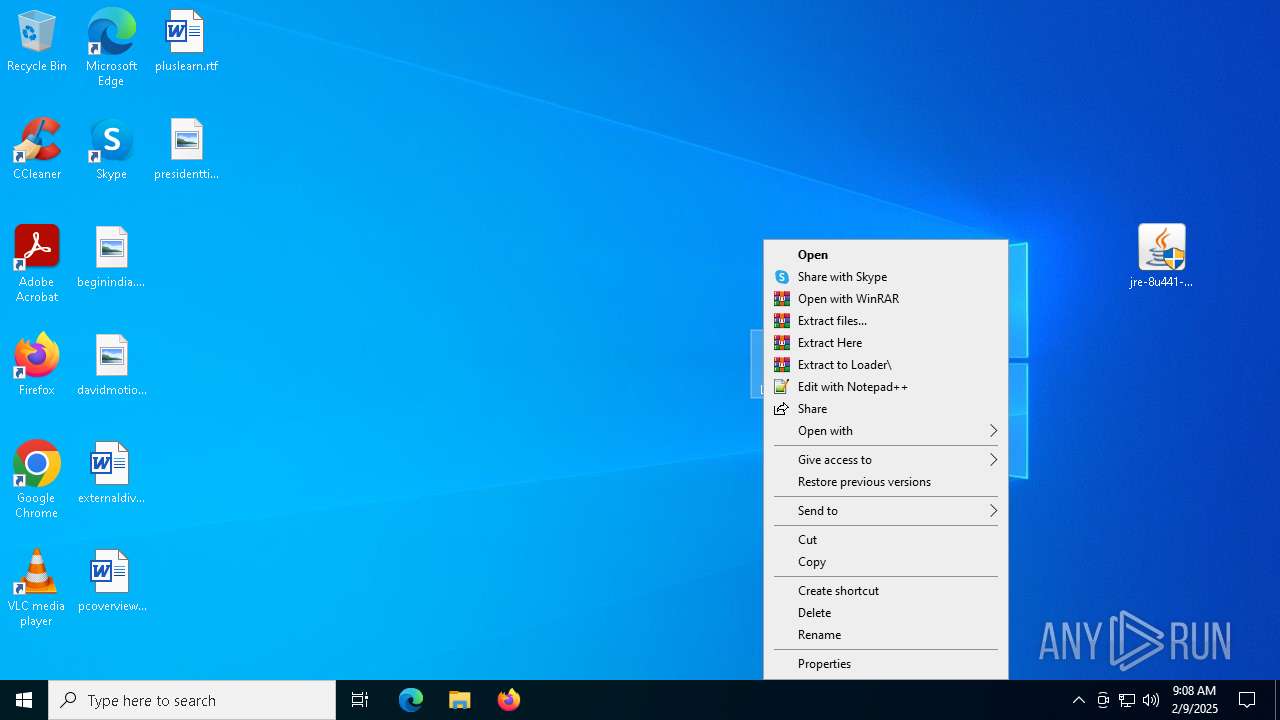
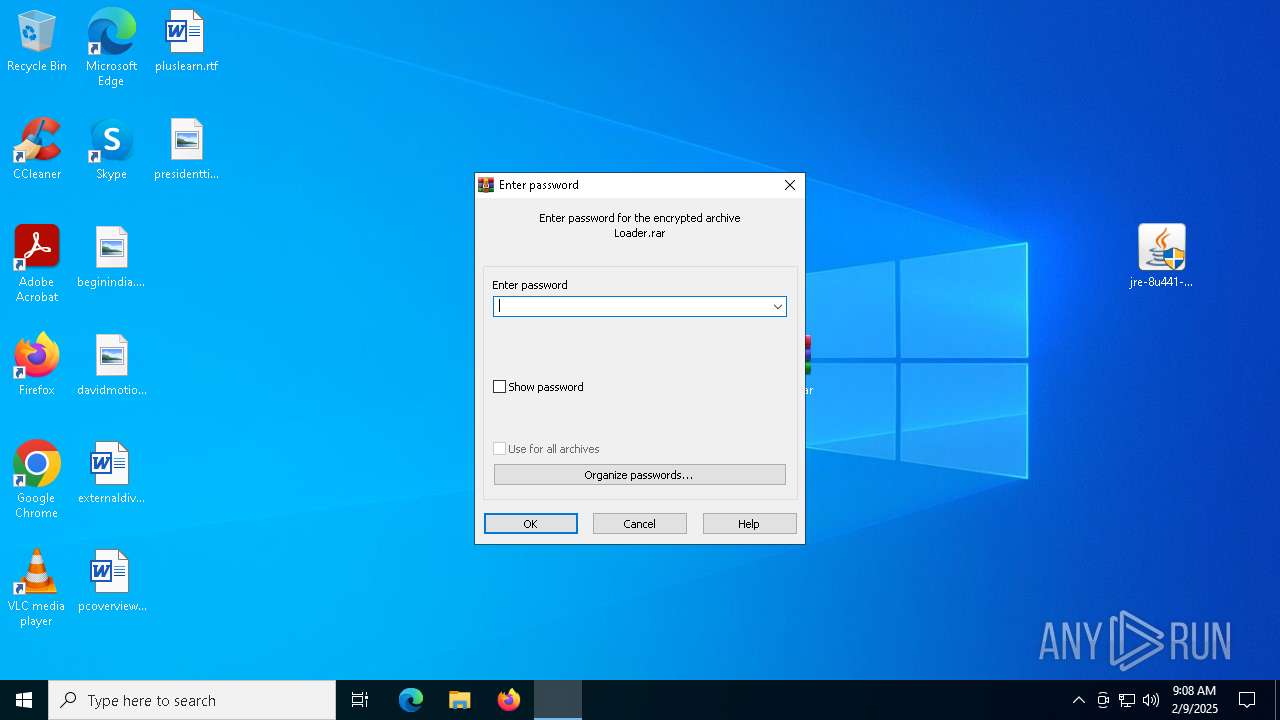
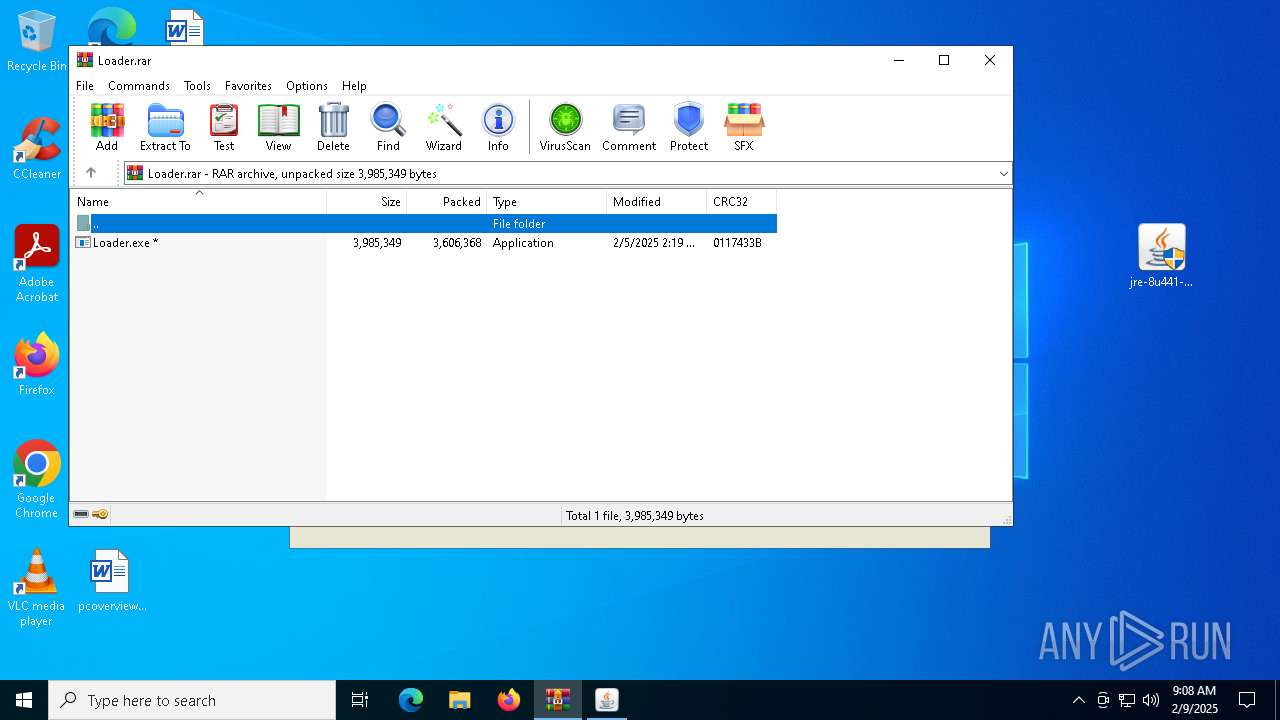
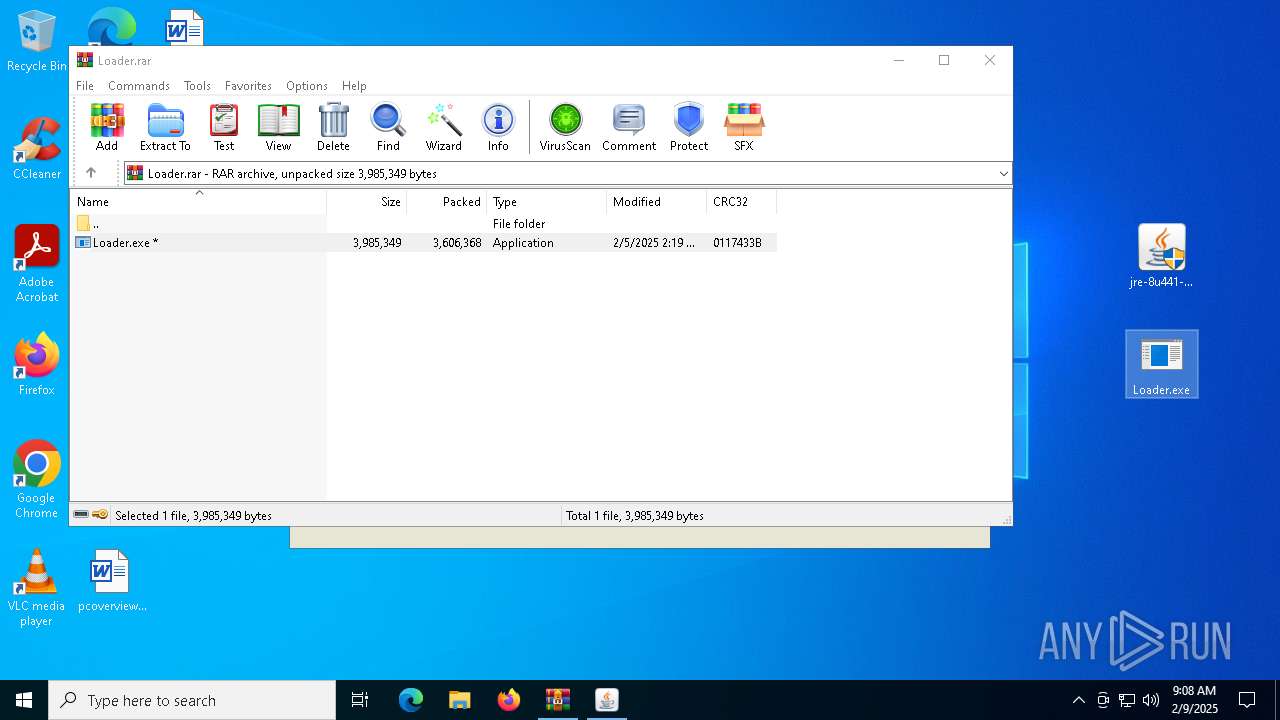
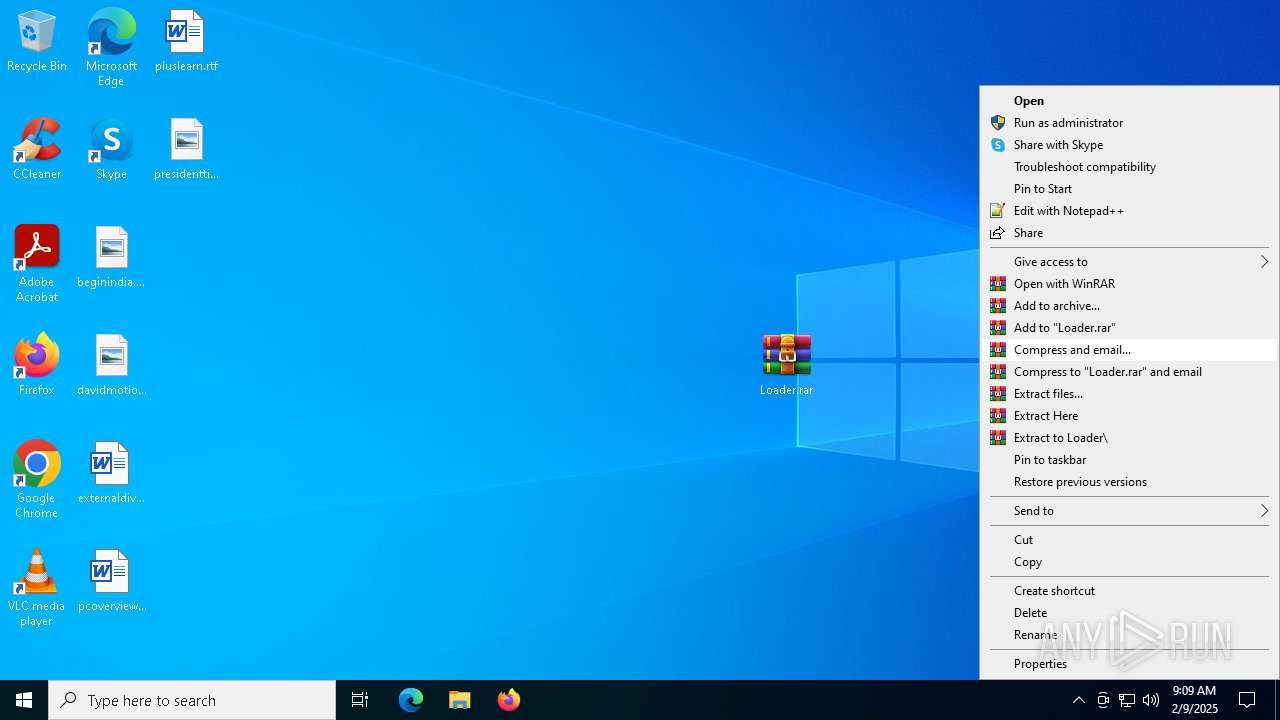
Generic archive extractor
- WinRAR.exe (PID: 6384)
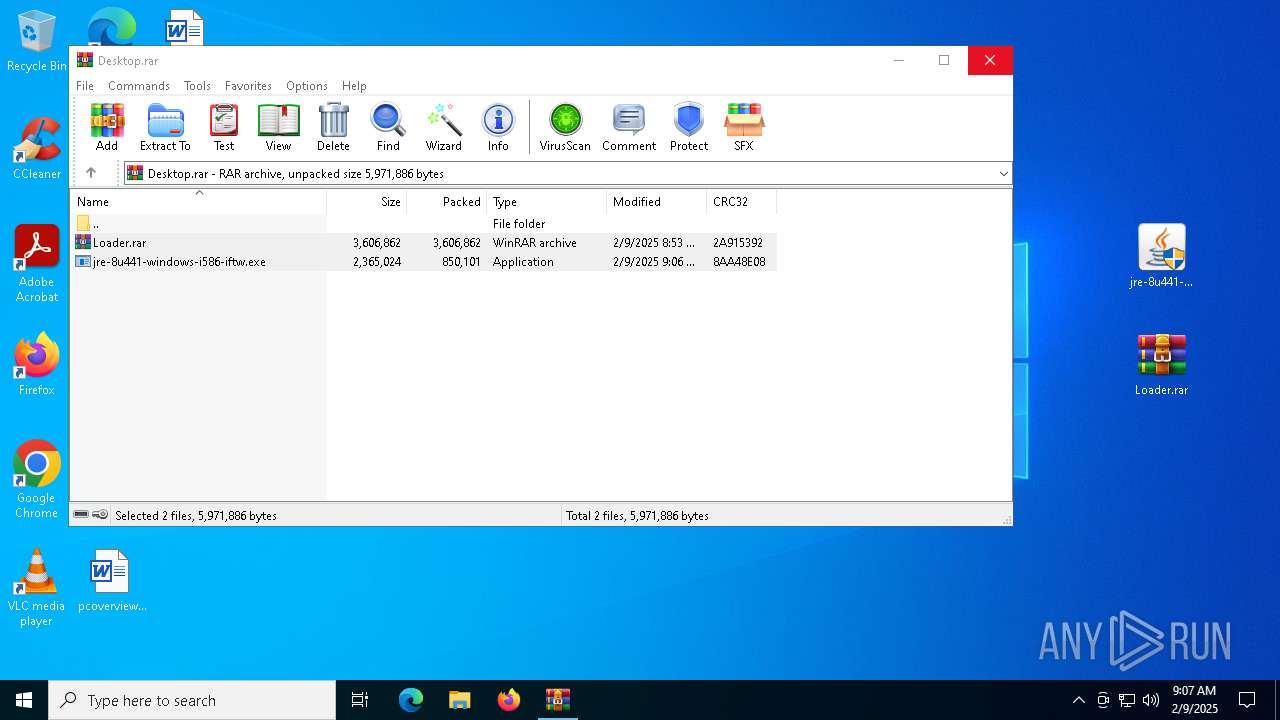
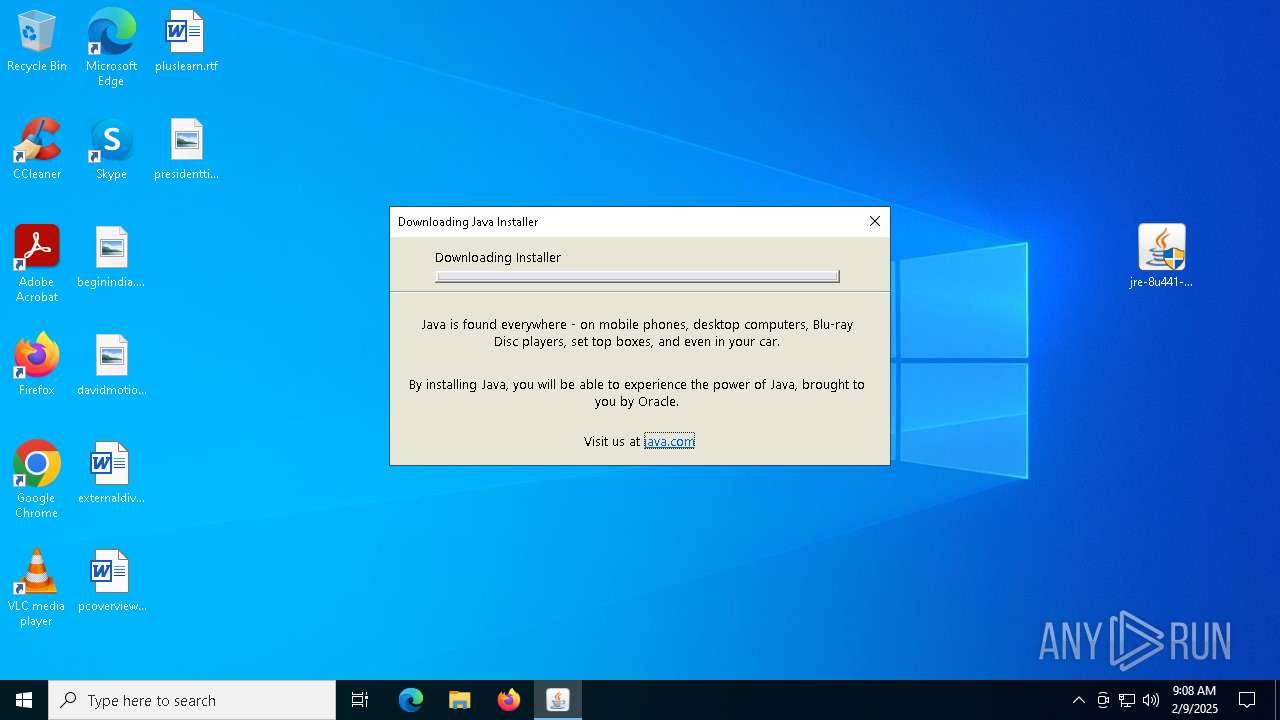
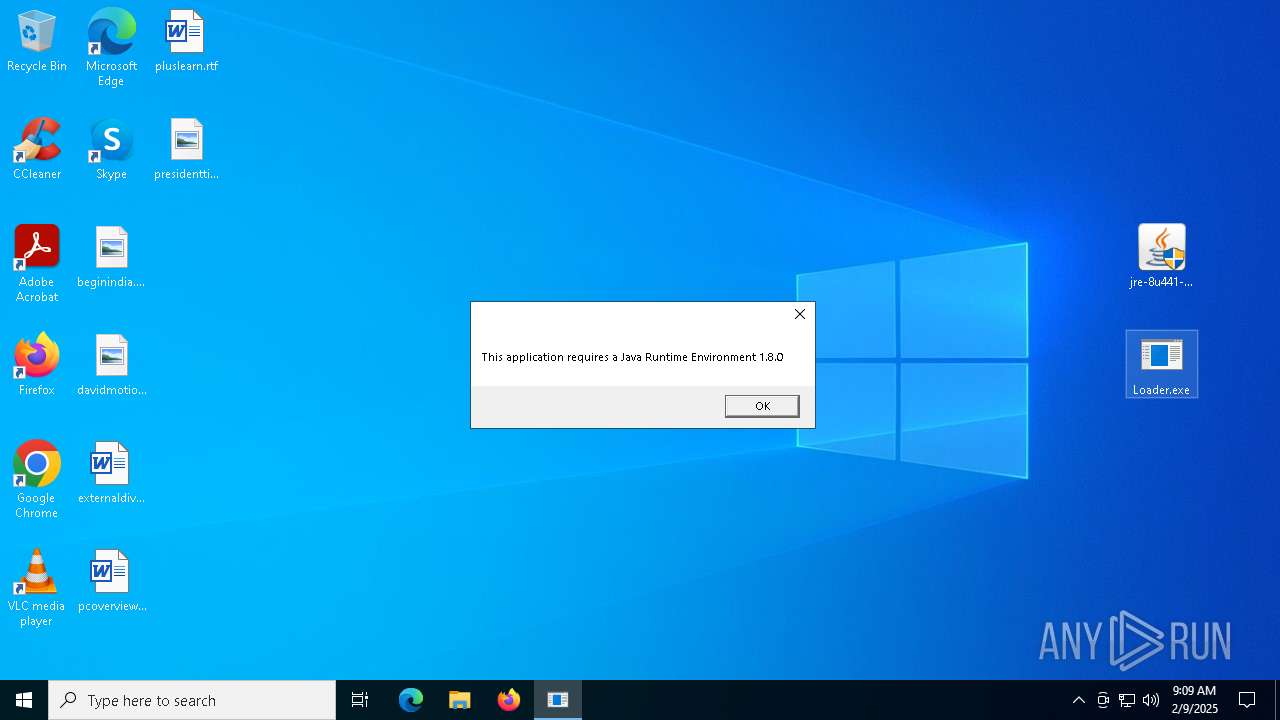
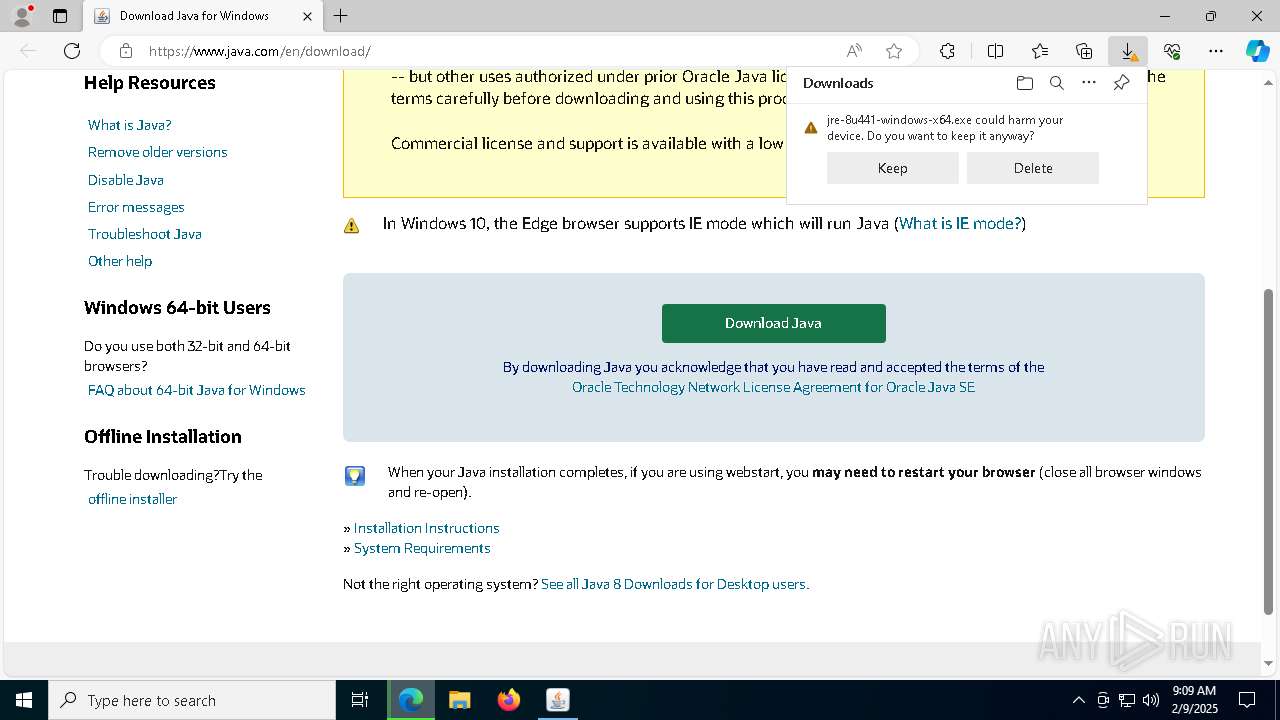
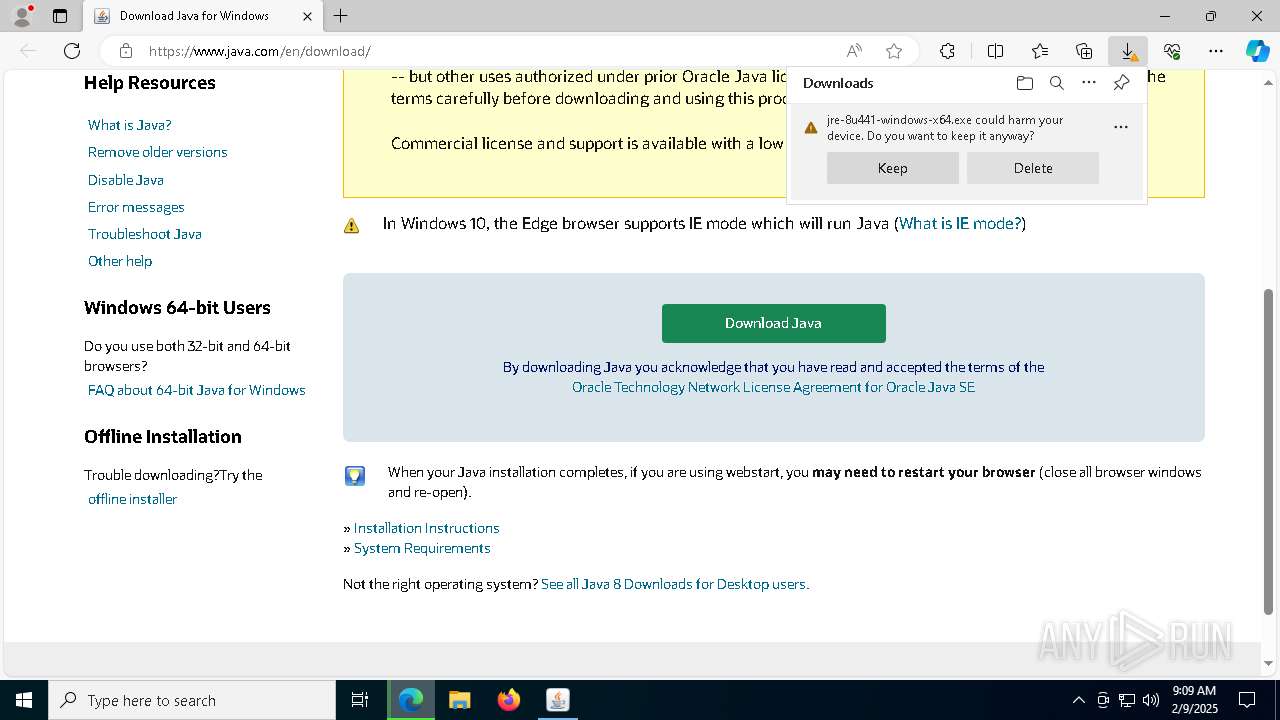
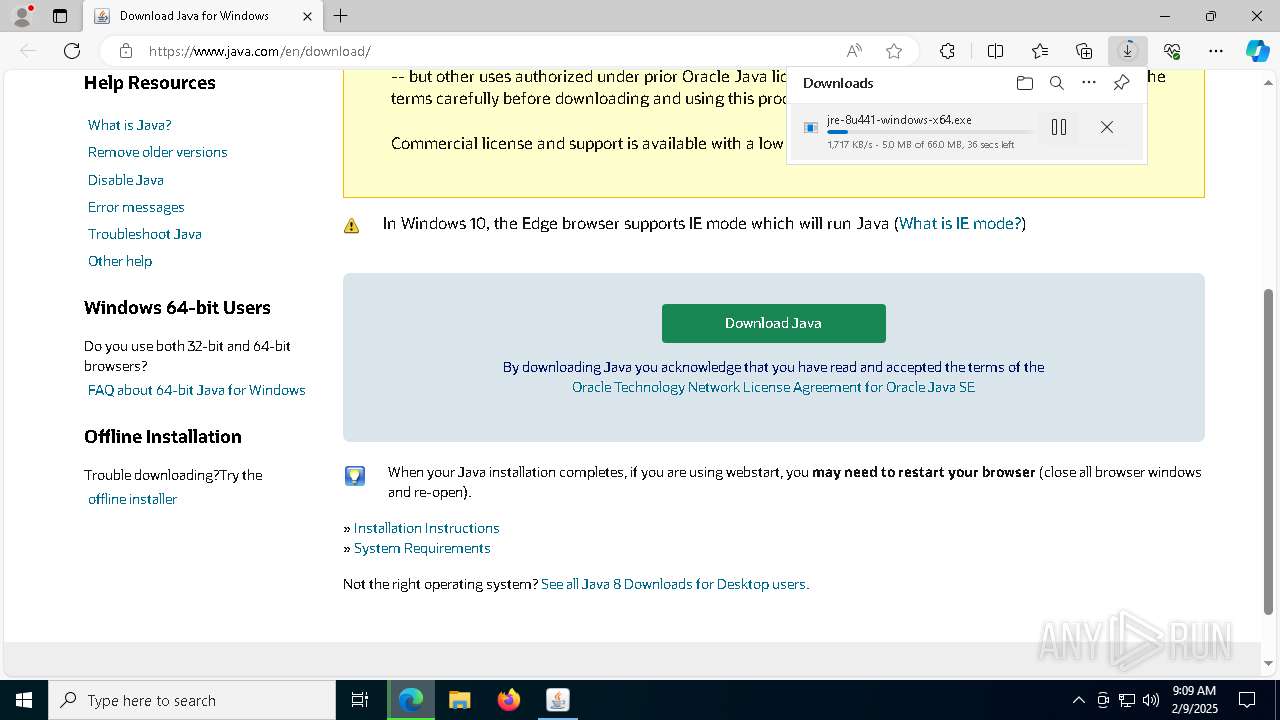
Executable content was dropped or overwritten
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- LZMA_EXE (PID: 2744)
- installer.exe (PID: 7084)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
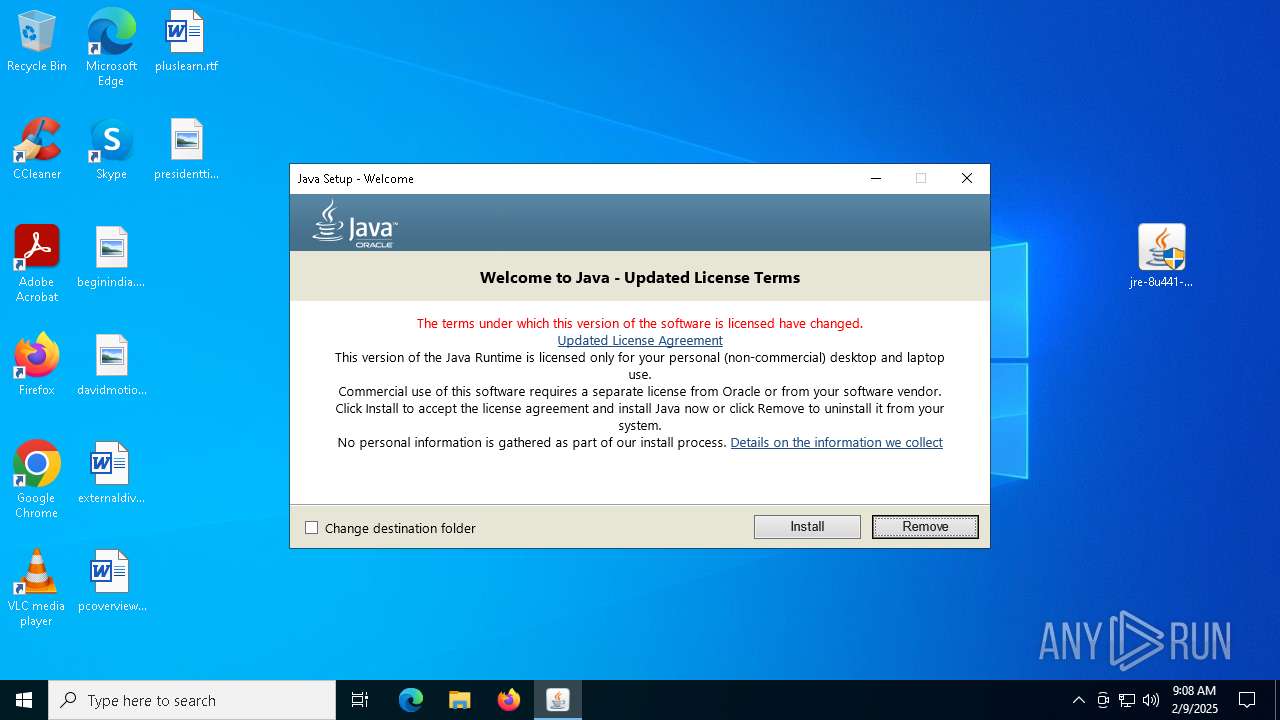
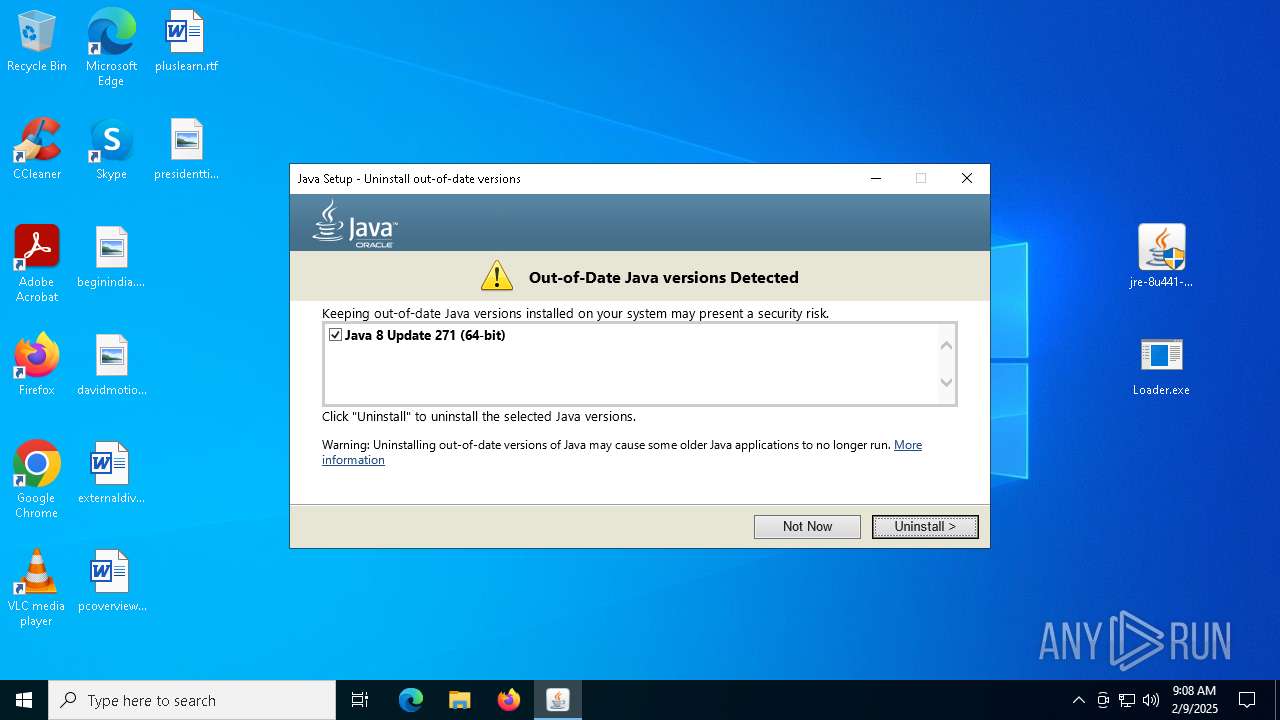
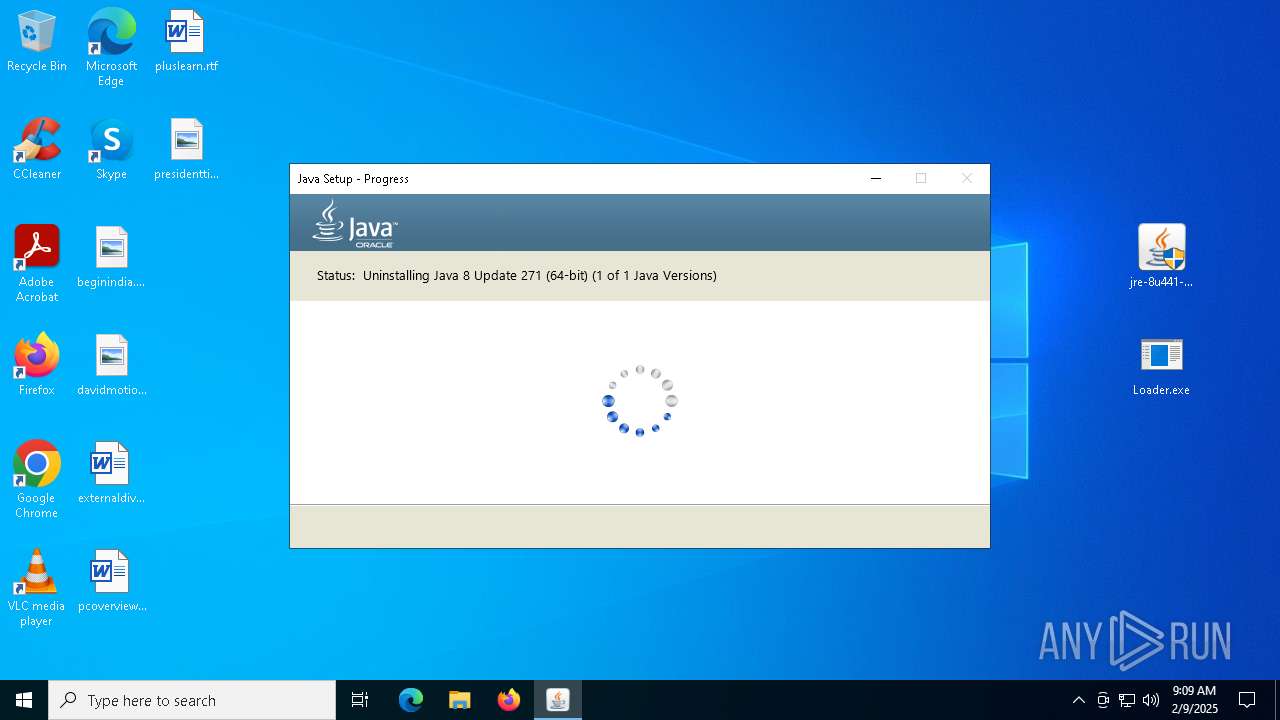
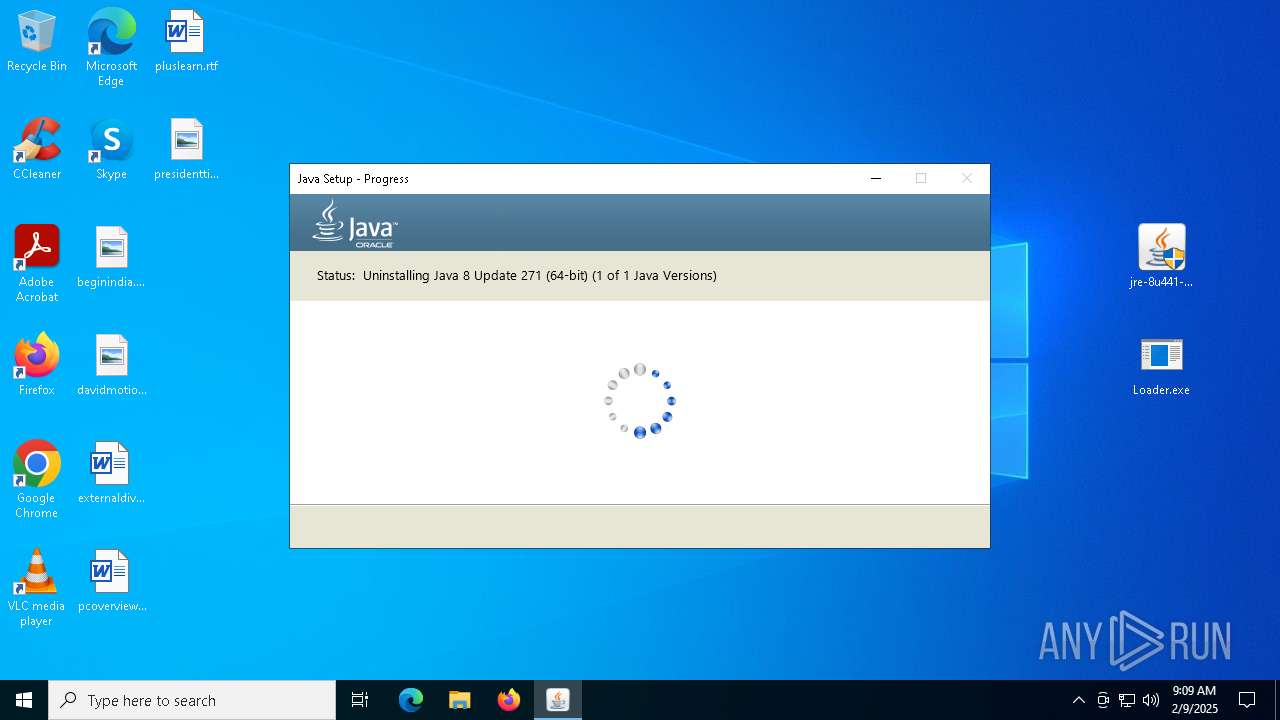
Checks for Java to be installed
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- msiexec.exe (PID: 3564)
- installer.exe (PID: 7084)
- ssvagent.exe (PID: 6200)
- jp2launcher.exe (PID: 732)
- msiexec.exe (PID: 3540)
- jp2launcher.exe (PID: 5112)
- msiexec.exe (PID: 5032)
Reads Microsoft Outlook installation path
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Reads security settings of Internet Explorer
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- installer.exe (PID: 7084)
- jp2launcher.exe (PID: 732)
- jp2launcher.exe (PID: 5112)
- Loader.exe (PID: 2976)
- Loader.exe (PID: 2164)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Checks Windows Trust Settings
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- msiexec.exe (PID: 3564)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Starts application with an unusual extension
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
Reads Internet Explorer settings
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
The process drops C-runtime libraries
- msiexec.exe (PID: 3564)
Process drops legitimate windows executable
- msiexec.exe (PID: 3564)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3564)
Reads Mozilla Firefox installation path
- MSI629B.tmp (PID: 7068)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 6200)
- installer.exe (PID: 7084)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6384)
- msiexec.exe (PID: 3564)
- msedge.exe (PID: 3984)
The sample compiled with english language support
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- WinRAR.exe (PID: 6384)
- LZMA_EXE (PID: 2744)
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- msiexec.exe (PID: 3564)
- installer.exe (PID: 7084)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
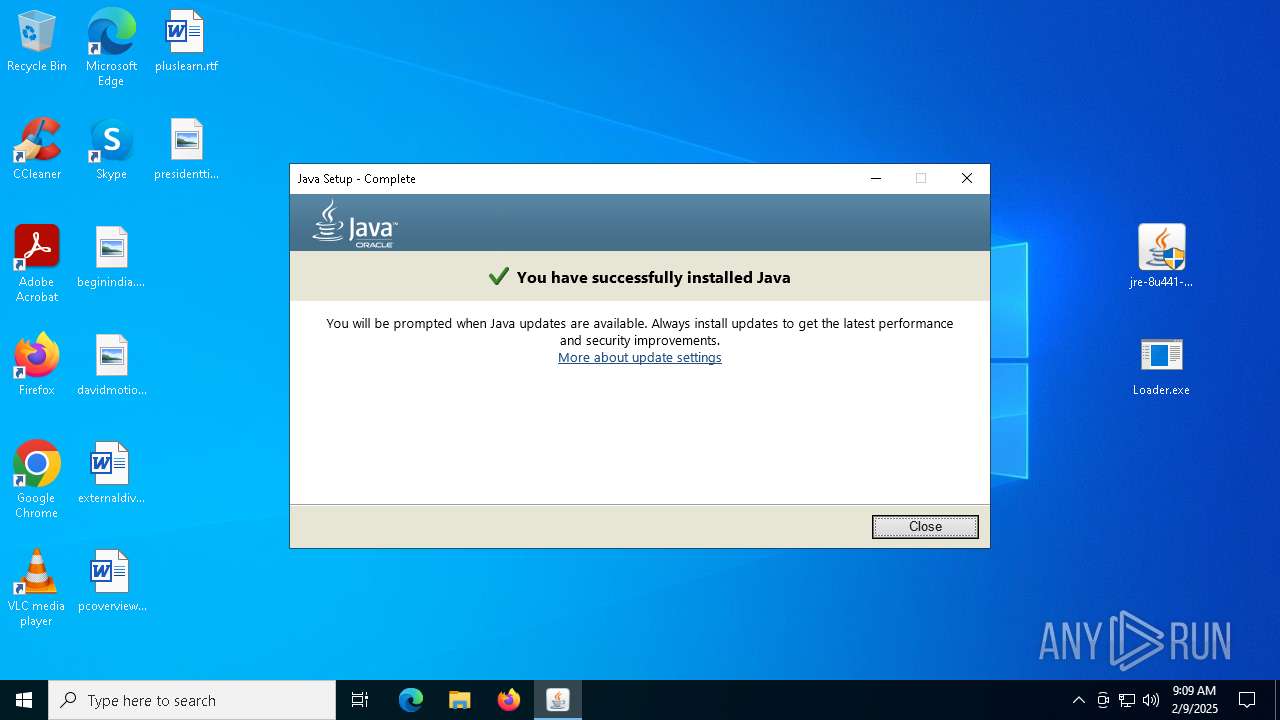
Java executable
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- installer.exe (PID: 7084)
- MSI629B.tmp (PID: 7068)
- jre-8u441-windows-i586-iftw.exe (PID: 5776)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
- MSID6C5.tmp (PID: 4328)
Reads the computer name
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- msiexec.exe (PID: 3564)
- msiexec.exe (PID: 4188)
- installer.exe (PID: 7084)
- javaws.exe (PID: 3744)
- jp2launcher.exe (PID: 732)
- msiexec.exe (PID: 3540)
- jp2launcher.exe (PID: 5112)
- javaws.exe (PID: 6400)
- msiexec.exe (PID: 5032)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 236)
- javaw.exe (PID: 6376)
- msiexec.exe (PID: 1596)
- MSI629B.tmp (PID: 7068)
- msiexec.exe (PID: 6584)
- javaw.exe (PID: 6652)
- javaw.exe (PID: 6600)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
- Loader.exe (PID: 2976)
- identity_helper.exe (PID: 4036)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
- msiexec.exe (PID: 6376)
- MSID6C5.tmp (PID: 4328)
- Loader.exe (PID: 2164)
- msiexec.exe (PID: 2152)
- msiexec.exe (PID: 6212)
Create files in a temporary directory
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- javaw.exe (PID: 7108)
- installer.exe (PID: 7084)
- jp2launcher.exe (PID: 732)
- jp2launcher.exe (PID: 5112)
- javaw.exe (PID: 6376)
- javaw.exe (PID: 6652)
- javaw.exe (PID: 6600)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
Checks supported languages
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- LZMA_EXE (PID: 2744)
- LZMA_EXE (PID: 3364)
- msiexec.exe (PID: 3564)
- msiexec.exe (PID: 4188)
- installer.exe (PID: 7084)
- javaw.exe (PID: 7108)
- ssvagent.exe (PID: 6200)
- javaws.exe (PID: 6400)
- jp2launcher.exe (PID: 732)
- msiexec.exe (PID: 3540)
- msiexec.exe (PID: 1596)
- jp2launcher.exe (PID: 5112)
- javaws.exe (PID: 3744)
- msiexec.exe (PID: 5032)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 236)
- javaw.exe (PID: 6376)
- MSI629B.tmp (PID: 7068)
- msiexec.exe (PID: 6584)
- jaureg.exe (PID: 6564)
- javaw.exe (PID: 6652)
- javaw.exe (PID: 6600)
- Loader.exe (PID: 2976)
- identity_helper.exe (PID: 4036)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
- msiexec.exe (PID: 6376)
- MSID6C5.tmp (PID: 4328)
- jaureg.exe (PID: 3744)
- Loader.exe (PID: 2164)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
- msiexec.exe (PID: 6212)
- msiexec.exe (PID: 2152)
Manual execution by a user
- jre-8u441-windows-i586-iftw.exe (PID: 4328)
- WinRAR.exe (PID: 2600)
- Loader.exe (PID: 2976)
- jre-8u441-windows-i586-iftw.exe (PID: 5776)
- jre-8u441-windows-i586-iftw.exe (PID: 3864)
- msedge.exe (PID: 5256)
- Loader.exe (PID: 2164)
Checks proxy server information
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Reads the machine GUID from the registry
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- msiexec.exe (PID: 3564)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Reads the software policy settings
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- msiexec.exe (PID: 3564)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Creates files or folders in the user directory
- jre-8u441-windows-i586-iftw.exe (PID: 6172)
- LZMA_EXE (PID: 2744)
- LZMA_EXE (PID: 3364)
- jre-8u441-windows-i586-iftw.exe (PID: 5004)
Reads CPU info
- msiexec.exe (PID: 3564)
Creates a software uninstall entry
- msiexec.exe (PID: 3564)
Creates files in the program directory
- javaw.exe (PID: 7108)
- installer.exe (PID: 7084)
Local mutex for internet shortcut management
- installer.exe (PID: 7084)
Starts application with an unusual extension
- msiexec.exe (PID: 3564)
Application launched itself
- msiexec.exe (PID: 3564)
- msedge.exe (PID: 3928)
- msedge.exe (PID: 5256)
- msedge.exe (PID: 3984)
Reads Environment values
- identity_helper.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 850101 |
| UncompressedSize: | 2365024 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | jre-8u441-windows-i586-iftw.exe |
Total processes
231
Monitored processes
97
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6660 --field-trial-handle=2308,i,3642322522542563042,9014506370233986314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 236 | C:\Windows\syswow64\MsiExec.exe -Embedding EEC685022E0A0ABF7B6F05C414E193D2 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 732 | "C:\Program Files (x86)\Java\jre1.8.0_441\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files (x86)\Java\jre1.8.0_441" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzICh4ODYpXEphdmFcanJlMS44LjBfNDQxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzICh4ODYpXEphdmFcanJlMS44LjBfNDQxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlcyAoeDg2KVxKYXZhXGpyZTEuOC4wXzQ0MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURzdW4uYXd0Lndhcm11cD10cnVlAC1YYm9vdGNsYXNzcGF0aC9hOkM6XFByb2dyYW0gRmlsZXMgKHg4NilcSmF2YVxqcmUxLjguMF80NDFcbGliXGphdmF3cy5qYXI7QzpcUHJvZ3JhbSBGaWxlcyAoeDg2KVxKYXZhXGpyZTEuOC4wXzQ0MVxsaWJcZGVwbG95LmphcjtDOlxQcm9ncmFtIEZpbGVzICh4ODYpXEphdmFcanJlMS44LjBfNDQxXGxpYlxwbHVnaW4uamFyAC1EamF2YS5hd3QuaGVhZGxlc3M9dHJ1ZQAtRGpubHB4Lmp2bT1DOlxQcm9ncmFtIEZpbGVzICh4ODYpXEphdmFcanJlMS44LjBfNDQxXGJpblxqYXZhdy5leGU= -ma LXdhaXQALWZpeAAtc2hvcnRjdXQALXNpbGVudAAtbm90V2ViSmF2YQ== | C:\Program Files (x86)\Java\jre1.8.0_441\bin\jp2launcher.exe | — | javaws.exe | |||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.441.2.07 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=5888 --field-trial-handle=2308,i,3642322522542563042,9014506370233986314,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
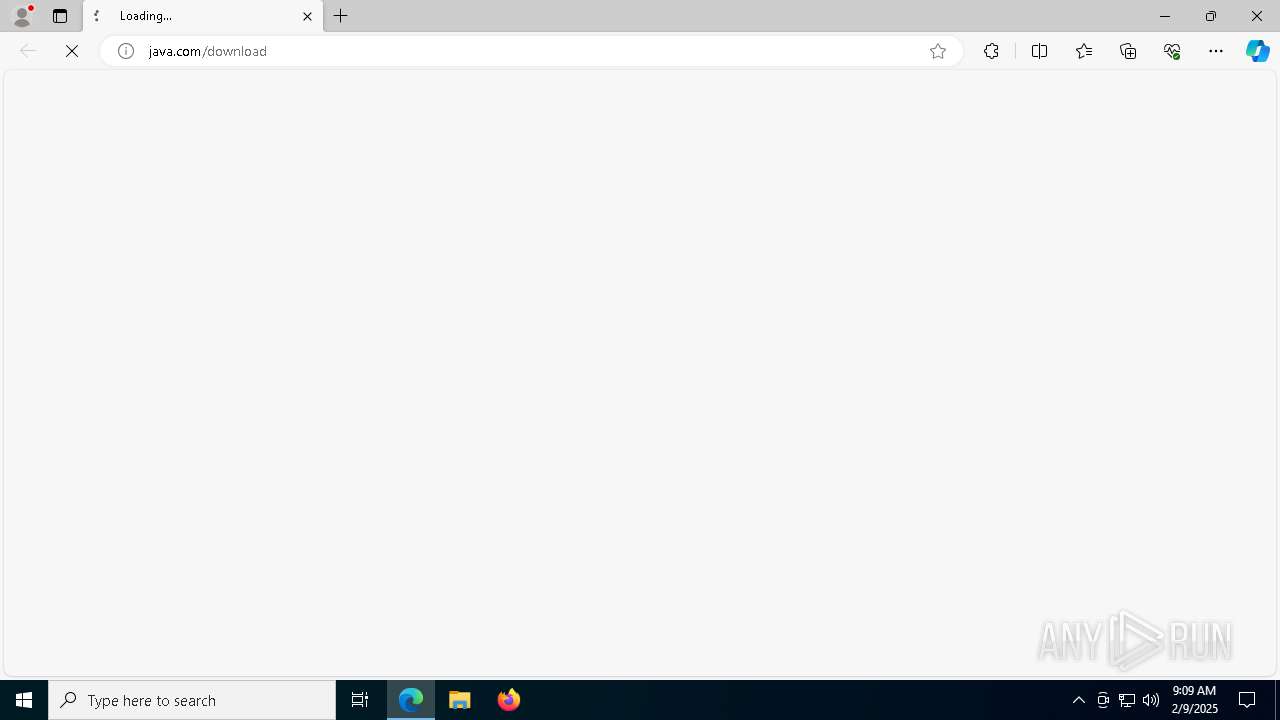
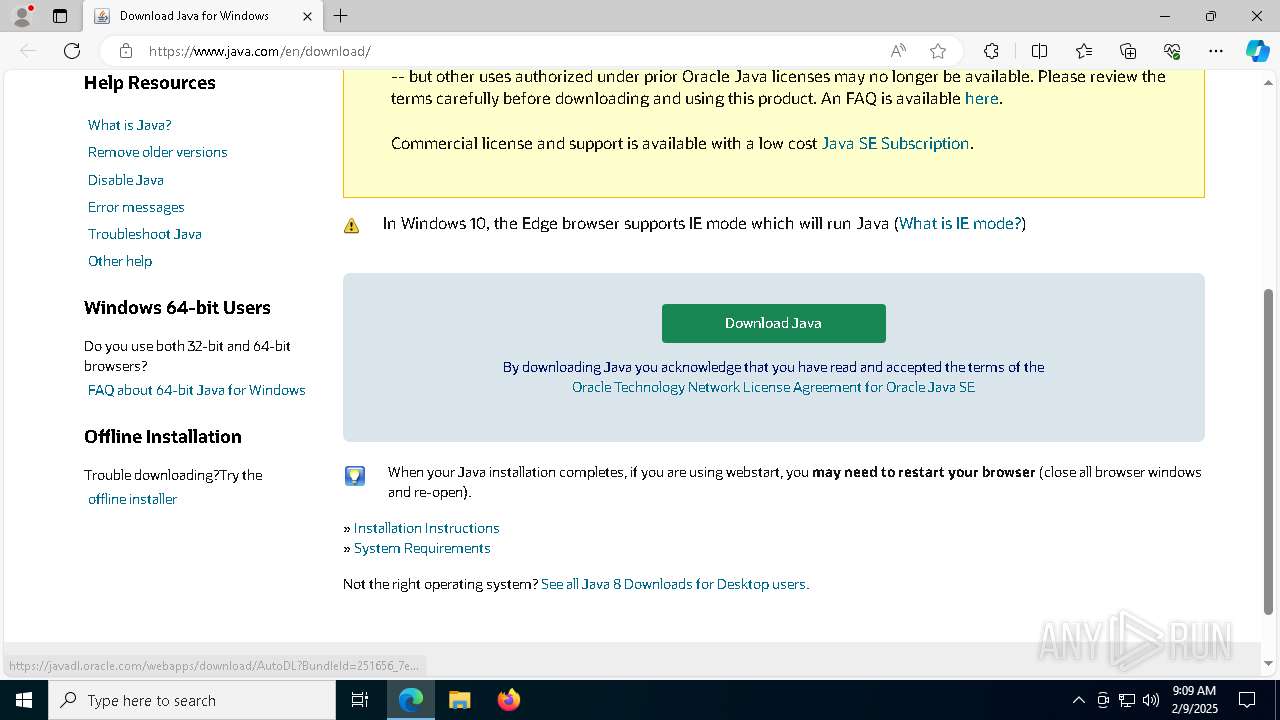
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://java.com/download | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1596 | C:\Windows\syswow64\MsiExec.exe -Embedding 00314D09F98845866EA5A1ABD554F0EF | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 1596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5356 --field-trial-handle=2308,i,3642322522542563042,9014506370233986314,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6216 --field-trial-handle=2308,i,3642322522542563042,9014506370233986314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2736 --field-trial-handle=2388,i,17593897662925412040,5440254665718132546,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | jaureg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
77 718
Read events
32 796
Write events
12 976
Delete events
31 946
Modification events
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Desktop.rar | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
551
Suspicious files
450
Text files
371
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jds1284078.tmp | — | |
MD5:— | SHA256:— | |||
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\jre1.8.0_441.msi | — | |
MD5:— | SHA256:— | |||
| 3364 | LZMA_EXE | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\msi.tmp | — | |
MD5:— | SHA256:— | |||
| 3564 | msiexec.exe | C:\Windows\Installer\13f2a0.msi | — | |
MD5:— | SHA256:— | |||
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\LZMA_EXE | executable | |
MD5:3842C46F2FBC7522EF625F1833530804 | SHA256:17CB7CF185355B60D6ED5138A86C78B9FD5A7D6D3C0DD90F2224246E823166E7 | |||
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:65C92DDD98A700B9239D19846BF80F71 | SHA256:282AB3CBC1FD260EB787F38AD113BF2C3C9C9DFDFF6BD643E13558771B85249C | |||
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_441\Java3BillDevices.png | image | |
MD5:8E52EFC6798ED074072F527309A1BA25 | SHA256:12491EBC4EB99BF014D3BC44F770114BDE013E84CBEC2633303559A8C6E5F991 | |||
| 4328 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\Local\Temp\jds1280781.tmp\jre-8u441-windows-i586-iftw.exe | executable | |
MD5:7097038DC20A6BF6C1C67BDBA98ED5A3 | SHA256:89855D18E5B8BE9E821B18EA9F3F42CD67179BD629C336CE8EB6DFA9C53ADD03 | |||
| 6172 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:10C2FD070F5636C7BD9289CA4BE08AC7 | SHA256:EE55C165721C20B5996722352E50DDBE304BD571E02F28194943BA8C50D9B7FE | |||
| 4328 | jre-8u441-windows-i586-iftw.exe | C:\Users\admin\AppData\Local\Temp\jusched.log | text | |
MD5:C5BCDE788E2D7B194CA6A3FCFDE99965 | SHA256:AFCBE807FC3ED16236481CCC333E4E0752991846ABD8639CC15E26FEB764D6A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
111
DNS requests
128
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5916 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6320 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6172 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
512 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
512 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6172 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAYOL4%2BeG4vlGNX%2BK2nPzLE%3D | unknown | — | — | whitelisted |
6172 | jre-8u441-windows-i586-iftw.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5916 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.154:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
arc.msn.com |
| whitelisted |