| File name: | Акт сверки новый.gz |
| Full analysis: | https://app.any.run/tasks/d5068bc9-46e1-4e09-866b-3fbd2a22da33 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 07:40:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
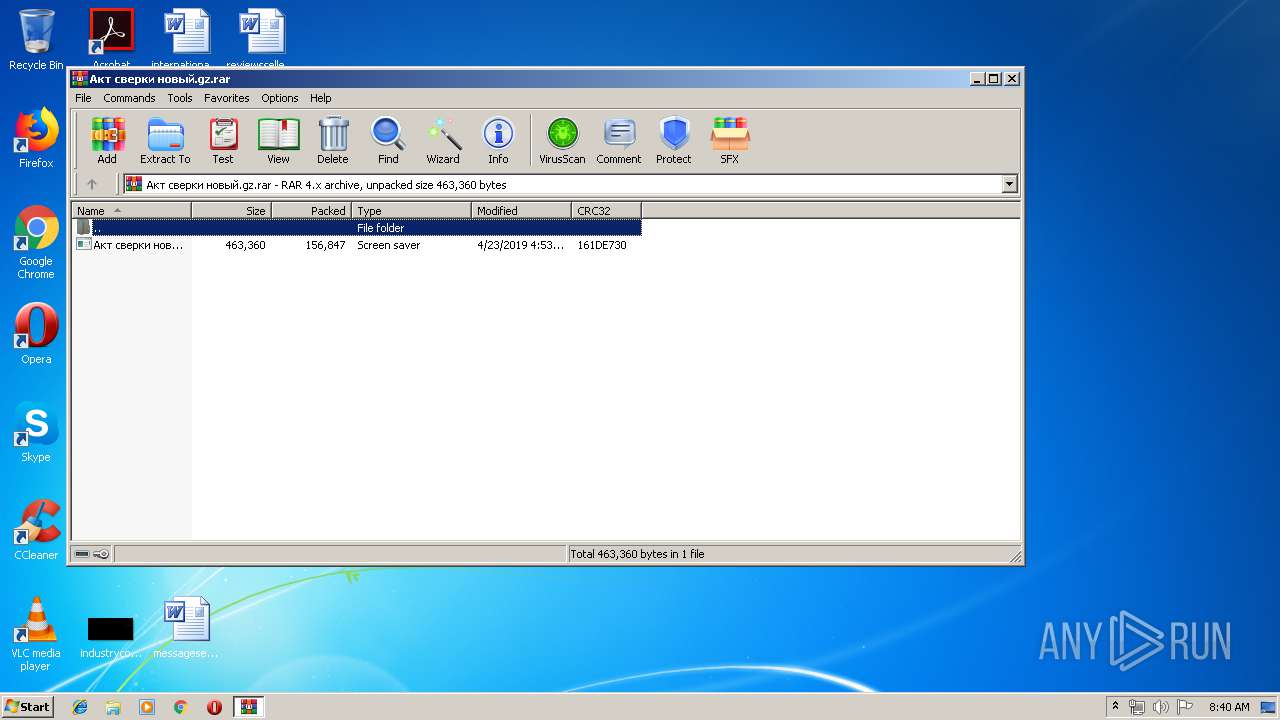
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 8D62E0739C61C9B850A311640F2ED983 |
| SHA1: | C56CA90C517666B215C21161317CE80098CD23DE |
| SHA256: | 8D122585AA9A83CA53733A23743C2C5FBB4341016D678EAC9D149840746BF36C |
| SSDEEP: | 3072:8ahhQIIM/S2ACMh+rofO4LnosAEbKdMon+5FrAZNcBeD6TG/ALyYlbLFmiIO:8AgCsD27s9bK2noOS/4miIO |
MALICIOUS
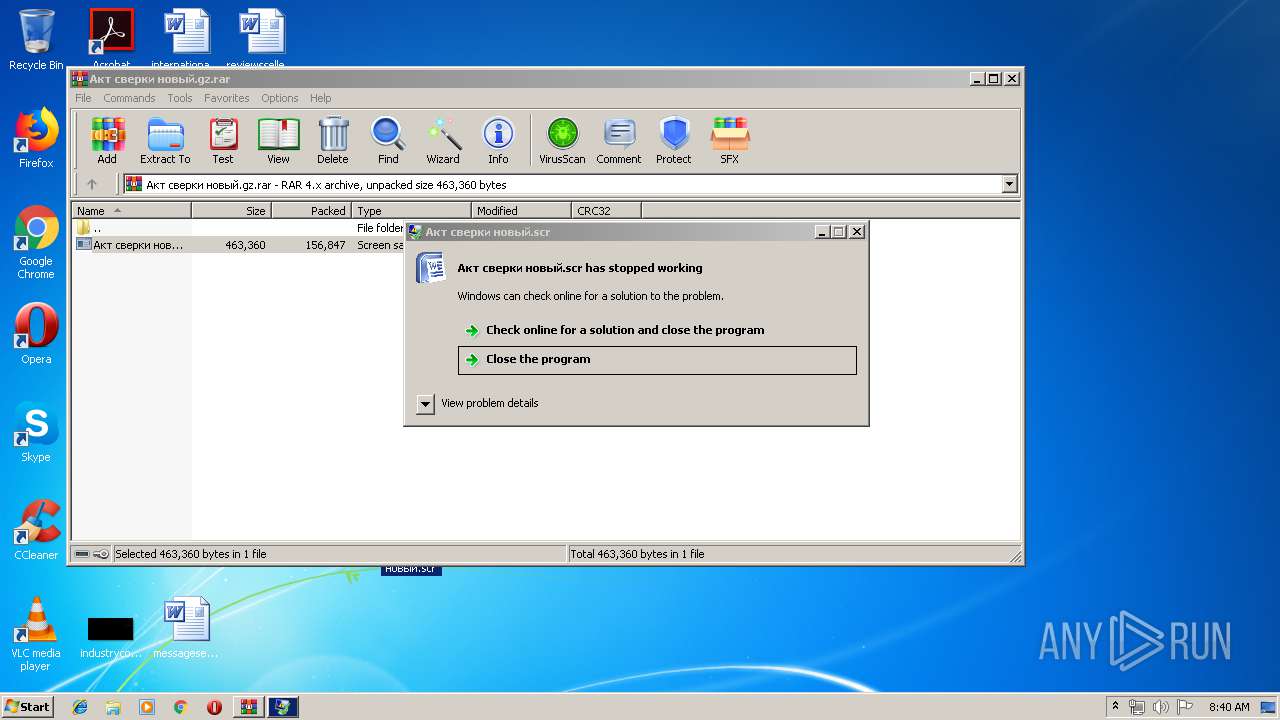
Application was dropped or rewritten from another process
- Акт сверки новый.scr (PID: 944)
- Акт сверки новый.scr (PID: 1412)
- int.exe (PID: 5928)
Deletes shadow copies
- cmd.exe (PID: 3180)
- cmd.exe (PID: 4252)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 4228)
Changes the autorun value in the registry
- mshta.exe (PID: 4276)
SUSPICIOUS
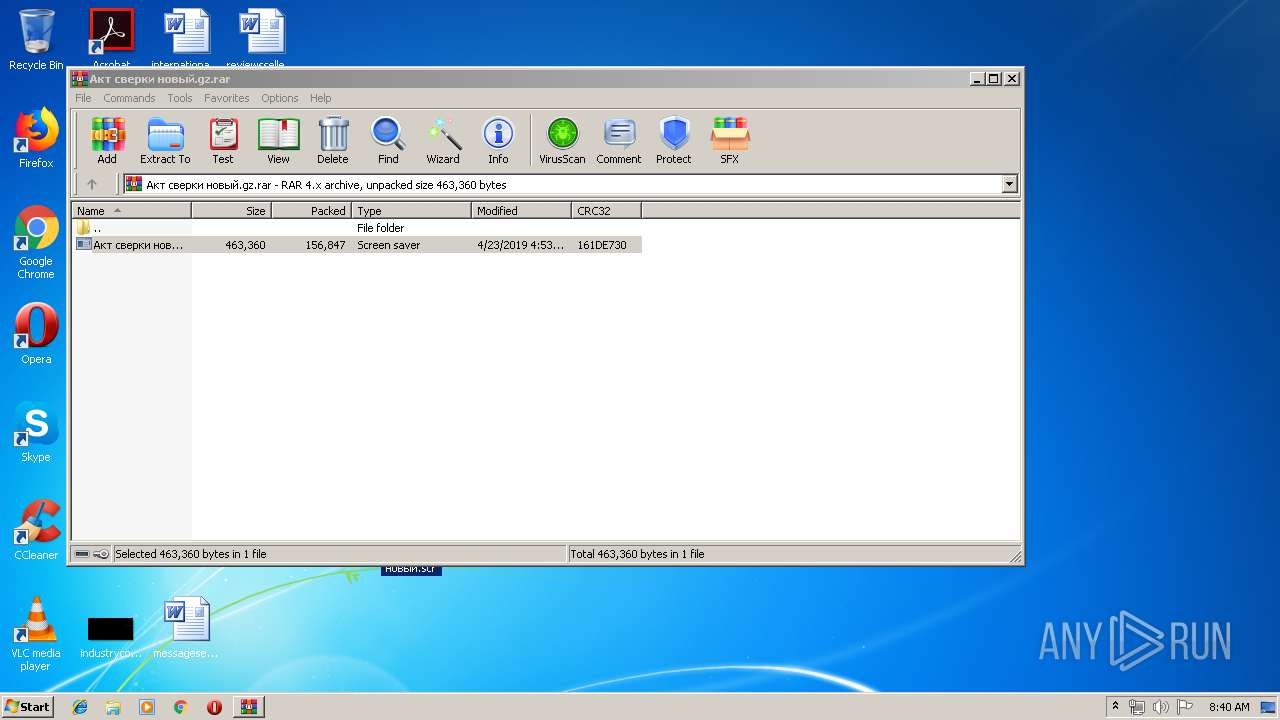
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2152)
- cmd.exe (PID: 5984)
Starts application with an unusual extension
- WinRAR.exe (PID: 2152)
Creates files in the user directory
- cmd.exe (PID: 5984)
Starts MSHTA.EXE for opening HTA or HTMLS files
- Акт сверки новый.scr (PID: 1412)
- int.exe (PID: 5928)
Starts itself from another location
- Акт сверки новый.scr (PID: 1412)
Starts CMD.EXE for commands execution
- Акт сверки новый.scr (PID: 1412)
- mshta.exe (PID: 5596)
Executed via COM
- DllHost.exe (PID: 3200)
- DllHost.exe (PID: 736)
Creates files in the program directory
- int.exe (PID: 5928)
INFO
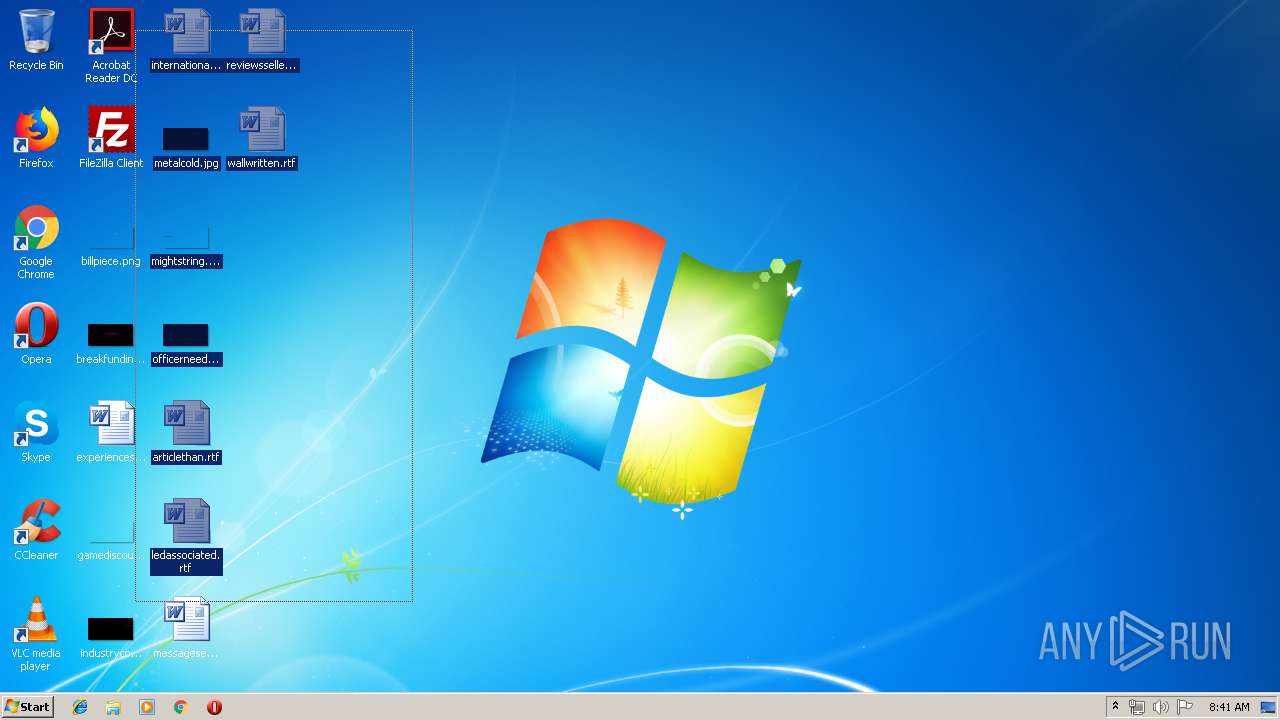
Manual execution by user
- Акт сверки новый.scr (PID: 1412)
- WINWORD.EXE (PID: 1680)
- WINWORD.EXE (PID: 2944)
Reads internet explorer settings
- mshta.exe (PID: 5768)
- mshta.exe (PID: 5596)
- mshta.exe (PID: 4276)
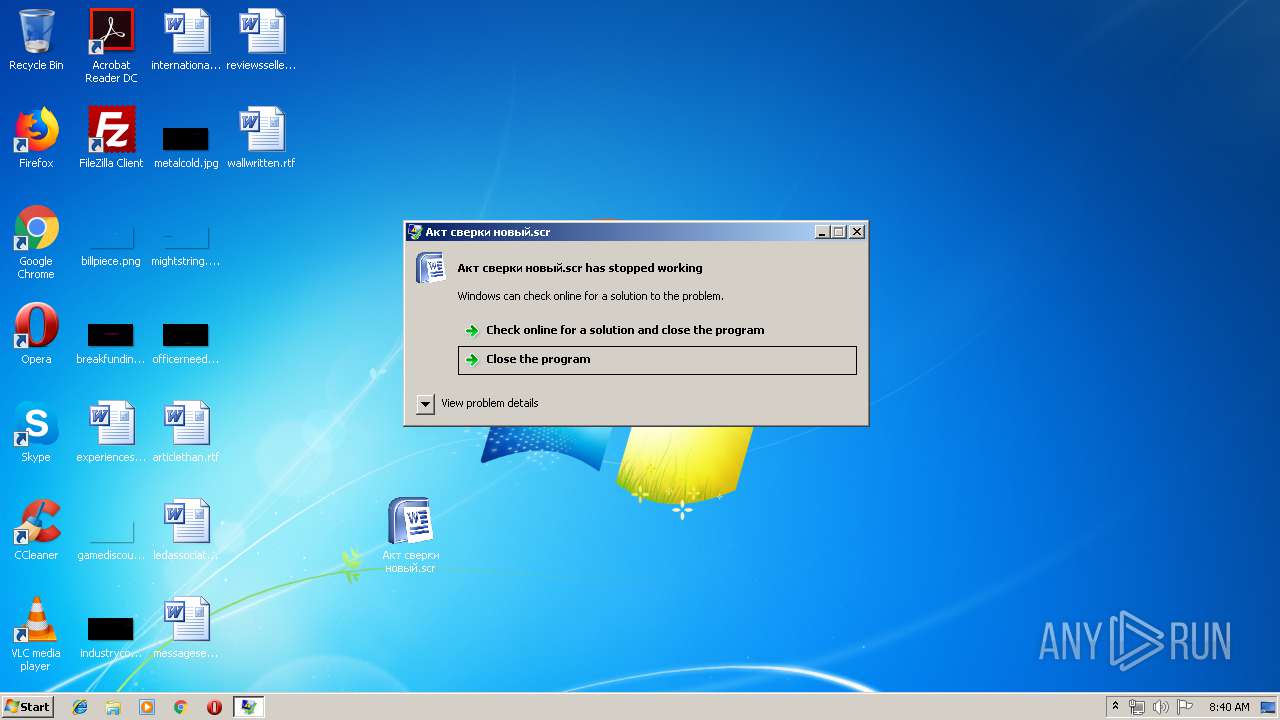
Application was crashed
- Акт сверки новый.scr (PID: 944)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 156914 |
|---|---|
| UncompressedSize: | 463360 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:04:23 04:53:19 |
| PackingMethod: | Normal |
| ArchivedFileName: | ??? ᢥન ?????.scr |
Total processes
63
Monitored processes
22
Malicious processes
6
Suspicious processes
0
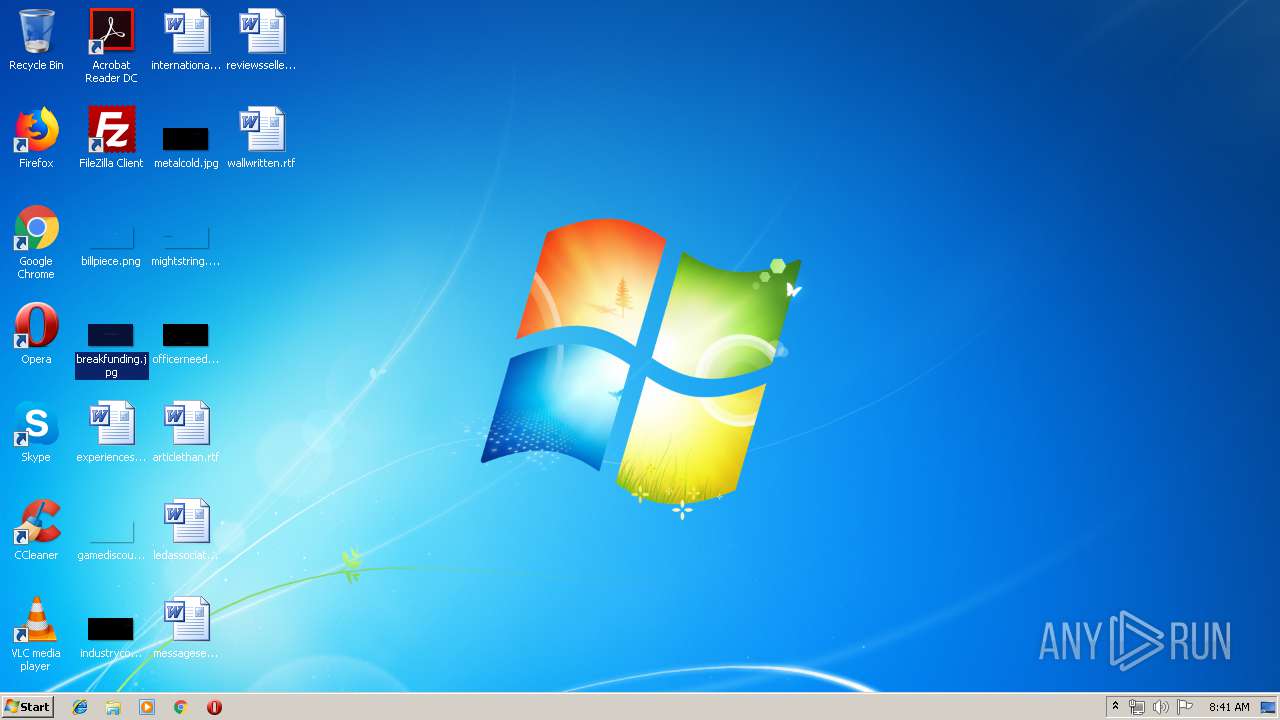
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa2152.13751\Акт сверки новый.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa2152.13751\Акт сверки новый.scr | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225725 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\Desktop\Акт сверки новый.scr" /S | C:\Users\admin\Desktop\Акт сверки новый.scr | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\wallwritten.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1976 | "C:\Windows\System32\cmd.exe" /c wbadmin DELETE SYSTEMSTATEBACKUP -keepVersions:0 | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967293 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Акт сверки новый.gz.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2368 | "C:\Windows\System32\cmd.exe" /c bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ledassociated.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3180 | "C:\Windows\System32\cmd.exe" /c vssadmin Delete Shadows /All /Quiet | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3200 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 167
Read events
1 212
Write events
1 953
Delete events
2
Modification events
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Акт сверки новый.gz.rar | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @shell32,-10162 |
Value: Screen saver | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
159
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2152.14004\Акт сверки новый.scr | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\я | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\=bvWYdiTLM+zrp+PH+4b8iq+n5dxsk.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\PkBv65gbk1wkiWhPgOHNgqwIRHw.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\d+z8LkxAY=CtZE4BizTSa1Szm1zuoA.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | — | |
MD5:— | SHA256:— | |||
| 5928 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\J3CFXlN68GOH9flJMCtpS5cj.bbbfl | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report