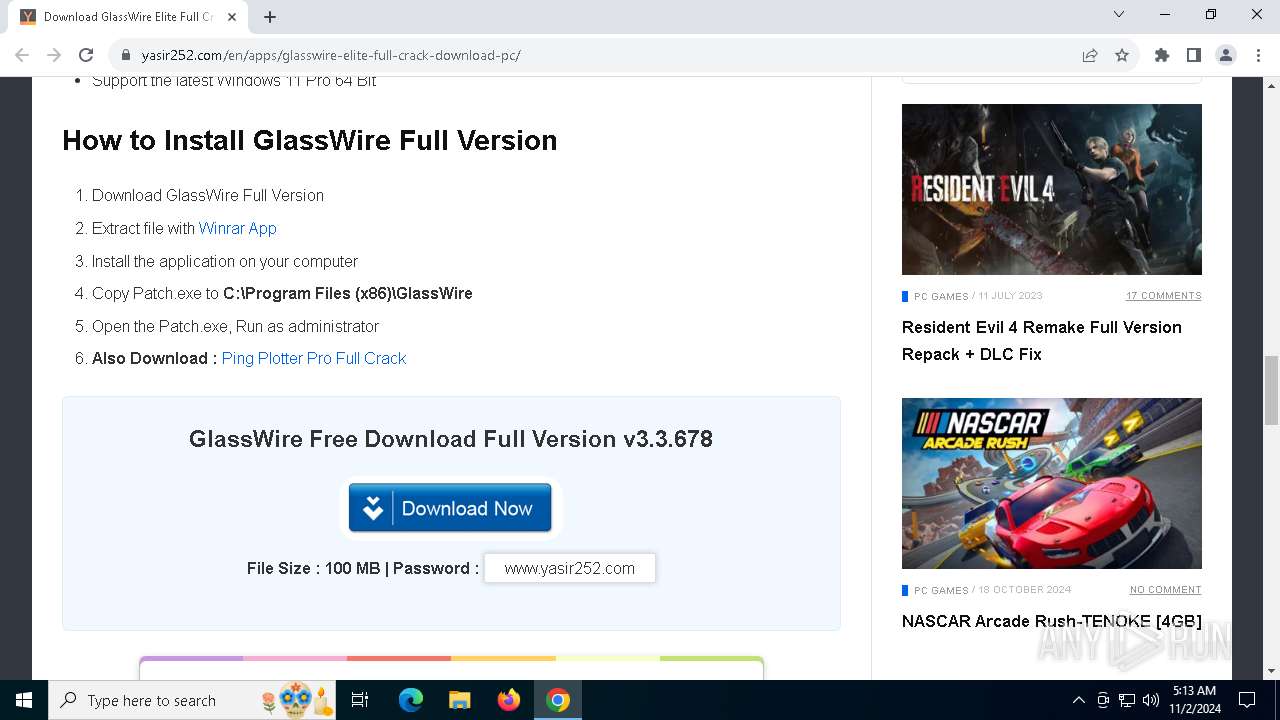
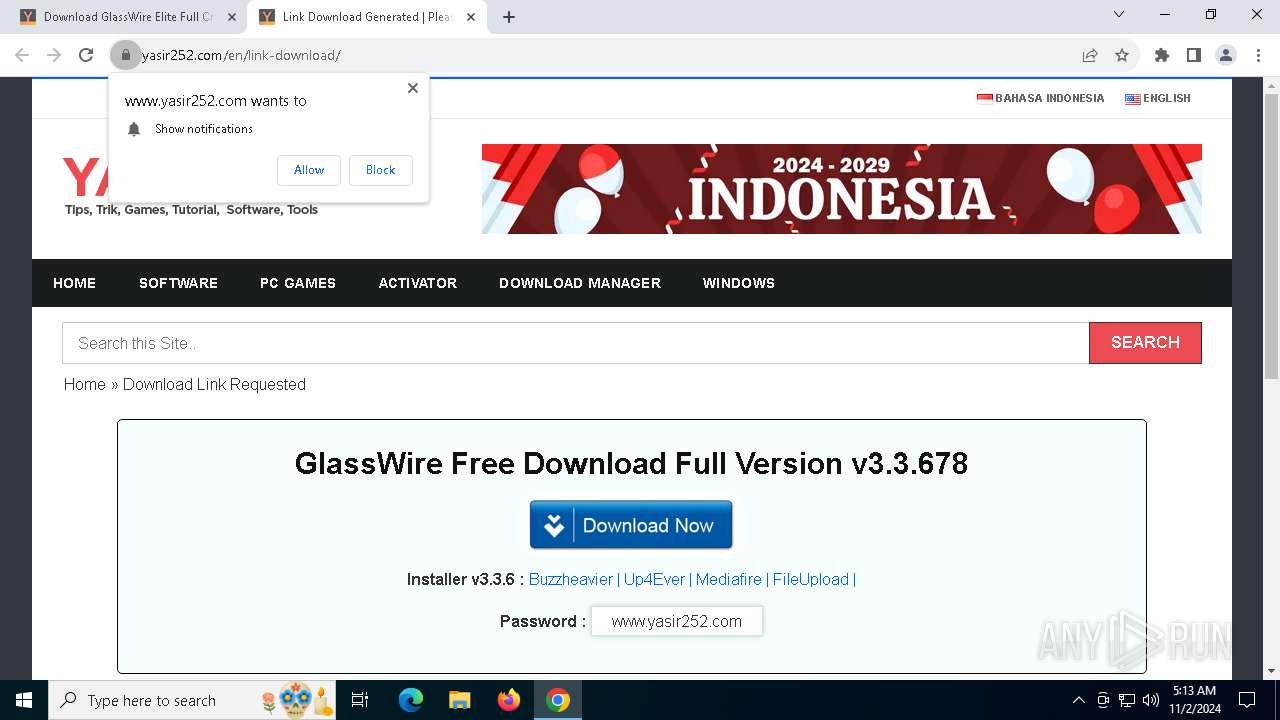
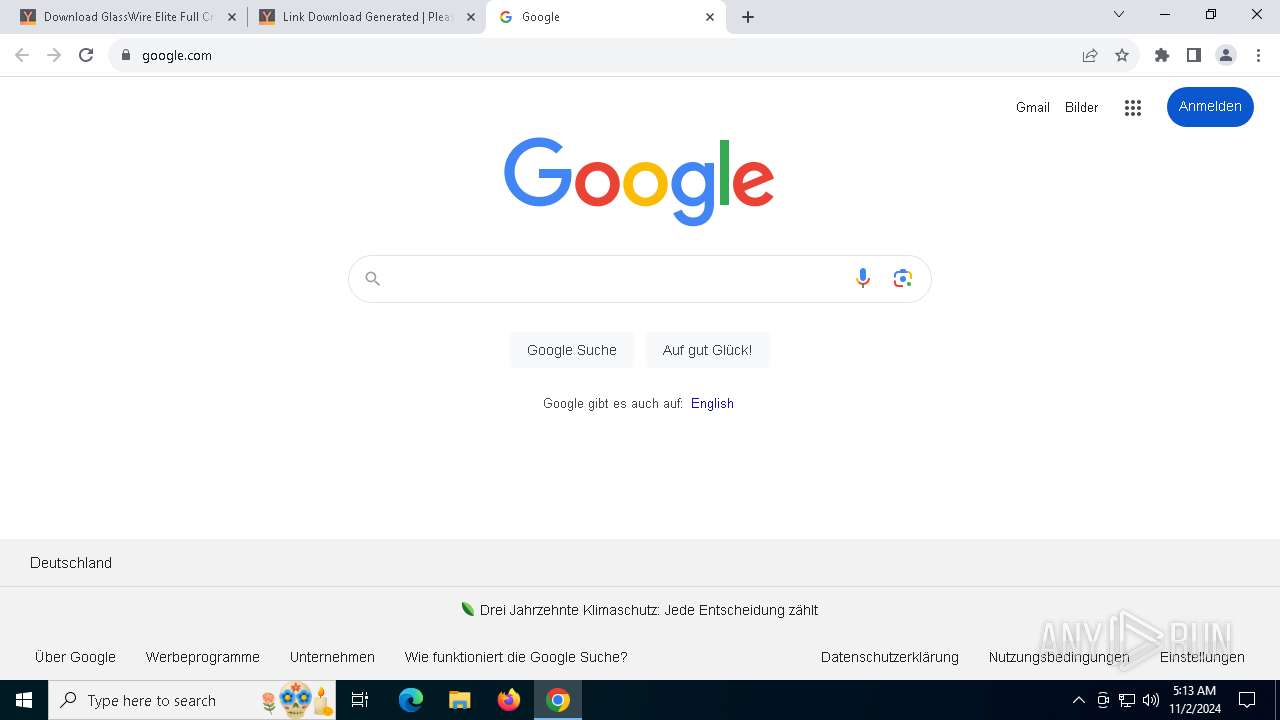
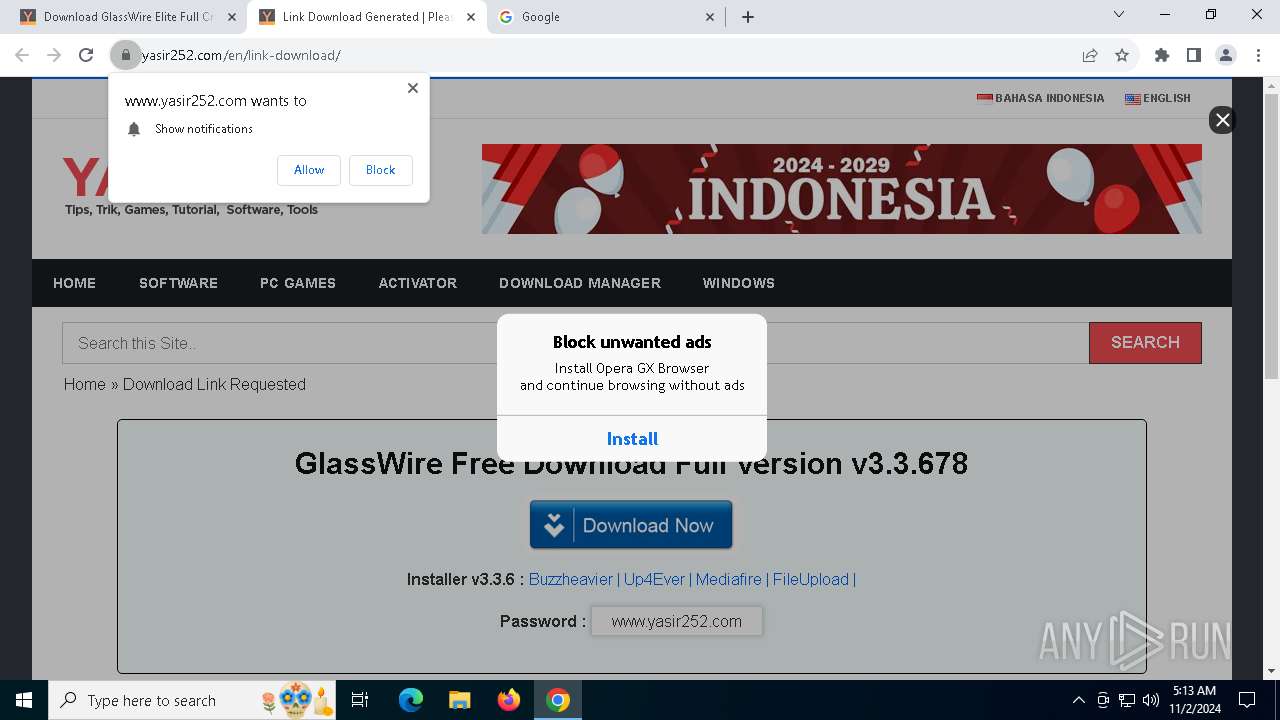
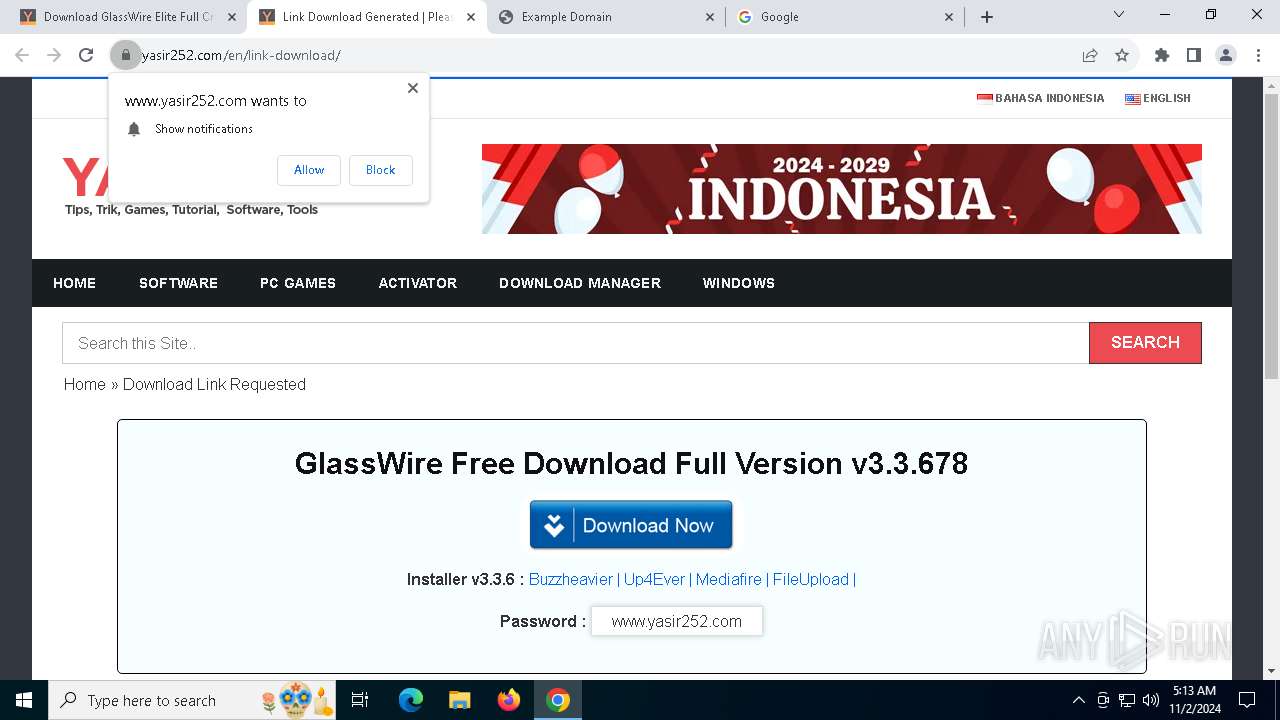
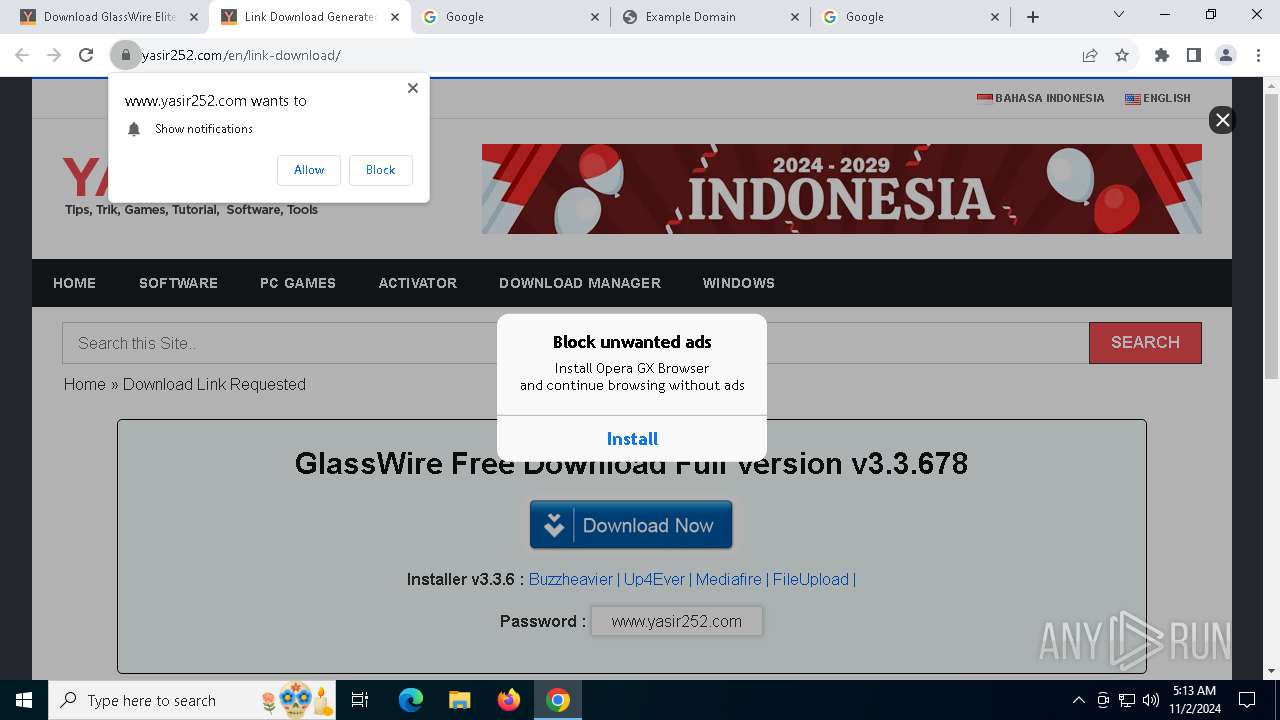
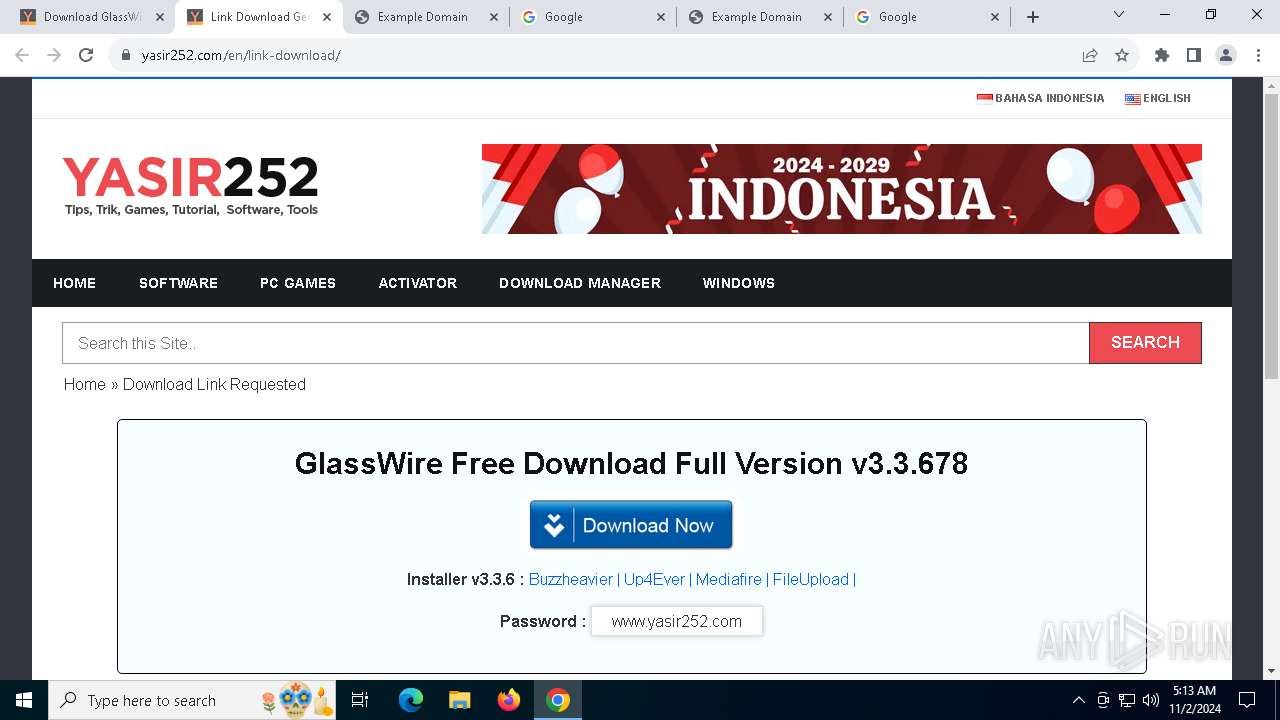
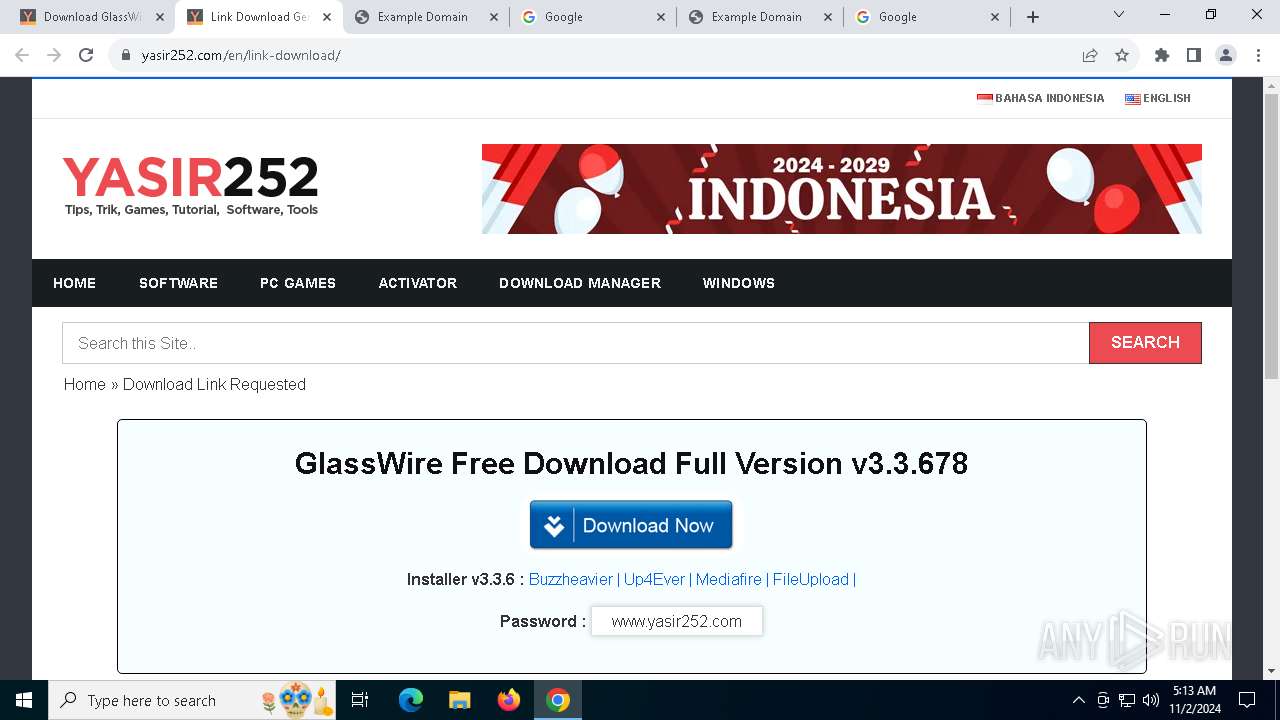
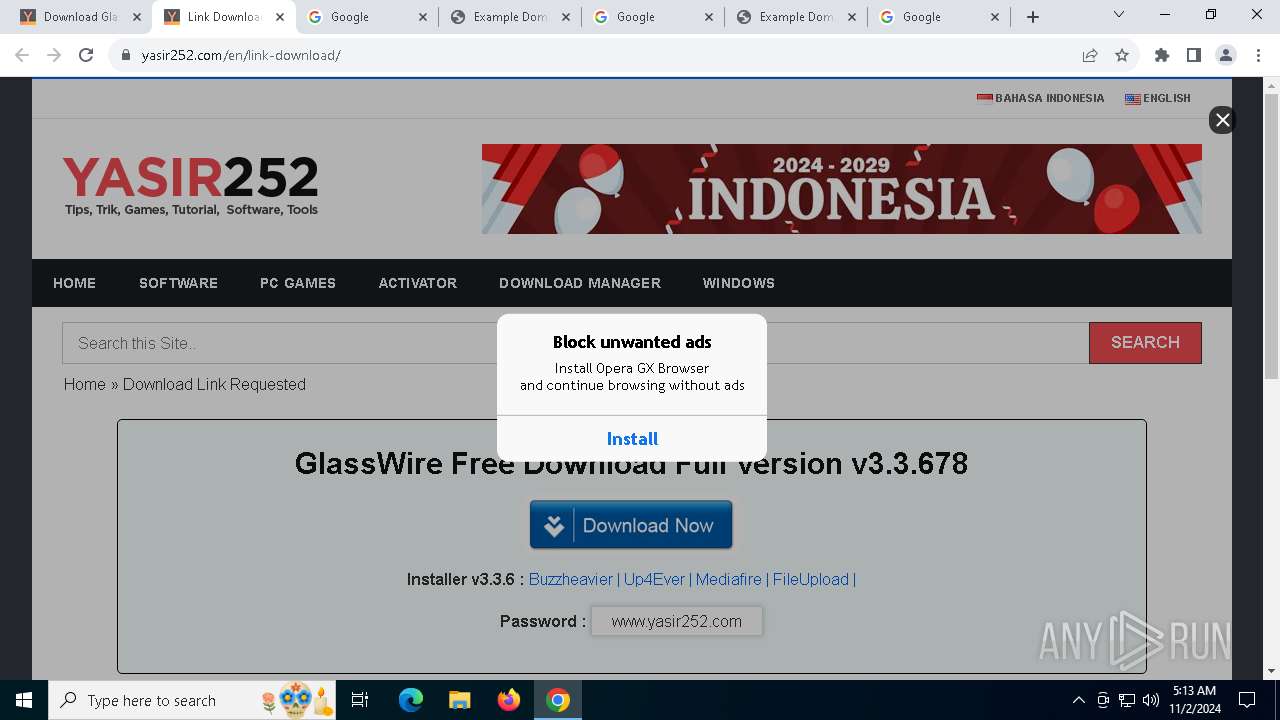
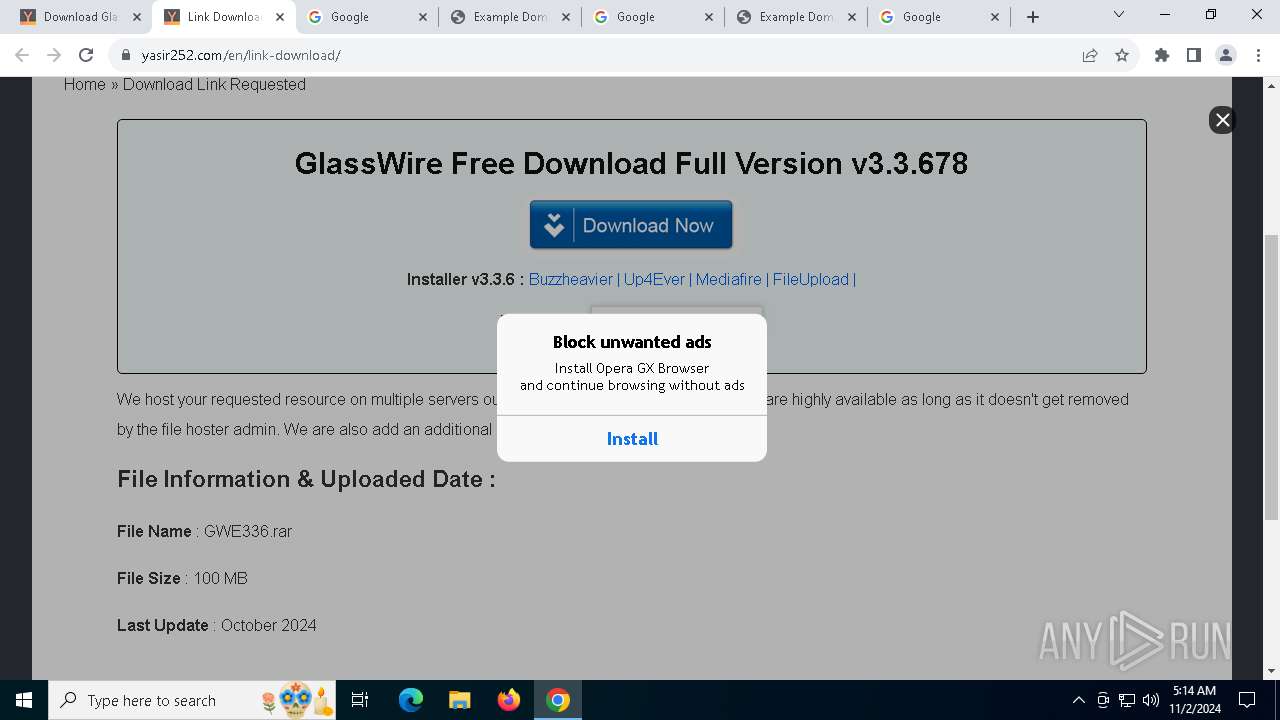
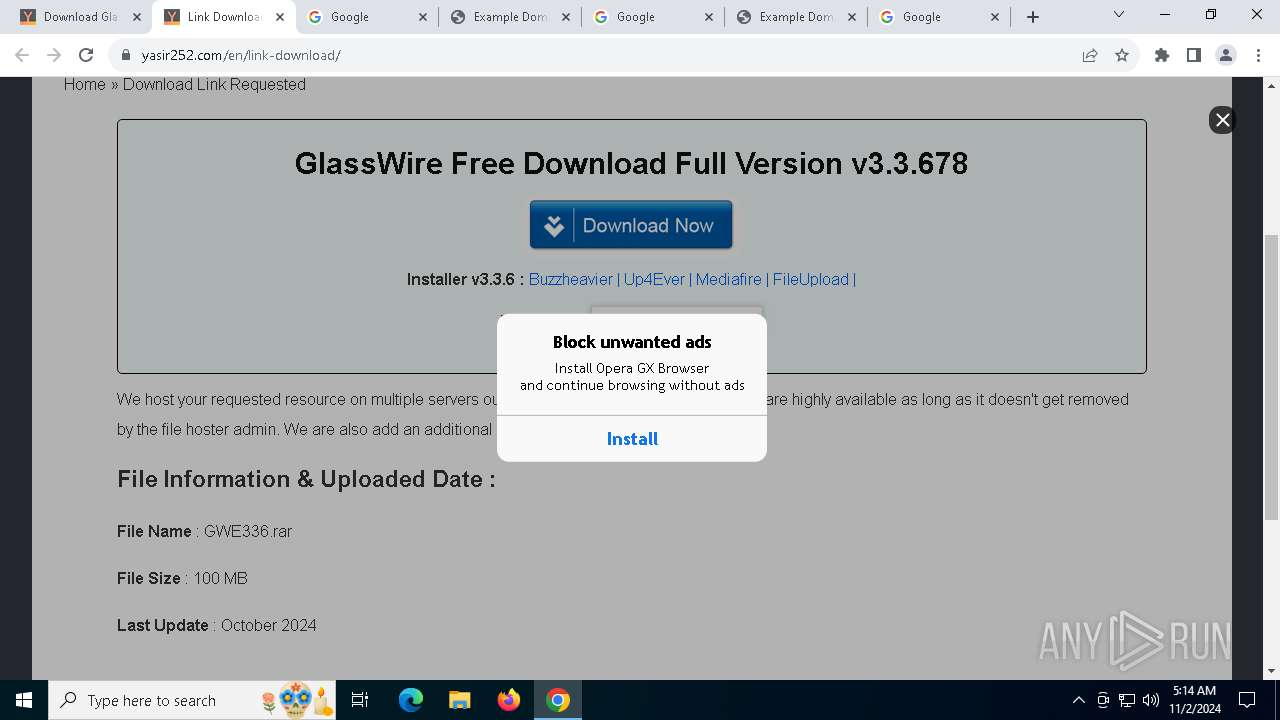
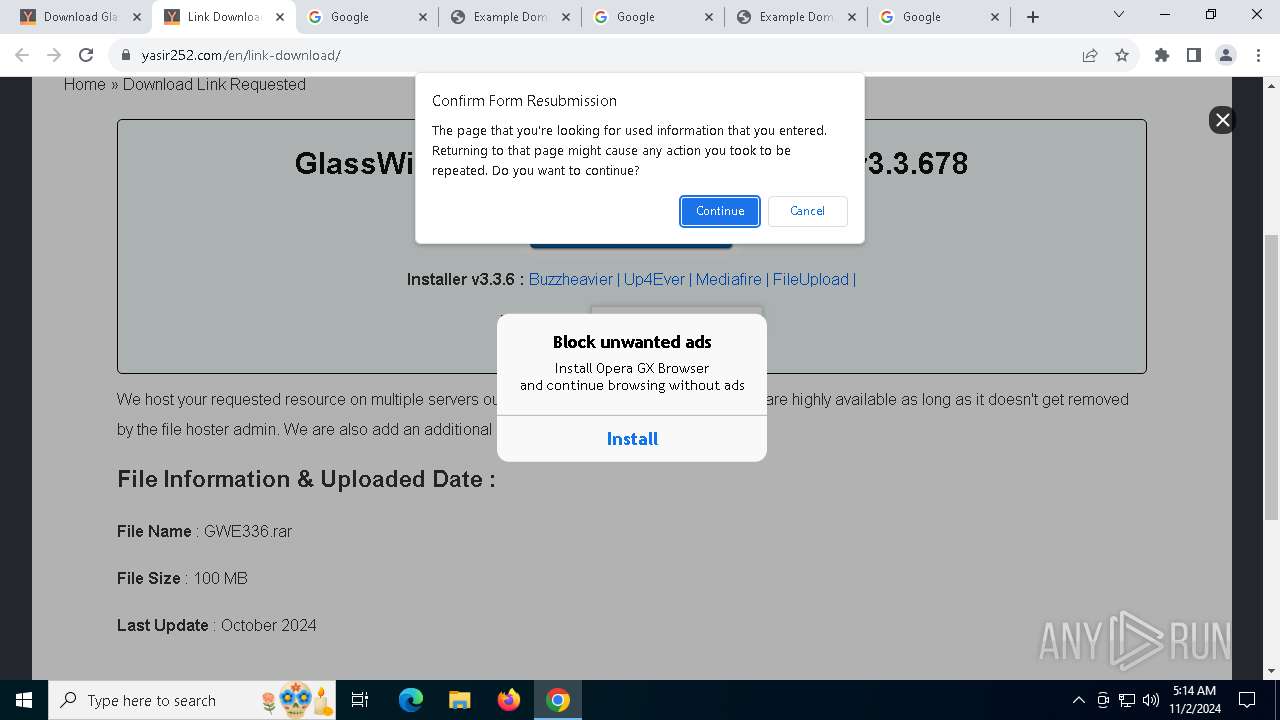
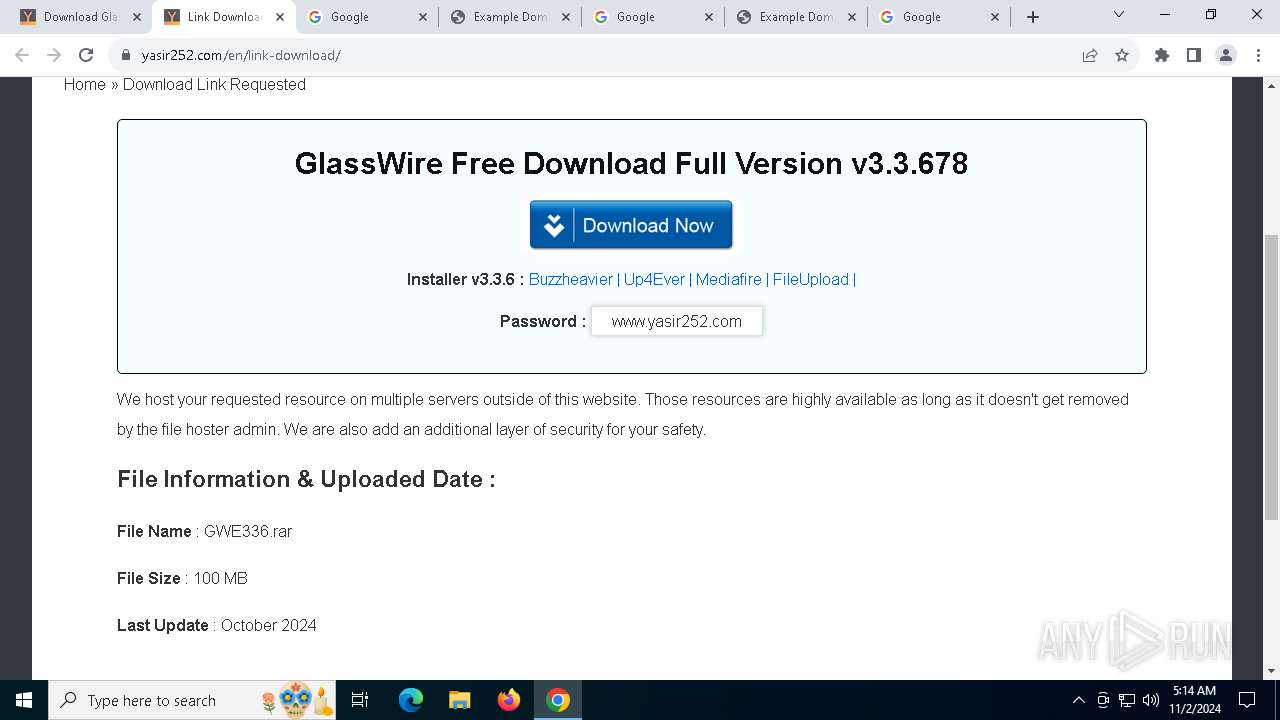
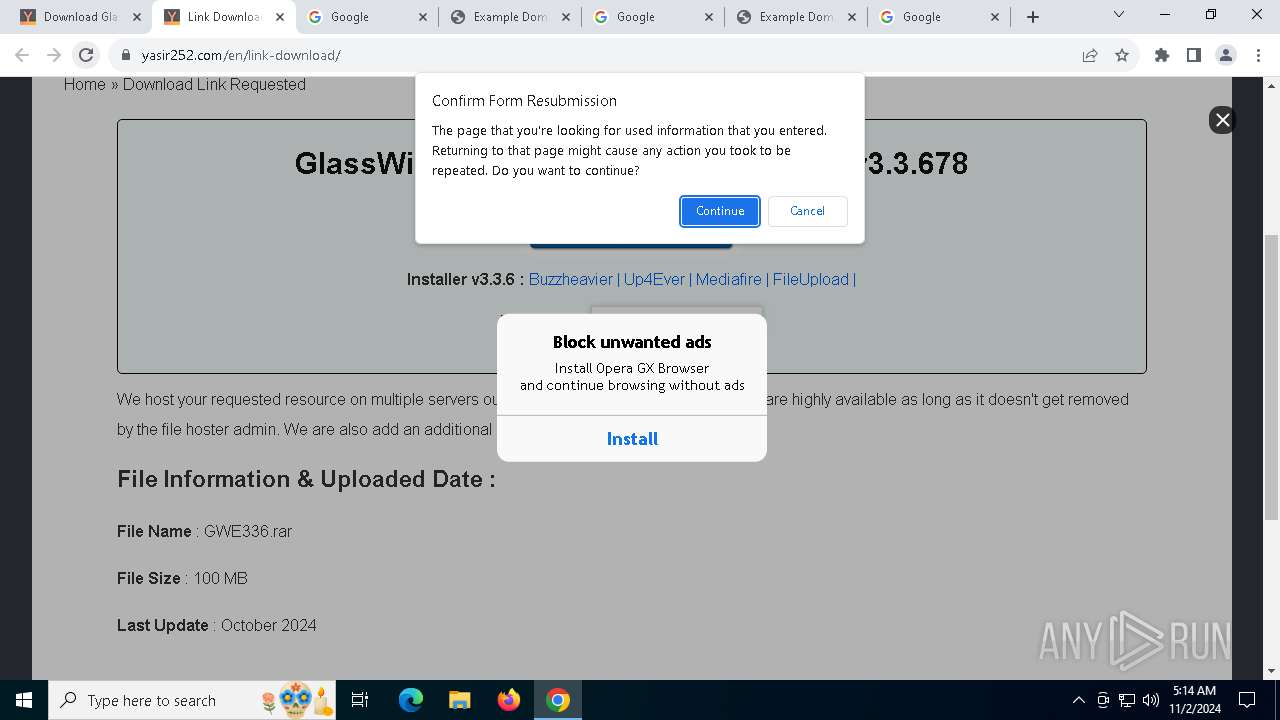
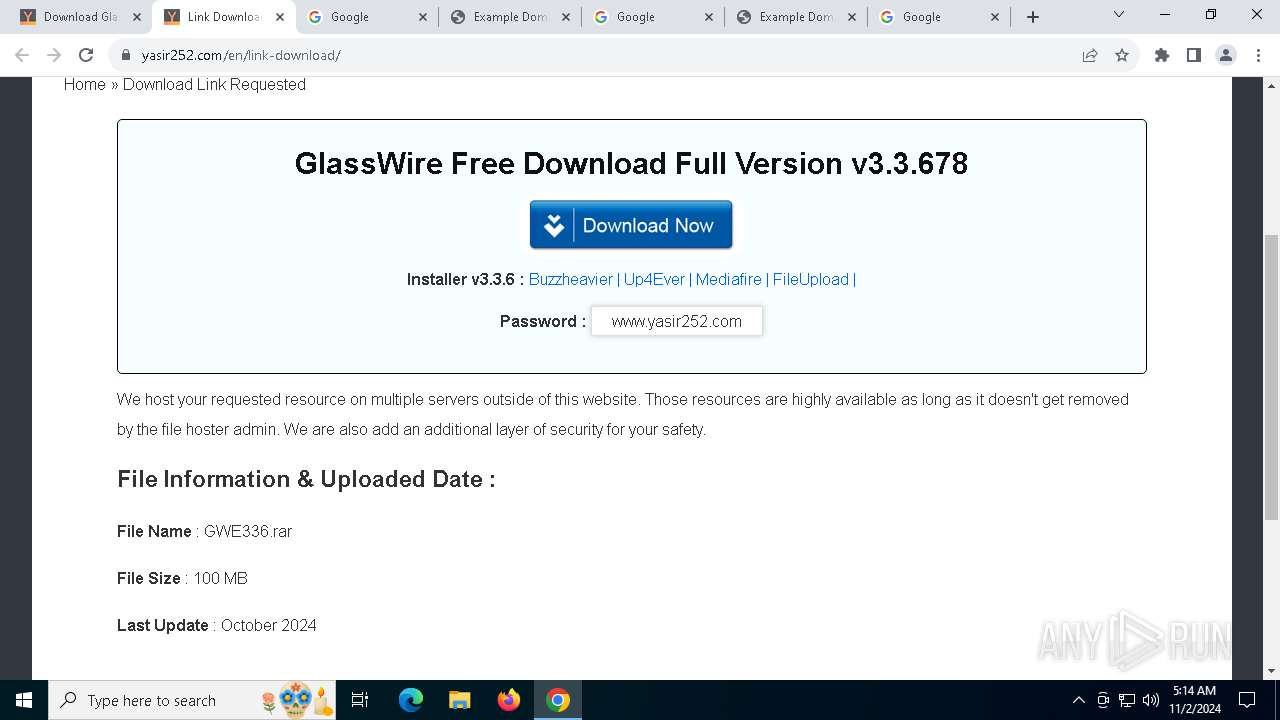
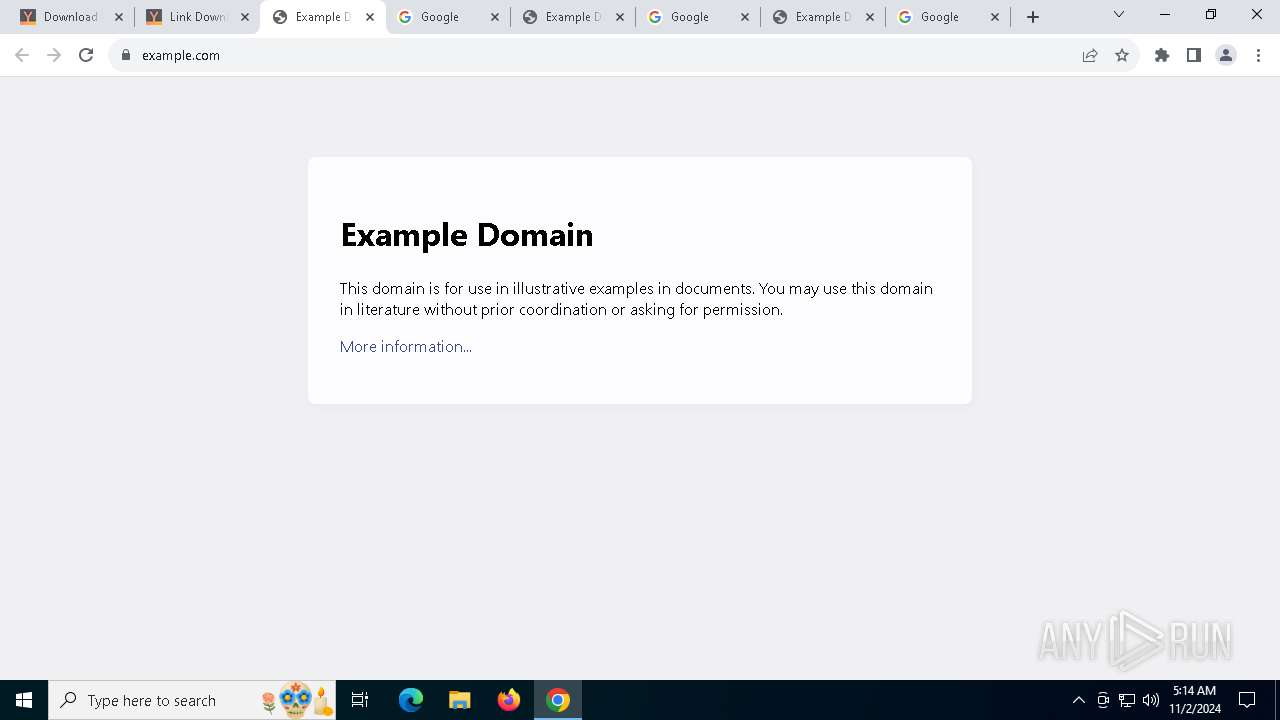
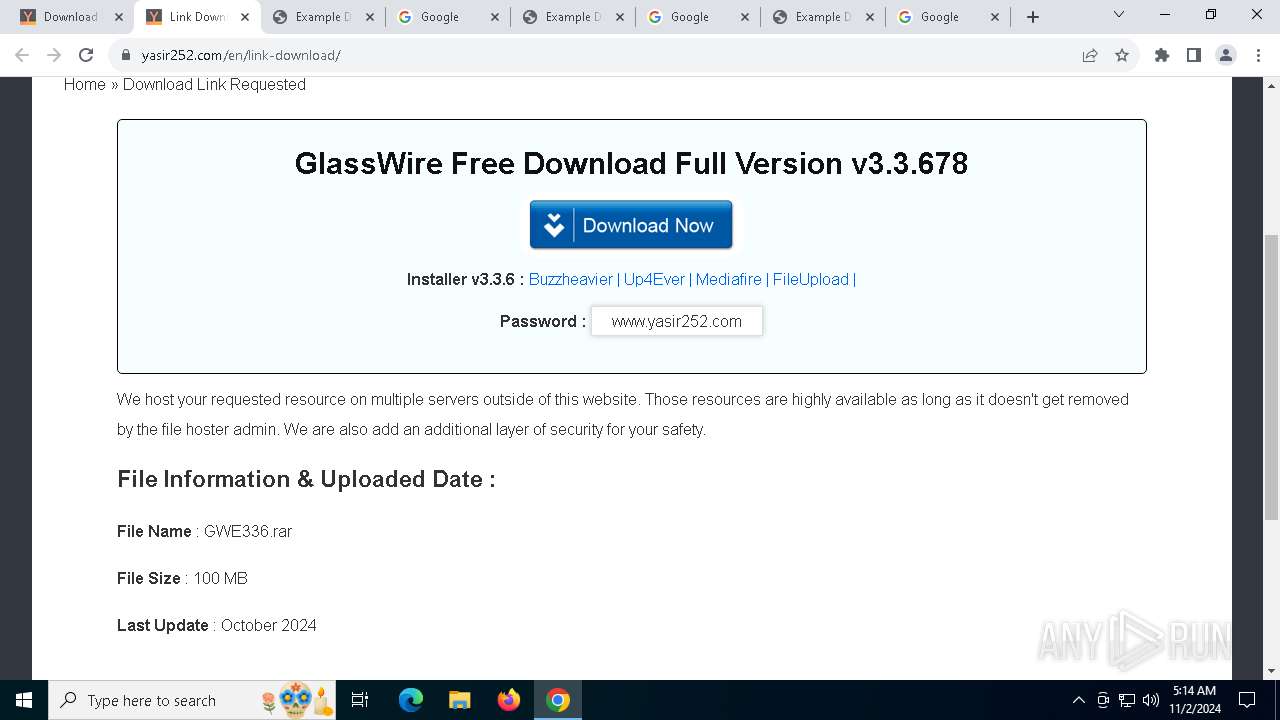
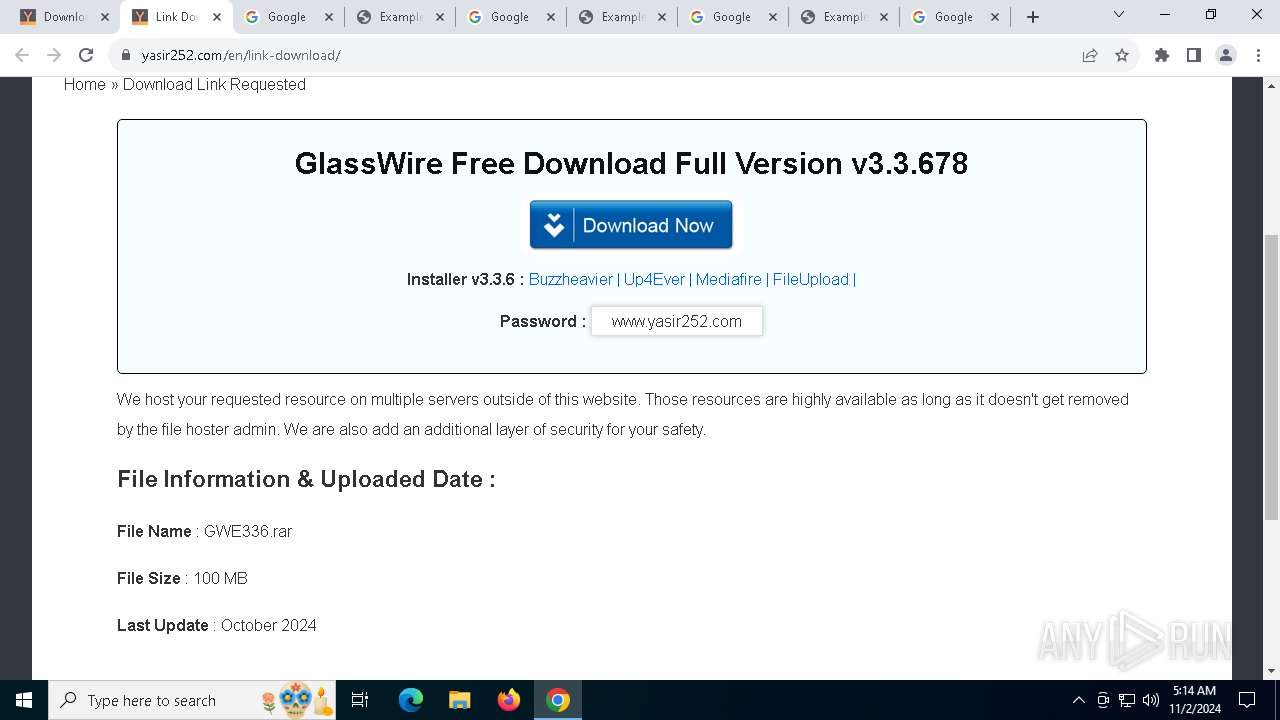
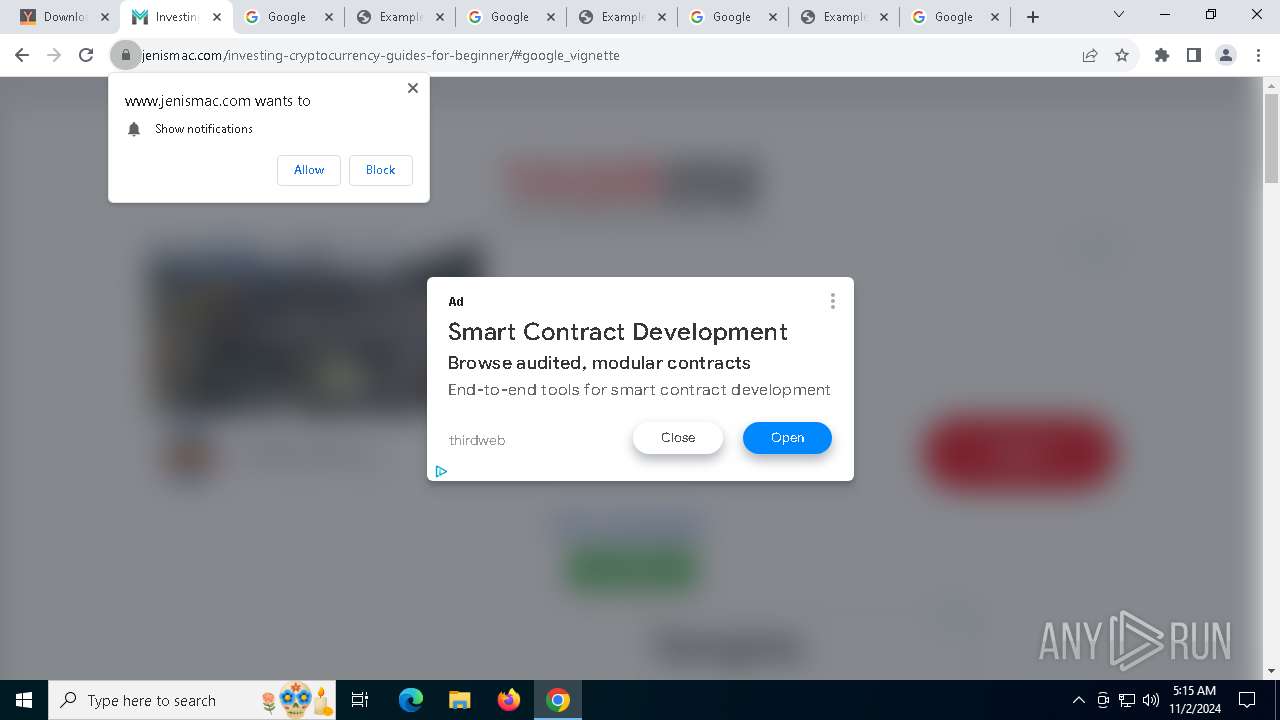
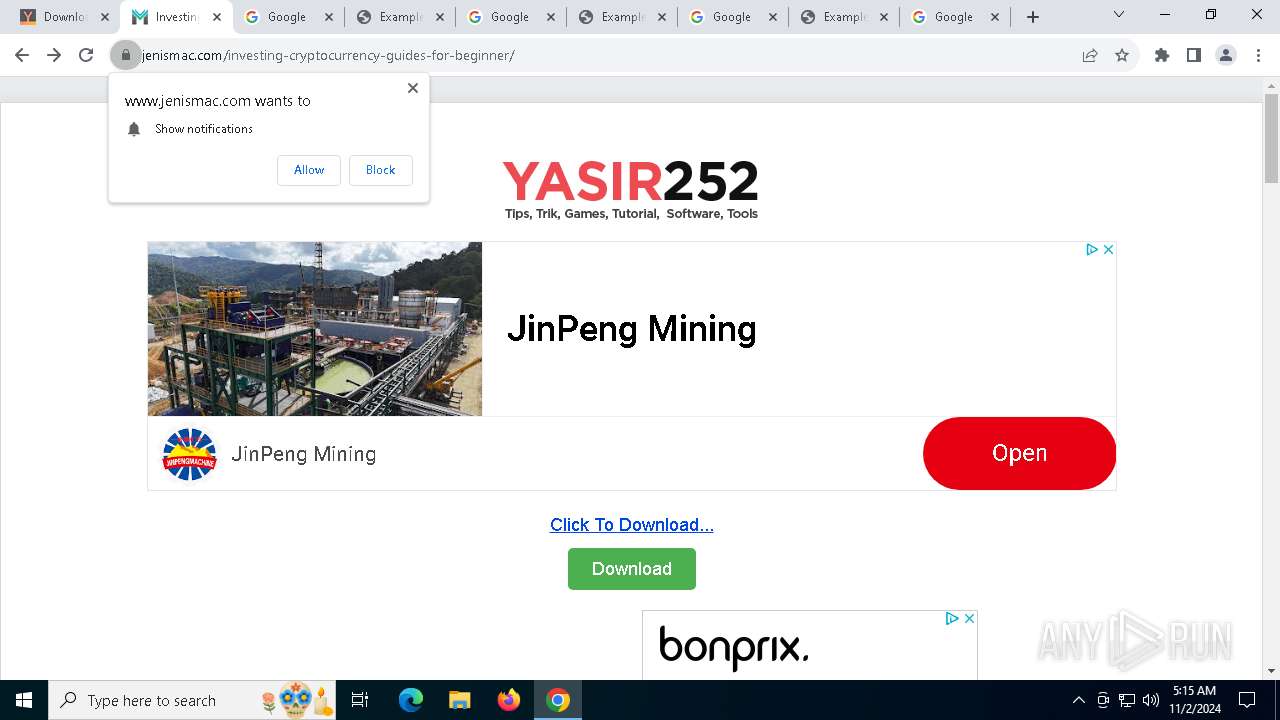
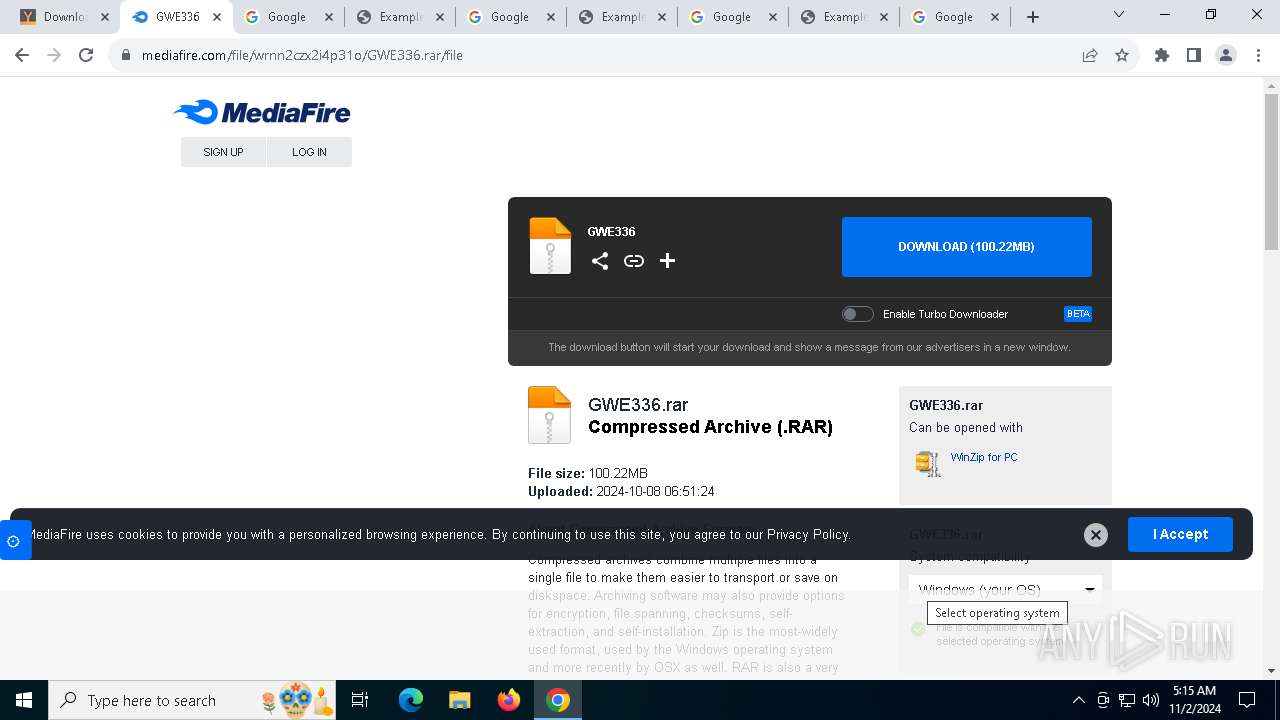
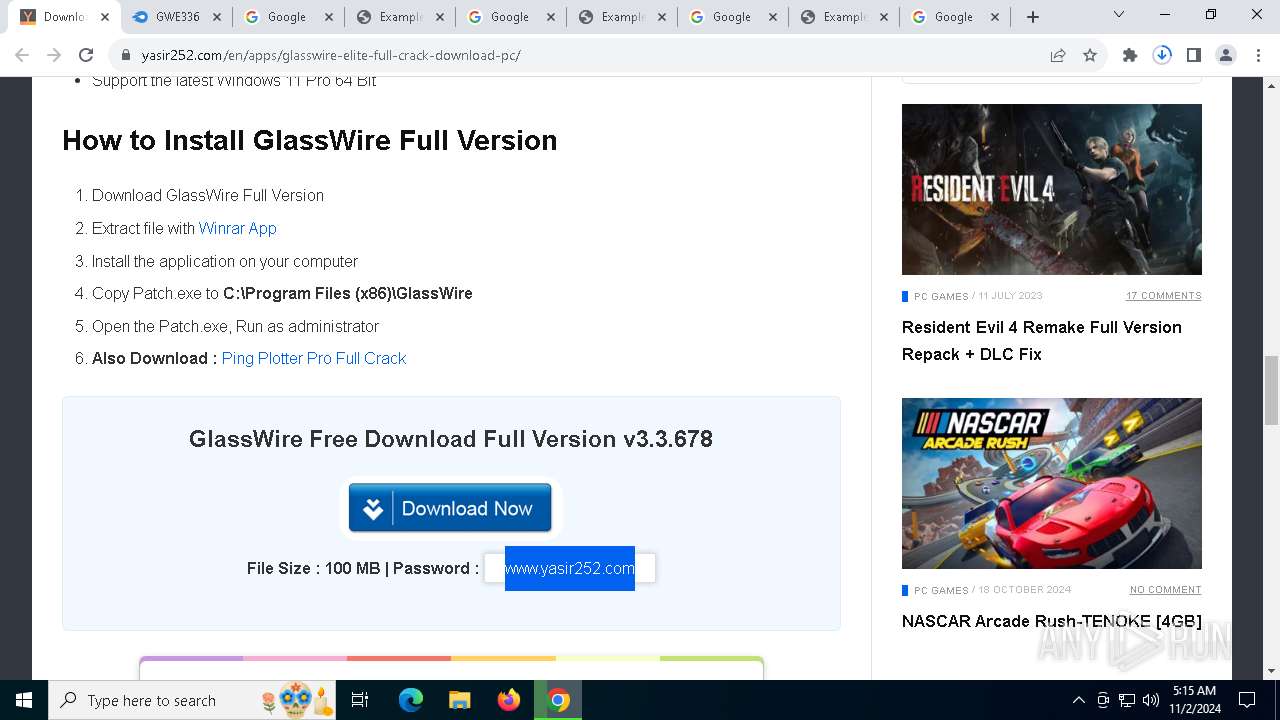
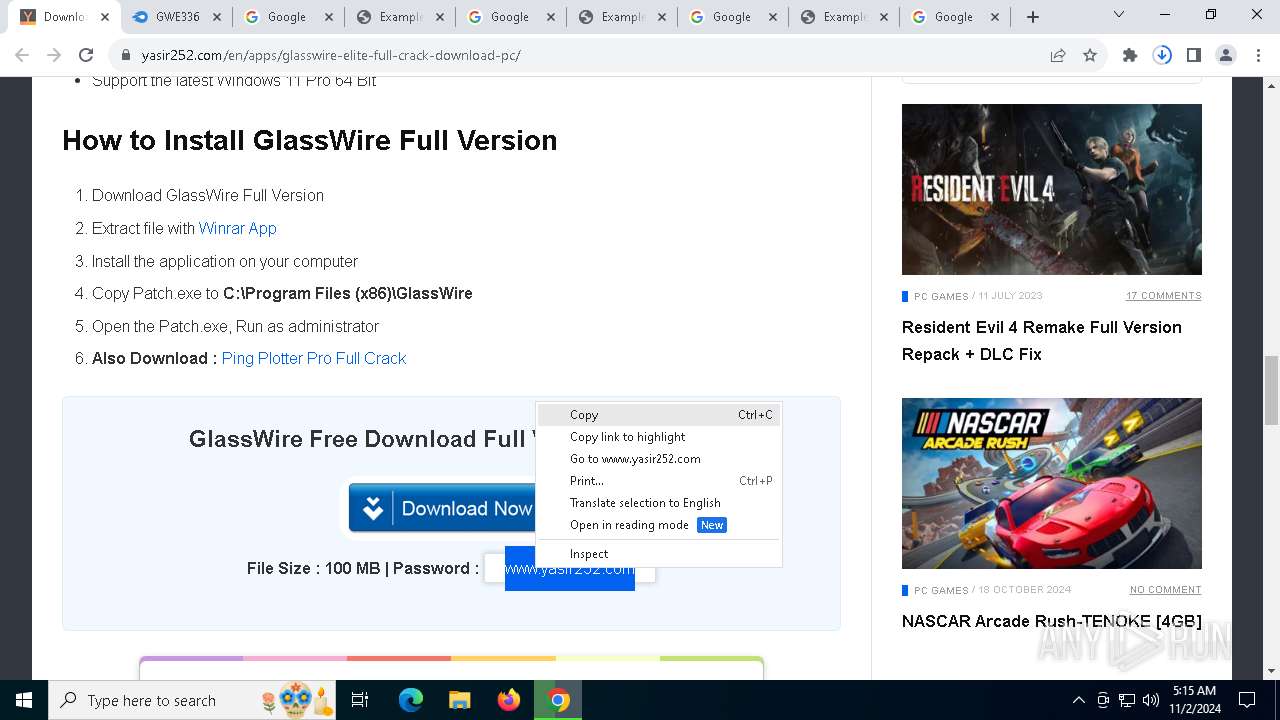
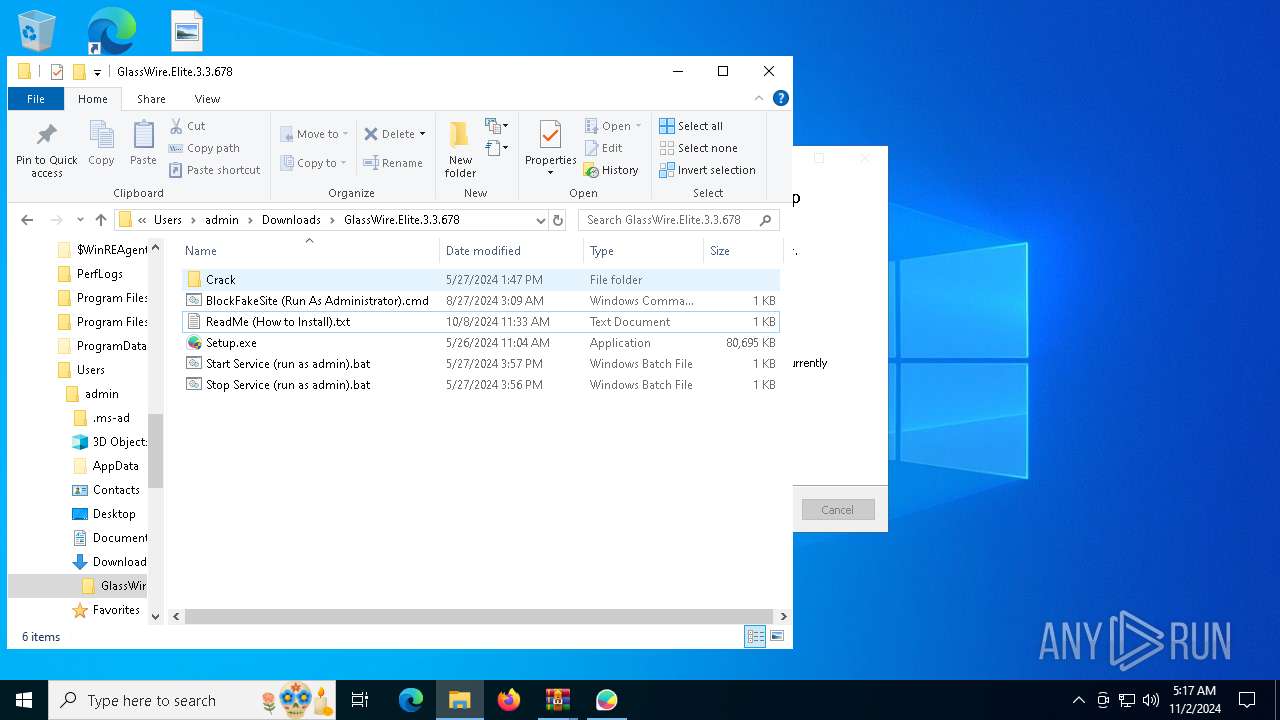
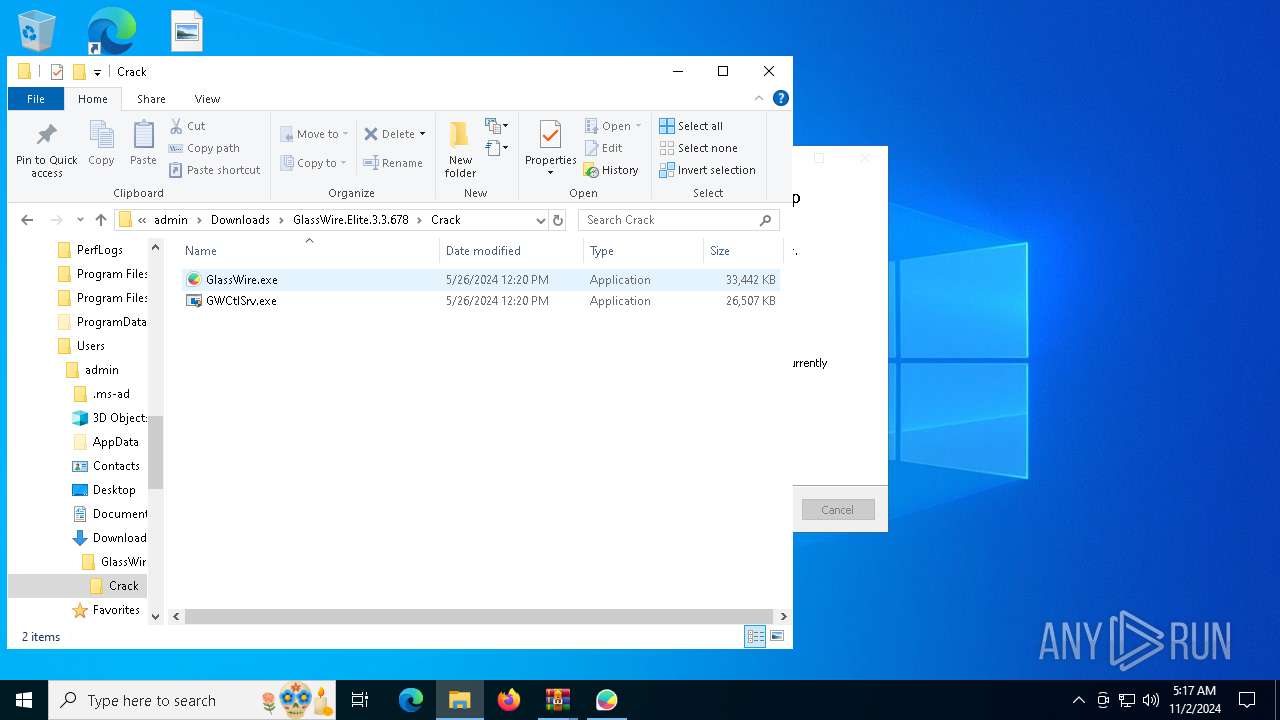
| URL: | https://www.yasir252.com/en/apps/glasswire-elite-full-crack-download-pc/ |
| Full analysis: | https://app.any.run/tasks/a4a6f091-6820-465c-9a41-4ad798346952 |
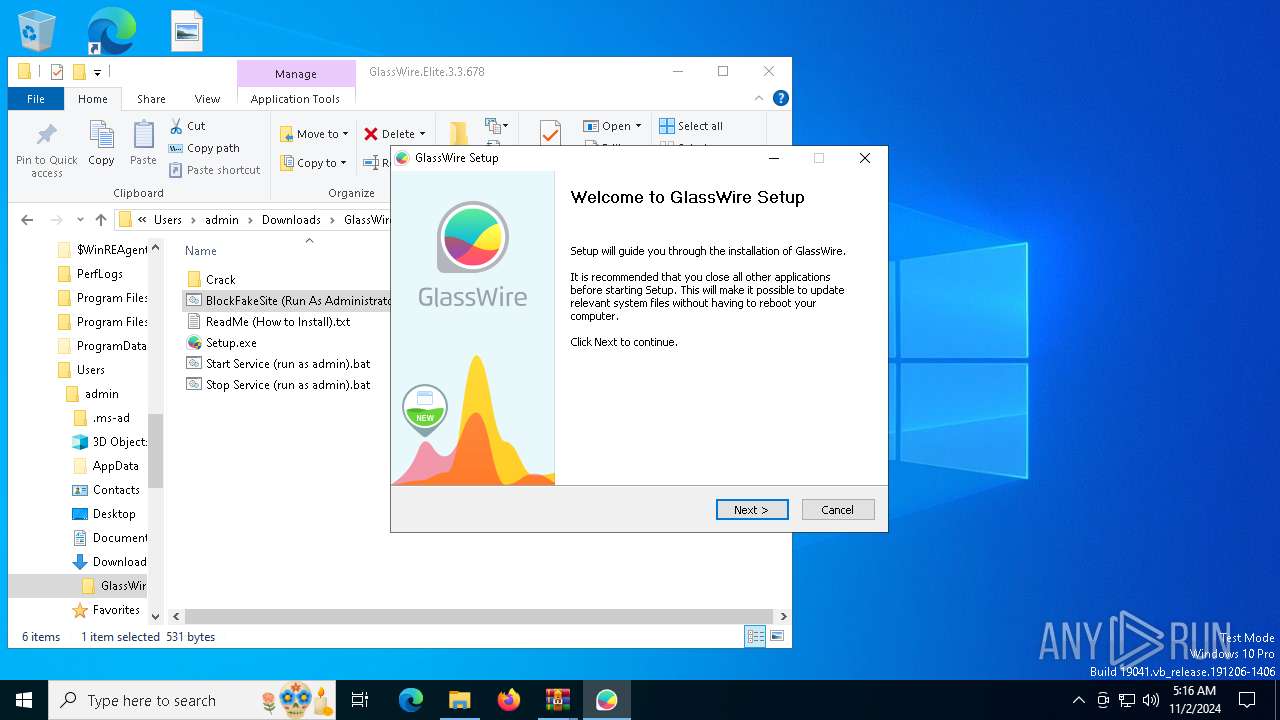
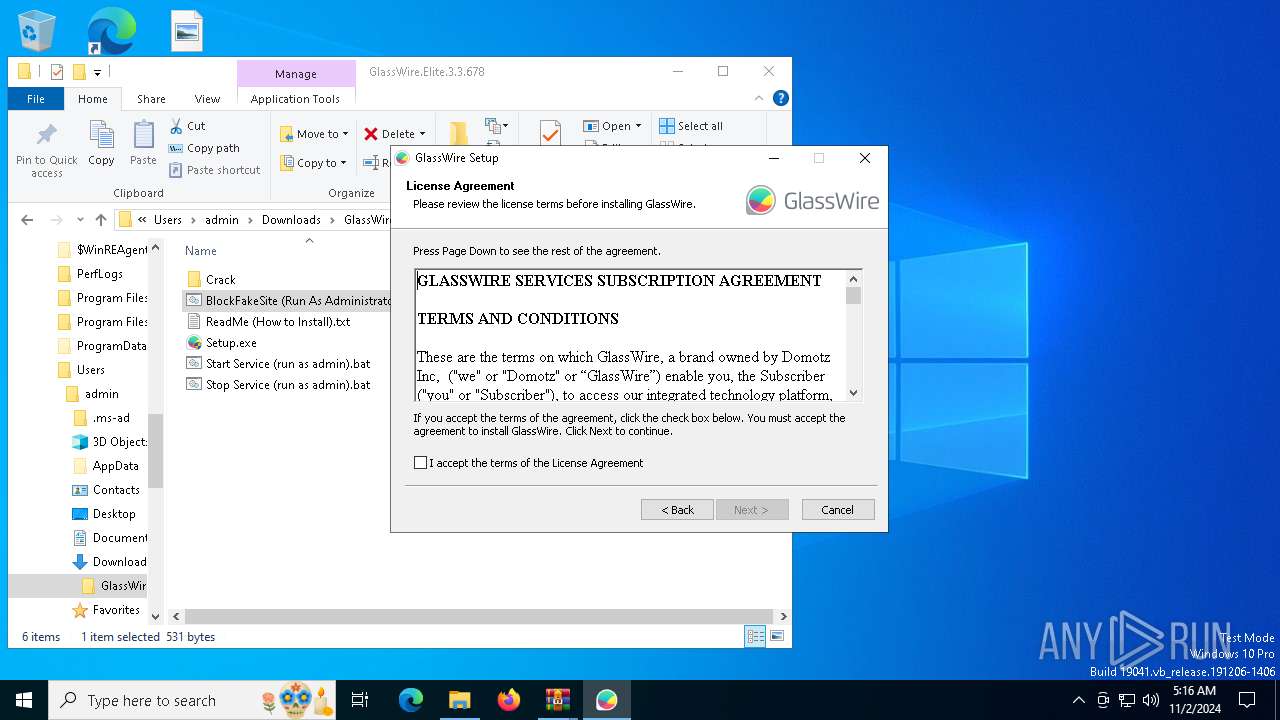
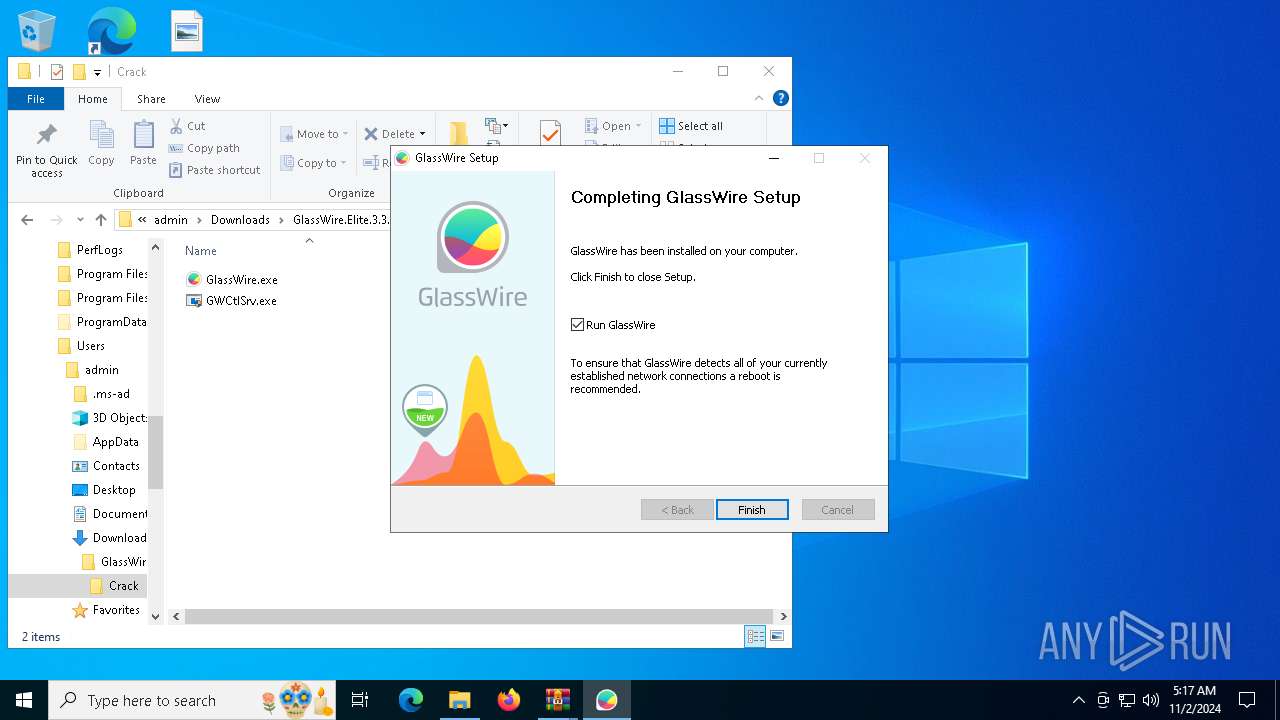
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2024, 05:13:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
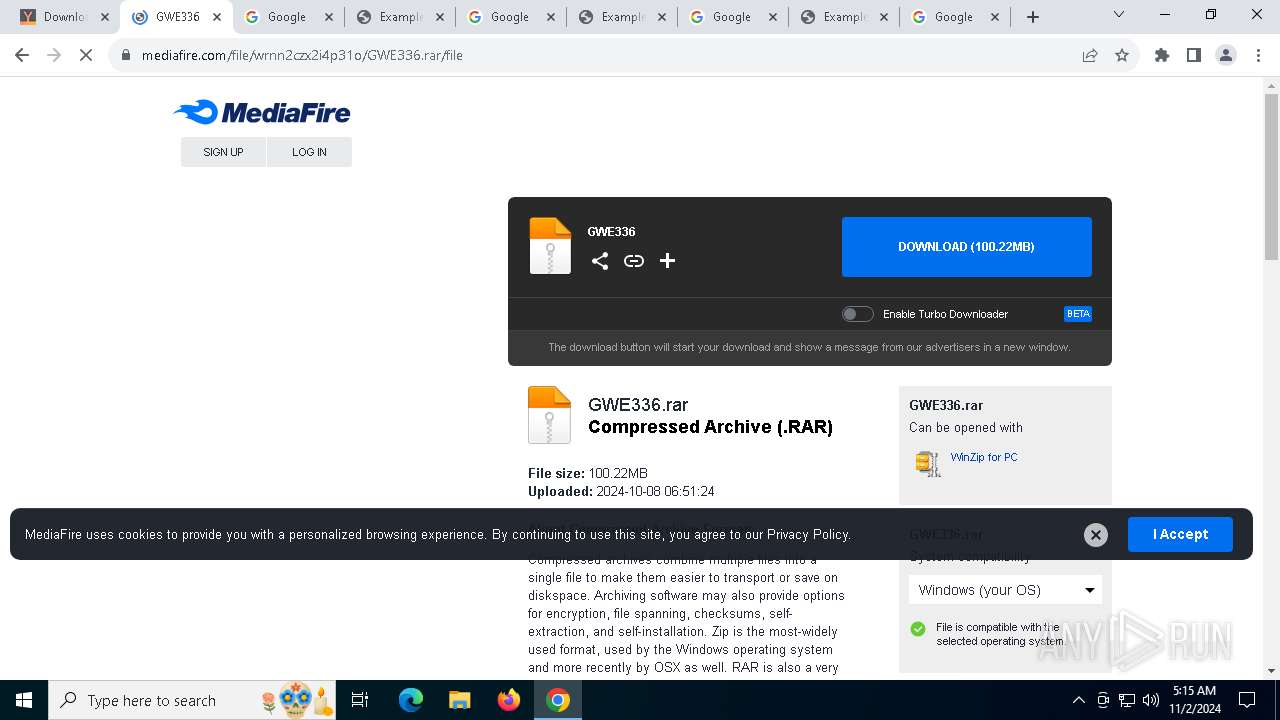
| MD5: | 03FFC1B4DCCD69B756025ABF54DC1F34 |
| SHA1: | 3445AB557C1196111839E553DDC08457C81D178B |
| SHA256: | 8D0A4D37404536FF9EBD5465331E08413CF9BEA1C6AA3628376C6D115ACD4F3E |
| SSDEEP: | 3:N8DSL1yy+EVpftjAIDcCGOskVGKn:2OLd+CpfxxKO1 |
MALICIOUS
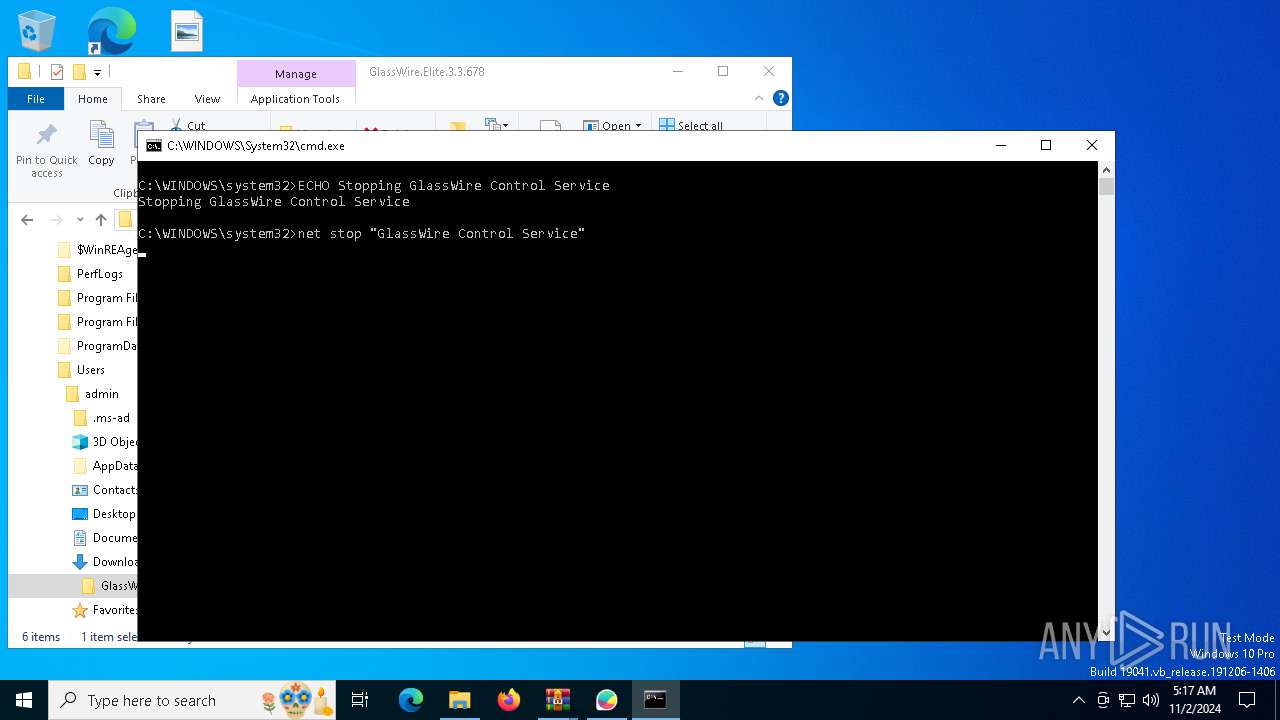
Starts NET.EXE for service management
- net.exe (PID: 6444)
- cmd.exe (PID: 2184)
- Setup.exe (PID: 8164)
- net.exe (PID: 1432)
Changes the autorun value in the registry
- rundll32.exe (PID: 7936)
SUSPICIOUS
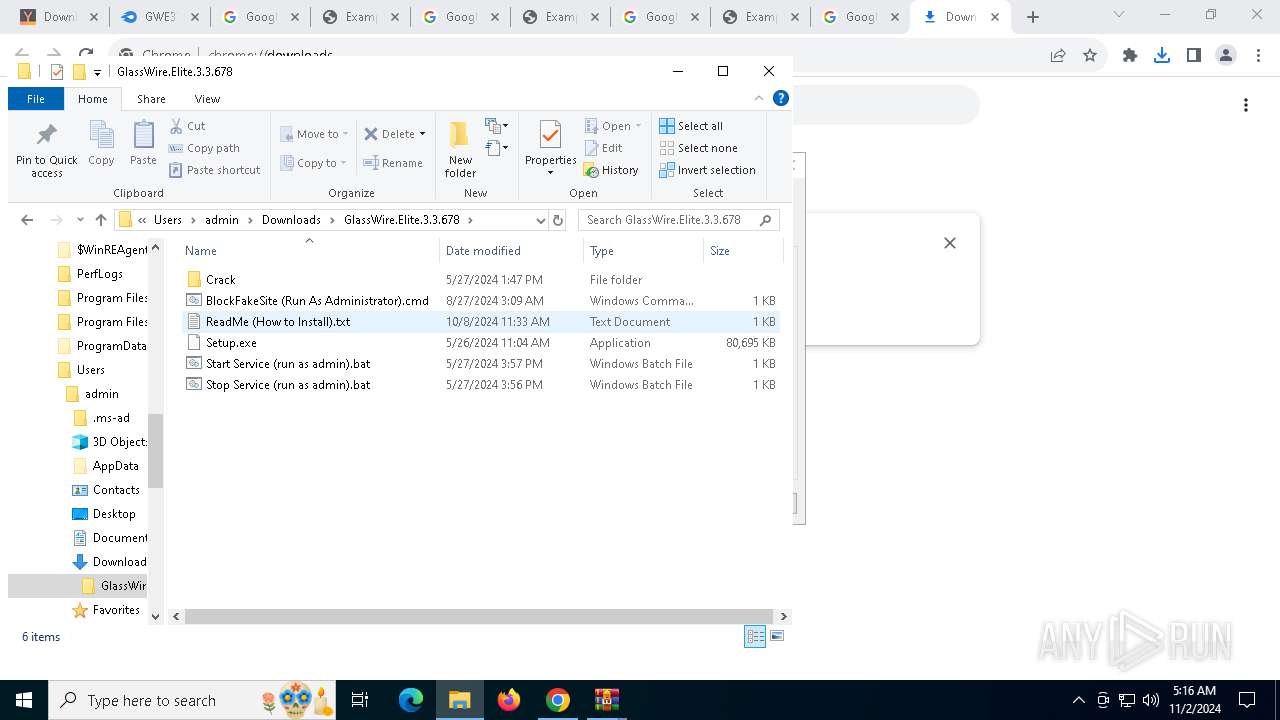
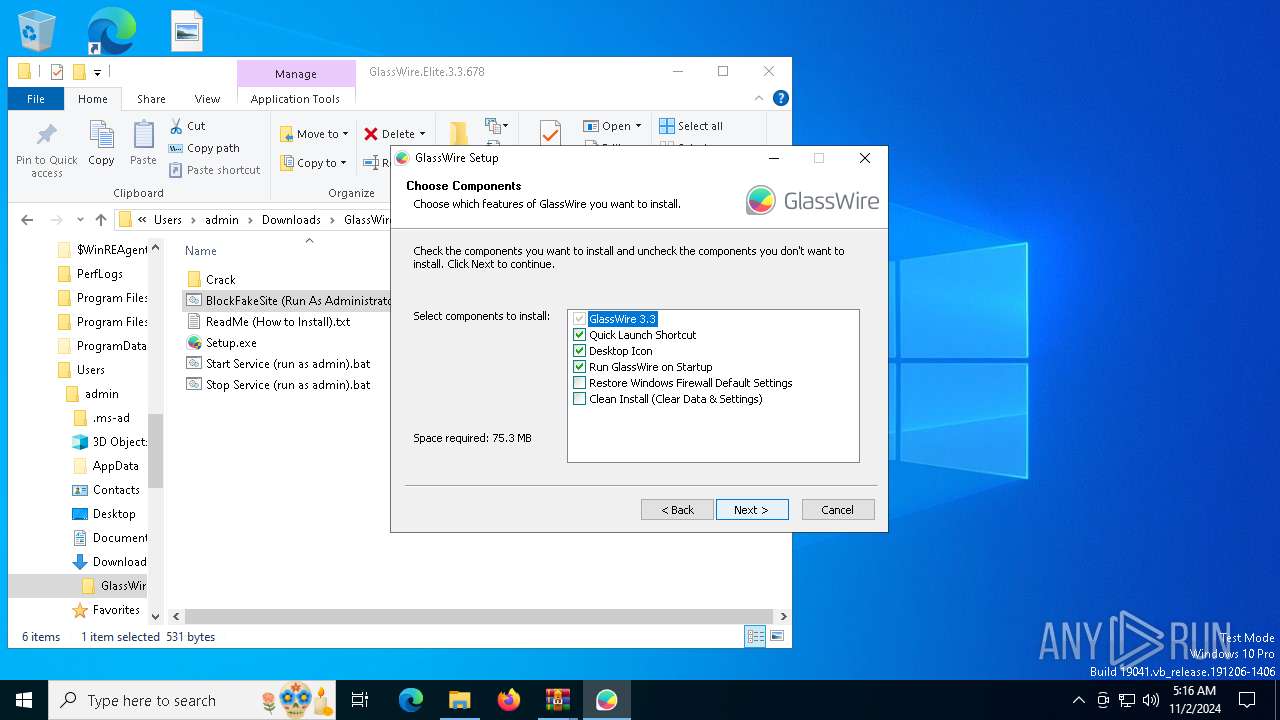
Executable content was dropped or overwritten
- Setup.exe (PID: 8164)
- vc_redist.x86.exe (PID: 1200)
- vc_redist.x86.exe (PID: 5324)
- rundll32.exe (PID: 7936)
The process creates files with name similar to system file names
- Setup.exe (PID: 8164)
Process drops legitimate windows executable
- Setup.exe (PID: 8164)
- vc_redist.x86.exe (PID: 1200)
Malware-specific behavior (creating "System.dll" in Temp)
- Setup.exe (PID: 8164)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 1200)
- vc_redist.x86.exe (PID: 5324)
Searches for installed software
- vc_redist.x86.exe (PID: 5324)
Reads the BIOS version
- Setup.exe (PID: 8164)
- GWInstSt.exe (PID: 7064)
- GWCtlSrv.exe (PID: 4516)
- GWCtlSrv.exe (PID: 2928)
- GWCtlSrv.exe (PID: 5420)
Reads security settings of Internet Explorer
- GWInstSt.exe (PID: 7064)
- Setup.exe (PID: 8164)
Checks Windows Trust Settings
- GWInstSt.exe (PID: 7064)
Creates files in the driver directory
- Setup.exe (PID: 8164)
Uses RUNDLL32.EXE to load library
- Setup.exe (PID: 8164)
Drops a system driver (possible attempt to evade defenses)
- Setup.exe (PID: 8164)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- Setup.exe (PID: 8164)
- wevtutil.exe (PID: 6880)
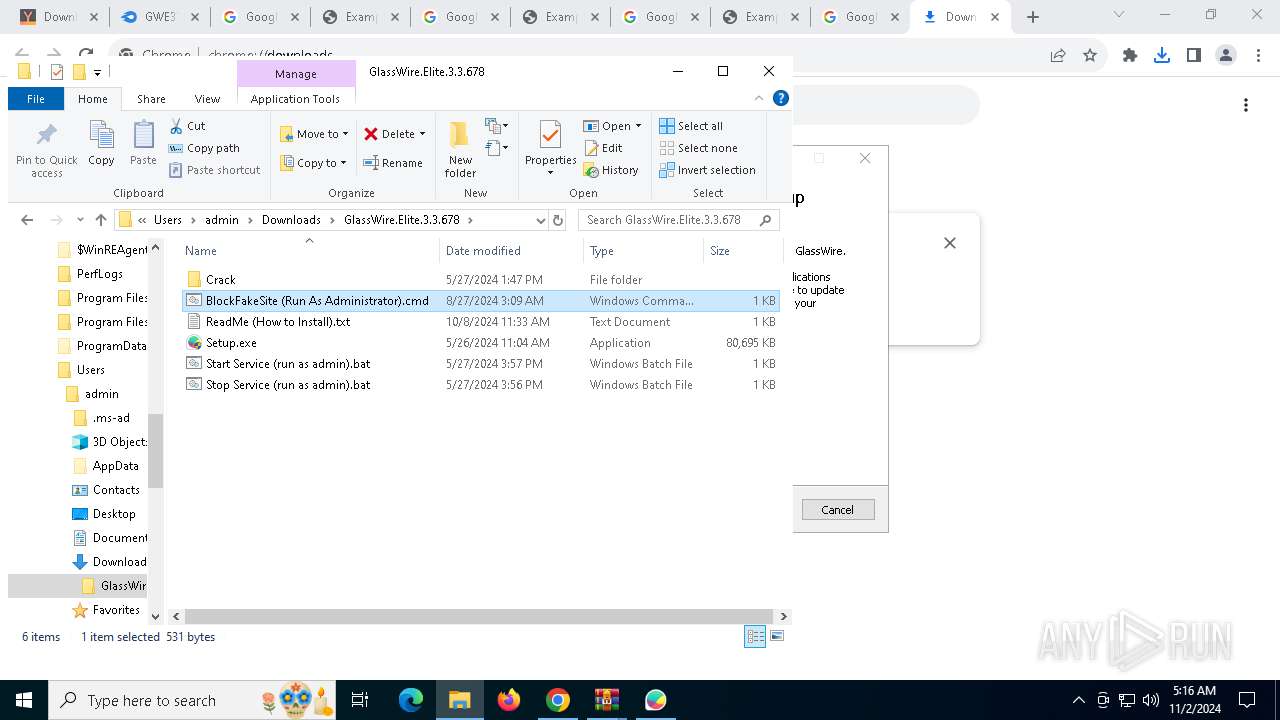
Creates or modifies Windows services
- GWCtlSrv.exe (PID: 4516)
Executes as Windows Service
- GWCtlSrv.exe (PID: 5420)
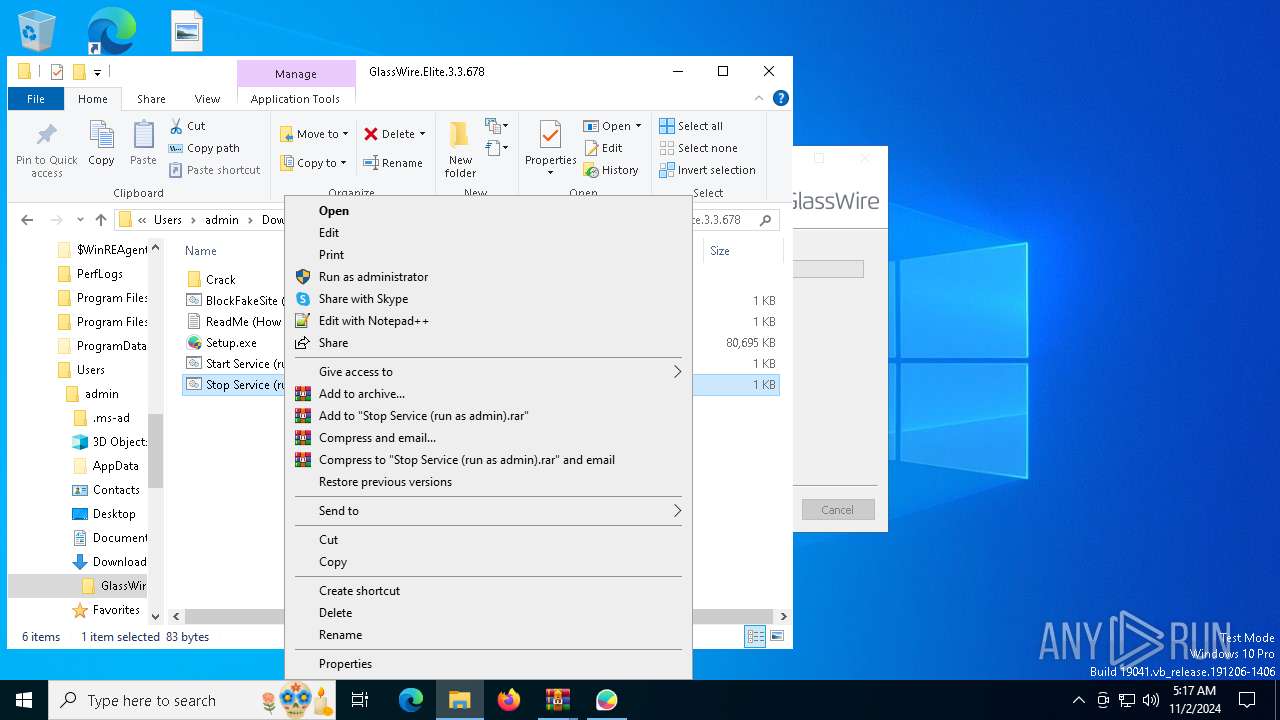
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7140)
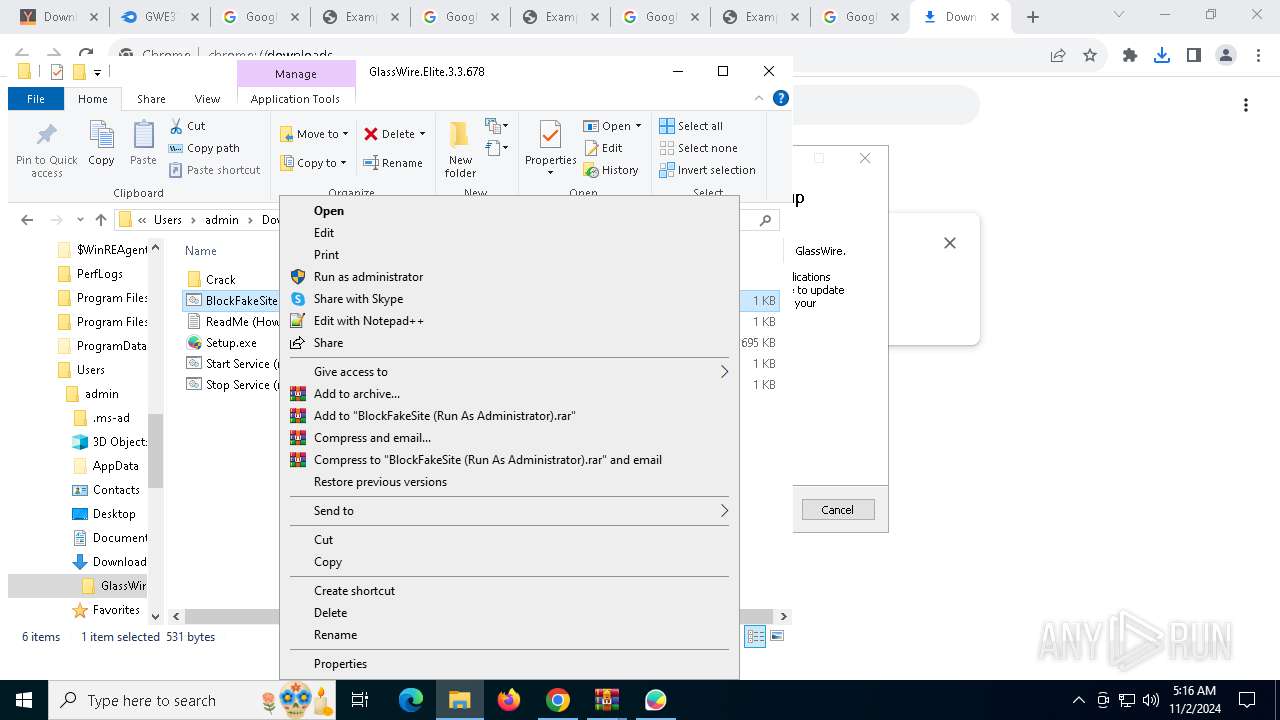
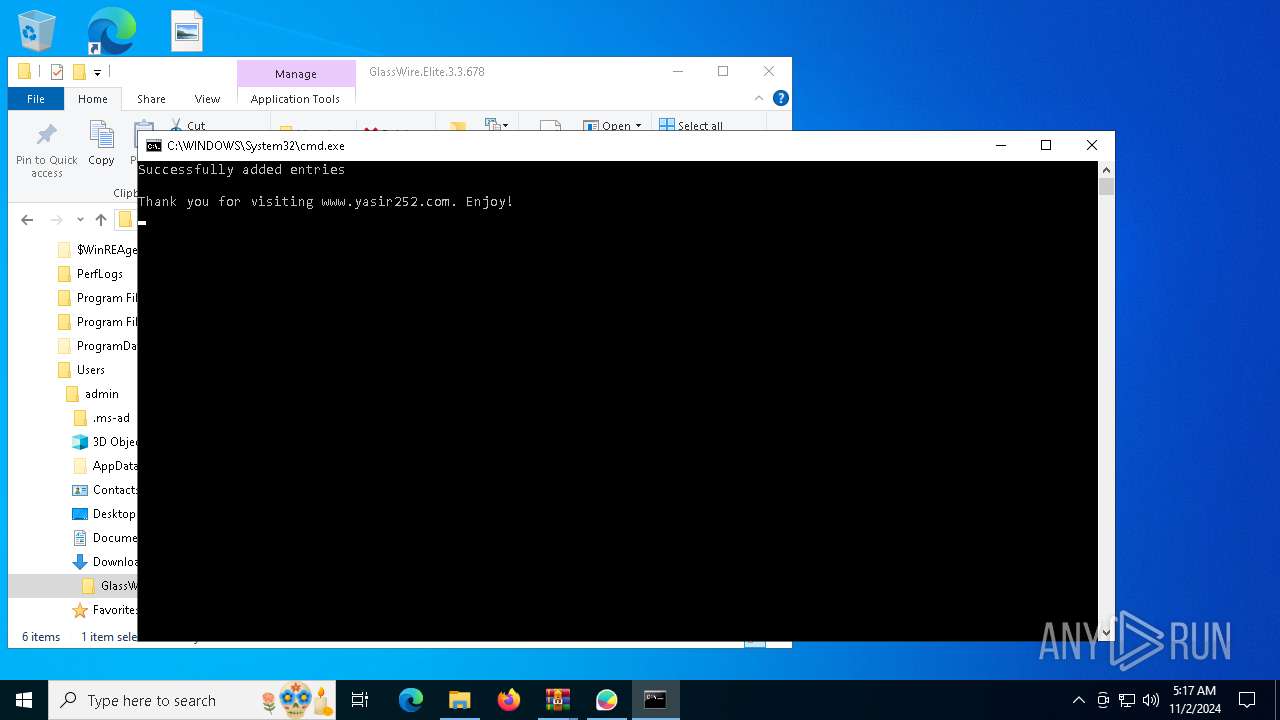
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7140)
INFO
Reads the software policy settings
- slui.exe (PID: 7964)
- slui.exe (PID: 7252)
- GWInstSt.exe (PID: 7064)
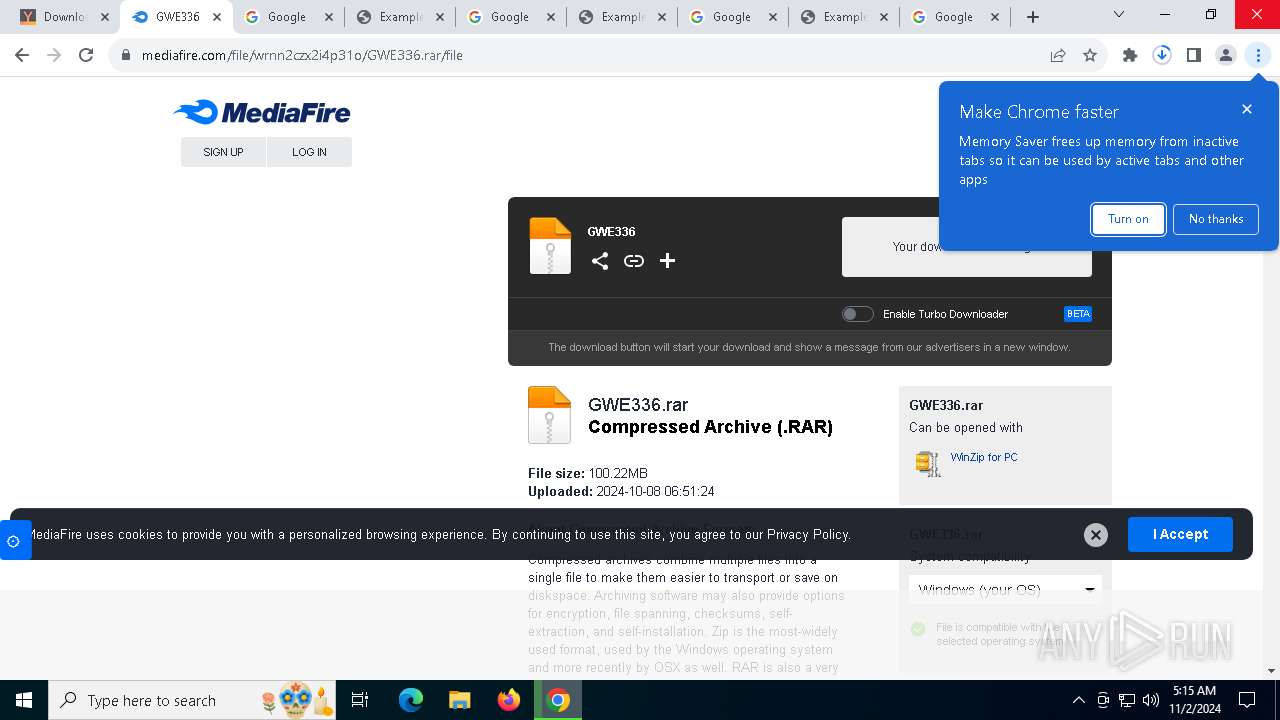
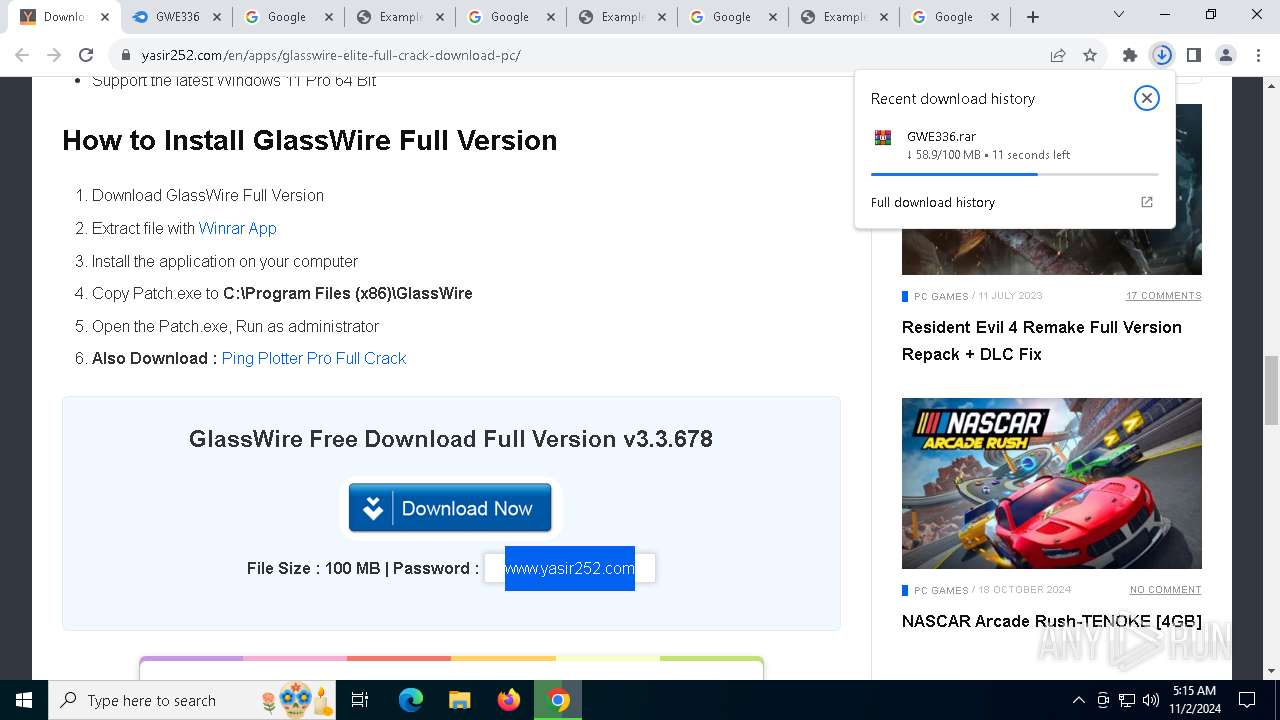
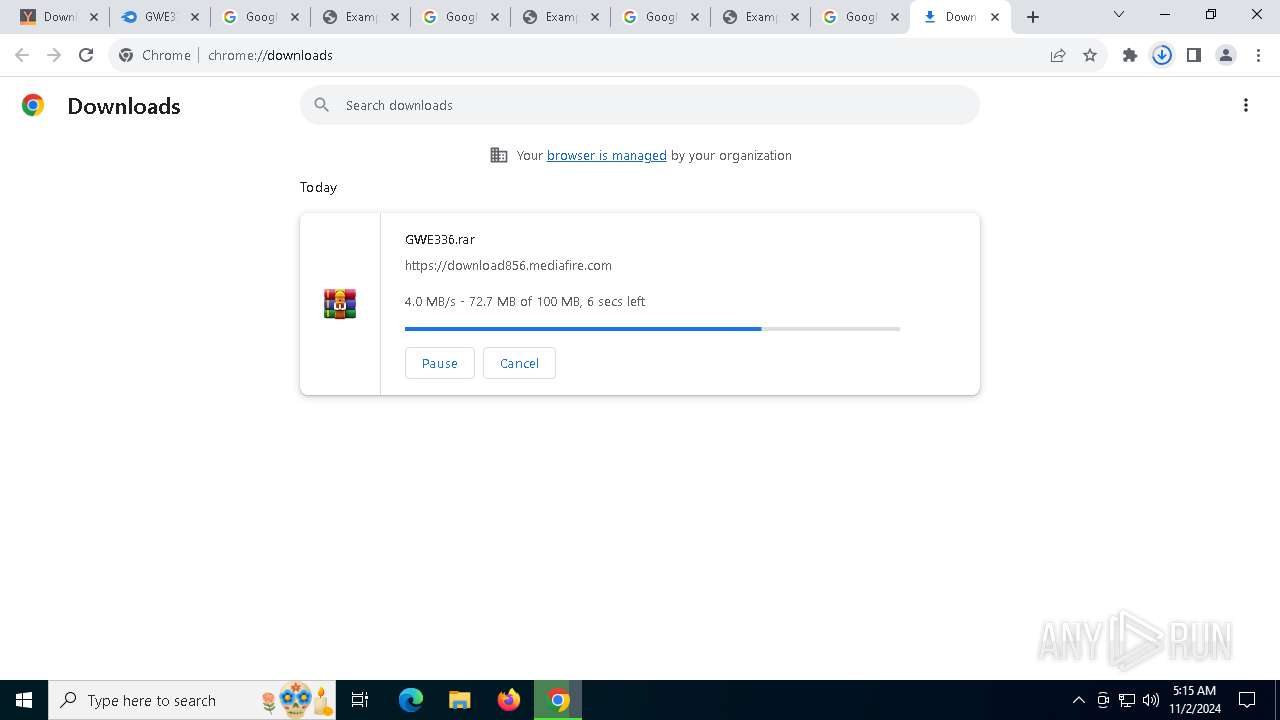
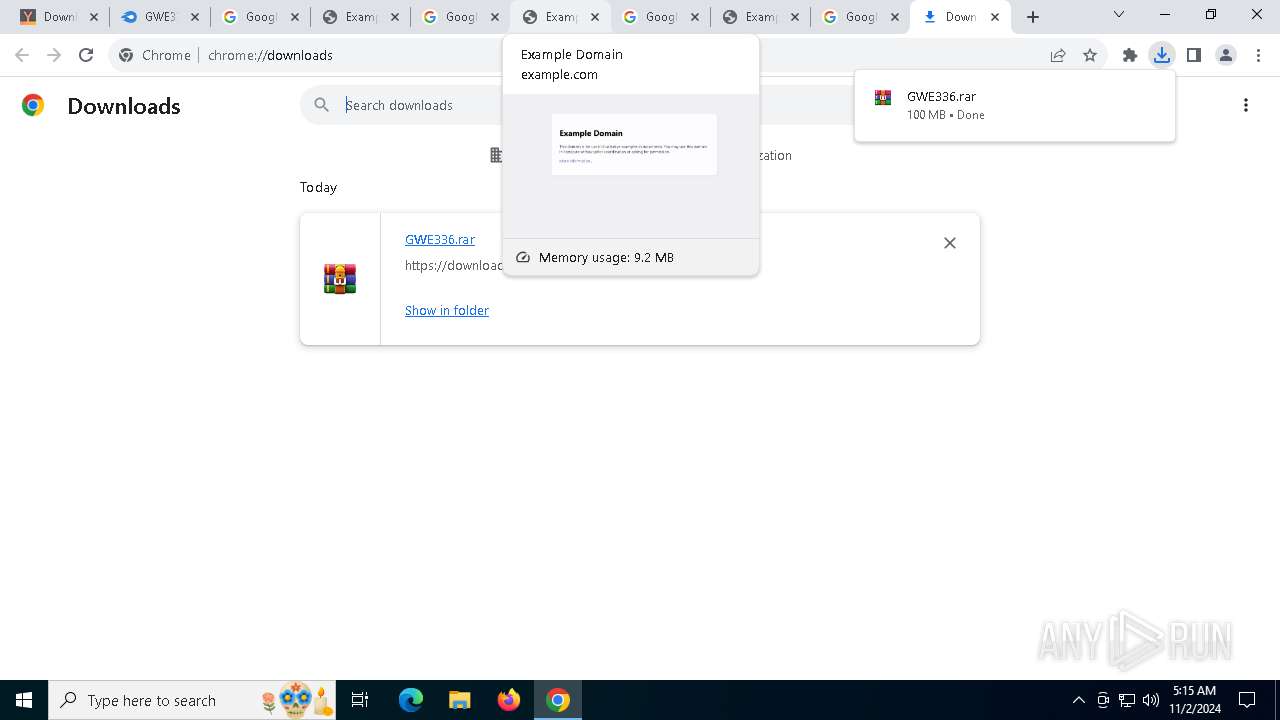
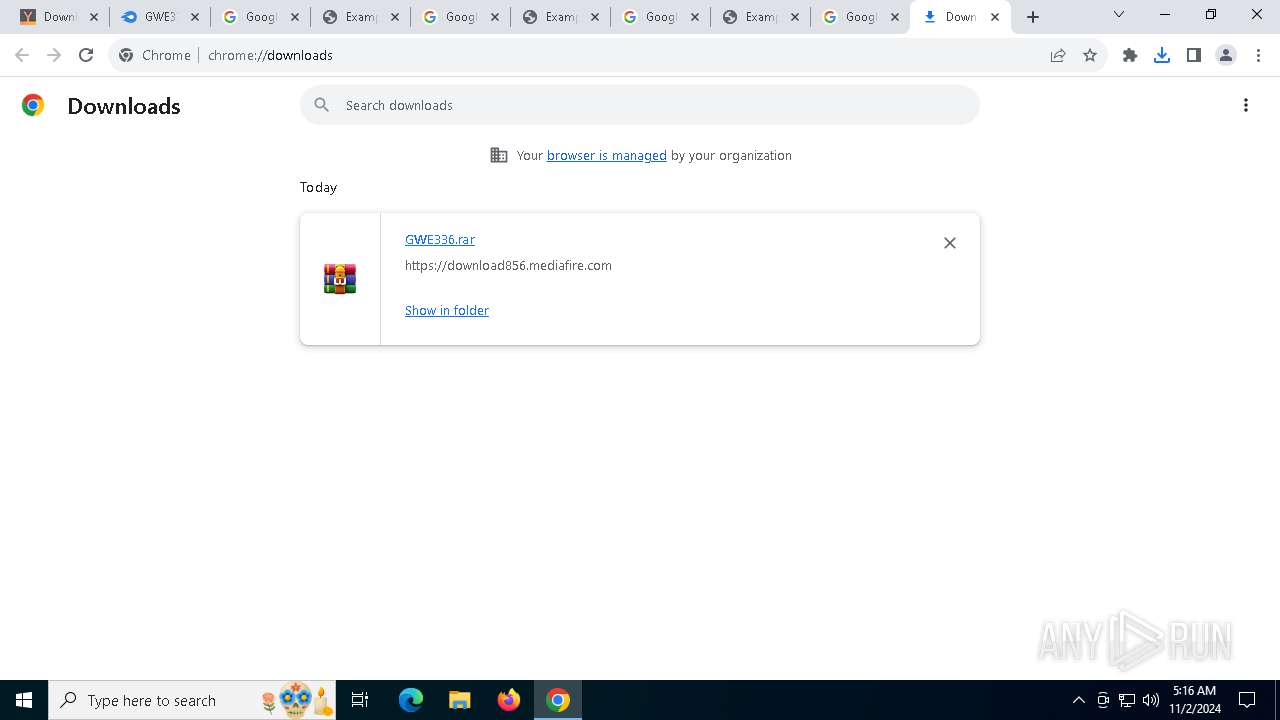
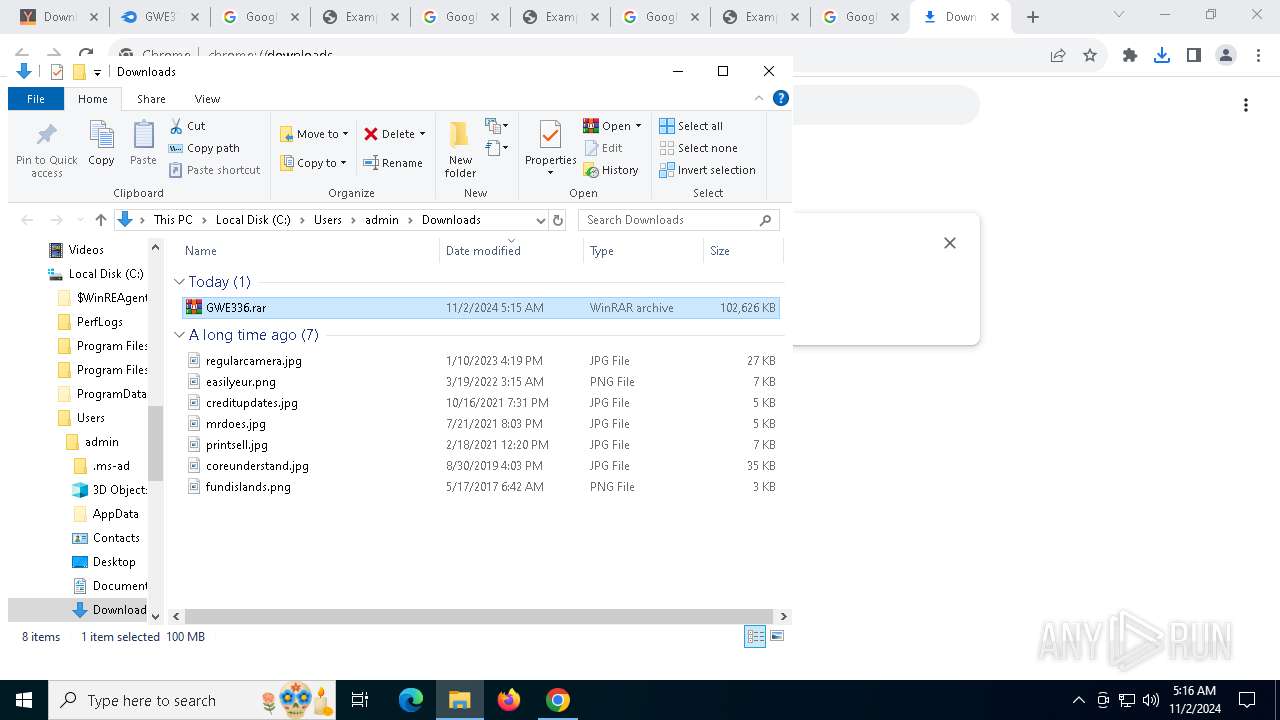
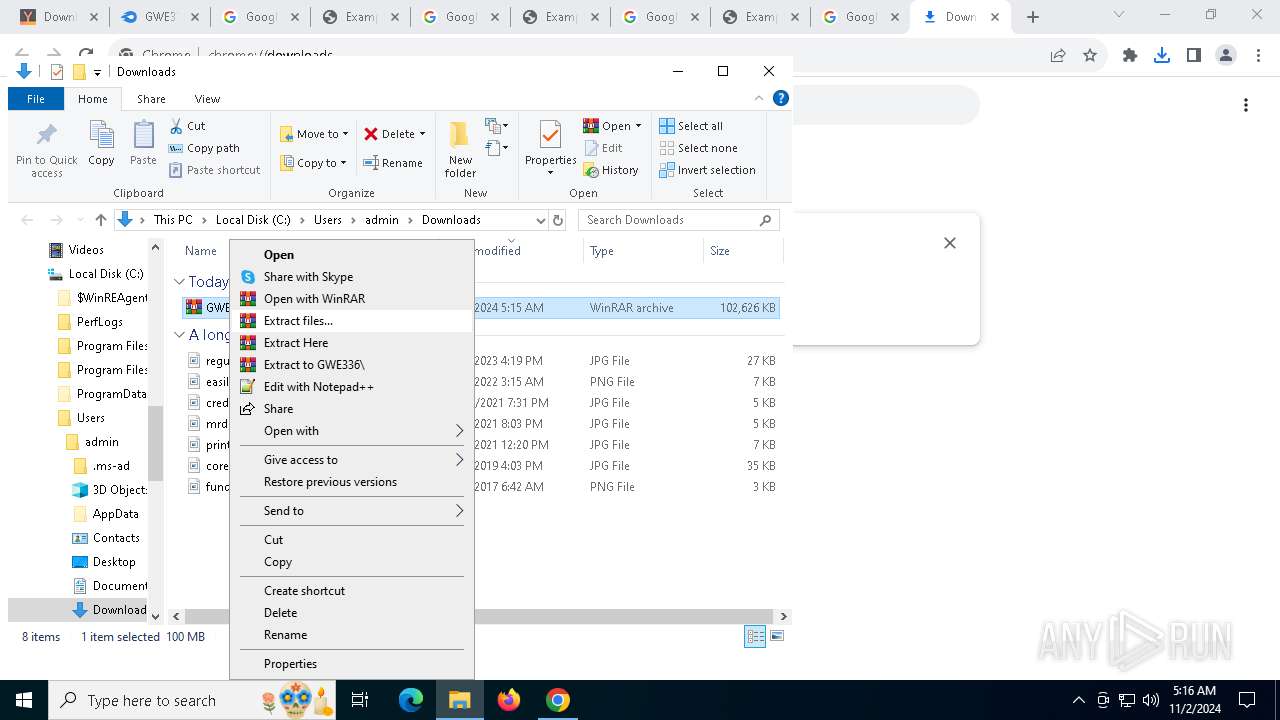
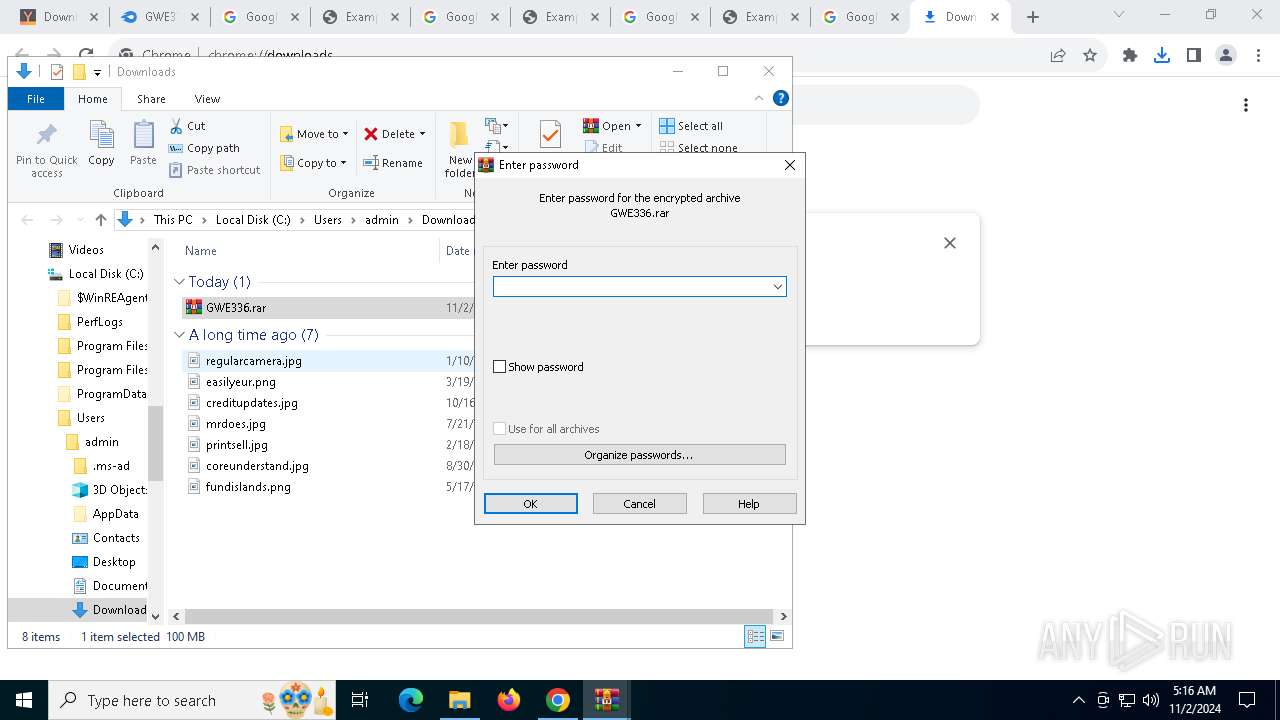
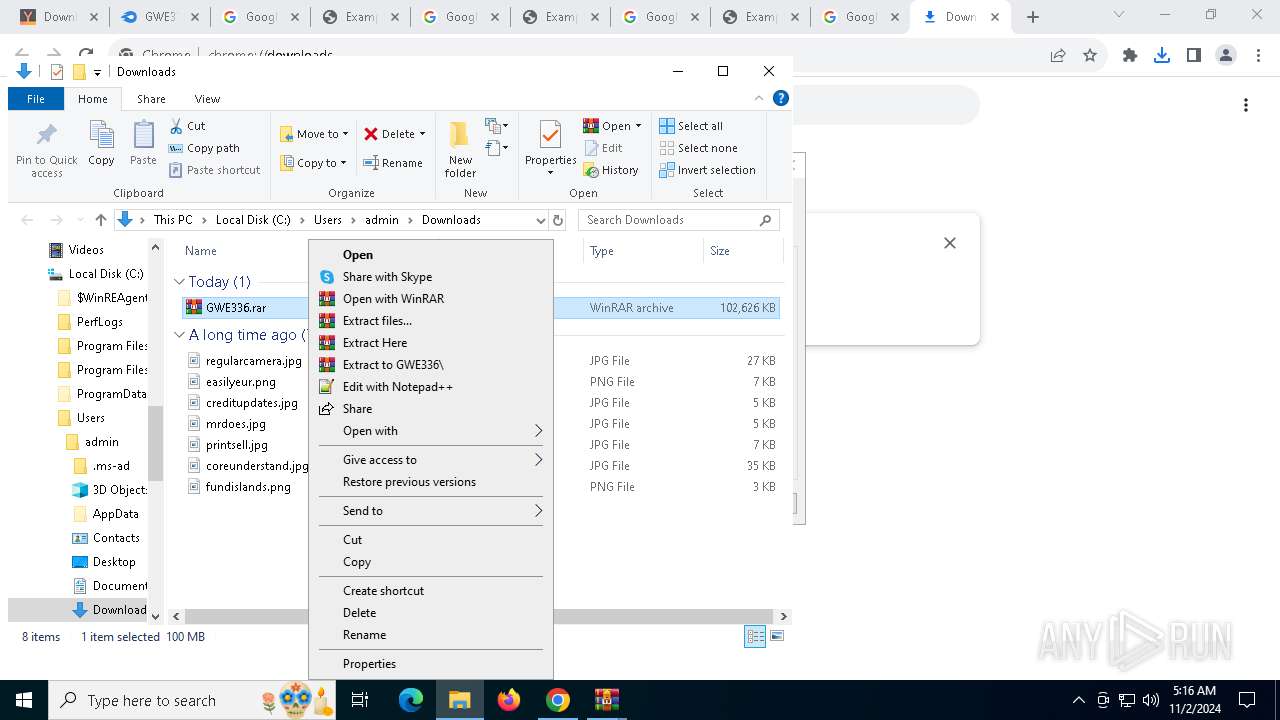
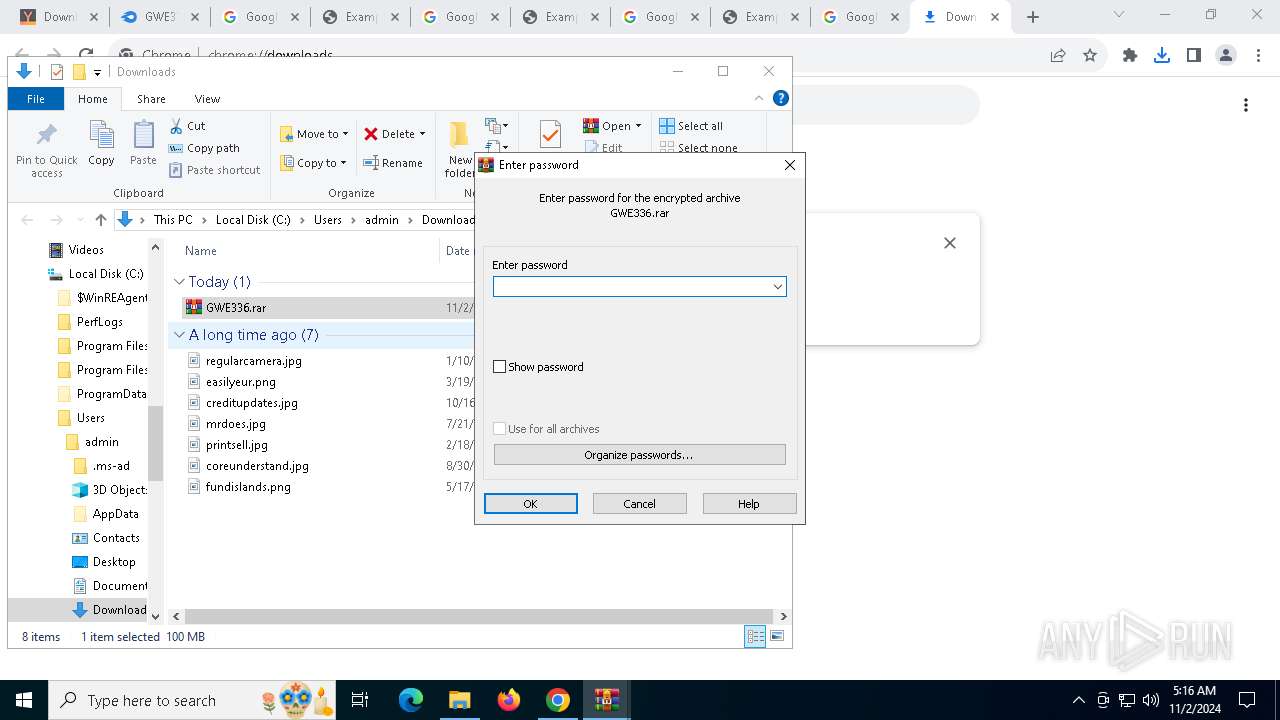
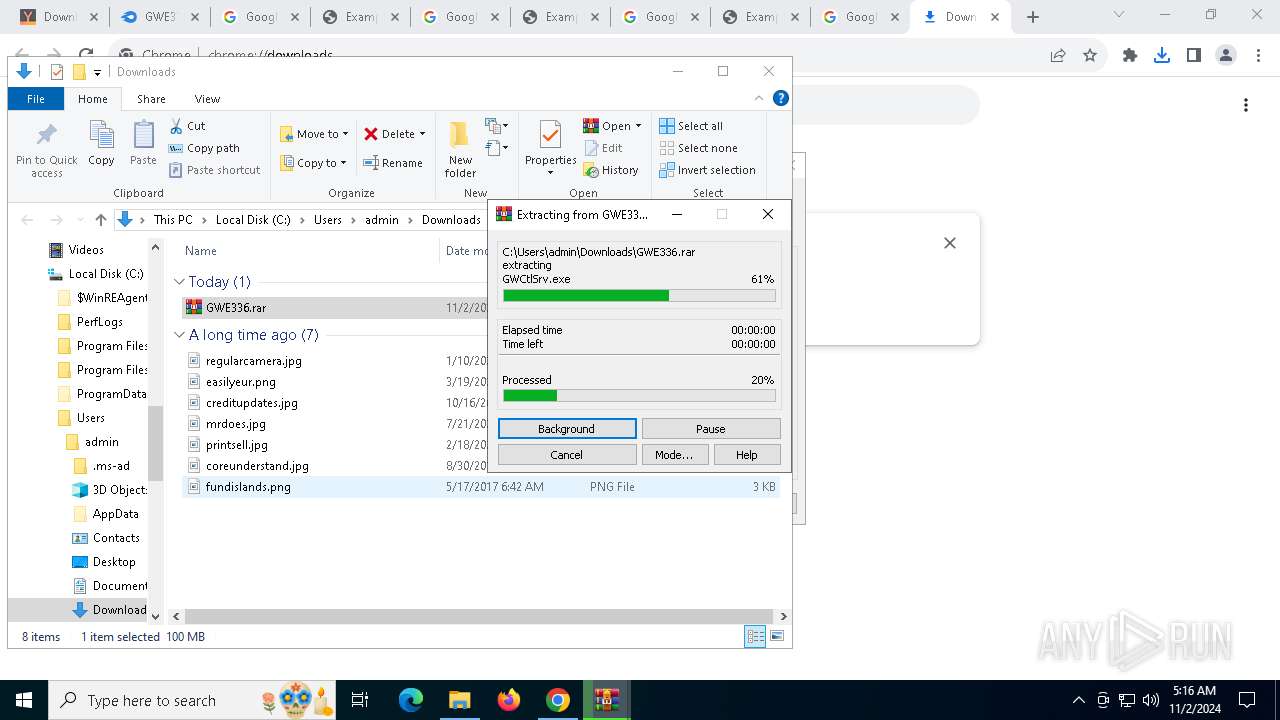
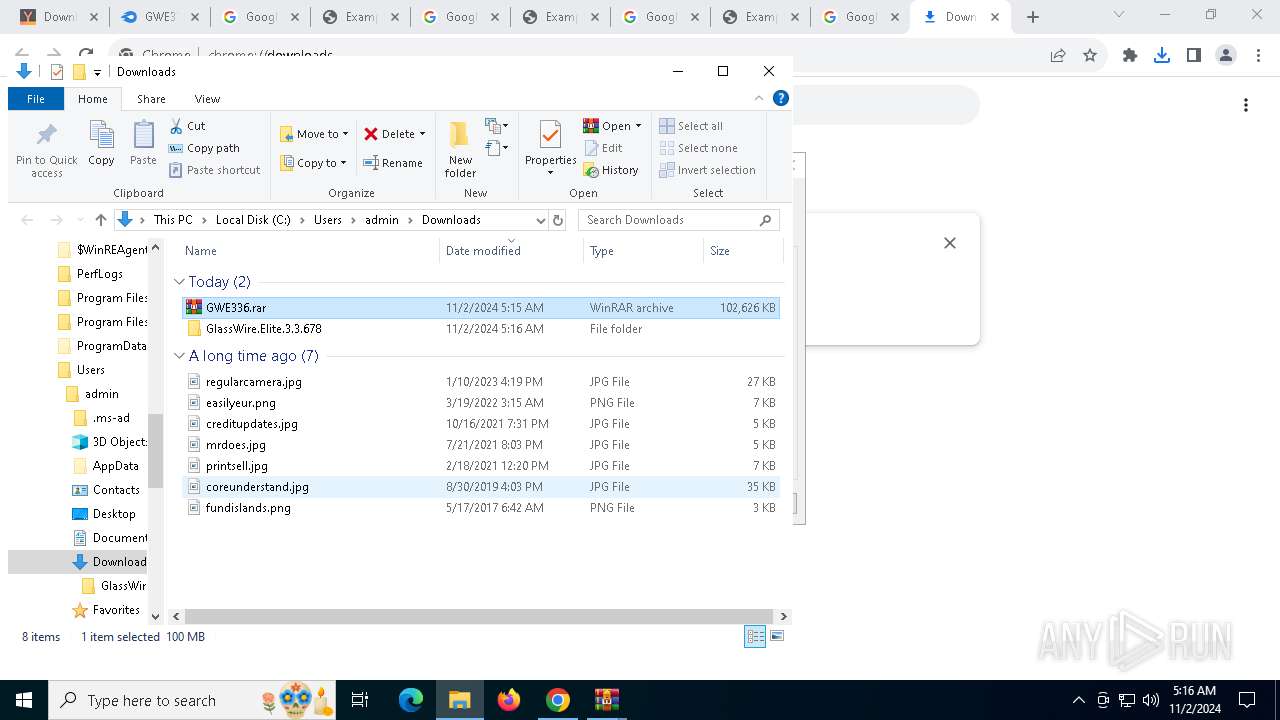
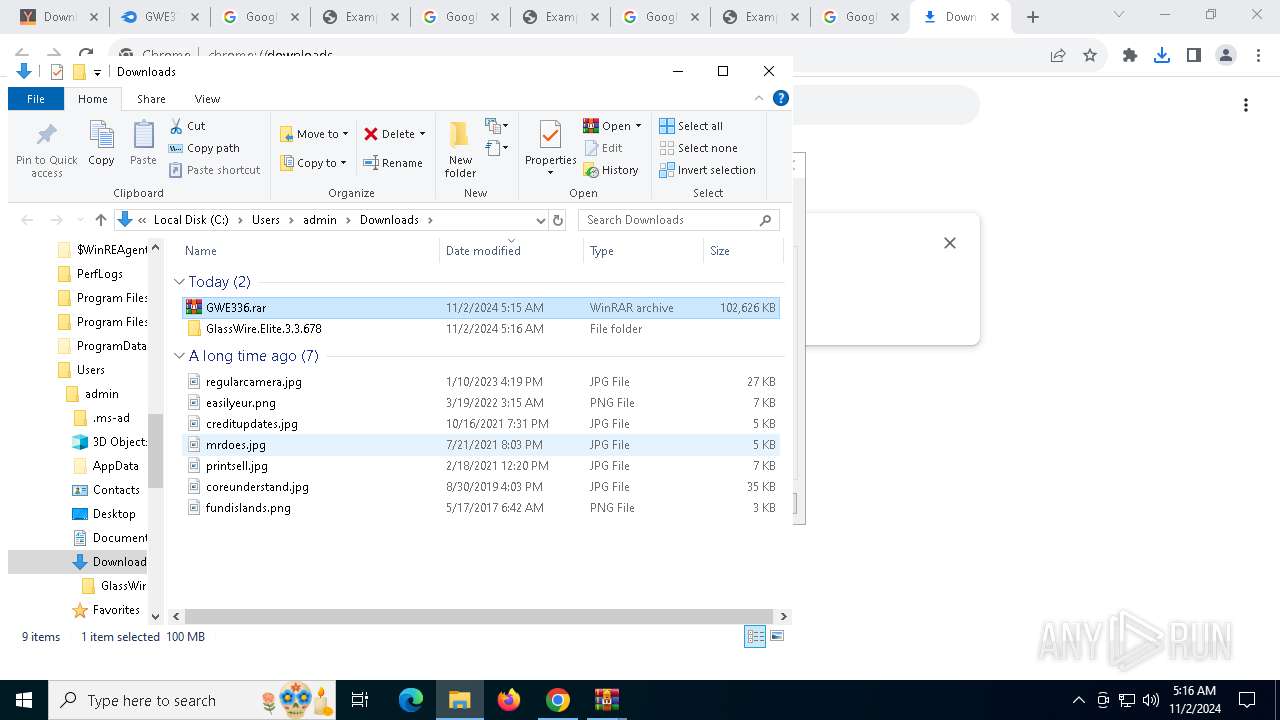
The process uses the downloaded file
- WinRAR.exe (PID: 7868)
- chrome.exe (PID: 6552)
- WinRAR.exe (PID: 6312)
- runonce.exe (PID: 1248)
Checks proxy server information
- slui.exe (PID: 7252)
- GWInstSt.exe (PID: 7064)
Connects to unusual port
- chrome.exe (PID: 5276)
Application launched itself
- chrome.exe (PID: 4076)
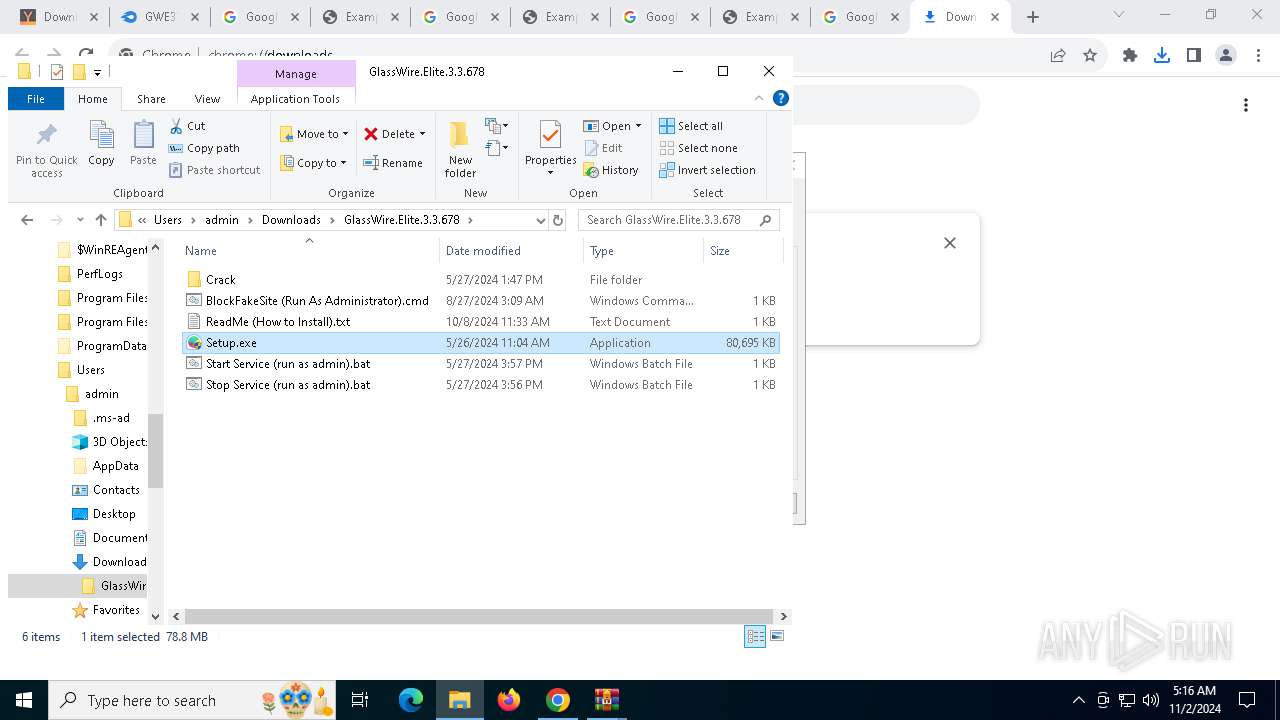
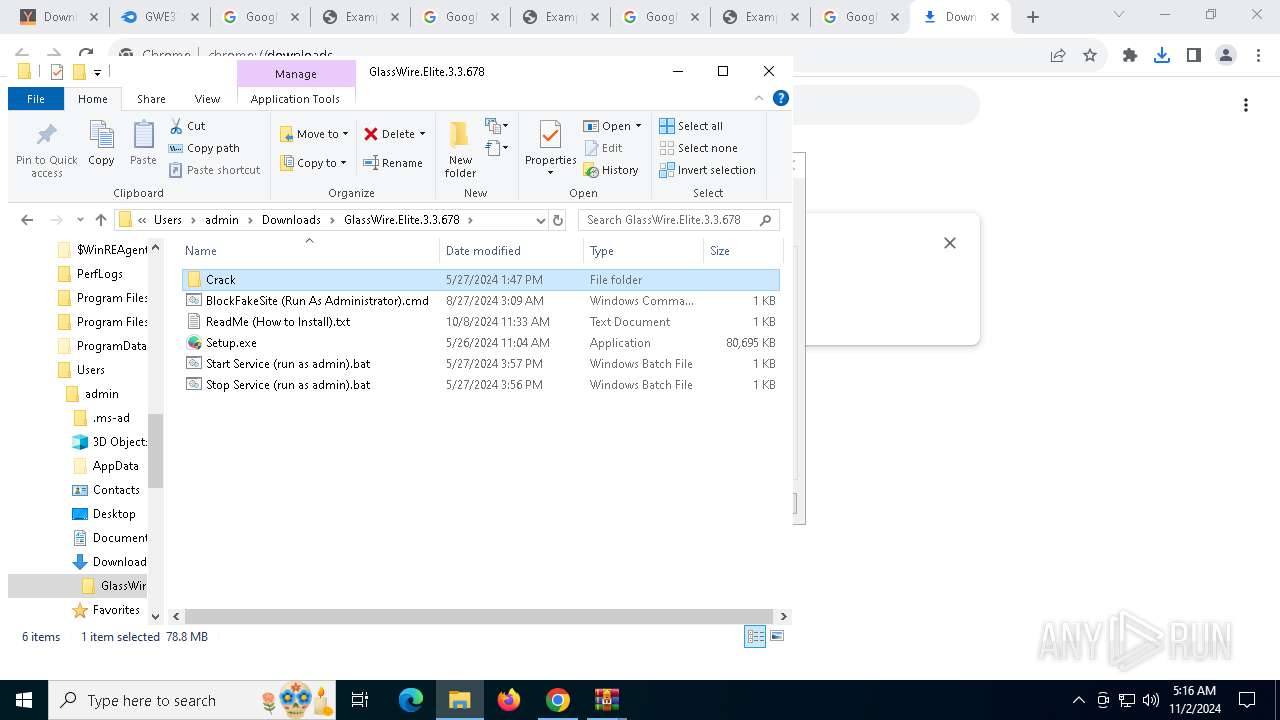
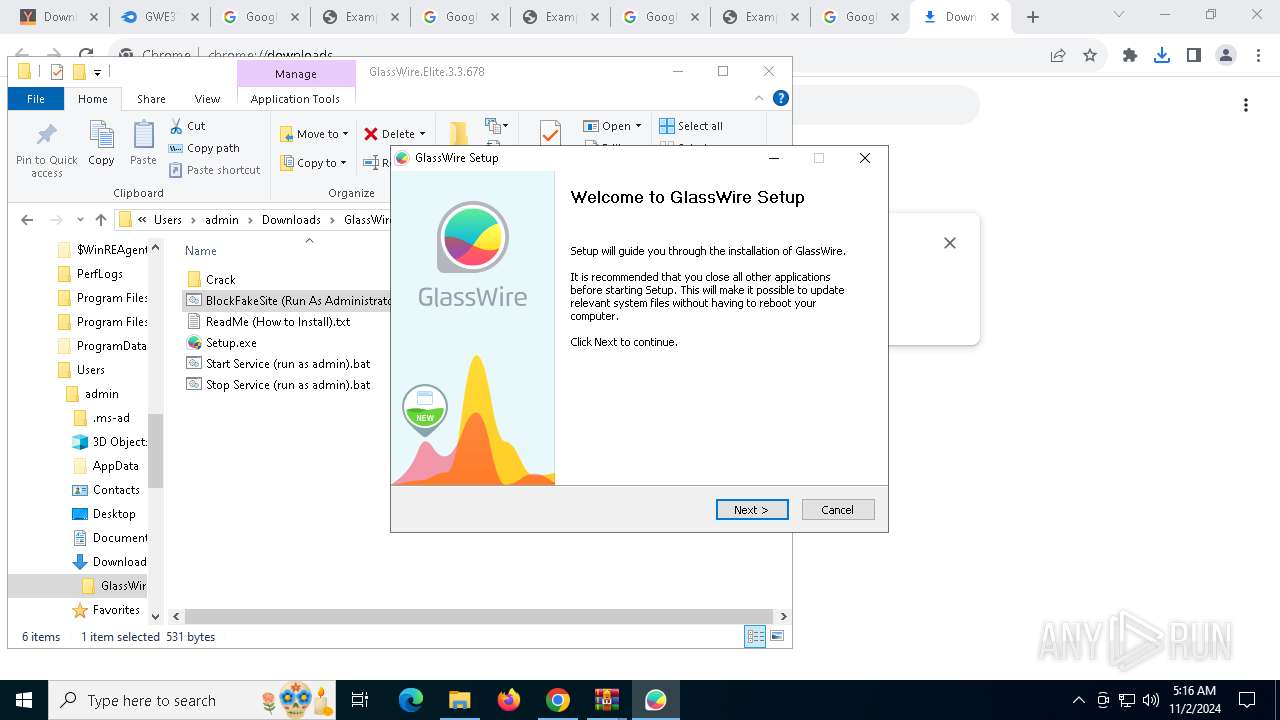
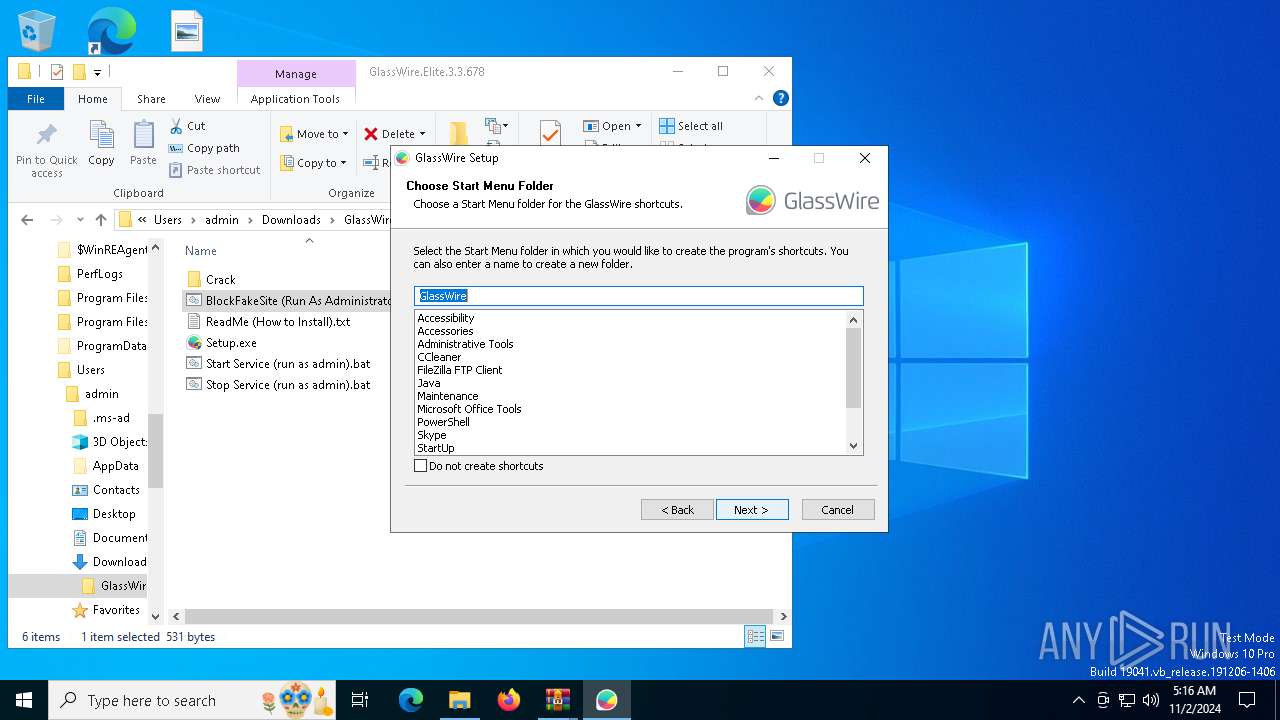
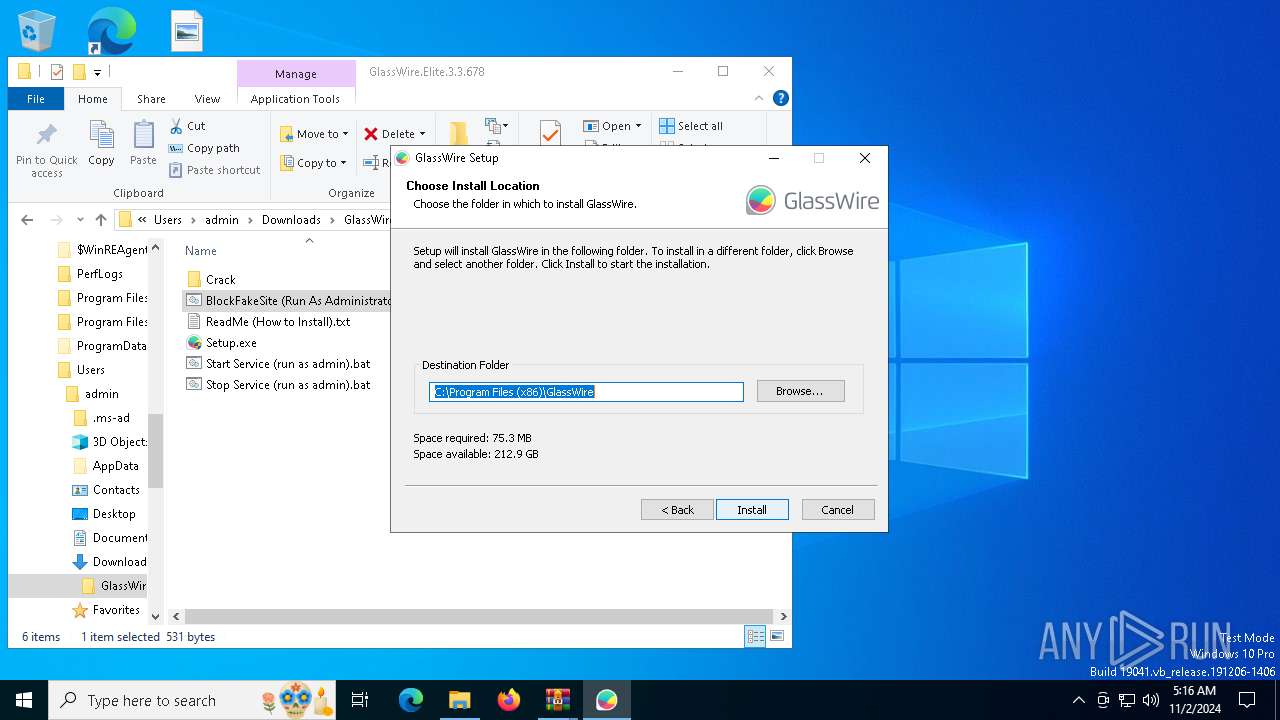
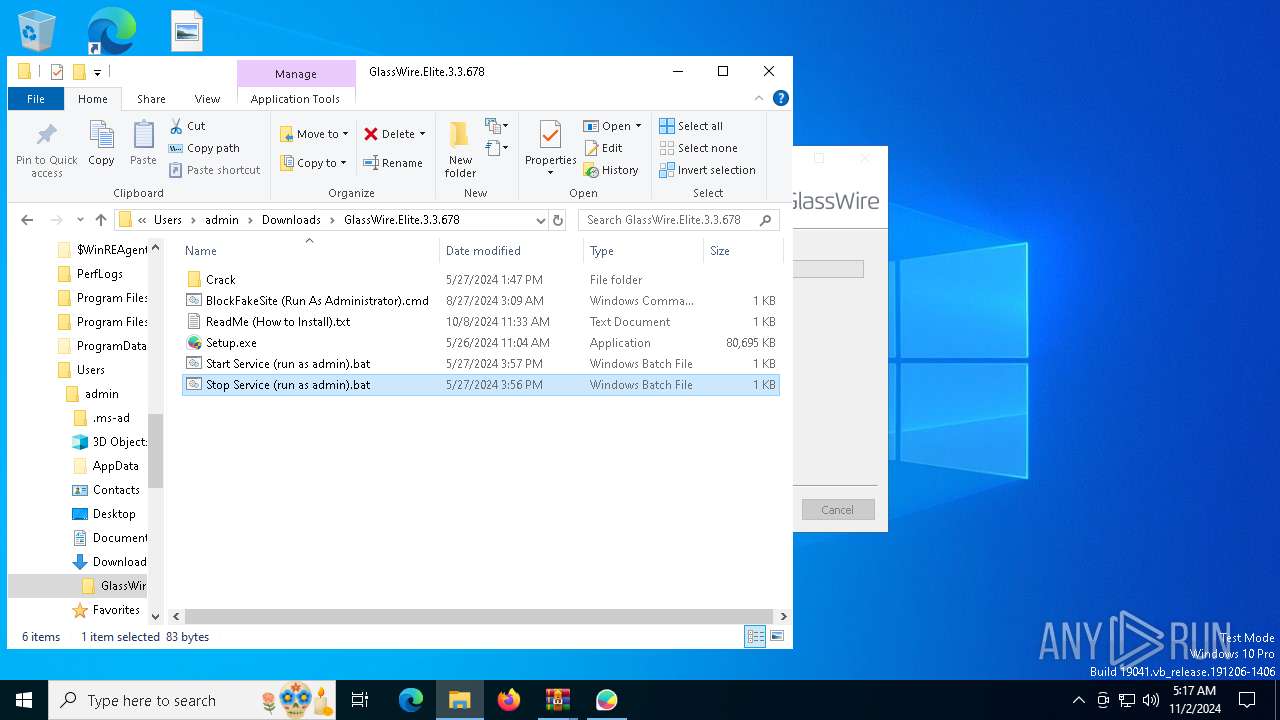
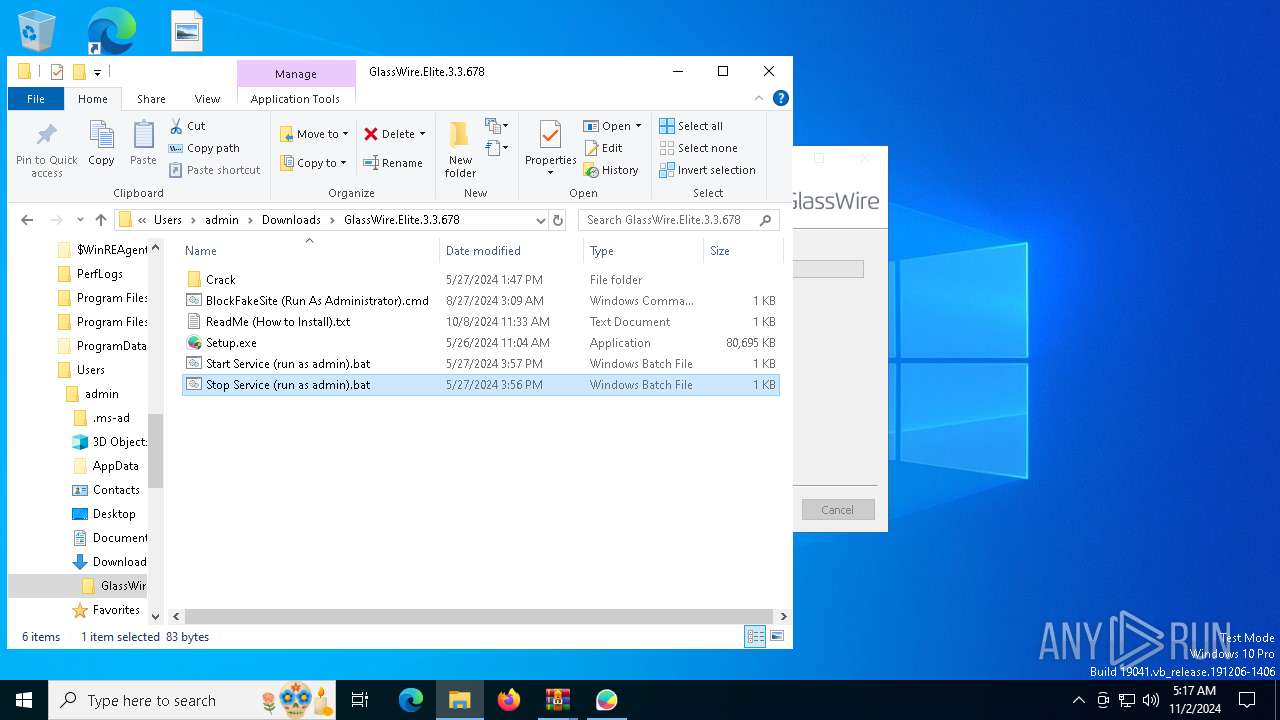
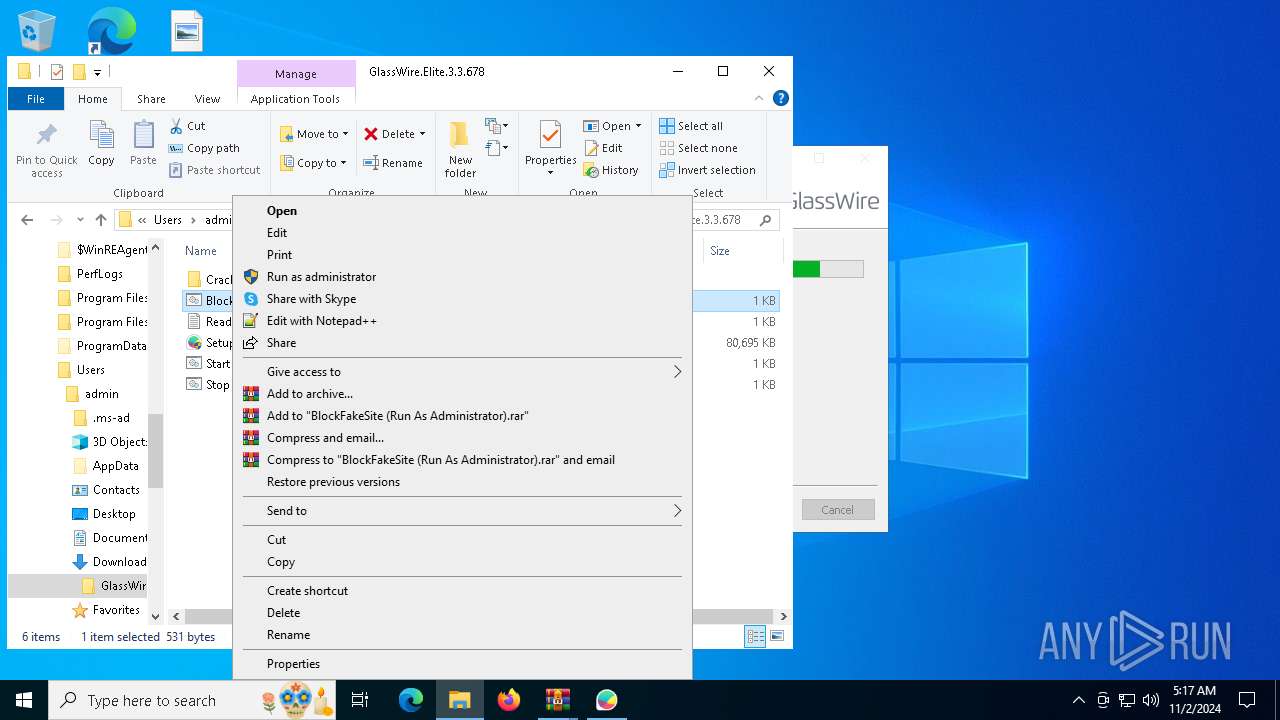
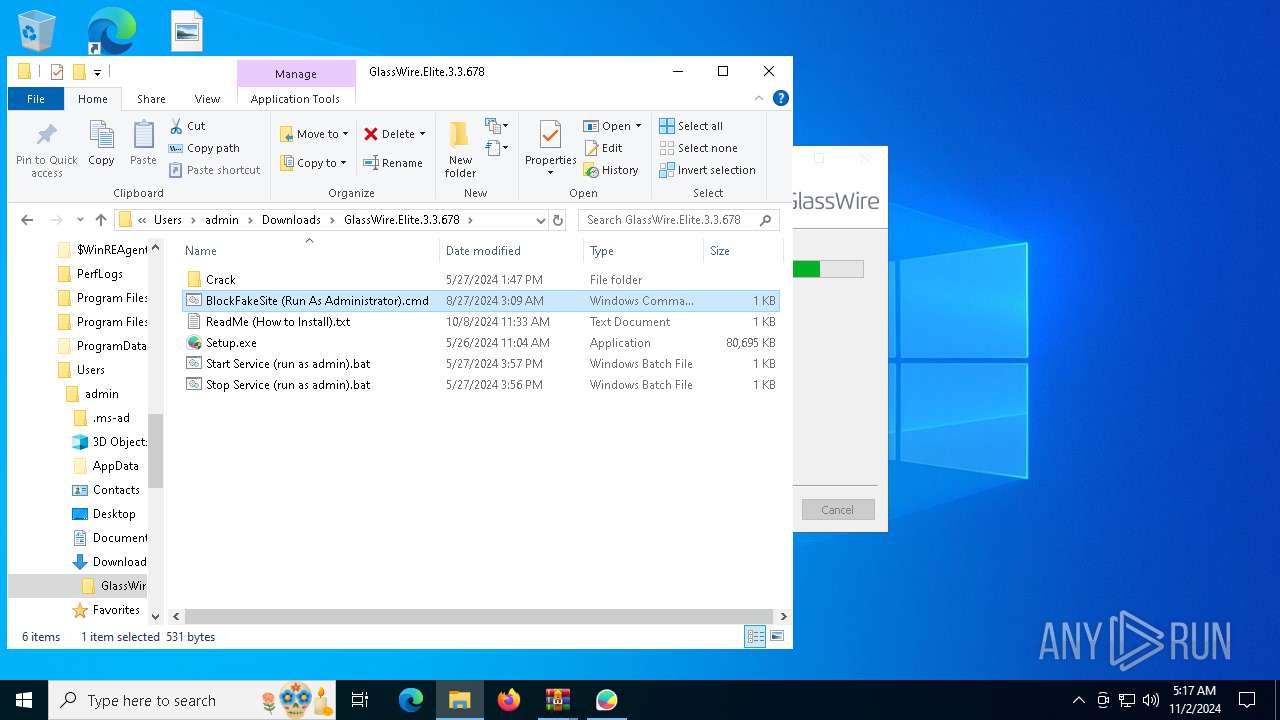
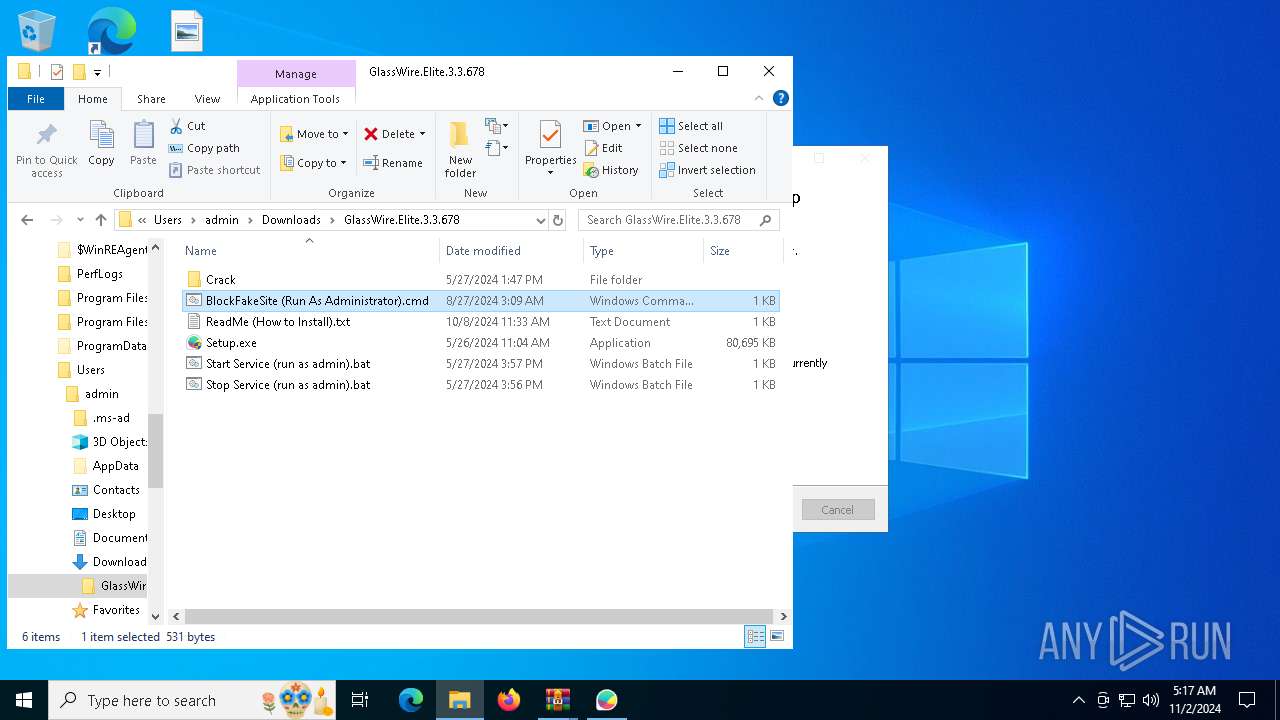
Manual execution by a user
- WinRAR.exe (PID: 7868)
- Setup.exe (PID: 5068)
- Setup.exe (PID: 8164)
- WinRAR.exe (PID: 6312)
- cmd.exe (PID: 2184)
- cmd.exe (PID: 7140)
Executable content was dropped or overwritten
- chrome.exe (PID: 6944)
- WinRAR.exe (PID: 6312)
Checks supported languages
- Setup.exe (PID: 8164)
- vc_redist.x86.exe (PID: 1200)
- vc_redist.x86.exe (PID: 5324)
- GWInstSt.exe (PID: 7064)
- GWCtlSrv.exe (PID: 4516)
- GWCtlSrv.exe (PID: 2928)
- GWCtlSrv.exe (PID: 5420)
Create files in a temporary directory
- Setup.exe (PID: 8164)
- vc_redist.x86.exe (PID: 5324)
Reads the computer name
- vc_redist.x86.exe (PID: 5324)
- Setup.exe (PID: 8164)
- GWInstSt.exe (PID: 7064)
- GWCtlSrv.exe (PID: 4516)
- GWCtlSrv.exe (PID: 2928)
- GWCtlSrv.exe (PID: 5420)
Process checks computer location settings
- Setup.exe (PID: 8164)
Process checks whether UAC notifications are on
- Setup.exe (PID: 8164)
- GWInstSt.exe (PID: 7064)
- GWCtlSrv.exe (PID: 4516)
- GWCtlSrv.exe (PID: 2928)
- GWCtlSrv.exe (PID: 5420)
Themida protector has been detected
- Setup.exe (PID: 8164)
- GWCtlSrv.exe (PID: 5420)
Creates files in the program directory
- Setup.exe (PID: 8164)
- GWCtlSrv.exe (PID: 5420)
Reads the machine GUID from the registry
- GWInstSt.exe (PID: 7064)
Creates files or folders in the user directory
- GWInstSt.exe (PID: 7064)
Reads the time zone
- runonce.exe (PID: 1248)
Reads security settings of Internet Explorer
- runonce.exe (PID: 1248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
103
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=6068 --field-trial-handle=1860,i,16054442905165429582,9729629971838128557,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 712 | choice /n /c y /d y /t 5 | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | findstr /c:"127.0.0.1 yasir-252.net" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4740 --field-trial-handle=1860,i,16054442905165429582,9729629971838128557,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=6272 --field-trial-handle=1860,i,16054442905165429582,9729629971838128557,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\AppData\Local\Temp\nsxDFDC.tmp\vc_redist.x86.exe" /install /quiet /norestart | C:\Users\admin\AppData\Local\Temp\nsxDFDC.tmp\vc_redist.x86.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.29.30139 Exit code: 1638 Version: 14.29.30139.0 Modules
| |||||||||||||||
| 1248 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | "C:\WINDOWS\system32\net.exe" start gwdrv | C:\Windows\System32\net.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3448 --field-trial-handle=1860,i,16054442905165429582,9729629971838128557,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1580 | findstr /c:"127.0.0.1 www.yasir-252.com" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 581
Read events
29 426
Write events
124
Delete events
31
Modification events
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
39
Suspicious files
279
Text files
139
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8bf03.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8bf03.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8bf13.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8bf03.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8bf13.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8bf03.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
440
DNS requests
522
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7144 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
7048 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6mhlwypzipnufijdvfyhdgvt4q_67/khaoiebndkojlmppeemjhbpbandiljpe_67_win_kfegpqlp6gezs4ree2ol2br2ym.crx3 | US | binary | 1.09 Kb | whitelisted |
8096 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6944 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
7048 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kkh6bhqzf3jnvouwqazr4ungqm_2024.10.31.1/jflhchccmppkfebkiaminageehmchikm_2024.10.31.01_all_h3fi2cv57kihjancqjlvoq3zwa.crx3 | US | compressed | 2.81 Kb | whitelisted |
7048 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kkh6bhqzf3jnvouwqazr4ungqm_2024.10.31.1/jflhchccmppkfebkiaminageehmchikm_2024.10.31.01_all_h3fi2cv57kihjancqjlvoq3zwa.crx3 | US | compressed | 875 b | whitelisted |
7048 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclacns2lwpknygjwzhz5vqbtzhq_1118/efniojlnjndmcbiieegkicadnoecjjef_1118_all_hykvkv5z4y5mqcsnbmogjjgb5m.crx3 | US | binary | 141 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3952 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4076 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5276 | chrome.exe | 62.72.45.137:443 | www.yasir252.com | PTGi International Carrier Services, Inc. | US | suspicious |
5276 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5276 | chrome.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | whitelisted |
5276 | chrome.exe | 142.250.185.168:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.yasir252.com |
| unknown |
accounts.google.com |
| whitelisted |
stats.wp.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
pixel.wp.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5276 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5276 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5276 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5276 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5276 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
5276 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
5276 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5276 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |