| File name: | cleanup_tool.exe |
| Full analysis: | https://app.any.run/tasks/2582e742-3448-4977-9969-61e8f40cdd79 |
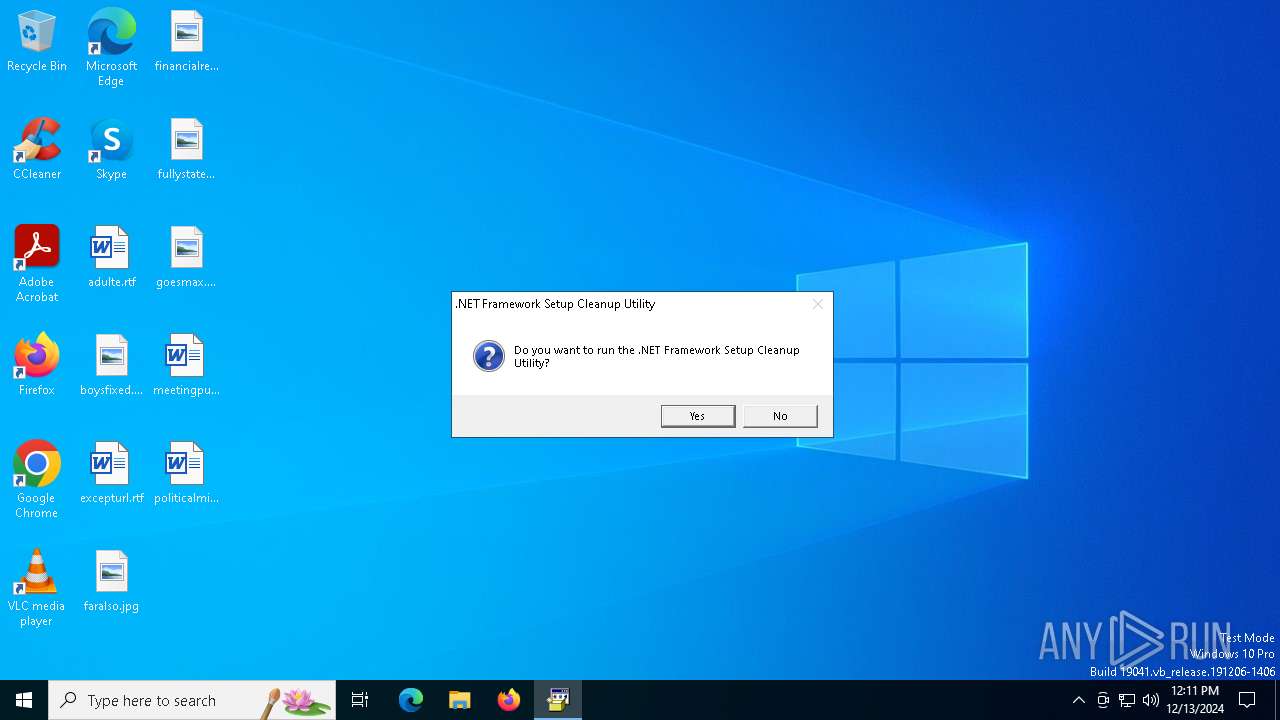
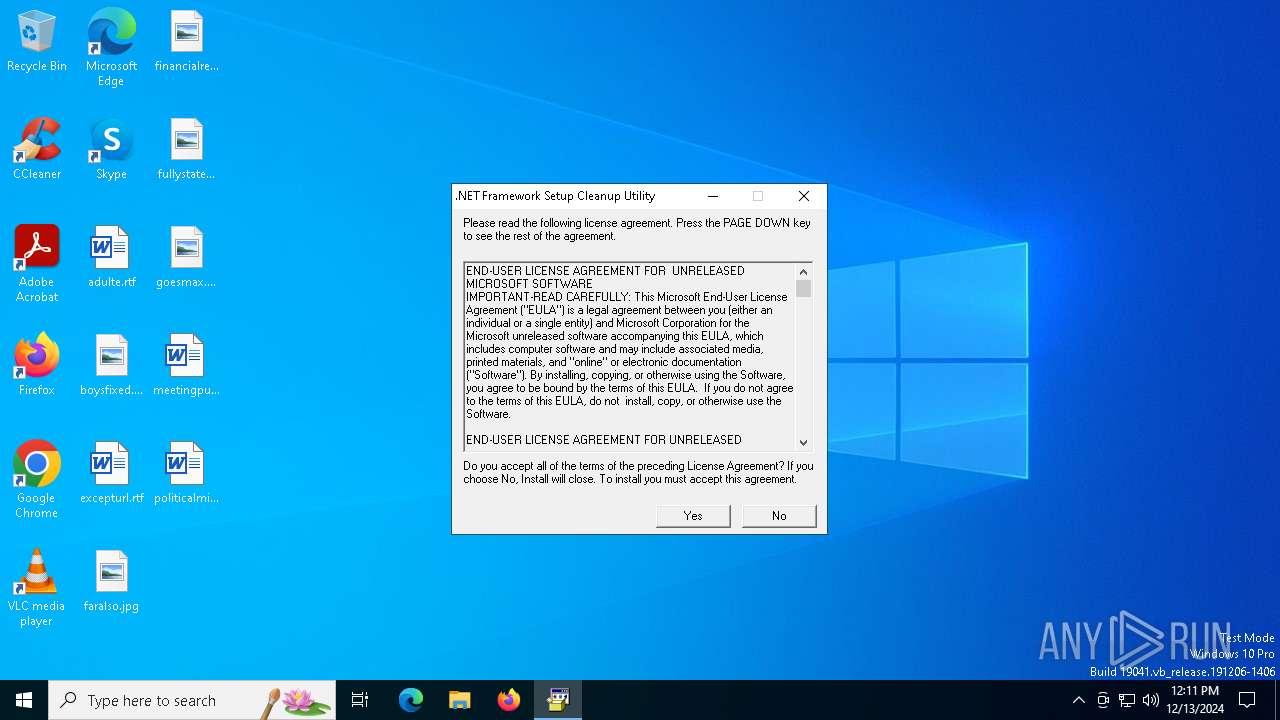
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 12:11:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 12438A4FDA479AC13A3849F26B9D281D |
| SHA1: | A6E9EF4BF46976F7B336EBAE0852F35AD2ECE8FF |
| SHA256: | 8CE9E674E2F302DD6BB6CBBDB9F1F79FC0A0AF37D0F85D98809B579C90A94CEB |
| SSDEEP: | 6144:ScN2go4Aw0m8GegnLh0HTWcdNONAtOIfnnSqIdOJS+2pPQIgUUg0TAIQiXj:ScN2gLegLhLwz/fnSROJV8PQv3VXj |
MALICIOUS
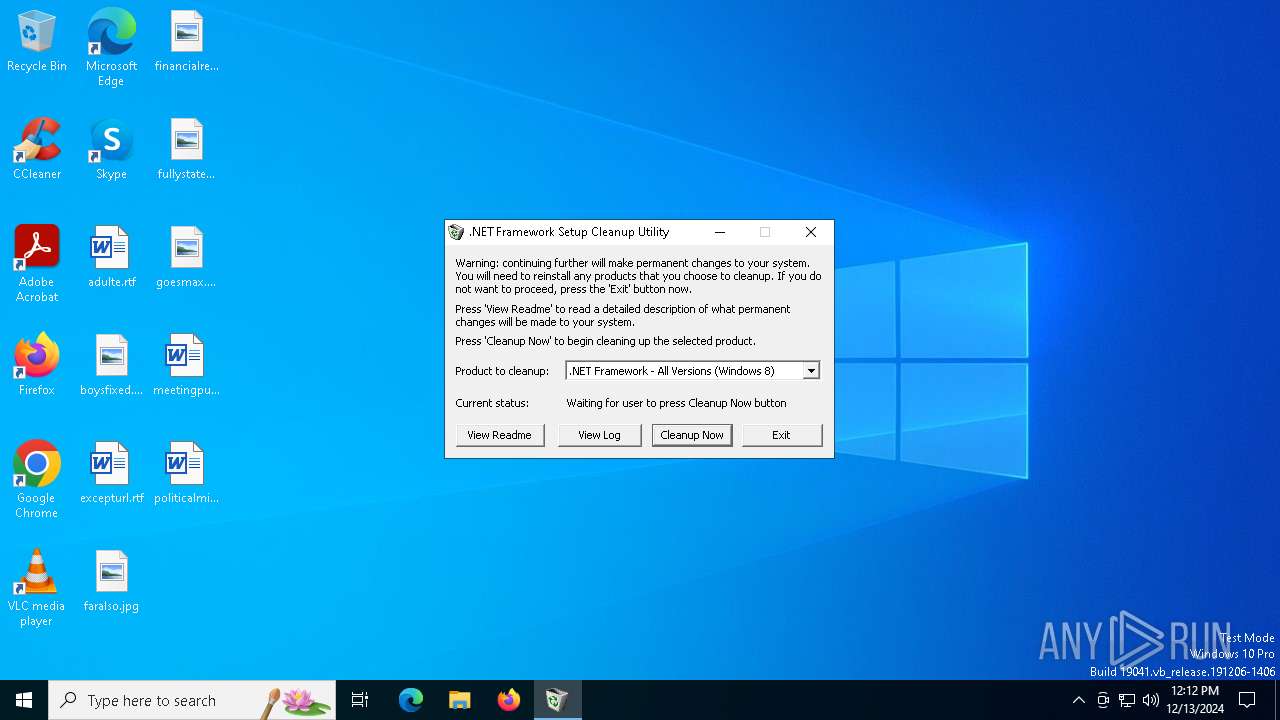
Changes the autorun value in the registry
- cleanup_tool.exe (PID: 6160)
SUSPICIOUS
Process drops legitimate windows executable
- cleanup_tool.exe (PID: 6160)
Starts a Microsoft application from unusual location
- cleanup_tool.exe (PID: 6160)
- cleanup_tool.exe (PID: 5588)
Reads security settings of Internet Explorer
- cleanup.exe (PID: 3032)
Executable content was dropped or overwritten
- cleanup_tool.exe (PID: 6160)
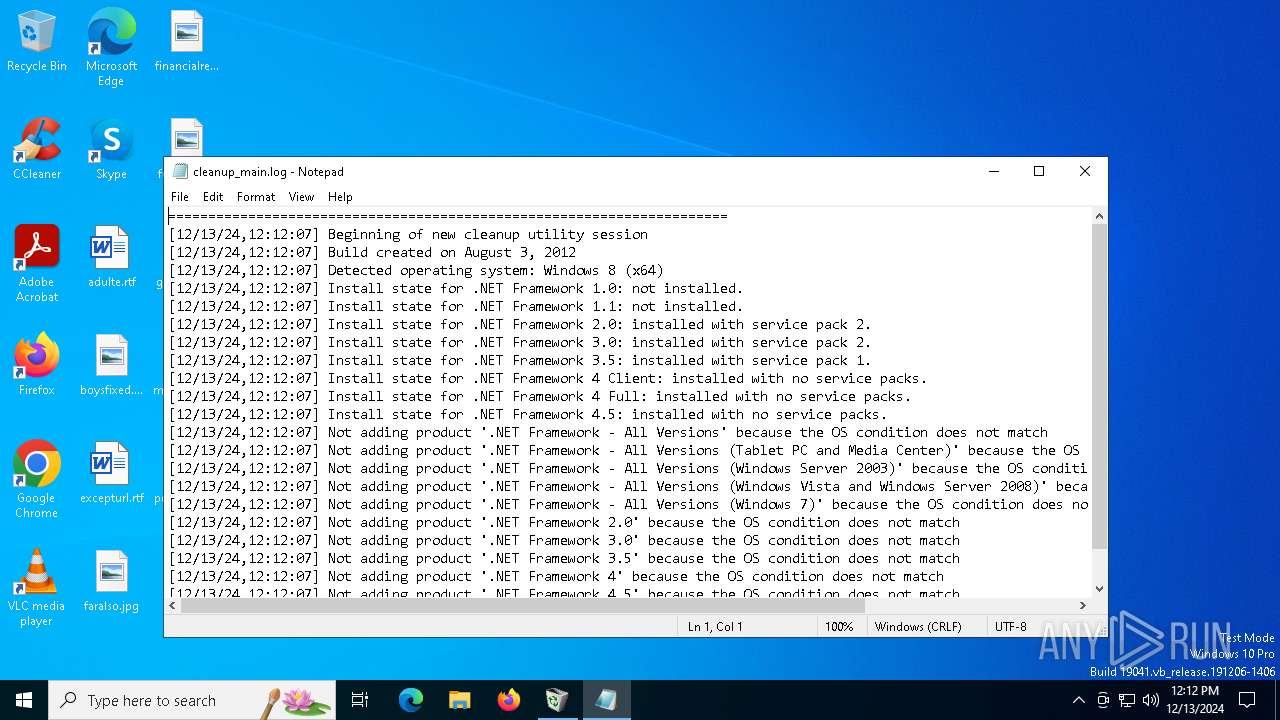
Start notepad (likely ransomware note)
- cleanup.exe (PID: 3032)
INFO
The sample compiled with english language support
- cleanup_tool.exe (PID: 6160)
Reads the computer name
- cleanup_tool.exe (PID: 6160)
- cleanup.exe (PID: 3032)
Checks supported languages
- cleanup_tool.exe (PID: 6160)
- cleanup.exe (PID: 3032)
Create files in a temporary directory
- cleanup_tool.exe (PID: 6160)
The process uses the downloaded file
- cleanup.exe (PID: 3032)
Process checks computer location settings
- cleanup.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:03:25 07:08:18+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 36864 |
| InitializedDataSize: | 260608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5d3c |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.3790.0 |
| ProductVersionNumber: | 6.0.3790.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 6.00.3790.0 (srv03_rtm.030324-2048) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.3790.0 |
Total processes
133
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\cleanup_main.log | C:\Windows\SysWOW64\notepad.exe | — | cleanup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cleanup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cleanup.exe | — | cleanup_tool.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5588 | "C:\Users\admin\AppData\Local\Temp\cleanup_tool.exe" | C:\Users\admin\AppData\Local\Temp\cleanup_tool.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 6.00.3790.0 (srv03_rtm.030324-2048) Modules
| |||||||||||||||
| 6160 | "C:\Users\admin\AppData\Local\Temp\cleanup_tool.exe" | C:\Users\admin\AppData\Local\Temp\cleanup_tool.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Version: 6.00.3790.0 (srv03_rtm.030324-2048) Modules
| |||||||||||||||
Total events
652
Read events
650
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6160) cleanup_tool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3032) cleanup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.log\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
4
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_errors.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\msizapa.exe | executable | |
MD5:8FF91F846A078660B415D84BBA98A003 | SHA256:F5B33D62B517B354C63A3A50F1E4859A9359D9F60C6E4408179960B4C15C5BCB | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\readme.txt | text | |
MD5:D021D37EAFBF50B591E869A8DFEE3D76 | SHA256:10992FA4DDD391612DBD8FA84F829223BF48397209B216A02943B76AC696A007 | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\msizapw.exe | executable | |
MD5:27D4BCC325306B1415A89DE550528E04 | SHA256:C8089B1734F68420E912978AC0DD29D8772B1F527D2BFFBAAA9D3FAD9F4051E5 | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cleanup.exe | executable | |
MD5:D8AB8704BCEE0FE201FEA3DD531F9AB5 | SHA256:B5DA0E45A75DEB0029AB106C62C5AE6C62D4098107CF52EABF44F24A2E70077E | |||
| 3032 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_main.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
| 3032 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_actions.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\cleanup.ini | text | |
MD5:F92B47A7BD64C38174796876F84C6258 | SHA256:F3629FAB7B898CCE2CF5C1135C0B1AA9ADA2C44E1D7F645990ACEE7B96B1B1AA | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\history.txt | text | |
MD5:666666F75FDC3E3BF33531B0C3DE0153 | SHA256:CA6545FD4089B3DC2784AB5FACFF86918E49C85A1B54E4217398783D07A2FC04 | |||
| 6160 | cleanup_tool.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\unicows.dll | executable | |
MD5:E1102CEDF0C818984C2ACA2A666D4C5F | SHA256:22F23CC65698741184EC34F46E6F69717644E0B5AABF5D5BD015101F2D72E56E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6264 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6264 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7112 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7112 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.140:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |