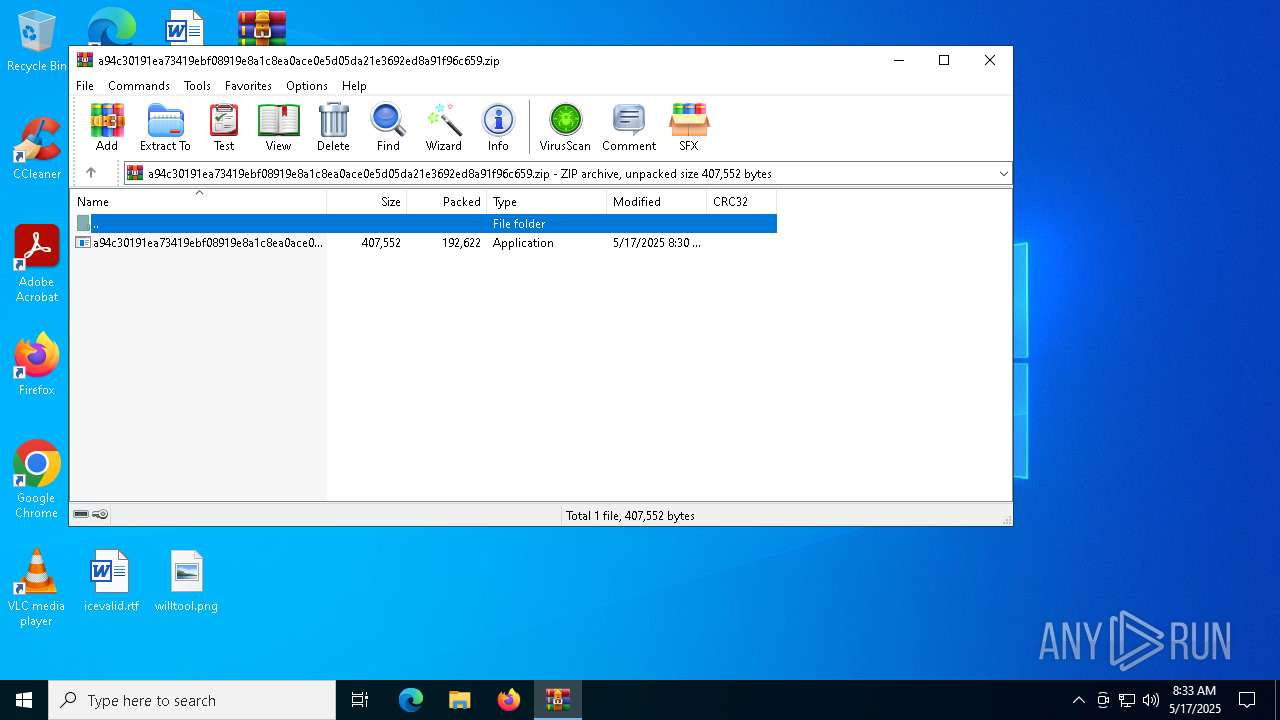
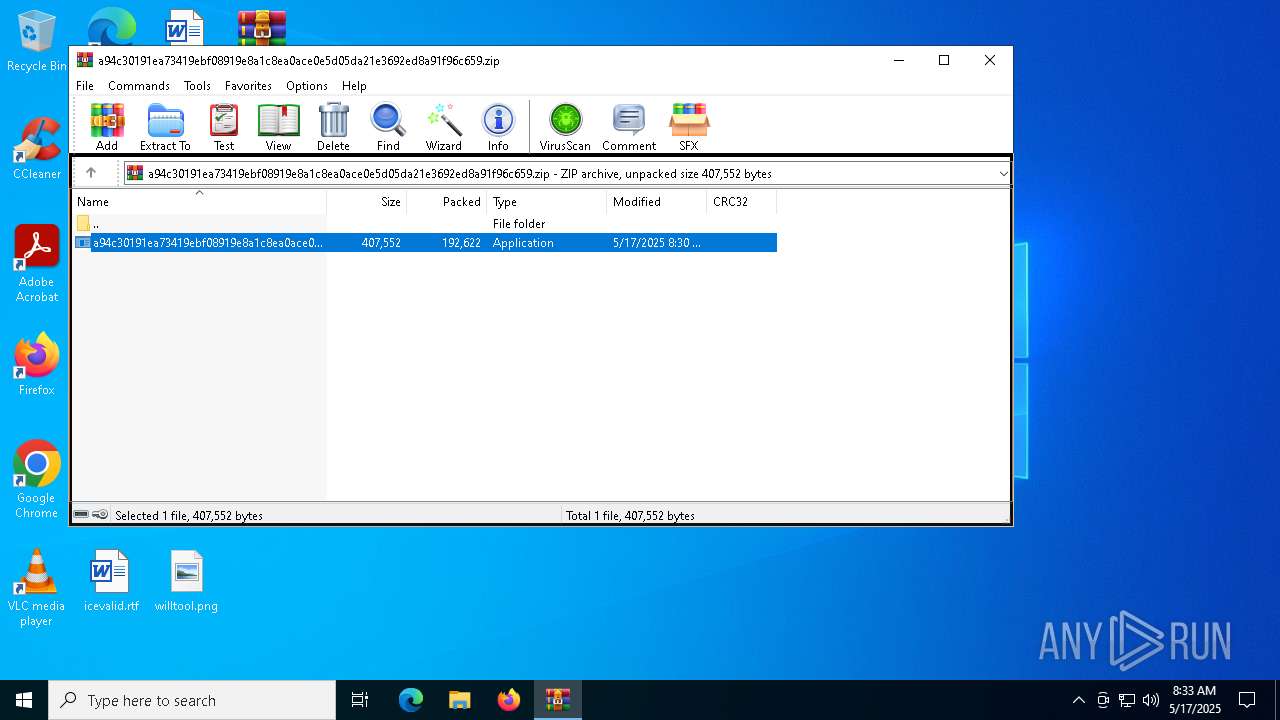
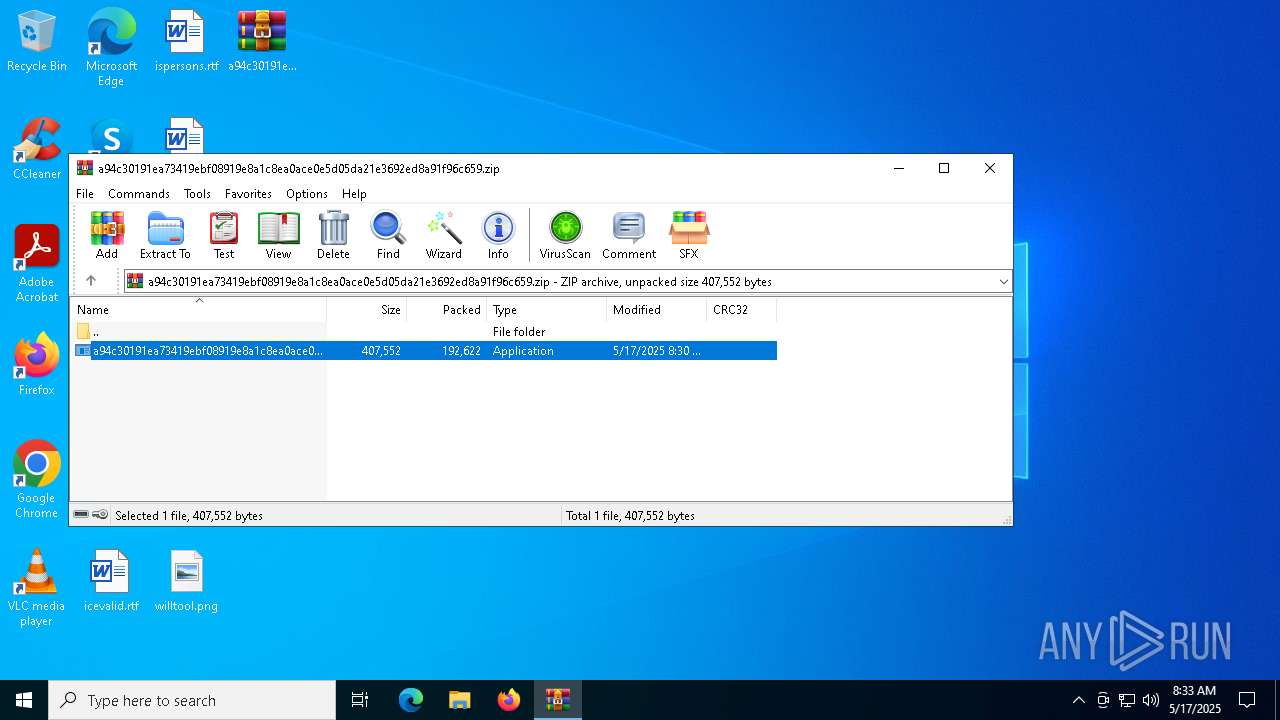
| File name: | a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.zip |
| Full analysis: | https://app.any.run/tasks/e97aea0e-ca33-4baa-b98c-f12b83a5d405 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 08:33:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
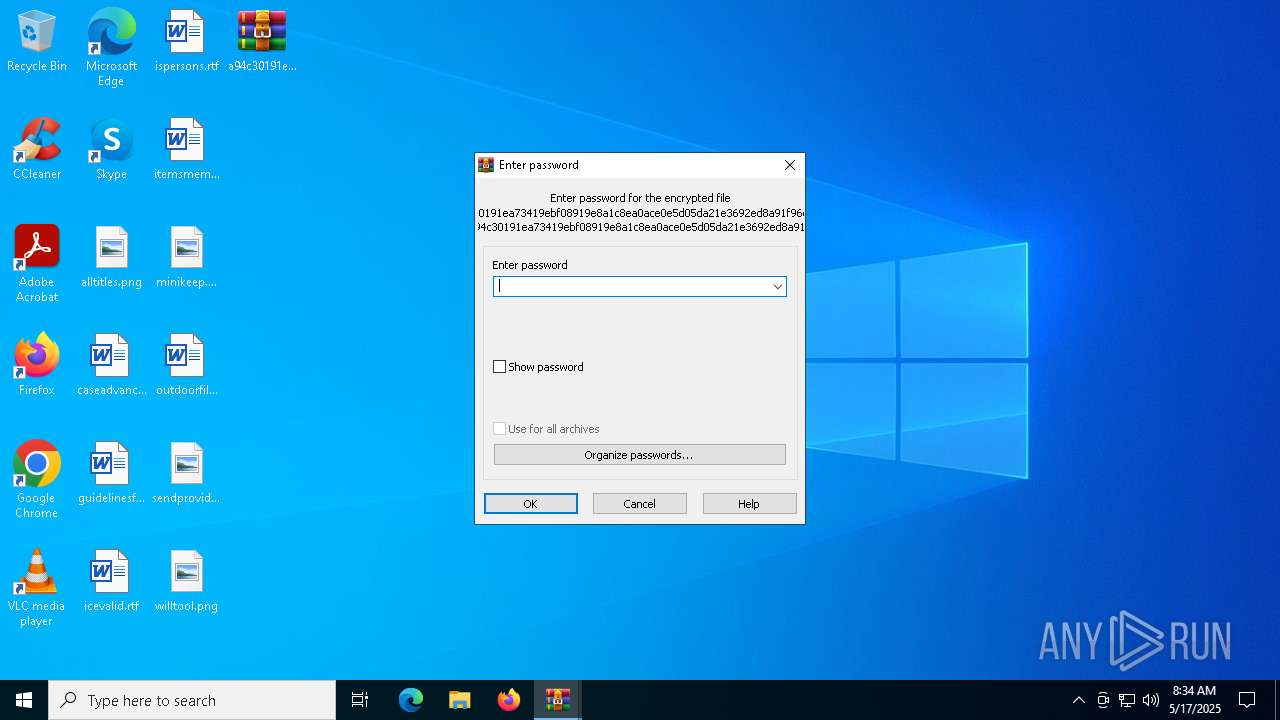
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | CA339EBEE052BD5B3618ED8DC63C9D9C |
| SHA1: | 1985BA35A7289A9AAE781D610E71F836A726524B |
| SHA256: | 8CE3717F118CD0E82C0A19168A4ABB15AABE46A1F6C57CBF77579F2188F4B40A |
| SSDEEP: | 6144:GJ2vqN5csT2Ku/snuzDzkWK0MItDTqFsWW3Uoissv:oLT5ukuzDzkWK9o2CHdFe |
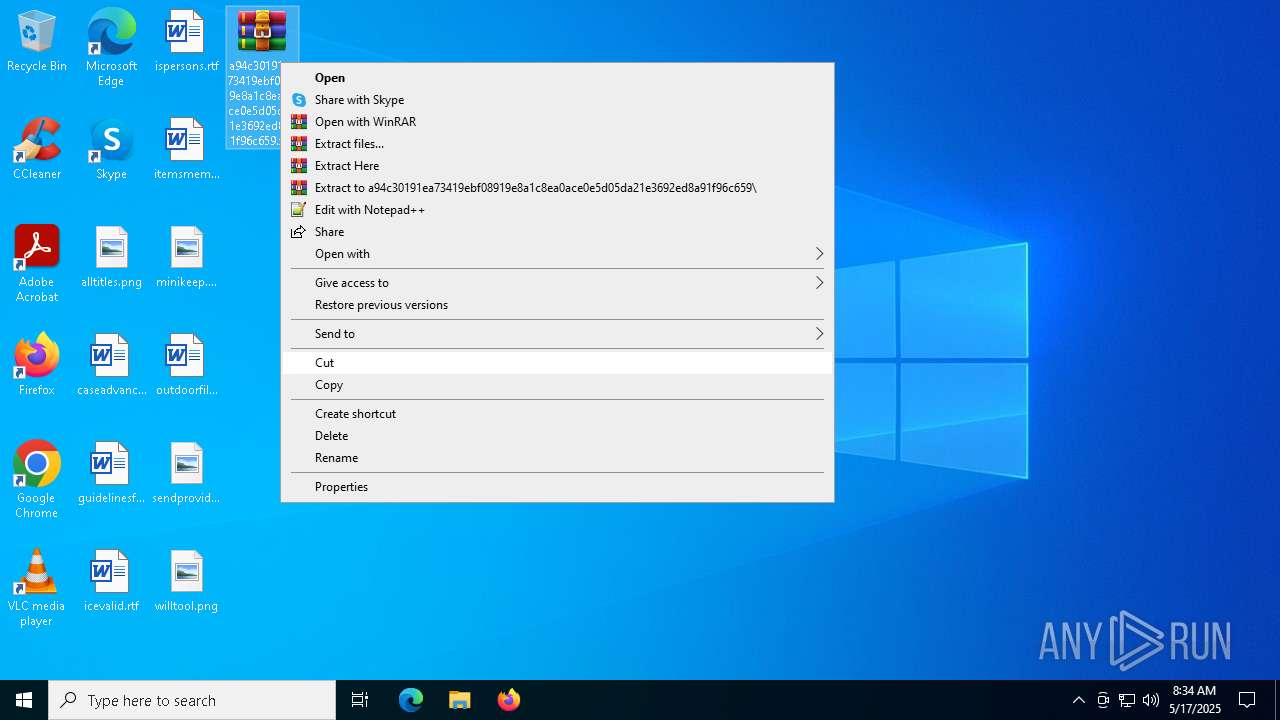
MALICIOUS
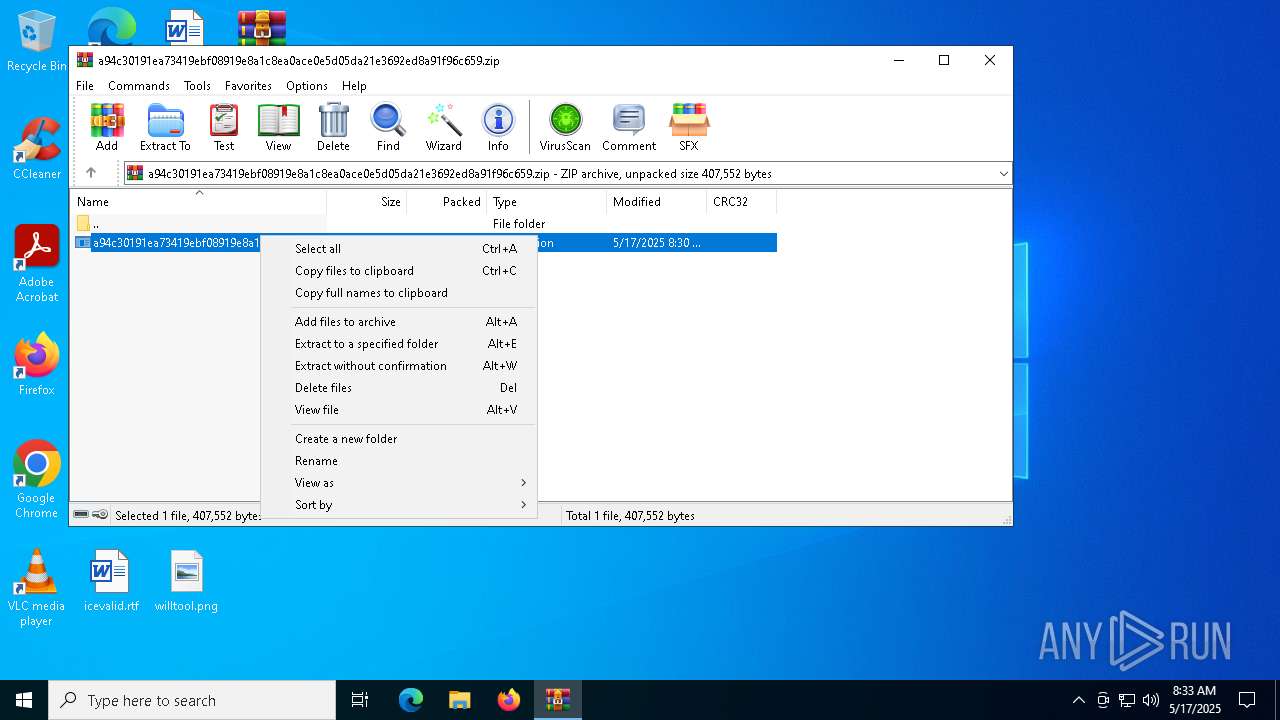
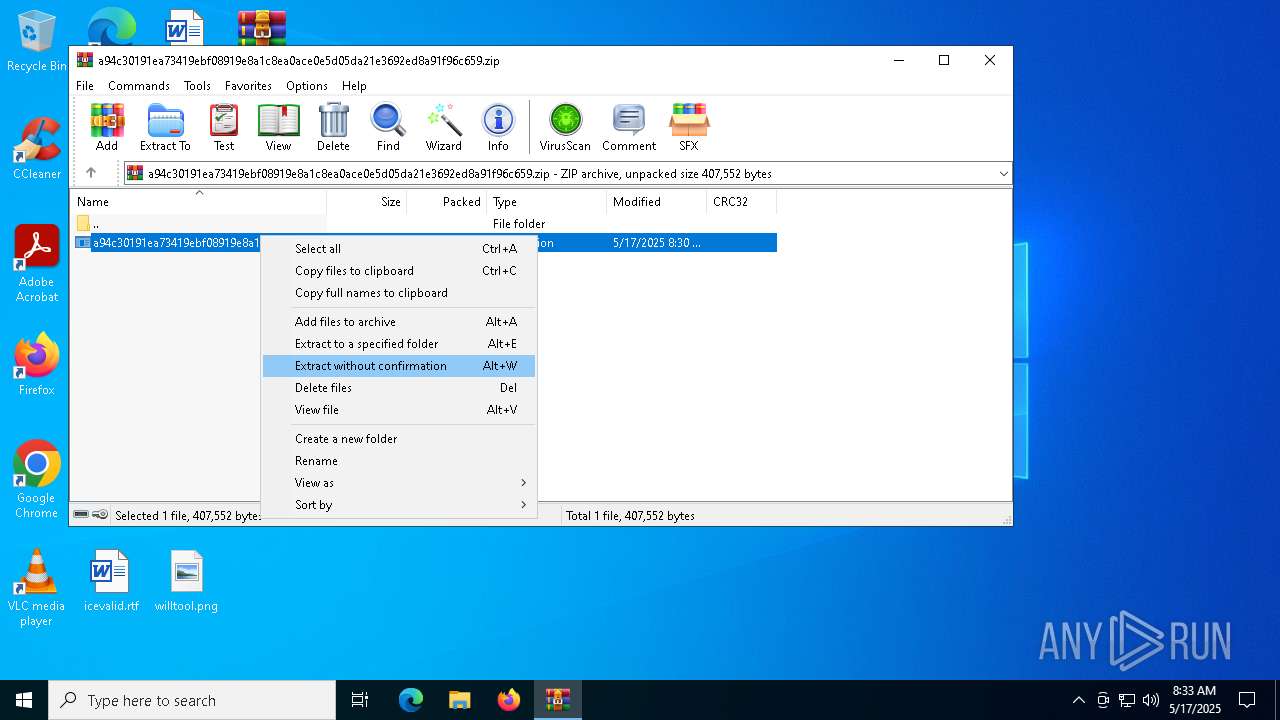
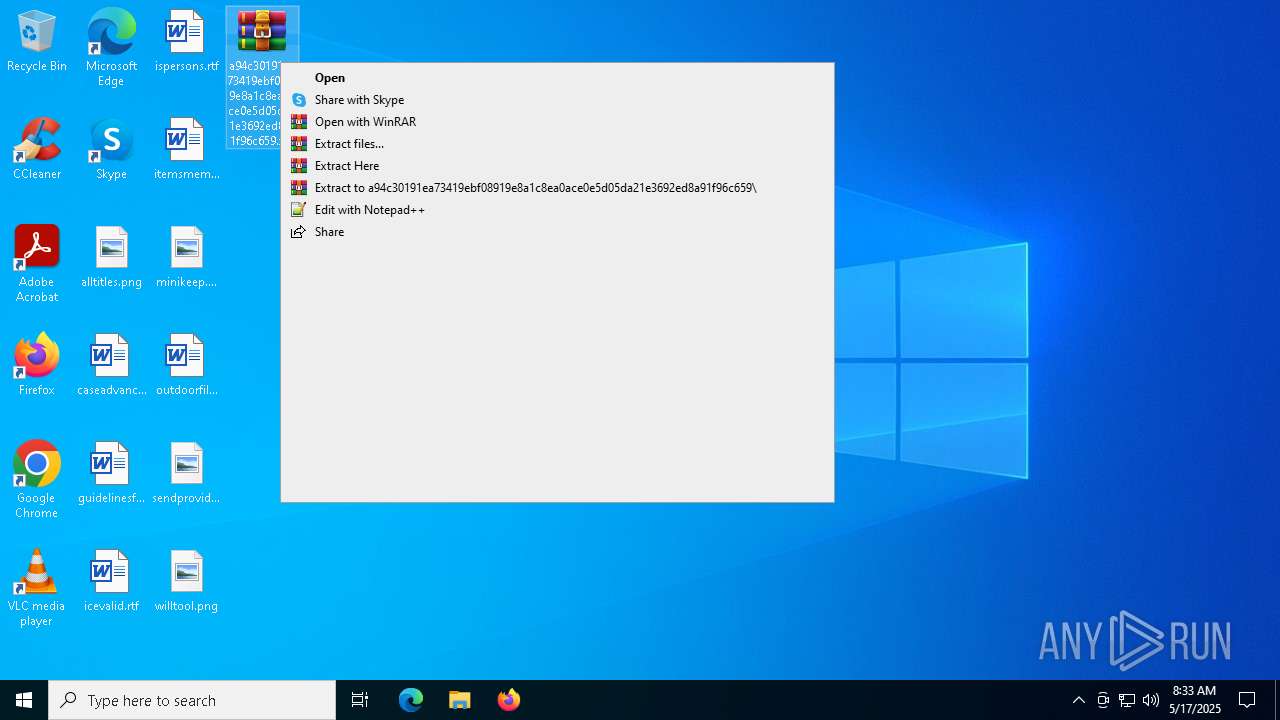
Generic archive extractor
- WinRAR.exe (PID: 6184)
Known privilege escalation attack
- dllhost.exe (PID: 6808)
Adds process to the Windows Defender exclusion list
- WinTemp-v4.exe (PID: 5380)
Changes Windows Defender settings
- WinTemp-v4.exe (PID: 5380)
Uses Task Scheduler to autorun other applications
- WinTemp-v4.exe (PID: 5380)
Changes the autorun value in the registry
- WinTemp-v4.exe (PID: 5380)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 4200)
SUSPICIOUS
Executable content was dropped or overwritten
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
- WinTemp-v4.exe (PID: 5380)
Script adds exclusion process to Windows Defender
- WinTemp-v4.exe (PID: 5380)
Starts POWERSHELL.EXE for commands execution
- WinTemp-v4.exe (PID: 5380)
Script adds exclusion path to Windows Defender
- WinTemp-v4.exe (PID: 5380)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 536)
- cmd.exe (PID: 1760)
Starts CMD.EXE for commands execution
- WinTemp-v4.exe (PID: 5380)
There is functionality for VM detection VMWare (YARA)
- WinTemp-v4.exe (PID: 5380)
There is functionality for VM detection VirtualBox (YARA)
- WinTemp-v4.exe (PID: 5380)
Hides command output
- cmd.exe (PID: 3140)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 132)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 660)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 856)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 240)
- cmd.exe (PID: 540)
- cmd.exe (PID: 632)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 236)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 6124)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 3016)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 4348)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 5624)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 4108)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 5972)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 2568)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 904)
- cmd.exe (PID: 6124)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 6820)
- cmd.exe (PID: 4812)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 5668)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 868)
- cmd.exe (PID: 1664)
- cmd.exe (PID: 720)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 6276)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 516)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 4108)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 4208)
Uses powercfg.exe to modify the power settings
- WinTemp-v4.exe (PID: 5380)
INFO
Manual execution by a user
- WinRAR.exe (PID: 1616)
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6808)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4380)
- powershell.exe (PID: 616)
- powershell.exe (PID: 920)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4380)
- powershell.exe (PID: 616)
- powershell.exe (PID: 920)
Reads the computer name
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
Checks transactions between databases Windows and Oracle
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1616)
Reads the machine GUID from the registry
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
Create files in a temporary directory
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
Checks supported languages
- a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe (PID: 6960)
- WinTemp-v4.exe (PID: 5380)
Creates files or folders in the user directory
- WinTemp-v4.exe (PID: 5380)
Reads the software policy settings
- slui.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:17 08:30:00 |
| ZipCRC: | 0xcb11eab0 |
| ZipCompressedSize: | 192622 |
| ZipUncompressedSize: | 407552 |
| ZipFileName: | a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe |
Total processes
543
Monitored processes
405
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | cmd.exe /c ping -n 1 -w 1000 8.8.8.8 > nul | C:\Windows\System32\cmd.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | ping -n 1 -w 1000 8.8.8.8 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | cmd.exe /c ping -n 1 -w 1000 8.8.8.8 > nul | C:\Windows\System32\cmd.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | cmd.exe /c ping -n 1 -w 1000 8.8.8.8 > nul | C:\Windows\System32\cmd.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | powercfg /change hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | ping -n 1 -w 1000 8.8.8.8 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | cmd.exe /c ping -n 1 -w 1000 8.8.8.8 > nul | C:\Windows\System32\cmd.exe | — | WinTemp-v4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 791
Read events
42 696
Write events
35
Delete events
60
Modification events
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.zip | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D00000099000000FD03000016020000 | |||
| (PID) Process: | (6184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
5
Suspicious files
2
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4200 | ReAgentc.exe | C:\Windows\System32\Recovery\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tehd1bko.anl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sfp4qatw.uyb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4380 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yl12lbtl.ffn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6960 | a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe | C:\Users\admin\AppData\Local\Temp\WinTemp-v4.exe | executable | |
MD5:84C5DF48853ECC23D000DB972FBA161E | SHA256:1526578E2C2BF890FCEFA092C28C975FF7D2A39165804636F778B3EDDF6FD39B | |||
| 1616 | WinRAR.exe | C:\Users\admin\Desktop\a94c30191ea73419ebf08919e8a1c8ea0ace0e5d05da21e3692ed8a91f96c659.exe | executable | |
MD5:4EDFA1364A6E703A3DE2F73DA22841C3 | SHA256:27E23AB71F60E78FB0705F42134EDC4F0E6B99B9F0C82A8238D59DBCDE2C7D14 | |||
| 616 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BC061E537631346C9A88D990EFE43B20 | SHA256:60F908B7483C26F78E8AAB3514AA4BFC2EF008029C08BE0F82FA3A658054EA73 | |||
| 5380 | WinTemp-v4.exe | C:\Windows\System32\Win-v42.exe | executable | |
MD5:BAA72BD2BCE7ECBF07C28E94A131490D | SHA256:A879B3D5E84C837D5FFF6E740BAF72C21B6289903D7E652D8FBC2382B0FFF963 | |||
| 4200 | ReAgentc.exe | C:\Windows\Panther\UnattendGC\diagerr.xml | text | |
MD5:3A8D2D92D67445734789F82D6E6D90A6 | SHA256:E80AA5A43C517844228A67E8A49E30EE8CF68979E54BA0A3FE660C80978808C6 | |||
| 4200 | ReAgentc.exe | C:\Windows\System32\Recovery\ReAgent.xml | xml | |
MD5:44B2DA39CEB2C183D5DCD43AA128C2DD | SHA256:894EE2B19608D10DF4BF8B8F5BBCF40CE38C09C1F4C5543B6164F40C04BB270D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 92.122.166.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4208 | RUXIMICS.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 104.75.232.13:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
920 | SIHClient.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
920 | SIHClient.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4208 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 92.122.166.169:80 | crl.microsoft.com | AKAMAI-AS | NL | whitelisted |
2104 | svchost.exe | 2.20.118.102:80 | www.microsoft.com | RCS & RDS | RO | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.118.102:80 | www.microsoft.com | RCS & RDS | RO | whitelisted |
4208 | RUXIMICS.exe | 2.20.118.102:80 | www.microsoft.com | RCS & RDS | RO | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 20.199.120.151:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |