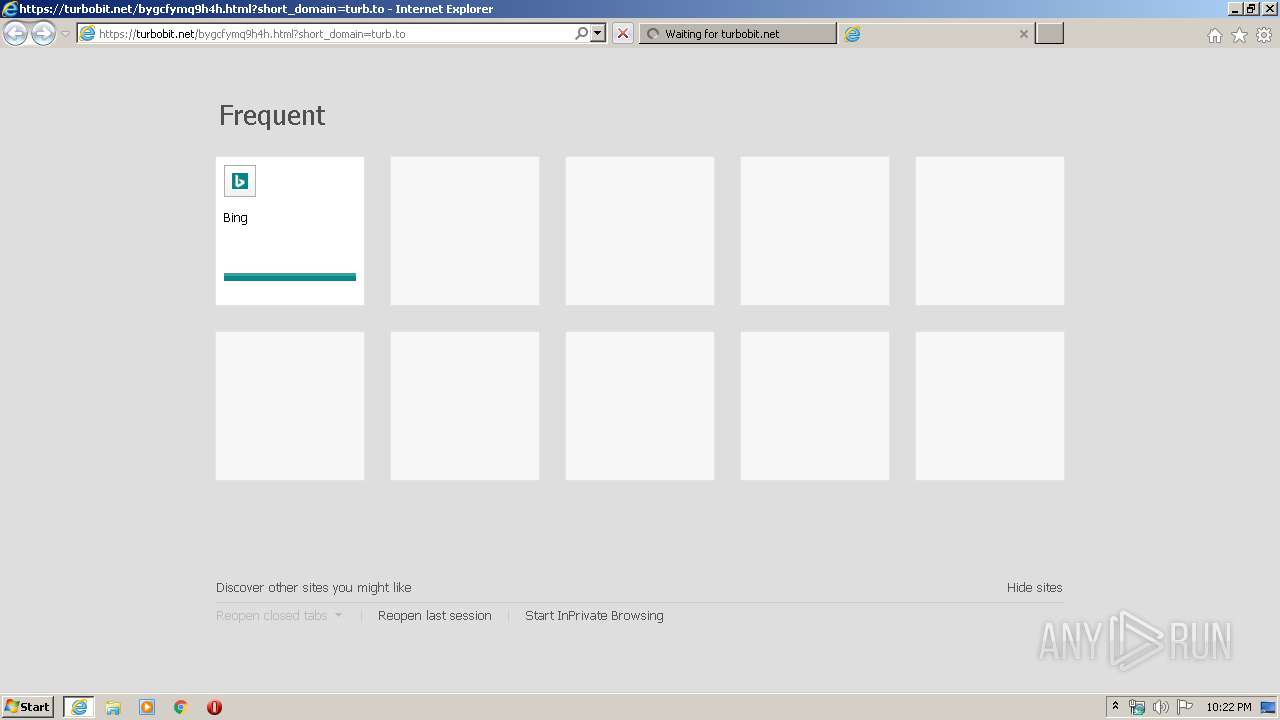
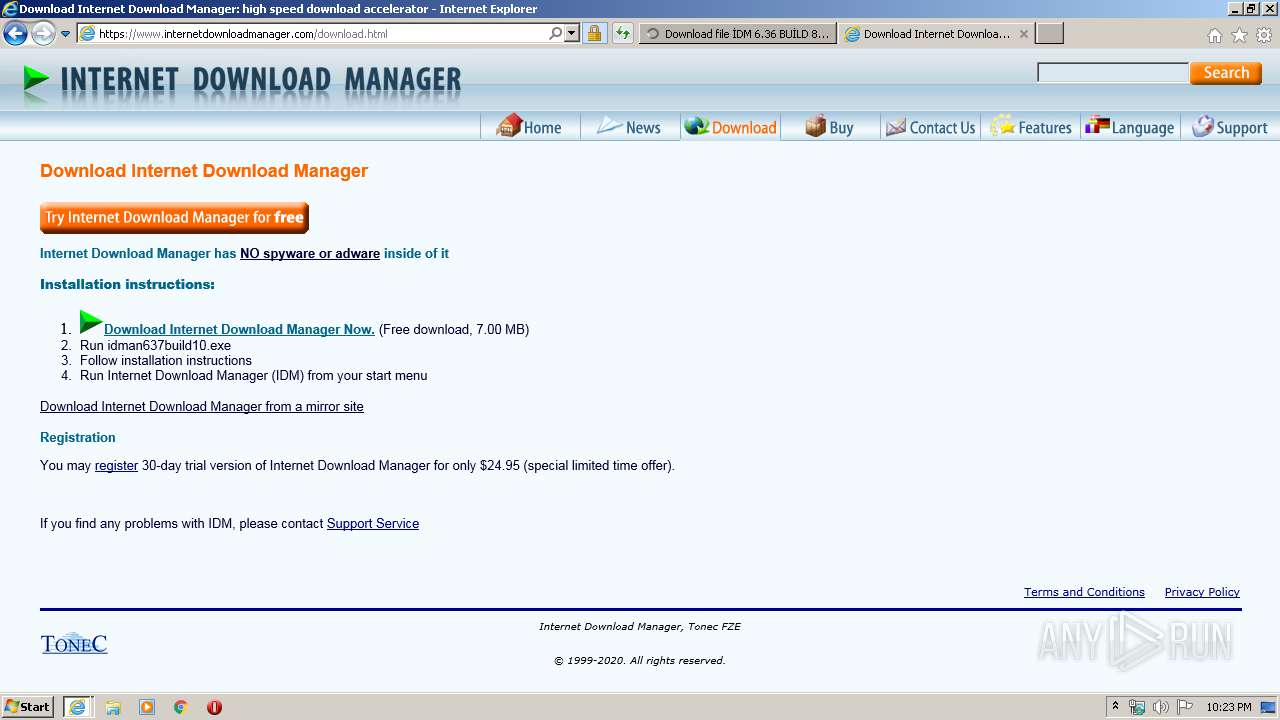
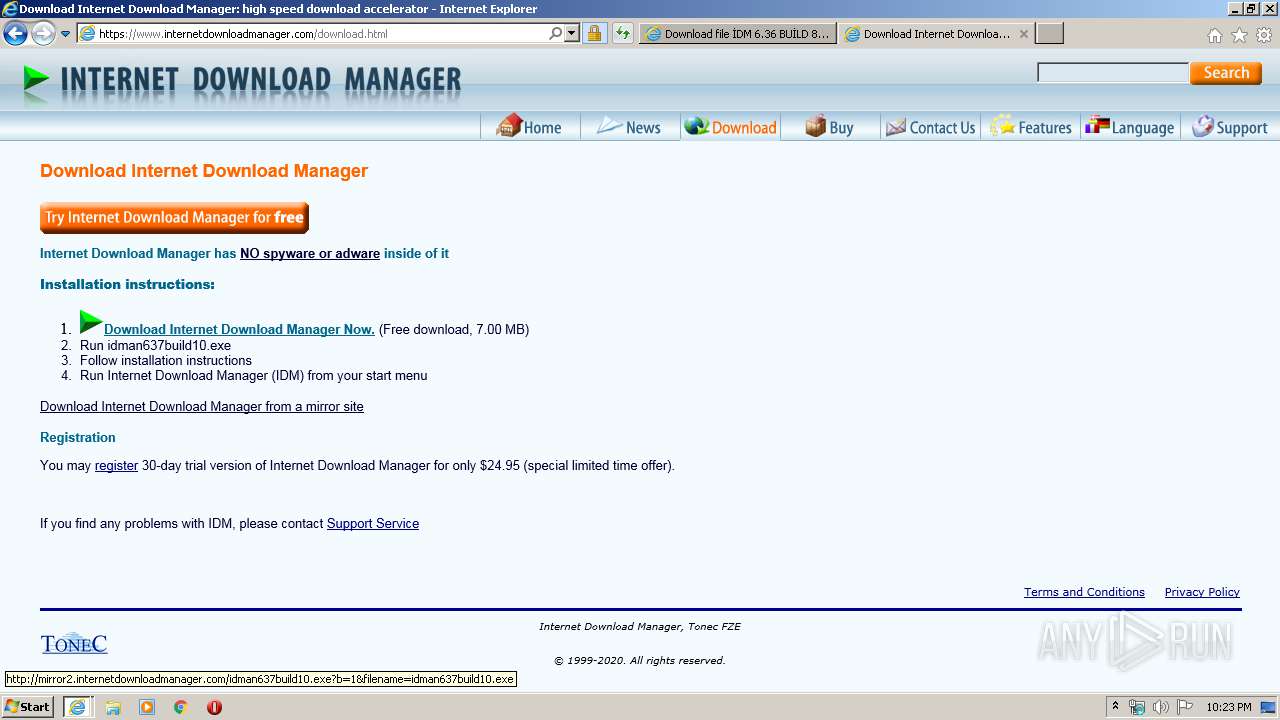
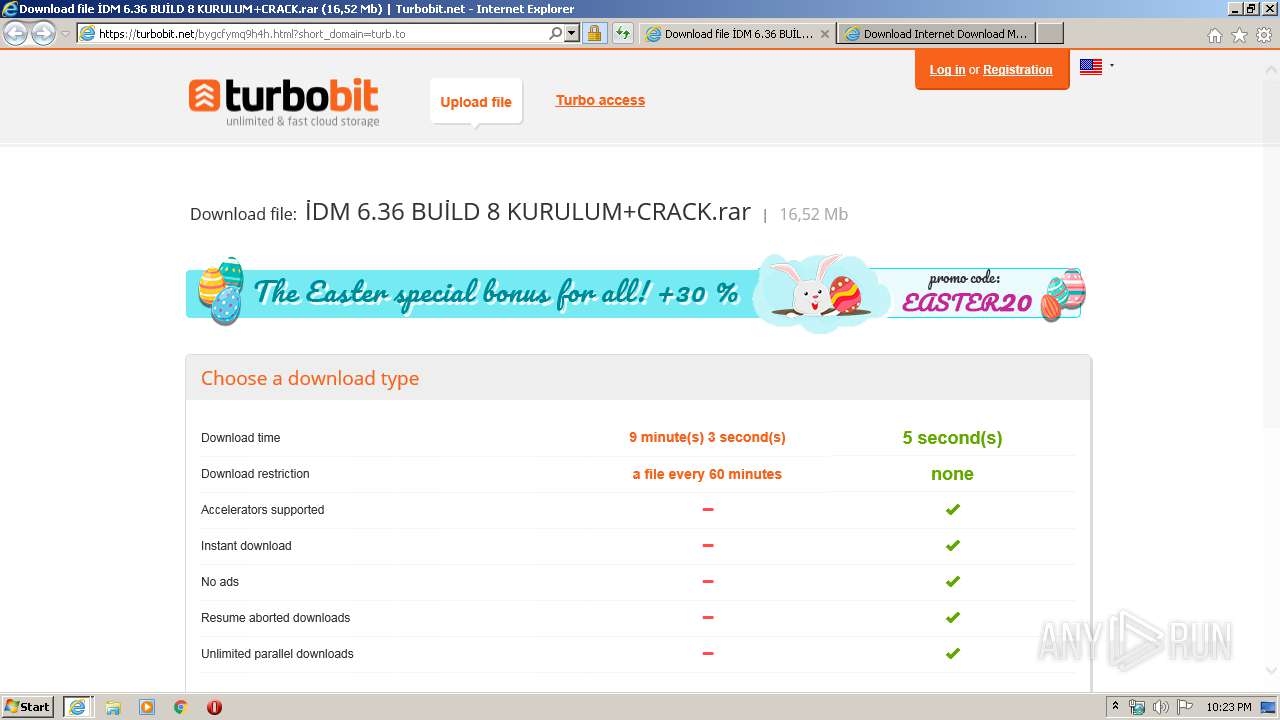
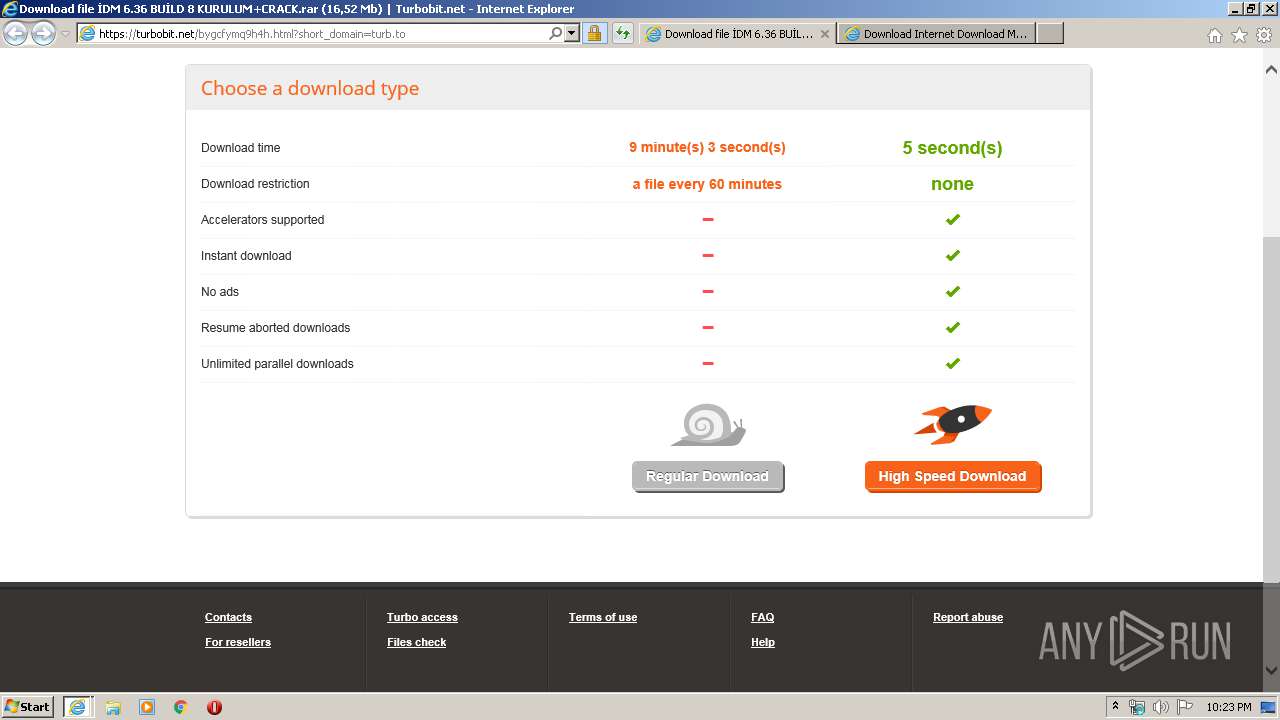
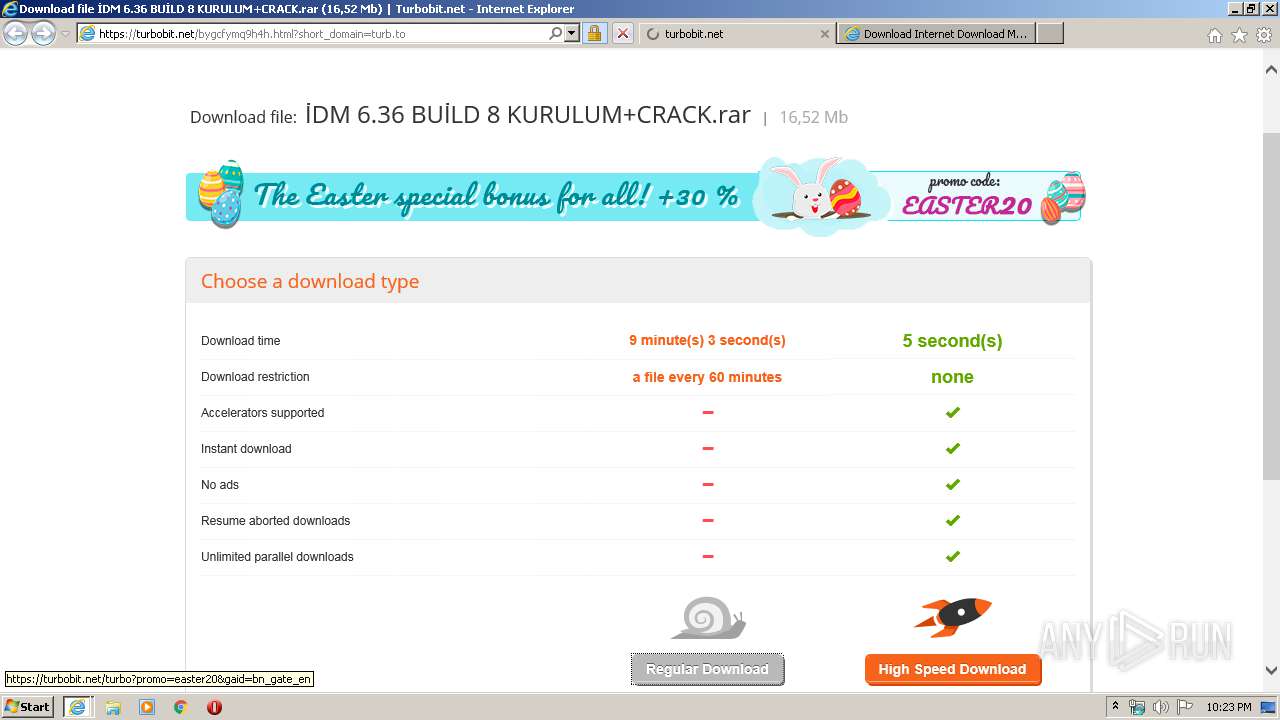
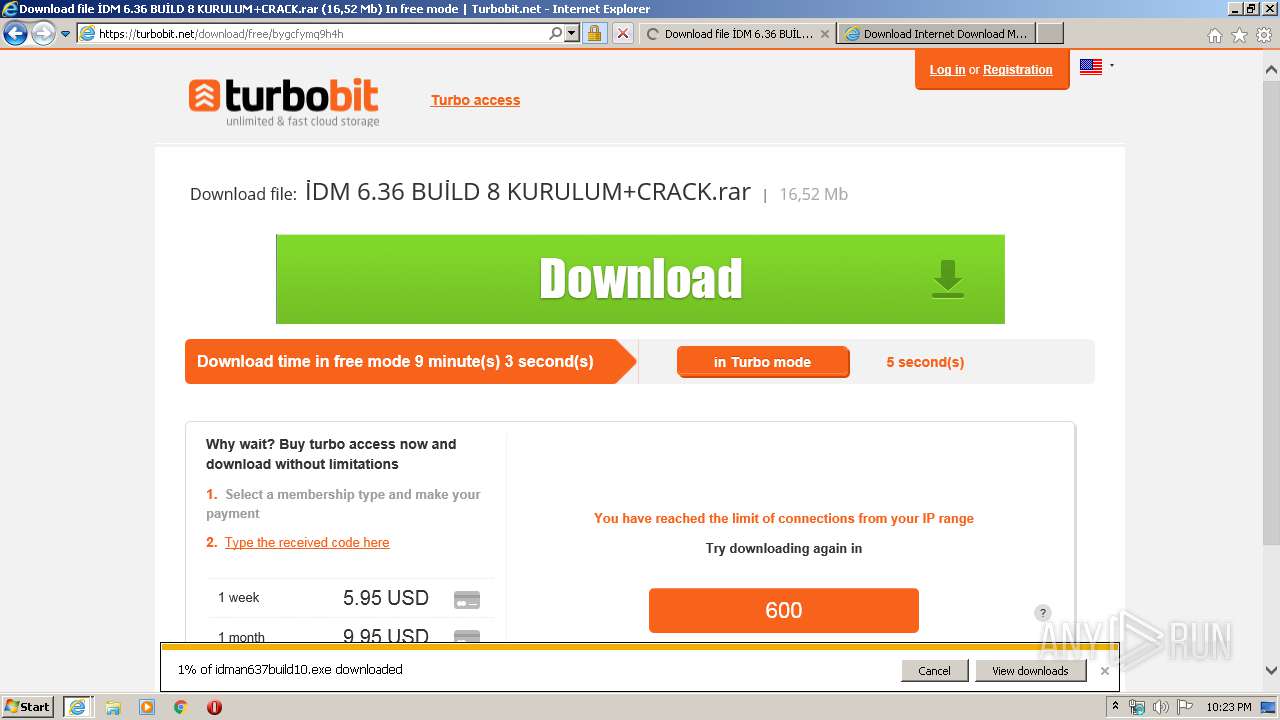
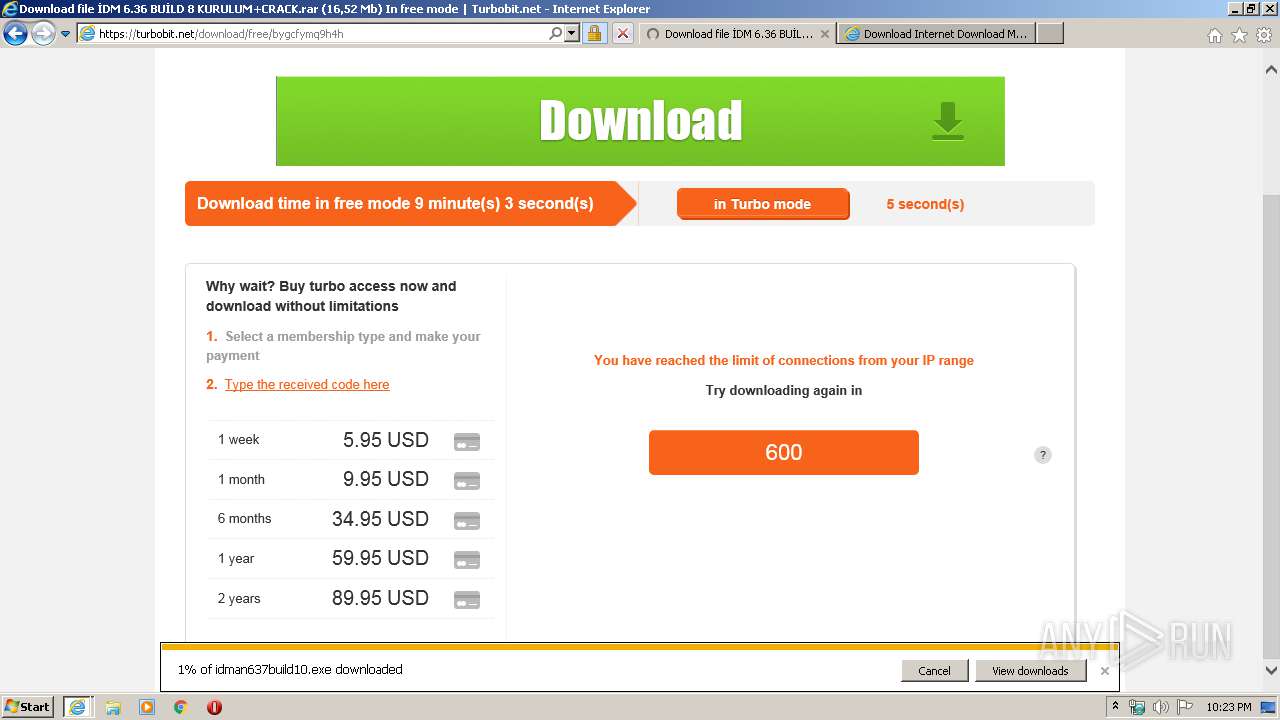
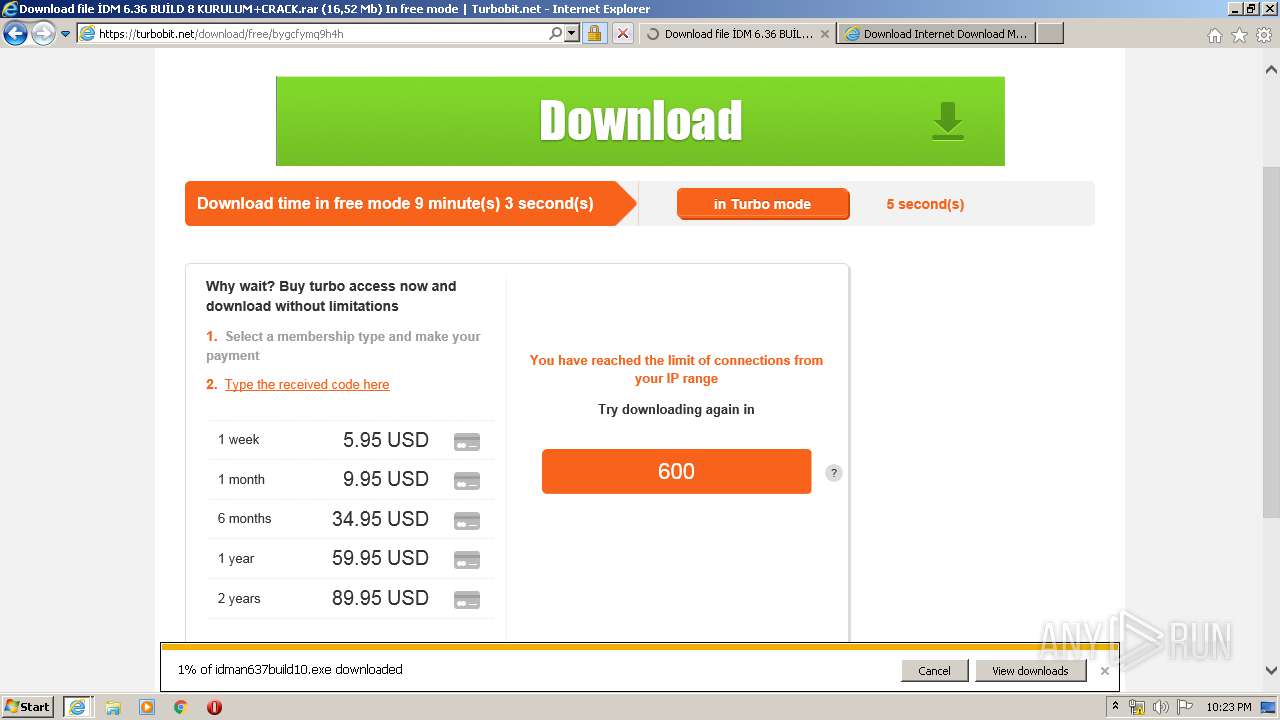
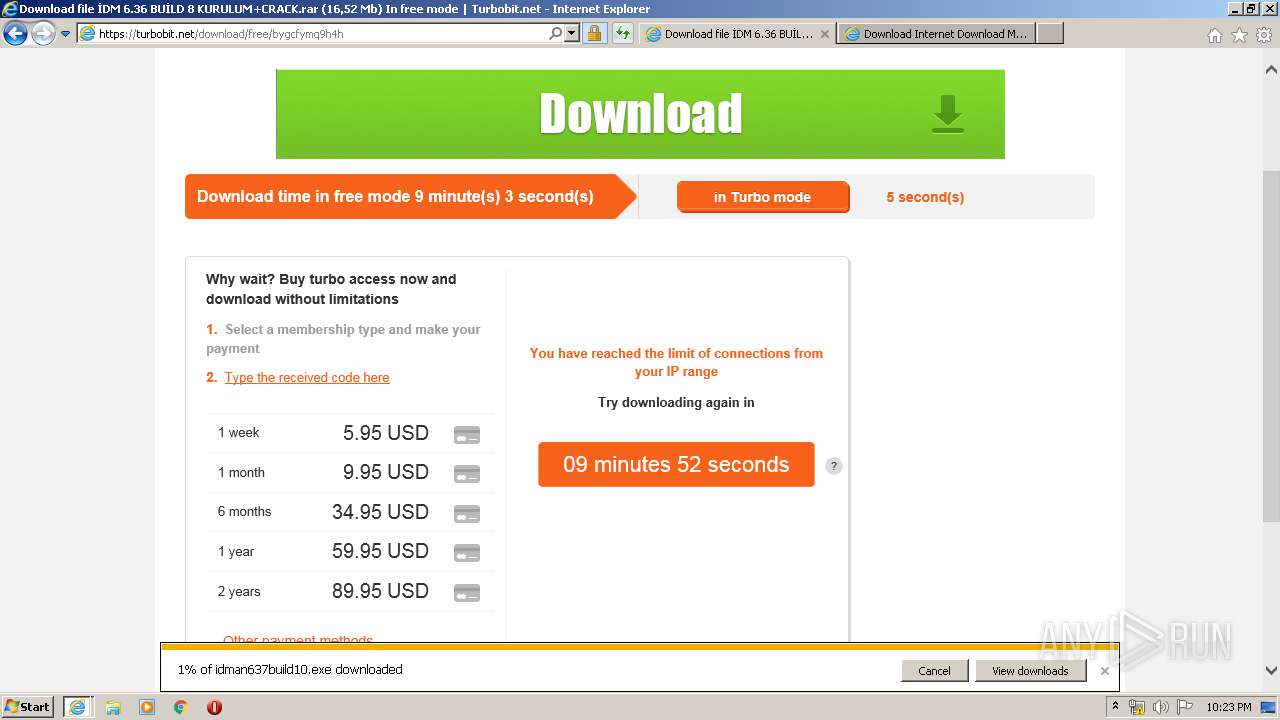
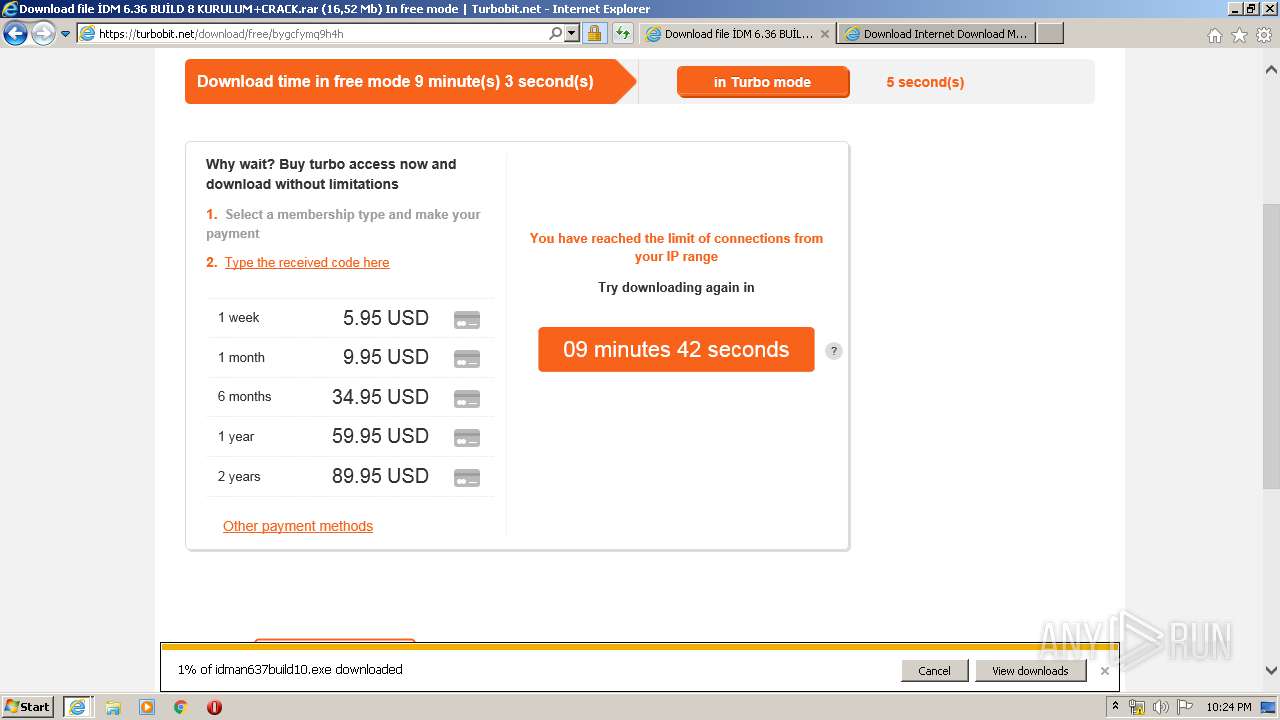
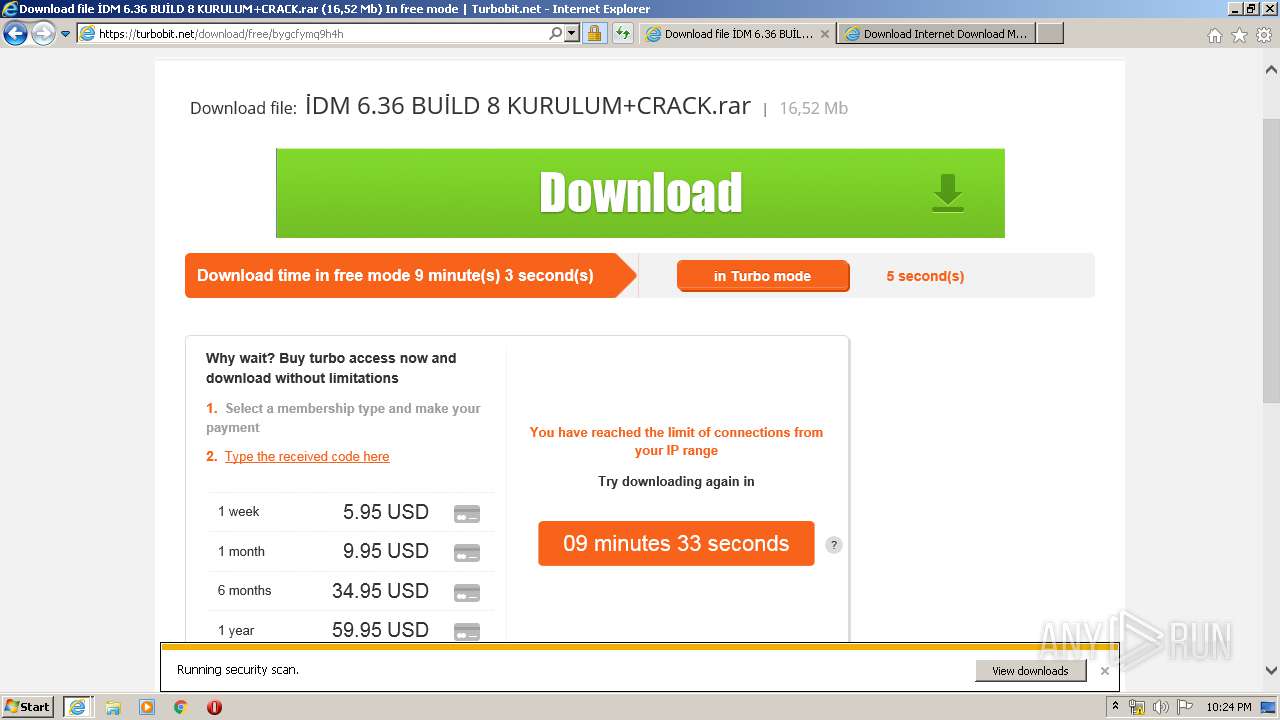
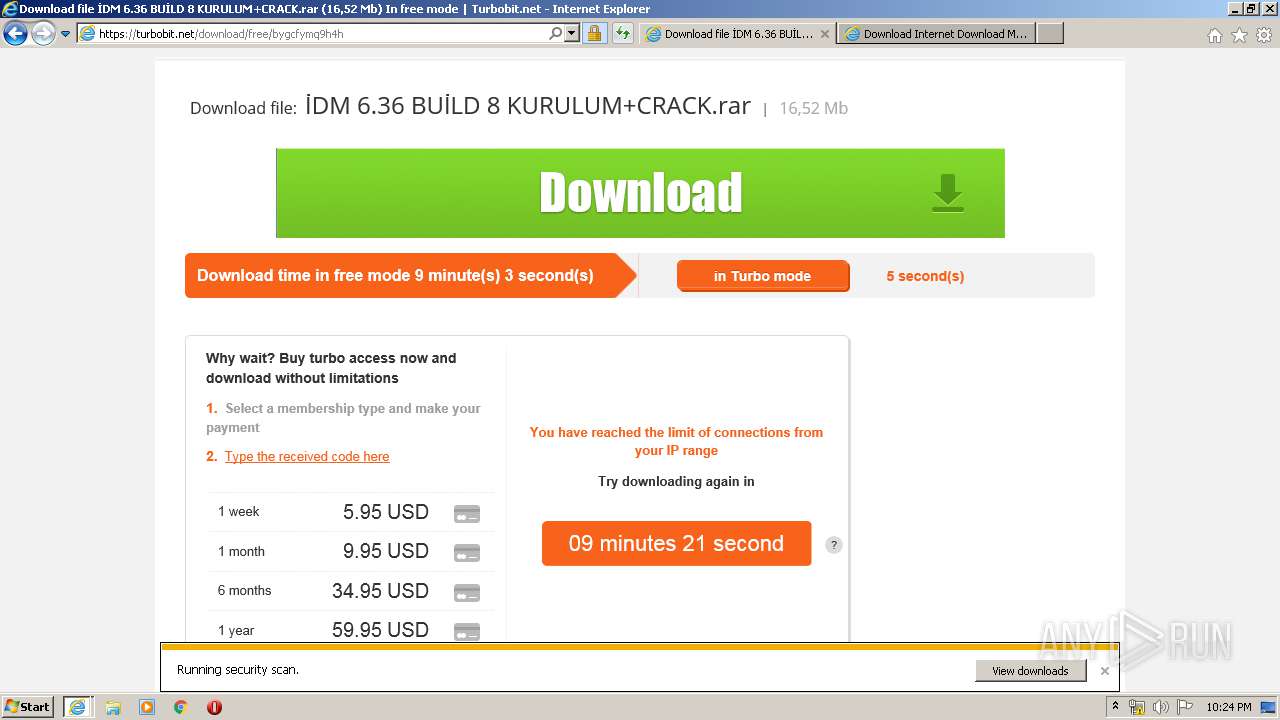
| URL: | https://turbobit.net/bygcfymq9h4h.html?short_domain=turb.to |
| Full analysis: | https://app.any.run/tasks/7dd720f5-3e2e-4f29-a35e-af9b7b6b9340 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2020, 21:22:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 999ED88C59606ED4A5497E20C2730B7E |
| SHA1: | 42747E74CA589A6C0F2F78331CF93D2DE148CC9E |
| SHA256: | 8CD936B73043C92E8B24E8D4CE0E4CDF3C3114CB2953B40B43864738E695B890 |
| SSDEEP: | 3:N8YMYFpcRLUPNQ6ZlNw:2YMaWUPNQ6Z/w |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3364)
- iexplore.exe (PID: 2748)
INFO
Application launched itself
- iexplore.exe (PID: 3364)
Changes internet zones settings
- iexplore.exe (PID: 3364)
Reads Internet Cache Settings
- iexplore.exe (PID: 3364)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2780)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3364)
Reads internet explorer settings
- iexplore.exe (PID: 2780)
- iexplore.exe (PID: 2748)
Reads settings of System Certificates
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3364)
Creates files in the user directory
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3364)
Changes settings of System certificates
- iexplore.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3364 CREDAT:267532 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3364 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://turbobit.net/bygcfymq9h4h.html?short_domain=turb.to" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 924
Read events
1 775
Write events
8 122
Delete events
4 027
Modification events
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1796867976 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30807294 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
94
Text files
193
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U7W4A8I1.txt | — | |
MD5:— | SHA256:— | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8KX6W3K1.txt | — | |
MD5:— | SHA256:— | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Q0RNRMGP.txt | — | |
MD5:— | SHA256:— | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | der | |
MD5:F068842EBC148AC467779278CD59FC06 | SHA256:F0EF65DCF5AD24BEDD874E42FE3DBF0867DB6512553D75A2B7CBDB168893CD47 | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\F071O371.txt | text | |
MD5:70E71C21F84E4286296812AF4EA6D0D6 | SHA256:F80526CB3B149799E54E4576FA58D97070E5BCD5DA06DFB1CEF82877D2A743B1 | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].xml | xml | |
MD5:98A1135763F12FF0DB653721562EAAF3 | SHA256:EAF8D7531BC75346DA5CD61715A01B67C4E00579D0494AA458DF7265D301E47B | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\29RTPZUF.txt | text | |
MD5:3FE69311AFDF56FE0A371973468453B1 | SHA256:01C243FD843C4F0A5F6880B8DE238724F872865C4E7D496933D53B9B7F88A2E8 | |||
| 2780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[2].xml | xml | |
MD5:F2CAD6387E64A4DD5747D9EE858E7067 | SHA256:3895E416BF580C55D1A6E604D8351C575B52D4373262C4AF406EC7B5736492A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
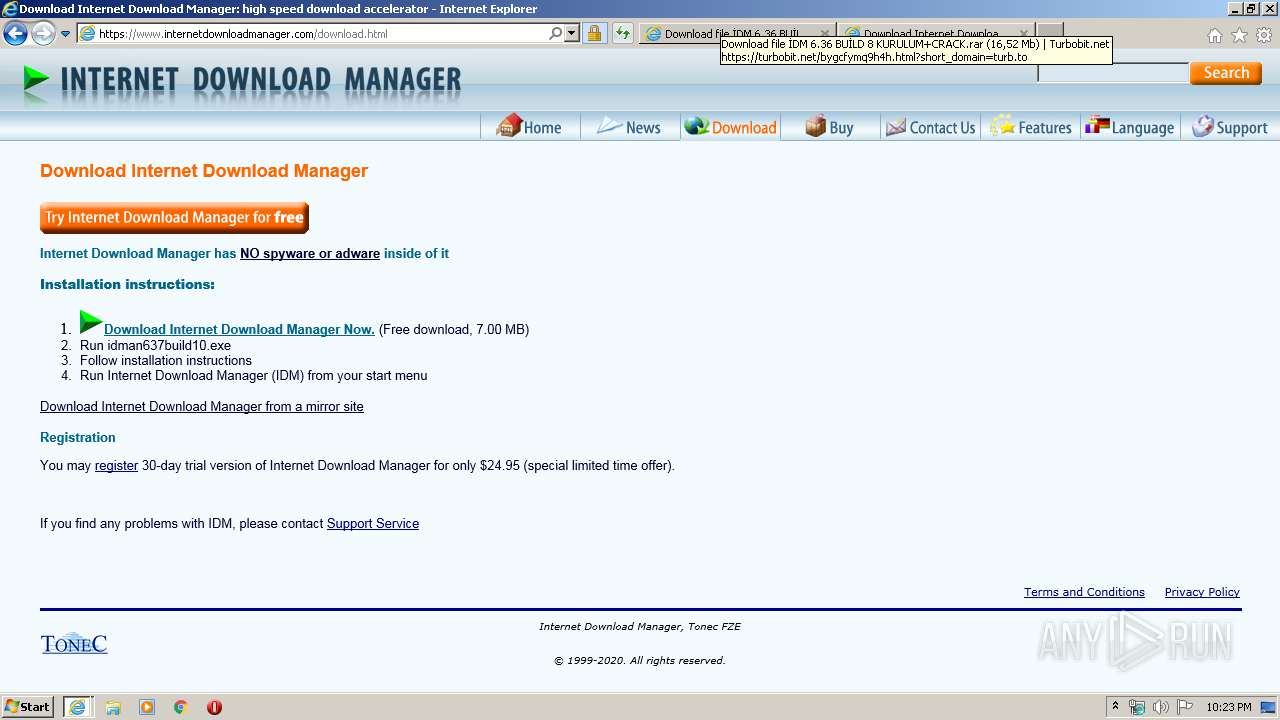
HTTP(S) requests
132
TCP/UDP connections
108
DNS requests
43
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
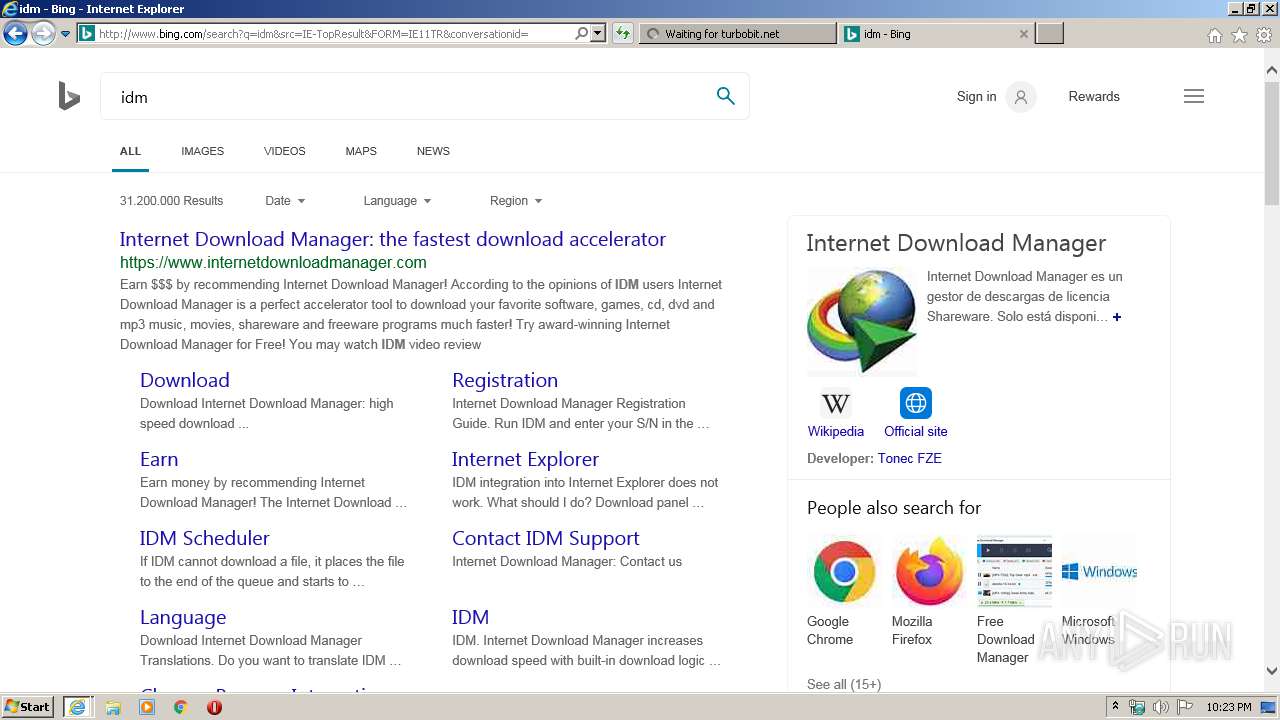
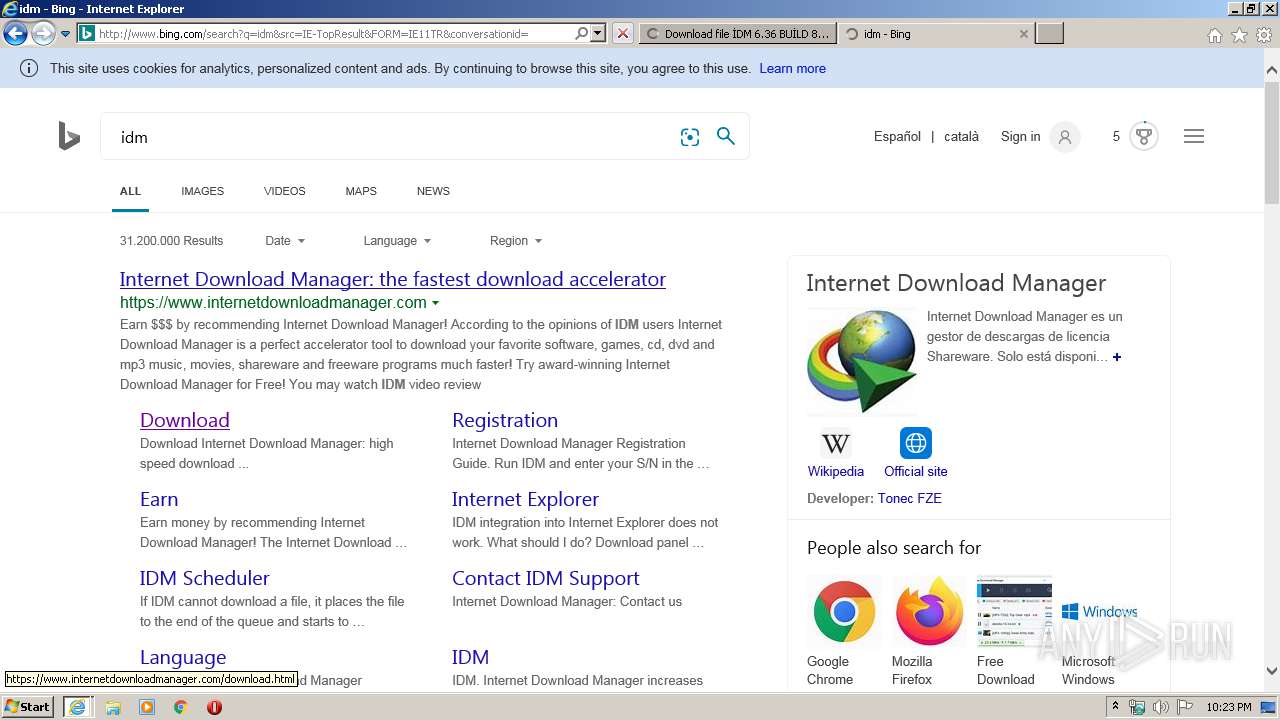
2748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=C8BC032208B14BDEBCCD15197C8FA739&CID=09E3575ABFB260783D0C59F5BE056107&Type=Event.CPT&DATA={"pp":{"S":"L","FC":82,"BC":215,"SE":-1,"TC":-1,"H":417,"BP":495,"CT":578,"IL":13},"ad":[-1,-1,1264,644,1264,2918,0]}&P=SERP&DA=DUB02 | US | image | 609 b | whitelisted |
2780 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2780 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
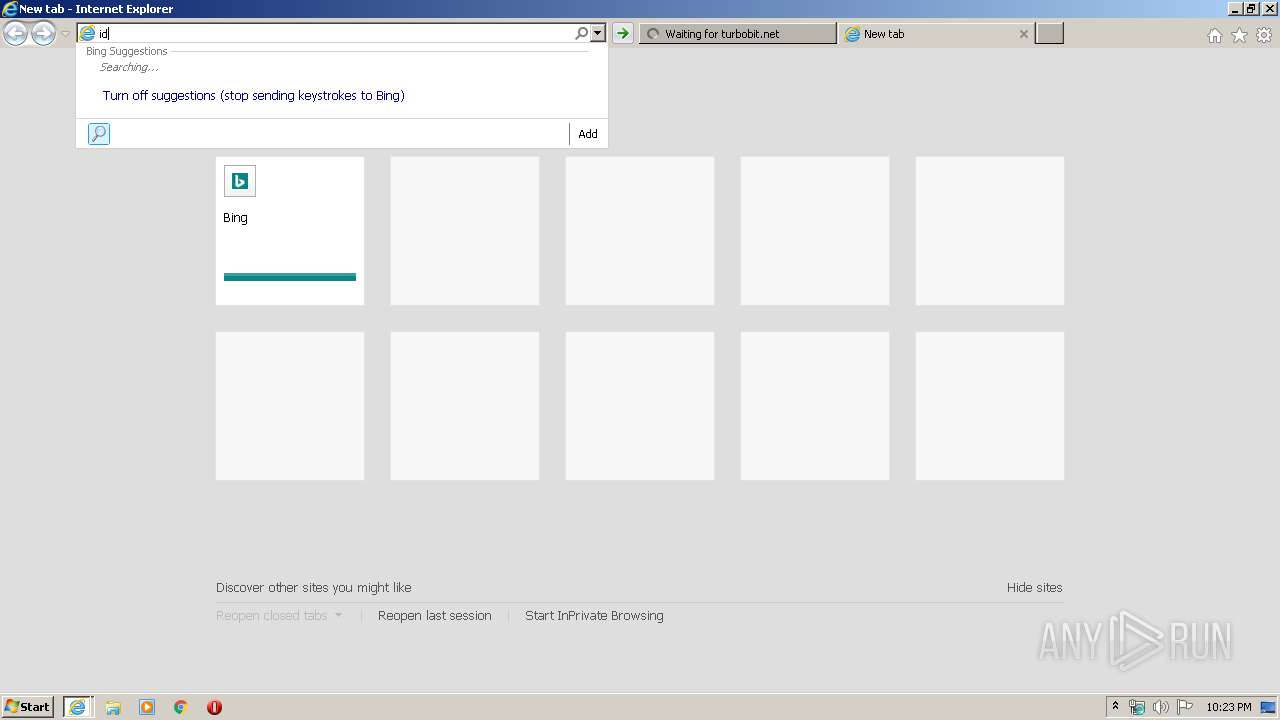
2780 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=i&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 235 b | whitelisted |
2748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5h/TP/ic/ZricD7XDh2XWjN68qgUU8lqqArQ.png | US | image | 609 b | whitelisted |
3364 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/th?id=OVP.J94Y7COWiTPmCTgh97Y_7QEsDh:OVP.iDXYEyg0vvtvbj1dY54o4gEsDh&w=197&h=110&c=7&rs=1&qlt=90&pid=1.7&bw=3&bc=ffffff | US | image | 24.8 Kb | whitelisted |
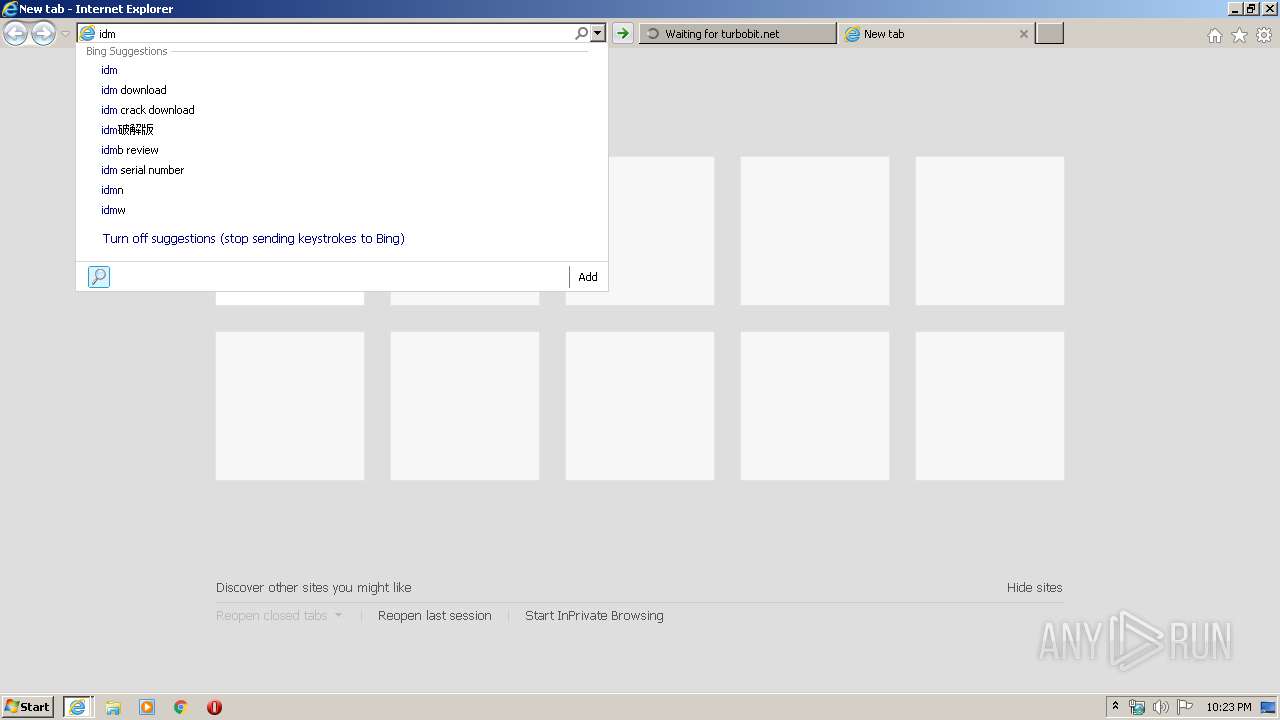
2780 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=idm&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 240 b | whitelisted |
2748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6h/158/cj,nj/JOVKK9CwtlLttGBW-c2T2aVxX_U.js | US | text | 297 b | whitelisted |
2748 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/-nK5HAtc03YD_-fIE4Q-t8DnnZY.js?bu=Di8Ycm13empgY7EBswEYngEY | US | text | 7.65 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2780 | iexplore.exe | 5.61.56.86:443 | turbobit.net | — | DE | unknown |
2780 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3364 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2780 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2748 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2748 | iexplore.exe | 40.126.1.128:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
2748 | iexplore.exe | 40.90.137.125:443 | login.live.com | Microsoft Corporation | US | unknown |
2748 | iexplore.exe | 195.138.255.24:80 | a4.bing.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
2748 | iexplore.exe | 104.18.25.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
2748 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
turbobit.net |
| unknown |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
login.live.com |
| whitelisted |
a4.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2748 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |