| File name: | DE_OfficeStandard2019_VL_64_BIT.exe |
| Full analysis: | https://app.any.run/tasks/2bf9642c-4a71-45fd-9b6a-5eaa6032d75a |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2020, 21:03:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 992C99D66014C4F90CBFFD9A29D9AD43 |
| SHA1: | 543857DA853F8A6CBE3B7DEEAD832D30D9DF65E6 |
| SHA256: | 8CCCB7055E6775571BD6F6E40C9A48E6766FE07AF7B970EDB88B77B06A65E967 |
| SSDEEP: | 49152:b8N/qJUSkhhTmrqb5oOJ5Q8H4zrLe8eI14tWeD7J+CIrK:b8N/r1mW5qz5eISttJ+Cx |
MALICIOUS
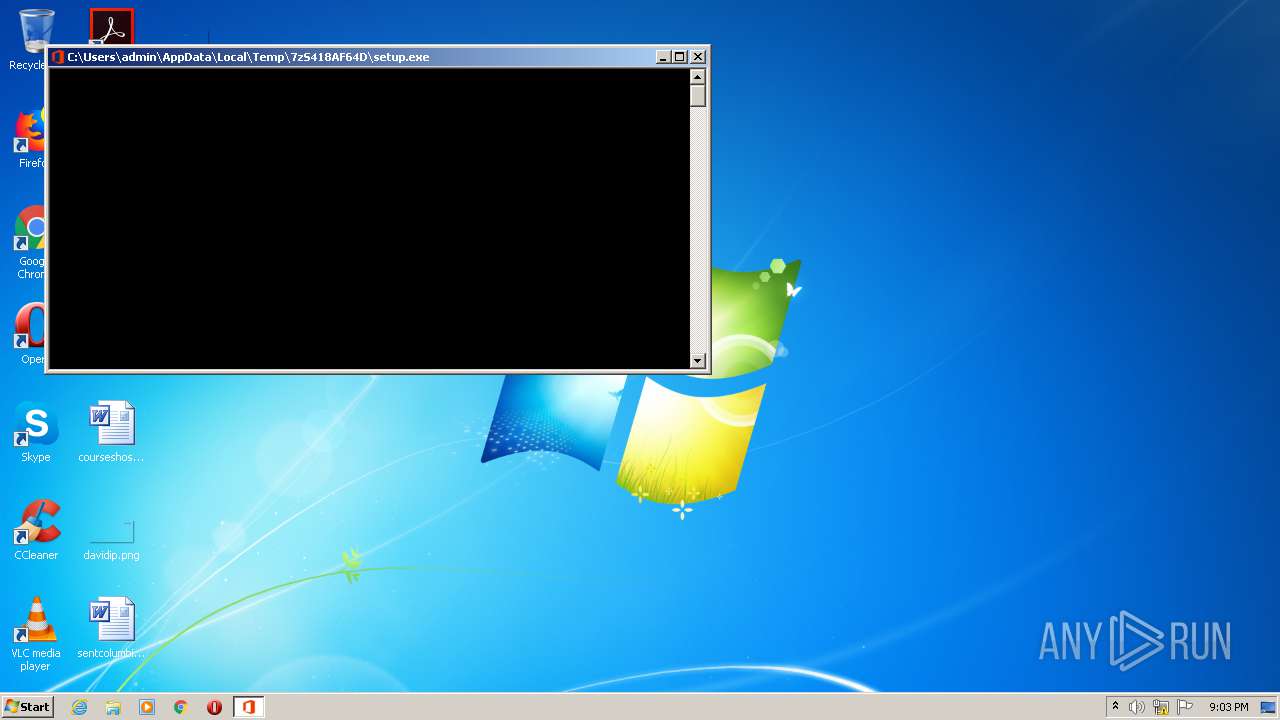
Application was dropped or rewritten from another process
- setup.exe (PID: 3224)
- ose.exe (PID: 668)
- ose00000.exe (PID: 2572)
Changes settings of System certificates
- setup.exe (PID: 3800)
- setup.exe (PID: 3224)
Actions looks like stealing of personal data
- DE_OfficeStandard2019_VL_64_BIT.exe (PID: 2068)
- setup.exe (PID: 3224)
Loads dropped or rewritten executable
- setup.exe (PID: 3800)
SUSPICIOUS
Executable content was dropped or overwritten
- DE_OfficeStandard2019_VL_64_BIT.exe (PID: 2068)
- setup.exe (PID: 3800)
- MsiExec.exe (PID: 3408)
- msiexec.exe (PID: 3724)
- MsiExec.exe (PID: 2576)
- MsiExec.exe (PID: 956)
- MsiExec.exe (PID: 3024)
- MsiExec.exe (PID: 612)
- MsiExec.exe (PID: 2088)
- MsiExec.exe (PID: 908)
- ose.exe (PID: 668)
Adds / modifies Windows certificates
- setup.exe (PID: 3224)
- setup.exe (PID: 3800)
Searches for installed software
- setup.exe (PID: 3224)
- setup.exe (PID: 3800)
Reads Internet Cache Settings
- setup.exe (PID: 3224)
Executed as Windows Service
- vssvc.exe (PID: 2072)
Executed via COM
- DllHost.exe (PID: 1916)
Starts itself from another location
- ose.exe (PID: 668)
Removes files from Windows directory
- msiexec.exe (PID: 3724)
Creates files in the Windows directory
- msiexec.exe (PID: 3724)
INFO
Reads settings of System Certificates
- setup.exe (PID: 3224)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2072)
Reads Microsoft Office registry keys
- setup.exe (PID: 3800)
Application launched itself
- msiexec.exe (PID: 3724)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3724)
- MsiExec.exe (PID: 2576)
- MsiExec.exe (PID: 2300)
- MsiExec.exe (PID: 3408)
- MsiExec.exe (PID: 3540)
- MsiExec.exe (PID: 3024)
- MsiExec.exe (PID: 3708)
- MsiExec.exe (PID: 612)
- MsiExec.exe (PID: 3276)
- MsiExec.exe (PID: 2312)
- MsiExec.exe (PID: 2088)
- MsiExec.exe (PID: 932)
- MsiExec.exe (PID: 956)
- MsiExec.exe (PID: 3320)
- MsiExec.exe (PID: 2776)
- MsiExec.exe (PID: 908)
- MsiExec.exe (PID: 2156)
- MsiExec.exe (PID: 1452)
- MsiExec.exe (PID: 3972)
Creates files in the program directory
- MsiExec.exe (PID: 2300)
- MsiExec.exe (PID: 3540)
- MsiExec.exe (PID: 3276)
- MsiExec.exe (PID: 3320)
- MsiExec.exe (PID: 3708)
- MsiExec.exe (PID: 932)
- MsiExec.exe (PID: 2156)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:04 17:12:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 93184 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x167d2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.4.0.0 |
| ProductVersionNumber: | 16.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
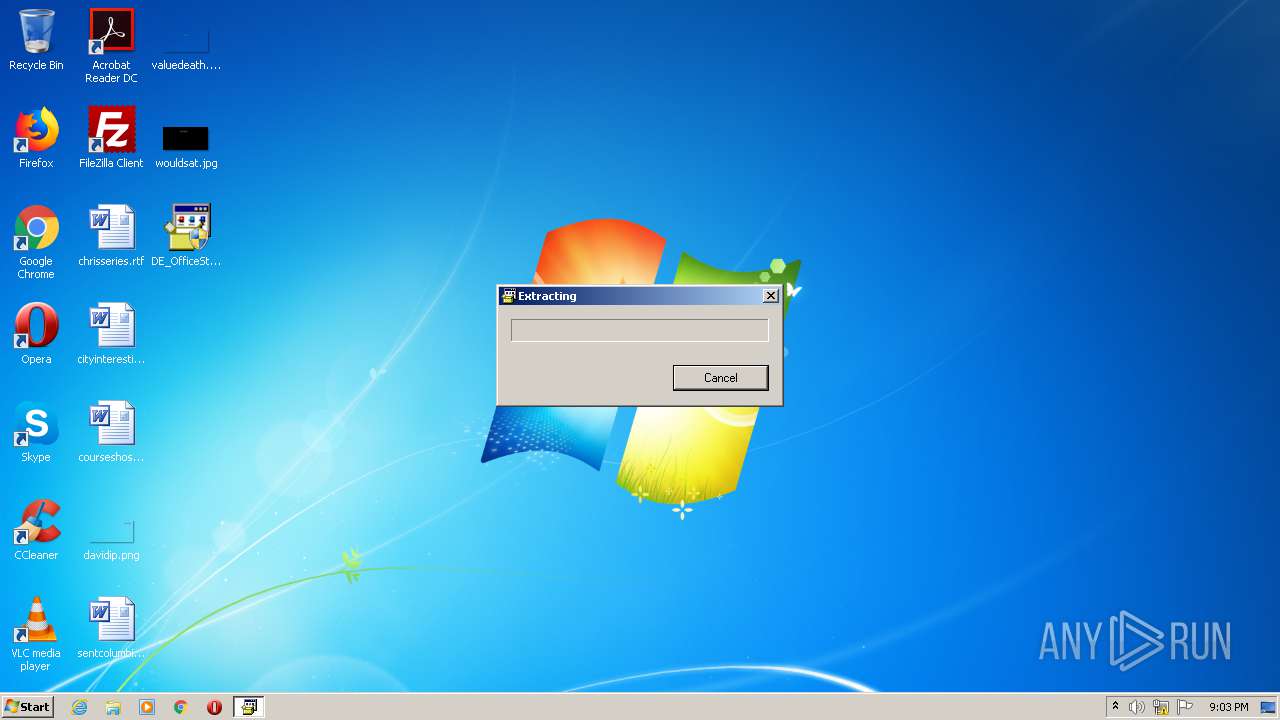
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Oct-2016 15:12:31 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Oct-2016 15:12:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00016BC5 | 0x00016C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63827 |
.rdata | 0x00018000 | 0x00003814 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23725 |
.data | 0x0001C000 | 0x00002430 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.87468 |
.sxdata | 0x0001F000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00020000 | 0x00000AB0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.331 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45504 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
97 | 3.04857 | 184 | UNKNOWN | English - United States | RT_DIALOG |
188 | 2.17822 | 84 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
68
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | C:\Windows\system32\MsiExec.exe -Embedding D96F49DE5DAEF73DC3E1514C44754232 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Common Files\Microsoft Shared\Source Engine\ose.exe" -standalone:temp | C:\Program Files\Common Files\Microsoft Shared\Source Engine\ose.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Office Source Engine Exit code: 0 Version: 14.0.4730.1010 Modules
| |||||||||||||||
| 908 | C:\Windows\system32\MsiExec.exe -Embedding 21B133DCA8E4D06CC1D0DB61AE0DDEB1 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | C:\Windows\system32\MsiExec.exe -Embedding 383CFDAB4EB63E0752ADA051DD31CCB9 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | C:\Windows\system32\MsiExec.exe -Embedding 5D6E56D700C20EE9ED0324302B094BA1 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | C:\Windows\system32\MsiExec.exe -Embedding 5B146685E9122113AFA2463155EA33C5 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\Desktop\DE_OfficeStandard2019_VL_64_BIT.exe" | C:\Users\admin\Desktop\DE_OfficeStandard2019_VL_64_BIT.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 2072 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\MsiExec.exe -Embedding 81D5228670967E590324ED580357C002 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 536
Read events
1 571
Write events
449
Delete events
2 516
Modification events
| (PID) Process: | (2068) DE_OfficeStandard2019_VL_64_BIT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2068) DE_OfficeStandard2019_VL_64_BIT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | FirstSessionTriggered |
Value: 1 | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | UIFallbackLanguages |
Value: x-none | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | HelpLanguageTag |
Value: en-US | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreviousPreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordMailChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (3224) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | XLChangeInstallLanguage |
Value: No | |||
Executable files
100
Suspicious files
131
Text files
135
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1916 | DllHost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSI9F04.tmp | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIA2CD.tmp | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA36284C15B5C32B3.TMP | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIA32D.tmp | — | |
MD5:— | SHA256:— | |||
| 2072 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIA542.tmp | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIA63D.tmp | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIABED.tmp | — | |
MD5:— | SHA256:— | |||
| 3724 | msiexec.exe | C:\Windows\Installer\MSIACE8.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | setup.exe | 13.107.5.88:443 | client-office365-tas.msedge.net | Microsoft Corporation | US | whitelisted |
3224 | setup.exe | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client-office365-tas.msedge.net |
| whitelisted |
config.edge.skype.com |
| malicious |
Threats
Process | Message |
|---|---|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1391
|
msiexec.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 278
|