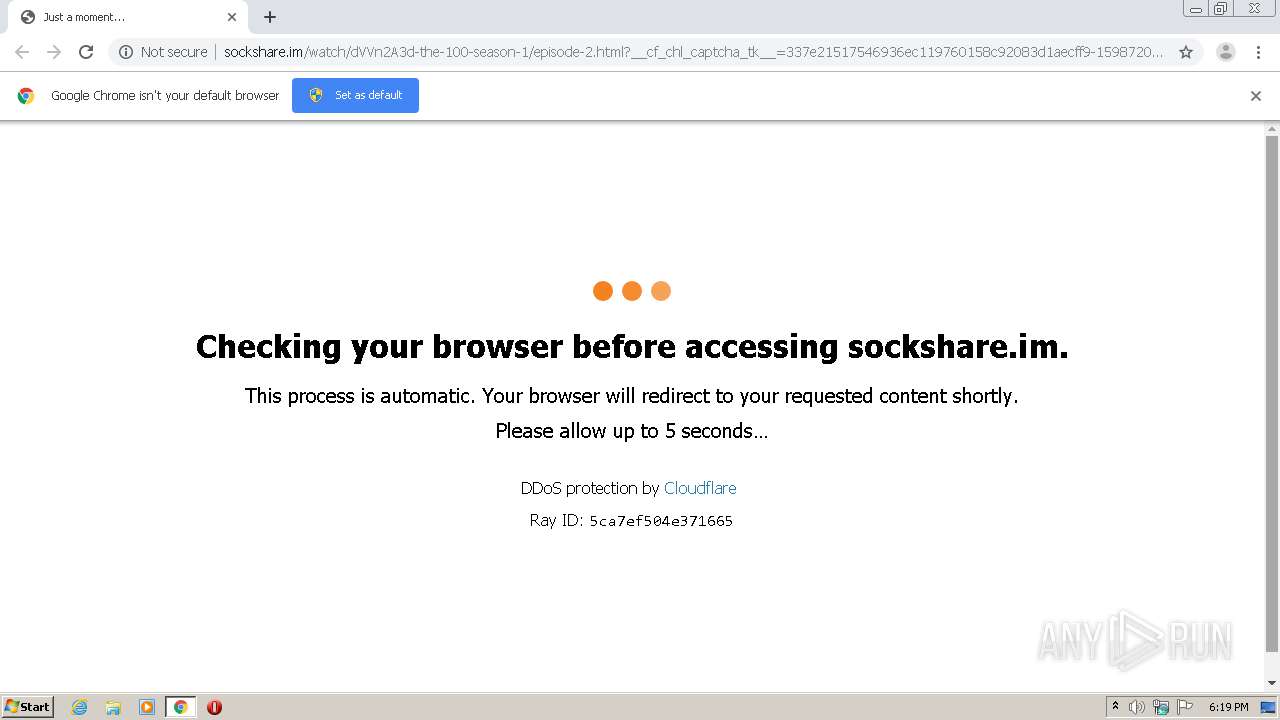
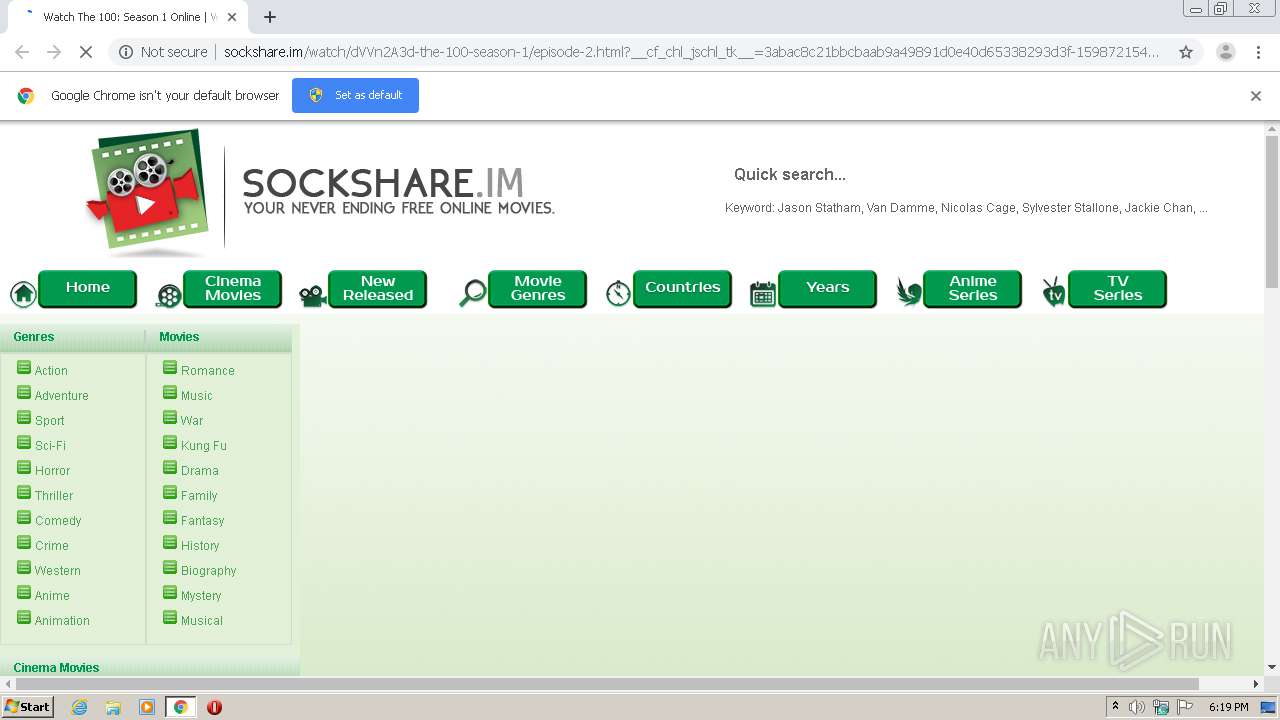
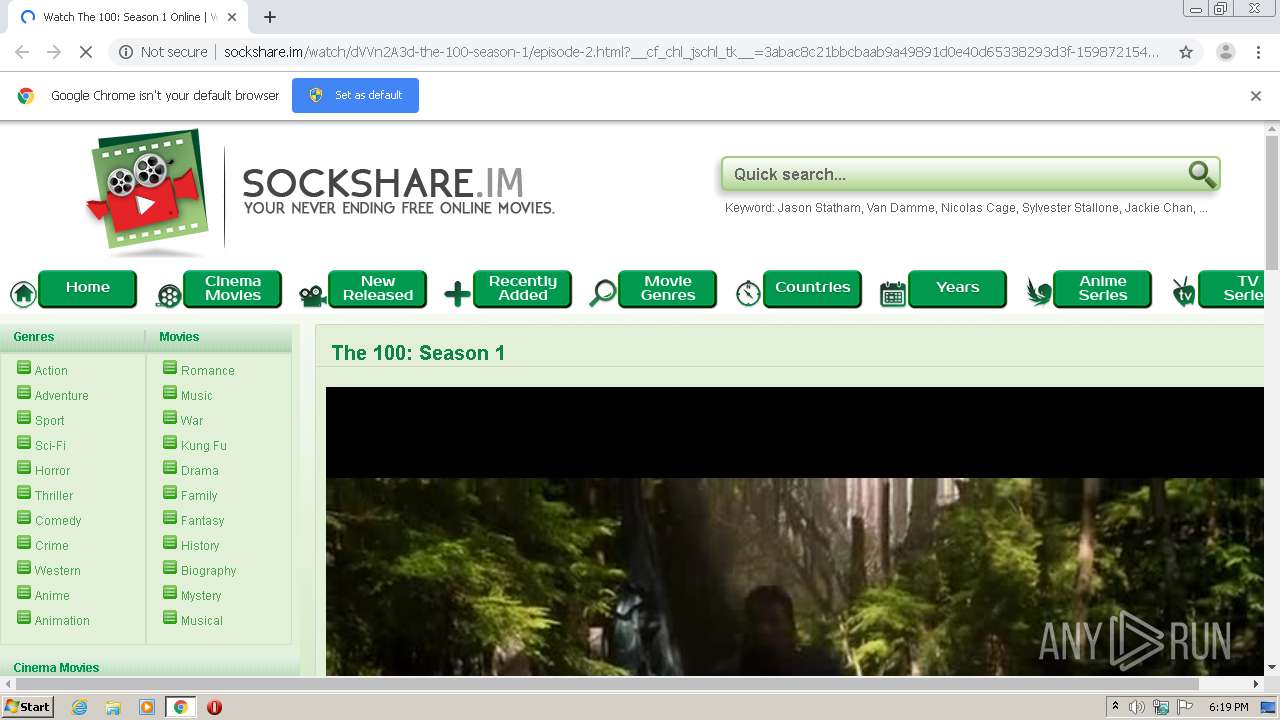
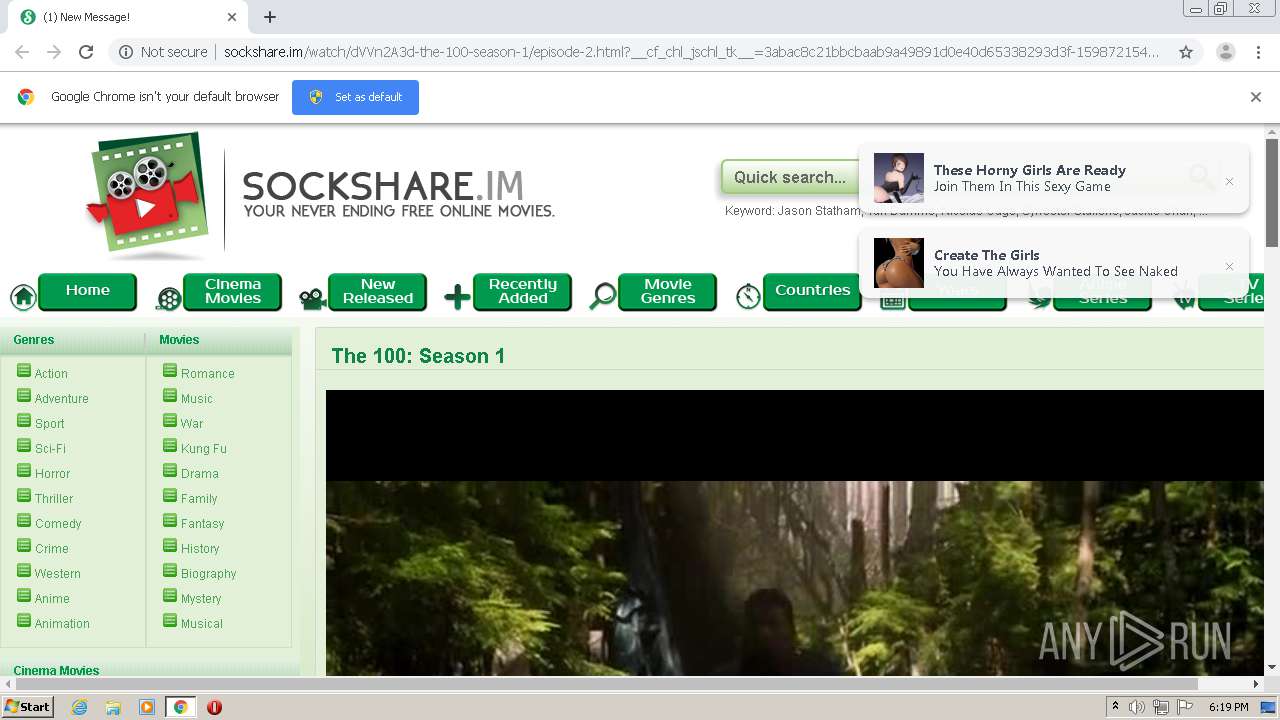
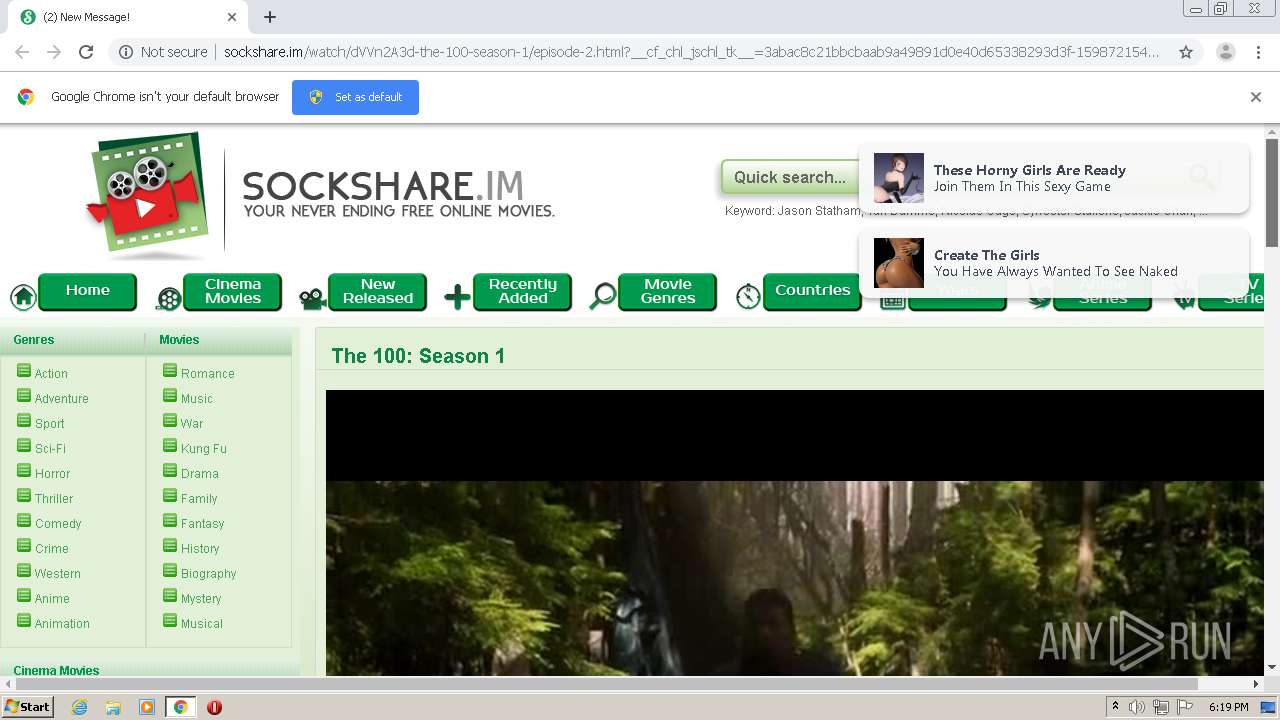
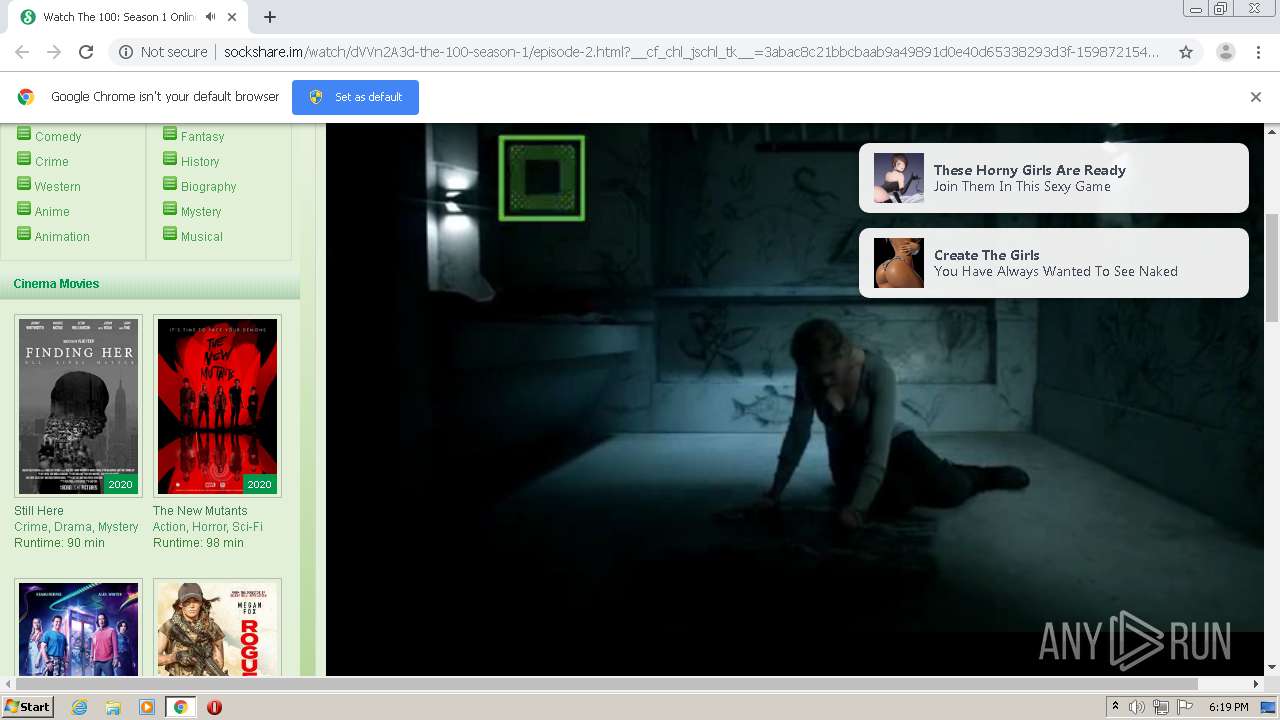
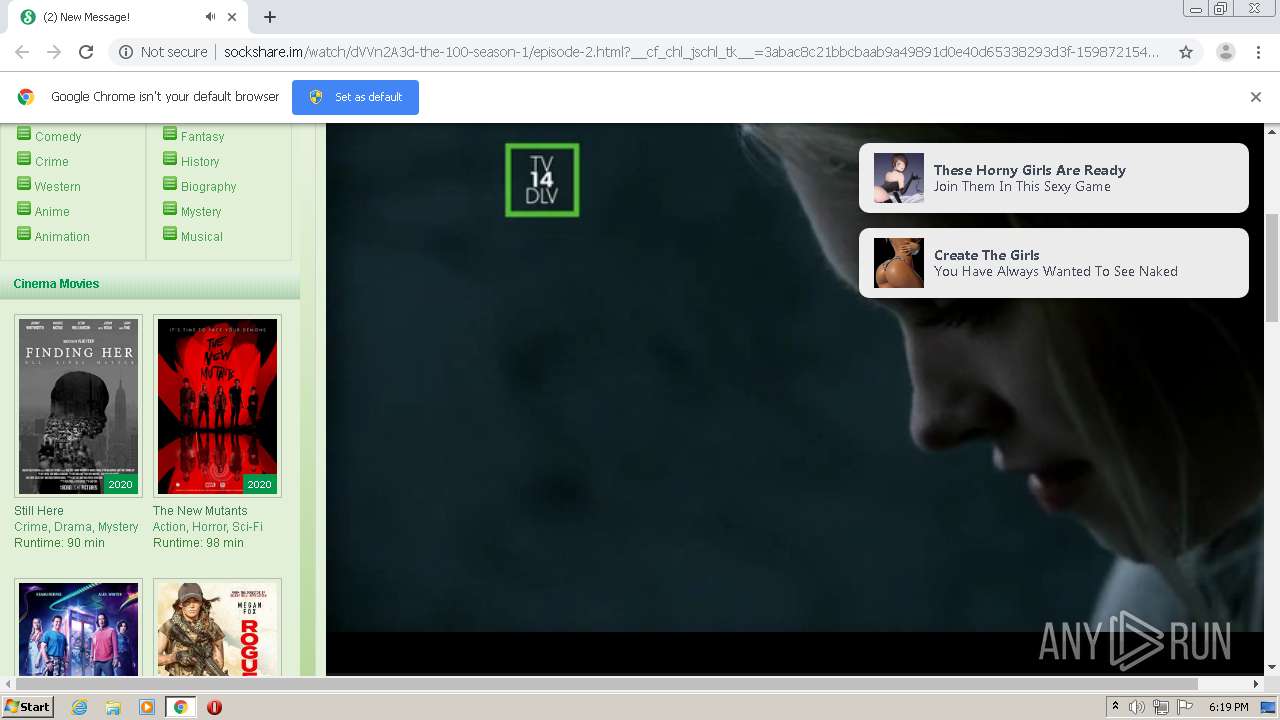
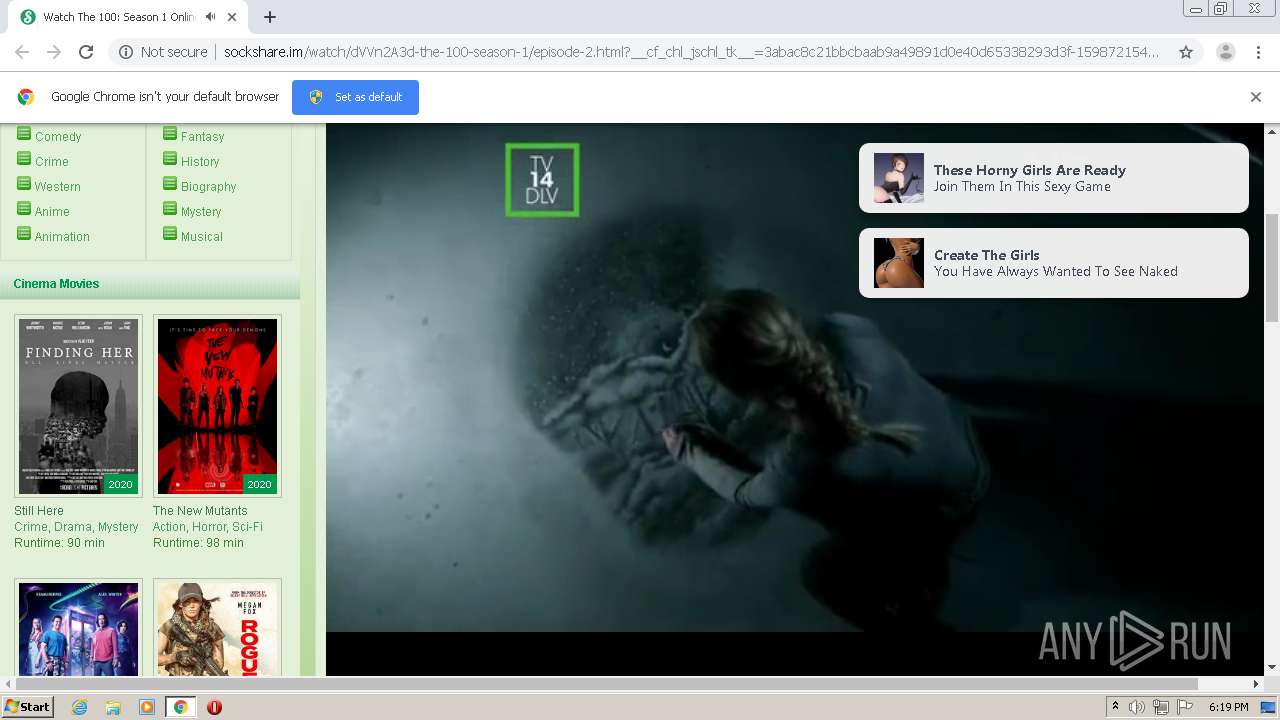
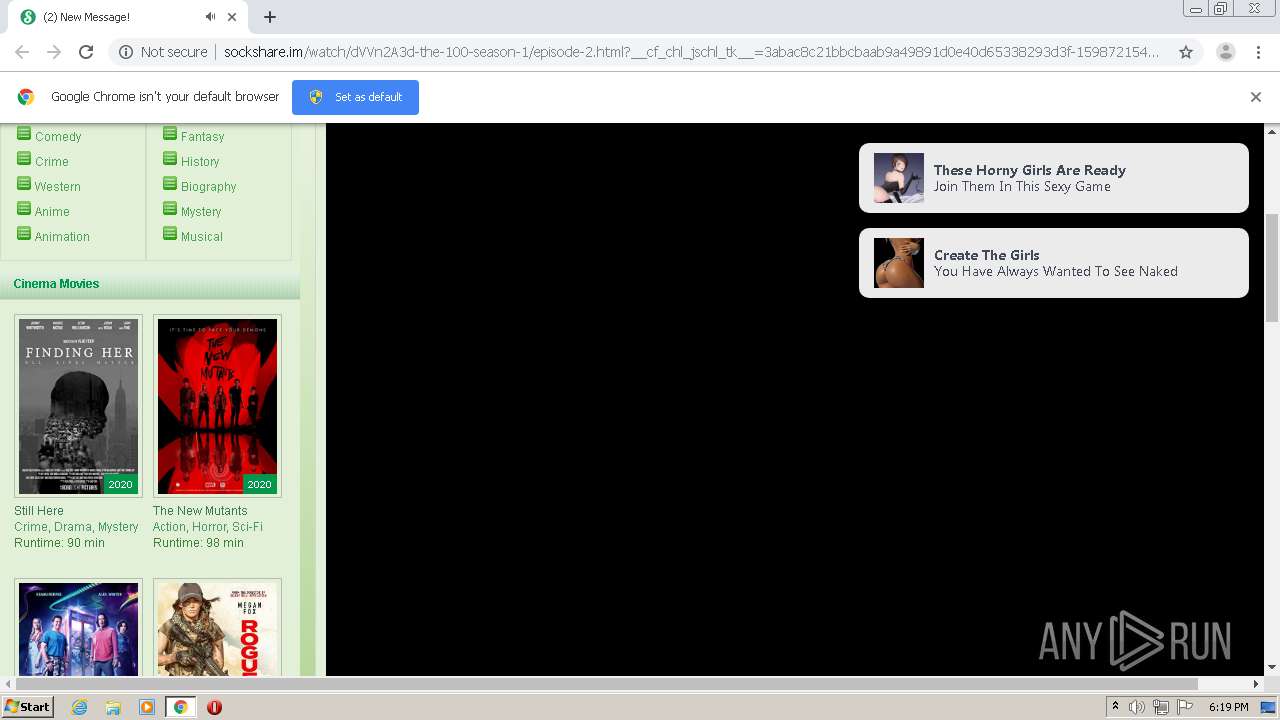
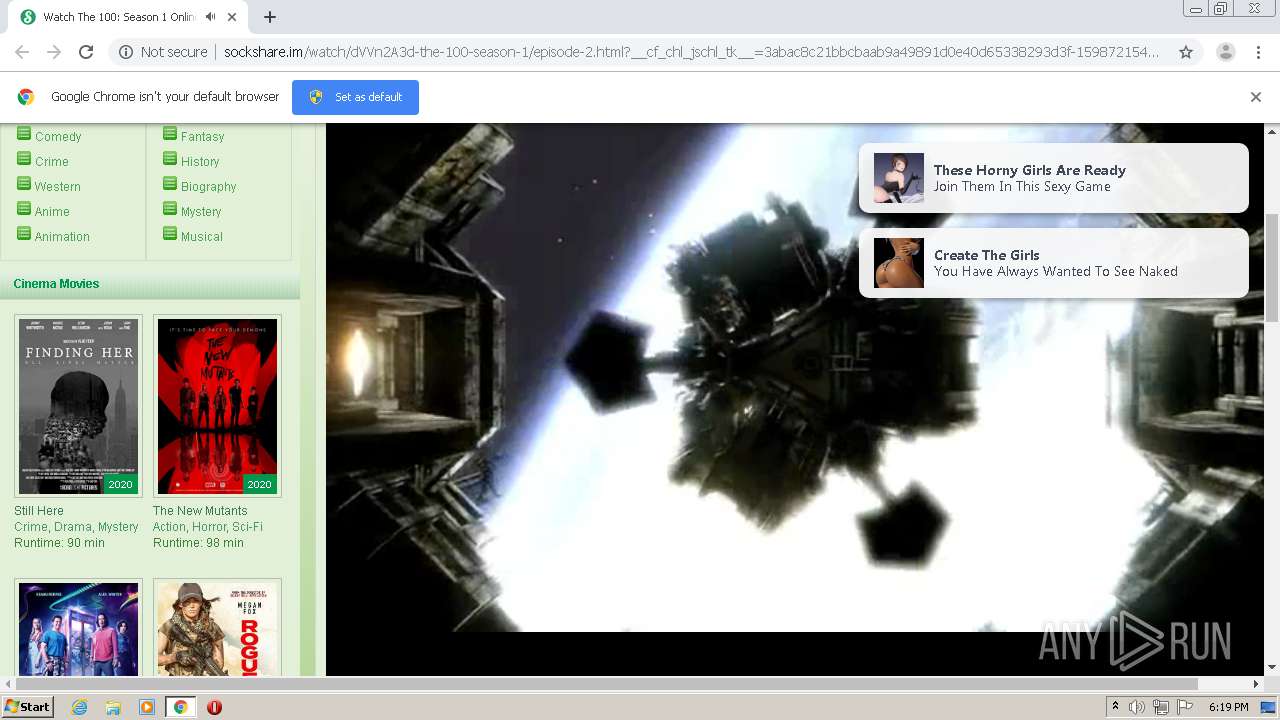
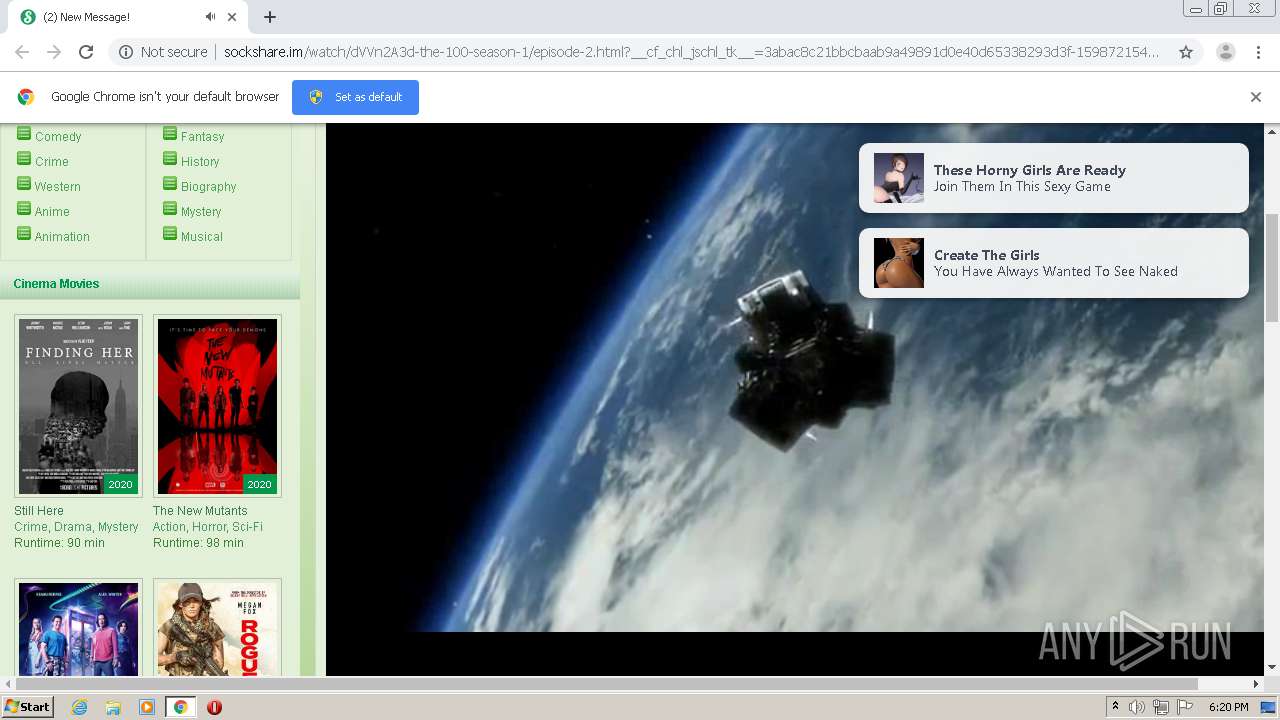
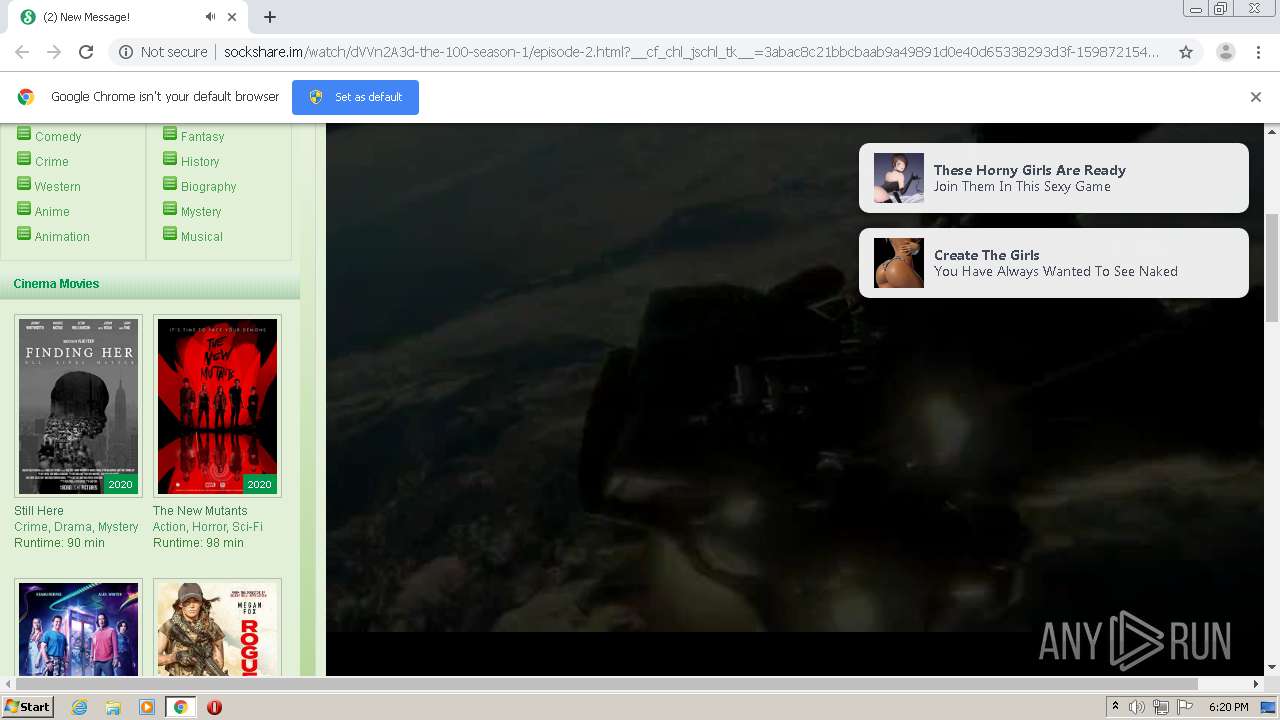
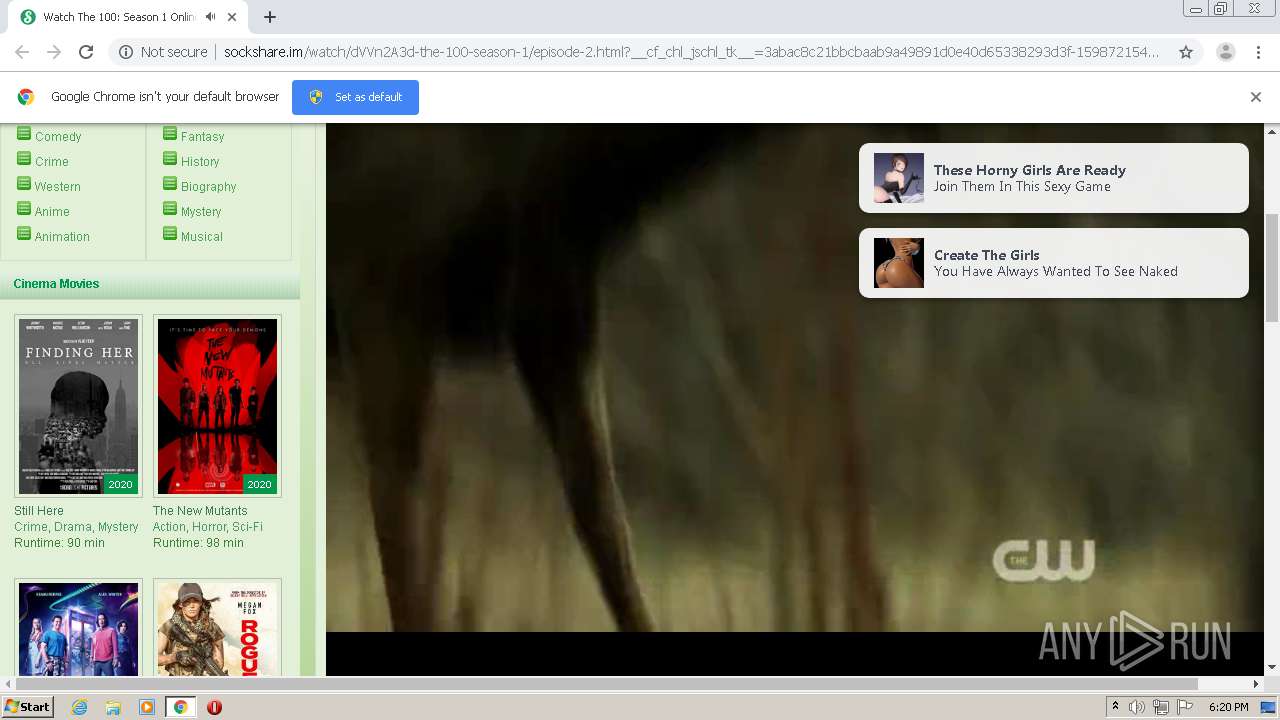
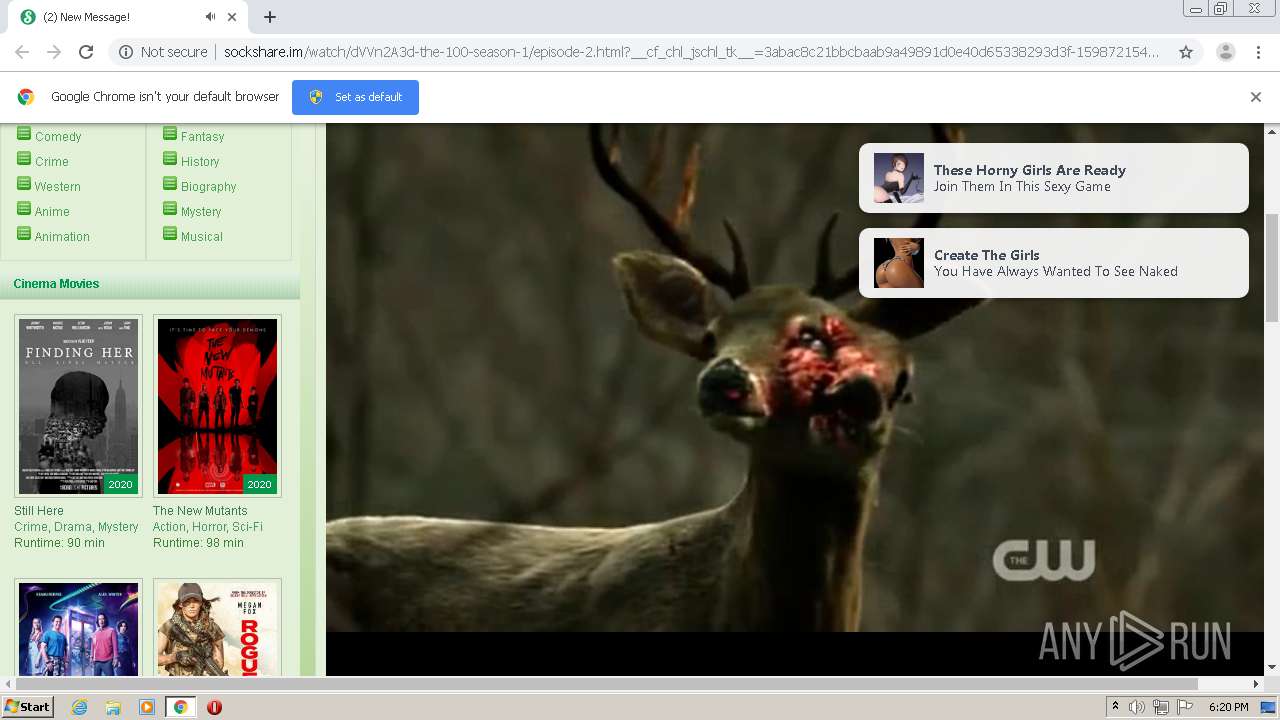
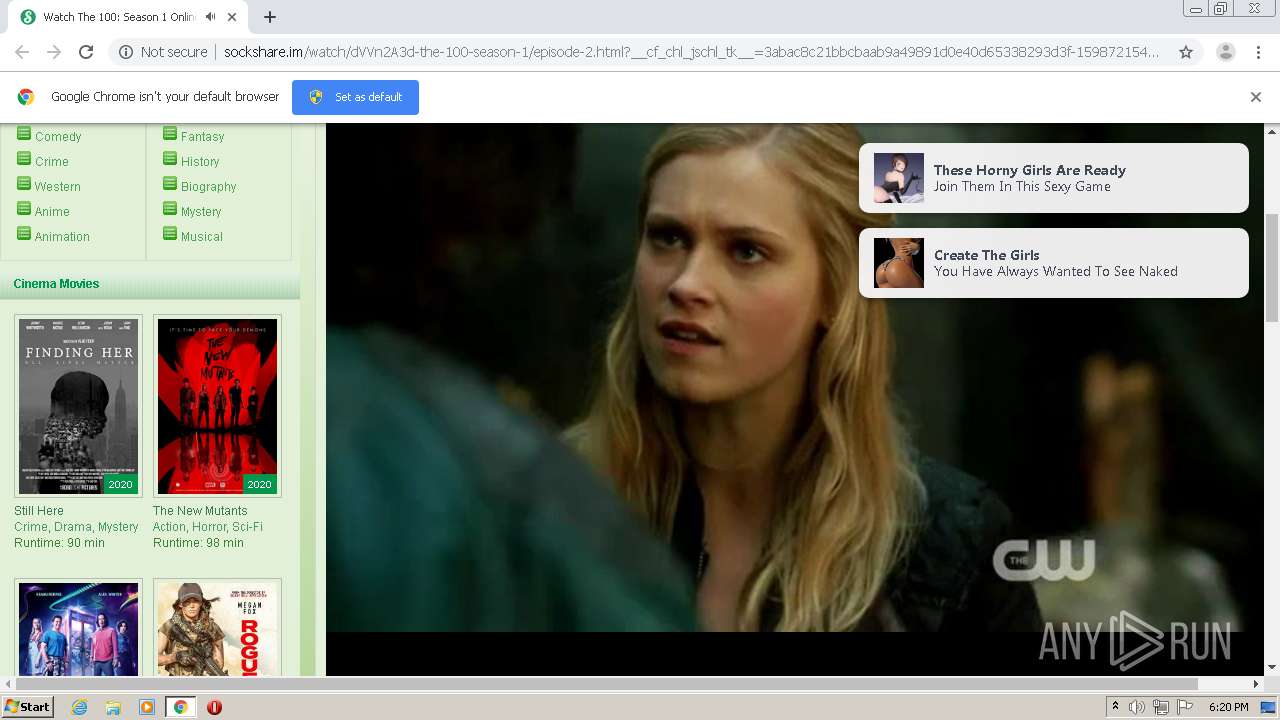
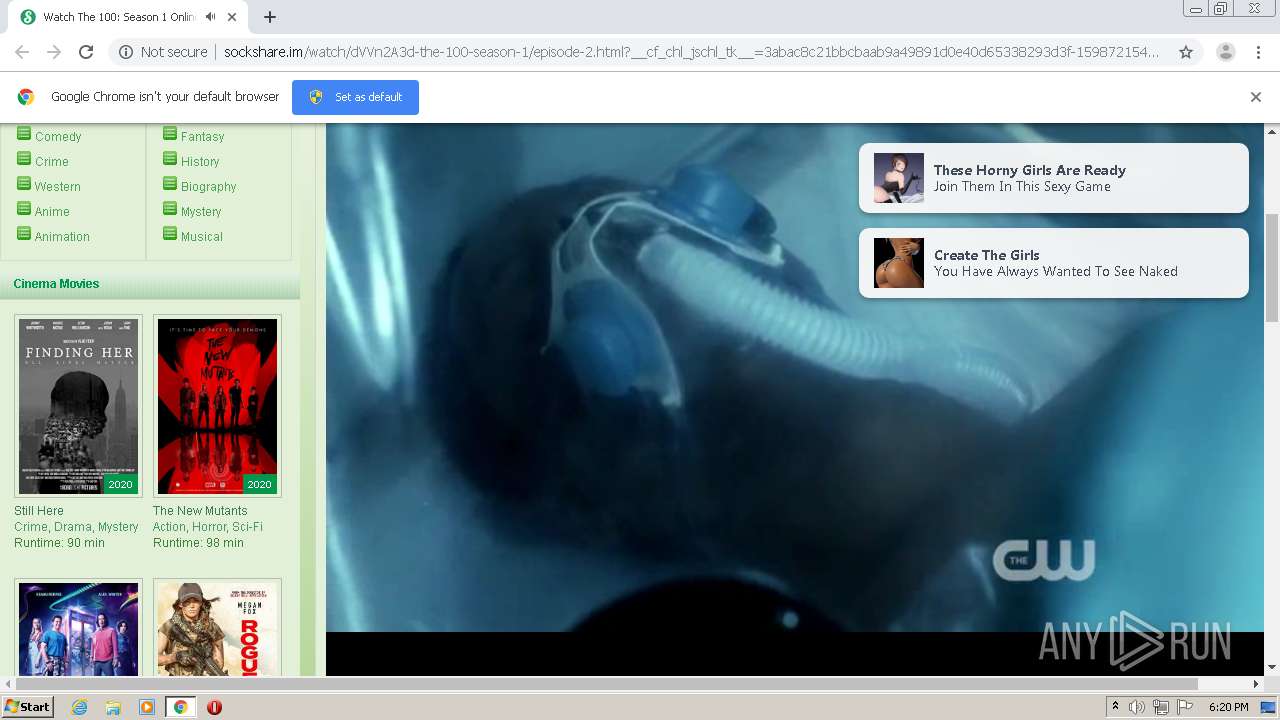
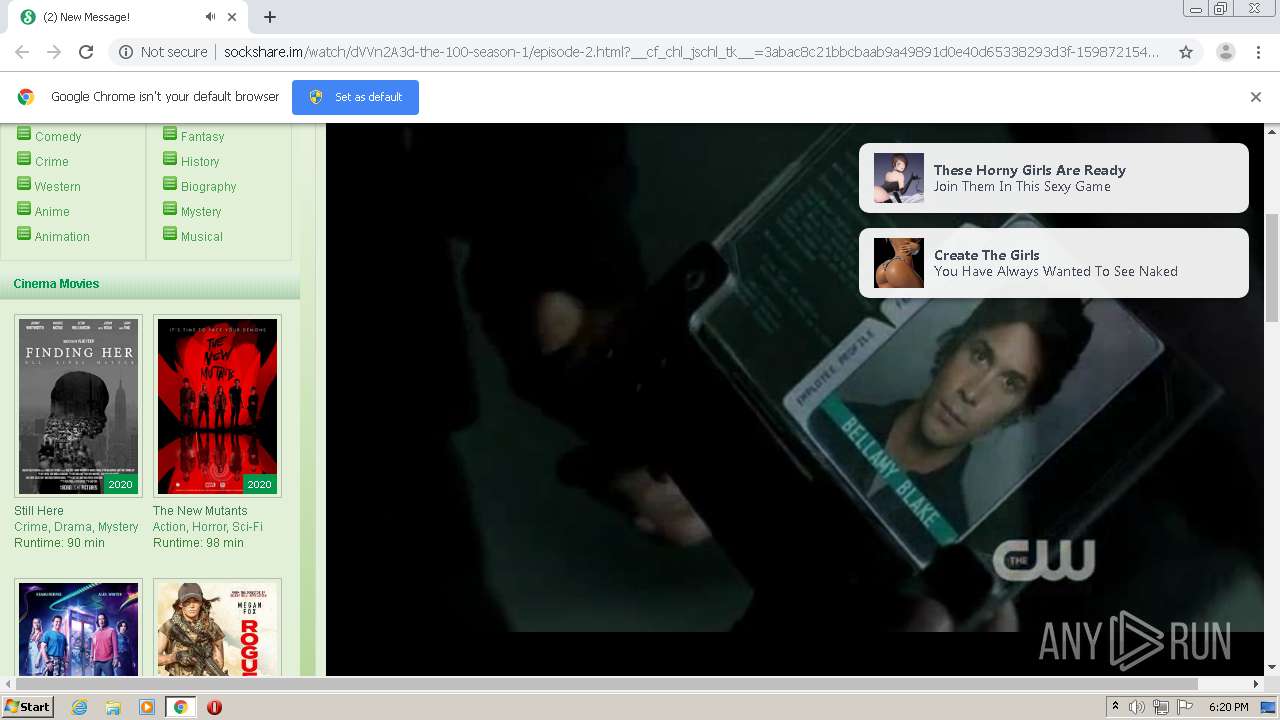
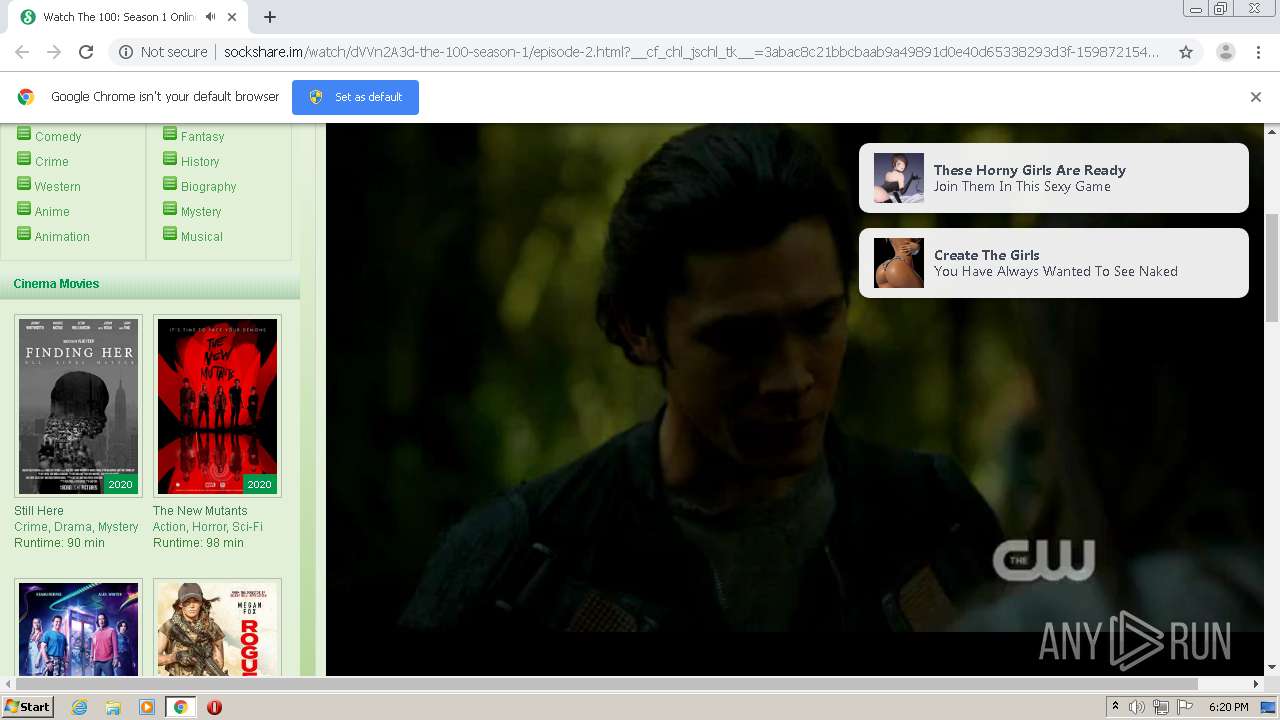
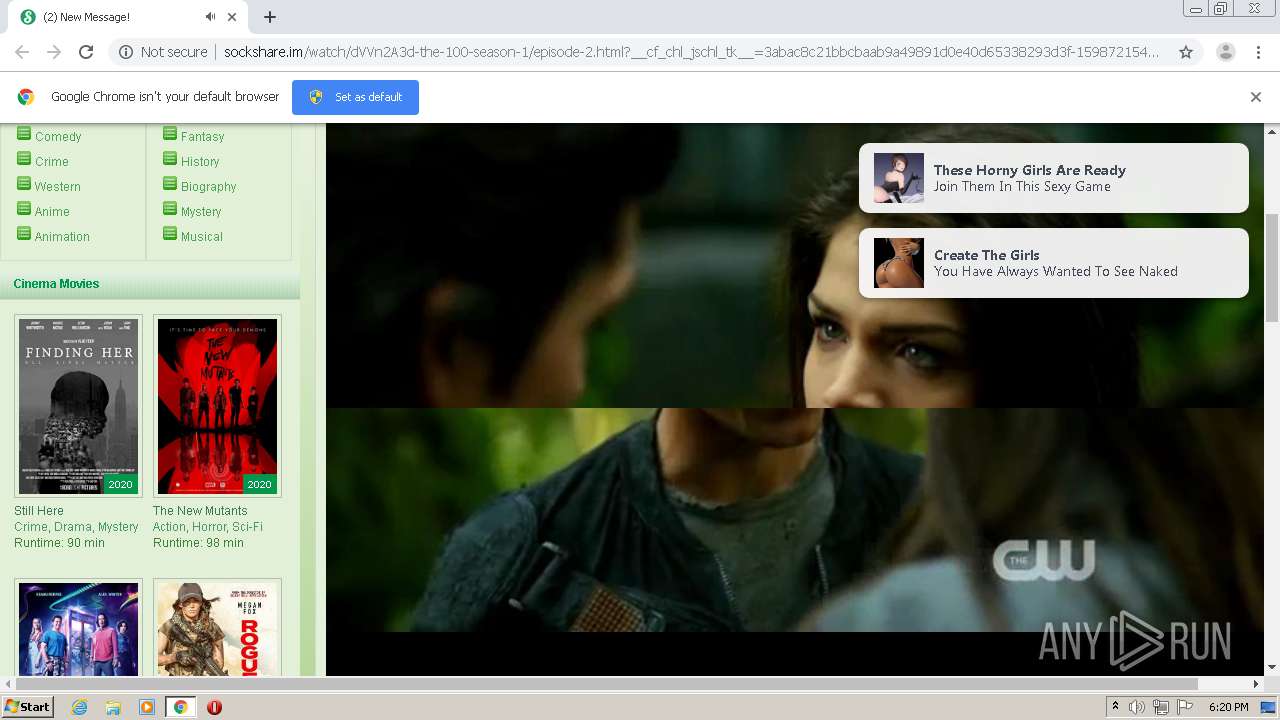
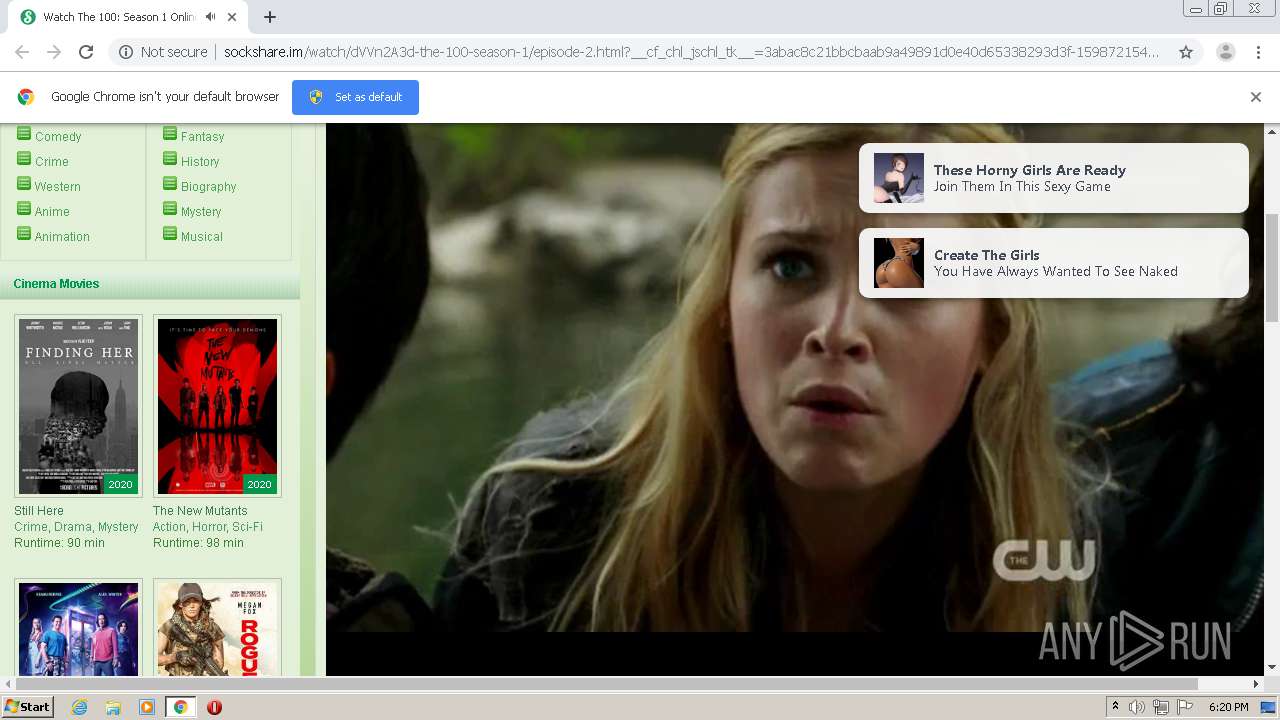
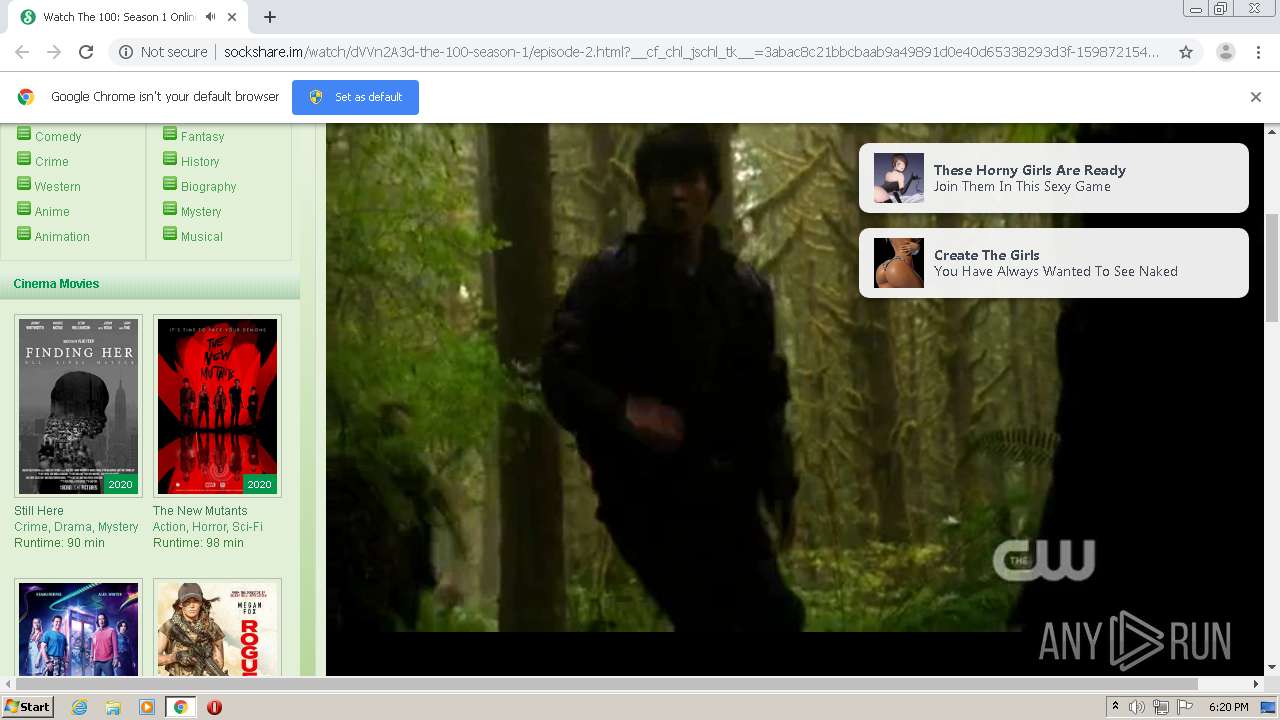
| URL: | http://sockshare.im/watch/dVVn2A3d-the-100-season-1/episode-2.html?__cf_chl_captcha_tk__=337e21517546936ec119760158c92083d1aecff9-1598720491-0-AZaATjvtT0OO-10aQKvQlXjD0N3-prL8QQFBCUfFnCQk3dB_24h-sAb1K4Z0qpqrIHqvhRPrINA9i3LmAChzb6nwRgs6Evw6DqH0D5nhyfwtJHxB8jbkyoklVEtchWmtvNK7Uh8zqLT_N6B3s8xX83YJ8_jIaa4xvRHOlRuk3hf3mAYNthLndcYO5cNve3w3Ka6kTtlPlK0U0PpVtHh8Wy7PXBzS35S_W-6A_spZ1eJMHqusbho8YzzK4G8y07USKCq1JOC1-xw7XoT7LuYvlC8EFzJQ1VrZuVTQnckJFwdDis1QAx8r8EOWD_903zPZ_wjdmpqoKrI_KeIKy3UgxrMj61Axhr7Hje7KyM_o0WOGAW8n3f5QlcP7Ki9Ak90BMI3q7enY13p_Use6SX9ciCAWmyD5w4kTekAtjkby8cpFOaDg2ilvbDh3t7JWJNKoRhQLbsb4VcrGF1WsVc4PounWO7SAirILnYFSWmyy3EYOx6W5gWn6S0W7_iZ93wjG_Mp_wJ--fh_ZqERRyOlCz9yy3QeY3KUql2svY0Zpzz5F |
| Full analysis: | https://app.any.run/tasks/a0640d63-b3f0-408e-91c8-288fae3791d4 |
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2020, 17:18:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A26706E727E7475023CE94944E28EB26 |
| SHA1: | 50D4467FE374896A69A7787AA7A11212A7BA3CA4 |
| SHA256: | 8CB4A46496BC2B2EFF78AD29BFD979CFBD476A2C4D30C1A864E0EE90366E5A21 |
| SSDEEP: | 12:TbpDiNPB3J/bj4cmCPuqIoqJyZM2KikhzAreH6b5B8Va8W0qt1fsuN:hmPrz9mGIoqJBmGAqH6b3oagqt1t |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1388)
Reads the hosts file
- chrome.exe (PID: 1388)
- chrome.exe (PID: 3800)
Creates files in the user directory
- chrome.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x71c4a9d0,0x71c4a9e0,0x71c4a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10800538486439485659 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7738050913898087090 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://sockshare.im/watch/dVVn2A3d-the-100-season-1/episode-2.html?__cf_chl_captcha_tk__=337e21517546936ec119760158c92083d1aecff9-1598720491-0-AZaATjvtT0OO-10aQKvQlXjD0N3-prL8QQFBCUfFnCQk3dB_24h-sAb1K4Z0qpqrIHqvhRPrINA9i3LmAChzb6nwRgs6Evw6DqH0D5nhyfwtJHxB8jbkyoklVEtchWmtvNK7Uh8zqLT_N6B3s8xX83YJ8_jIaa4xvRHOlRuk3hf3mAYNthLndcYO5cNve3w3Ka6kTtlPlK0U0PpVtHh8Wy7PXBzS35S_W-6A_spZ1eJMHqusbho8YzzK4G8y07USKCq1JOC1-xw7XoT7LuYvlC8EFzJQ1VrZuVTQnckJFwdDis1QAx8r8EOWD_903zPZ_wjdmpqoKrI_KeIKy3UgxrMj61Axhr7Hje7KyM_o0WOGAW8n3f5QlcP7Ki9Ak90BMI3q7enY13p_Use6SX9ciCAWmyD5w4kTekAtjkby8cpFOaDg2ilvbDh3t7JWJNKoRhQLbsb4VcrGF1WsVc4PounWO7SAirILnYFSWmyy3EYOx6W5gWn6S0W7_iZ93wjG_Mp_wJ--fh_ZqERRyOlCz9yy3QeY3KUql2svY0Zpzz5F" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7697900332890483878 --mojo-platform-channel-handle=3520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17342409865305098688 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12907089812231771718 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3362778001439599008 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12921905211837221779 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13206164202152080163,5403815055457893323,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14635874076684743274 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
648
Read events
561
Write events
83
Delete events
4
Modification events
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1388-13243195141811375 |
Value: 259 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
41
Text files
95
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe6405.TMP | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe6405.TMP | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\af63b89b-0a85-4791-9ae7-3304091b0ff2.tmp | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe65f9.TMP | — | |
MD5:— | SHA256:— | |||
| 1388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe6415.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
66
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3800 | chrome.exe | GET | — | 104.18.37.127:80 | http://sockshare.im/watch/dVVn2A3d-the-100-season-1/episode-2.html?__cf_chl_captcha_tk__=337e21517546936ec119760158c92083d1aecff9-1598720491-0-AZaATjvtT0OO-10aQKvQlXjD0N3-prL8QQFBCUfFnCQk3dB_24h-sAb1K4Z0qpqrIHqvhRPrINA9i3LmAChzb6nwRgs6Evw6DqH0D5nhyfwtJHxB8jbkyoklVEtchWmtvNK7Uh8zqLT_N6B3s8xX83YJ8_jIaa4xvRHOlRuk3hf3mAYNthLndcYO5cNve3w3Ka6kTtlPlK0U0PpVtHh8Wy7PXBzS35S_W-6A_spZ1eJMHqusbho8YzzK4G8y07USKCq1JOC1-xw7XoT7LuYvlC8EFzJQ1VrZuVTQnckJFwdDis1QAx8r8EOWD_903zPZ_wjdmpqoKrI_KeIKy3UgxrMj61Axhr7Hje7KyM_o0WOGAW8n3f5QlcP7Ki9Ak90BMI3q7enY13p_Use6SX9ciCAWmyD5w4kTekAtjkby8cpFOaDg2ilvbDh3t7JWJNKoRhQLbsb4VcrGF1WsVc4PounWO7SAirILnYFSWmyy3EYOx6W5gWn6S0W7_iZ93wjG_Mp_wJ--fh_ZqERRyOlCz9yy3QeY3KUql2svY0Zpzz5F | US | — | — | malicious |
3800 | chrome.exe | GET | 200 | 104.18.37.127:80 | http://sockshare.im/cdn-cgi/challenge-platform/orchestrate/jsch/v1 | US | text | 11.4 Kb | malicious |
3800 | chrome.exe | POST | 200 | 104.18.37.127:80 | http://sockshare.im/cdn-cgi/challenge-platform/generate/ov1/0.6934934869520241:1598720945:185ac1baecef21ed10536cfa32e4d66a9656e3e5a29e05fdf353995c3bb3b719/5ca7ef504e371665/e5685e829acc49a | US | binary | 6.06 Kb | malicious |
3800 | chrome.exe | POST | 200 | 104.18.37.127:80 | http://sockshare.im/cdn-cgi/challenge-platform/generate/ov1/0.6934934869520241:1598720945:185ac1baecef21ed10536cfa32e4d66a9656e3e5a29e05fdf353995c3bb3b719/5ca7ef504e371665/e5685e829acc49a | US | binary | 1.01 Kb | malicious |
3800 | chrome.exe | GET | 404 | 104.18.37.127:80 | http://sockshare.im/favicon.ico | US | html | 2.25 Kb | malicious |
3800 | chrome.exe | GET | 200 | 104.18.37.127:80 | http://sockshare.im/js/base64.js | US | text | 900 b | malicious |
3800 | chrome.exe | GET | 200 | 104.18.37.127:80 | http://sockshare.im/themes/movies/style.css | US | text | 4.48 Kb | malicious |
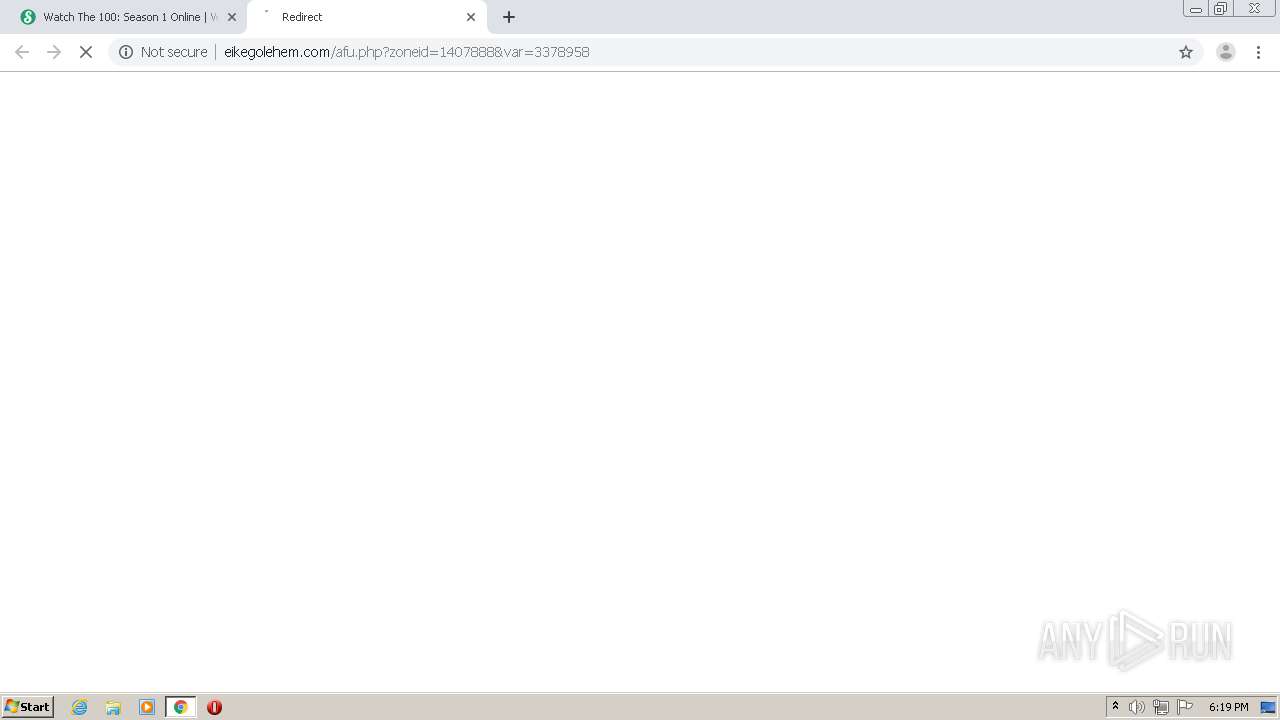
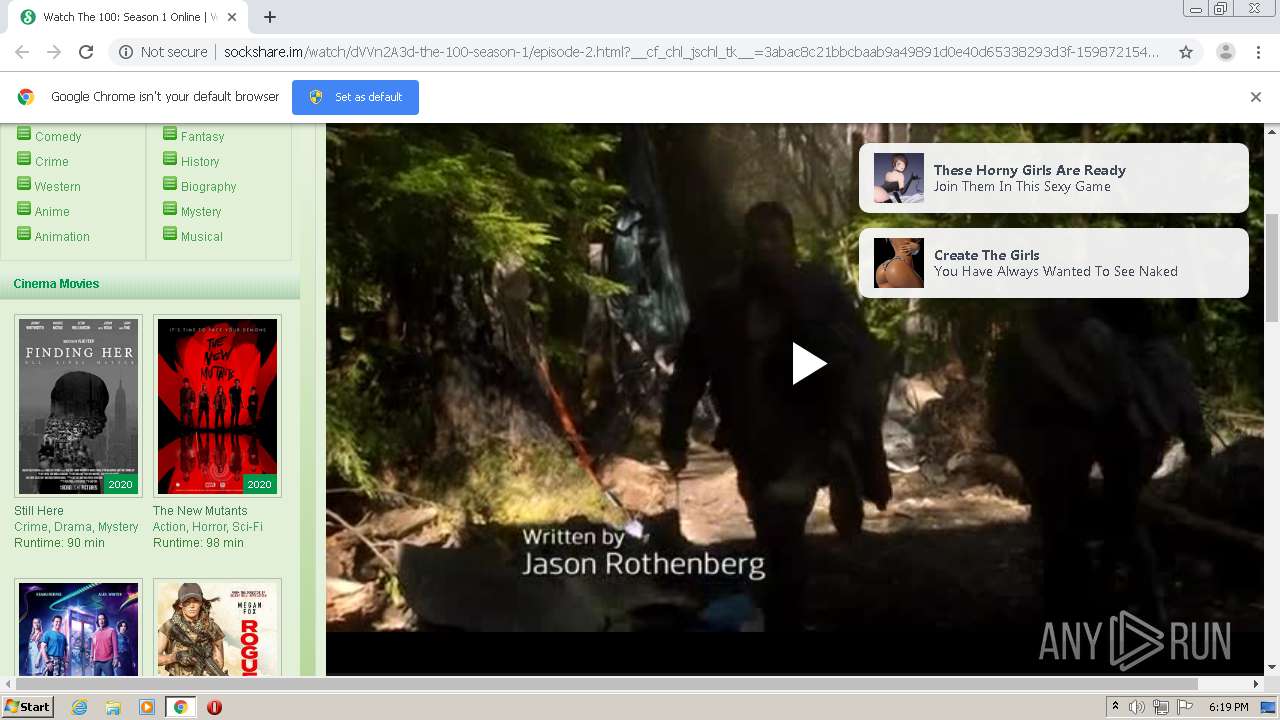
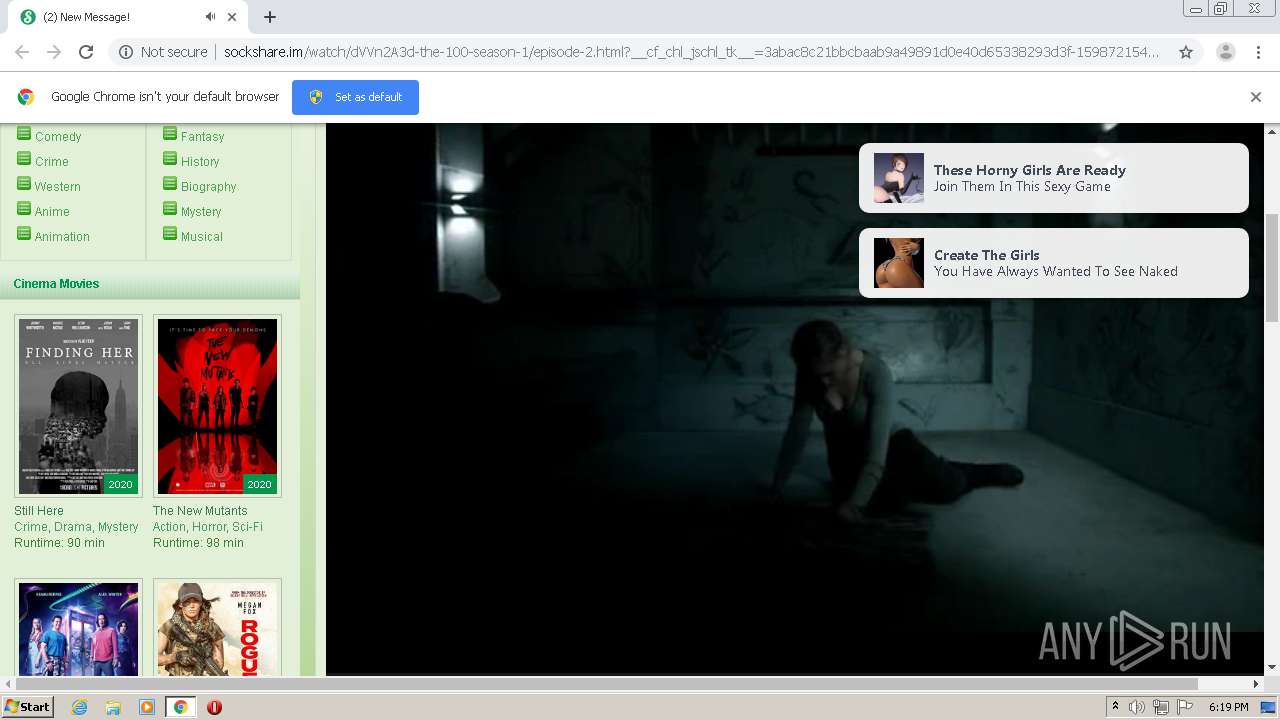
3800 | chrome.exe | POST | 200 | 104.18.37.127:80 | http://sockshare.im/watch/dVVn2A3d-the-100-season-1/episode-2.html?__cf_chl_jschl_tk__=3abac8c21bbcbaab9a49891d0e40d65338293d3f-1598721543-0-ARY-89G4UNwy3TaEXCCc0zptVMrirUD2smwyB1LN_dHWihXYrzFceVQBhzRZNTbgs84dOBtoTHnp6WHaf2JK2SQkLYagItM8_J9TWEfka_9wC7fjknNq5a2fqu_0CeMF4Tvzm_KYqXRc7Ahe7UCuN-1xCDOUX2SblhEgWri0t5Bps_vzheBP_i1dLrOqs_aV8UMztMY8TSsuuws3VjY9xAXFt_0eUrGsFTJgSlWRnxgJ7iMN4aK-V7hPF3nm5ccRnlOdomWT5b-6qbQXGVSP7V-IZa4azI2nBikIvSLkQCbFgi5E62qKykJrCWozCB195x_5oiiGHLmN8mqMEkCVHdg | US | html | 42.9 Kb | malicious |
3800 | chrome.exe | GET | 200 | 104.18.37.127:80 | http://sockshare.im/themes/movies/img/button/Home.png | US | image | 6.19 Kb | malicious |
3800 | chrome.exe | GET | 200 | 104.18.37.127:80 | http://sockshare.im/js/load.js | US | text | 2.78 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3800 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.18.37.127:80 | sockshare.im | Cloudflare Inc | US | shared |
3800 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 104.18.37.127:80 | sockshare.im | Cloudflare Inc | US | shared |
3800 | chrome.exe | 172.217.23.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 104.18.36.127:80 | sockshare.im | Cloudflare Inc | US | shared |
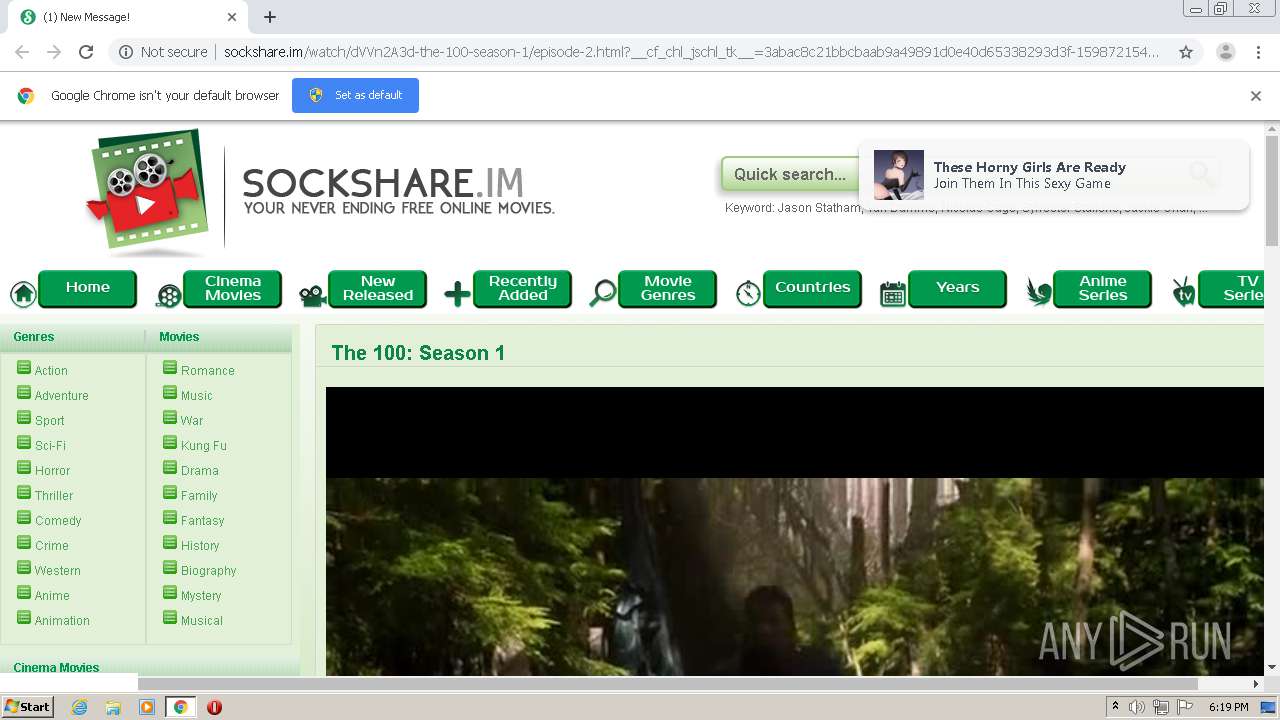
3800 | chrome.exe | 192.243.59.13:80 | cyih0e43aty7.com | DataWeb Global Group B.V. | US | malicious |
3800 | chrome.exe | 104.27.188.128:80 | eplayvid.com | Cloudflare Inc | US | unknown |
3800 | chrome.exe | 85.217.223.40:80 | — | Natskovi & Sie Ltd. | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sockshare.im |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
macinline.com |
| malicious |
www.cloudflare.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
cdn.sockshare.im |
| malicious |
cyih0e43aty7.com |
| malicious |
eplayvid.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3800 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |