| File name: | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35 |
| Full analysis: | https://app.any.run/tasks/0a4efe58-40f9-4af7-b3e6-4017677943b2 |
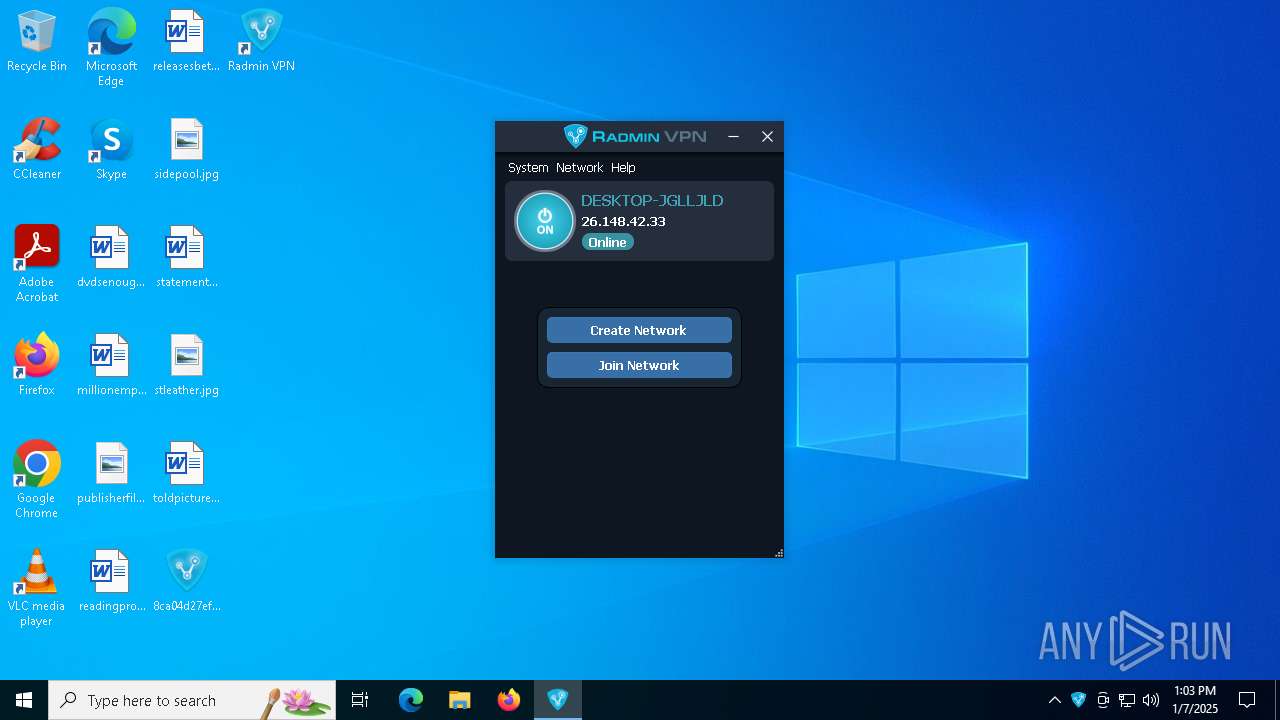
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2025, 13:03:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 5D8706970DD725471DCBC5ACB4DBDDCE |
| SHA1: | C86DAD0644FE6B38351FE16ADD60B12444E23FD0 |
| SHA256: | 8CA04D27EF8C28E0EDAC3B740EBE7FB8839B4794752A0D359AE18DE22FC6BE35 |
| SSDEEP: | 98304:gmkUbQN6ipwTcvc2k9Fjuui/celwR0gk4K7UMZhYAXpFGCC2aRPhmfdrMhk9mi8l:DBC88/9byzjupZzihQS6jlVlIxTRwYT |
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 6920)
SUSPICIOUS
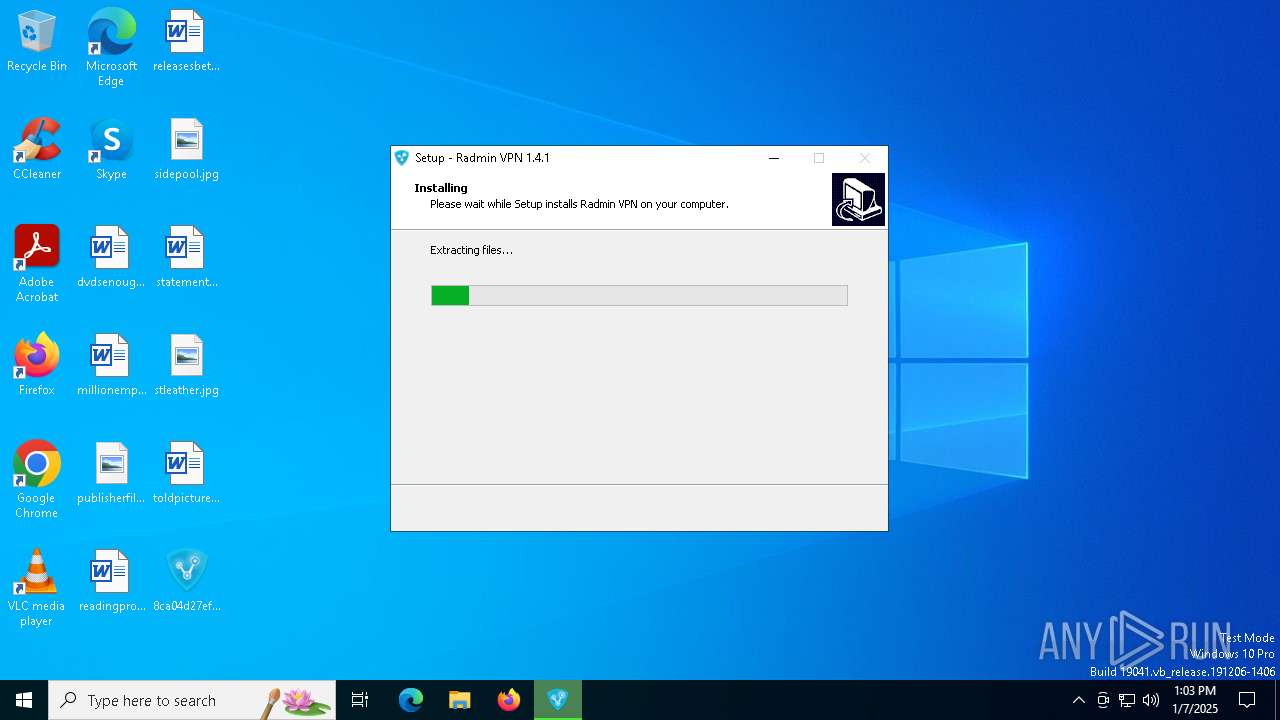
Executable content was dropped or overwritten
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6348)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6576)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- drvinst.exe (PID: 6200)
- drvinst.exe (PID: 4308)
Reads security settings of Internet Explorer
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6372)
Reads the Windows owner or organization settings
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- msiexec.exe (PID: 6920)
Process drops legitimate windows executable
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- msiexec.exe (PID: 6920)
Checks Windows Trust Settings
- msiexec.exe (PID: 6920)
- drvinst.exe (PID: 6200)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6920)
The process drops C-runtime libraries
- msiexec.exe (PID: 6920)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6920)
- drvinst.exe (PID: 6200)
- drvinst.exe (PID: 4308)
Creates files in the driver directory
- drvinst.exe (PID: 6200)
- MSIAD4B.tmp (PID: 6220)
- drvinst.exe (PID: 4308)
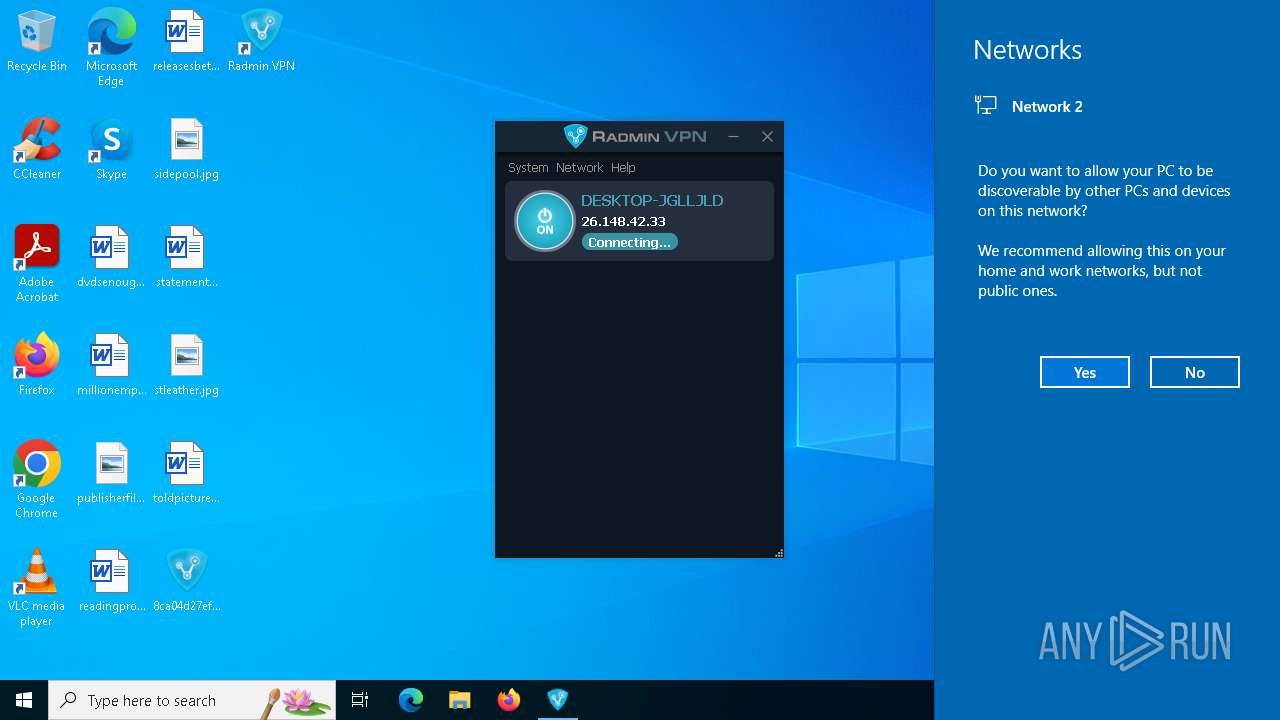
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 3724)
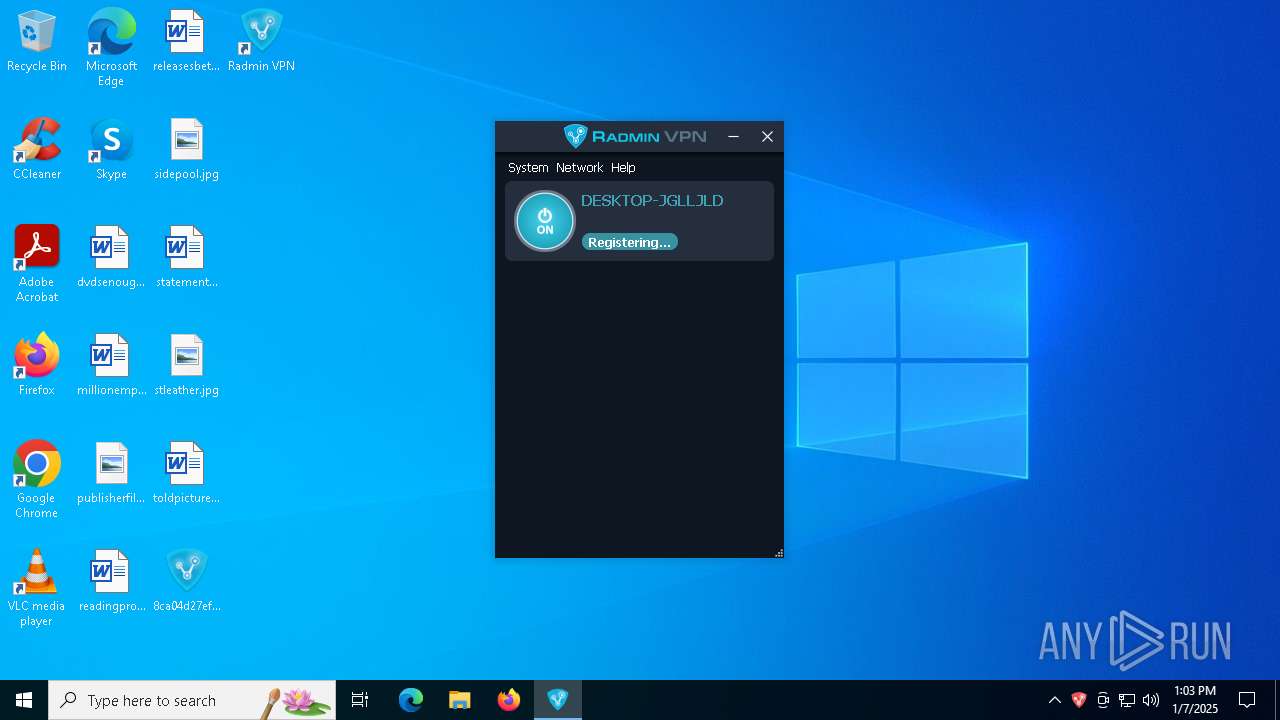
Executes as Windows Service
- RvControlSvc.exe (PID: 4556)
Creates or modifies Windows services
- drvinst.exe (PID: 4308)
Starts CMD.EXE for commands execution
- RvControlSvc.exe (PID: 4556)
Connects to unusual port
- RvControlSvc.exe (PID: 4556)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5964)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 6732)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 7004)
There is functionality for taking screenshot (YARA)
- RvRvpnGui.exe (PID: 2996)
INFO
Checks supported languages
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6348)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6372)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6576)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- msiexec.exe (PID: 6920)
- msiexec.exe (PID: 7144)
- MSIAD4B.tmp (PID: 6220)
- drvinst.exe (PID: 6200)
- msiexec.exe (PID: 3724)
- drvinst.exe (PID: 4308)
- RvControlSvc.exe (PID: 4556)
- RvRvpnGui.exe (PID: 2996)
Create files in a temporary directory
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6348)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe (PID: 6576)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
Reads the computer name
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6372)
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- msiexec.exe (PID: 6920)
- msiexec.exe (PID: 7144)
- MSIAD4B.tmp (PID: 6220)
- drvinst.exe (PID: 4308)
- RvControlSvc.exe (PID: 4556)
- RvRvpnGui.exe (PID: 2996)
Process checks computer location settings
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6372)
The sample compiled with english language support
- 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp (PID: 6612)
- msiexec.exe (PID: 6920)
- drvinst.exe (PID: 6200)
- drvinst.exe (PID: 4308)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6920)
- MSIAD4B.tmp (PID: 6220)
- drvinst.exe (PID: 6200)
- RvControlSvc.exe (PID: 4556)
- RvRvpnGui.exe (PID: 2996)
Reads the software policy settings
- msiexec.exe (PID: 6920)
- MSIAD4B.tmp (PID: 6220)
- drvinst.exe (PID: 6200)
Creates files or folders in the user directory
- msiexec.exe (PID: 6920)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6920)
The sample compiled with russian language support
- msiexec.exe (PID: 6920)
Starts application with an unusual extension
- msiexec.exe (PID: 6920)
Creates files in the program directory
- RvControlSvc.exe (PID: 4556)
Manual execution by a user
- RvRvpnGui.exe (PID: 2996)
Disables trace logs
- netsh.exe (PID: 6664)
- netsh.exe (PID: 6888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:01:30 14:21:56+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 123904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.4642.1 |
| ProductVersionNumber: | 1.4.4642.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Famatech Corp. |
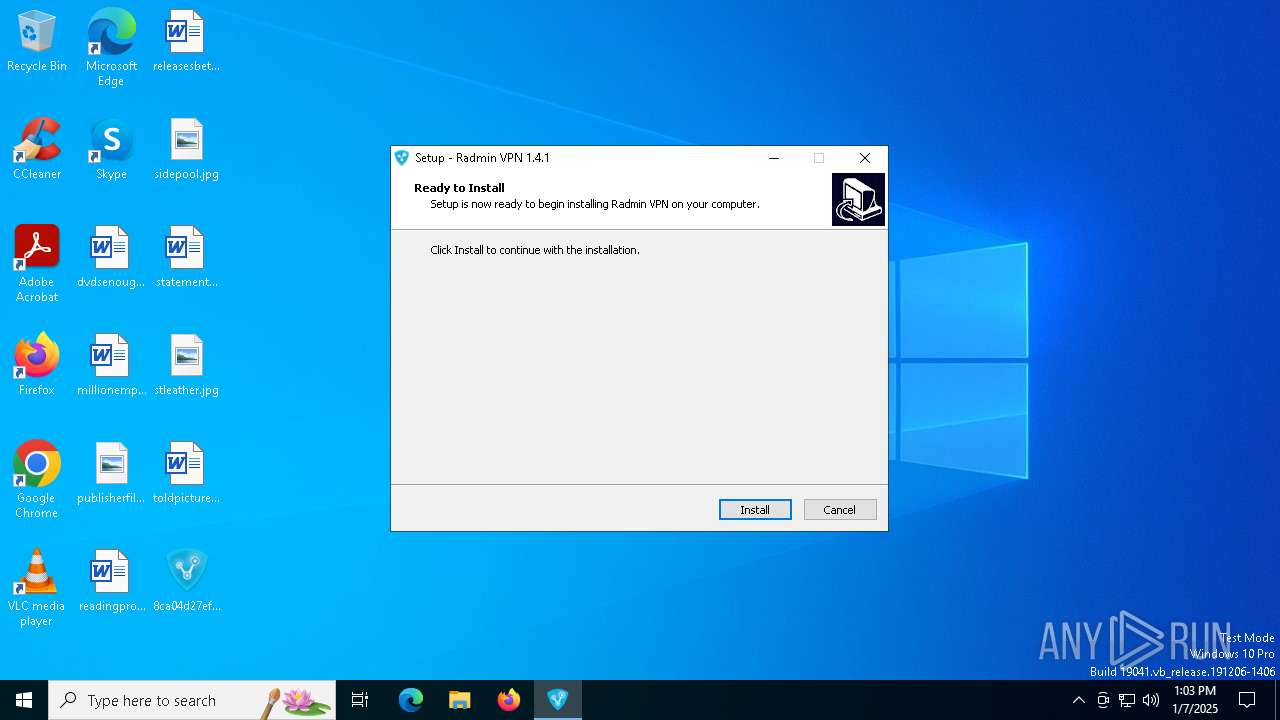
| FileDescription: | Radmin VPN Setup |
| FileVersion: | 1.4.4642.1 |
| LegalCopyright: | Copyright © 2017-2023 Famatech Corp. and its licensors. All rights reserved. |
| ProductName: | Radmin VPN |
| ProductVersion: | 1.4.4642.1 |
Total processes
157
Monitored processes
32
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1852 | C:\WINDOWS\system32\netsh.exe interface ip delete route prefix=0.0.0.0/0 interface="Radmin VPN" nexthop=26.0.0.1 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | netsh advfirewall firewall add rule name="Radmin VPN Control Service" dir=in action=allow program="C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe" enable=yes profile=any edge=yes | C:\Windows\SysWOW64\netsh.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | "C:\Program Files (x86)\Radmin VPN\RvRvpnGui.exe" /show | C:\Program Files (x86)\Radmin VPN\RvRvpnGui.exe | — | explorer.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin VPN Version: 1.4.4642.1 Modules
| |||||||||||||||
| 3436 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3724 | C:\Windows\syswow64\MsiExec.exe -Embedding 53550358F6C6A542482EF44458C5FEB7 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4076 | netsh advfirewall firewall add rule name="Radmin VPN icmpv4" action=allow enable=yes dir=in profile=any remoteip=26.0.0.0/8 protocol=icmpv4 | C:\Windows\SysWOW64\netsh.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:c36c271bc64eefc9:RVpnNetMP.ndi:15.39.54.8:{b06d84d1-af78-41ec-a5b9-3cce676528b2}\rvnetmp60," "42f731a47" "0000000000000174" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4556 | "C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe" /service | C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin VPN Control Service Version: 1.4.4642.1 Modules
| |||||||||||||||
| 4596 | C:\WINDOWS\system32\netsh.exe interface ipv6 add address interface="Radmin VPN" address=fdfd::1a94:2a21 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 945
Read events
15 735
Write events
183
Delete events
27
Modification events
| (PID) Process: | (7144) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (7144) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\msiexec.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 249C130000000000 | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\8C6E7C6DFBE2C1848BEC3F22750829D6 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\E104CB945A7524D499630F50E59EBBD9 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\9244A40E4C2F7D04DBFA8CC503C0D050 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: C:\Program Files (x86)\Radmin VPN\Driver.1.1\RvNetMP60.sys | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\8F435FCB0A41E684B9321EA32AAE9CE8 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\4835C2DD2FCDE6A4BAECFC15AEA61EC4 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: C:\Program Files (x86)\Radmin VPN\RvFwHelper.exe | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\265A90E3DB8F137439DFB40C03898E08 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: C:\Program Files (x86)\Radmin VPN\RvRvpnGui.exe | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\1799D7BDBD3D3694794B61E7C34C4C65 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: 01:\SOFTWARE\Famatech\Radmin VPN\ui\Language | |||
| (PID) Process: | (6920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\C96E1BA649A6581479496B0CFD498932 |
| Operation: | write | Name: | 9713ADC21A76A014189ABAA1F48DD99F |
Value: C:\Program Files (x86)\Radmin VPN\Qt5Core.dll | |||
Executable files
118
Suspicious files
69
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6612 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | C:\Users\admin\AppData\Local\Temp\is-0FT2U.tmp\is-IVMV2.tmp | — | |
MD5:— | SHA256:— | |||
| 6612 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | C:\Users\admin\AppData\Local\Temp\is-0FT2U.tmp\RadminVPN_1.4.4642.1.msi | — | |
MD5:— | SHA256:— | |||
| 6920 | msiexec.exe | C:\Windows\Installer\13959c.msi | — | |
MD5:— | SHA256:— | |||
| 6576 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.exe | C:\Users\admin\AppData\Local\Temp\is-E1LQE.tmp\8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | executable | |
MD5:EC5312E06DA51691D2E26820F3C93ECE | SHA256:421CB7E48E3063D927EEFE28940E119FB1309A3990BC7325C7F7052A2B286A09 | |||
| 6920 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:24C48C99C212B1203CA8D8A38395CA80 | SHA256:485261D4383D7FC6D08B836212ADD2203872A6CC67CF9BAE014F91ADC62A2861 | |||
| 6920 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:ECFC080250045654D0779203E07485AA | SHA256:6C865709966696C3D381E362DFFC5EA97A16E3CAB10F4F73E19DA0E30D0E5323 | |||
| 6920 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_E8A1D4619D52FB86B679531C48D42087 | binary | |
MD5:D65FE1D391E02B2FE93C3BBC4D7E5A05 | SHA256:46CE4ADD6ED4732E7FE1890211A084AE59F3391A74BCEDDFC1AB51E6A90195CB | |||
| 6612 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | C:\Users\admin\AppData\Local\Temp\is-0FT2U.tmp\_isetup\_setup64.tmp | executable | |
MD5:C8871EFD8AF2CF4D9D42D1FF8FADBF89 | SHA256:E4FC574A01B272C2D0AED0EC813F6D75212E2A15A5F5C417129DD65D69768F40 | |||
| 6612 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | C:\Users\admin\AppData\Local\Temp\is-0FT2U.tmp\Rvis_install_dll.dll | executable | |
MD5:2CF9BAC0B1E6AF2F444E993659454476 | SHA256:19D00D00079177F3E78533ECB9F2E797092DD4D6BDDAE7D394218501AFA4D51E | |||
| 6612 | 8ca04d27ef8c28e0edac3b740ebe7fb8839b4794752a0d359ae18de22fc6be35.tmp | C:\Users\admin\AppData\Local\Temp\is-0FT2U.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4516 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1752 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
1752 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
— | — | POST | 204 | 95.101.136.223:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
4516 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
6920 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEANmchMIZYHj%2F%2B8%2Bj8Y68sw%3D | US | binary | 727 b | whitelisted |
6920 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4516 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1752 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4516 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1752 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4516 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1752 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fail.radminte.com |
| unknown |
www.bing.com |
| whitelisted |
win1910.ipv6.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |