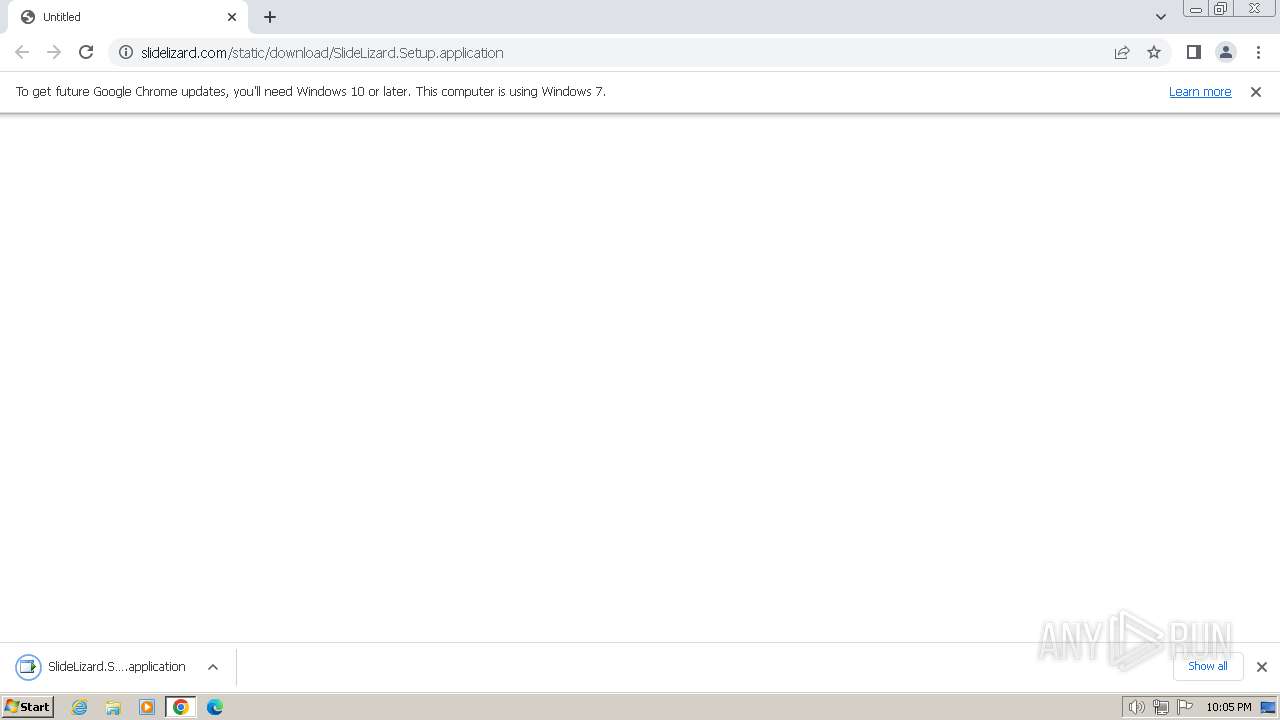
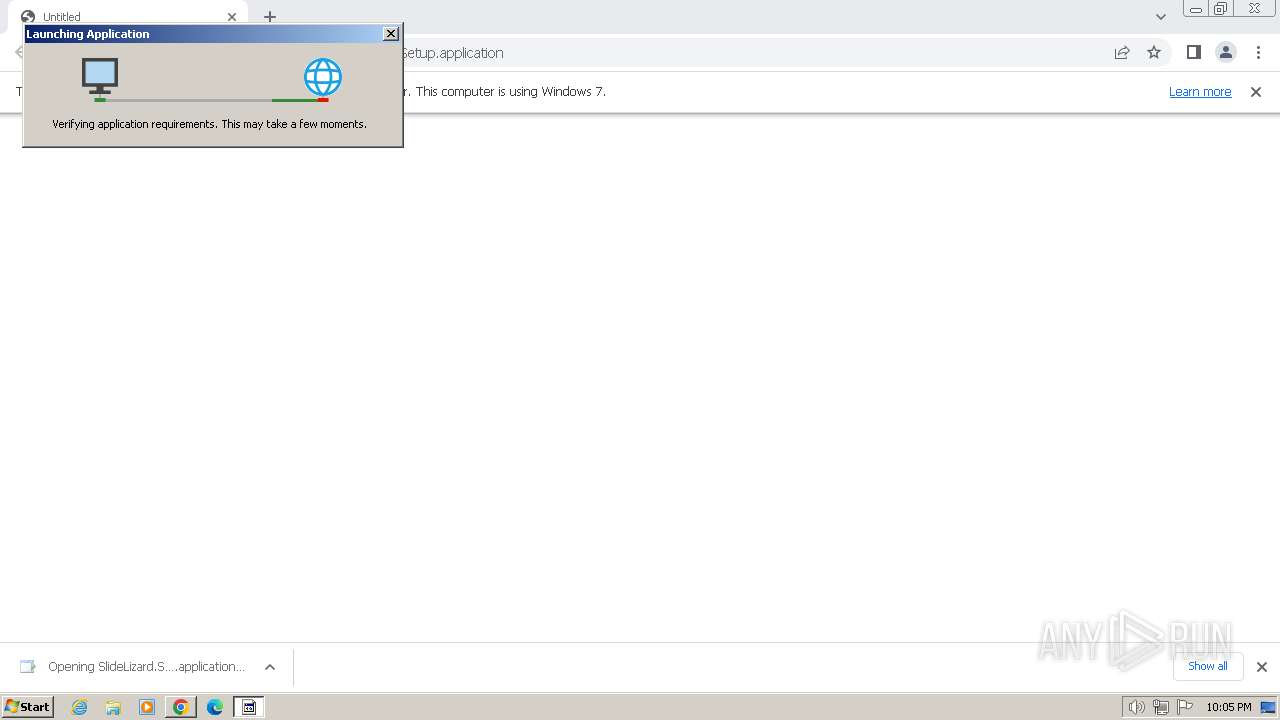
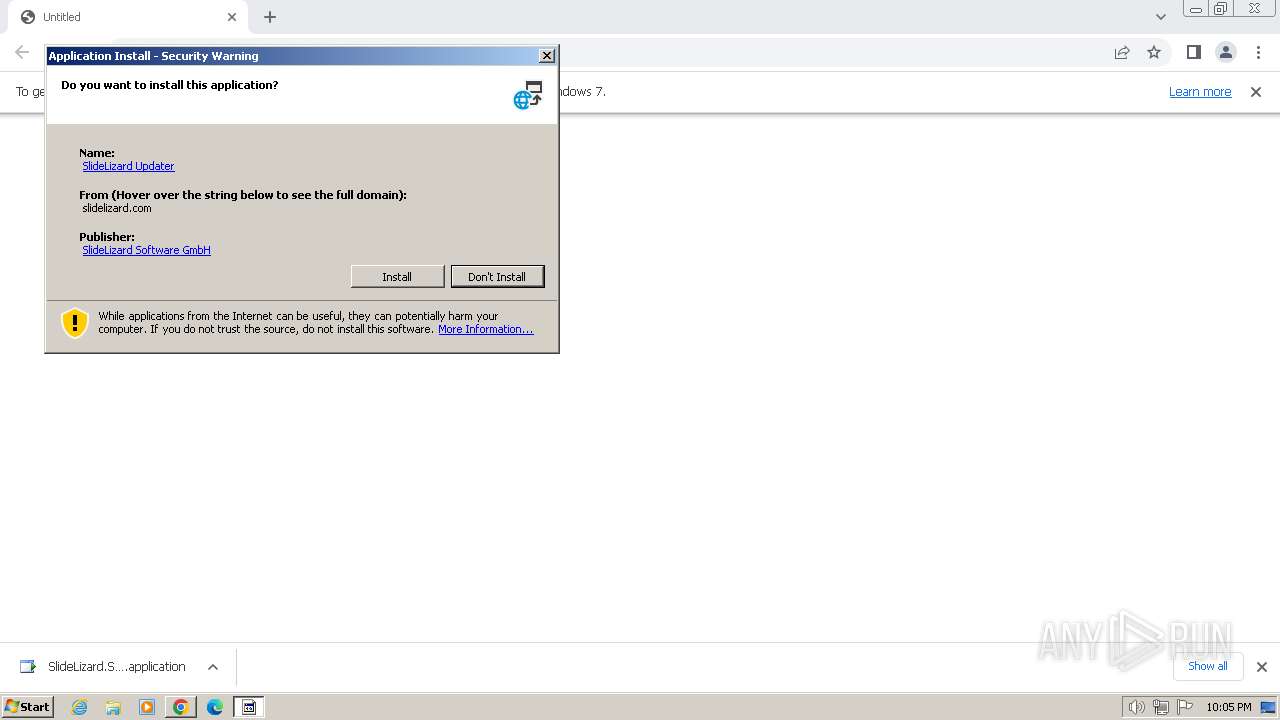
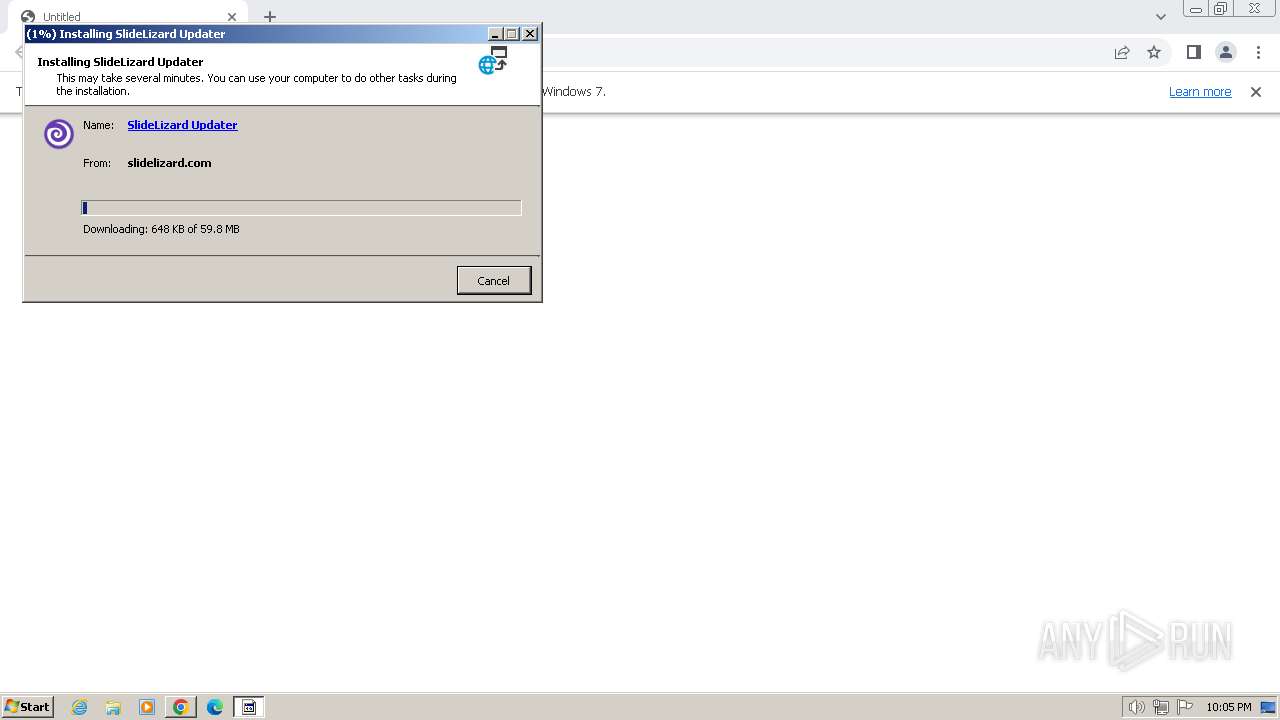
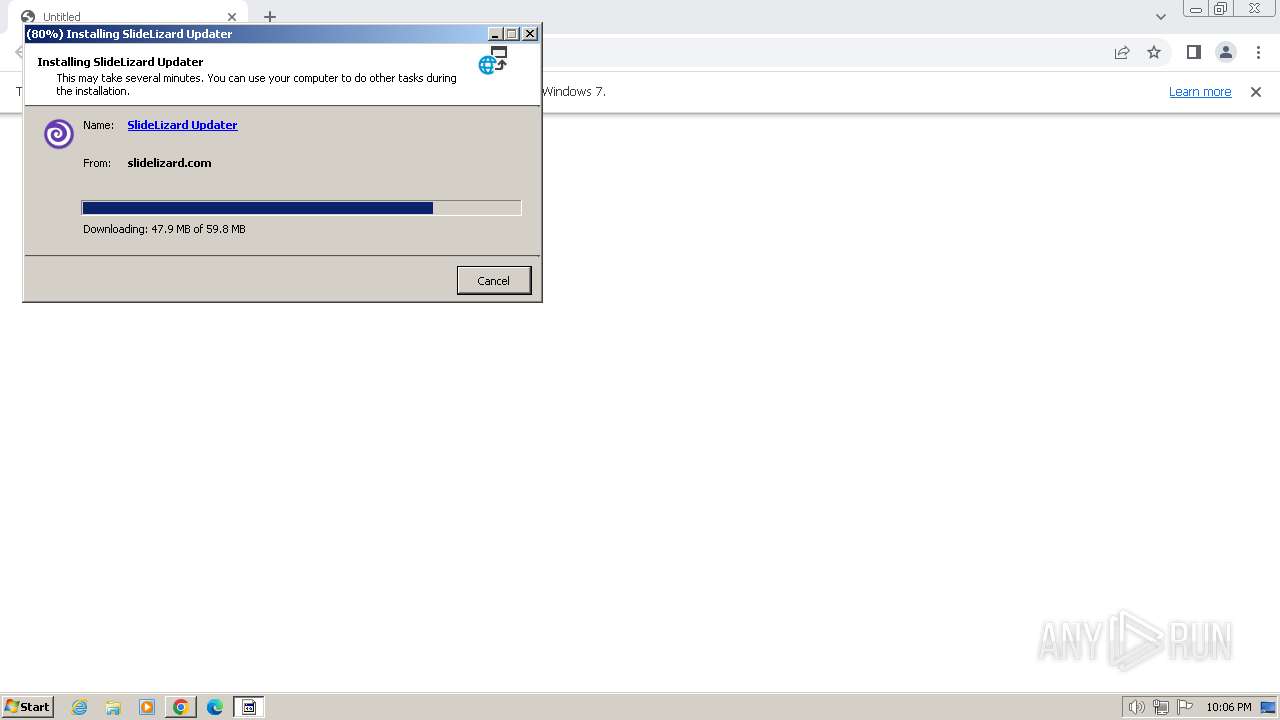
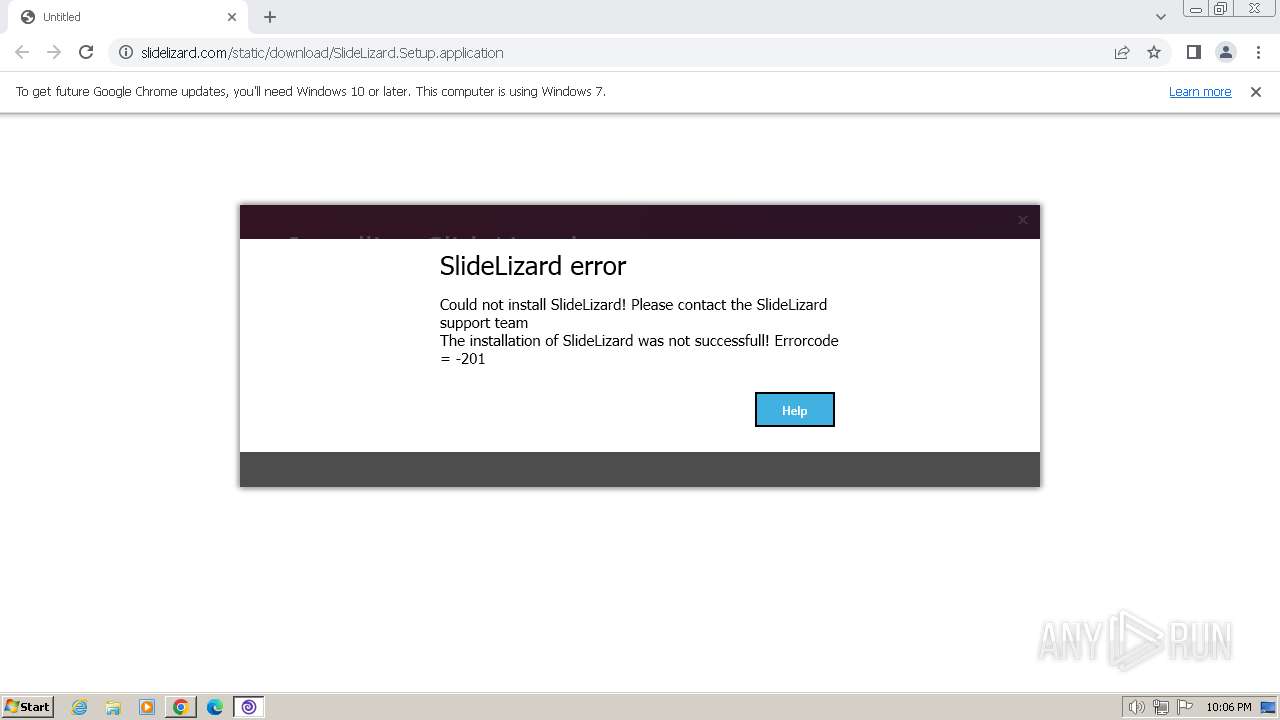
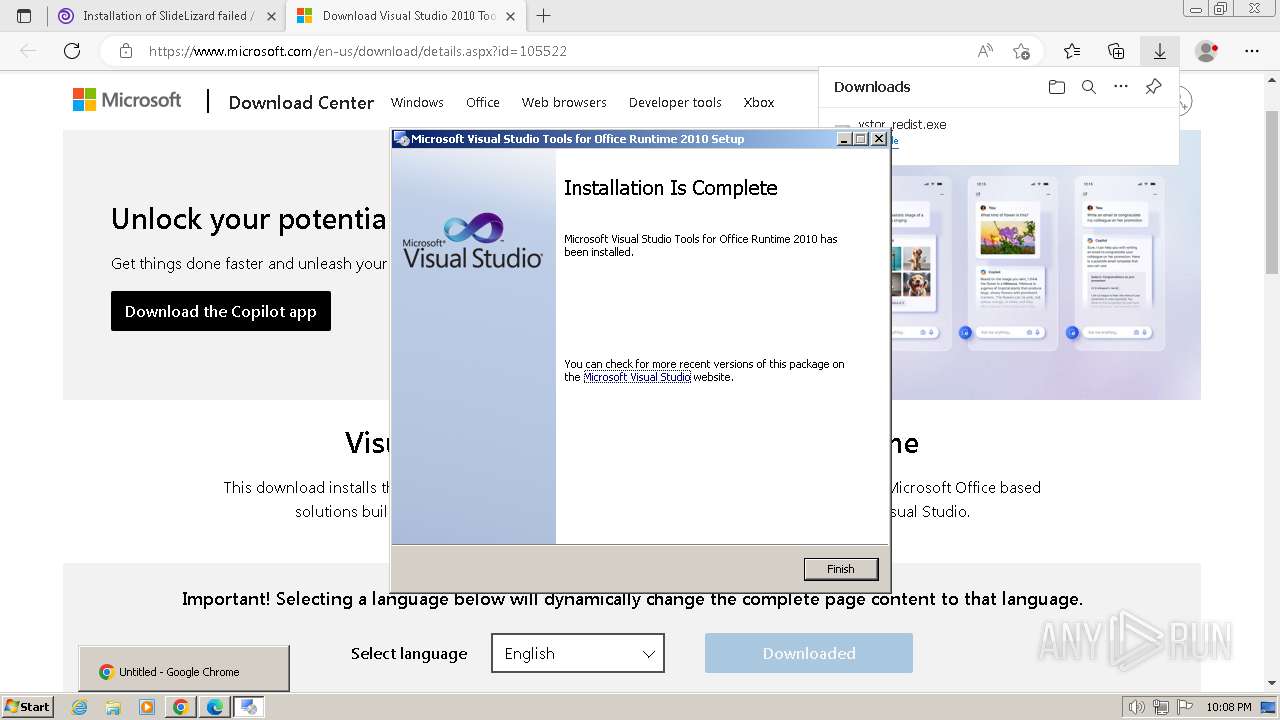
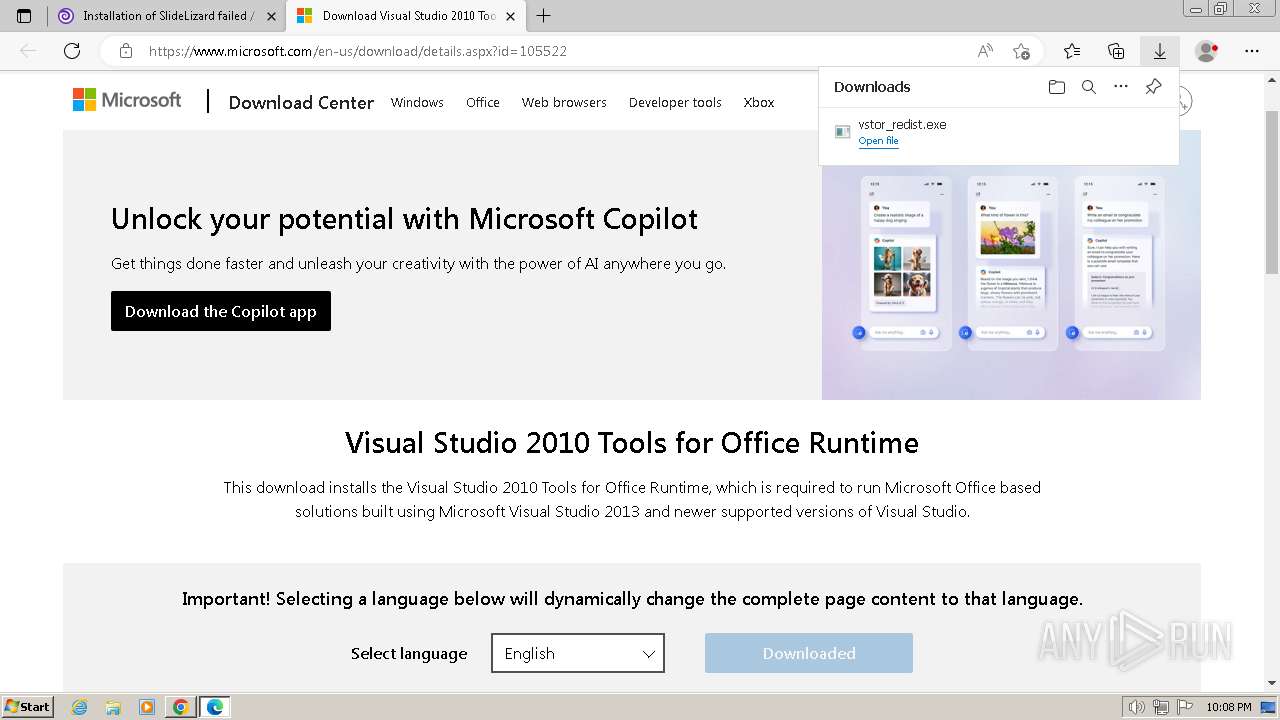
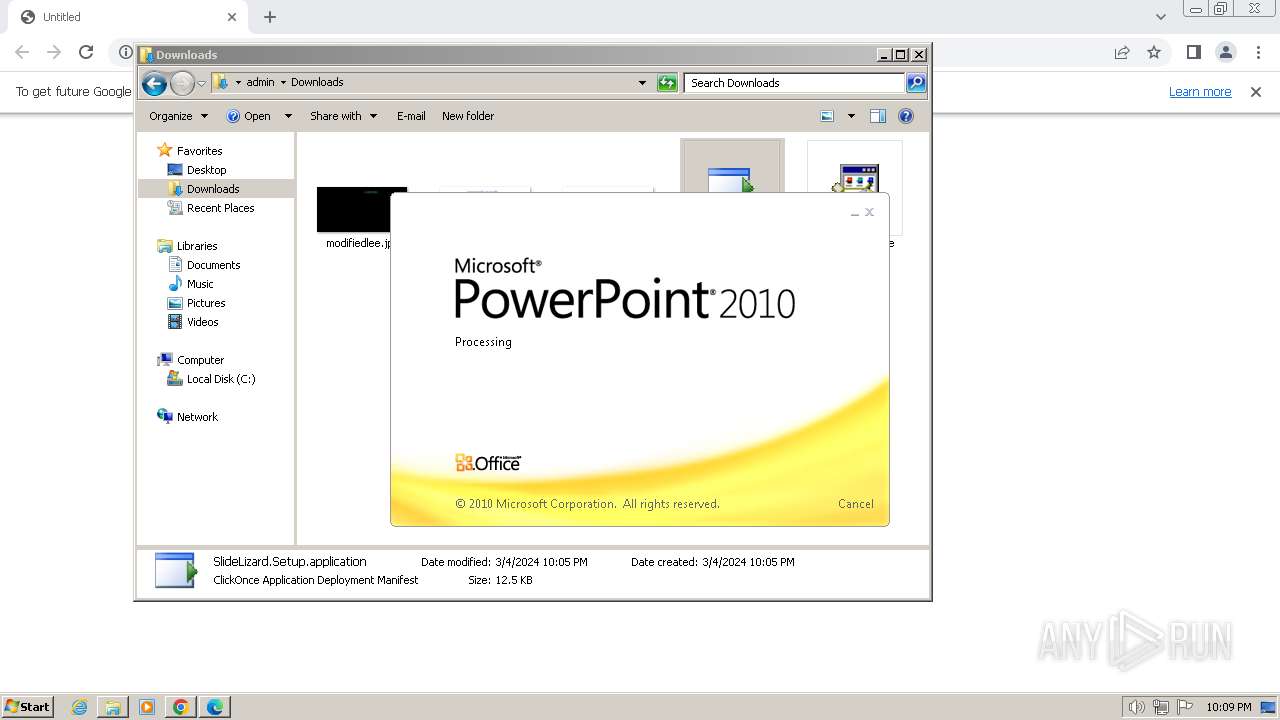
| URL: | https://slidelizard.com/static/download/SlideLizard.Setup.application |
| Full analysis: | https://app.any.run/tasks/cb06c477-d064-4101-83b9-abedefbae9b3 |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2024, 22:05:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4CB04AF2C6CABA07B72916D7D1500F16 |
| SHA1: | 6344730024A1E22E9ECB0EA0E178DC1AAA88F64F |
| SHA256: | 8C9A7AC6EF30AD47FF5EDD90052666C6B64563F631D6D2BB895A1010E3B371D4 |
| SSDEEP: | 3:N8EAsbKBGK2uMjsRWgMMQn:2EAsbK8jsZm |
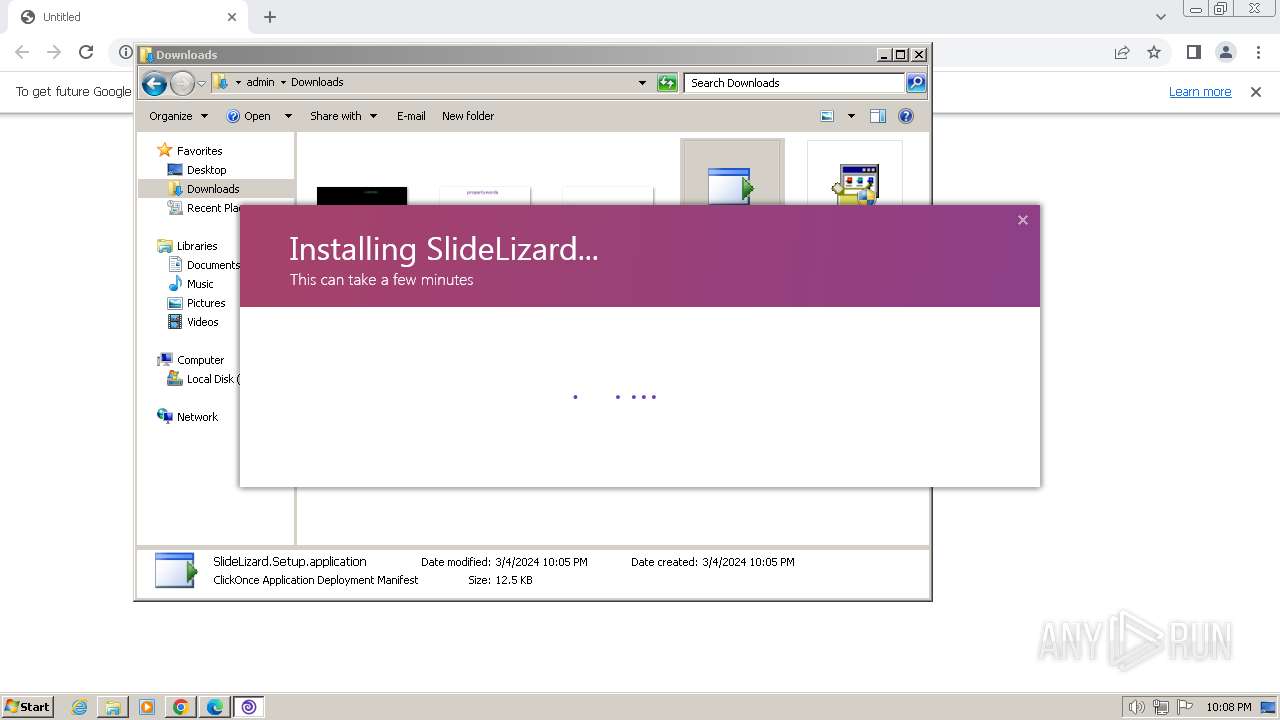
MALICIOUS
Drops the executable file immediately after the start
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
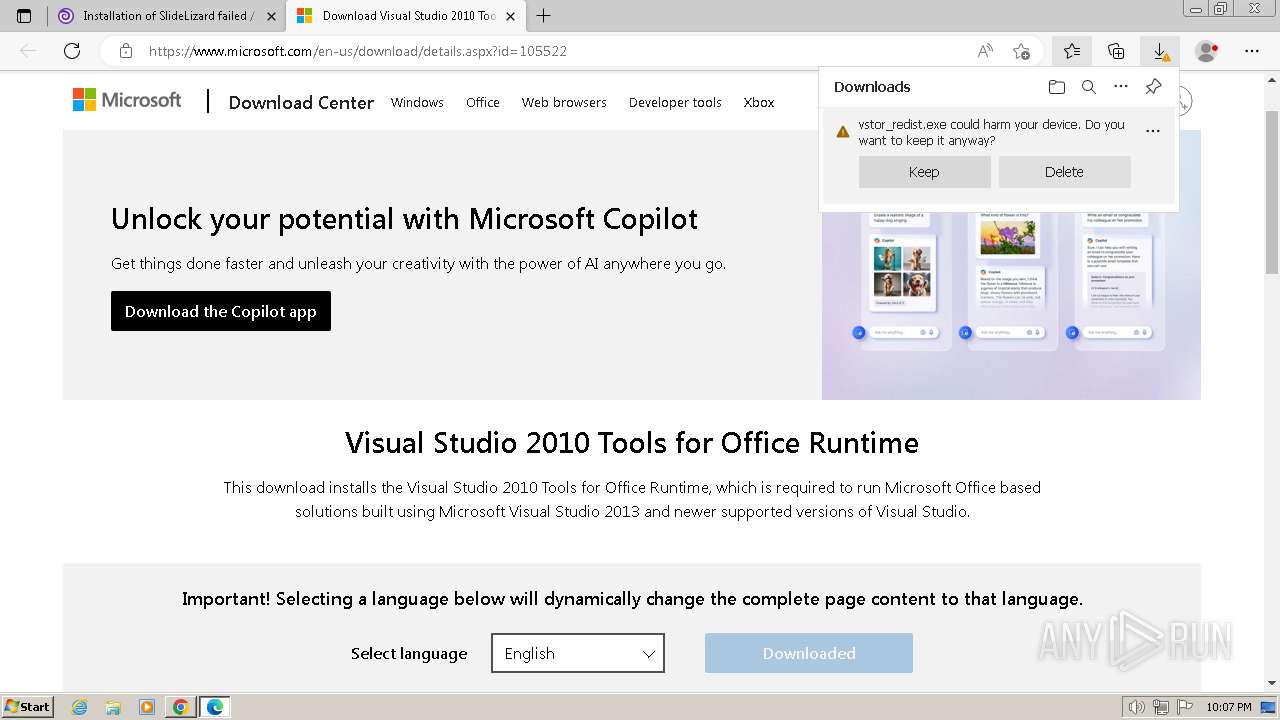
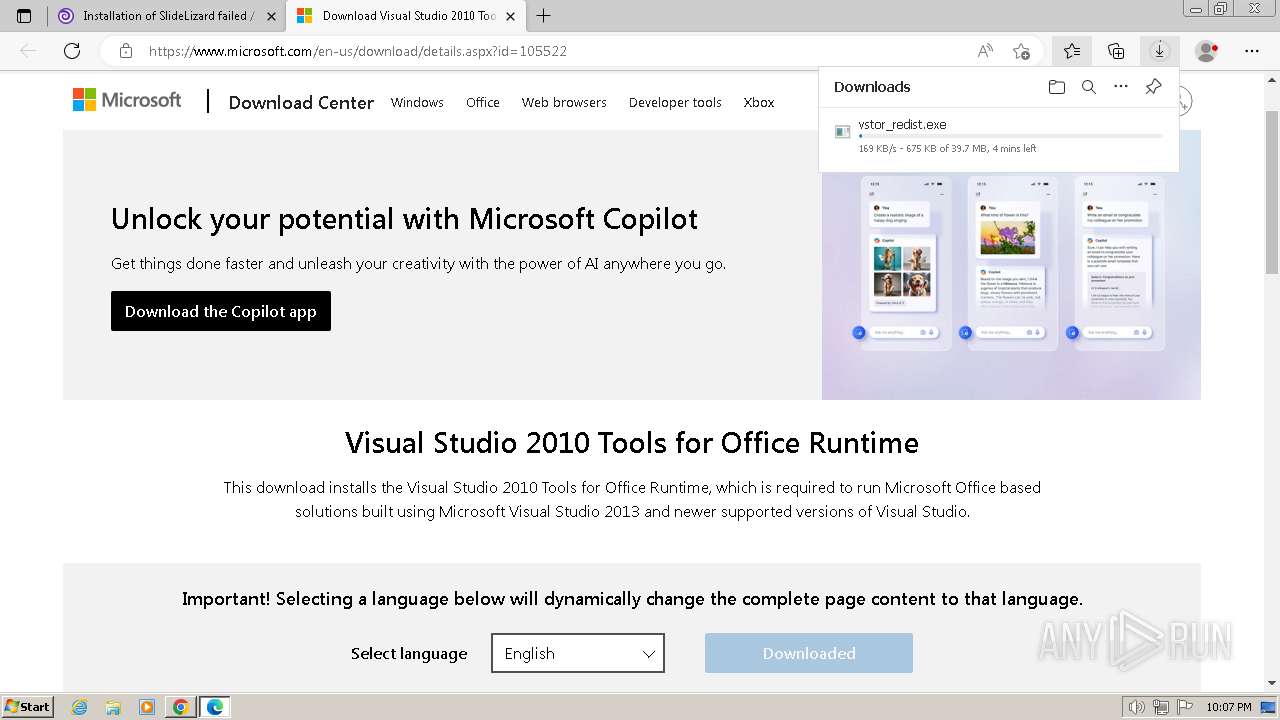
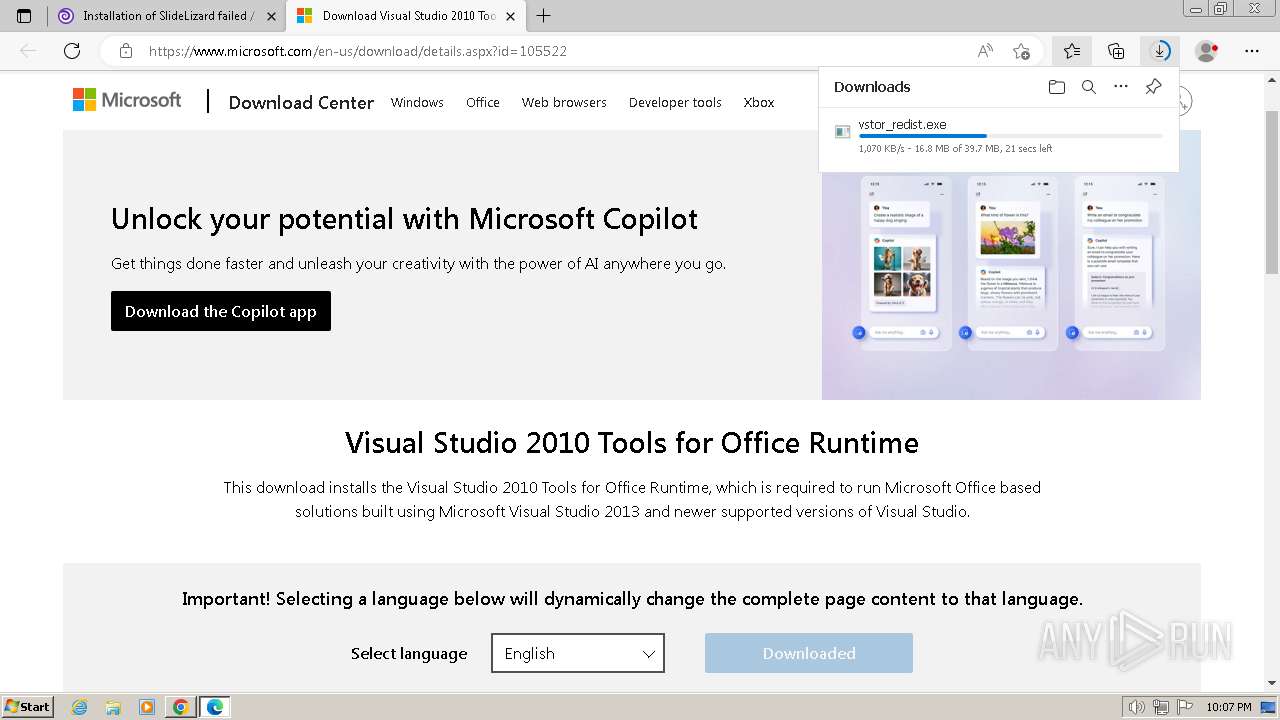
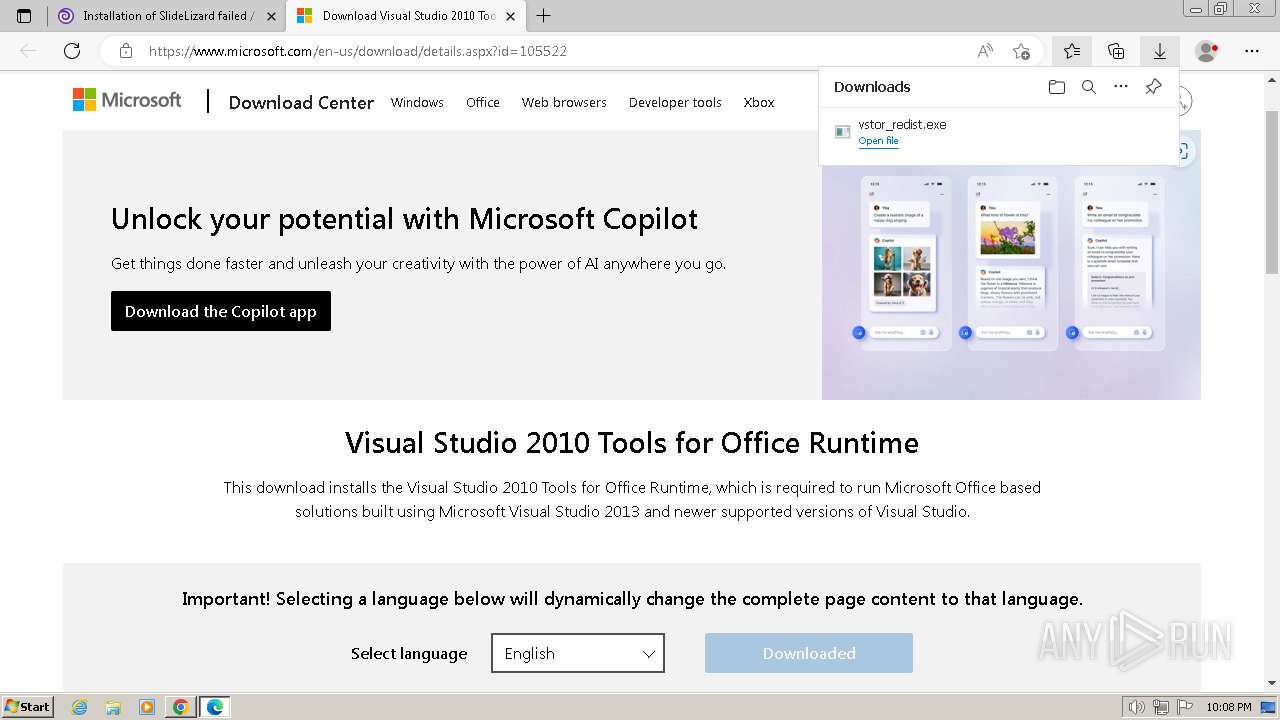
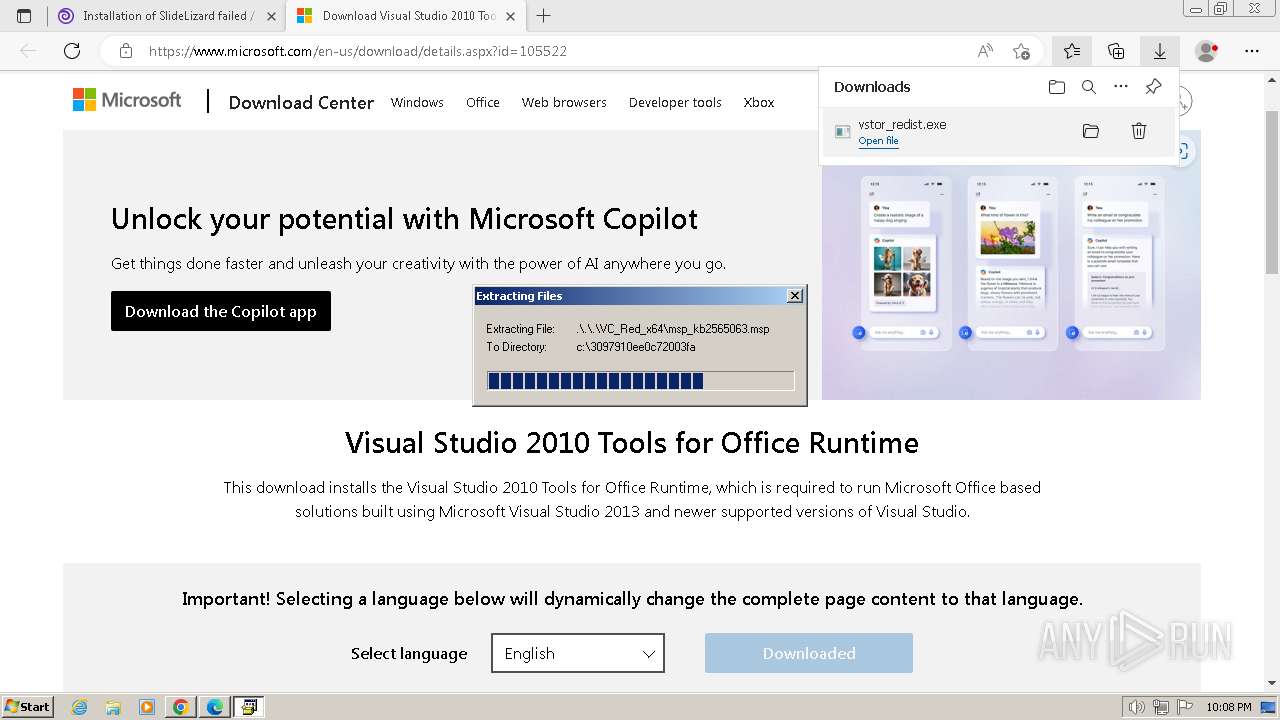
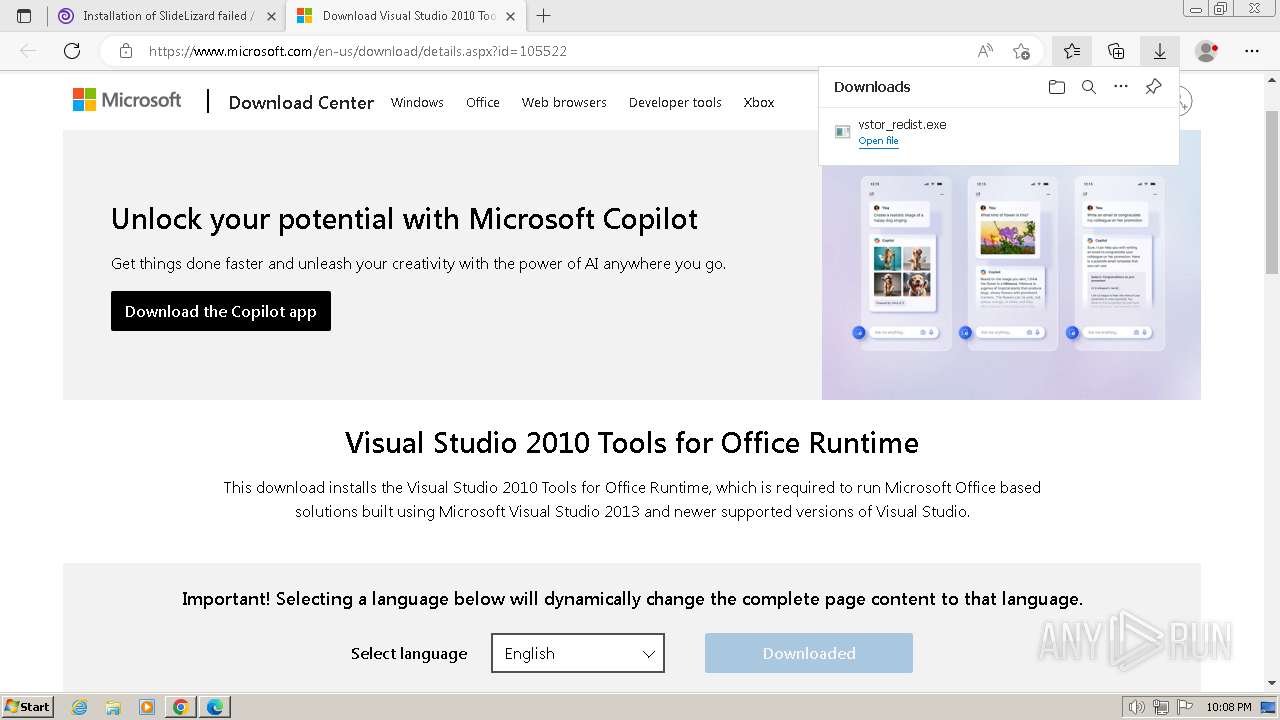
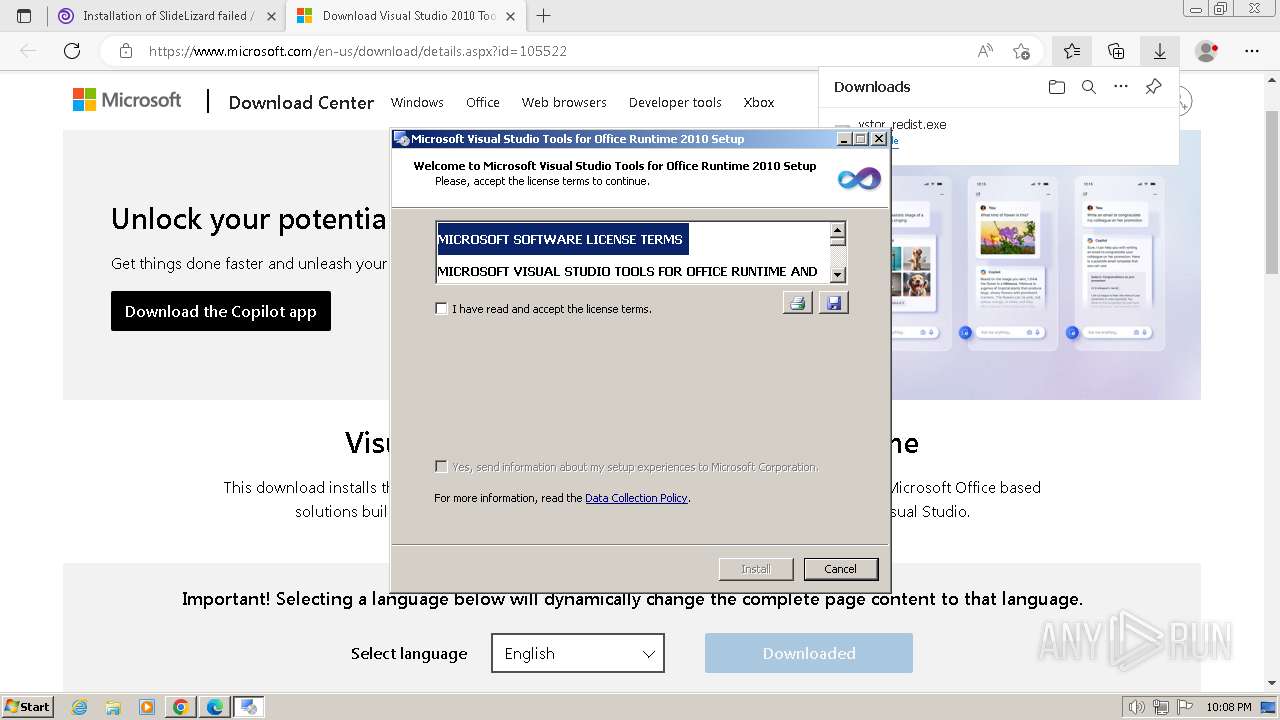
- vstor_redist.exe (PID: 2516)
- vstor40_x86.exe (PID: 3992)
- msiexec.exe (PID: 1408)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
Creates a writable file in the system directory
- msiexec.exe (PID: 1408)
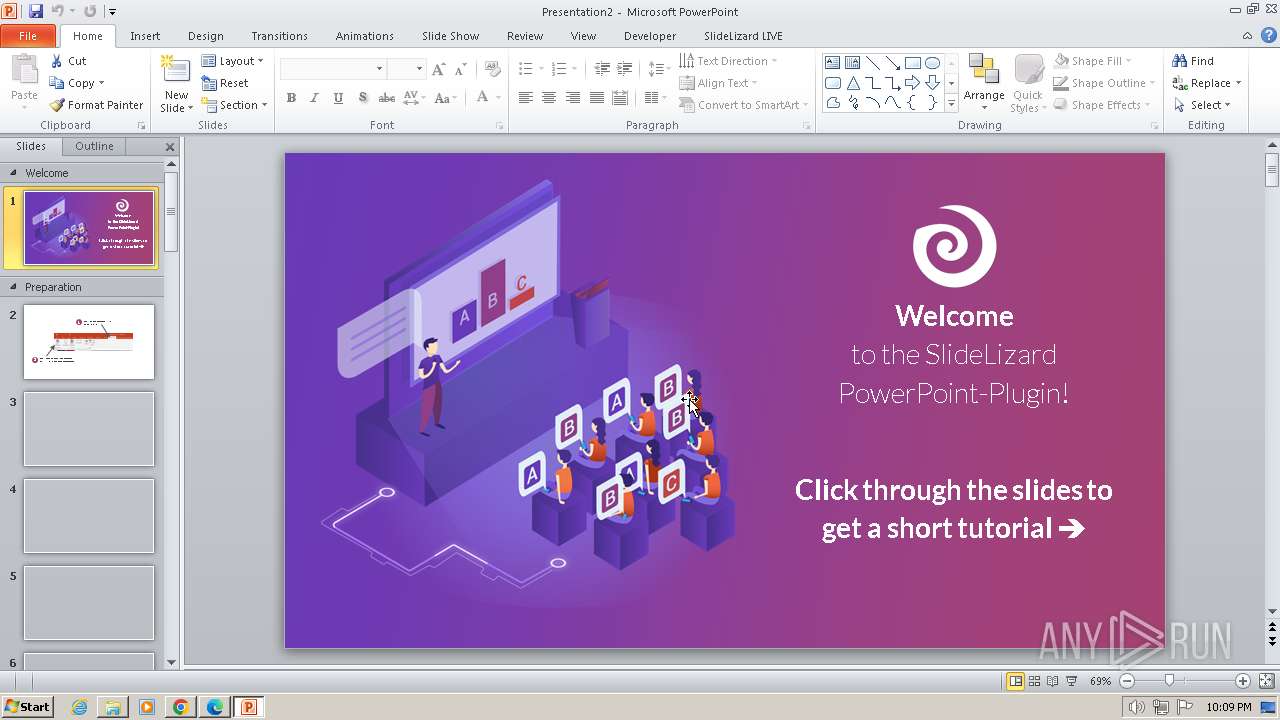
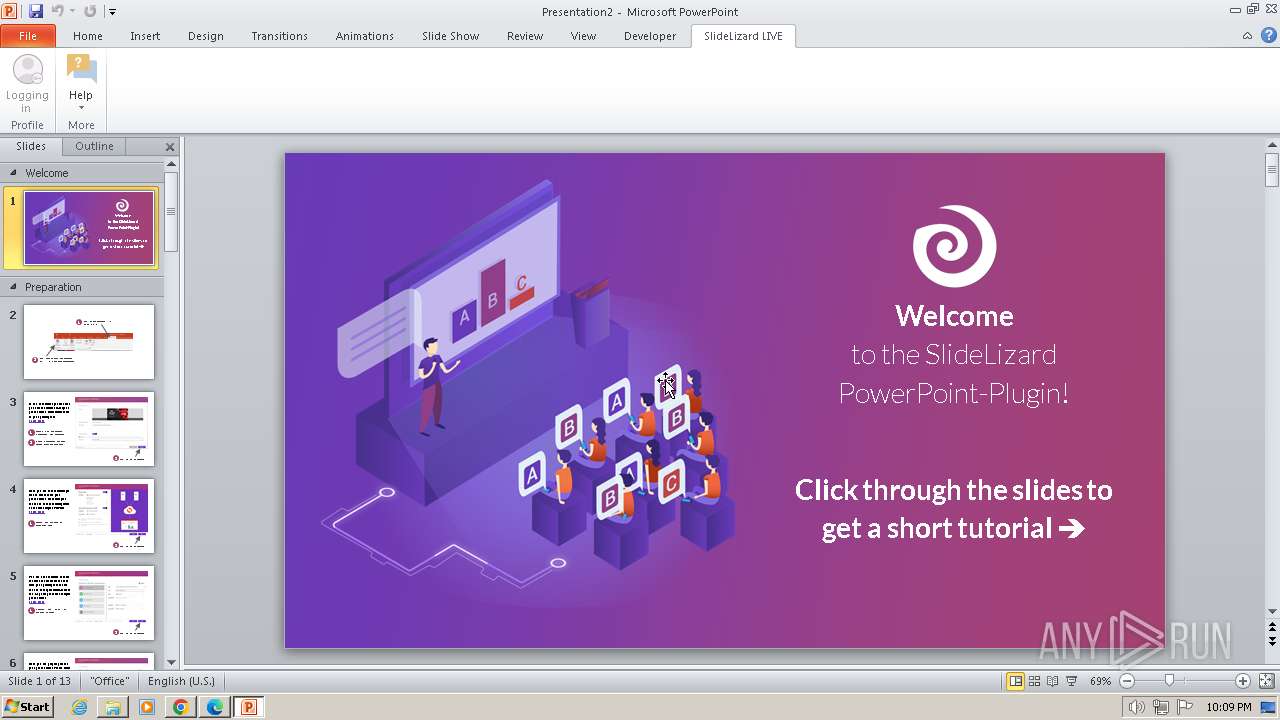
Connection from MS Office application
- POWERPNT.EXE (PID: 2136)
Executable content was dropped or overwritten
- POWERPNT.EXE (PID: 2136)
Unusual execution from MS Office
- POWERPNT.EXE (PID: 2136)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 3672)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- SlideLizard.Setup.exe (PID: 3444)
- Setup.exe (PID: 2396)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
Reads the Internet Settings
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- VSTOInstaller.exe (PID: 1636)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
Reads settings of System Certificates
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- SlideLizard.Setup.exe (PID: 3444)
- Setup.exe (PID: 2396)
- VSTOInstaller.exe (PID: 3396)
- SlideLizard.Setup.exe (PID: 3620)
Checks Windows Trust Settings
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- VSTOInstaller.exe (PID: 3396)
Adds/modifies Windows certificates
- dfsvc.exe (PID: 2112)
Reads Internet Explorer settings
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- VSTOInstaller.exe (PID: 3396)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- vstor_redist.exe (PID: 2516)
- vstor40_x86.exe (PID: 3992)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
Process drops legitimate windows executable
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- vstor_redist.exe (PID: 2516)
- msiexec.exe (PID: 1408)
- vstor40_x86.exe (PID: 3992)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
- POWERPNT.EXE (PID: 2136)
Searches for installed software
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- VSTOInstaller.exe (PID: 3396)
Creates a software uninstall entry
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- VSTOInstaller.exe (PID: 3396)
- POWERPNT.EXE (PID: 2136)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1408)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 1408)
Changes Internet Explorer settings (feature browser emulation)
- POWERPNT.EXE (PID: 2136)
INFO
Application launched itself
- chrome.exe (PID: 3672)
- msedge.exe (PID: 1264)
- msiexec.exe (PID: 1408)
Checks supported languages
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- VSTOInstaller.exe (PID: 1636)
- wmpnscfg.exe (PID: 3576)
- vstor_redist.exe (PID: 2516)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- vstor40_x86.exe (PID: 3992)
- install.exe (PID: 2976)
- msiexec.exe (PID: 2092)
- ngen.exe (PID: 3060)
- ngen.exe (PID: 1236)
- ngen.exe (PID: 2192)
- ngen.exe (PID: 3480)
- msiexec.exe (PID: 2544)
- ngen.exe (PID: 2624)
- ngen.exe (PID: 2136)
- ngen.exe (PID: 2444)
- ngen.exe (PID: 896)
- ngen.exe (PID: 1172)
- ngen.exe (PID: 2660)
- ngen.exe (PID: 3940)
- ngen.exe (PID: 3084)
- ngen.exe (PID: 3504)
- ngen.exe (PID: 2664)
- ngen.exe (PID: 3476)
- ngen.exe (PID: 2024)
- ngen.exe (PID: 4056)
- ngen.exe (PID: 2336)
- ngen.exe (PID: 764)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 1848)
- ngen.exe (PID: 2468)
- ngen.exe (PID: 3068)
- ngen.exe (PID: 2156)
- ngen.exe (PID: 1976)
- ngen.exe (PID: 2588)
- ngen.exe (PID: 1636)
- ngen.exe (PID: 3396)
- ngen.exe (PID: 3096)
- ngen.exe (PID: 2404)
- ngen.exe (PID: 448)
- ngen.exe (PID: 2308)
- ngen.exe (PID: 4072)
- ngen.exe (PID: 3016)
- ngen.exe (PID: 1748)
- ngen.exe (PID: 2748)
- ngen.exe (PID: 2568)
- ngen.exe (PID: 2204)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 3932)
- ngen.exe (PID: 3264)
- ngen.exe (PID: 240)
- ngen.exe (PID: 668)
- ngen.exe (PID: 2000)
- ngen.exe (PID: 1624)
- ngen.exe (PID: 2408)
- ngen.exe (PID: 748)
- ngen.exe (PID: 316)
- ngen.exe (PID: 2876)
- ngen.exe (PID: 2024)
- ngen.exe (PID: 296)
- ngen.exe (PID: 2764)
- ngen.exe (PID: 3220)
- ngen.exe (PID: 3780)
- ngen.exe (PID: 1696)
- ngen.exe (PID: 3640)
- ngen.exe (PID: 1544)
- ngen.exe (PID: 2988)
- ngen.exe (PID: 4056)
- ngen.exe (PID: 932)
- ngen.exe (PID: 324)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 1860)
- ngen.exe (PID: 4036)
- addinutil.exe (PID: 2444)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
- addinutil.exe (PID: 1624)
- DpiDetection.exe (PID: 2760)
Reads the computer name
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- VSTOInstaller.exe (PID: 1636)
- wmpnscfg.exe (PID: 3576)
- vstor_redist.exe (PID: 2516)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- vstor40_x86.exe (PID: 3992)
- install.exe (PID: 2976)
- msiexec.exe (PID: 2092)
- ngen.exe (PID: 2192)
- msiexec.exe (PID: 2544)
- ngen.exe (PID: 3480)
- ngen.exe (PID: 2444)
- ngen.exe (PID: 1236)
- ngen.exe (PID: 2624)
- ngen.exe (PID: 3060)
- ngen.exe (PID: 2136)
- ngen.exe (PID: 1172)
- ngen.exe (PID: 2024)
- ngen.exe (PID: 896)
- ngen.exe (PID: 2660)
- ngen.exe (PID: 3940)
- ngen.exe (PID: 3504)
- ngen.exe (PID: 2664)
- ngen.exe (PID: 3476)
- ngen.exe (PID: 3084)
- ngen.exe (PID: 4056)
- ngen.exe (PID: 2336)
- ngen.exe (PID: 764)
- ngen.exe (PID: 1848)
- ngen.exe (PID: 2468)
- ngen.exe (PID: 3068)
- ngen.exe (PID: 1976)
- ngen.exe (PID: 2156)
- ngen.exe (PID: 2588)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 3396)
- ngen.exe (PID: 3096)
- ngen.exe (PID: 2404)
- ngen.exe (PID: 4072)
- ngen.exe (PID: 448)
- ngen.exe (PID: 2308)
- ngen.exe (PID: 3016)
- ngen.exe (PID: 1748)
- ngen.exe (PID: 2748)
- ngen.exe (PID: 1636)
- ngen.exe (PID: 2408)
- ngen.exe (PID: 2568)
- ngen.exe (PID: 3264)
- ngen.exe (PID: 2204)
- ngen.exe (PID: 3932)
- ngen.exe (PID: 240)
- ngen.exe (PID: 3072)
- ngen.exe (PID: 668)
- ngen.exe (PID: 1624)
- ngen.exe (PID: 2764)
- ngen.exe (PID: 748)
- ngen.exe (PID: 316)
- ngen.exe (PID: 2876)
- ngen.exe (PID: 296)
- ngen.exe (PID: 1696)
- ngen.exe (PID: 3780)
- ngen.exe (PID: 3220)
- ngen.exe (PID: 2000)
- ngen.exe (PID: 2024)
- ngen.exe (PID: 3640)
- ngen.exe (PID: 1544)
- ngen.exe (PID: 4056)
- ngen.exe (PID: 932)
- ngen.exe (PID: 1428)
- ngen.exe (PID: 1860)
- ngen.exe (PID: 324)
- ngen.exe (PID: 4036)
- ngen.exe (PID: 2988)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
- DpiDetection.exe (PID: 2760)
Reads Environment values
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- vstor_redist.exe (PID: 2516)
- vstor40_x86.exe (PID: 3992)
- VSTOInstaller.exe (PID: 3396)
- SlideLizard.Setup.exe (PID: 3620)
Reads the machine GUID from the registry
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- VSTOInstaller.exe (PID: 1636)
- vstor_redist.exe (PID: 2516)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- vstor40_x86.exe (PID: 3992)
- install.exe (PID: 2976)
- msiexec.exe (PID: 2544)
- msiexec.exe (PID: 2092)
- addinutil.exe (PID: 2444)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
- addinutil.exe (PID: 1624)
- DpiDetection.exe (PID: 2760)
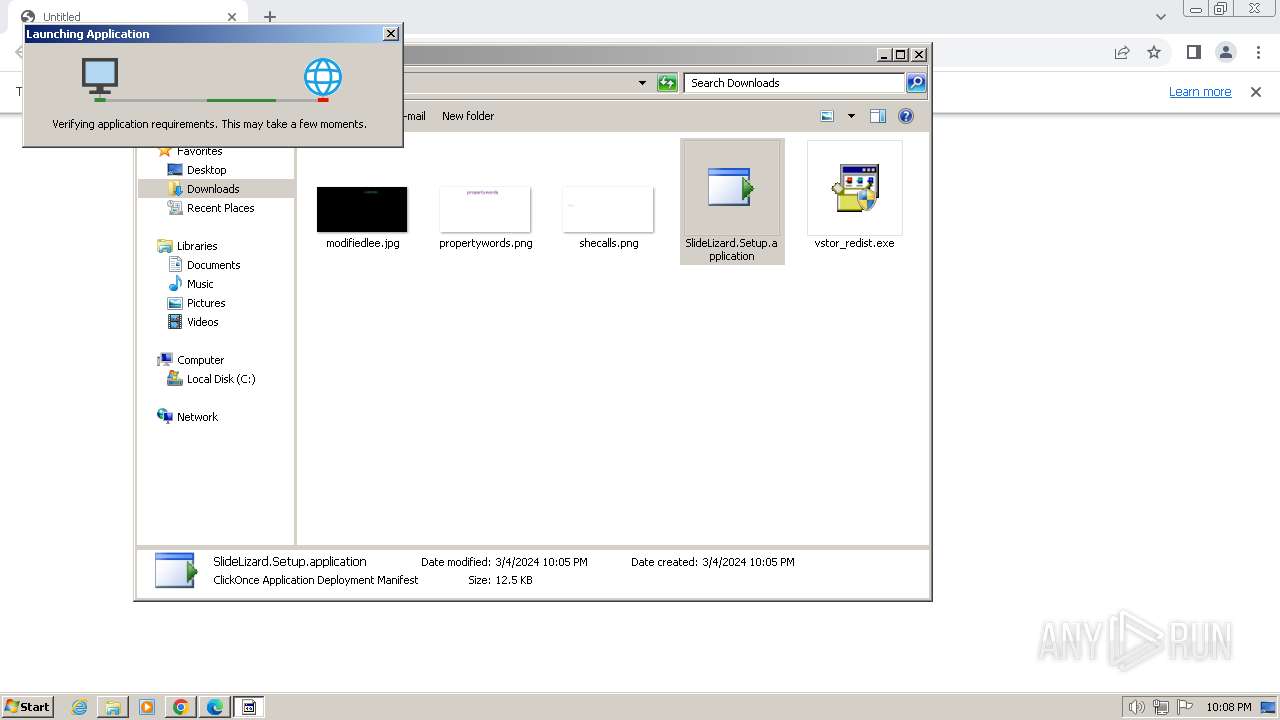
The process uses the downloaded file
- chrome.exe (PID: 2184)
- dfsvc.exe (PID: 2112)
- msedge.exe (PID: 996)
- msedge.exe (PID: 1264)
Creates files or folders in the user directory
- dfsvc.exe (PID: 2112)
- SlideLizard.Setup.exe (PID: 3444)
- VSTOInstaller.exe (PID: 1636)
- SlideLizard.Setup.exe (PID: 3620)
- VSTOInstaller.exe (PID: 3396)
Checks proxy server information
- dfsvc.exe (PID: 2112)
Reads the software policy settings
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- SlideLizard.Setup.exe (PID: 3444)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- VSTOInstaller.exe (PID: 3396)
- SlideLizard.Setup.exe (PID: 3620)
Create files in a temporary directory
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 1636)
- Setup.exe (PID: 2396)
- msiexec.exe (PID: 1408)
- install.exe (PID: 2976)
- VSTOInstaller.exe (PID: 3396)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 2112)
- VSTOInstaller.exe (PID: 3396)
Executable content was dropped or overwritten
- chrome.exe (PID: 3760)
- msedge.exe (PID: 1264)
- msiexec.exe (PID: 1408)
- chrome.exe (PID: 1376)
Drops the executable file immediately after the start
- chrome.exe (PID: 3760)
- msedge.exe (PID: 1264)
- chrome.exe (PID: 1376)
- POWERPNT.EXE (PID: 2136)
Manual execution by a user
- wmpnscfg.exe (PID: 3576)
- explorer.exe (PID: 1044)
- rundll32.exe (PID: 3640)
Reads CPU info
- Setup.exe (PID: 2396)
Creates a software uninstall entry
- msiexec.exe (PID: 1408)
Reads Microsoft Office registry keys
- msiexec.exe (PID: 1408)
- VSTOInstaller.exe (PID: 3396)
Creates files in the program directory
- POWERPNT.EXE (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
280
Monitored processes
131
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "c:\Program Files\Common Files\Microsoft Shared\VSTA\Pipeline.v10.0\HostSideAdapters\Microsoft.VisualStudio.Tools.Office.Excel.HostAdapter.v10.0.dll" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 268 | "C:\Users\admin\Downloads\vstor_redist.exe" | C:\Users\admin\Downloads\vstor_redist.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual Studio Tools for Office Runtime 2010 Redistributable Setup Exit code: 3221226540 Version: 10.0.60910.00 Modules
| |||||||||||||||
| 296 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "Microsoft.Office.Tools.v4.0.Framework, Version=10.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 316 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "Microsoft.VisualStudio.Tools.Applications.Runtime, Version=10.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 324 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe update /queue | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 448 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "Microsoft.VisualStudio.Tools.Office.Contract.v9.0, Version=9.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x5551f598,0x5551f5a8,0x5551f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 668 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "c:\Program Files\Common Files\Microsoft Shared\VSTA\Pipeline.v10.0\HostSideAdapters\Microsoft.VisualStudio.Tools.Office.Word.HostAdapter.v10.0.dll" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2000 --field-trial-handle=1148,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "Microsoft.VisualStudio.Tools.Office.ContainerControl.v10.0, Version=10.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" /queue:3 /NoDependencies | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
114 571
Read events
104 916
Write events
7 674
Delete events
1 981
Modification events
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
827
Suspicious files
214
Text files
530
Unknown types
159
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f83b.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF17fa8c.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f83b.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f84a.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1318e532-68e5-4f55-8de5-74ceafc414e8.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
84
DNS requests
156
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 43.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 156 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 84.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 269 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 415 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.11 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.55 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.26 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.58 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.49 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3672 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3672 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3944 | chrome.exe | 142.251.163.84:443 | accounts.google.com | GOOGLE | US | unknown |
3944 | chrome.exe | 116.202.203.74:443 | slidelizard.com | Hetzner Online GmbH | DE | unknown |
3944 | chrome.exe | 142.250.185.238:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
2112 | dfsvc.exe | 116.202.203.74:443 | slidelizard.com | Hetzner Online GmbH | DE | unknown |
2112 | dfsvc.exe | 192.229.221.95:80 | cacerts.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
slidelizard.com |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
cacerts.digicert.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
dc.services.visualstudio.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
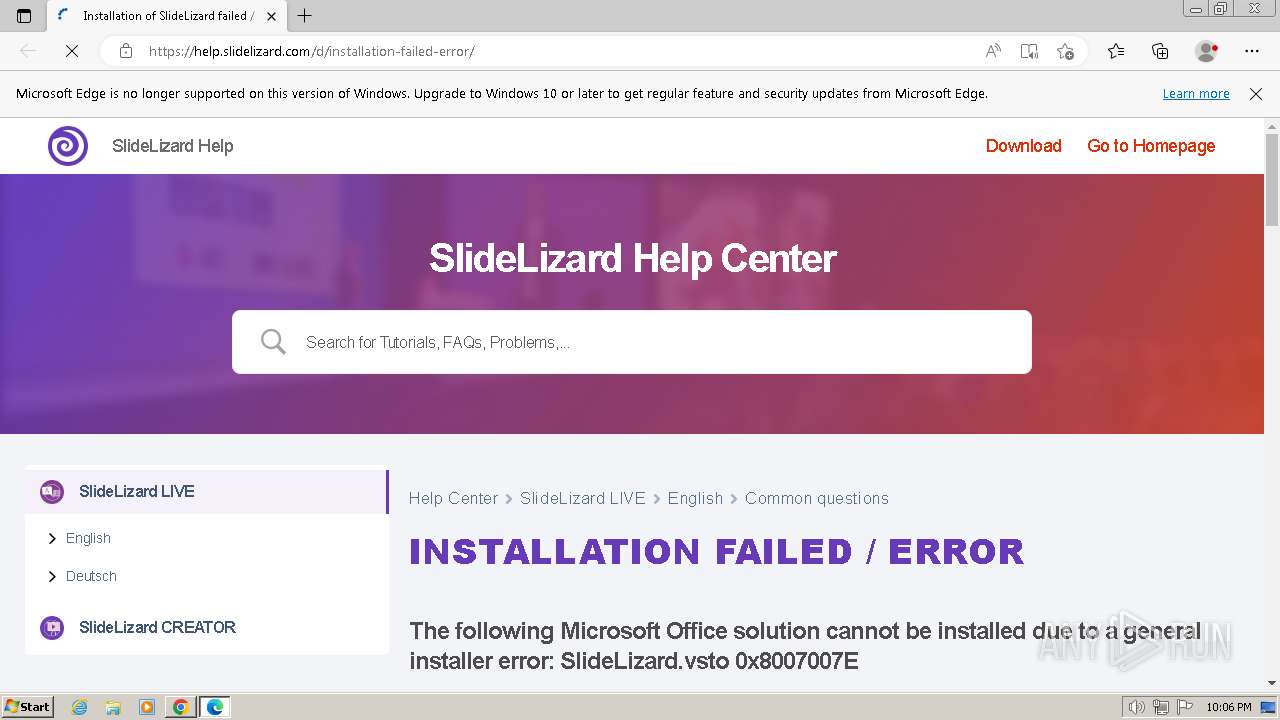
help.slidelizard.com |
| unknown |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3412 | msedge.exe | Potential Corporate Privacy Violation | AV POLICY Observed TikTok Domain in TLS SNI (tiktok.com) |
Process | Message |
|---|---|
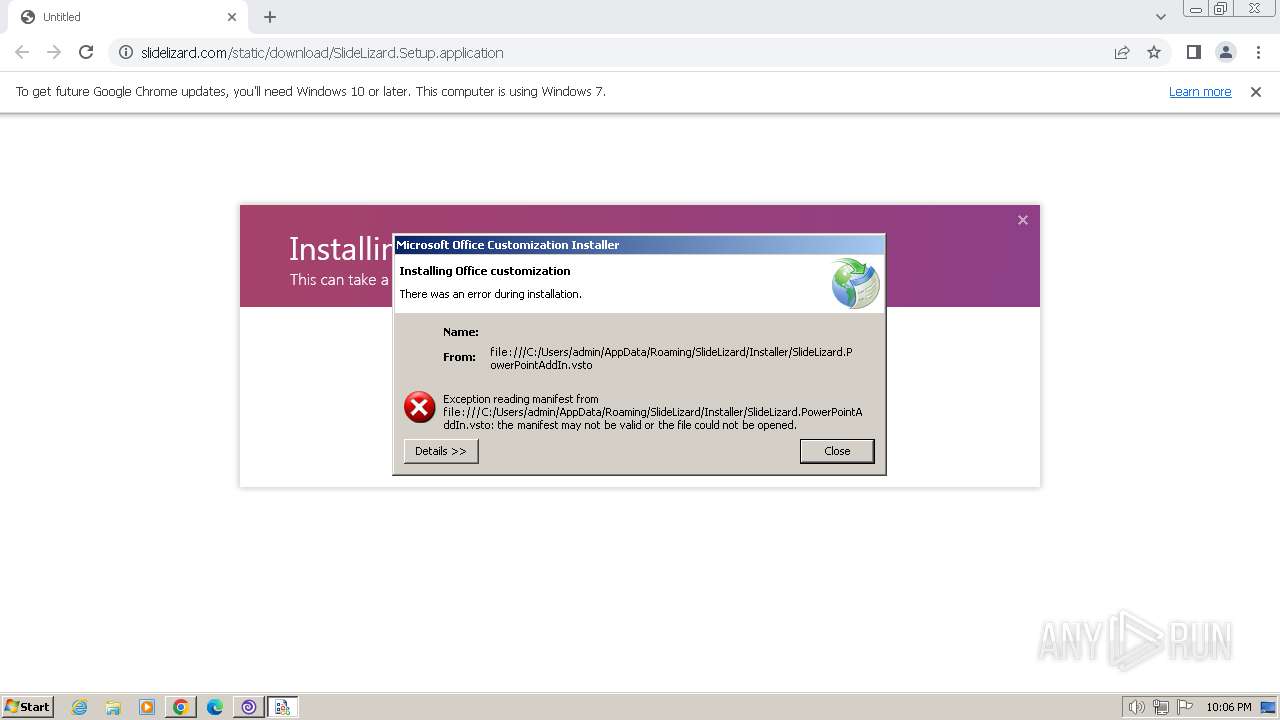
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|