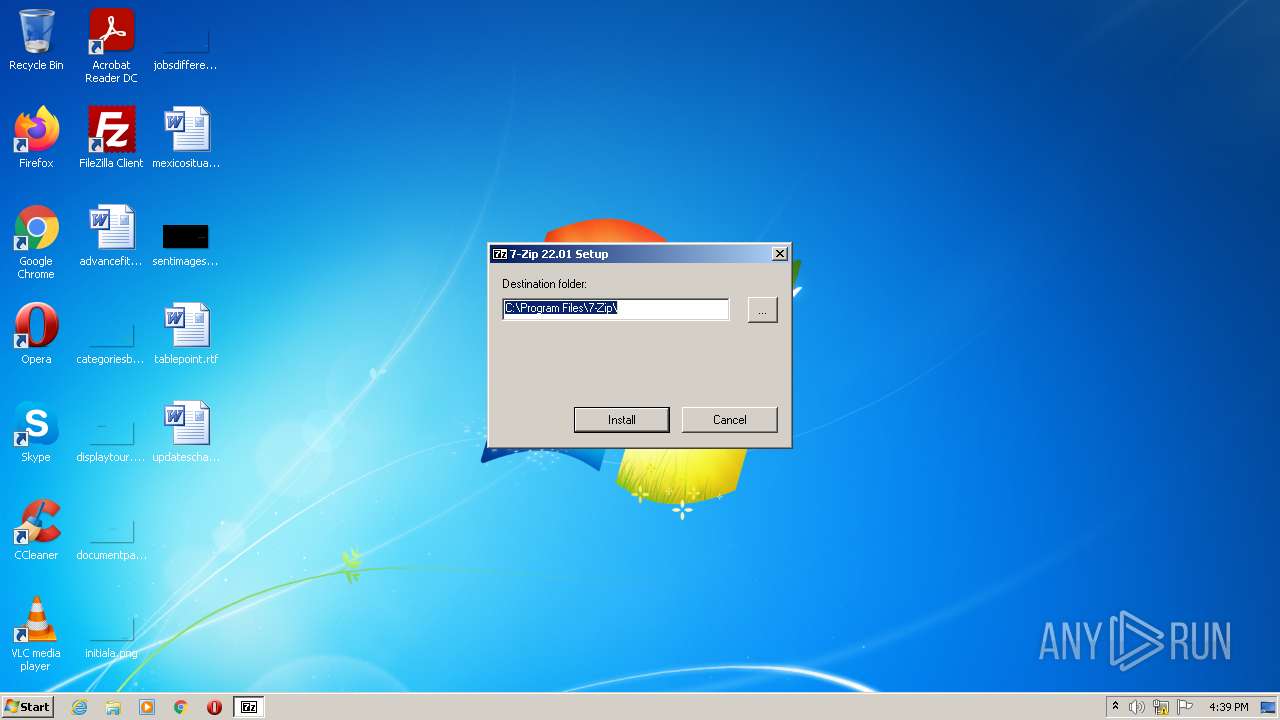
| File name: | 7z2201.exe |
| Full analysis: | https://app.any.run/tasks/7e5a6e47-699e-4764-87ef-45f4874e08c0 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2022, 15:39:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 734E95CDBE04F53FE7C28EEAAAAD7327 |
| SHA1: | E49A4D750F83BC81D79F1C4C3F3648A817C7D3DA |
| SHA256: | 8C8FBCF80F0484B48A07BD20E512B103969992DBF81B6588832B08205E3A1B43 |
| SSDEEP: | 24576:wcLNixBMj+/A2d+mN6MsByRD7v0FLVIj6+7gIlUZC7kYeNp7Dmfuk1TO04:wc1j+/BXo5o5MA6VI97kHto94 |
MALICIOUS
Application was dropped or rewritten from another process
- 7zFM.exe (PID: 1472)
Drops executable file immediately after starts
- 7z2201.exe (PID: 1672)
SUSPICIOUS
Checks supported languages
- 7z2201.exe (PID: 1672)
- 7zFM.exe (PID: 1472)
Reads the computer name
- 7z2201.exe (PID: 1672)
- 7zFM.exe (PID: 1472)
Creates/Modifies COM task schedule object
- 7z2201.exe (PID: 1672)
Creates a software uninstall entry
- 7z2201.exe (PID: 1672)
Drops a file with a compile date too recent
- 7z2201.exe (PID: 1672)
Creates a directory in Program Files
- 7z2201.exe (PID: 1672)
Executable content was dropped or overwritten
- 7z2201.exe (PID: 1672)
Creates files in the program directory
- 7z2201.exe (PID: 1672)
INFO
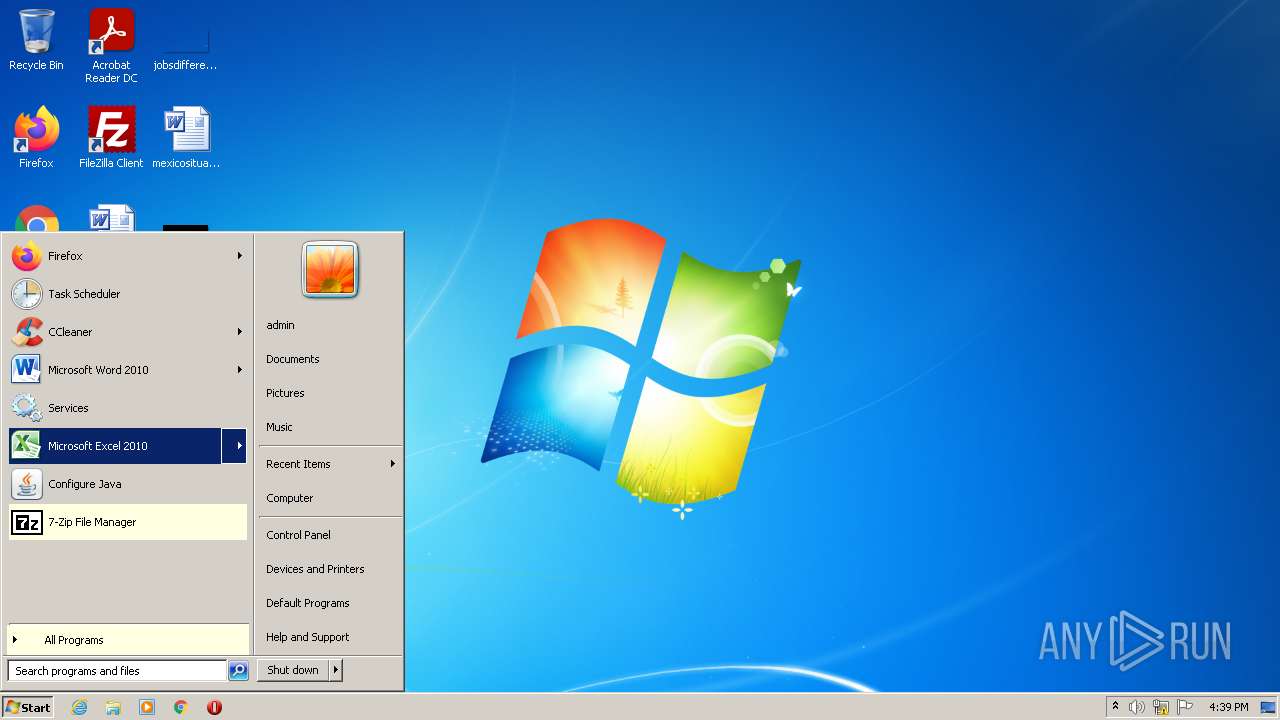
Manual execution by user
- 7zFM.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 22.01 |
|---|---|
| ProductName: | 7-Zip |
| OriginalFileName: | 7zipInstall.exe |
| LegalCopyright: | Copyright (c) 1999-2022 Igor Pavlov |
| InternalName: | 7zipInstall |
| FileVersion: | 22.01 |
| FileDescription: | 7-Zip Installer |
| CompanyName: | Igor Pavlov |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 22.1.0.0 |
| FileVersionNumber: | 22.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x7444 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 19968 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2022:07:15 18:00:00+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jul-2022 16:00:00 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7-Zip Installer |
| FileVersion: | 22.01 |
| InternalName: | 7zipInstall |
| LegalCopyright: | Copyright (c) 1999-2022 Igor Pavlov |
| OriginalFilename: | 7zipInstall.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 22.01 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Jul-2022 16:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000065DC | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61335 |
.rdata | 0x00008000 | 0x00001308 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59246 |
.data | 0x0000A000 | 0x000028F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x0000D000 | 0x00000FE8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36731 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38456 | 1458 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
100 | 3.19524 | 374 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Program Files\7-Zip\7zFM.exe" | C:\Program Files\7-Zip\7zFM.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 22.01 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\7z2201.exe" | C:\Users\admin\AppData\Local\Temp\7z2201.exe | Explorer.EXE | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 22.01 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\7z2201.exe" | C:\Users\admin\AppData\Local\Temp\7z2201.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 22.01 Modules
| |||||||||||||||
Total events
443
Read events
416
Write events
27
Delete events
0
Modification events
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip |
| Operation: | write | Name: | Path32 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path32 |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\7-Zip |
| Operation: | write | Name: | Path |
Value: C:\Program Files\7-Zip\ | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000} |
| Operation: | write | Name: | (default) |
Value: 7-Zip Shell Extension | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\7-Zip\7-zip.dll | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{23170F69-40C1-278A-1000-000100020000}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shellex\ContextMenuHandlers\7-Zip |
| Operation: | write | Name: | (default) |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Directory\shellex\ContextMenuHandlers\7-Zip |
| Operation: | write | Name: | (default) |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
| (PID) Process: | (1672) 7z2201.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Folder\ShellEx\ContextMenuHandlers\7-Zip |
| Operation: | write | Name: | (default) |
Value: {23170F69-40C1-278A-1000-000100020000} | |||
Executable files
8
Suspicious files
0
Text files
97
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\History.txt | text | |
MD5:B1206A5ABF93BC64601A3CAA2DFF47D4 | SHA256:24A8A7C00F0BB8AC3096F58F53BD47FA392B8D220C1C43D372100BD692C68E5F | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\descript.ion | text | |
MD5:EB7E322BDC62614E49DED60E0FB23845 | SHA256:1DA513F5A4E8018B9AE143884EB3EAF72454B606FD51F2401B7CFD9BE4DBBF4F | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\bn.txt | text | |
MD5:D0E788F64268D15B4391F052B1F4B18A | SHA256:216CC780E371DC318C8B15B84DE8A5EC0E28F712B3109A991C8A09CDDAA2A81A | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\7-zip.chm | chm | |
MD5:34208890A28244903621CD32CC3FBDFC | SHA256:4B6939646570C9DDB5BFD39B8503EED99D8C64337E72F6DD4F9DDCFB4AC76703 | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\an.txt | text | |
MD5:BF8564B2DAD5D2506887F87AEE169A0A | SHA256:0E8DD119DFA6C6C1B3ACA993715092CDF1560947871092876D309DBC1940A14A | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\ba.txt | text | |
MD5:D83B65AC086DA0C94D6EB57BEE669C2B | SHA256:2901B54F7621C95429658CB4EDB28ABD0CB5B6E257C7D9A364FC468A8B86BAAE | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\ar.txt | text | |
MD5:1C45E6A6ECB3B71A7316C466B6A77C1C | SHA256:972261B53289DE2BD8A65E787A6E7CD6DEFC2B5F7E344128F2FE0492ED30CCF1 | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\bg.txt | text | |
MD5:833AFB4F88FDB5F48245C9B65577DC19 | SHA256:4DCABCC8AB8069DB79143E4C62B6B76D2CF42666A09389EACFC35074B61779E3 | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\ast.txt | text | |
MD5:1F86AE235BC747A279C9E9EC72675CE4 | SHA256:8FCD1B8CE6FED05F406C4B81AEA821132800BC494D3FD6F42A4258A81F8998EC | |||
| 1672 | 7z2201.exe | C:\Program Files\7-Zip\Lang\be.txt | text | |
MD5:3C21135144AC7452E7DB66F0214F9D68 | SHA256:D095879B8BBC67A1C9875C5E9896942BACF730BD76155C06105544408068C59E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report