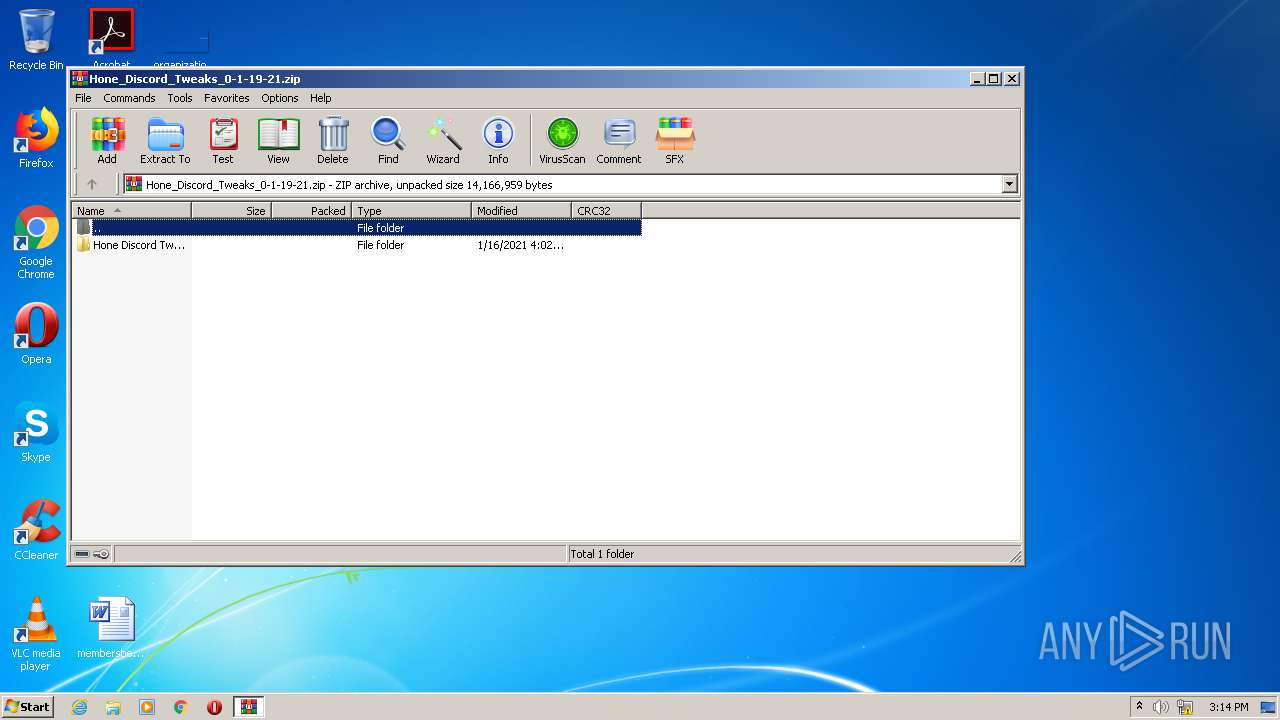
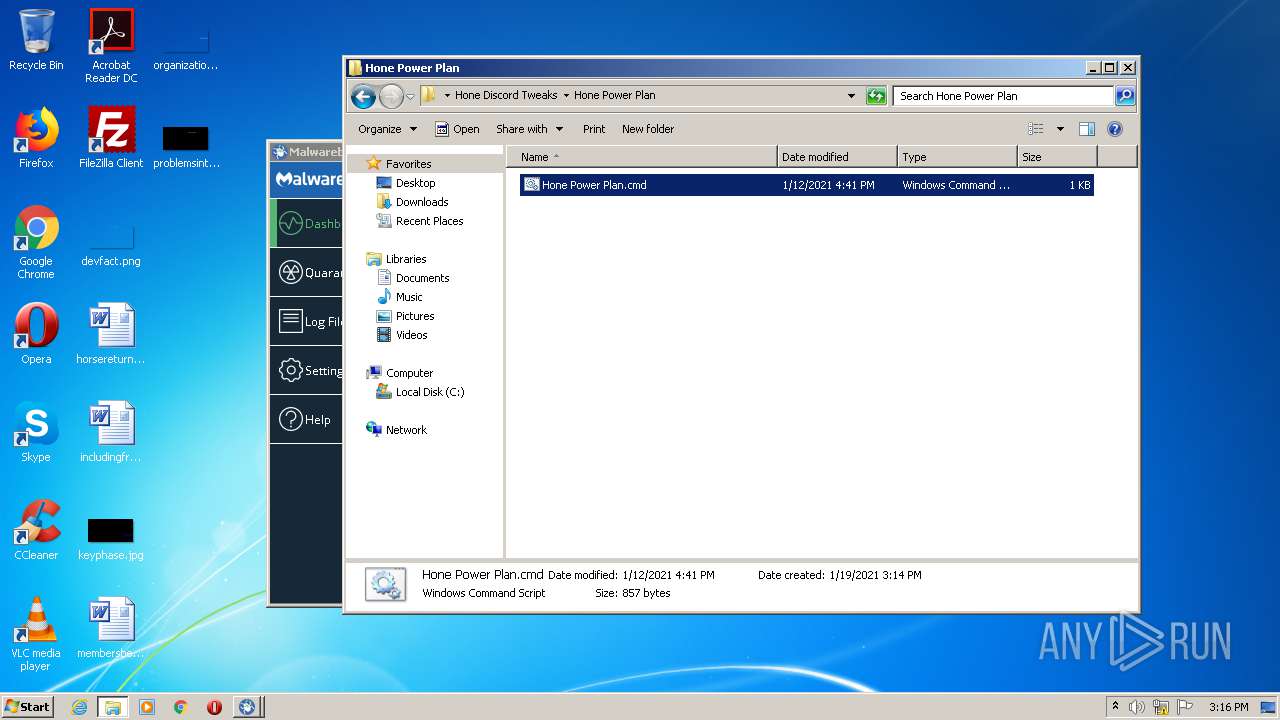
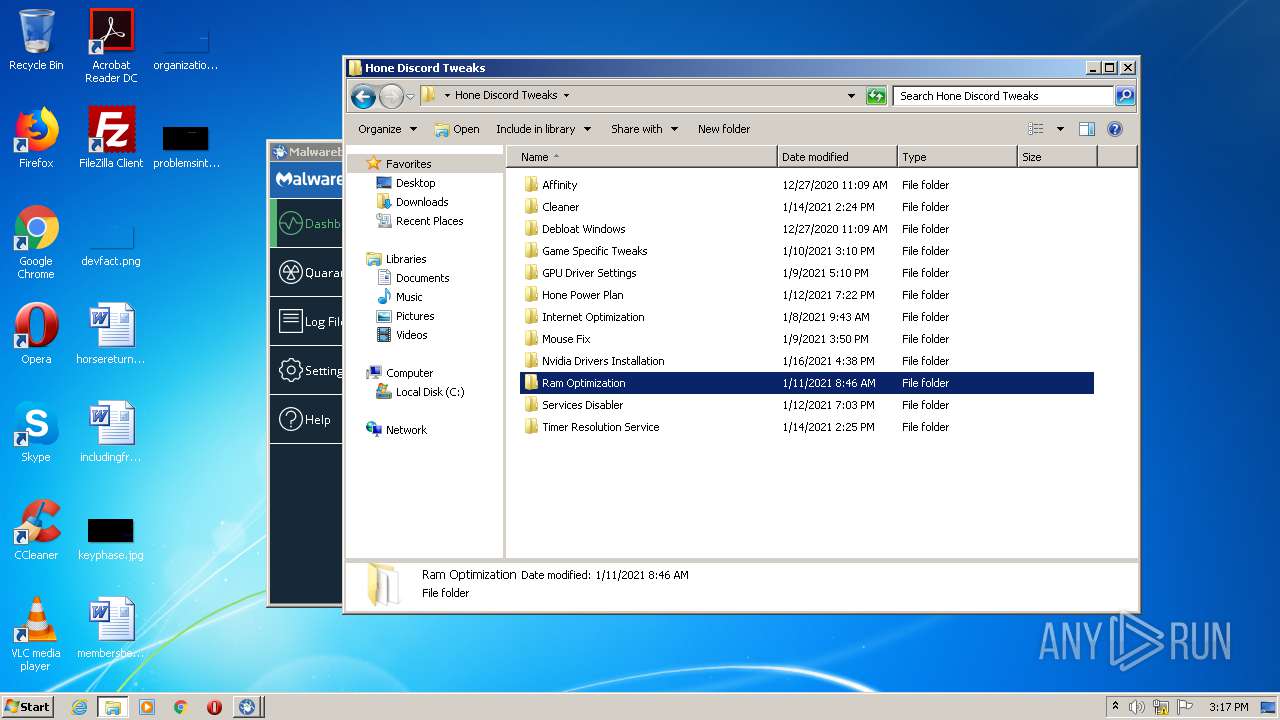
| File name: | Hone_Discord_Tweaks_0-1-19-21.zip |
| Full analysis: | https://app.any.run/tasks/eaeef522-0b76-487c-83ac-f5d6fe38c25f |
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2021, 15:13:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 2B35D5531C69E3B83445709D552AFA30 |
| SHA1: | 5AA5144E8818FE7BA5465CE060100F8E2E09548E |
| SHA256: | 8C81F41794974B02B2BB348FEE4BAF3B1469DFCA41A98638E810A9251437BA3C |
| SSDEEP: | 393216:I2Zi7X8eYO56+E8+6XZ/98X4czCfreMaAK32:0iOY+l+6XZ/9mwreZAKG |
MALICIOUS
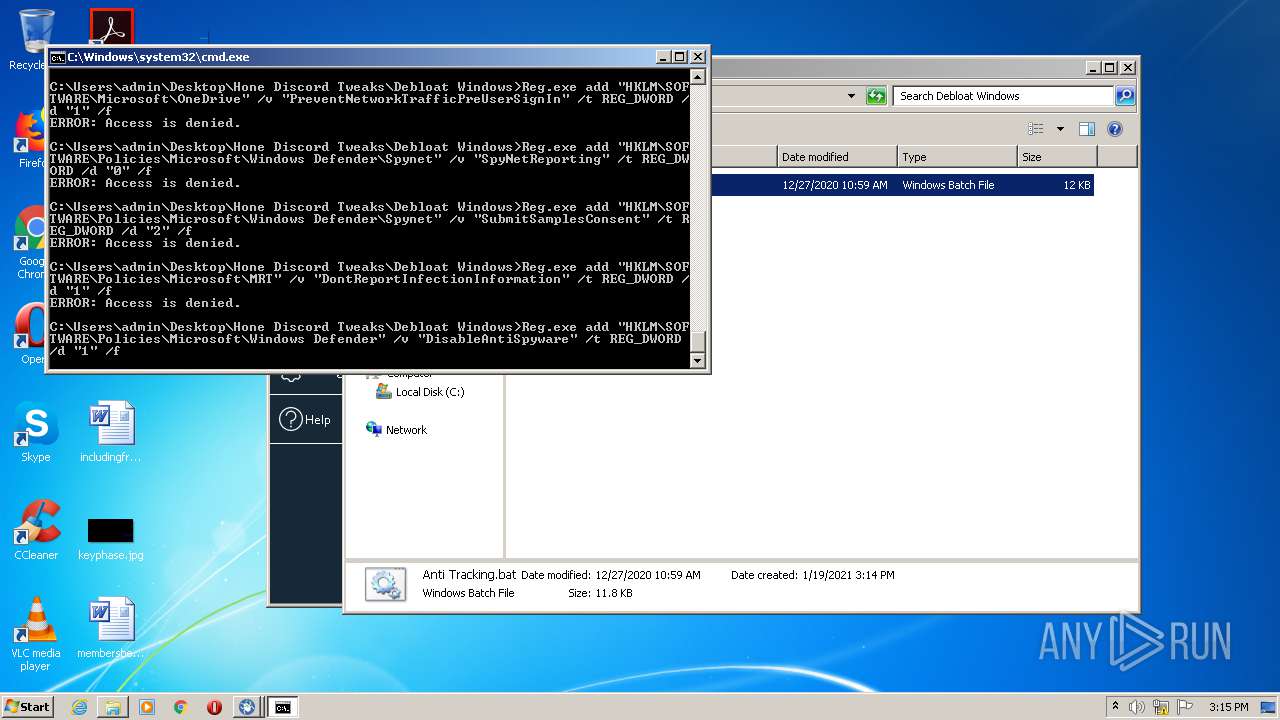
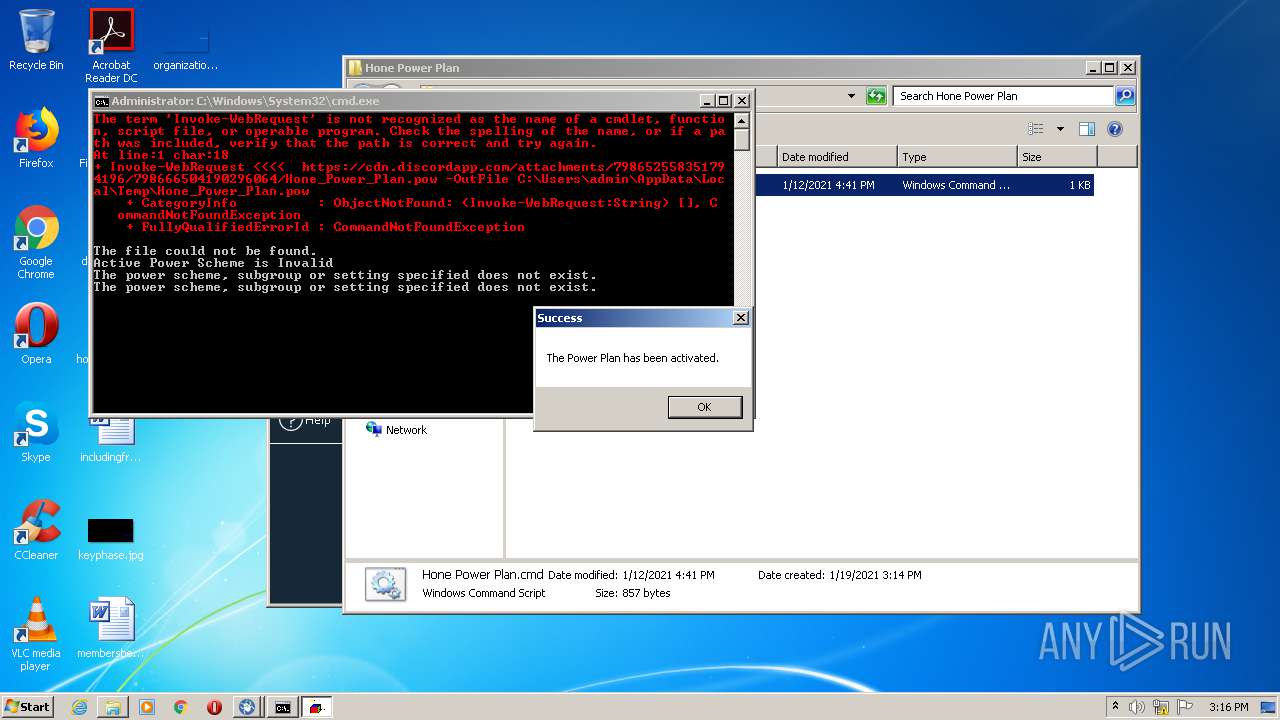
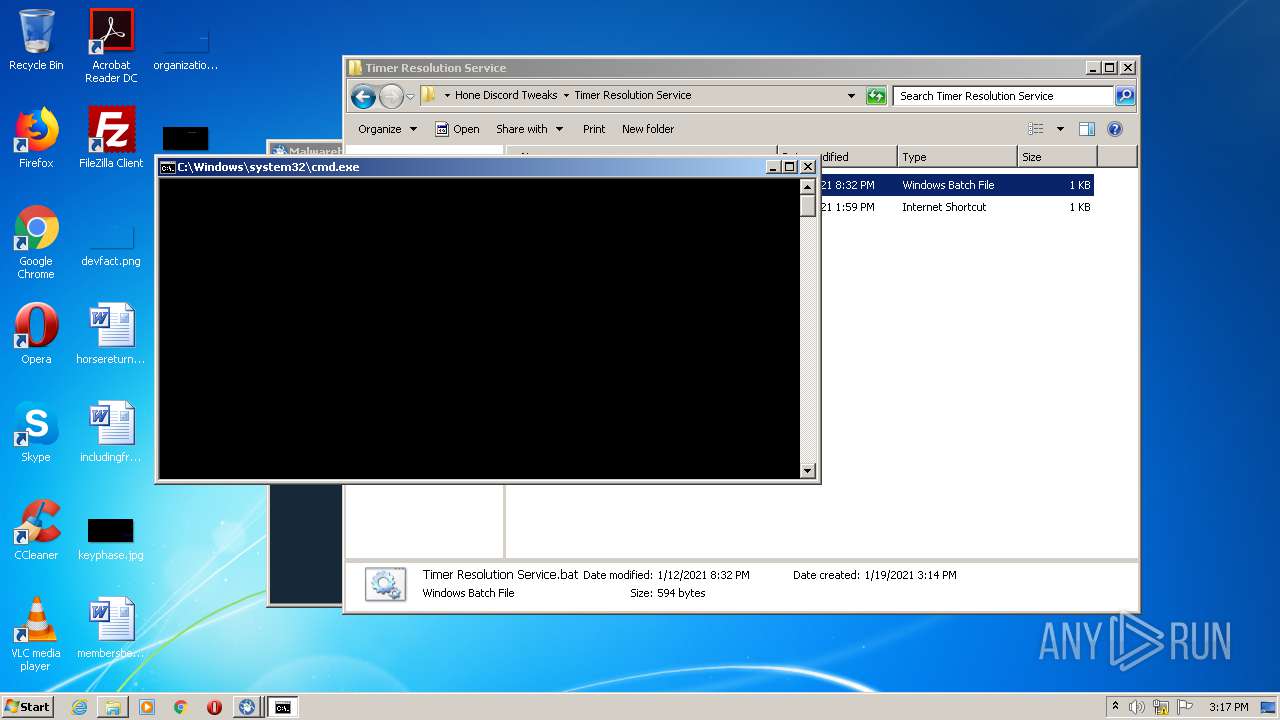
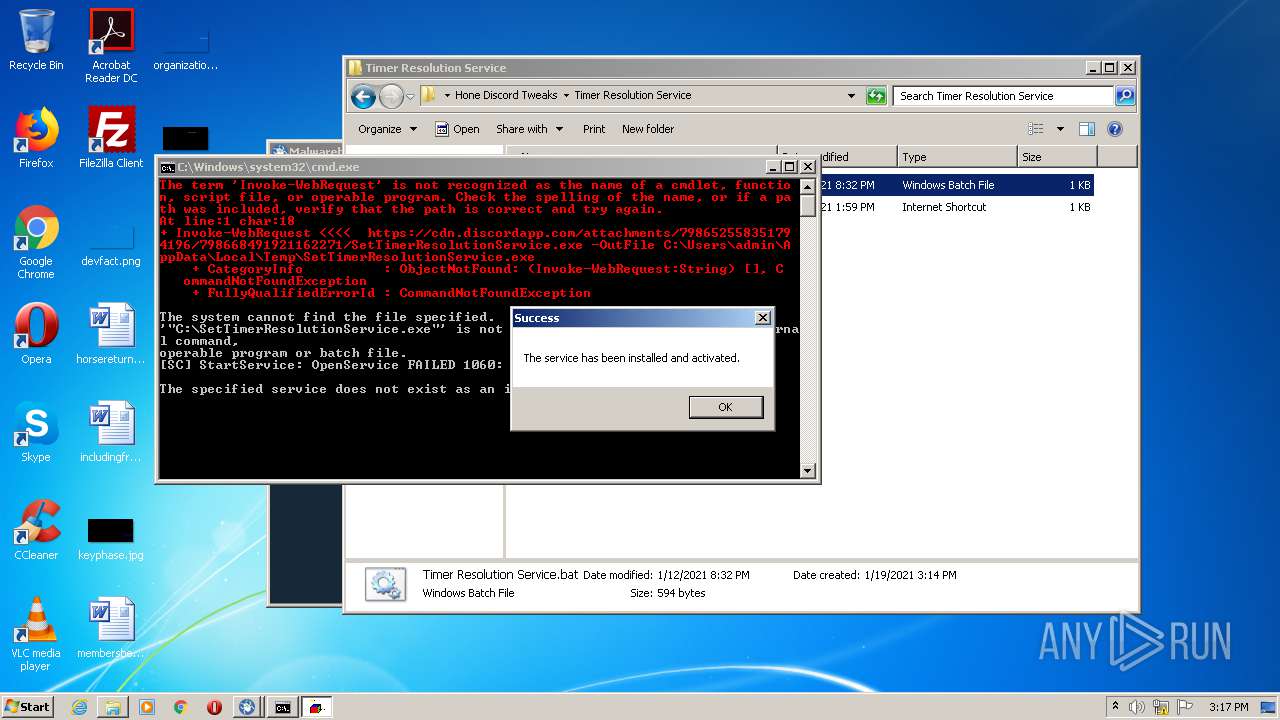
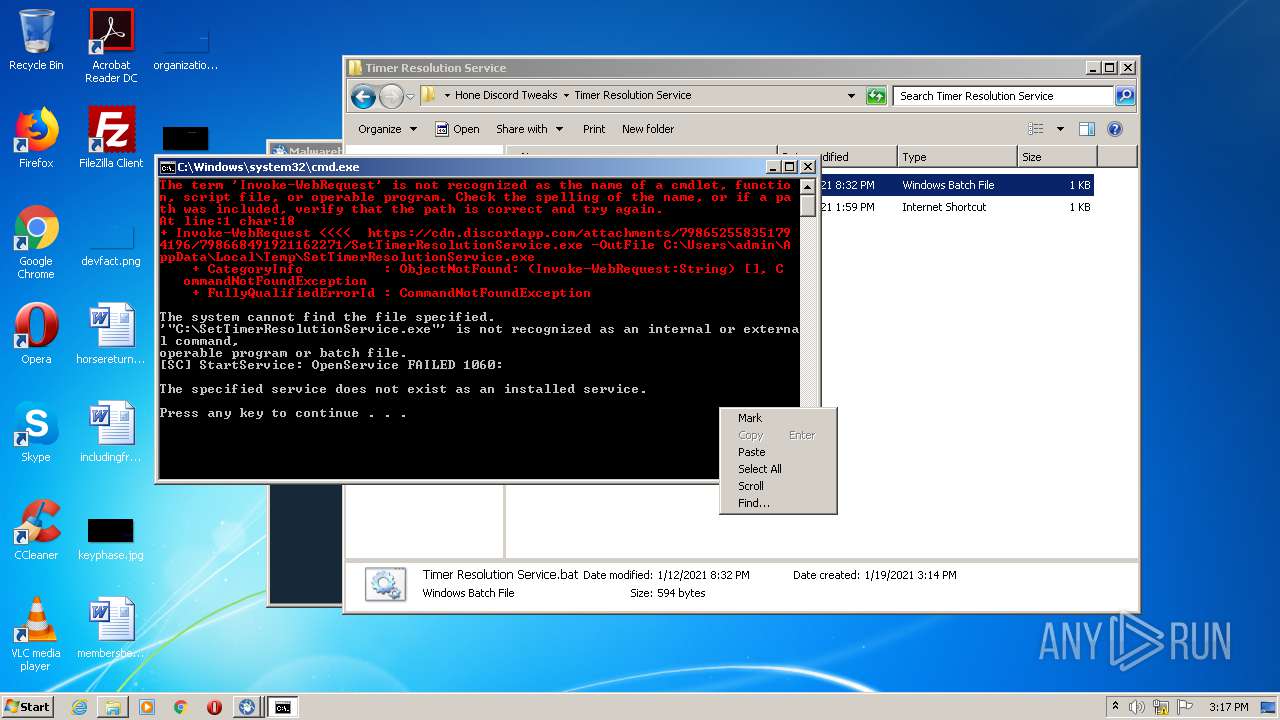
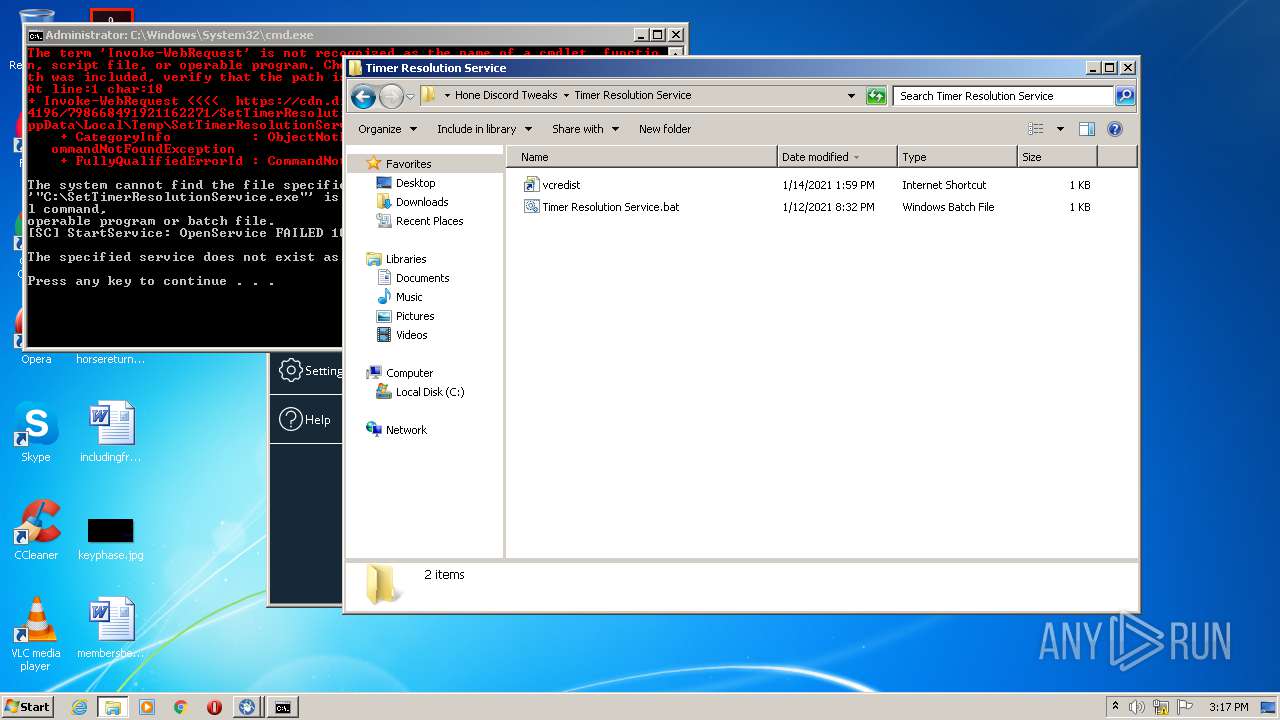
Executes PowerShell scripts
- cmd.exe (PID: 3500)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 2508)
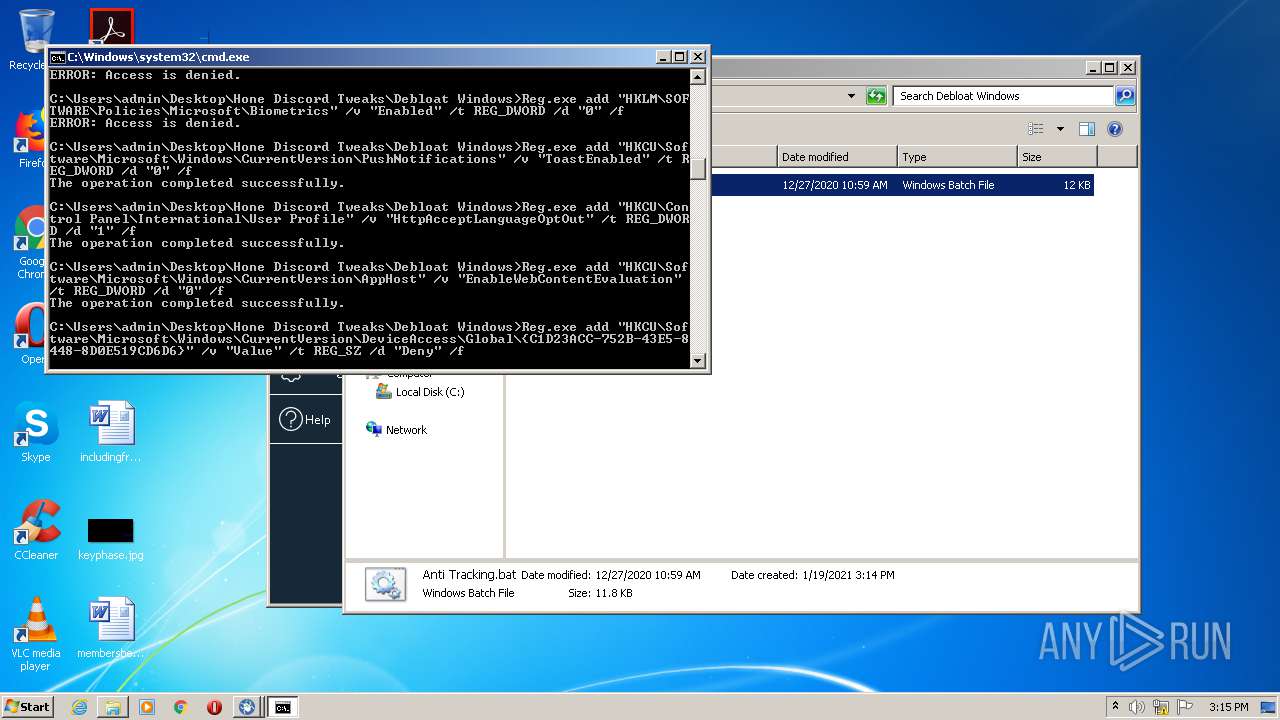
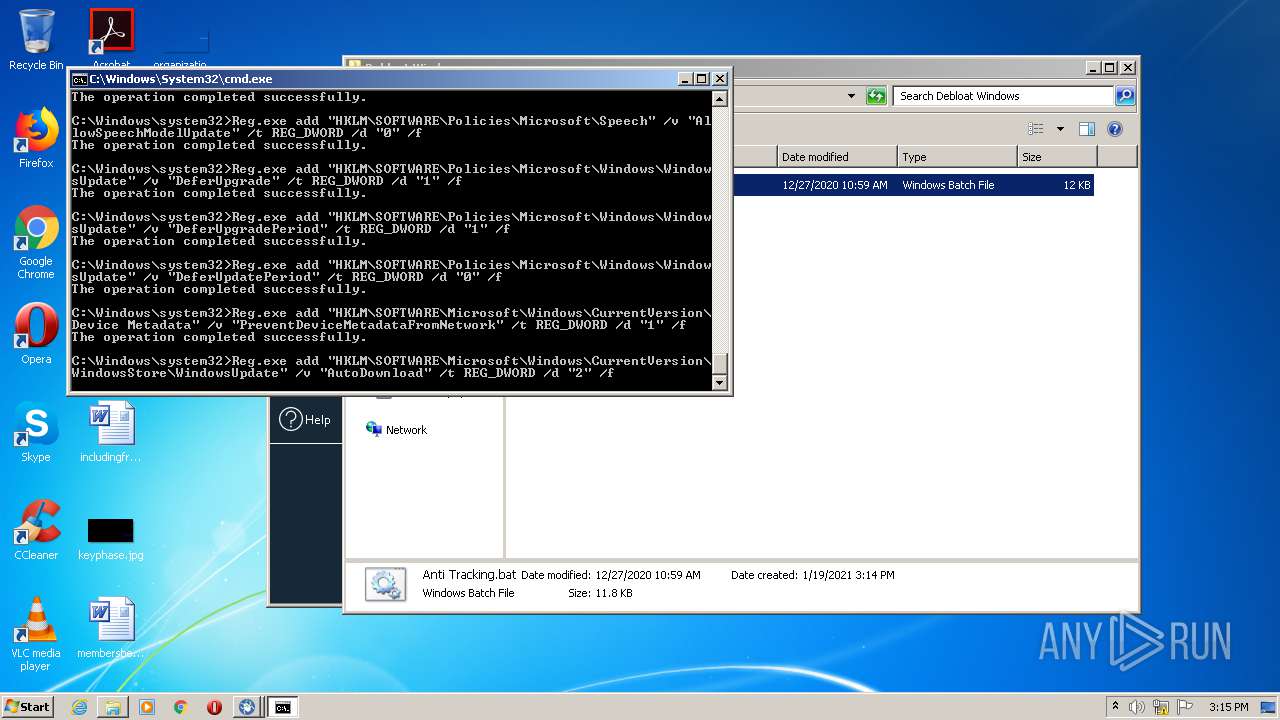
Changes Windows auto-update feature
- reg.exe (PID: 1140)
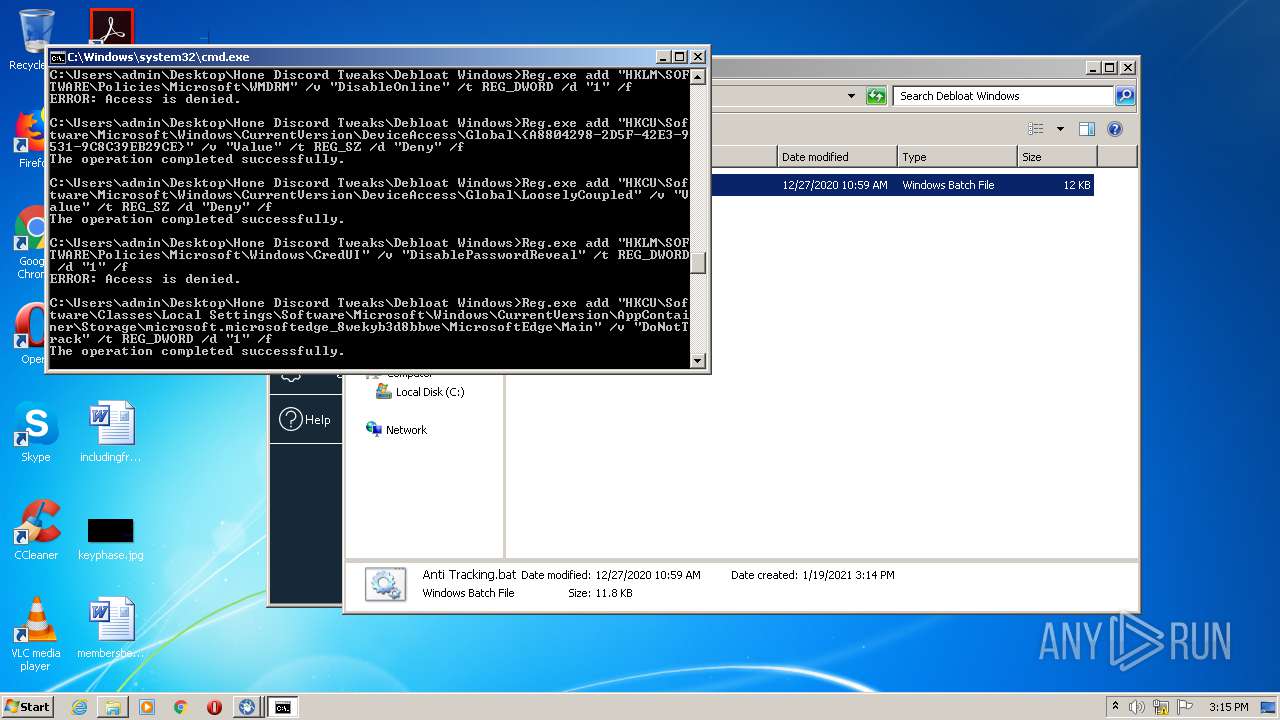
Modifies Windows security services settings
- reg.exe (PID: 3160)
Disables Windows Defender
- reg.exe (PID: 1588)
SUSPICIOUS
Creates or modifies windows services
- reg.exe (PID: 624)
- reg.exe (PID: 3956)
- reg.exe (PID: 3100)
- reg.exe (PID: 2088)
Executes scripts
- cmd.exe (PID: 2508)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 3500)
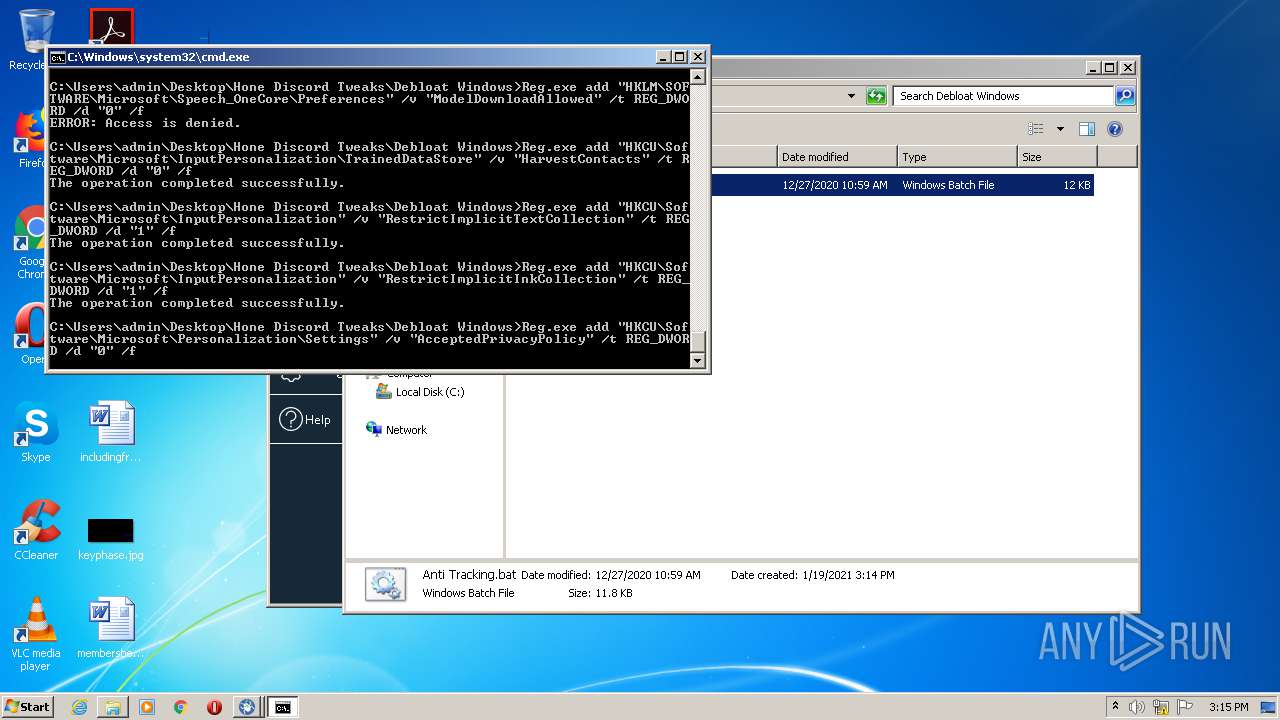
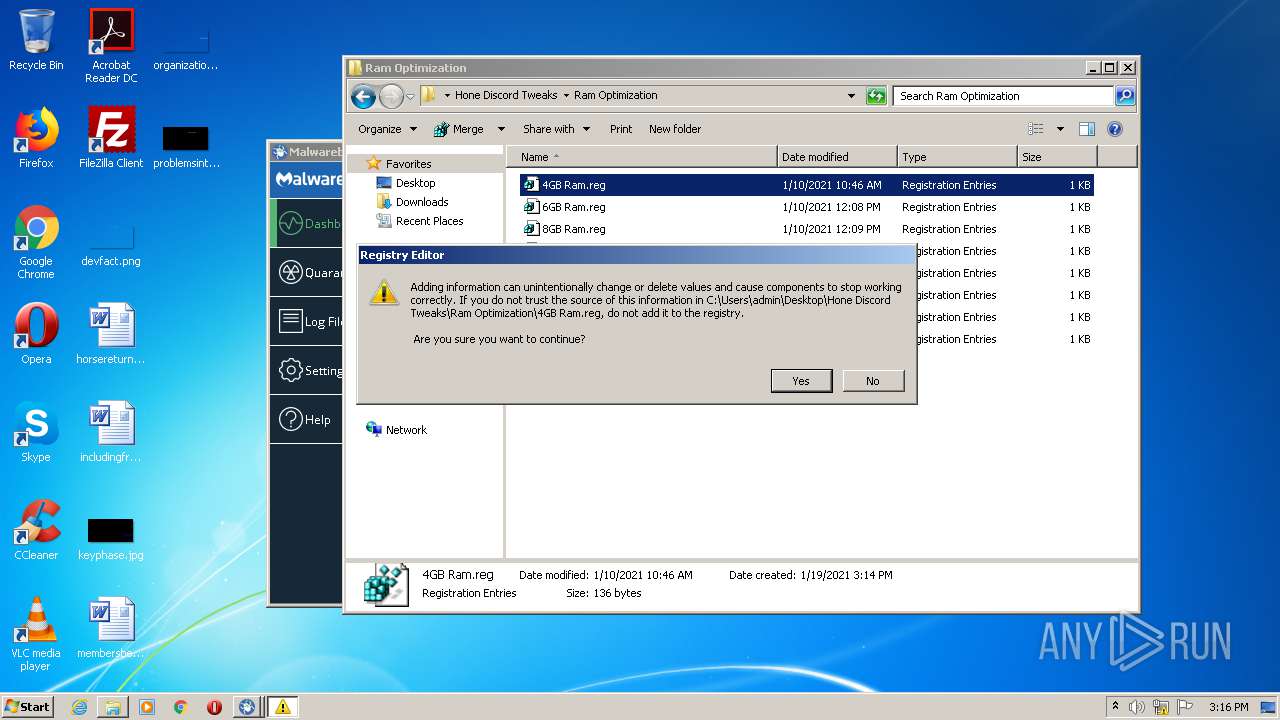
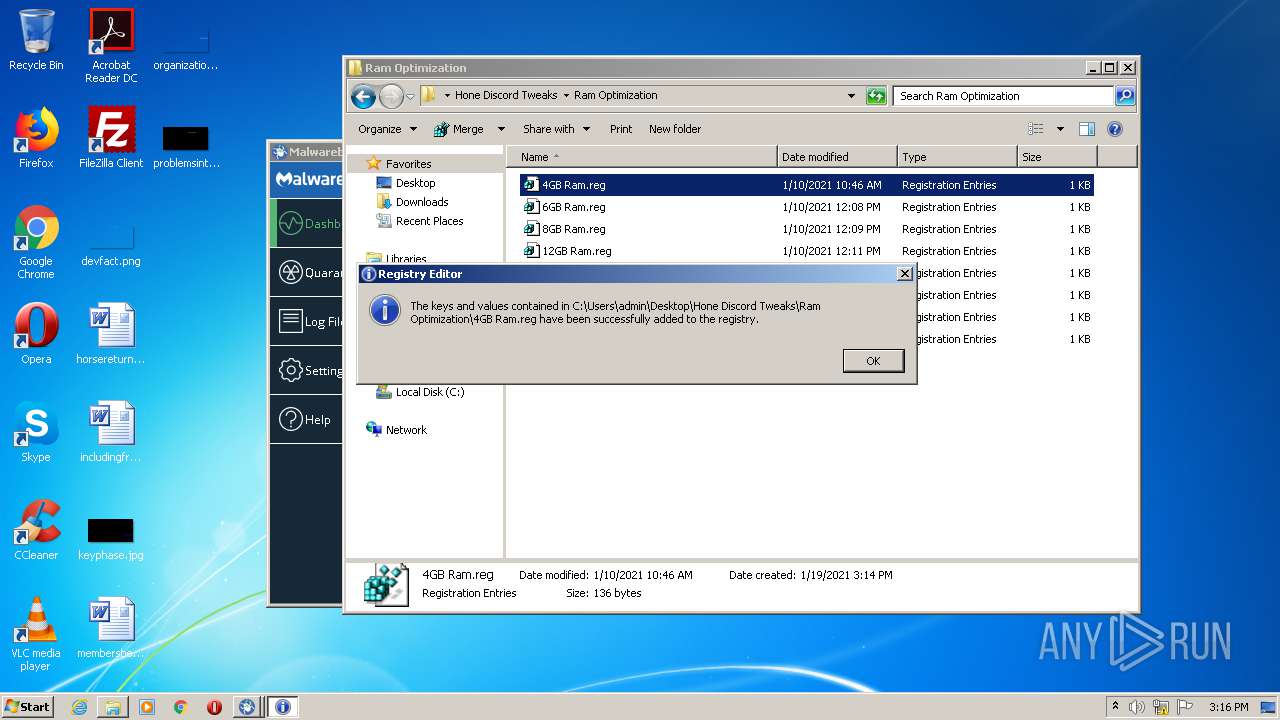
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2156)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3044)
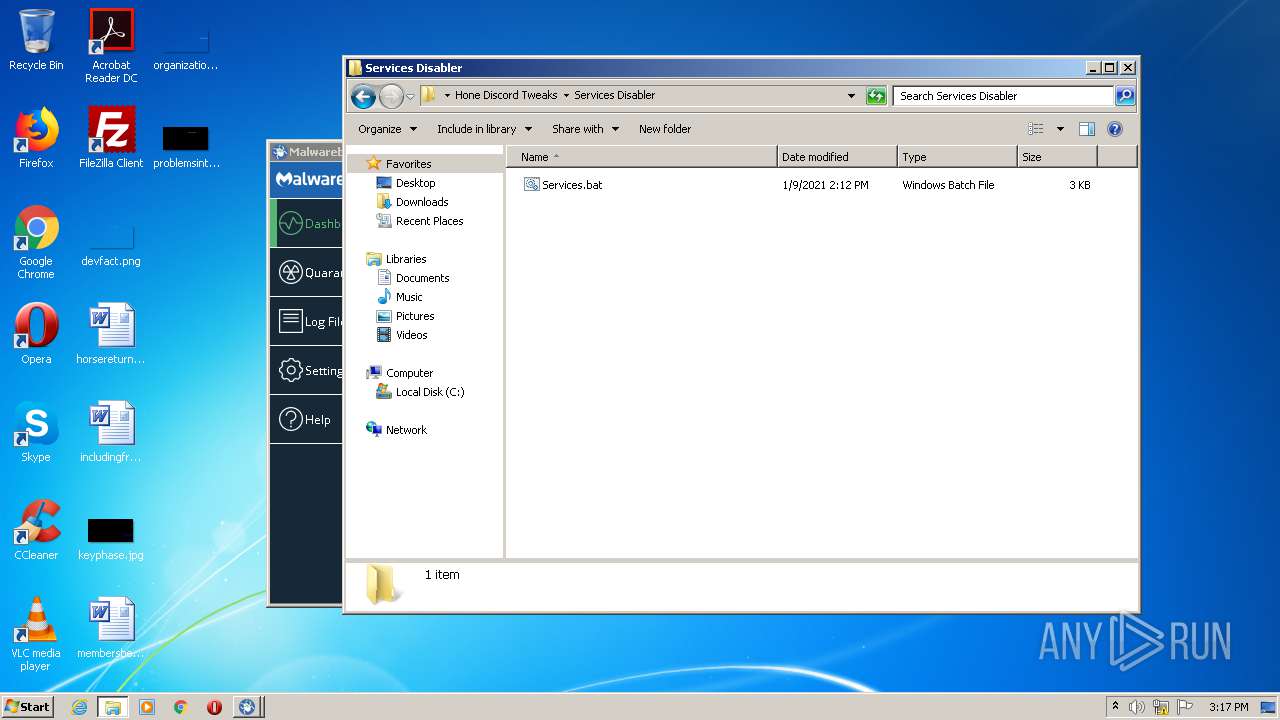
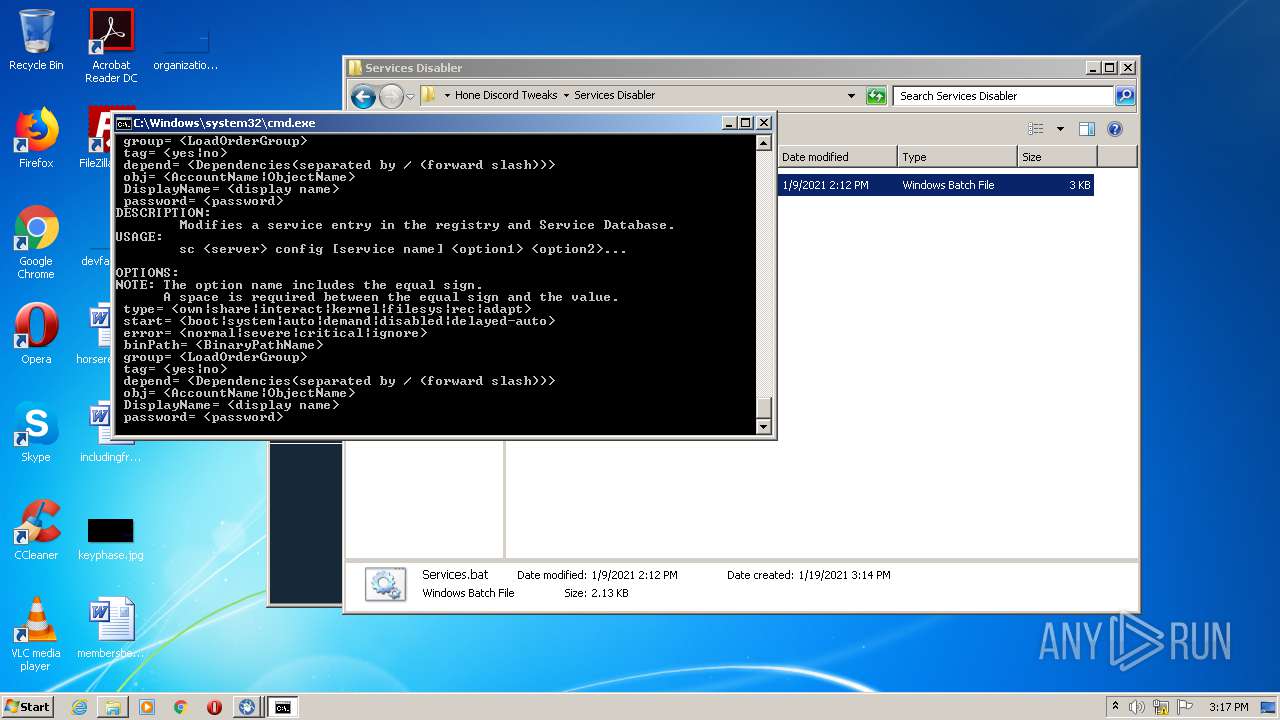
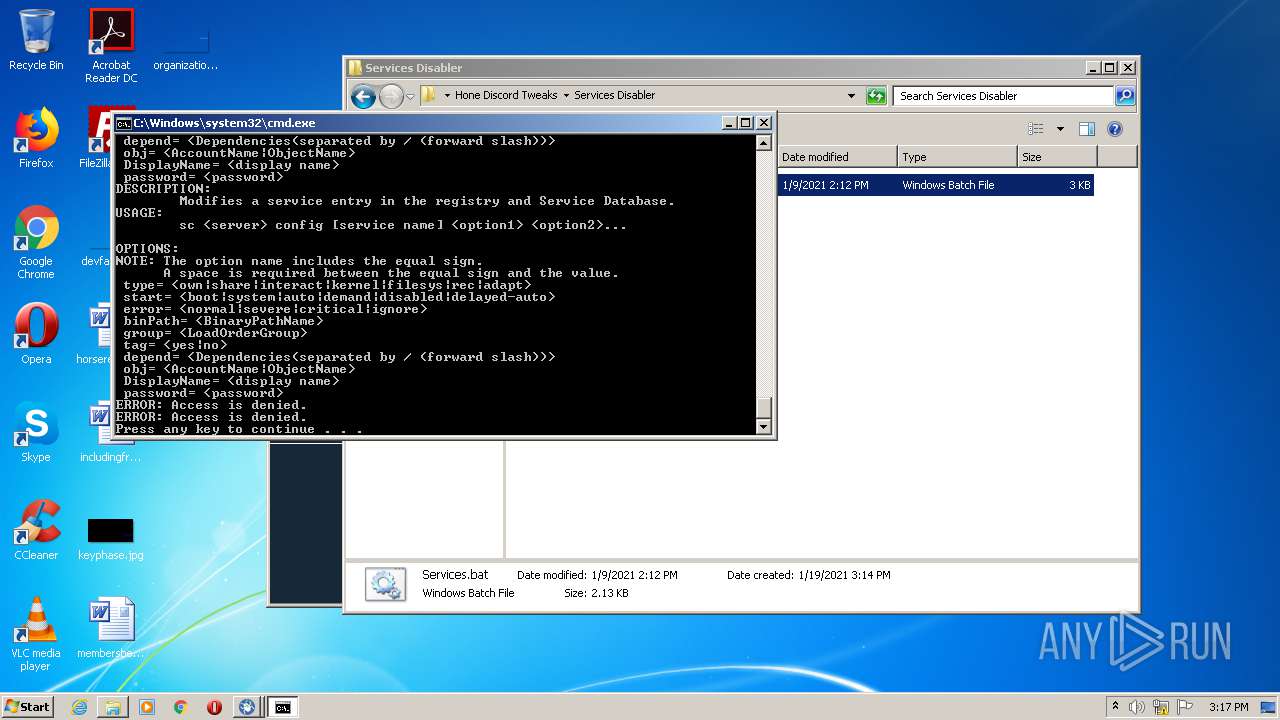
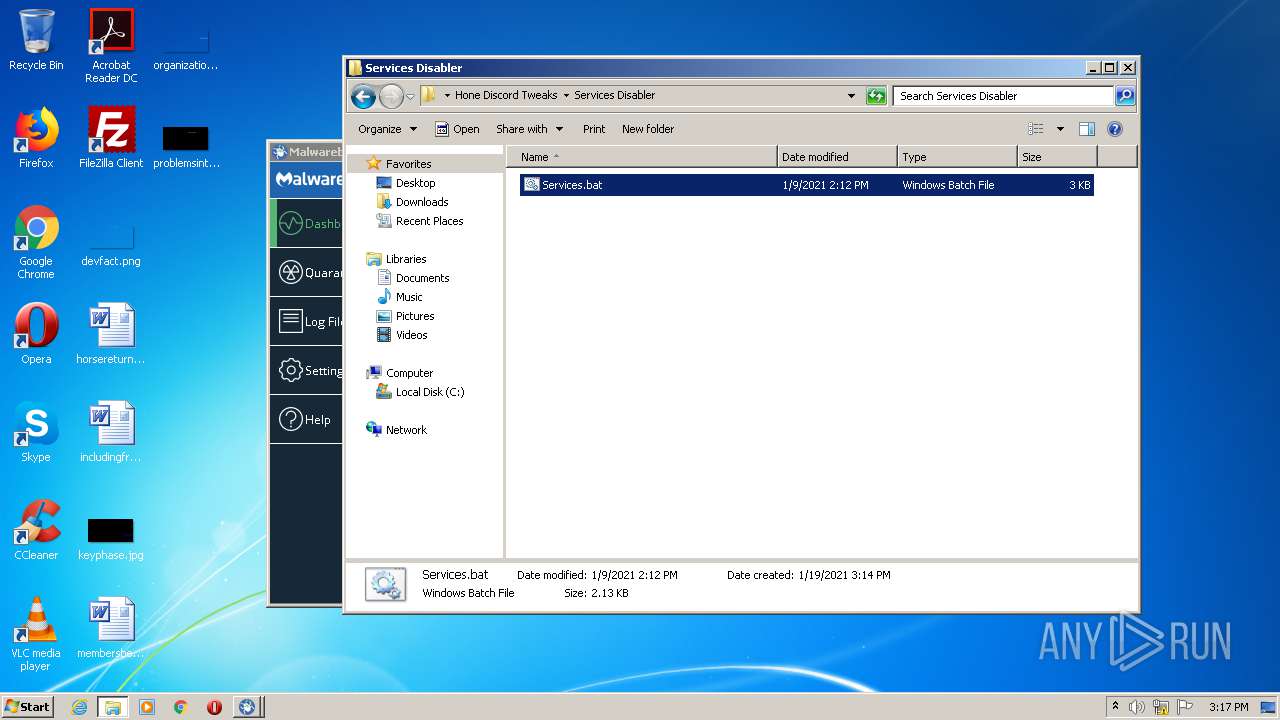
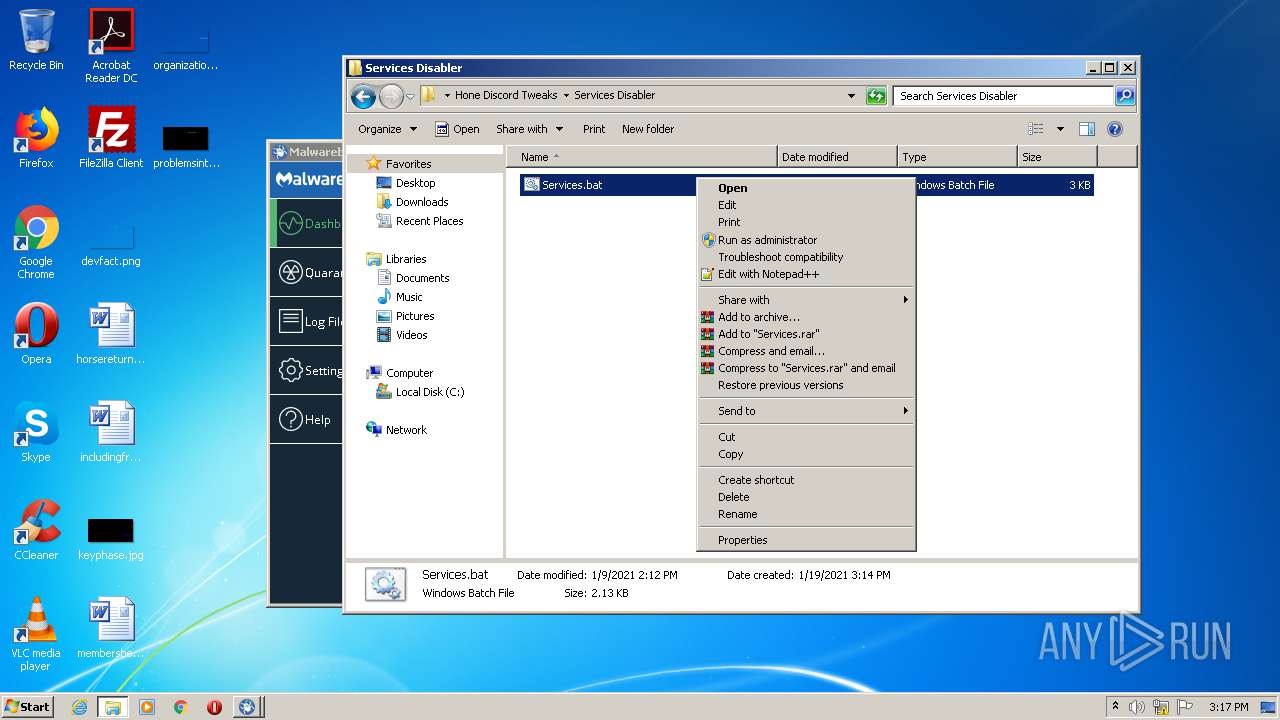
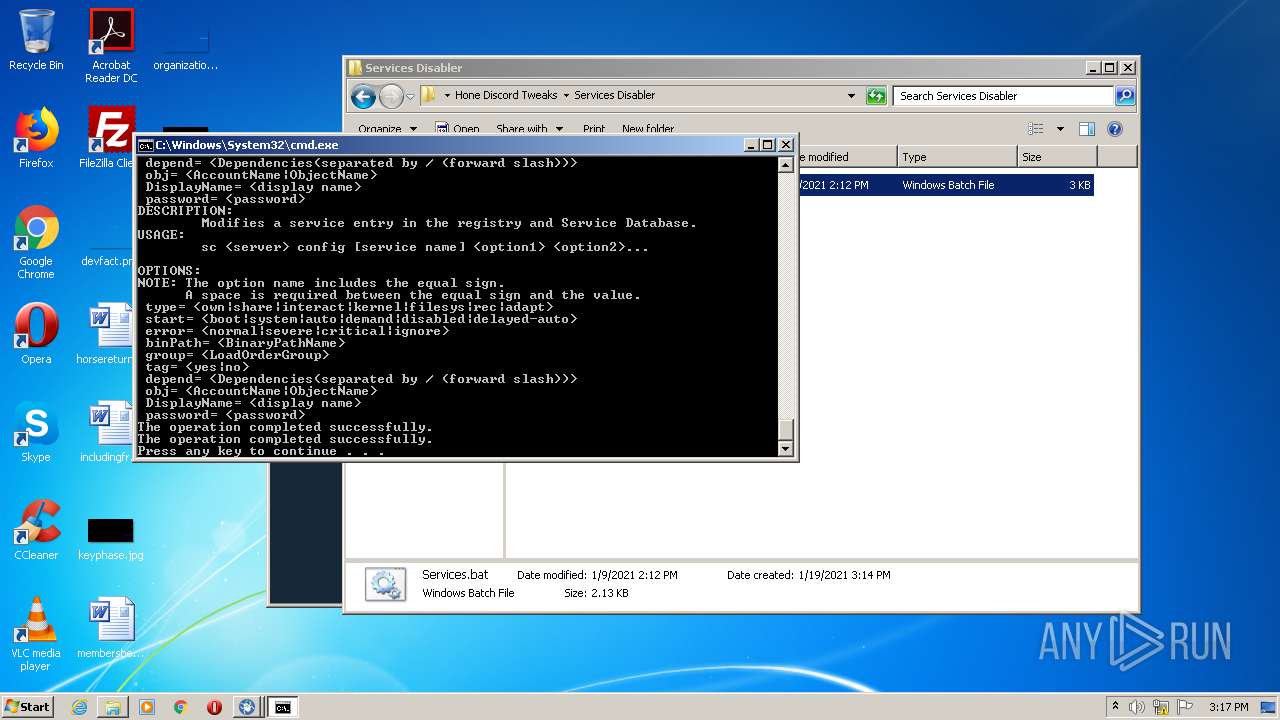
Starts SC.EXE for service management
- cmd.exe (PID: 3044)
- cmd.exe (PID: 2156)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 3764)
Creates files in the user directory
- powershell.exe (PID: 3472)
- powershell.exe (PID: 3560)
- powershell.exe (PID: 2148)
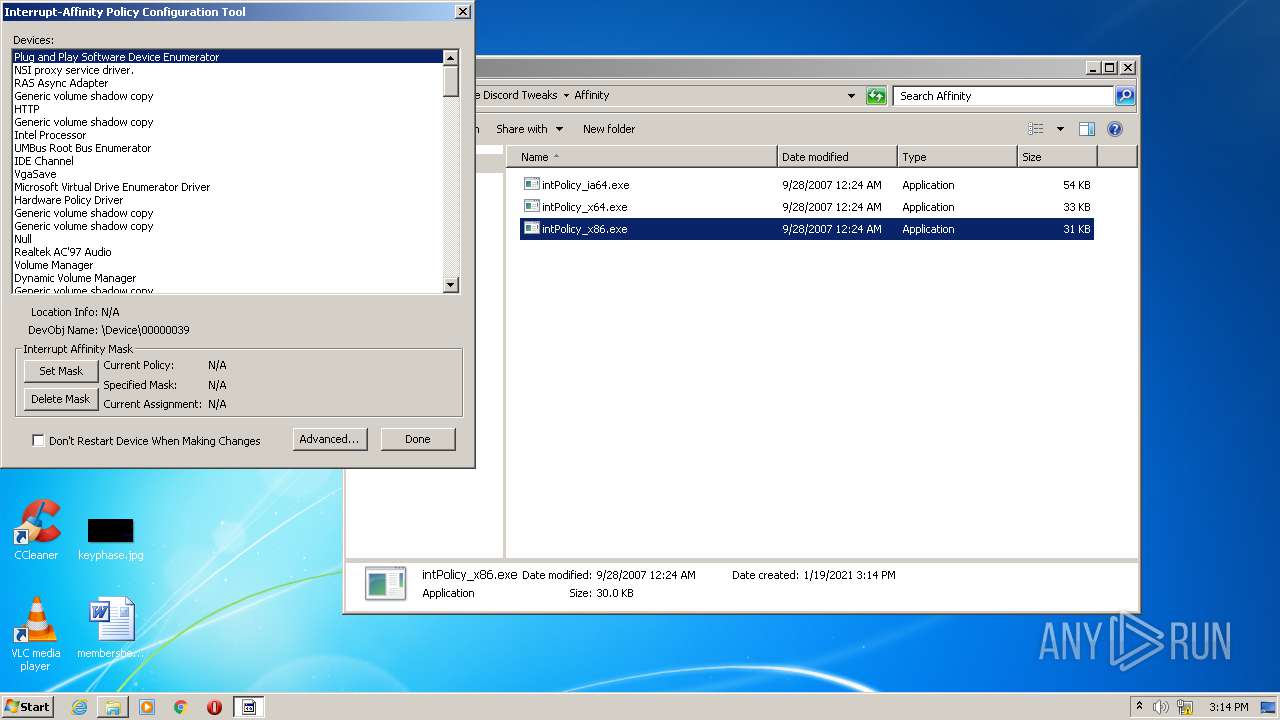
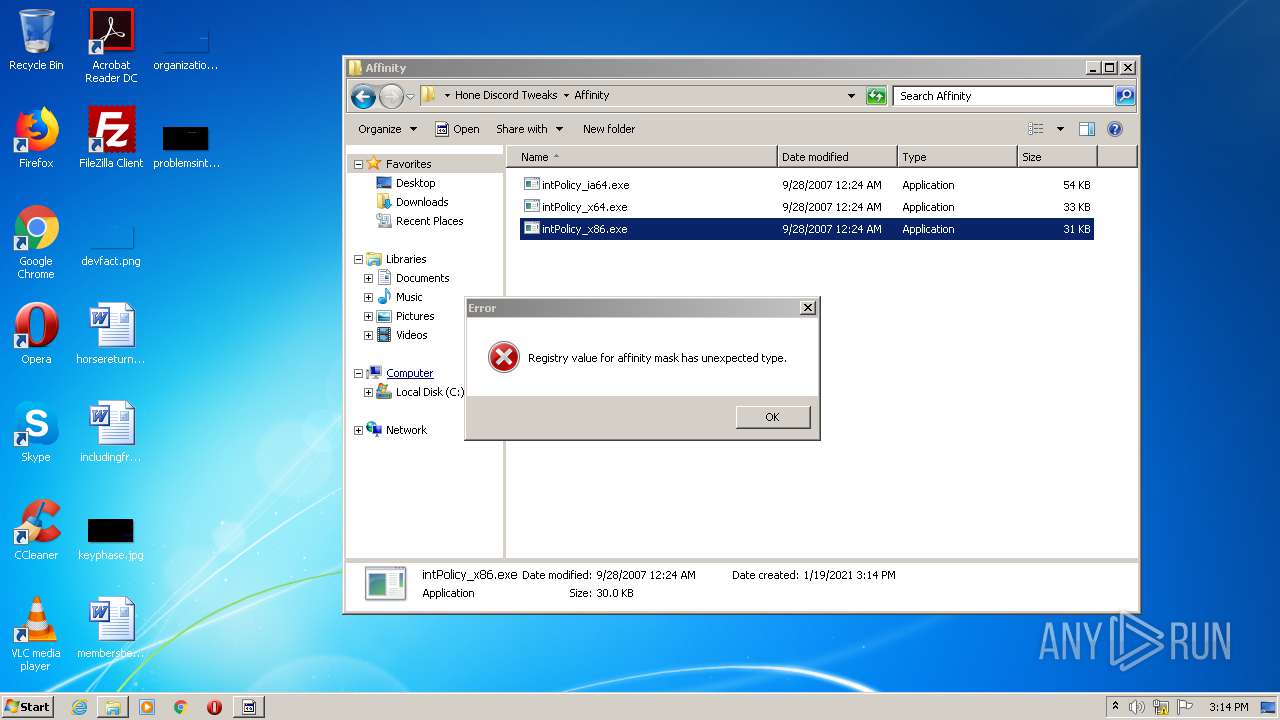
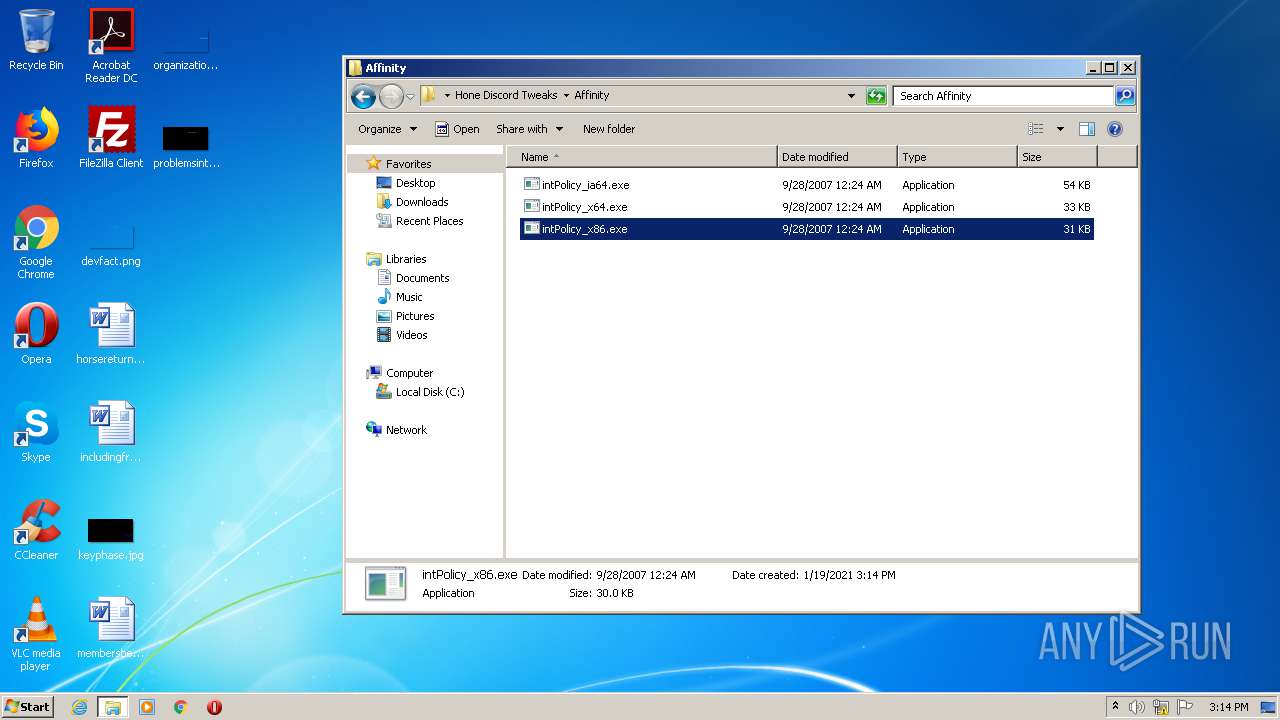
INFO
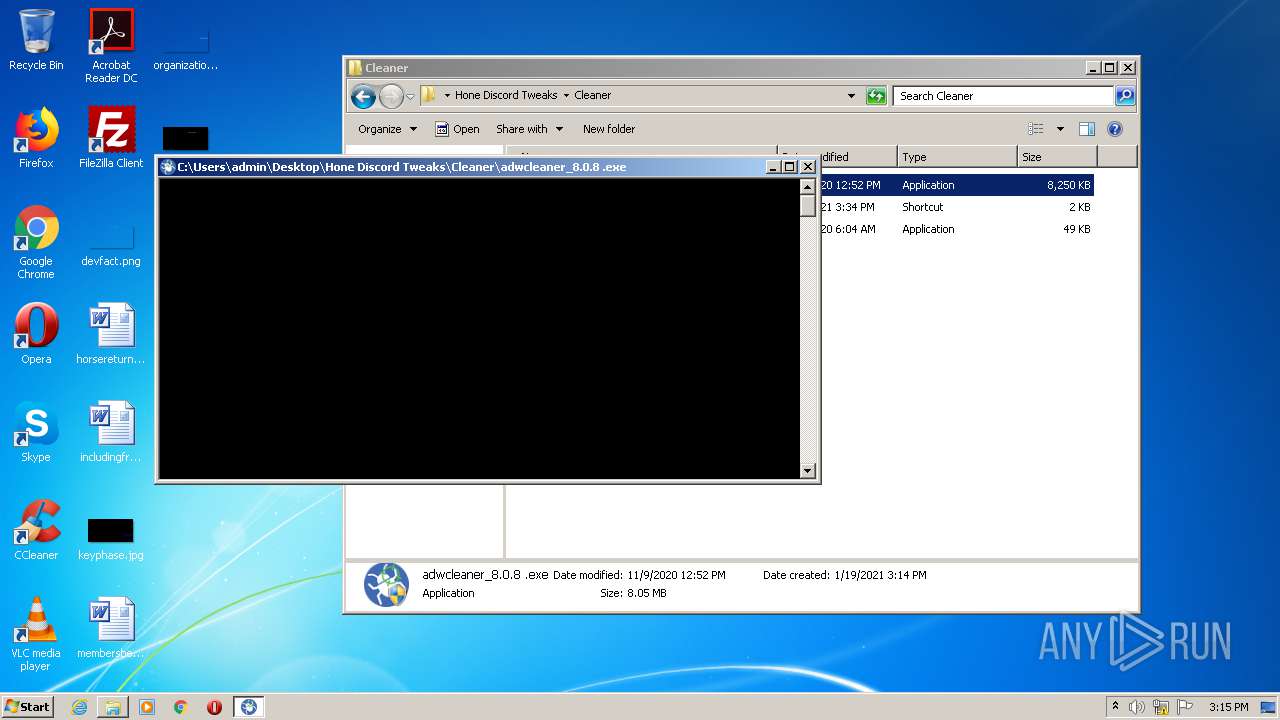
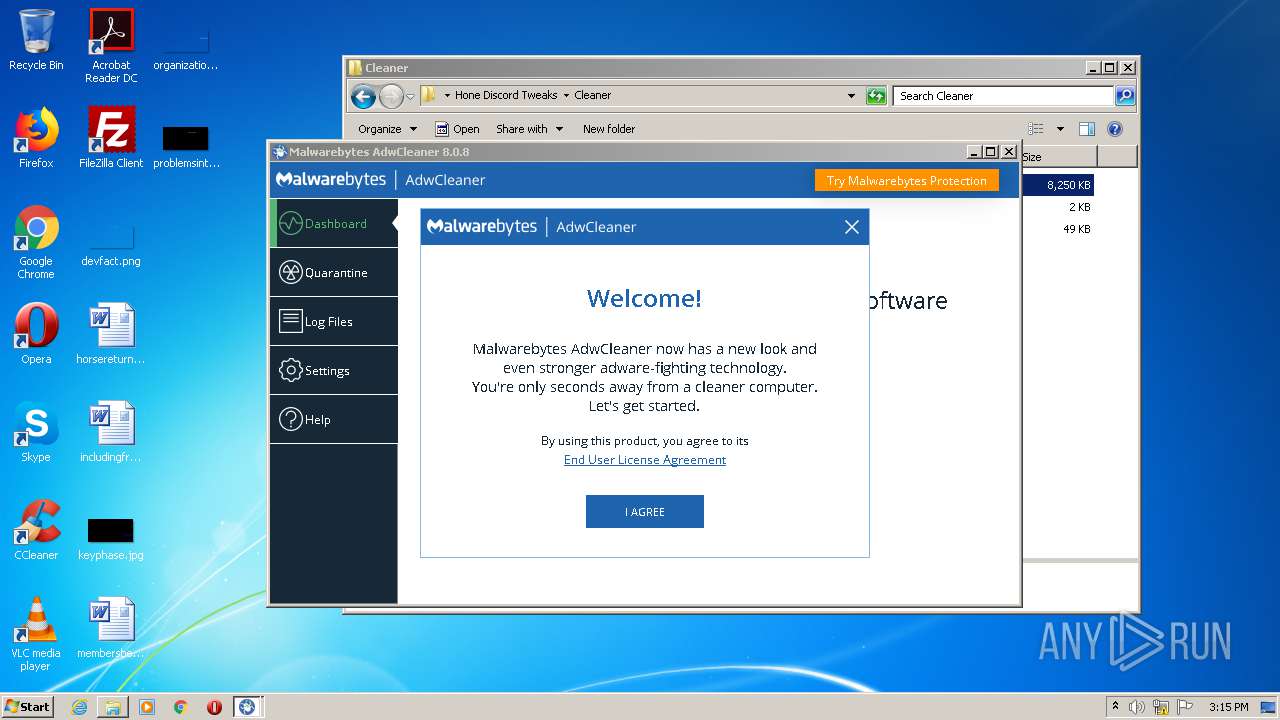
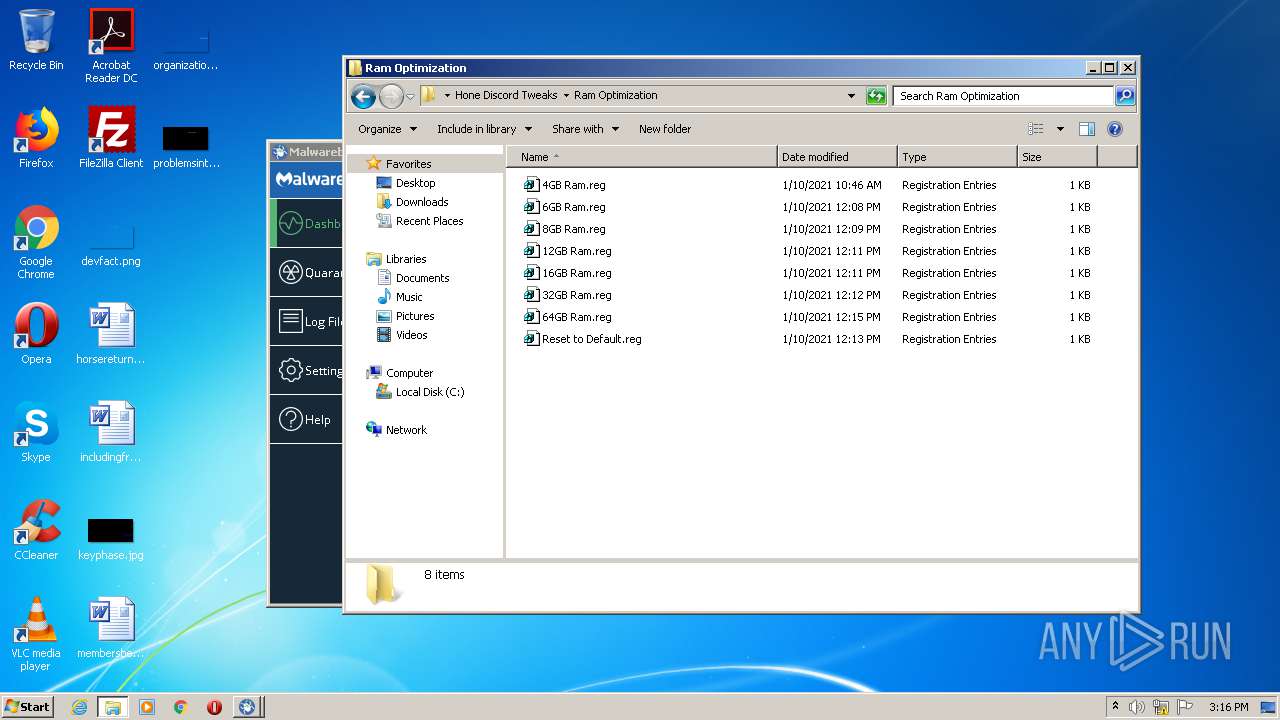
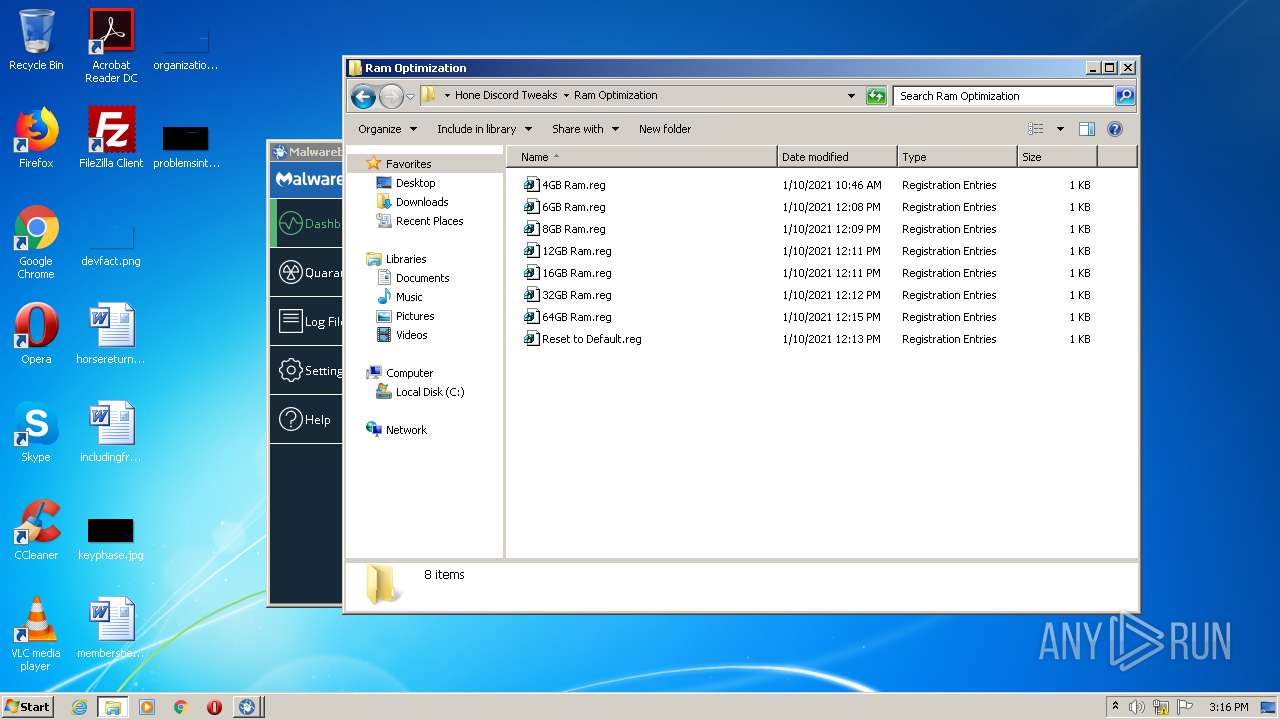
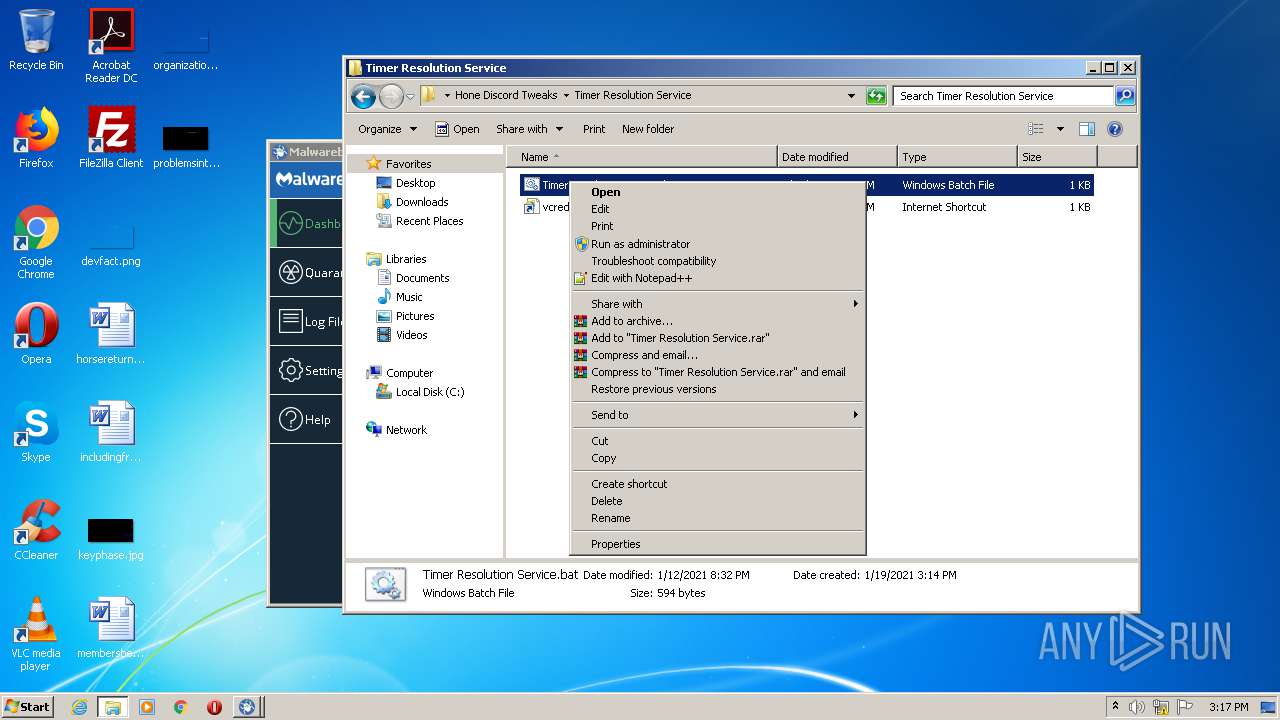
Manual execution by user
- adwcleaner_8.0.8 .exe (PID: 3528)
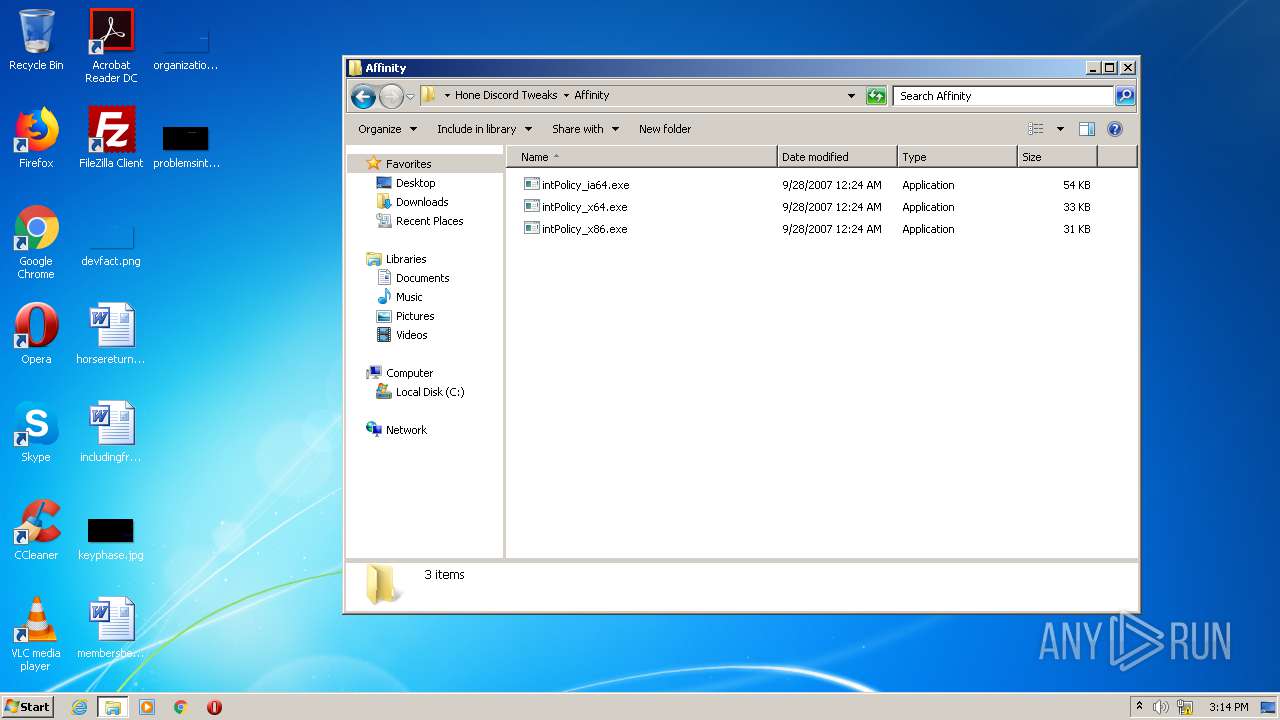
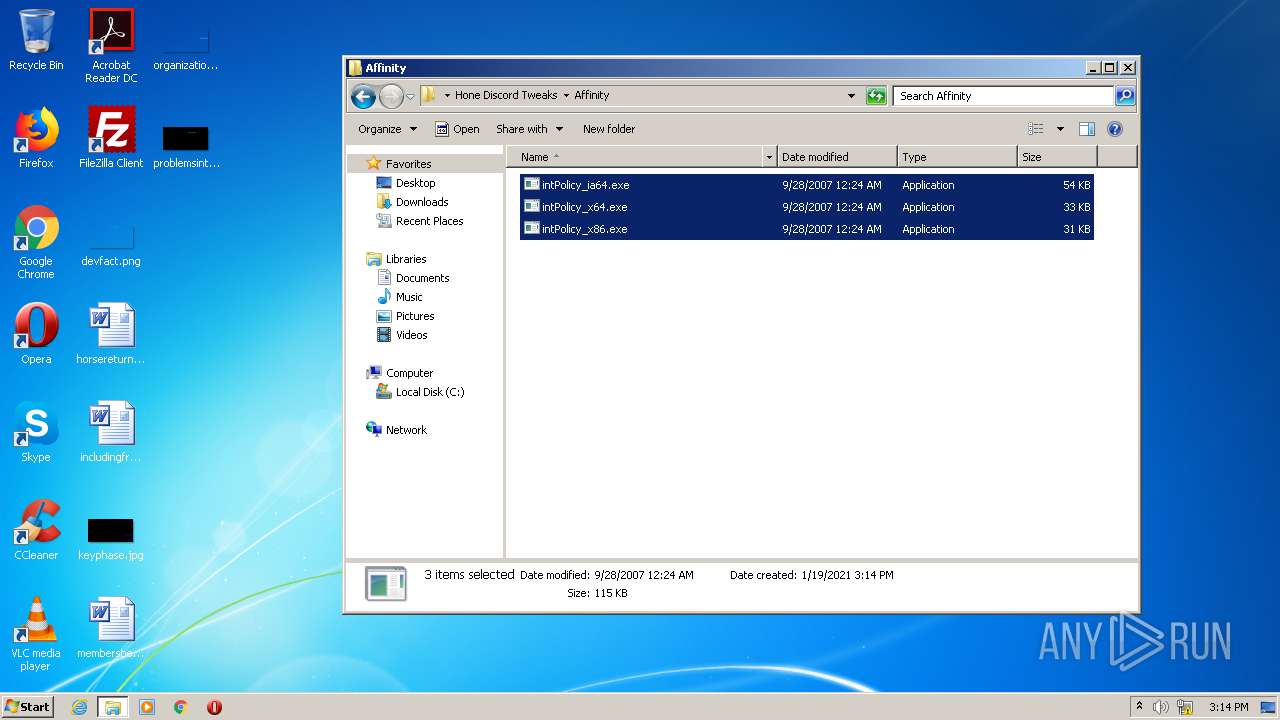
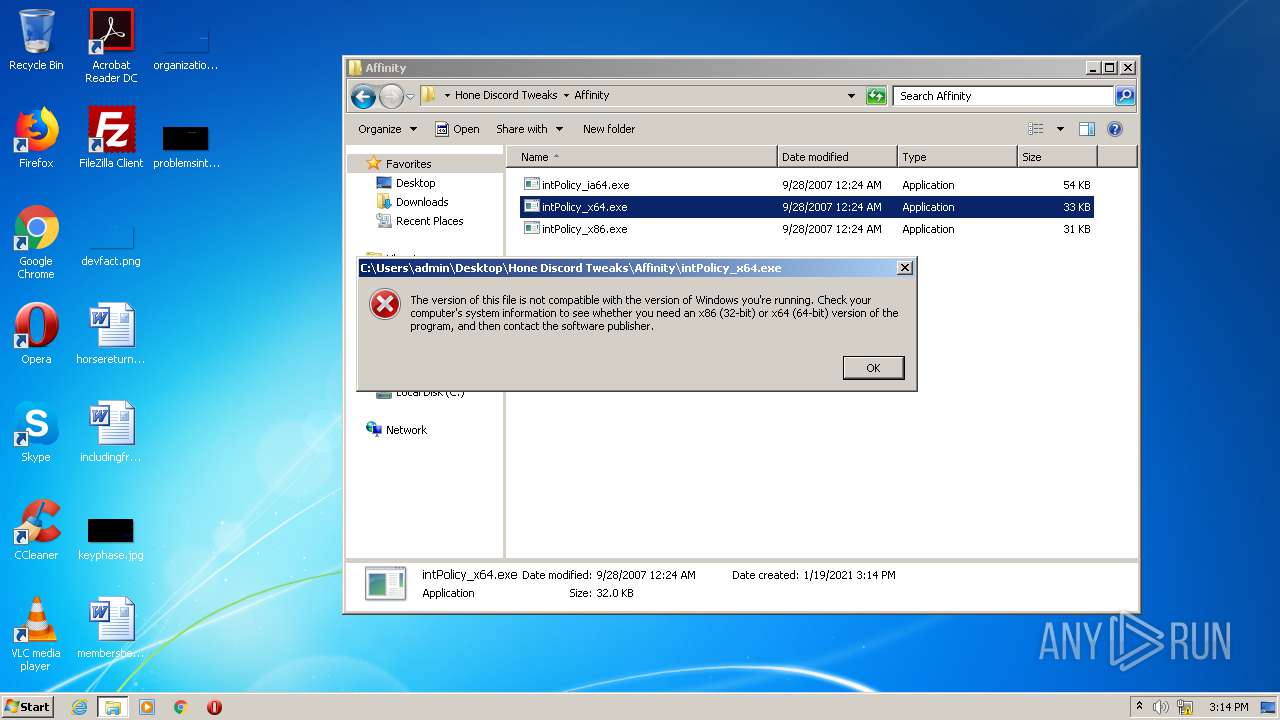
- intPolicy_x86.exe (PID: 3108)
- adwcleaner_8.0.8 .exe (PID: 2096)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 3404)
- regedit.exe (PID: 3920)
- regedit.exe (PID: 3544)
- cmd.exe (PID: 2156)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:01:16 16:02:19 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
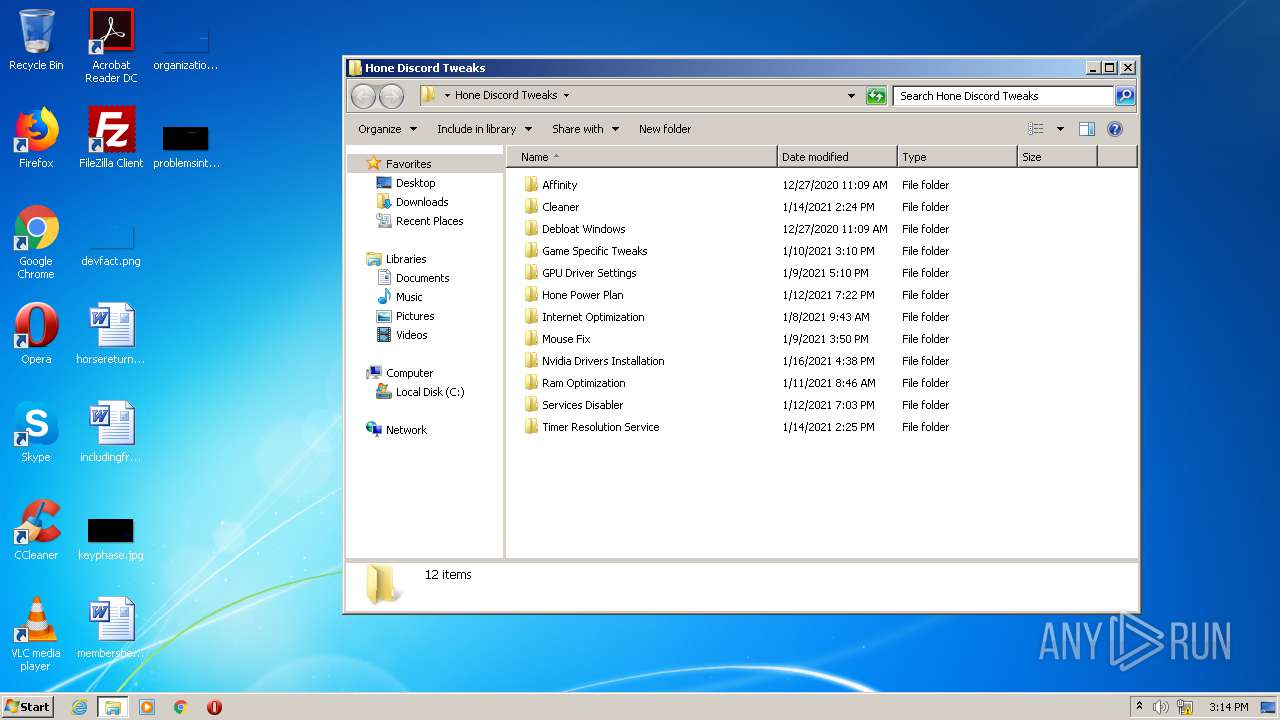
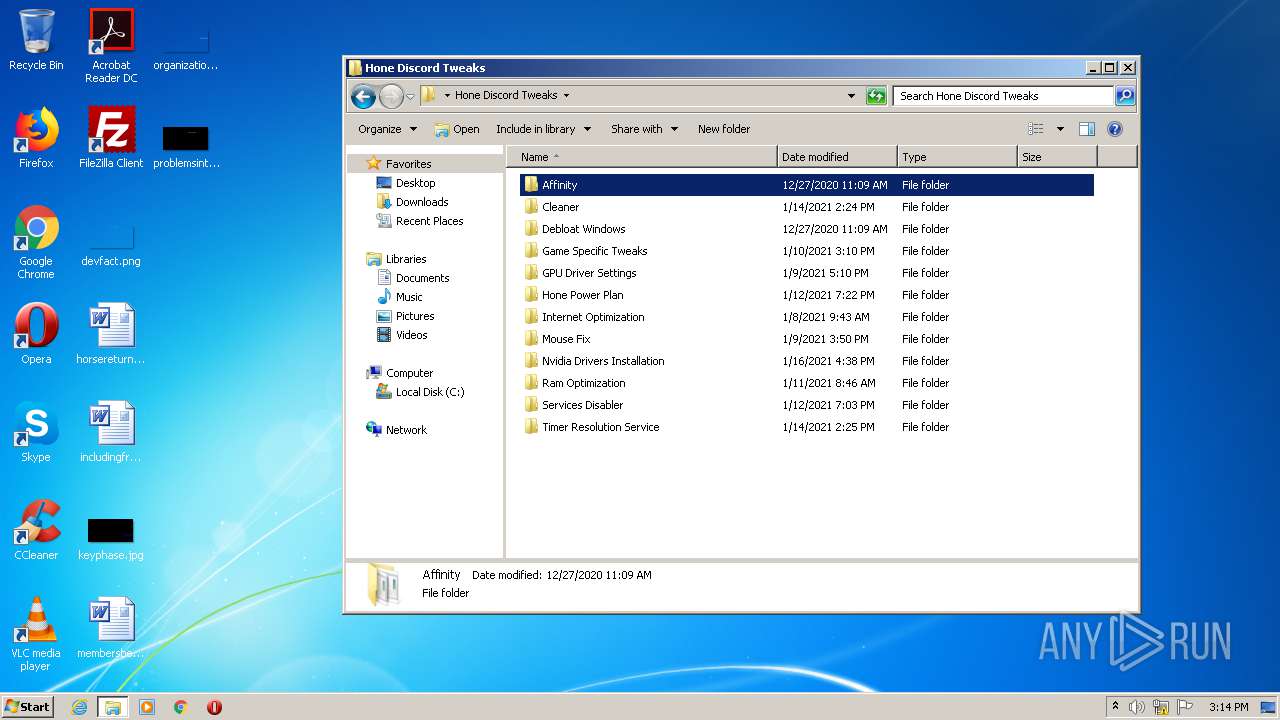
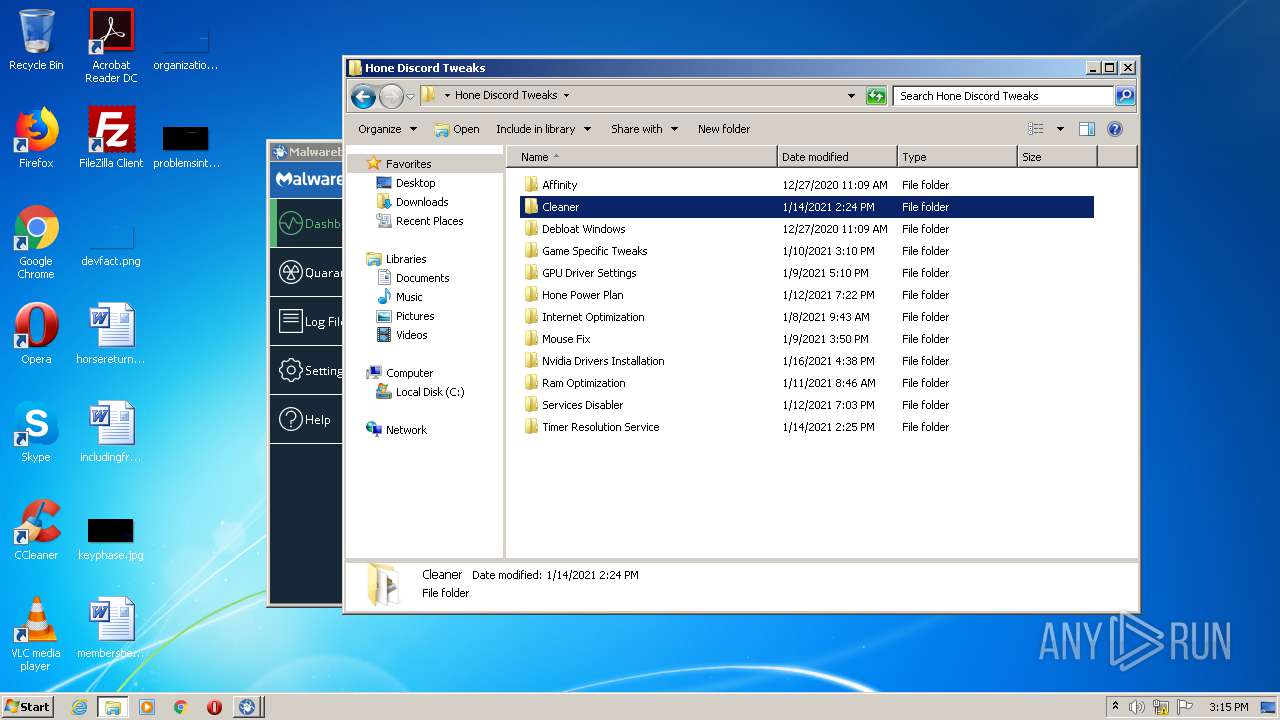
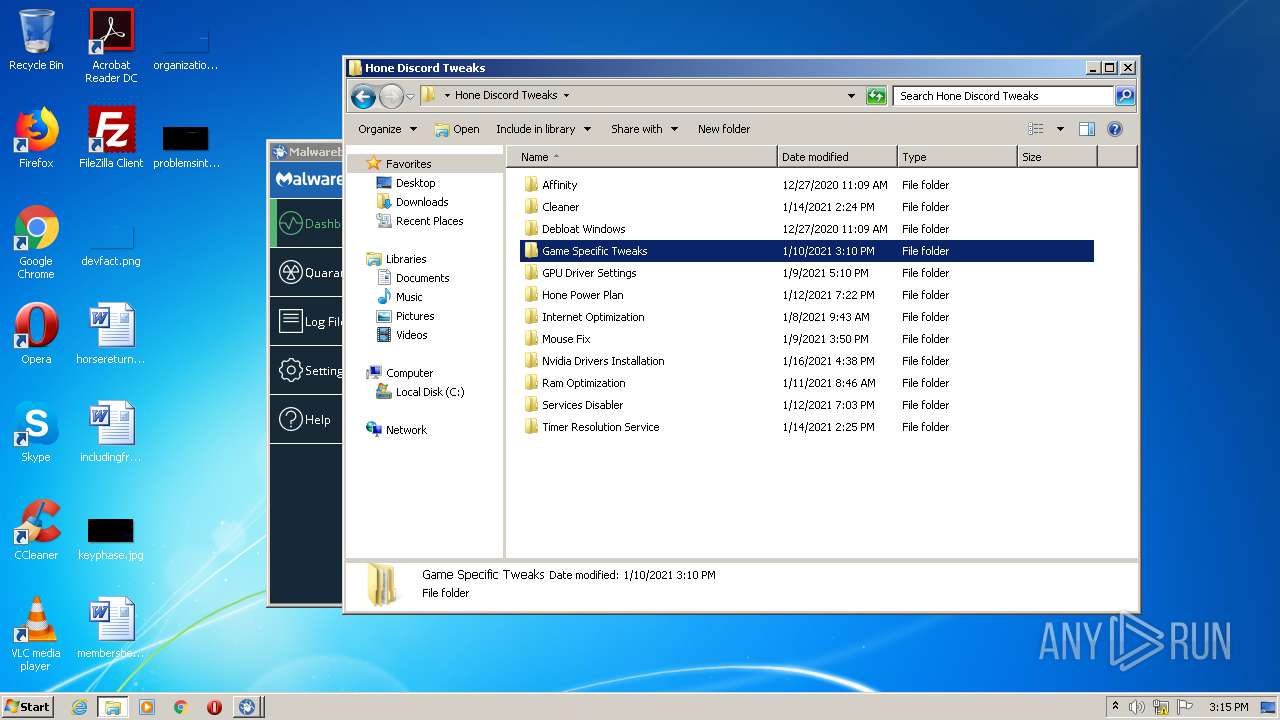
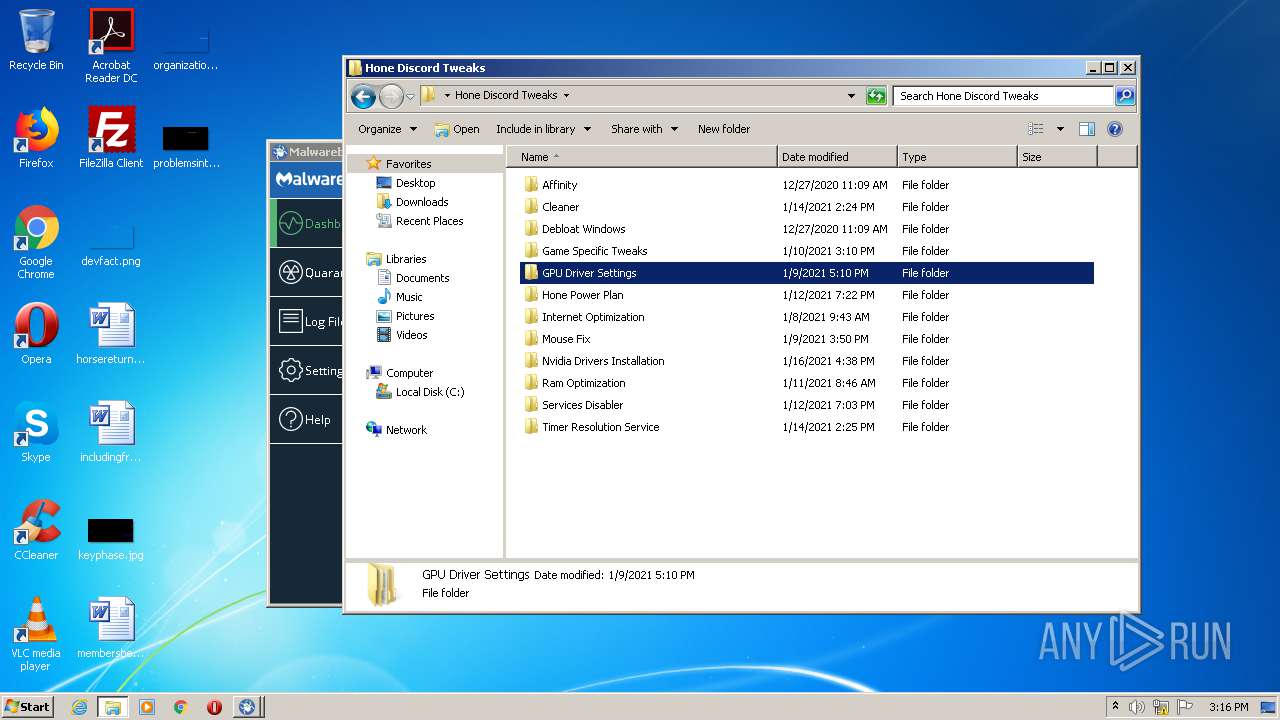
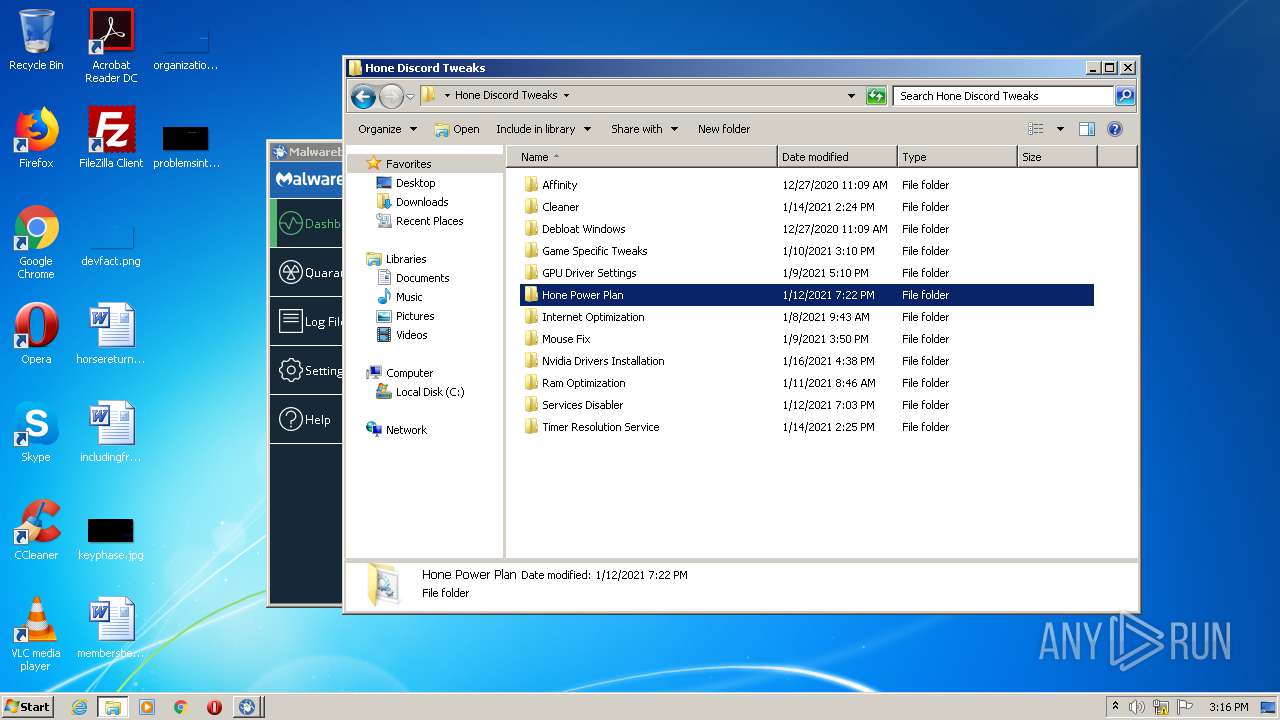
| ZipFileName: | Hone Discord Tweaks/ |
Total processes
391
Monitored processes
316
Malicious processes
9
Suspicious processes
1
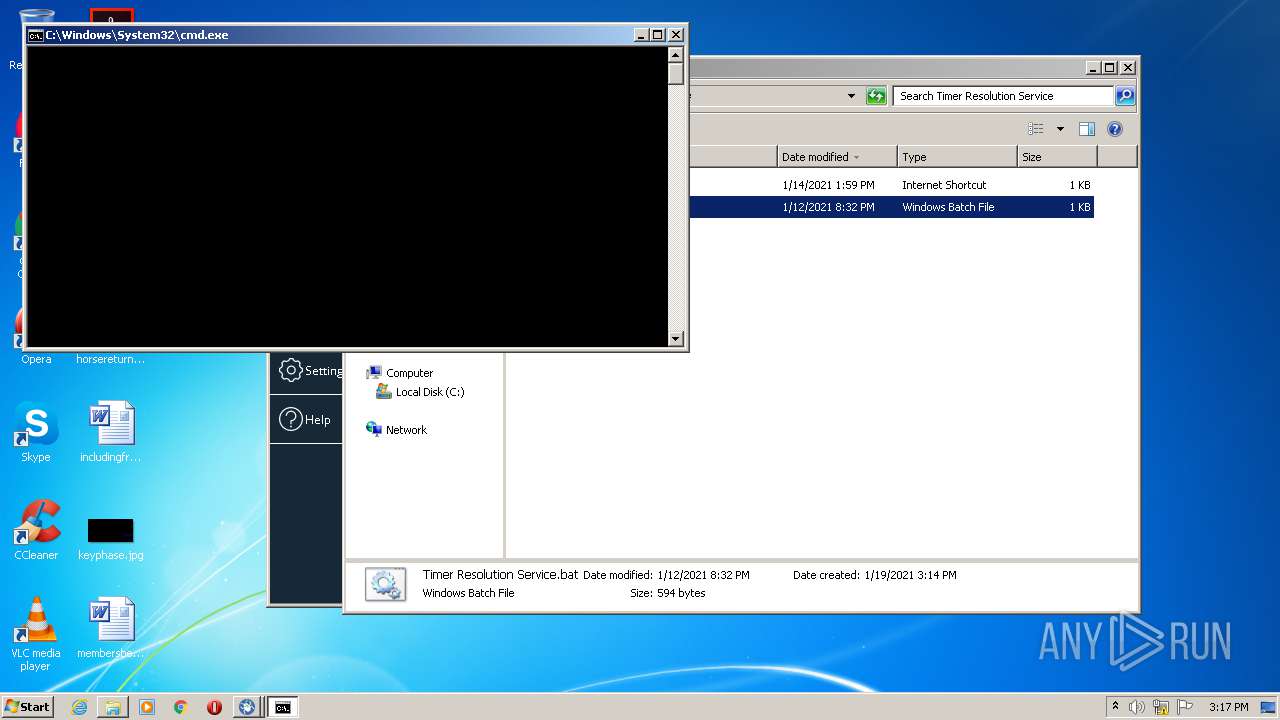
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | Reg.exe add "HKCU\Software\Microsoft\Windows\CurrentVersion\BackgroundAccessApplications" /v "GlobalUserDisabled" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 120 | Reg.exe add "HKCU\Software\Microsoft\Windows\CurrentVersion\DeviceAccess\Global\{992AFA70-6F47-4148-B3E9-3003349C1548}" /v "Value" /t REG_SZ /d "Deny" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
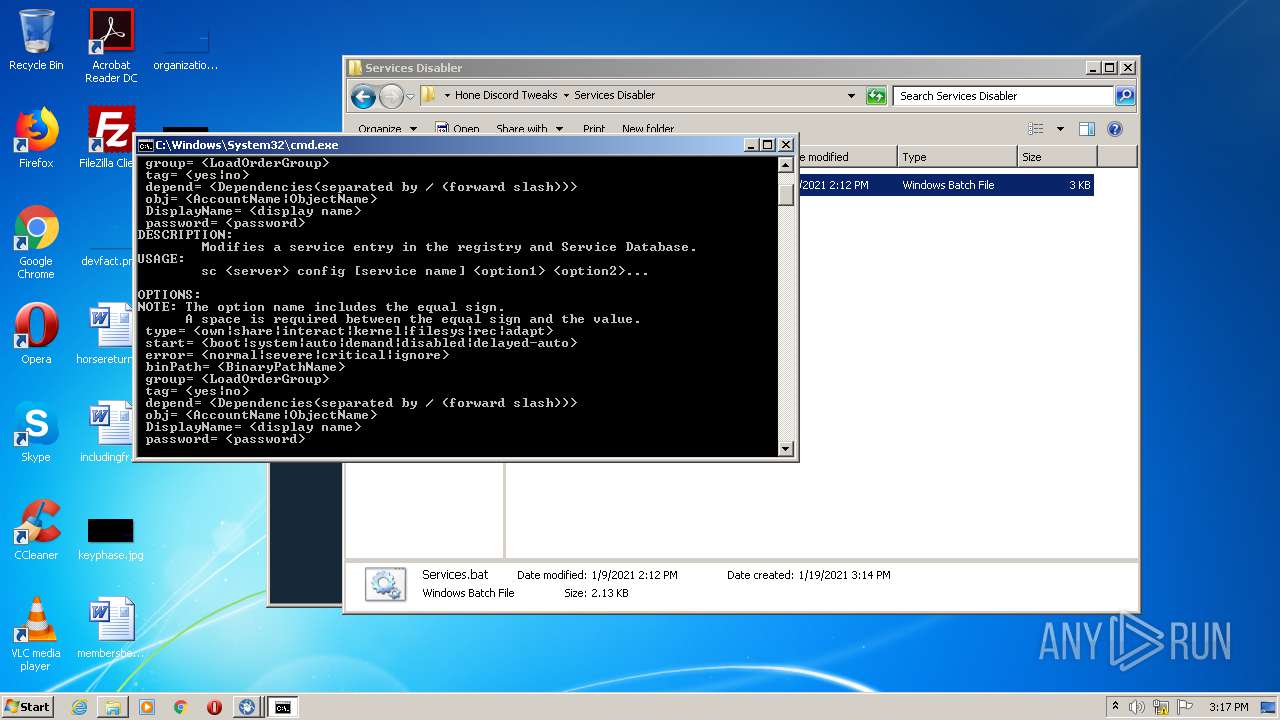
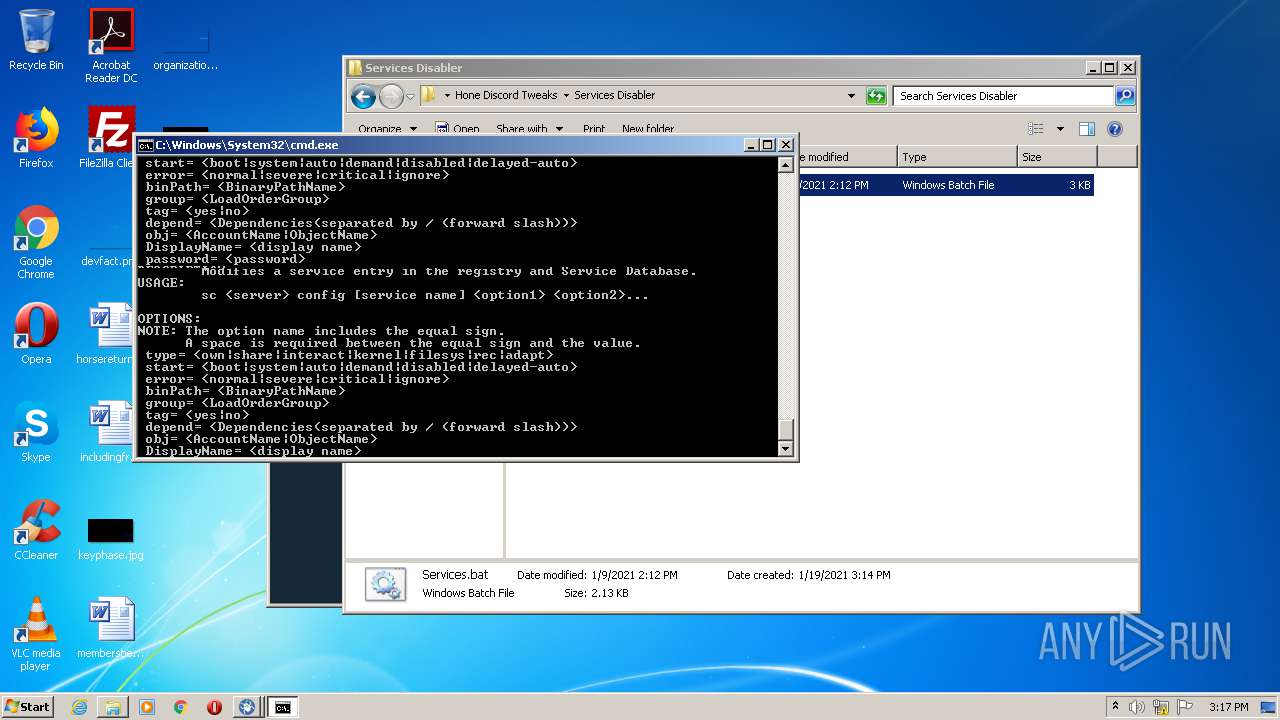
| 124 | sc config CertPropSvc start=disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | Reg.exe add "HKLM\SOFTWARE\Policies\Microsoft\Windows\Windows Search" /v "AllowCloudSearch" /t REG_DWORD /d "0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | Reg.exe add "HKLM\SOFTWARE\Policies\Microsoft\Windows\TabletPC" /v "PreventHandwritingDataSharing" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | WSCRIPT "C:\Users\admin\AppData\Local\Temp\~tmpmsgbox.vbs" | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 376 | sc config gupdate start=disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | sc config ibtsiva start=disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | Reg.exe add "HKLM\SOFTWARE\Microsoft\PolicyManager\current\device\System" /v "AllowExperimentation" /t REG_DWORD /d "0" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | sc config DoSvc start=disabled | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 253
Read events
928
Write events
325
Delete events
0
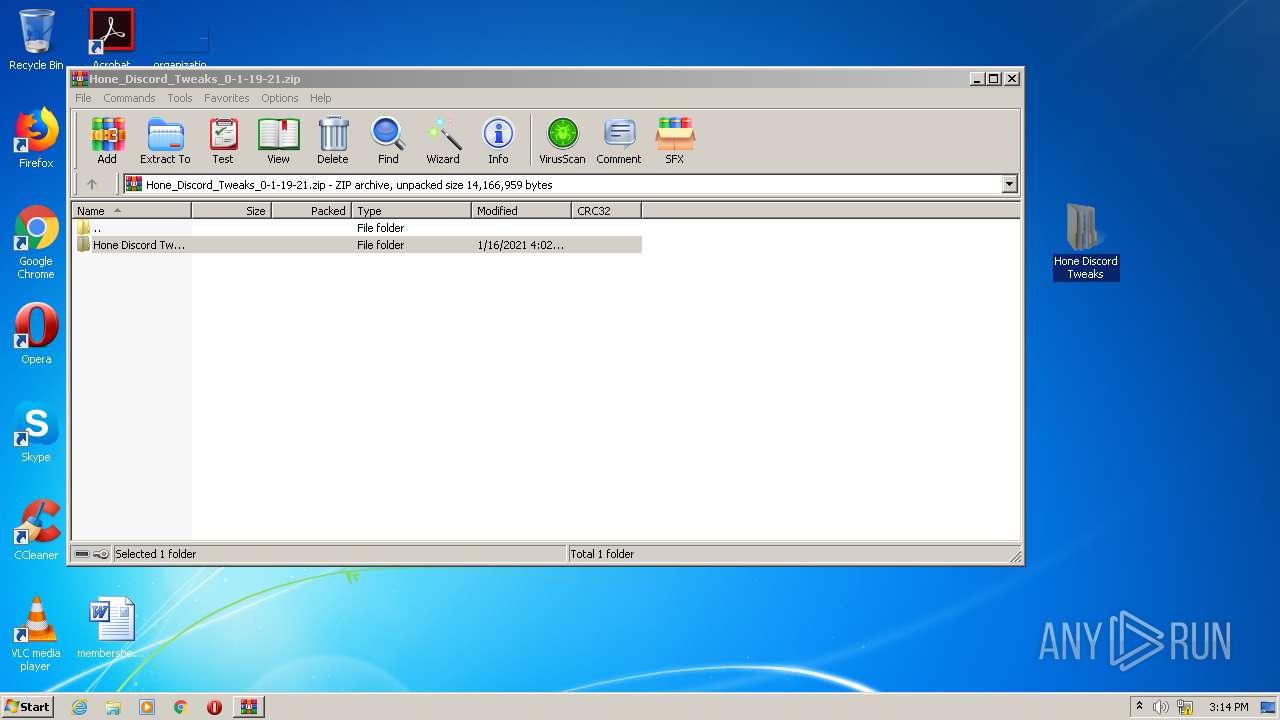
Modification events
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Hone_Discord_Tweaks_0-1-19-21.zip | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
6
Text files
3
Unknown types
0
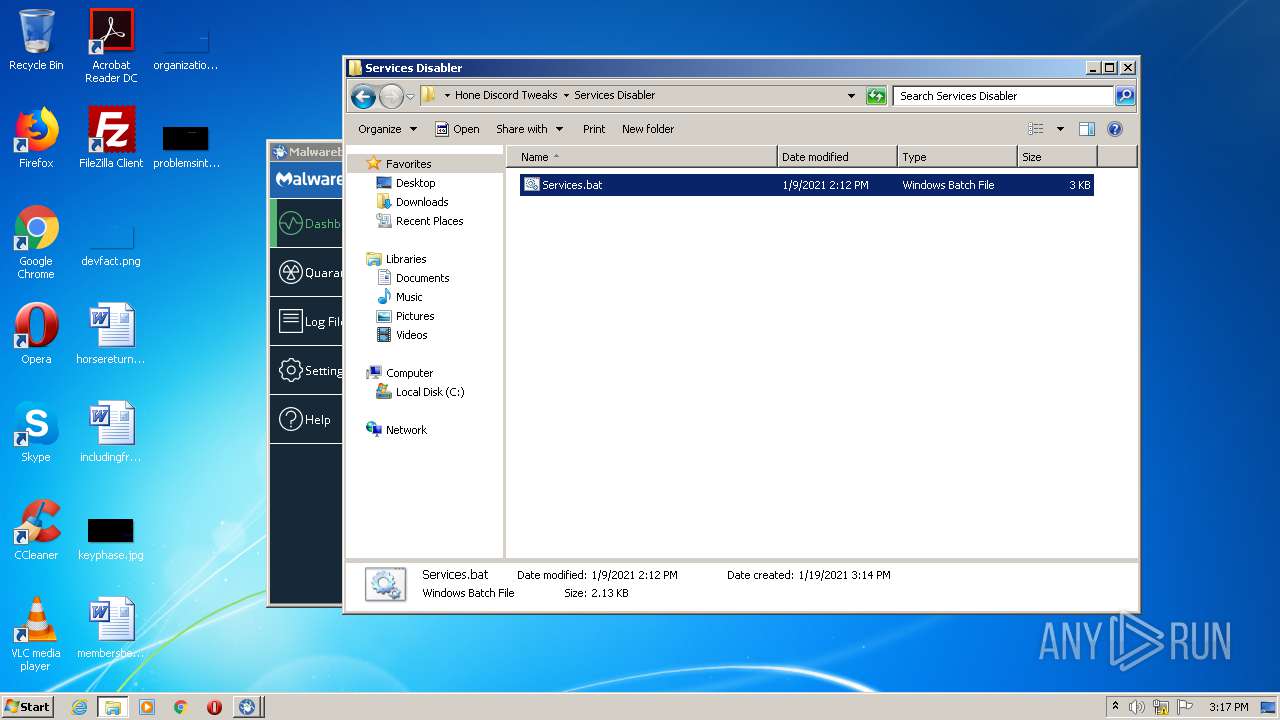
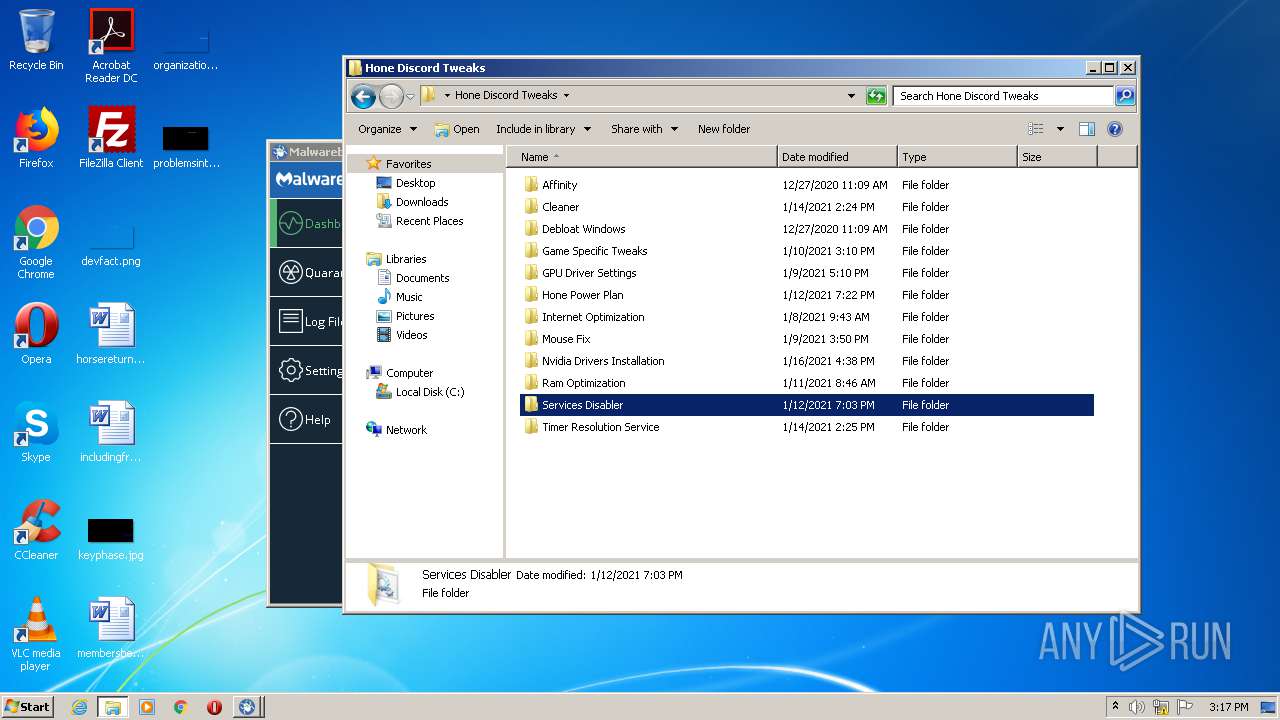
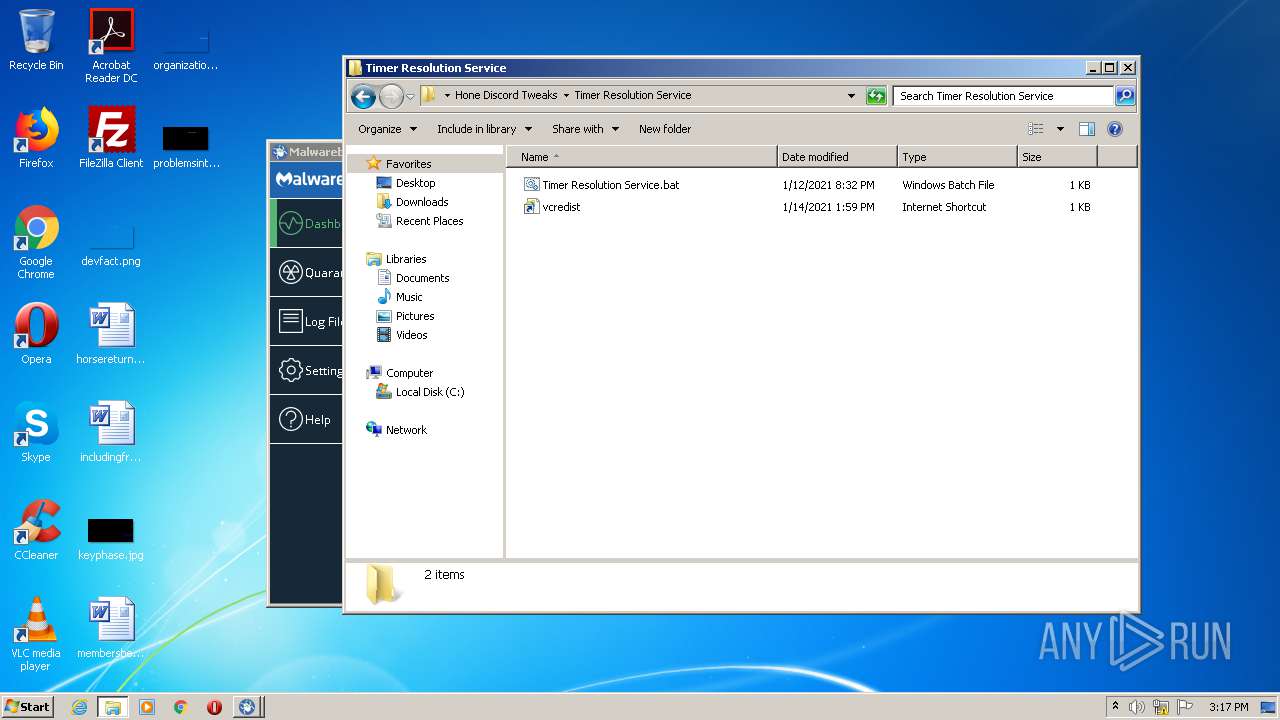
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
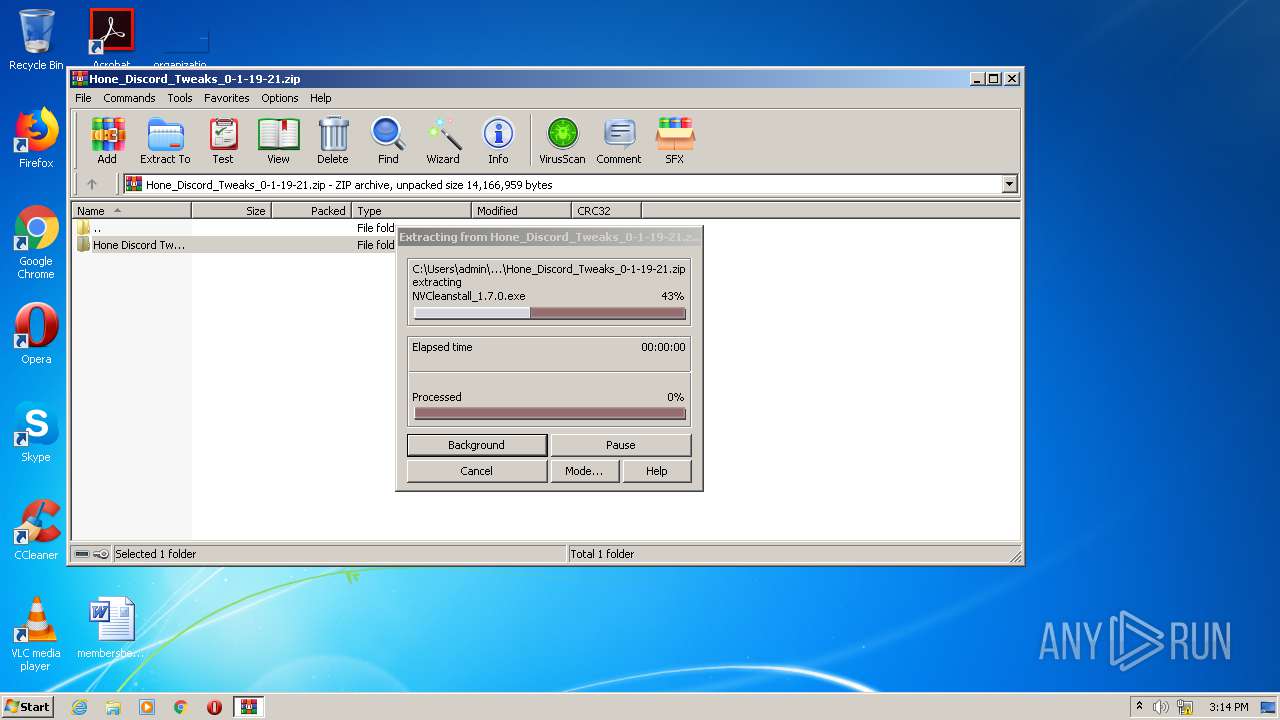
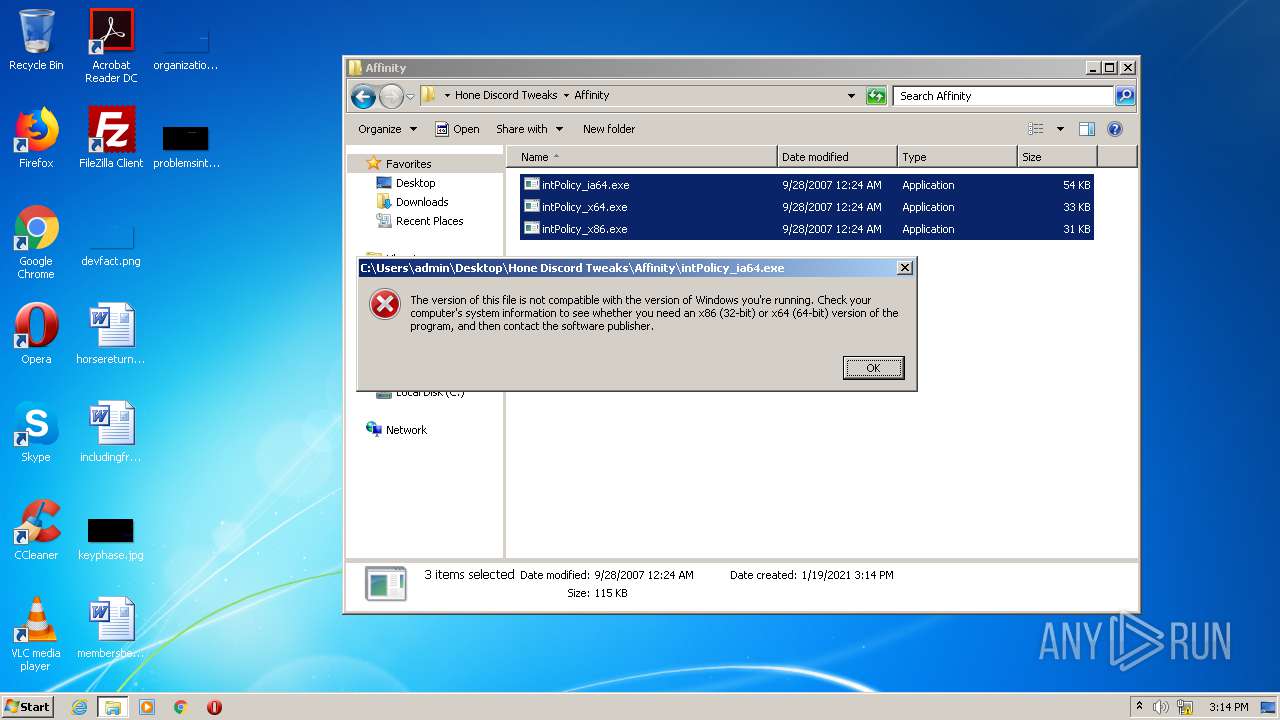
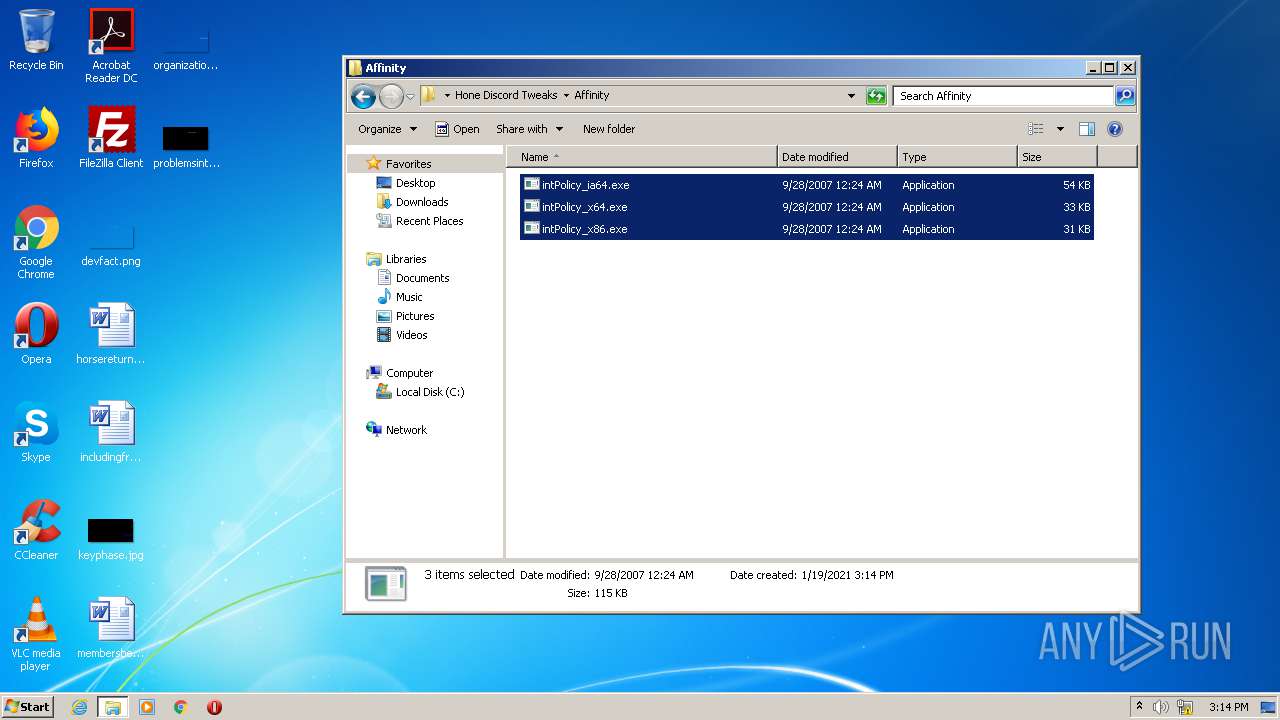
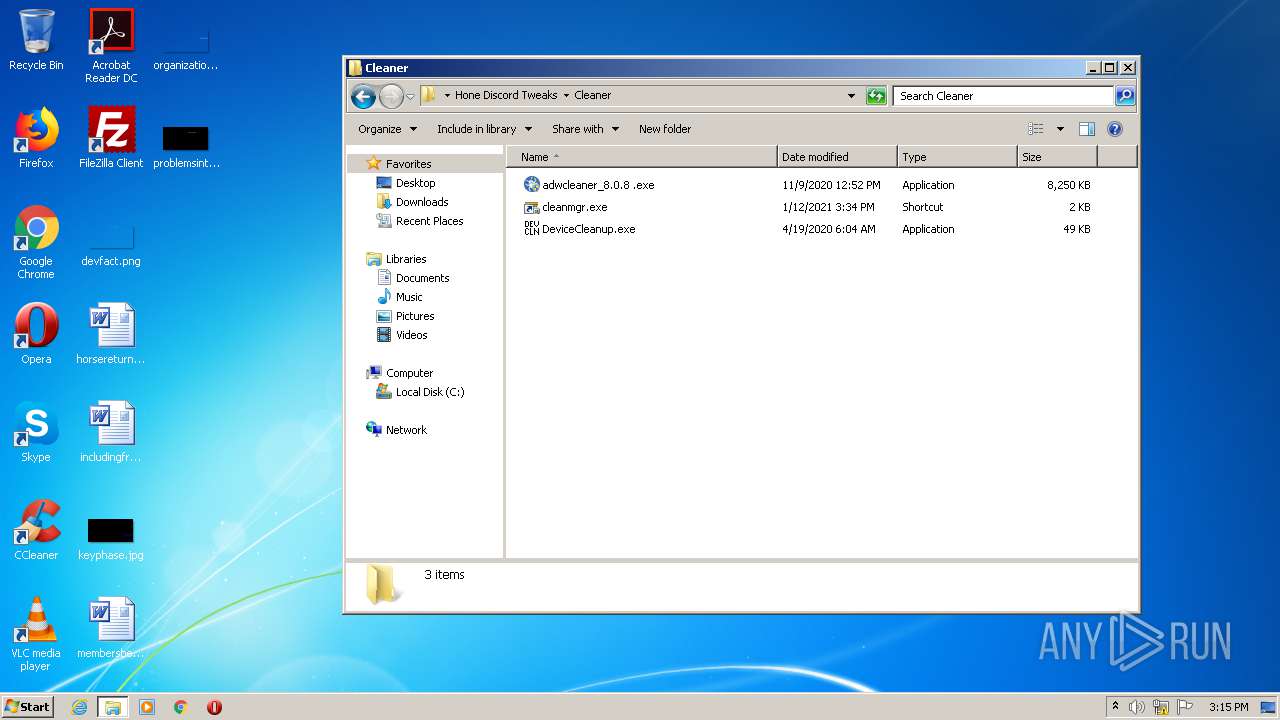
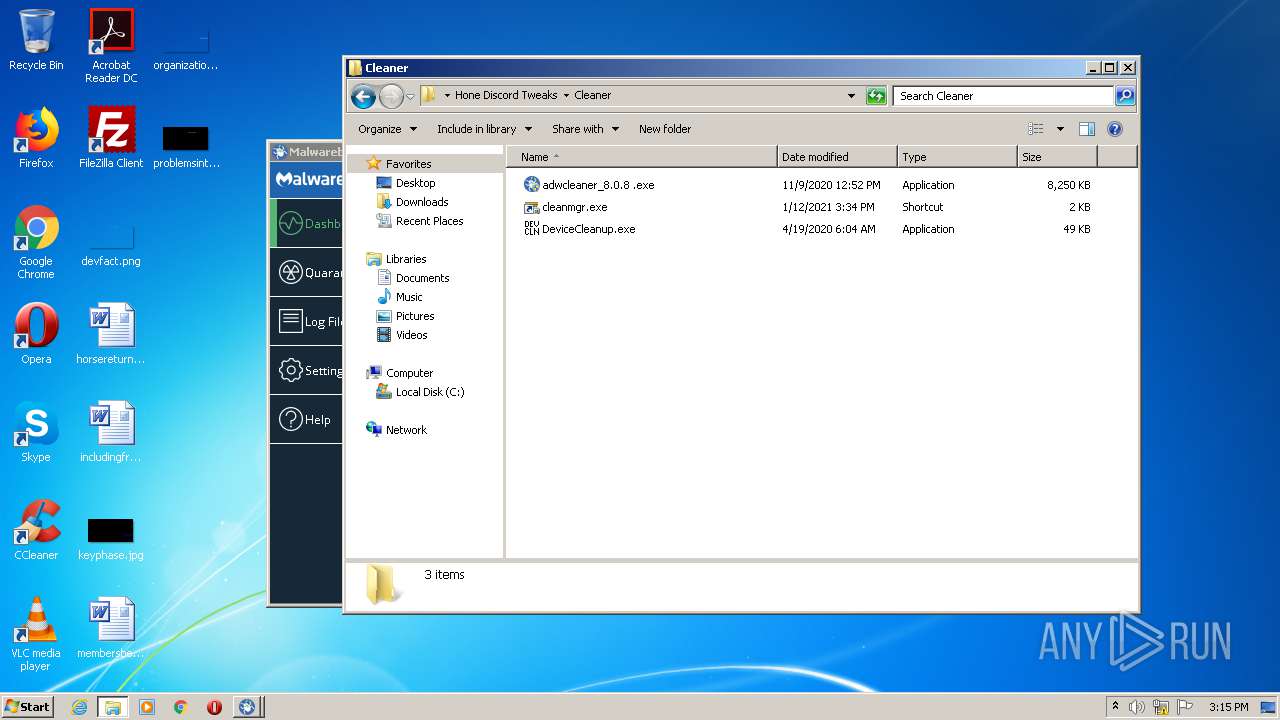
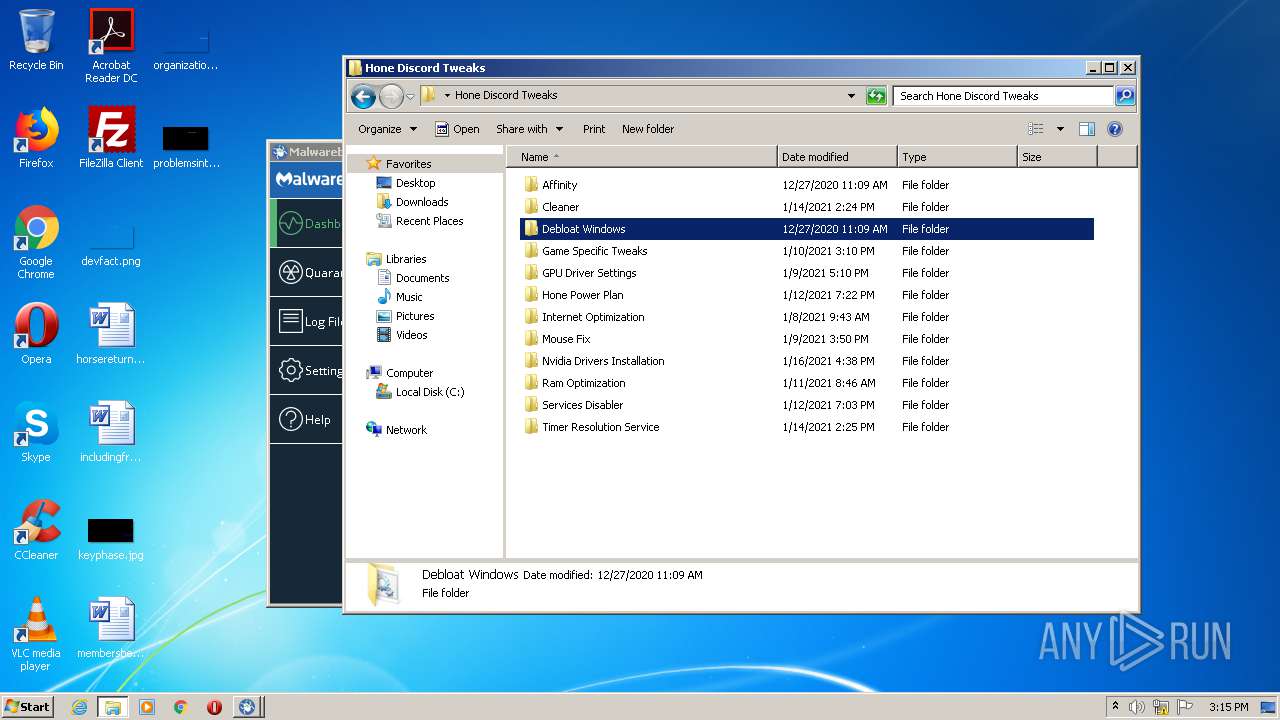
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Affinity\intPolicy_ia64.exe | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Affinity\intPolicy_x64.exe | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Affinity\intPolicy_x86.exe | — | |
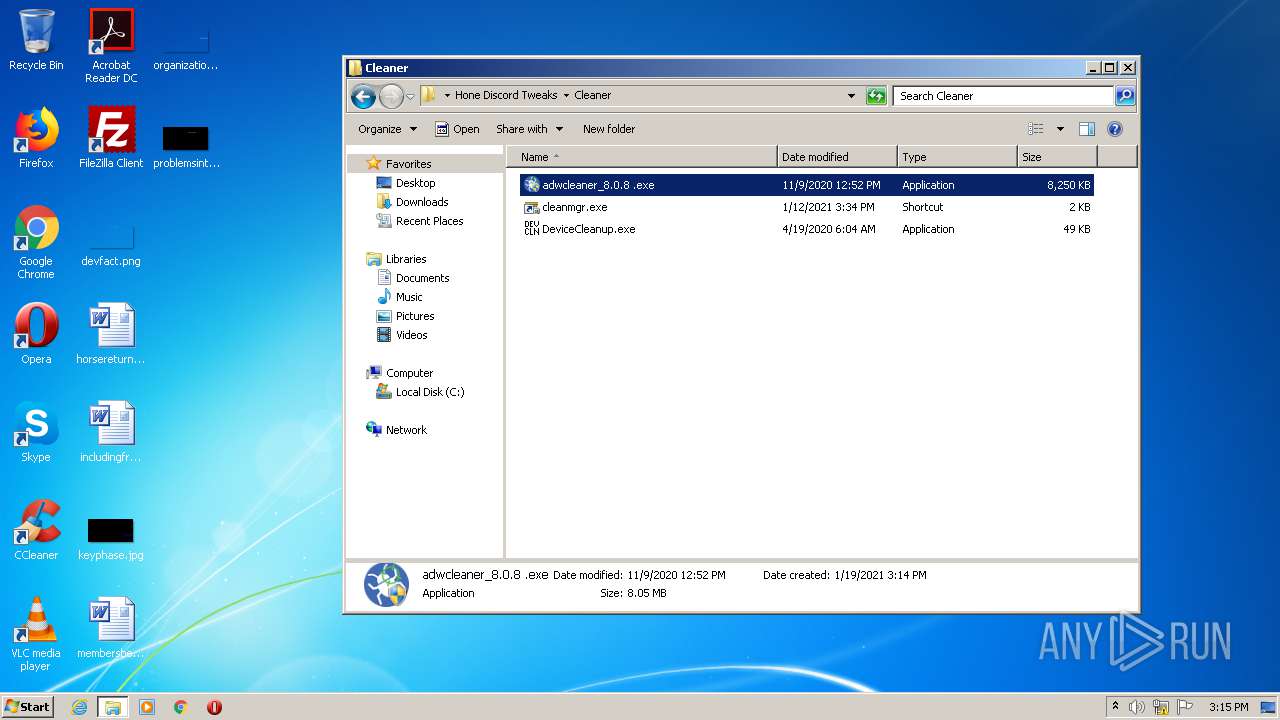
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Cleaner\adwcleaner_8.0.8 .exe | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Cleaner\cleanmgr.exe.lnk | — | |
MD5:— | SHA256:— | |||
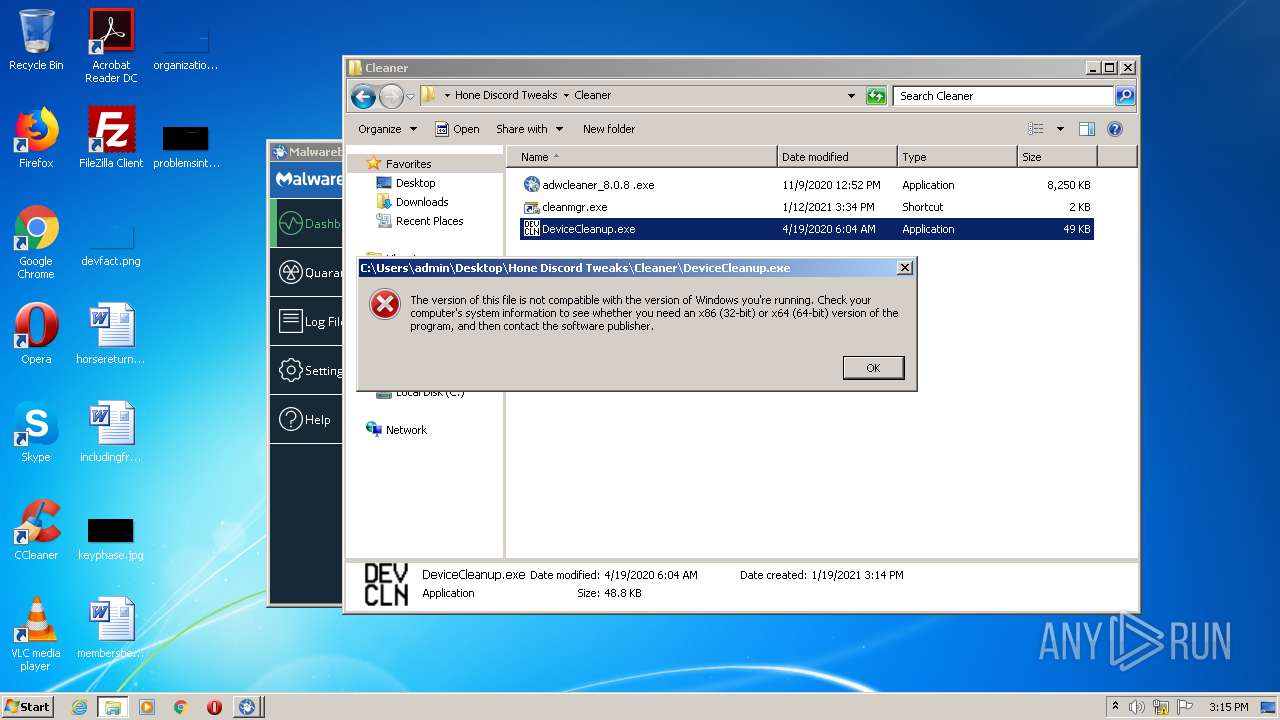
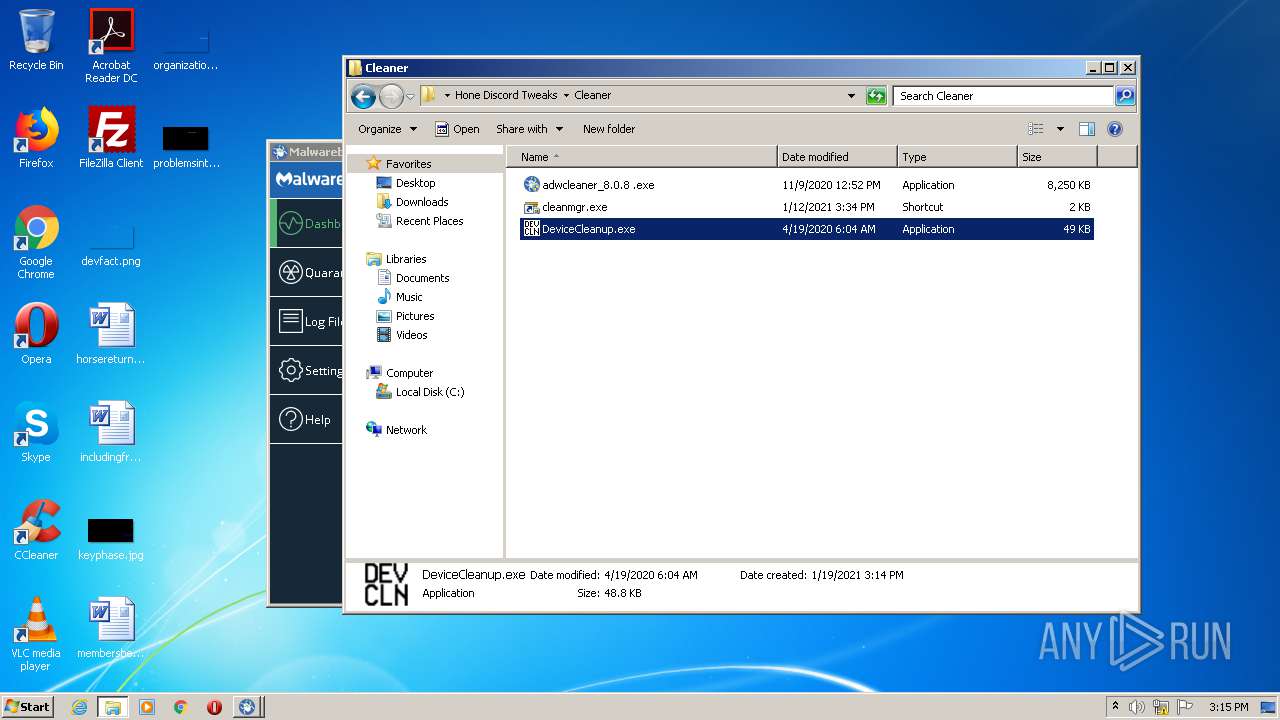
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Cleaner\DeviceCleanup.exe | — | |
MD5:— | SHA256:— | |||
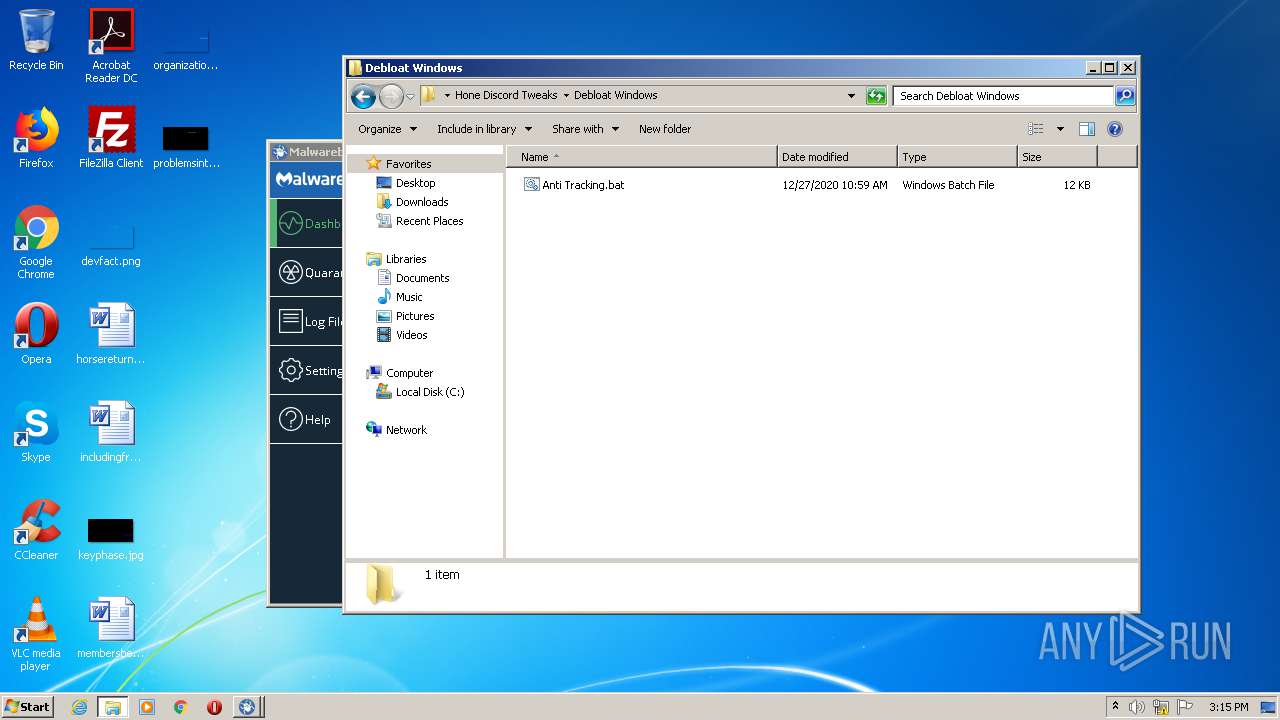
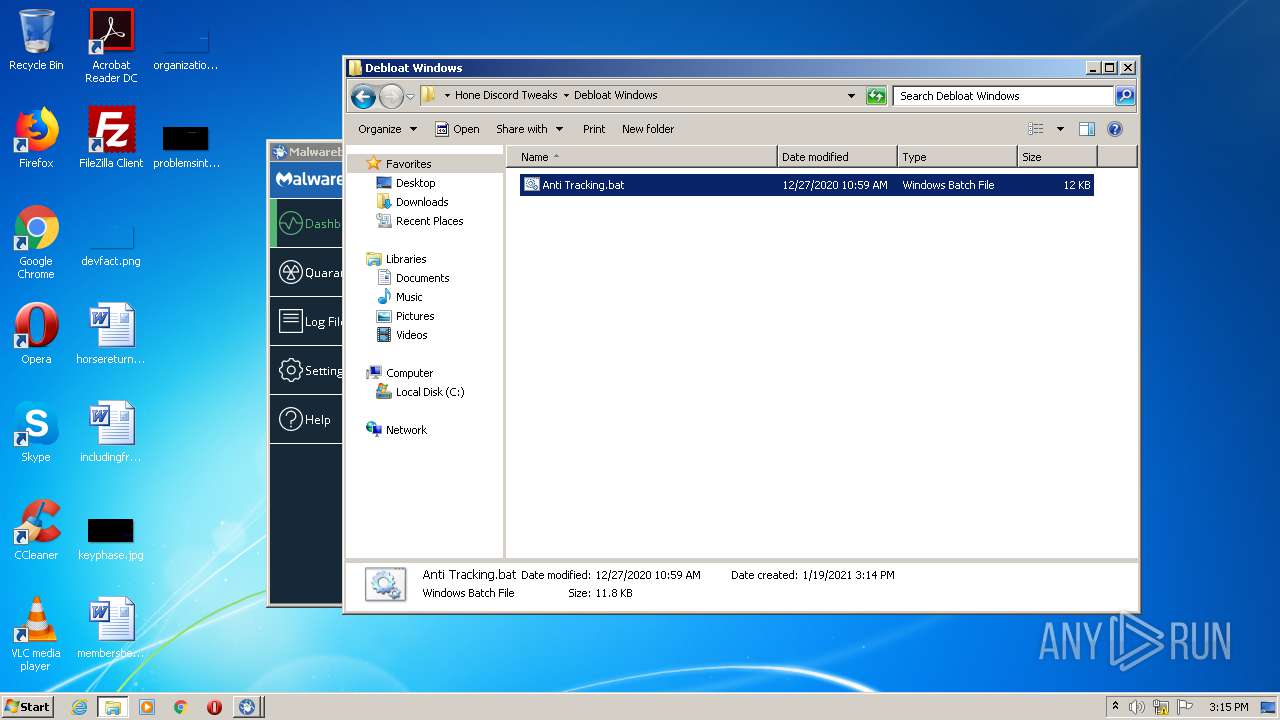
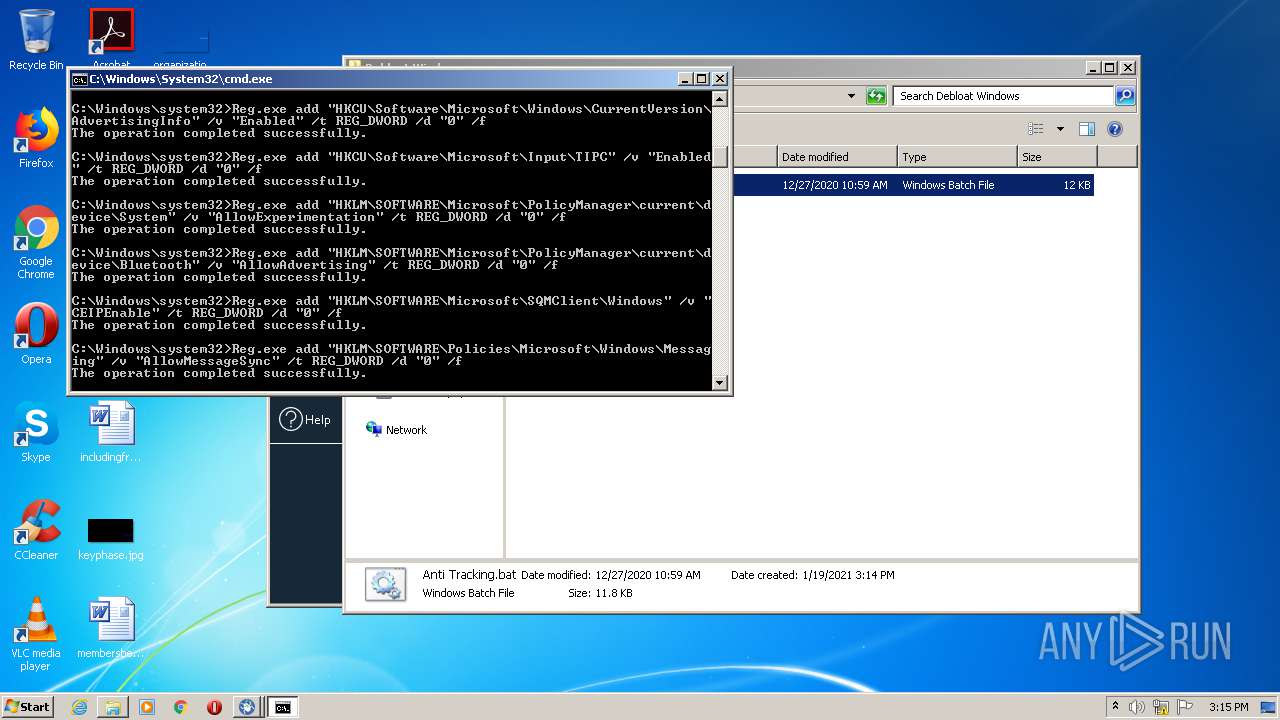
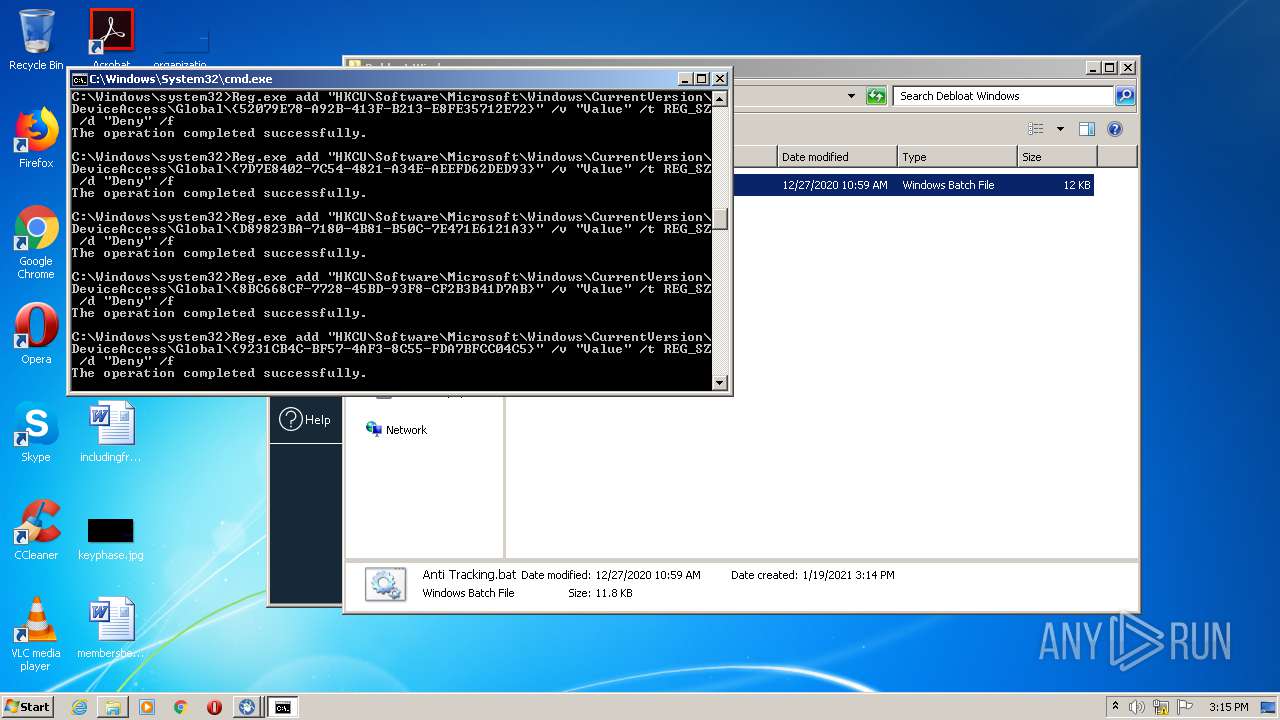
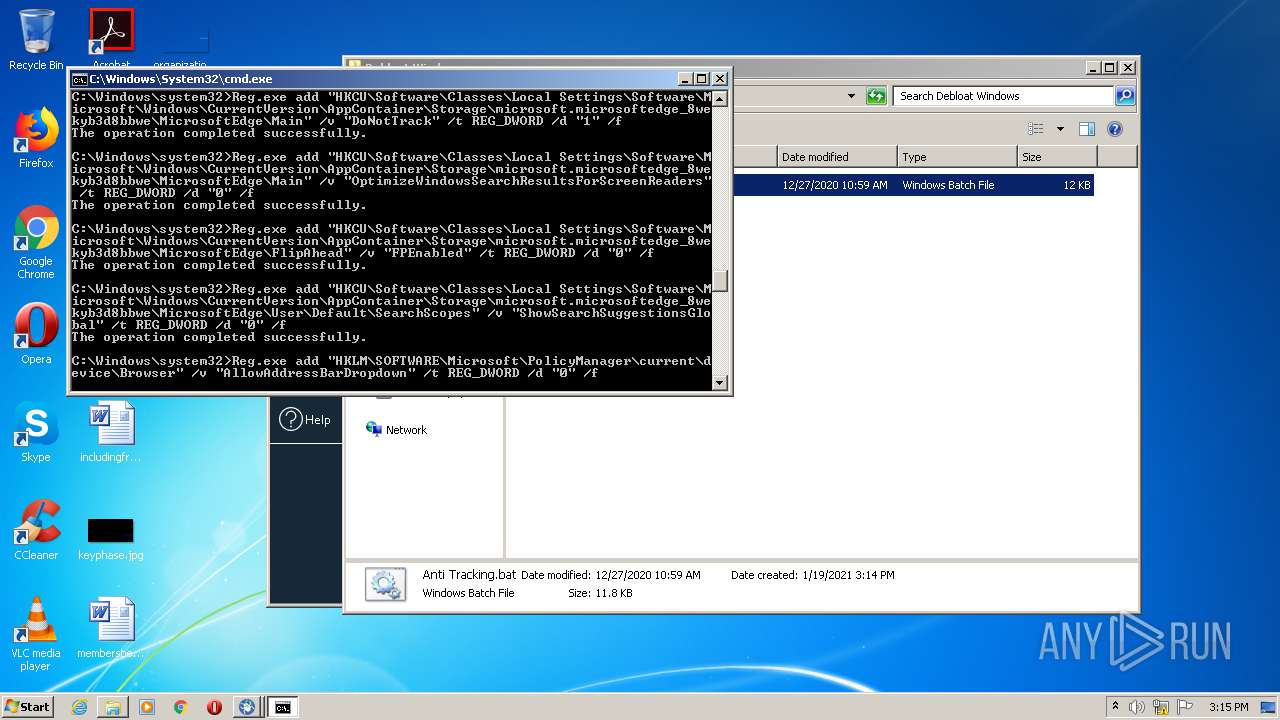
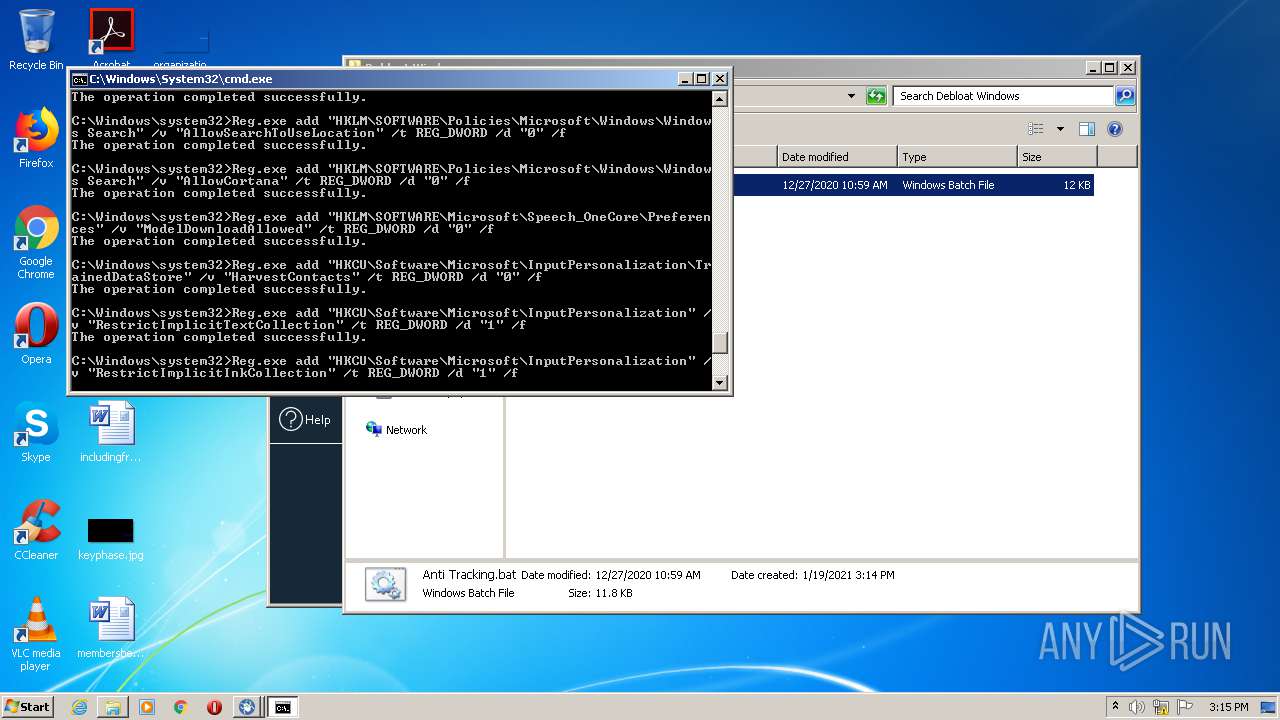
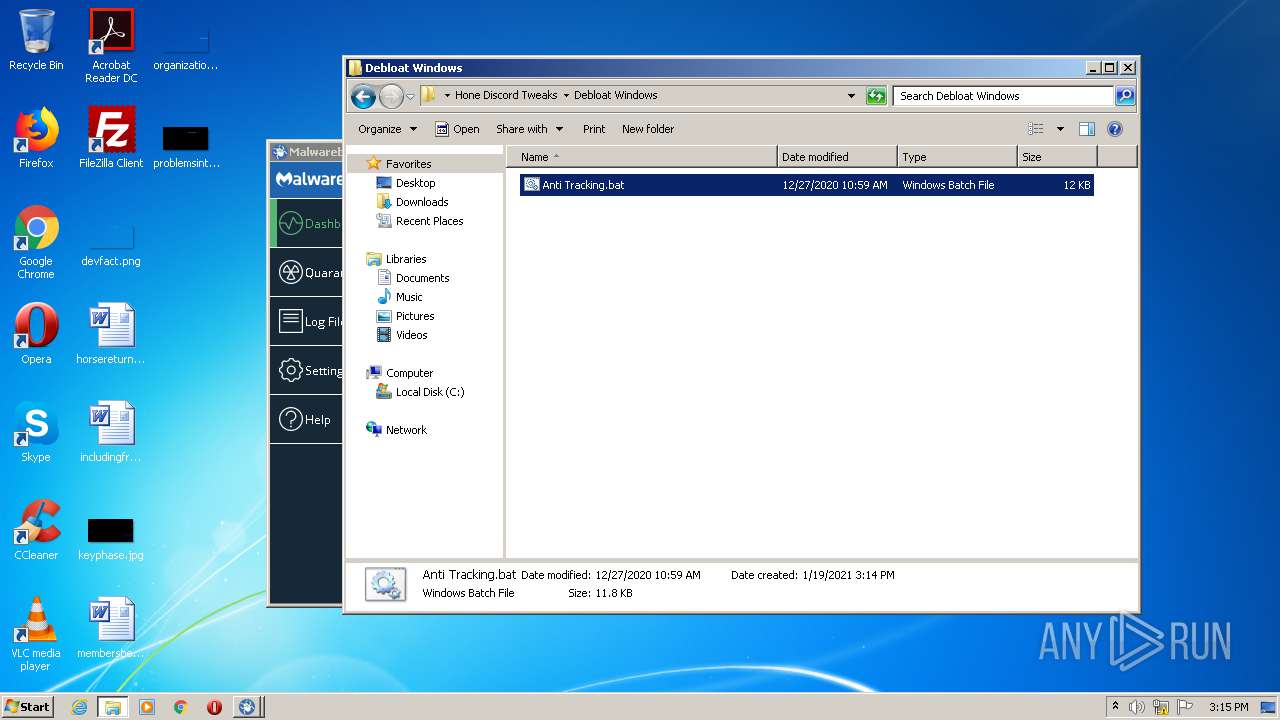
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\Debloat Windows\Anti Tracking.bat | — | |
MD5:— | SHA256:— | |||
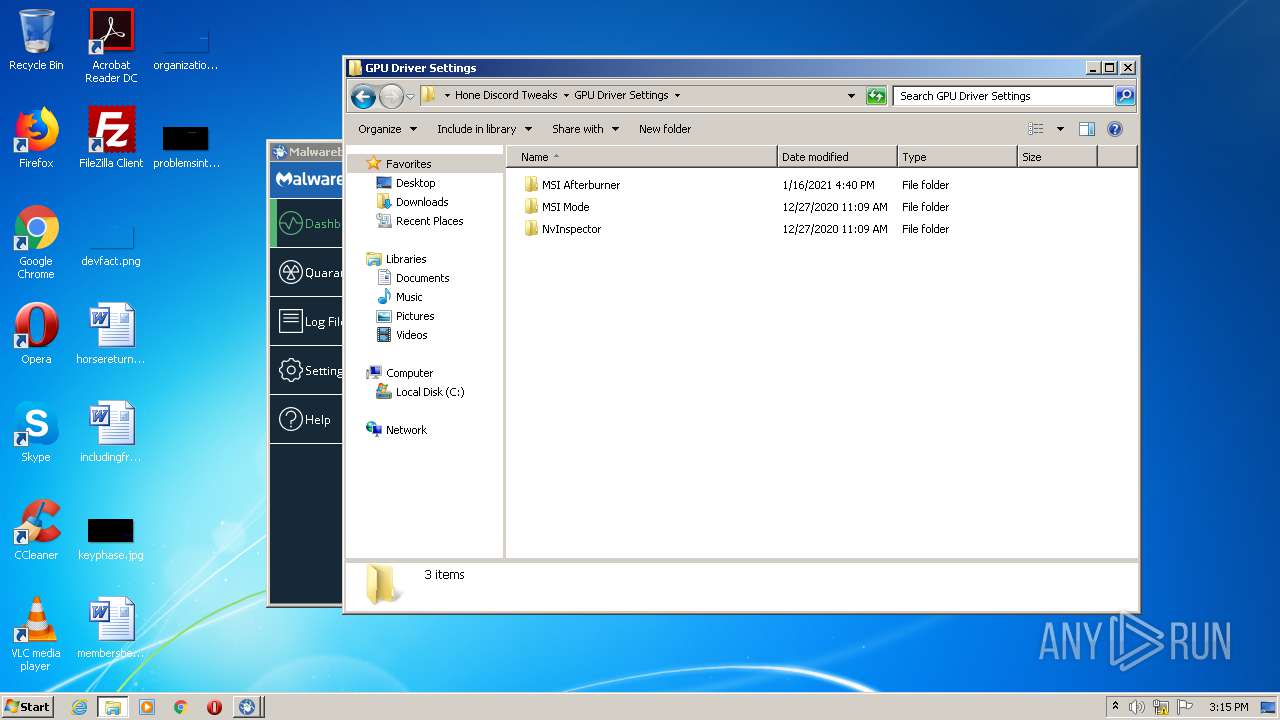
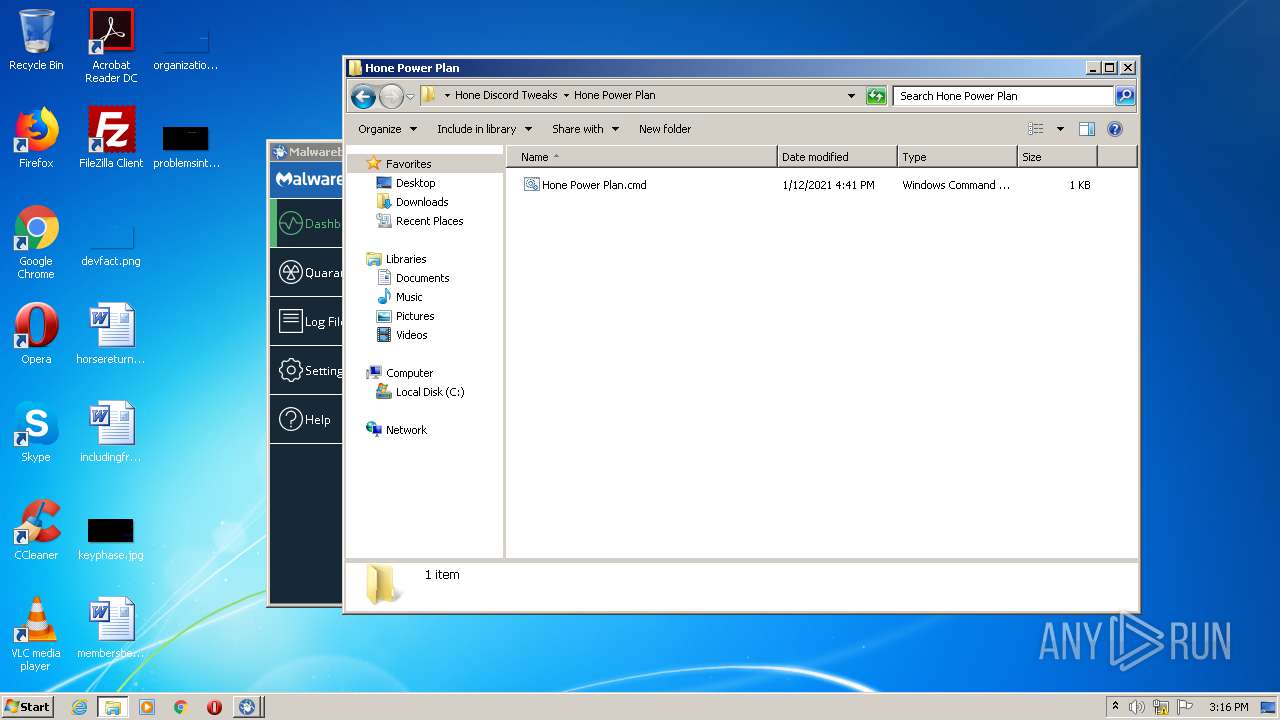
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\GPU Driver Settings\MSI Afterburner\Move Skin.cmd | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\GPU Driver Settings\MSI Afterburner\MSI Afterburner Download.url | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.9335\Hone Discord Tweaks\GPU Driver Settings\MSI Mode\MSI Mode Tool.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
adwcleaner_8.0.8 .exe | [Json Parser] Failed to open file "C:\\AdwCleaner\\settings" ( "The system cannot find the file specified." )
|
adwcleaner_8.0.8 .exe | [Application] AdwCleaner 8 . 0 . 8 launched
|
adwcleaner_8.0.8 .exe | [AdwUpgrade] Checking application updates
|
adwcleaner_8.0.8 .exe | [Telemetry] Sending hello
|
adwcleaner_8.0.8 .exe | [Telemetry] Status code: QVariant(Invalid)
|
adwcleaner_8.0.8 .exe | [File Downloader] Error downloading ( QNetworkReply::UnknownNetworkError )
|
adwcleaner_8.0.8 .exe | QIODevice::read (QDisabledNetworkReply): device not open
|