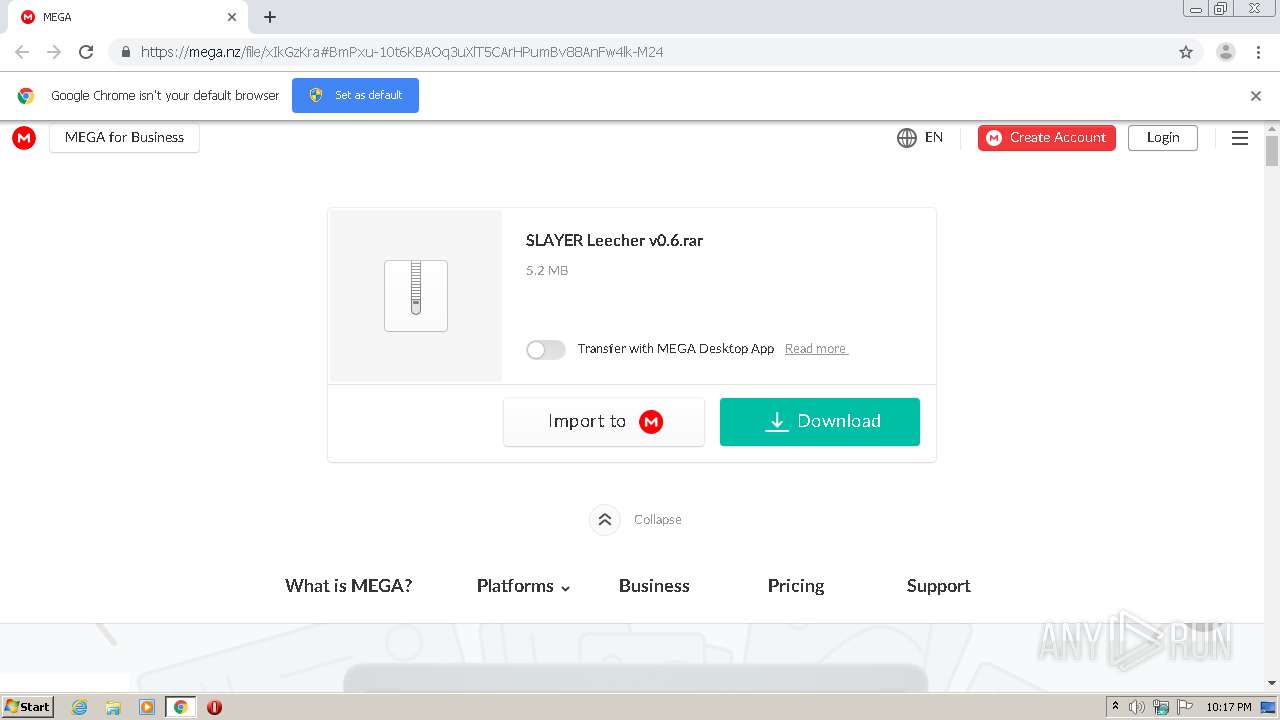
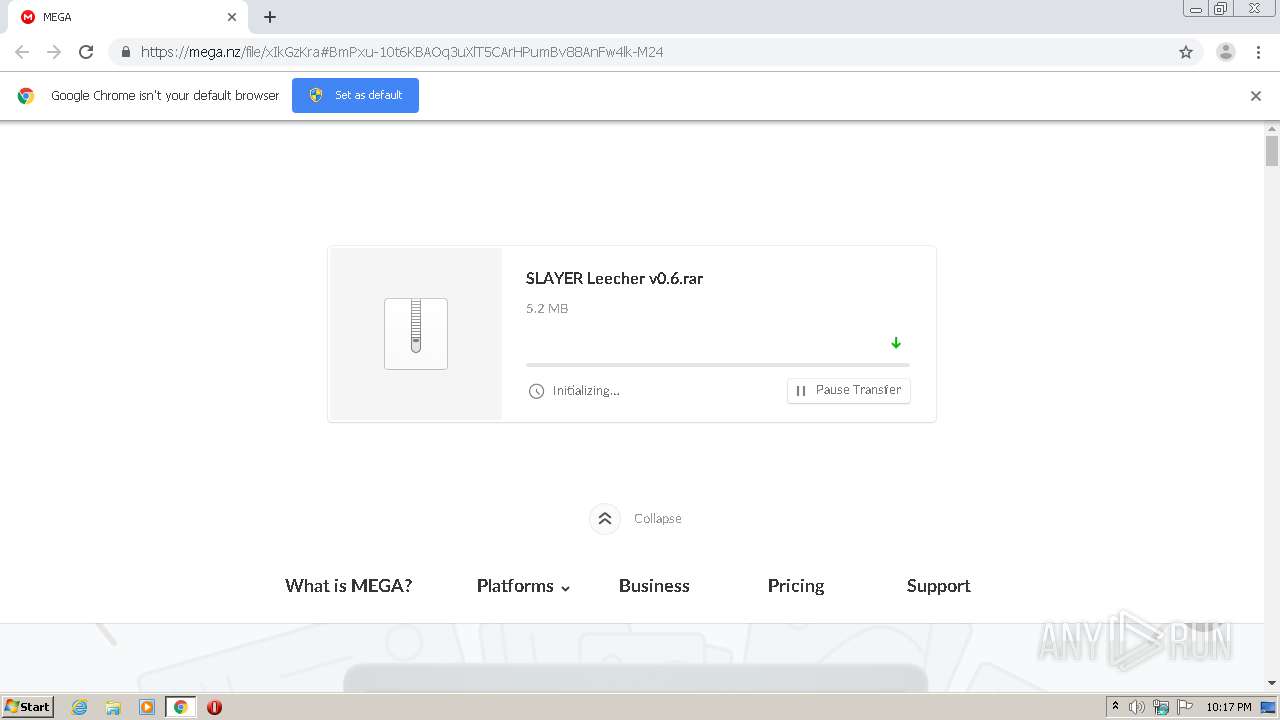
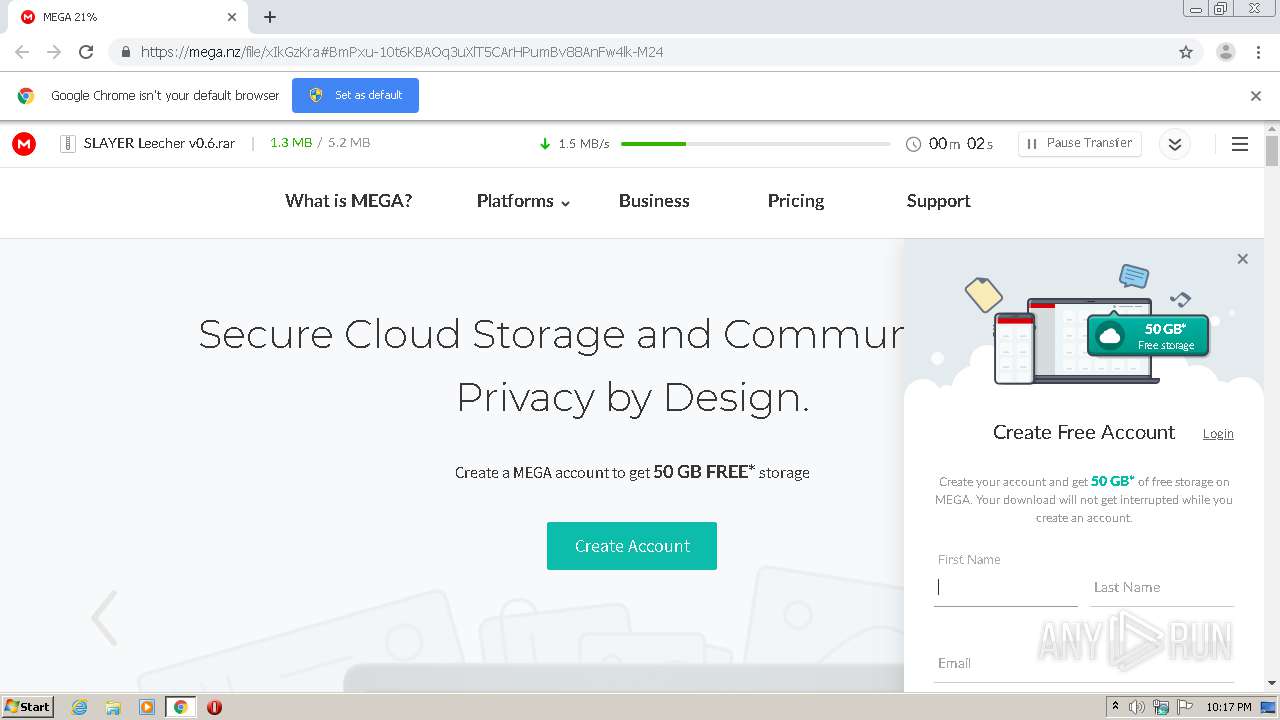
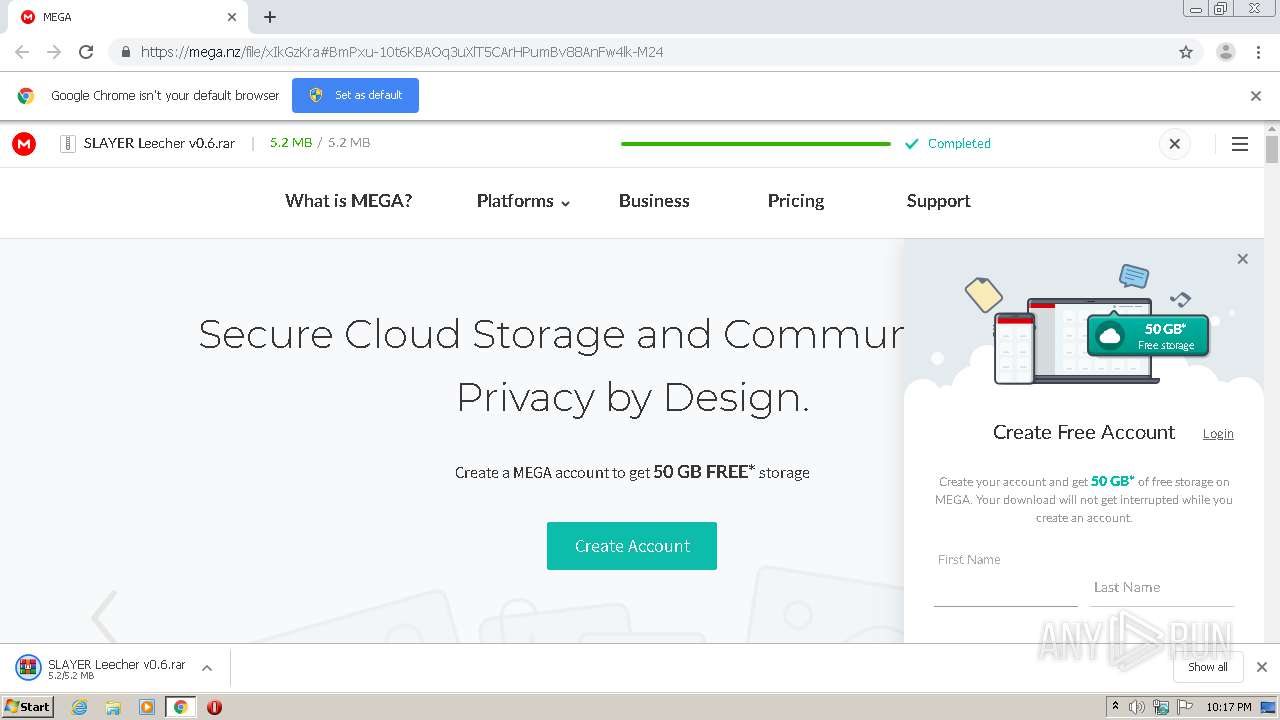
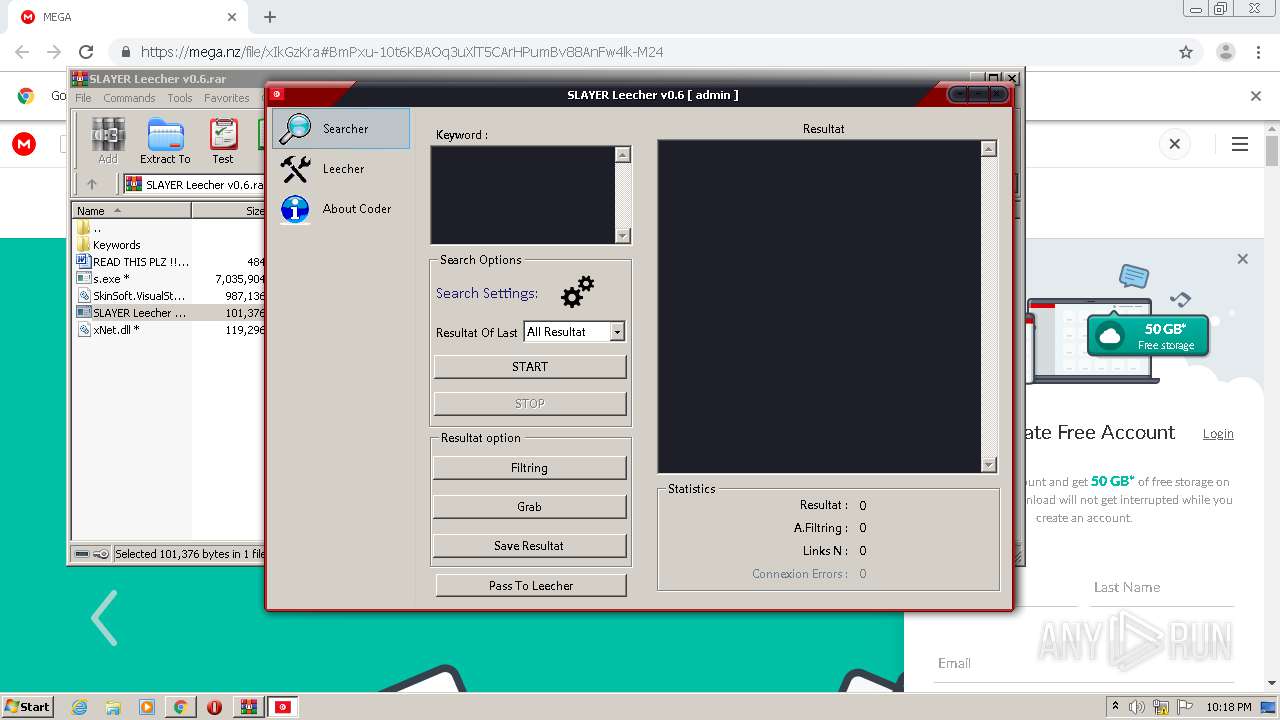
| URL: | https://mega.nz/file/xIkGzKra#BmPxu-10t6KBAOq3uXlT5CArHPumBv88AnFw4lk-M24 |
| Full analysis: | https://app.any.run/tasks/31757ebc-0c5a-4f47-838c-0ce3d8f0faaa |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2020, 21:17:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0607C2BB6CE8E9ACCB65DD643B2FA379 |
| SHA1: | 525906C773D493DB2598F4F01560CF1426AF79A7 |
| SHA256: | 8C805E002BAE5CBFA5004BE99A8B67E77F0E5AF21E6D5C2C03C298E33E0FCB65 |
| SSDEEP: | 3:N8X/iM8pGVSk9LmQwAVB:2R8cP9LwaB |
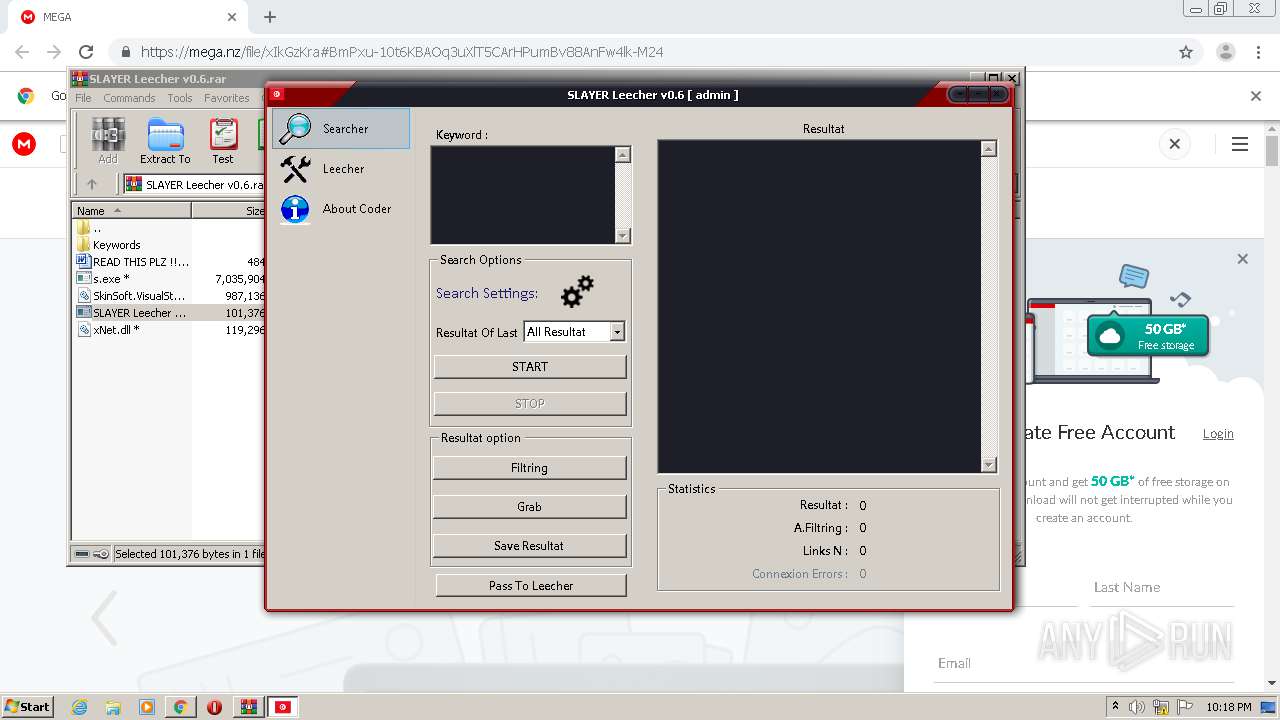
MALICIOUS
Loads dropped or rewritten executable
- s.exe (PID: 2428)
Application was dropped or rewritten from another process
- SLAYER Leecher v0.6.exe (PID: 3204)
- s.exe (PID: 2428)
- SLAYER Leecher v0.6.exe (PID: 2604)
Changes settings of System certificates
- s.exe (PID: 2428)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2316)
Starts CMD.EXE for commands execution
- SLAYER Leecher v0.6.exe (PID: 2604)
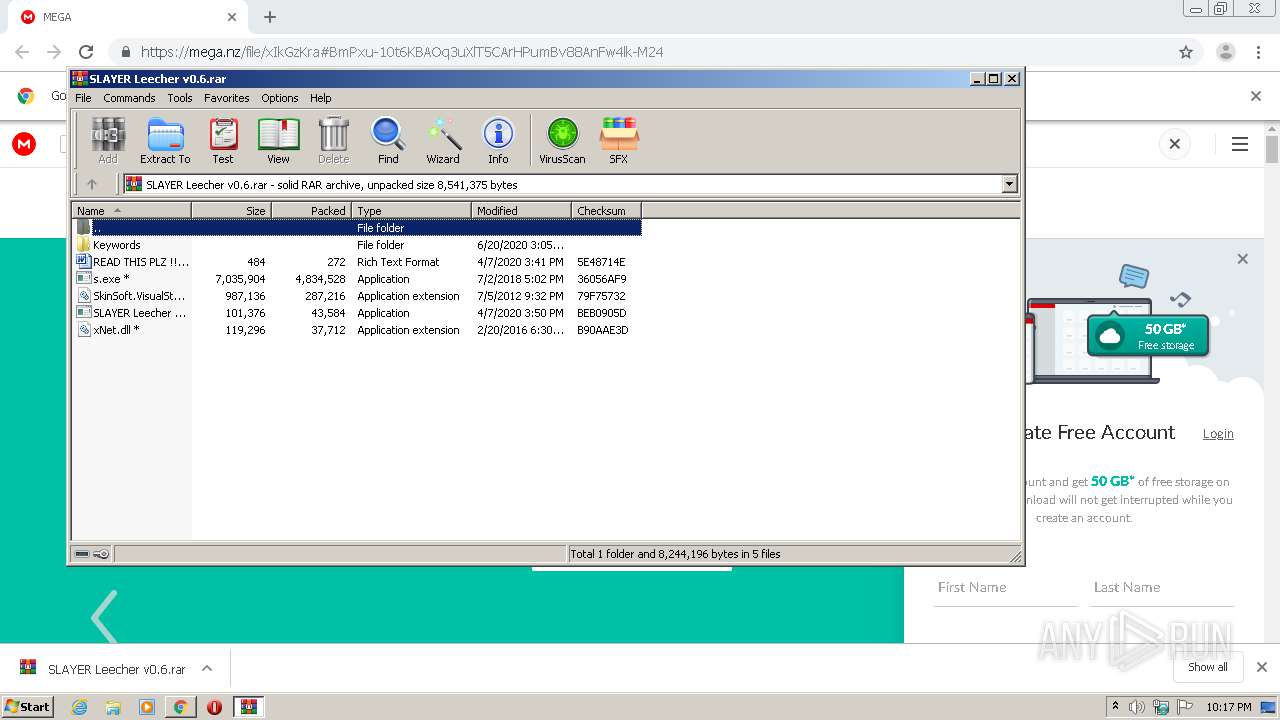
Executable content was dropped or overwritten
- s.exe (PID: 2428)
- WinRAR.exe (PID: 956)
Reads Environment values
- s.exe (PID: 2428)
Adds / modifies Windows certificates
- s.exe (PID: 2428)
INFO
Application launched itself
- chrome.exe (PID: 2316)
Reads the hosts file
- chrome.exe (PID: 3892)
- chrome.exe (PID: 2316)
Reads settings of System Certificates
- s.exe (PID: 2428)
- chrome.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
31
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18131213744337169684 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
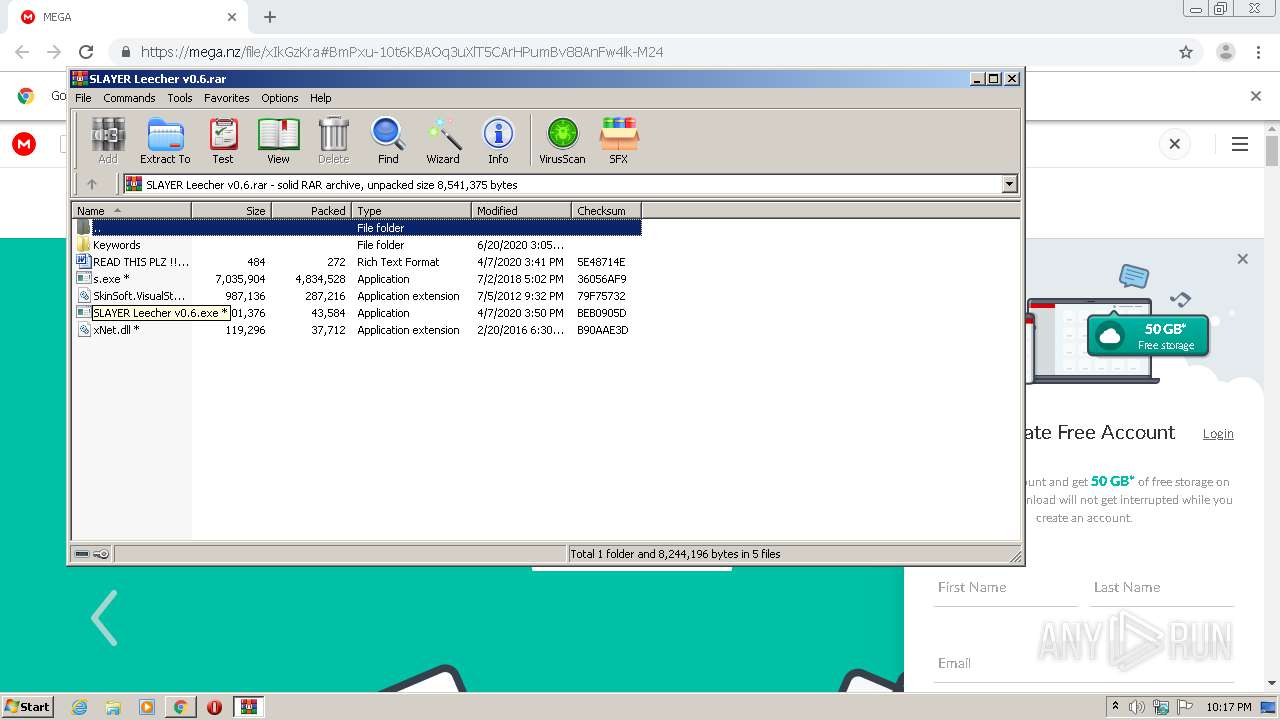
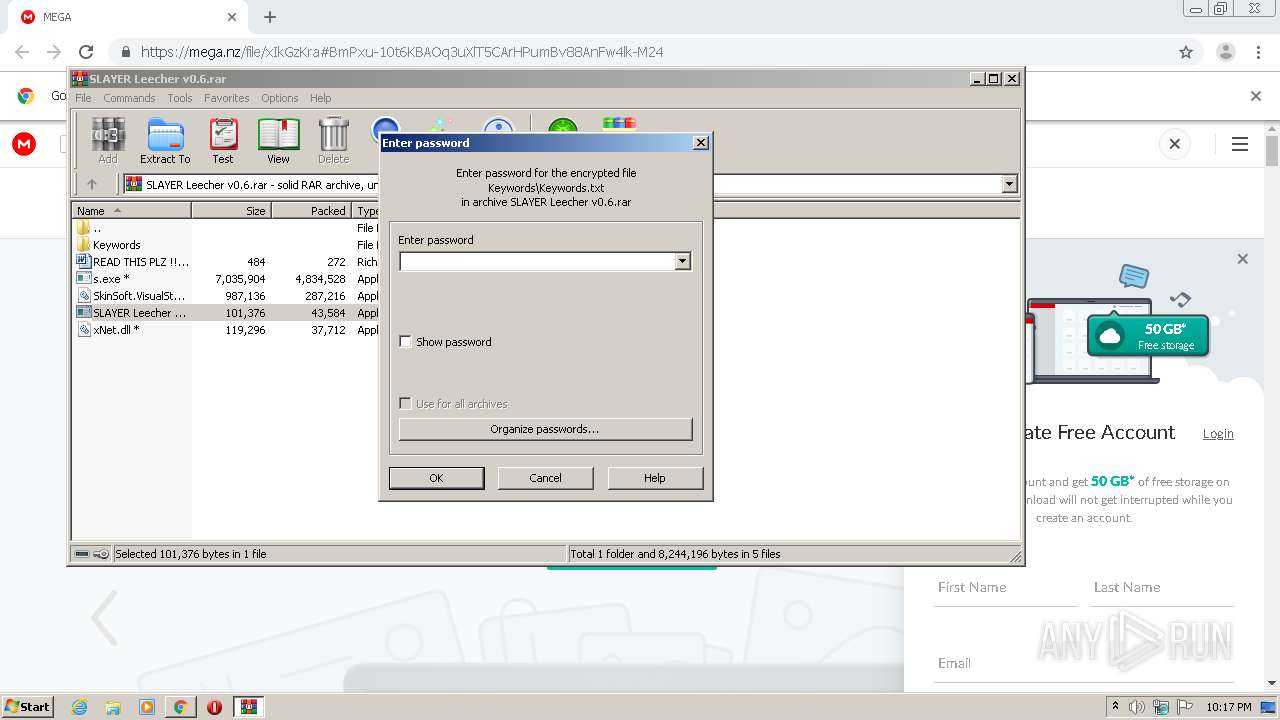
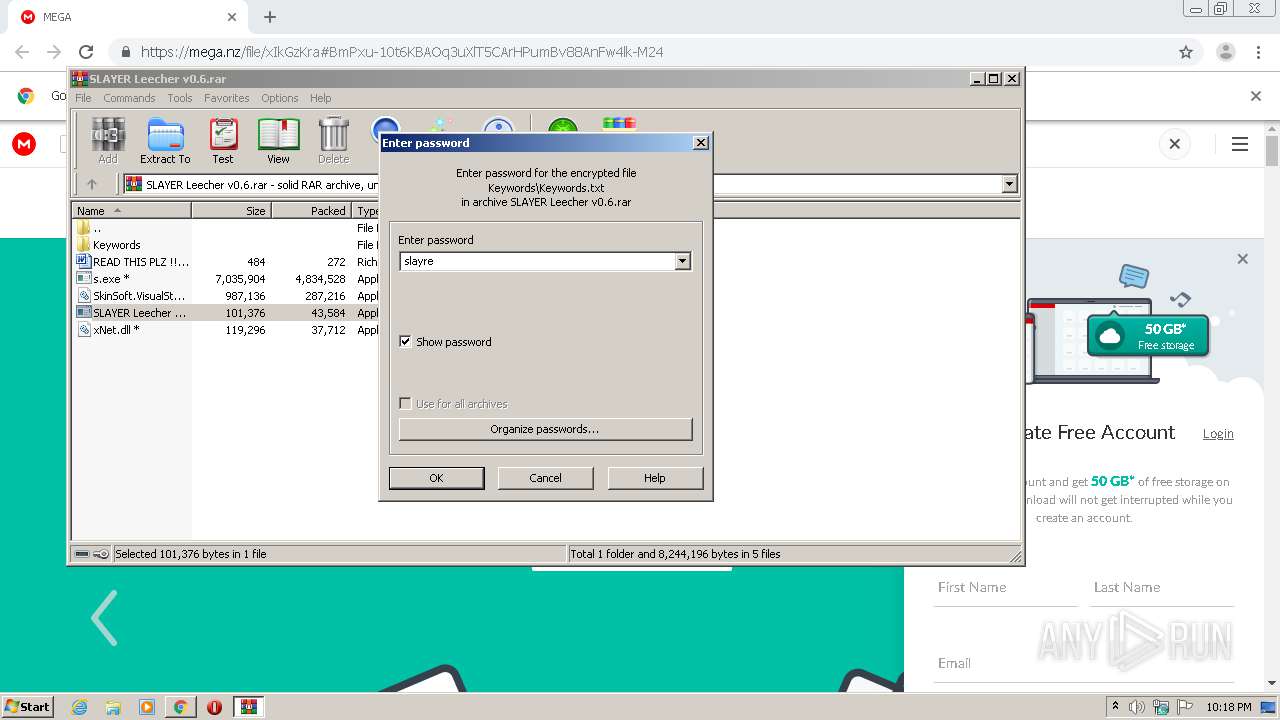
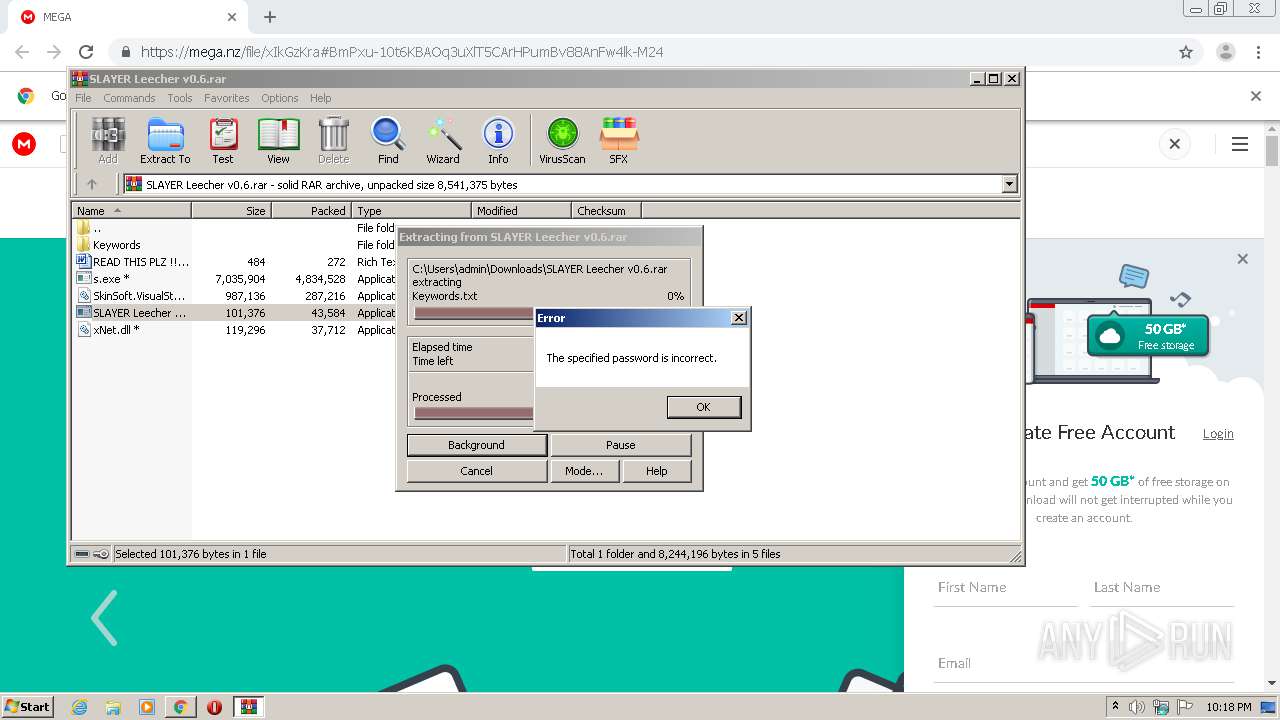
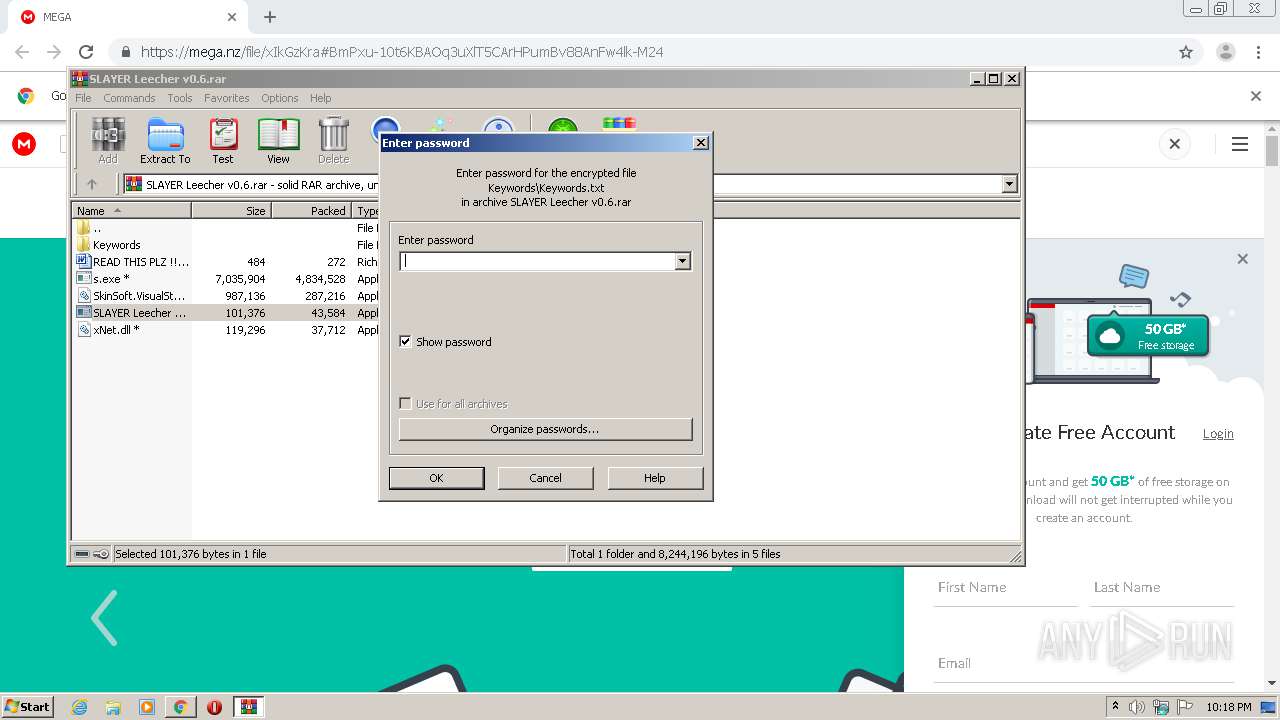
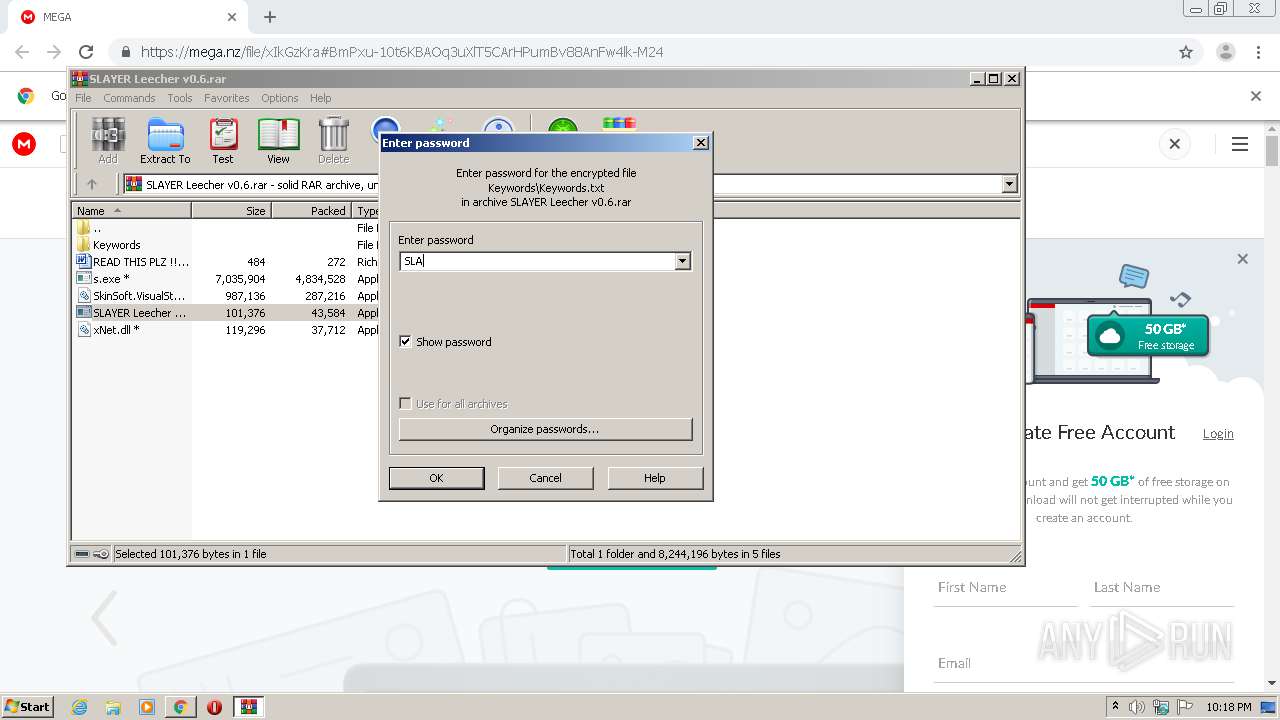
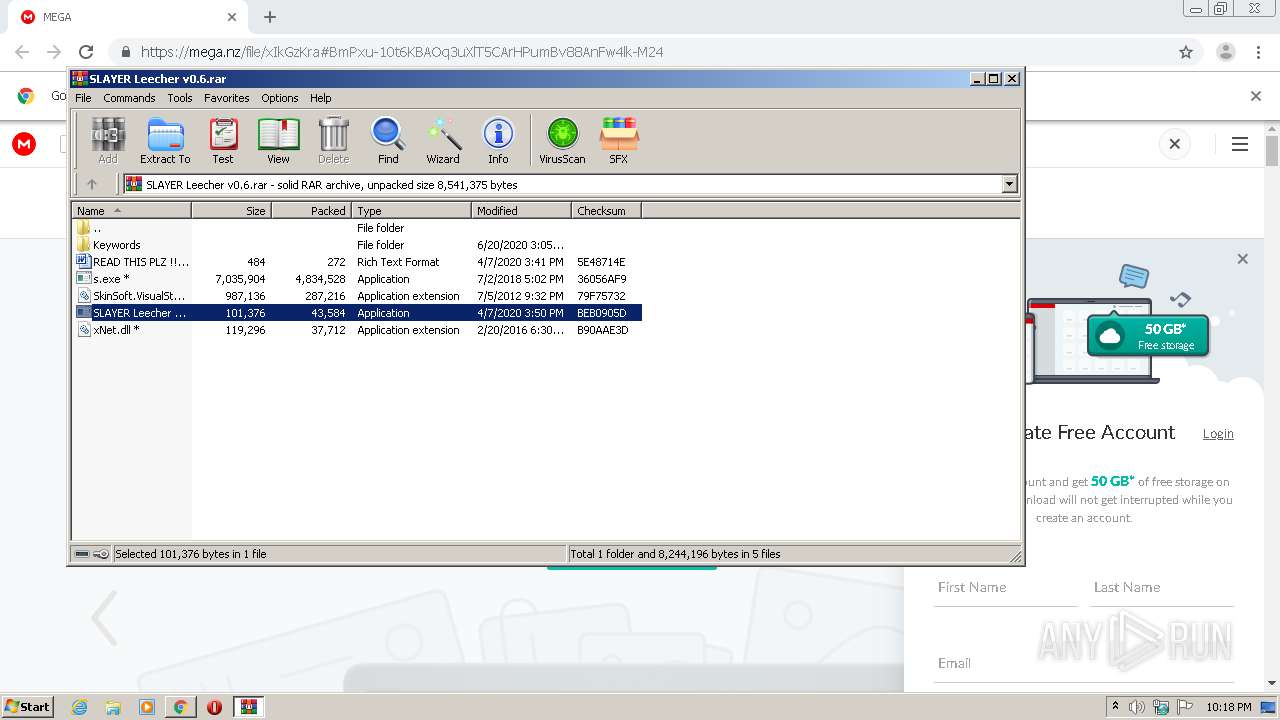
| 956 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\SLAYER Leecher v0.6.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1884 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8977747069465295978 --mojo-platform-channel-handle=3836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12637610753469497201 --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7673447306507518233 --mojo-platform-channel-handle=4988 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17509787856377982610 --mojo-platform-channel-handle=4500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14749223362577807783 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4076609445875940279 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6252725338639059457,464196391227591808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11314841011382969098 --mojo-platform-channel-handle=4376 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 368
Read events
1 599
Write events
764
Delete events
5
Modification events
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2316-13238457445324125 |
Value: 259 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2316) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
7
Suspicious files
39
Text files
282
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F024366-90C.pma | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\19b781b1-17a9-477b-a3a4-2aa7bb594b04.tmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf695f.TMP | text | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf6b92.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
40
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | chrome.exe | GET | 200 | 173.194.183.72:80 | http://r3---sn-aigl6ned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.192.69.26&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1593983771&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
3892 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3892 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3892 | chrome.exe | GET | 200 | 173.194.5.203:80 | http://r5---sn-aigl6n76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.192.69.26&mm=28&mn=sn-aigl6n76&ms=nvh&mt=1593983771&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
3892 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
3892 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |