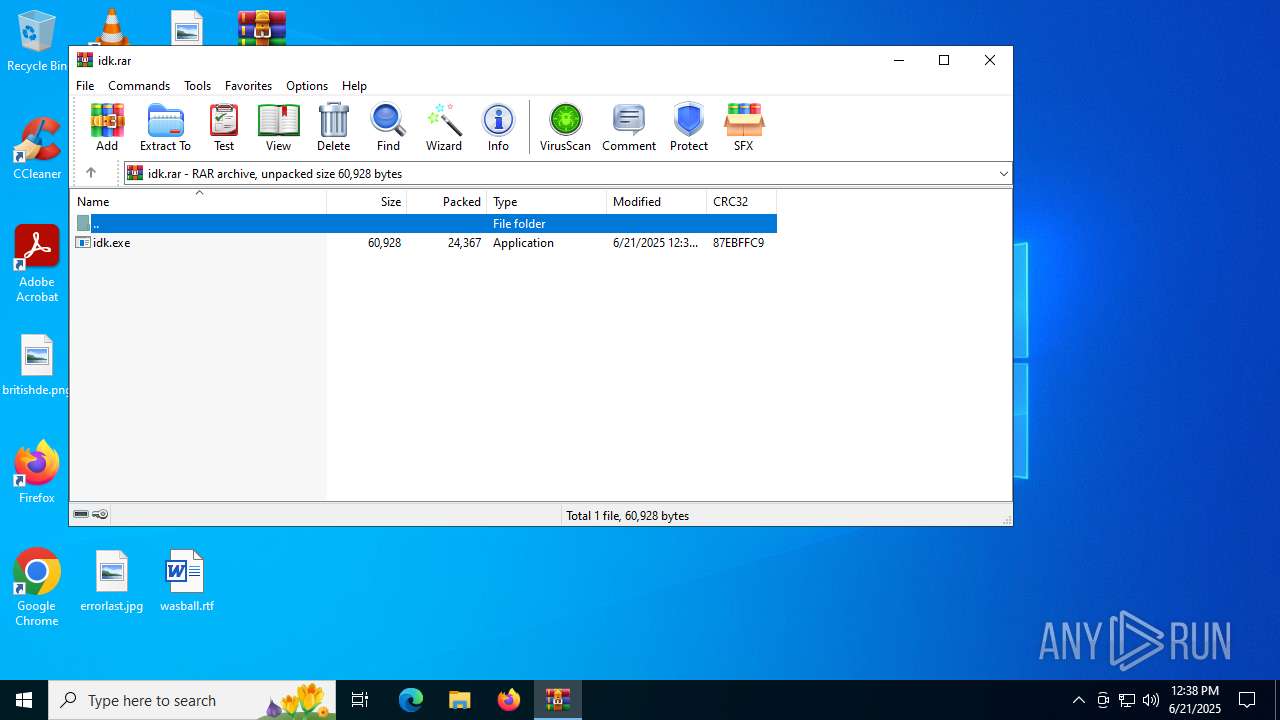
| File name: | idk.rar |
| Full analysis: | https://app.any.run/tasks/dc3e5b62-28ae-41af-b1e5-d408c030eec2 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:38:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | E9F6D33606BE70BD42B58277D1BB3794 |
| SHA1: | C0906C153951780C6B288475CA88CA4BE6598E2F |
| SHA256: | 8C7845530CDCD8B24B60FA80C708D474A222FBA5A311B9758FCCD424404EFC9C |
| SSDEEP: | 768:4i2JyWgWOpgG7hxSG5CPrdDxdzJ4E+uICI:5ALtohxS6CPJJ+PCI |
MALICIOUS
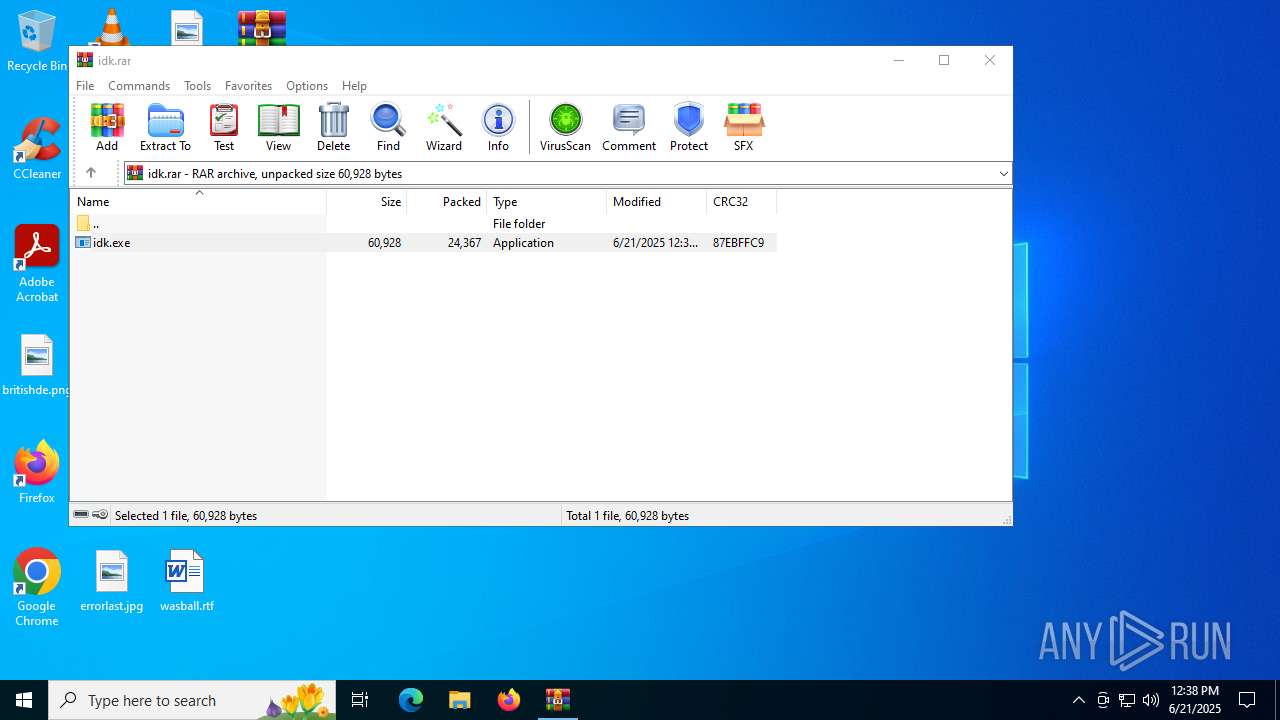
Generic archive extractor
- WinRAR.exe (PID: 3976)
SUSPICIOUS
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 6016)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 5368)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 1180)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 1192)
Starts CMD.EXE for commands execution
- idk.exe (PID: 4800)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 5824)
Reads security settings of Internet Explorer
- idk.exe (PID: 4800)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- idk.exe (PID: 4800)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3976)
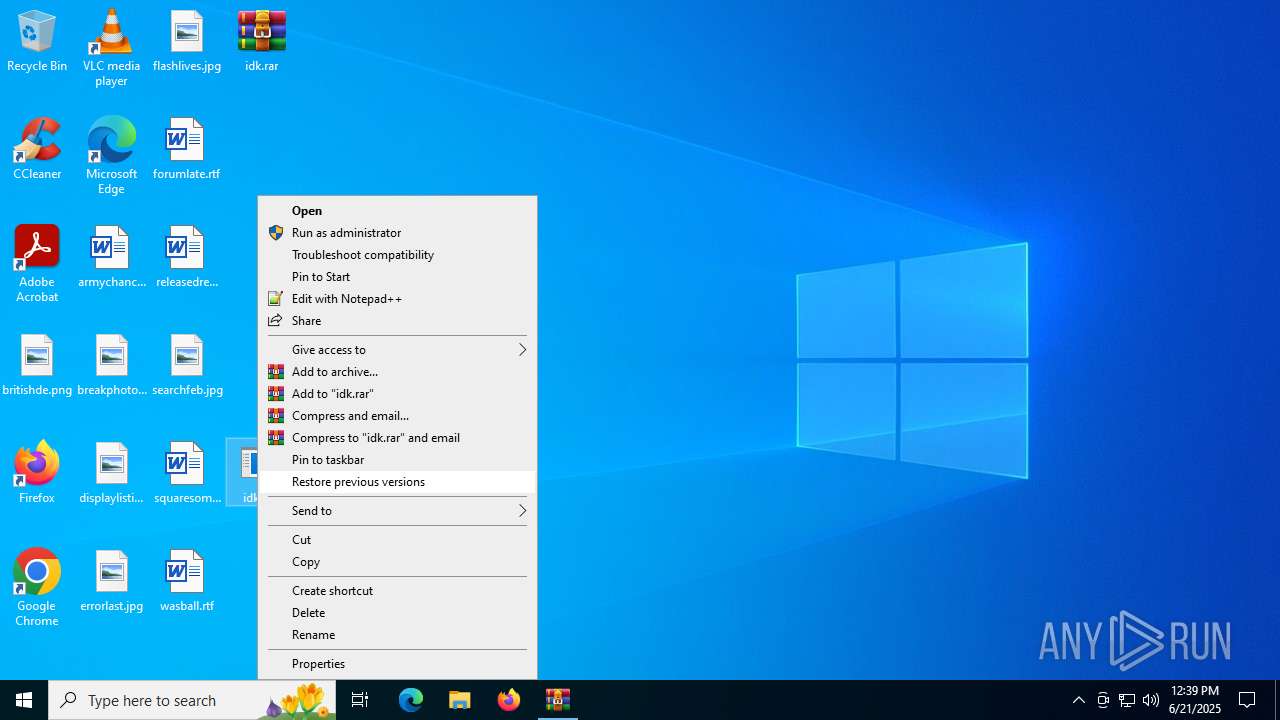
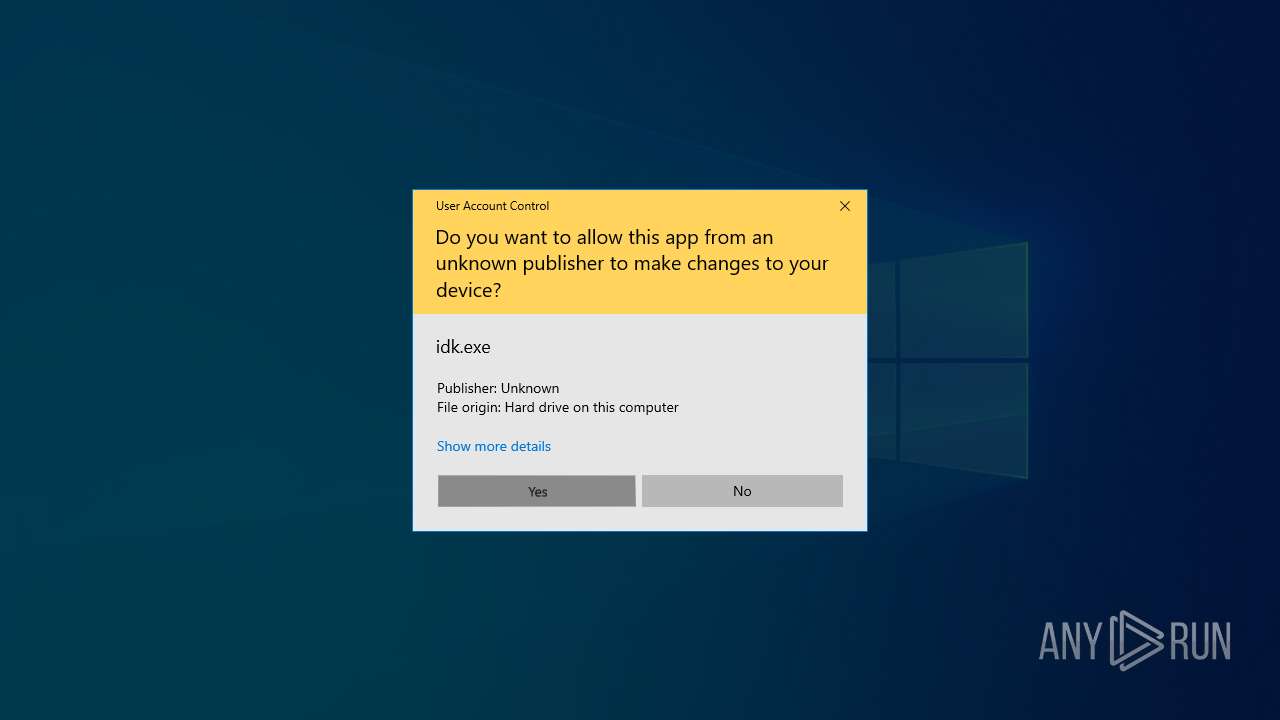
Manual execution by a user
- idk.exe (PID: 4800)
Reads the computer name
- idk.exe (PID: 4800)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1180)
- WMIC.exe (PID: 1052)
- WMIC.exe (PID: 3960)
- WMIC.exe (PID: 3788)
Checks supported languages
- idk.exe (PID: 4800)
Checks proxy server information
- idk.exe (PID: 4800)
Reads the machine GUID from the registry
- idk.exe (PID: 4800)
Creates files or folders in the user directory
- idk.exe (PID: 4800)
Reads the software policy settings
- idk.exe (PID: 4800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 24367 |
| UncompressedSize: | 60928 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | idk.exe |
Total processes
140
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | wmic cpu get ProcessorId | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | wmic path win32_VideoController get name | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | C:\WINDOWS\system32\cmd.exe /c wmic bios get serialnumber | C:\Windows\System32\cmd.exe | — | idk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3788 | wmic diskdrive get SerialNumber,Model | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3960 | wmic bios get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3976 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\idk.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4800 | "C:\Users\admin\Desktop\idk.exe" | C:\Users\admin\Desktop\idk.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5368 | C:\WINDOWS\system32\cmd.exe /c wmic path win32_VideoController get name | C:\Windows\System32\cmd.exe | — | idk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | idk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5824 | C:\WINDOWS\system32\cmd.exe /c wmic diskdrive get SerialNumber,Model | C:\Windows\System32\cmd.exe | — | idk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 858
Read events
2 847
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\idk.rar | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4800) idk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4800) idk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4800 | idk.exe | C:\Windows\INF\machine.PNF | binary | |
MD5:4C103190BC521FF032845C1B5FDADC4F | SHA256:28C1DEE803488C32BF5229B05FB3F6DA8959A436BB17D331E68AFA61A3BE932F | |||
| 4800 | idk.exe | C:\Windows\INF\basicrender.PNF | binary | |
MD5:8567F128605CC616A38D0870D077D165 | SHA256:7B2D28D317F49EED7BC242241E54EB3FFFB512C5FB6F719C4F5E9395E6B1F533 | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.34500\idk.exe | executable | |
MD5:3AB69B83726B5C16A2249C55B03BA13A | SHA256:D1FA6AF98ECCC77D4B62CB4D5D30981A774F7E7CE375D11D173AD825C3602A64 | |||
| 4800 | idk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:B948C388459A33F7700C3AF48D3891CC | SHA256:33BBDEBF9DAB433A1CF14D0115223209E2D671F61080C65C1847892205414413 | |||
| 4800 | idk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:524E14D71D866097D97F983DB221CEAB | SHA256:48DAA86BF178FC1020770C3DC0ABDE1C42963C3AE29BF73B2ECF1E0D8B0D60CE | |||
| 4800 | idk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:386B22A87DF5778837C5FD54949F3830 | SHA256:F6E34ABAEA4090C2F1C25594AE3C20FA464F204EDC4FBF27E55D7D9BB5FEBF51 | |||
| 4800 | idk.exe | C:\Users\admin\Desktop\report.txt | text | |
MD5:FD4BC4DB0C1066033ED2A4D0360C814D | SHA256:7BCBC9D18C4F4664EDE304A1296F3DCAFCA40BDDF90551073F5465BD5DFDAE63 | |||
| 4800 | idk.exe | C:\Windows\INF\basicdisplay.PNF | binary | |
MD5:914DCB989709A0CE3F4B24A4CD147F1A | SHA256:C2FEE0EAD23C7B3B509FDDE94DDD6A549F999F364C5CA9D09AC084F22BC0ECB4 | |||
| 4800 | idk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:1B462073252E95DB1CA3B54C1D2DFCBB | SHA256:6C9EDAFFF008D48DD0B8F7782FBB52AC7F430F4951FE28089F304DD61B9A4982 | |||
| 4800 | idk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACA7D89F79C6EF86F63EB2FF5D5C876A_8AD14988285EE6F6CBBCCEE3BD7C8E58 | binary | |
MD5:73C5E9447BAD1C3257B18C5FB7FBE7FB | SHA256:410FD808121A861EBEA8F0FBBF9B12E0FBD2E67D15EE5A0DE42990702A7C28E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2596 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4800 | idk.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | unknown | — | — | whitelisted |
4800 | idk.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | whitelisted |
4800 | idk.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCEVy5zGFpEO7 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4156 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2596 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2596 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4800 | idk.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger Inc | GB | whitelisted |
4800 | idk.exe | 192.124.249.36:80 | ocsp.godaddy.com | SUCURI-SEC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.telegram.org |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
4800 | idk.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
4800 | idk.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |