| File name: | ep_setup.exe |
| Full analysis: | https://app.any.run/tasks/608cea06-601a-4a81-884c-59fb55712963 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2025, 22:40:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | F164888A6FBC646B093F6AF6663F4E63 |
| SHA1: | 3C0BB9F9A4AD9B1C521AD9FC30EC03668577C97C |
| SHA256: | 8C5A3597666F418B5C857E68C9A13B7B6D037EA08A988204B572F053450ADD67 |
| SSDEEP: | 98304:R/TvjMleJaJ4kJQeSWSeWdzPSkAdsC5pqNP+/YTXjM/cIcSoIov1UXuykZyzZ2Cg:mriEcSB6mCsb5x |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- ep_setup.exe (PID: 6800)
SUSPICIOUS
Reads security settings of Internet Explorer
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
- StartMenuExperienceHost.exe (PID: 6544)
Reads the date of Windows installation
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
- StartMenuExperienceHost.exe (PID: 6544)
- SearchApp.exe (PID: 1708)
Application launched itself
- ep_setup.exe (PID: 6584)
Starts SC.EXE for service management
- ep_setup.exe (PID: 6800)
Uses TASKKILL.EXE to kill process
- ep_setup.exe (PID: 6800)
Stops a currently running service
- sc.exe (PID: 7048)
Executable content was dropped or overwritten
- ep_setup.exe (PID: 6800)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5864)
- regsvr32.exe (PID: 5496)
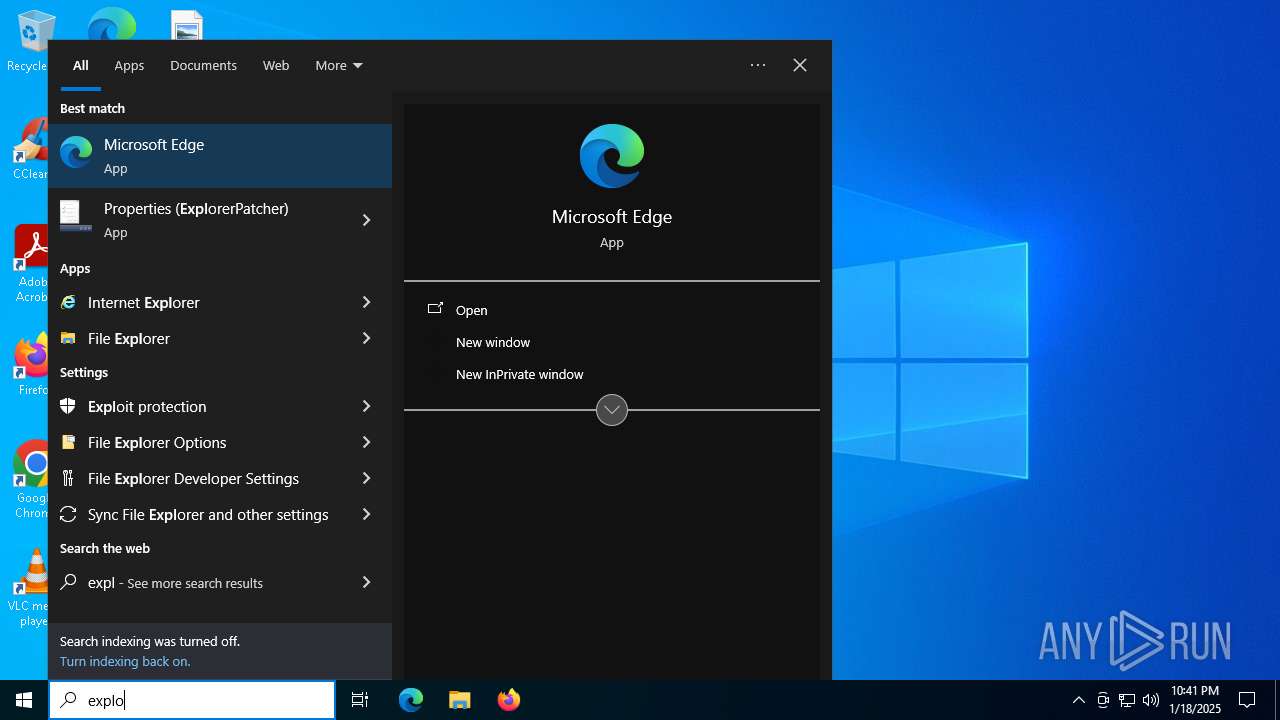
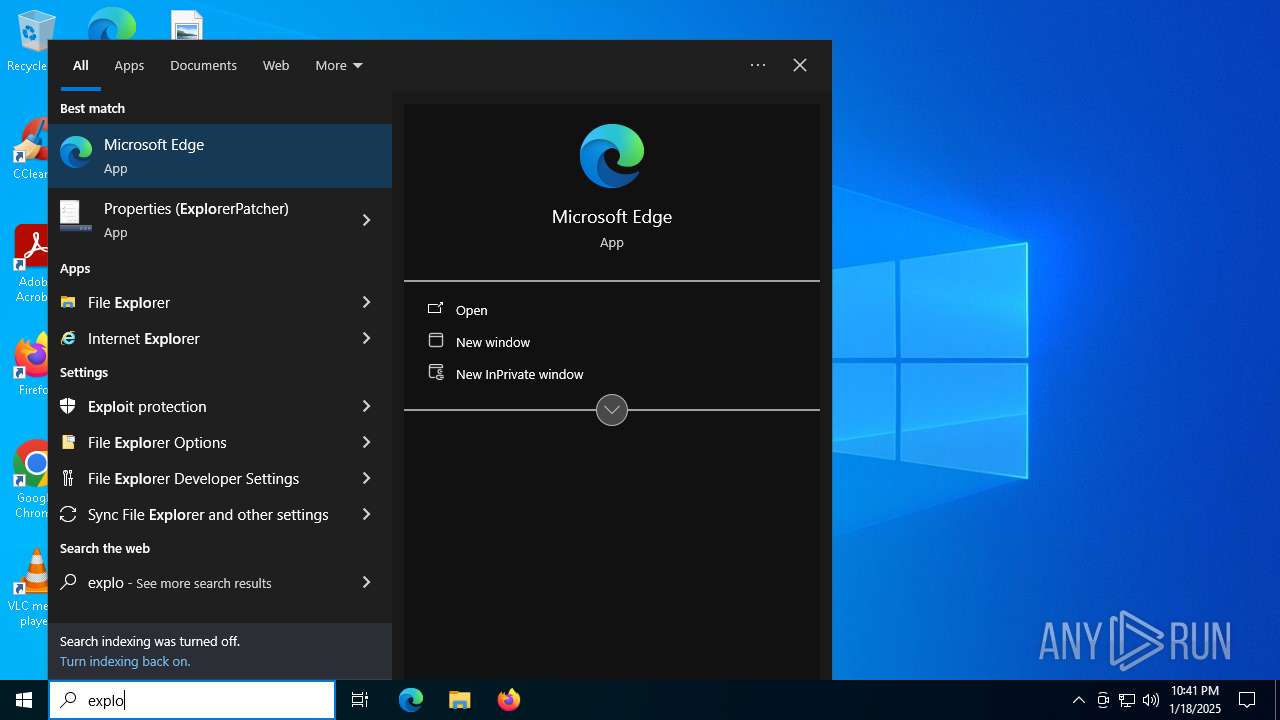
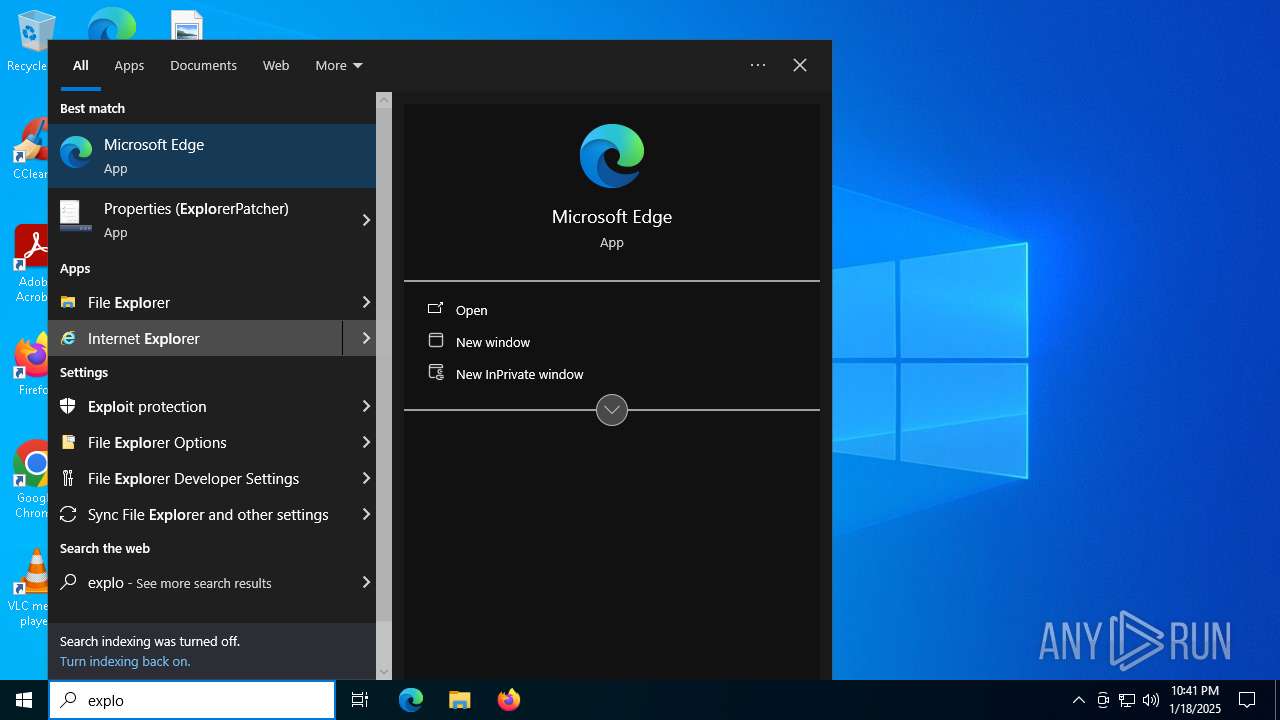
The process executes via Task Scheduler
- explorer.exe (PID: 3544)
Process drops legitimate windows executable
- ep_setup.exe (PID: 6800)
The process creates files with name similar to system file names
- ep_setup.exe (PID: 6800)
Windows service management via SC.EXE
- sc.exe (PID: 7116)
Creates a software uninstall entry
- ep_setup.exe (PID: 6800)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 3544)
INFO
The sample compiled with english language support
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
Creates files in the program directory
- ep_setup.exe (PID: 6800)
Checks supported languages
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
- TextInputHost.exe (PID: 6504)
- SearchApp.exe (PID: 1708)
- StartMenuExperienceHost.exe (PID: 6544)
Reads the computer name
- ep_setup.exe (PID: 6800)
- ep_setup.exe (PID: 6584)
- StartMenuExperienceHost.exe (PID: 6544)
- TextInputHost.exe (PID: 6504)
- SearchApp.exe (PID: 1708)
Process checks computer location settings
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
- StartMenuExperienceHost.exe (PID: 6544)
- SearchApp.exe (PID: 1708)
The process uses the downloaded file
- ep_setup.exe (PID: 6584)
- ep_setup.exe (PID: 6800)
- explorer.exe (PID: 3544)
Reads security settings of Internet Explorer
- explorer.exe (PID: 3544)
- BackgroundTransferHost.exe (PID: 5268)
- BackgroundTransferHost.exe (PID: 2144)
- BackgroundTransferHost.exe (PID: 1576)
- BackgroundTransferHost.exe (PID: 2432)
- BackgroundTransferHost.exe (PID: 7056)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 6544)
Reads Environment values
- SearchApp.exe (PID: 1708)
Checks proxy server information
- SearchApp.exe (PID: 1708)
- BackgroundTransferHost.exe (PID: 2144)
- explorer.exe (PID: 3544)
Reads the software policy settings
- explorer.exe (PID: 3544)
- SearchApp.exe (PID: 1708)
- BackgroundTransferHost.exe (PID: 2144)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 1708)
Creates files or folders in the user directory
- explorer.exe (PID: 3544)
- BackgroundTransferHost.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:02 13:43:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 151552 |
| InitializedDataSize: | 10995712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8c18 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 22621.4317.67.1 |
| ProductVersionNumber: | 22621.4317.67.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | ExplorerPatcher Developers |
| FileDescription: | ExplorerPatcher Setup Program |
| FileVersion: | 22621.4317.67.1 |
| InternalName: | ep_setup.exe |
| LegalCopyright: | (C) 2021-2024 ExplorerPatcher Developers. All rights reserved. |
| OriginalFileName: | ep_setup.exe |
| ProductName: | ExplorerPatcher |
| ProductVersion: | 22621.4317.67.1 |
Total processes
162
Monitored processes
23
Malicious processes
2
Suspicious processes
1
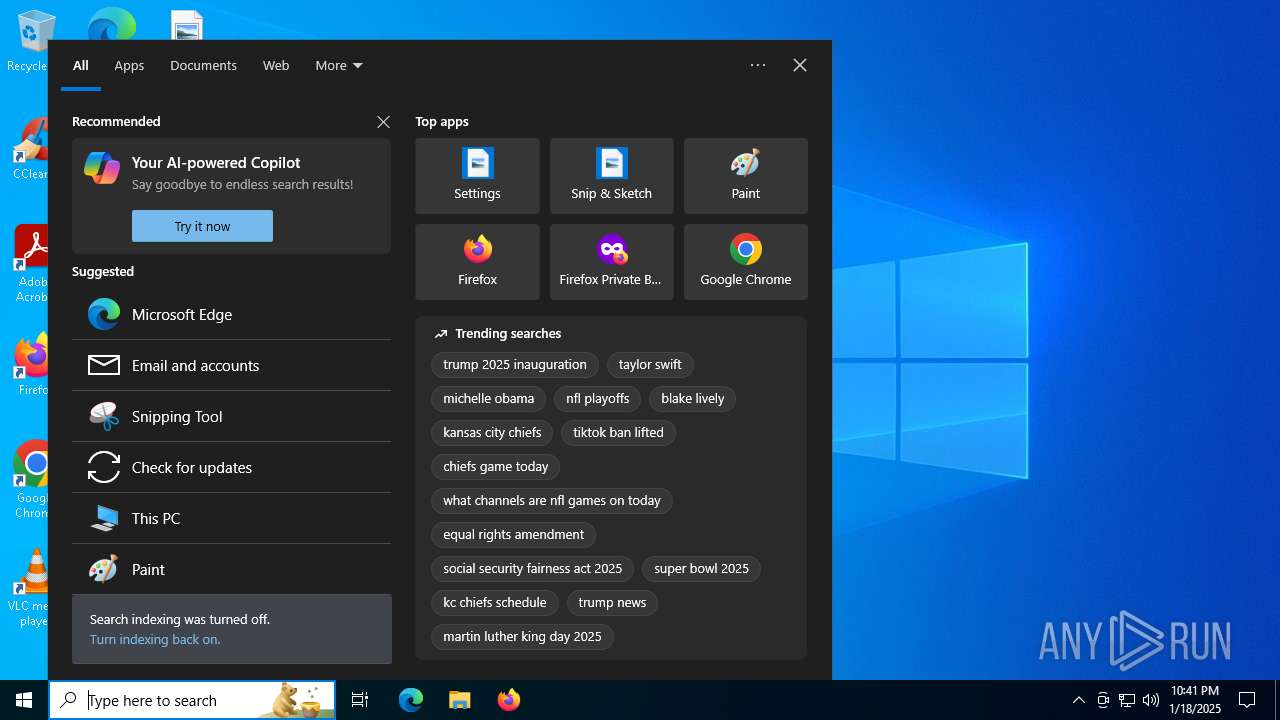
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1708 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2160 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | "C:\WINDOWS\explorer.exe" /NoUACCheck | C:\Windows\explorer.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | "C:\WINDOWS\explorer.exe" | C:\Windows\explorer.exe | — | ep_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 2 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5268 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5496 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\ExplorerPatcher\ep_weather_host_stub.dll" | C:\Windows\System32\regsvr32.exe | — | ep_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5864 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\ExplorerPatcher\ep_weather_host.dll" | C:\Windows\System32\regsvr32.exe | — | ep_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 974
Read events
34 623
Write events
323
Delete events
28
Modification events
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\ExplorerPatcher\ep_setup.exe" /uninstall | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | DisplayName |
Value: ExplorerPatcher | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | Publisher |
Value: VALINET Solutions SRL | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | DisplayVersion |
Value: 22621.4317.67.1 | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | VersionMajor |
Value: 67 | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (6800) ep_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{D17F1E1A-5919-4427-8F89-A1A8503CA3EB}_ExplorerPatcher |
| Operation: | write | Name: | DisplayIcon |
Value: C:\WINDOWS\explorer.exe | |||
| (PID) Process: | (5864) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{A6EA9C2D-4982-4827-9204-0AC532959F6D} |
| Operation: | write | Name: | AppID |
Value: {A6EA9C2D-4982-4827-9204-0AC532959F6D} | |||
Executable files
12
Suspicious files
72
Text files
168
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6800 | ep_setup.exe | C:\Program Files\ExplorerPatcher\ExplorerPatcher.IA-32.dll | executable | |
MD5:E5BB14C2B9AF4D5BF6C38E0759F454DD | SHA256:A4FD75AC8F852EDC8BDB88A705EEEE2C93F6EC51EF9FA0739A11A690A067C66D | |||
| 2160 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:AB5E64163C799810FBAE0EDF3F84DED0 | SHA256:E59DEB538F7811C40D70C6688E043A751562DDE8EDB00780E29C6FA9ED28135B | |||
| 1708 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:F6151100CDD56CA5BA1AC730E11AC82D | SHA256:BA1C917CB4FD4F2168ACBBAF2515DDB9DCA69BCD6AB743FD2EB220E70243CDC5 | |||
| 1708 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
| 6800 | ep_setup.exe | C:\Program Files\ExplorerPatcher\ExplorerPatcher.amd64.dll | executable | |
MD5:8BFCA71ADD96D3DE75173D464792E2B9 | SHA256:5AAA6BAB20B7116B32BDDBA1DF216F7476557BB48397E1968A49EDE14E6C377D | |||
| 6800 | ep_setup.exe | C:\Windows\dxgi.dll | executable | |
MD5:047B192A9C703FC5A2C2764DB869FF5C | SHA256:1971C57F88849B4069BE06D3784E0968755C916FA1564A3F8F05610D3B02CDCC | |||
| 6800 | ep_setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\ExplorerPatcher\Properties (ExplorerPatcher).lnk | binary | |
MD5:EBA08817F08D4CFCA8AC98059DCFC003 | SHA256:9AB43DBD6C4EA0D84A1CC11760601A6A3D8D00526444BFB5D1DA85024D44B21E | |||
| 6800 | ep_setup.exe | C:\Program Files\ExplorerPatcher\ep_dwm.exe | executable | |
MD5:6563C5338177FF66050EADFE3960C567 | SHA256:315AF6DF079B31BAC26156C9DDA8CC415C76408A39972346C238888AAFF79921 | |||
| 6800 | ep_setup.exe | C:\Program Files\ExplorerPatcher\WebView2Loader.dll | executable | |
MD5:C5F0C46E91F354C58ECEC864614157D7 | SHA256:465A7DDFB3A0DA4C3965DAF2AD6AC7548513F42329B58AEBC337311C10EA0A6F | |||
| 1708 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\vOJNaIfAXvJzmnBm845ss-M9YR8[1].css | text | |
MD5:87BBB1A289EDC24C9F06B88229765467 | SHA256:85B291C46F9D1EEEC71DB839F649D748F48B203EA836F3ACE3B9B761947D960C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
60
DNS requests
38
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
3544 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
3544 | explorer.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
3544 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEE4o94a2bBo7lCzSxA63QqU%3D | unknown | — | — | whitelisted |
3544 | explorer.exe | GET | 302 | 204.79.197.219:80 | http://msdl.microsoft.com/download/symbols/twinui.pcshell.pdb/3F0945AE4BC25ECE16353588B05D30B61/twinui.pcshell.pdb | unknown | — | — | whitelisted |
3544 | explorer.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2632 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |