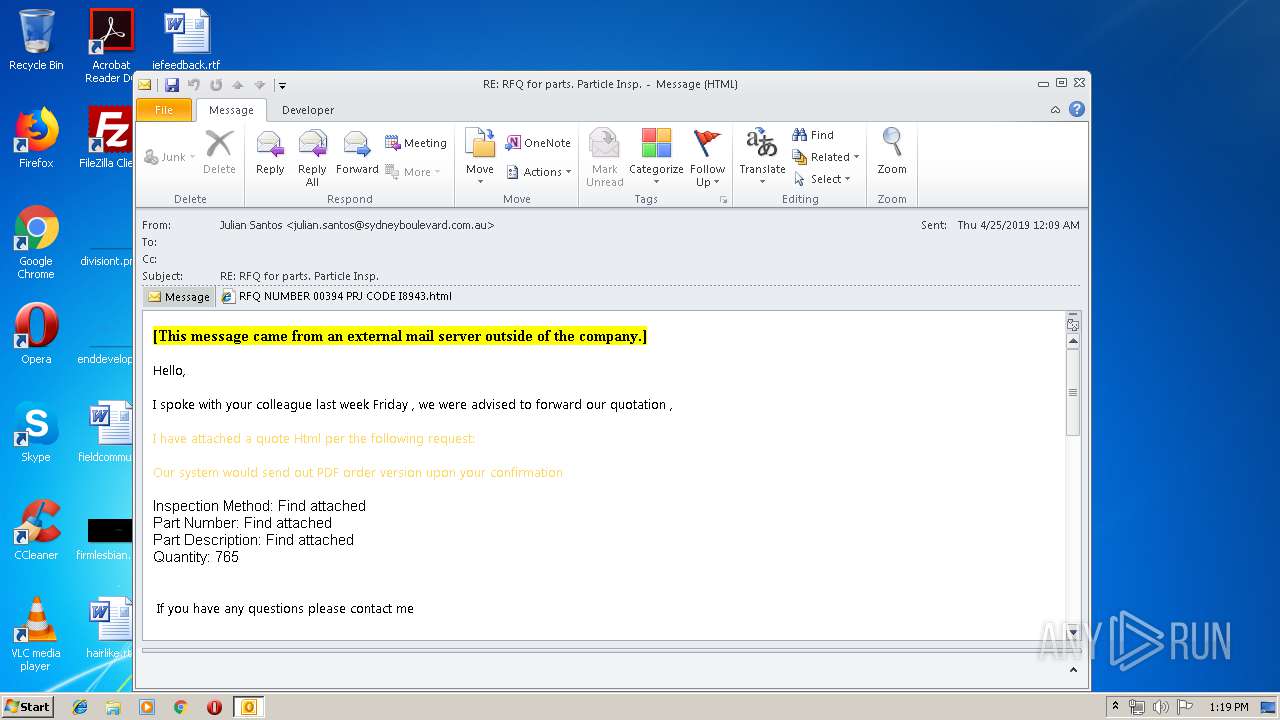
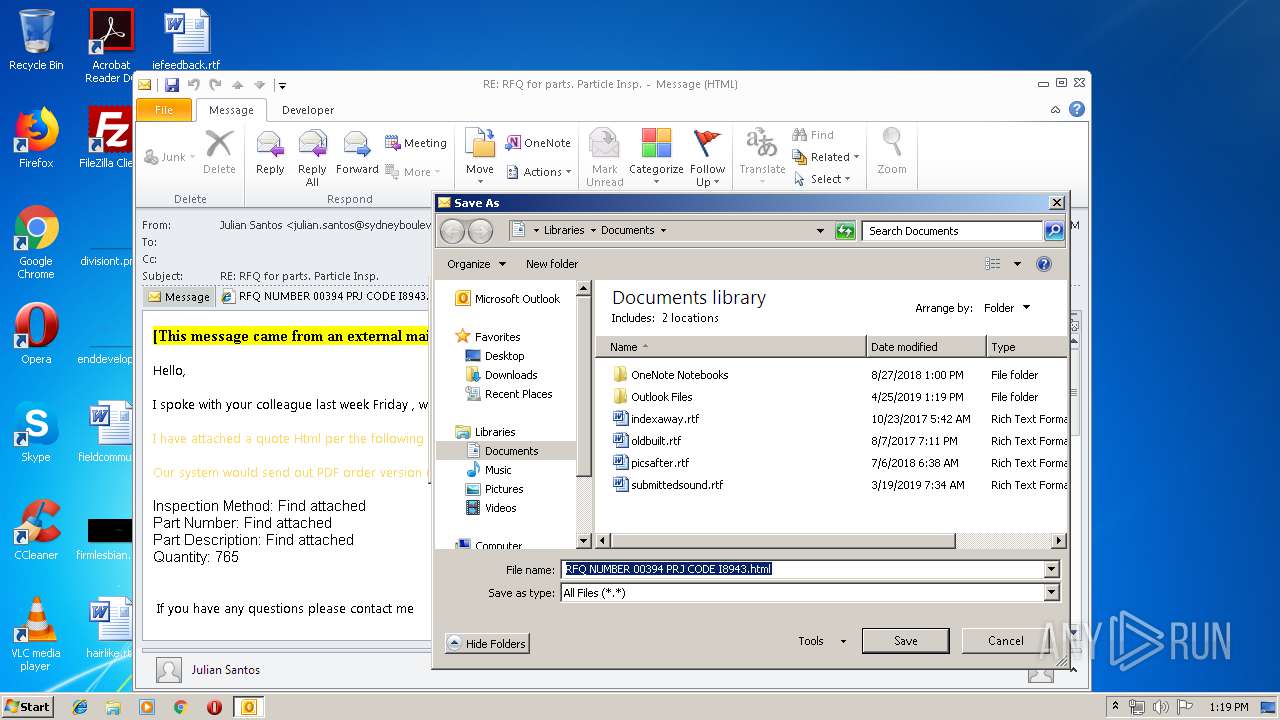
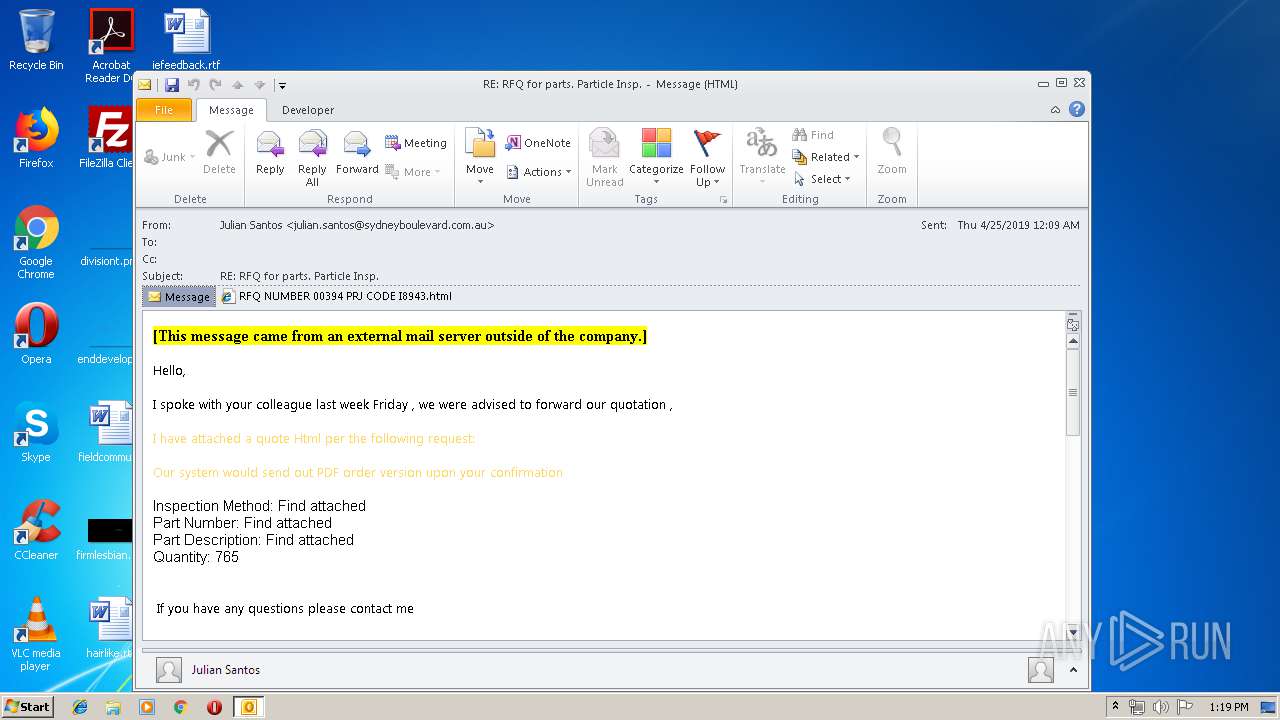
| File name: | RE RFQ for parts. Particle Insp.msg |
| Full analysis: | https://app.any.run/tasks/a5749851-143f-4937-ade2-f46ff0991528 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 12:18:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 063DC8E948596662501CB8693283AA51 |
| SHA1: | 4383671FE7CB231346BA19780FF66050E0A57B39 |
| SHA256: | 8C401A2CF506E1173AAF3EA67BEEC20D6B49C4EF7FEA3161BBAA252CEA536F69 |
| SSDEEP: | 3072:5q+zCDdoXSF27lBFF4TfU+pPx70zkbAxGbm9v6lHy/sQEU6LM2t8f:QICZoXY4lSgYqqAxGoJRB8t8f |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2344)
Modifies files in Chrome extension folder
- chrome.exe (PID: 636)
INFO
Application launched itself
- chrome.exe (PID: 636)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
53
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
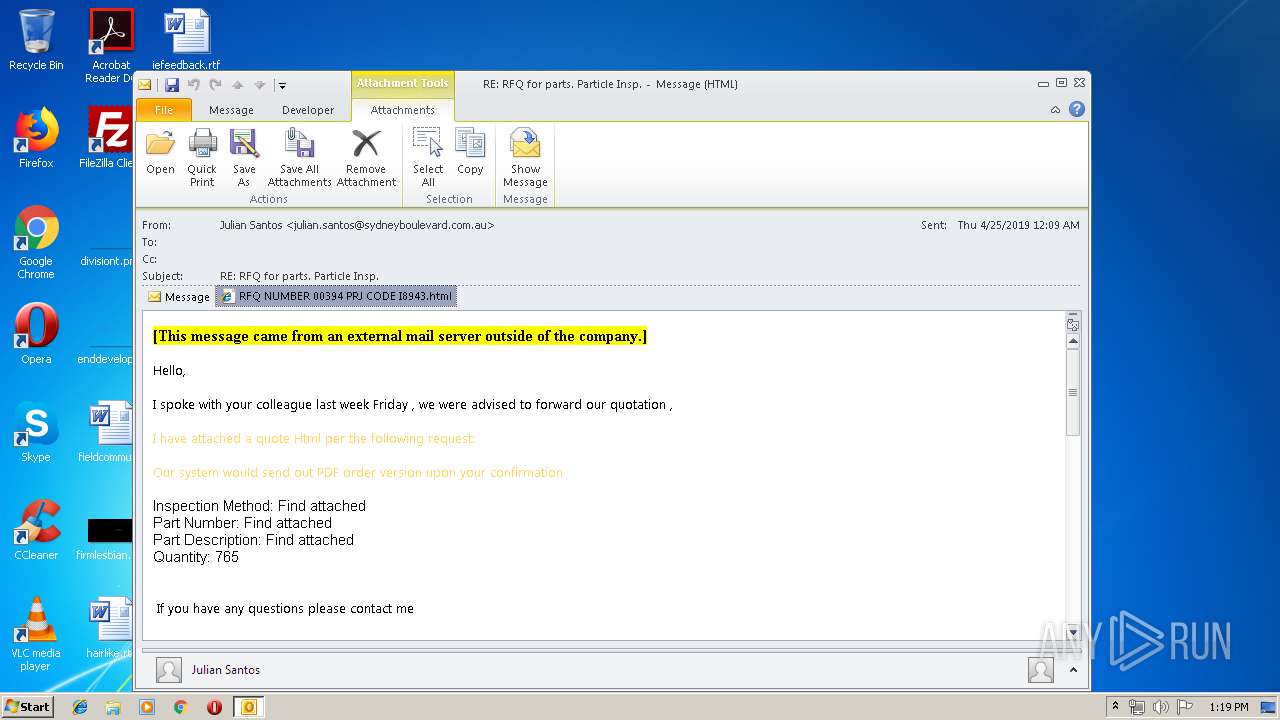
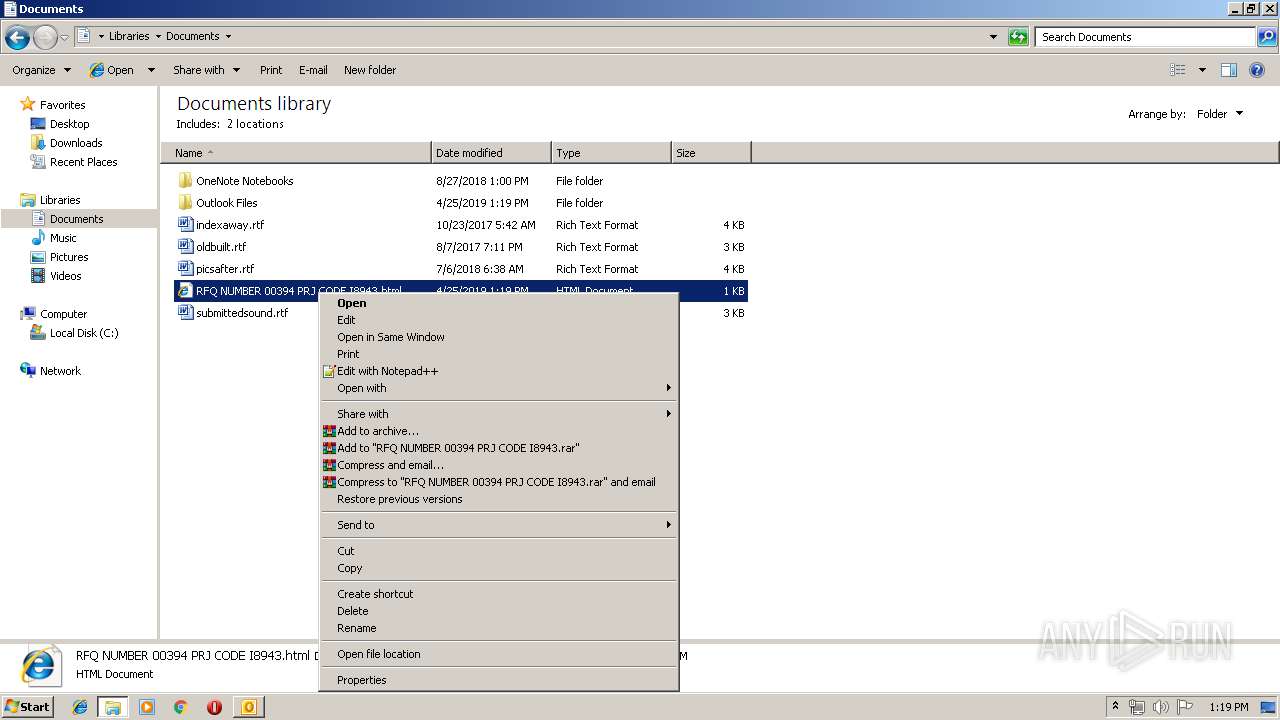
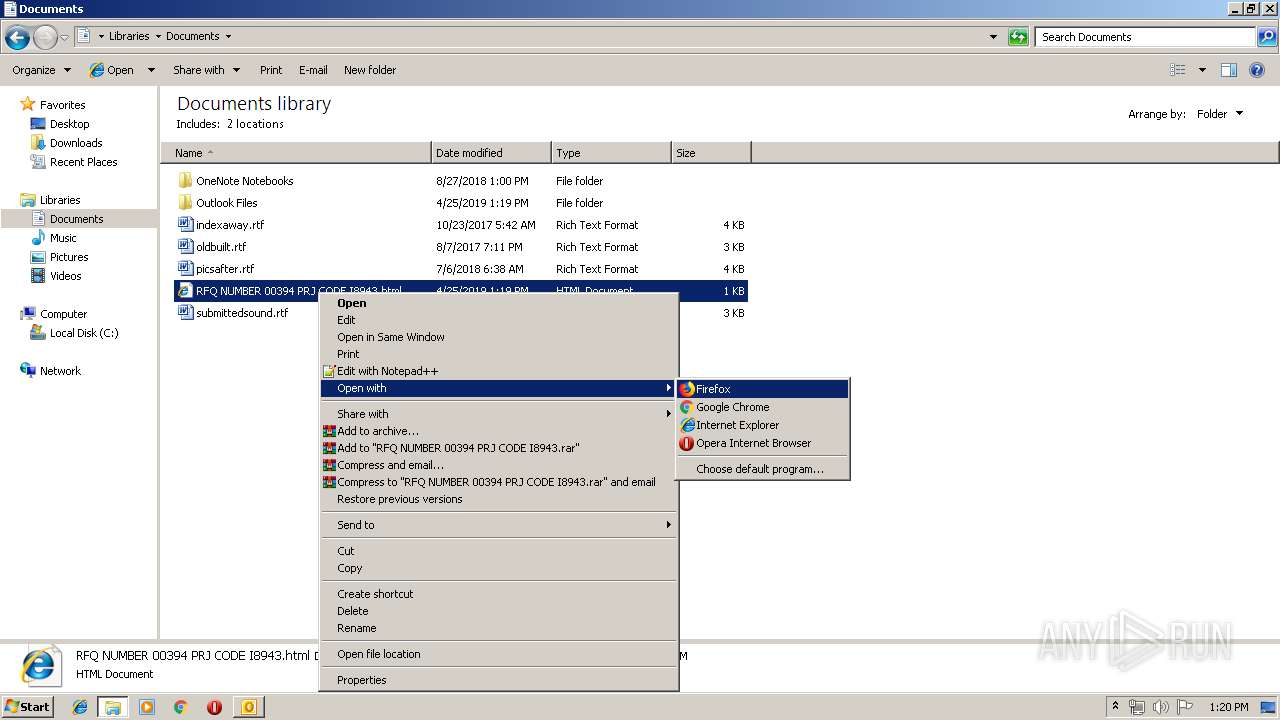
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" -- "C:\Users\admin\Documents\RFQ NUMBER 00394 PRJ CODE I8943.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1004 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10195227376147084992 --mojo-platform-channel-handle=4180 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6601685289455084685 --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x61740f18,0x61740f28,0x61740f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4943523395149000993 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --service-pipe-token=18080074414713321374 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18080074414713321374 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12218829839087895405 --mojo-platform-channel-handle=4060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8971284398078627240,1724721789439921001,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6137423404798337463 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6137423404798337463 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RE RFQ for parts. Particle Insp.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 266
Read events
1 728
Write events
511
Delete events
27
Modification events
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | s'2 |
Value: 7327320028090000010000000000000000000000 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 280900005A356D1161FBD40100000000 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220010400 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2344) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1318649877 | |||
Executable files
0
Suspicious files
18
Text files
147
Unknown types
3
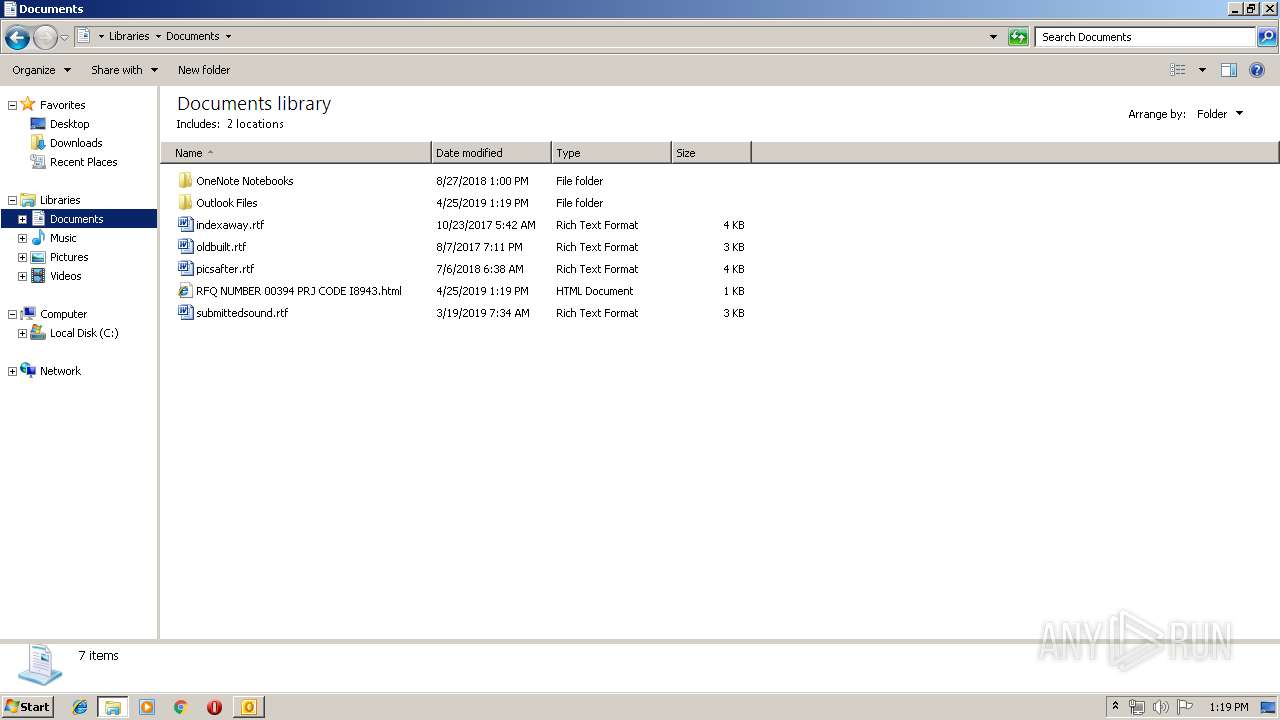
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2373.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2344 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso28A4.tmp | — | |
MD5:— | SHA256:— | |||
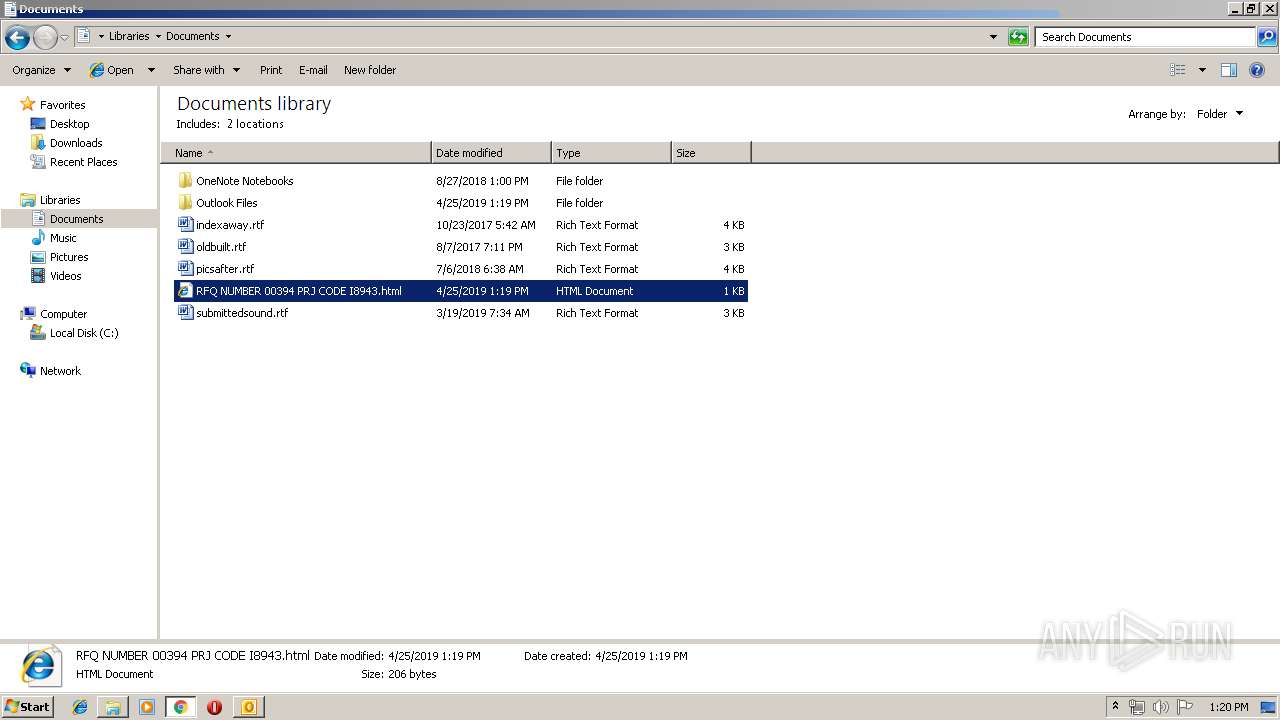
| 2344 | OUTLOOK.EXE | C:\Users\admin\Documents\RFQ NUMBER 00394 PRJ CODE I8943.html\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2344 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
25
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2344 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
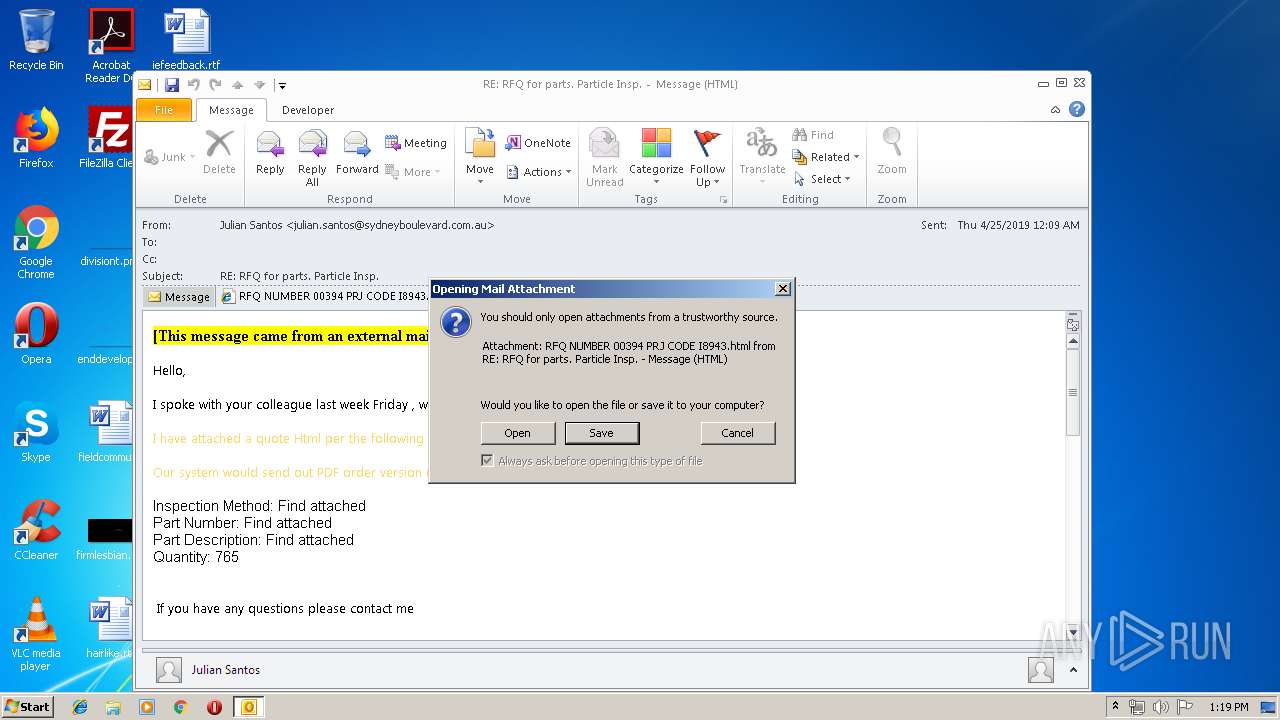
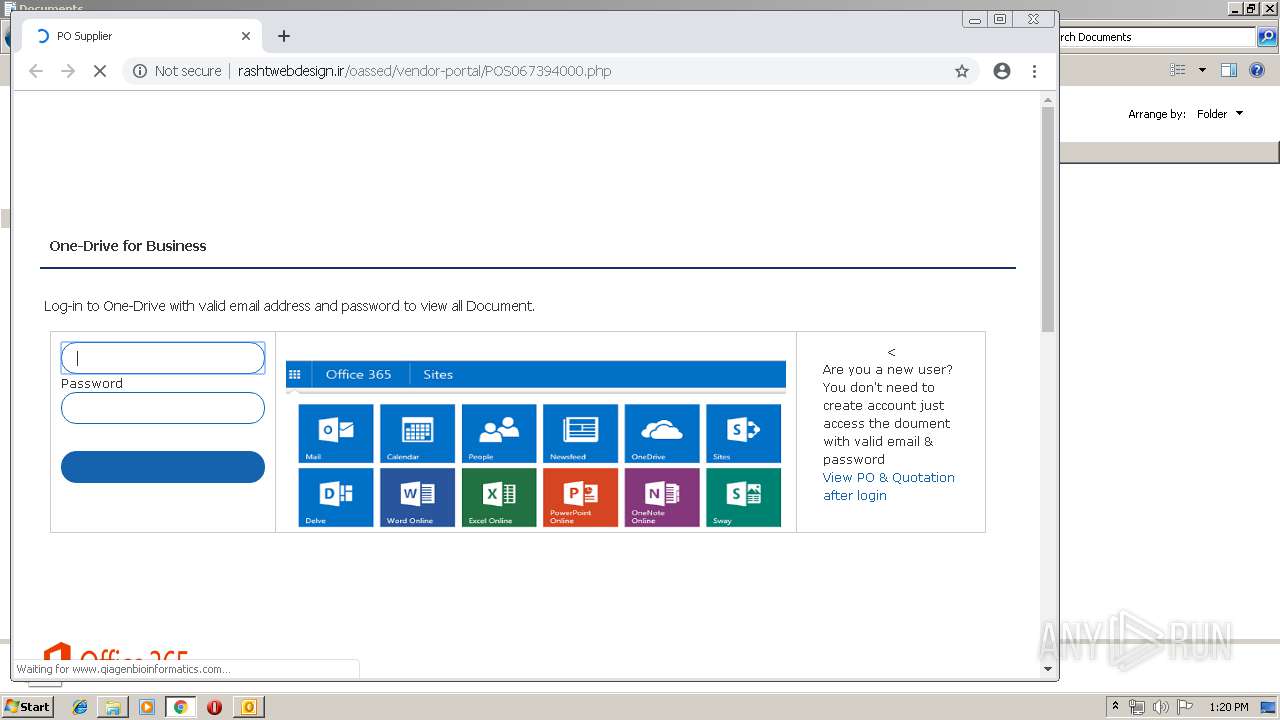
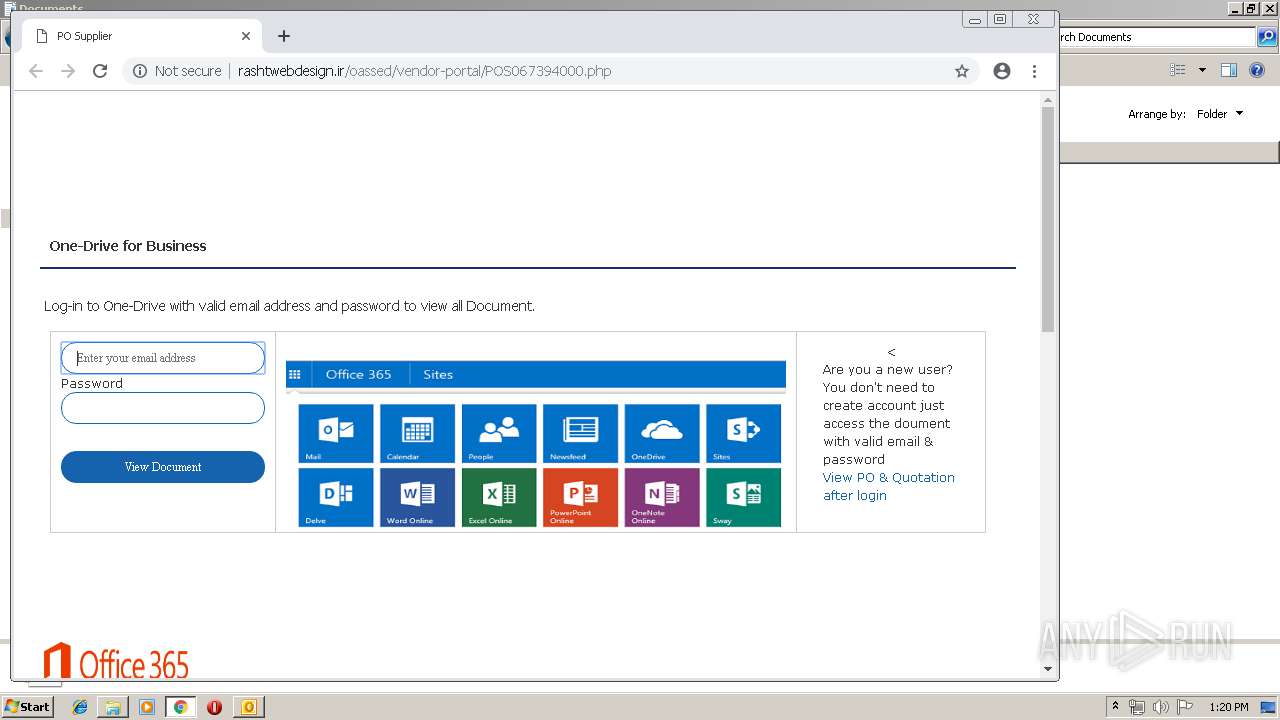
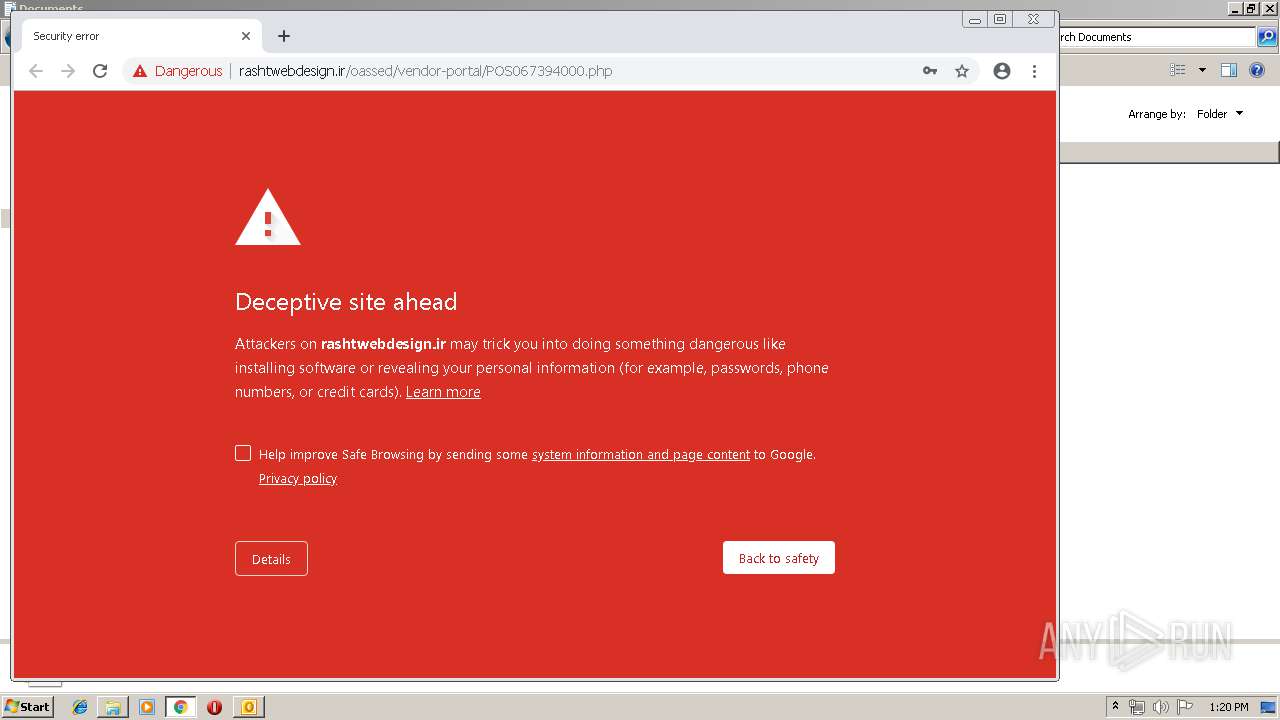
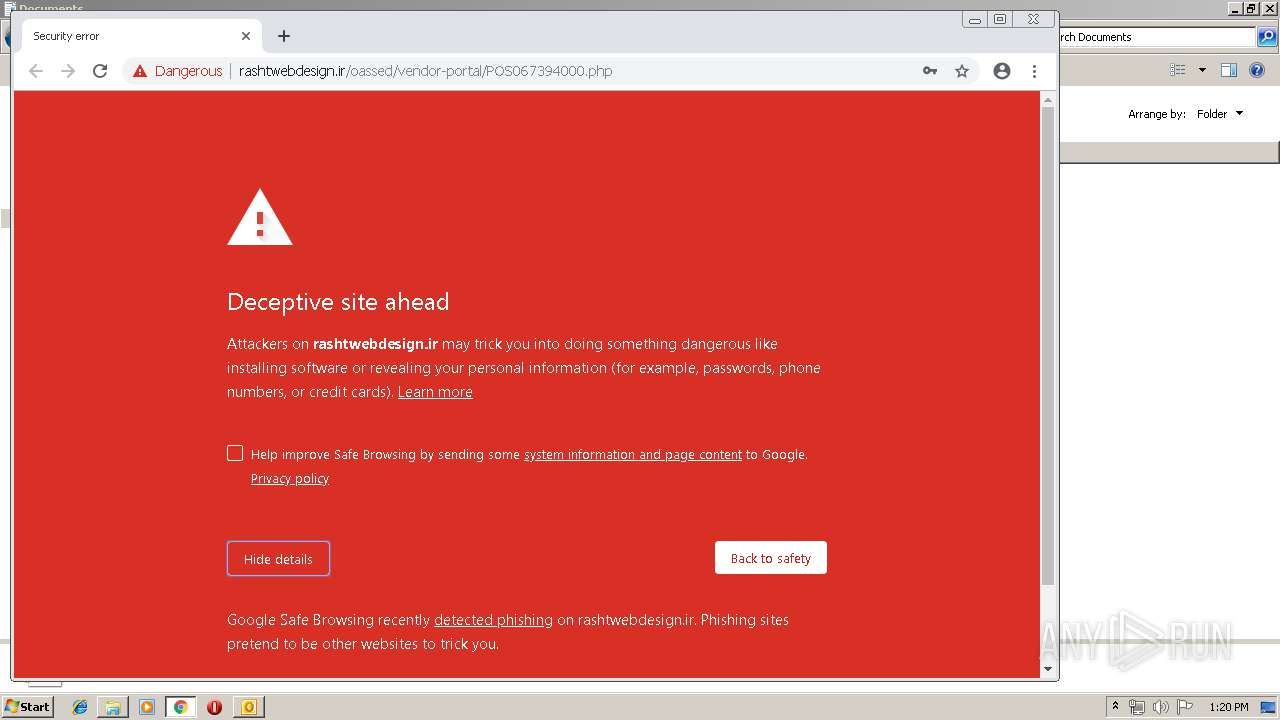
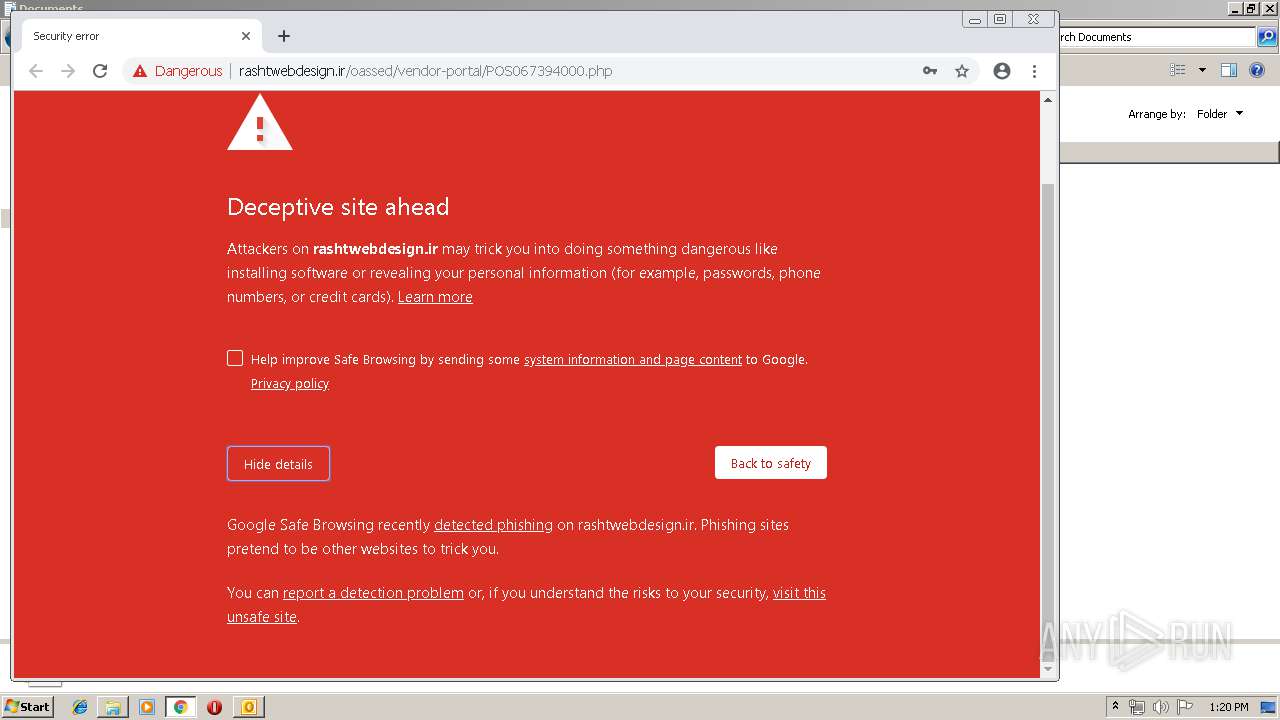
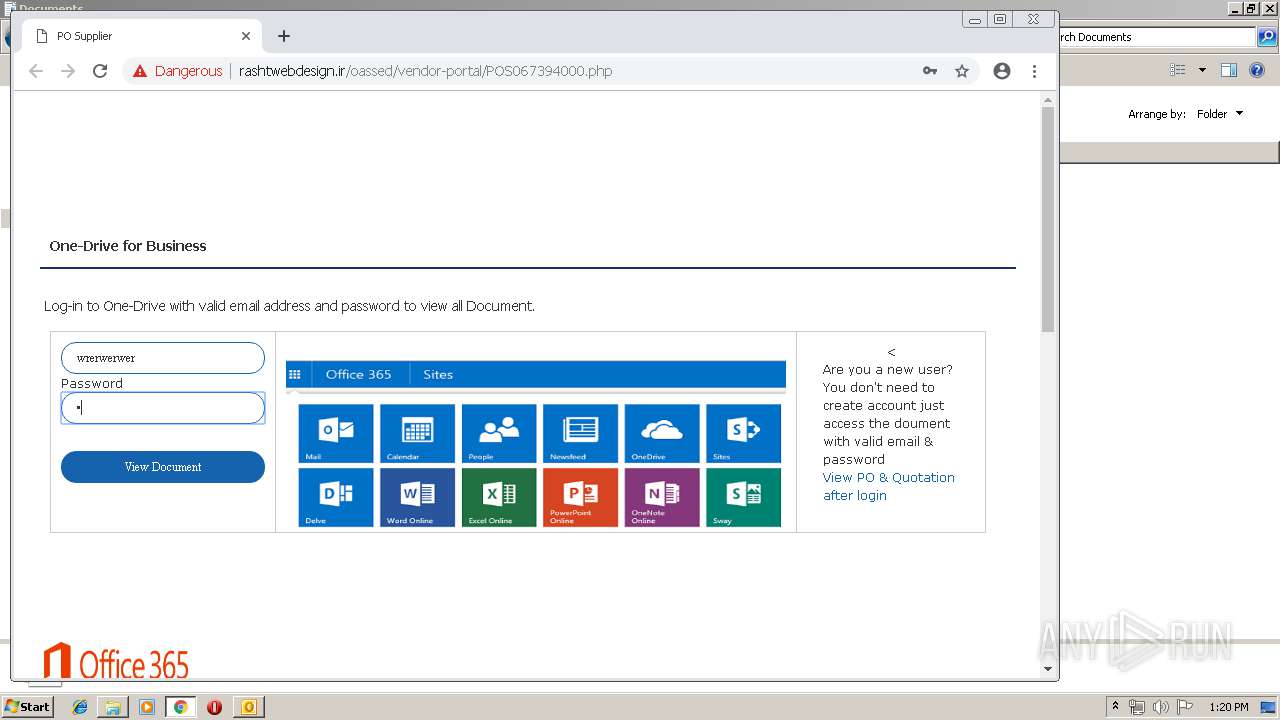
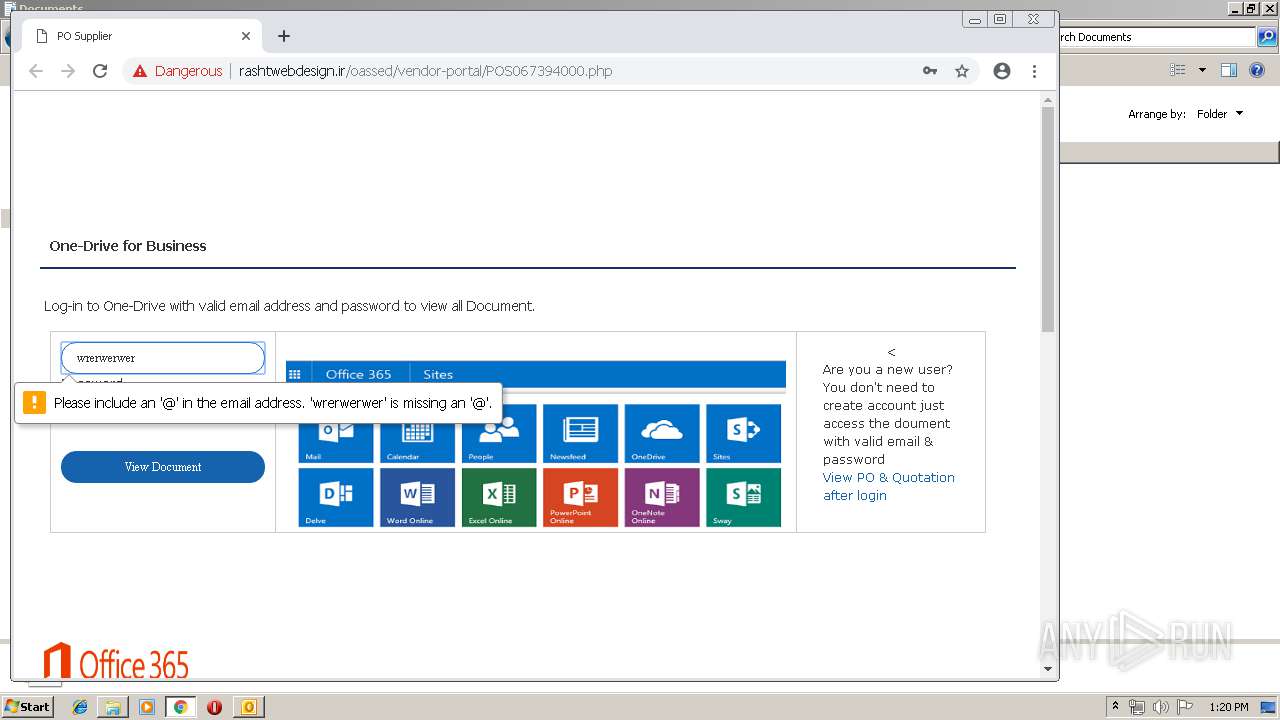
636 | chrome.exe | GET | 302 | 104.27.164.12:80 | http://qiagenbioinformatics.com/wp-content/assets/imgs/Sample-to-insight.png | US | html | 265 b | malicious |
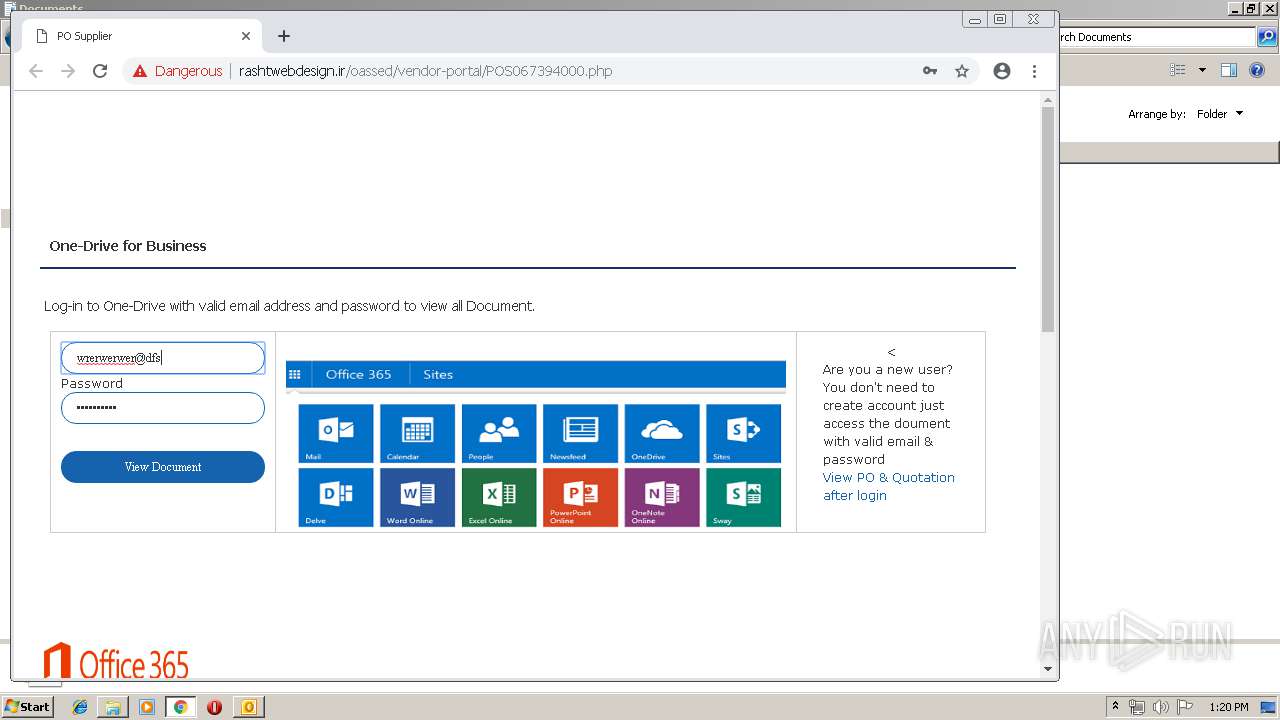
636 | chrome.exe | GET | 200 | 88.198.14.102:80 | http://rashtwebdesign.ir/oassed/vendor-portal/POS067394000.php | DE | html | 3.14 Kb | unknown |
636 | chrome.exe | GET | 301 | 173.236.139.84:80 | http://networksthatwork.net/wp-content/uploads/2016/11/office365-1.png | US | html | 228 b | unknown |
636 | chrome.exe | GET | 200 | 204.12.60.150:80 | http://sai-innovations.com/images/One-Drive-Office-365.png | US | image | 45.5 Kb | unknown |
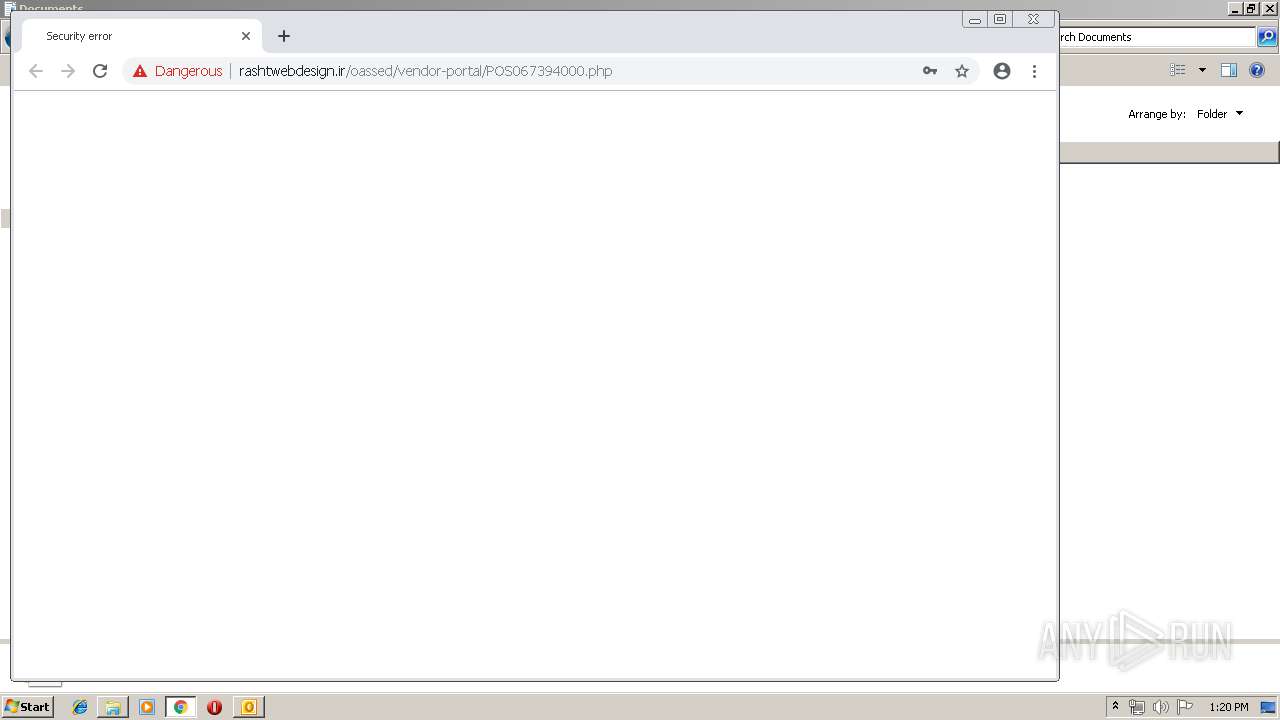
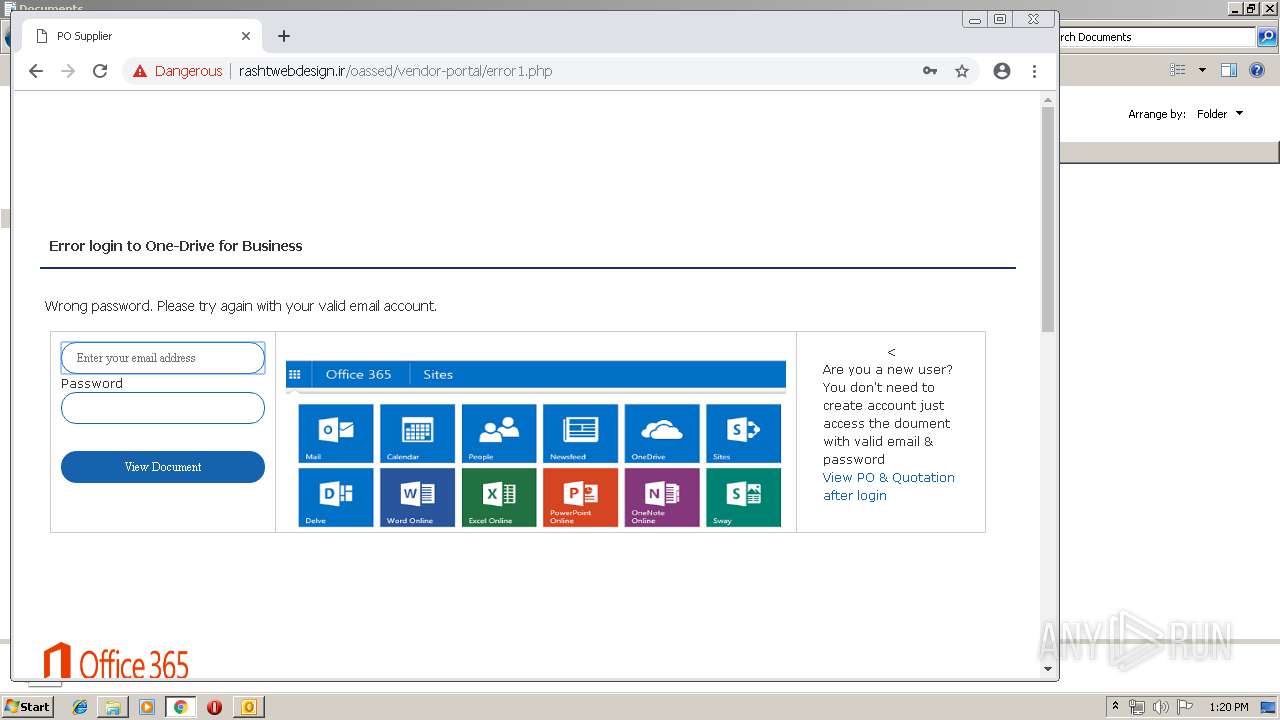
636 | chrome.exe | GET | 200 | 88.198.14.102:80 | http://rashtwebdesign.ir/oassed/vendor-portal/error1.php | DE | html | 3.13 Kb | unknown |
636 | chrome.exe | GET | 200 | 88.198.14.102:80 | http://rashtwebdesign.ir/oassed/vendor-portal/error1.php | DE | html | 3.13 Kb | unknown |
636 | chrome.exe | POST | 302 | 88.198.14.102:80 | http://rashtwebdesign.ir/oassed/vendor-portal/index.php | DE | — | — | unknown |
636 | chrome.exe | GET | 404 | 88.198.14.102:80 | http://rashtwebdesign.ir/portal/prototype.js | DE | html | 1.12 Kb | unknown |
636 | chrome.exe | GET | 404 | 88.198.14.102:80 | http://rashtwebdesign.ir/oassed/vendor-portal/fastclick.js | DE | html | 1.12 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2344 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
636 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 104.27.164.12:443 | qiagenbioinformatics.com | Cloudflare Inc | US | shared |
636 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
636 | chrome.exe | 204.12.60.150:80 | sai-innovations.com | HostMySite | US | unknown |
636 | chrome.exe | 173.236.139.84:80 | networksthatwork.net | New Dream Network, LLC | US | unknown |
636 | chrome.exe | 104.18.99.79:443 | app-sjqe.marketo.com | Cloudflare Inc | US | shared |
636 | chrome.exe | 173.236.139.84:443 | networksthatwork.net | New Dream Network, LLC | US | unknown |
636 | chrome.exe | 104.27.164.12:80 | qiagenbioinformatics.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
rashtwebdesign.ir |
| unknown |
qiagenbioinformatics.com |
| malicious |
app-sjqe.marketo.com |
| whitelisted |
networksthatwork.net |
| unknown |
sai-innovations.com |
| unknown |
safebrowsing.googleapis.com |
| whitelisted |
www.qiagenbioinformatics.com |
| malicious |