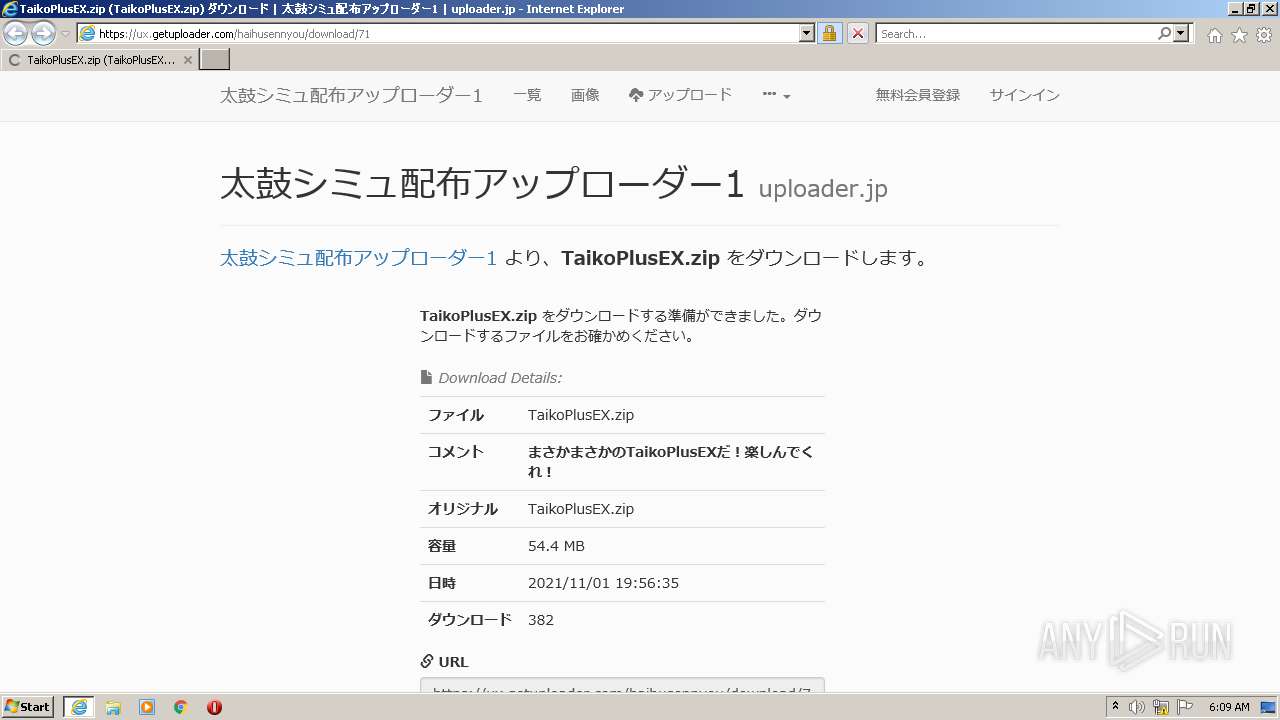
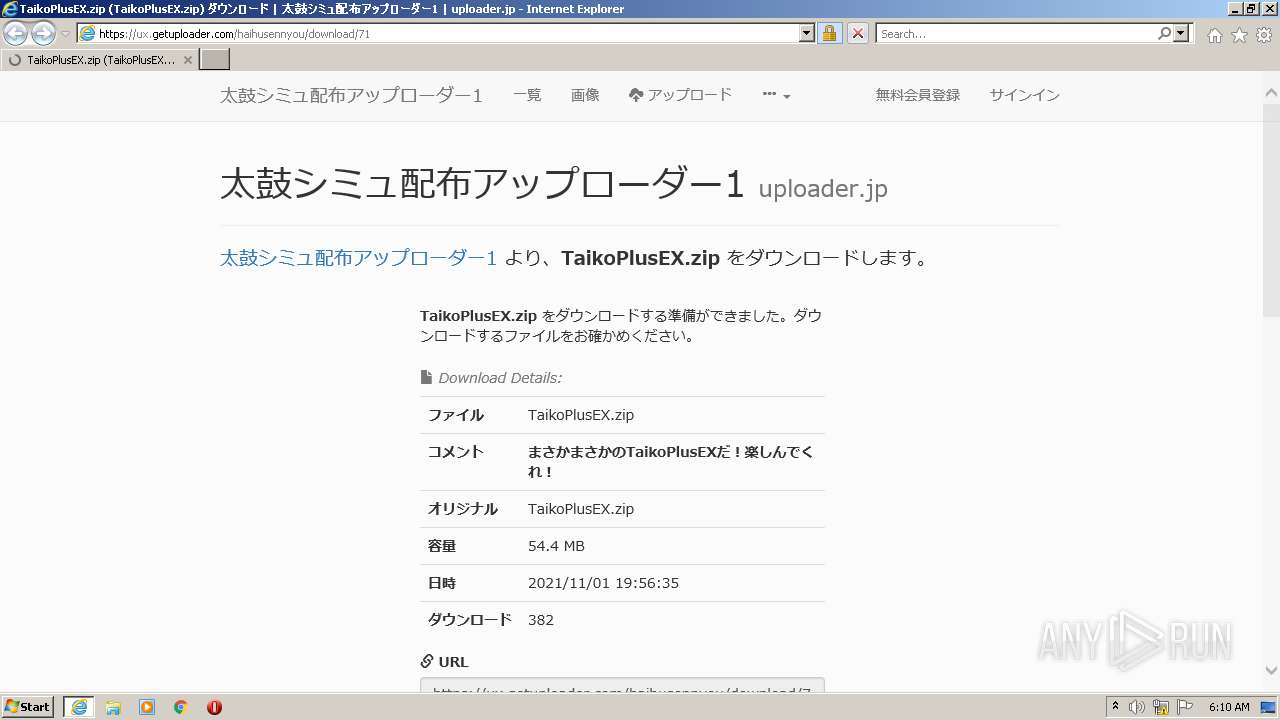
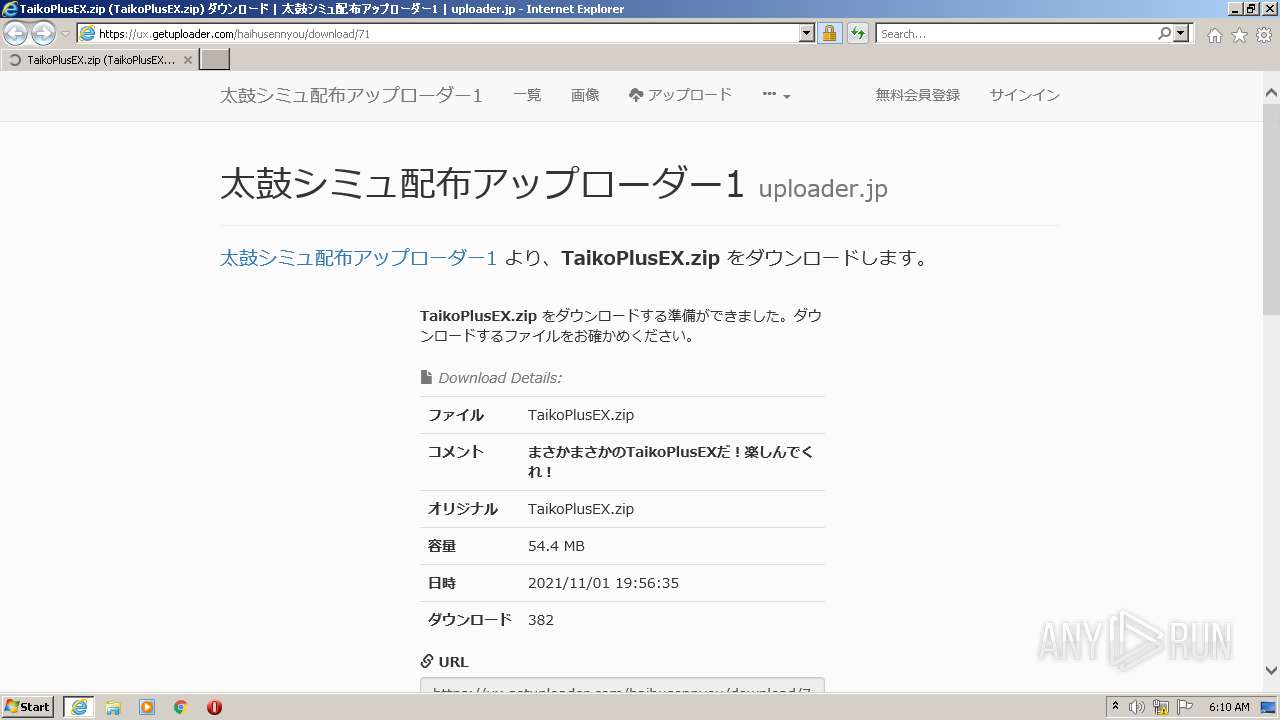
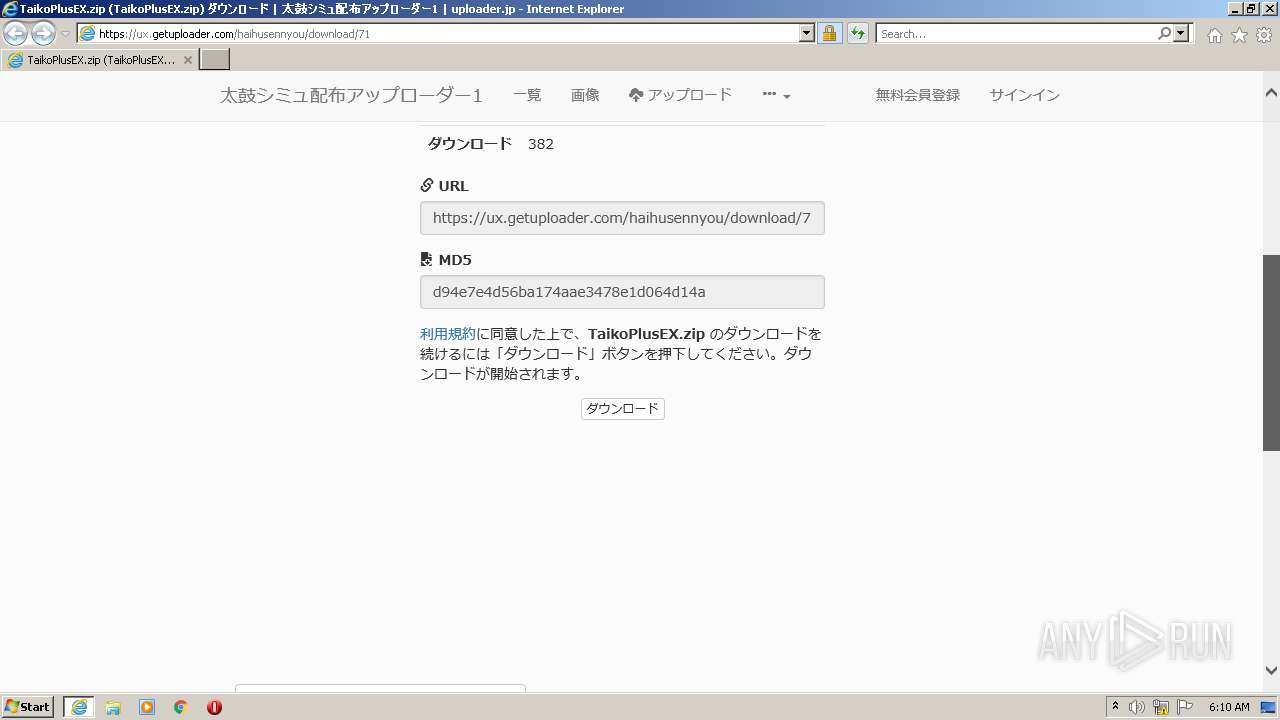
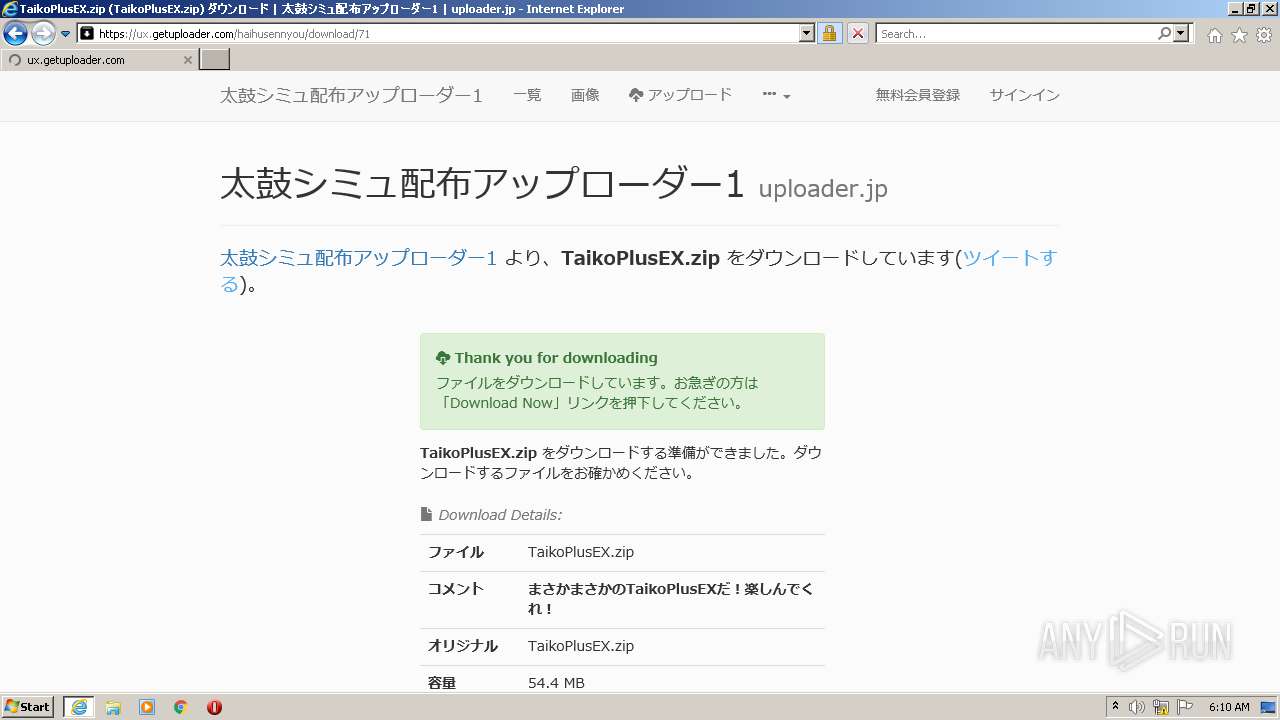
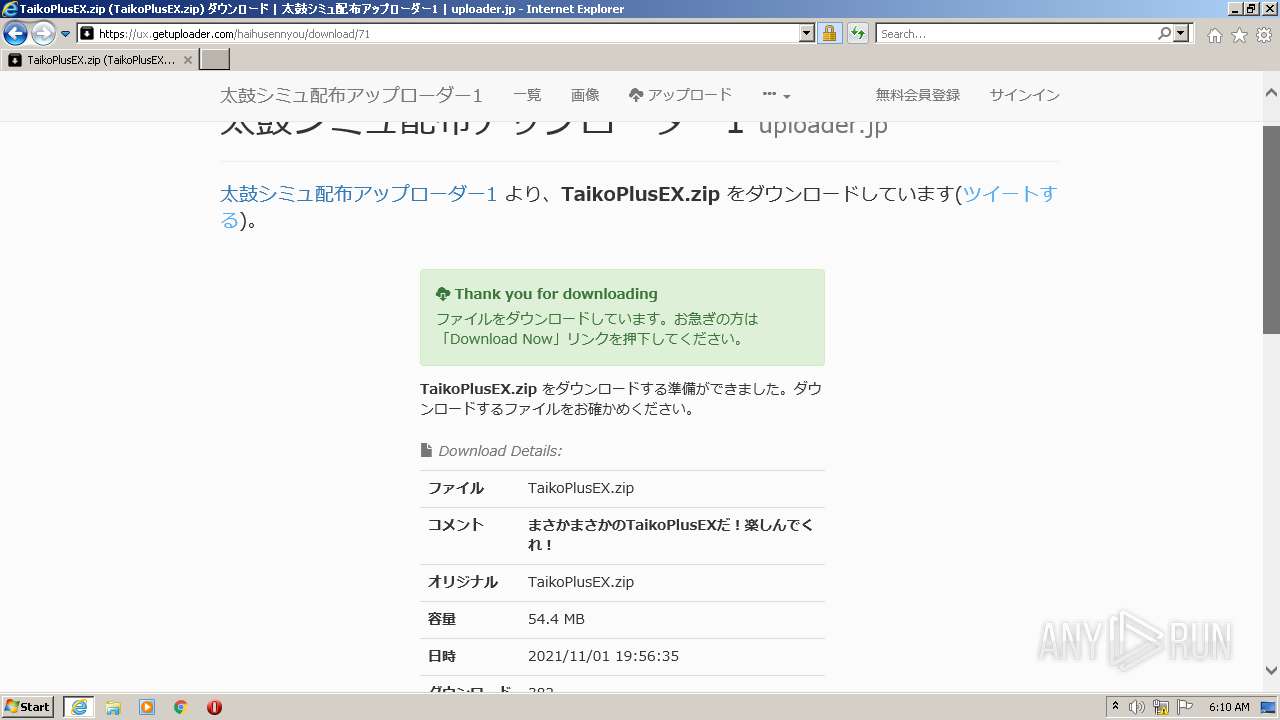
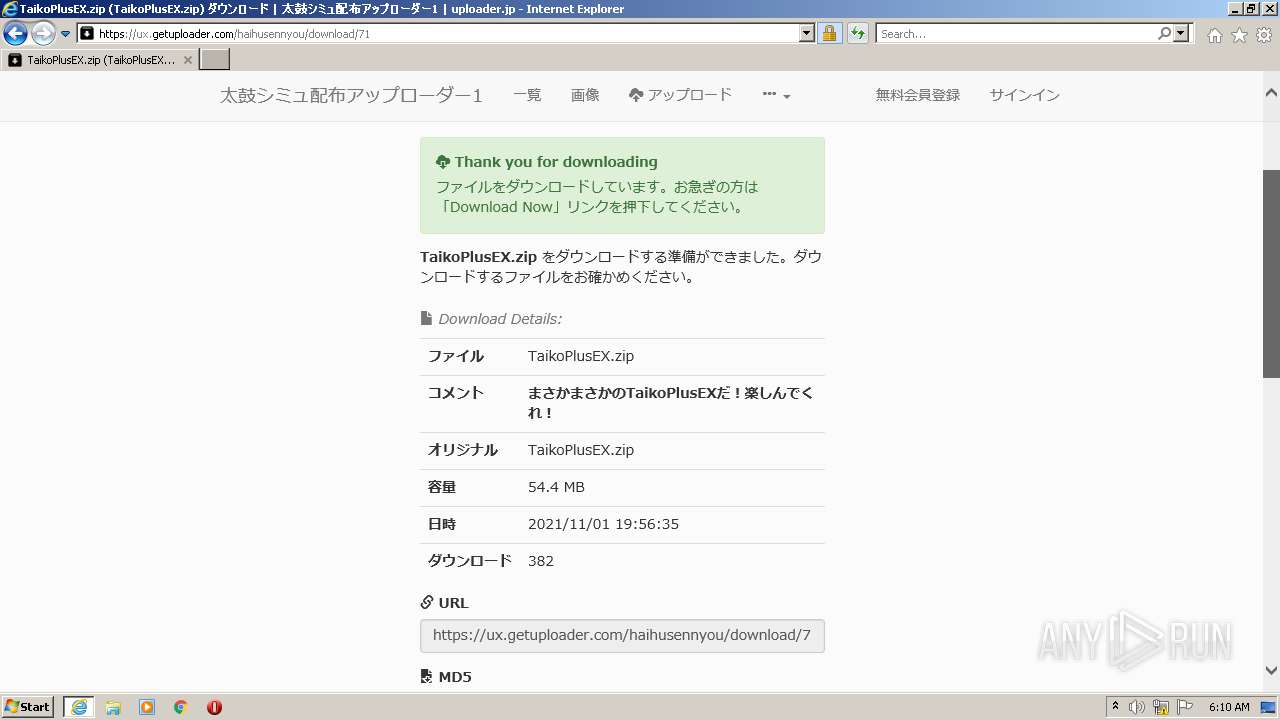
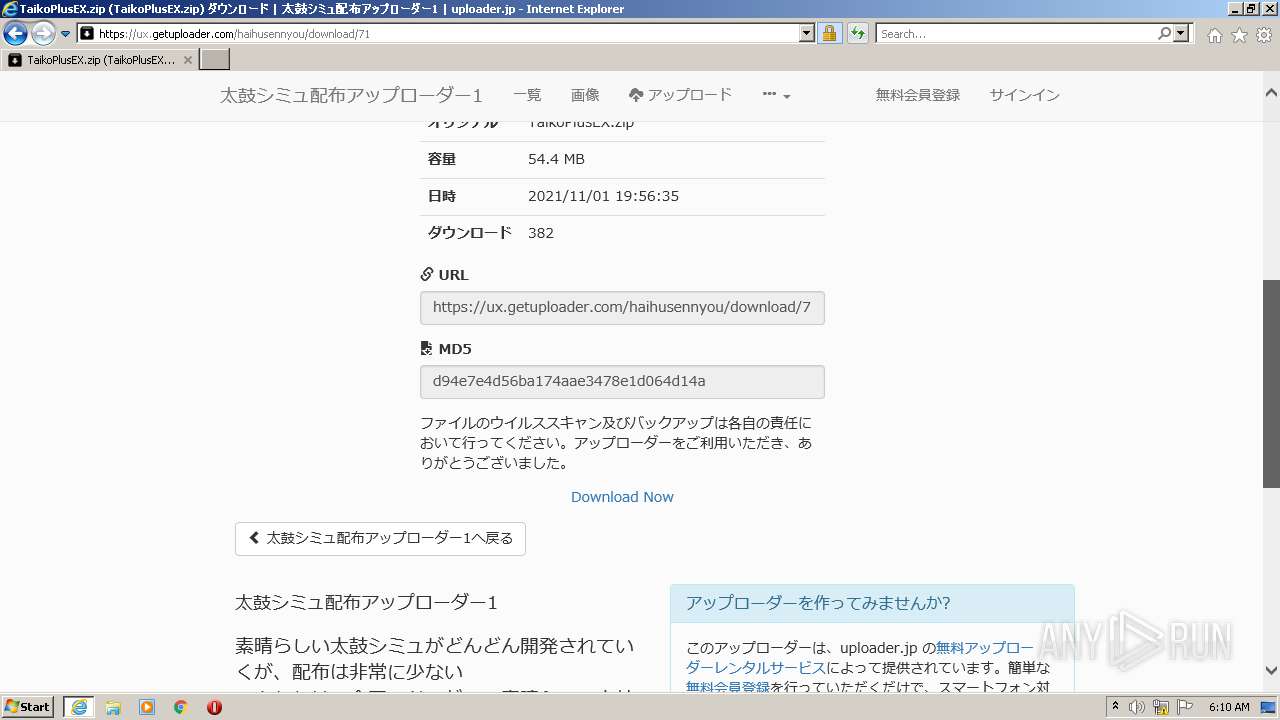
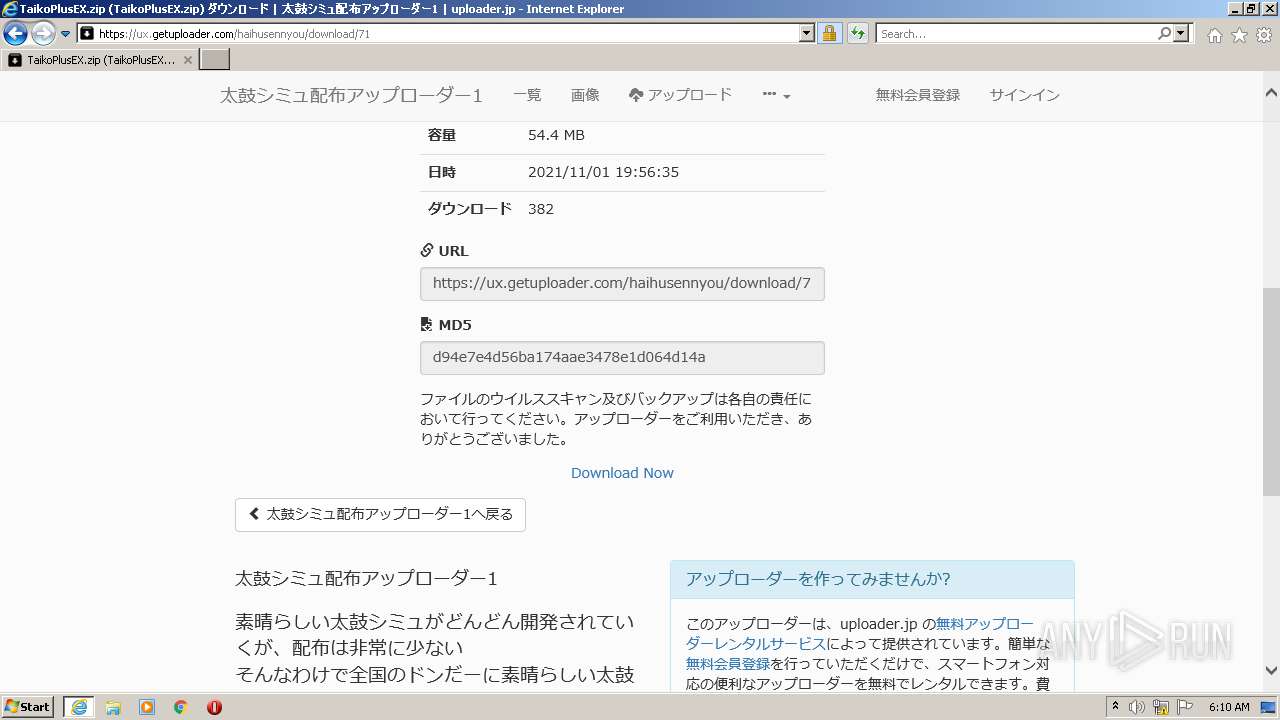
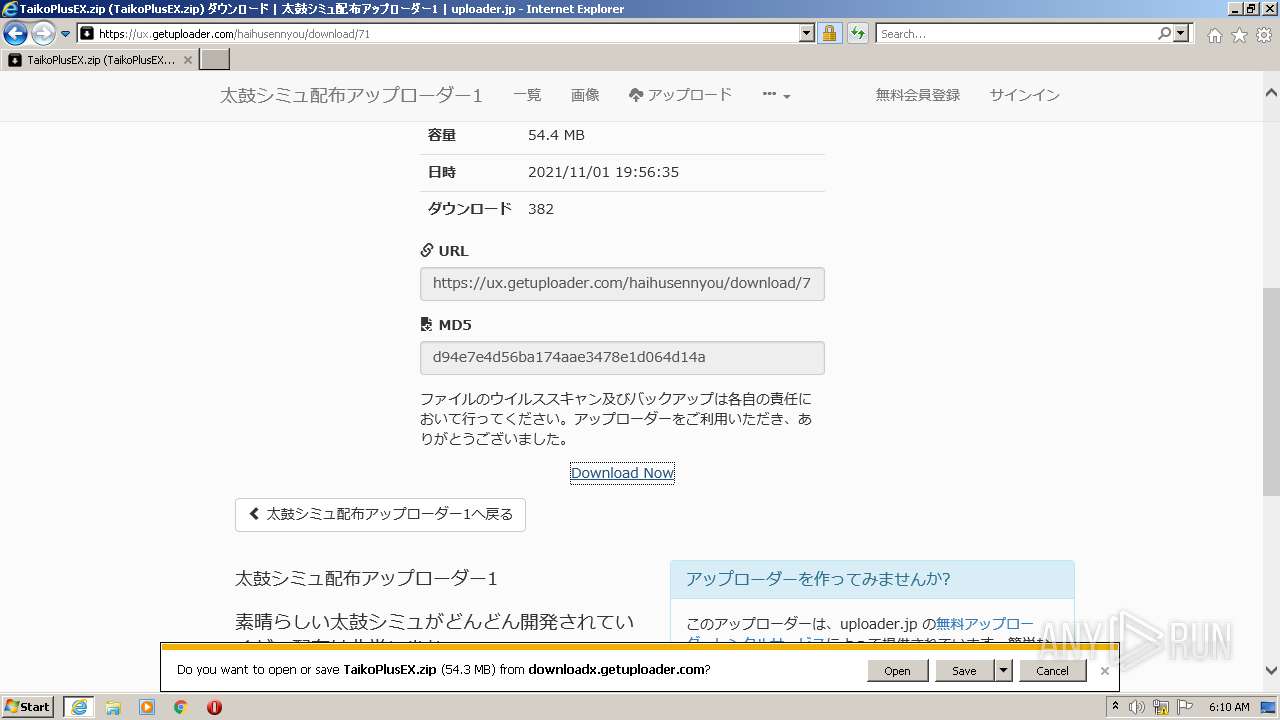
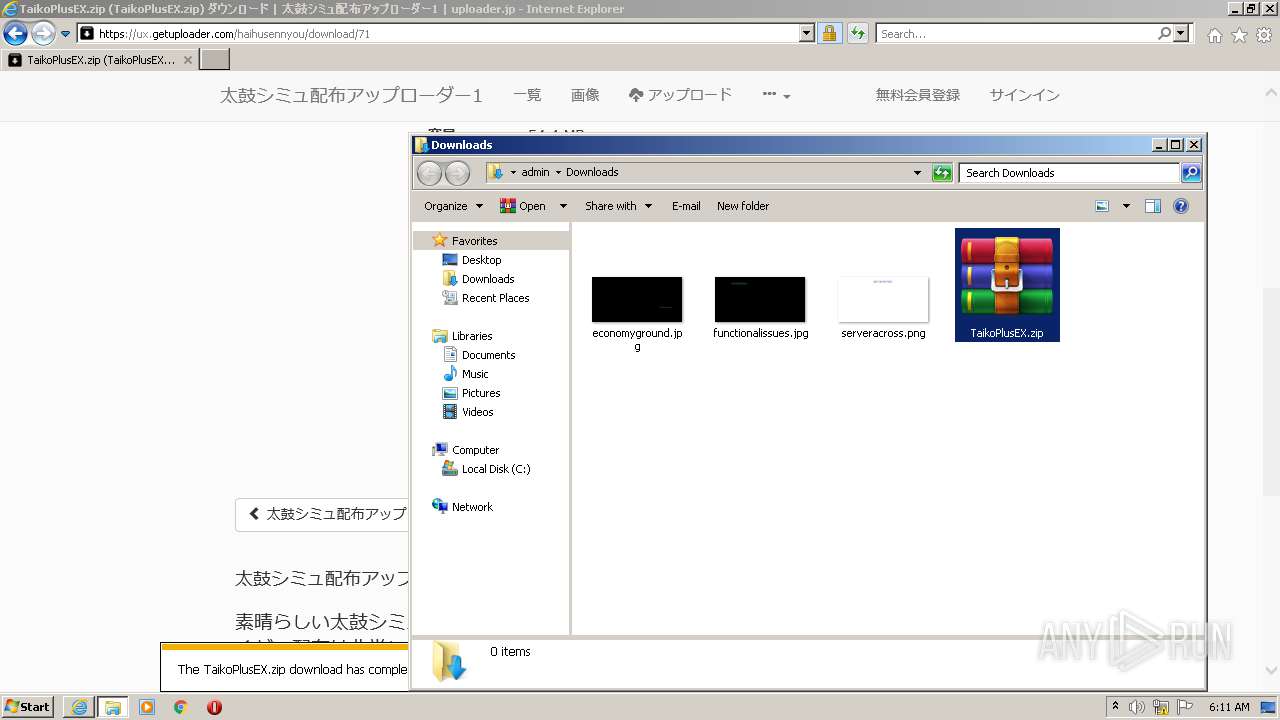
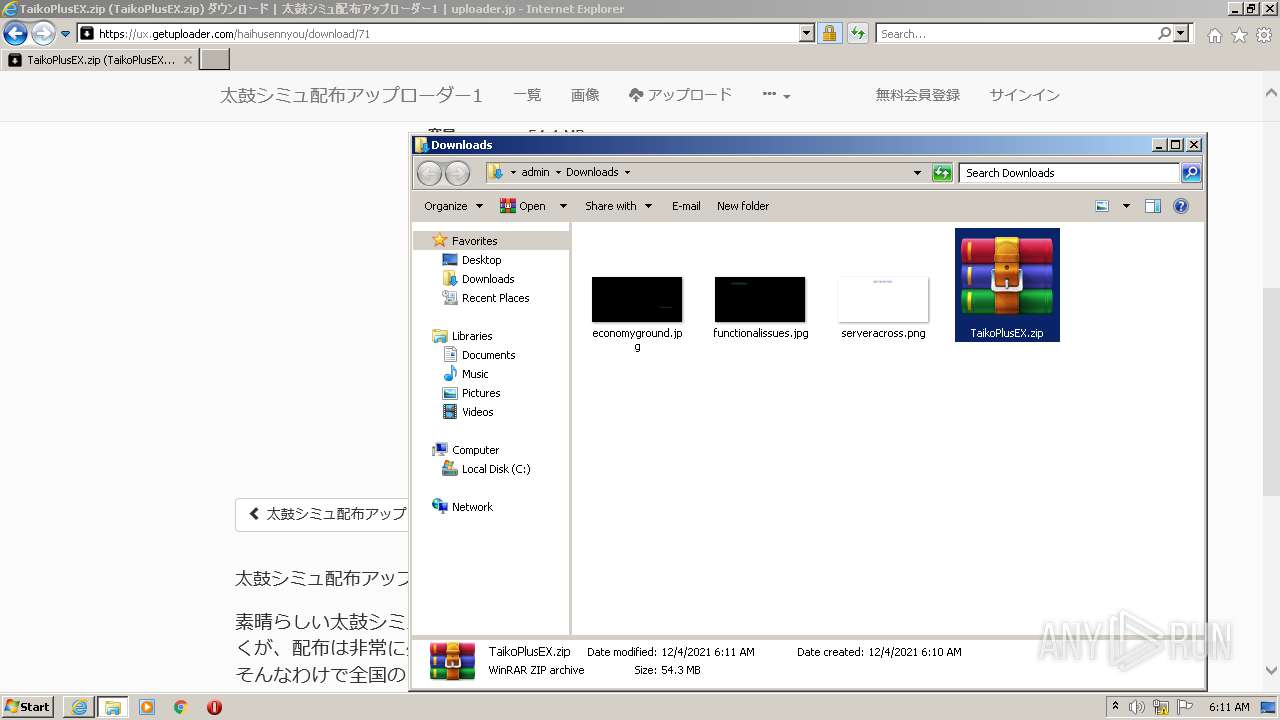
| URL: | https://ux.getuploader.com/haihusennyou/download/71 |
| Full analysis: | https://app.any.run/tasks/d67c7274-742d-4a08-87b5-9d7ba20867d8 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2021, 06:09:37 |
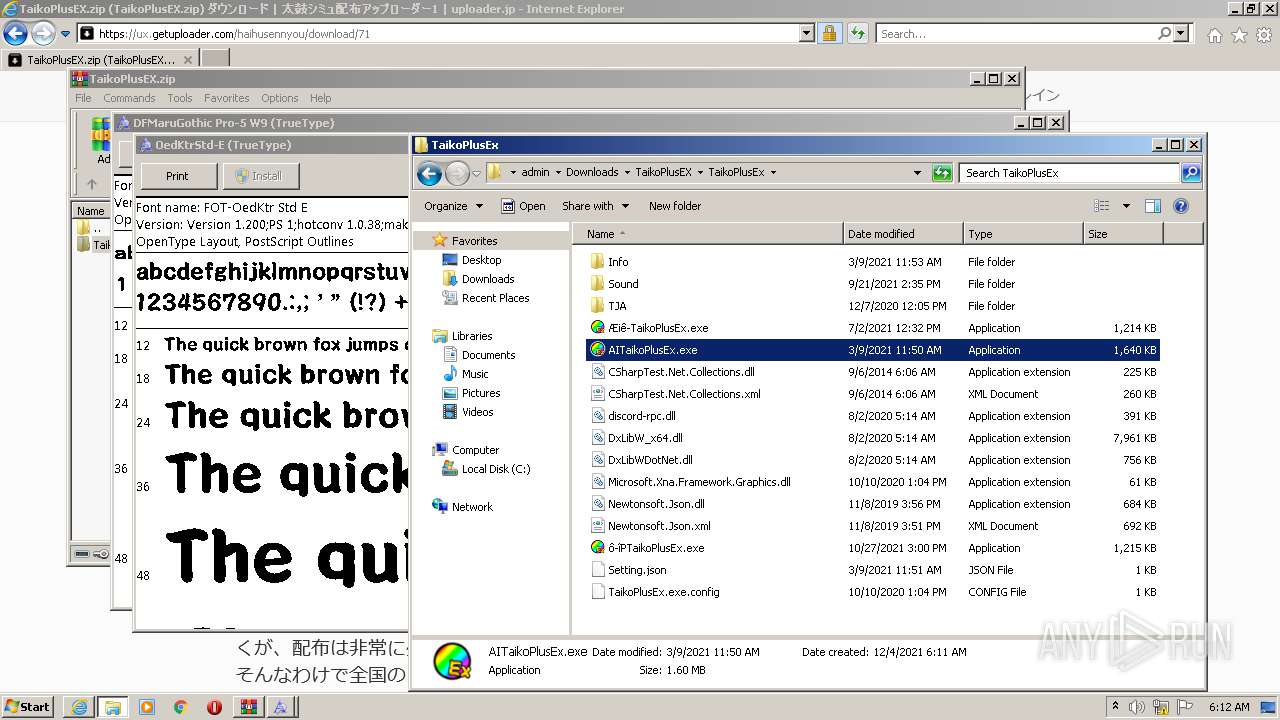
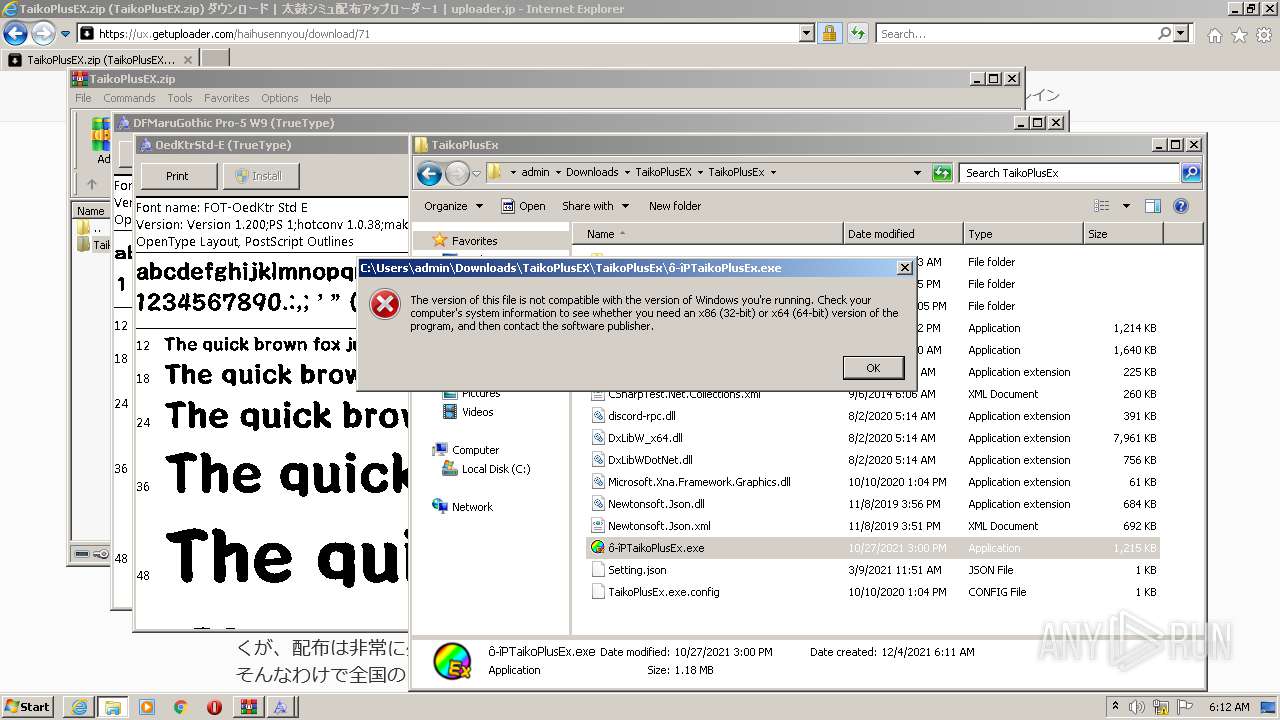
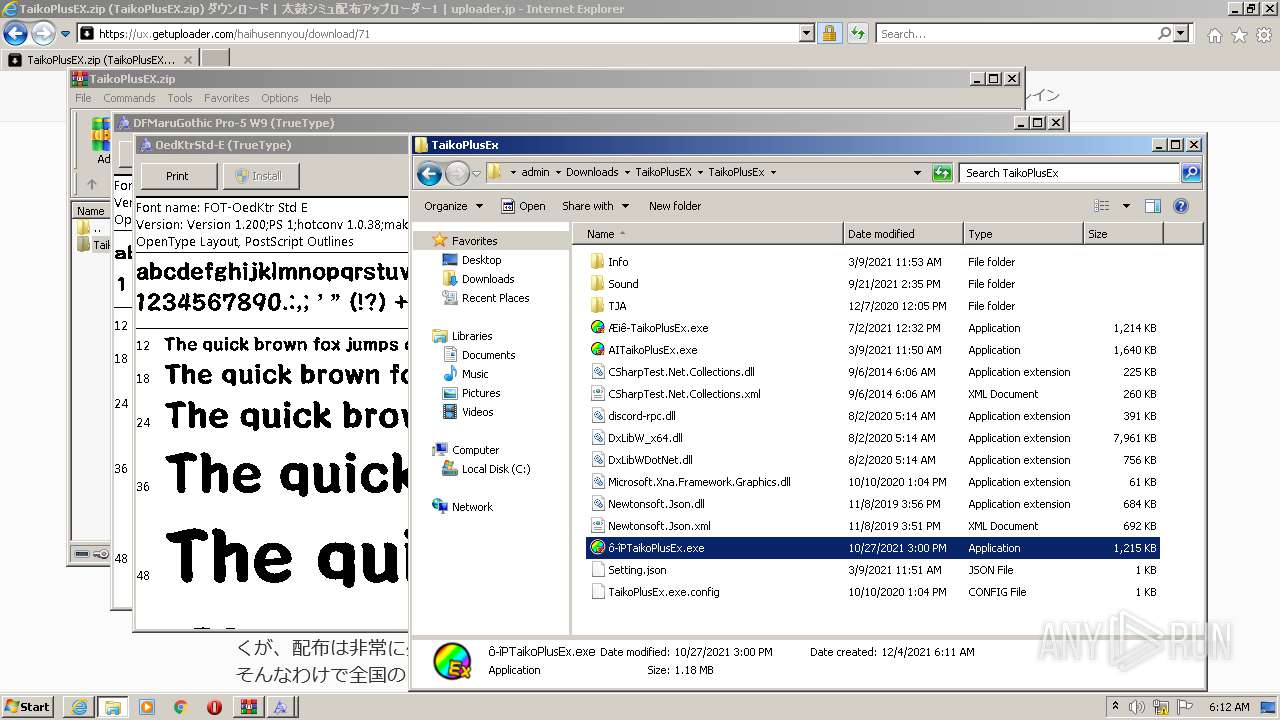
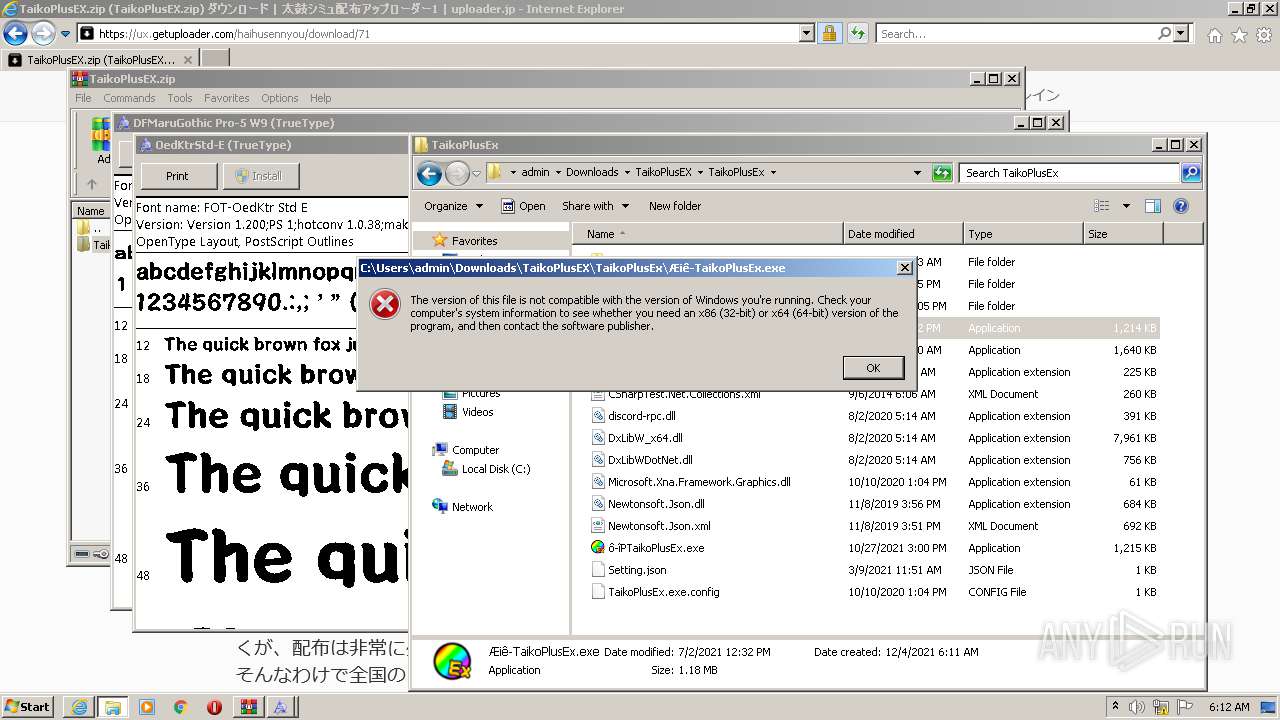
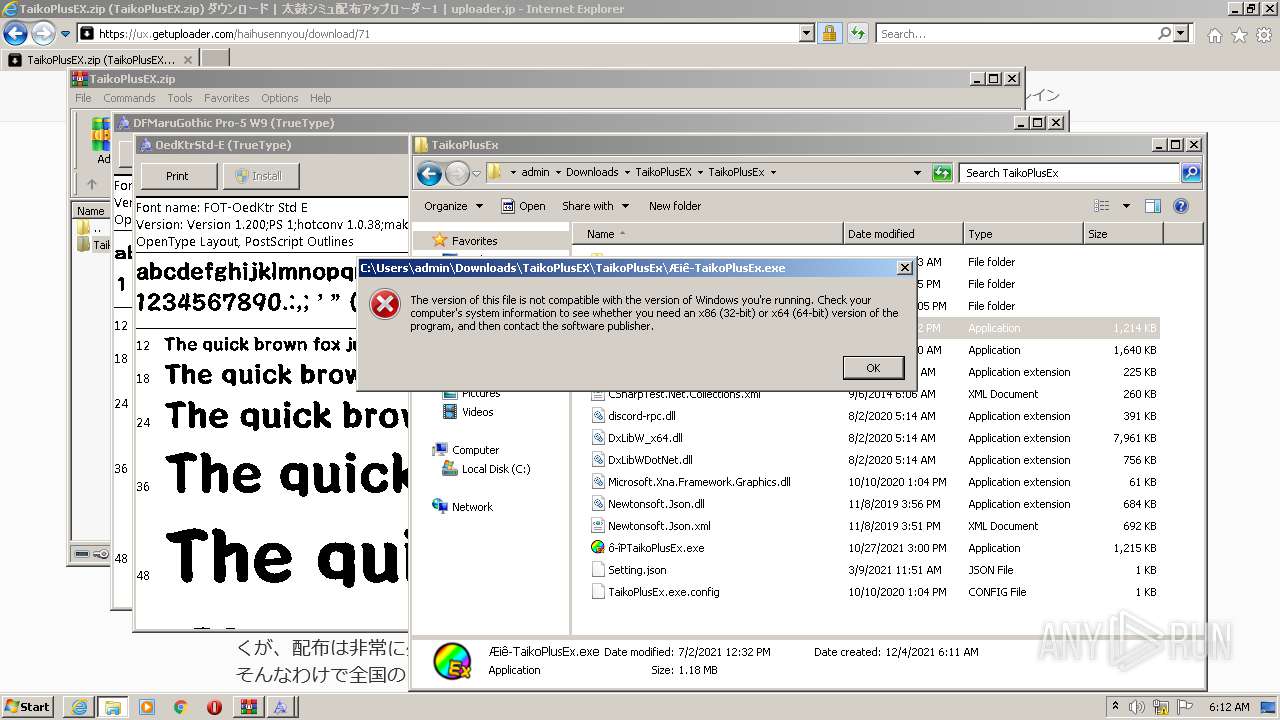
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 89116A322C6C5D48B1C65B177B634857 |
| SHA1: | AAAD182E849732BD24185CAE085F6D36A5E0CF6E |
| SHA256: | 8C3B2BE146A22CBD1AAFD5A1A65E2949DAE6A81FE3307C08364B6D0E80737738 |
| SSDEEP: | 3:N8f0pyKmMD1+J9kSU:2fDPw1oU |
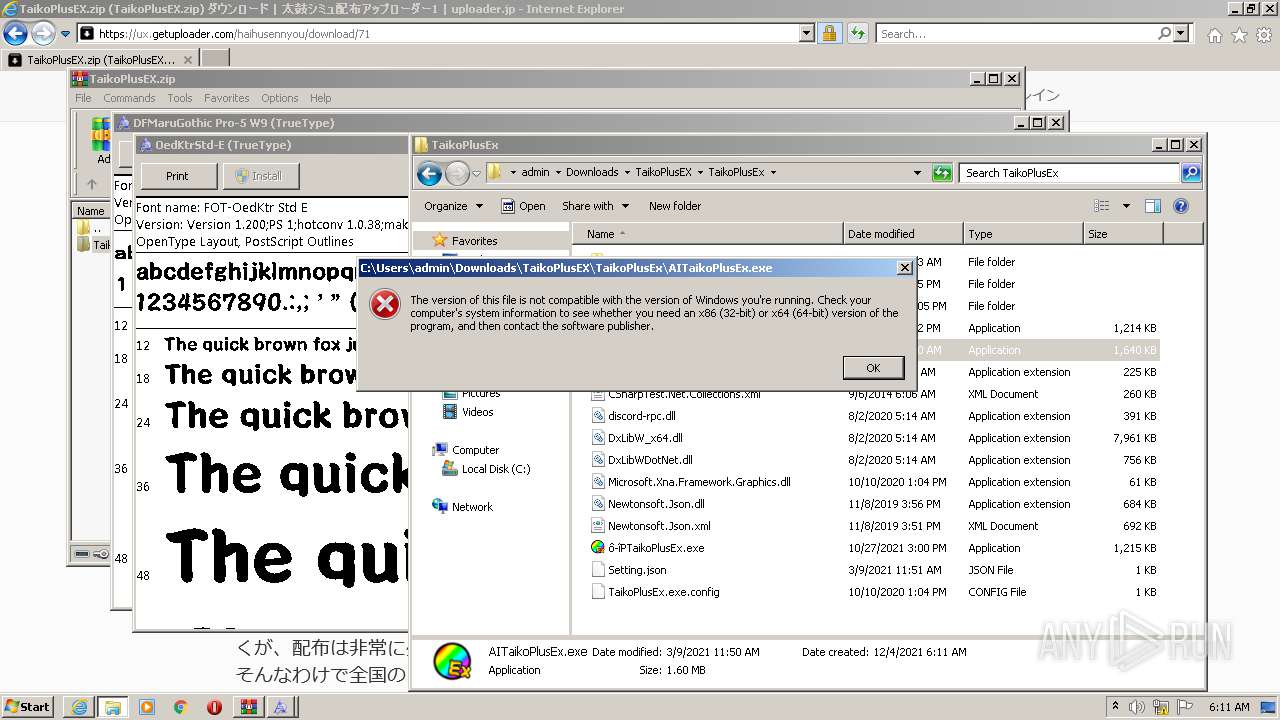
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3472)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2628)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1648)
Reads the computer name
- WinRAR.exe (PID: 2628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2628)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2628)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2628)
Executed via COM
- DllHost.exe (PID: 3112)
- DllHost.exe (PID: 2252)
- DllHost.exe (PID: 3388)
Creates files in the Windows directory
- DllHost.exe (PID: 3112)
- DllHost.exe (PID: 2252)
- DllHost.exe (PID: 3388)
INFO
Checks supported languages
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 1648)
- fontview.exe (PID: 472)
- DllHost.exe (PID: 3112)
- fontview.exe (PID: 3188)
- DllHost.exe (PID: 2252)
- fontview.exe (PID: 3900)
- DllHost.exe (PID: 3388)
Reads the computer name
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 1648)
- fontview.exe (PID: 472)
- DllHost.exe (PID: 3112)
- DllHost.exe (PID: 2252)
- fontview.exe (PID: 3188)
- fontview.exe (PID: 3900)
- DllHost.exe (PID: 3388)
Application launched itself
- iexplore.exe (PID: 3904)
Reads settings of System Certificates
- iexplore.exe (PID: 1648)
- iexplore.exe (PID: 3904)
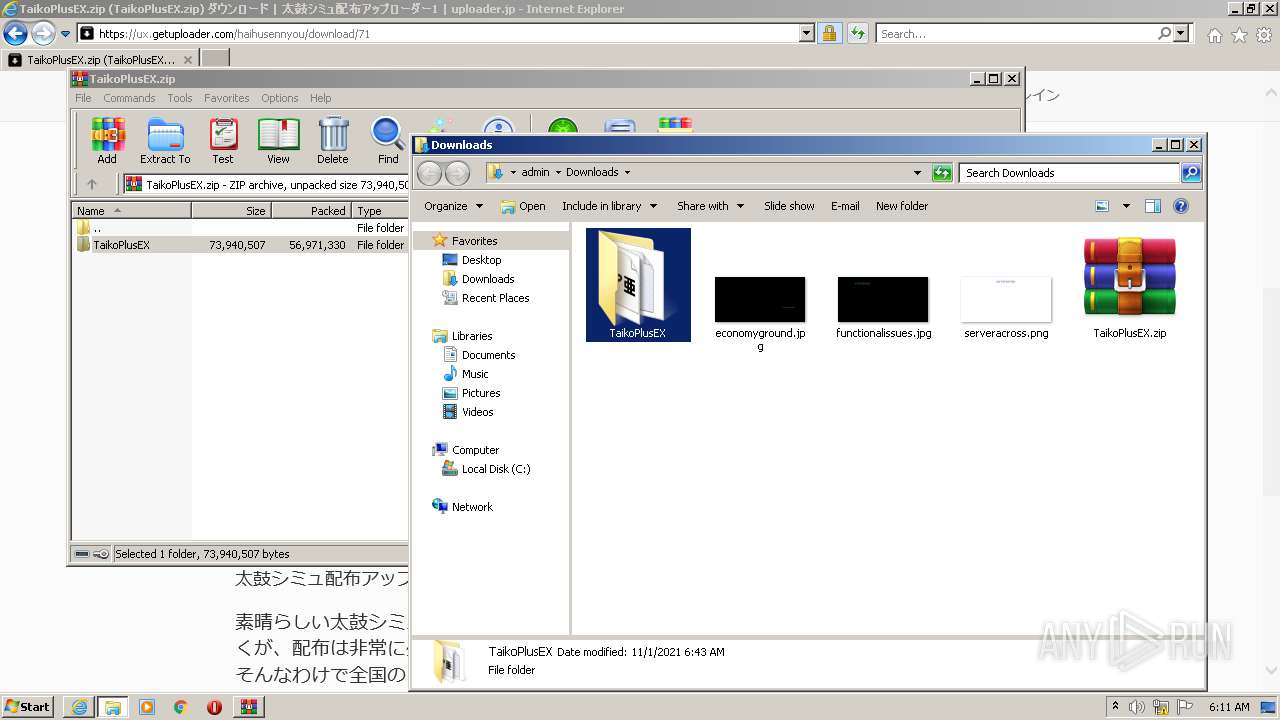
Creates files in the user directory
- iexplore.exe (PID: 1648)
- iexplore.exe (PID: 3904)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3904)
Changes internet zones settings
- iexplore.exe (PID: 3904)
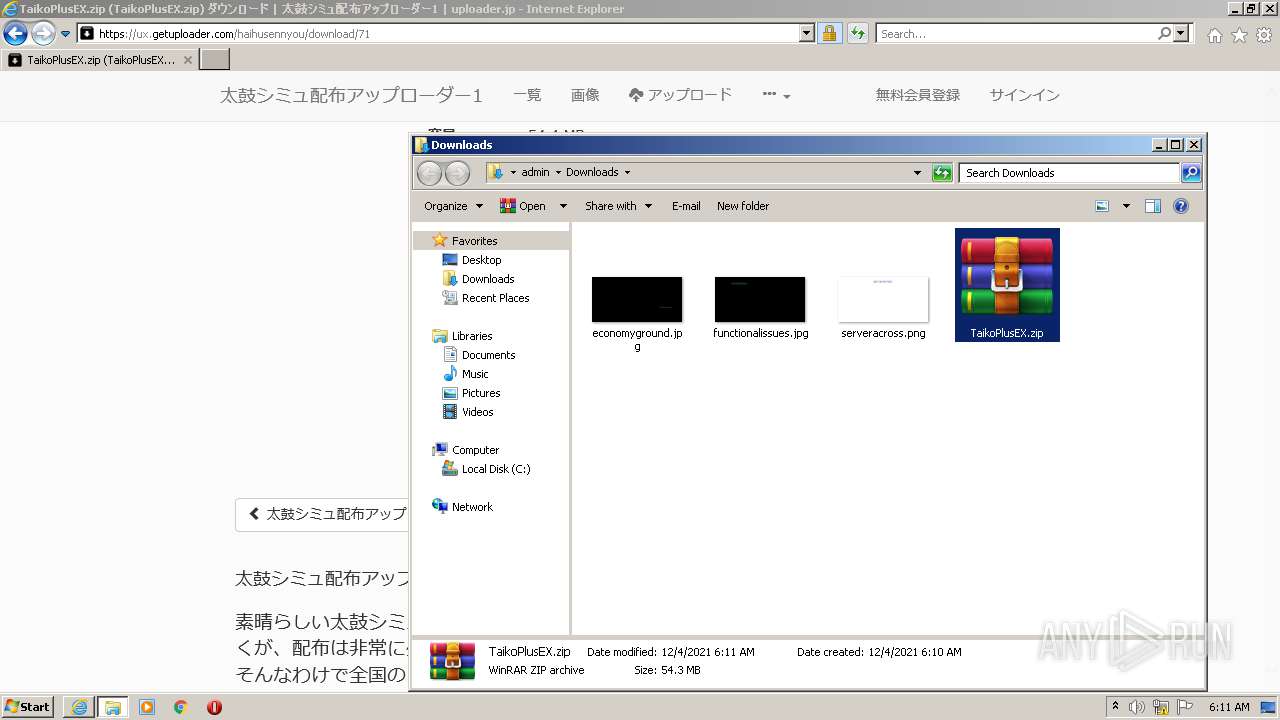
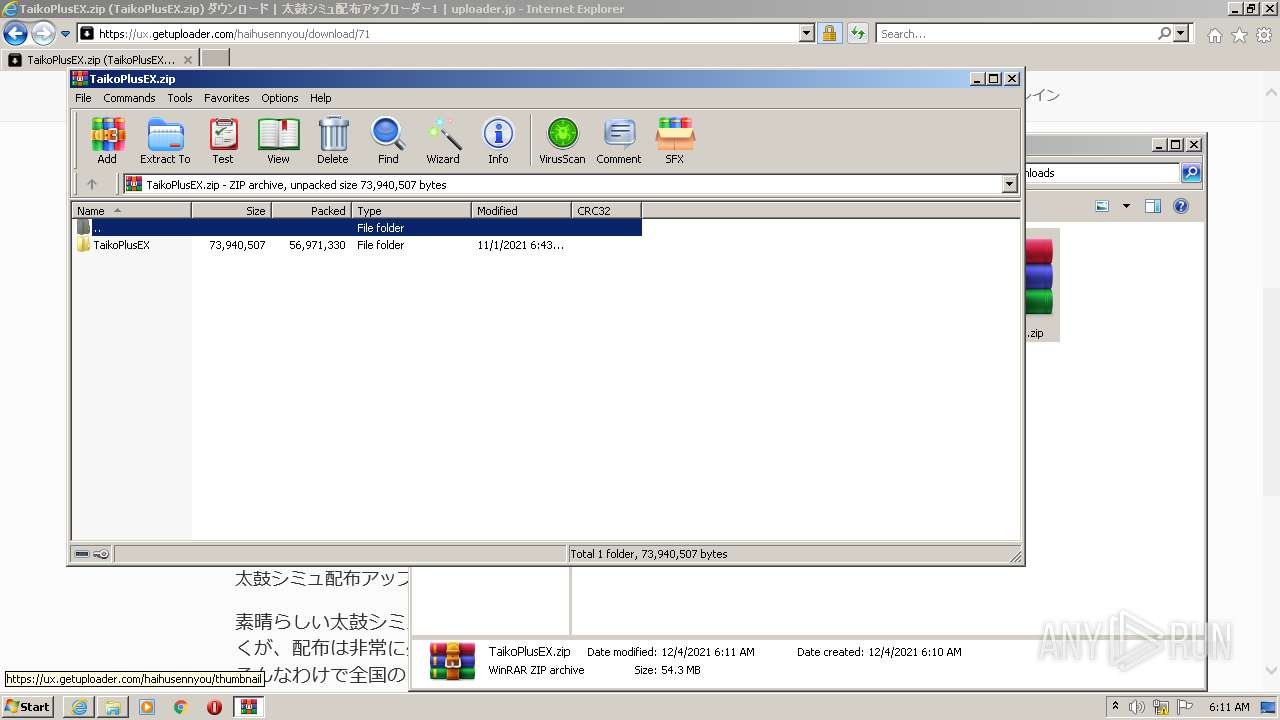
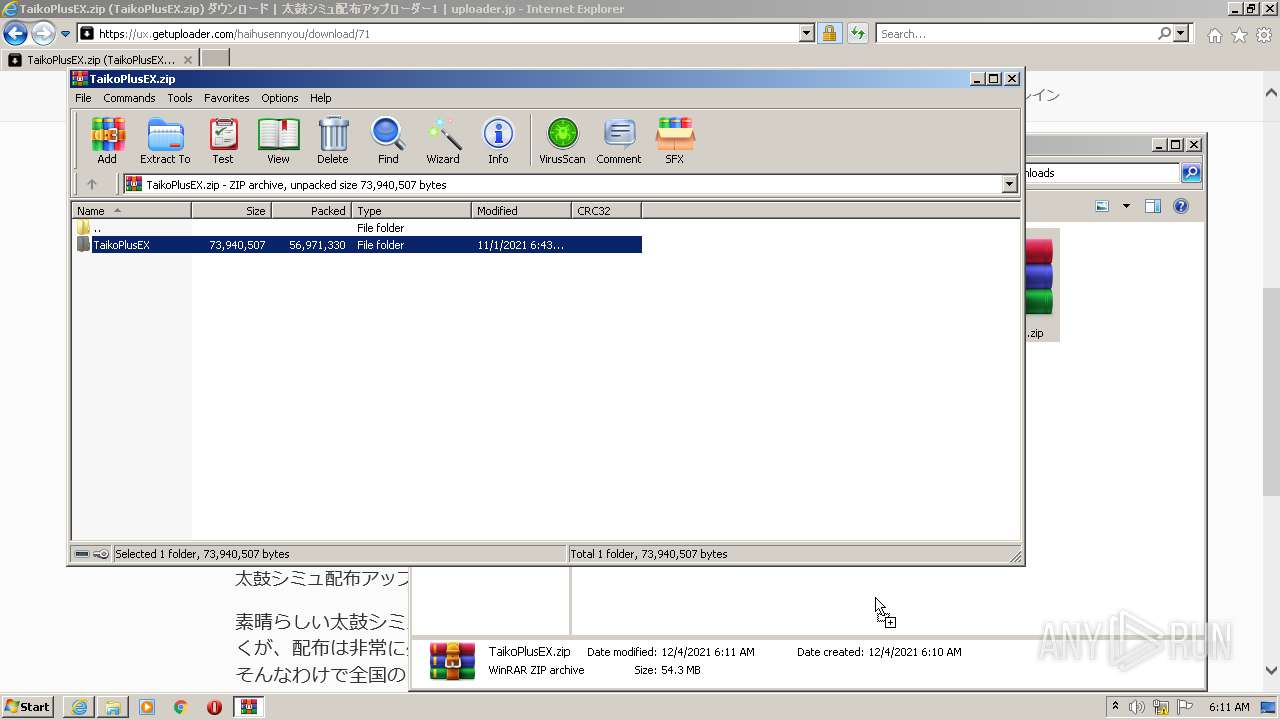
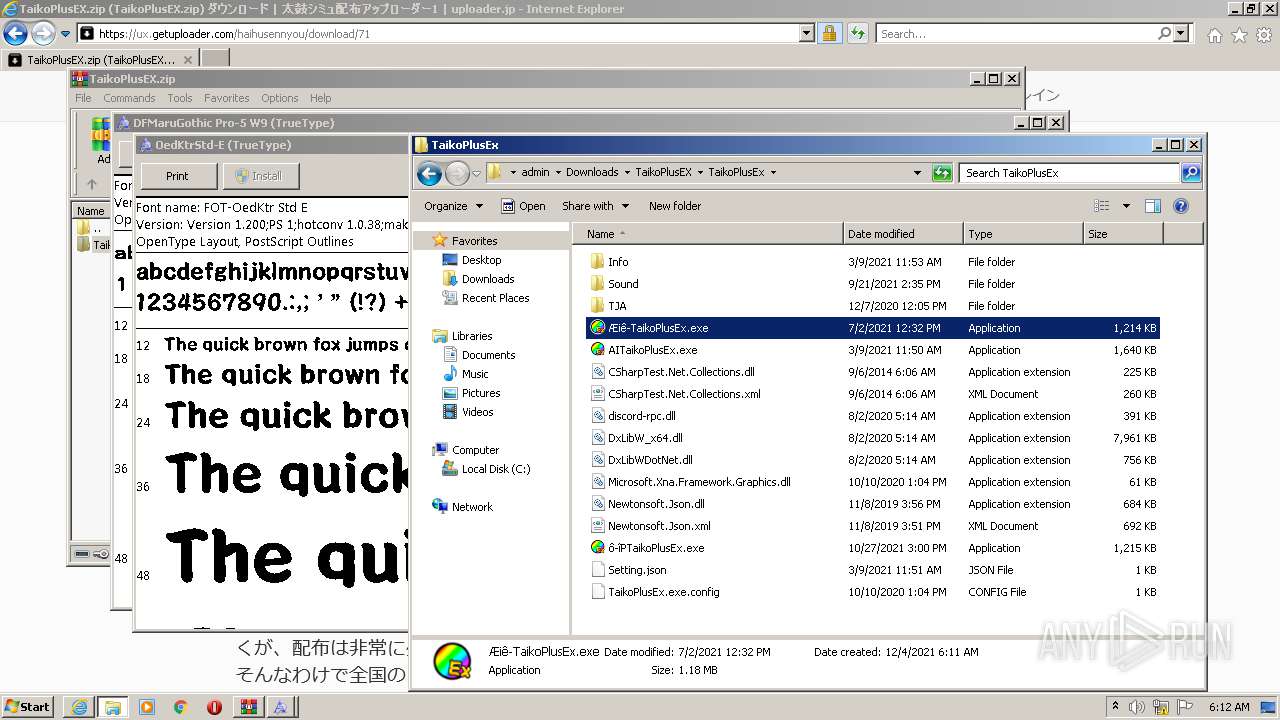
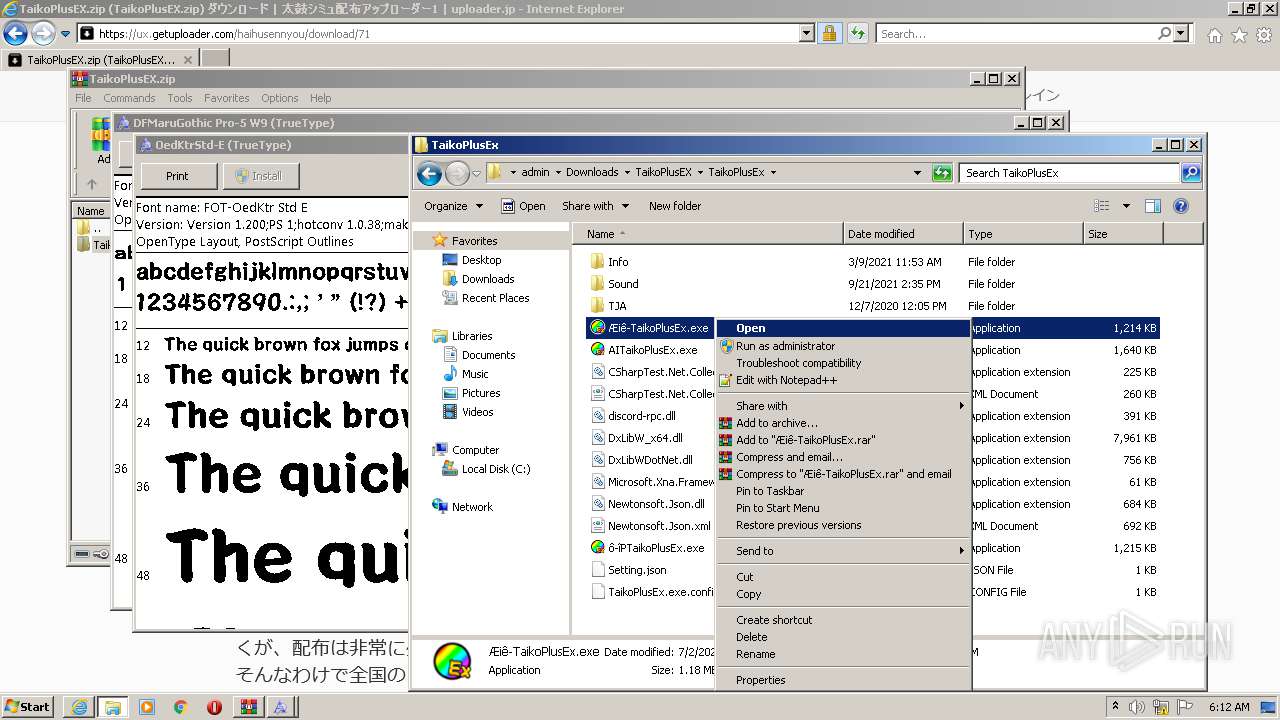
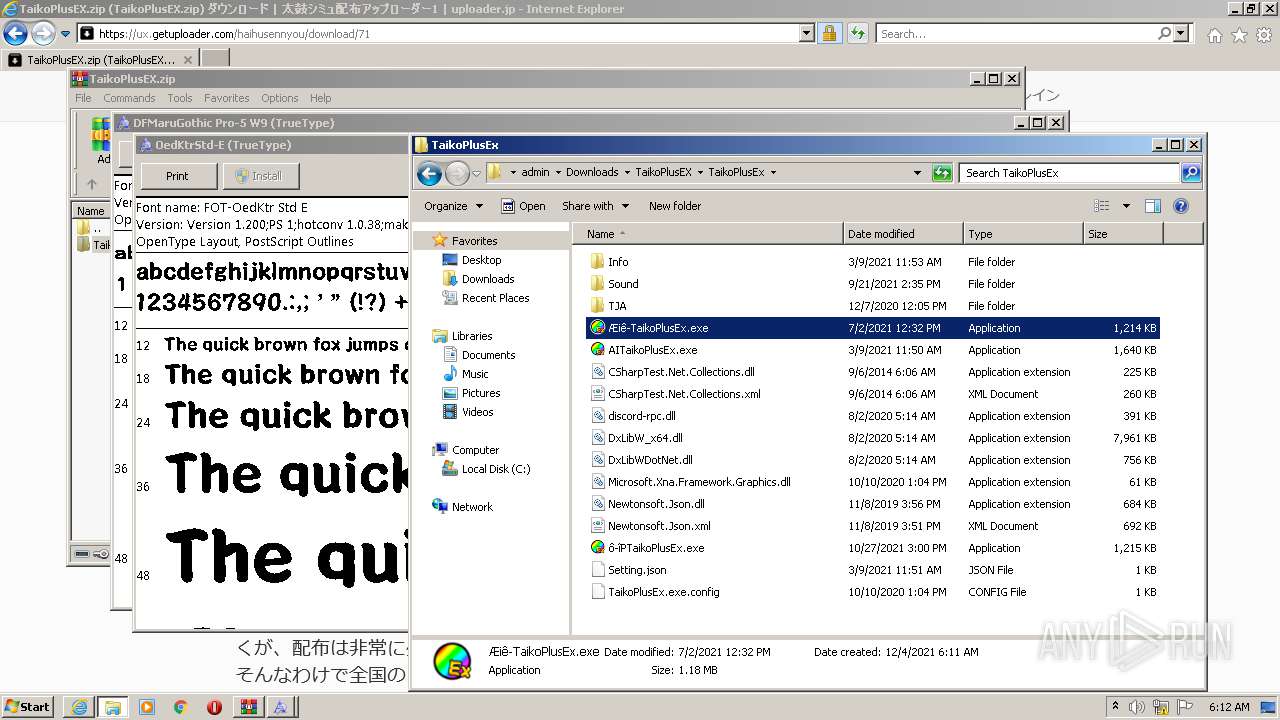
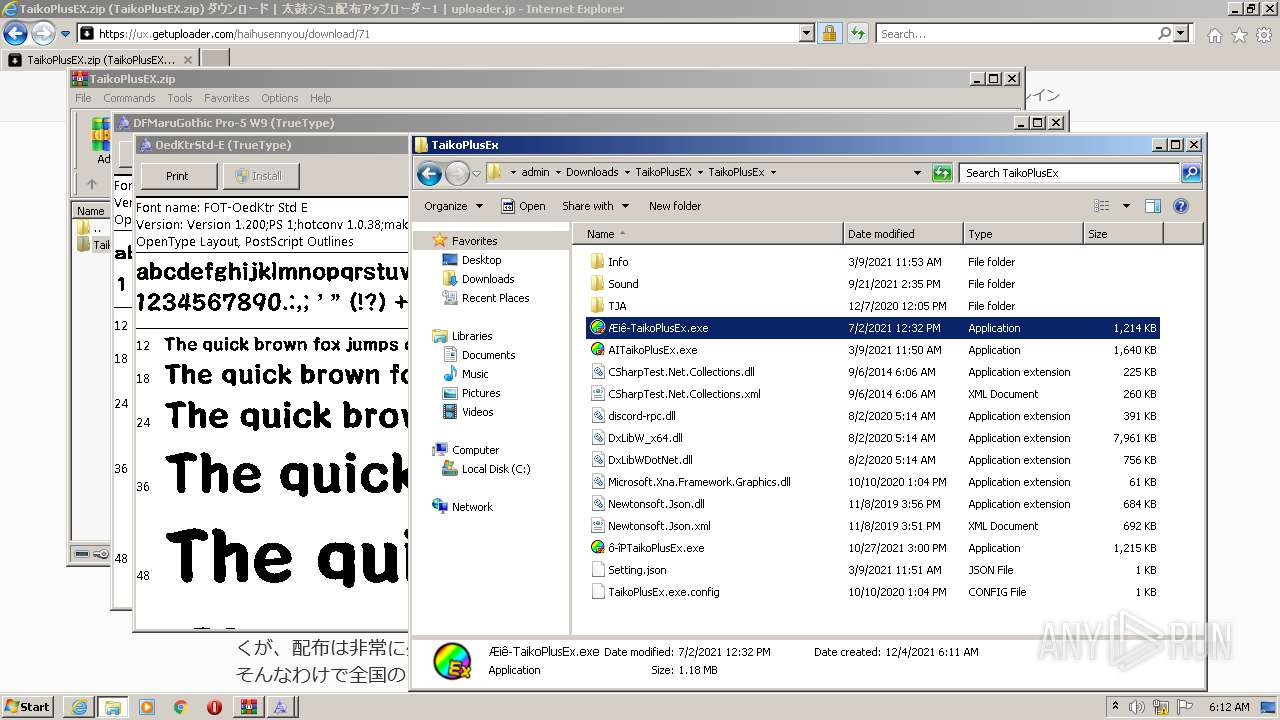
Manual execution by user
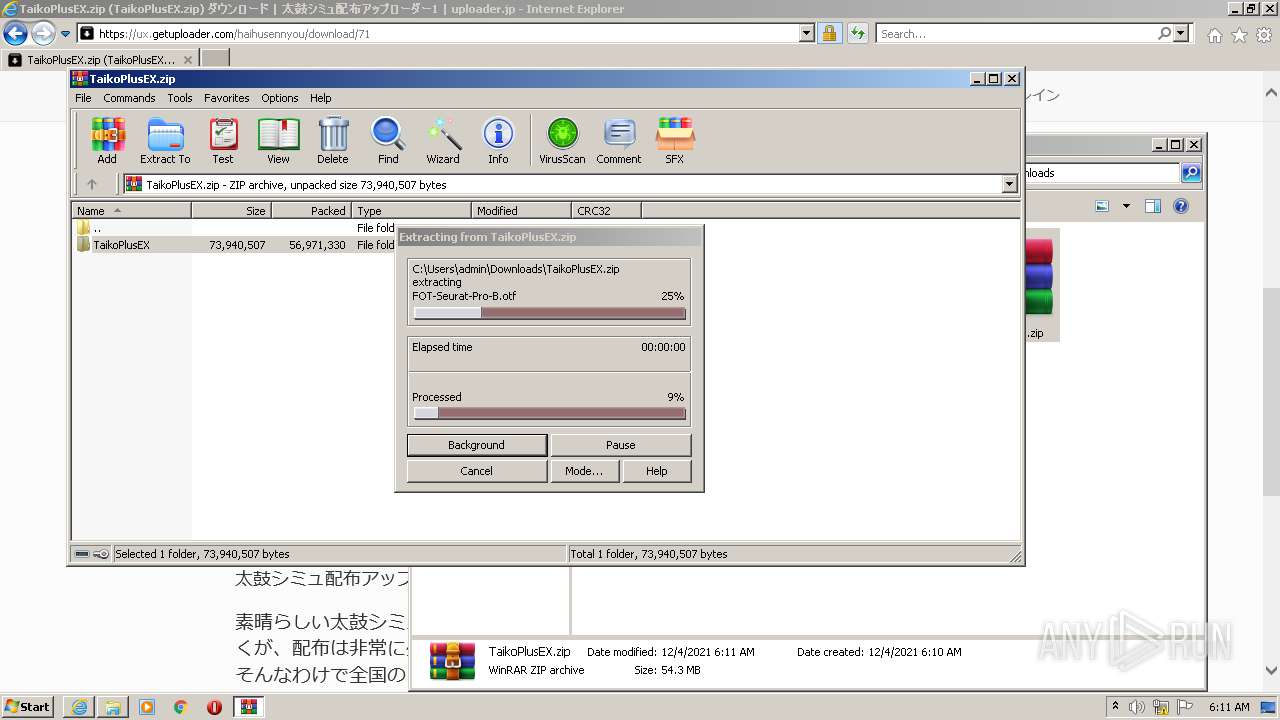
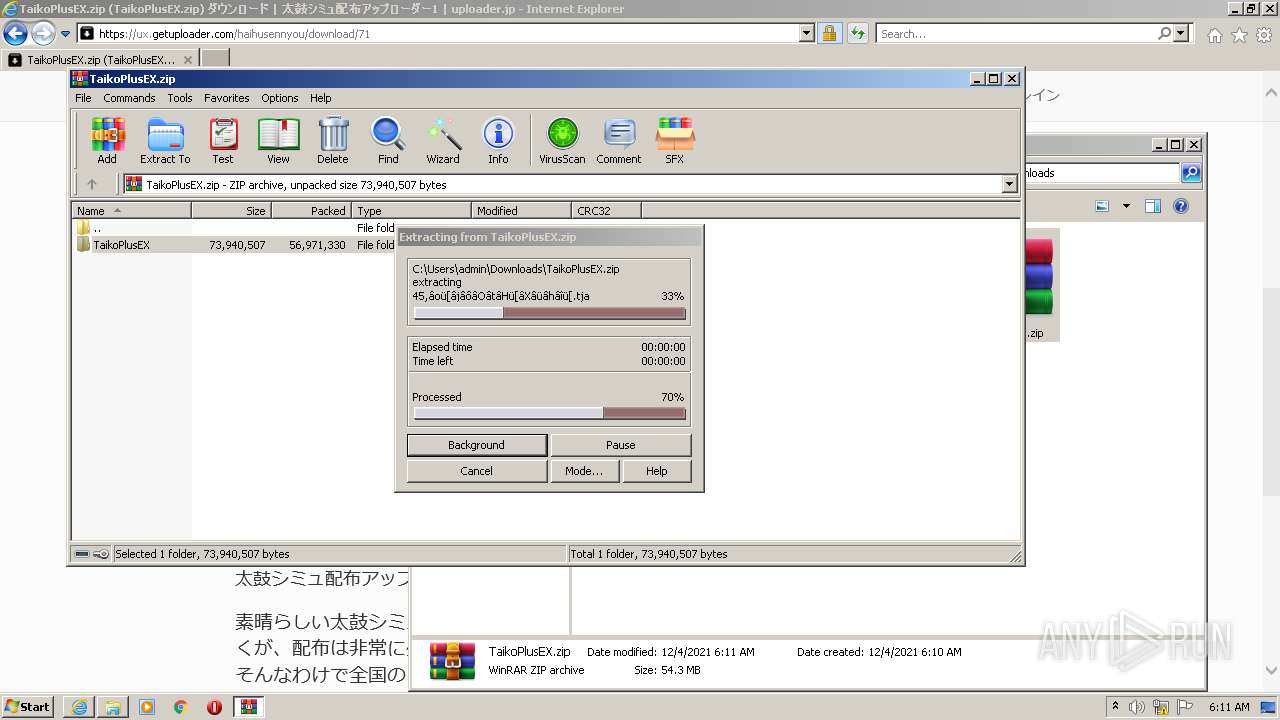
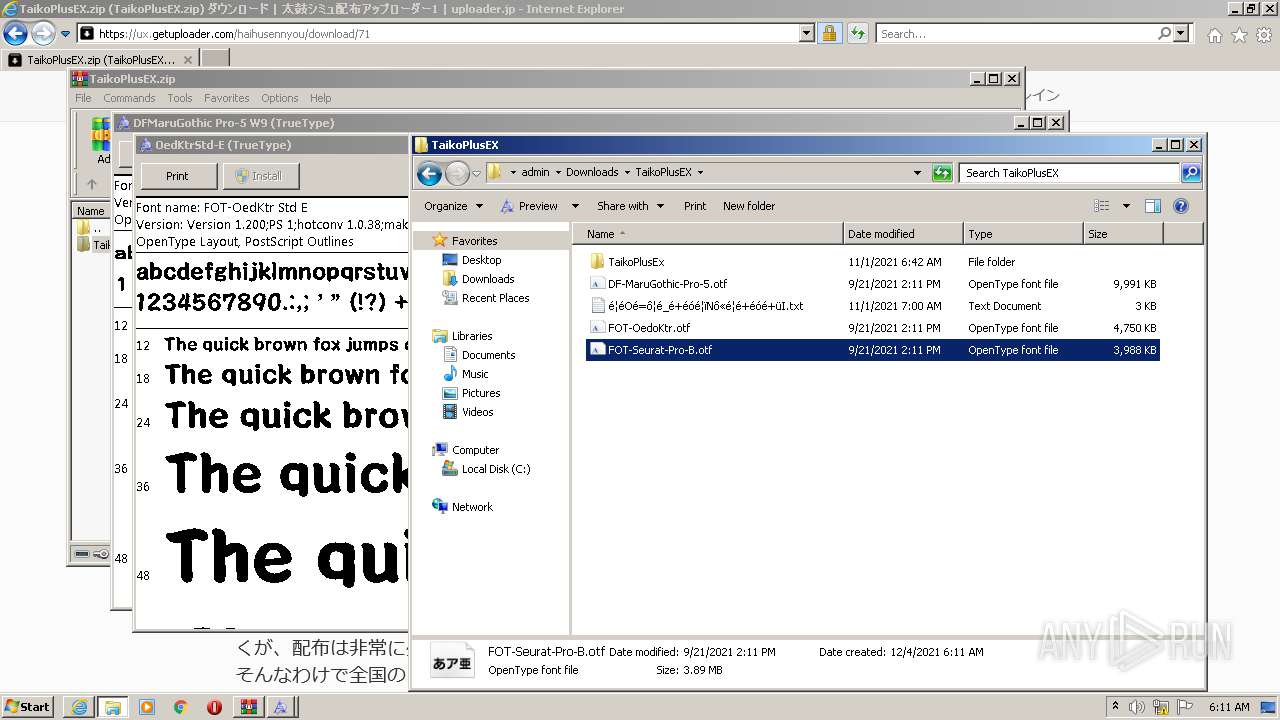
- WinRAR.exe (PID: 2628)
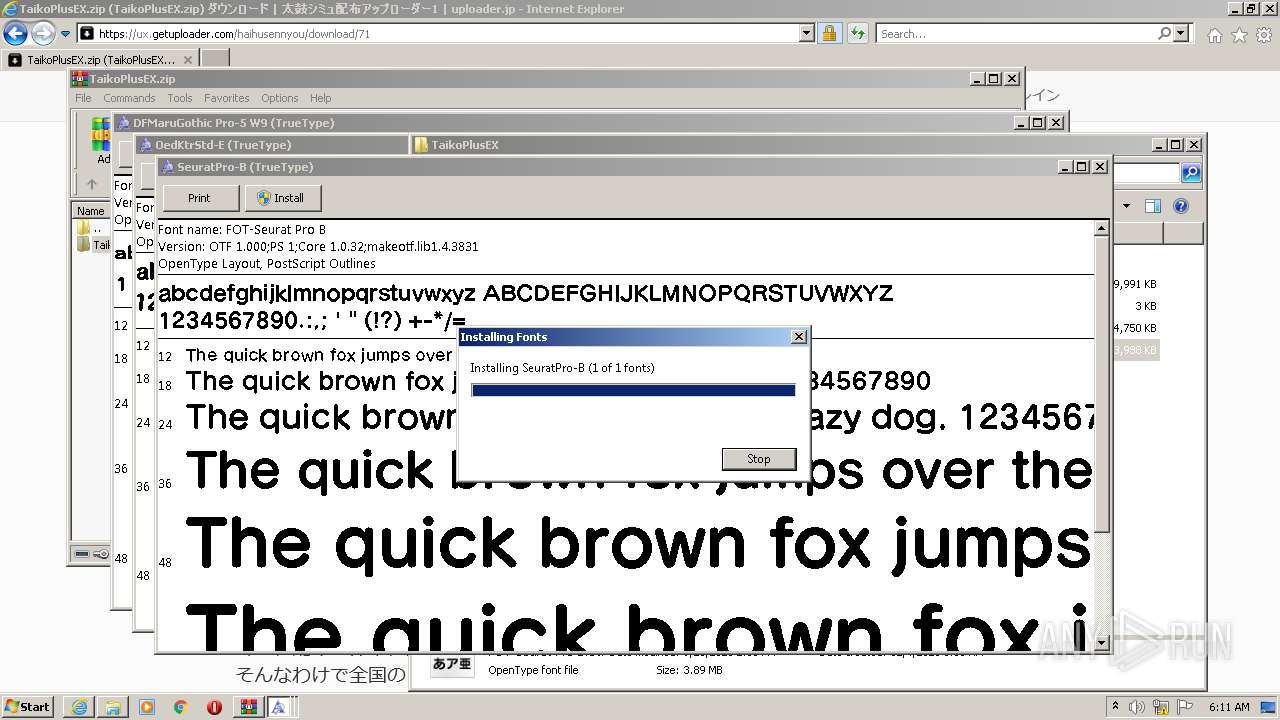
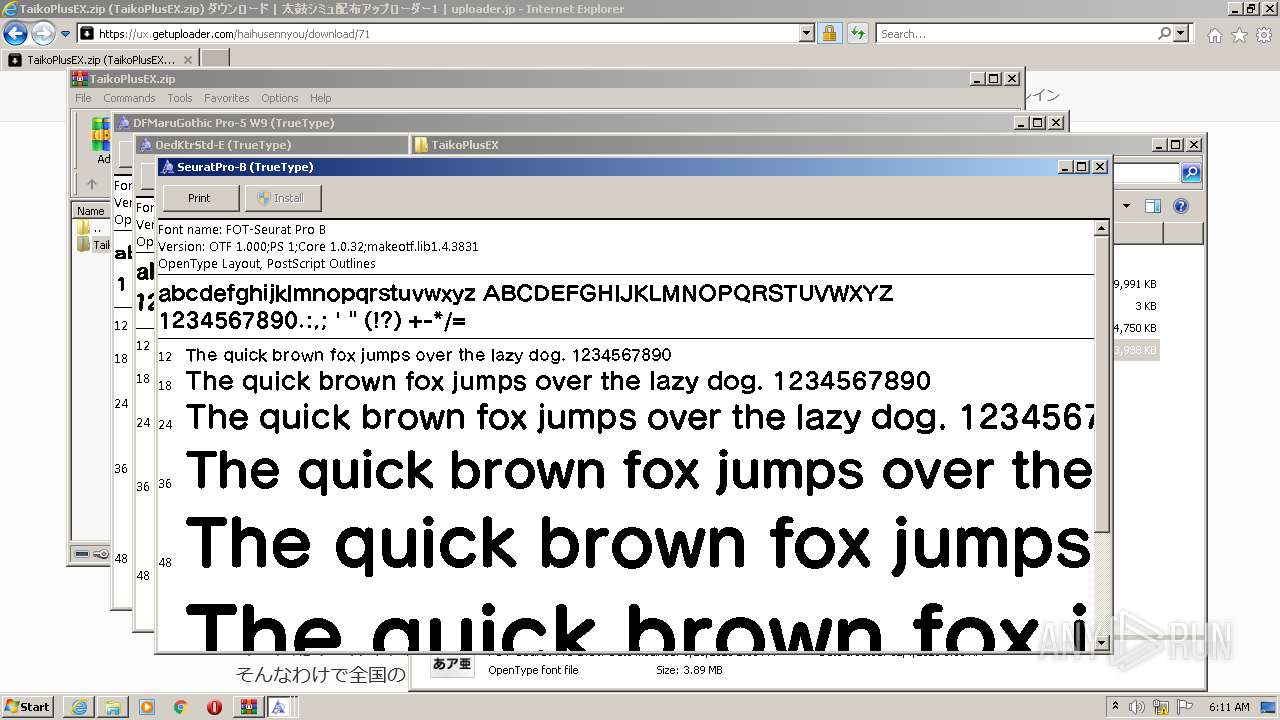
- fontview.exe (PID: 472)
- fontview.exe (PID: 3188)
- fontview.exe (PID: 3900)
Reads internet explorer settings
- iexplore.exe (PID: 1648)
Checks Windows Trust Settings
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 1648)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3904)
Changes settings of System certificates
- iexplore.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
10
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
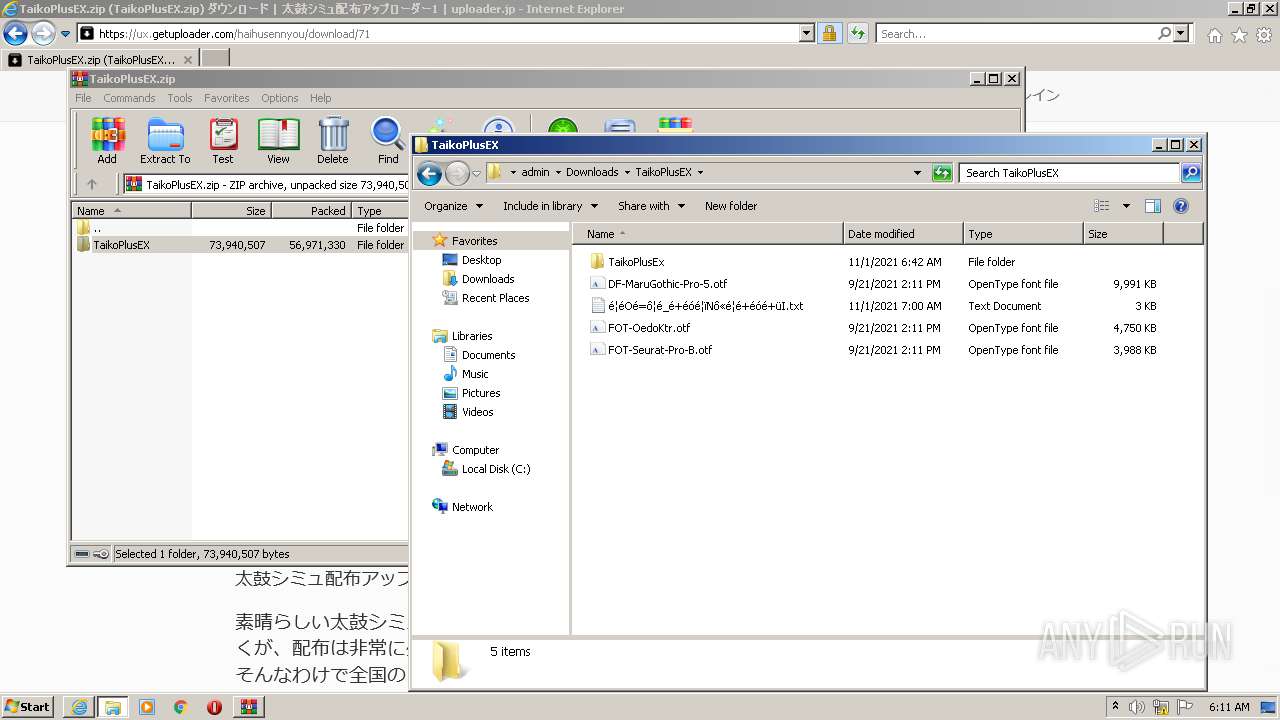
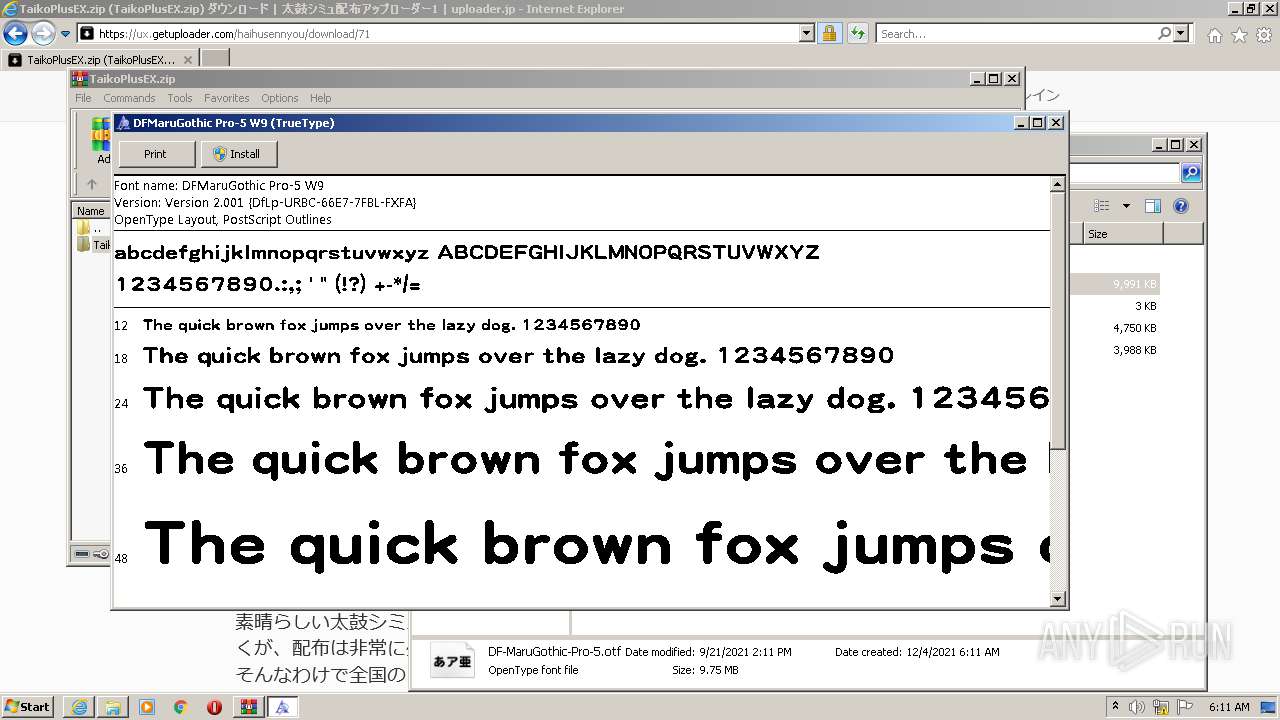
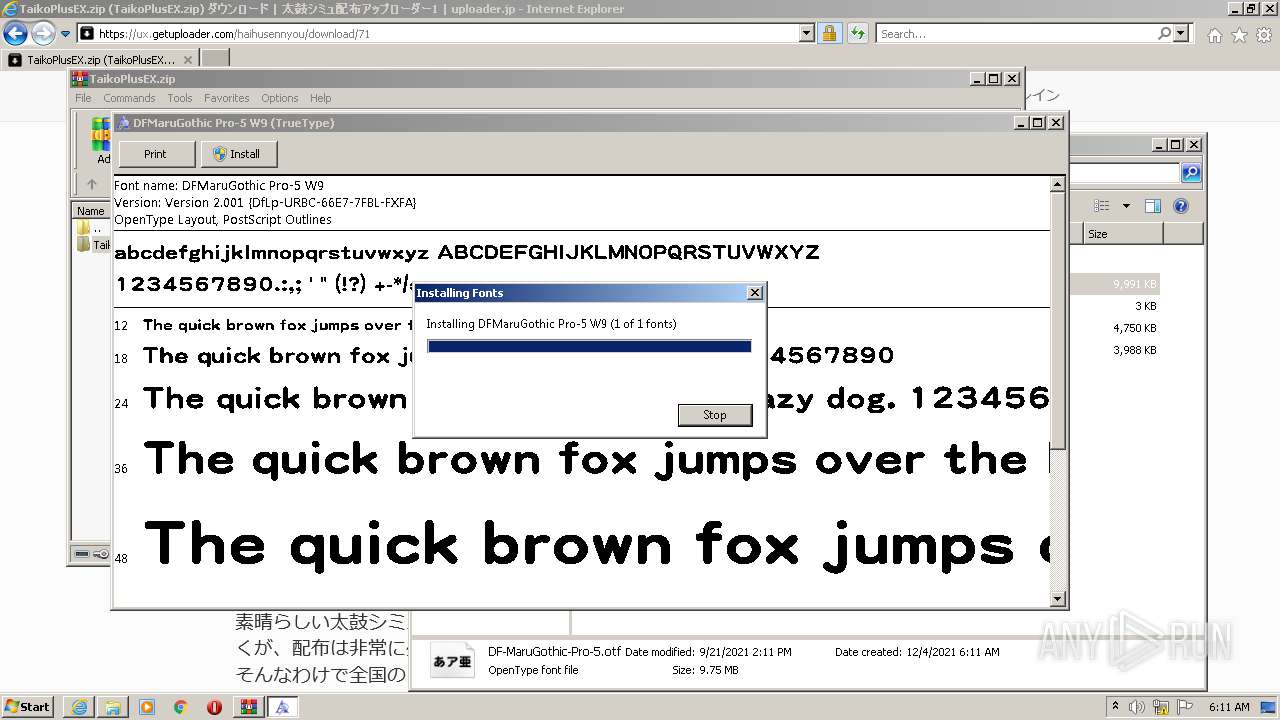
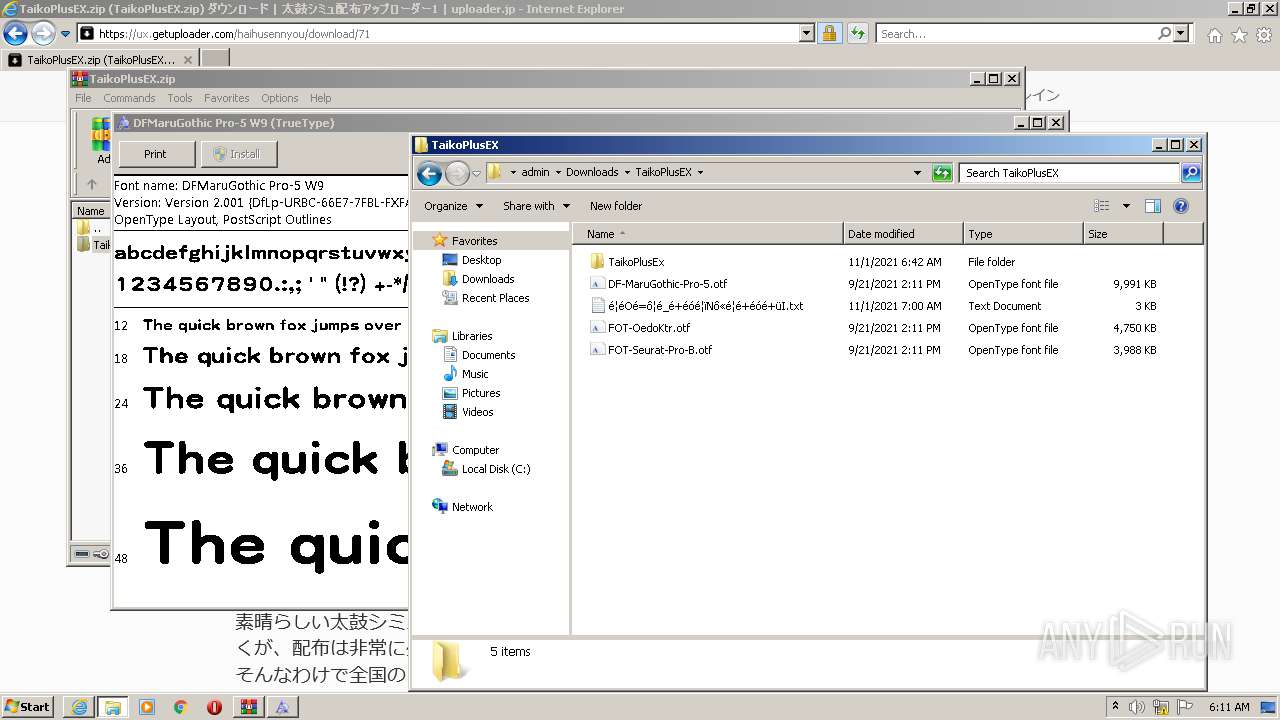
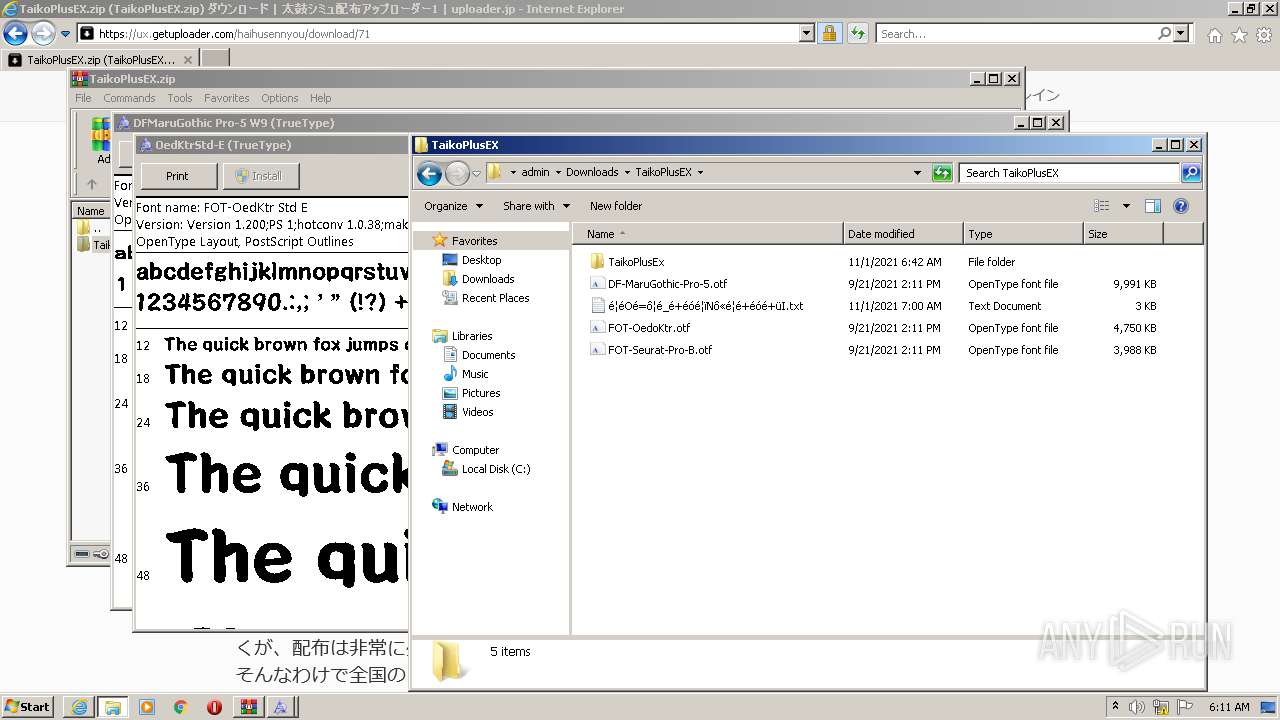
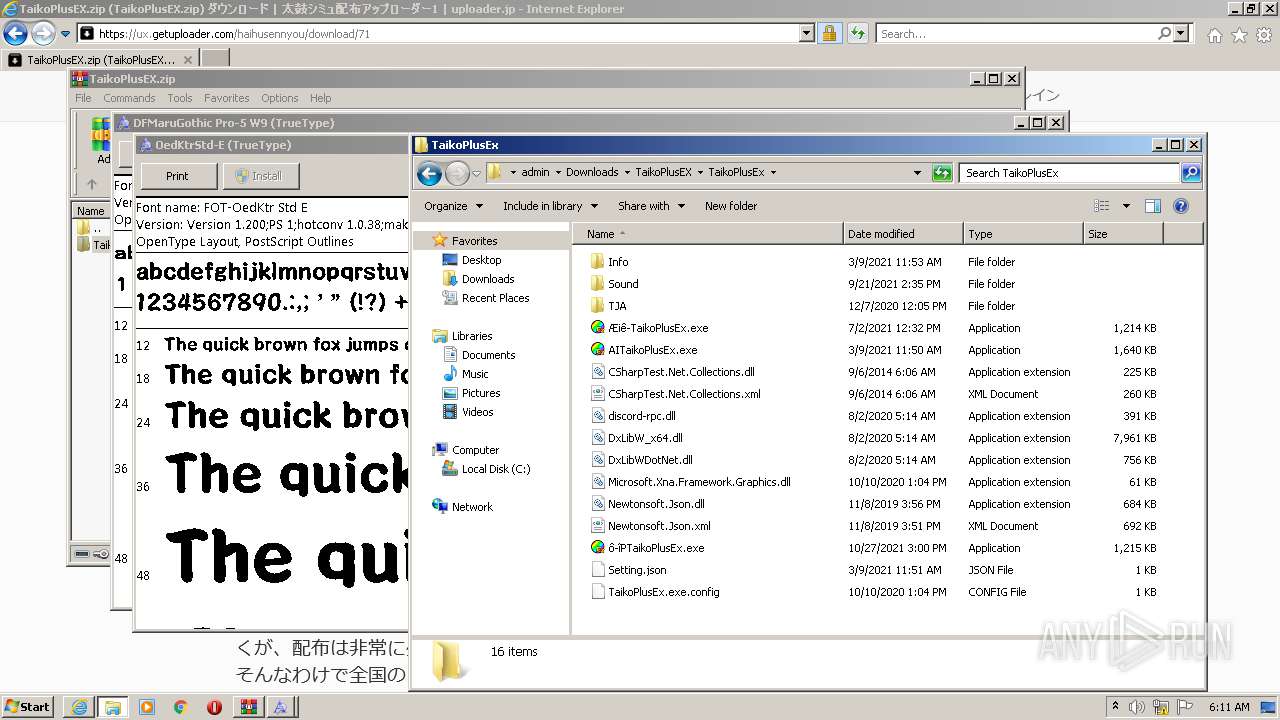
| 472 | "C:\Windows\System32\fontview.exe" C:\Users\admin\Downloads\TaikoPlusEX\DF-MaruGothic-Pro-5.otf | C:\Windows\System32\fontview.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3904 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2252 | C:\Windows\system32\DllHost.exe /Processid:{642EF9D6-48A5-476B-919A-A507CFD02C0F} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\TaikoPlusEX.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3112 | C:\Windows\system32\DllHost.exe /Processid:{642EF9D6-48A5-476B-919A-A507CFD02C0F} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
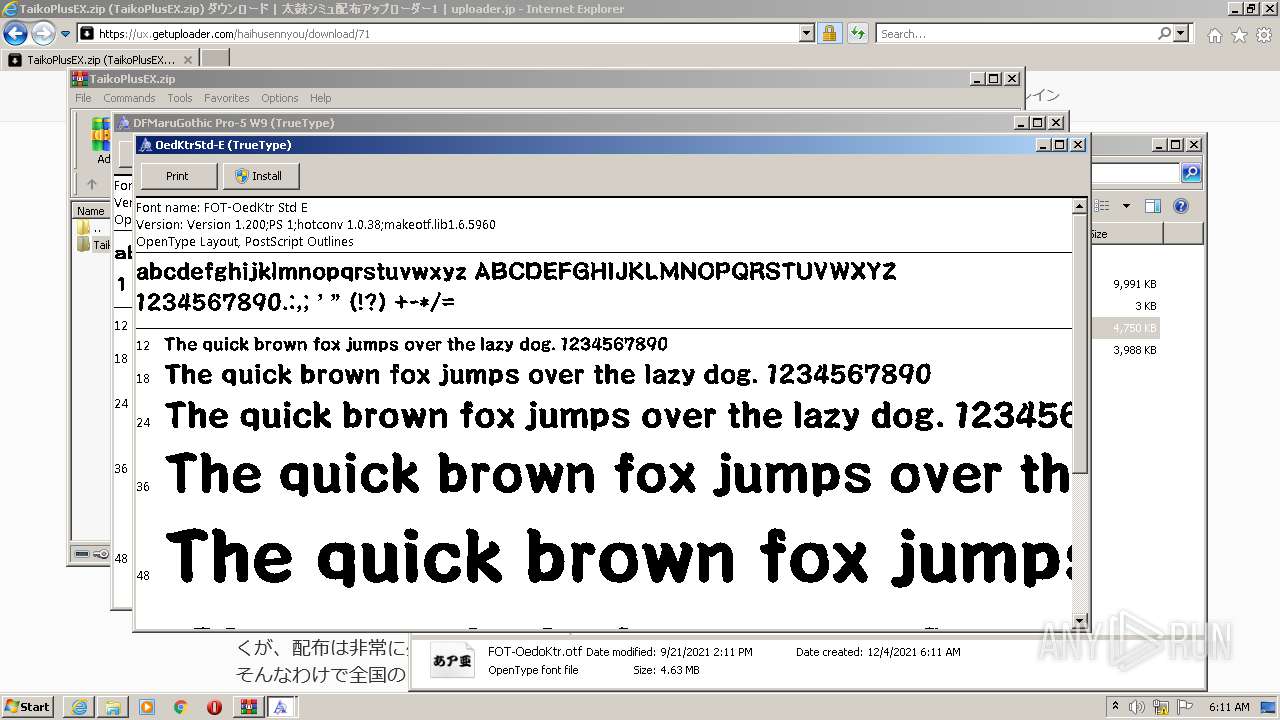
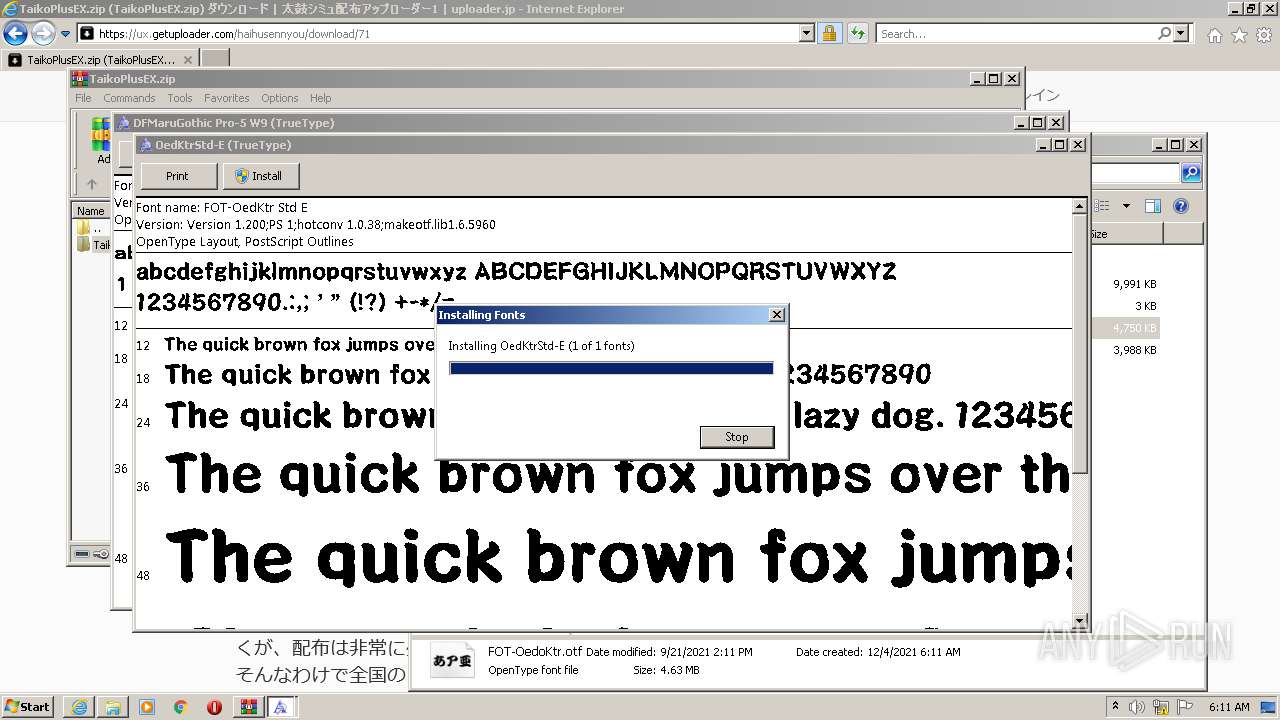
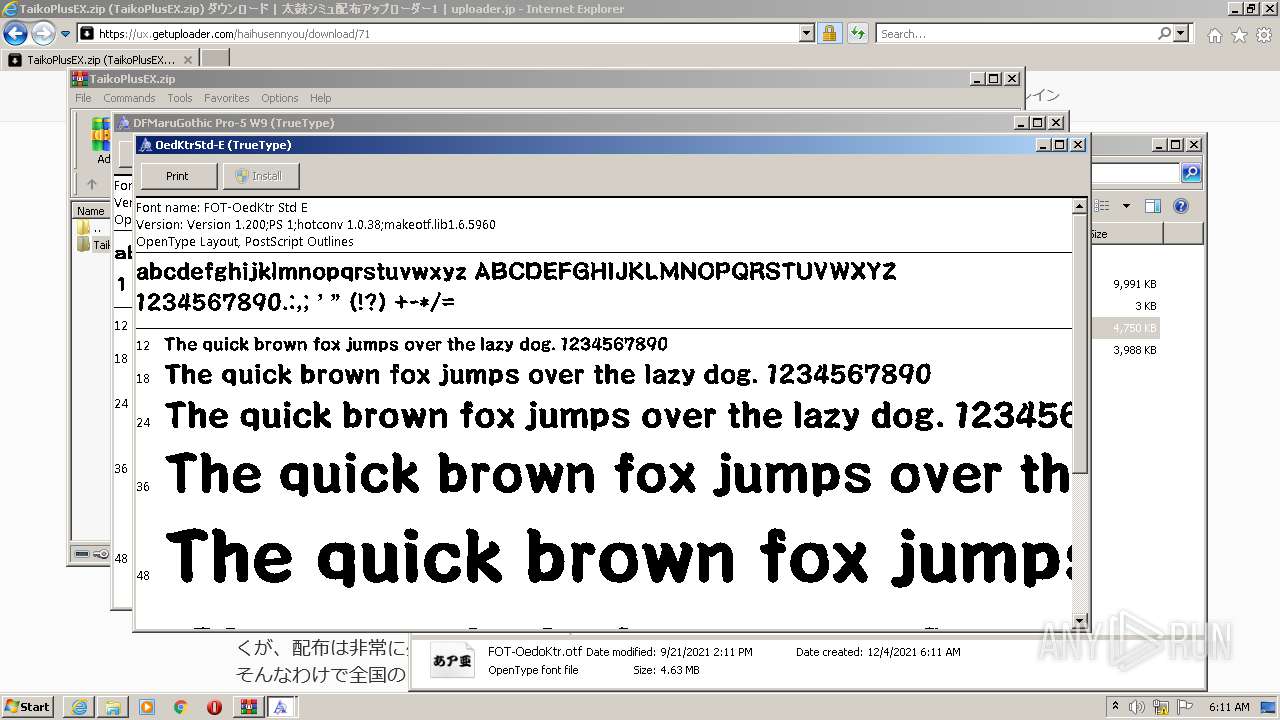
| 3188 | "C:\Windows\System32\fontview.exe" C:\Users\admin\Downloads\TaikoPlusEX\FOT-OedoKtr.otf | C:\Windows\System32\fontview.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | C:\Windows\system32\DllHost.exe /Processid:{642EF9D6-48A5-476B-919A-A507CFD02C0F} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
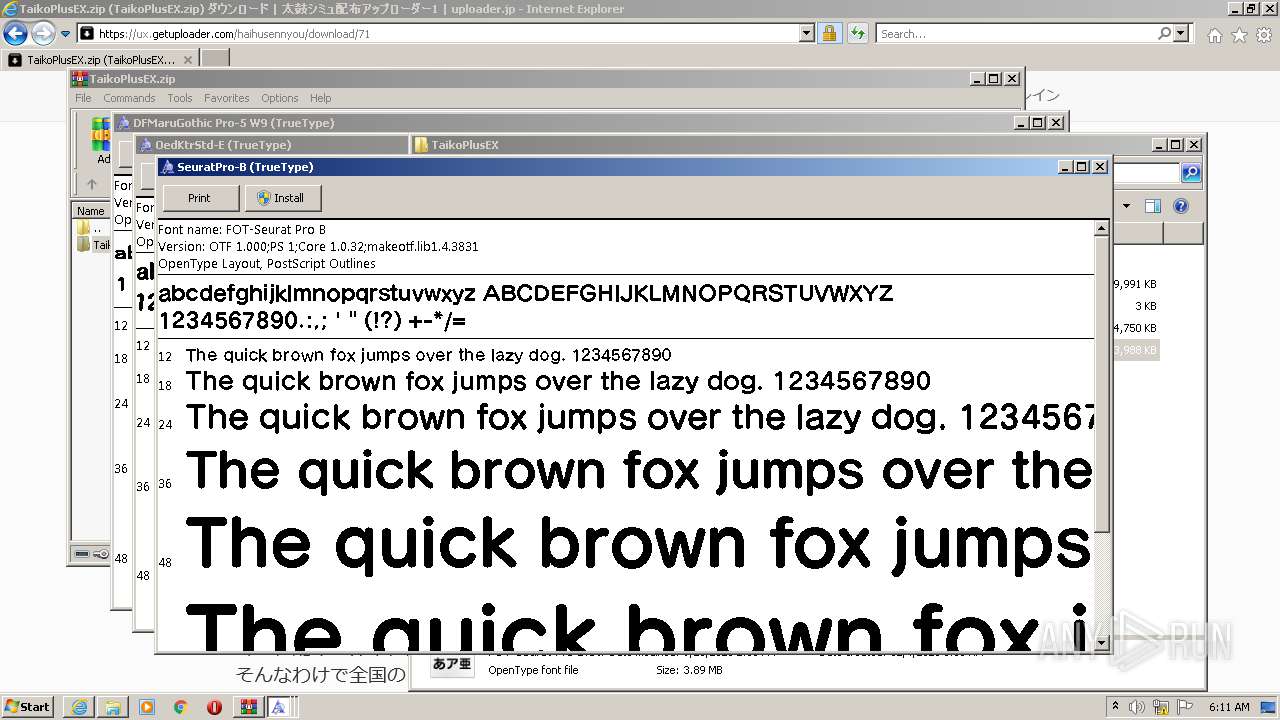
| 3900 | "C:\Windows\System32\fontview.exe" C:\Users\admin\Downloads\TaikoPlusEX\FOT-Seurat-Pro-B.otf | C:\Windows\System32\fontview.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ux.getuploader.com/haihusennyou/download/71" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
26 929
Read events
26 750
Write events
177
Delete events
2
Modification events
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30927061 | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30927061 | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3904) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
47
Text files
180
Unknown types
145
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1648 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JBRLR9CF.txt | text | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_236E243F97CD352248042AF77144B4DB | der | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_236E243F97CD352248042AF77144B4DB | binary | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_68449E40D6F23F8A5B26E120F6AB763F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
119
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAmpuUSjLEJZgAbQkVLxk3Y%3D | US | der | 471 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1648 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC%2BknyXl6Z3%2FgoAAAABGVGI | US | der | 472 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAinCdw%2FKARACgAAAAEZU2s%3D | US | der | 471 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
1648 | iexplore.exe | GET | 200 | 13.32.23.206:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAliLR8wLmtw3X6v58kbOI4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1648 | iexplore.exe | 104.21.60.253:443 | ux.getuploader.com | Cloudflare Inc | US | unknown |
1648 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1648 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
1648 | iexplore.exe | 172.67.204.7:443 | ux.getuploader.com | — | US | unknown |
1648 | iexplore.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
1648 | iexplore.exe | 142.250.184.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1648 | iexplore.exe | 130.211.14.194:443 | cdn-fluct.sh.adingo.jp | Google Inc. | US | whitelisted |
1648 | iexplore.exe | 142.250.185.206:443 | translate.google.com | Google Inc. | US | whitelisted |
1648 | iexplore.exe | 52.68.156.115:443 | sh.adingo.jp | Amazon.com, Inc. | JP | unknown |
1648 | iexplore.exe | 54.168.158.14:443 | i.adingo.jp | Amazon.com, Inc. | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ux.getuploader.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
r.getuploader.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn-fluct.sh.adingo.jp |
| unknown |
translate.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
sh.adingo.jp |
| suspicious |