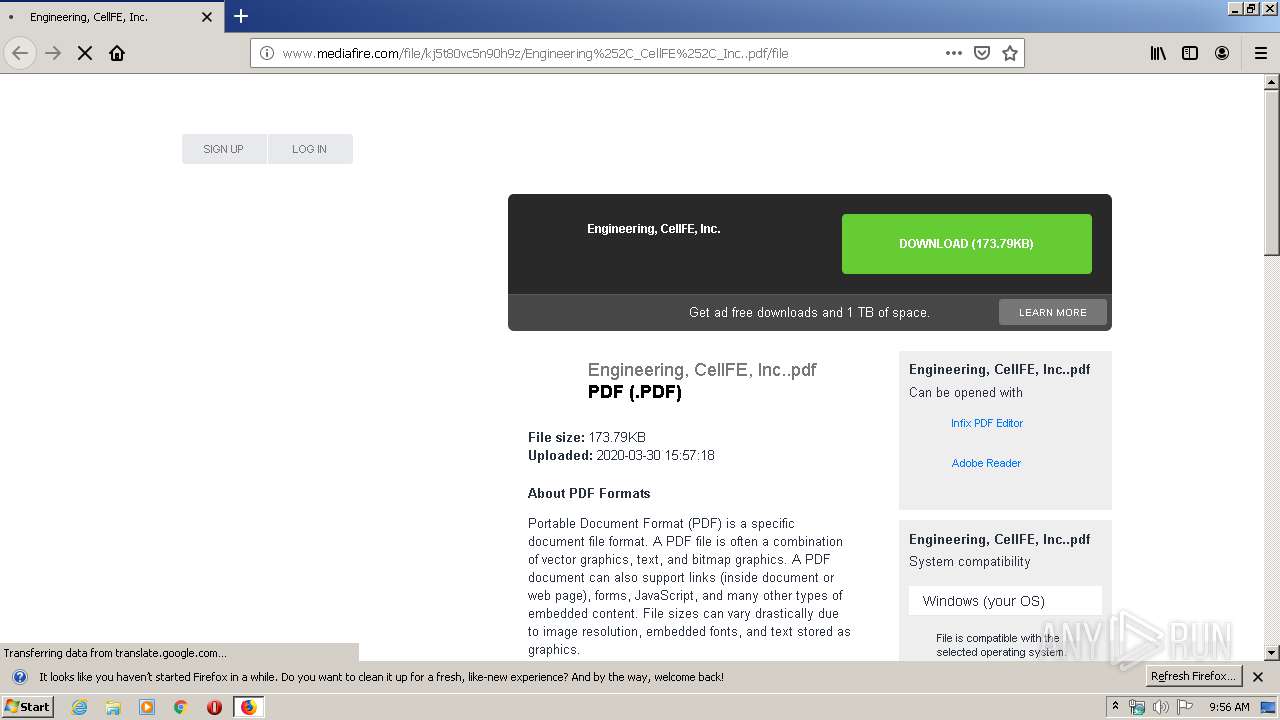
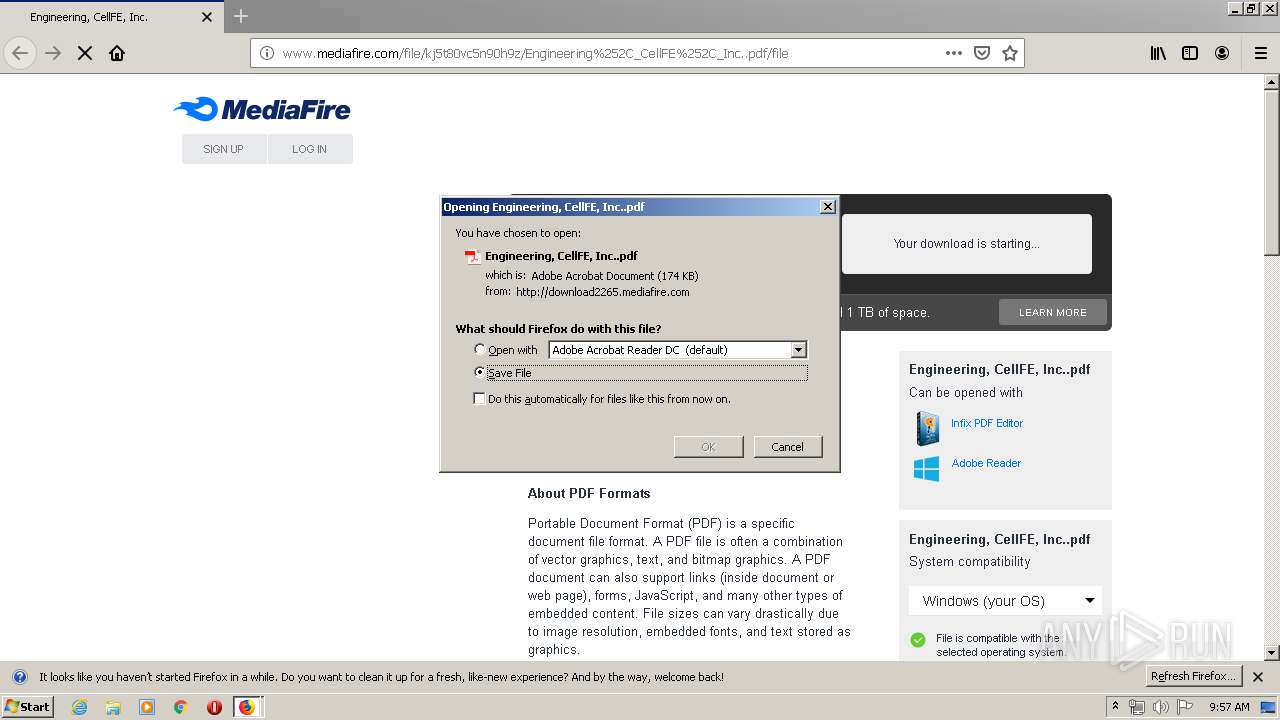
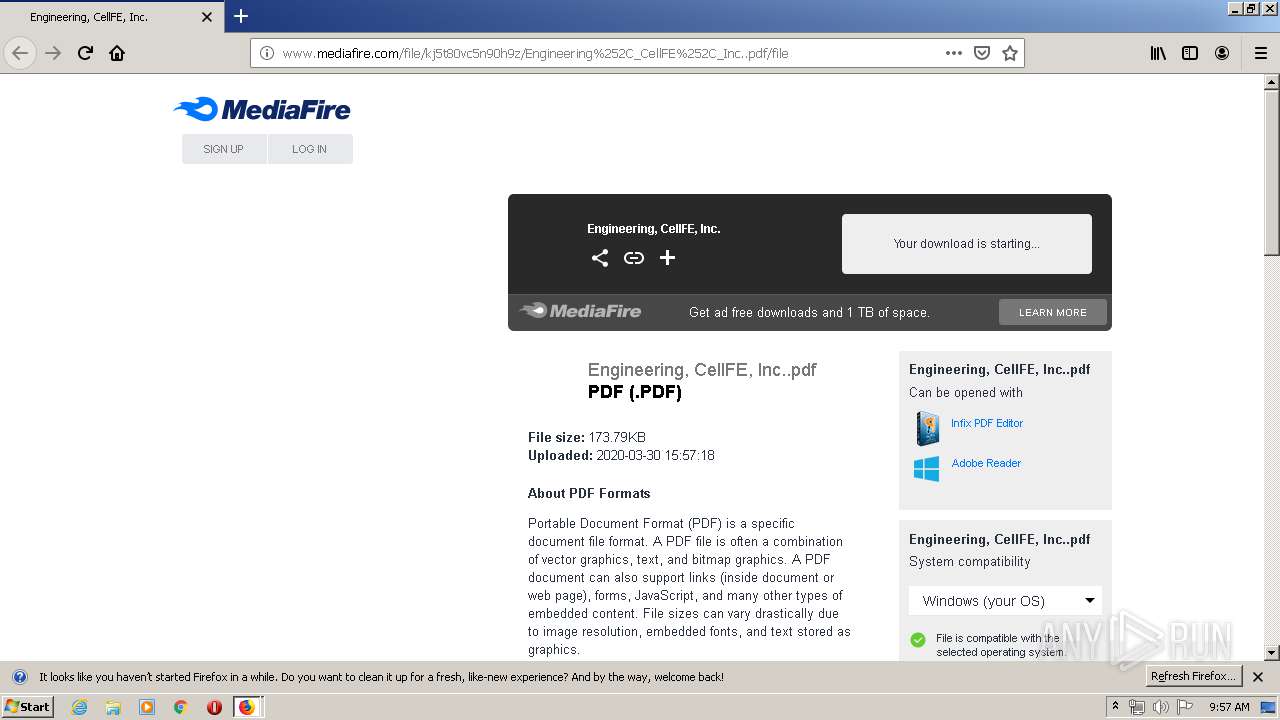
| URL: | https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkj5t80vc5n90h9z%2FEngineering%25252C_CellFE%25252C_Inc..pdf%2Ffile&data=02%7C01%7C%7C0940c47caf1c41a58dd108d7d523fc39%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637212222838233097&sdata=nzROIilJnh1k7YQex6mFYrt%2BaYdJqOQk6ypnOXAkLCg%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/e0ffe292-5b66-43a6-846c-9135eda0db9f |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:56:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AAAD46ED9681FF060A7842C070935934 |
| SHA1: | AB70C6EE0C288F896AA9B11B91ADC72E2CC5C00C |
| SHA256: | 8C3853E6F58EE200B5689C79B84EC53DD15B62093925EAA125FB0BB59AD54293 |
| SSDEEP: | 6:2U9V9iRXPNHszh3eG/fsA9OYcR713oGTksXQILgWES/wkafYwHLiS:2U9qVsF3eefs4O73bnLZjgfjriS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2312)
Loads DLL from Mozilla Firefox
- plugin-container.exe (PID: 3240)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 816)
Connects to server without host name
- firefox.exe (PID: 2312)
Starts Internet Explorer
- AcroRd32.exe (PID: 816)
INFO
Application launched itself
- firefox.exe (PID: 3772)
- firefox.exe (PID: 2312)
- iexplore.exe (PID: 2096)
- AcroRd32.exe (PID: 816)
- RdrCEF.exe (PID: 1024)
Reads CPU info
- firefox.exe (PID: 2312)
Reads Internet Cache Settings
- firefox.exe (PID: 3144)
- firefox.exe (PID: 2312)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2096)
- AcroRd32.exe (PID: 2352)
- AcroRd32.exe (PID: 816)
Dropped object may contain TOR URL's
- firefox.exe (PID: 2312)
Changes internet zones settings
- iexplore.exe (PID: 2096)
Reads the hosts file
- RdrCEF.exe (PID: 1024)
Reads internet explorer settings
- iexplore.exe (PID: 3552)
Reads settings of System Certificates
- AcroRd32.exe (PID: 816)
- iexplore.exe (PID: 3552)
- iexplore.exe (PID: 2096)
Creates files in the user directory
- firefox.exe (PID: 2312)
Changes settings of System certificates
- iexplore.exe (PID: 2096)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
17
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 816 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Downloads\Engineering, CellFE, Inc..pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | firefox.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2312.0.1341437325\876402343" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2312 "\\.\pipe\gecko-crash-server-pipe.2312" 1176 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1024.1.202641780\155185487" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
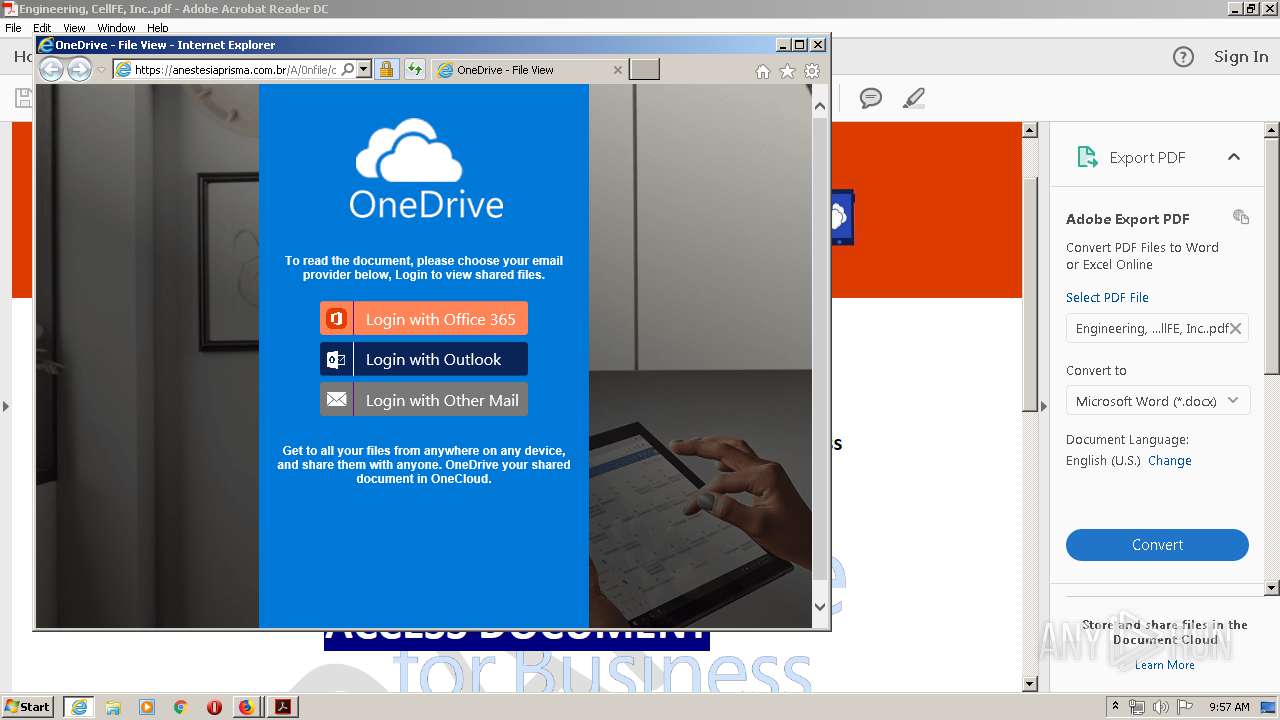
| 2096 | "C:\Program Files\Internet Explorer\iexplore.exe" https://anestesiaprisma.com.br/A/0nfile/oneddrive/ | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2312.20.1653837285\1266945055" -childID 3 -isForBrowser -prefsHandle 3884 -prefMapHandle 3880 -prefsLen 7196 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2312 "\\.\pipe\gecko-crash-server-pipe.2312" 3964 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://eur01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fkj5t80vc5n90h9z%2FEngineering%25252C_CellFE%25252C_Inc..pdf%2Ffile&data=02%7C01%7C%7C0940c47caf1c41a58dd108d7d523fc39%7C28042244bb514cd680347776fa3703e8%7C1%7C0%7C637212222838233097&sdata=nzROIilJnh1k7YQex6mFYrt%2BaYdJqOQk6ypnOXAkLCg%3D&reserved=0 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Downloads\Engineering, CellFE, Inc..pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1024.0.847042876\1090525923" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
4 441
Read events
2 180
Write events
1 541
Delete events
720
Modification events
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 1AD271EE08000000 | |||
| (PID) Process: | (3772) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: B8AD6EEE08000000 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2312) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | AcroExch.Document.DC |
Value: | |||
| (PID) Process: | (2352) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2352) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
Executable files
0
Suspicious files
279
Text files
173
Unknown types
182
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
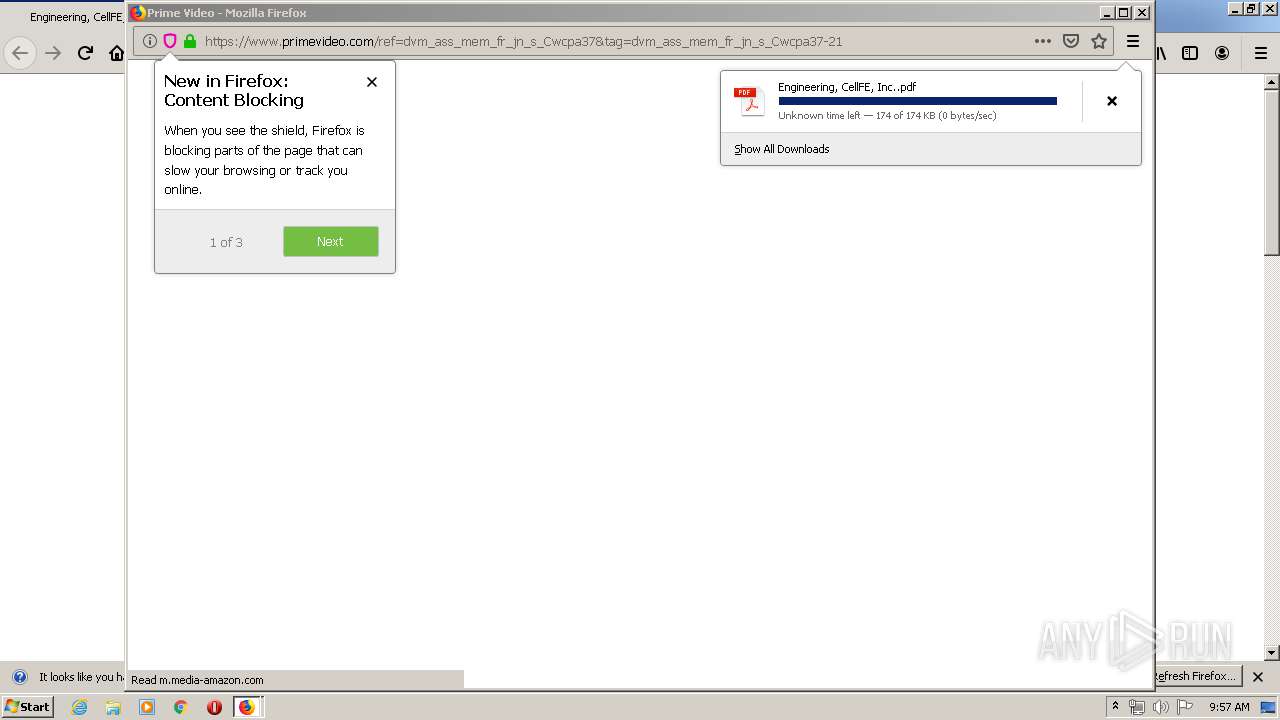
| 2312 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2312 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
189
DNS requests
292
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2312 | firefox.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/kj5t80vc5n90h9z/Engineering%252C_CellFE%252C_Inc..pdf/file | US | html | 82.2 Kb | shared |
2312 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2312 | firefox.exe | GET | 200 | 216.58.208.46:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
2312 | firefox.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
2312 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2312 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2312 | firefox.exe | POST | 200 | 185.33.223.209:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 248 b | whitelisted |
2312 | firefox.exe | POST | 200 | 185.33.223.209:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 249 b | whitelisted |
2312 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2312 | firefox.exe | POST | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
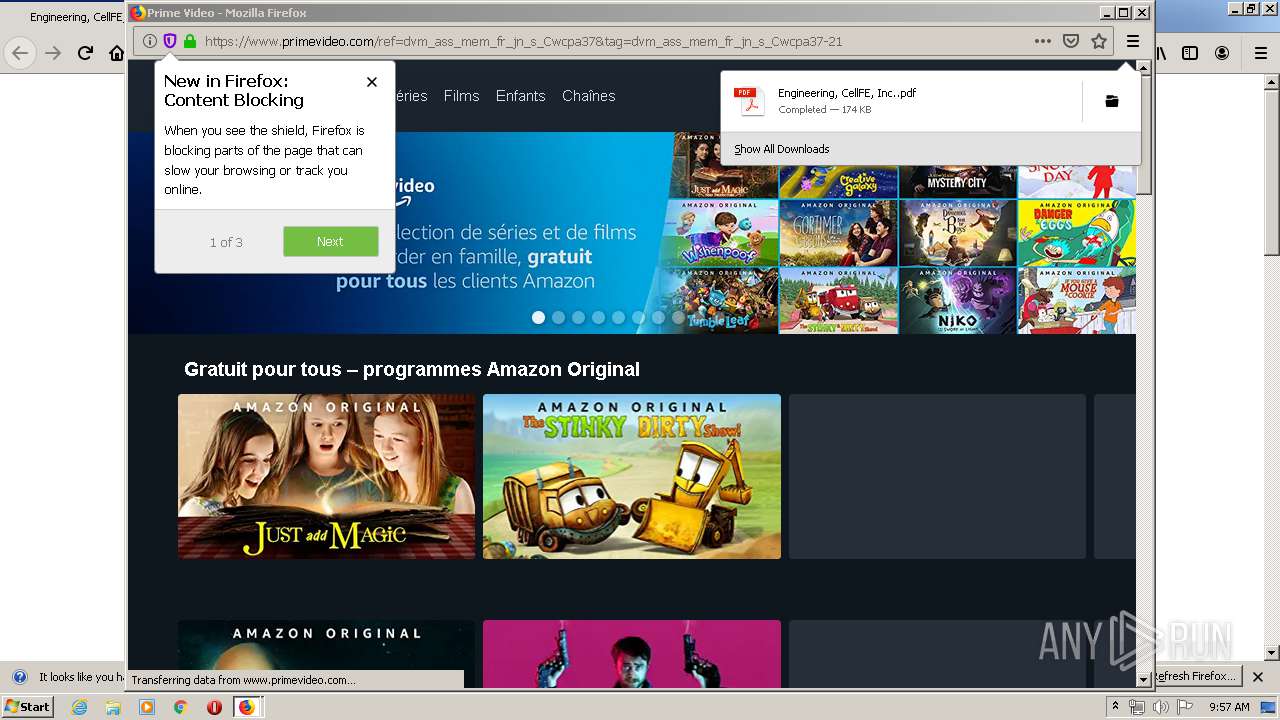
2312 | firefox.exe | 104.103.100.114:443 | c.aaxads.com | Akamai Technologies, Inc. | NL | whitelisted |
2312 | firefox.exe | 172.217.16.130:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
2312 | firefox.exe | 216.58.208.46:80 | translate.google.com | Google Inc. | US | whitelisted |
2312 | firefox.exe | 172.217.22.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2312 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2312 | firefox.exe | 104.16.68.69:443 | dmx.districtm.io | Cloudflare Inc | US | shared |
2312 | firefox.exe | 23.55.110.80:80 | detectportal.firefox.com | NTT America, Inc. | US | unknown |
2312 | firefox.exe | 52.38.153.3:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2312 | firefox.exe | 104.47.0.28:443 | eur01.safelinks.protection.outlook.com | Microsoft Corporation | FI | whitelisted |
2312 | firefox.exe | 54.186.106.198:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
eur01.safelinks.protection.outlook.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
2312 | firefox.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2312 | firefox.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2312 | firefox.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |