| download: | index.html |
| Full analysis: | https://app.any.run/tasks/3b65c249-dfa8-469e-a737-e3ac6fa9c8ed |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2019, 16:48:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 991B98888CEA431C5BB03402177A9B8B |
| SHA1: | 36D53E04FBEF6E8C8C9284F1573D31CC7002D910 |
| SHA256: | 8C33FFF2AAFE5DD82C09B233A57C992FE63AA7561130926B744D3CF3DD2201B4 |
| SSDEEP: | 768:Euh6wkPE/sPaJeaPSlwh2cFhg2kZPk6CFAg5++bGhAh9PJhohchfhV7hghWhDhza:E1PEUSLKlHGZPPhJXZG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2860)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2740)
Reads Internet Cache Settings
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 3812)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2860)
- iexplore.exe (PID: 1992)
- iexplore.exe (PID: 3812)
Application launched itself
- iexplore.exe (PID: 2740)
Reads settings of System Certificates
- iexplore.exe (PID: 3812)
Reads internet explorer settings
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 1992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
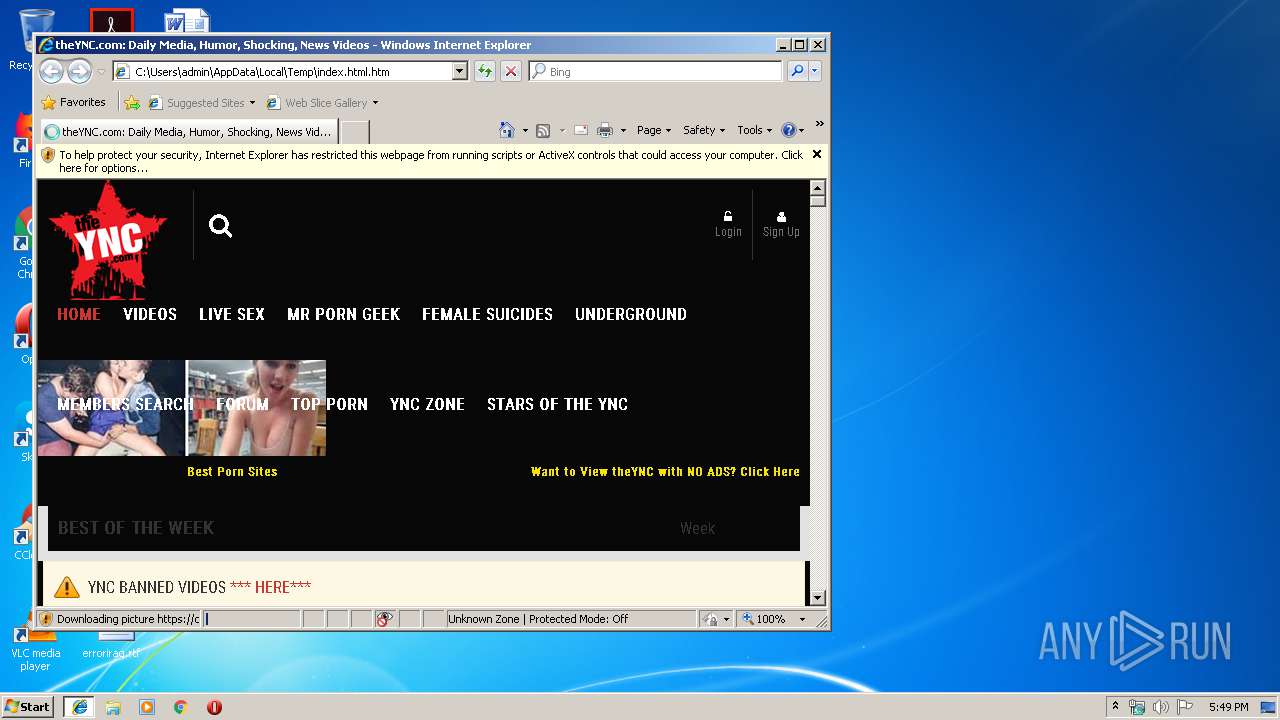
| Title: | theYNC.com: Daily Media, Humor, Shocking, News Videos |
|---|---|
| referrer: | always |
| HTTPEquivXUACompatible: | IE=edge |
| viewport: | width=device-width, initial-scale=1.0 |
| Description: | - |
| Keywords: | - |
| exoclickSiteVerification: | 399cb04a65dbe227c2f205e66b54ba1b |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1992 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2740 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2740 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
784
Read events
667
Write events
117
Delete events
0
Modification events
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8106E551-F810-11E9-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2740) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A0006001A00100030003B00E501 | |||
Executable files
0
Suspicious files
2
Text files
379
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\overwrite[1].css | text | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\bootstrap-select[1].css | text | |
MD5:6FE94CCD98E1ACCE5FFAD8EB1CF9352D | SHA256:00A1C49B6F67F67B10AB6B70B6F9146ACF7941FF2CD46266560D1CE69DC9C8A8 | |||
| 2740 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\font-awesome[1].css | text | |
MD5:8E12157DA5FC90094AE4113BA110456B | SHA256:8E17416059F9E1ADA9694AE457D869C6C2941D9DA66C9E9AC5D725AB45B50D81 | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\jquery.min[1].js | text | |
MD5:F03E5A3BF534F4A738BC350631FD05BD | SHA256:AEC3D419D50F05781A96F223E18289AEB52598B5DB39BE82A7B71DC67D6A7947 | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\toggle-switch[1].css | text | |
MD5:1C14FC377DAB278297DFB9A46A27BF8D | SHA256:E630EADE59E07E24CCBA032505D90CA5E544ED3E71037BC07F6C987BEB6F0E4D | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\rwd[1].css | text | |
MD5:752DB48DA39178E30E0C6AB3D982EF1A | SHA256:A4B029B00037BBC979E93DB5BC52837434B60BBA9B75297AD19E92E63EADE68F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
251
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2740 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3812 | iexplore.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3812 | iexplore.exe | 104.18.226.52:443 | cdn.onesignal.com | Cloudflare Inc | US | malicious |
3812 | iexplore.exe | 151.139.128.10:443 | cdn1.traffichaus.com | Highwinds Network Group, Inc. | US | malicious |
3812 | iexplore.exe | 104.20.121.36:443 | theync.com | Cloudflare Inc | US | unknown |
3812 | iexplore.exe | 172.217.16.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3812 | iexplore.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1992 | iexplore.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3812 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
3812 | iexplore.exe | 162.247.242.21:443 | bam.nr-data.net | New Relic | US | whitelisted |
3812 | iexplore.exe | 104.19.242.83:443 | chatws11.stream.highwebmedia.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
theync.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn1.traffichaus.com |
| whitelisted |
cdn.onesignal.com |
| whitelisted |
thumbs.theync.com |
| unknown |
cdn2.theync.com |
| unknown |
chaturbate.com |
| suspicious |