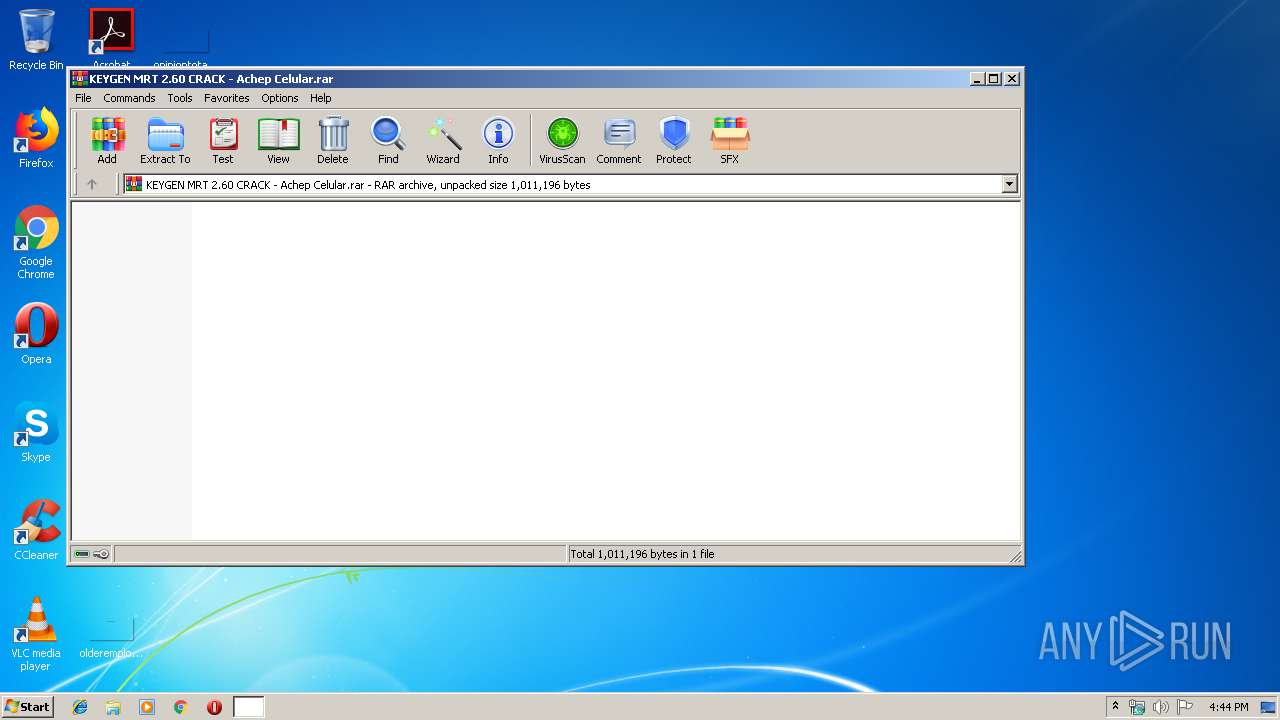
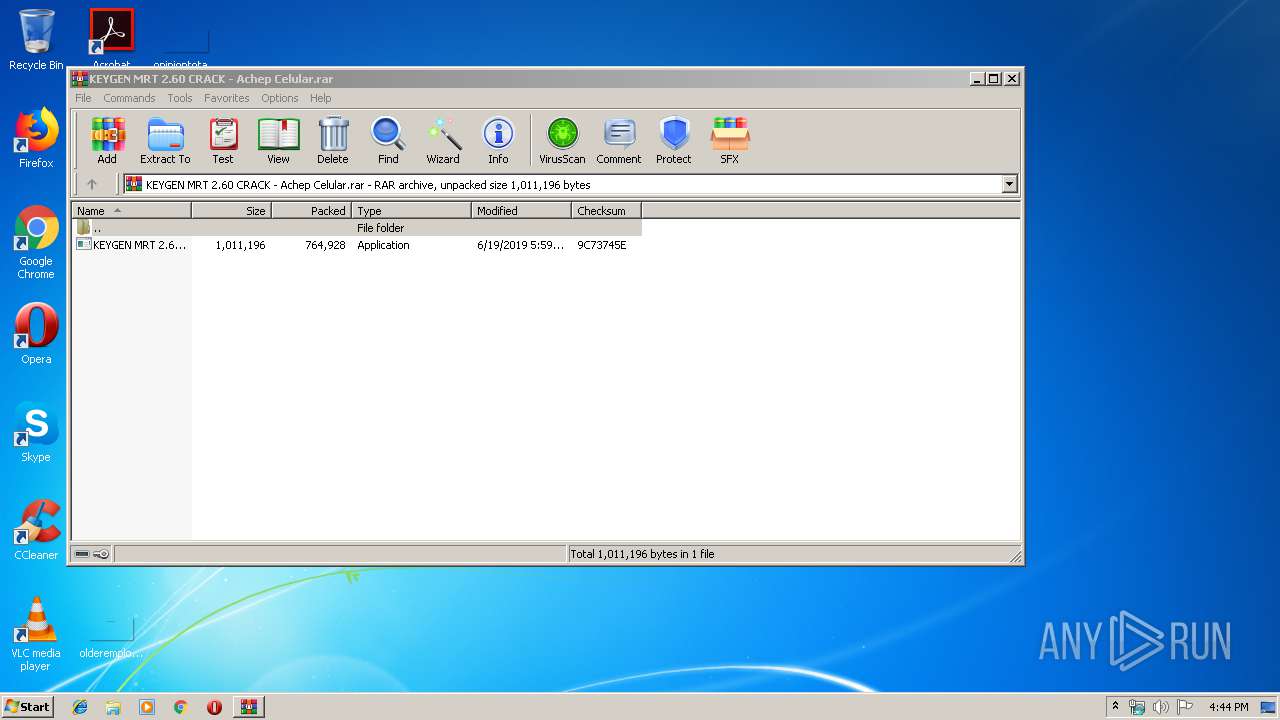
| File name: | KEYGEN MRT 2.60 CRACK - Achep Celular.rar |
| Full analysis: | https://app.any.run/tasks/0d7c3346-ac5c-4eaf-9bc2-c5a79724bf73 |
| Verdict: | No threats detected |
| Analysis date: | November 21, 2019, 16:43:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 907CE10B35EA328D38EE35BCAB71416D |
| SHA1: | 93CD1CB2F6A6B4E0918BD0B410D1067D2C0A93E6 |
| SHA256: | 8C091063656F3E540B97C1D2E0D325E849BC25A6A0D733392F04A6EB7A0BC919 |
| SSDEEP: | 12288:VVO1+4/vsa8lOPsV4llV5hnPzRyvRuGmYdief7p0CfLGY6+BRdMjgQns+VpAF62V:VVO1+JAP44llDRPzRyUGNdB1fLGY11ME |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Manual execution by user
- opera.exe (PID: 3928)
Creates files in the user directory
- opera.exe (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
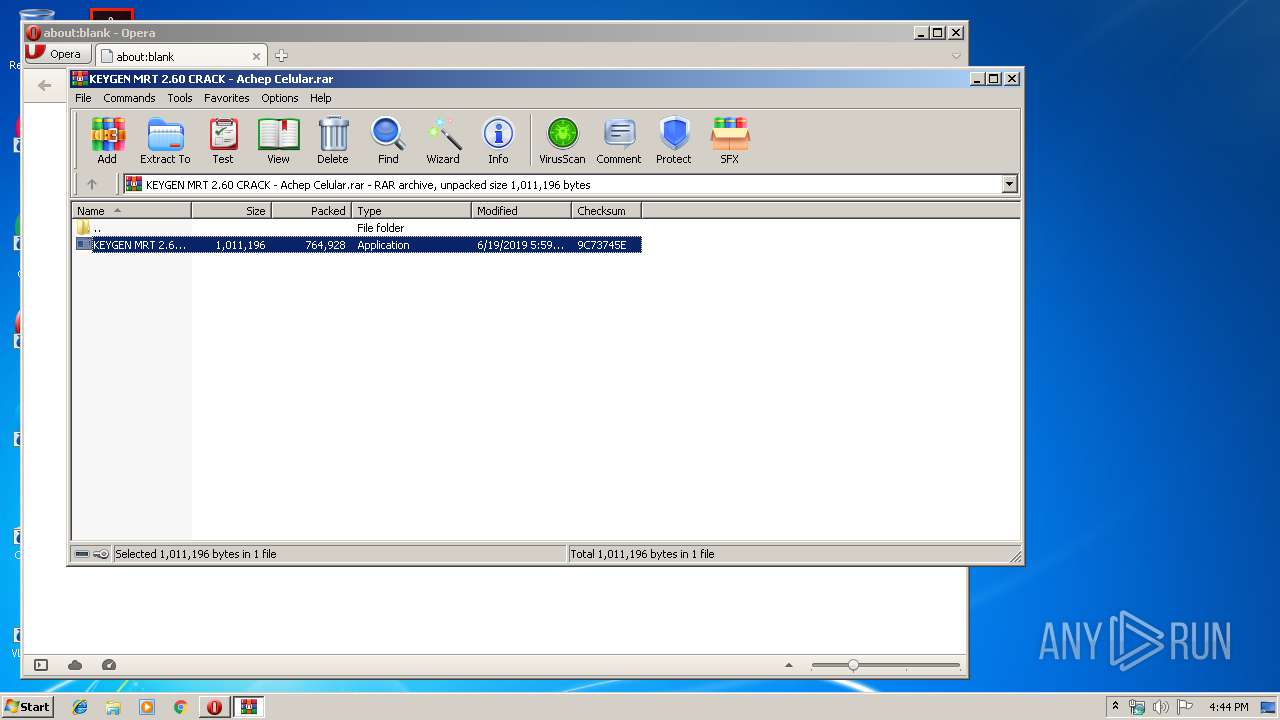
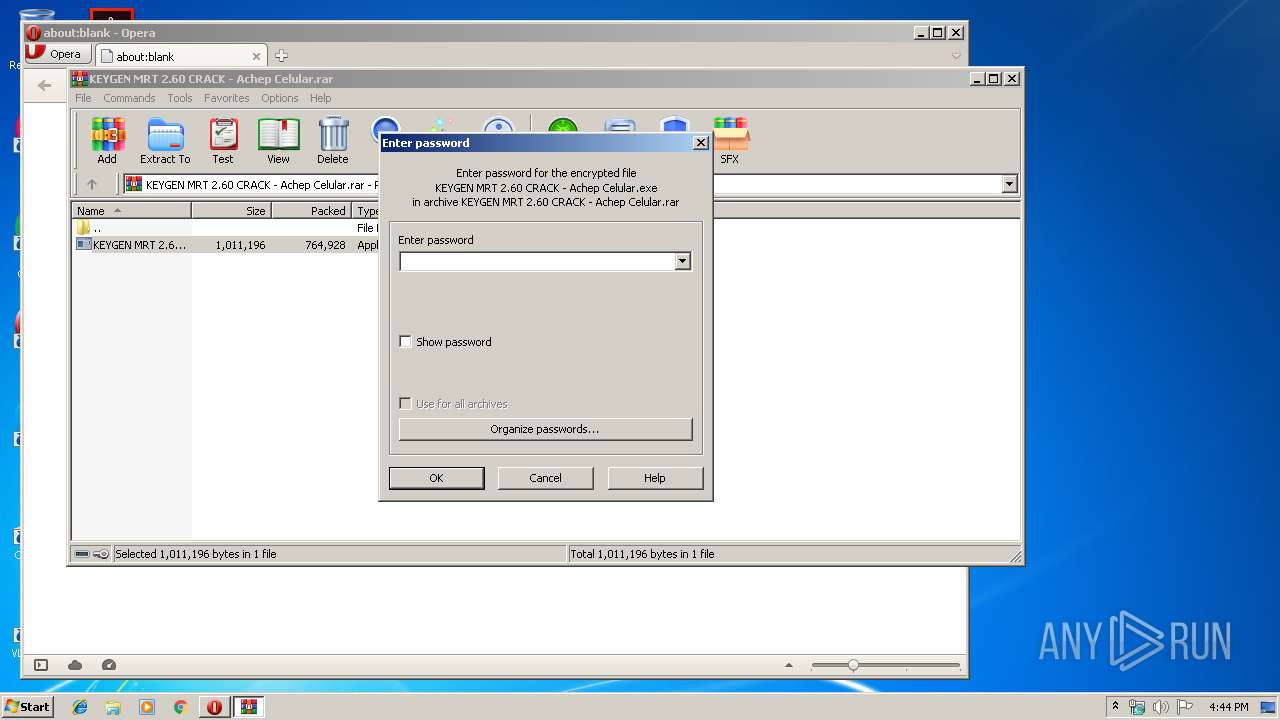
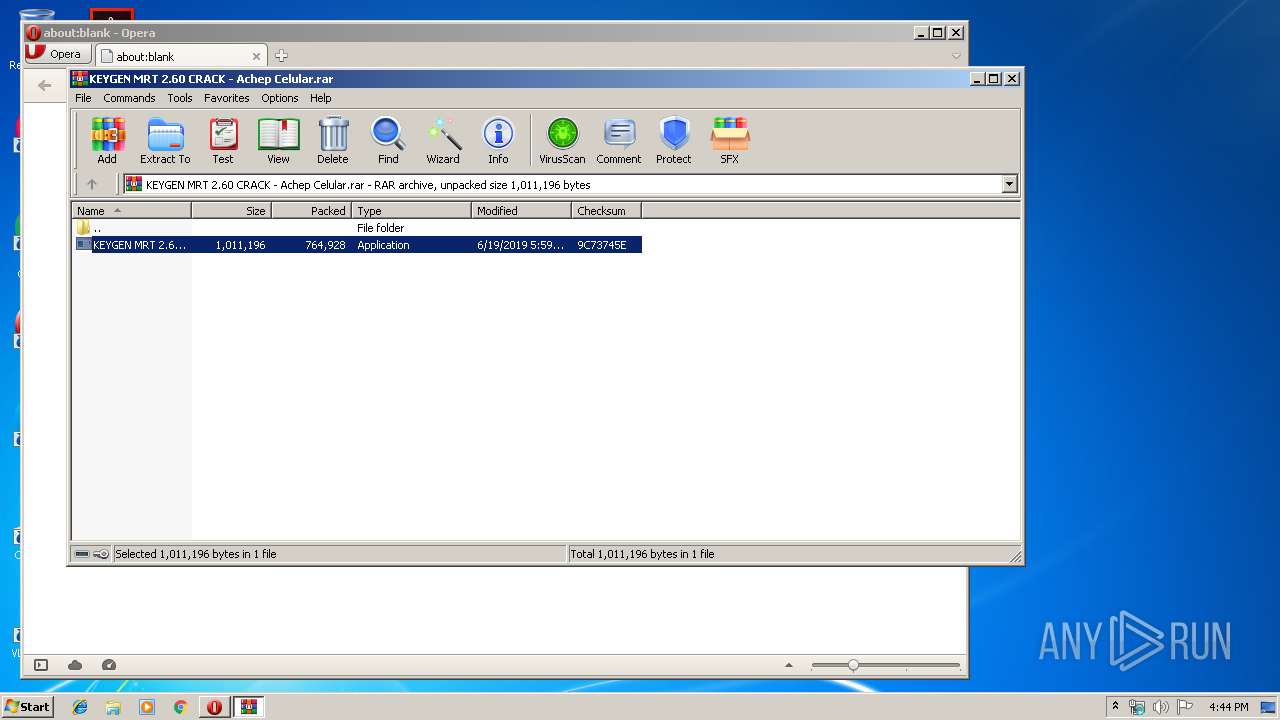
| 1648 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\KEYGEN MRT 2.60 CRACK - Achep Celular.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3928 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
635
Read events
557
Write events
78
Delete events
0
Modification events
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KEYGEN MRT 2.60 CRACK - Achep Celular.rar | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1648) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3928) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3928) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
23
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC752.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC782.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XFT6LZDTJRL9DNSG9XCH.temp | — | |
MD5:— | SHA256:— | |||
| 1648 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1648.15873\KEYGEN MRT 2.60 CRACK - Achep Celular.exe | — | |
MD5:— | SHA256:— | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr13ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:5FB367ABF6ED7507D871B665D8CA8E6F | SHA256:1FE76E9FB61A7D977F8D8857ED46B95D0C79B61BCCDA62B44D87CC5C7B333137 | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:214B1AF678519D9437606E566F2A809F | SHA256:86EFF0172D0DDD27AD4068777C9CFCF2803DB634E380C5F79EDADD82542972FE | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF39d2db.TMP | binary | |
MD5:214B1AF678519D9437606E566F2A809F | SHA256:86EFF0172D0DDD27AD4068777C9CFCF2803DB634E380C5F79EDADD82542972FE | |||
| 3928 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:74608439F87EB62B2B8EF3E17C52A366 | SHA256:7E262322EE2550A39B2548772E211EBAD9998D851638C23F45829EE4ECCC4732 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
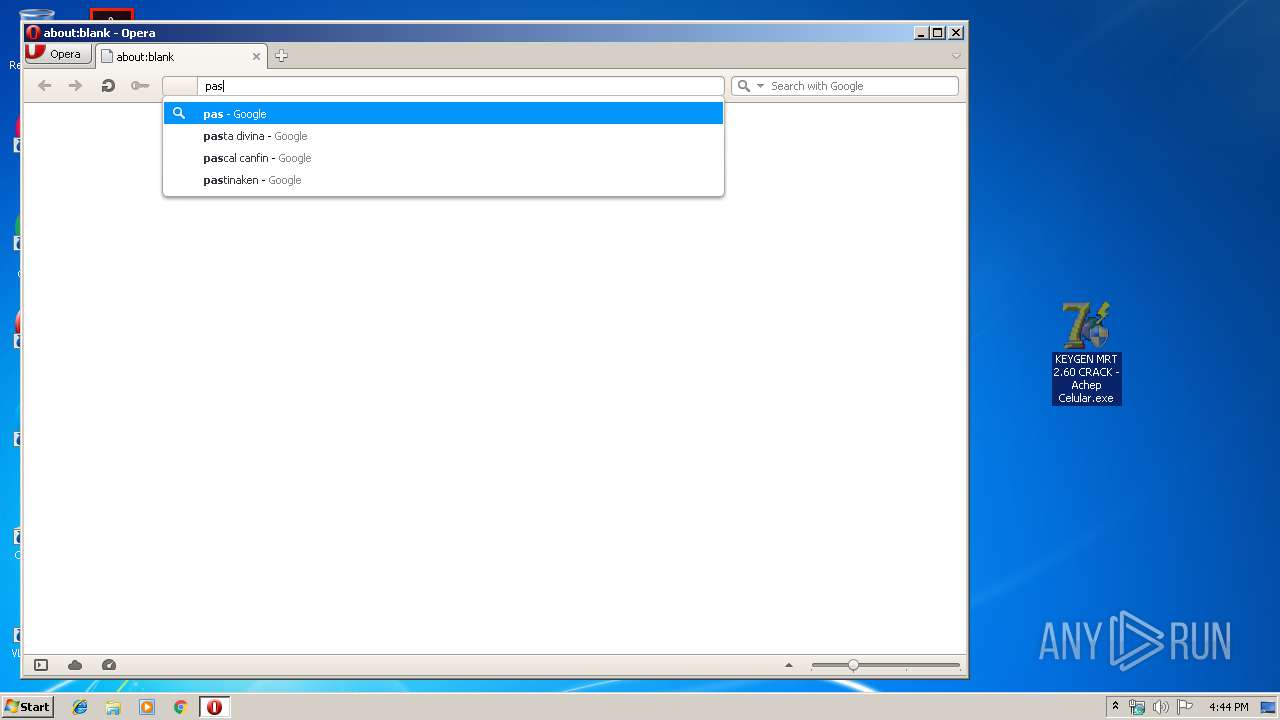
3928 | opera.exe | GET | 200 | 172.217.18.174:80 | http://clients1.google.com/complete/search?q=pas&client=opera-suggest-omnibox&hl=de | US | text | 117 b | whitelisted |
3928 | opera.exe | GET | 200 | 172.217.18.174:80 | http://clients1.google.com/complete/search?q=paste&client=opera-suggest-omnibox&hl=de | US | text | 98 b | whitelisted |
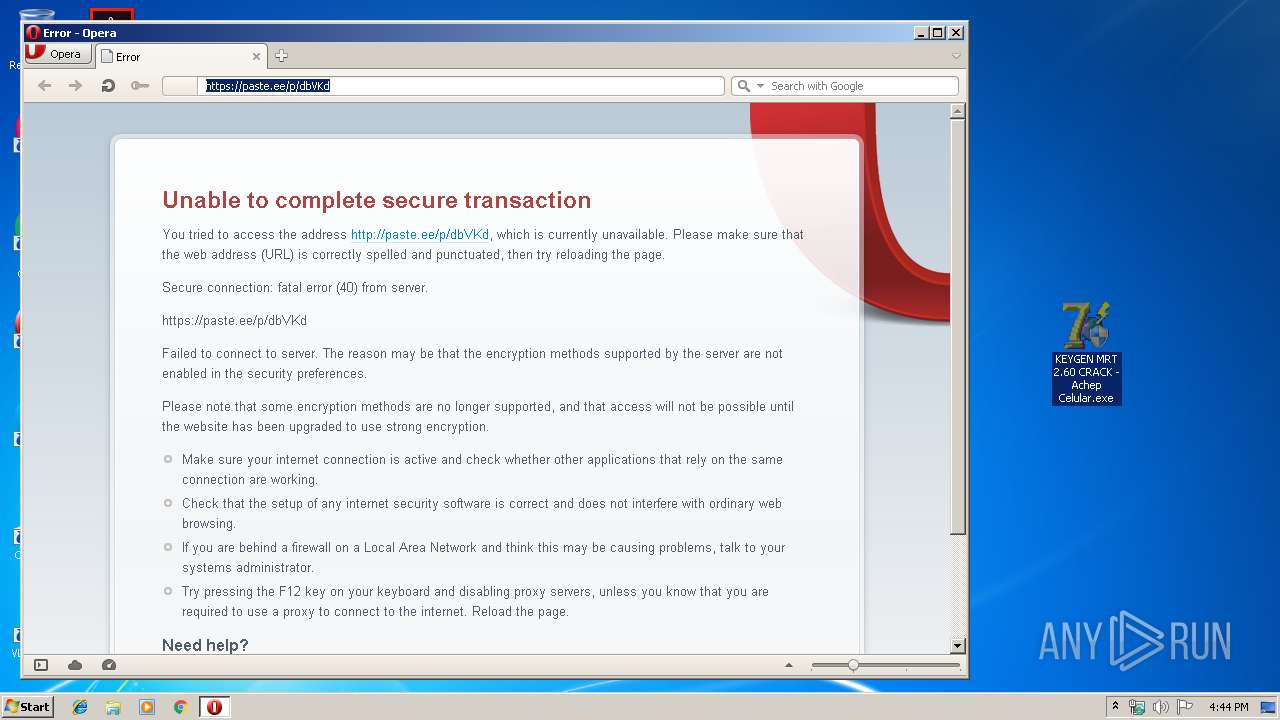
3928 | opera.exe | GET | 301 | 104.18.48.20:80 | http://paste.ee/p/dbVKd | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3928 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3928 | opera.exe | 172.217.18.174:80 | clients1.google.com | Google Inc. | US | whitelisted |
3928 | opera.exe | 107.167.110.216:80 | sitecheck2.opera.com | Opera Software Americas LLC | US | malicious |
3928 | opera.exe | 107.167.110.211:80 | sitecheck2.opera.com | Opera Software Americas LLC | US | suspicious |
3928 | opera.exe | 104.18.48.20:80 | paste.ee | Cloudflare Inc | US | shared |
3928 | opera.exe | 104.18.48.20:443 | paste.ee | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
paste.ee |
| malicious |
sitecheck2.opera.com |
| whitelisted |