| File name: | part_a73bef5ca4f69882a4e9214e09d85284f3720174f384825bdd828ee0952621bd.zip |
| Full analysis: | https://app.any.run/tasks/4b82344c-b5f4-4951-8a01-7d708357ddd8 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 15:07:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 02210EF4B6F80FB1D80D1993D1371BD9 |
| SHA1: | 64FF2A5E6A0D494ED521EC1BCC5BA4294BA45979 |
| SHA256: | 8BEFC85A67A6963D2F8442D167E6851155F40FAC559DA0AADE2D6ABE4D440151 |
| SSDEEP: | 192:M18yw0E+sAjWh/Ibb6KdJ52mhZBRayTw+hXykDyaU+4:JH0j5RNJ52mhZBs0XyFaH4 |
MALICIOUS
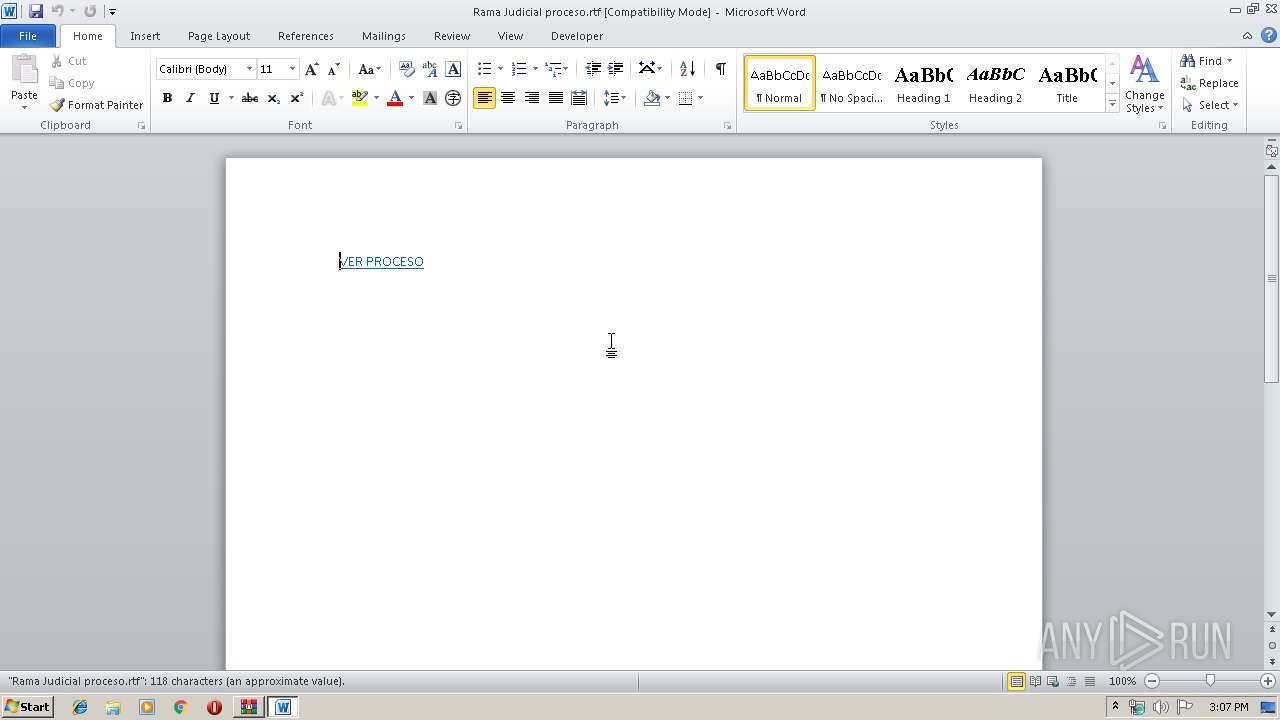
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 236)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 2344)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 236)
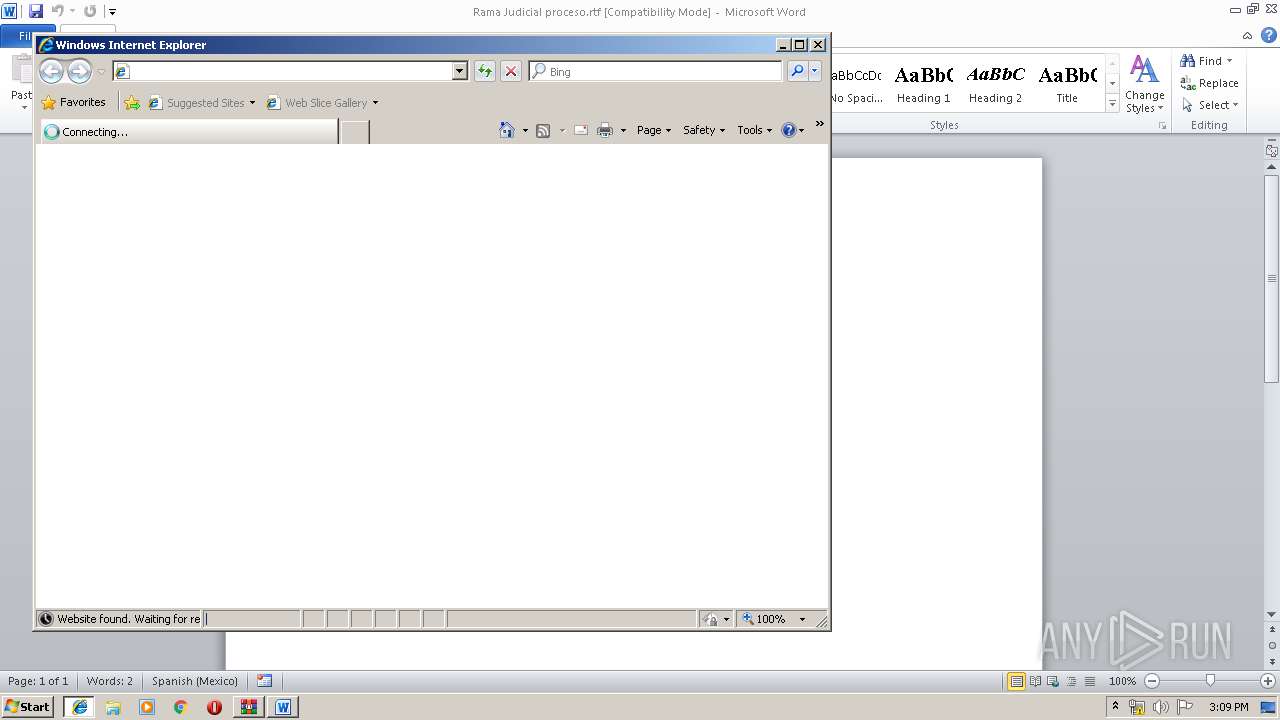
Starts Internet Explorer
- WINWORD.EXE (PID: 236)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 236)
Changes internet zones settings
- iexplore.exe (PID: 2060)
- iexplore.exe (PID: 1516)
Reads Internet Cache Settings
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 1876)
Creates files in the user directory
- WINWORD.EXE (PID: 236)
Reads settings of System Certificates
- WINWORD.EXE (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:08 15:07:02 |
| ZipCRC: | 0xf50512f9 |
| ZipCompressedSize: | 8784 |
| ZipUncompressedSize: | 40954 |
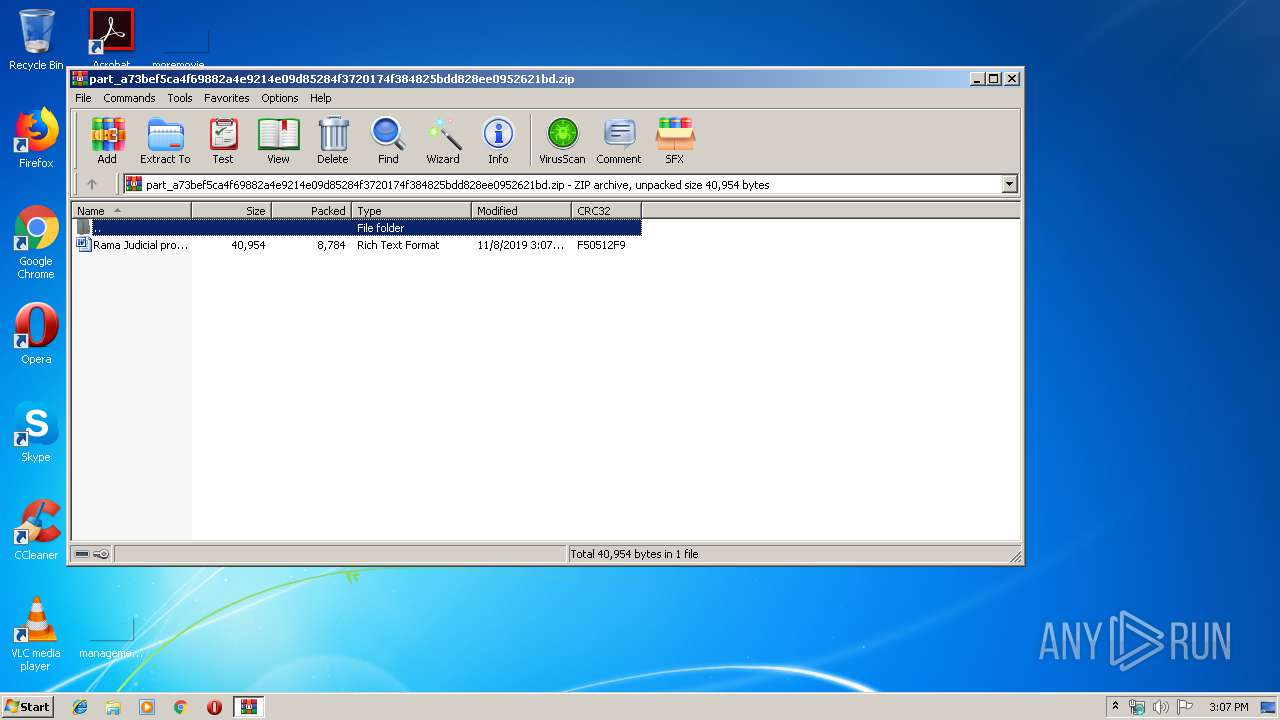
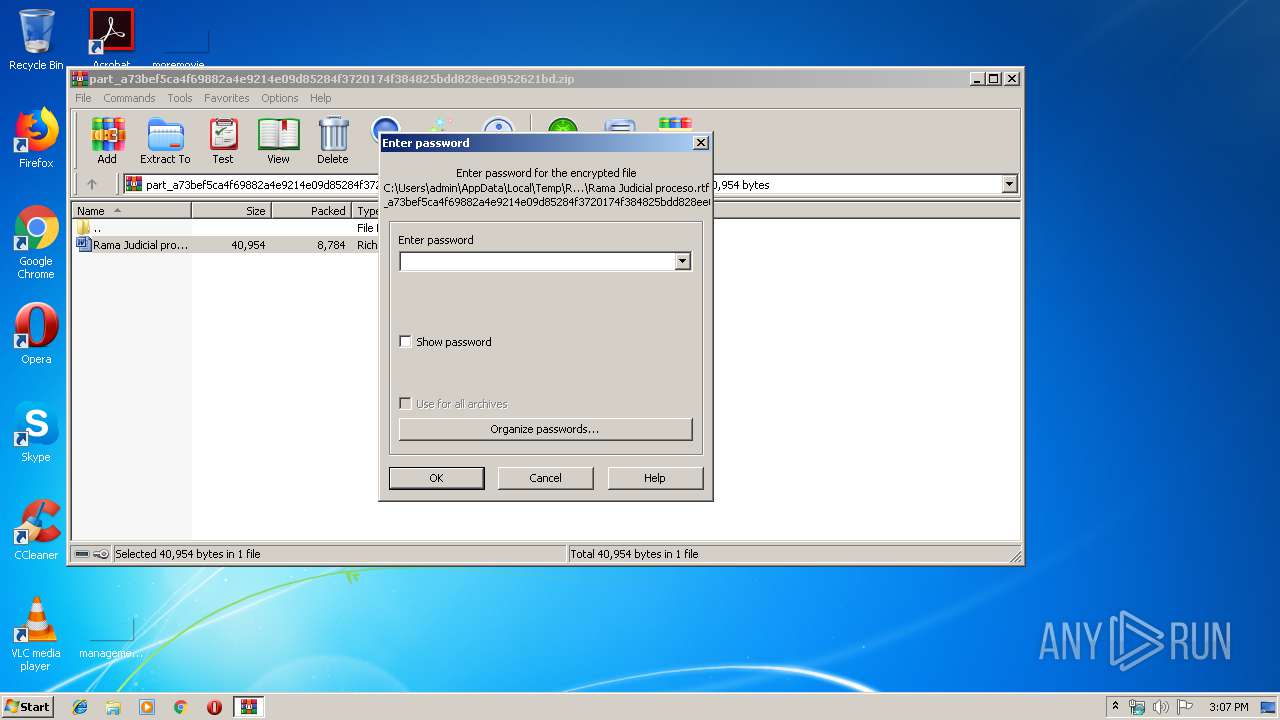
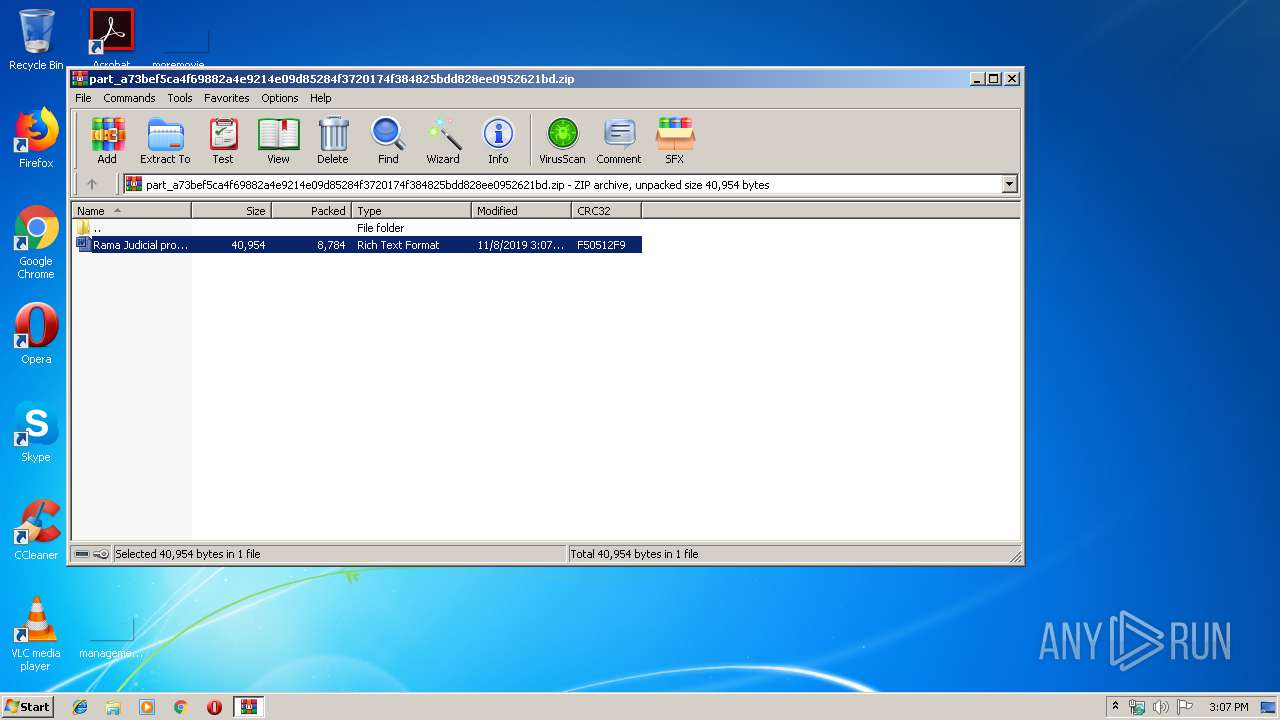
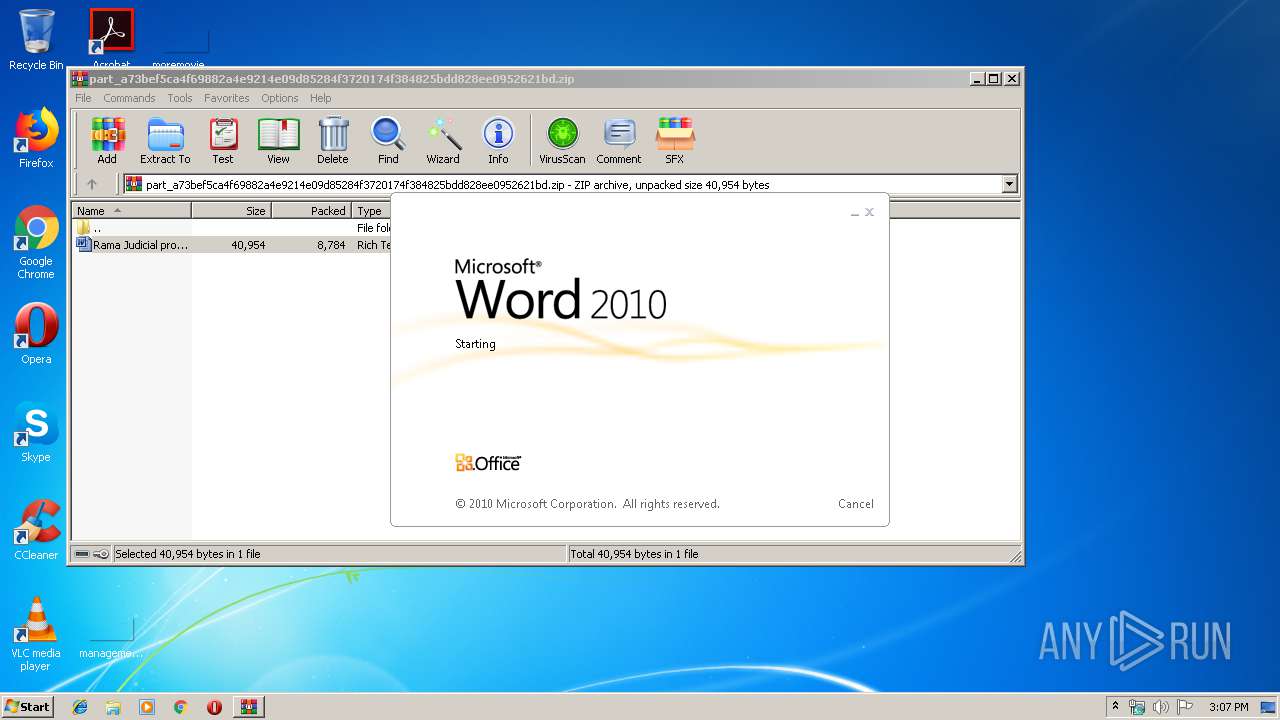
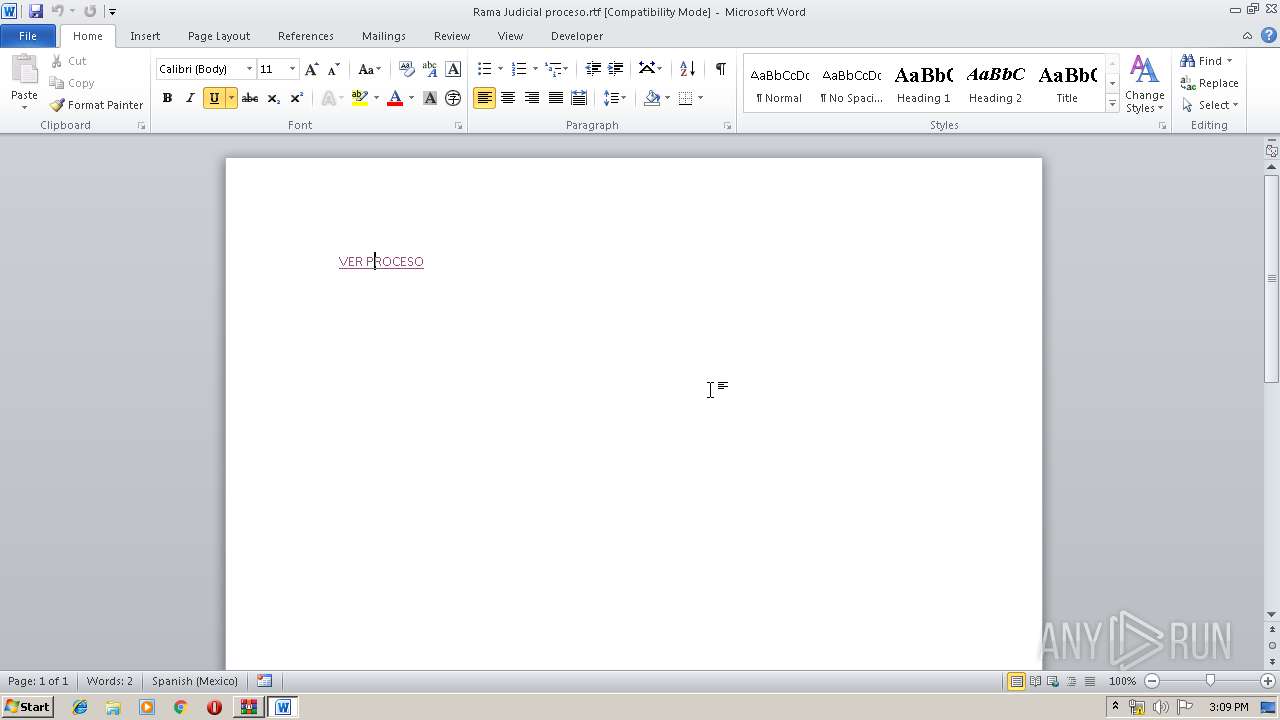
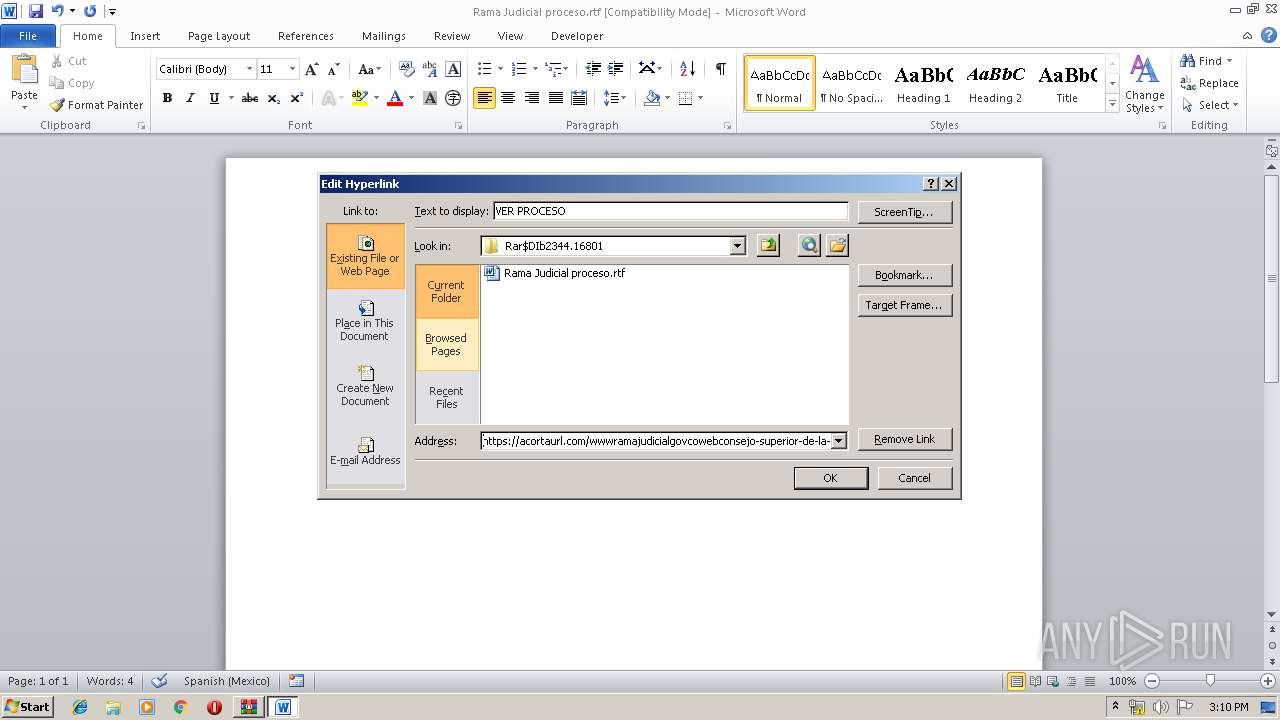
| ZipFileName: | Rama Judicial proceso.rtf |
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2344.16801\Rama Judicial proceso.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2060 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\part_a73bef5ca4f69882a4e9214e09d85284f3720174f384825bdd828ee0952621bd.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1516 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 144
Read events
1 994
Write events
1 017
Delete events
133
Modification events
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\part_a73bef5ca4f69882a4e9214e09d85284f3720174f384825bdd828ee0952621bd.zip | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2344) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
0
Suspicious files
3
Text files
11
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD377.tmp.cvr | — | |
MD5:— | SHA256:— | |||
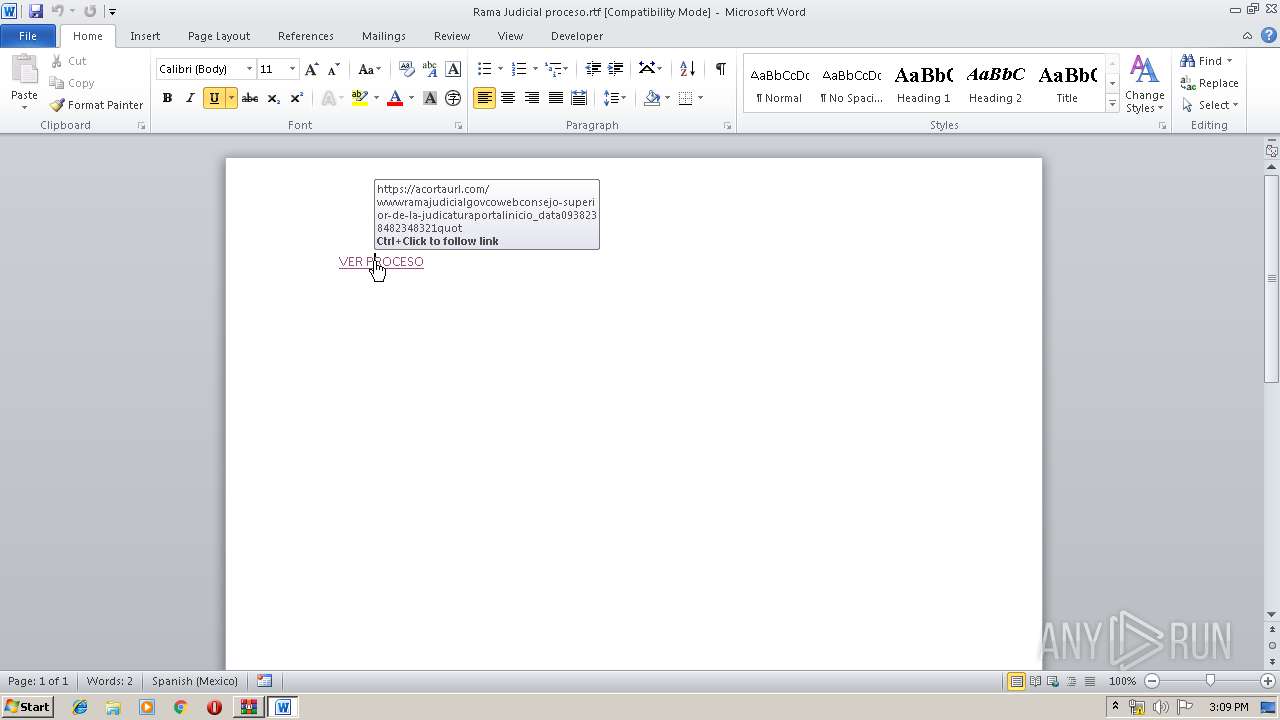
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@acortaurl[1].txt | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@mediafire[1].txt | — | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB33BD7AEF499CF41.TMP | — | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDA5C281D962DBB9F.TMP | — | |
MD5:— | SHA256:— | |||
| 2060 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{A9DC174D-0239-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC2E8116788FF616E.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
9
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
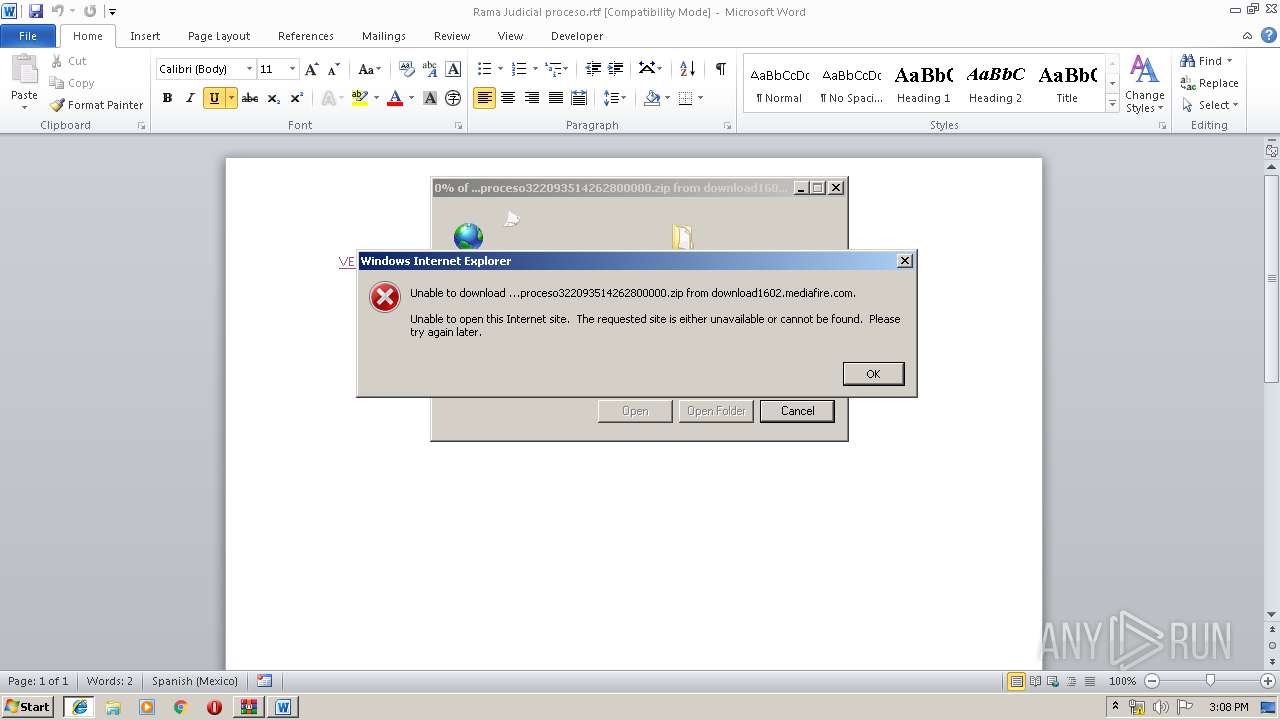
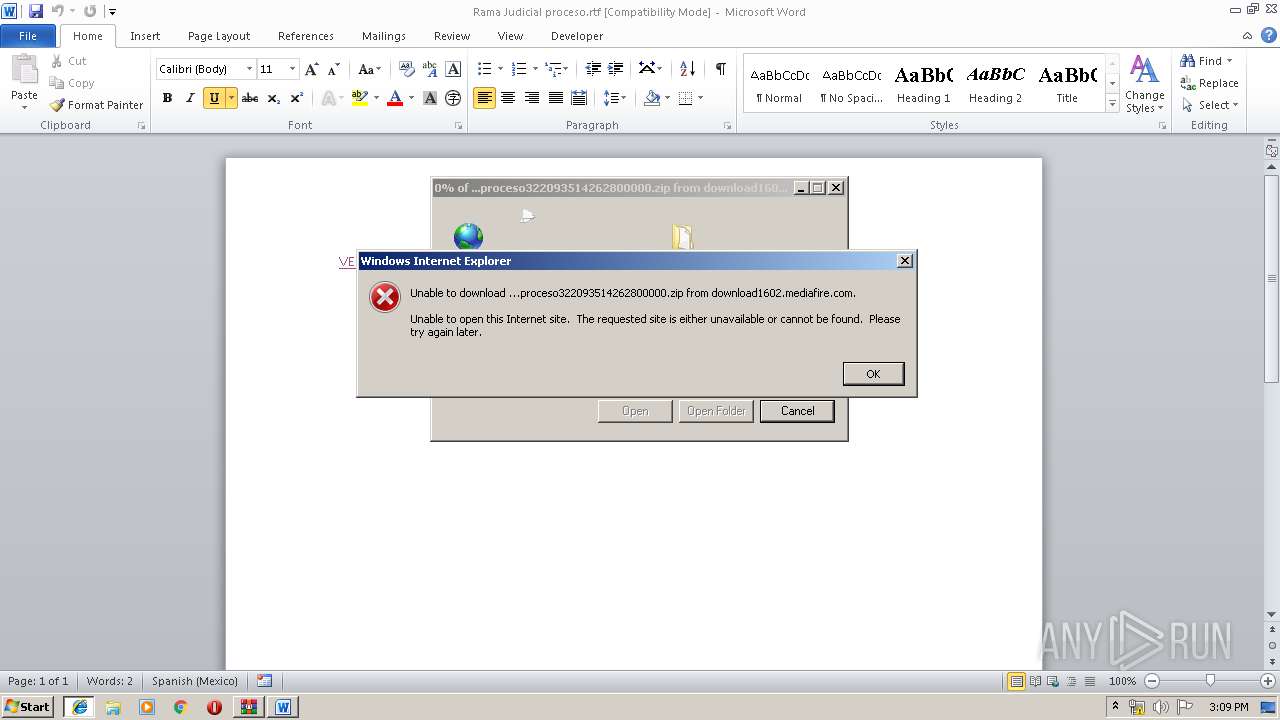
236 | WINWORD.EXE | GET | — | 199.91.152.102:80 | http://download1602.mediafire.com/68bcgycct1og/61axhom6fjrlru9/docproceso322093514262800000.zip | US | — | — | unknown |
236 | WINWORD.EXE | GET | 302 | 104.16.202.237:80 | http://www.mediafire.com/file/61axhom6fjrlru9/docproceso322093514262800000.zip/file | US | — | — | shared |
236 | WINWORD.EXE | GET | 302 | 104.16.202.237:80 | http://www.mediafire.com/file/61axhom6fjrlru9/docproceso322093514262800000.zip/file | US | — | — | shared |
2504 | iexplore.exe | GET | 200 | 199.91.152.102:80 | http://download1602.mediafire.com/68bcgycct1og/61axhom6fjrlru9/docproceso322093514262800000.zip | US | compressed | 655 Kb | unknown |
1876 | iexplore.exe | GET | 200 | 199.91.152.102:80 | http://download1602.mediafire.com/68bcgycct1og/61axhom6fjrlru9/docproceso322093514262800000.zip | US | compressed | 655 Kb | unknown |
236 | WINWORD.EXE | GET | — | 199.91.152.102:80 | http://download1602.mediafire.com/68bcgycct1og/61axhom6fjrlru9/docproceso322093514262800000.zip | US | — | — | unknown |
2060 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | iexplore.exe | 199.91.152.102:80 | download1602.mediafire.com | MediaFire, LLC | US | unknown |
1876 | iexplore.exe | 199.91.152.102:80 | download1602.mediafire.com | MediaFire, LLC | US | unknown |
2060 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
236 | WINWORD.EXE | 199.91.152.102:80 | download1602.mediafire.com | MediaFire, LLC | US | unknown |
236 | WINWORD.EXE | 104.24.114.152:443 | acortaurl.com | Cloudflare Inc | US | shared |
236 | WINWORD.EXE | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acortaurl.com |
| whitelisted |
www.mediafire.com |
| shared |
download1602.mediafire.com |
| unknown |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2504 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |