| File name: | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871 |
| Full analysis: | https://app.any.run/tasks/714ad6dd-a2c5-473f-9524-43b81d4173b2 |
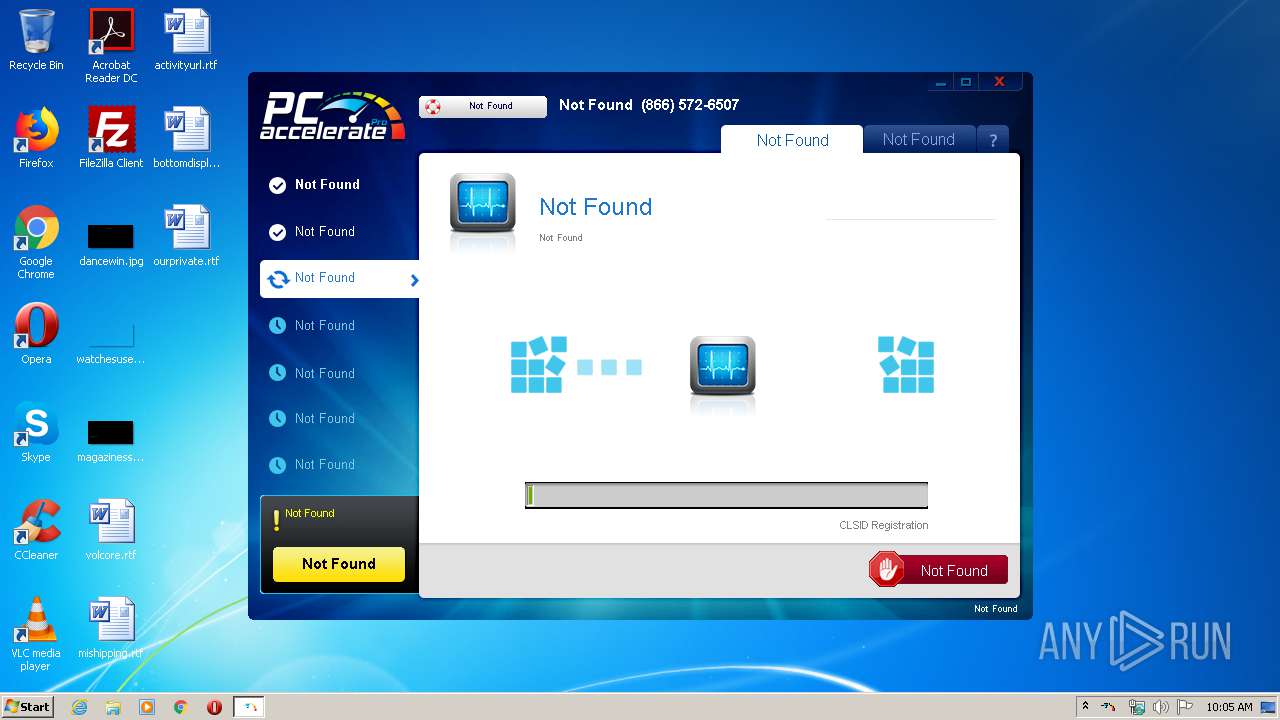
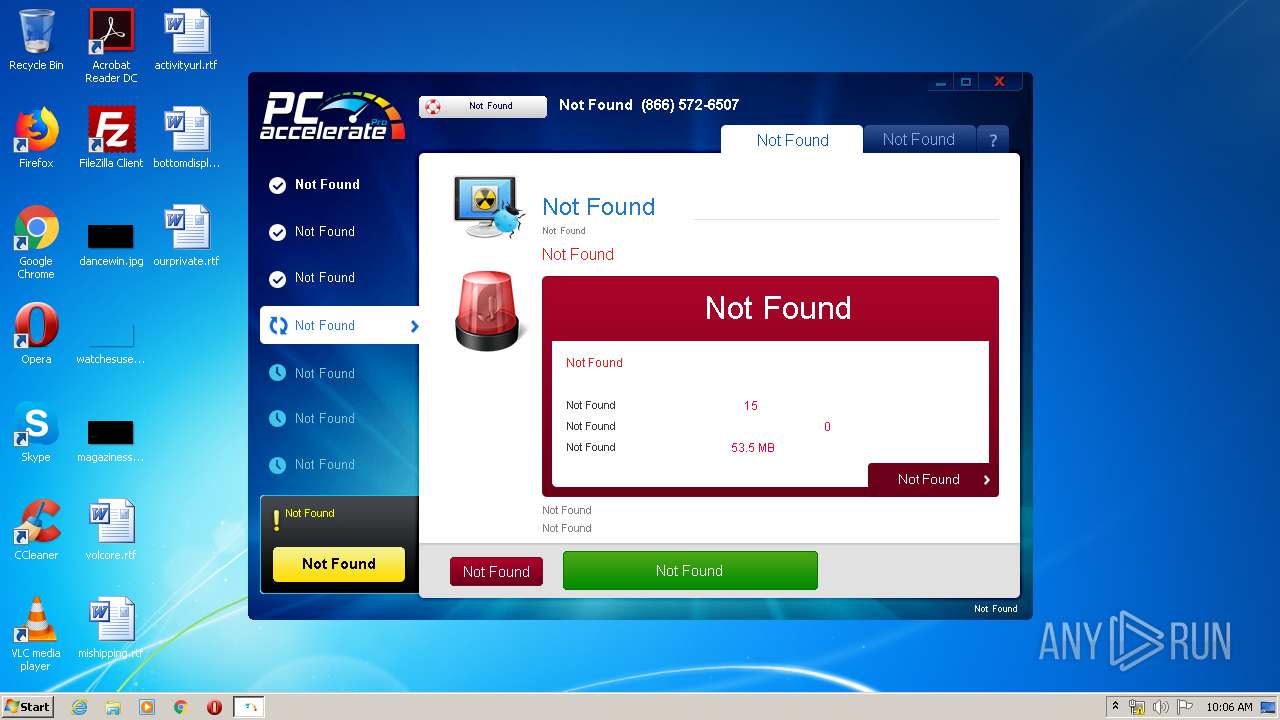
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2020, 10:05:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2616EEA8A95464614CB81F8DC7F24D5E |
| SHA1: | 577B828664A671E2B1DB9A10A9AB2D7A7F53C4B7 |
| SHA256: | 8BE6021B7893875C989D466B1A0A2BD6EB912B19D3CBC3626E5D5D16AFF63871 |
| SSDEEP: | 98304:1wjWLi36/UWvA8yTvKwnpkNa8q0oyHJh1kGNXxTLo64+pl+/Hy:MqC7KwA0Uh1kGNXxTLHOS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Changes IE settings (feature browser emulation)
- 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe (PID: 3824)
Reads Internet Cache Settings
- 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe (PID: 3824)
Creates files in the user directory
- 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe (PID: 3824)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (21.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.1) |
| .exe | | | Win32 Executable (generic) (2.3) |
| .exe | | | Generic Win/DOS Executable (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:08 11:06:11+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2582016 |
| InitializedDataSize: | 2778624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14d620 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5.6 |
| ProductVersionNumber: | 1.0.5.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | bPCAPq Bits |
| FileDescription: | bPCAPq |
| InternalName: | bPCAPq |
| OriginalFileName: | bPCAPq |
| ProductName: | bPCAPq |
| FileVersion: | 1.0.5.06 |
| LegalCopyright: | (C) 2020 bPCAPq Bits |
| ProductVersion: | 1.0.5.06 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Mar-2020 10:06:11 |
| Detected languages: |
|
| CompanyName: | bPCAPq Bits |
| FileDescription: | bPCAPq |
| InternalName: | bPCAPq |
| OriginalFilename: | bPCAPq |
| ProductName: | bPCAPq |
| FileVersion: | 1.0.5.06 |
| LegalCopyright: | (C) 2020 bPCAPq Bits |
| ProductVersion: | 1.0.5.06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 08-Mar-2020 10:06:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00259E89 | 0x0025A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43373 |
.flj7rl | 0x0025B000 | 0x0000C681 | 0x0000C800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03475 |
.qank20 | 0x00268000 | 0x0000FD24 | 0x0000FE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.00732 |
.rdata | 0x00278000 | 0x0007A86E | 0x0007AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08454 |
.data | 0x002F3000 | 0x00020350 | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.72017 |
.rsrc | 0x00314000 | 0x00198880 | 0x00198A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.26133 |
.reloc | 0x004AD000 | 0x00072CAA | 0x00072E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.26359 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17402 | 1974 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.70687 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 1.59267 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 5.14664 | 4232 | UNKNOWN | English - United States | RT_ICON |
5 | 4.50079 | 3548 | UNKNOWN | English - United States | RT_ICON |
6 | 3.02745 | 1712 | UNKNOWN | English - United States | RT_ICON |
7 | 5.15662 | 3616 | UNKNOWN | English - United States | RT_ICON |
8 | 6.94403 | 368 | UNKNOWN | English - United States | RT_ICON |
9 | 3.90096 | 2000 | UNKNOWN | English - United States | RT_ICON |
10 | 5.46337 | 10112 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SETUPAPI.dll |
SHELL32.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3824 | "C:\Users\admin\AppData\Local\Temp\8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe" | C:\Users\admin\AppData\Local\Temp\8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | explorer.exe | ||||||||||||
User: admin Company: bPCAPq Bits Integrity Level: MEDIUM Description: bPCAPq Exit code: 0 Version: 1.0.5.06 Modules
| |||||||||||||||
Total events
458
Read events
436
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe |
Value: 9999 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\bPCAPq |
| Operation: | write | Name: | SrvcHrtBt |
Value: 202003121005 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3824) 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Key: | HKEY_CURRENT_USER\Software\APCTab |
| Operation: | write | Name: | hb |
Value: 1 | |||
Executable files
0
Suspicious files
5
Text files
33
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8QU1CQCK.txt | — | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Local\8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871\t001.dat | — | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Local\Temp\CabAE0B.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Local\Temp\TarAE0C.tmp | — | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Local\8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871\8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.cfg | text | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\1UAOJV3W.txt | text | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | binary | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9EC3B71635F8BA3FC68DE181A104A0EF_F6C39EF89D8A3A72327D8412589658B2 | der | |
MD5:— | SHA256:— | |||
| 3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\WQ37RWQU.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 172.245.127.171:80 | http://config.instantsupport.help/api/get_phone/pcap/05c9df37f97e18faf584e2fa7dedf91d | US | text | 88 b | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 104.18.184.70:80 | http://pcacceleratepro.com/clamav.php | US | text | 26 b | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=dpi_96&c=0&id=05c9df37f97e18faf584e2fa7dedf91d&t=12100544&v=506&aff= | US | binary | 1 b | suspicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=hb&c=0&id=05c9df37f97e18faf584e2fa7dedf91d&t=12100544&v=506&aff= | US | binary | 1 b | suspicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 104.17.205.32:80 | http://spywaremaid.com/wsm.dat | US | binary | 30.9 Kb | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 104.17.205.32:80 | http://spywaremaid.com/whitelist?smv=1.0.1.2&wlv=0.0&id=05c9df37f97e18faf584e2fa7dedf91d | US | text | 30 b | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | POST | 200 | 104.16.216.36:80 | http://softremoval.pcaccel.com/extensions | US | text | 4 b | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=rs&c=137&id=05c9df37f97e18faf584e2fa7dedf91d&t=12100610&v=506&aff= | US | binary | 1 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 172.245.127.102:80 | softwarehelpdata.com | ColoCrossing | US | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 104.17.205.32:80 | spywaremaid.com | Cloudflare Inc | US | shared |
— | — | 104.18.184.70:80 | pcacceleratepro.com | Cloudflare Inc | US | shared |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 104.17.233.32:443 | backend.driver-fixer.com | Cloudflare Inc | US | shared |
— | — | 172.245.127.102:80 | softwarehelpdata.com | ColoCrossing | US | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 172.245.127.171:80 | config.instantsupport.help | ColoCrossing | US | malicious |
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | 104.16.216.36:80 | softremoval.pcaccel.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
spywaremaid.com |
| malicious |
pcacceleratepro.com |
| malicious |
softwarehelpdata.com |
| suspicious |
config.instantsupport.help |
| malicious |
softremoval.pcaccel.com |
| malicious |
backend.driver-fixer.com |
| suspicious |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3824 | 8be6021b7893875c989d466b1a0a2bd6eb912b19d3cbc3626e5d5d16aff63871.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |